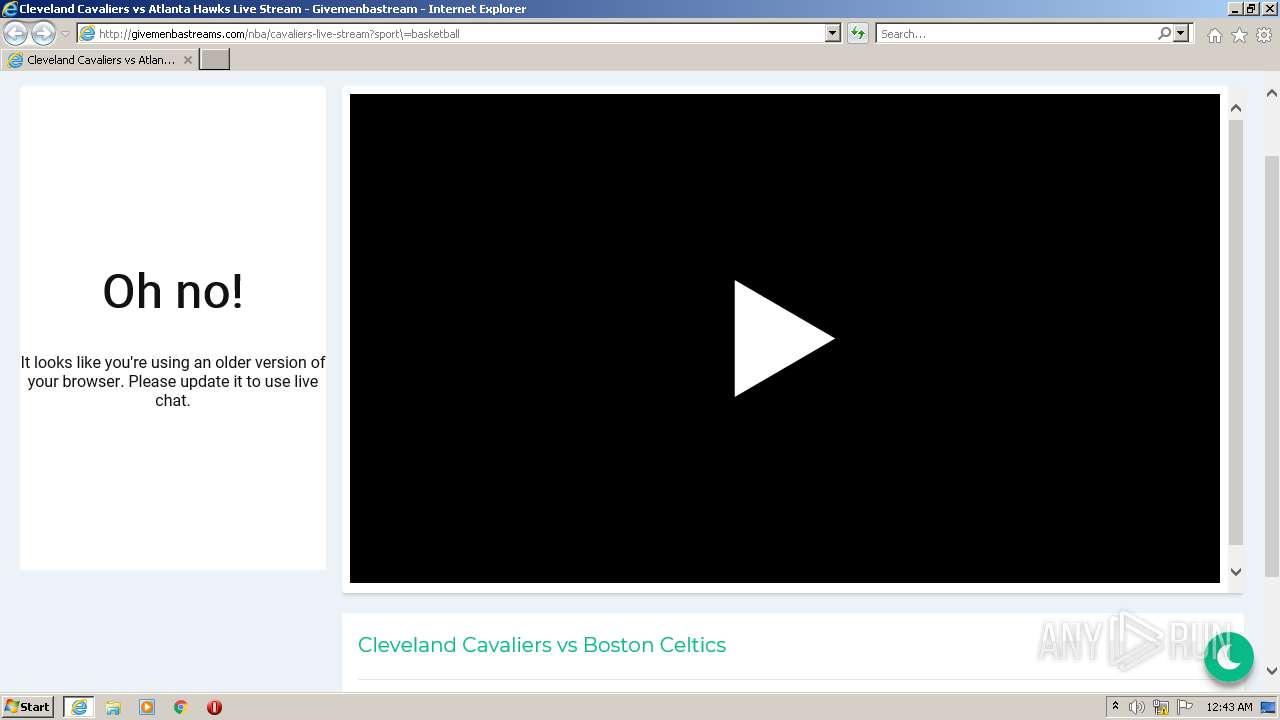
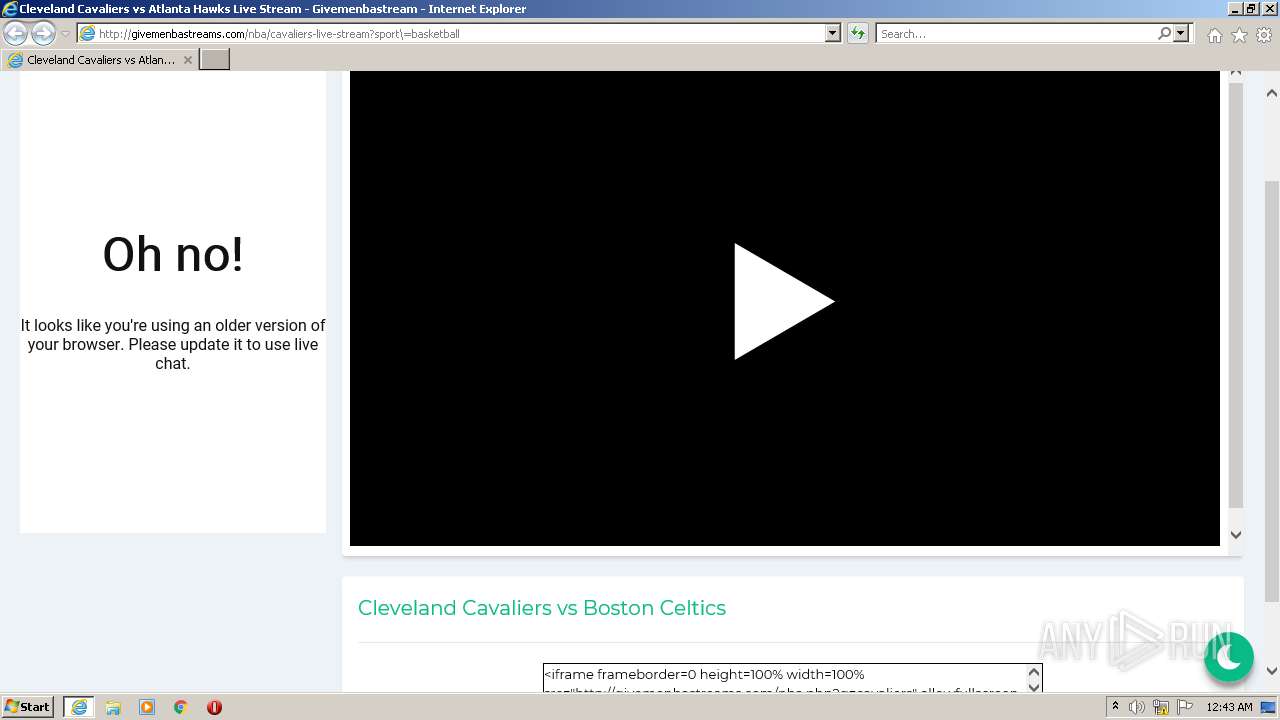
| URL: | http://givemenbastreams.com/nba/cavaliers-live-stream?sport\=basketball |
| Full analysis: | https://app.any.run/tasks/da46bb09-8a21-41b5-be86-0c3c07657798 |
| Verdict: | Malicious activity |
| Analysis date: | November 16, 2021, 00:43:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | DAB79A3F1895B5F387037B0CEEF7E1DE |
| SHA1: | 4AD8019890D6BC1E693E69C99847B23064B8F03B |
| SHA256: | 429748CAB3AB3B7758FE9E28141099688372B6D62C632C00CFA523820A3C0AE2 |
| SSDEEP: | 3:N1KZMTA9zuEfRLDTTJHTAFQhaB4kH:CyM9zLNTF8QhaBfH |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3696)
Checks supported languages
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 3136)
Reads the computer name
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 3136)
Executed via COM
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 3136)
Creates files in the user directory
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 3136)
INFO
Checks supported languages
- iexplore.exe (PID: 3796)
- iexplore.exe (PID: 3696)
Reads the computer name
- iexplore.exe (PID: 3796)
- iexplore.exe (PID: 3696)
Changes internet zones settings
- iexplore.exe (PID: 3796)
Reads settings of System Certificates
- iexplore.exe (PID: 3696)
- iexplore.exe (PID: 3796)
Application launched itself
- iexplore.exe (PID: 3796)
Reads CPU info
- iexplore.exe (PID: 3696)
Reads internet explorer settings
- iexplore.exe (PID: 3696)
Checks Windows Trust Settings
- iexplore.exe (PID: 3796)
- iexplore.exe (PID: 3696)
Creates files in the user directory
- iexplore.exe (PID: 3696)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
37
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3136 | C:\Windows\system32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Integrity Level: MEDIUM Description: Adobe� Flash� Player Installer/Uninstaller 32.0 r0 Exit code: 0 Version: 32,0,0,453 Modules
| |||||||||||||||
| 3696 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3796 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3796 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://givemenbastreams.com/nba/cavaliers-live-stream?sport\=basketball" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
30 202
Read events
30 028
Write events
174
Delete events
0
Modification events
| (PID) Process: | (3796) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3796) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3796) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30923394 | |||
| (PID) Process: | (3796) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 186545080 | |||
| (PID) Process: | (3796) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30923395 | |||
| (PID) Process: | (3796) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3796) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3796) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3796) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3796) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
23
Text files
83
Unknown types
61
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3696 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\cavaliers-live-stream[1].htm | html | |
MD5:3AB31EB420DD8EEB0B738DFC96636A37 | SHA256:3D7C4281FD7ADC4E6EE8B5E86E1D5E062A7788723C751773480923C44770649D | |||
| 3696 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\su[1].js | html | |
MD5:765A50E18DB5BDC3BADF43040834C22A | SHA256:C0A97A9799BBA7CBACA2FF35B43DAAEF3AC0C679BA39A90DF166C39AAD65BEA3 | |||
| 3696 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:E0FB0697901825BB2BB55C4E0F1C00E2 | SHA256:9F7D522AB380641B1DA05A3DE1E6393BC34AFDAB8502CA0ECC26E1EF1C13647B | |||
| 3696 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | der | |
MD5:1EA20C60FAE95B68D65CB7E481AB94D9 | SHA256:C132D92D701836917F33E6288842BC1519F8FA4EC7D81062E28CE2EC8E08E926 | |||
| 3696 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CAF4703619713E3F18D8A9D5D88D6288_A7725538C46DE2D0088EE44974E2CEBA | der | |
MD5:64E9B8BB98E2303717538CE259BEC57D | SHA256:76BD459EC8E467EFC3E3FB94CB21B9C77A2AA73C9D4C0F3FAF823677BE756331 | |||
| 3696 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\app[1].css | text | |
MD5:E6773685C39BB6160100E16549464843 | SHA256:62C031004C064A2F52F36A3B7854C485707819FDE26D9AC8827347F38972F64C | |||
| 3696 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\css[1].css | text | |
MD5:9DAD6B561EBD3A706B3BC16120C74F83 | SHA256:834BBF693F44BF7BB58521E82B9FA3241CBF7A523C66A4266603EDD65D442945 | |||
| 3696 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:6739717955E10A5A00E5099DBE53995D | SHA256:A804C27EB0B48DB2982F63653DA5CBE7CE885B863D2D5DF57EC7E5E5F9D6786C | |||
| 3696 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | der | |
MD5:4B05C5BD6DB27E9B7EA23704F5011DC2 | SHA256:B8B6AE9E2BF1232FF2A9C8ABB61D1721B2C726FA6B5868B5F83F7EE1E107E3CE | |||
| 3696 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:3C347530759AD41E5B01881E82298FF8 | SHA256:BA05F2E7D289932B1E82EDACF17BB6CA2AB7DDEE4D77E7E65CB64EF80CC77574 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
40
TCP/UDP connections
82
DNS requests
37
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3696 | iexplore.exe | GET | 200 | 104.21.235.146:80 | http://givemenbastreams.com/public/js/app.js | US | compressed | 468 b | malicious |
3696 | iexplore.exe | GET | 200 | 104.21.235.146:80 | http://givemenbastreams.com/nba/cavaliers-live-stream?sport\=basketball | US | html | 7.08 Kb | malicious |
3696 | iexplore.exe | GET | 200 | 104.21.235.146:80 | http://givemenbastreams.com/public/css/app.css | US | compressed | 2.90 Kb | malicious |
3696 | iexplore.exe | GET | 200 | 104.17.172.62:80 | http://velocecdn.com/script/su.js | US | html | 7.14 Kb | shared |
3696 | iexplore.exe | GET | 200 | 67.27.234.126:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?66cd8714c22849a9 | US | compressed | 4.70 Kb | whitelisted |
3696 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
3696 | iexplore.exe | GET | 200 | 216.58.212.131:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
3696 | iexplore.exe | GET | 200 | 216.58.212.131:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEAiWJA%2FUYGrvCgAAAAEQNk8%3D | US | der | 471 b | whitelisted |
3696 | iexplore.exe | GET | 200 | 67.27.234.126:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?46ac1d775c9f5039 | US | compressed | 59.9 Kb | whitelisted |
3696 | iexplore.exe | GET | 200 | 104.117.200.9:80 | http://x1.c.lencr.org/ | US | der | 717 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3696 | iexplore.exe | 158.69.248.123:443 | s4.histats.com | OVH SAS | CA | suspicious |
3696 | iexplore.exe | 172.217.16.138:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
3696 | iexplore.exe | 104.117.200.9:80 | x1.c.lencr.org | TPG Telecom Limited | US | unknown |
3696 | iexplore.exe | 104.21.235.146:80 | givemenbastreams.com | Cloudflare Inc | US | unknown |
3696 | iexplore.exe | 142.250.186.42:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3696 | iexplore.exe | 104.18.10.207:443 | maxcdn.bootstrapcdn.com | Cloudflare Inc | US | suspicious |
3696 | iexplore.exe | 104.17.172.62:80 | velocecdn.com | Cloudflare Inc | US | shared |
3696 | iexplore.exe | 67.27.234.126:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
3796 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3696 | iexplore.exe | 2.18.233.74:443 | geo2.adobe.com | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
givemenbastreams.com |
| malicious |
fonts.googleapis.com |
| whitelisted |
maxcdn.bootstrapcdn.com |
| whitelisted |
velocecdn.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
s10.histats.com |
| whitelisted |
www.displayvertising.com |
| suspicious |
fonts.gstatic.com |
| whitelisted |