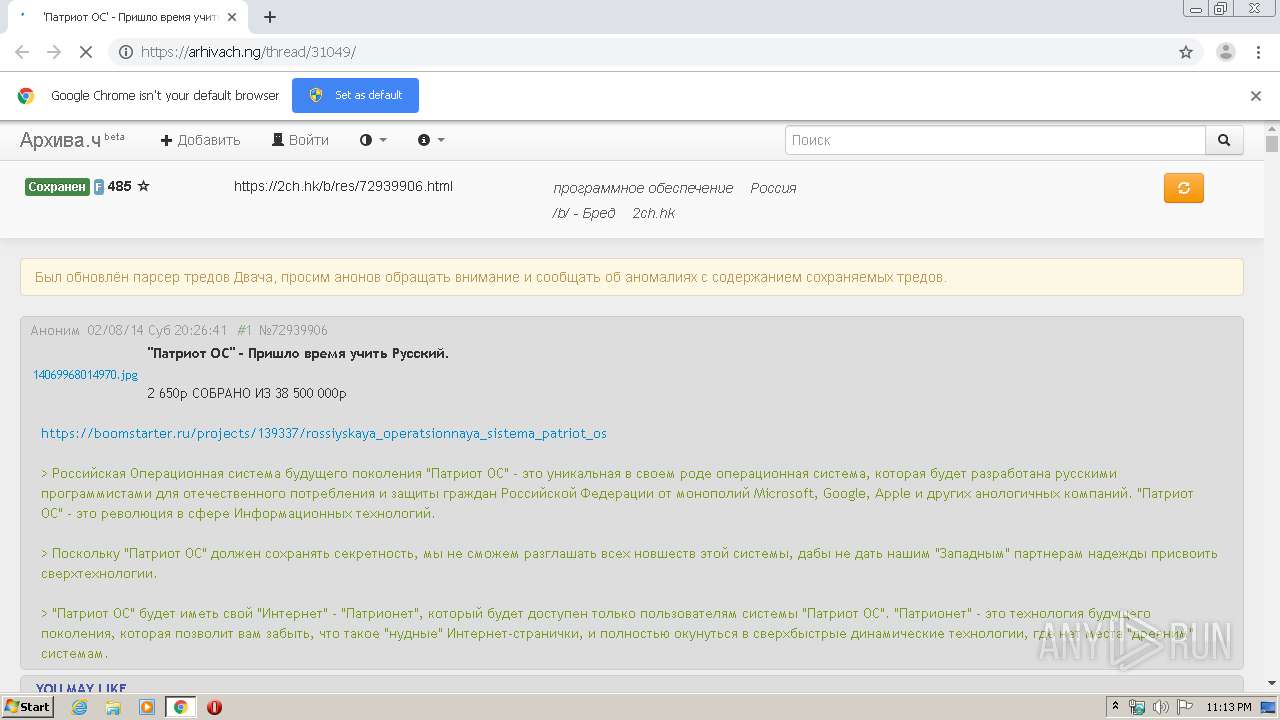
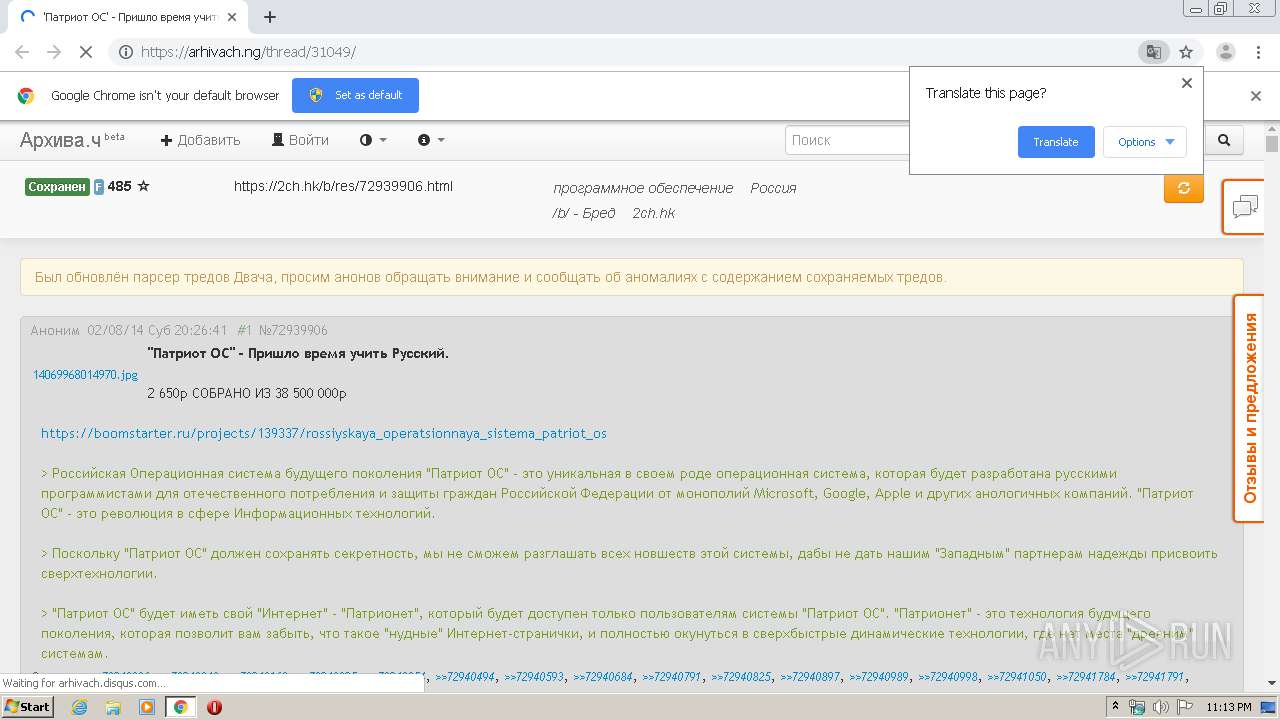
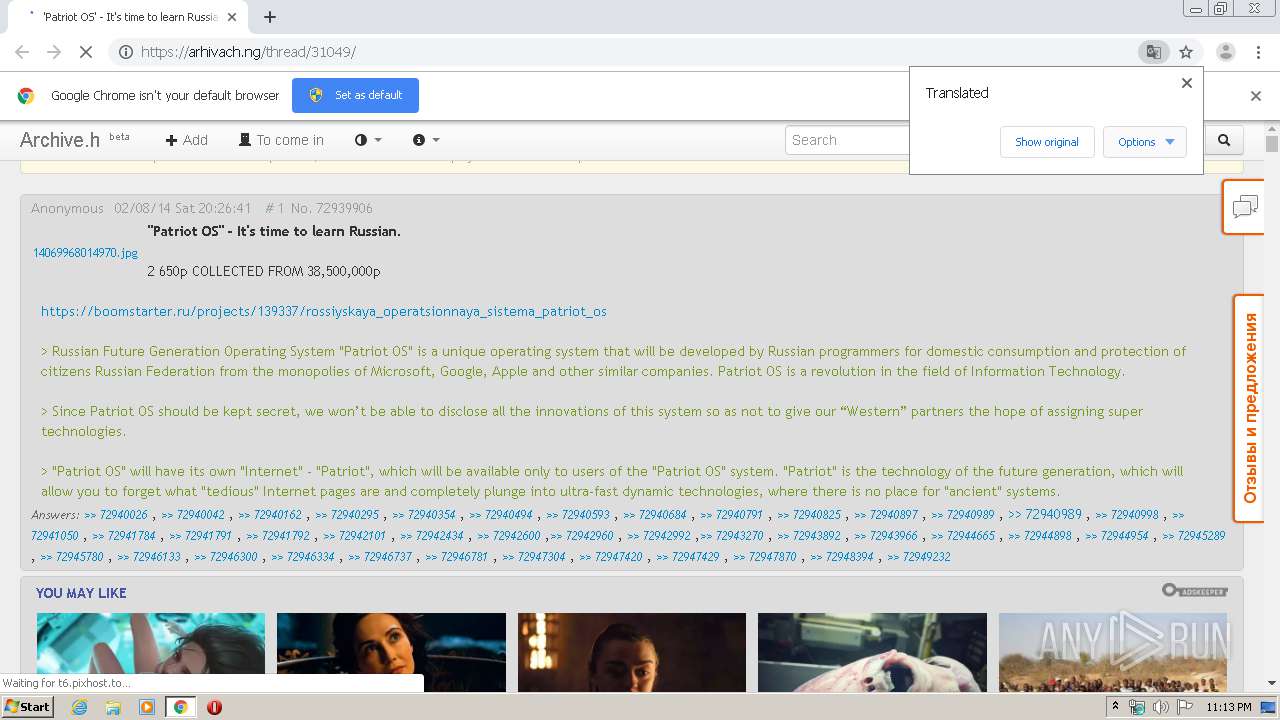
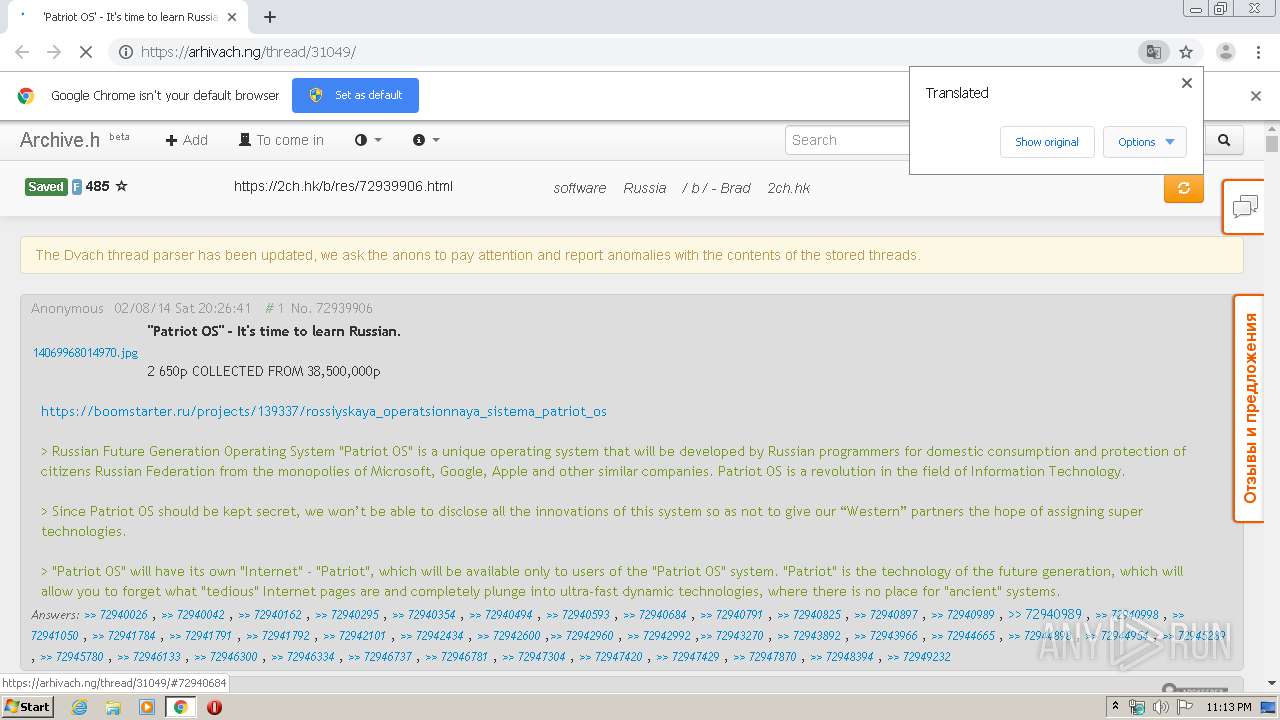
| URL: | https://arhivach.ng/thread/31049/ |
| Full analysis: | https://app.any.run/tasks/a9d101bf-ac7e-428a-8793-852c77611baa |
| Verdict: | Suspicious activity |
| Analysis date: | February 20, 2020, 23:13:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 58106E363A2A009BF721ED8A71BB4CAF |
| SHA1: | A9A48240C1D7EFE1F59BDB3516DEDB72FD9CB8DD |
| SHA256: | 4278E2A8248C2CD929AD599D2584938C947D4F8AC9371F64AB19D33E2D99347D |
| SSDEEP: | 3:N8hEu3k:2f3k |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 3000)
Reads the hosts file
- chrome.exe (PID: 3000)
- chrome.exe (PID: 3404)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
46
Monitored processes
10
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2012 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,894858092661550116,311963814960945234,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6844633688967063951 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2252 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2372 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2896 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2400 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1000,894858092661550116,311963814960945234,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=7669907008522316684 --mojo-platform-channel-handle=3564 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2568 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1000,894858092661550116,311963814960945234,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=16910317887828790031 --mojo-platform-channel-handle=1008 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2880 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6fa8a9d0,0x6fa8a9e0,0x6fa8a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2960 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,894858092661550116,311963814960945234,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3707915202610010254 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2504 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3000 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://arhivach.ng/thread/31049/" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3380 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,894858092661550116,311963814960945234,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=117993844846362204 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2216 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3404 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,894858092661550116,311963814960945234,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=6124000807212483802 --mojo-platform-channel-handle=1596 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3408 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,894858092661550116,311963814960945234,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=14585599485105563512 --mojo-platform-channel-handle=1056 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
557
Read events
518
Write events
36
Delete events
3
Modification events
| (PID) Process: | (2372) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3000-13226714003958000 |
Value: 259 | |||
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3000-13226714003958000 |
Value: 259 | |||
Executable files
0
Suspicious files
32
Text files
62
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E4F1294-BB8.pma | — | |
MD5:— | SHA256:— | |||
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\6f8d275e-edcc-40be-83e9-ecfe77dc587c.tmp | — | |
MD5:— | SHA256:— | |||
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFa66a99.TMP | text | |
MD5:— | SHA256:— | |||
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFa66a8a.TMP | text | |
MD5:— | SHA256:— | |||
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa66c7e.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
55
DNS requests
27
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3404 | chrome.exe | GET | — | 94.229.45.3:80 | http://t6.pixhost.to/thumbs/2261/27769062_fe84c247e56d46fdbdeb9c3d3547949a.jpg | SK | — | — | suspicious |
3404 | chrome.exe | GET | — | 94.229.45.3:80 | http://t6.pixhost.to/thumbs/718/26020368_5d5334f11a83e998f877e04fcd817e89.jpg | SK | — | — | suspicious |
3404 | chrome.exe | GET | 200 | 176.9.51.10:80 | http://abload.de/thumb/6d5ef149810d40586a29fhxui1.jpg | DE | image | 8.88 Kb | whitelisted |
3404 | chrome.exe | GET | 200 | 176.9.51.10:80 | http://abload.de/thumb/fc62783dfab0a9a82440e3me57.jpg | DE | image | 6.99 Kb | whitelisted |
3404 | chrome.exe | GET | 200 | 176.9.51.10:80 | http://abload.de/thumb/1404776121807r7stw.gif | DE | image | 8.42 Kb | whitelisted |
3404 | chrome.exe | GET | 200 | 176.9.51.10:80 | http://abload.de/thumb/bf76845d3d98014f8b1d3bars8.gif | DE | image | 7.27 Kb | whitelisted |
3404 | chrome.exe | GET | 200 | 176.9.51.10:80 | http://abload.de/thumb/2f7aa859f61ba3000dacdr6usu.jpg | DE | image | 9.44 Kb | whitelisted |
3404 | chrome.exe | GET | 200 | 176.9.51.10:80 | http://abload.de/thumb/cb79756468d85bca9543821eju.gif | DE | image | 1.09 Kb | whitelisted |
3404 | chrome.exe | GET | 302 | 94.229.45.3:80 | http://t6.pixhost.to/thumbs/1565/27020004_5466003bafd986755f6acfa39040c606.jpg | SK | html | 170 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3404 | chrome.exe | 13.35.250.20:443 | farm6.staticflickr.com | — | US | unknown |
3404 | chrome.exe | 143.204.212.72:443 | farm3.staticflickr.com | — | US | unknown |
3404 | chrome.exe | 176.9.51.10:80 | abload.de | Hetzner Online GmbH | DE | unknown |
3404 | chrome.exe | 216.58.207.46:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
3404 | chrome.exe | 172.217.21.202:443 | translate.googleapis.com | Google Inc. | US | whitelisted |
3404 | chrome.exe | 104.31.2.181:443 | arhivach.ng | Cloudflare Inc | US | unknown |
3404 | chrome.exe | 216.58.208.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
3404 | chrome.exe | 172.217.22.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3404 | chrome.exe | 216.58.210.3:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3404 | chrome.exe | 172.217.21.227:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
arhivach.ng |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
t6.pixhost.to |
| suspicious |
jsc.adskeeper.co.uk |
| whitelisted |
www.google.com |
| malicious |
farm3.staticflickr.com |
| whitelisted |
farm4.staticflickr.com |
| whitelisted |
farm6.staticflickr.com |
| whitelisted |
abload.de |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |