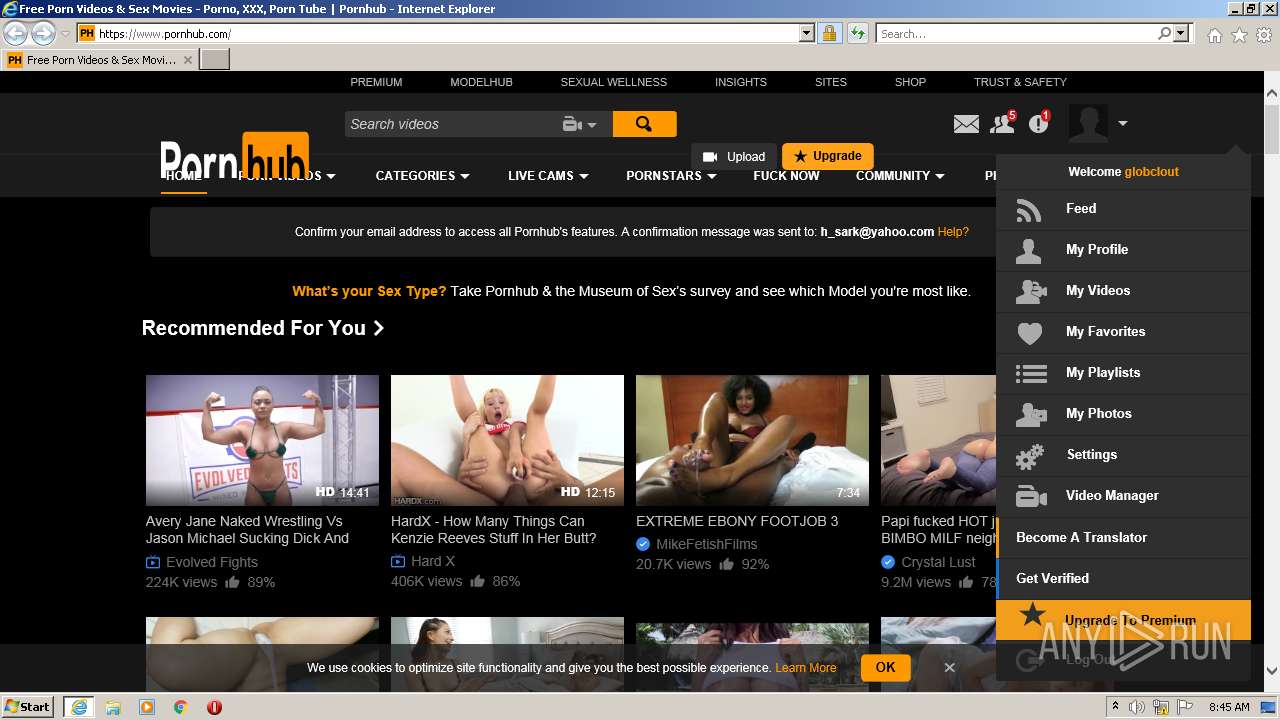
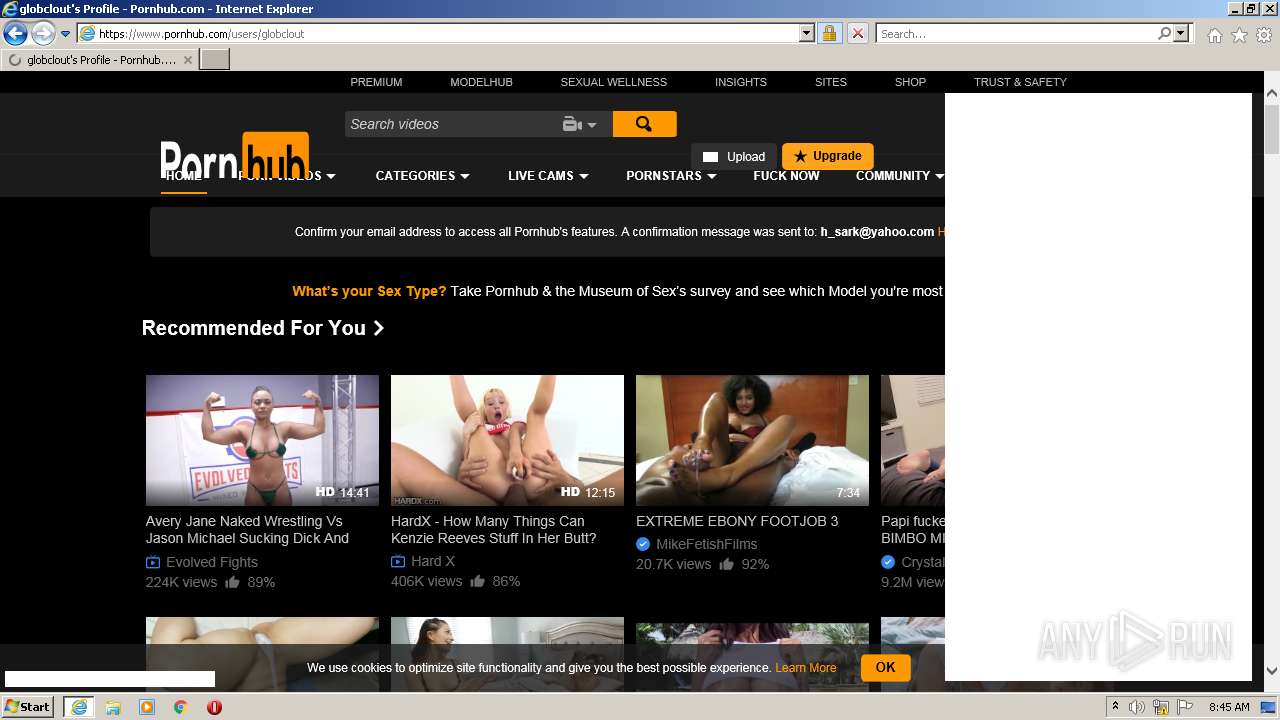
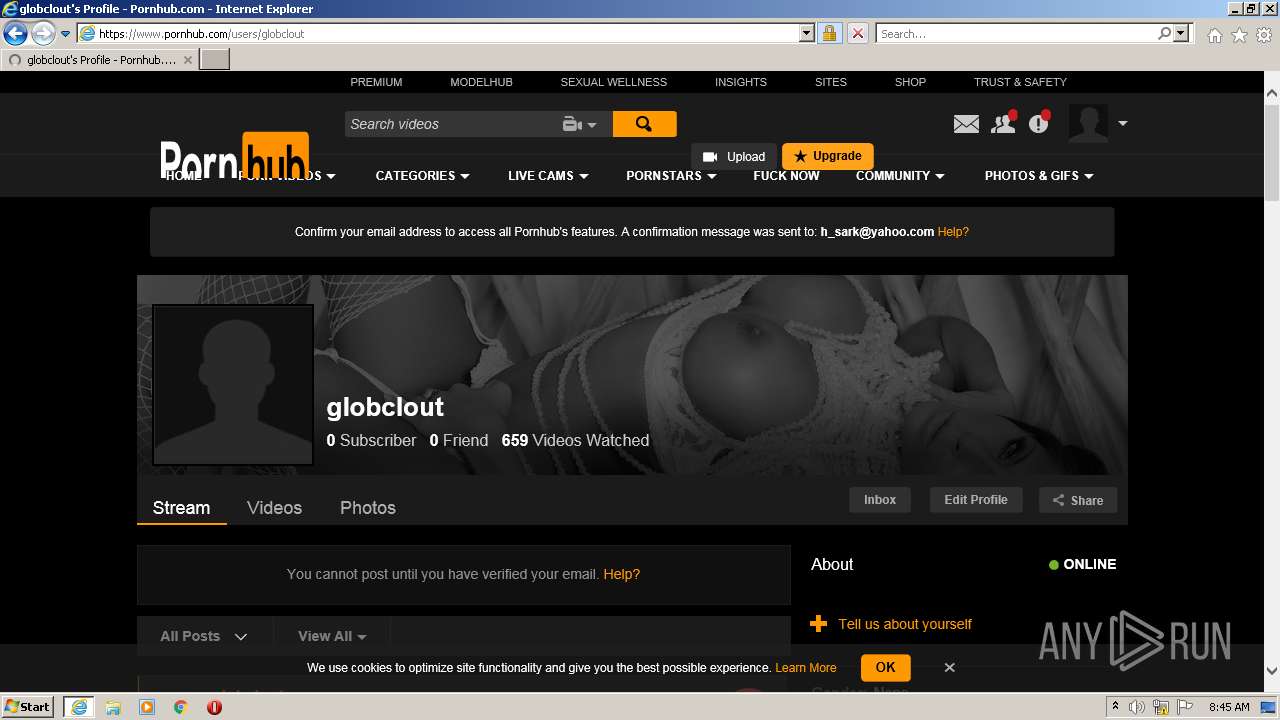
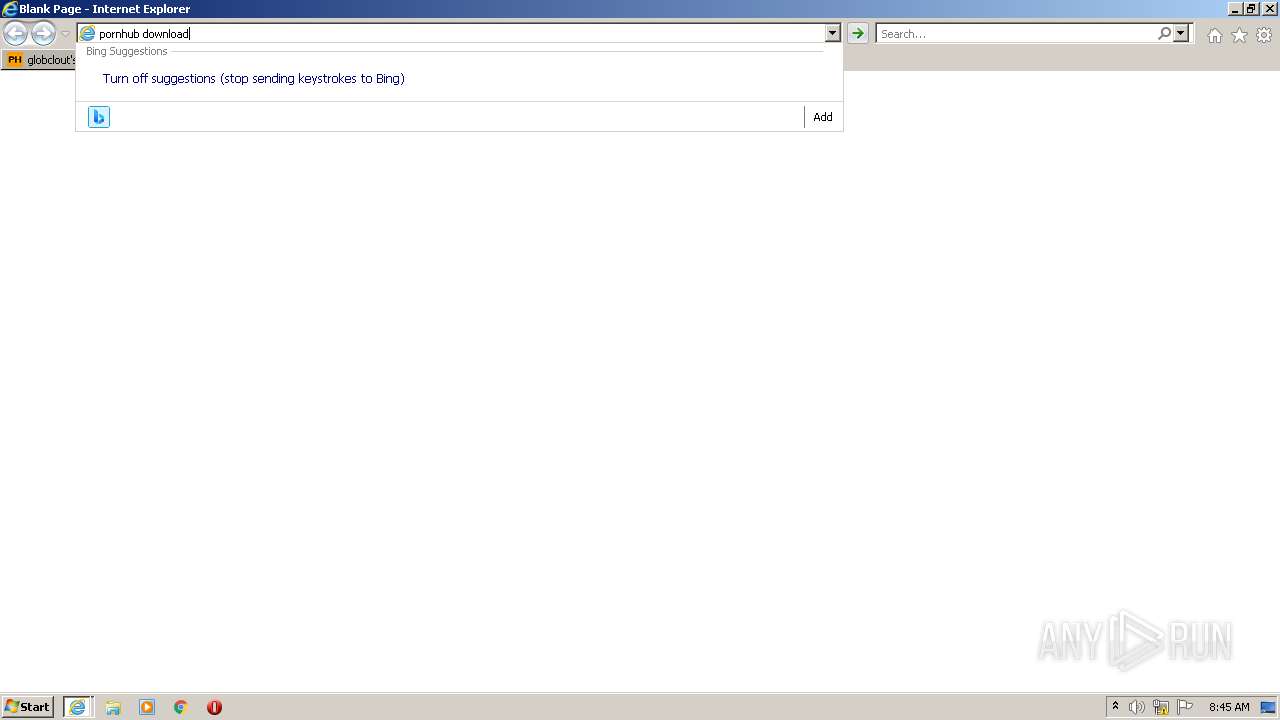
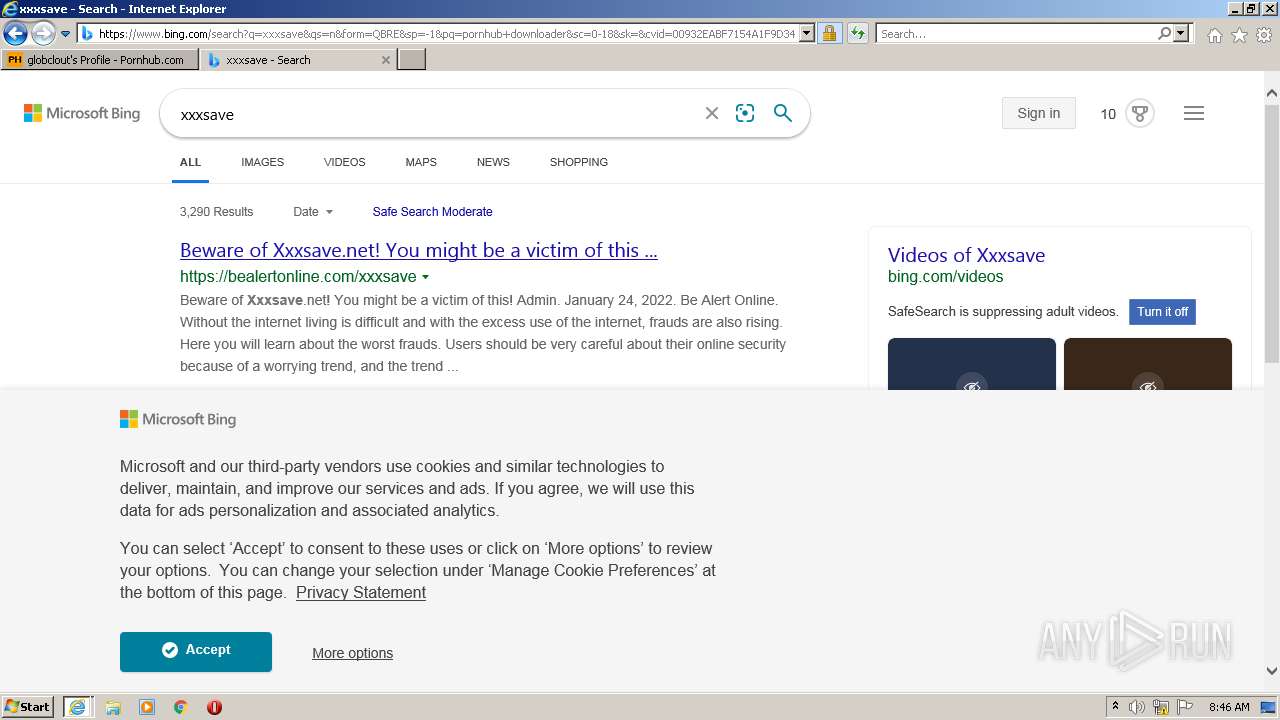
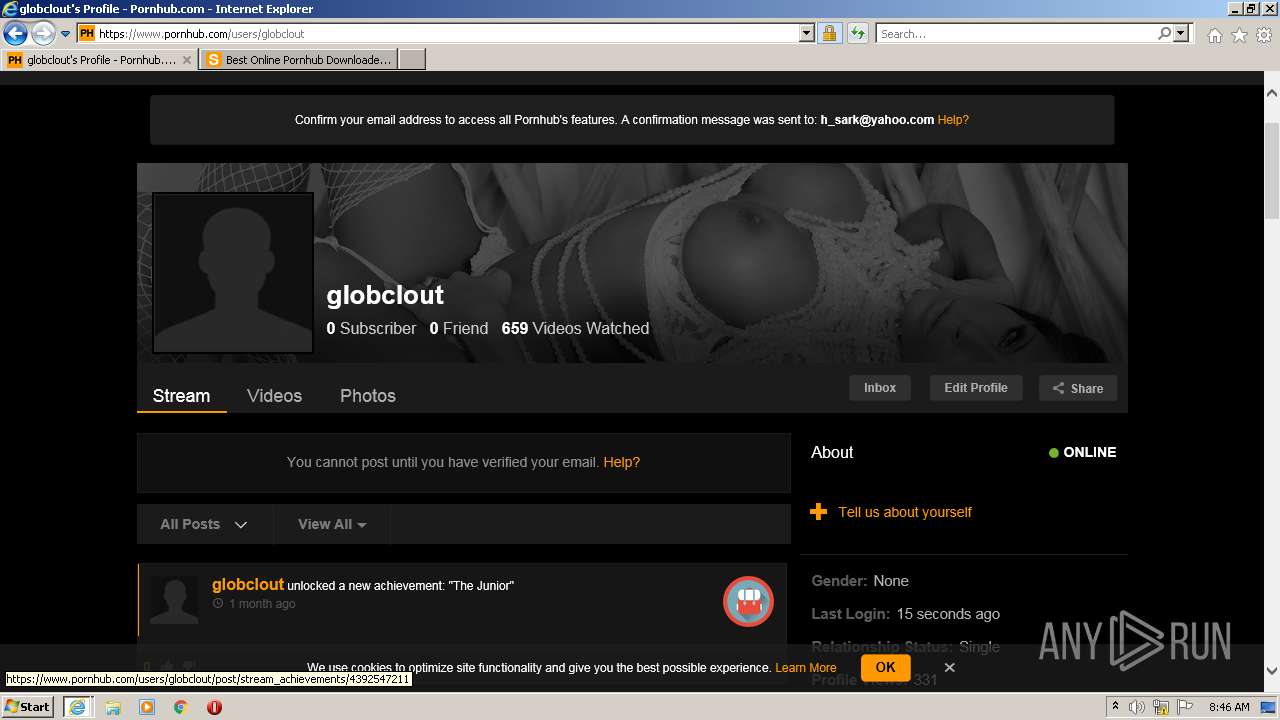
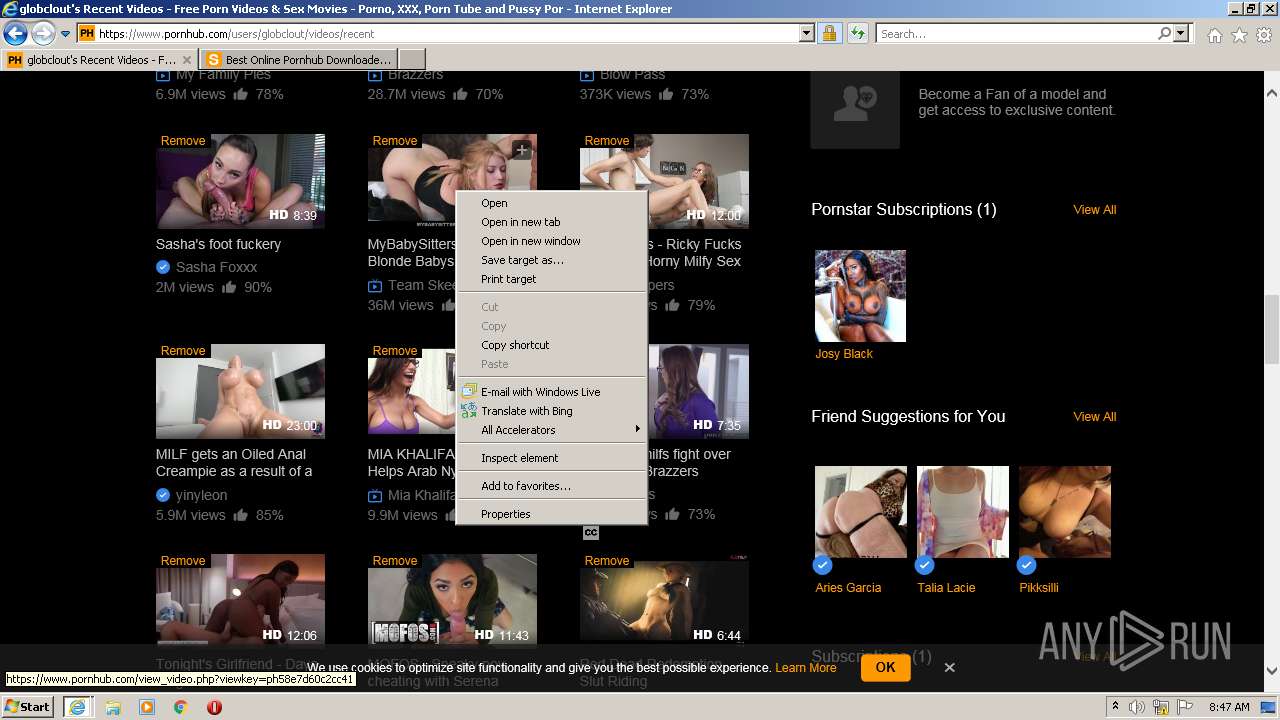
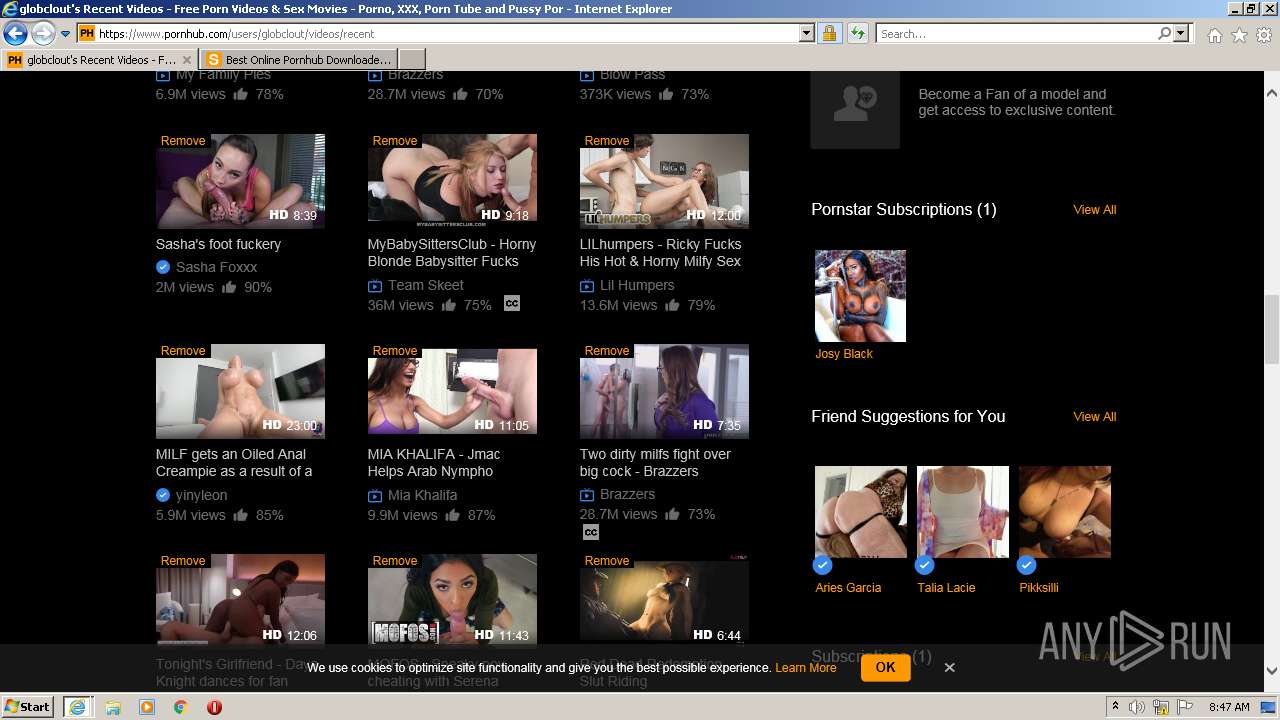
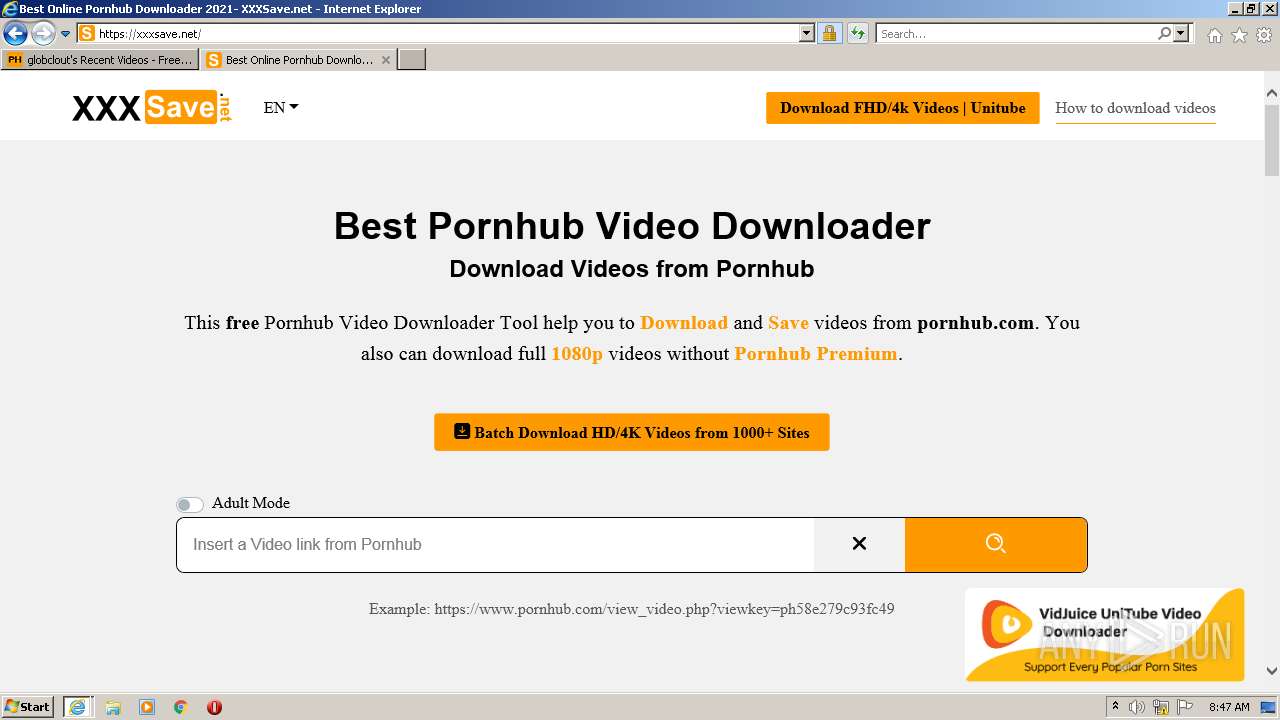
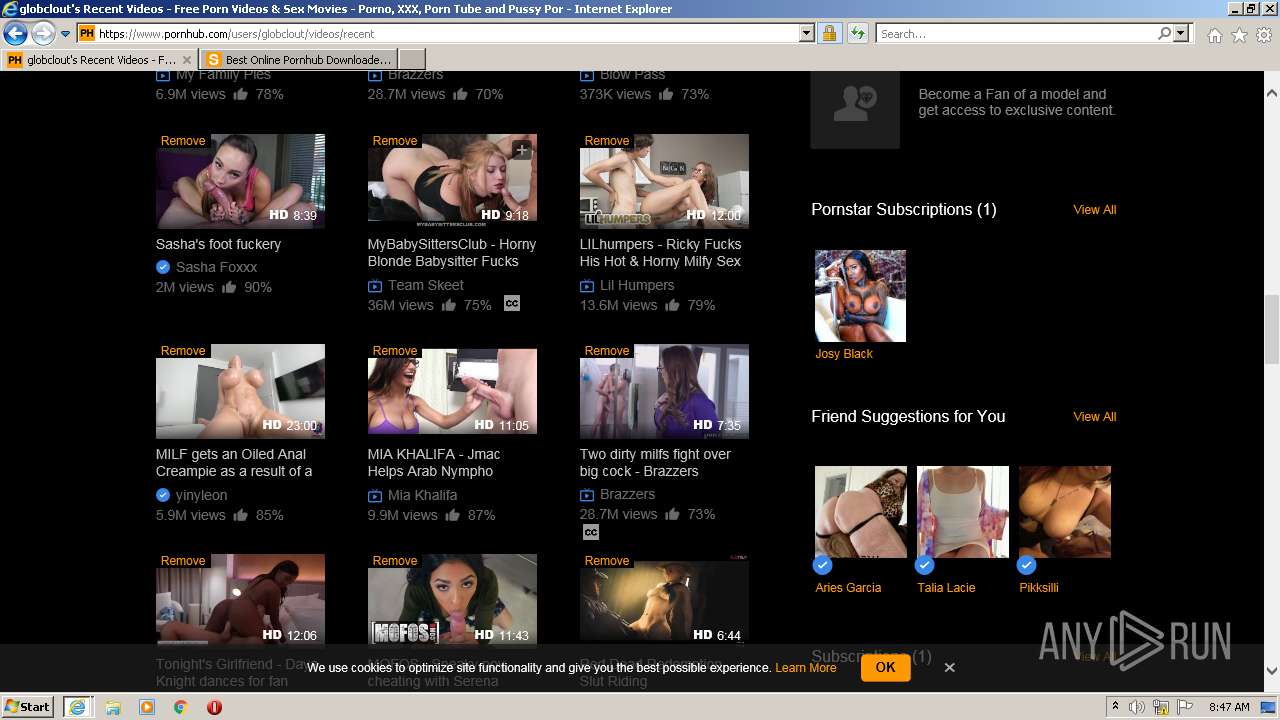
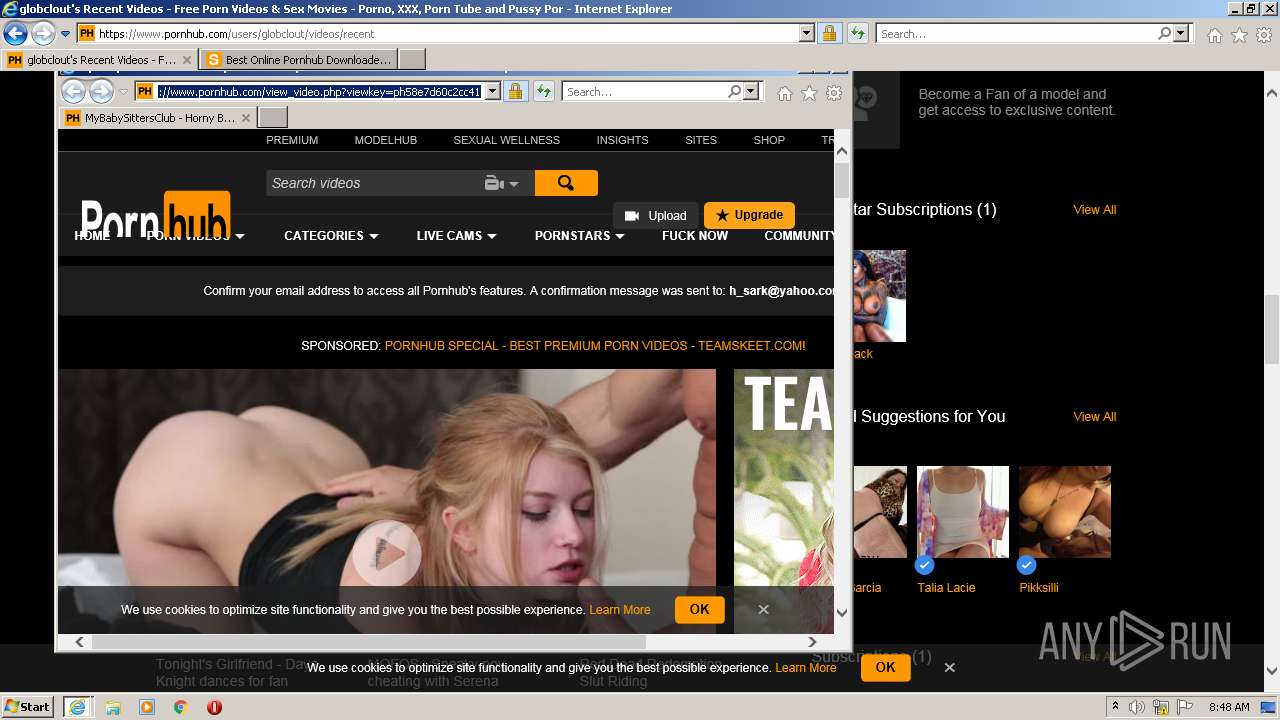
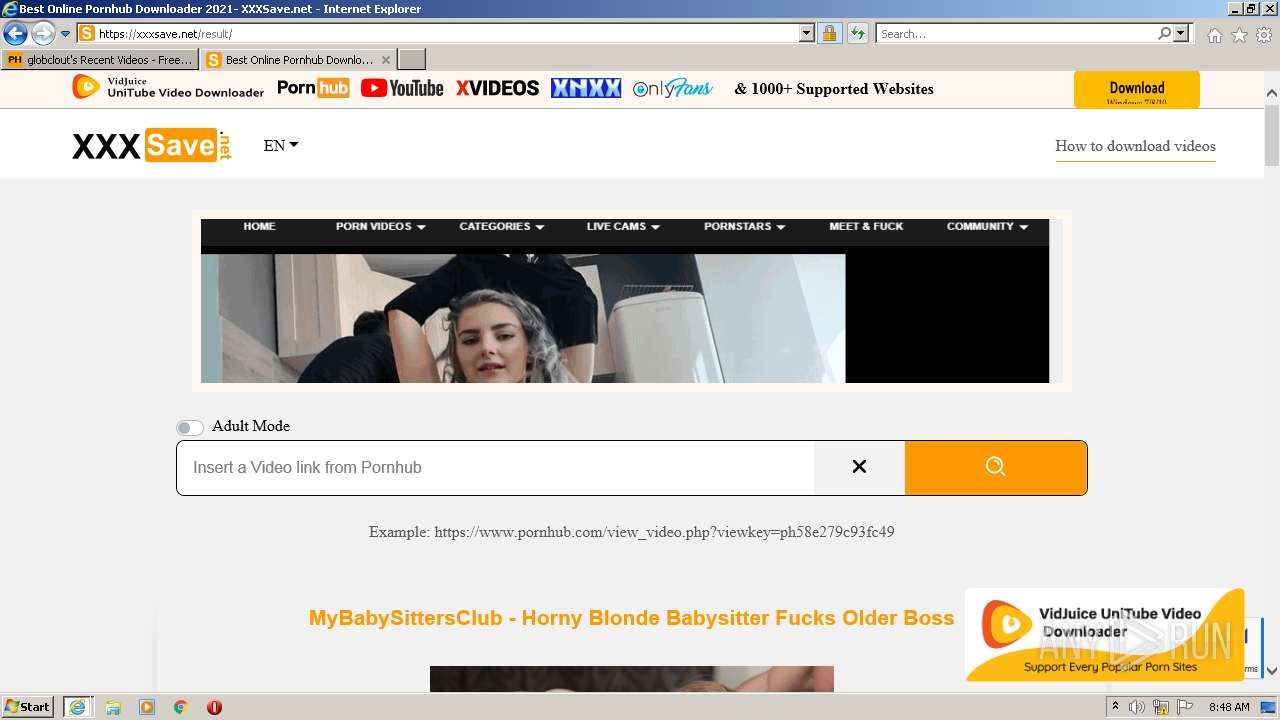
| URL: | https://www.pornhub.com |
| Full analysis: | https://app.any.run/tasks/dccbb39a-1a9f-44eb-adc2-b7646d43cc51 |
| Verdict: | Malicious activity |
| Analysis date: | February 02, 2022, 08:44:50 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 0BABB28FBAA5A0557CBECB21A8A24715 |
| SHA1: | 79CE9FA0965762F0B43CF6DC71BD9672D62B3892 |
| SHA256: | 428FEE64F7249D15B802857D45F3A2FEAA44BB3B870DD187D64CF7EBBA3DDE8C |
| SSDEEP: | 3:N8DSLN2:2OLo |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3680)
- iexplore.exe (PID: 2300)
- iexplore.exe (PID: 404)
- iexplore.exe (PID: 3840)
- iexplore.exe (PID: 2080)
INFO
Checks supported languages
- iexplore.exe (PID: 2300)
- iexplore.exe (PID: 3680)
- iexplore.exe (PID: 404)
- iexplore.exe (PID: 3840)
- iexplore.exe (PID: 2080)
Application launched itself
- iexplore.exe (PID: 2300)
Reads the computer name
- iexplore.exe (PID: 3680)
- iexplore.exe (PID: 404)
- iexplore.exe (PID: 2300)
- iexplore.exe (PID: 3840)
- iexplore.exe (PID: 2080)
Reads settings of System Certificates
- iexplore.exe (PID: 3680)
- iexplore.exe (PID: 2300)
- iexplore.exe (PID: 404)
- iexplore.exe (PID: 3840)
- iexplore.exe (PID: 2080)
Checks Windows Trust Settings
- iexplore.exe (PID: 2300)
- iexplore.exe (PID: 404)
- iexplore.exe (PID: 3840)
- iexplore.exe (PID: 3680)
- iexplore.exe (PID: 2080)
Creates files in the user directory
- iexplore.exe (PID: 3680)
- iexplore.exe (PID: 404)
- iexplore.exe (PID: 2300)
- iexplore.exe (PID: 3840)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 3680)
- iexplore.exe (PID: 3840)
- iexplore.exe (PID: 2300)
Reads internet explorer settings
- iexplore.exe (PID: 404)
- iexplore.exe (PID: 3680)
- iexplore.exe (PID: 3840)
- iexplore.exe (PID: 2080)
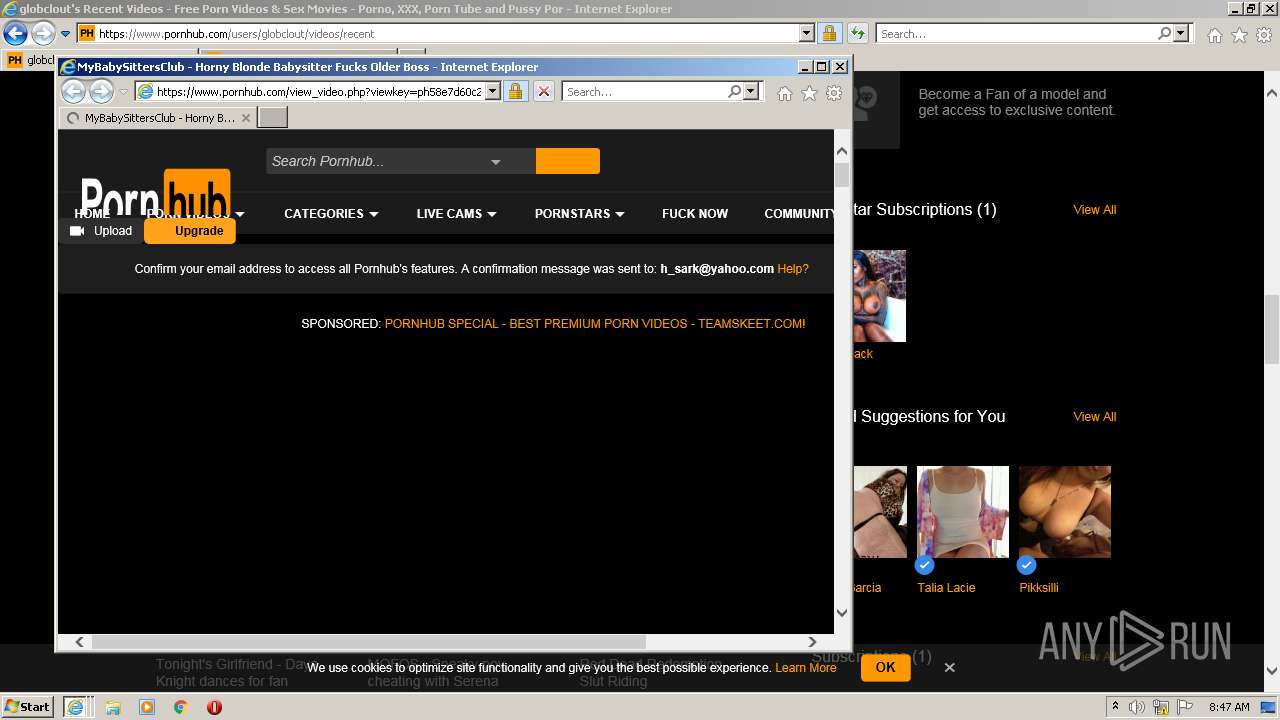
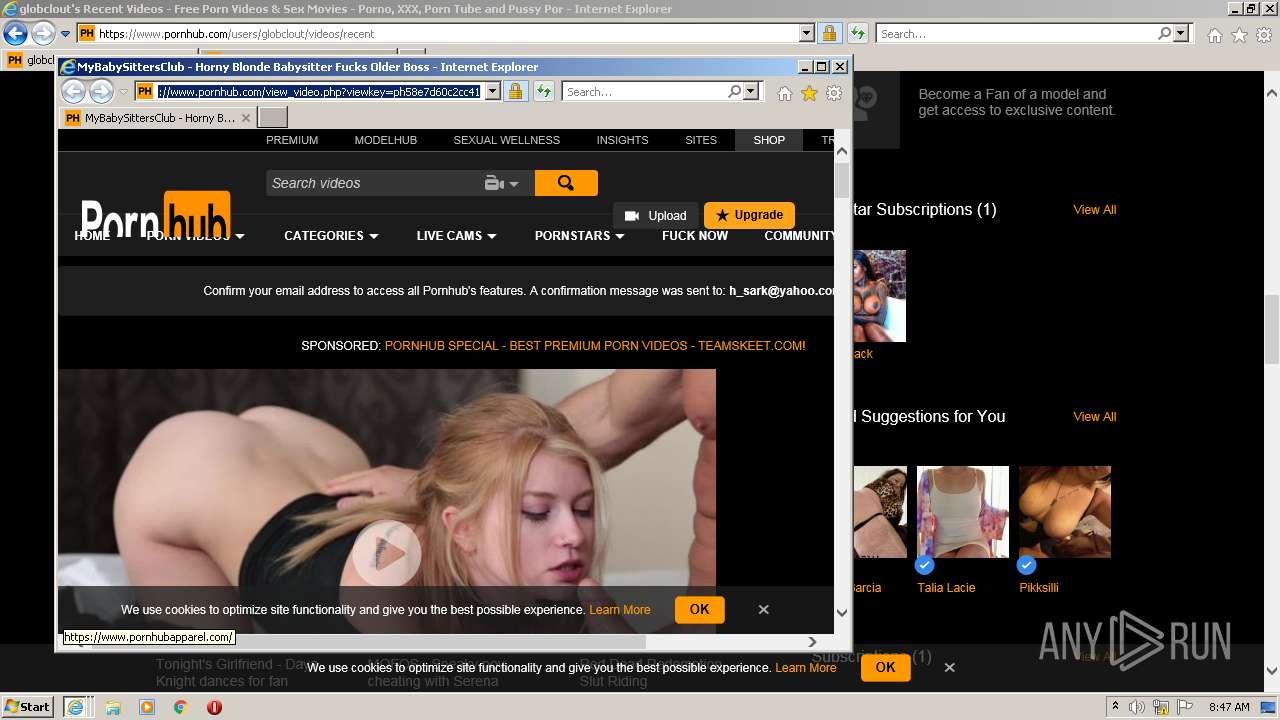
Changes internet zones settings
- iexplore.exe (PID: 2300)
Changes settings of System certificates
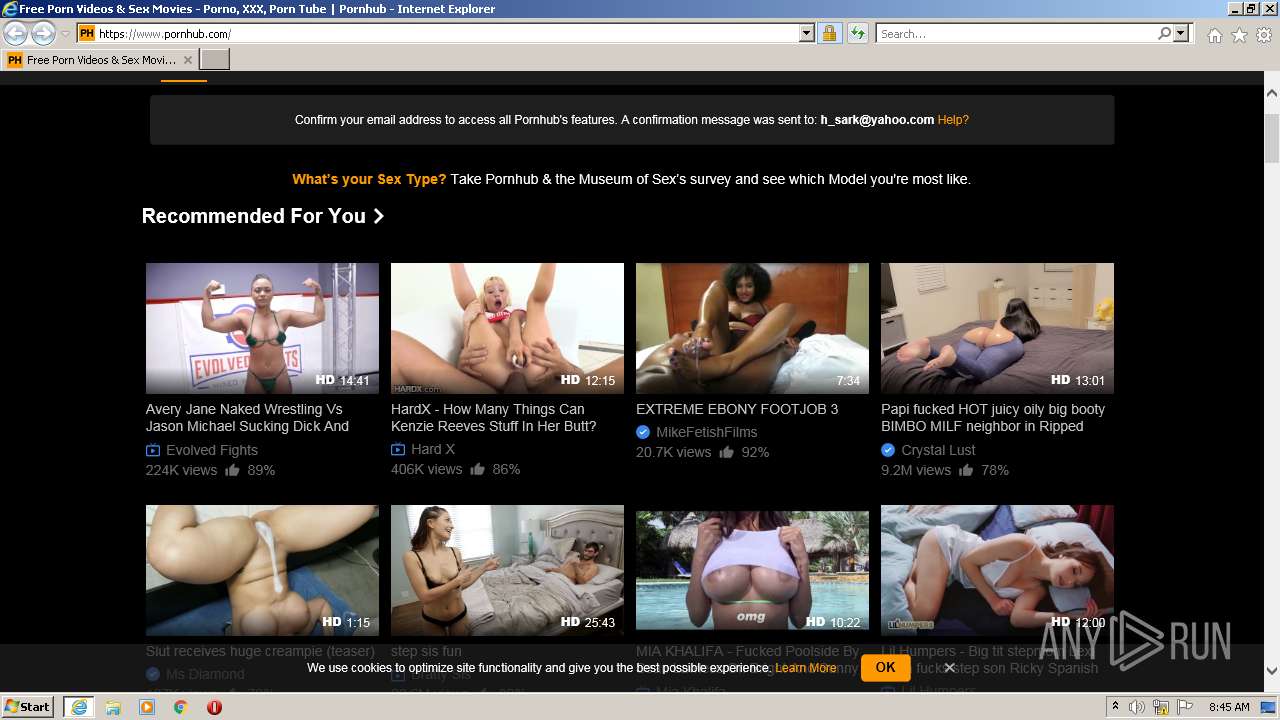
- iexplore.exe (PID: 2300)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2300)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2300)
Reads the date of Windows installation
- iexplore.exe (PID: 2300)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
43
Monitored processes
5
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 404 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2300 CREDAT:1709328 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2080 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2300 CREDAT:3675430 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
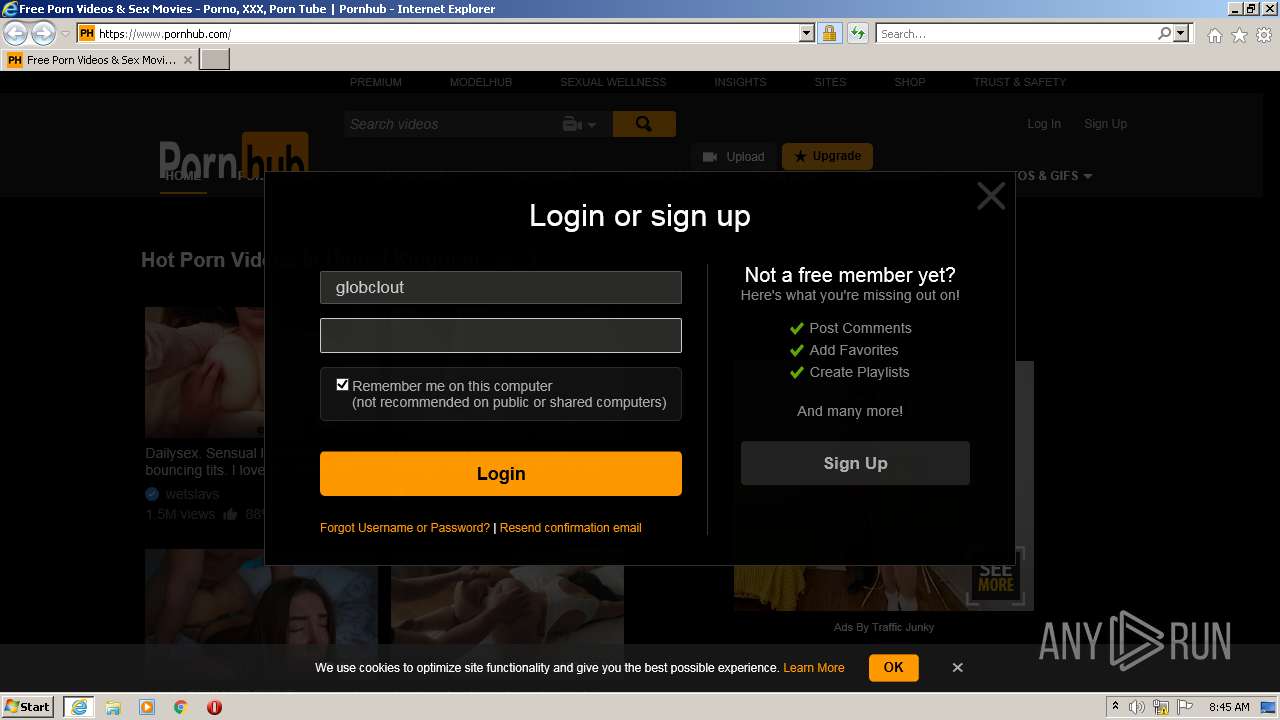
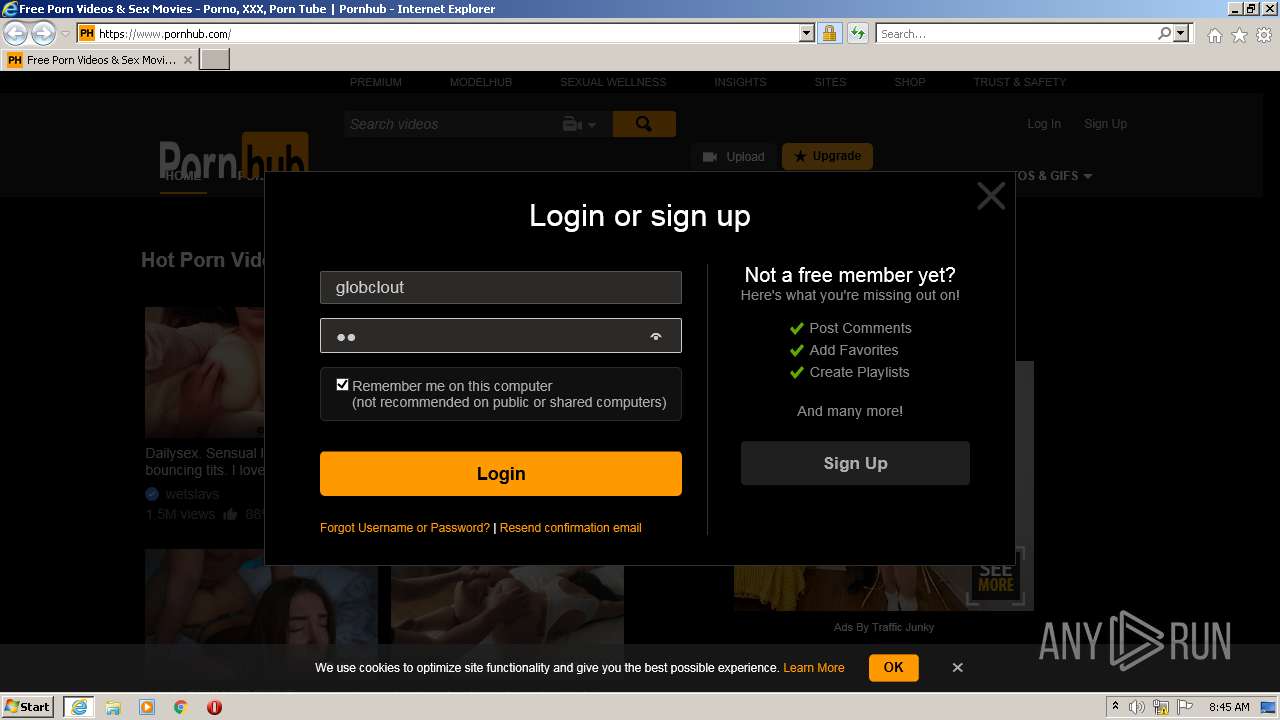
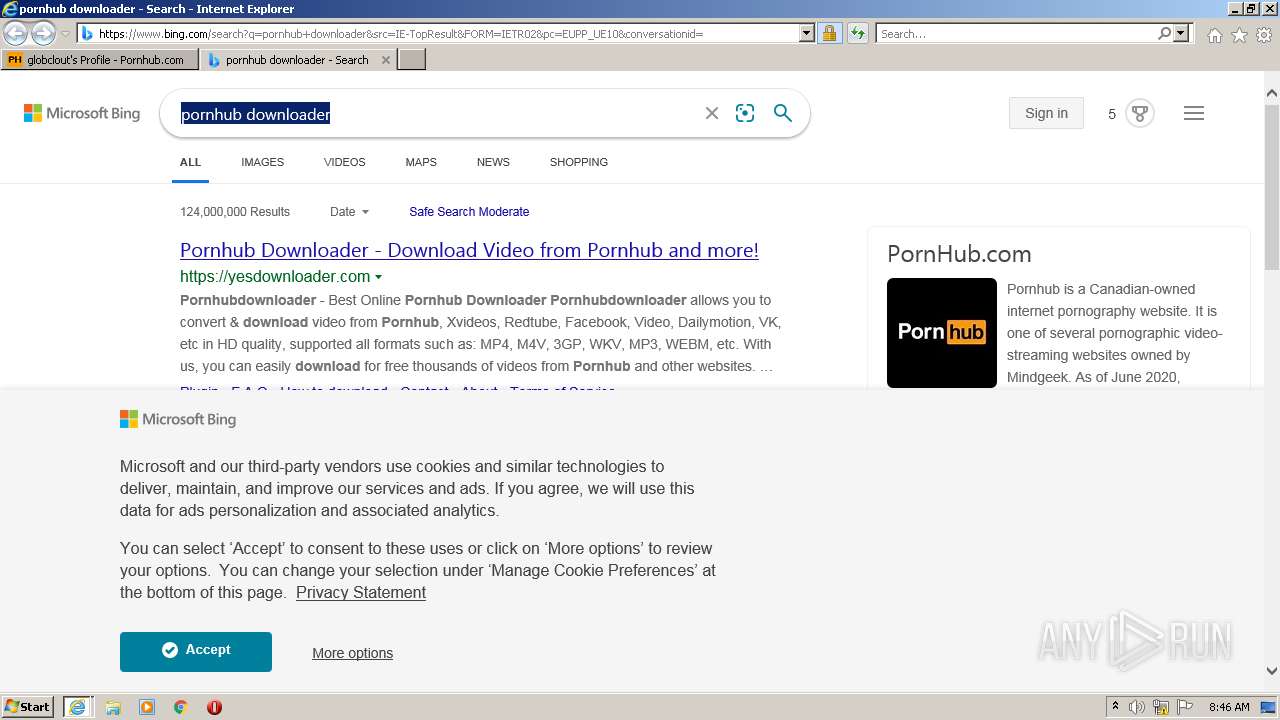
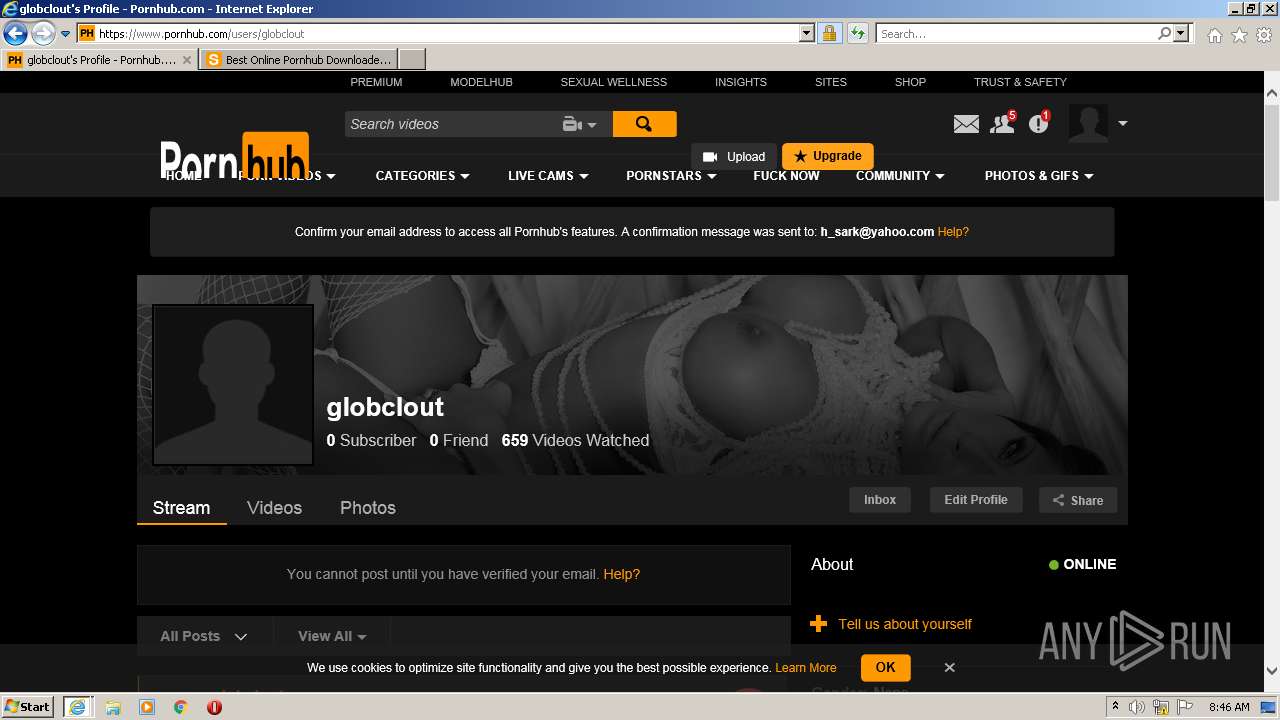
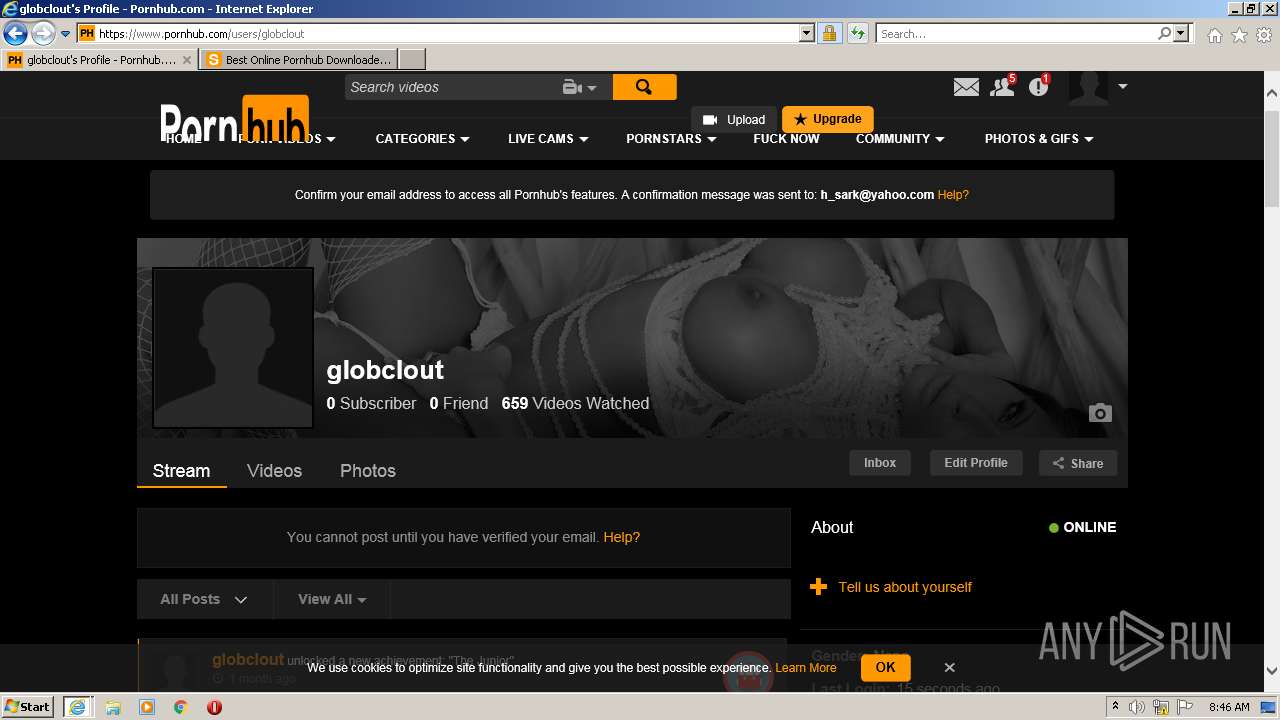
| 2300 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://www.pornhub.com" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3680 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2300 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3840 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2300 CREDAT:3347737 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
58 395
Read events
57 827
Write events
566
Delete events
2
Modification events
| (PID) Process: | (2300) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2300) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 630449712 | |||
| (PID) Process: | (2300) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30939153 | |||
| (PID) Process: | (2300) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 930457212 | |||
| (PID) Process: | (2300) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30939153 | |||
| (PID) Process: | (2300) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2300) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2300) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2300) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2300) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
52
Text files
890
Unknown types
53
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3680 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\69C6F6EC64E114822DF688DC12CDD86C | der | |
MD5:— | SHA256:— | |||
| 3680 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\69C6F6EC64E114822DF688DC12CDD86C | binary | |
MD5:— | SHA256:— | |||
| 3680 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\50CD3D75D026C82E2E718570BD6F44D0_41264EE4E268B443986A5A0E2A2EC9C6 | der | |
MD5:— | SHA256:— | |||
| 3680 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\Q04QKM4N.txt | text | |
MD5:— | SHA256:— | |||
| 3680 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B9C0457FE8FDF881D9EA458DAD3D4142_79C09928C2DEED6D69E117D673E3388B | der | |
MD5:— | SHA256:— | |||
| 2300 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:— | SHA256:— | |||
| 3680 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\5AQSILP6.txt | text | |
MD5:— | SHA256:— | |||
| 3680 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\MDERF9GH.txt | text | |
MD5:— | SHA256:— | |||
| 2300 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:— | SHA256:— | |||
| 3680 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\6TBSRVMC.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
29
TCP/UDP connections
302
DNS requests
72
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
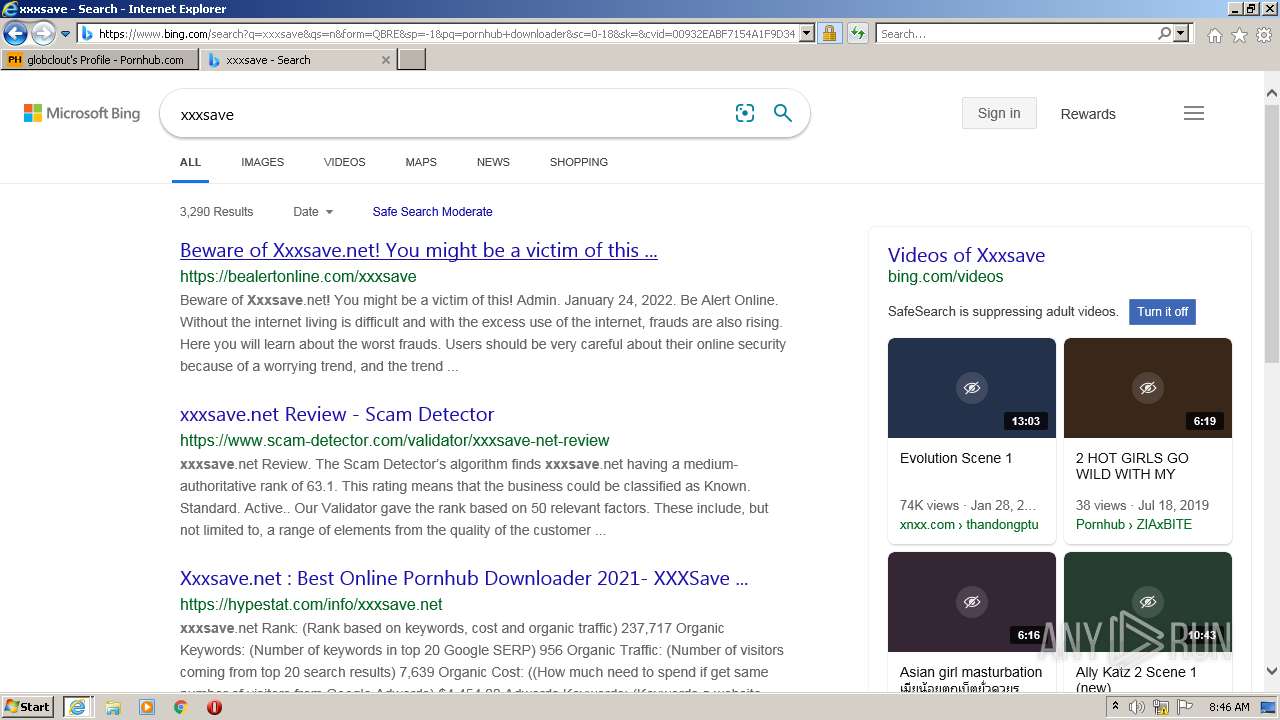
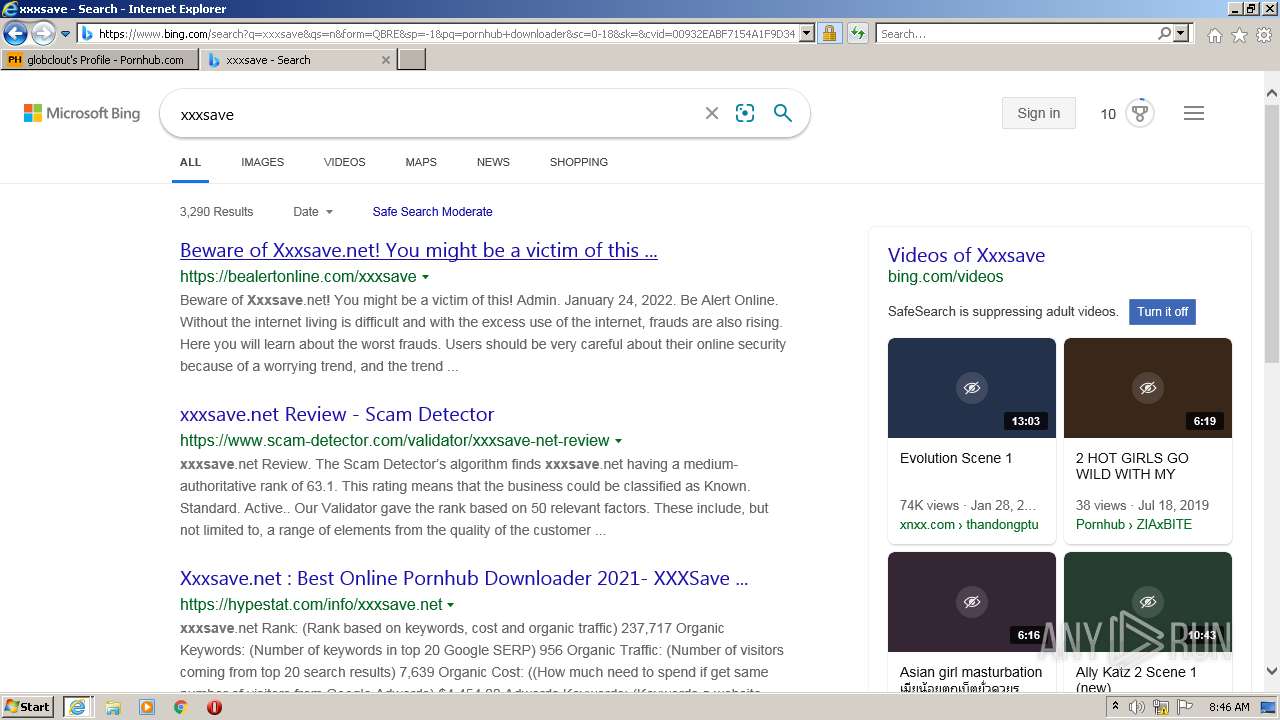
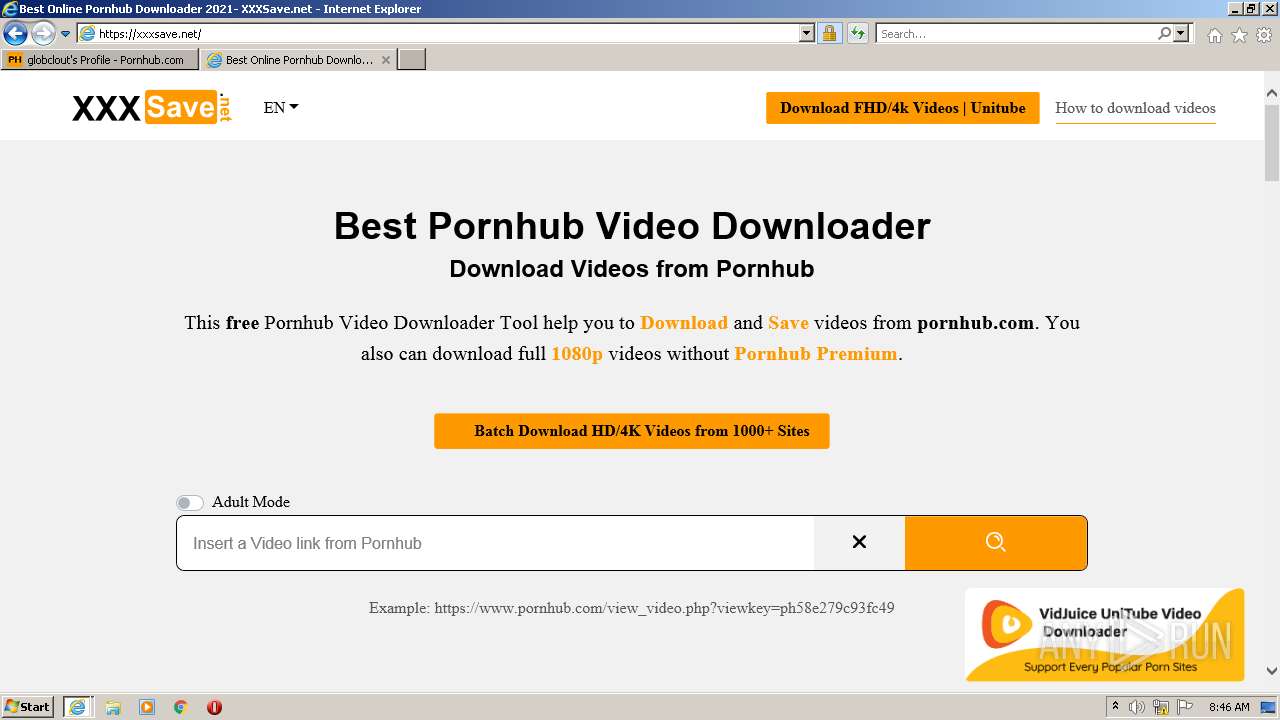
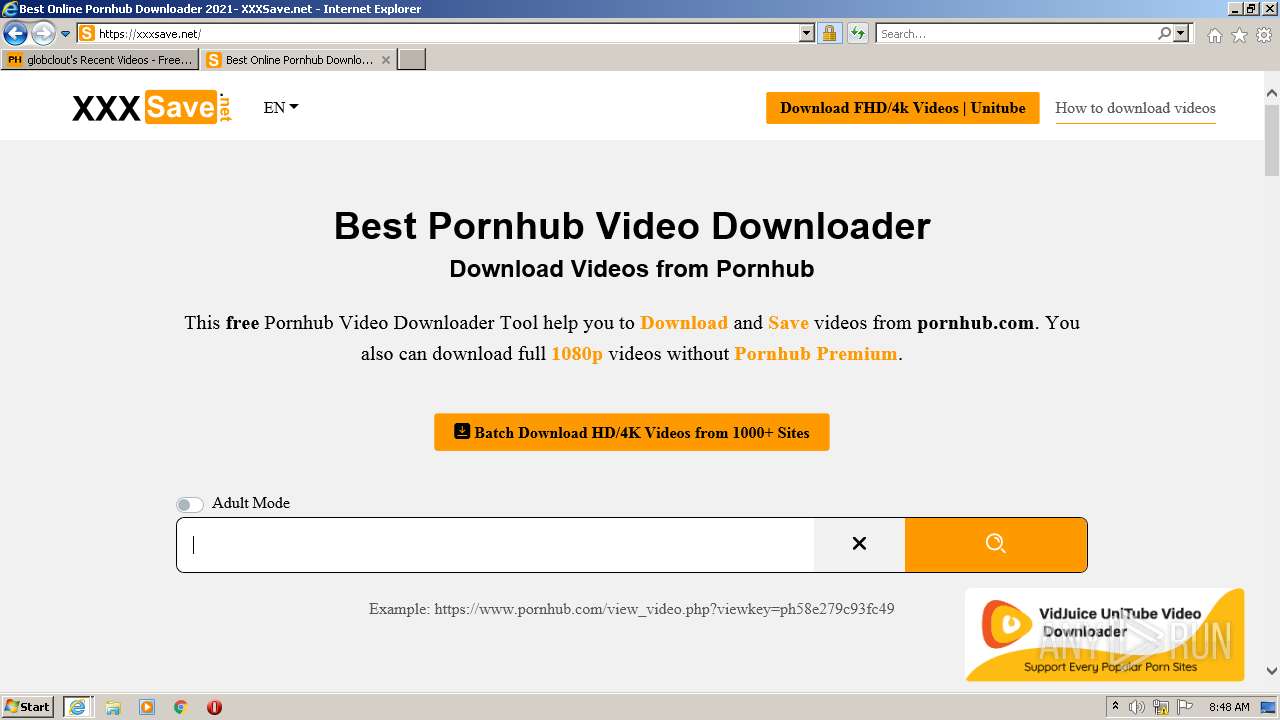
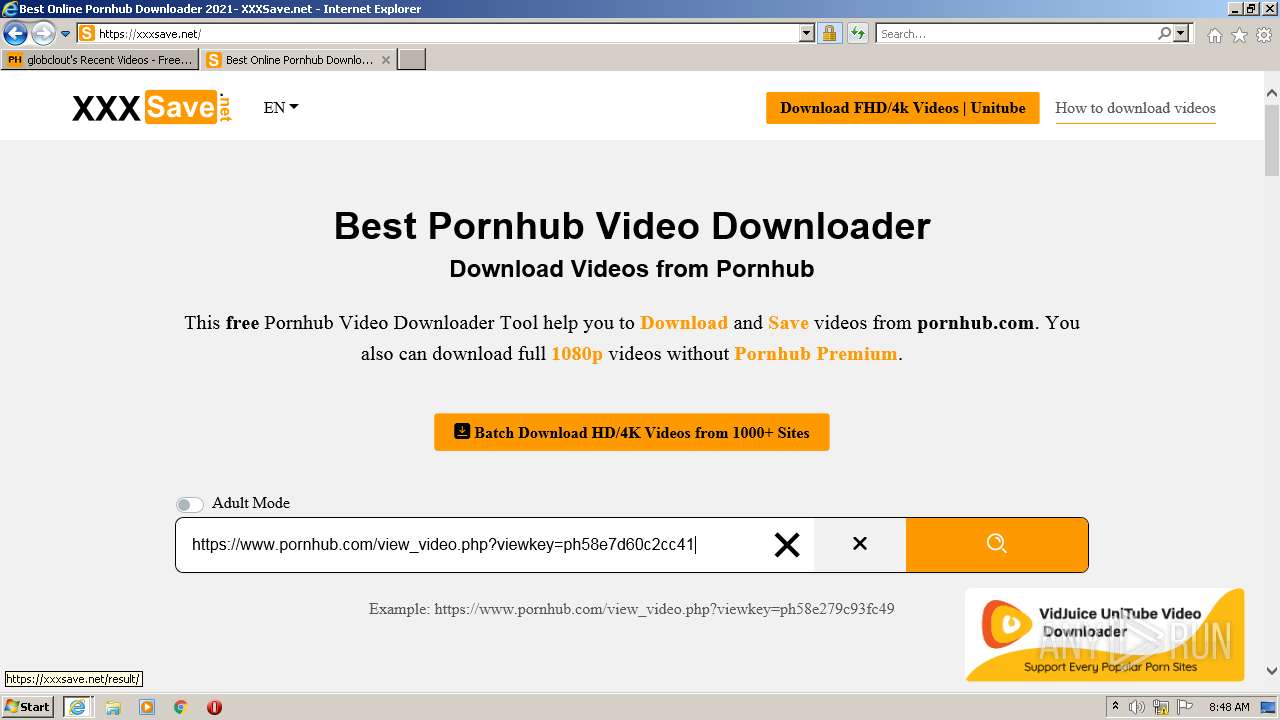
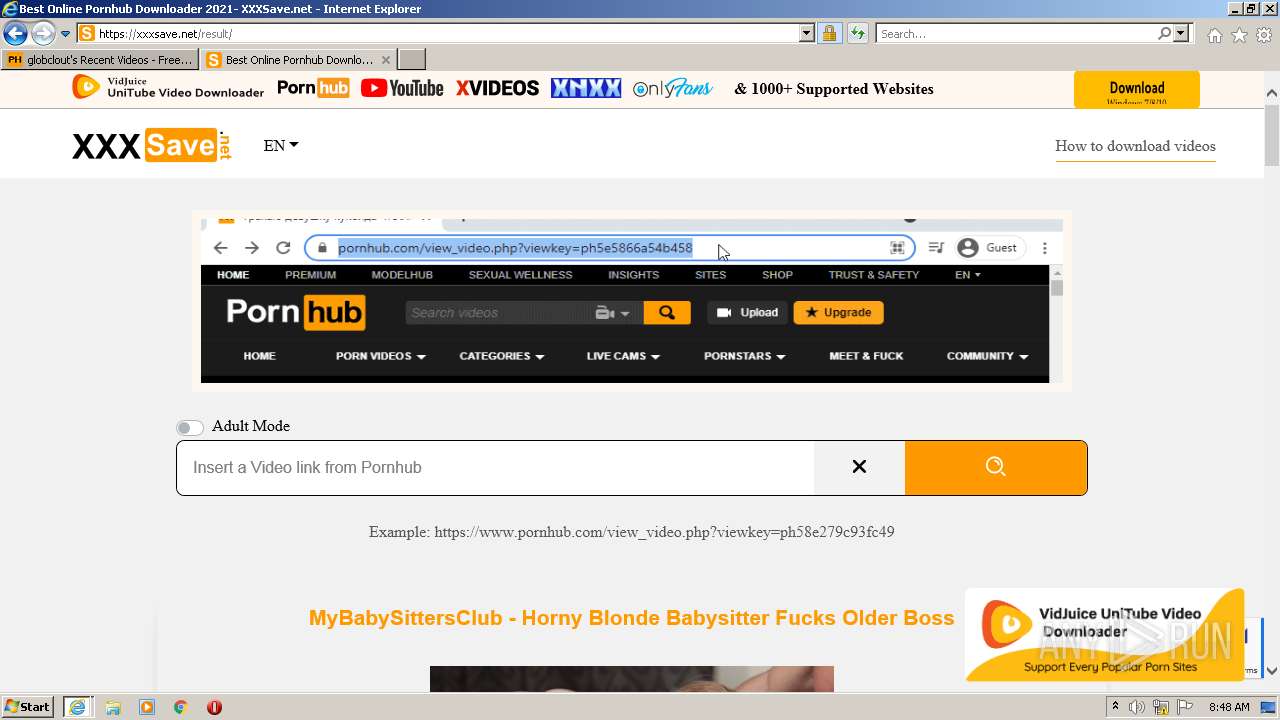
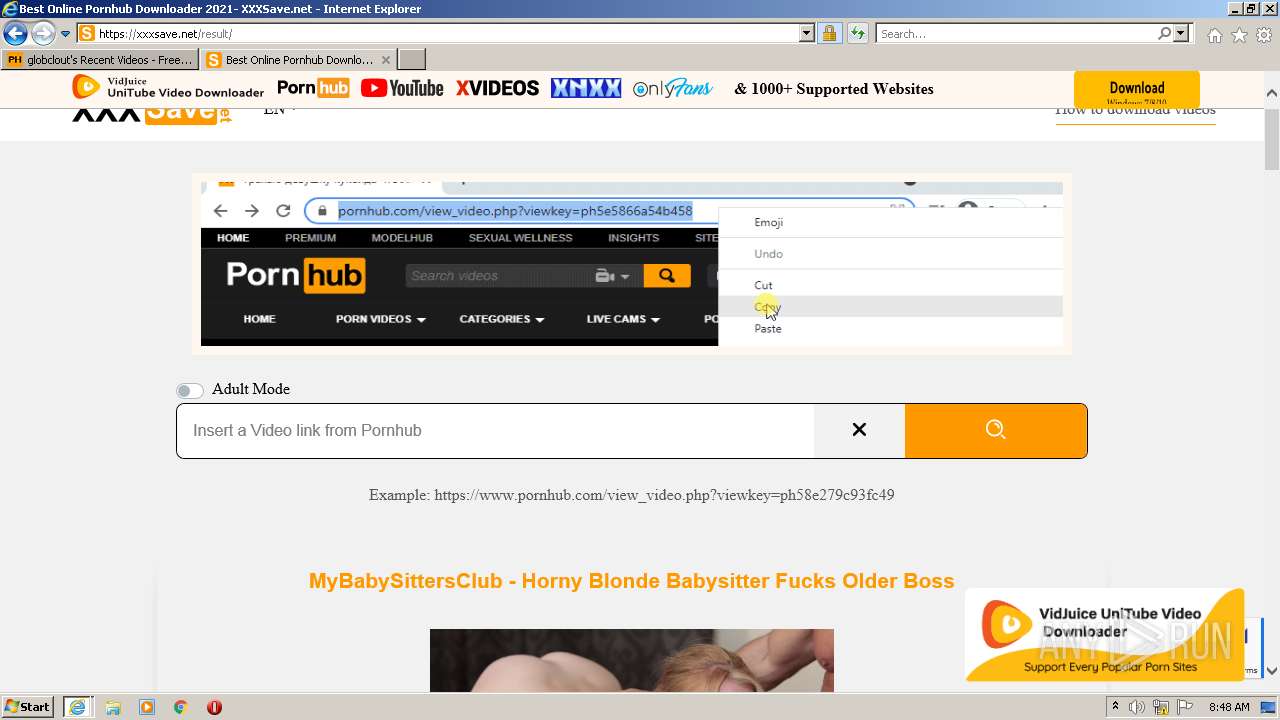
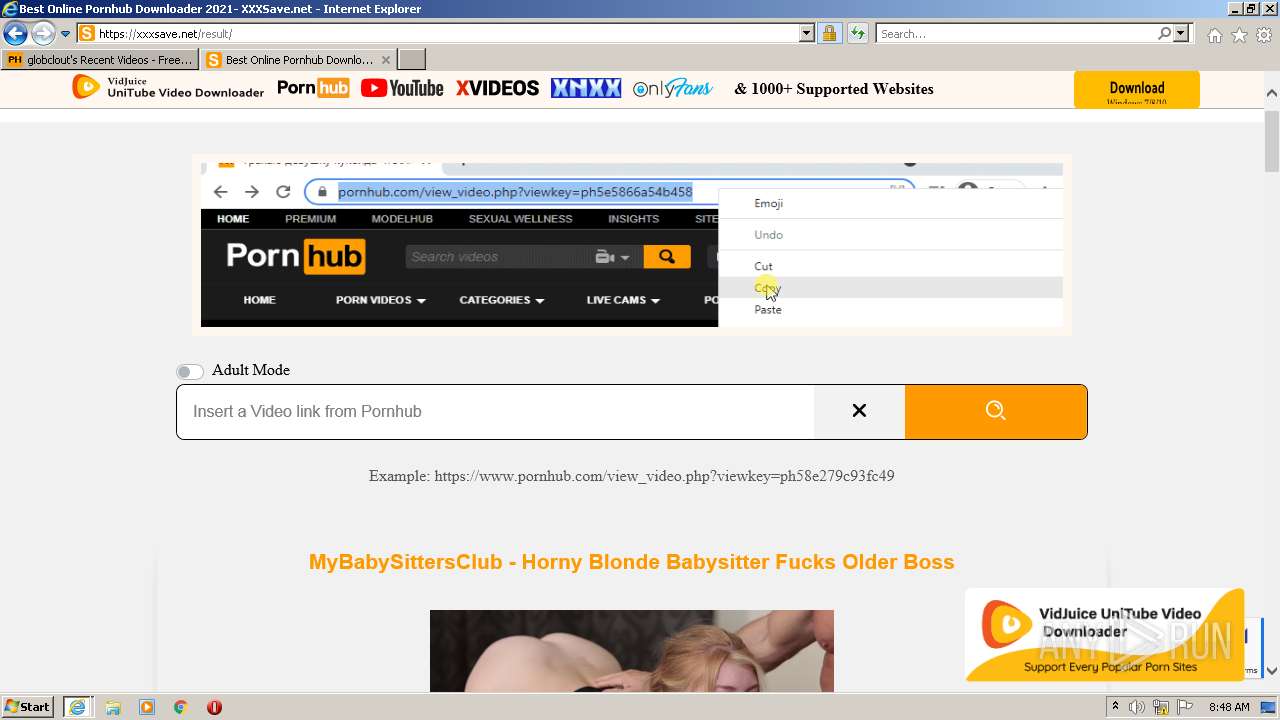
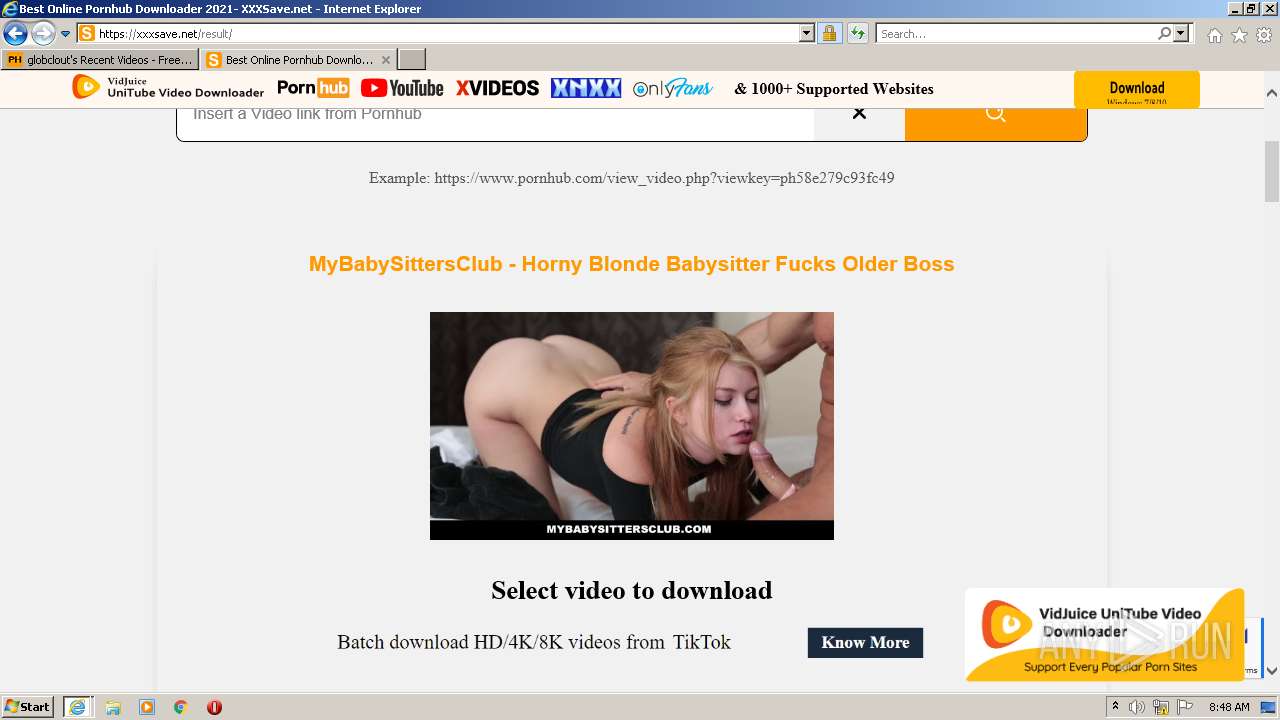
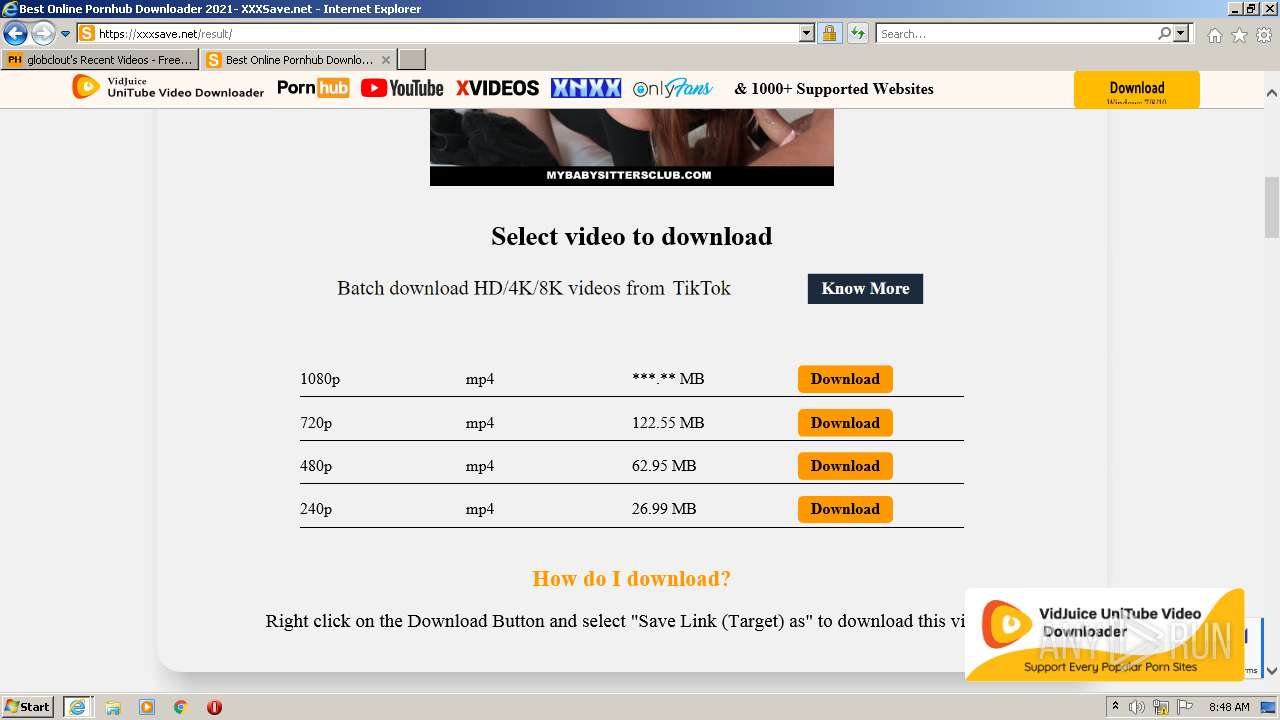
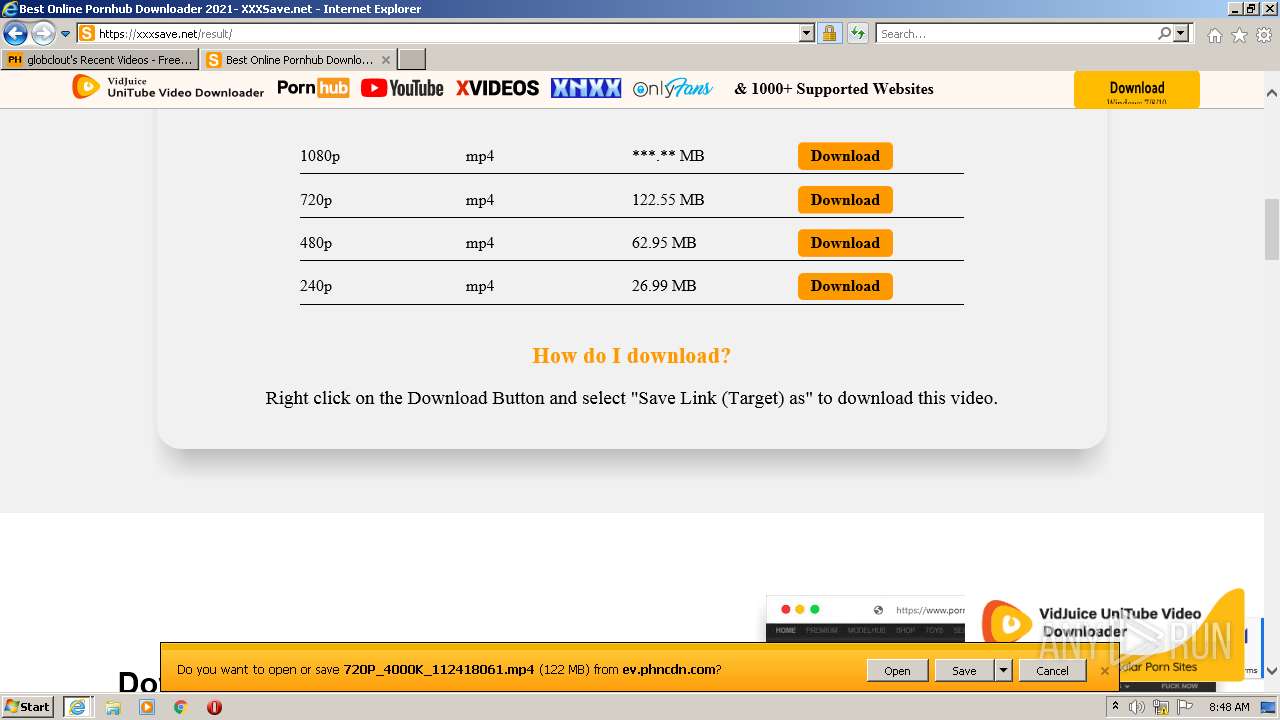
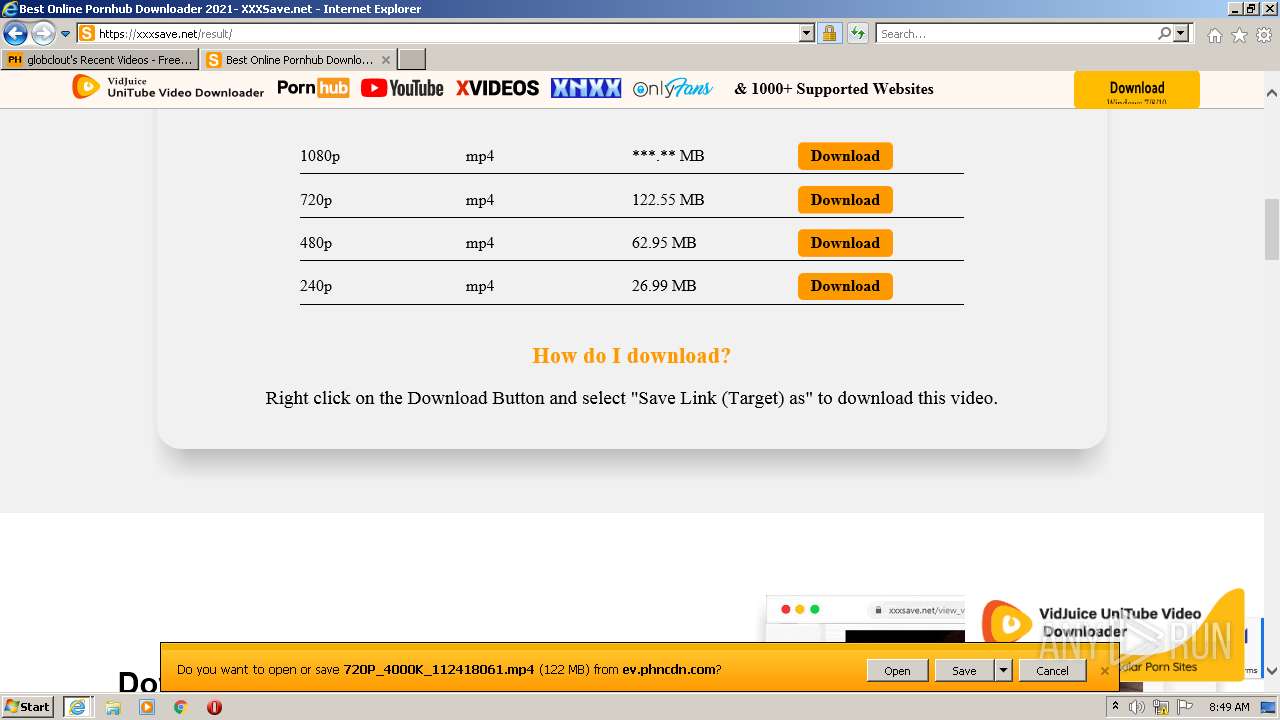
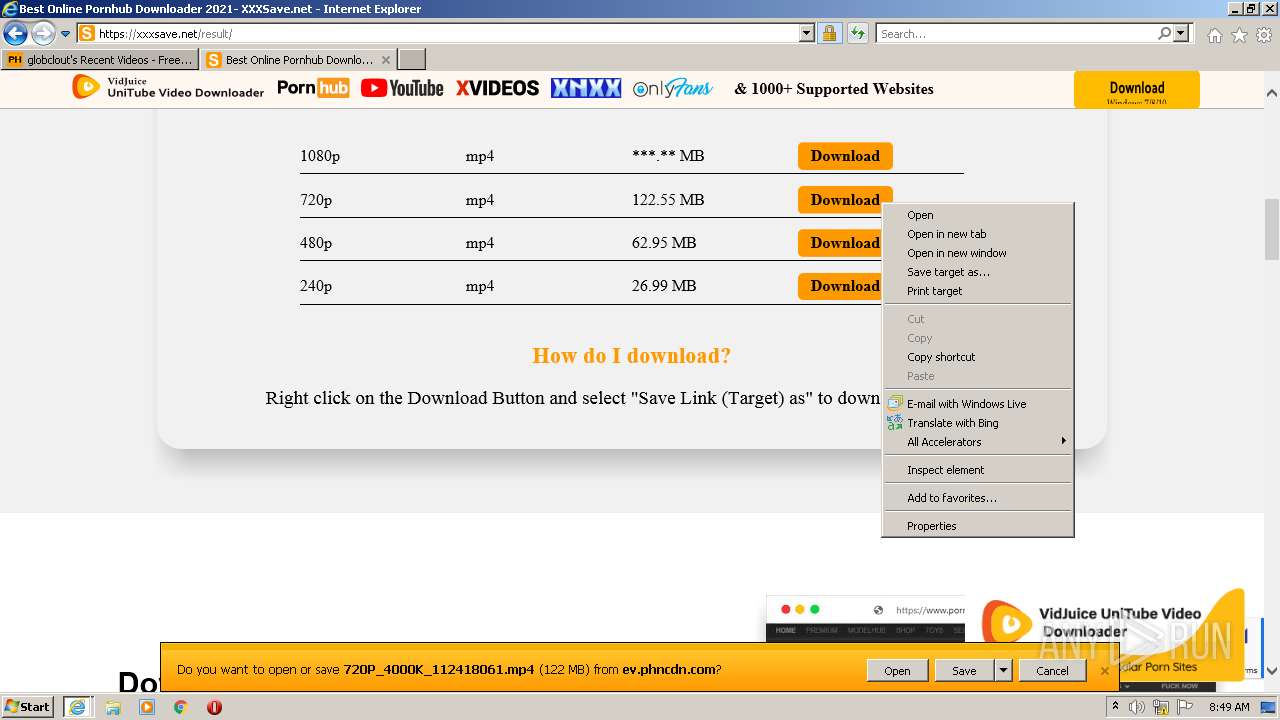
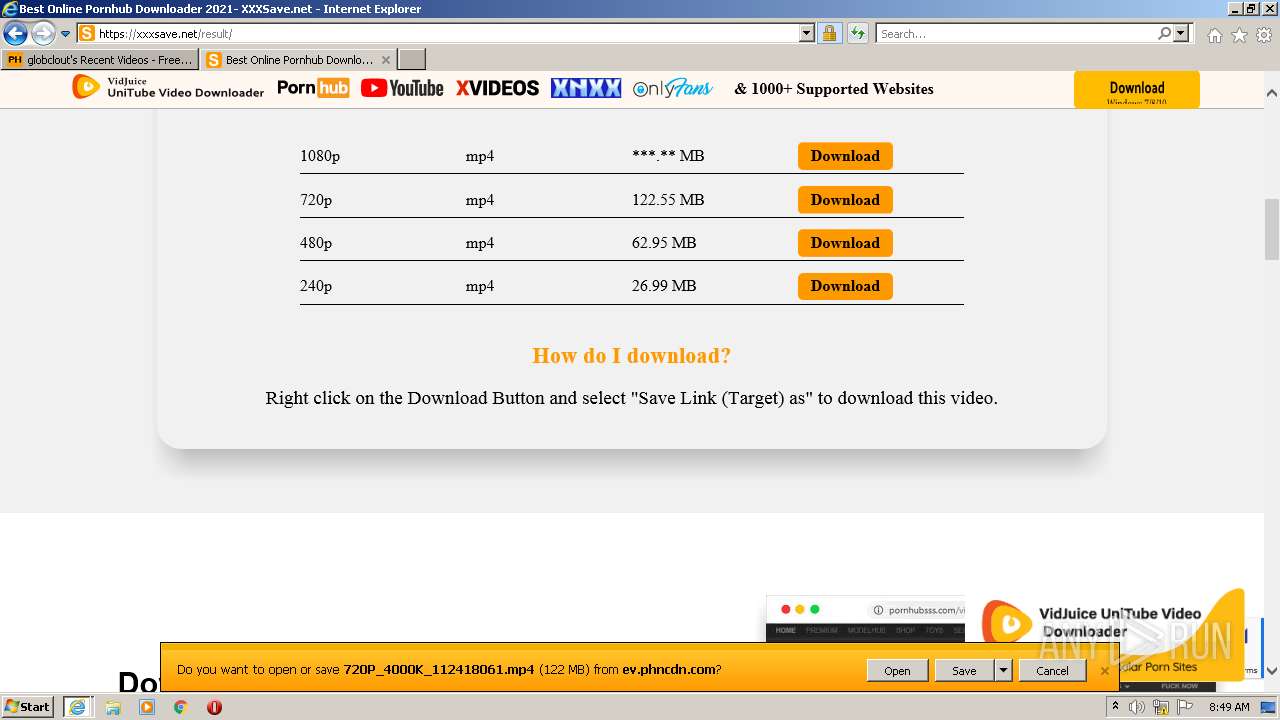
404 | iexplore.exe | GET | 301 | 104.21.35.228:80 | http://xxxsave.net/ | US | — | — | suspicious |
2300 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
3680 | iexplore.exe | GET | 200 | 142.250.185.67:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
3680 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQrHR6YzPN2BNbByL0VoiTIBBMAOAQUCrwIKReMpTlteg7OM8cus%2B37w3oCEAd3SBjpSMd4ojHOUsfJYh8%3D | US | der | 313 b | whitelisted |
3680 | iexplore.exe | GET | 200 | 142.250.185.67:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
3680 | iexplore.exe | GET | 200 | 142.250.185.67:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDgAde1VeKYIQoAAAABK4GI | US | der | 472 b | whitelisted |
3680 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQrHR6YzPN2BNbByL0VoiTIBBMAOAQUCrwIKReMpTlteg7OM8cus%2B37w3oCEAesnwjCDw5EIfkDmxEaF14%3D | US | der | 312 b | whitelisted |
3680 | iexplore.exe | GET | 200 | 142.250.185.67:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQC2PrP09fGo%2BgoAAAABK3x6 | US | der | 472 b | whitelisted |
2300 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA177el9ggmWelJjG4vdGL0%3D | US | der | 471 b | whitelisted |
404 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3680 | iexplore.exe | 66.254.114.41:443 | www.pornhub.com | Reflected Networks, Inc. | US | malicious |
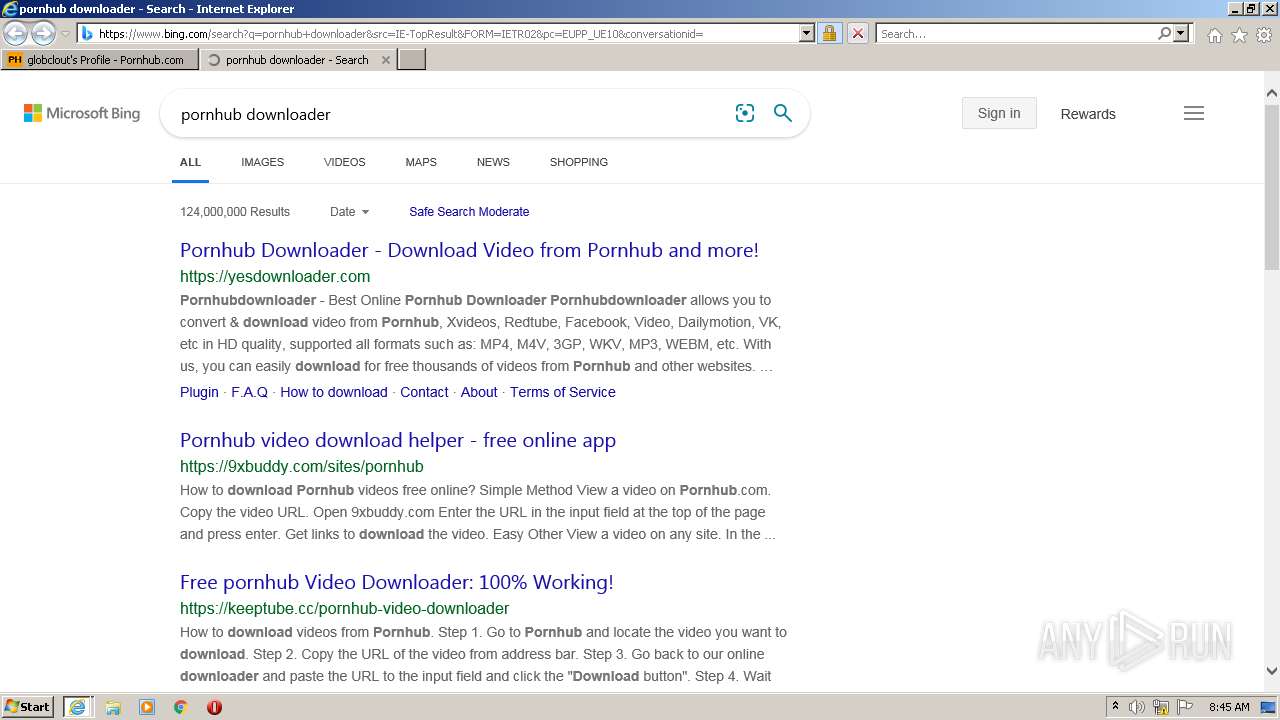
2300 | iexplore.exe | 13.107.21.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3680 | iexplore.exe | 205.185.208.79:443 | static.trafficjunky.com | Highwinds Network Group, Inc. | US | unknown |
2300 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3680 | iexplore.exe | 216.18.168.30:443 | hubt.pornhub.com | Reflected Networks, Inc. | US | unknown |
3680 | iexplore.exe | 142.250.185.67:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3680 | iexplore.exe | 142.250.184.206:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
3680 | iexplore.exe | 66.254.122.18:443 | ei.phncdn.com | Reflected Networks, Inc. | US | suspicious |
3680 | iexplore.exe | 66.254.114.171:443 | a.adtng.com | Reflected Networks, Inc. | US | suspicious |
3680 | iexplore.exe | 66.254.114.38:443 | ads.trafficjunky.net | Reflected Networks, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.pornhub.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |
ei.phncdn.com |
| whitelisted |
static.trafficjunky.com |
| whitelisted |
di.phncdn.com |
| whitelisted |
hubt.pornhub.com |
| whitelisted |