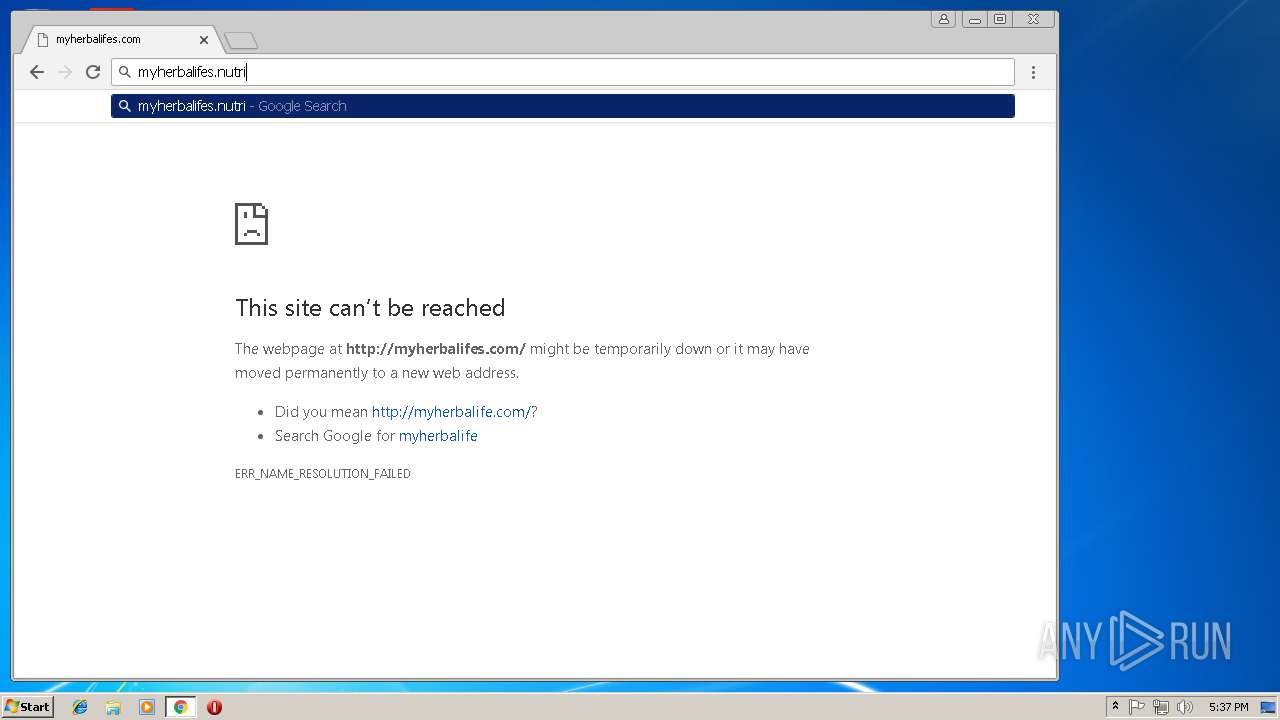
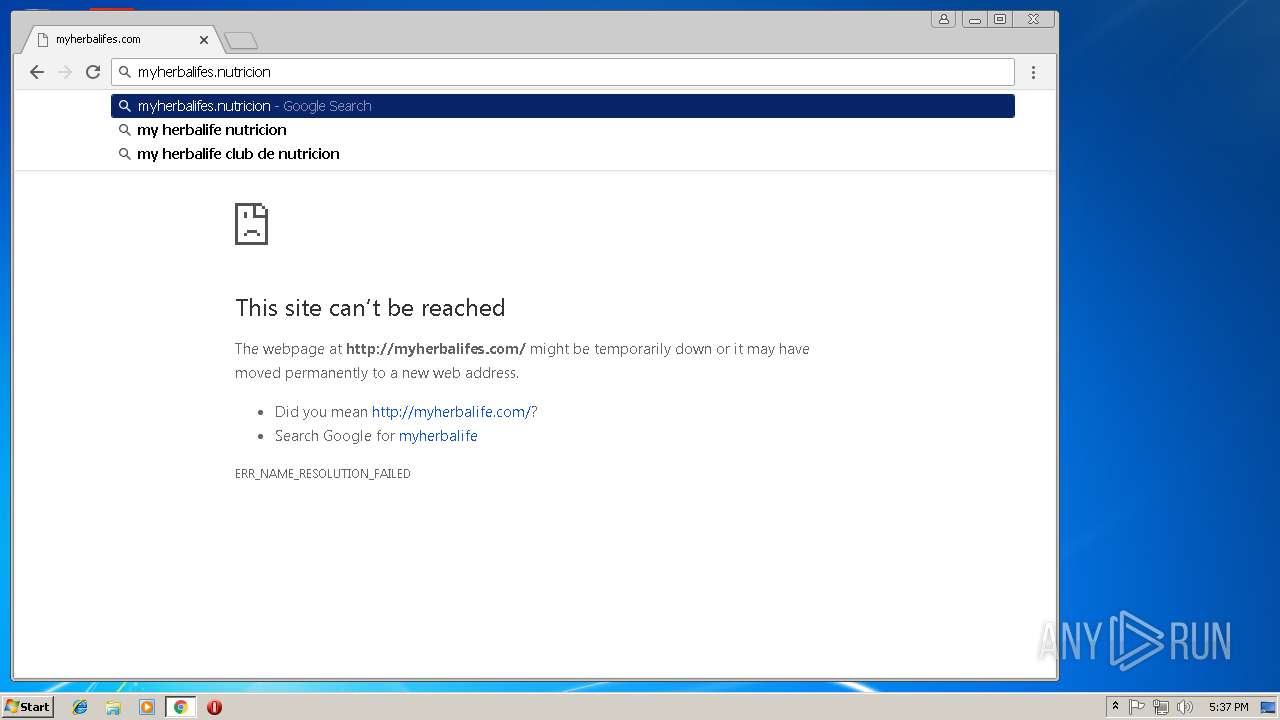
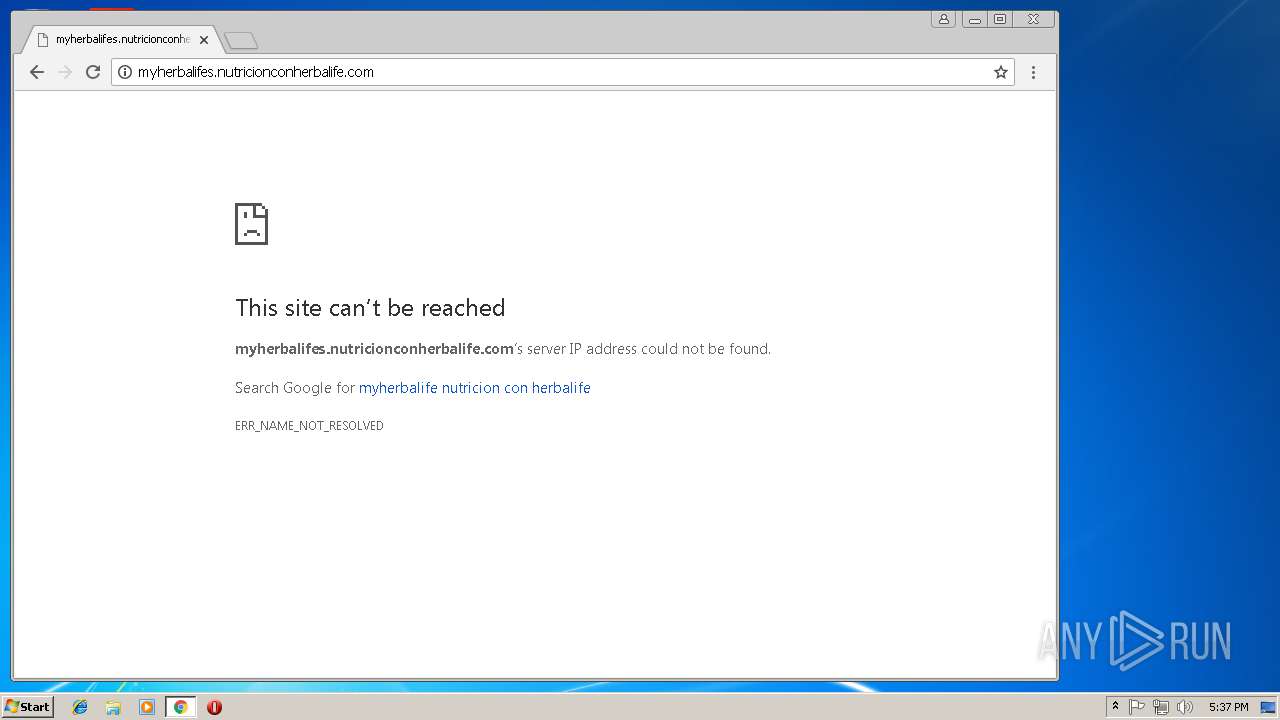
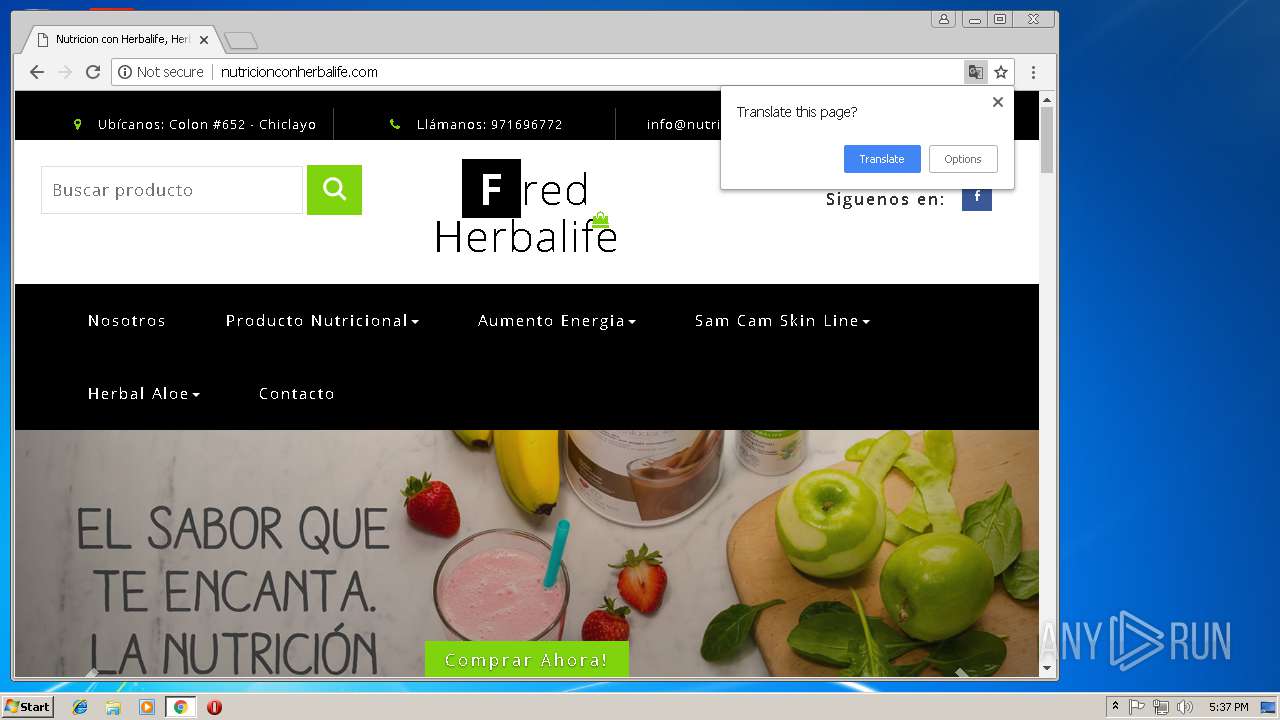
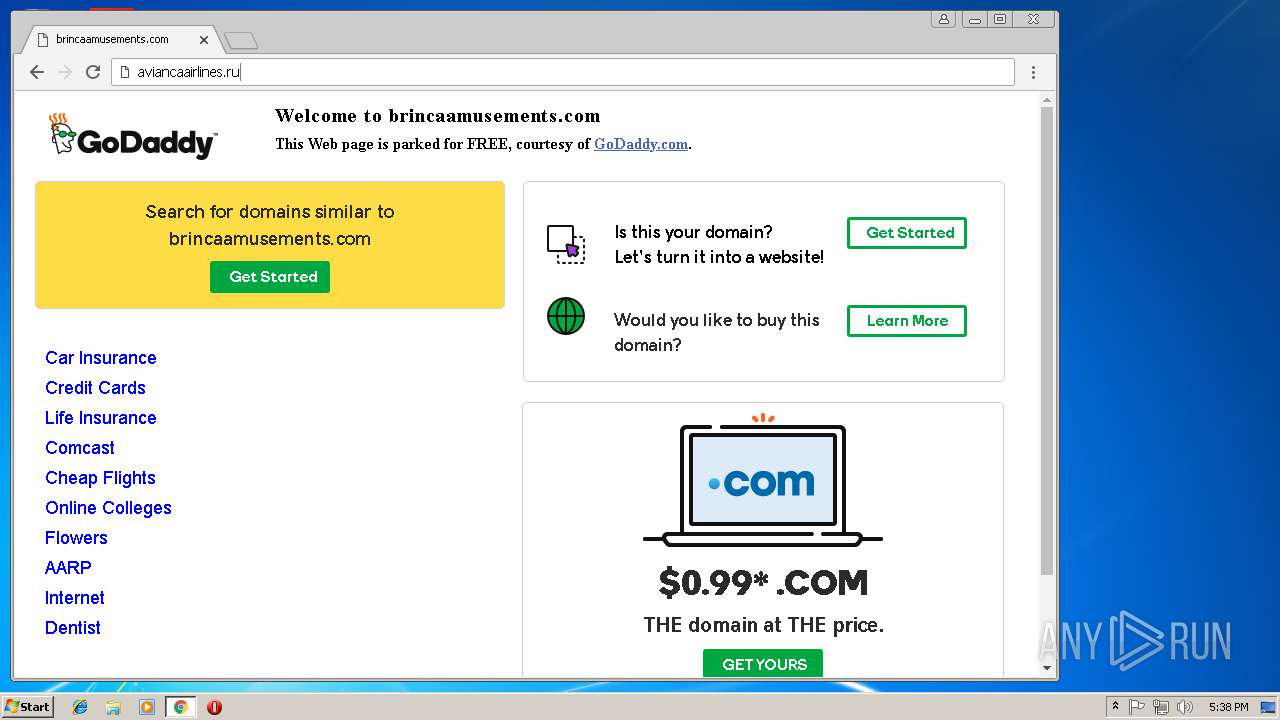
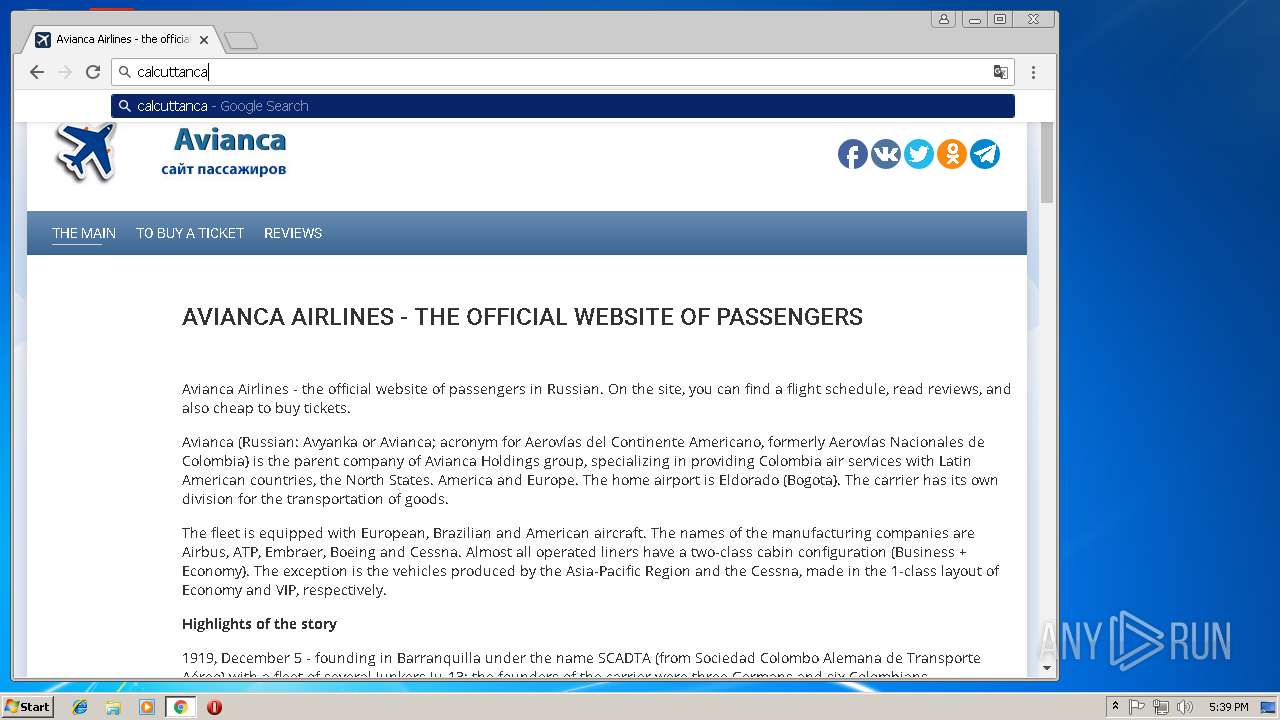
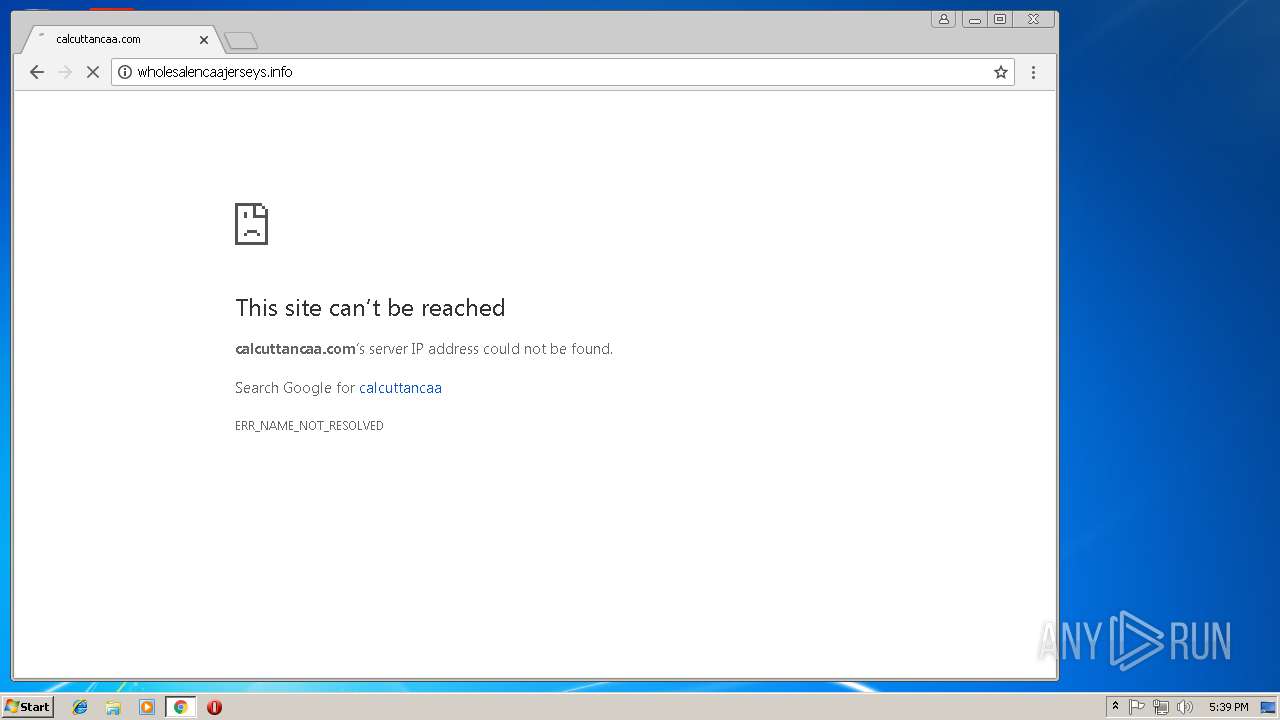
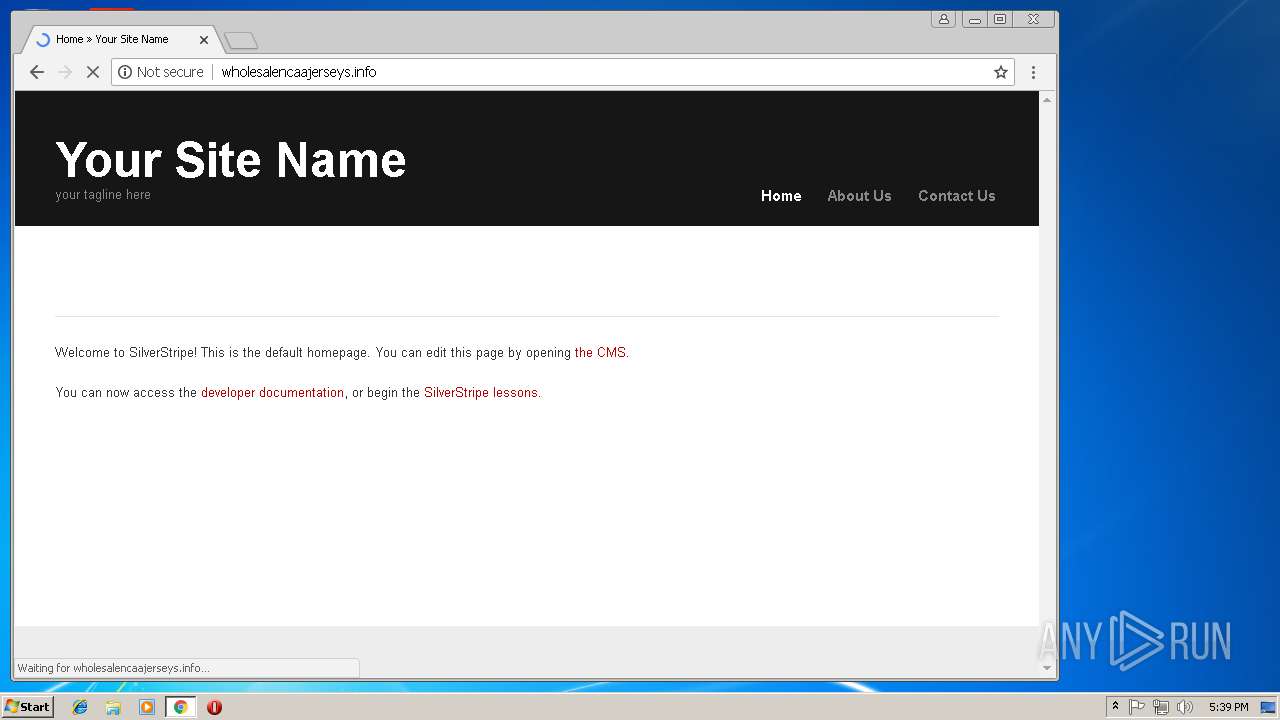
| URL: | http://herbalifehalisekilic.com |
| Full analysis: | https://app.any.run/tasks/6af66c85-e0a3-49be-ad13-f57e4a150afc |
| Verdict: | Malicious activity |
| Analysis date: | November 15, 2018, 17:35:26 |
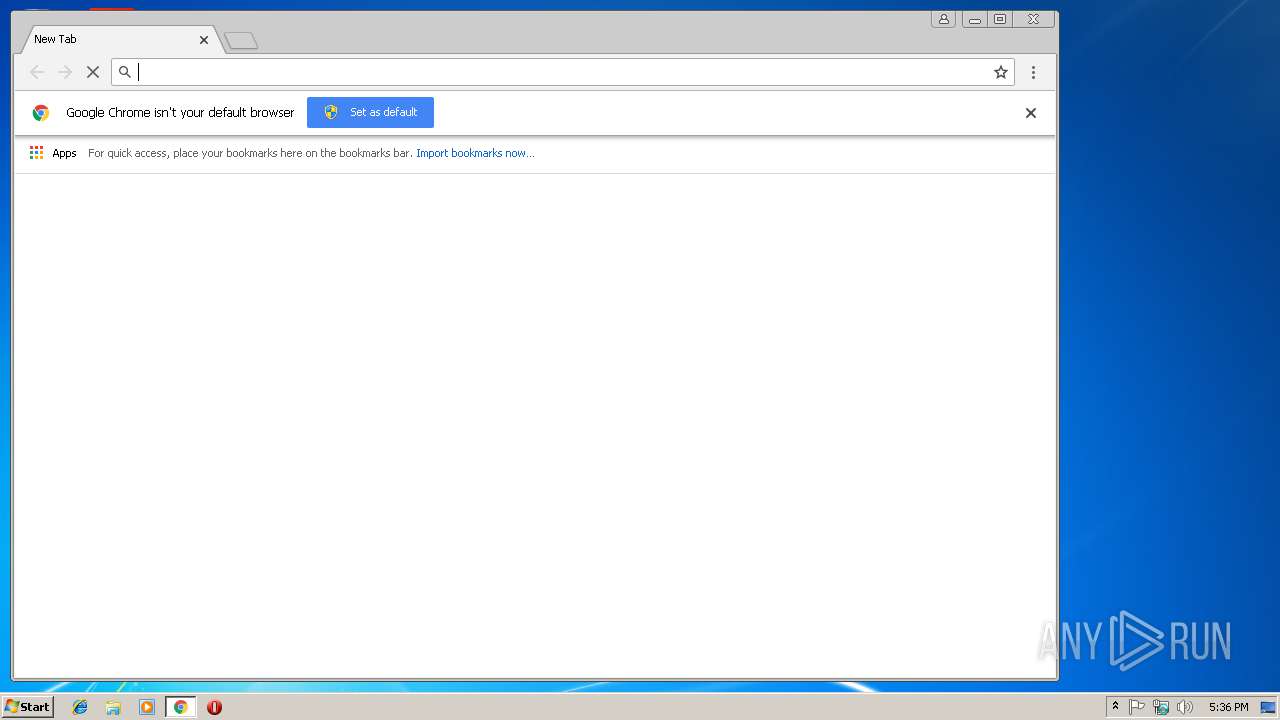
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | D8D02E3ABC6F4D30C286B2687C87FCBF |
| SHA1: | 8756FA5438284AE5EECCD339308517D65F761987 |
| SHA256: | 42D18CDBBC0A941C7E0064A89796383E98091522B273044AFDEA9CF4381F7FD9 |
| SSDEEP: | 3:N1KWAXEJMc7tdIn:CWUEJDfIn |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Changes internet zones settings
- iexplore.exe (PID: 2788)
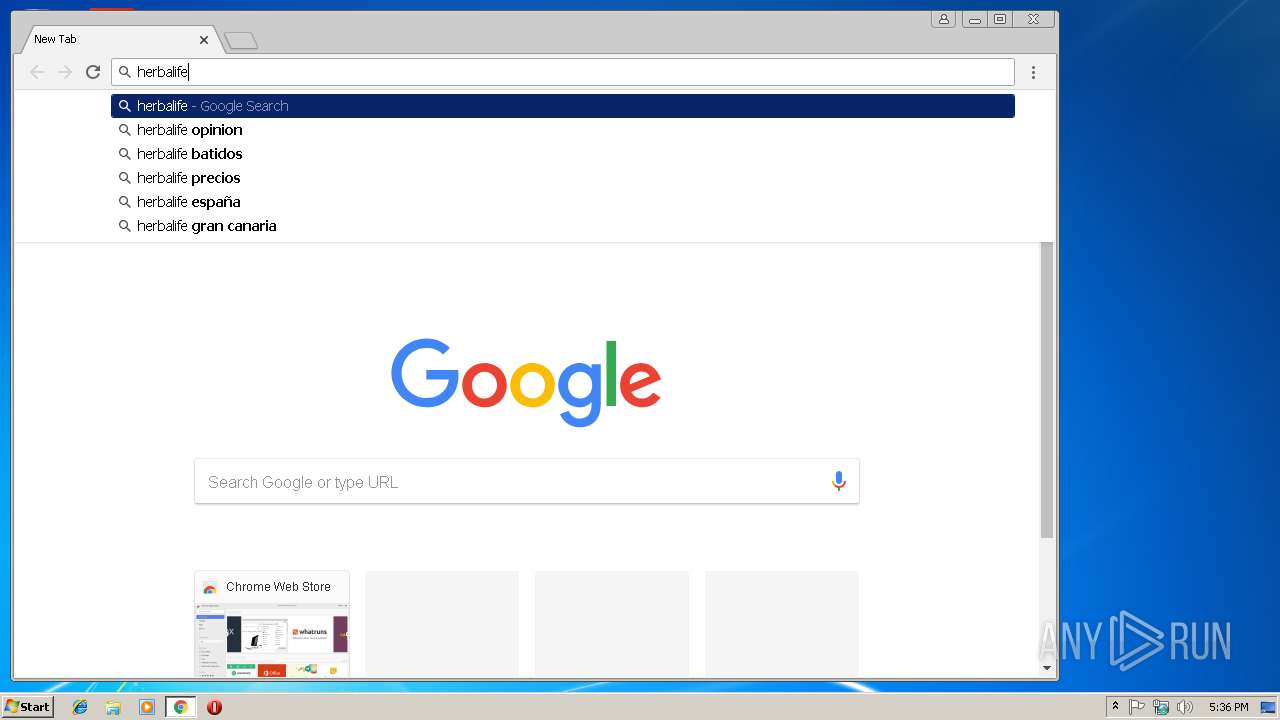
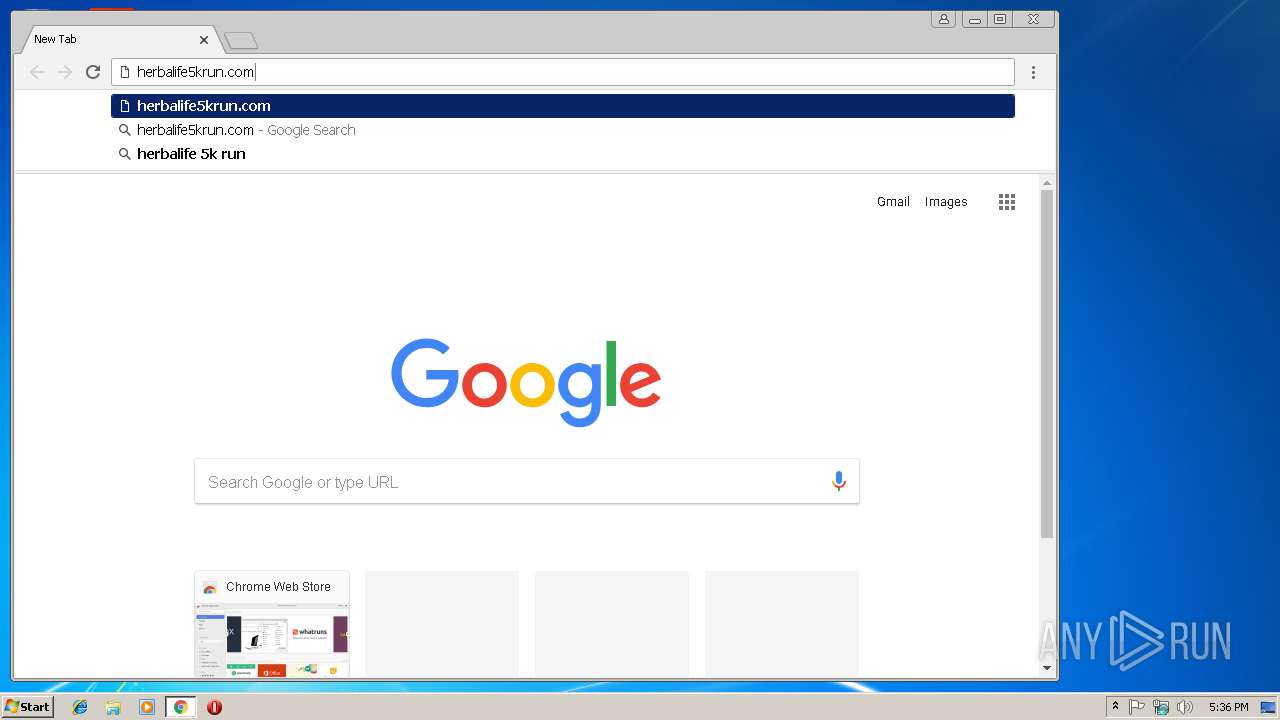
Application launched itself
- iexplore.exe (PID: 2788)
- chrome.exe (PID: 2776)
Reads Internet Cache Settings
- iexplore.exe (PID: 3680)
- iexplore.exe (PID: 2788)
Reads internet explorer settings
- iexplore.exe (PID: 3680)
Reads settings of System Certificates
- iexplore.exe (PID: 3680)
Creates files in the user directory
- iexplore.exe (PID: 3680)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
56
Monitored processes
24
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 568 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=884,5212728993505563693,12324524413794377909,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=6D837F232BB6BC0D696BF7C55011459D --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6D837F232BB6BC0D696BF7C55011459D --renderer-client-id=17 --mojo-platform-channel-handle=948 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 864 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=884,5212728993505563693,12324524413794377909,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=8CAD0B0B380E9696DAB13CC2AB187B62 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8CAD0B0B380E9696DAB13CC2AB187B62 --renderer-client-id=18 --mojo-platform-channel-handle=3468 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2088 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=884,5212728993505563693,12324524413794377909,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=F88EF4B6A8D0F5E1DFA3E54371B8A0BC --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=F88EF4B6A8D0F5E1DFA3E54371B8A0BC --renderer-client-id=16 --mojo-platform-channel-handle=2328 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2120 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=884,5212728993505563693,12324524413794377909,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=D5944EA9DEDC5608618EC4BB73E8FFBB --mojo-platform-channel-handle=3856 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=884,5212728993505563693,12324524413794377909,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=1BA2C3322C3F11969D3E13CC82755CC1 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1BA2C3322C3F11969D3E13CC82755CC1 --renderer-client-id=14 --mojo-platform-channel-handle=612 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2260 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=884,5212728993505563693,12324524413794377909,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2093B8290FD80429ACF4EF682C729C2B --mojo-platform-channel-handle=2112 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2276 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=884,5212728993505563693,12324524413794377909,131072 --enable-features=PasswordImport --service-pipe-token=B98C4881B3019F72C4C9CED98B79186B --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=B98C4881B3019F72C4C9CED98B79186B --renderer-client-id=3 --mojo-platform-channel-handle=2160 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=884,5212728993505563693,12324524413794377909,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=503152950A24243CFE9B318B840032DA --mojo-platform-channel-handle=848 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2424 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=884,5212728993505563693,12324524413794377909,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=053BFAC20307A2F7A89852B23AAEA898 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=053BFAC20307A2F7A89852B23AAEA898 --renderer-client-id=8 --mojo-platform-channel-handle=3976 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2540 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=884,5212728993505563693,12324524413794377909,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=AE9B49E3F7E27F2CFF30597EB42B7F40 --mojo-platform-channel-handle=1468 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
1 040
Read events
899
Write events
133
Delete events
8
Modification events
| (PID) Process: | (2788) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2788) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2788) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2788) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2788) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2788) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2788) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {DC8F2475-E8FC-11E8-A67C-5254004AAD11} |
Value: 0 | |||
| (PID) Process: | (2788) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2788) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (2788) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E2070B0004000F001100230026000400 | |||
Executable files
0
Suspicious files
96
Text files
215
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2788 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2788 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3680 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\PP6KS563\ortak[1].css | text | |
MD5:— | SHA256:— | |||
| 3680 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\js[1].js | text | |
MD5:— | SHA256:— | |||
| 3680 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\U2ZG9DE0\style[1].css | text | |
MD5:— | SHA256:— | |||
| 3680 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\BWPPCY0O\font[1].css | text | |
MD5:— | SHA256:— | |||
| 3680 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\pf_din_text_comp_pro_regular-webfont[1].eot | eot | |
MD5:— | SHA256:— | |||
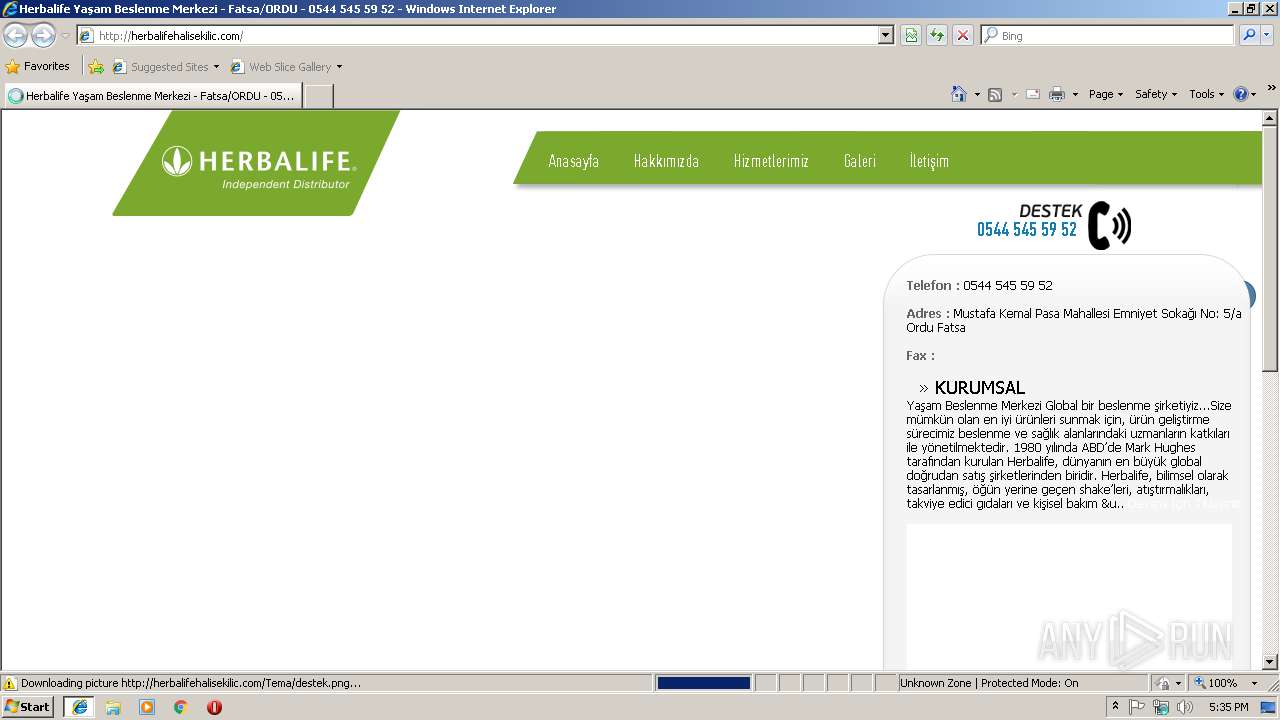
| 3680 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\herbalifehalisekilic_com[1].htm | html | |
MD5:— | SHA256:— | |||
| 3680 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\pf_din_text_comp_pro_medium-webfont[1].eot | eot | |
MD5:— | SHA256:— | |||
| 3680 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\PP6KS563\pfdindisplaypro_regular-webfont[1].eot | eot | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
192
TCP/UDP connections
184
DNS requests
114
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3680 | iexplore.exe | GET | — | 37.123.99.17:80 | http://herbalifehalisekilic.com/qinternet/jquery-1.7.2.js | TR | — | — | suspicious |
3680 | iexplore.exe | GET | 200 | 37.123.99.17:80 | http://herbalifehalisekilic.com/qinternet/js.js | TR | text | 1.34 Kb | suspicious |
3680 | iexplore.exe | GET | 200 | 37.123.99.17:80 | http://herbalifehalisekilic.com/qinternet/font.css | TR | text | 350 b | suspicious |
3680 | iexplore.exe | GET | 200 | 37.123.99.17:80 | http://herbalifehalisekilic.com/ | TR | html | 3.43 Kb | suspicious |
3680 | iexplore.exe | GET | 200 | 37.123.99.17:80 | http://herbalifehalisekilic.com/qinternet/fontlar/pfdindisplaypro_regular-webfont.eot? | TR | eot | 17.7 Kb | suspicious |
3680 | iexplore.exe | GET | 200 | 37.123.99.17:80 | http://herbalifehalisekilic.com/qinternet/fontlar/pf_din_text_comp_pro_regular-webfont.eot? | TR | eot | 16.8 Kb | suspicious |
3680 | iexplore.exe | GET | 200 | 37.123.99.17:80 | http://herbalifehalisekilic.com/qinternet/ortak.css | TR | text | 525 b | suspicious |
3680 | iexplore.exe | GET | 200 | 37.123.99.17:80 | http://herbalifehalisekilic.com/qinternet/flexslider/flexslider.css | TR | eot | 16.8 Kb | suspicious |
3680 | iexplore.exe | GET | 200 | 37.123.99.17:80 | http://herbalifehalisekilic.com/qinternet/fontlar/pfdindisplaypro_medium-webfont.eot? | TR | eot | 17.7 Kb | suspicious |
3680 | iexplore.exe | GET | 200 | 37.123.99.17:80 | http://herbalifehalisekilic.com/qinternet/alibox/lightbox/themes/facebook/jquery.lightbox.css | TR | text | 1.15 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2776 | chrome.exe | 216.58.215.234:443 | maps.googleapis.com | Google Inc. | US | whitelisted |
2776 | chrome.exe | 216.58.215.237:443 | accounts.google.com | Google Inc. | US | whitelisted |
2776 | chrome.exe | 216.58.215.238:443 | apis.google.com | Google Inc. | US | whitelisted |
2776 | chrome.exe | 172.217.168.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
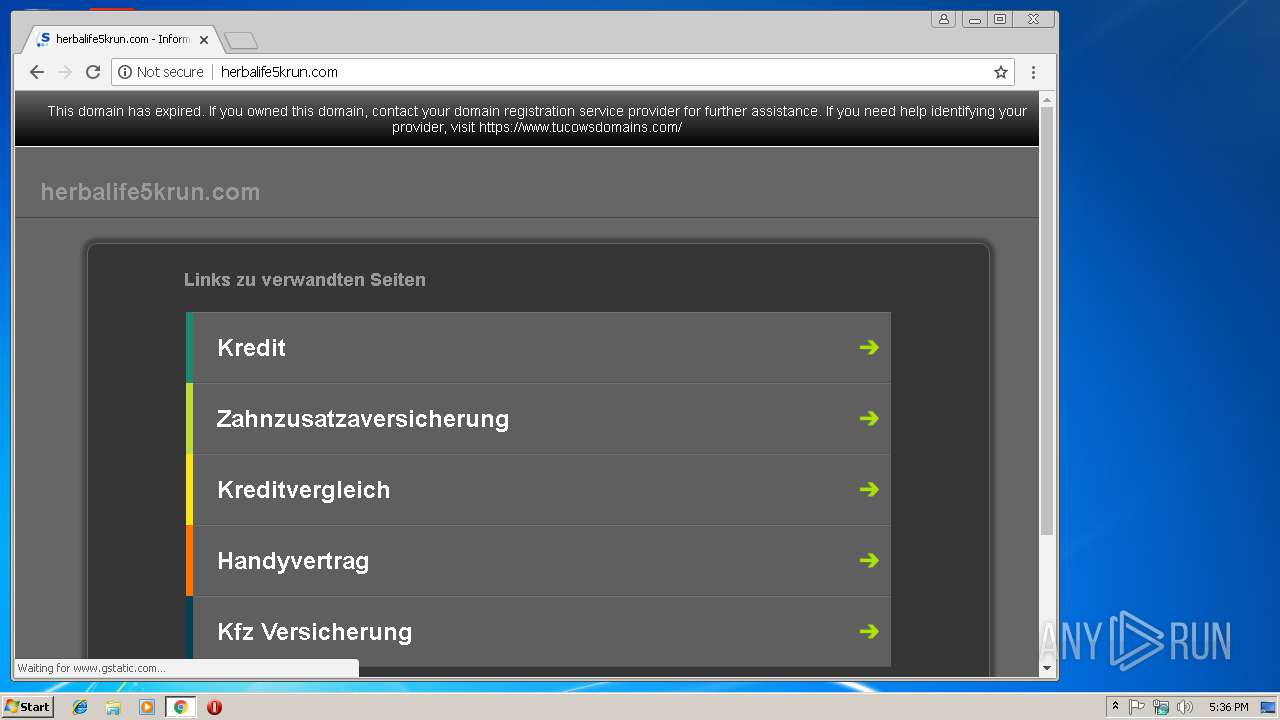
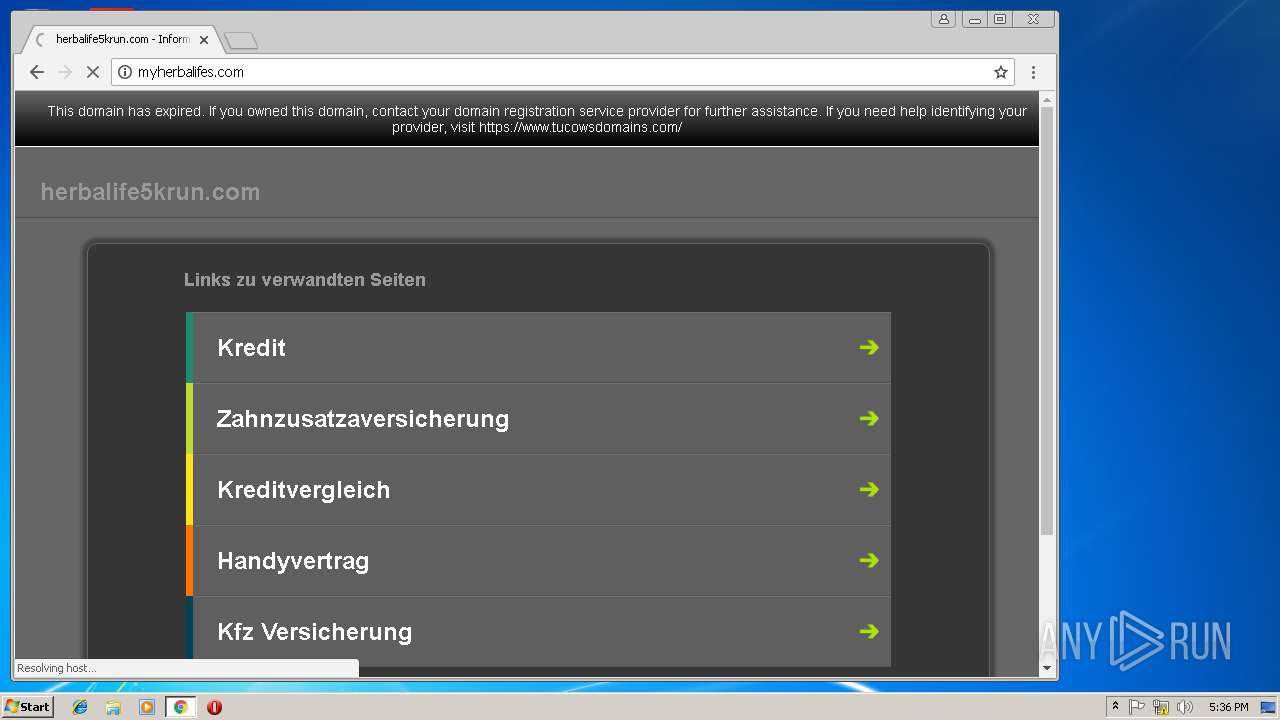
2776 | chrome.exe | 209.200.154.54:80 | herbalife5krun.com | Akamai Technologies, Inc. | US | whitelisted |
2776 | chrome.exe | 172.217.168.36:443 | www.google.com | Google Inc. | US | whitelisted |
2788 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3680 | iexplore.exe | 37.123.99.17:80 | herbalifehalisekilic.com | SPDNet Telekomunikasyon Hizmetleri Bilgi Teknolojileri Taahhut Sanayi Ve Ticaret A.S. | TR | suspicious |
3680 | iexplore.exe | 172.217.168.36:443 | www.google.com | Google Inc. | US | whitelisted |
2776 | chrome.exe | 91.215.103.64:443 | script.ioam.de | INFOnline GmbH | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
herbalifehalisekilic.com |
| suspicious |
www.bing.com |
| whitelisted |
www.google.com |
| malicious |
maps.googleapis.com |
| whitelisted |
maps.gstatic.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
www.google.de |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
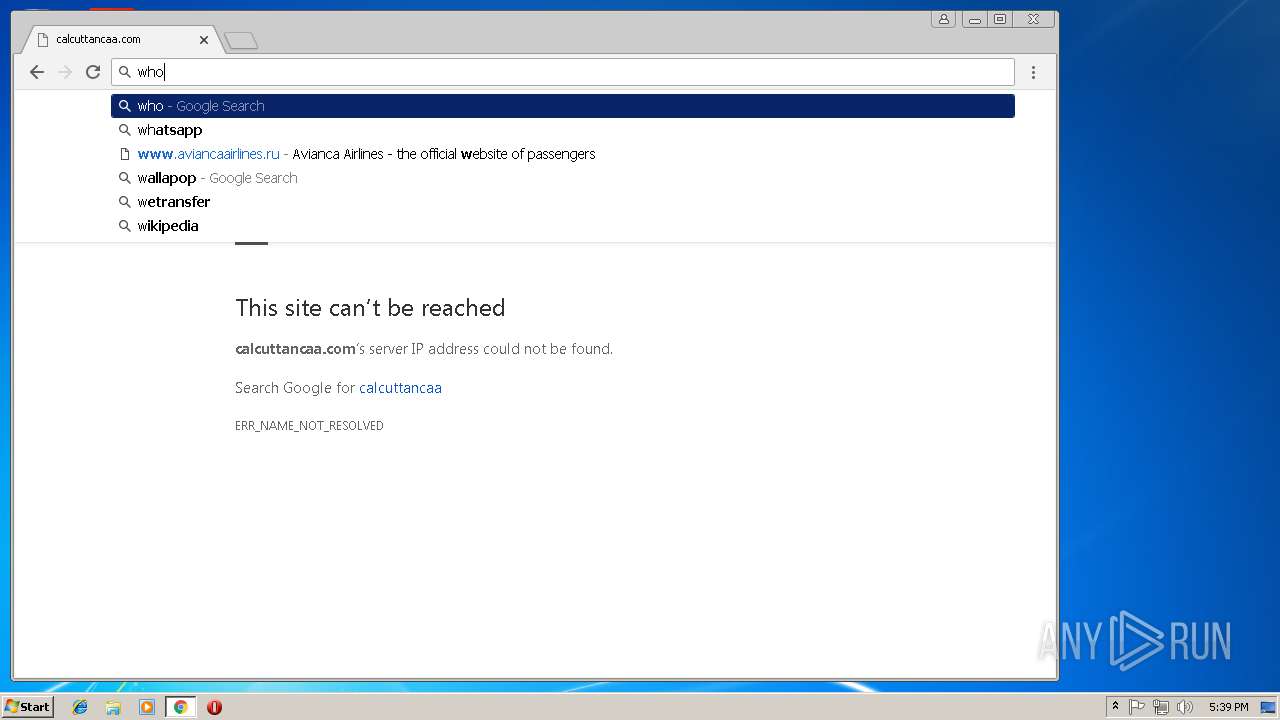
2776 | chrome.exe | A Network Trojan was detected | SC BAD_UNKNOWN Trojan Unknown JS |
2776 | chrome.exe | Generic Protocol Command Decode | SURICATA Applayer Wrong direction first Data |