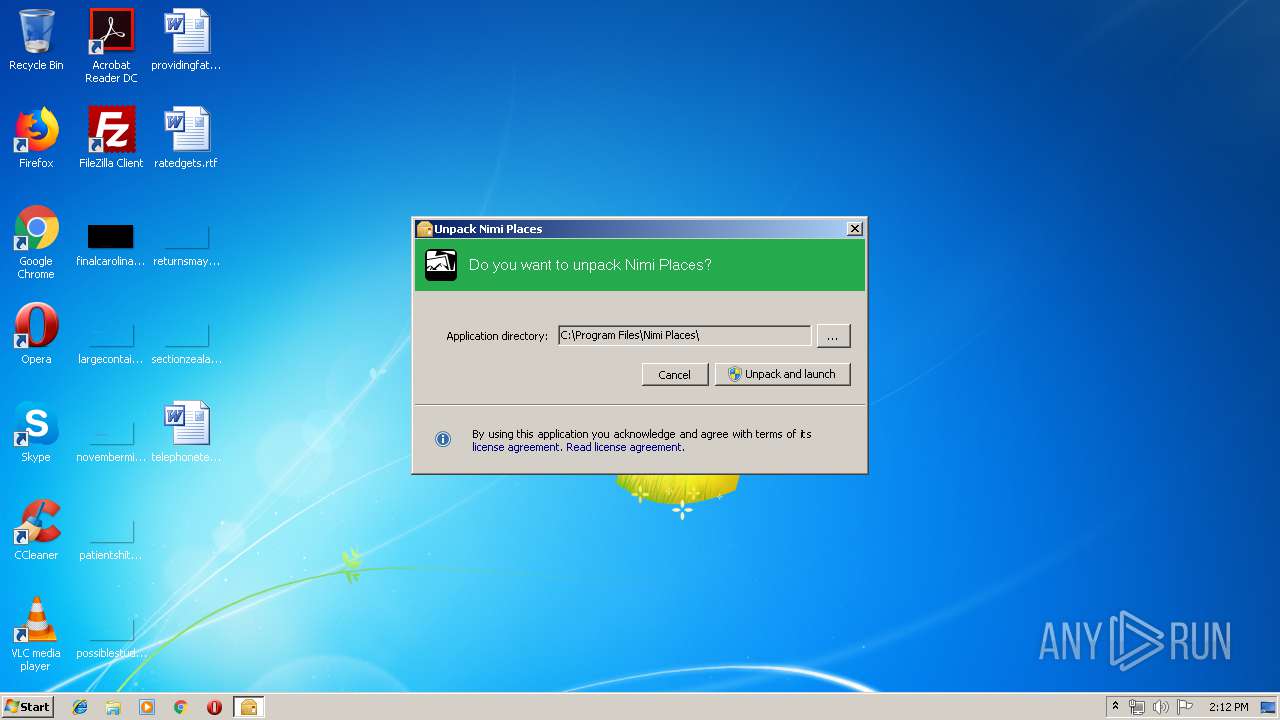
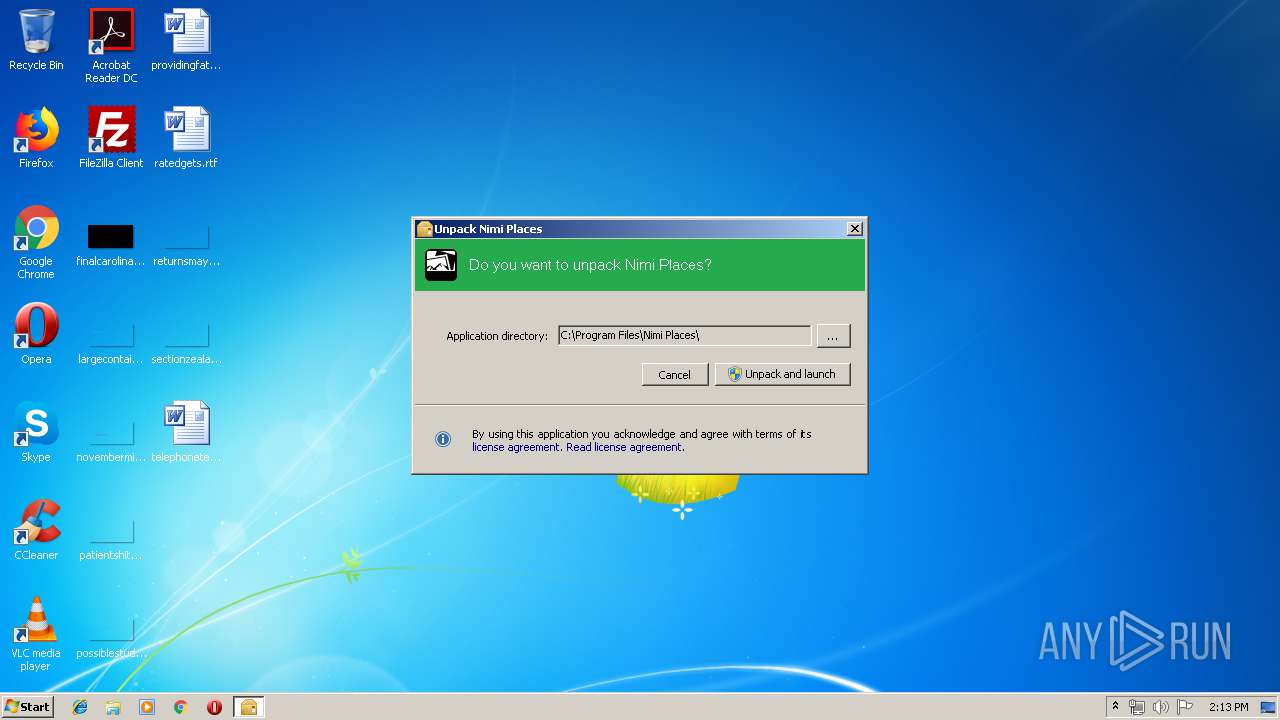
| File name: | Extract Nimi Places (portable).exe |
| Full analysis: | https://app.any.run/tasks/650eb533-d76d-489b-9a9c-44c3502b133b |
| Verdict: | Suspicious activity |
| Analysis date: | April 30, 2019, 13:12:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | C16F6510206198A8F14BFFFDFE99E184 |
| SHA1: | 2A9D54A55C2138463E935BB447F1304B326621A5 |
| SHA256: | 42801BD46DA21AE8B416693EB1569F12BA3EFEBC1EE6352266DB28C1DF2316E9 |
| SSDEEP: | 6144:8AYRoAt1OYLsrfgkfnxyCSNFyBd0QaZt1RfHuP2PvVH7lljc57rvGTcPXLI9YiU:XY/yYgsInACS3yr0QaPzuP2n9l1ivGTa |
MALICIOUS
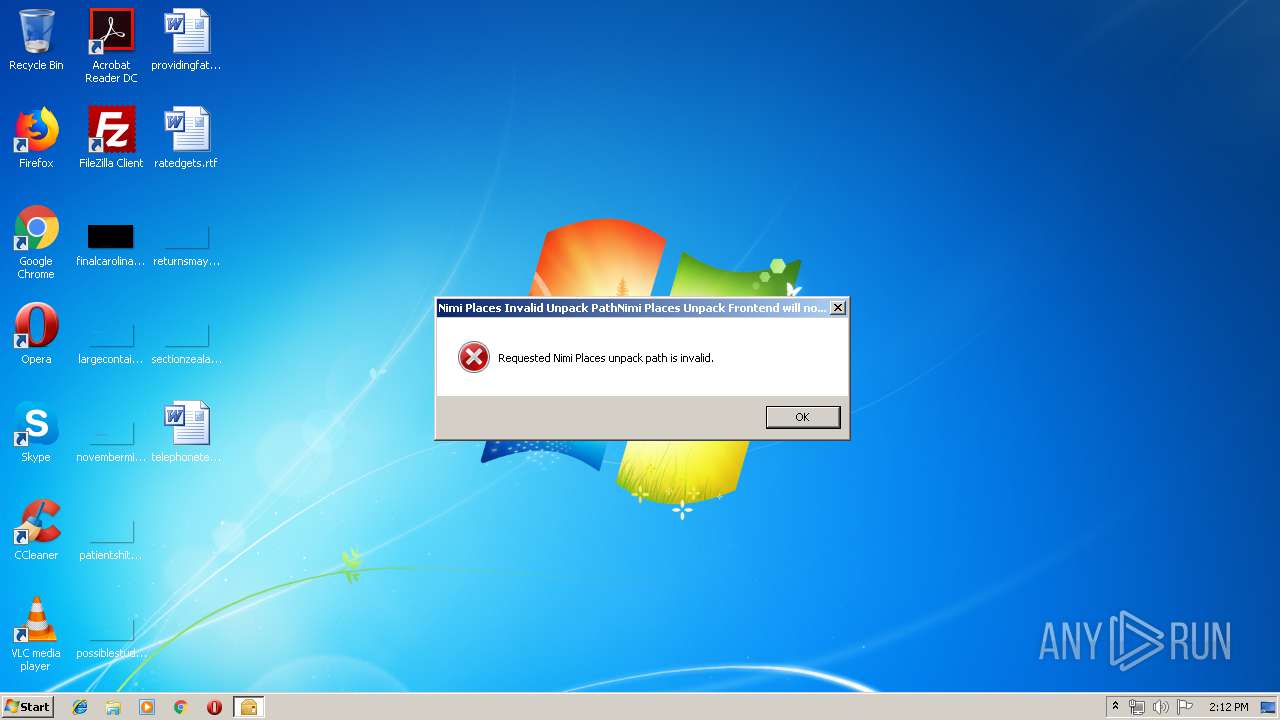
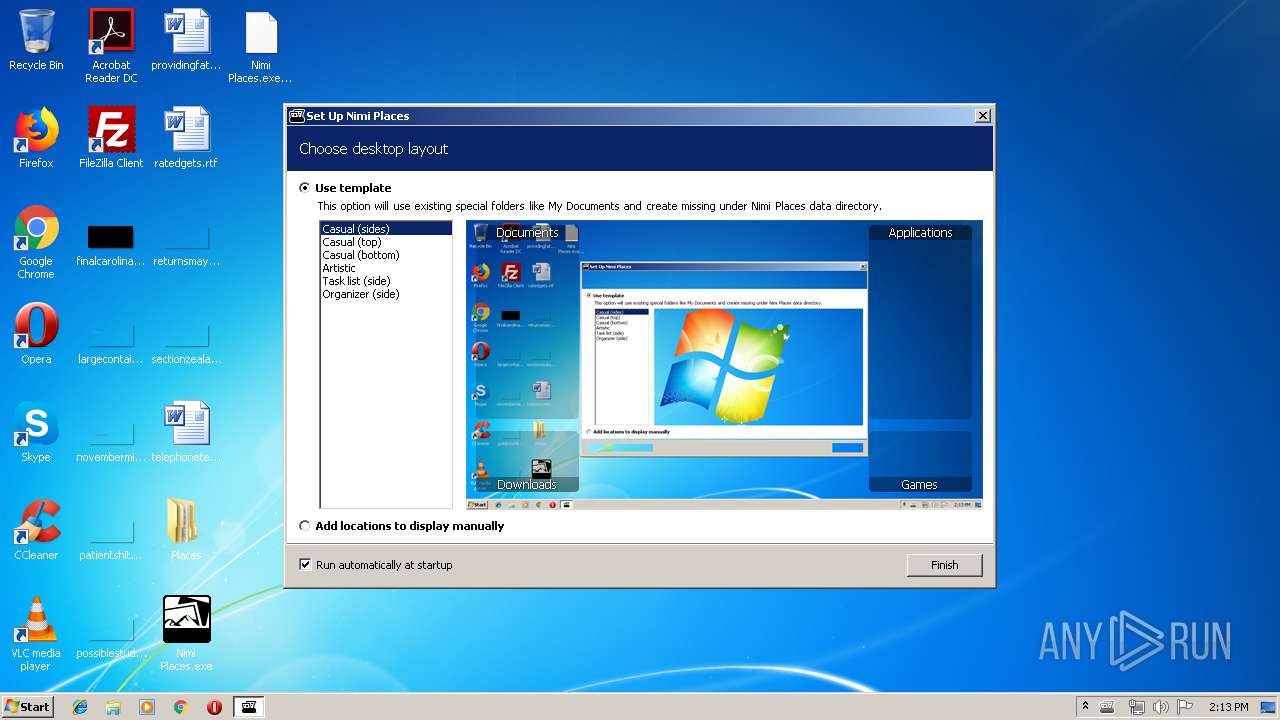
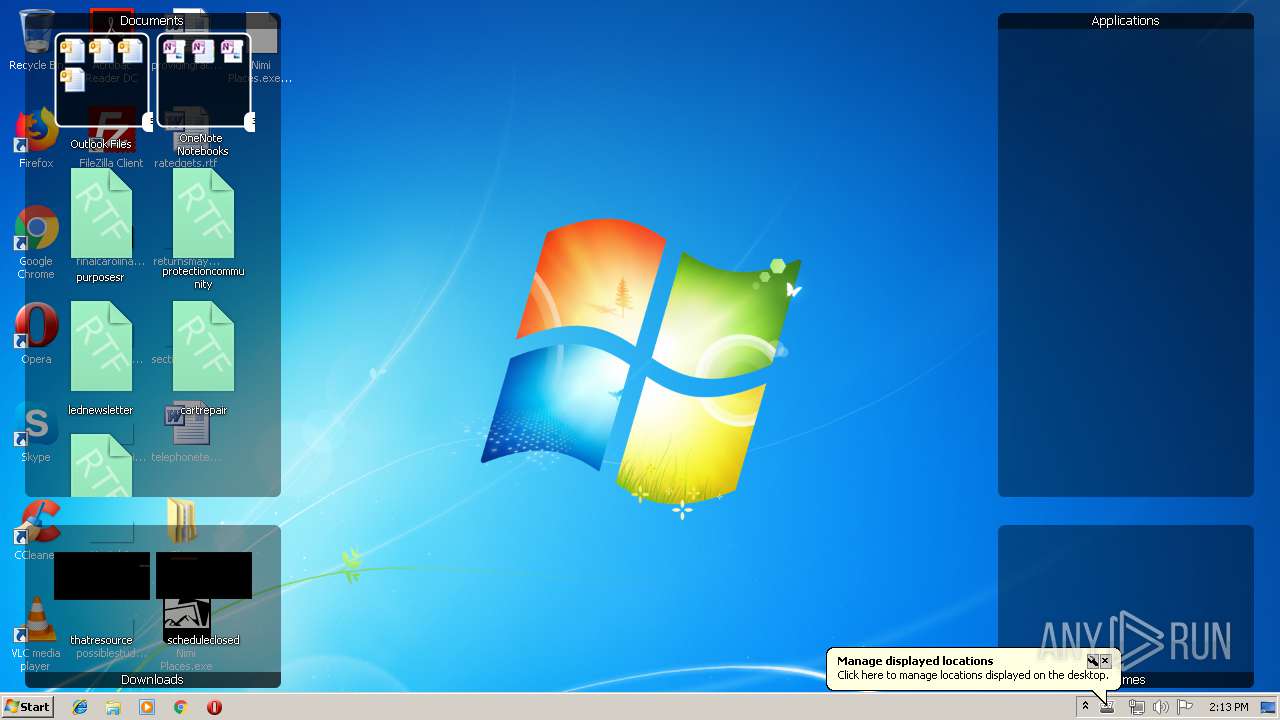
Application was dropped or rewritten from another process
- Nimi Places.exe (PID: 2888)
Changes the autorun value in the registry
- Nimi Places.exe (PID: 2888)
SUSPICIOUS
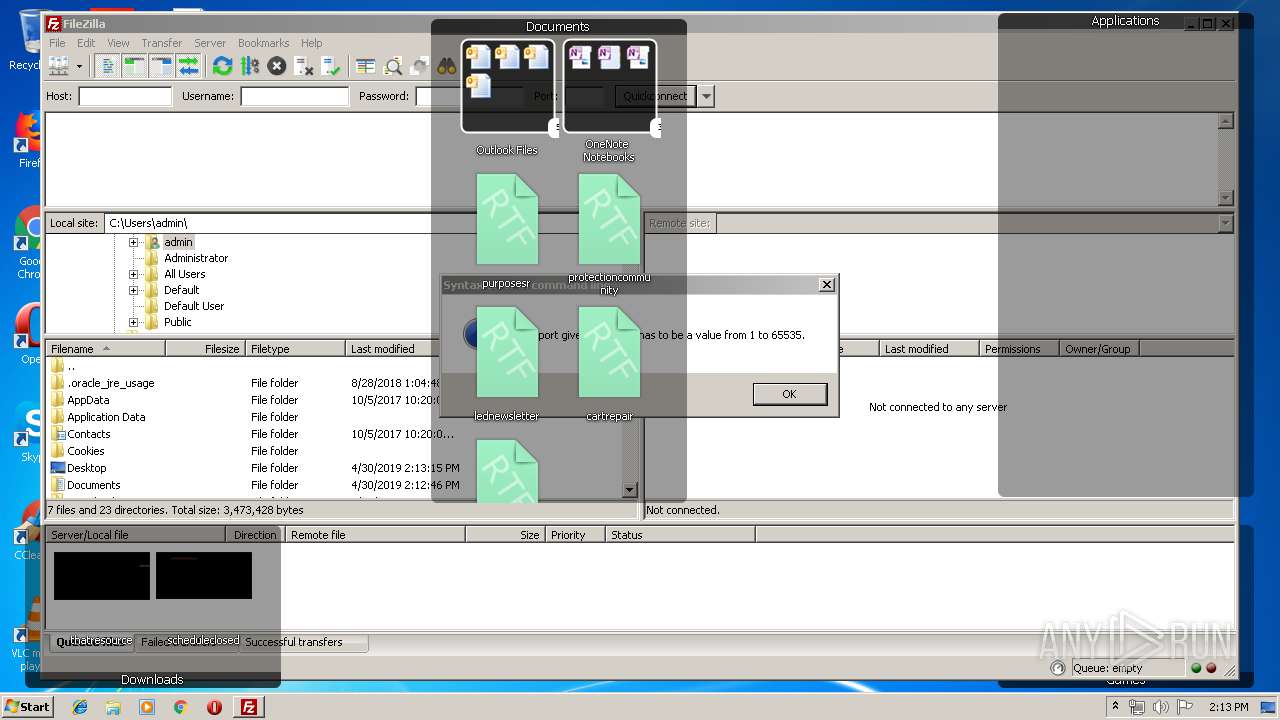
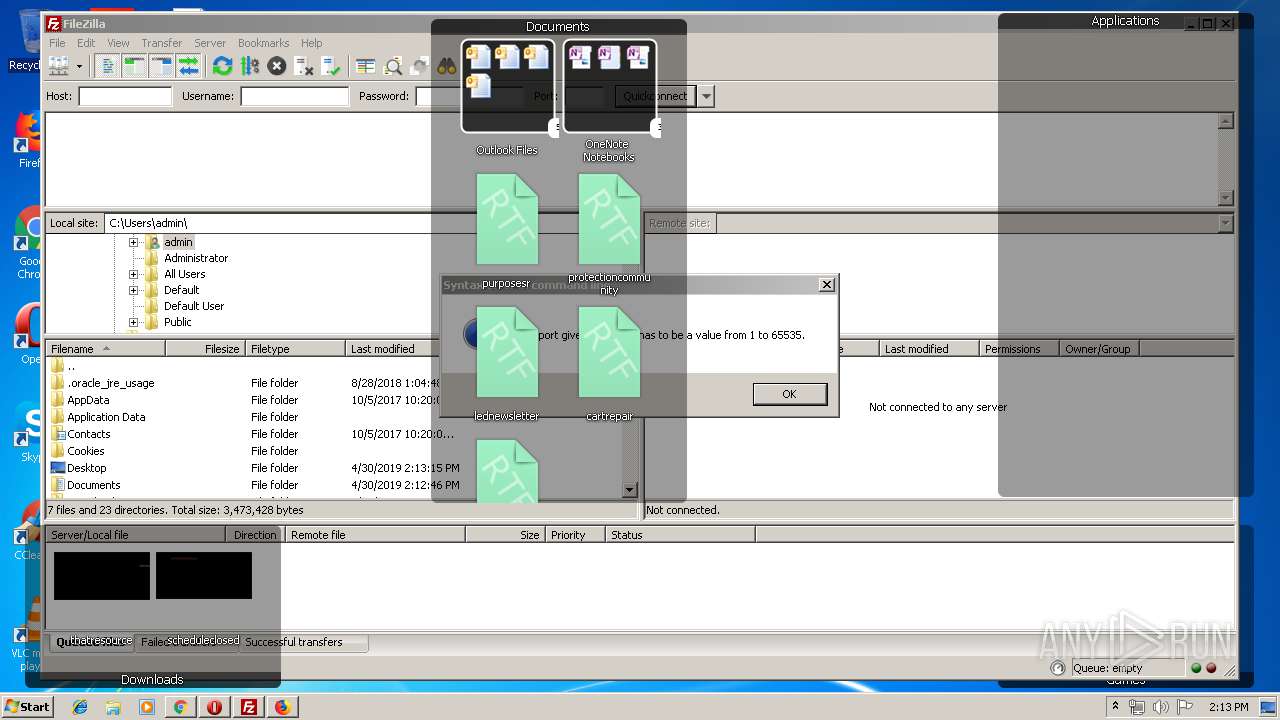
Creates files in the user directory
- filezilla.exe (PID: 2036)
Creates files in the program directory
- firefox.exe (PID: 3956)
Creates files in the Windows directory
- expand.exe (PID: 1700)
Executable content was dropped or overwritten
- expand.exe (PID: 1700)
Uses ICACLS.EXE to modify access control list
- Extract Nimi Places (portable).exe (PID: 1740)
Application launched itself
- Extract Nimi Places (portable).exe (PID: 3796)
INFO
Reads settings of System Certificates
- chrome.exe (PID: 1000)
Application launched itself
- firefox.exe (PID: 3956)
- chrome.exe (PID: 1000)
Creates files in the user directory
- firefox.exe (PID: 3956)
- opera.exe (PID: 3484)
Reads CPU info
- firefox.exe (PID: 3956)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (56.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21.3) |
| .scr | | | Windows screen saver (10.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:04:28 23:56:40+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 345600 |
| InitializedDataSize: | 18432 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x563fe |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 18.7.17.0 |
| ProductVersionNumber: | 18.7.17.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
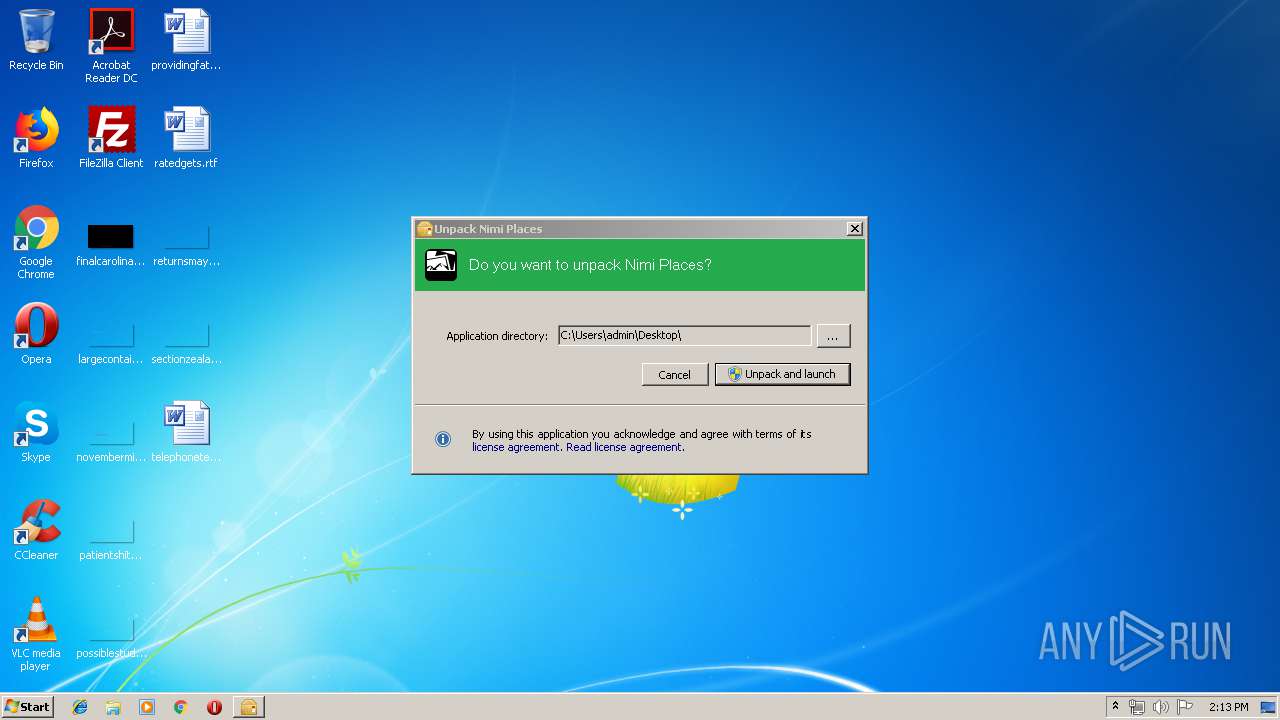
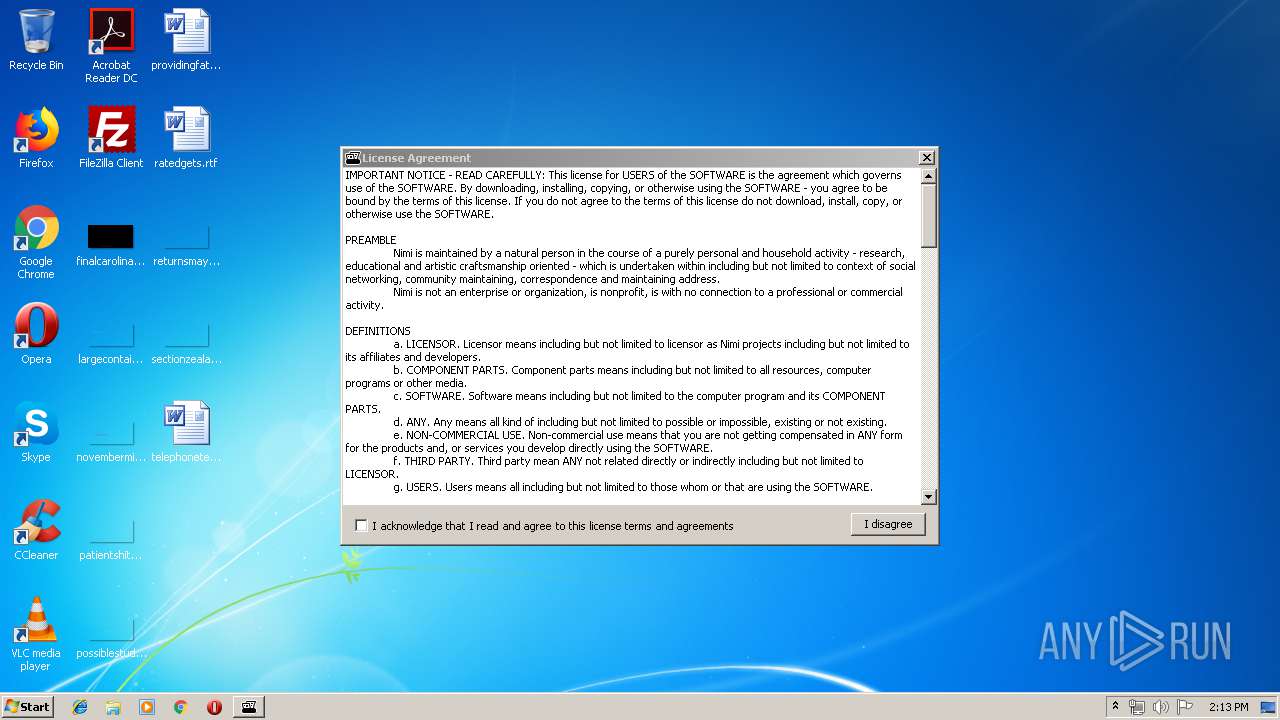
| Comments: | Nimi Places 20190428 distribution package with unpack frontend. |
| CompanyName: | Nimi projects |
| FileDescription: | Package for Nimi Places 20190428 |
| FileVersion: | 18.7.17.0 |
| InternalName: | nimn_Nimi Places.exe |
| LegalCopyright: | |
| OriginalFileName: | nimn_Nimi Places.exe |
| ProductName: | Nimi Package project |
| ProductVersion: | 18.7.17.0 |
| AssemblyVersion: | 18.7.17.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 28-Apr-2019 21:56:40 |
| Comments: | Nimi Places 20190428 distribution package with unpack frontend. |
| CompanyName: | Nimi projects |
| FileDescription: | Package for Nimi Places 20190428 |
| FileVersion: | 18.7.17.0 |
| InternalName: | nimn_Nimi Places.exe |
| LegalCopyright: | - |
| OriginalFilename: | nimn_Nimi Places.exe |
| ProductName: | Nimi Package project |
| ProductVersion: | 18.7.17.0 |
| Assembly Version: | 18.7.17.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 28-Apr-2019 21:56:40 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x00054404 | 0x00054600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.848 |
.rsrc | 0x00058000 | 0x000044A0 | 0x00004600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.85289 |
.reloc | 0x0005E000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.0815394 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.2458 | 1358 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 4.29139 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 4.4533 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 6.63742 | 872 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.5515 | 48 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
59
Monitored processes
22
Malicious processes
0
Suspicious processes
3
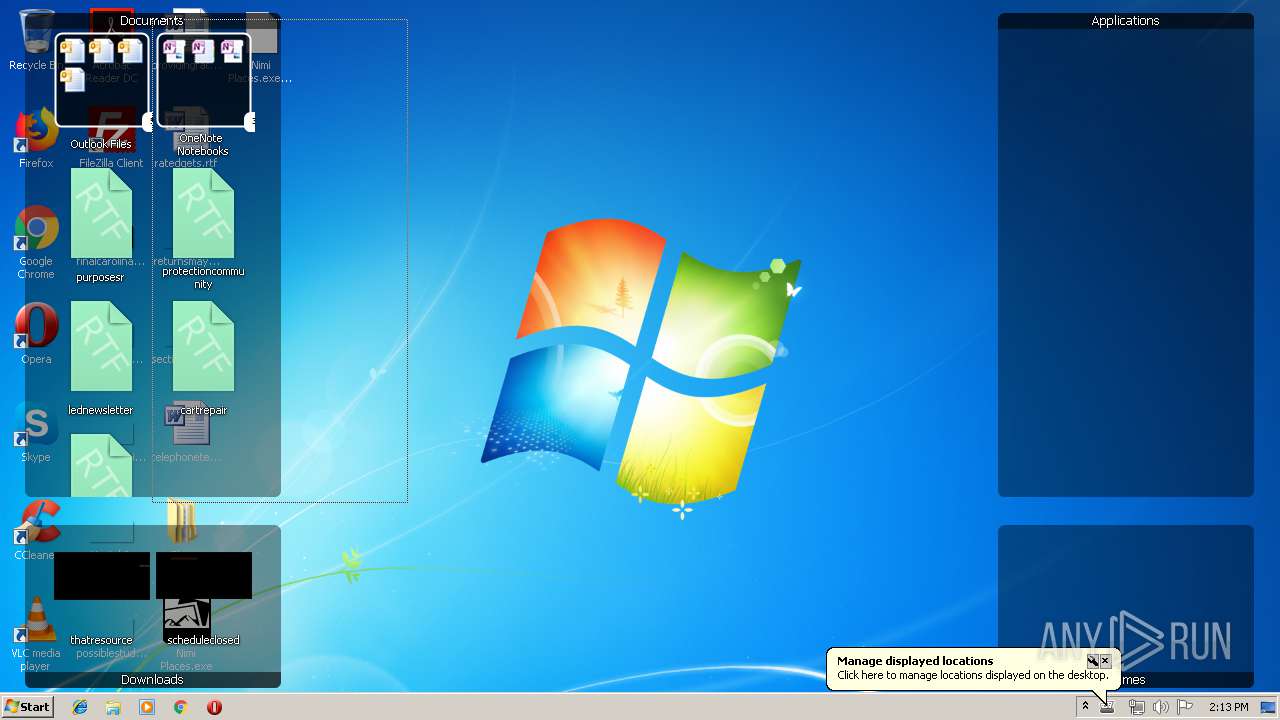
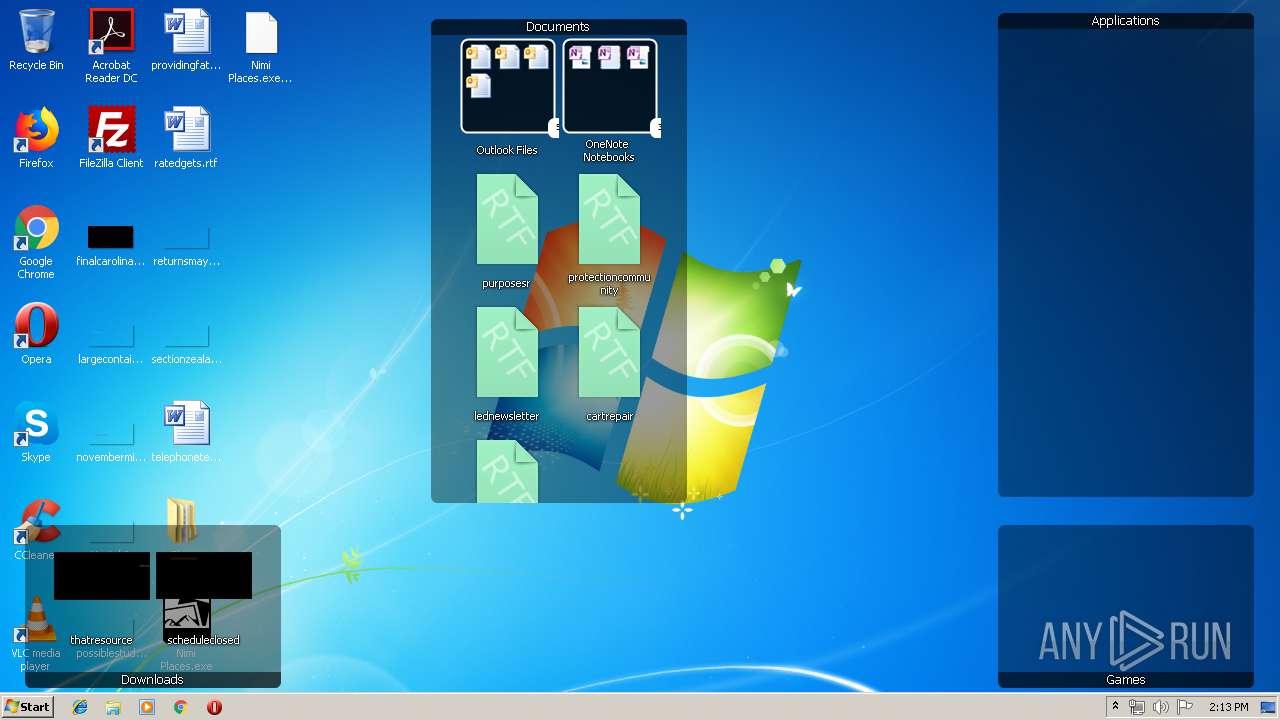
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 288 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=964,11897266867201573771,820355393509810569,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=3704621313744917520 --mojo-platform-channel-handle=952 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 304 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3956.0.391224796\1677393794" -parentBuildID 20190225143501 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - "C:\Users\admin\AppData\LocalLow\Mozilla\Temp-{ce348e4c-7d33-445e-89f9-60108c51bcaf}" 3956 "\\.\pipe\gecko-crash-server-pipe.3956" 1120 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 65.0.2 Modules
| |||||||||||||||
| 1000 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1668 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,11897266867201573771,820355393509810569,131072 --enable-features=PasswordImport --service-pipe-token=9087801091592781096 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9087801091592781096 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2216 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1692 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,11897266867201573771,820355393509810569,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2276022974161757305 --mojo-platform-channel-handle=2500 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1700 | "expand" "C:\Users\admin\Desktop\Nimi Places.cab" -F:* "C:\Users\admin\Desktop" | C:\Windows\system32\expand.exe | Extract Nimi Places (portable).exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: LZ Expansion Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1740 | "C:\Users\admin\AppData\Local\Temp\Extract Nimi Places (portable).exe" "C:\Program Files\Nimi Places\Nimi Places.exe" 1 | C:\Users\admin\AppData\Local\Temp\Extract Nimi Places (portable).exe | Extract Nimi Places (portable).exe | ||||||||||||
User: admin Company: Nimi projects Integrity Level: HIGH Description: Package for Nimi Places 20190428 Exit code: 0 Version: 18.7.17.0 Modules
| |||||||||||||||
| 1848 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,11897266867201573771,820355393509810569,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=10494048938453472951 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10494048938453472951 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3096 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
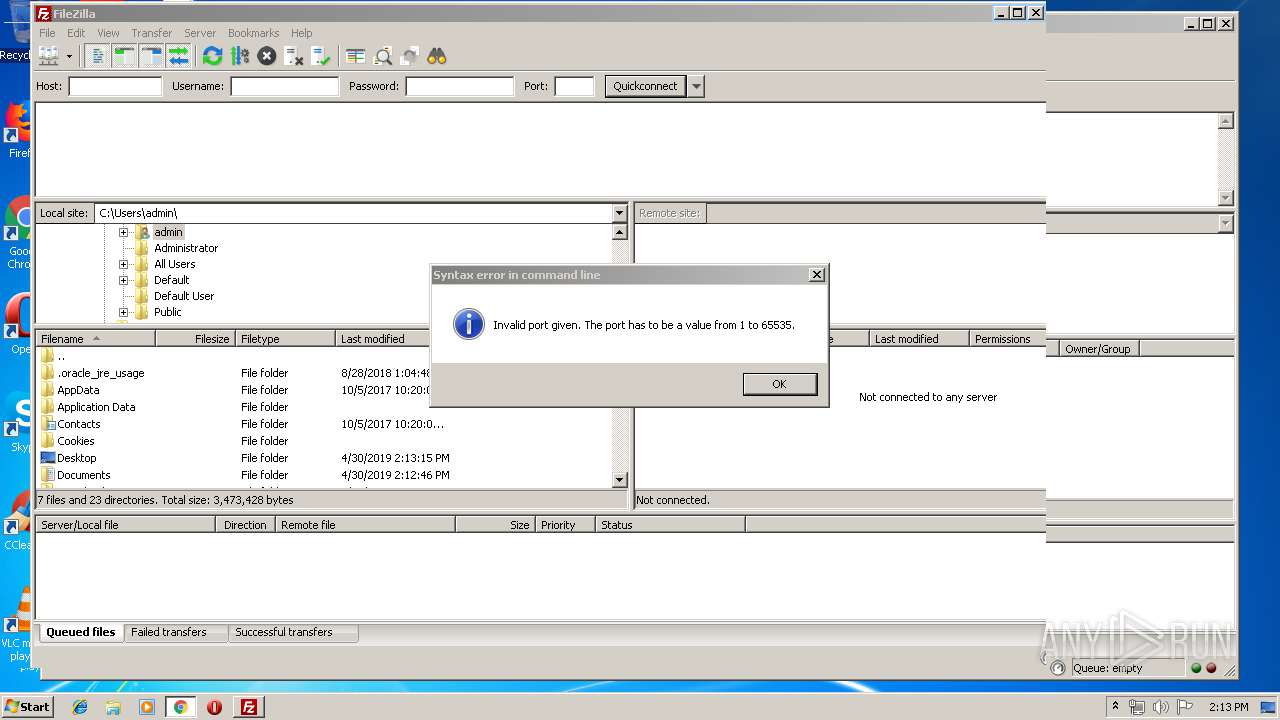
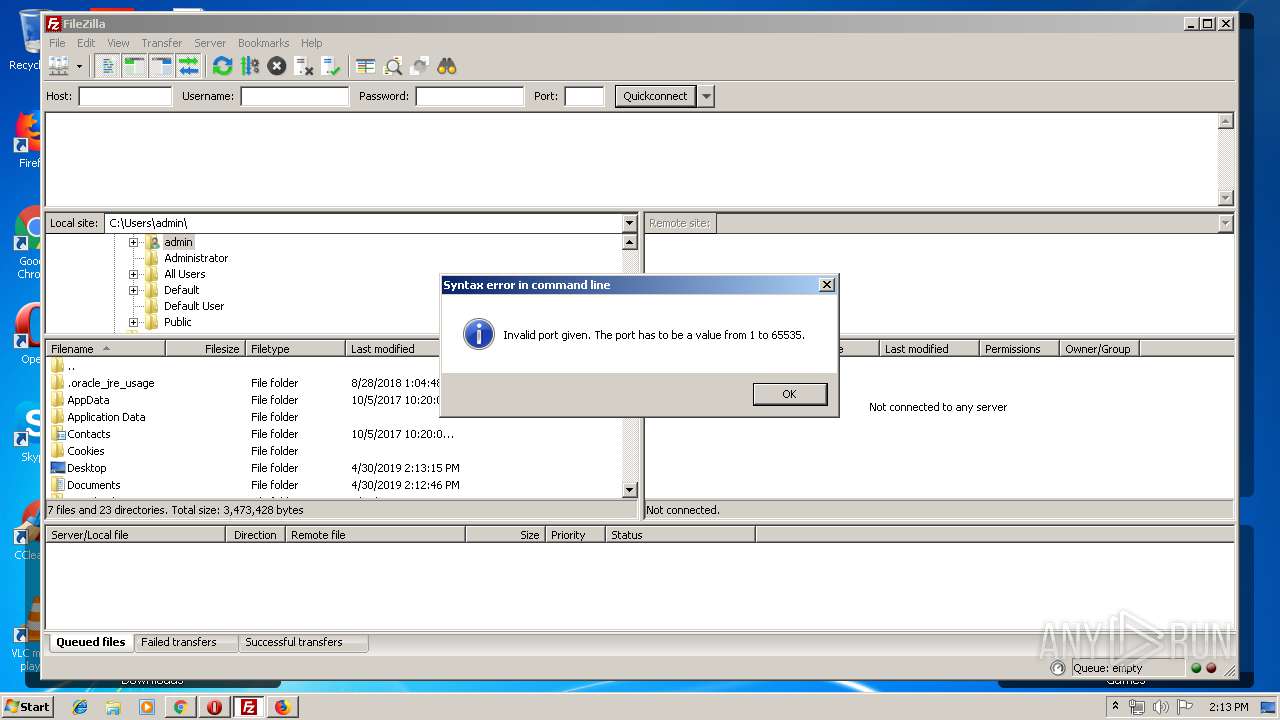
| 2036 | "C:\Program Files\FileZilla FTP Client\filezilla.exe" C:\Users\Public\Desktop\Firefox.lnk | C:\Program Files\FileZilla FTP Client\filezilla.exe | — | explorer.exe | |||||||||||
User: admin Company: FileZilla Project Integrity Level: MEDIUM Description: FileZilla FTP Client Exit code: 0 Version: 3, 36, 0, 0 Modules
| |||||||||||||||
| 2308 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3956.20.1663825224\111082226" -childID 3 -isForBrowser -prefsHandle 3408 -prefMapHandle 3412 -prefsLen 5824 -prefMapSize 180950 -schedulerPrefs 0001,2 -parentBuildID 20190225143501 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3956 "\\.\pipe\gecko-crash-server-pipe.3956" 3396 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 65.0.2 Modules
| |||||||||||||||
Total events
1 554
Read events
1 425
Write events
126
Delete events
3
Modification events
| (PID) Process: | (3796) Extract Nimi Places (portable).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3796) Extract Nimi Places (portable).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1740) Extract Nimi Places (portable).exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
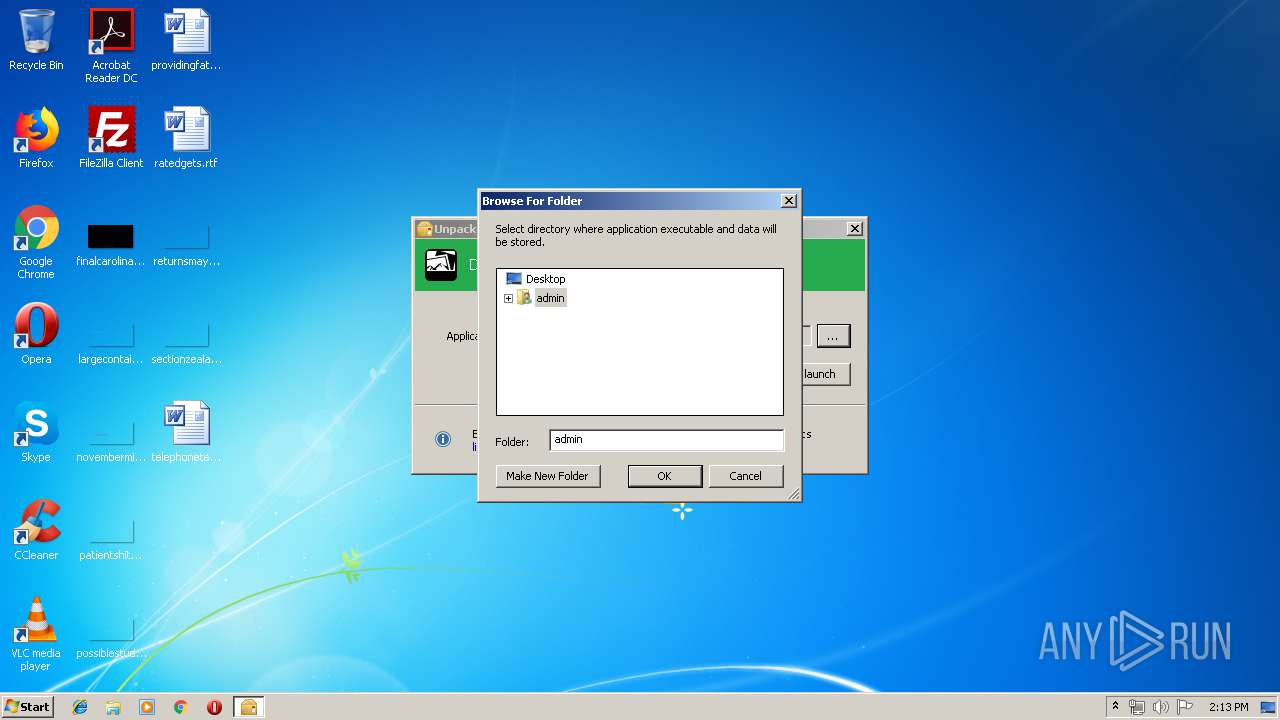
| (PID) Process: | (1740) Extract Nimi Places (portable).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | Browse For Folder Width |
Value: 318 | |||
| (PID) Process: | (1740) Extract Nimi Places (portable).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | Browse For Folder Height |
Value: 288 | |||
| (PID) Process: | (1740) Extract Nimi Places (portable).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1740) Extract Nimi Places (portable).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2888) Nimi Places.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Nimi Places_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2888) Nimi Places.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Nimi Places_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2888) Nimi Places.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Nimi Places_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
Executable files
1
Suspicious files
79
Text files
52
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1740 | Extract Nimi Places (portable).exe | C:\Users\admin\Desktop\Nimi Places.cab | — | |
MD5:— | SHA256:— | |||
| 1700 | expand.exe | C:\Users\admin\Desktop\$dpx$.tmp\0bd440550f0bf14291cc1fa3668e7d6b.tmp | — | |
MD5:— | SHA256:— | |||
| 1700 | expand.exe | C:\Users\admin\Desktop\$dpx$.tmp\9e75407417a62641a7c9e304377b0d68.tmp | — | |
MD5:— | SHA256:— | |||
| 1700 | expand.exe | C:\Users\admin\Desktop\$dpx$.tmp\1d994e7432a3ca40aba247b82fdb6ecf.tmp | — | |
MD5:— | SHA256:— | |||
| 1700 | expand.exe | C:\Users\admin\Desktop\$dpx$.tmp\744b44cb5b430141bdb33864d073888e.tmp | — | |
MD5:— | SHA256:— | |||
| 1700 | expand.exe | C:\Users\admin\Desktop\$dpx$.tmp\ed96a9a37b7ca84e98a479fef4890f10.tmp | — | |
MD5:— | SHA256:— | |||
| 1700 | expand.exe | C:\Users\admin\Desktop\$dpx$.tmp\4f4663f170e60e40876297d725e26133.tmp | — | |
MD5:— | SHA256:— | |||
| 1700 | expand.exe | C:\Users\admin\Desktop\$dpx$.tmp\b893dbb963617242935589505094efa6.tmp | — | |
MD5:— | SHA256:— | |||
| 1700 | expand.exe | C:\Users\admin\Desktop\$dpx$.tmp\d2e2e29147a0f246a57acb1db6e696fc.tmp | — | |
MD5:— | SHA256:— | |||
| 1700 | expand.exe | C:\Users\admin\Desktop\$dpx$.tmp\9a75f169b83c034aa28eaeedb7b262d5.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
28
DNS requests
60
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3484 | opera.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEAOXQPQlVpLtFek%2BmcpabOk%3D | US | der | 471 b | whitelisted |
3956 | firefox.exe | GET | 200 | 2.16.106.152:80 | http://detectportal.firefox.com/success.txt | unknown | text | 8 b | whitelisted |
3956 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3956 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3956 | firefox.exe | POST | 200 | 172.217.16.131:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
3484 | opera.exe | GET | 200 | 66.225.197.197:80 | http://crl4.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 543 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1000 | chrome.exe | 172.217.21.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1000 | chrome.exe | 172.217.18.99:443 | www.google.com.ua | Google Inc. | US | whitelisted |
1000 | chrome.exe | 172.217.18.14:443 | clients1.google.com | Google Inc. | US | whitelisted |
1000 | chrome.exe | 172.217.23.163:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3484 | opera.exe | 82.145.215.40:443 | certs.opera.com | Opera Software AS | — | whitelisted |
3484 | opera.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3484 | opera.exe | 66.225.197.197:80 | crl4.digicert.com | CacheNetworks, Inc. | US | whitelisted |
1000 | chrome.exe | 172.217.16.163:443 | www.gstatic.com | Google Inc. | US | whitelisted |
1000 | chrome.exe | 216.58.205.238:443 | apis.google.com | Google Inc. | US | whitelisted |
3956 | firefox.exe | 35.164.82.230:443 | aus5.mozilla.org | Amazon.com, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.com.ua |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
clients1.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
certs.opera.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl4.digicert.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |