| File name: | abba.exe |
| Full analysis: | https://app.any.run/tasks/6a34748c-33ee-47ff-a563-0d18d1074773 |
| Verdict: | Malicious activity |
| Analysis date: | December 18, 2021, 11:49:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 8606155DE5B680684D77AA0469AE8CE1 |
| SHA1: | 05BBE640AFC5D59FBBA07C439EB4C2824C23E6C2 |
| SHA256: | 4270FE37886BCA259B5A989C9F148B598629F12DE2E4DDDC5D23A14BF98DC954 |
| SSDEEP: | 98304:0AI+oO/XLPEb1pQAt4TcQK66AiXPRNd+09DWc9ck38afhR+Mr+OvuiyUj508jL1N:TtoOPL8hIvcz9iUclaH+a+Ov5pX8Oui |
MALICIOUS
Drops executable file immediately after starts
- abba.exe (PID: 3956)
- seescenicelfa.exe (PID: 596)
- pub4.exe (PID: 2152)
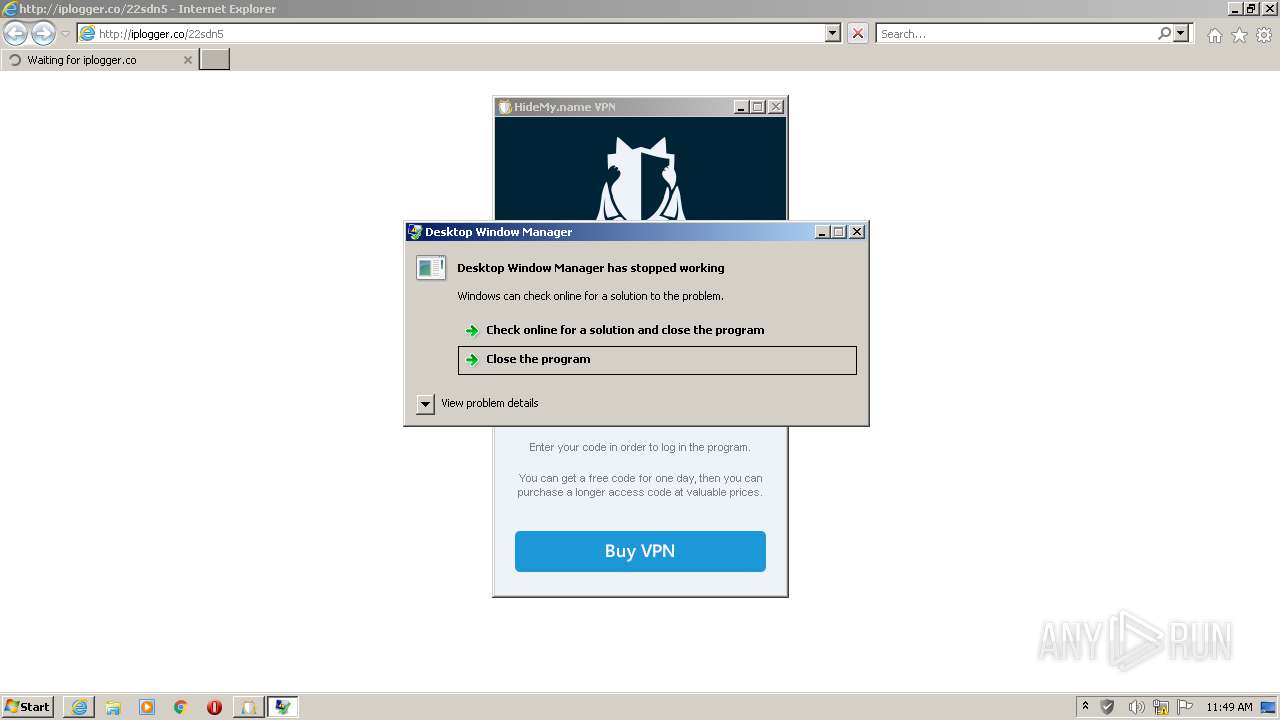
Changes the autorun value in the registry
- dwm.exe (PID: 2276)
Steals credentials from Web Browsers
- seescenicelfa.exe (PID: 596)
Actions looks like stealing of personal data
- seescenicelfa.exe (PID: 596)
Application was dropped or rewritten from another process
- seescenicelfa.exe (PID: 596)
- kosmix.exe (PID: 1536)
- dwm.exe (PID: 2276)
- pub4.exe (PID: 2152)
- Start.exe (PID: 1012)
Loads dropped or rewritten executable
- seescenicelfa.exe (PID: 596)
- Start.exe (PID: 1012)
- kosmix.exe (PID: 1536)
SUSPICIOUS
Checks supported languages
- abba.exe (PID: 3956)
- dwm.exe (PID: 2276)
- pub4.exe (PID: 2152)
- kosmix.exe (PID: 1536)
- seescenicelfa.exe (PID: 596)
- cmd.exe (PID: 2272)
- Start.exe (PID: 1012)
- cmd.exe (PID: 2424)
Creates files in the program directory
- abba.exe (PID: 3956)
- seescenicelfa.exe (PID: 596)
- pub4.exe (PID: 2152)
- Start.exe (PID: 1012)
Reads the computer name
- abba.exe (PID: 3956)
- dwm.exe (PID: 2276)
- seescenicelfa.exe (PID: 596)
- cmd.exe (PID: 2272)
- pub4.exe (PID: 2152)
- Start.exe (PID: 1012)
- kosmix.exe (PID: 1536)
Executable content was dropped or overwritten
- abba.exe (PID: 3956)
- seescenicelfa.exe (PID: 596)
- pub4.exe (PID: 2152)
Drops a file that was compiled in debug mode
- abba.exe (PID: 3956)
- pub4.exe (PID: 2152)
Creates a directory in Program Files
- abba.exe (PID: 3956)
- pub4.exe (PID: 2152)
- Start.exe (PID: 1012)
Drops a file with a compile date too recent
- abba.exe (PID: 3956)
Drops a file with too old compile date
- abba.exe (PID: 3956)
- pub4.exe (PID: 2152)
Creates a software uninstall entry
- abba.exe (PID: 3956)
- pub4.exe (PID: 2152)
Starts CMD.EXE for commands execution
- abba.exe (PID: 3956)
- kosmix.exe (PID: 1536)
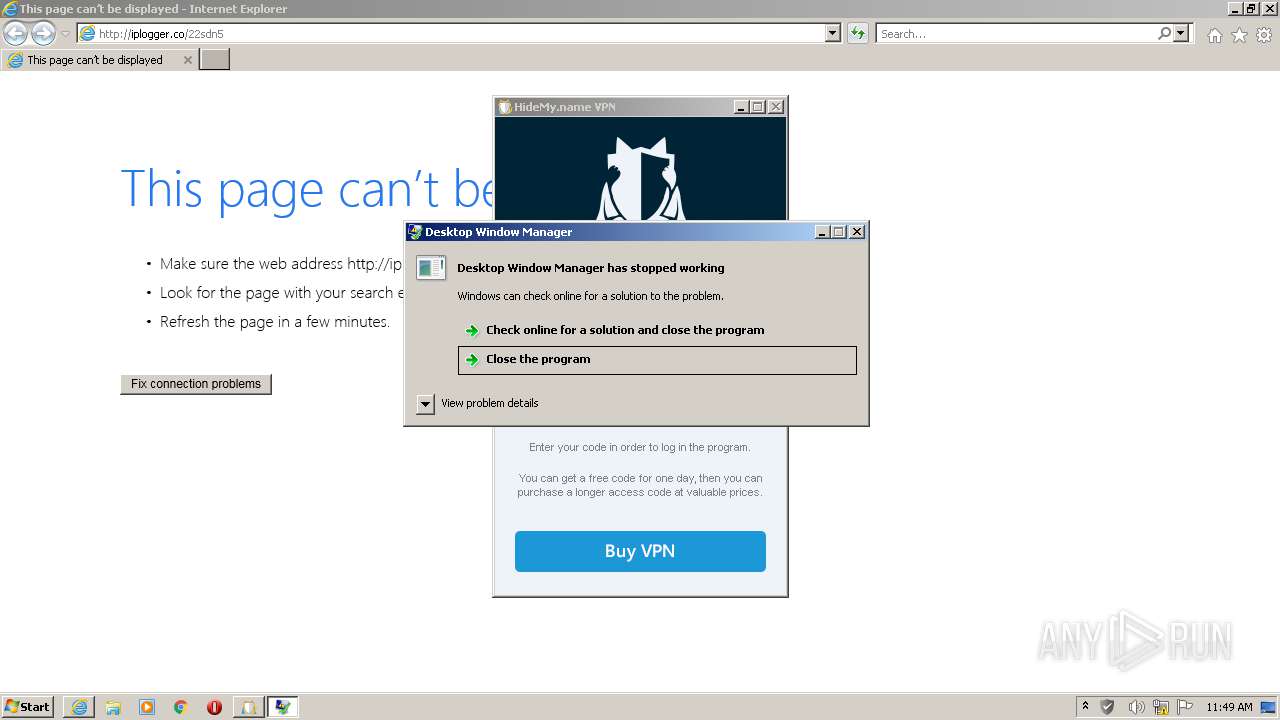
Starts Internet Explorer
- cmd.exe (PID: 2272)
Reads Environment values
- dwm.exe (PID: 2276)
Reads the cookies of Google Chrome
- seescenicelfa.exe (PID: 596)
Reads the cookies of Mozilla Firefox
- seescenicelfa.exe (PID: 596)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 1748)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 2424)
INFO
Reads the computer name
- iexplore.exe (PID: 3132)
- iexplore.exe (PID: 1748)
- nslookup.exe (PID: 592)
- nslookup.exe (PID: 1420)
- taskkill.exe (PID: 4076)
Checks supported languages
- iexplore.exe (PID: 3132)
- iexplore.exe (PID: 1748)
- nslookup.exe (PID: 592)
- nslookup.exe (PID: 1420)
- taskkill.exe (PID: 4076)
Application launched itself
- iexplore.exe (PID: 3132)
Changes internet zones settings
- iexplore.exe (PID: 3132)
Checks Windows Trust Settings
- iexplore.exe (PID: 1748)
- iexplore.exe (PID: 3132)
Reads settings of System Certificates
- iexplore.exe (PID: 1748)
- Start.exe (PID: 1012)
- iexplore.exe (PID: 3132)
- kosmix.exe (PID: 1536)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1748)
Changes settings of System certificates
- iexplore.exe (PID: 1748)
Reads internet explorer settings
- iexplore.exe (PID: 1748)
Creates files in the user directory
- iexplore.exe (PID: 1748)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (37.4) |
|---|---|---|
| .scr | | | Windows screen saver (34.5) |
| .exe | | | Win32 Executable (generic) (11.9) |
| .exe | | | Win16/32 Executable Delphi generic (5.4) |
| .exe | | | Generic Win/DOS Executable (5.2) |
EXIF
EXE
| LegalCopyright: | BROOM |
|---|---|
| FileVersion: | 1.00 |
| FileDescription: | BROOM PC Cleaner 1.00 Installation |
| CompanyName: | BROOM |
| Comments: | - |
| CharacterSet: | Windows, Latin1 |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 0.0.0.0 |
| FileVersionNumber: | 1.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x25468 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 314880 |
| CodeSize: | 148992 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| Comments: | - |
| CompanyName: | BROOM |
| FileDescription: | BROOM PC Cleaner 1.00 Installation |
| FileVersion: | 1.00 |
| LegalCopyright: | BROOM |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x000244CC | 0x00024600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.59443 |
DATA | 0x00026000 | 0x00002894 | 0x00002A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.79376 |
BSS | 0x00029000 | 0x000010F5 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0002B000 | 0x00001798 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.88555 |
.tls | 0x0002D000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0002E000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.204488 |
.reloc | 0x0002F000 | 0x00001884 | 0x00001A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.58665 |
.rsrc | 0x00031000 | 0x00046F60 | 0x00047000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 1.82559 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.93923 | 886 | UNKNOWN | Russian - Russia | RT_MANIFEST |
50 | 2.70313 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
51 | 2.10652 | 2440 | UNKNOWN | UNKNOWN | RT_ICON |
52 | 2.14611 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
53 | 2.15952 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
54 | 1.73674 | 270376 | UNKNOWN | UNKNOWN | RT_ICON |
DVCLAL | 4 | 16 | UNKNOWN | UNKNOWN | RT_RCDATA |
PACKAGEINFO | 5.28362 | 272 | UNKNOWN | UNKNOWN | RT_RCDATA |
MAINICON | 2.75922 | 76 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
advapi32.dll |
cabinet.dll |
comctl32.dll |
gdi32.dll |
kernel32.dll |
ole32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
winmm.dll |
Total processes
60
Monitored processes
14
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 592 | nslookup -querytype=A -timeout=1 justapi.info 208.67.222.222 | C:\Windows\system32\nslookup.exe | Start.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: nslookup Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 596 | "C:\Program Files\BROOM\BROOM PC Cleaner\seescenicelfa.exe" /s | C:\Program Files\BROOM\BROOM PC Cleaner\seescenicelfa.exe | abba.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
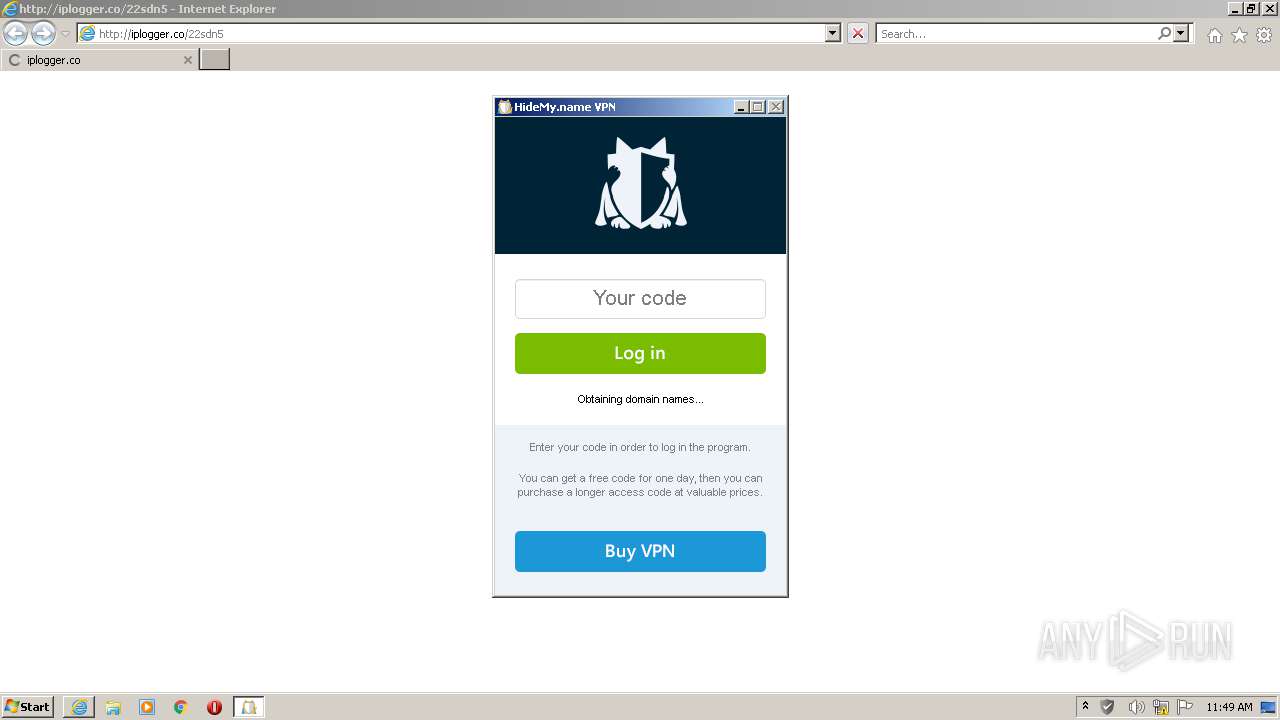
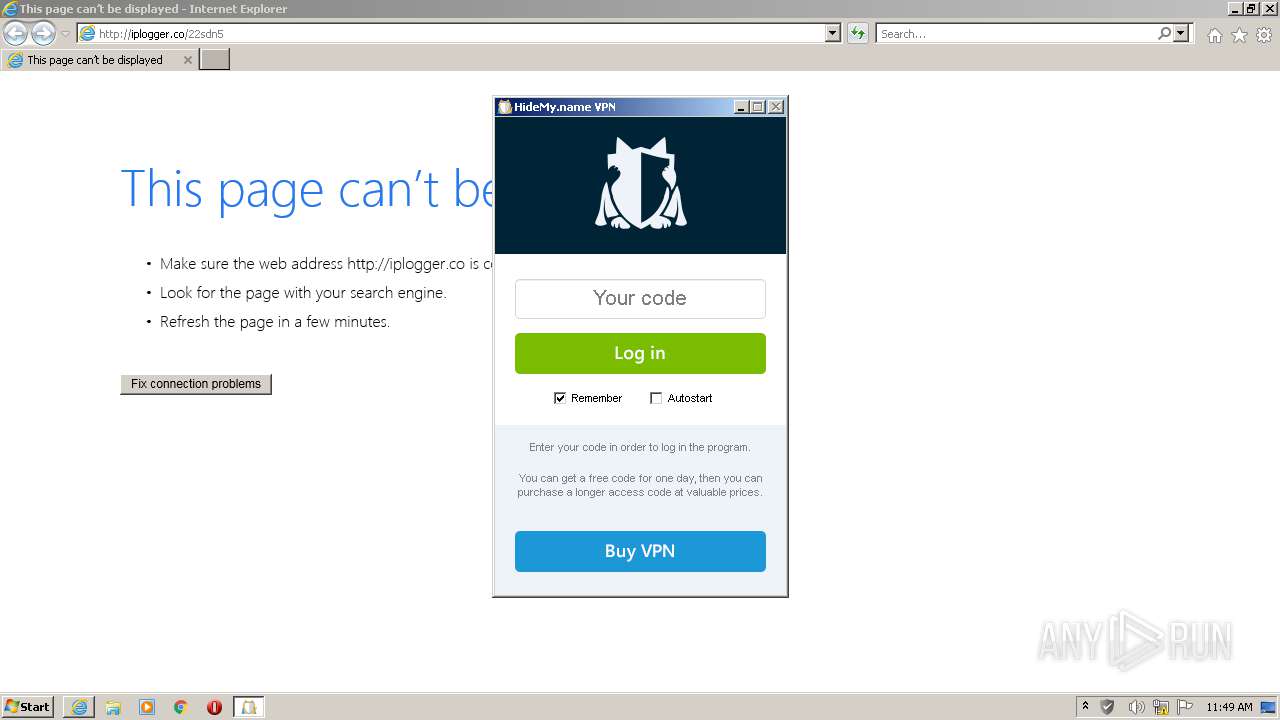
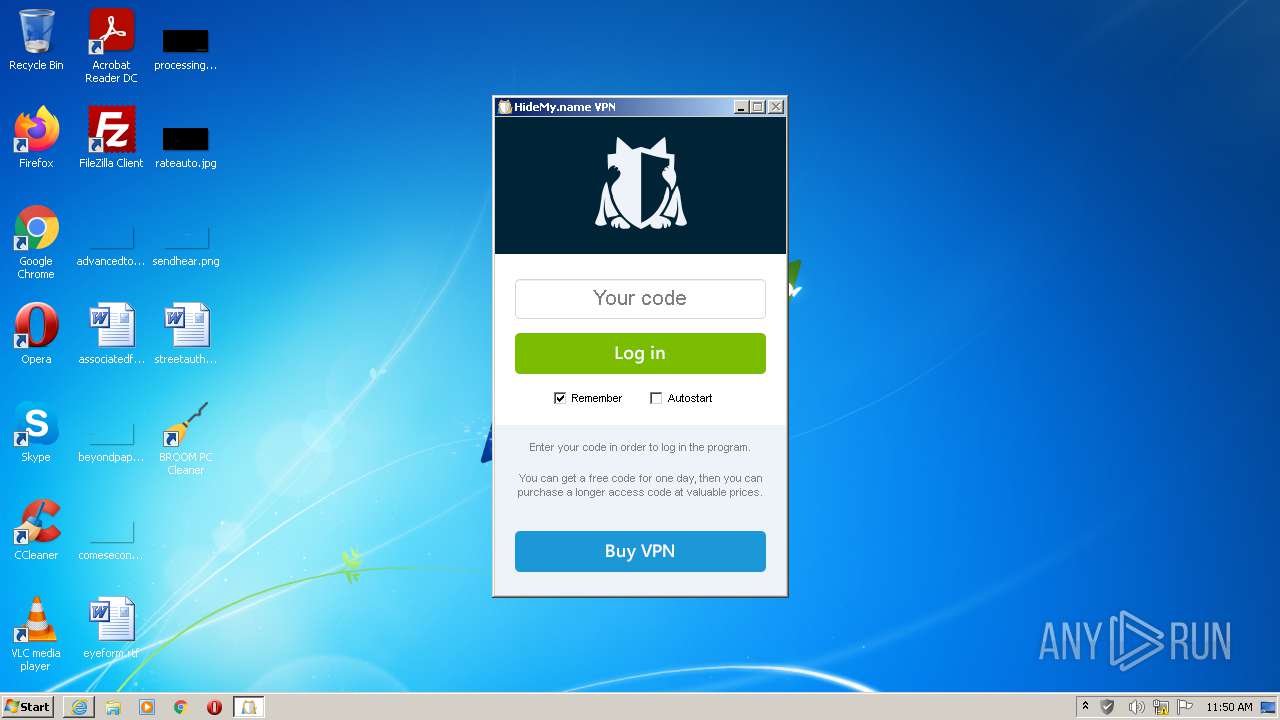
| 1012 | "C:\Program Files\tex\tex\Start.exe" | C:\Program Files\tex\tex\Start.exe | pub4.exe | ||||||||||||
User: admin Company: inCloak Network Ltd. Integrity Level: HIGH Exit code: 0 Version: 1.44 Modules
| |||||||||||||||
| 1420 | nslookup -querytype=A -timeout=1 checker.justapi.info 208.67.222.222 | C:\Windows\system32\nslookup.exe | Start.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: nslookup Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1536 | "C:\Program Files\BROOM\BROOM PC Cleaner\kosmix.exe" /mixfive | C:\Program Files\BROOM\BROOM PC Cleaner\kosmix.exe | abba.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 1748 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3132 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2152 | "C:\Program Files\BROOM\BROOM PC Cleaner\pub4.exe" | C:\Program Files\BROOM\BROOM PC Cleaner\pub4.exe | abba.exe | ||||||||||||
User: admin Company: tex Integrity Level: HIGH Description: tex 1.00 Installation Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 2272 | C:\Windows\system32\cmd.exe /c ""C:\Program Files\BROOM\BROOM PC Cleaner\stats.bat" " | C:\Windows\system32\cmd.exe | — | abba.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2276 | "C:\Program Files\BROOM\BROOM PC Cleaner\dwm.exe" | C:\Program Files\BROOM\BROOM PC Cleaner\dwm.exe | abba.exe | ||||||||||||
User: admin Company: (c) Microsoft Corporation Integrity Level: HIGH Description: Desktop Window Manager Exit code: 3762504530 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2424 | "C:\Windows\System32\cmd.exe" /c taskkill /im "kosmix.exe" /f & erase "C:\Program Files\BROOM\BROOM PC Cleaner\kosmix.exe" & exit | C:\Windows\System32\cmd.exe | — | kosmix.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
20 183
Read events
19 935
Write events
248
Delete events
0
Modification events
| (PID) Process: | (3956) abba.exe | Key: | HKEY_CURRENT_USER\Software\BROOM |
| Operation: | write | Name: | Key |
Value: YZWEN-98MCX-Z9FV1-9TUSW | |||
| (PID) Process: | (3956) abba.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\BROOM PC Cleaner 1.00 |
| Operation: | write | Name: | DisplayName |
Value: BROOM PC Cleaner 1.00 | |||
| (PID) Process: | (3956) abba.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\BROOM PC Cleaner 1.00 |
| Operation: | write | Name: | DisplayVersion |
Value: 1.00 | |||
| (PID) Process: | (3956) abba.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\BROOM PC Cleaner 1.00 |
| Operation: | write | Name: | VersionMajor |
Value: 1 | |||
| (PID) Process: | (3956) abba.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\BROOM PC Cleaner 1.00 |
| Operation: | write | Name: | VersionMinor |
Value: 0 | |||
| (PID) Process: | (3956) abba.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\BROOM PC Cleaner 1.00 |
| Operation: | write | Name: | Publisher |
Value: BROOM | |||
| (PID) Process: | (3956) abba.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\BROOM PC Cleaner 1.00 |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files\BROOM\BROOM PC Cleaner\Uninstall.exe | |||
| (PID) Process: | (3956) abba.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\BROOM PC Cleaner 1.00 |
| Operation: | write | Name: | UninstallString |
Value: C:\Program Files\BROOM\BROOM PC Cleaner\Uninstall.exe | |||
| (PID) Process: | (3956) abba.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\BROOM PC Cleaner 1.00 |
| Operation: | write | Name: | URLInfoAbout |
Value: https://www.broomcleaner.com | |||
| (PID) Process: | (3956) abba.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\BROOM PC Cleaner 1.00 |
| Operation: | write | Name: | HelpLink |
Value: mailto:support@broomcleaner.com | |||
Executable files
35
Suspicious files
22
Text files
329
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3956 | abba.exe | C:\Users\admin\AppData\Local\Temp\$inst\temp_0.tmp | — | |
MD5:— | SHA256:— | |||
| 2152 | pub4.exe | C:\Users\admin\AppData\Local\Temp\$inst\temp_0.tmp | — | |
MD5:— | SHA256:— | |||
| 3956 | abba.exe | C:\Program Files\BROOM\BROOM PC Cleaner\Broom.exe | executable | |
MD5:— | SHA256:— | |||
| 3956 | abba.exe | C:\Program Files\BROOM\BROOM PC Cleaner\Readme.txt | text | |
MD5:— | SHA256:— | |||
| 3956 | abba.exe | C:\Program Files\BROOM\BROOM PC Cleaner\broom-64.png | image | |
MD5:— | SHA256:— | |||
| 3956 | abba.exe | C:\Program Files\BROOM\BROOM PC Cleaner\Changes.txt | text | |
MD5:— | SHA256:— | |||
| 3956 | abba.exe | C:\Program Files\BROOM\BROOM PC Cleaner\License.txt | text | |
MD5:— | SHA256:— | |||
| 3956 | abba.exe | C:\Program Files\BROOM\BROOM PC Cleaner\dwm.exe | executable | |
MD5:— | SHA256:— | |||
| 3956 | abba.exe | C:\Program Files\BROOM\BROOM PC Cleaner\seescenicelfa.exe | executable | |
MD5:— | SHA256:— | |||
| 3956 | abba.exe | C:\Program Files\BROOM\BROOM PC Cleaner\kosmix.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
28
DNS requests
20
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1536 | kosmix.exe | GET | 301 | 104.21.19.200:80 | http://freegeoip.app/json | US | — | — | whitelisted |
3132 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
3132 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
1536 | kosmix.exe | GET | 301 | 104.26.13.31:80 | http://api.ip.sb/geoip | US | html | 162 b | whitelisted |
1748 | iexplore.exe | GET | 301 | 148.251.234.93:80 | http://iplogger.co/22sdn5 | DE | html | 178 b | shared |
1748 | iexplore.exe | GET | 200 | 23.45.105.185:80 | http://x1.c.lencr.org/ | NL | der | 717 b | whitelisted |
1748 | iexplore.exe | GET | 200 | 2.16.186.81:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?4d3545589191afa0 | unknown | compressed | 4.70 Kb | whitelisted |
1748 | iexplore.exe | GET | 200 | 2.16.186.81:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?828c203937be3c5e | unknown | compressed | 59.9 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1748 | iexplore.exe | 148.251.234.93:80 | iplogger.co | Hetzner Online GmbH | DE | malicious |
1748 | iexplore.exe | 148.251.234.83:443 | iplogger.org | Hetzner Online GmbH | DE | malicious |
1012 | Start.exe | 104.25.209.23:443 | — | Cloudflare Inc | US | shared |
3132 | iexplore.exe | 13.107.21.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
1012 | Start.exe | 104.26.8.174:443 | — | Cloudflare Inc | US | suspicious |
3132 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1536 | kosmix.exe | 104.26.13.31:443 | api.ip.sb | Cloudflare Inc | US | suspicious |
1536 | kosmix.exe | 104.26.13.31:80 | api.ip.sb | Cloudflare Inc | US | suspicious |
— | — | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3132 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
iplogger.co |
| shared |
uploadbase.in |
| malicious |
www.eodeysua.com |
| unknown |
iplogger.org |
| shared |
ctldl.windowsupdate.com |
| whitelisted |
222.222.67.208.in-addr.arpa |
| unknown |
justapi.info |
| suspicious |
checker.justapi.info |
| suspicious |
incloaknetwork.com |
| unknown |
x1.c.lencr.org |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1012 | Start.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
1012 | Start.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
1012 | Start.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
1012 | Start.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
10 ETPRO signatures available at the full report