| File name: | GameDownload_PUBG_MOBILE_100103_1.0.5727.123.exe |
| Full analysis: | https://app.any.run/tasks/e204bb52-4a9e-486e-bb15-74f50fe24789 |
| Verdict: | Malicious activity |
| Analysis date: | October 02, 2020, 09:05:19 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 79DA347F4183C208A22CD5E6EB8ACFA5 |
| SHA1: | 59C996CD875462688D64F797142690DFCA3BC2B1 |
| SHA256: | 42BD8317EBA4D042FE1970BD12D5782A3F4E4D1B514955AD71DD2E01E4674B06 |
| SSDEEP: | 196608:BeKqqlUgN7AktVweDOaG5eWWi/zio/iXo:Ba2ONwWrX/Wo |
MALICIOUS
Loads dropped or rewritten executable
- TenioDL.exe (PID: 952)
- GameDownload_PUBG_MOBILE_100103_1.0.5727.123.exe (PID: 4088)
- QMEmulatorService.exe (PID: 3268)
- AppMarket.exe (PID: 2284)
- TBSWebRenderer.exe (PID: 3180)
- GameDownload.exe (PID: 1208)
Application was dropped or rewritten from another process
- TenioDL.exe (PID: 952)
- QMEmulatorService.exe (PID: 3268)
- Tinst.exe (PID: 2140)
- AppMarket.exe (PID: 2284)
- syzs_dl_svr.exe (PID: 896)
- TBSWebRenderer.exe (PID: 3180)
- GameDownload.exe (PID: 1208)
- vcredist.exe (PID: 1924)
Adds new firewall rule via NETSH.EXE
- Tinst.exe (PID: 2140)
- Tinst.exe (PID: 560)
Actions looks like stealing of personal data
- AppMarket.exe (PID: 2284)
Changes settings of System certificates
- AppMarket.exe (PID: 2284)
- msiexec.exe (PID: 3596)
Changes the autorun value in the registry
- vcredist.exe (PID: 1924)
SUSPICIOUS
Creates files in the user directory
- TenioDL.exe (PID: 952)
- GameDownload_PUBG_MOBILE_100103_1.0.5727.123.exe (PID: 4088)
- Tinst.exe (PID: 2140)
- AppMarket.exe (PID: 2284)
- GameDownload.exe (PID: 1208)
Creates files in the program directory
- QMEmulatorService.exe (PID: 3268)
- GameDownload_PUBG_MOBILE_100103_1.0.5727.123.exe (PID: 4088)
- AppMarket.exe (PID: 2284)
- syzs_dl_svr.exe (PID: 896)
- Tinst.exe (PID: 2140)
- AOW_Rootfs.exe (PID: 4032)
- Tinst.exe (PID: 560)
Uses NETSH.EXE for network configuration
- Tinst.exe (PID: 2140)
- GameDownload_PUBG_MOBILE_100103_1.0.5727.123.exe (PID: 4088)
- Tinst.exe (PID: 560)
Executable content was dropped or overwritten
- GameDownload_PUBG_MOBILE_100103_1.0.5727.123.exe (PID: 4088)
- Tinst.exe (PID: 2140)
- Market.exe (PID: 2168)
- GameDownload.exe (PID: 1208)
- vcredist.exe (PID: 1924)
- msiexec.exe (PID: 3596)
- UI.exe (PID: 3556)
- Tinst.exe (PID: 560)
Low-level read access rights to disk partition
- GameDownload_PUBG_MOBILE_100103_1.0.5727.123.exe (PID: 4088)
- QMEmulatorService.exe (PID: 3268)
- AppMarket.exe (PID: 2284)
- GameDownload.exe (PID: 1208)
Uses ICACLS.EXE to modify access control list
- TenioDL.exe (PID: 952)
Reads Internet Cache Settings
- GameDownload_PUBG_MOBILE_100103_1.0.5727.123.exe (PID: 4088)
- AppMarket.exe (PID: 2284)
Executed as Windows Service
- QMEmulatorService.exe (PID: 3268)
Modifies the open verb of a shell class
- Tinst.exe (PID: 2140)
Creates a software uninstall entry
- Tinst.exe (PID: 2140)
Creates files in the Windows directory
- QMEmulatorService.exe (PID: 3268)
- msiexec.exe (PID: 3596)
Adds / modifies Windows certificates
- msiexec.exe (PID: 3596)
- AppMarket.exe (PID: 2284)
Removes files from Windows directory
- msiexec.exe (PID: 3596)
INFO
Reads the hosts file
- GameDownload_PUBG_MOBILE_100103_1.0.5727.123.exe (PID: 4088)
- AppMarket.exe (PID: 2284)
- GameDownload.exe (PID: 1208)
Reads settings of System Certificates
- GameDownload_PUBG_MOBILE_100103_1.0.5727.123.exe (PID: 4088)
- AppMarket.exe (PID: 2284)
Application launched itself
- msiexec.exe (PID: 3596)
Loads dropped or rewritten executable
- msiexec.exe (PID: 3596)
Creates a software uninstall entry
- msiexec.exe (PID: 3596)
Creates files in the program directory
- msiexec.exe (PID: 3596)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (18.9) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (13.7) |
| .exe | | | Win64 Executable (generic) (12.1) |
| .exe | | | Win32 Executable (generic) (1.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:06:27 14:15:55+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 950272 |
| InitializedDataSize: | 8122368 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xc43a2 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.5727.123 |
| ProductVersionNumber: | 1.0.5727.123 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
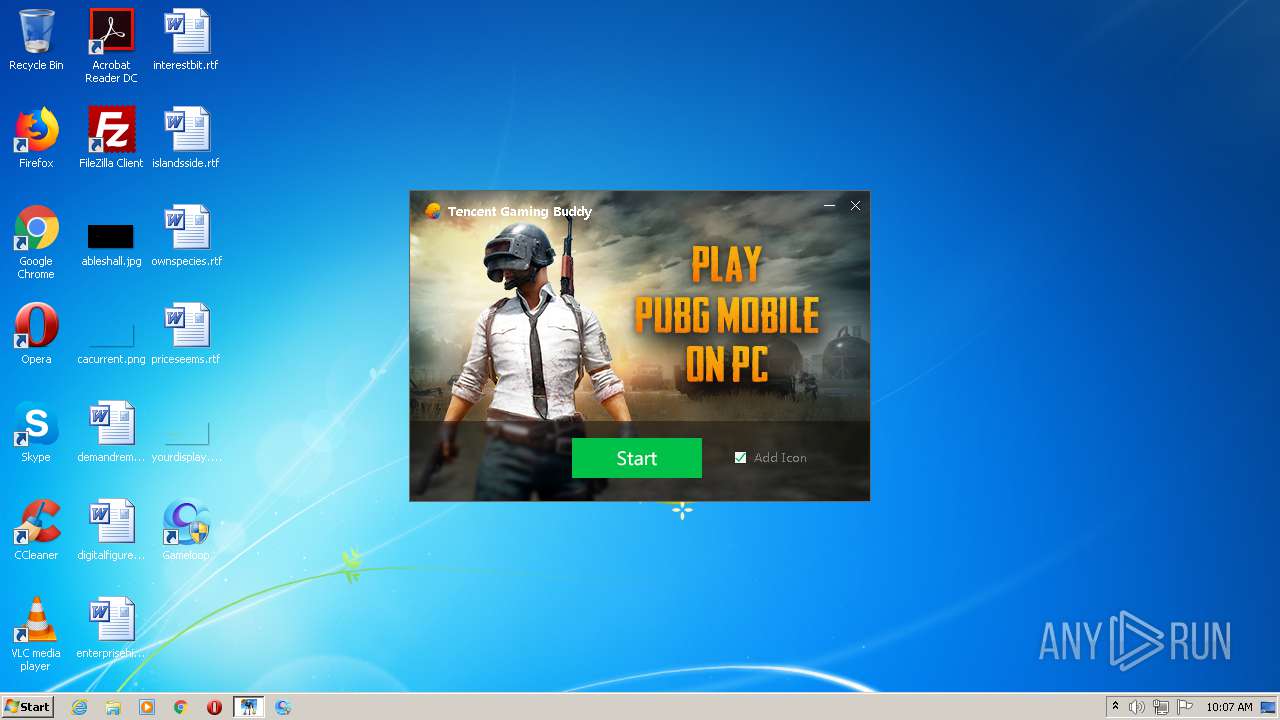
| CompanyName: | Tencent |
| FileDescription: | Tencent Gaming Buddy - Install |
| FileVersion: | 1.0.5727.123 |
| InternalName: | GameDownload |
| LegalCopyright: | Copyright © 2017 Tencent. All Rights Reserved. |
| OriginalFileName: | GameDownload.exe |
| ProductName: | Tencent Gaming Buddy |
| ProductVersion: | 1,0,5727,123 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 27-Jun-2018 12:15:55 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Tencent |
| FileDescription: | Tencent Gaming Buddy - Install |
| FileVersion: | 1.0.5727.123 |
| InternalName: | GameDownload |
| LegalCopyright: | Copyright © 2017 Tencent. All Rights Reserved. |
| OriginalFilename: | GameDownload.exe |
| ProductName: | Tencent Gaming Buddy |
| ProductVersion: | 1,0,5727,123 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 27-Jun-2018 12:15:55 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000E7B87 | 0x000E8000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.56657 |
.rdata | 0x000E9000 | 0x00032F75 | 0x00033000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.07736 |
.data | 0x0011C000 | 0x00007448 | 0x00005000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.67227 |
.rsrc | 0x00124000 | 0x00786738 | 0x00787000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.42523 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.77304 | 333 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 2.89005 | 744 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
3 | 2.54353 | 296 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
4 | 4.35478 | 3752 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
5 | 5.17501 | 2216 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
6 | 3.47748 | 1384 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
7 | 3.0167 | 150 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
8 | 2.12138 | 68 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
9 | 4.05874 | 1128 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
107 | 1.98048 | 20 | Latin 1 / Western European | Chinese - PRC | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
IMM32.dll |
KERNEL32.dll |
OLEAUT32.dll |
PSAPI.DLL |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
curl_easy_cleanup | 1 | 0x00092780 |
curl_easy_duphandle | 2 | 0x00092800 |
curl_easy_escape | 3 | 0x000B8CE0 |
curl_easy_getinfo | 4 | 0x000927E0 |
curl_easy_init | 5 | 0x00092630 |
curl_easy_pause | 6 | 0x00092A70 |
curl_easy_perform | 7 | 0x000926A0 |
curl_easy_recv | 8 | 0x00092BE0 |
curl_easy_reset | 9 | 0x000929D0 |
curl_easy_send | 10 | 0x00092C40 |
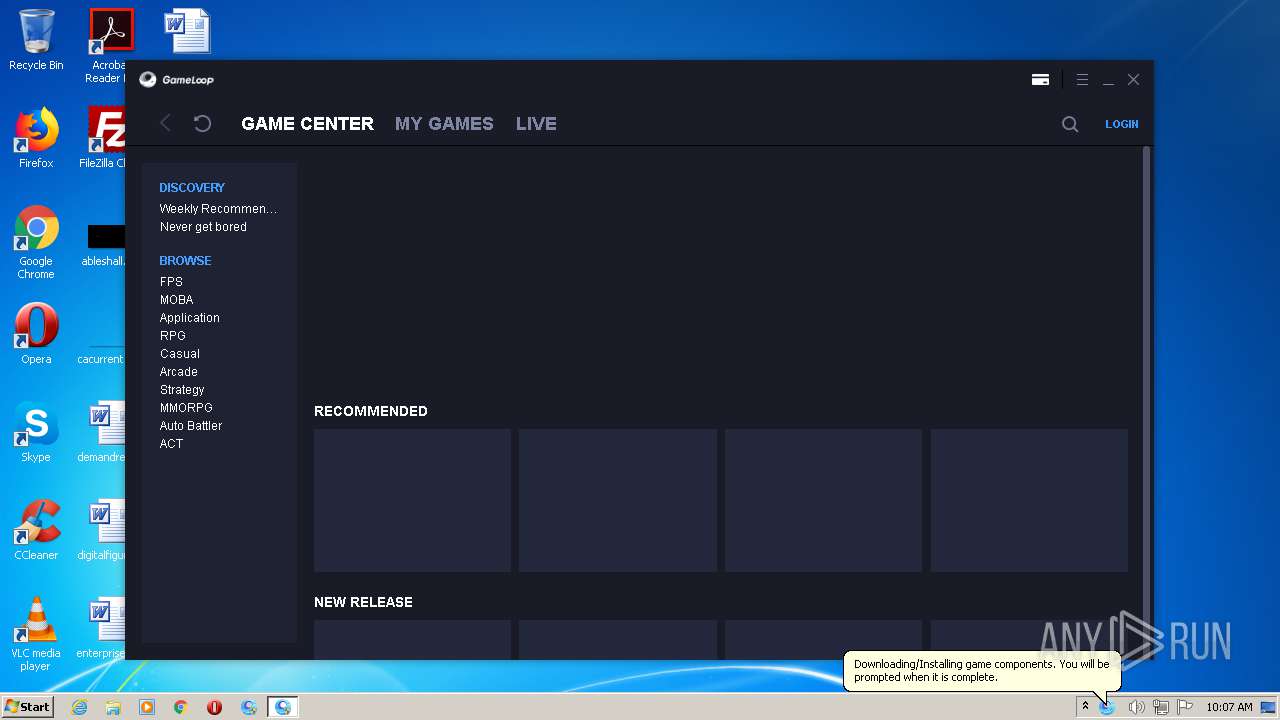
Total processes
86
Monitored processes
31
Malicious processes
9
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 256 | "C:\Windows\system32\Netsh.exe" advfirewall firewall add rule name="TInst" dir=in program="c:\program files\txgameassistant\ui\TInst.exe" action=allow | C:\Windows\system32\Netsh.exe | — | Tinst.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 560 | "C:\Temp\TxGameDownload\Component\UI\Setup\Tinst.exe" | C:\Temp\TxGameDownload\Component\UI\Setup\Tinst.exe | GameDownload.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: TUiInst Exit code: 0 Version: 3.21.1282.100 Modules
| |||||||||||||||
| 612 | "C:\Windows\system32\Netsh.exe" advfirewall firewall add rule name="TxGaDcc" dir=in program="c:\program files\txgameassistant\ui\TxGaDcc.exe" action=allow | C:\Windows\system32\Netsh.exe | — | Tinst.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 896 | "C:\Program Files\TxGameAssistant\AppMarket\DL\syzs_dl_svr.exe" --conf-path="C:\Program Files\TxGameAssistant\AppMarket\DL\syzs_dl_svr.cfg" --daemon --log="C:\Program Files\TxGameAssistant\AppMarket\DL\syzs_dl_svr.log" | C:\Program Files\TxGameAssistant\AppMarket\DL\syzs_dl_svr.exe | AppMarket.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 952 | C:\Users\admin\AppData\Roaming\Tencent\TxGameAssistant\GameDownload\TenioDL.exe | C:\Users\admin\AppData\Roaming\Tencent\TxGameAssistant\GameDownload\TenioDL.exe | GameDownload_PUBG_MOBILE_100103_1.0.5727.123.exe | ||||||||||||
User: admin Company: Tencent Integrity Level: HIGH Description: 腾讯游戏云加速下载引擎(旋风Inside) Exit code: 0 Version: 2, 0, 15, 26 Modules
| |||||||||||||||
| 1008 | "C:\Windows\system32\Netsh.exe" advfirewall firewall add rule name="bugreport" dir=in program="c:\program files\txgameassistant\ui\bugreport.exe" action=allow | C:\Windows\system32\Netsh.exe | — | Tinst.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1208 | "C:\Program Files\TxGameAssistant\AppMarket\GameDownload.exe" -component -noupdate -from appmark -notiywnd 1311138 -pkg com.tencent.ig -vdiver aow_44 -downspeedlimit 0 -no_install_vdi -no_install_vdi44 -no_install_vbox -install_aow_rootfs -aeparam -engine aow -aeparamend | C:\Program Files\TxGameAssistant\AppMarket\GameDownload.exe | AppMarket.exe | ||||||||||||
User: admin Company: Tencent Integrity Level: HIGH Description: Gameloop - Install Exit code: 0 Version: 3.11.726.100 Modules
| |||||||||||||||
| 1924 | "C:\Temp\TxGameDownload\Component\vcredist.exe" /q:a /c:"msiexec /i vcredist.msi /qn" | C:\Temp\TxGameDownload\Component\vcredist.exe | GameDownload.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: IExpress Setup Exit code: 0 Version: 2.0.50727.4053 Modules
| |||||||||||||||
| 2052 | msiexec /i vcredist.msi /qn | C:\Windows\system32\msiexec.exe | — | vcredist.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2068 | "C:\Windows\system32\Netsh.exe" advfirewall firewall add rule name="TUpdate" dir=in program="c:\program files\txgameassistant\appmarket\GF186\TUpdate.exe" action=allow | C:\Windows\system32\Netsh.exe | — | Tinst.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 591
Read events
913
Write events
1 660
Delete events
18
Modification events
| (PID) Process: | (4088) GameDownload_PUBG_MOBILE_100103_1.0.5727.123.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Tencent\MobileGamePC |
| Operation: | write | Name: | SupplyId |
Value: 100103 | |||
| (PID) Process: | (4088) GameDownload_PUBG_MOBILE_100103_1.0.5727.123.exe | Key: | HKEY_CURRENT_USER\Software\Tencent\MobileGamePC |
| Operation: | write | Name: | sf |
Value: C:\Temp\TxGameDownload\MobileGamePCShared | |||
| (PID) Process: | (952) TenioDL.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (952) TenioDL.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (952) TenioDL.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\metnsd\clsid |
| Operation: | write | Name: | SequenceID |
Value: A3EFA1A36B077049B818F3A14104781A | |||
| (PID) Process: | (4088) GameDownload_PUBG_MOBILE_100103_1.0.5727.123.exe | Key: | HKEY_CURRENT_USER\Software\Tencent\MobileGamePC |
| Operation: | write | Name: | UserLanguage |
Value: en | |||
| (PID) Process: | (4088) GameDownload_PUBG_MOBILE_100103_1.0.5727.123.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (4088) GameDownload_PUBG_MOBILE_100103_1.0.5727.123.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (4088) GameDownload_PUBG_MOBILE_100103_1.0.5727.123.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (4088) GameDownload_PUBG_MOBILE_100103_1.0.5727.123.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
350
Suspicious files
335
Text files
2 623
Unknown types
28
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4088 | GameDownload_PUBG_MOBILE_100103_1.0.5727.123.exe | C:\test.tmp | — | |
MD5:— | SHA256:— | |||
| 952 | TenioDL.exe | C:\Users\admin\AppData\Local\Temp\etilqs_6tEc0lkeGW8Ys8T | — | |
MD5:— | SHA256:— | |||
| 952 | TenioDL.exe | C:\Users\admin\AppData\Local\Temp\etilqs_2N08rOu2pUbjCeD | — | |
MD5:— | SHA256:— | |||
| 4088 | GameDownload_PUBG_MOBILE_100103_1.0.5727.123.exe | C:\Users\admin\AppData\Local\Temp\CabDECA.tmp | — | |
MD5:— | SHA256:— | |||
| 4088 | GameDownload_PUBG_MOBILE_100103_1.0.5727.123.exe | C:\Users\admin\AppData\Local\Temp\TarDECB.tmp | — | |
MD5:— | SHA256:— | |||
| 952 | TenioDL.exe | C:\Temp\TxGameDownload\Component\AppMarket\Market.exe.ttd | — | |
MD5:— | SHA256:— | |||
| 952 | TenioDL.exe | C:\Users\admin\AppData\Roaming\Tencent\TenioDL\1502\cache\download.db-journal | — | |
MD5:— | SHA256:— | |||
| 952 | TenioDL.exe | C:\Temp\TxGameDownload\Component\AppMarket\Market.exe | — | |
MD5:— | SHA256:— | |||
| 4088 | GameDownload_PUBG_MOBILE_100103_1.0.5727.123.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\A053CFB63FC8E6507871752236B5CCD5_BAF66407D863B465065B7E5475ADA340 | der | |
MD5:— | SHA256:— | |||
| 952 | TenioDL.exe | C:\Users\admin\AppData\Roaming\Tencent\TenioDL\1502\cache\download.db | sqlite | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
52
TCP/UDP connections
288
DNS requests
52
Threats
62
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
952 | TenioDL.exe | GET | — | 2.16.186.75:80 | http://dldir1.qq.com/syzs/oversea_component/Market_3.11.726.100.dat | unknown | — | — | whitelisted |
952 | TenioDL.exe | GET | — | 2.16.186.75:80 | http://dldir1.qq.com/syzs/oversea_component/Market_3.11.726.100.dat | unknown | — | — | whitelisted |
952 | TenioDL.exe | GET | — | 2.16.186.75:80 | http://dldir1.qq.com/syzs/oversea_component/Market_3.11.726.100.dat | unknown | — | — | whitelisted |
4088 | GameDownload_PUBG_MOBILE_100103_1.0.5727.123.exe | GET | 200 | 104.18.20.226:80 | http://ocsp2.globalsign.com/gsorganizationvalsha2g2/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBQMnk2cPe3vhNiR6XLHz4QGvBl7BwQUlt5h8b0cFilTHMDMfTuDAEDmGnwCDHGQKtP62BOm98s81w%3D%3D | US | der | 1.54 Kb | whitelisted |
952 | TenioDL.exe | GET | 206 | 2.16.186.75:80 | http://dldir1.qq.com/syzs/oversea_component/Market_3.11.726.100.dat | unknown | binary | 9.50 Mb | whitelisted |
4088 | GameDownload_PUBG_MOBILE_100103_1.0.5727.123.exe | GET | 200 | 203.205.253.183:80 | http://syzs.qq.com/downloads/xml/compoment.xml | CN | xml | 3.48 Kb | suspicious |
952 | TenioDL.exe | GET | 206 | 2.16.186.75:80 | http://dldir1.qq.com/syzs/oversea_component/Market_3.11.726.100.dat | unknown | binary | 9.50 Mb | whitelisted |
1056 | svchost.exe | GET | 200 | 2.16.186.74:80 | http://crl.microsoft.com/pki/crl/products/microsoftrootcert.crl | unknown | der | 781 b | whitelisted |
1056 | svchost.exe | GET | 200 | 216.58.208.163:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjqTAc%2FHIGOD%2BaUx0%3D | US | der | 492 b | whitelisted |
1056 | svchost.exe | GET | 200 | 2.21.38.54:80 | http://www.microsoft.com/pkiops/crl/MicCodSigPCA2011_2011-07-08.crl | FR | der | 813 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4088 | GameDownload_PUBG_MOBILE_100103_1.0.5727.123.exe | 58.251.106.185:443 | master.etl.desktop.qq.com | China Unicom Guangdong IP network | CN | malicious |
952 | TenioDL.exe | 111.161.108.243:8000 | p2pupgrade.gamedl.qq.com | CHINA UNICOM China169 Backbone | CN | unknown |
952 | TenioDL.exe | 60.28.190.146:8000 | ps2.gamedl.qq.com | CHINA UNICOM China169 Backbone | CN | unknown |
— | — | 163.177.93.249:8000 | — | China Unicom Shenzen network | CN | unknown |
4088 | GameDownload_PUBG_MOBILE_100103_1.0.5727.123.exe | 203.205.253.140:443 | syzs.qq.com | — | CN | suspicious |
4088 | GameDownload_PUBG_MOBILE_100103_1.0.5727.123.exe | 203.205.253.183:80 | syzs.qq.com | — | CN | suspicious |
— | — | 185.246.208.197:24340 | — | — | — | unknown |
952 | TenioDL.exe | 101.89.238.160:8443 | ga.gamedl.qq.com | China Telecom (Group) | CN | unknown |
952 | TenioDL.exe | 2.16.186.75:80 | dldir1.qq.com | Akamai International B.V. | — | whitelisted |
4088 | GameDownload_PUBG_MOBILE_100103_1.0.5727.123.exe | 104.18.20.226:80 | ocsp2.globalsign.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
p2pupgrade.gamedl.qq.com |
| unknown |
master.etl.desktop.qq.com |
| whitelisted |
config.gamedl.qq.com |
| whitelisted |
stat.gamedl.qq.com |
| unknown |
stun.qqlive.qq.com |
| suspicious |
ps2.gamedl.qq.com |
| unknown |
p2pupdate.gamedl.qq.com |
| unknown |
syzs.qq.com |
| unknown |
c.gj.qq.com |
| unknown |
ga.gamedl.qq.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
952 | TenioDL.exe | Generic Protocol Command Decode | ET INFO Session Traversal Utilities for NAT (STUN Binding Request obsolete rfc 3489 CHANGE-REQUEST attribute change IP flag false change port flag false) |
4088 | GameDownload_PUBG_MOBILE_100103_1.0.5727.123.exe | Generic Protocol Command Decode | SURICATA TLS error message encountered |
4088 | GameDownload_PUBG_MOBILE_100103_1.0.5727.123.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
4088 | GameDownload_PUBG_MOBILE_100103_1.0.5727.123.exe | Generic Protocol Command Decode | SURICATA TLS error message encountered |
952 | TenioDL.exe | Generic Protocol Command Decode | ET INFO Session Traversal Utilities for NAT (STUN Binding Request obsolete rfc 3489 CHANGE-REQUEST attribute change IP flag true change port flag false) |
952 | TenioDL.exe | Generic Protocol Command Decode | ET INFO Session Traversal Utilities for NAT (STUN Binding Request obsolete rfc 3489 CHANGE-REQUEST attribute change IP flag false change port flag true) |
— | — | Generic Protocol Command Decode | ET INFO Session Traversal Utilities for NAT (STUN Binding Request obsolete rfc 3489 CHANGE-REQUEST attribute change IP flag false change port flag false) |
— | — | Generic Protocol Command Decode | ET INFO Session Traversal Utilities for NAT (STUN Binding Request obsolete rfc 3489 CHANGE-REQUEST attribute change IP flag false change port flag false) |
4088 | GameDownload_PUBG_MOBILE_100103_1.0.5727.123.exe | Generic Protocol Command Decode | SURICATA TLS error message encountered |
4088 | GameDownload_PUBG_MOBILE_100103_1.0.5727.123.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
3 ETPRO signatures available at the full report
Process | Message |
|---|---|
GameDownload_PUBG_MOBILE_100103_1.0.5727.123.exe | [Downloader] DriverType C: = 3
|
GameDownload_PUBG_MOBILE_100103_1.0.5727.123.exe | [Downloader] GetLogicalDrives 4
|
GameDownload_PUBG_MOBILE_100103_1.0.5727.123.exe | [Downloader] DriverType C: = 3
|
GameDownload_PUBG_MOBILE_100103_1.0.5727.123.exe | [Downloader] DriverType C: = 3
|
AppMarket.exe | Standard VGA Graphics Adapter |
AppMarket.exe | [1002/100706:INFO:exception_record.cc(518)] [QB]Process ID: 2284 Type: 1
|
TBSWebRenderer.exe | [1002/100707:INFO:exception_record.cc(518)] [QB]Process ID: 3180 Type: 2
|
GameDownload.exe | [Downloader] DriverType C: = 3
|
GameDownload.exe | [Downloader] GetLogicalDrives 4
|
GameDownload.exe | [Downloader] DriverType C: = 3
|