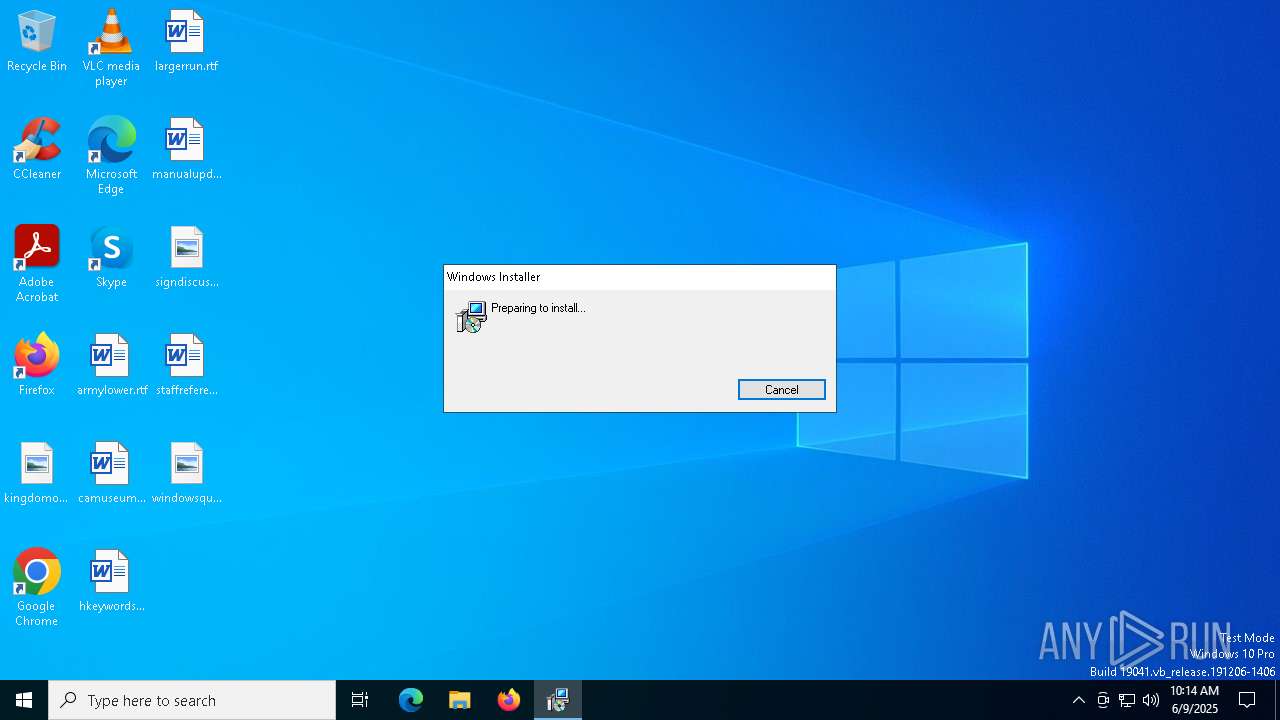
| File name: | Adblock360Installer.exe |
| Full analysis: | https://app.any.run/tasks/a006d383-fc5d-4d18-8f15-84d0f32dec24 |
| Verdict: | Malicious activity |
| Analysis date: | June 09, 2025, 10:14:25 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 14 sections |
| MD5: | 8EE371D19B491429DABC3E70499A8676 |
| SHA1: | F3F75924E96F31A30D42FA8840EA8B095DA48D51 |
| SHA256: | 42BD0DA29E48491CA6FCB90C7371ACDA83FA9EB0DE6D2BC3BCA6493803638662 |
| SSDEEP: | 98304:qnxm0+wnTgJEnrZSSnVJFtcFHfsGGcqORi3uGNDO9kQYgoVMV5nY1sg77mKS86hQ:BYFzmcB |
MALICIOUS
Changes powershell execution policy (Bypass)
- msiexec.exe (PID: 1244)
Bypass execution policy to execute commands
- powershell.exe (PID: 5232)
- powershell.exe (PID: 6880)
- powershell.exe (PID: 8064)
SUSPICIOUS
Reads security settings of Internet Explorer
- Adblock360Installer.exe (PID: 7256)
Application launched itself
- Adblock360Installer.exe (PID: 7256)
The process bypasses the loading of PowerShell profile settings
- msiexec.exe (PID: 1244)
The process executes Powershell scripts
- msiexec.exe (PID: 1244)
Starts POWERSHELL.EXE for commands execution
- msiexec.exe (PID: 1244)
The process hide an interactive prompt from the user
- msiexec.exe (PID: 1244)
Detects AdvancedInstaller (YARA)
- msiexec.exe (PID: 7588)
- msiexec.exe (PID: 7496)
INFO
The sample compiled with english language support
- Adblock360Installer.exe (PID: 7256)
- msiexec.exe (PID: 7588)
- msiexec.exe (PID: 7496)
Checks supported languages
- Adblock360Installer.exe (PID: 7256)
- Adblock360Installer.exe (PID: 7048)
- msiexec.exe (PID: 5776)
- msiexec.exe (PID: 7496)
- msiexec.exe (PID: 1244)
Reads the computer name
- Adblock360Installer.exe (PID: 7256)
- Adblock360Installer.exe (PID: 7048)
- msiexec.exe (PID: 5776)
- msiexec.exe (PID: 7496)
- msiexec.exe (PID: 1244)
Process checks computer location settings
- Adblock360Installer.exe (PID: 7256)
Reads the machine GUID from the registry
- Adblock360Installer.exe (PID: 7048)
Reads the software policy settings
- Adblock360Installer.exe (PID: 7048)
- msiexec.exe (PID: 7588)
- powershell.exe (PID: 5232)
- powershell.exe (PID: 6880)
- powershell.exe (PID: 8064)
Create files in a temporary directory
- Adblock360Installer.exe (PID: 7048)
- msiexec.exe (PID: 7588)
- msiexec.exe (PID: 1244)
- msiexec.exe (PID: 7496)
- powershell.exe (PID: 8064)
- powershell.exe (PID: 6880)
- powershell.exe (PID: 5232)
Drops encrypted JS script (Microsoft Script Encoder)
- Adblock360Installer.exe (PID: 7048)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 7588)
- powershell.exe (PID: 5232)
- powershell.exe (PID: 6880)
- powershell.exe (PID: 8064)
Checks proxy server information
- msiexec.exe (PID: 7588)
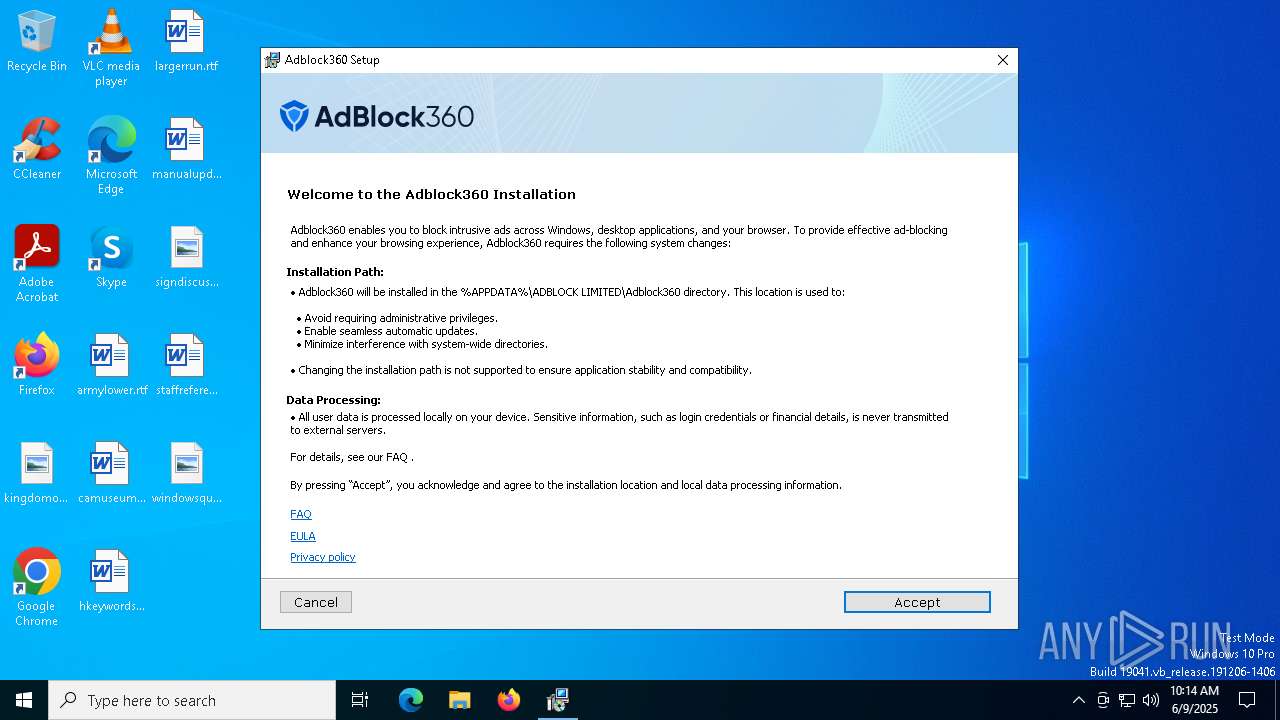
Creates files or folders in the user directory
- msiexec.exe (PID: 7588)
- msiexec.exe (PID: 7496)
Reads Environment values
- msiexec.exe (PID: 7496)
- msiexec.exe (PID: 1244)
Executable content was dropped or overwritten
- msiexec.exe (PID: 7496)
- msiexec.exe (PID: 7588)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 5232)
- powershell.exe (PID: 6880)
- powershell.exe (PID: 8064)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 6880)
Detects GO elliptic curve encryption (YARA)
- Adblock360Installer.exe (PID: 7048)
Application based on Golang
- Adblock360Installer.exe (PID: 7048)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 6880)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (36.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (26.6) |
| .exe | | | Win64 Executable (generic) (23.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 0000:00:00 00:00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 3 |
| CodeSize: | 3017728 |
| InitializedDataSize: | 251392 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x72f40 |
| OSVersion: | 6.1 |
| ImageVersion: | 1 |
| SubsystemVersion: | 6.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | - |
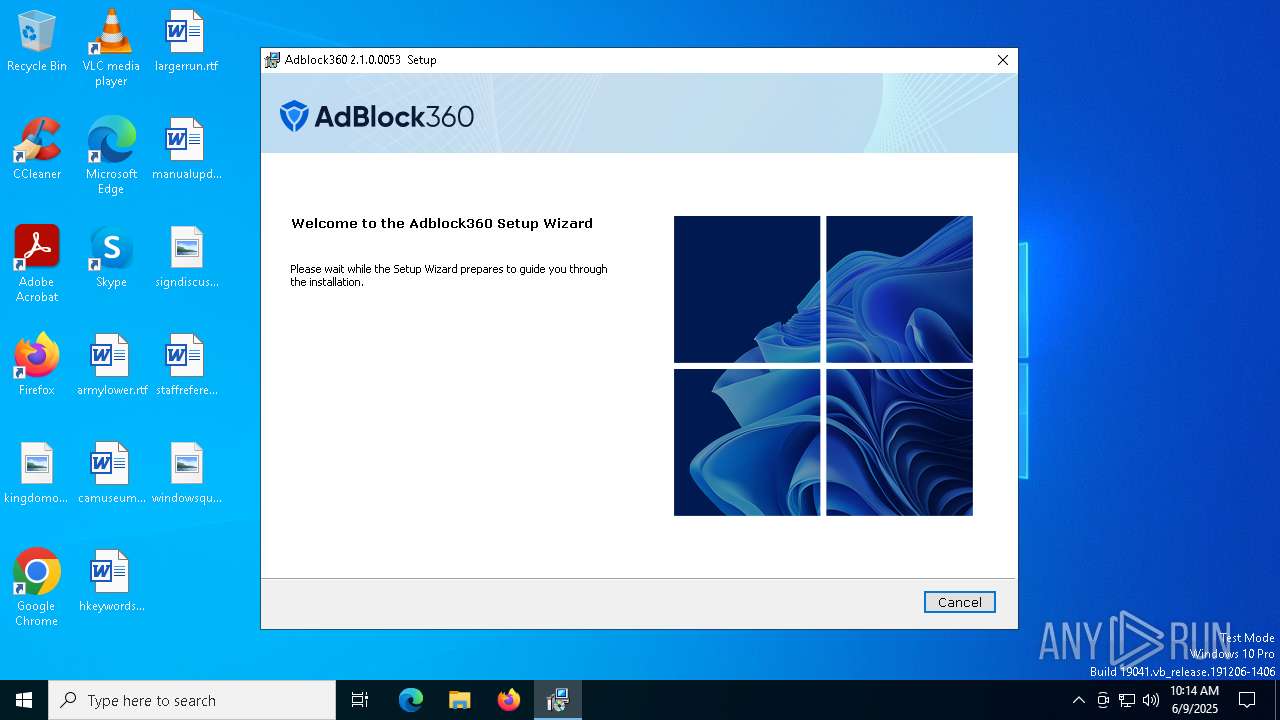
| CompanyName: | ADBLOCK LIMITED |
| FileDescription: | Adblock360 Downloader and Installer |
| FileVersion: | 1.0.0.0 |
| InternalName: | - |
| LegalCopyright: | Copyright (c) 2025 ADBLOCK LIMITED |
| LegalTrademarks: | - |
| OriginalFileName: | Adblock360Installer.exe |
| PrivateBuild: | - |
| ProductName: | Adblock360Installer |
| ProductVersion: | 1.0.0.0 |
| SpecialBuild: | - |
Total processes
135
Monitored processes
13
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1244 | C:\Windows\syswow64\MsiExec.exe -Embedding CEB0DC85CBA748E3A61AA58C1267CE5F C | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4040 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5232 | -NoProfile -Noninteractive -ExecutionPolicy Bypass -File "C:\Users\admin\AppData\Local\Temp\pssDA7.ps1" -propFile "C:\Users\admin\AppData\Local\Temp\msiDA4.txt" -scriptFile "C:\Users\admin\AppData\Local\Temp\scrDA5.ps1" -scriptArgsFile "C:\Users\admin\AppData\Local\Temp\scrDA6.txt" -propSep " :<->: " -lineSep " <<:>> " -testPrefix "_testValue." | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5328 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5776 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6488 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6880 | -NoProfile -Noninteractive -ExecutionPolicy Bypass -File "C:\Users\admin\AppData\Local\Temp\pss1984.ps1" -propFile "C:\Users\admin\AppData\Local\Temp\msi1972.txt" -scriptFile "C:\Users\admin\AppData\Local\Temp\scr1973.ps1" -scriptArgsFile "C:\Users\admin\AppData\Local\Temp\scr1974.txt" -propSep " :<->: " -lineSep " <<:>> " -testPrefix "_testValue." | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7048 | "C:\Users\admin\AppData\Local\Temp\Adblock360Installer.exe" | C:\Users\admin\AppData\Local\Temp\Adblock360Installer.exe | Adblock360Installer.exe | ||||||||||||
User: admin Company: ADBLOCK LIMITED Integrity Level: HIGH Description: Adblock360 Downloader and Installer Version: 1.0.0.0 Modules
| |||||||||||||||
| 7256 | "C:\Users\admin\AppData\Local\Temp\Adblock360Installer.exe" | C:\Users\admin\AppData\Local\Temp\Adblock360Installer.exe | — | explorer.exe | |||||||||||
User: admin Company: ADBLOCK LIMITED Integrity Level: MEDIUM Description: Adblock360 Downloader and Installer Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 7364 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
25 654
Read events
25 650
Write events
4
Delete events
0
Modification events
| (PID) Process: | (7588) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\Interface\{618736E0-3C3D-11CF-810C-00AA00389B71}\TypeLib |
| Operation: | write | Name: | Version |
Value: 1.1 | |||
| (PID) Process: | (7588) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{618736E0-3C3D-11CF-810C-00AA00389B71}\TypeLib |
| Operation: | write | Name: | Version |
Value: 1.1 | |||
| (PID) Process: | (7588) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Volatile\00\MACHINE\SOFTWARE\Classes\WOW6432Node\Interface\{03022430-ABC4-11D0-BDE2-00AA001A1953}\TypeLib |
| Operation: | write | Name: | Version |
Value: 1.1 | |||
| (PID) Process: | (7588) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Volatile\00\MACHINE\SOFTWARE\Classes\Interface\{03022430-ABC4-11D0-BDE2-00AA001A1953}\TypeLib |
| Operation: | write | Name: | Version |
Value: 1.1 | |||
Executable files
13
Suspicious files
5
Text files
20
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7048 | Adblock360Installer.exe | C:\Users\admin\AppData\Local\Temp\Adblock360-Setup_2.1.0.0053.msi | — | |
MD5:— | SHA256:— | |||
| 1244 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\msiDA4.txt | — | |
MD5:— | SHA256:— | |||
| 1244 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\scrDA5.ps1 | — | |
MD5:— | SHA256:— | |||
| 1244 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\scrDA6.txt | — | |
MD5:— | SHA256:— | |||
| 1244 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\pssDA7.ps1 | — | |
MD5:— | SHA256:— | |||
| 7588 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\C8E534EE129F27D55460CE17FD628216_1130D9B25898B0DB0D4F04DC5B93F141 | der | |
MD5:1808B182E6D53FFF0C388A681C71E27E | SHA256:940552CFAC42D98AD272F6872DF1708BF9C713D9C4340E3279BD7D902B4C390F | |||
| 7588 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI11084\embeddeduiproxy.dll | executable | |
MD5:9DC11997374CA79880F5694E8F459EFC | SHA256:7C4EF3DC1235B3CC7C7C9E7B9042682AD9C397D8F4CBBC2E2DD60CFF58E38B3E | |||
| 7496 | msiexec.exe | C:\Users\admin\AppData\Local\AdvinstAnalytics\668fe6355a890781773f449f\2.1.0.0053\tracking.ini | text | |
MD5:595A29F1F4E79D694D1FF3706E75C3EF | SHA256:D876186DC4FC51EE4F07C70B7EB2BD23D32C25A9DB1F5B550321B1654D414E58 | |||
| 7588 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\8EC9B1D0ABBD7F98B401D425828828CE_16C89CE78CC9E46E9E5FC013C79851B1 | binary | |
MD5:6E732DEFEC2D541691D1BB7194735B69 | SHA256:ABD2DF9C220D415F05EE24033872F9110BA92A68B38EE7BFD0BBAFA7D859B5EA | |||
| 7496 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI11084\InstallerAnalytics.dll | executable | |
MD5:5293D61DDB99767CAD4BC4E952517163 | SHA256:B784371C1278E079AE201226079BECE93456F9D38DD733FC29F51E79CF4EA705 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
19
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6208 | svchost.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7588 | msiexec.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
7588 | msiexec.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
7588 | msiexec.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEAEldo4y1XhTxXnw4hY%2Bw5A%3D | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6960 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6960 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
6208 | svchost.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
3760 | RUXIMICS.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7048 | Adblock360Installer.exe | 65.9.66.120:443 | api.adblock360.com | AMAZON-02 | US | unknown |
7588 | msiexec.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
6544 | svchost.exe | 20.190.160.4:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
api.adblock360.com |
| unknown |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |