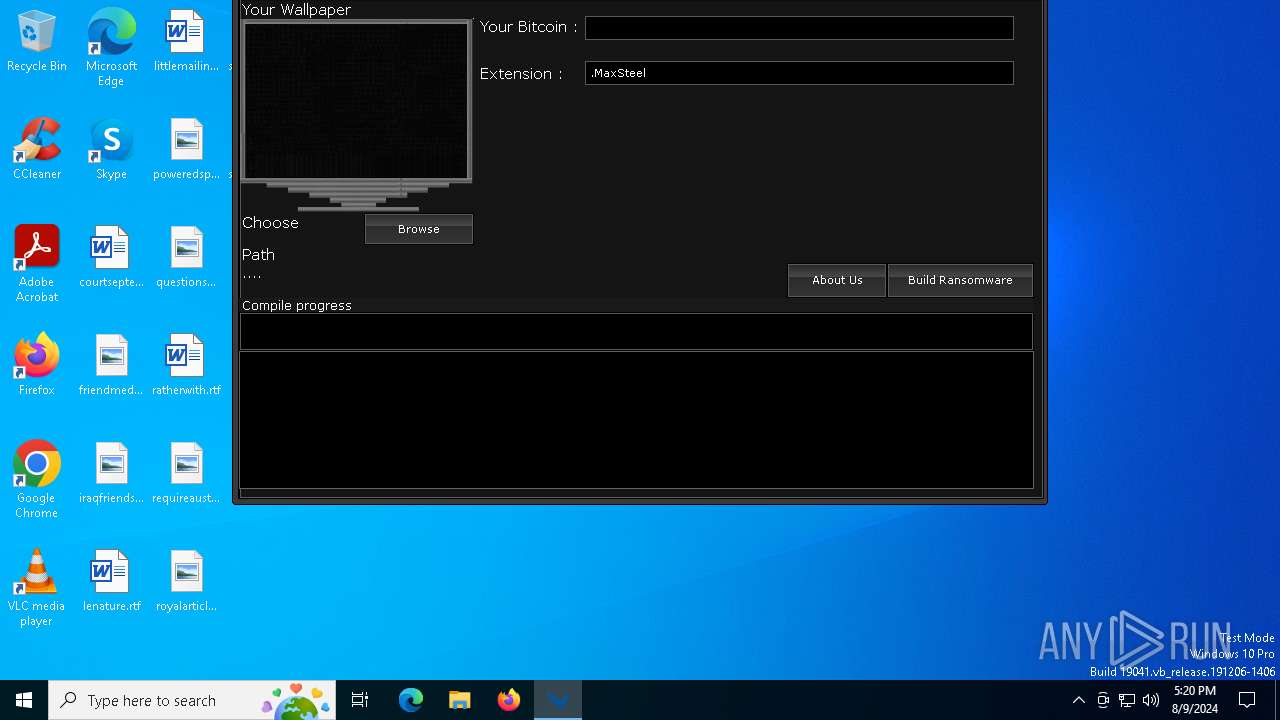
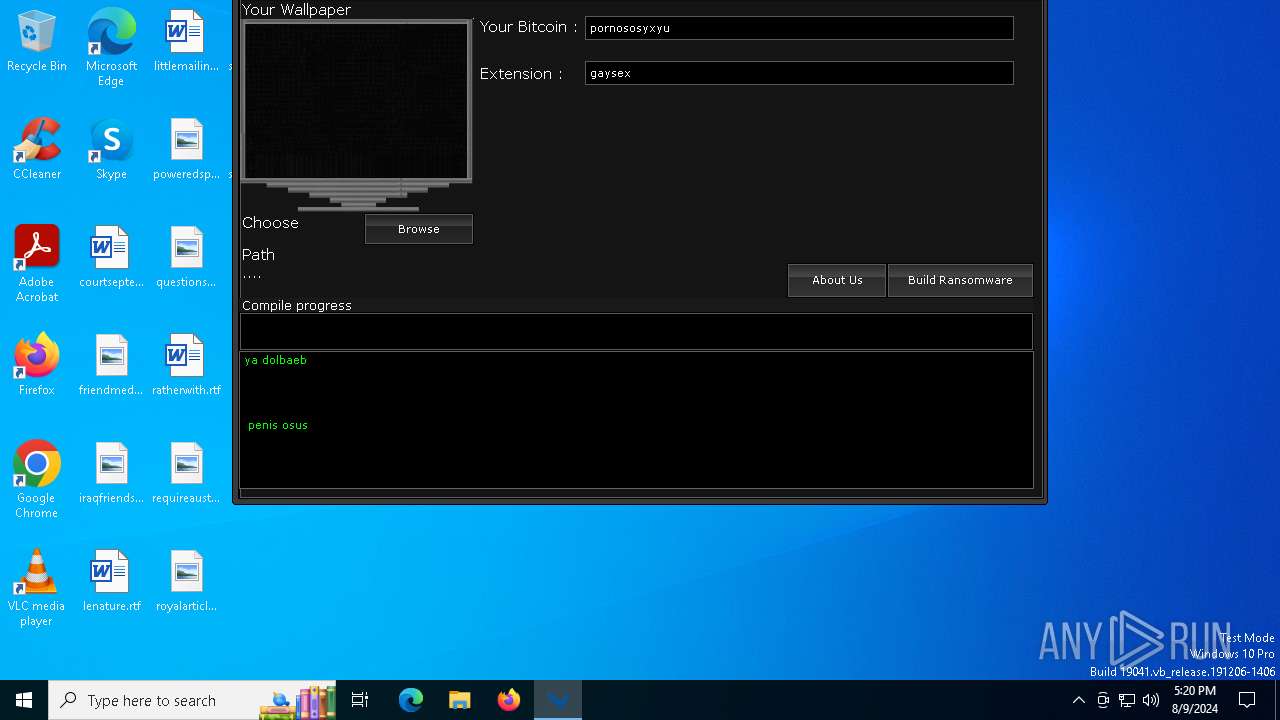
| File name: | SaherBlueEagleRansomwareBuilder.exe |
| Full analysis: | https://app.any.run/tasks/5321b315-dc8a-49a1-9773-b2090cfcc2ee |
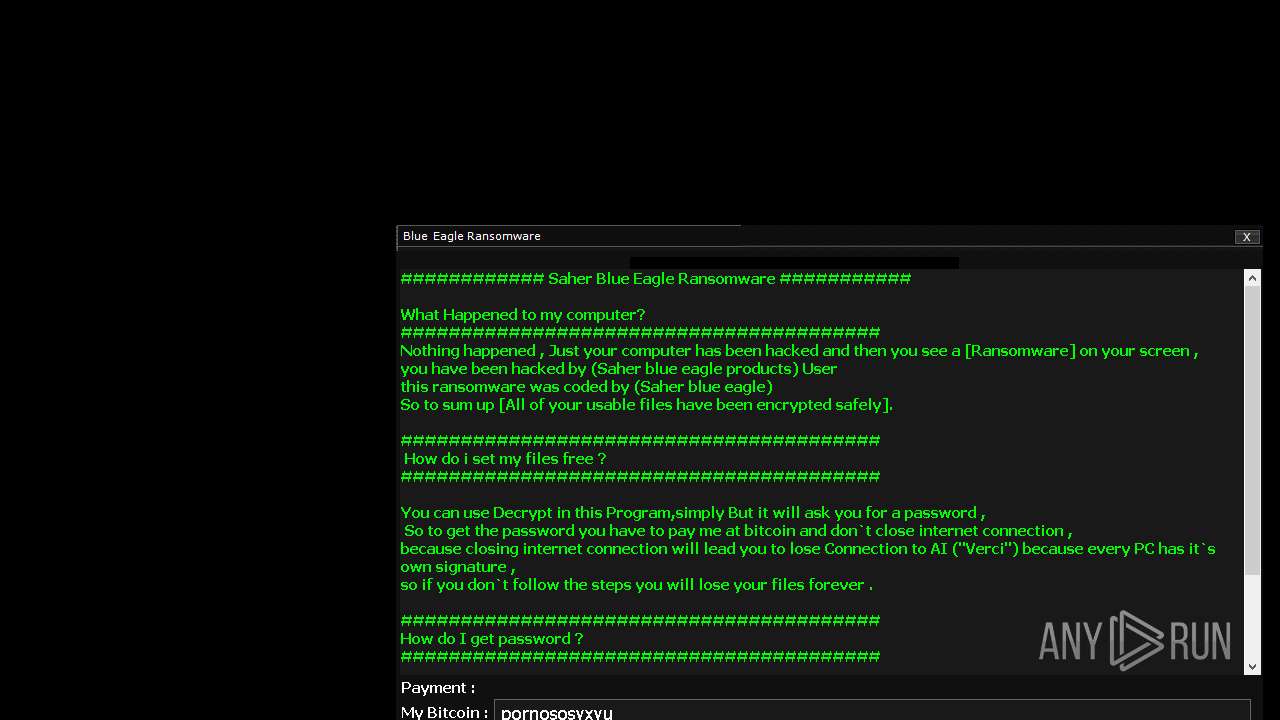
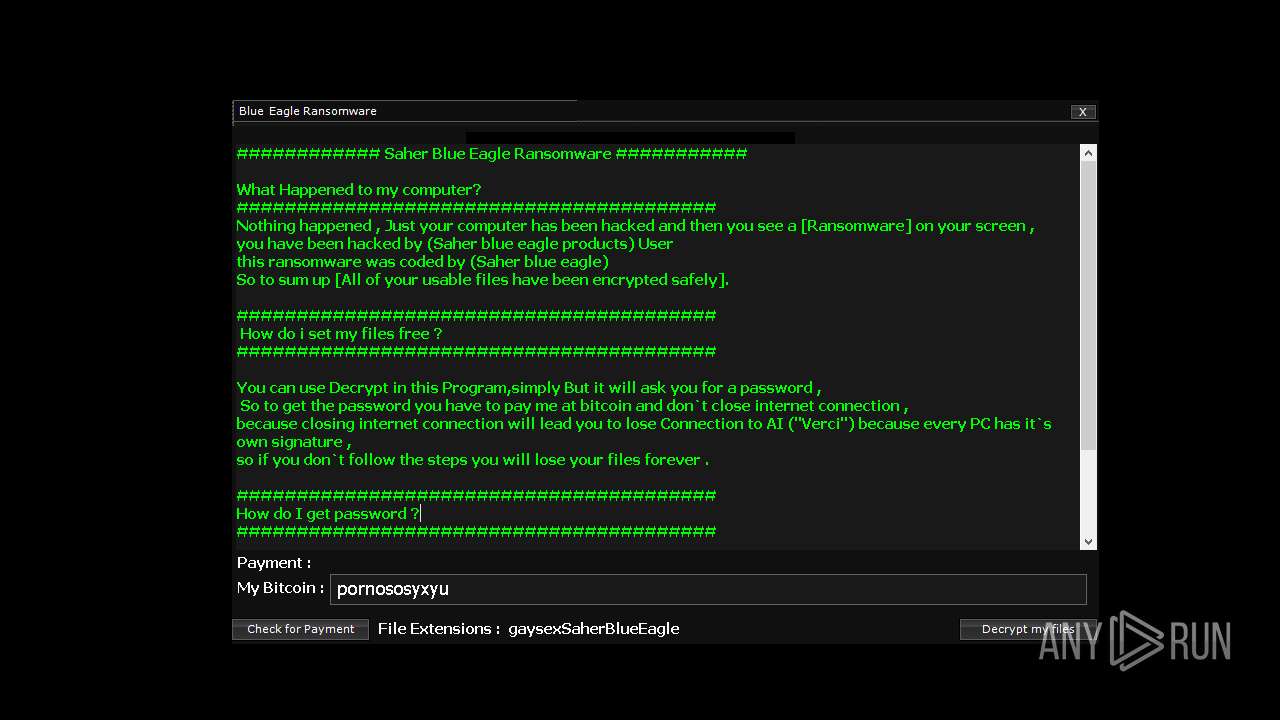
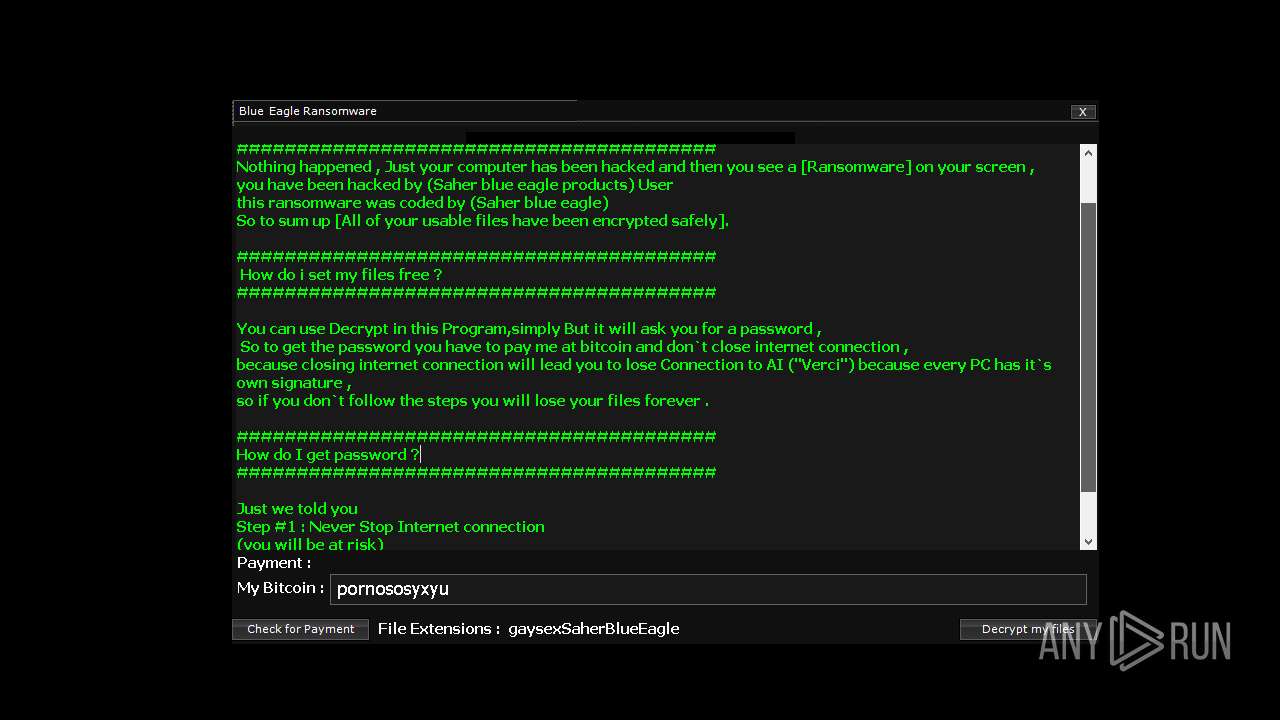
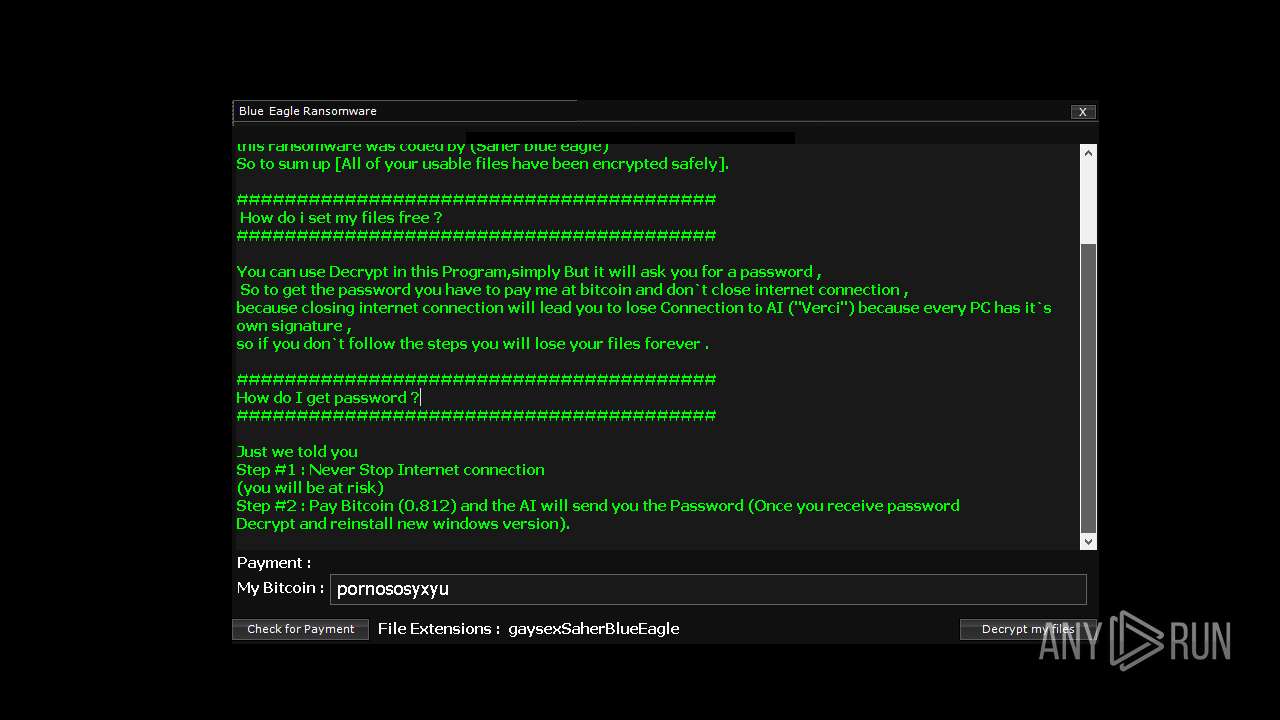
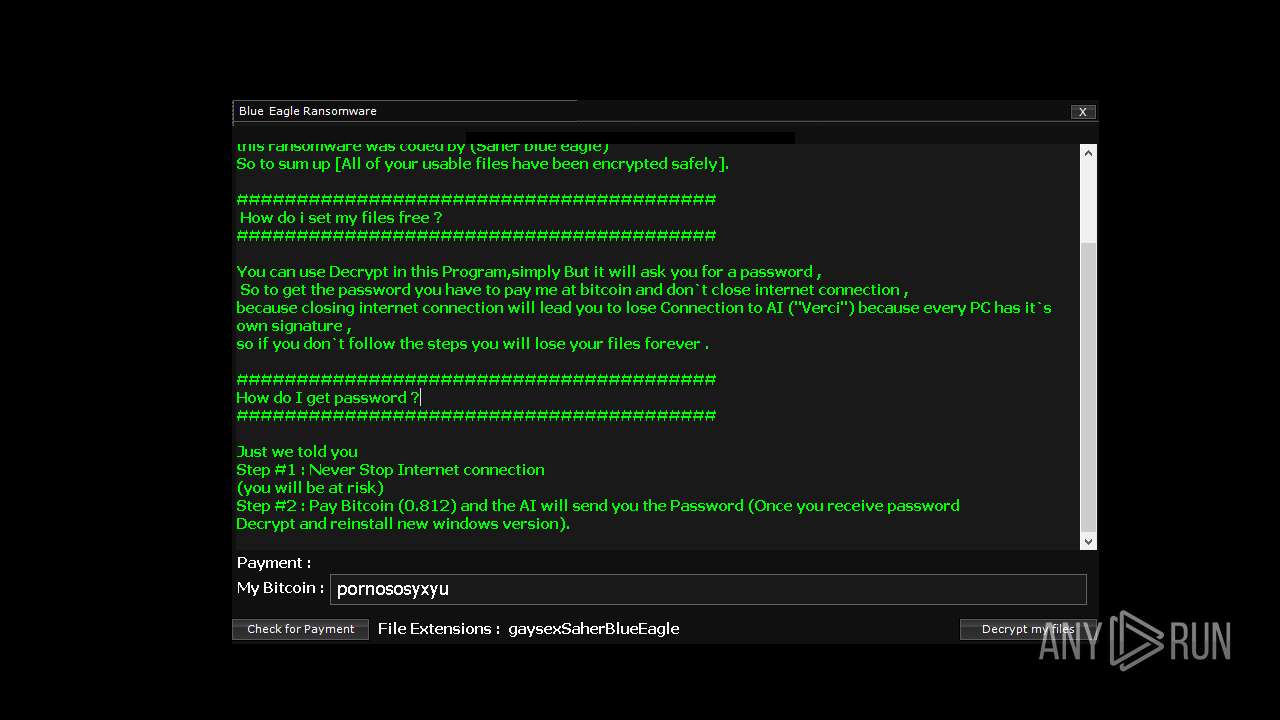
| Verdict: | Malicious activity |
| Analysis date: | August 09, 2024, 17:20:12 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 9EB3BE83C0259C37E2D82C820003B3B6 |
| SHA1: | 36F7443C1ADA2AA4A7603DEA99CF4CA06ED8D1F7 |
| SHA256: | 427C286F191E3A09EEFC9B11F3F21BCBF10BFEF7FF63666816832D73FB173555 |
| SSDEEP: | 49152:7+VSdkb2dMlsT4f1aphqr3puh3qt/GABAmAnq3Egr2HQzmTgIT7IxqihzKxoj:SVUkadysT4AhqMh6VGABApnq3lr27TgV |
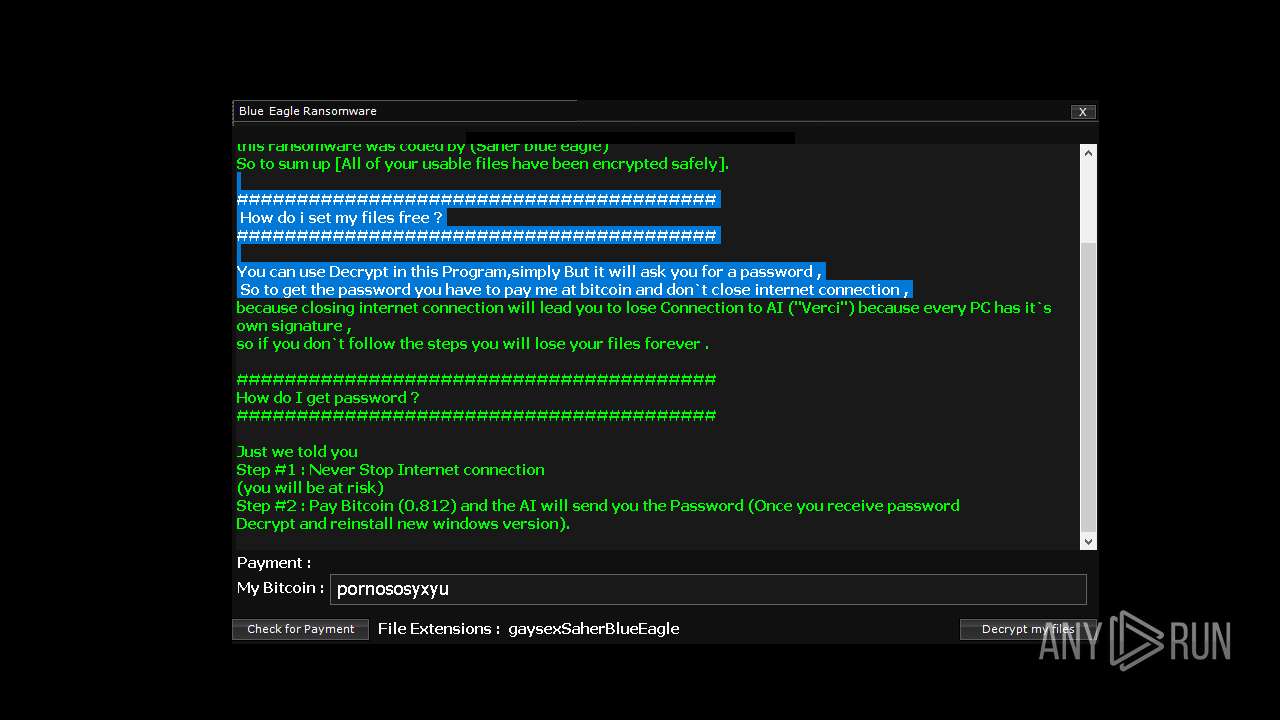
MALICIOUS
UAC/LUA settings modification
- reg.exe (PID: 1224)
SUSPICIOUS
Reads security settings of Internet Explorer
- SaherBlueEagleRansomwareBuilder.exe (PID: 6376)
- xyecoc.exe.exe (PID: 4064)
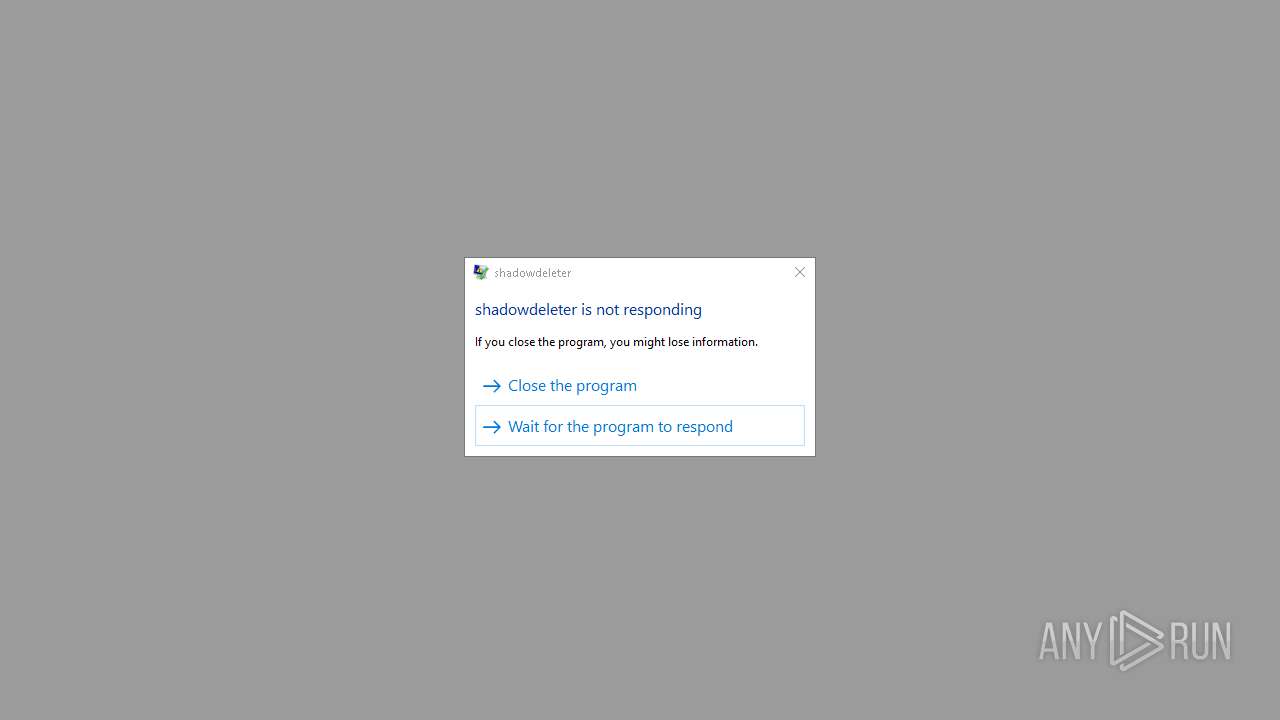
- shadowdeleter.exe (PID: 1116)
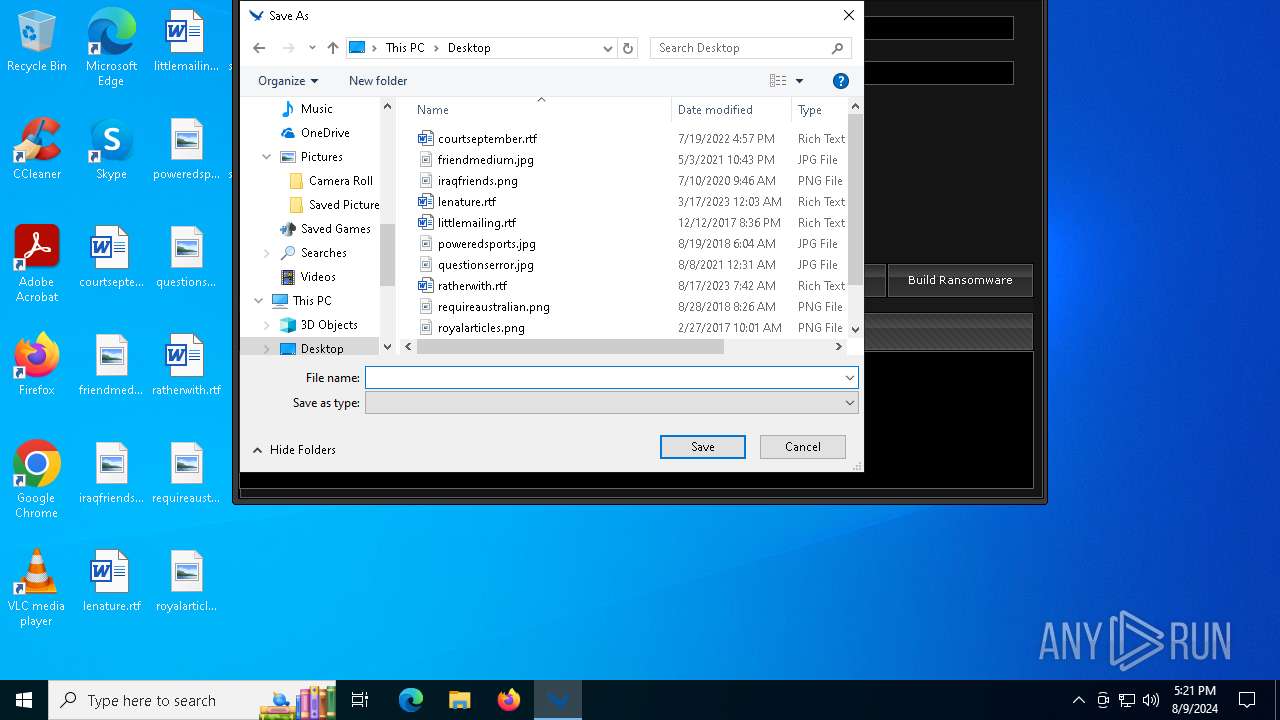
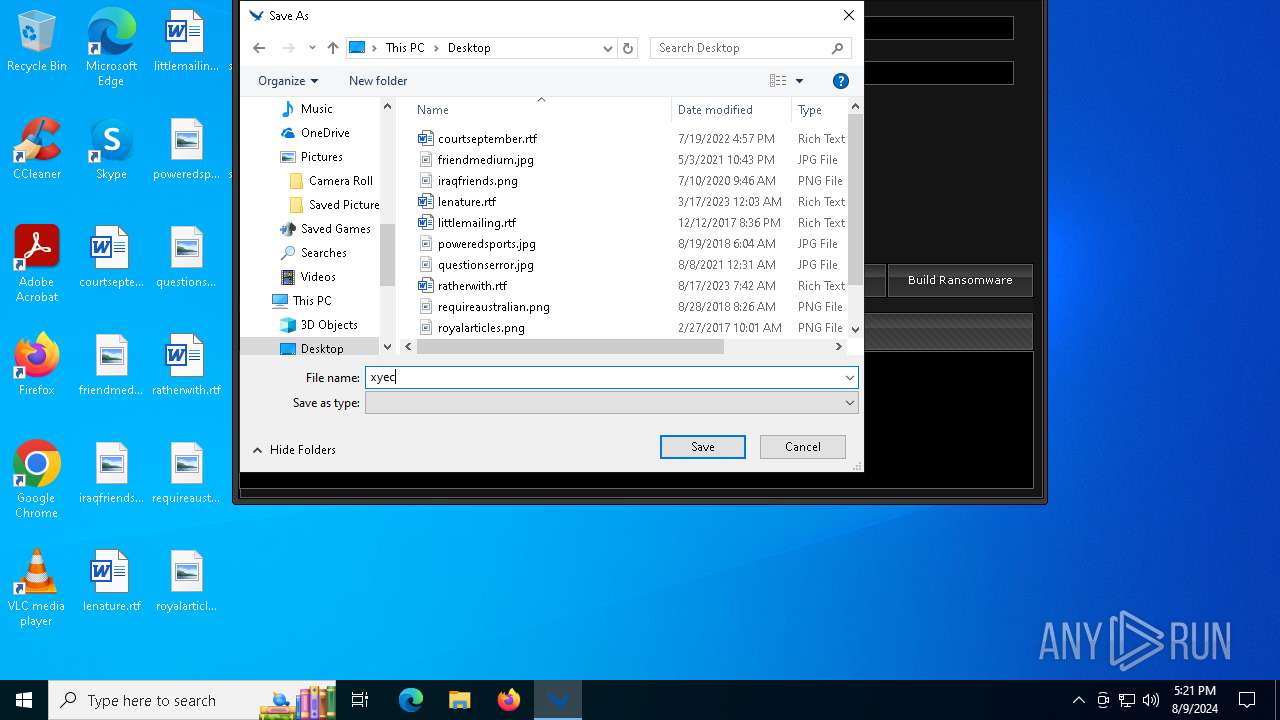
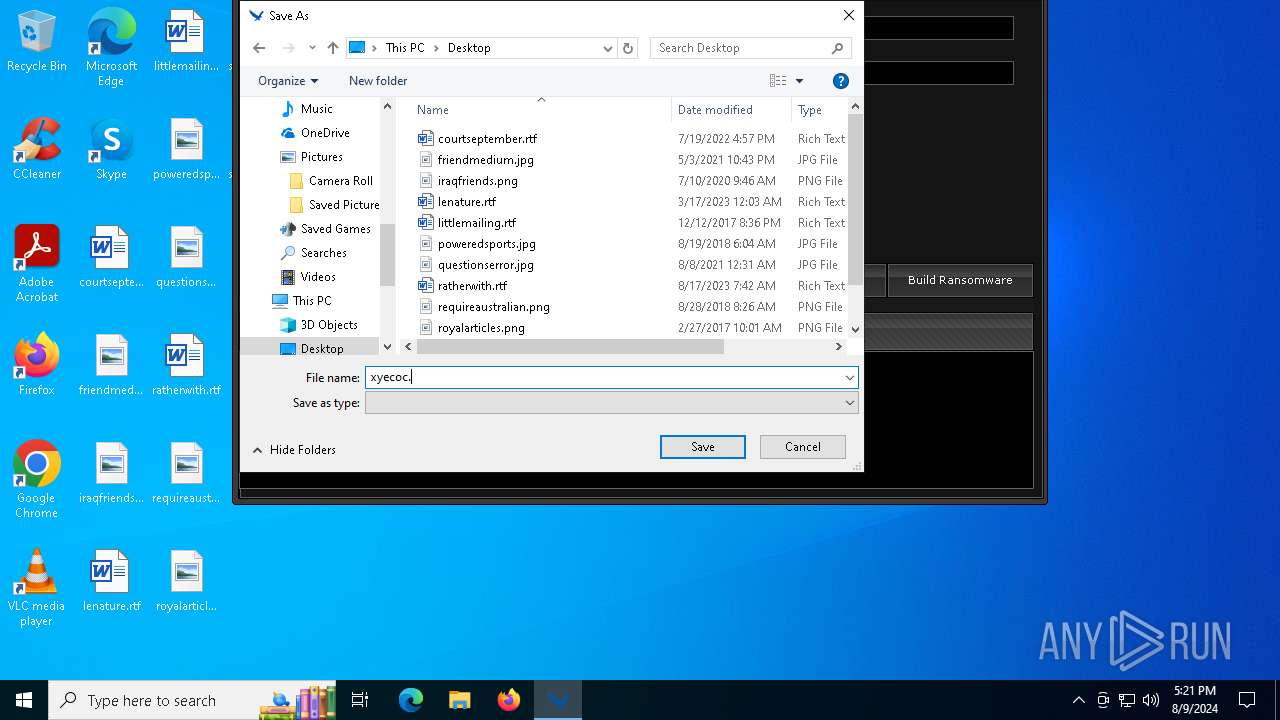
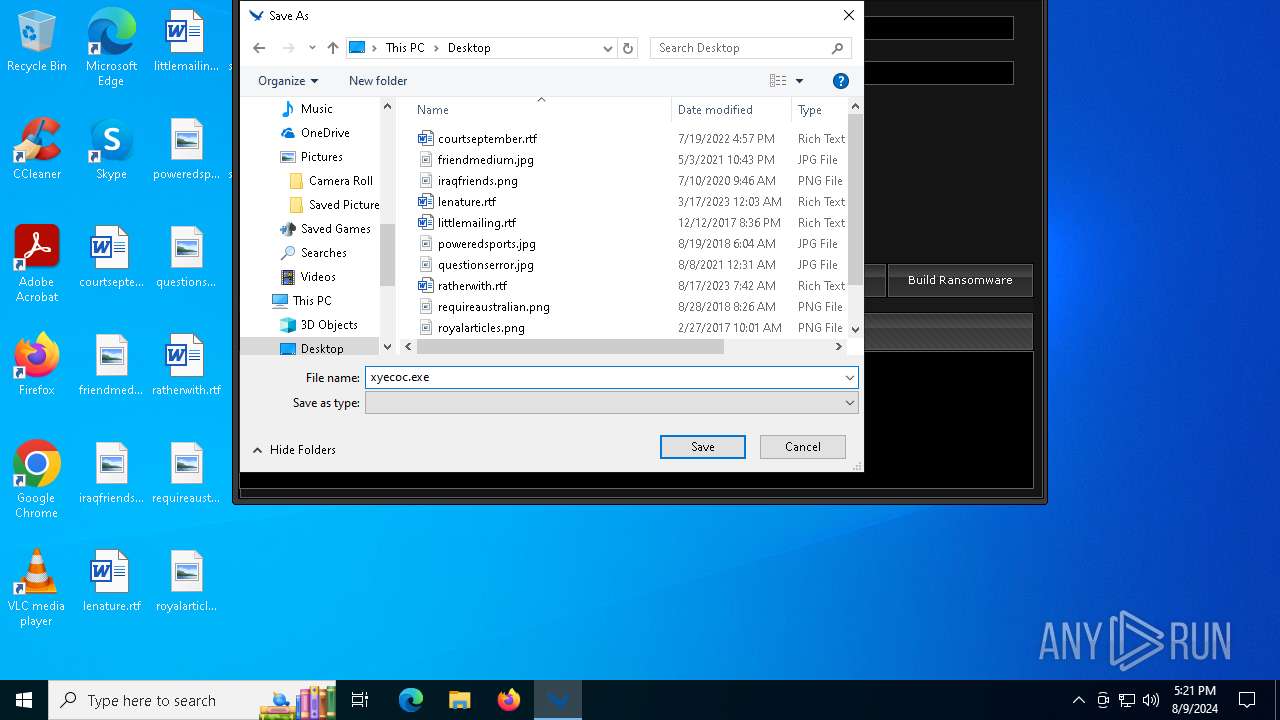
Drops the executable file immediately after the start
- SaherBlueEagleRansomwareBuilder.exe (PID: 6376)
- xyecoc.exe.exe (PID: 4064)
Executable content was dropped or overwritten
- xyecoc.exe.exe (PID: 4064)
- SaherBlueEagleRansomwareBuilder.exe (PID: 6376)
Reads the date of Windows installation
- xyecoc.exe.exe (PID: 4064)
- shadowdeleter.exe (PID: 1116)
Uses TASKKILL.EXE to kill process
- xyecoc.exe.exe (PID: 4064)
Creates file in the systems drive root
- svcran.exe (PID: 876)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 964)
Starts CMD.EXE for commands execution
- shadowdeleter.exe (PID: 1116)
- xyecoc.exe.exe (PID: 4064)
INFO
Checks supported languages
- SaherBlueEagleRansomwareBuilder.exe (PID: 6376)
- TextInputHost.exe (PID: 2128)
- svcran.exe (PID: 876)
- xyecoc.exe.exe (PID: 4064)
- shadowdeleter.exe (PID: 1116)
Reads the computer name
- SaherBlueEagleRansomwareBuilder.exe (PID: 6376)
- xyecoc.exe.exe (PID: 4064)
- svcran.exe (PID: 876)
- shadowdeleter.exe (PID: 1116)
- TextInputHost.exe (PID: 2128)
Reads Environment values
- xyecoc.exe.exe (PID: 4064)
- SaherBlueEagleRansomwareBuilder.exe (PID: 6376)
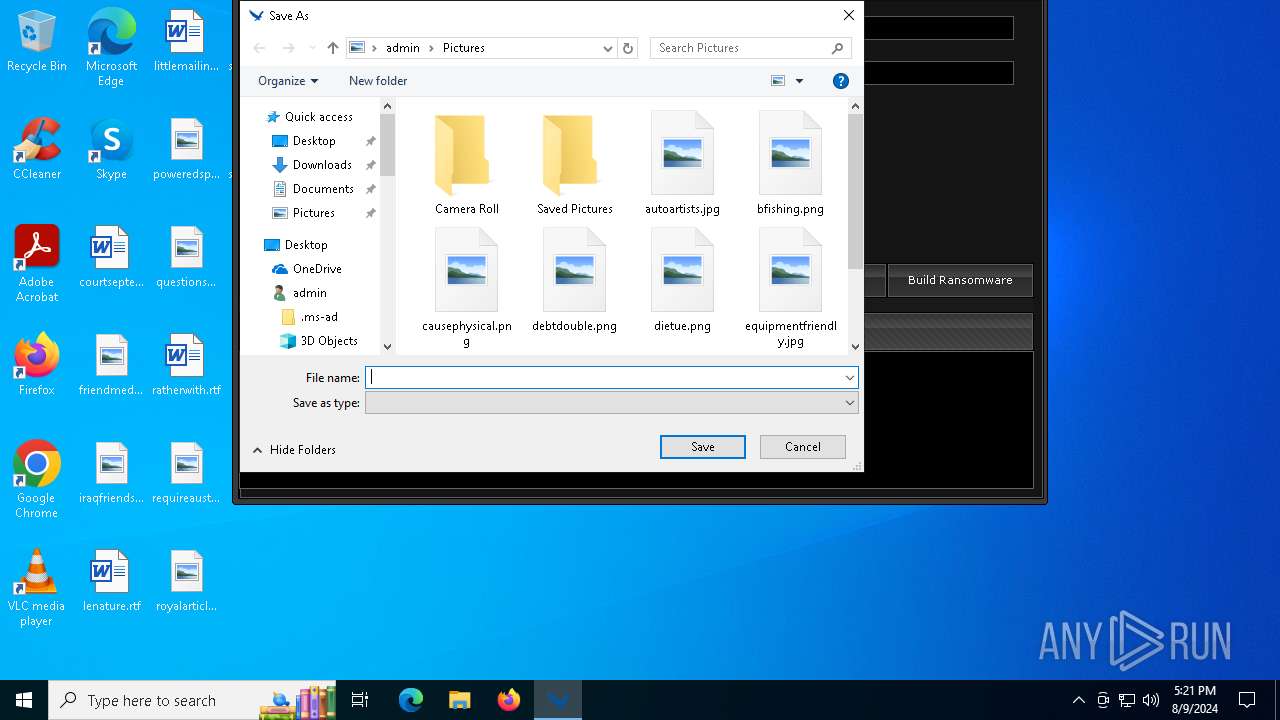
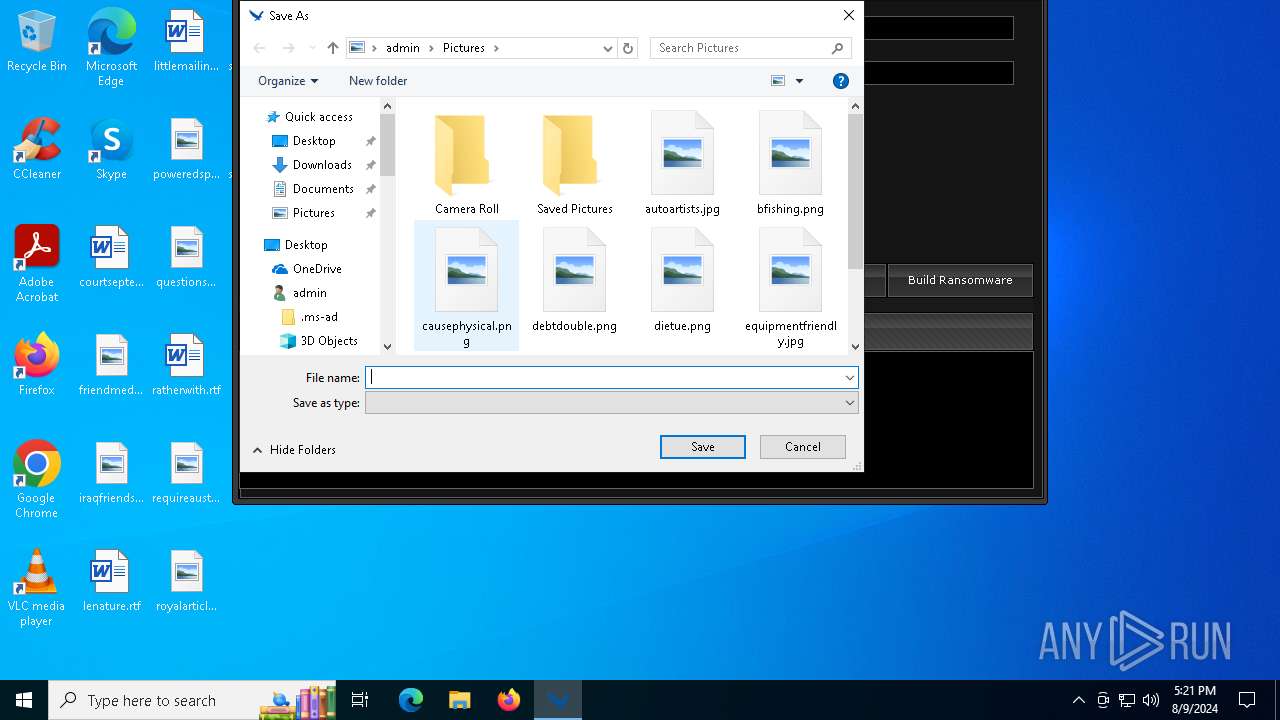
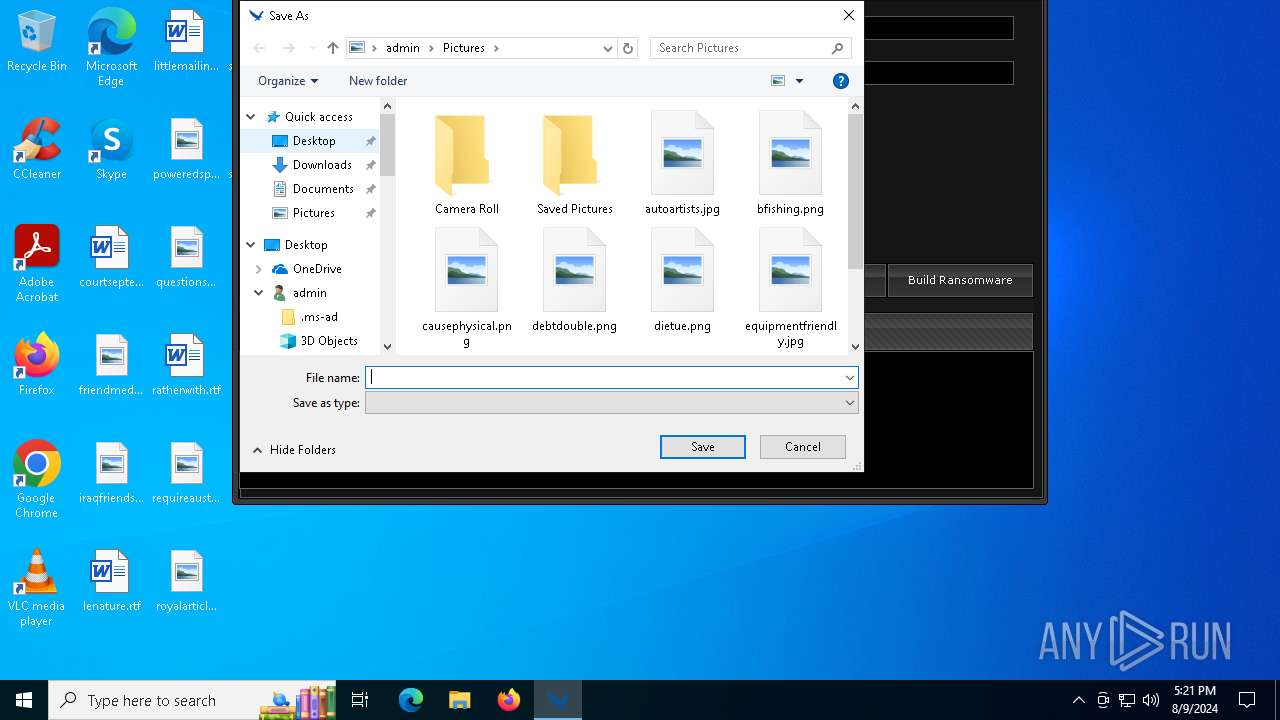
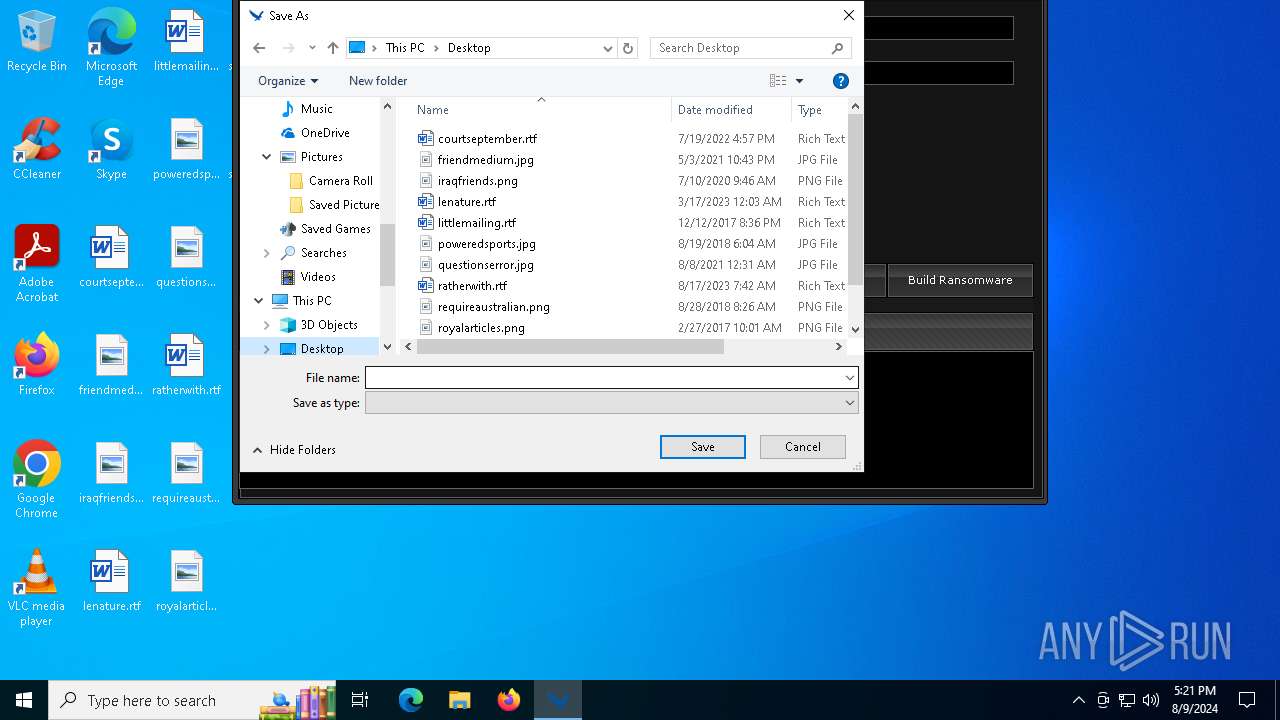
Creates files or folders in the user directory
- xyecoc.exe.exe (PID: 4064)
- SaherBlueEagleRansomwareBuilder.exe (PID: 6376)
- svcran.exe (PID: 876)
- shadowdeleter.exe (PID: 1116)
.NET Reactor protector has been detected
- SaherBlueEagleRansomwareBuilder.exe (PID: 6376)
Create files in a temporary directory
- SaherBlueEagleRansomwareBuilder.exe (PID: 6376)
- xyecoc.exe.exe (PID: 4064)
Reads the machine GUID from the registry
- SaherBlueEagleRansomwareBuilder.exe (PID: 6376)
- xyecoc.exe.exe (PID: 4064)
- svcran.exe (PID: 876)
- shadowdeleter.exe (PID: 1116)
Manual execution by a user
- xyecoc.exe.exe (PID: 4064)
Process checks computer location settings
- xyecoc.exe.exe (PID: 4064)
- shadowdeleter.exe (PID: 1116)
Reads Microsoft Office registry keys
- explorer.exe (PID: 6688)
Reads security settings of Internet Explorer
- explorer.exe (PID: 6688)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:09:06 15:13:33+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 104448 |
| InitializedDataSize: | 1112576 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xffef |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
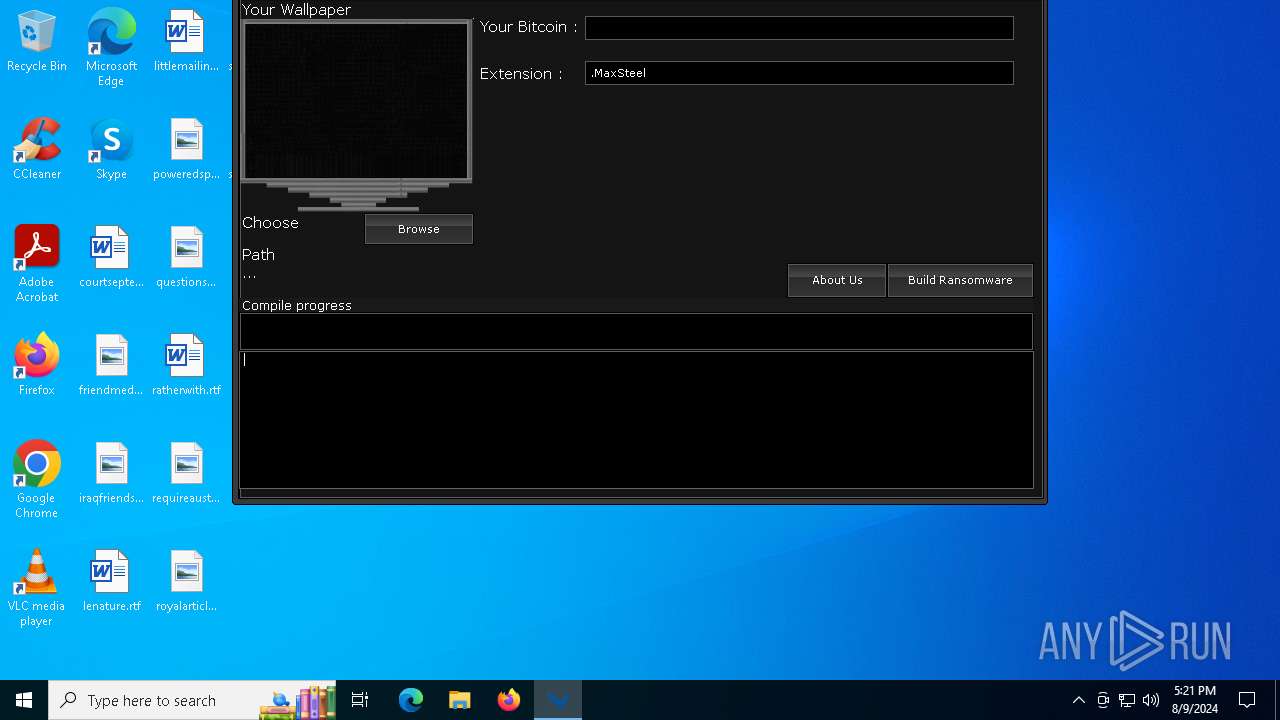
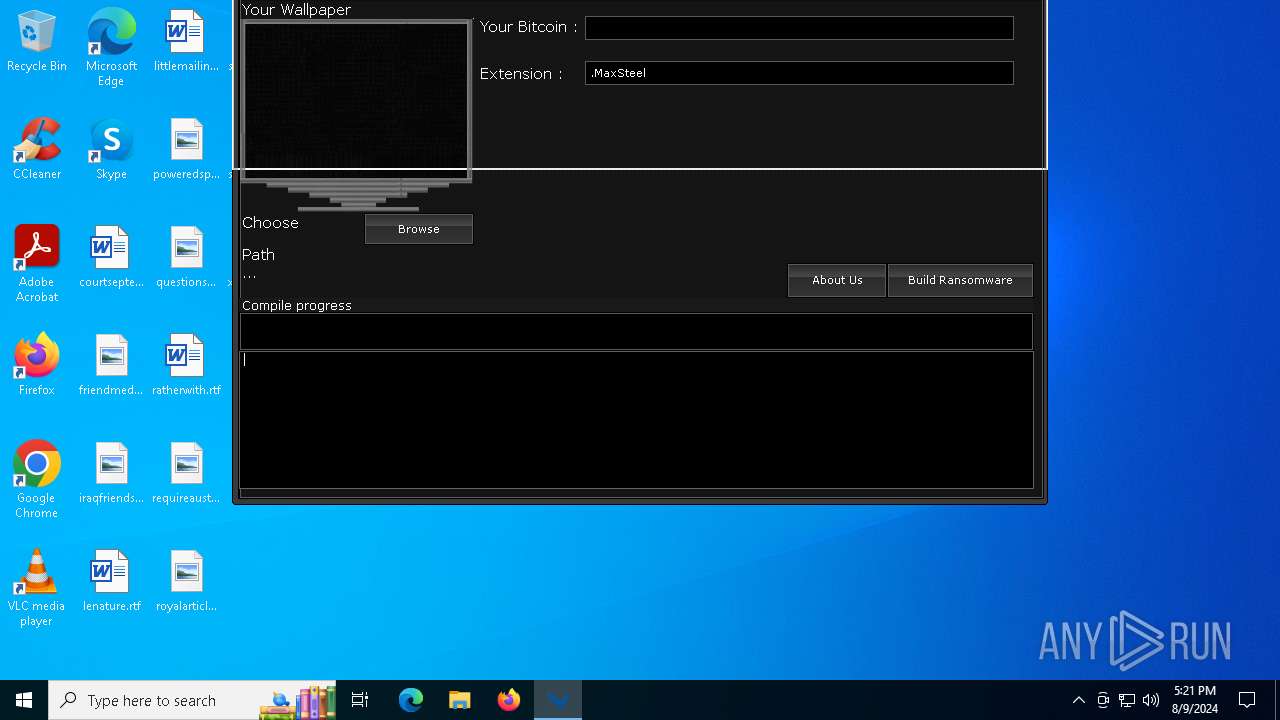
| FileDescription: | SaherBlueEagleRansomwareBuilder |
| FileVersion: | 1.0.0.0 |
| InternalName: | SaherBlueEagleRansomwareBuilder.exe |
| LegalCopyright: | Copyright BlueEagle© 2017 |
| OriginalFileName: | SaherBlueEagleRansomwareBuilder.exe |
| ProductName: | SaherBlueEagleRansomwareBuilder |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
181
Monitored processes
37
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 876 | "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\svcran.exe" | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\svcran.exe | — | xyecoc.exe.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: svcran Version: 1.0.0.0 Modules
| |||||||||||||||
| 964 | "C:\WINDOWS\SysWOW64\cmd.exe" C:\Windows\System32\cmd.exe /k %windir%\System32\reg.exe ADD HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System /v EnableLUA /t REG_DWORD /d 0 /f | C:\Windows\SysWOW64\cmd.exe | xyecoc.exe.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1116 | "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\shadowdeleter.exe" | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\shadowdeleter.exe | xyecoc.exe.exe | ||||||||||||
User: admin Company: Saher_Blue_Eagle Integrity Level: HIGH Description: shadowdeleter Exit code: 3489660927 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1224 | C:\WINDOWS\System32\reg.exe ADD HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System /v EnableLUA /t REG_DWORD /d 0 /f | C:\Windows\SysWOW64\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2128 | "C:\WINDOWS\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe" -ServerName:InputApp.AppXjd5de1g66v206tj52m9d0dtpppx4cgpn.mca | C:\Windows\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Version: 123.26505.0.0 Modules
| |||||||||||||||
| 2636 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | taskkill.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3276 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3508 | taskkill /F /IM sqlserver.exe | C:\Windows\SysWOW64\taskkill.exe | — | xyecoc.exe.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
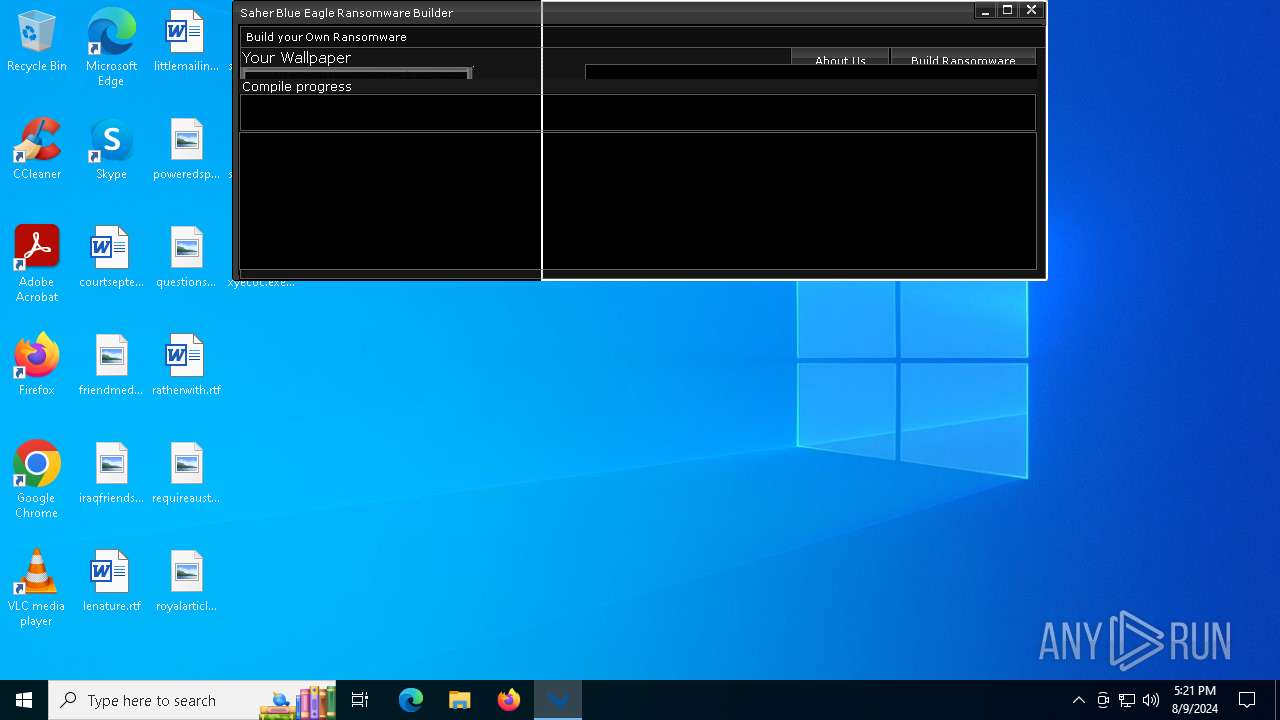
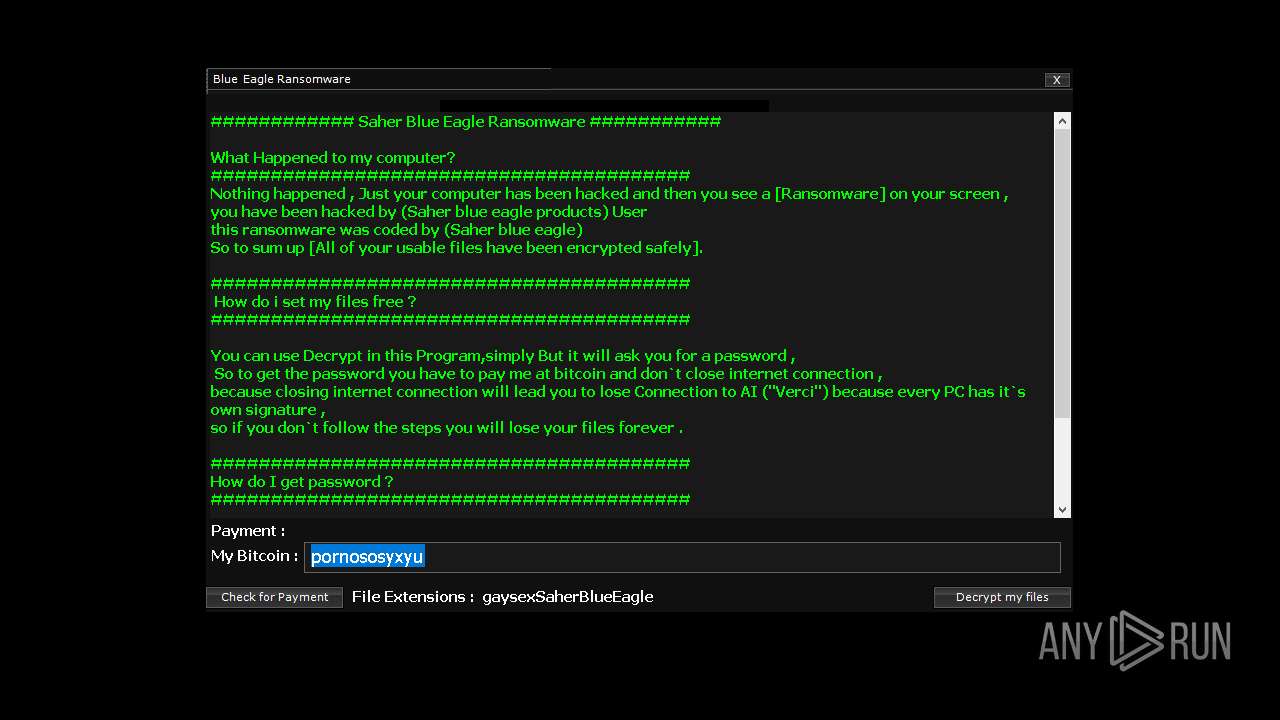
| 4064 | "C:\Users\admin\Desktop\xyecoc.exe.exe" | C:\Users\admin\Desktop\xyecoc.exe.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Saher Blue Eagle Ransomware Version: 1.0.0.0 Modules
| |||||||||||||||
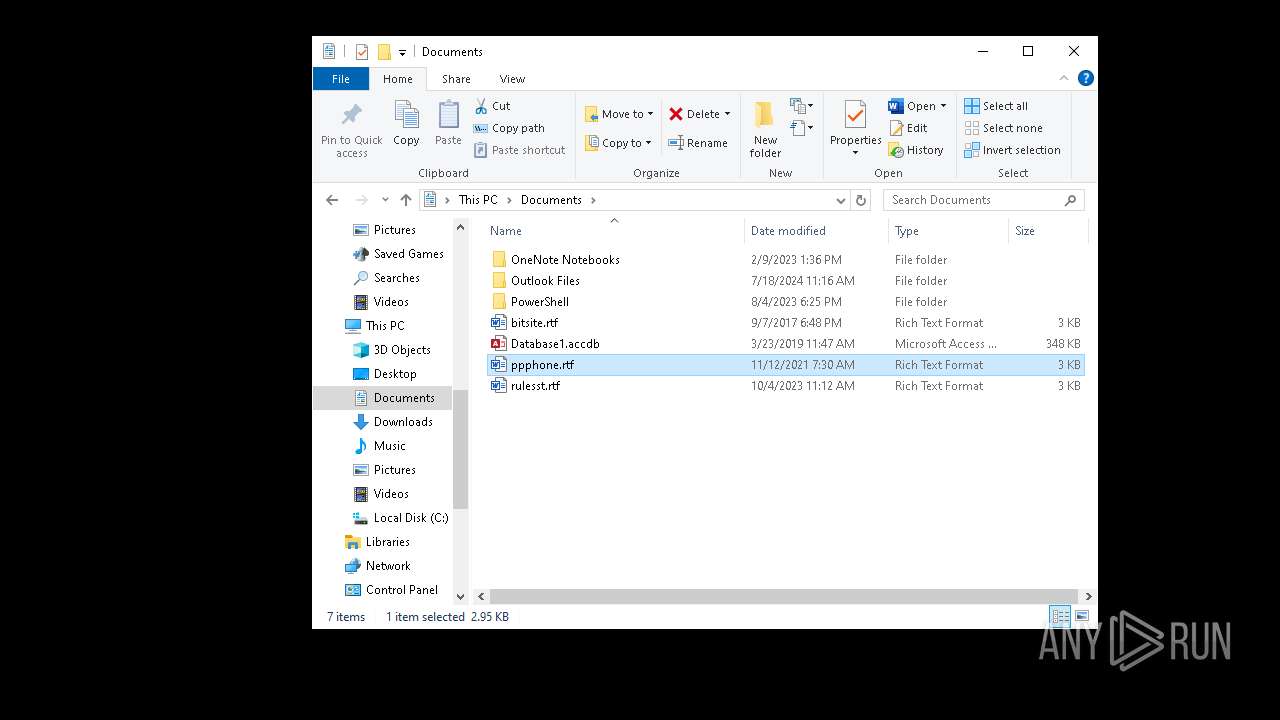
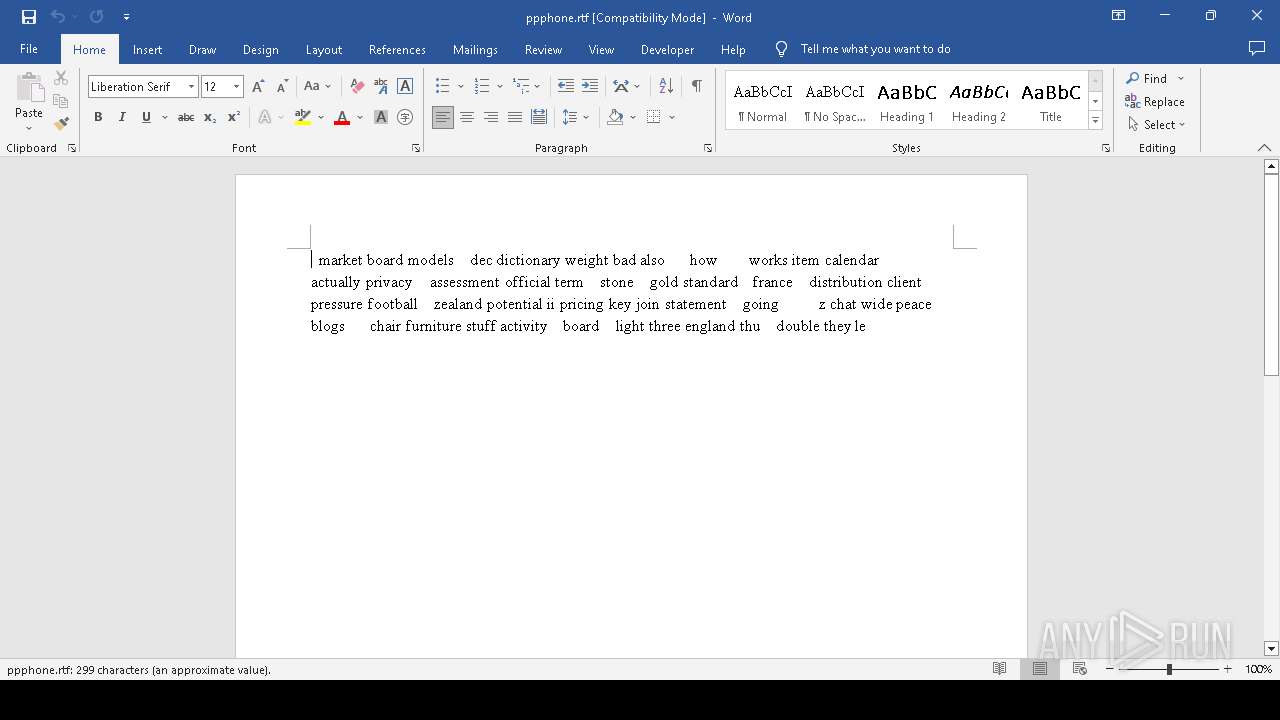
| 4556 | "C:\Program Files\Microsoft Office\Root\Office16\WINWORD.EXE" /n "C:\Users\admin\Documents\ppphone.rtf" /o "" | C:\Program Files\Microsoft Office\root\Office16\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 16.0.16026.20146 Modules
| |||||||||||||||
Total events
59 861
Read events
58 985
Write events
817
Delete events
59
Modification events
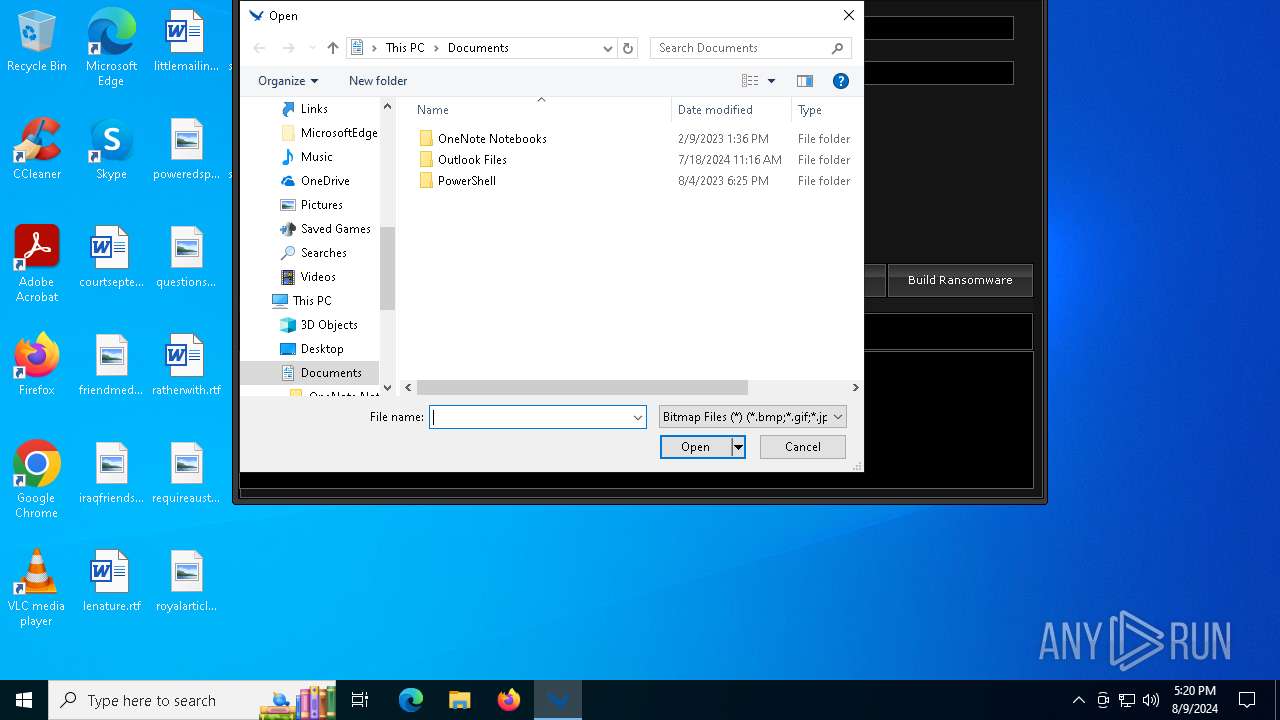
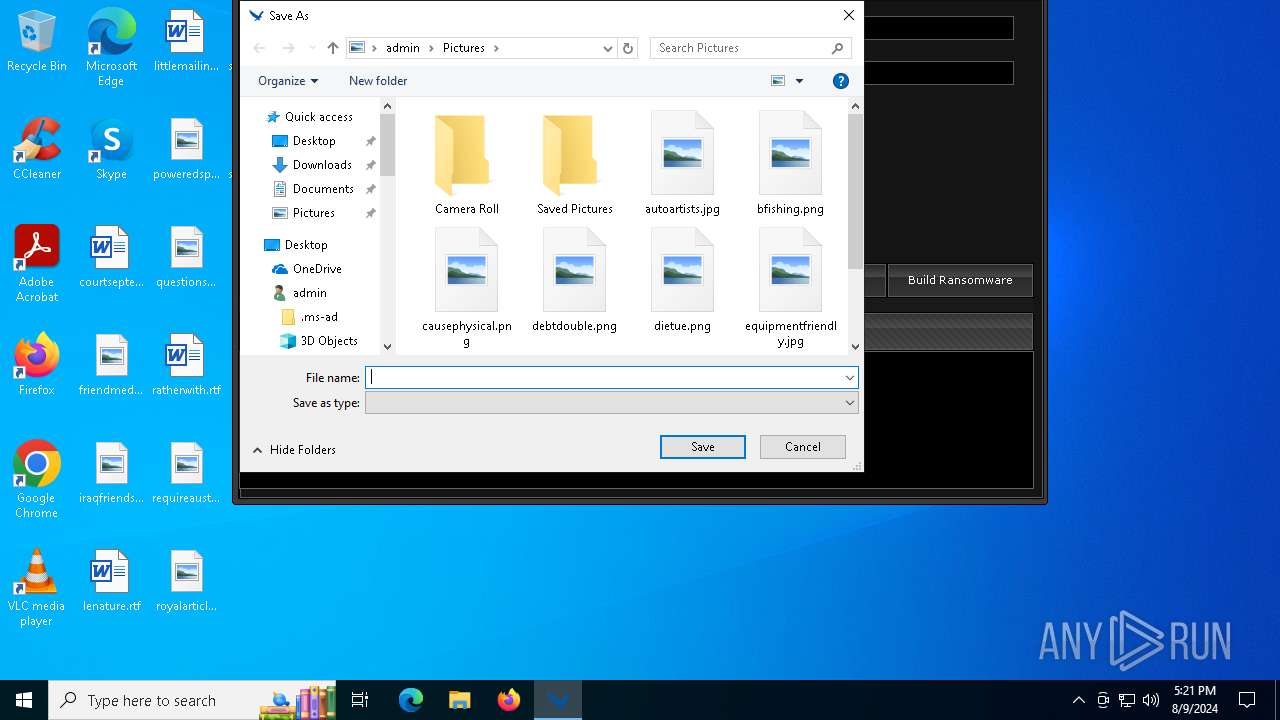
| (PID) Process: | (6376) SaherBlueEagleRansomwareBuilder.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (6376) SaherBlueEagleRansomwareBuilder.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 04000000030000000E0000000F000000000000000C0000000D0000000B000000050000000A000000090000000800000001000000070000000600000002000000FFFFFFFF | |||
| (PID) Process: | (6376) SaherBlueEagleRansomwareBuilder.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\4 |
| Operation: | write | Name: | MRUListEx |
Value: 040000000000000005000000020000000100000003000000FFFFFFFF | |||
| (PID) Process: | (6376) SaherBlueEagleRansomwareBuilder.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\119\Shell |
| Operation: | write | Name: | SniffedFolderType |
Value: Documents | |||
| (PID) Process: | (6376) SaherBlueEagleRansomwareBuilder.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 93 | |||
| (PID) Process: | (6376) SaherBlueEagleRansomwareBuilder.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\3c\52C64B7E |
| Operation: | write | Name: | @C:\Program Files (x86)\Common Files\system\wab32res.dll,-10100 |
Value: Contacts | |||
| (PID) Process: | (6376) SaherBlueEagleRansomwareBuilder.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\OneDrive\Accounts |
| Operation: | write | Name: | LastUpdate |
Value: EE4FB66600000000 | |||
| (PID) Process: | (6376) SaherBlueEagleRansomwareBuilder.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6376) SaherBlueEagleRansomwareBuilder.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6376) SaherBlueEagleRansomwareBuilder.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
Executable files
8
Suspicious files
131
Text files
7
Unknown types
2
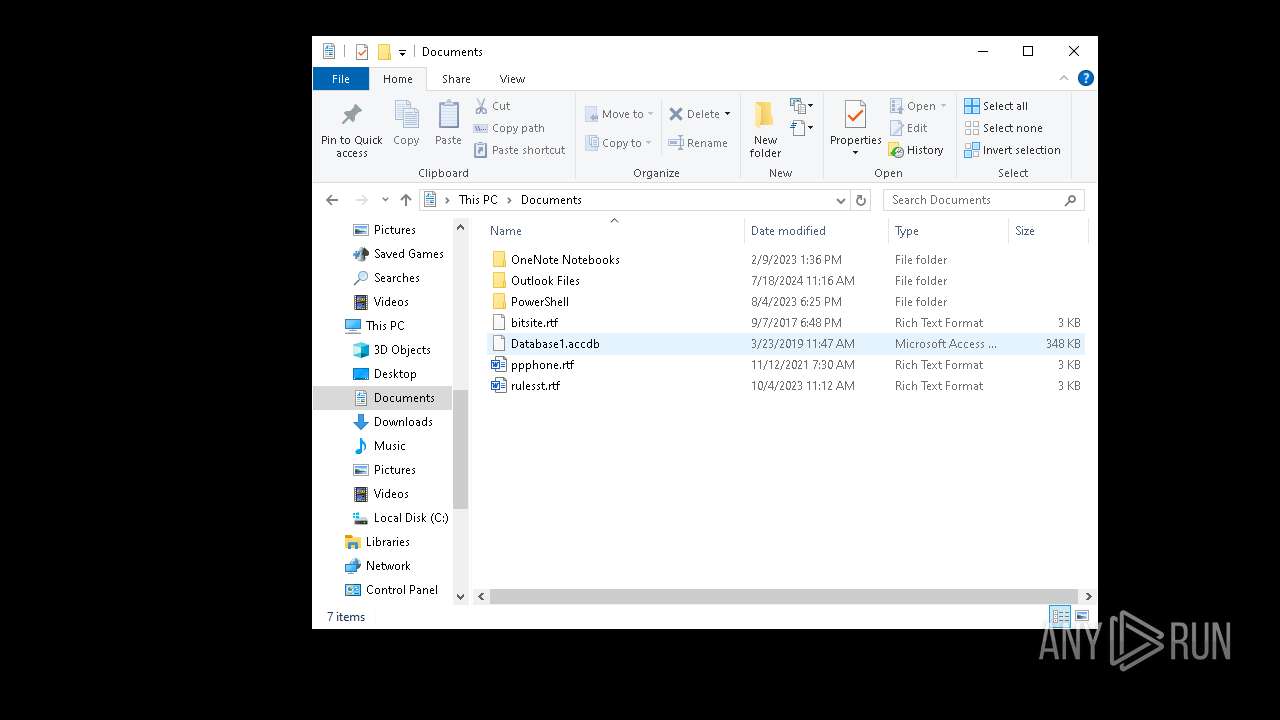
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
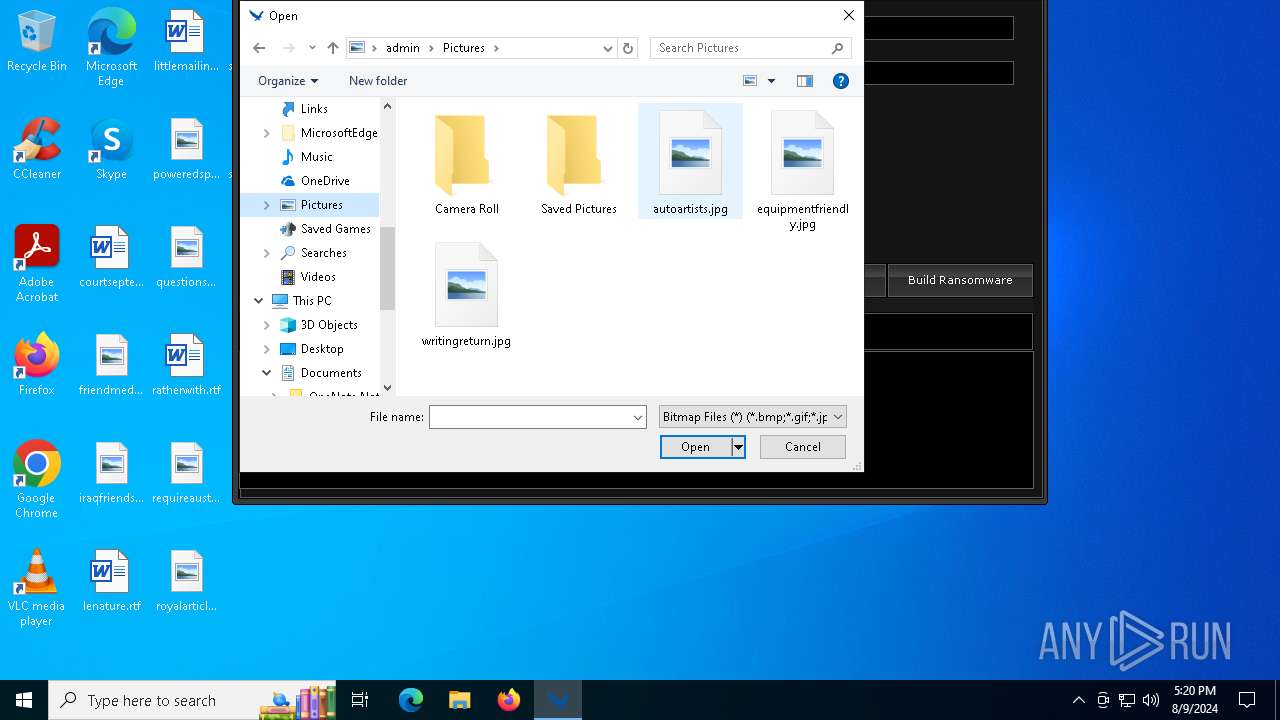
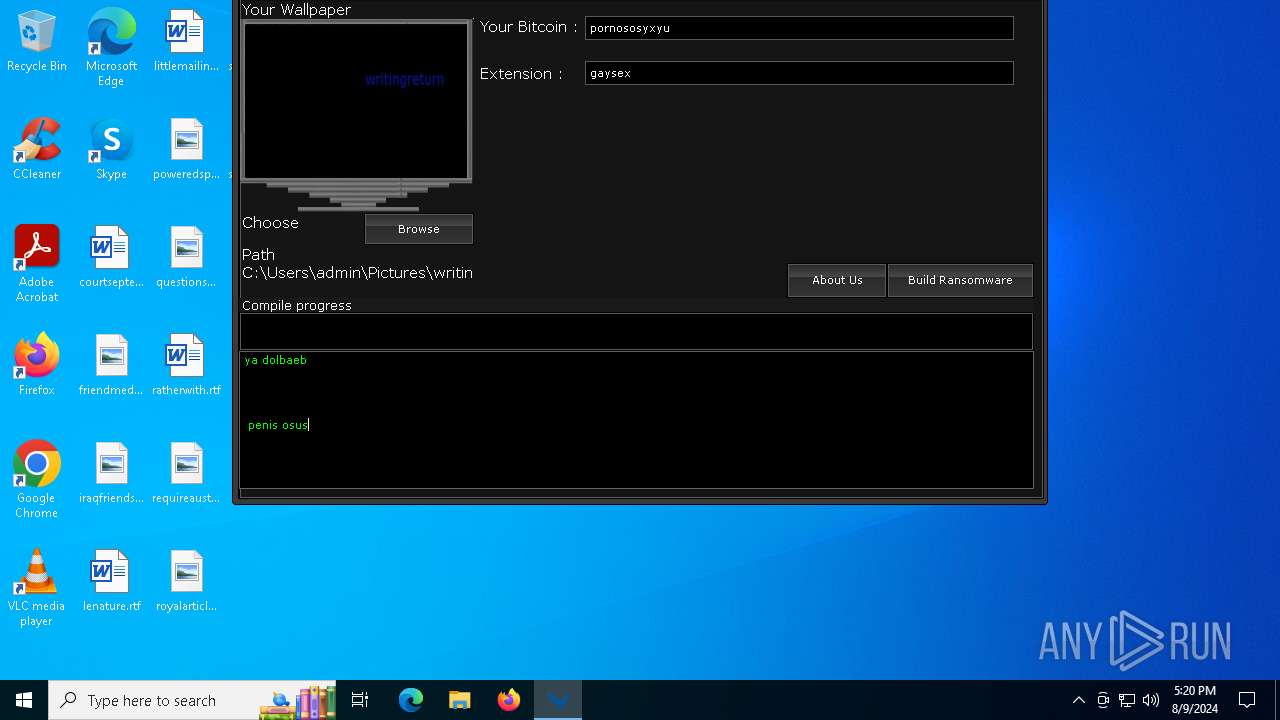
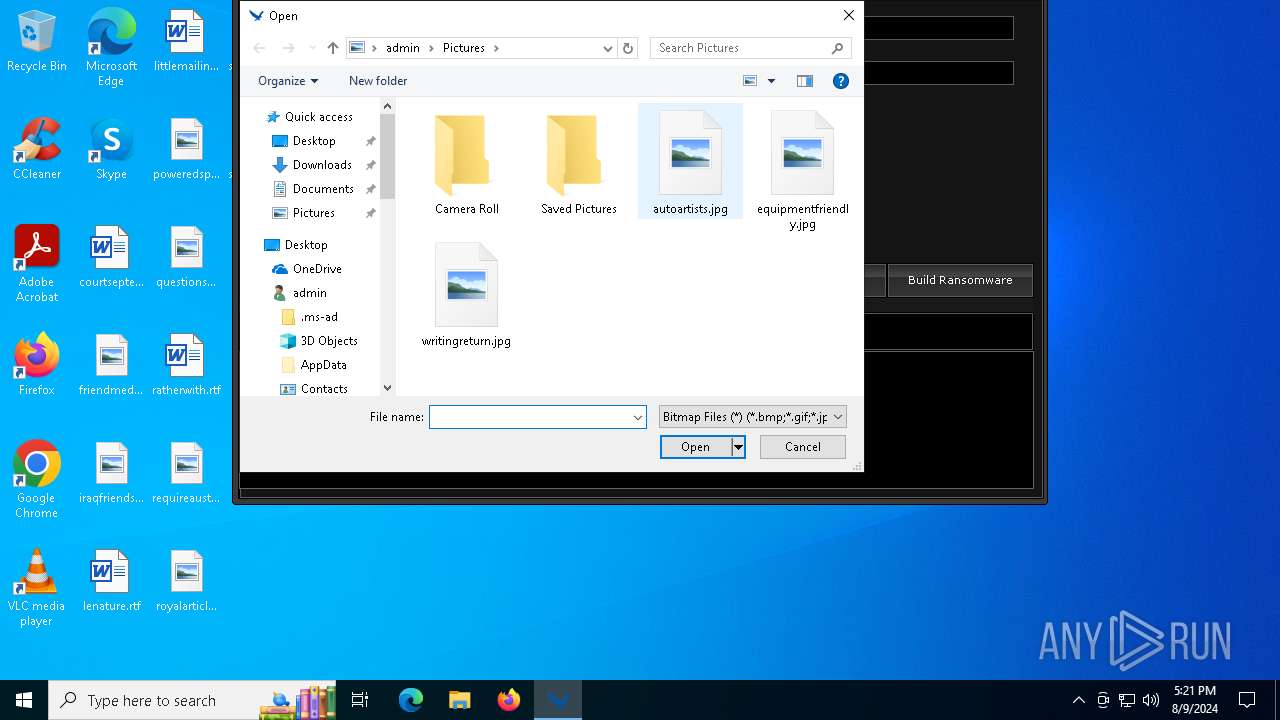
| 6376 | SaherBlueEagleRansomwareBuilder.exe | C:\Users\admin\AppData\Roaming\BackBone.jpg | image | |
MD5:F5D37179578BDB0E7E9AF6BAB6B2C157 | SHA256:CFE8D631696630EE5DFD7E274615AD2335147844C10ADED40869CCE0E1C1F2B4 | |||
| 6376 | SaherBlueEagleRansomwareBuilder.exe | C:\Users\admin\AppData\Local\Temp\Ransomware.exe | executable | |
MD5:474F062DD9642296C05739CC21D6977A | SHA256:A7E3DB7ABB720C1E777A6322BCD969E3E92735586DF2CDC05B59BDEEC7CD71E9 | |||
| 4556 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\WebServiceCache\AllUsers\officeclient.microsoft.com\A1AAE597-9319-44CC-97A6-043AD566EA1F | xml | |
MD5:A10228A70390B2056023A862C641C933 | SHA256:AA52BE15DD81BB3780ADBB5EF6FC32516A054241E4F83E0756EF5D99FC4BA6A4 | |||
| 4064 | xyecoc.exe.exe | C:\Users\admin\AppData\Local\Temp\svran-Thread.exe | executable | |
MD5:B5D8F2F3B980460E3D09DD57A26D9F08 | SHA256:149F4227332BE7AC426167B022511B2EE91F368322DA0CC5C27B7F732D8B17FA | |||
| 4064 | xyecoc.exe.exe | C:\Users\admin\AppData\Local\Temp\svran.exe | executable | |
MD5:8C6843F3EEF6C0901DA747E19309FE7B | SHA256:933F6EE5C927DCEB50BA1532A8DA2E406DE7C0983F667AE324F5081D24223035 | |||
| 1116 | shadowdeleter.exe | C:\Users\admin\AppData\Roaming\Microsoft\Speech\Files\UserLexicons\SP_436F262F5980425E9A78D581D76F8231.dat | binary | |
MD5:3CDBDE648E4809EED1CEACF5BC808C94 | SHA256:9319C5C27F7175E8B57DC8CB810A2D72B86C817CBF7D03B5EFD1D11ADF5FC7C9 | |||
| 4064 | xyecoc.exe.exe | C:\Users\admin\AppData\Roaming\Back.jpg | image | |
MD5:549032C49DB6806029F3F56C3322E134 | SHA256:021D53E79408EF77DCD796DB46CC724FFC4609AC3AA9E7ED640ADEC4202D1A19 | |||
| 4556 | WINWORD.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_6372E0472AFF76BB926C97818BC773B9 | binary | |
MD5:FD39119FA5D131600737D14633F9CA1F | SHA256:99DC1DF2864478938C41F963FEFA018EE6FB9F52CB96AEB70763DF5C40257943 | |||
| 4064 | xyecoc.exe.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\svran-Thread.exe | executable | |
MD5:AD6809619DB90B788265BED6A0BE9F1E | SHA256:9C3F94E1C312A60DC03428BE7ACC67913B909D459208C4FAE755074A4F86F969 | |||
| 4556 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\56a61aeb75d8f5be186c26607f4bb213abe7c5ec.tbres | binary | |
MD5:952729F80FFA2DDB3FA0A9A9827F72B3 | SHA256:D8F62310A07FCCCE64B3F990BACBC1E274F6AA4BA87ABF16C02847E501D1E864 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
52
DNS requests
28
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3812 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6852 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6892 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
4556 | WINWORD.EXE | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
4556 | WINWORD.EXE | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1536 | RUXIMICS.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
2120 | MoUsoCoreWorker.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4084 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4084 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5336 | SearchApp.exe | 2.23.209.160:443 | www.bing.com | Akamai International B.V. | GB | unknown |
5336 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
3812 | svchost.exe | 20.190.159.68:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
th.bing.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
WINWORD.EXE | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
WINWORD.EXE | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
WINWORD.EXE | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|