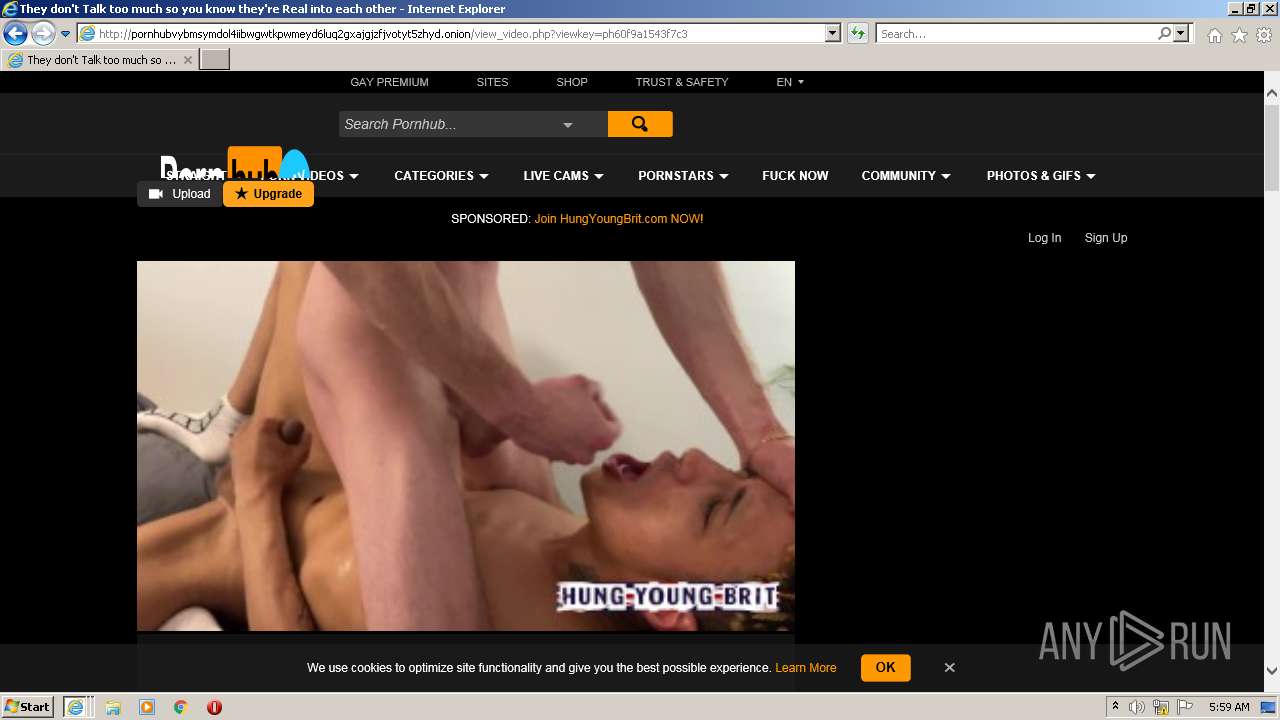
| URL: | https://www.pornhub.com |
| Full analysis: | https://app.any.run/tasks/01fb6ccc-2d52-4c8b-bd34-9d4644e1ef28 |
| Verdict: | Malicious activity |
| Analysis date: | February 24, 2022, 05:58:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 0BABB28FBAA5A0557CBECB21A8A24715 |
| SHA1: | 79CE9FA0965762F0B43CF6DC71BD9672D62B3892 |
| SHA256: | 428FEE64F7249D15B802857D45F3A2FEAA44BB3B870DD187D64CF7EBBA3DDE8C |
| SSDEEP: | 3:N8DSLN2:2OLo |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 892)
- iexplore.exe (PID: 2676)
- iexplore.exe (PID: 440)
- iexplore.exe (PID: 3548)
- iexplore.exe (PID: 3544)
- iexplore.exe (PID: 1368)
INFO
Checks supported languages
- iexplore.exe (PID: 3548)
- iexplore.exe (PID: 892)
- iexplore.exe (PID: 440)
- iexplore.exe (PID: 2676)
- iexplore.exe (PID: 3544)
- iexplore.exe (PID: 1368)
Reads the computer name
- iexplore.exe (PID: 3548)
- iexplore.exe (PID: 440)
- iexplore.exe (PID: 892)
- iexplore.exe (PID: 2676)
- iexplore.exe (PID: 1368)
- iexplore.exe (PID: 3544)
Application launched itself
- iexplore.exe (PID: 3548)
Reads settings of System Certificates
- iexplore.exe (PID: 3548)
- iexplore.exe (PID: 892)
- iexplore.exe (PID: 3544)
- iexplore.exe (PID: 440)
- iexplore.exe (PID: 2676)
- iexplore.exe (PID: 1368)
Creates files in the user directory
- iexplore.exe (PID: 892)
- iexplore.exe (PID: 3548)
- iexplore.exe (PID: 3544)
- iexplore.exe (PID: 440)
- iexplore.exe (PID: 1368)
Changes internet zones settings
- iexplore.exe (PID: 3548)
Checks Windows Trust Settings
- iexplore.exe (PID: 3548)
- iexplore.exe (PID: 892)
- iexplore.exe (PID: 3544)
- iexplore.exe (PID: 440)
- iexplore.exe (PID: 2676)
- iexplore.exe (PID: 1368)
Reads internet explorer settings
- iexplore.exe (PID: 892)
- iexplore.exe (PID: 440)
- iexplore.exe (PID: 3544)
- iexplore.exe (PID: 2676)
- iexplore.exe (PID: 1368)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
42
Monitored processes
6
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 440 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3548 CREDAT:529685 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 892 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3548 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1368 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3548 CREDAT:1250613 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2676 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3548 CREDAT:3806481 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3544 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3548 CREDAT:1185043 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3548 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://www.pornhub.com" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
51 682
Read events
51 208
Write events
474
Delete events
0
Modification events
| (PID) Process: | (3548) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3548) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3548) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30943555 | |||
| (PID) Process: | (3548) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3548) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30943555 | |||
| (PID) Process: | (3548) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3548) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3548) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3548) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3548) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
54
Text files
455
Unknown types
28
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 892 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:CAACCE9AA5F733EE2AE74750F3F7D226 | SHA256:DA049BD09DEE3B2A410BF4E56DAB35CCCB2ADC4BE5EFF81E3A185B34C52E0005 | |||
| 892 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_B514E3306E9B5CC22C1D3DB90570477A | der | |
MD5:AF8F8C2F8E1D46717188FA3B78285963 | SHA256:3B54150D46A34D42788B9E38AF39C9FAB7D2186B18FD3BA2B6F3D928C68FC4CC | |||
| 892 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\9ESR5212.htm | html | |
MD5:799F618D5C9012B2F2069889D9463996 | SHA256:C7ACECDF1BC637AFF8319496E3713A2AF0C0482F24919038CFE5C96B539FE341 | |||
| 892 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\fn-polyfills[1].js | text | |
MD5:3CF955967ACBCED0F31A66168603BA9F | SHA256:3F00F8251B7426FDFAEDA4C603CE596EE421A8DC645CE49D686D50F1F38504B8 | |||
| 892 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\ph-functions[1].js | text | |
MD5:C7F94C12CE20B663EEA39B5DEA7B5F42 | SHA256:80000C00A2B74C6866E04C5A4D6821F237E85DE480259FBB7E388F35ED0961B4 | |||
| 892 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\50CD3D75D026C82E2E718570BD6F44D0_E353C9EBFD1BAB837760A84408CED896 | der | |
MD5:2332F744B22D1C11EE936DF49154E31E | SHA256:ACF493E8E788FB5A472C805981009324E189DBFEB639F204330670D1FAE8A50D | |||
| 3548 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:93C468C22F976B61EBFE4D1F95DEAE2D | SHA256:8A4B9884D39F40CA5E73E875D53A635210369BF68707221755C94D18B30B9F89 | |||
| 892 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B126BF247C927A243E186240F06A7849 | der | |
MD5:EA8D5825BDBC99C5D7217BA6C29392BA | SHA256:907C1A6B5AF72322C8495477AA87FAD630B5C09B871543A7C526DE941A5EEBAA | |||
| 892 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_B514E3306E9B5CC22C1D3DB90570477A | binary | |
MD5:86705F62845028B0C5E4D8DF782A54F7 | SHA256:0BE251013CB7329C1BD3A480F5E49404D03295FB8E0BCFA45EED319FC3BD8206 | |||
| 892 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\generated-header[1].css | text | |
MD5:97CF47829B2C7195CB09DB39CB1D0D5C | SHA256:AE7AA56FC1196771735EAA056A951E514FCD3566553B8A32092D25DA63D791A0 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
40
TCP/UDP connections
279
DNS requests
53
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
892 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQrHR6YzPN2BNbByL0VoiTIBBMAOAQUCrwIKReMpTlteg7OM8cus%2B37w3oCEAj38N9xI%2FjwgeSye4NQBA4%3D | US | der | 313 b | whitelisted |
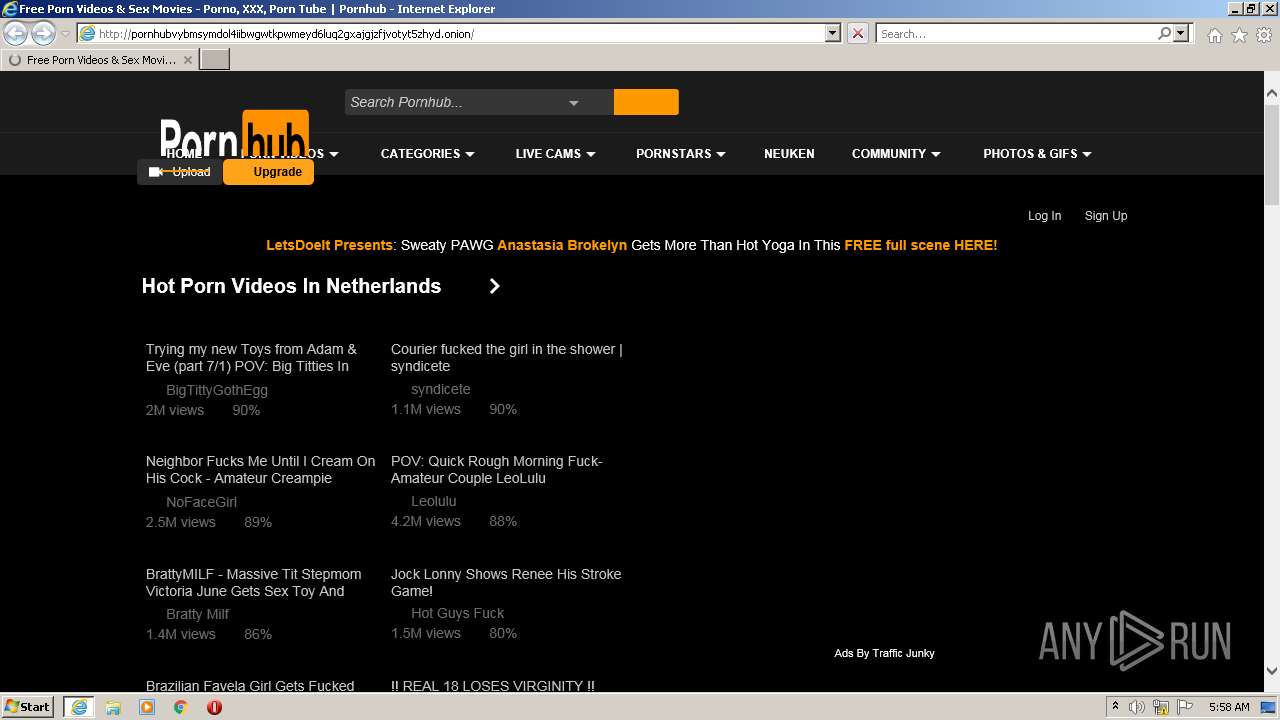
892 | iexplore.exe | GET | 200 | 10.233.64.243:80 | http://pornhubvybmsymdol4iibwgwtkpwmeyd6luq2gxajgjzfjvotyt5zhyd.onion/front/menu_livesex?segment=straight&token=MTY0NTY4MjMxMJR2YOX_EMOApHsDaJaPvD5sBESHAKhmZW62iXPlVZzCve5nwKmObA9_ieVYT1QE-VbsRVz5J9uO4KlAhLpRK-A.? | unknown | compressed | 2.71 Kb | unknown |
892 | iexplore.exe | GET | 200 | 88.221.255.147:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?c3386e041cbb23ba | unknown | compressed | 4.70 Kb | whitelisted |
892 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/DigiCertGlobalRootCA.crl | US | der | 631 b | whitelisted |
3548 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
892 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAonX%2BcE1u7LI9XNW0saTgQ%3D | US | der | 471 b | whitelisted |
892 | iexplore.exe | GET | 200 | 10.233.64.243:80 | http://pornhubvybmsymdol4iibwgwtkpwmeyd6luq2gxajgjzfjvotyt5zhyd.onion/ | unknown | compressed | 117 Kb | unknown |
892 | iexplore.exe | GET | 200 | 88.221.255.147:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?6a5cd14f4dcc91df | unknown | compressed | 4.70 Kb | whitelisted |
892 | iexplore.exe | GET | 200 | 172.217.168.195:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEFh7xVzrbXwYEgAAAAADcI8%3D | US | der | 471 b | whitelisted |
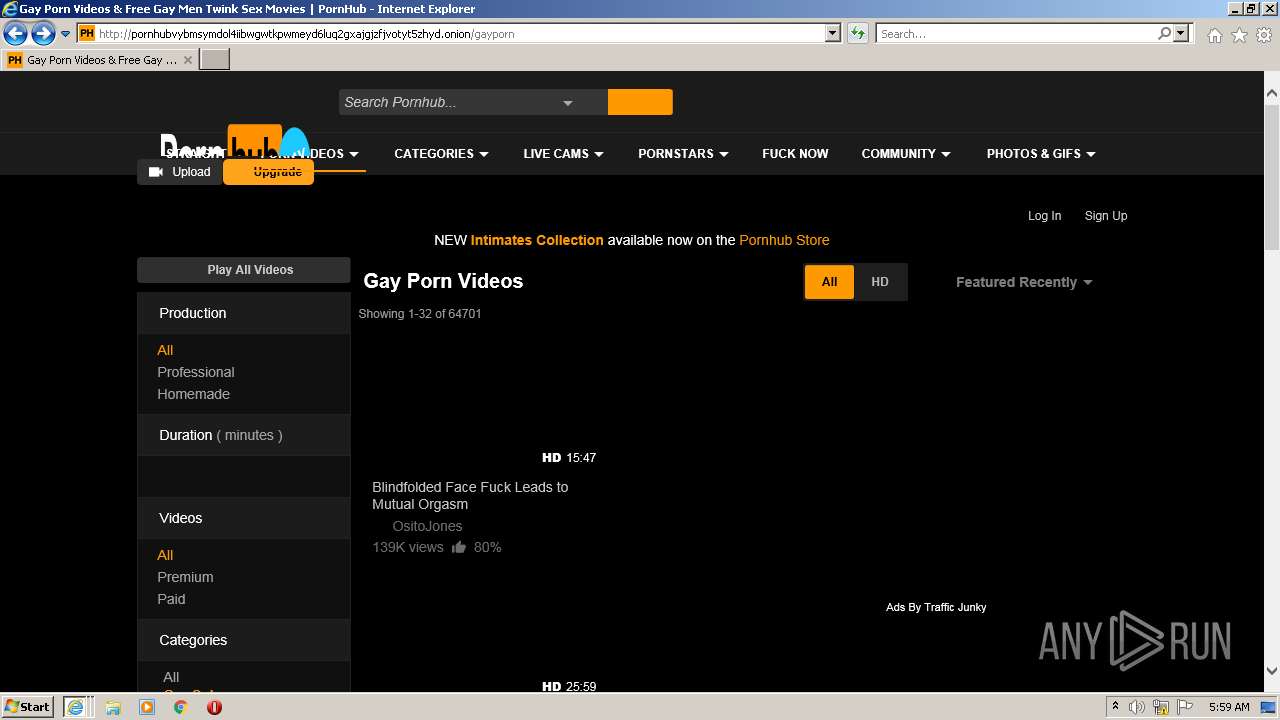
892 | iexplore.exe | GET | 200 | 10.233.64.243:80 | http://pornhubvybmsymdol4iibwgwtkpwmeyd6luq2gxajgjzfjvotyt5zhyd.onion/gayporn | unknown | compressed | 105 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3548 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
892 | iexplore.exe | 10.233.64.243:80 | pornhubvybmsymdol4iibwgwtkpwmeyd6luq2gxajgjzfjvotyt5zhyd.onion | — | — | unknown |
892 | iexplore.exe | 205.185.208.142:443 | di.phncdn.com | Highwinds Network Group, Inc. | US | suspicious |
892 | iexplore.exe | 205.185.208.79:443 | static.trafficjunky.com | Highwinds Network Group, Inc. | US | unknown |
892 | iexplore.exe | 152.195.34.118:443 | ci.phncdn.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
892 | iexplore.exe | 216.18.168.30:443 | hubt.pornhub.com | Reflected Networks, Inc. | US | unknown |
892 | iexplore.exe | 64.210.135.113:443 | ss.phncdn.com | Swiftwill, Inc. | US | unknown |
892 | iexplore.exe | 66.254.114.156:443 | cdn1-smallimg.phncdn.com | Reflected Networks, Inc. | US | suspicious |
892 | iexplore.exe | 142.251.39.110:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
892 | iexplore.exe | 172.217.168.195:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.pornhub.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |
pornhubvybmsymdol4iibwgwtkpwmeyd6luq2gxajgjzfjvotyt5zhyd.onion |
| unknown |
di.phncdn.com |
| whitelisted |
static.trafficjunky.com |
| whitelisted |
ci.phncdn.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potential Corporate Privacy Violation | ET POLICY DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
— | — | Potential Corporate Privacy Violation | AV POLICY DNS Query for .onion Domain Via TOR - Not Google |
— | — | Potential Corporate Privacy Violation | ET POLICY DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
— | — | Potential Corporate Privacy Violation | AV POLICY DNS Query for .onion Domain Via TOR - Not Google |