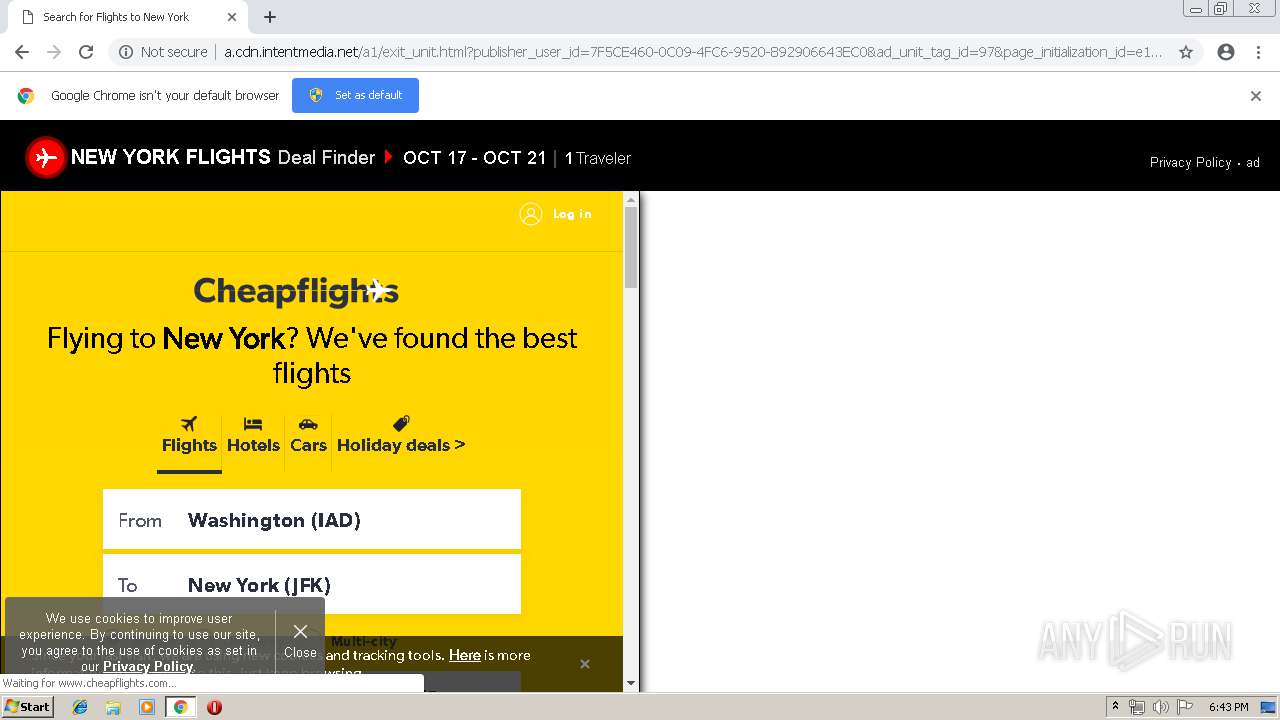
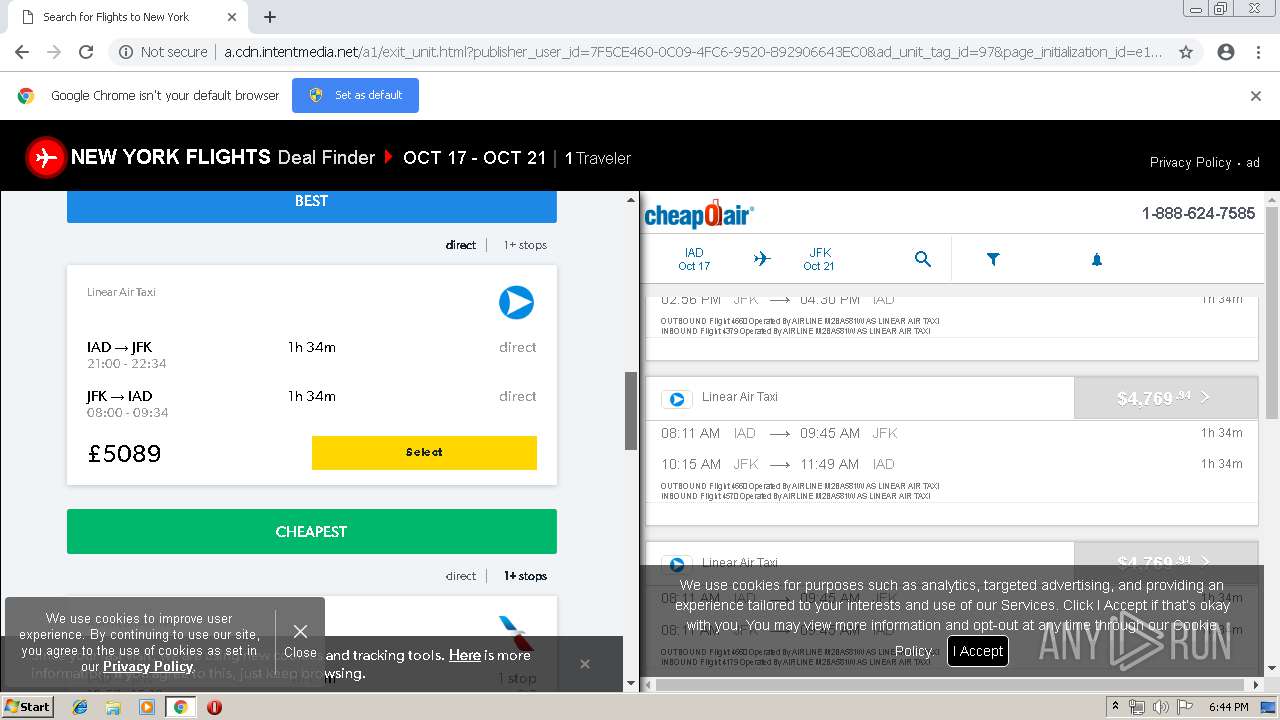
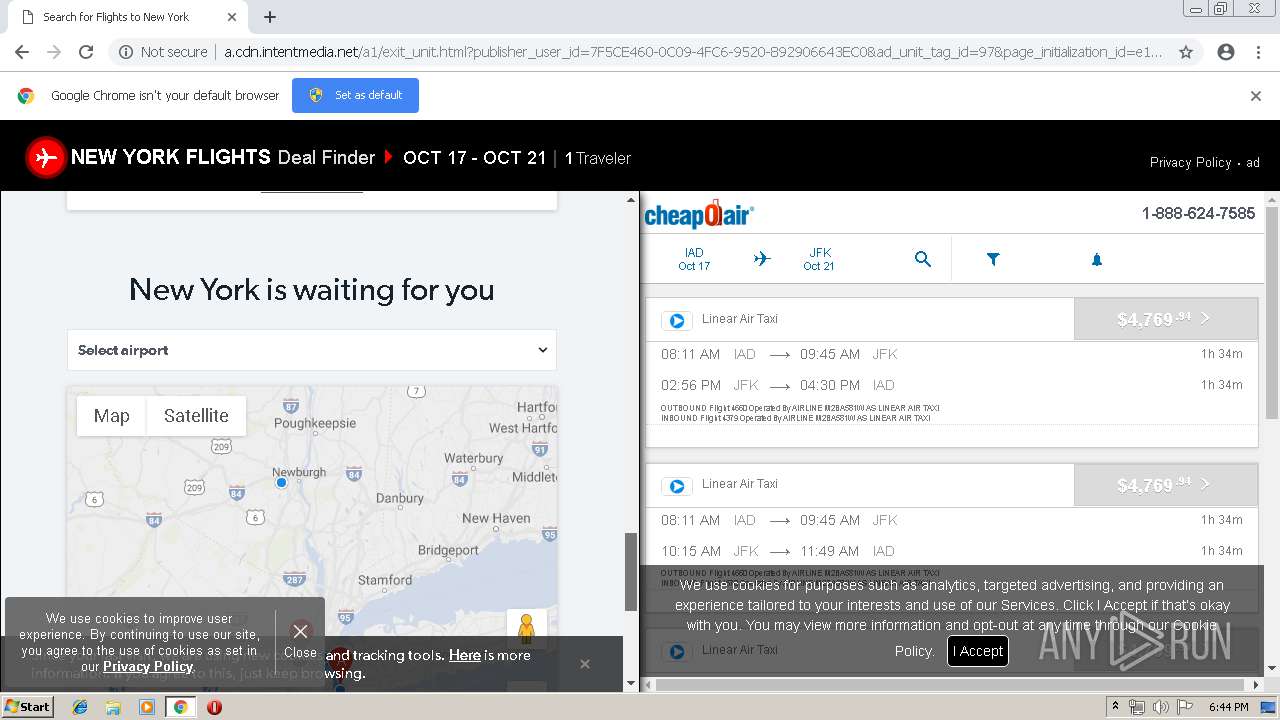
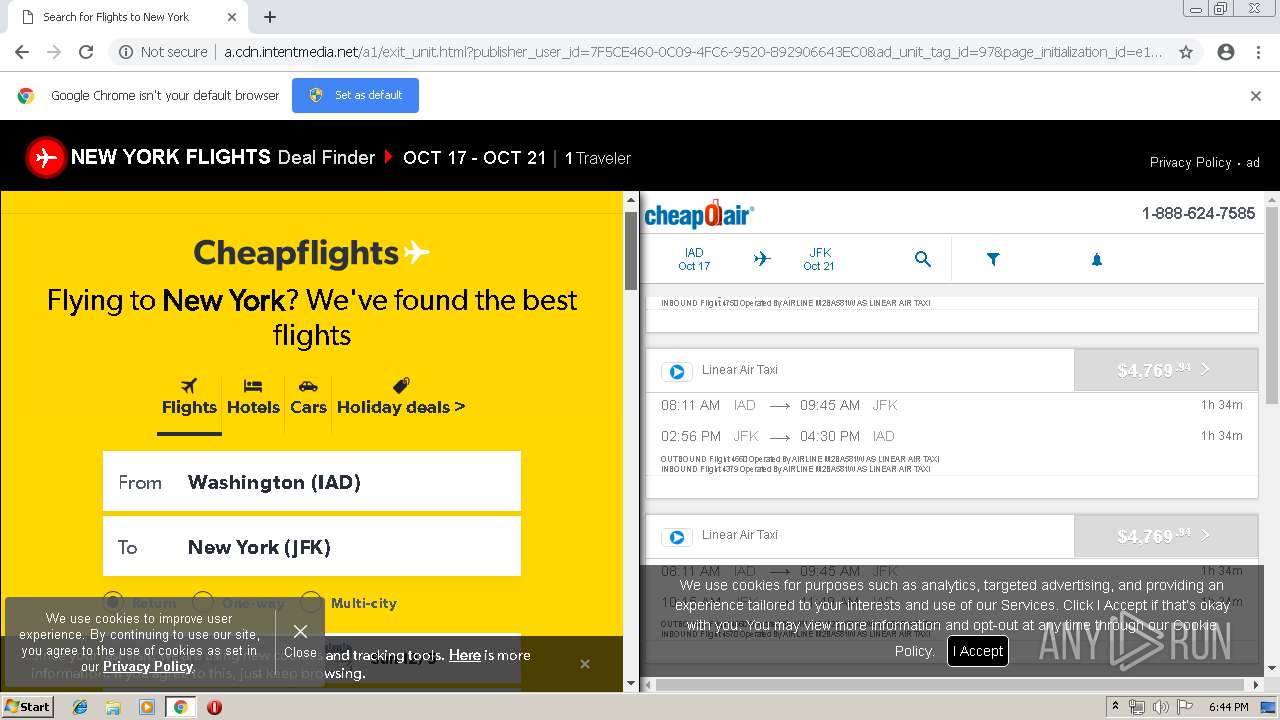
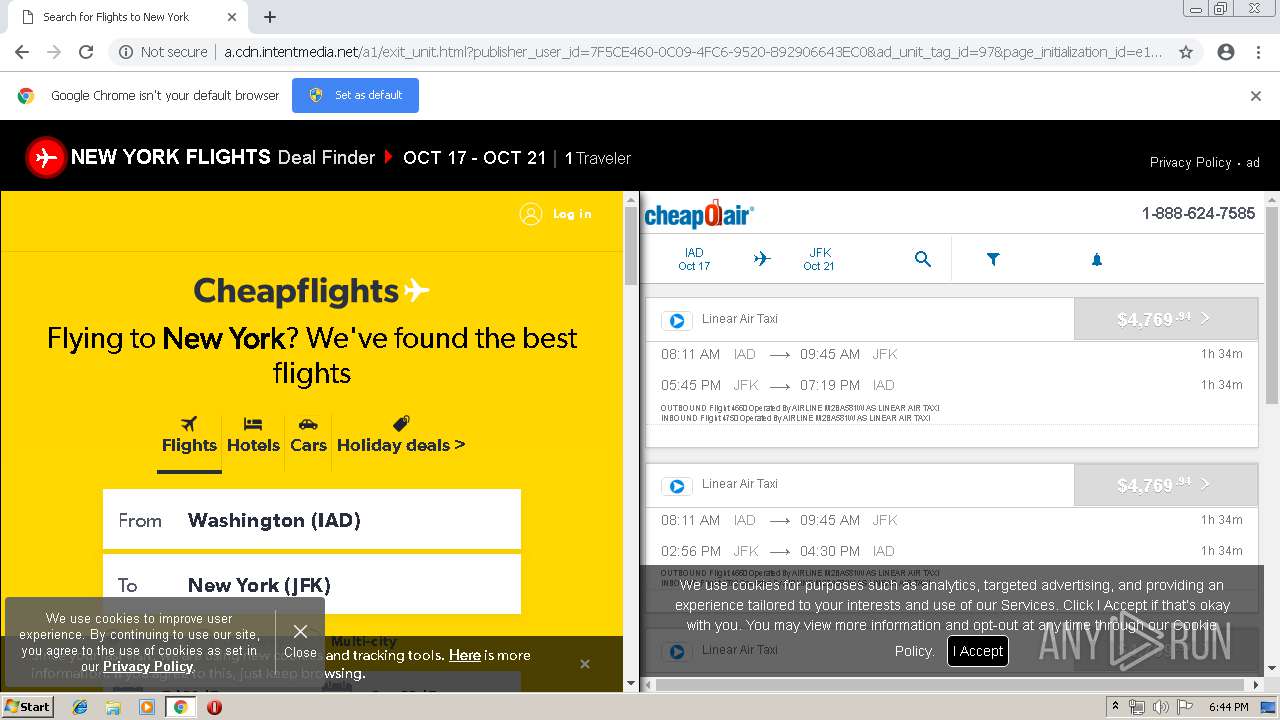
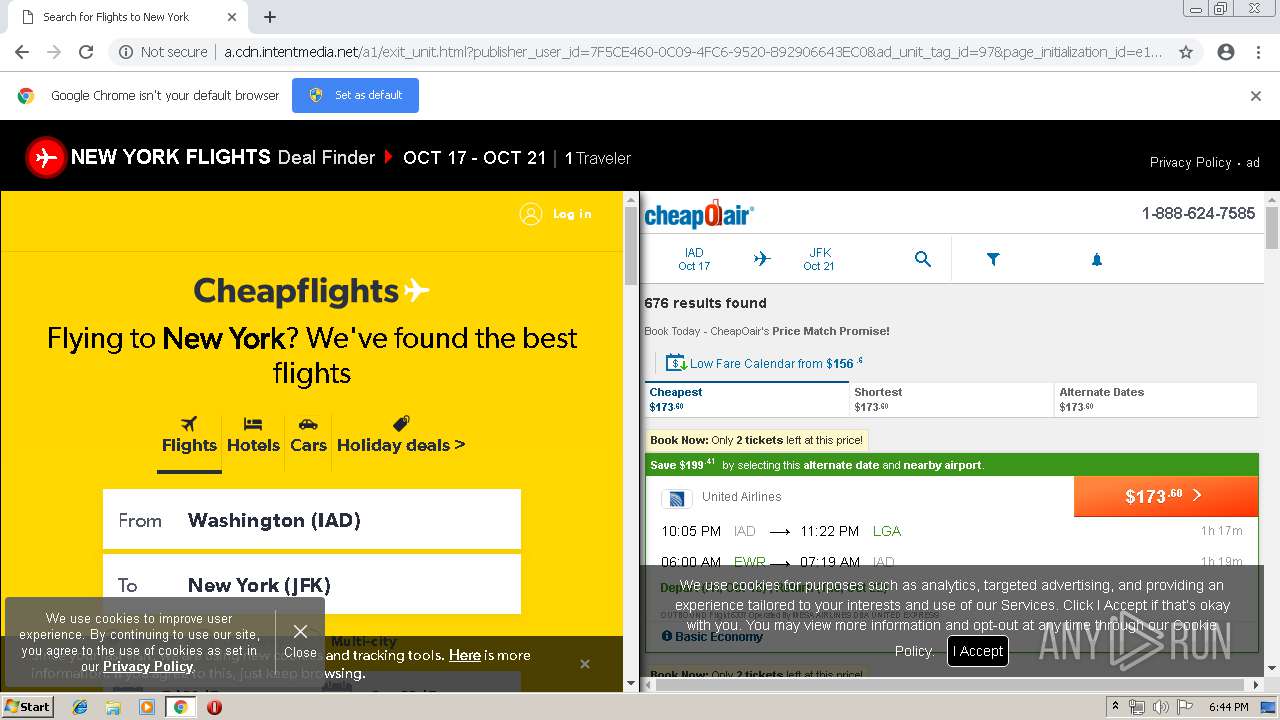
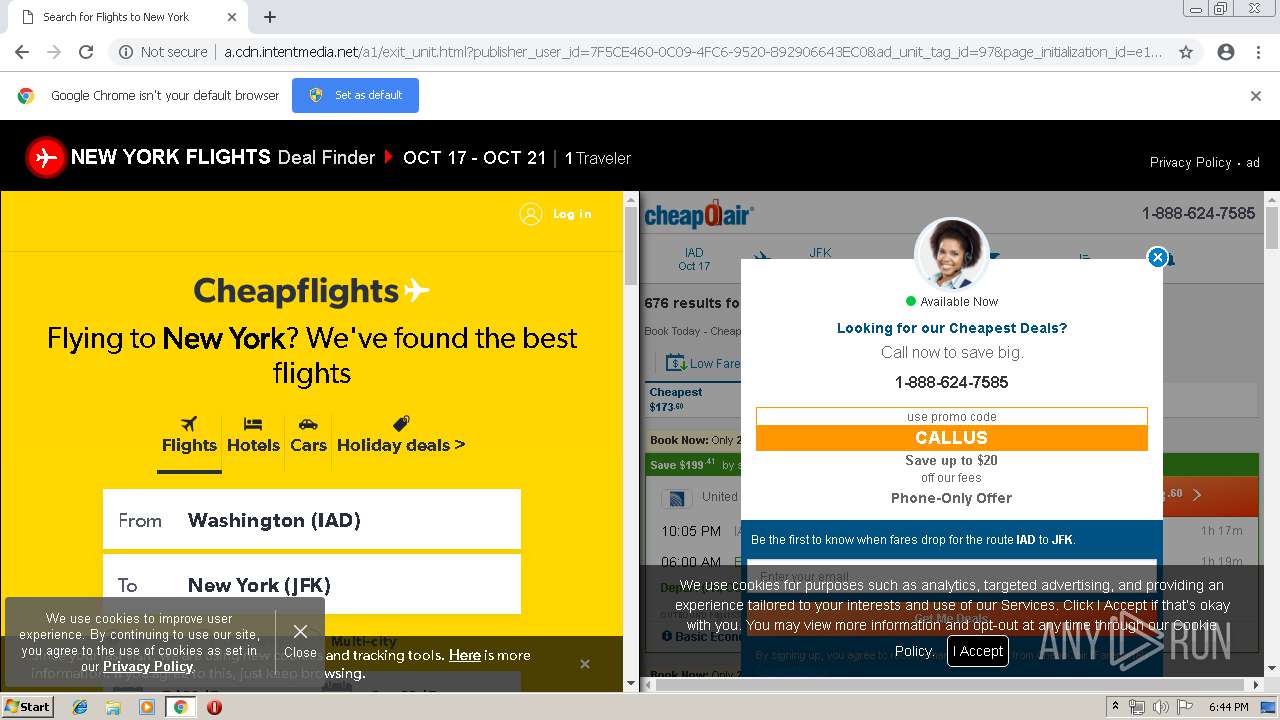
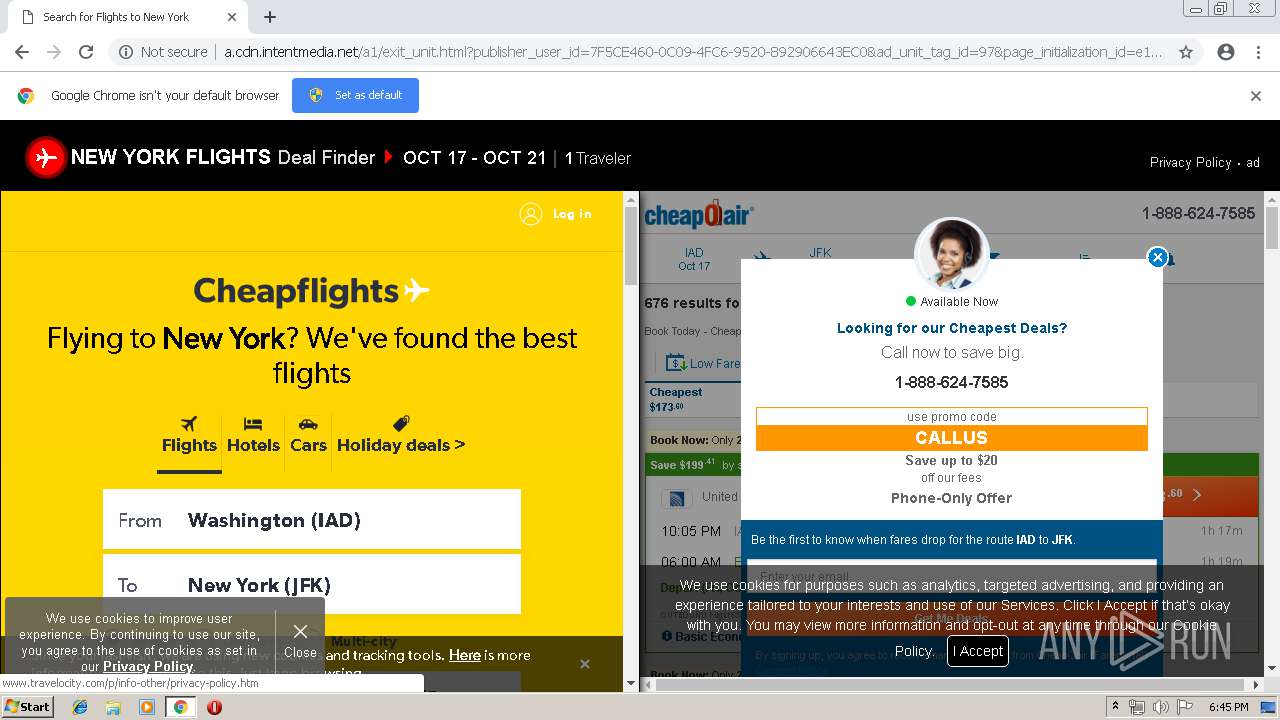
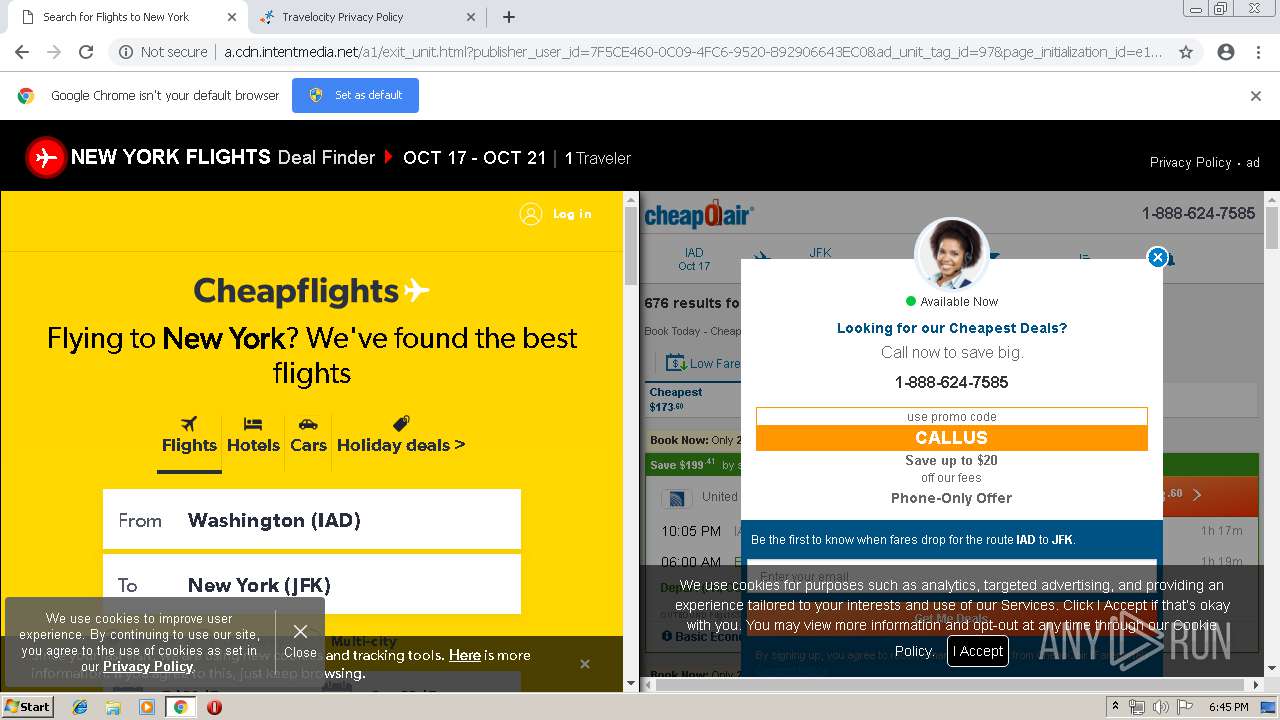
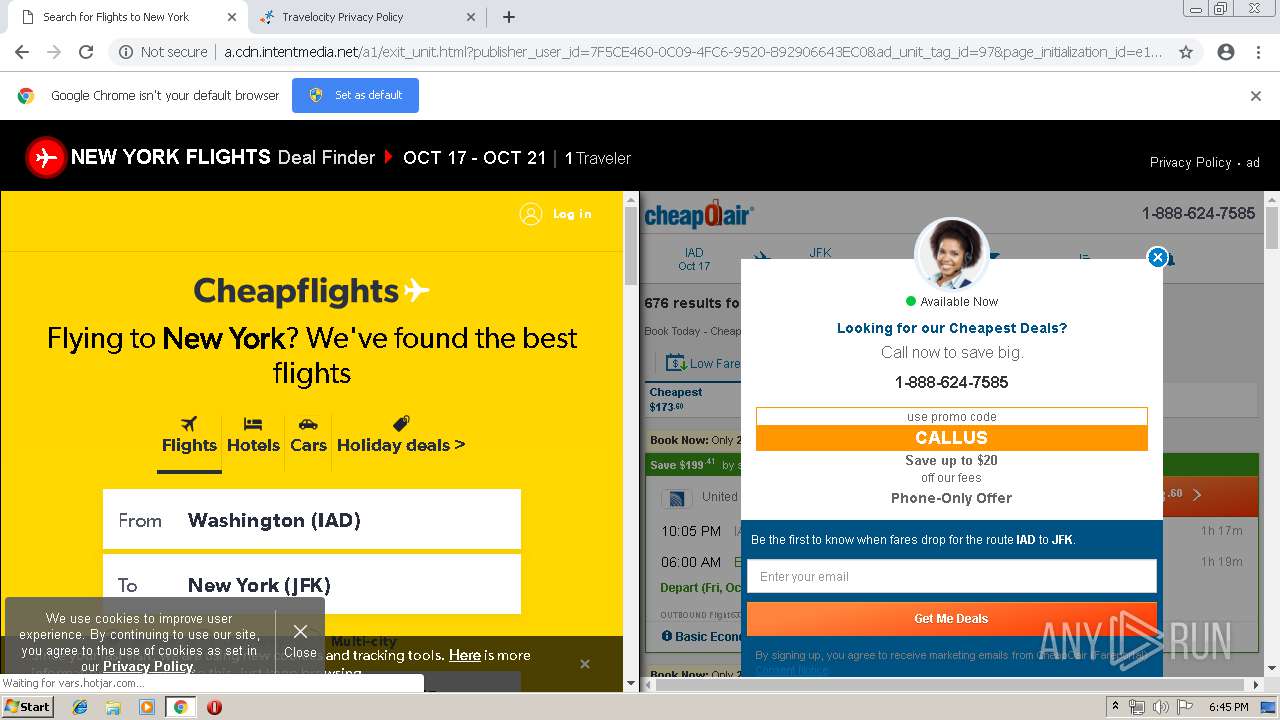
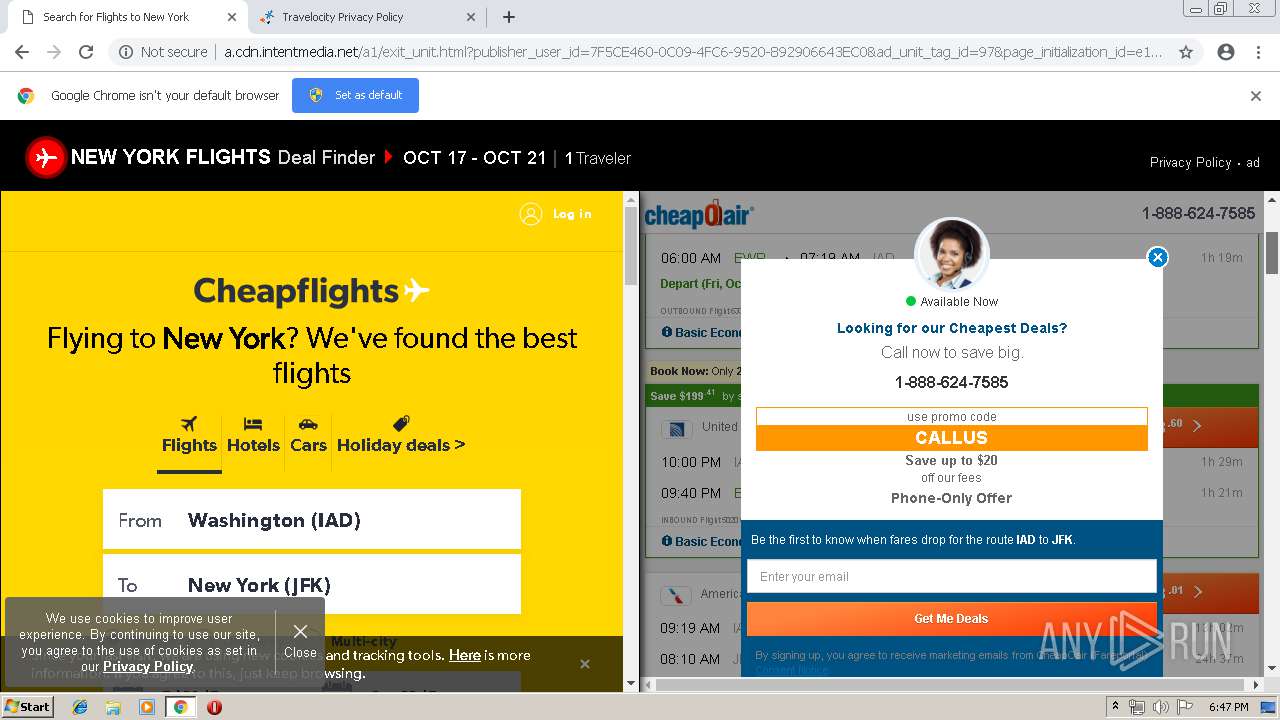
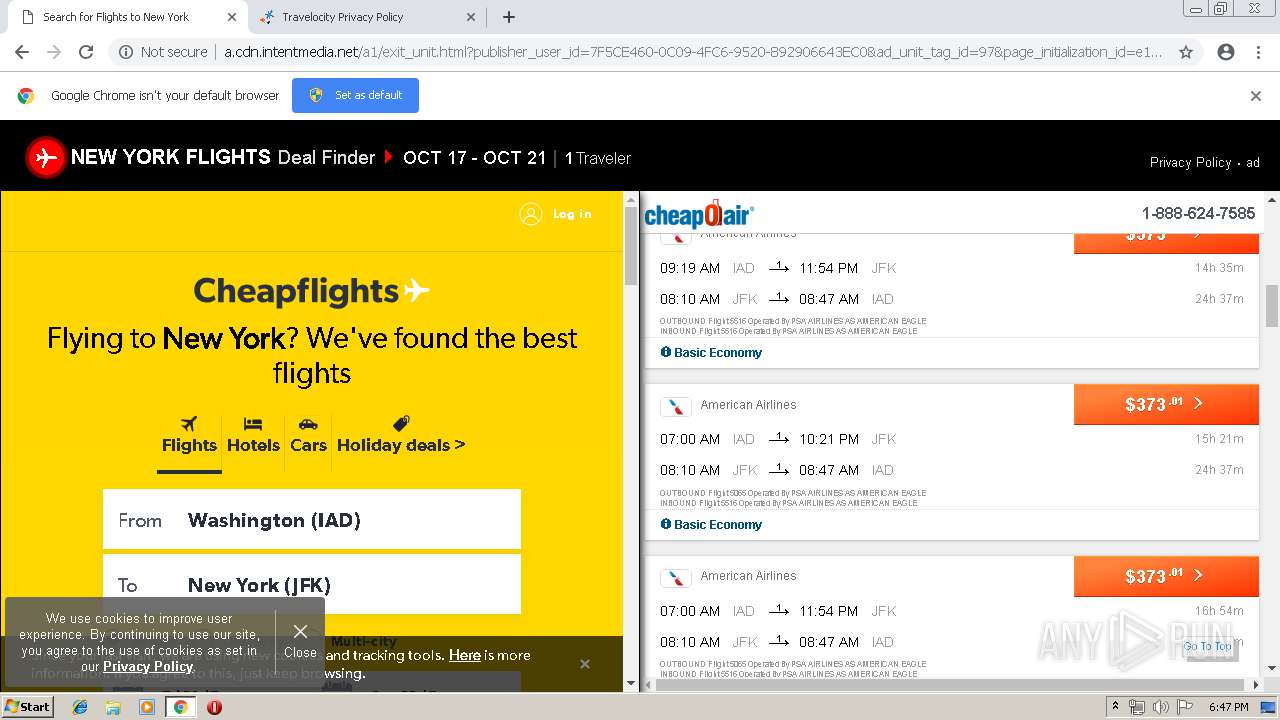
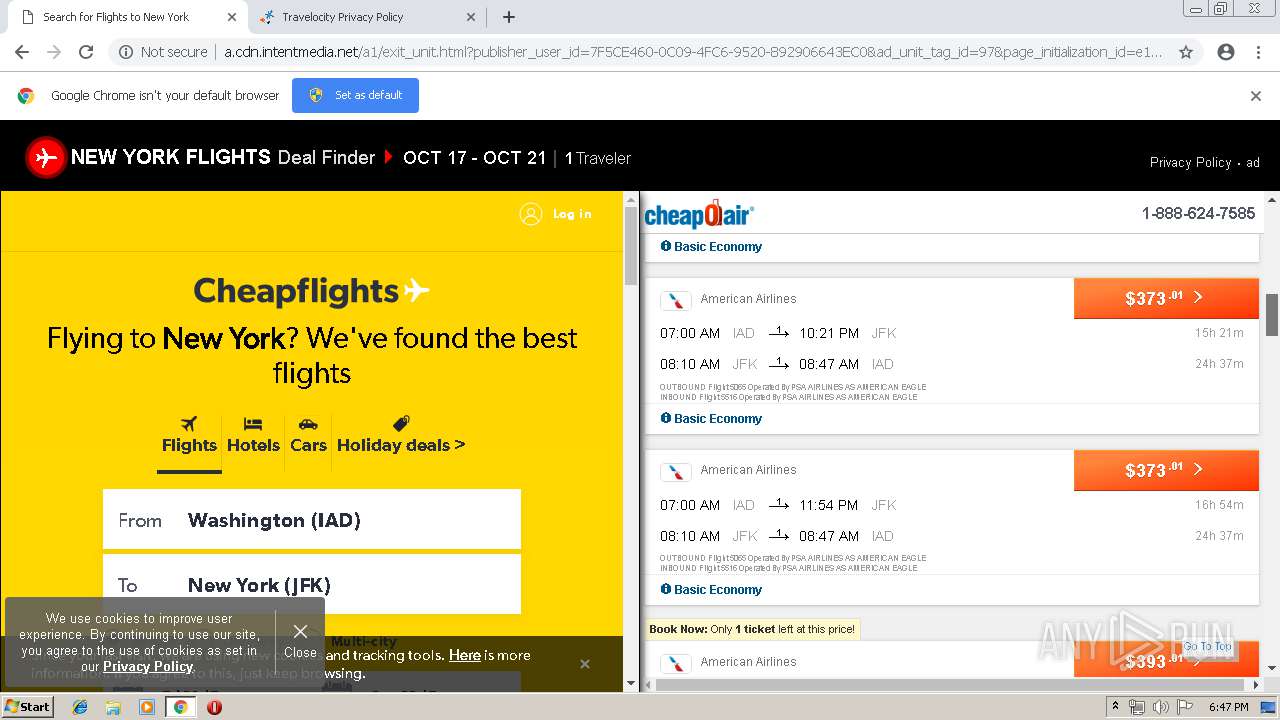
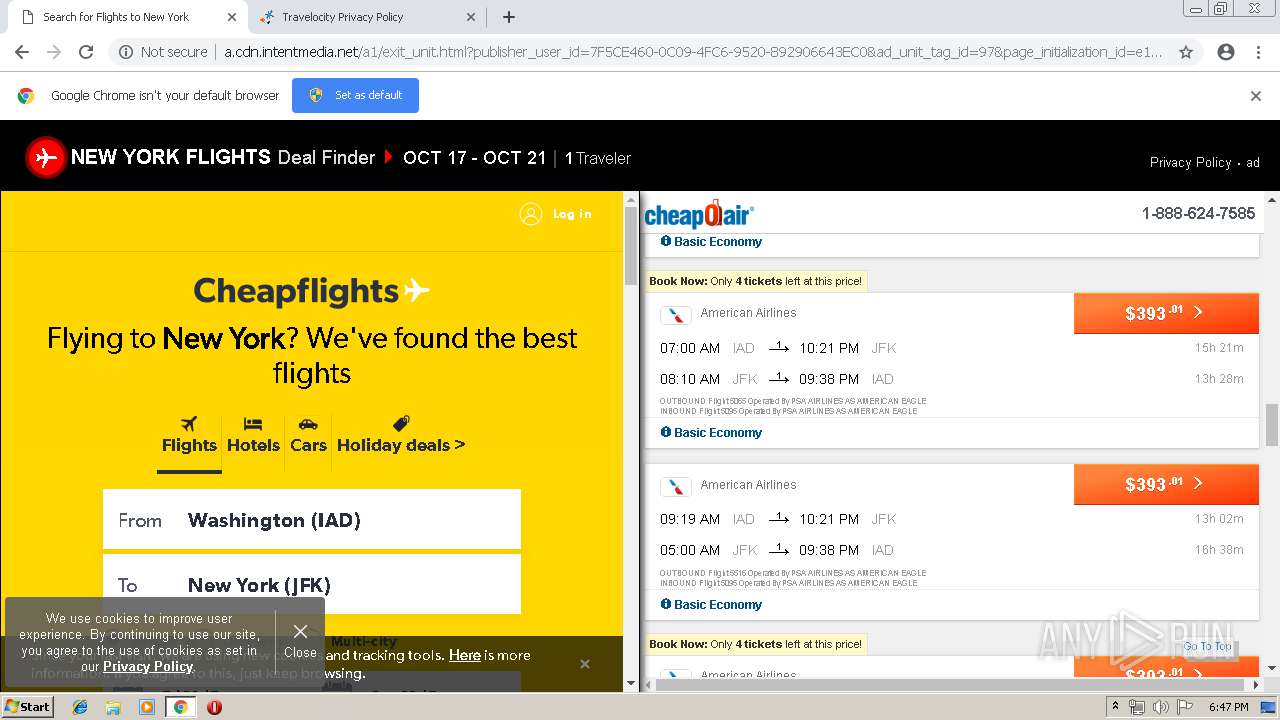
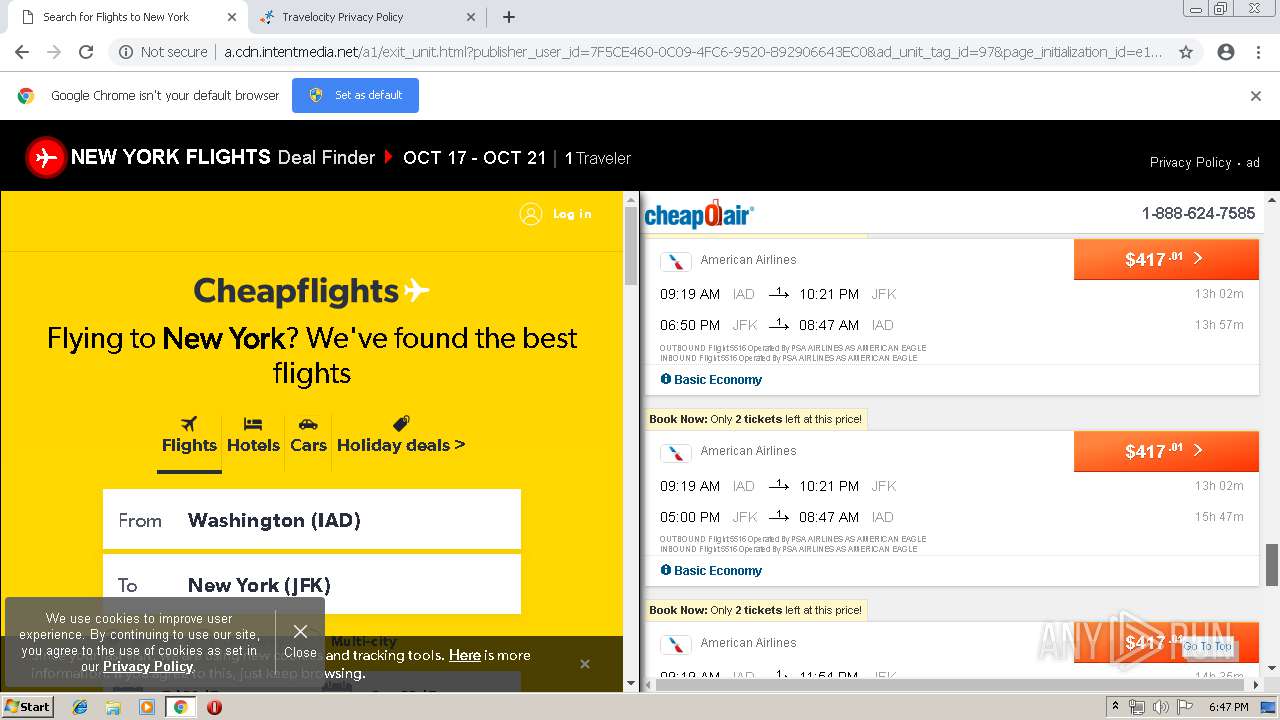
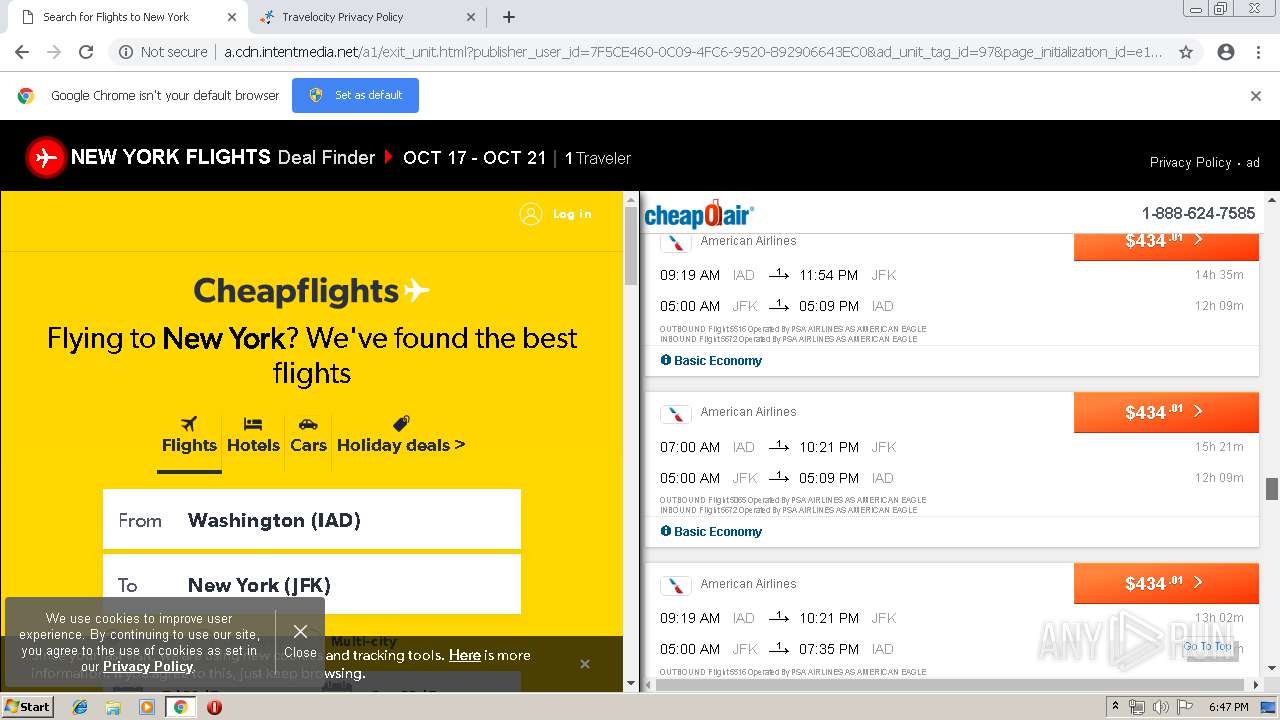
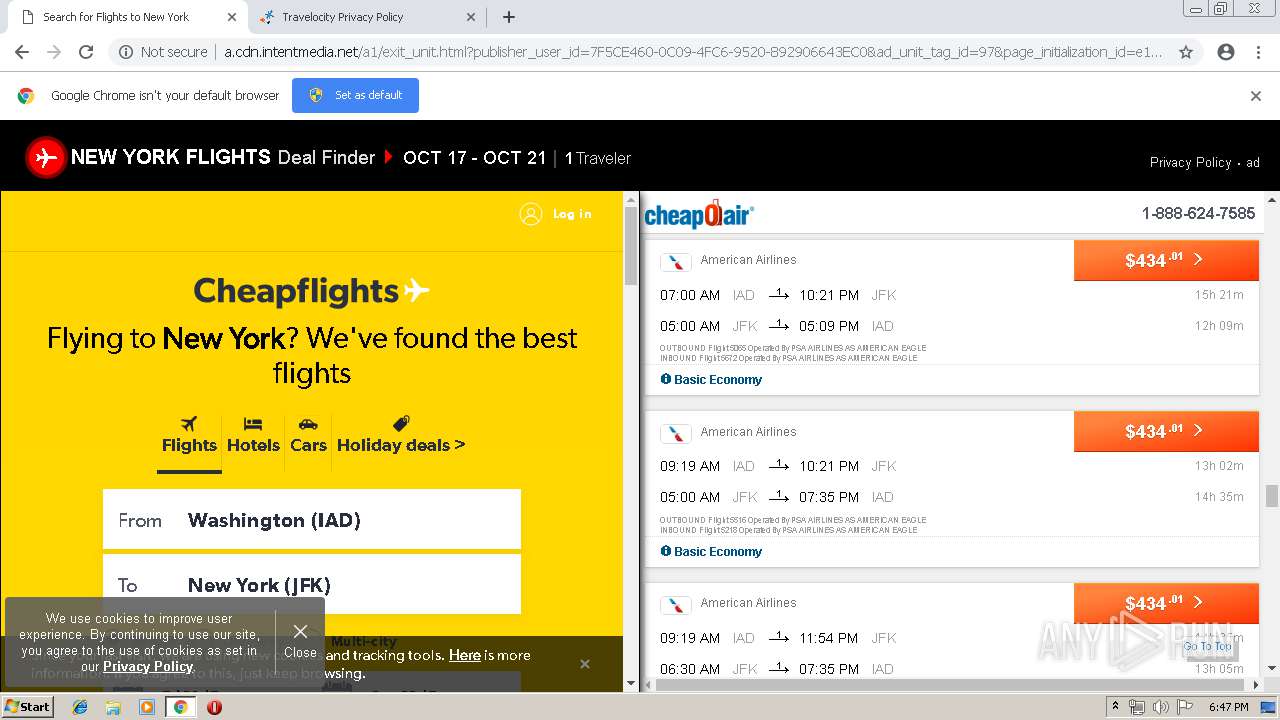
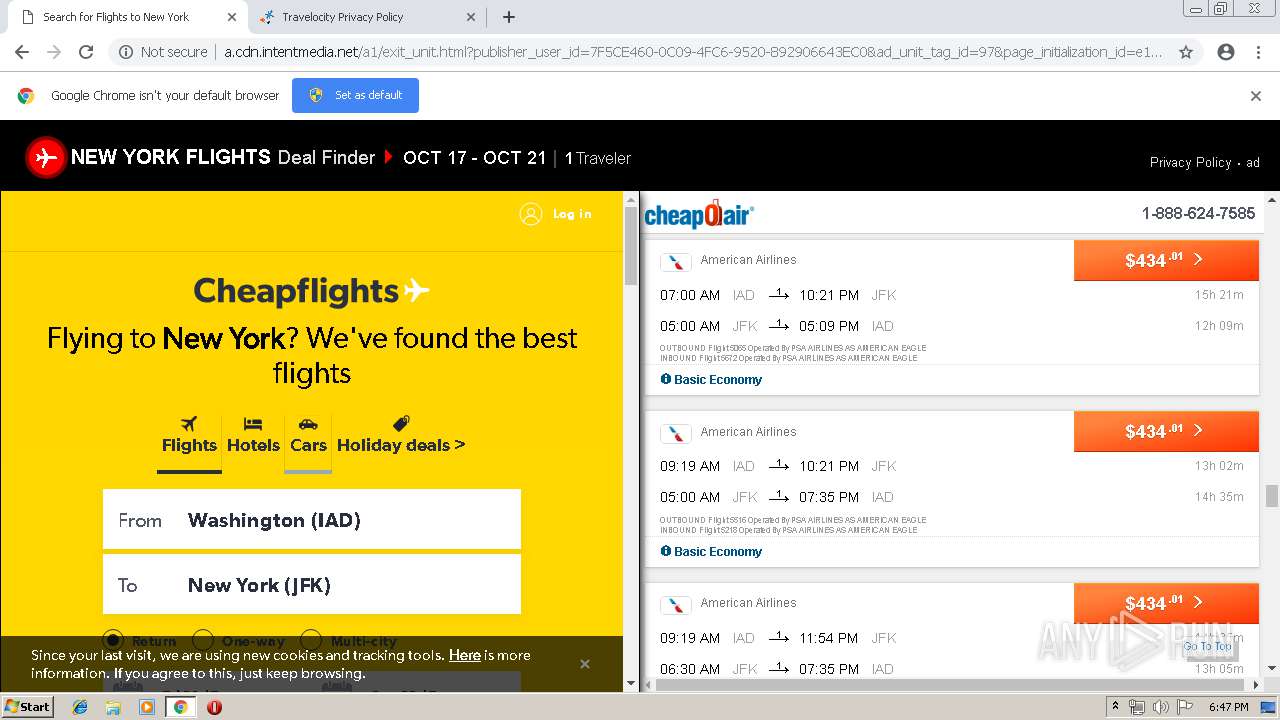
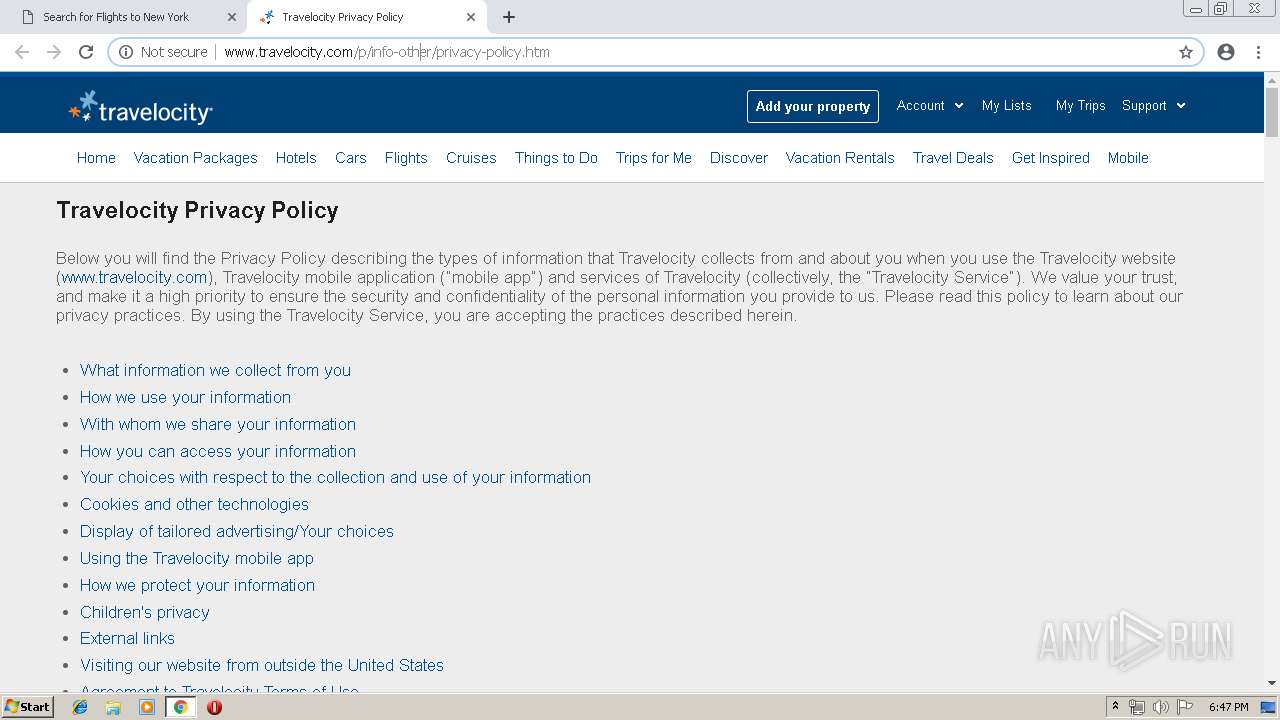
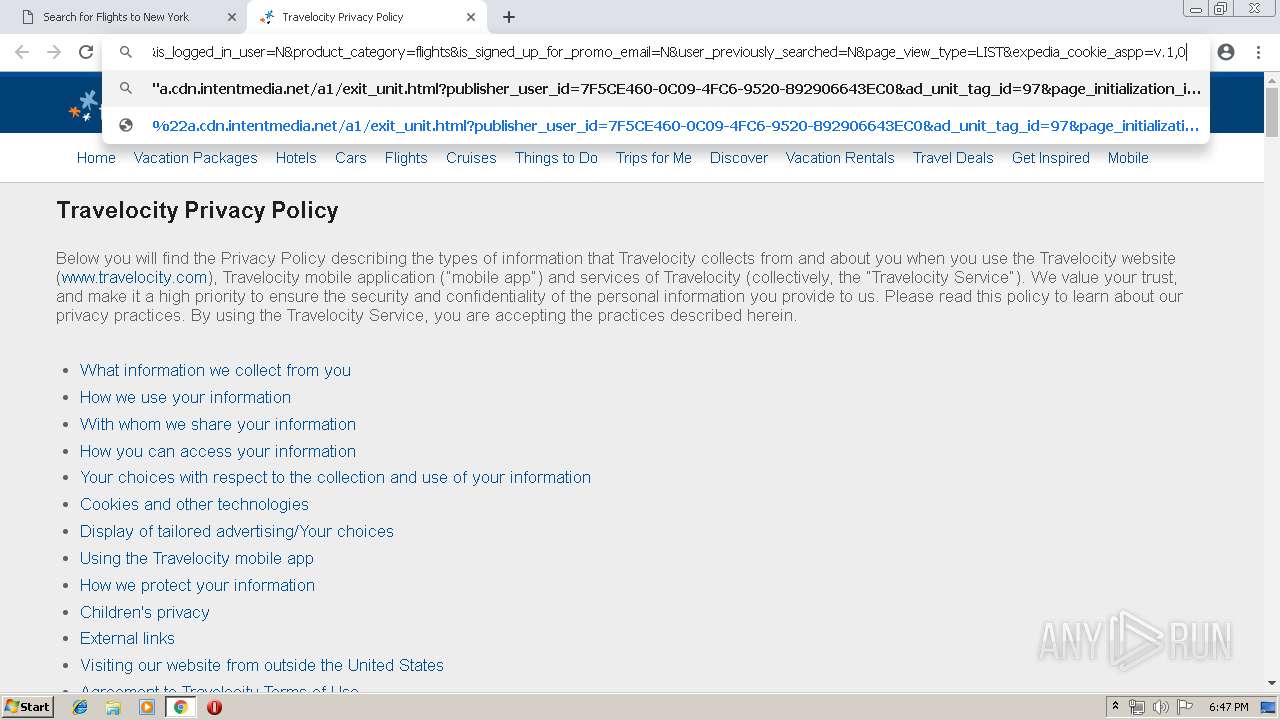
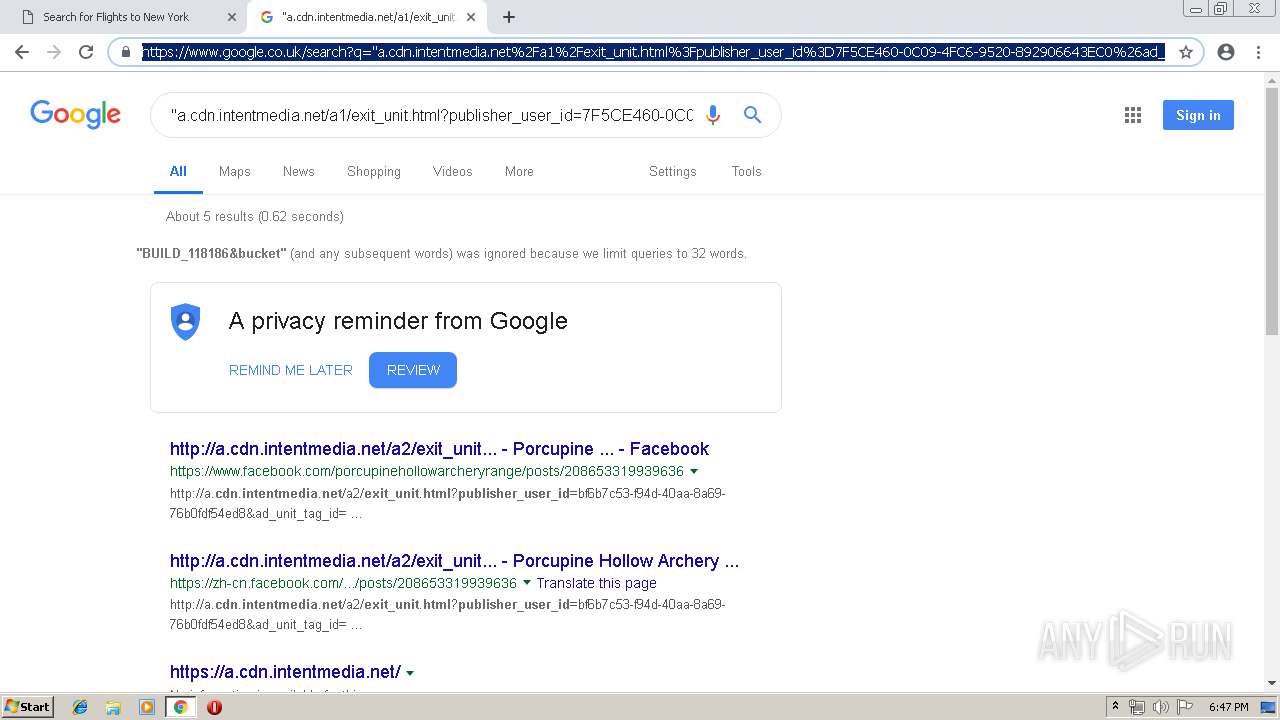
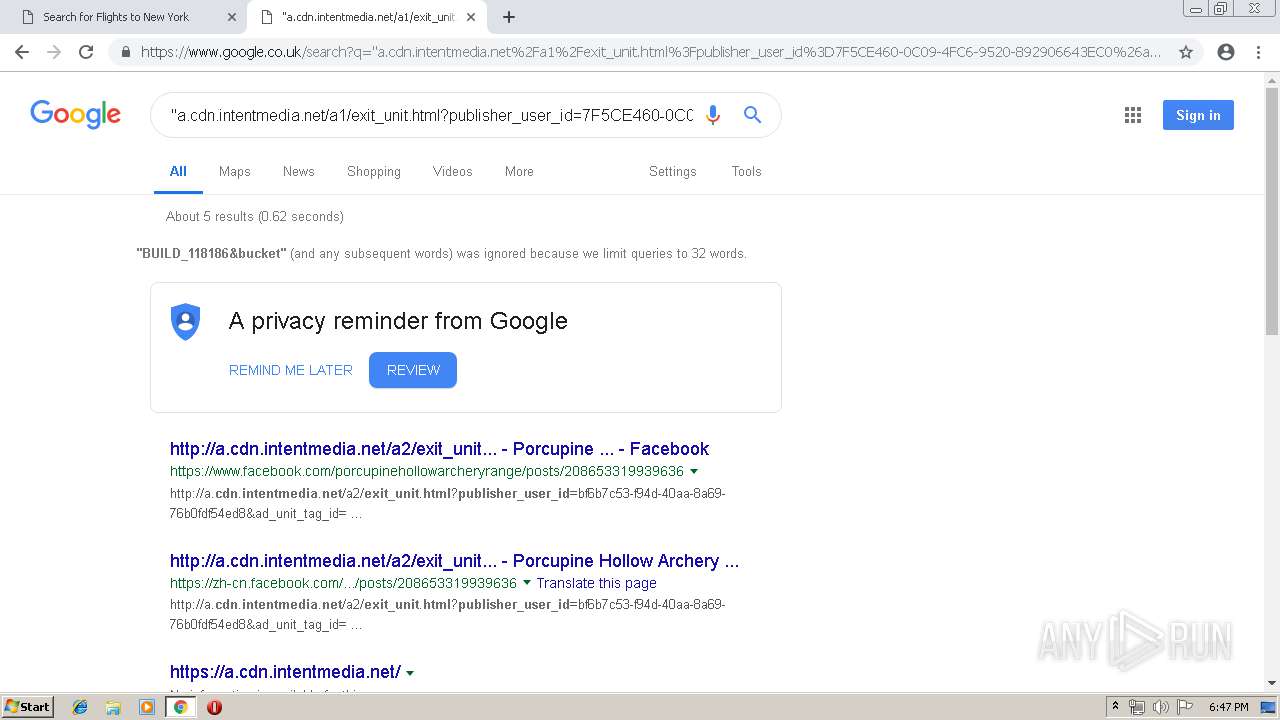
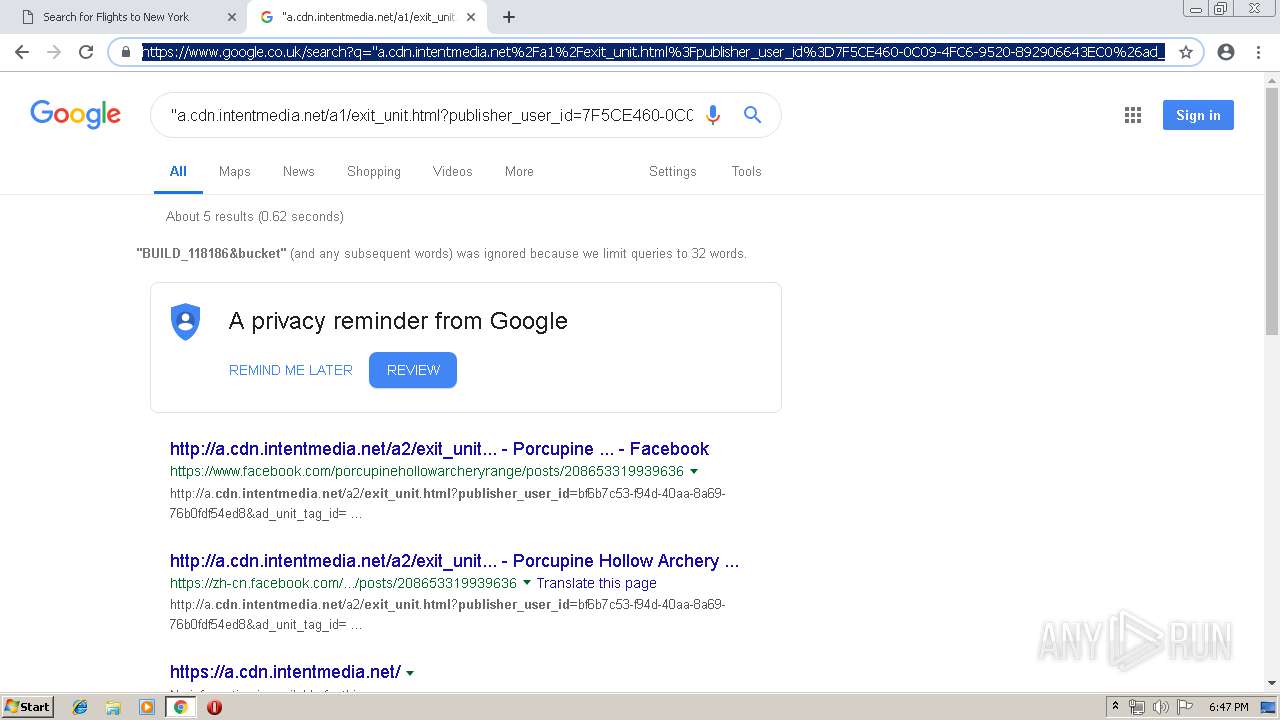
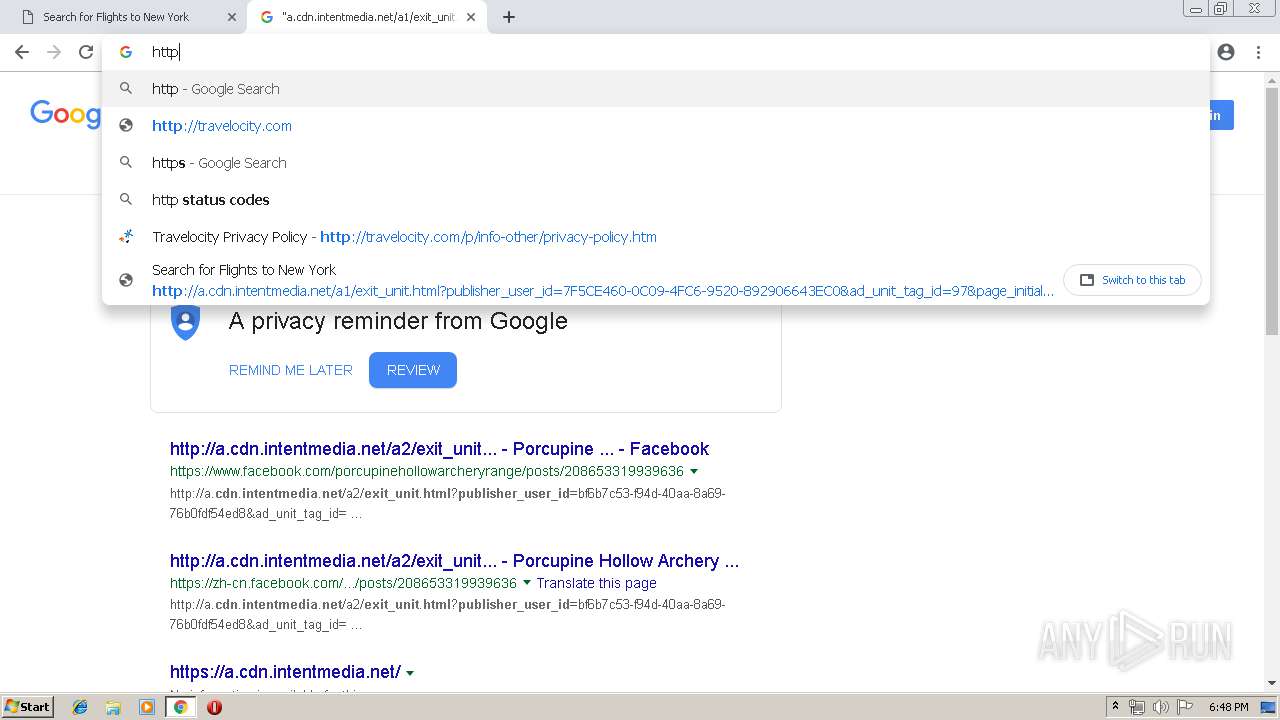
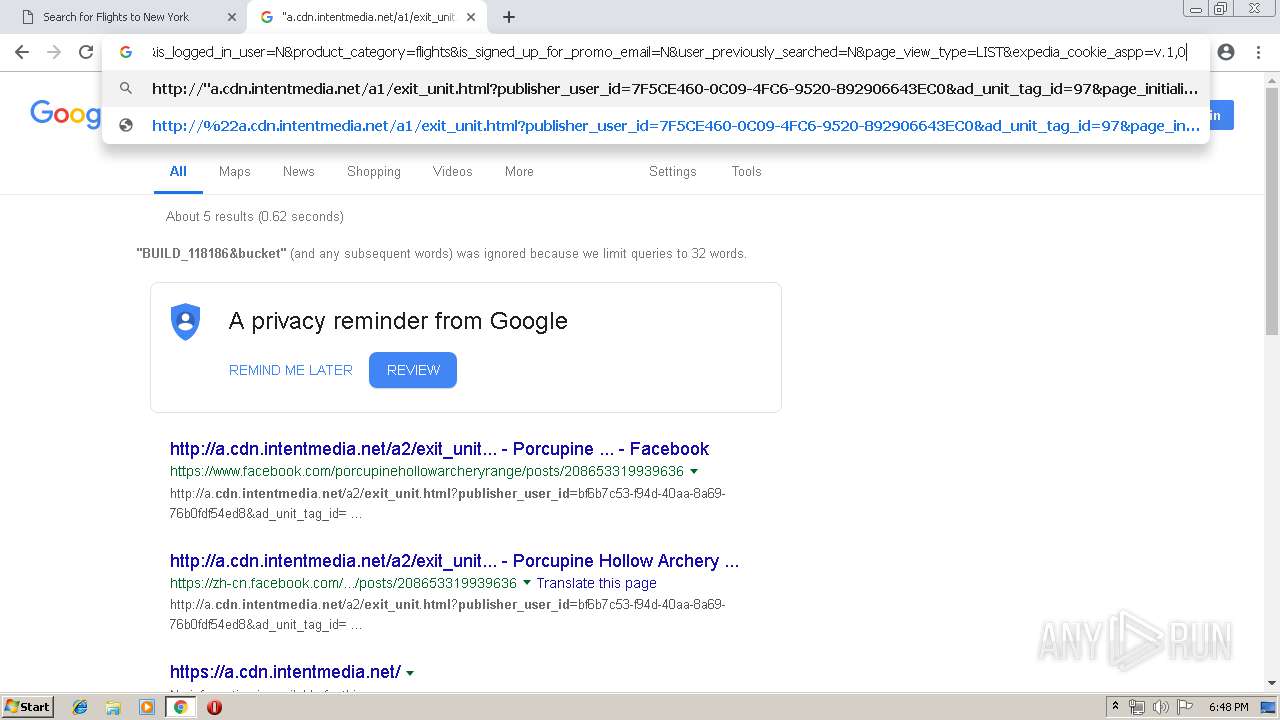
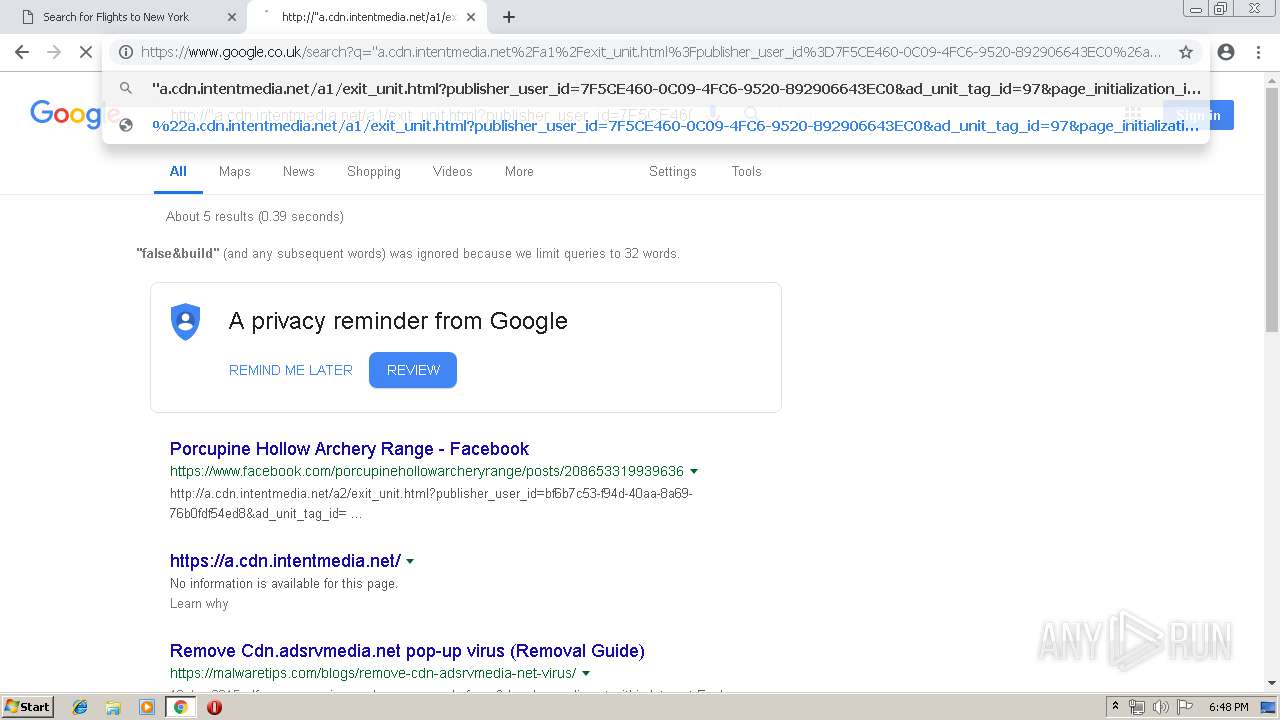
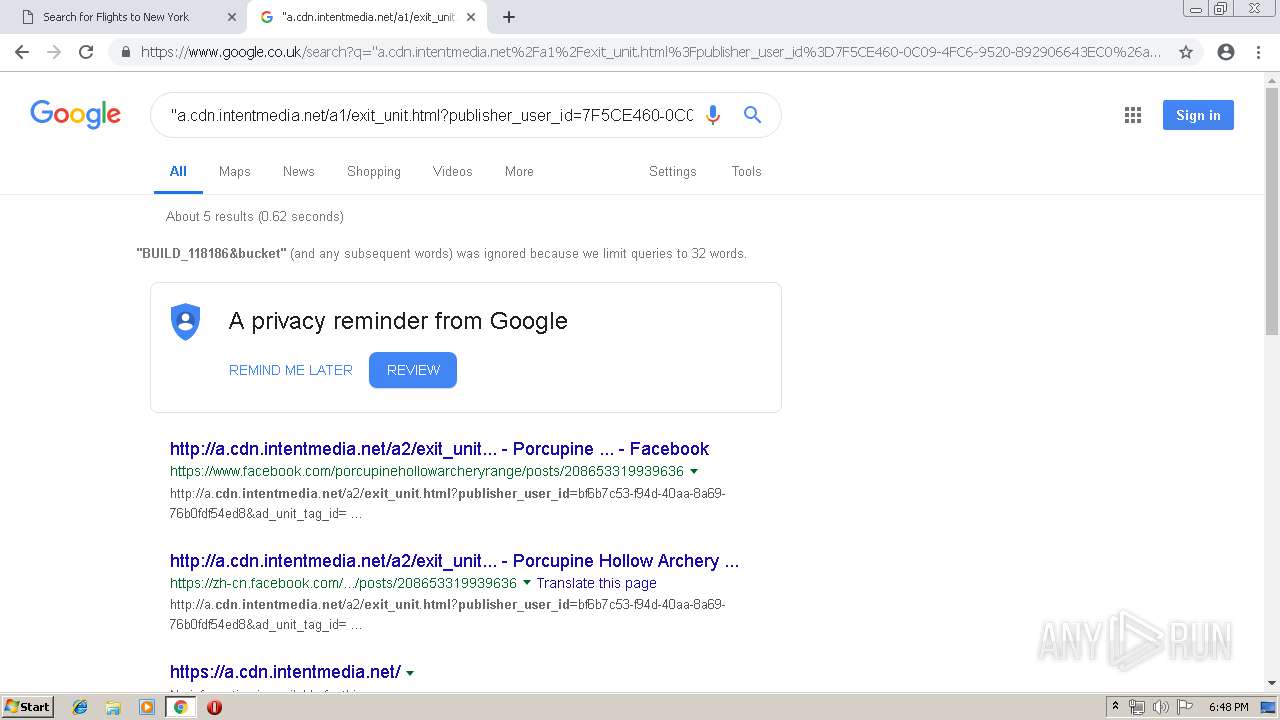
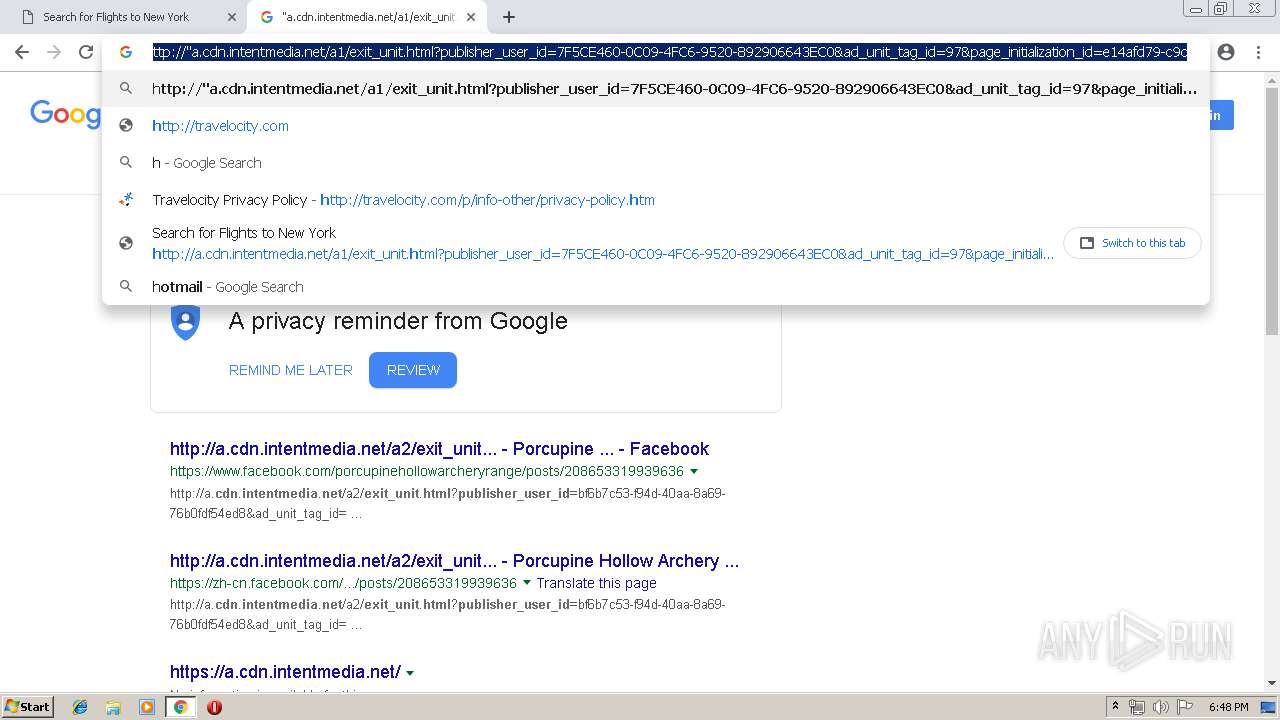
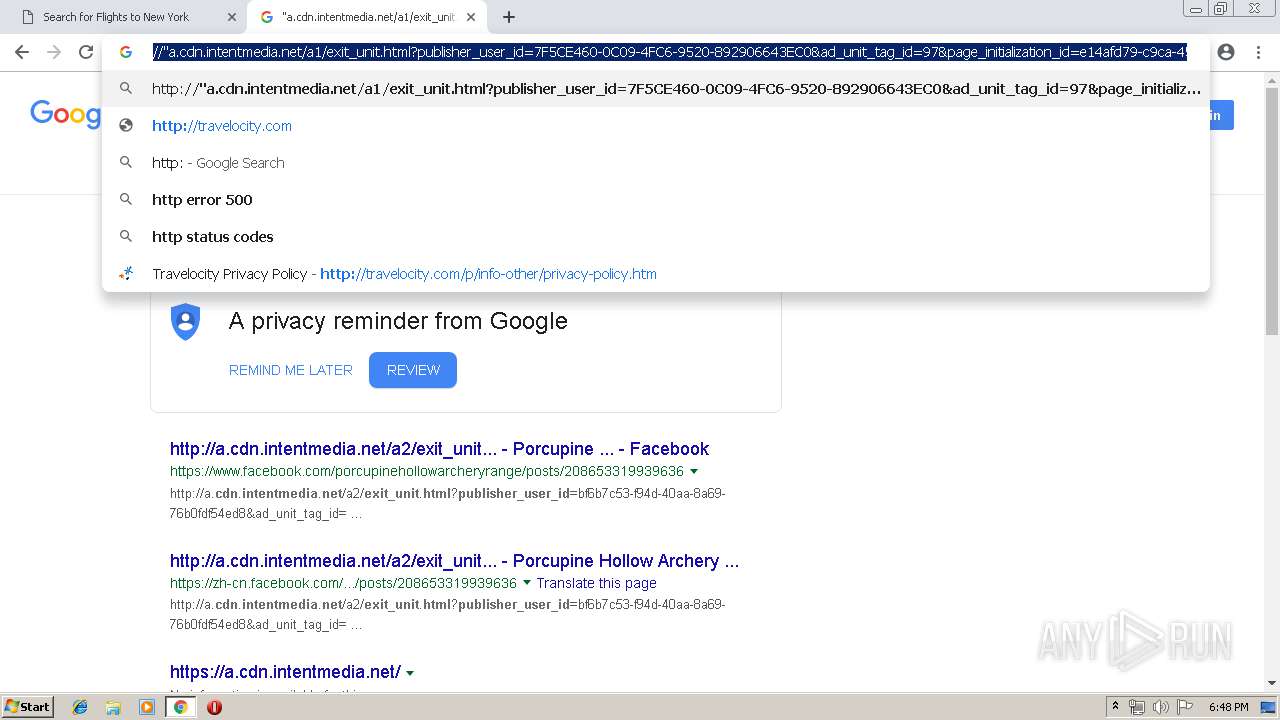
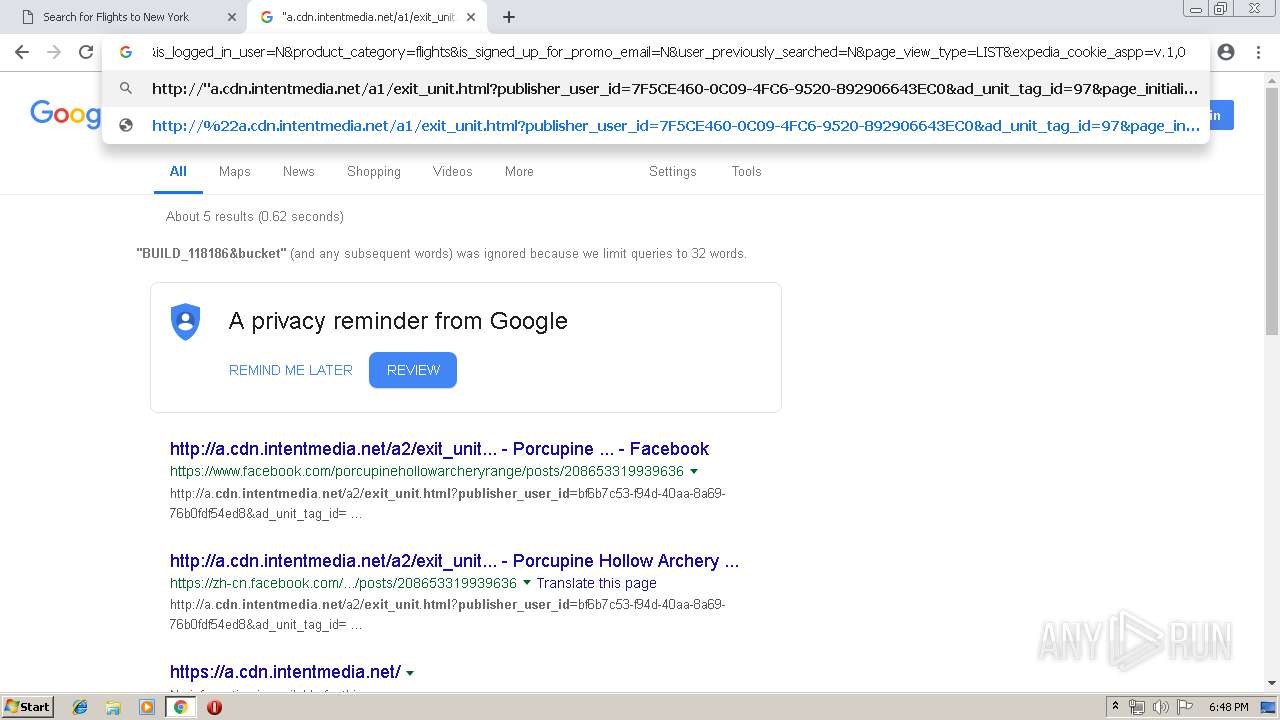
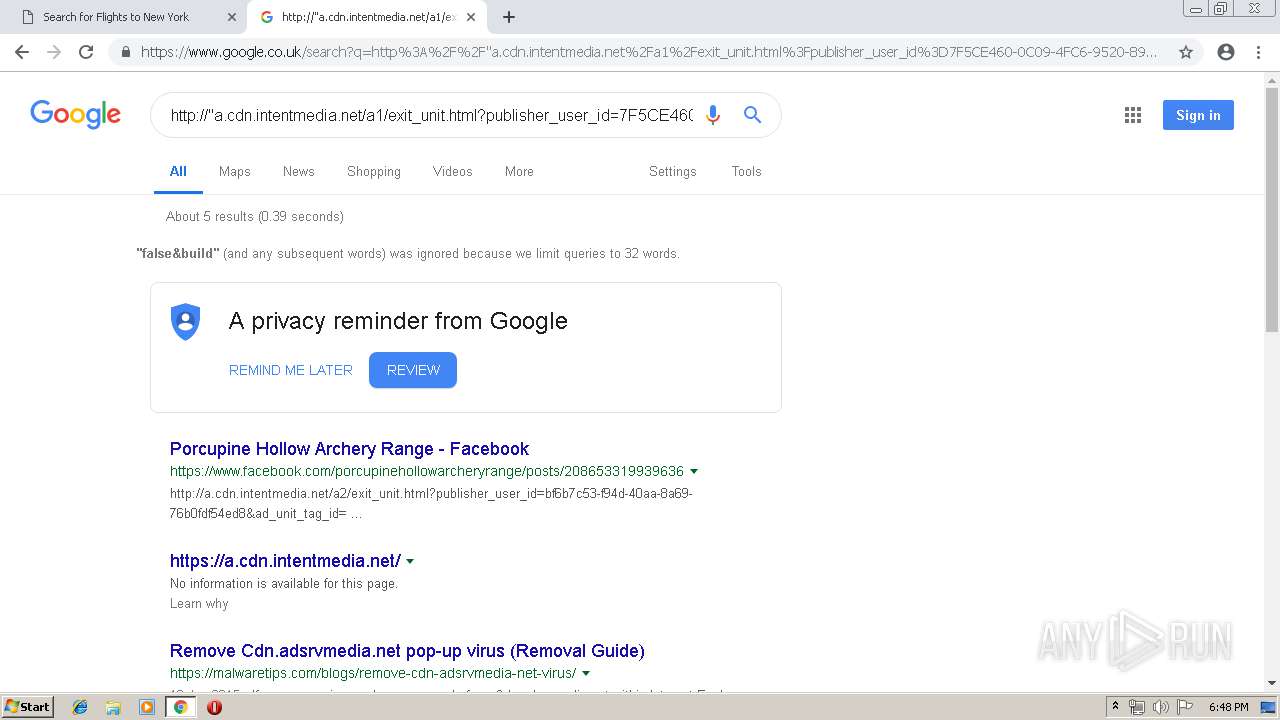
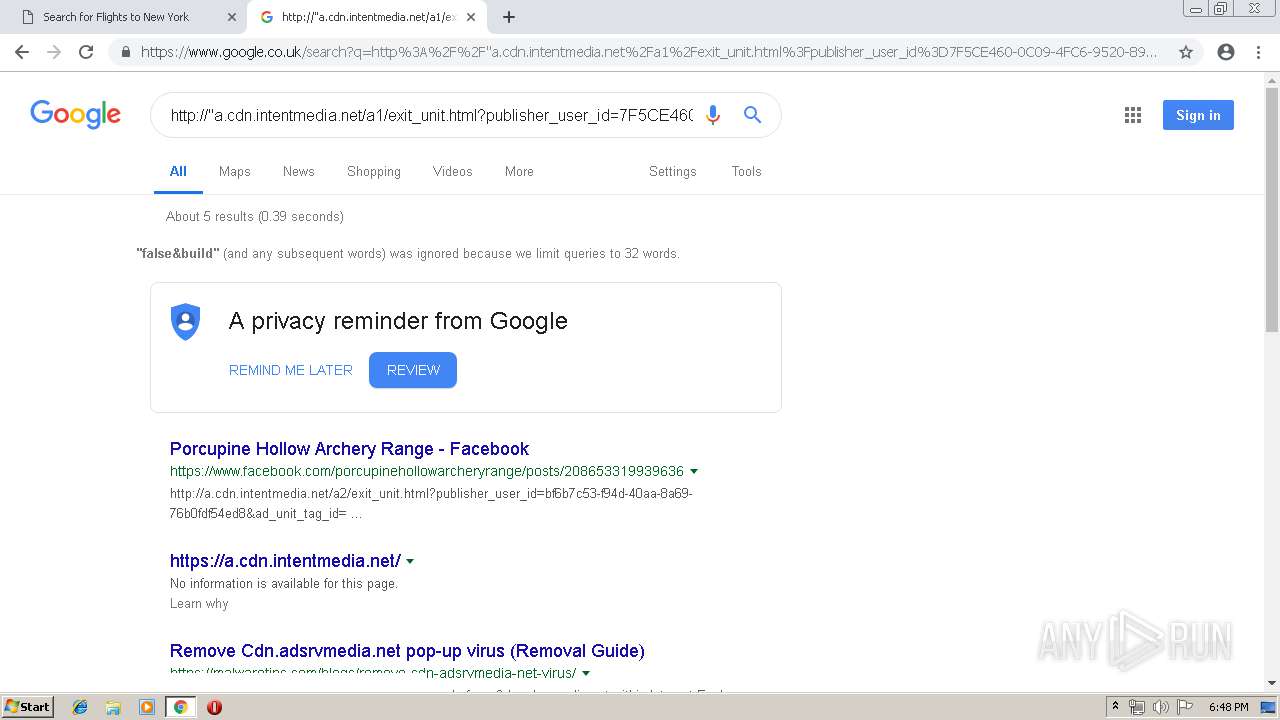
| URL: | http://a.cdn.intentmedia.net/a1/exit_unit.html?publisher_user_id=7F5CE460-0C09-4FC6-9520-892906643EC0&ad_unit_tag_id=97&page_initialization_id=e14afd79-c9ca-45e2-8e73-be655a02de15&exit_unit_source=flight_list_page&origination=IAD&destination=JFK&page_id=flights.results.redesign&site=TVLY&site_name=TVLY&site_country=US&site_language=en&site_currency=USD&opens_remote_exit_unit=true&exit_unit_remote_polling=false&build=BUILD_118186&bucket=a1&privacy_policy_link=http://www.travelocity.com/p/info-other/privacy-policy.htm&trip_type=ROUND_TRIP&flight_origin=IAD&flight_destination=JFK&show_overlay=N&travel_date_start=20191017&travel_date_end=20191021&travelers=1&adults=1&children=0&display_format_type=Desktop&show_ads=Y&show_exit_units=Y&publisher_member_id=648697732&expedia_id=324809771&publisher_session_id=4fb29783-00cf-40e4-8803-d285d2536693&is_member=Y&is_logged_in_user=N&product_category=flights&is_signed_up_for_promo_email=N&user_previously_searched=N&page_view_type=LIST&expedia_cookie_aspp=v.1,0|TRAVELOCITY-US.MR.SH |
| Full analysis: | https://app.any.run/tasks/768b62a3-5424-419f-a156-d7c6ea9aec18 |
| Verdict: | No threats detected |
| Analysis date: | May 09, 2019, 17:43:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | BC8FB9103CC08770365B84E5F418396F |
| SHA1: | 3C9FA70B7F5A9405D4C4A30CC8E439AADC3E7124 |
| SHA256: | 42E0BD94AFEC2DD8182F1F4370D682849FFC8C8EBBB852CF052EB5DF410A2E02 |
| SSDEEP: | 24:NxACaTJDIMFFE9uHKEwx9M8fOScG8ALkD/TODAK1mLgYn:NCC6sMFS9kKEwQ8feG/L2TyAK1mLgYn |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2472)
INFO
Reads settings of System Certificates
- chrome.exe (PID: 2472)
Changes settings of System certificates
- chrome.exe (PID: 2472)
Application launched itself
- chrome.exe (PID: 2472)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
60
Monitored processes
30
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 352 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,16778797066664449721,11563423376205373355,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=11297063738724636299 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11297063738724636299 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3812 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 760 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,16778797066664449721,11563423376205373355,131072 --enable-features=PasswordImport --service-pipe-token=11527489997902732934 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11527489997902732934 --renderer-client-id=3 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2236 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 796 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,16778797066664449721,11563423376205373355,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=17354794984775222754 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17354794984775222754 --renderer-client-id=20 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2132 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1076 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,16778797066664449721,11563423376205373355,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=5538483153125985649 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5538483153125985649 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3684 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1240 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,16778797066664449721,11563423376205373355,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2095016521038182496 --mojo-platform-channel-handle=4920 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1672 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,16778797066664449721,11563423376205373355,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4703367991037696031 --mojo-platform-channel-handle=5116 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1908 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,16778797066664449721,11563423376205373355,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=12760737911054376718 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12760737911054376718 --renderer-client-id=26 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5724 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2172 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,16778797066664449721,11563423376205373355,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12446168902343702686 --mojo-platform-channel-handle=4660 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,16778797066664449721,11563423376205373355,131072 --enable-features=PasswordImport --service-pipe-token=13686398766935211119 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13686398766935211119 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1972 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2208 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,16778797066664449721,11563423376205373355,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=1162608585635023023 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1162608585635023023 --renderer-client-id=21 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3624 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
614
Read events
512
Write events
97
Delete events
5
Modification events
| (PID) Process: | (2472) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2472) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2472) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2472) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2472) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2472) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2472) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2472) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (2472) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2472) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2472-13201897421641250 |
Value: 259 | |||
Executable files
0
Suspicious files
257
Text files
208
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\f385200e-83f0-4718-9bc7-2eaa0d1776f5.tmp | — | |
MD5:— | SHA256:— | |||
| 2472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
66
TCP/UDP connections
159
DNS requests
129
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
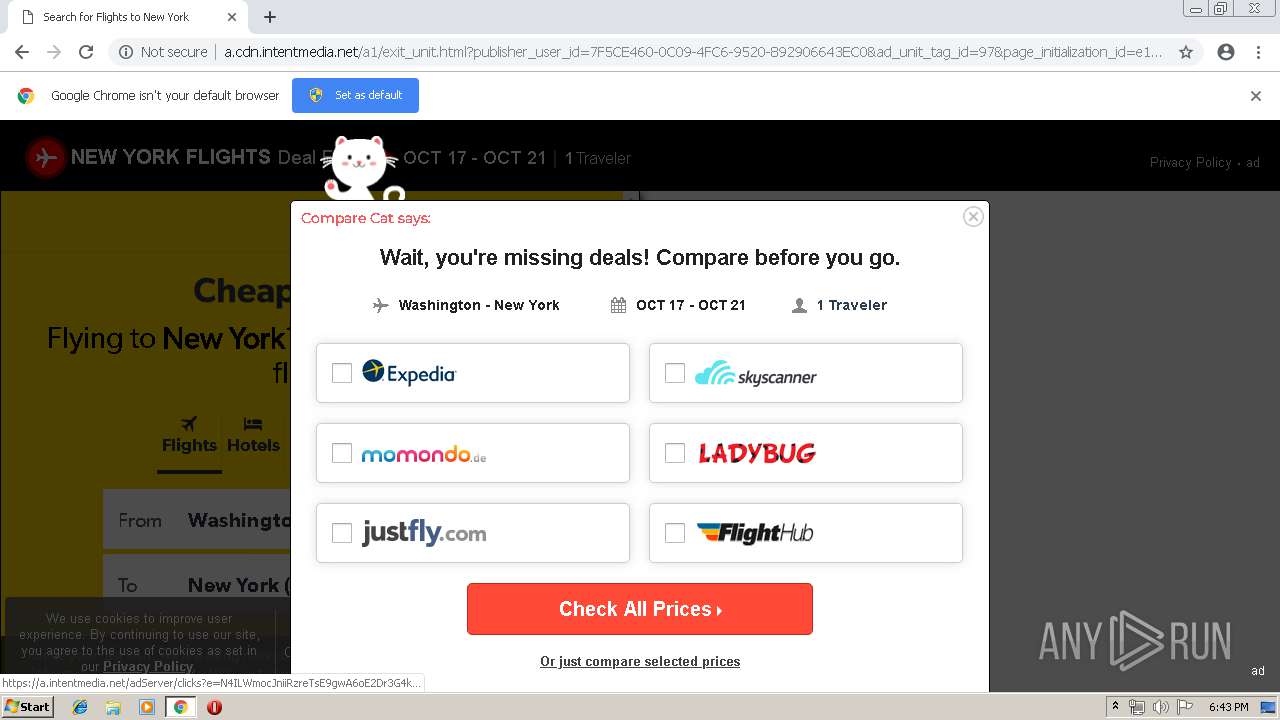
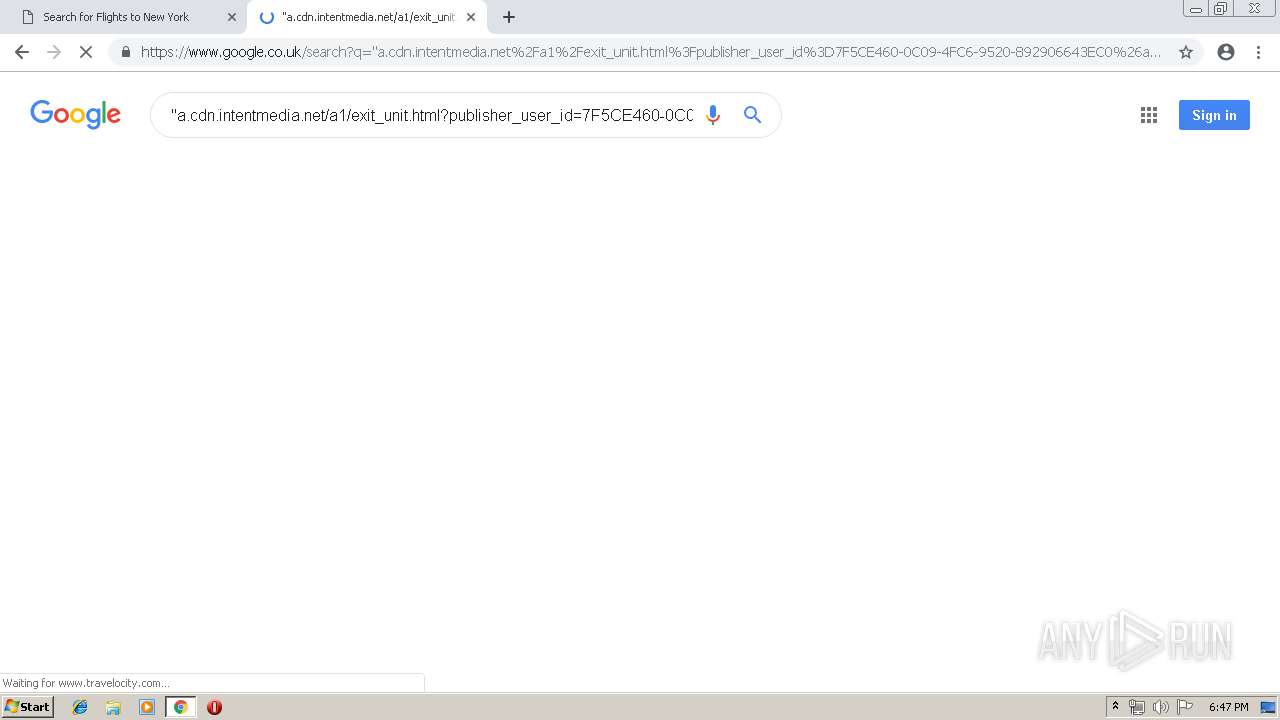
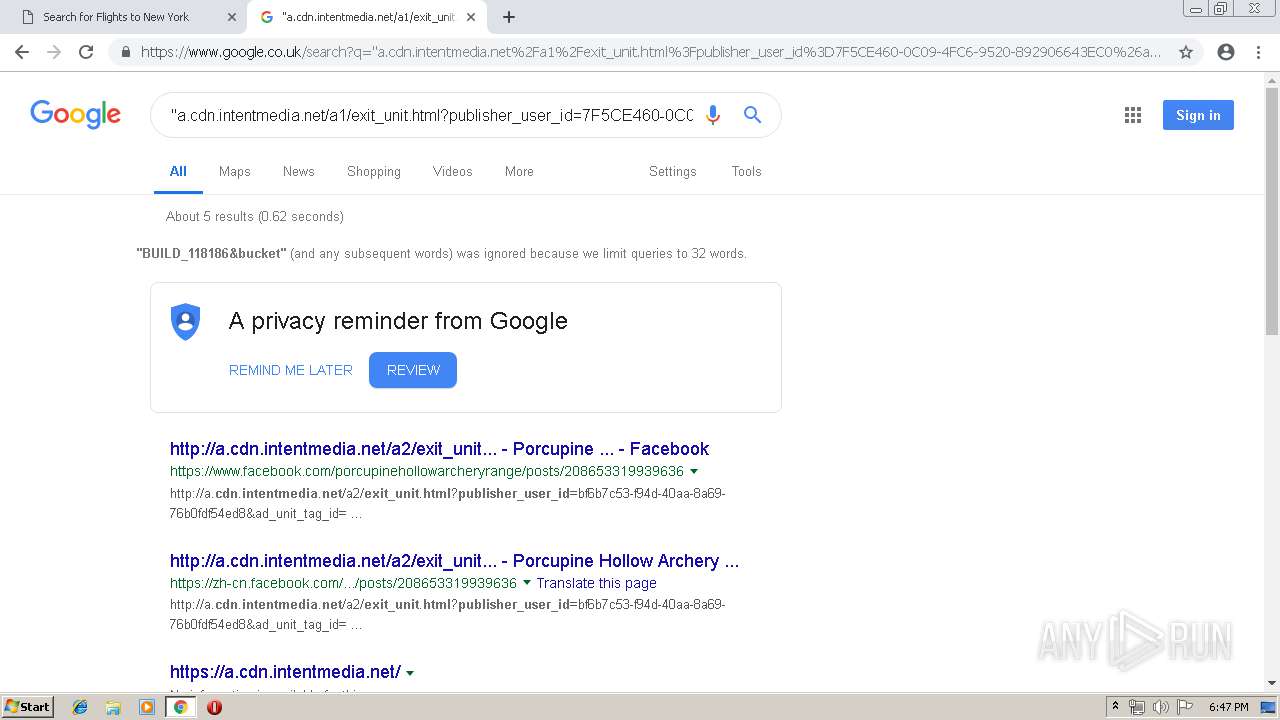
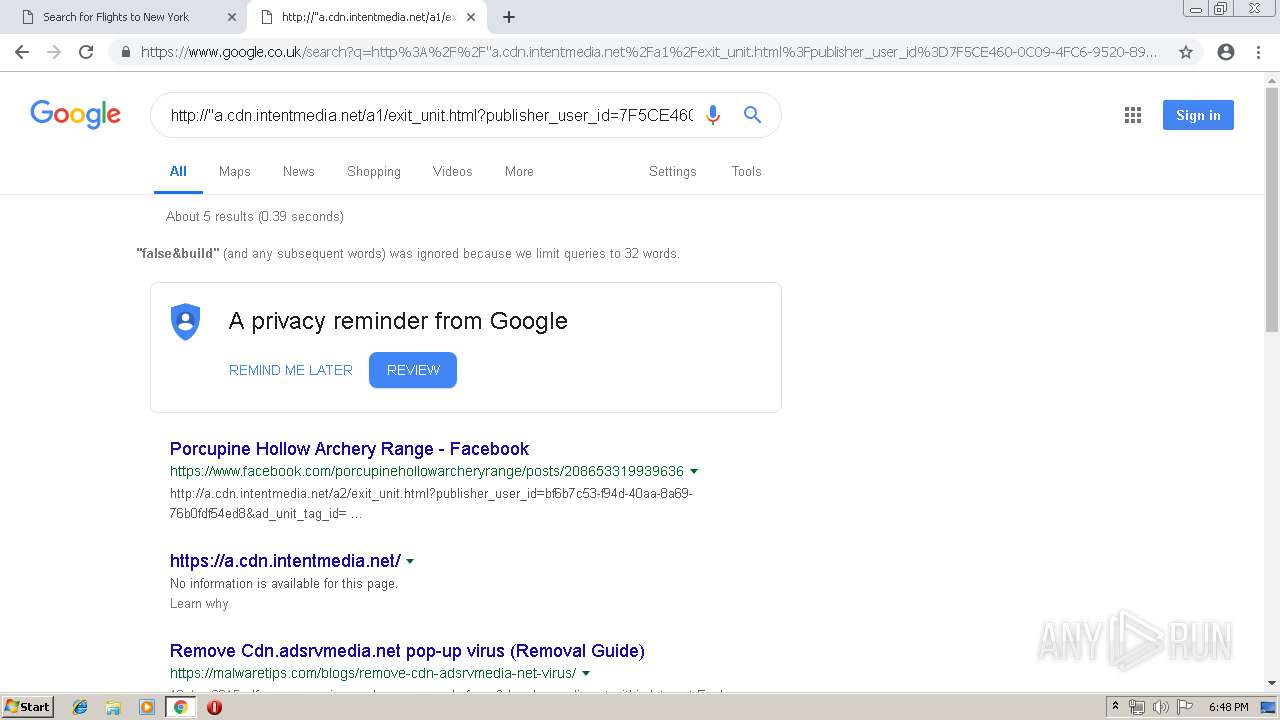
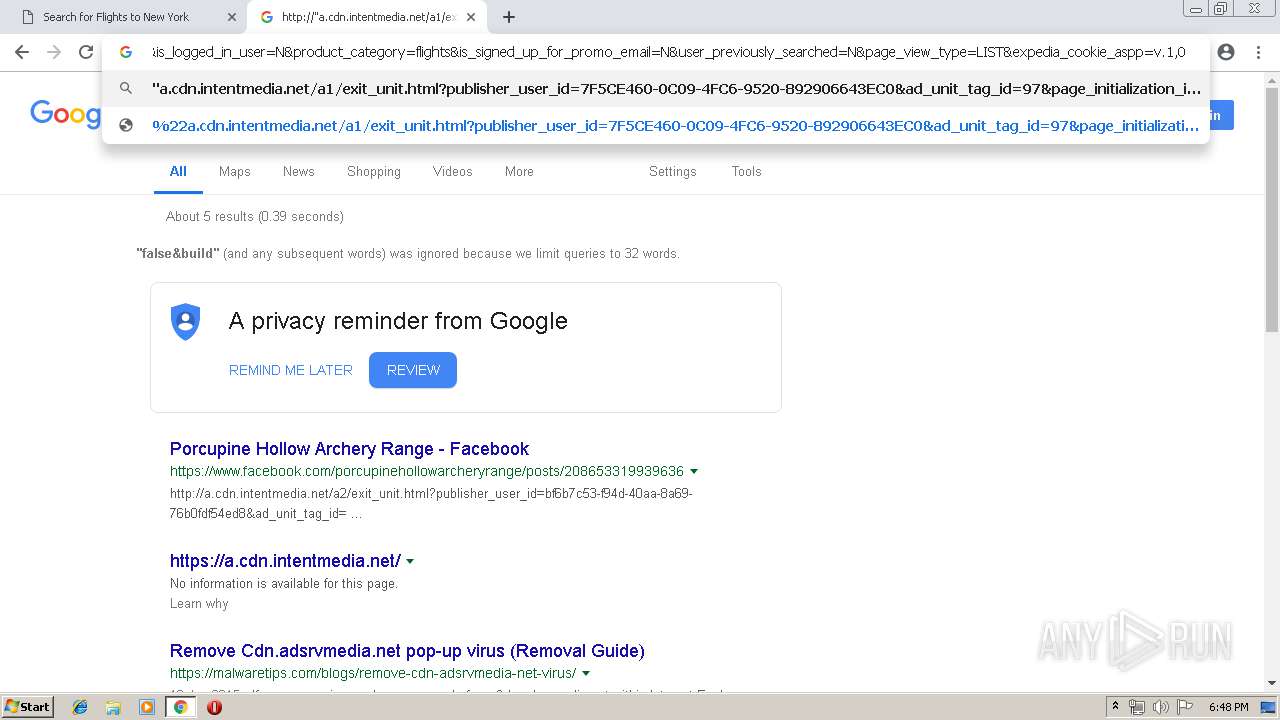
2472 | chrome.exe | GET | 200 | 151.101.2.111:80 | http://a.cdn.intentmedia.net/a1/exit_unit.html?publisher_user_id=7F5CE460-0C09-4FC6-9520-892906643EC0&ad_unit_tag_id=97&page_initialization_id=e14afd79-c9ca-45e2-8e73-be655a02de15&exit_unit_source=flight_list_page&origination=IAD&destination=JFK&page_id=flights.results.redesign&site=TVLY&site_name=TVLY&site_country=US&site_language=en&site_currency=USD&opens_remote_exit_unit=true&exit_unit_remote_polling=false&build=BUILD_118186&bucket=a1&privacy_policy_link=http://www.travelocity.com/p/info-other/privacy-policy.htm&trip_type=ROUND_TRIP&flight_origin=IAD&flight_destination=JFK&show_overlay=N&travel_date_start=20191017&travel_date_end=20191021&travelers=1&adults=1&children=0&display_format_type=Desktop&show_ads=Y&show_exit_units=Y&publisher_member_id=648697732&expedia_id=324809771&publisher_session_id=4fb29783-00cf-40e4-8803-d285d2536693&is_member=Y&is_logged_in_user=N&product_category=flights&is_signed_up_for_promo_email=N&user_previously_searched=N&page_view_type=LIST&expedia_cookie_aspp=v.1,0|TRAVELOCITY-US.MR.SH | US | html | 993 b | malicious |
2472 | chrome.exe | GET | 200 | 151.101.2.111:80 | http://a.cdn.intentmedia.net/a1/javascripts/intent_media_exit_unit_redirector_standard.js | US | text | 174 Kb | malicious |
2472 | chrome.exe | GET | 200 | 151.101.2.111:80 | http://a.cdn.intentmedia.net/javascripts/v1/intent_media_core.js | US | text | 20.1 Kb | malicious |
2472 | chrome.exe | GET | 200 | 52.85.182.102:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
2472 | chrome.exe | GET | 200 | 54.175.56.139:80 | http://a.intentmedia.net/adServer/page?page_id=flights.results.redesign&site_name=TVLY&build=BUILD_118186 | US | text | 822 b | unknown |
2472 | chrome.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/47BEABC922EAE80E78783462A79F45C254FDE68B.crt | US | der | 969 b | whitelisted |
2472 | chrome.exe | GET | 200 | 151.101.2.111:80 | http://a.cdn.intentmedia.net/images/carousel/carousel_product_icon_bg_2x.png | US | image | 2.29 Kb | malicious |
2472 | chrome.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 56.1 Kb | whitelisted |
2472 | chrome.exe | GET | 200 | 151.101.2.111:80 | http://a.cdn.intentmedia.net/creative_sizes/430_cheapoair.png | US | image | 6.69 Kb | malicious |
2472 | chrome.exe | GET | 200 | 151.101.2.111:80 | http://a.cdn.intentmedia.net/creative_sizes/2455_CheapFlights_favicon_%281%29.png | US | image | 2.85 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2472 | chrome.exe | 172.217.18.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2472 | chrome.exe | 151.101.2.111:80 | a.cdn.intentmedia.net | Fastly | US | unknown |
2472 | chrome.exe | 172.217.18.109:443 | accounts.google.com | Google Inc. | US | suspicious |
2472 | chrome.exe | 151.101.2.111:443 | a.cdn.intentmedia.net | Fastly | US | unknown |
2472 | chrome.exe | 93.184.221.240:80 | www.download.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2472 | chrome.exe | 104.108.59.112:443 | www.cheapoair.com | Akamai Technologies, Inc. | NL | whitelisted |
2472 | chrome.exe | 172.217.18.99:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2472 | chrome.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2472 | chrome.exe | 151.101.1.29:443 | www.cheapflights.com | Fastly | US | unknown |
2472 | chrome.exe | 172.217.22.14:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
a.cdn.intentmedia.net |
| malicious |
accounts.google.com |
| shared |
a.intentmedia.net |
| unknown |
x.ss2.us |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
intentmedia.com |
| malicious |
www.travelocity.com |
| suspicious |
fonts.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2472 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |
2472 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |
2472 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |
2472 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
2472 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
2472 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
2472 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
2472 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
2472 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
2472 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
Process | Message |
|---|---|
chrome.exe | Error - |
chrome.exe | Too long restart command line passed |
chrome.exe |