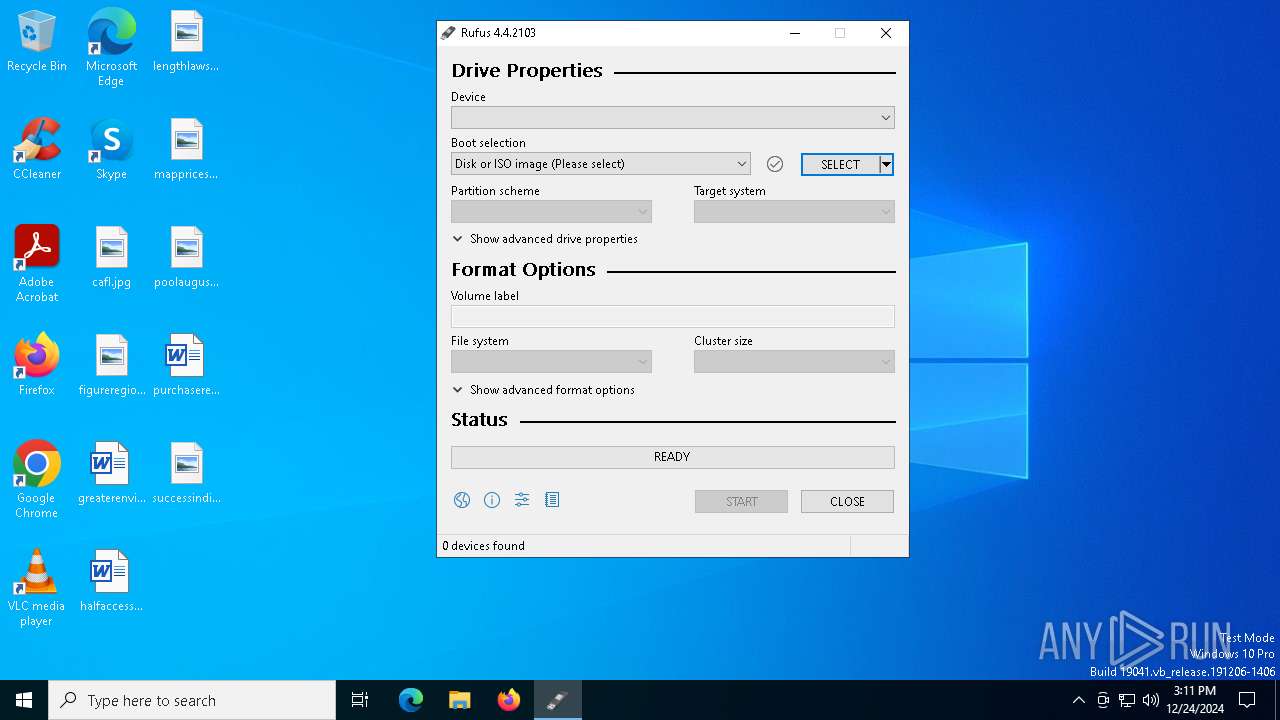
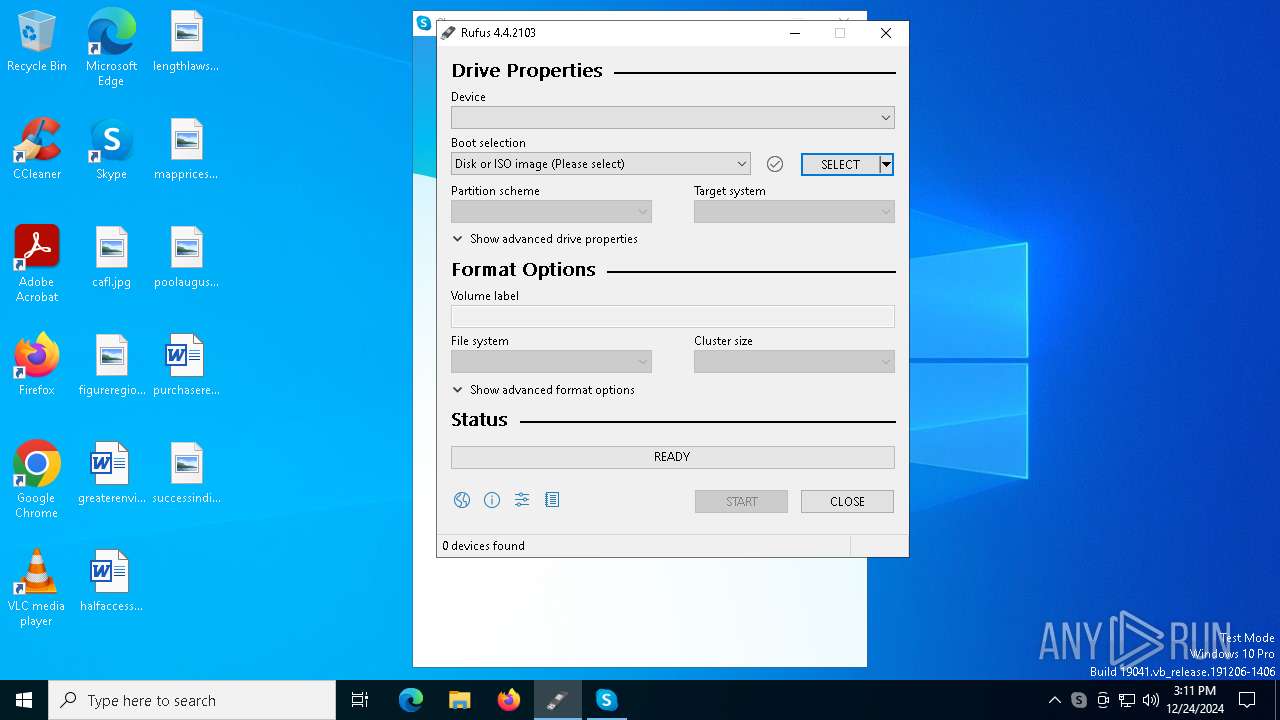
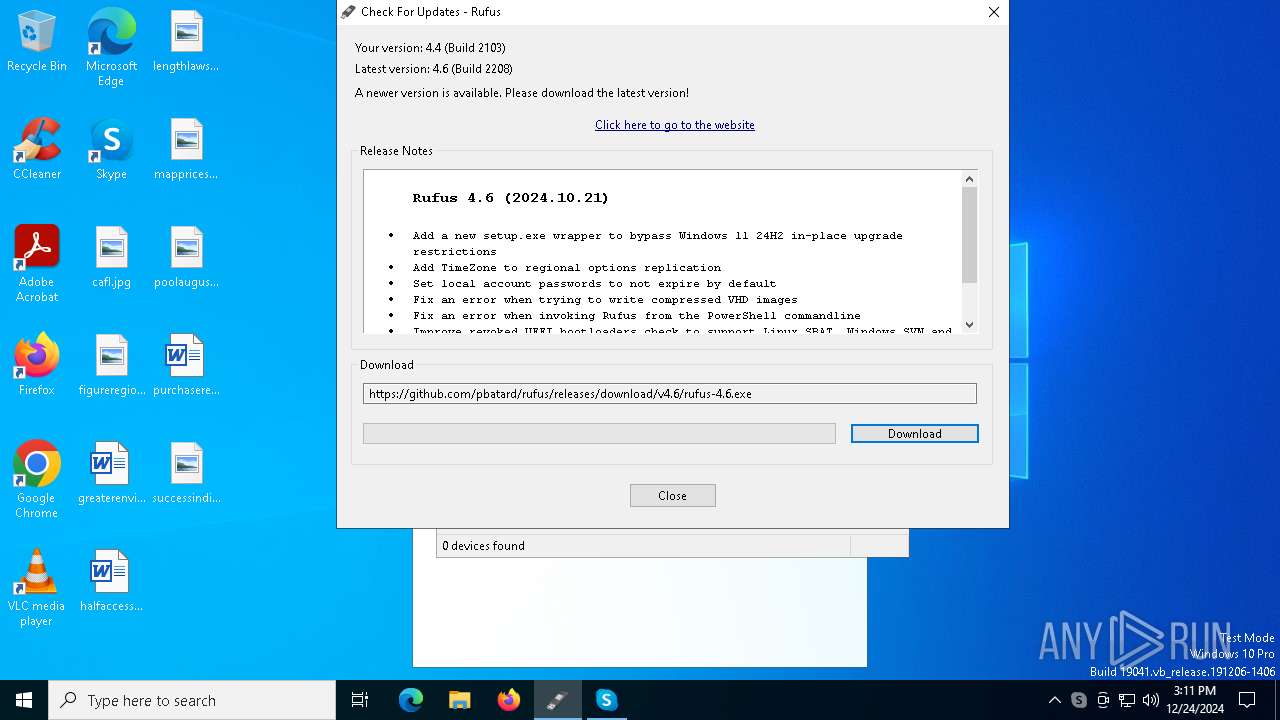
| File name: | rufus-4.4.exe |
| Full analysis: | https://app.any.run/tasks/36ba2748-708c-429e-8e77-eb3b7cfff65d |
| Verdict: | Malicious activity |
| Analysis date: | December 24, 2024, 15:10:58 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64 (stripped to external PDB), for MS Windows, 3 sections |
| MD5: | 7A4662BB7F331D2252F3D949657D821D |
| SHA1: | AD53FDDFBCEAD7B3E6C322C0AAD8C4A826BD4967 |
| SHA256: | 42CDB16F6DD64C4FEC30C7A71960FE4D0015862C37E7B02C8DBA5C0D68384C74 |
| SSDEEP: | 49152:cVDHlx7SwaaRhXjrt2n11roEyeJvQ2PNZLOylTYazB0fRki1S4La2FMhwCYUuFQb:cVXTRZjrtG11rHy8vTlZL7TYazWR5FLm |
MALICIOUS
Changes the Windows auto-update feature
- rufus-4.4.exe (PID: 6344)
Changes the autorun value in the registry
- reg.exe (PID: 3680)
SUSPICIOUS
Executes as Windows Service
- vds.exe (PID: 6420)
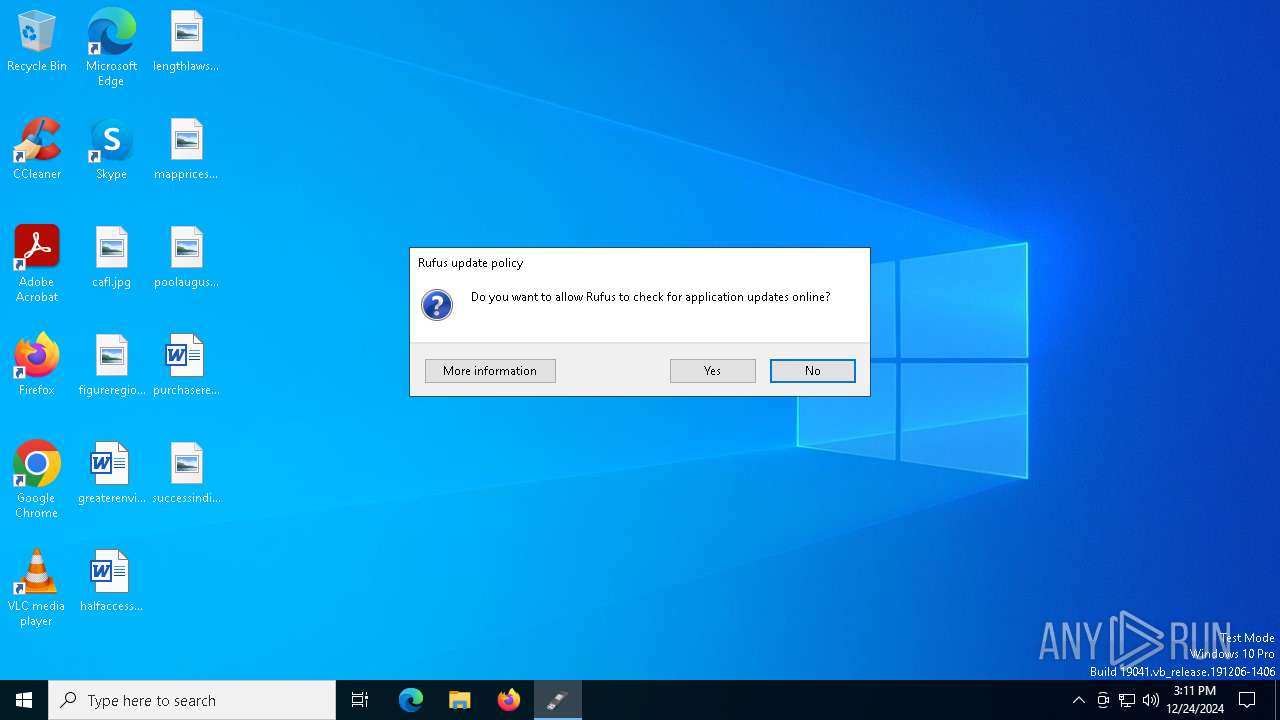
Checks Windows Trust Settings
- rufus-4.4.exe (PID: 6344)
Reads security settings of Internet Explorer
- rufus-4.4.exe (PID: 6344)
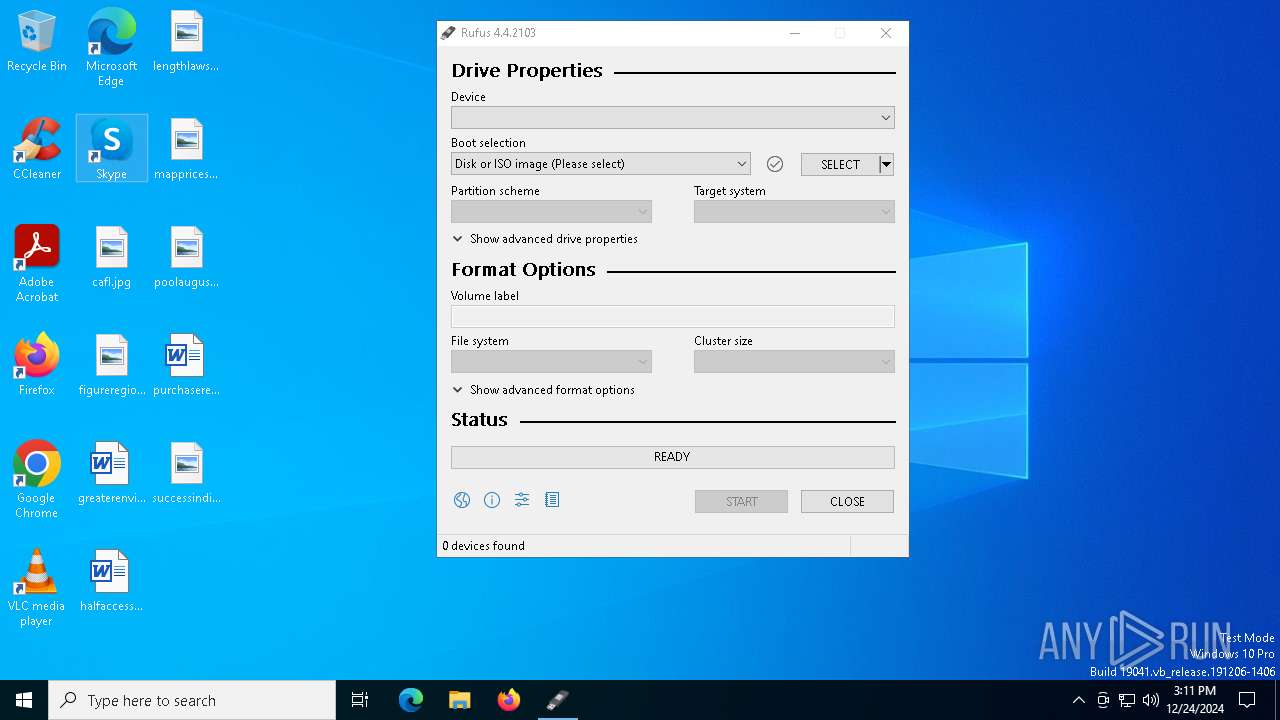
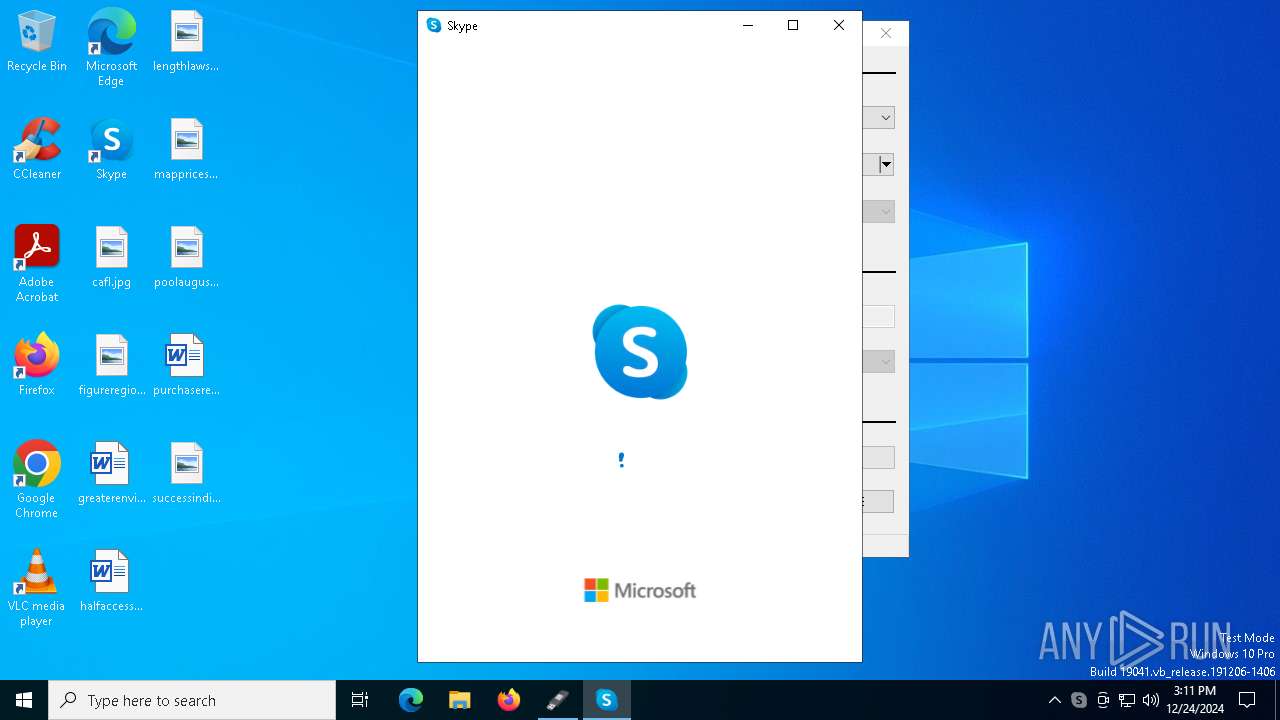
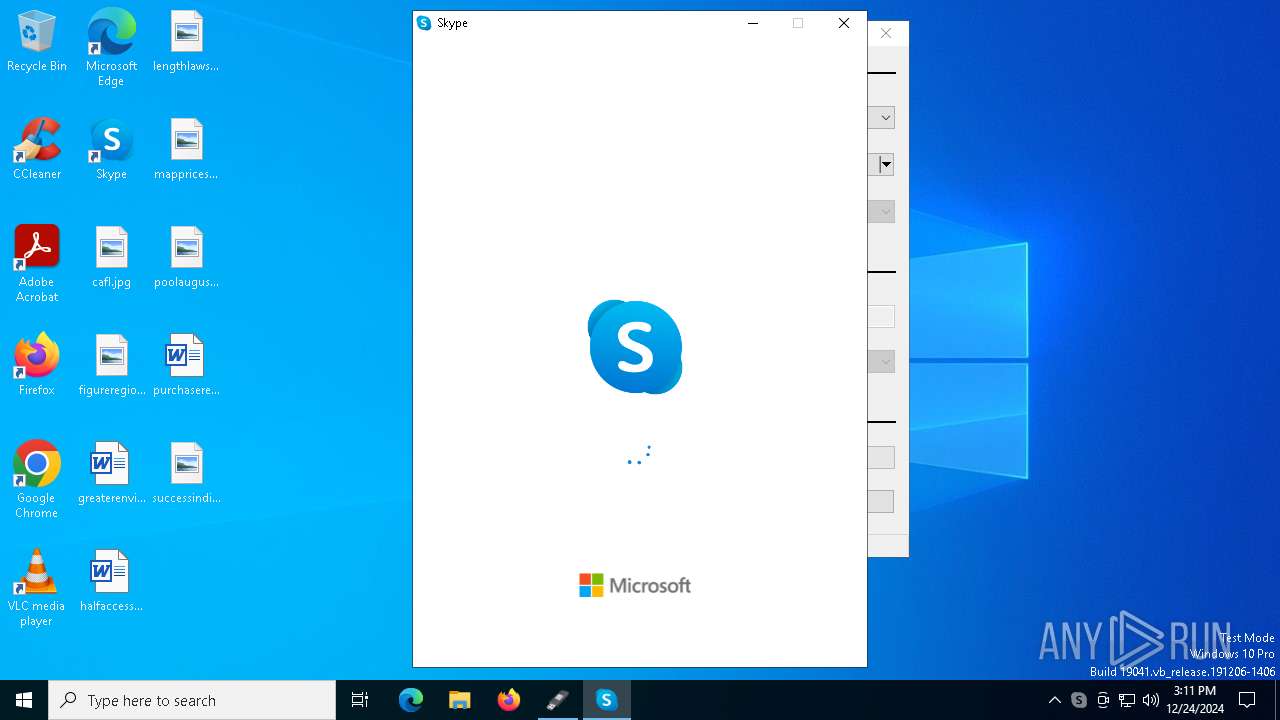
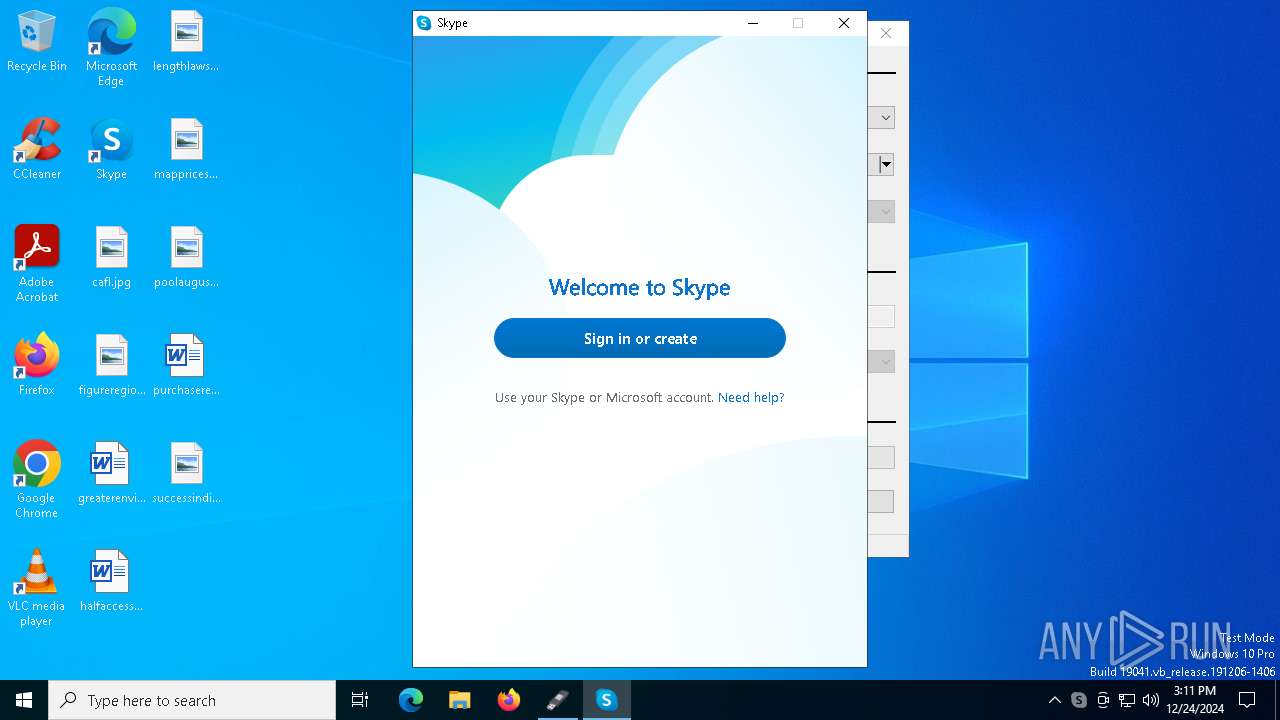
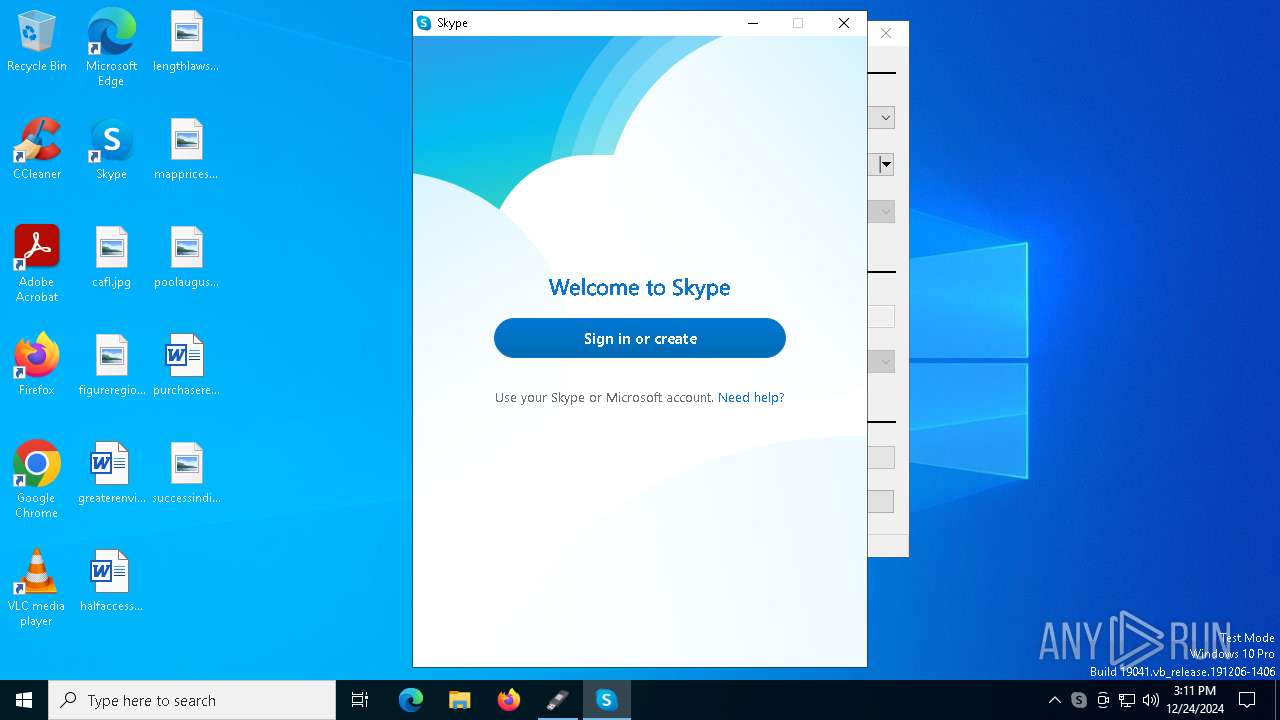
Application launched itself
- Skype.exe (PID: 6616)
Uses REG/REGEDIT.EXE to modify registry
- Skype.exe (PID: 6616)
Detected use of alternative data streams (AltDS)
- Skype.exe (PID: 6616)
INFO
Checks supported languages
- rufus-4.4.exe (PID: 6344)
- Skype.exe (PID: 1412)
- Skype.exe (PID: 6616)
- Skype.exe (PID: 3524)
- Skype.exe (PID: 5244)
- Skype.exe (PID: 5544)
Reads the computer name
- rufus-4.4.exe (PID: 6344)
- Skype.exe (PID: 3524)
- Skype.exe (PID: 5888)
- Skype.exe (PID: 5244)
Reads the machine GUID from the registry
- rufus-4.4.exe (PID: 6344)
Sends debugging messages
- rufus-4.4.exe (PID: 6344)
Process checks whether UAC notifications are on
- rufus-4.4.exe (PID: 6344)
Reads the software policy settings
- rufus-4.4.exe (PID: 6344)
- Skype.exe (PID: 6616)
Creates files or folders in the user directory
- rufus-4.4.exe (PID: 6344)
- Skype.exe (PID: 6616)
- Skype.exe (PID: 5244)
- Skype.exe (PID: 5888)
Manual execution by a user
- Skype.exe (PID: 6616)
Checks proxy server information
- rufus-4.4.exe (PID: 6344)
- Skype.exe (PID: 6616)
Reads CPU info
- Skype.exe (PID: 6616)
Process checks computer location settings
- Skype.exe (PID: 6616)
- Skype.exe (PID: 5244)
- Skype.exe (PID: 5544)
Create files in a temporary directory
- Skype.exe (PID: 6616)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (87.1) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.4) |
| .exe | | | DOS Executable Generic (6.4) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:01:17 14:16:26+00:00 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, Large address aware, No debug |
| PEType: | PE32+ |
| LinkerVersion: | 2.41 |
| CodeSize: | 1380352 |
| InitializedDataSize: | 45056 |
| UninitializedDataSize: | 2629632 |
| EntryPoint: | 0x3d3270 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows GUI |
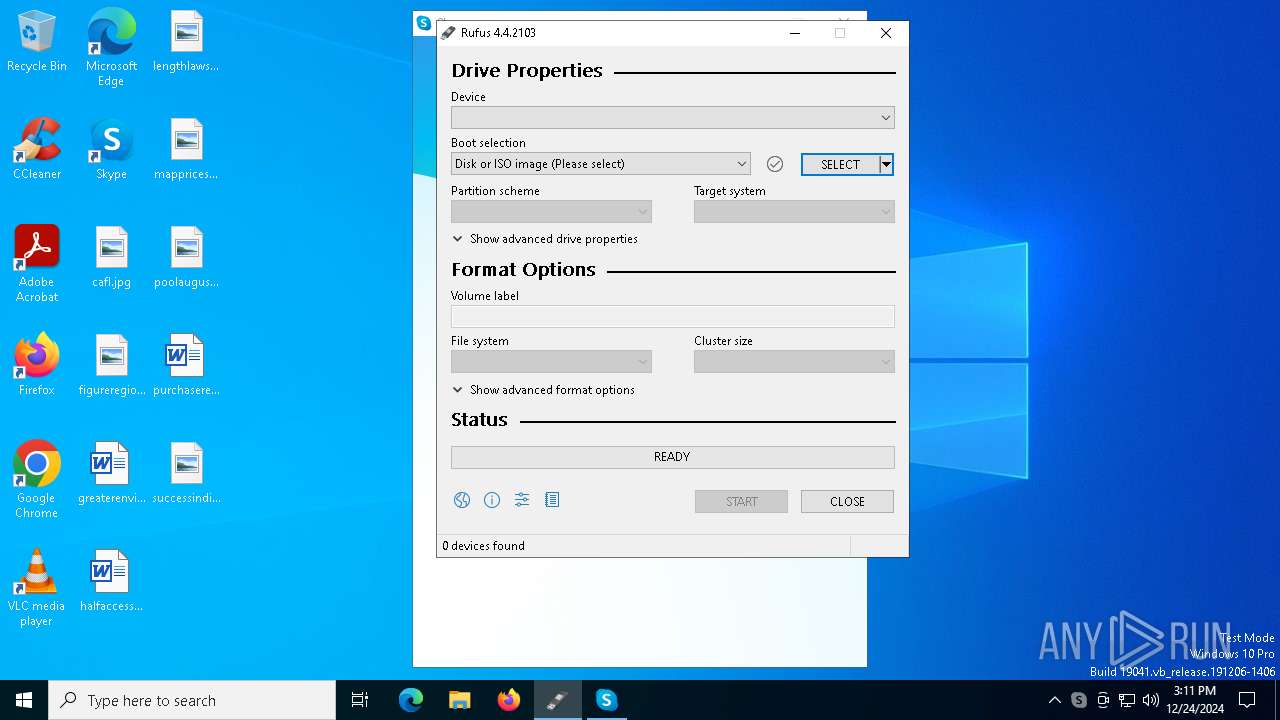
| FileVersionNumber: | 4.4.2103.0 |
| ProductVersionNumber: | 4.4.2103.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | https://rufus.ie |
| CompanyName: | Akeo Consulting |
| FileDescription: | Rufus |
| FileVersion: | 4.4.2103 |
| InternalName: | Rufus |
| LegalCopyright: | © 2011-2024 Pete Batard (GPL v3) |
| LegalTrademarks: | https://www.gnu.org/licenses/gpl-3.0.html |
| OriginalFileName: | rufus-4.4.exe |
| ProductName: | Rufus |
| ProductVersion: | 4.4.2103 |
Total processes
157
Monitored processes
24
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1412 | "C:\Program Files (x86)\Microsoft\Skype for Desktop\Skype.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Roaming\Microsoft\Skype for Desktop" /prefetch:7 --no-rate-limit --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Roaming\Microsoft\Skype for Desktop\Crashpad" --url=appcenter://generic?aid=a7417433-29d9-4bc0-8826-af367733939d&iid=868d4f0b-b29b-4967-461d-2a3581a09553&uid=868d4f0b-b29b-4967-461d-2a3581a09553 --annotation=IsOfficialBuild=1 --annotation=_companyName=Skype --annotation=_productName=skype-preview --annotation=_version=8.104.0.207 "--annotation=exe=C:\Program Files (x86)\Microsoft\Skype for Desktop\Skype.exe" --annotation=plat=Win32 --annotation=prod=Electron --annotation=ver=19.1.8 --initial-client-data=0x580,0x584,0x588,0x57c,0x58c,0x7633398,0x76333a8,0x76333b4 | C:\Program Files (x86)\Microsoft\Skype for Desktop\Skype.exe | — | Skype.exe | |||||||||||
User: admin Company: Skype Technologies S.A. Integrity Level: MEDIUM Description: Skype Version: 8.104.0.207 Modules
| |||||||||||||||
| 1684 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | reg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1740 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | reg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1904 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | reg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2008 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | reg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3140 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | reg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3524 | "C:\Program Files (x86)\Microsoft\Skype for Desktop\Skype.exe" --type=gpu-process --user-data-dir="C:\Users\admin\AppData\Roaming\Microsoft\Skype for Desktop" --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=2084 --field-trial-handle=2132,i,6043829111957808452,16553112951559395075,131072 --enable-features=WinUseBrowserSpellChecker,WinUseHybridSpellChecker,WinrtGeolocationImplementation --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:2 | C:\Program Files (x86)\Microsoft\Skype for Desktop\Skype.exe | — | Skype.exe | |||||||||||
User: admin Company: Skype Technologies S.A. Integrity Level: LOW Description: Skype Version: 8.104.0.207 Modules
| |||||||||||||||
| 3680 | C:\WINDOWS\system32\reg.exe ADD HKCU\Software\Microsoft\Windows\CurrentVersion\Run /v "Skype for Desktop" /t REG_SZ /d "C:\Program Files (x86)\Microsoft\Skype for Desktop\Skype.exe" /f | C:\Windows\SysWOW64\reg.exe | Skype.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3816 | C:\WINDOWS\system32\reg.exe QUERY HKCU\Software\Microsoft\Edge\BLBeacon /v version | C:\Windows\SysWOW64\reg.exe | — | Skype.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3876 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | reg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
6 293
Read events
6 209
Write events
34
Delete events
50
Modification events
| (PID) Process: | (6344) rufus-4.4.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Group Policy Objects\{5D843170-3C1B-4394-89E6-3A82B5220648}Machine\Software\Policies\Microsoft\AppHVSI |
| Operation: | write | Name: | AllowAppHVSI_ProviderSet |
Value: 0 | |||
| (PID) Process: | (6344) rufus-4.4.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Group Policy Objects\{5D843170-3C1B-4394-89E6-3A82B5220648}Machine\Software\Policies\Microsoft\EdgeUpdate |
| Operation: | write | Name: | UpdateDefault |
Value: 0 | |||
| (PID) Process: | (6344) rufus-4.4.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Group Policy Objects\{5D843170-3C1B-4394-89E6-3A82B5220648}Machine\Software\Policies\Microsoft\Windows\Network Connections |
| Operation: | write | Name: | NC_DoNotShowLocalOnlyIcon |
Value: 1 | |||
| (PID) Process: | (6344) rufus-4.4.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Group Policy Objects\{5D843170-3C1B-4394-89E6-3A82B5220648}Machine\Software\Policies\Microsoft\Windows\Windows Feeds |
| Operation: | write | Name: | EnableFeeds |
Value: 0 | |||
| (PID) Process: | (6344) rufus-4.4.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Group Policy Objects\{5D843170-3C1B-4394-89E6-3A82B5220648}Machine\Software\Policies\Microsoft\Windows\WindowsUpdate |
| Operation: | write | Name: | WUServer |
Value: http://neverupdatewindows10.com | |||
| (PID) Process: | (6344) rufus-4.4.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Group Policy Objects\{5D843170-3C1B-4394-89E6-3A82B5220648}Machine\Software\Policies\Microsoft\Windows\WindowsUpdate |
| Operation: | write | Name: | WUStatusServer |
Value: http://neverupdatewindows10.com | |||
| (PID) Process: | (6344) rufus-4.4.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Group Policy Objects\{5D843170-3C1B-4394-89E6-3A82B5220648}Machine\Software\Policies\Microsoft\Windows\WindowsUpdate |
| Operation: | write | Name: | UpdateServiceUrlAlternate |
Value: http://neverupdatewindows10.com | |||
| (PID) Process: | (6344) rufus-4.4.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Group Policy Objects\{5D843170-3C1B-4394-89E6-3A82B5220648}Machine\Software\Policies\Microsoft\Windows\WindowsUpdate |
| Operation: | write | Name: | **del.FillEmptyContentUrls |
Value: | |||
| (PID) Process: | (6344) rufus-4.4.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Group Policy Objects\{5D843170-3C1B-4394-89E6-3A82B5220648}Machine\Software\Policies\Microsoft\Windows\WindowsUpdate\AU |
| Operation: | write | Name: | UseWUServer |
Value: 1 | |||
| (PID) Process: | (6344) rufus-4.4.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Group Policy Objects\{5D843170-3C1B-4394-89E6-3A82B5220648}Machine\Software\Policies\Microsoft\Windows\WindowsUpdate\AU |
| Operation: | write | Name: | NoAutoUpdate |
Value: 0 | |||
Executable files
0
Suspicious files
50
Text files
11
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6344 | rufus-4.4.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_89854CA6A0F0936A4D2ECA78845CEA25 | binary | |
MD5:9FC863048443AA9F0A5C4C7D5A5E33DB | SHA256:2B9AAAD554465807B3043B15B8A020941776271DA76639DE71A9A5FD6835DE1B | |||
| 6616 | Skype.exe | C:\Users\admin\AppData\Roaming\Microsoft\Skype for Desktop\Crashpad\settings.dat | binary | |
MD5:9D0439A794AA96ABD6AFF504C86C7F31 | SHA256:5DBC3A5DAF431973E245D83AB51B128E9C4CC2F3ECD61C45C88DB161ACC25B7B | |||
| 6344 | rufus-4.4.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\A66A8DB907BADC9D16AD67B2FBFFDD5C | binary | |
MD5:96D3940285F7CD40FE5F0E4496F3E663 | SHA256:181385919E9BF052199E4B1BB415363C5AACA6D4BC2176987231CCA3B3EB365F | |||
| 6616 | Skype.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\CX8HZ52SG49BYIPJVCRG.temp | binary | |
MD5:21DF407175BFA4D5A84F85B3FE4EB9F1 | SHA256:8A75F521039B51B2BCAA63938B96F4E8D3C6E83F89E393C84105C876FF171BD8 | |||
| 6616 | Skype.exe | C:\Users\admin\AppData\Roaming\Microsoft\Spelling\en-US\default.acl | text | |
MD5:F3B25701FE362EC84616A93A45CE9998 | SHA256:B3D510EF04275CA8E698E5B3CBB0ECE3949EF9252F0CDC839E9EE347409A2209 | |||
| 6616 | Skype.exe | C:\Users\admin\AppData\Roaming\Microsoft\Skype for Desktop\Local Storage\leveldb\LOG.old | text | |
MD5:46EED8B7CAAD25F7F453617DA0FB0857 | SHA256:5BC1DE0E32F2969386351B2BE088F13B6CC3DF7693EE9E92FEEF59DB6AF1FB92 | |||
| 6616 | Skype.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\b916037c1e115fe0.customDestinations-ms | binary | |
MD5:21DF407175BFA4D5A84F85B3FE4EB9F1 | SHA256:8A75F521039B51B2BCAA63938B96F4E8D3C6E83F89E393C84105C876FF171BD8 | |||
| 6616 | Skype.exe | C:\Users\admin\AppData\Roaming\Microsoft\Spelling\en-US\default.dic | text | |
MD5:F3B25701FE362EC84616A93A45CE9998 | SHA256:B3D510EF04275CA8E698E5B3CBB0ECE3949EF9252F0CDC839E9EE347409A2209 | |||
| 6344 | rufus-4.4.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_49536AB5156BDD74EFF881D01C36A419 | binary | |
MD5:1DF3D9D524E78F02EF5D06FEFE62CC23 | SHA256:D41A4A23ED123A2C645F12781FC01DD371647C5259E8952378FE476F36BA6484 | |||
| 6344 | rufus-4.4.exe | C:\Windows\System32\GroupPolicy\gpt.ini | text | |
MD5:3D89F23265C9E30A0CF055C3EB4D637C | SHA256:806582F6221C79BD4C7EACDC4B63E937CE247EEE2BA159F55C545CDFB2B1C25B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
57
DNS requests
39
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6344 | rufus-4.4.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.usertrust.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBSr83eyJy3njhjVpn5bEpfc6MXawQQUOuEJhtTPGcKWdnRJdtzgNcZjY5oCEQDzZE5rbgBQI34JRr174fUd | unknown | — | — | whitelisted |
6344 | rufus-4.4.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAz1vQYrVgL0erhQLCPM8GY%3D | unknown | — | — | whitelisted |
6344 | rufus-4.4.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPlNxcMEqnlIVyH5VuZ4lawhZX3QQU9oUKOxGG4QR9DqoLLNLuzGR7e64CEE4o94a2bBo7lCzSxA63QqU%3D | unknown | — | — | whitelisted |
6344 | rufus-4.4.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEFZnHQTqT5lMbxCBR1nSdZQ%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1356 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1356 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
4536 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 2.23.181.156:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 2.21.110.146:443 | www.bing.com | AKAMAI-AS | DE | whitelisted |
1076 | svchost.exe | 23.213.166.81:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
1176 | svchost.exe | 20.190.159.0:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
rufus.ie |
| unknown |
github.com |
| shared |
ocsp.comodoca.com |
| whitelisted |
Threats
Process | Message |
|---|---|
rufus-4.4.exe | *** Rufus init ***
|
rufus-4.4.exe | App dir: 'C:\Users\admin\AppData\Local\Temp\'
|
rufus-4.4.exe | Cur dir: 'C:\Users\admin\AppData\Local\Temp\'
|
rufus-4.4.exe | Tmp dir: 'C:\Users\admin\AppData\Local\Temp\'
|
rufus-4.4.exe | Sys dir: 'C:\WINDOWS\system32'
|
rufus-4.4.exe | Dat dir: 'C:\Users\admin\AppData\Local'
|
rufus-4.4.exe | Usr dir: 'C:\Users\admin'
|
rufus-4.4.exe | Binary executable is signed by 'Akeo Consulting'
|
rufus-4.4.exe | Will use settings from registry
|
rufus-4.4.exe | loc file not found in current directory - embedded one will be used
|