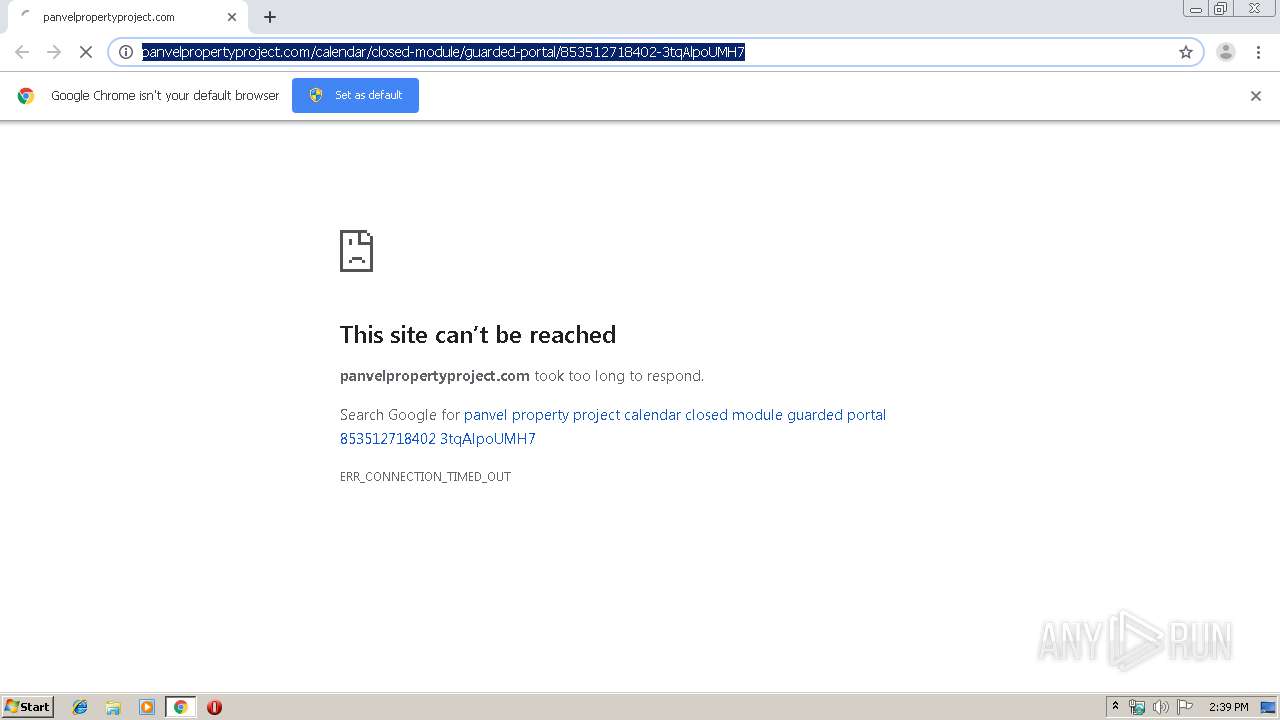
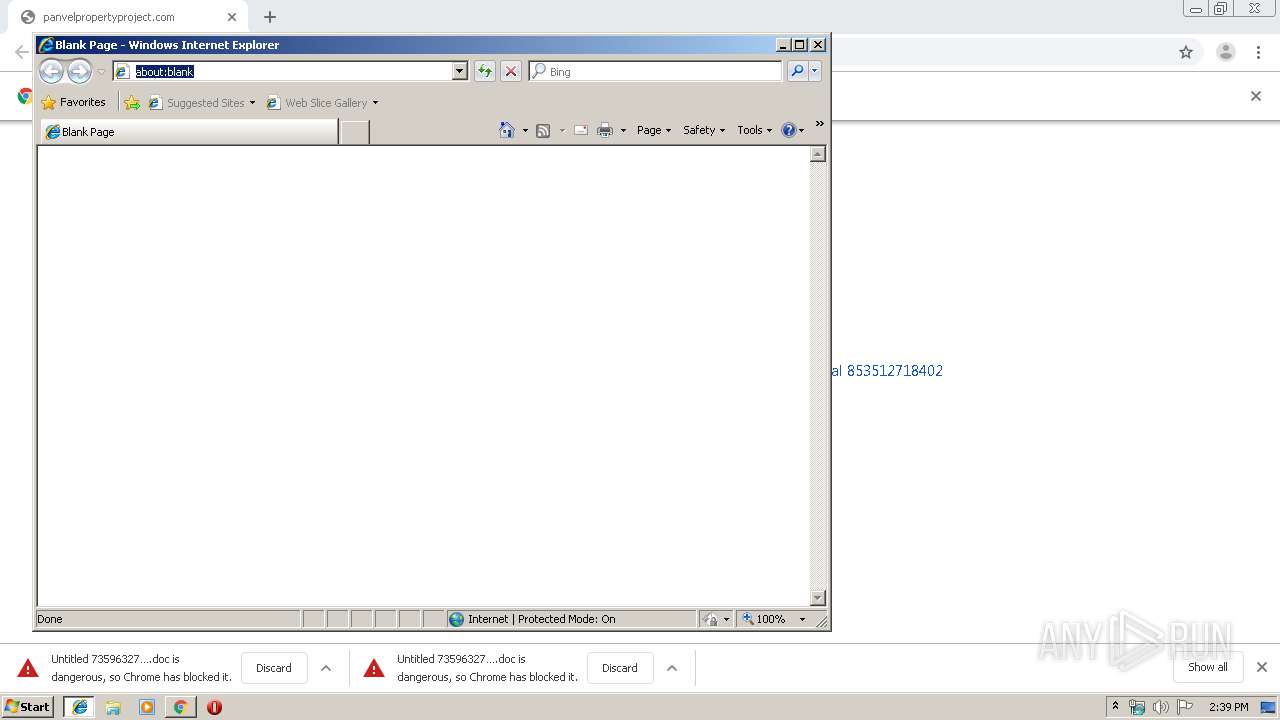
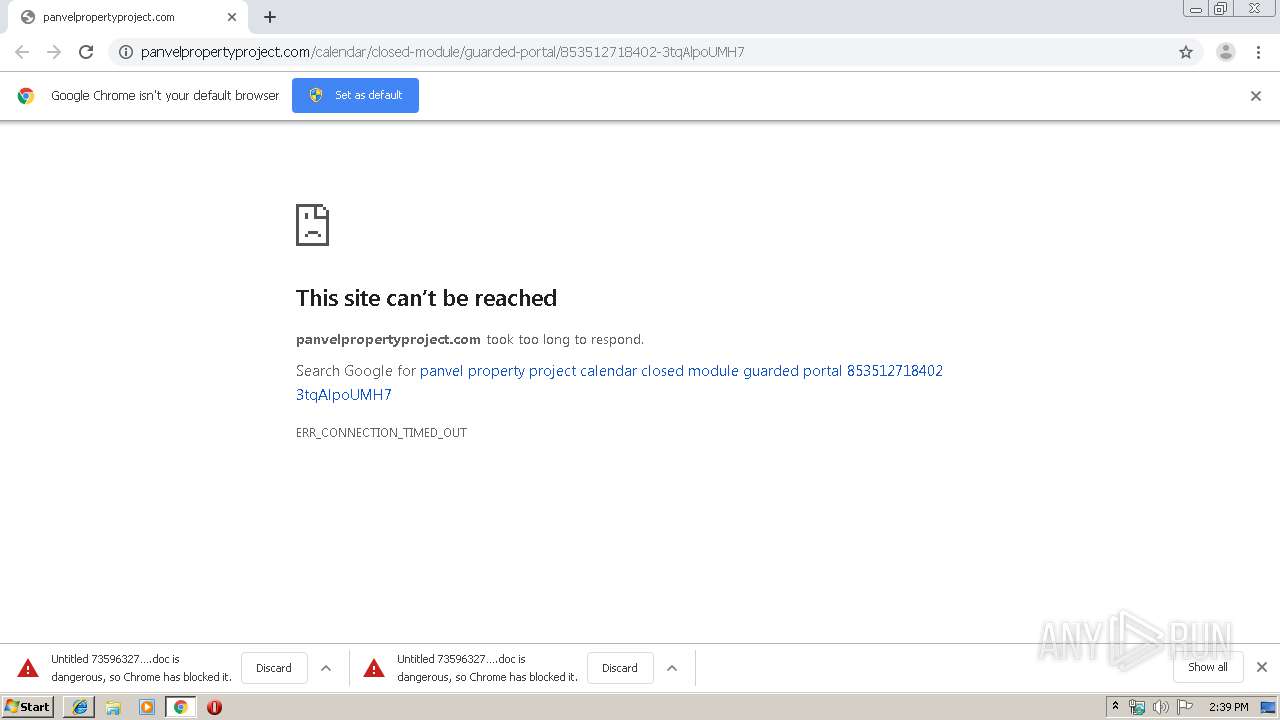
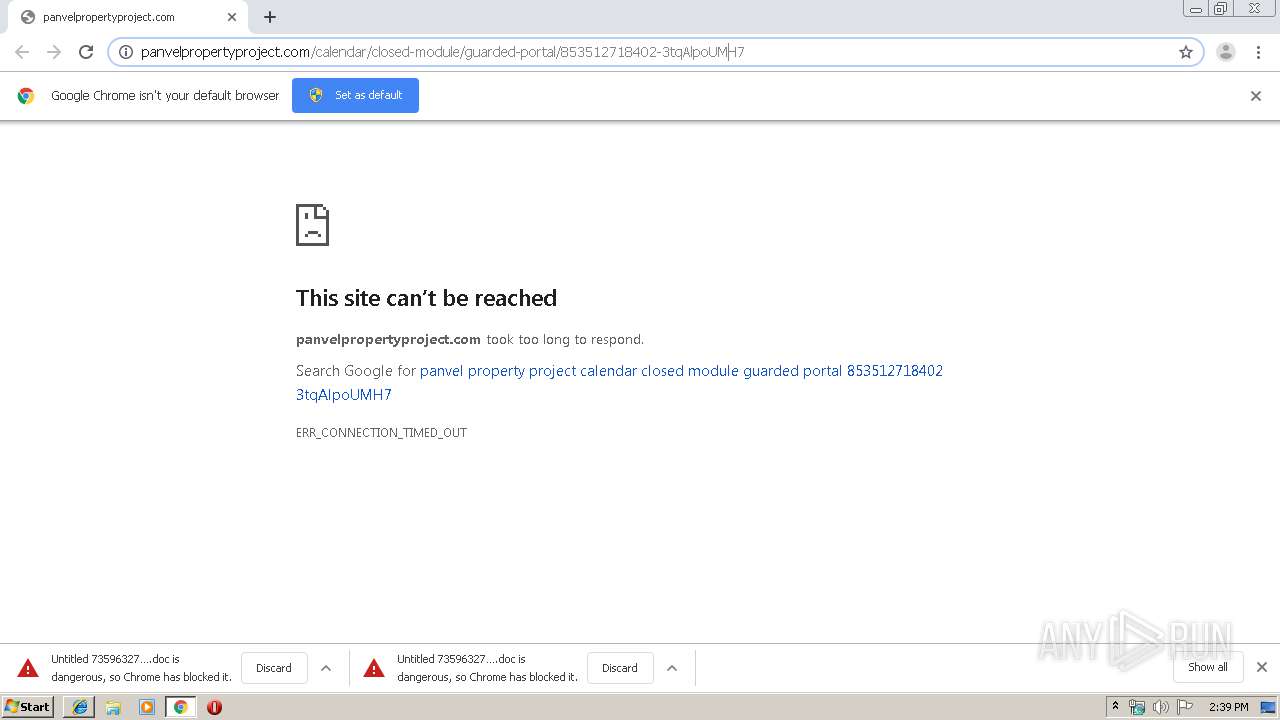
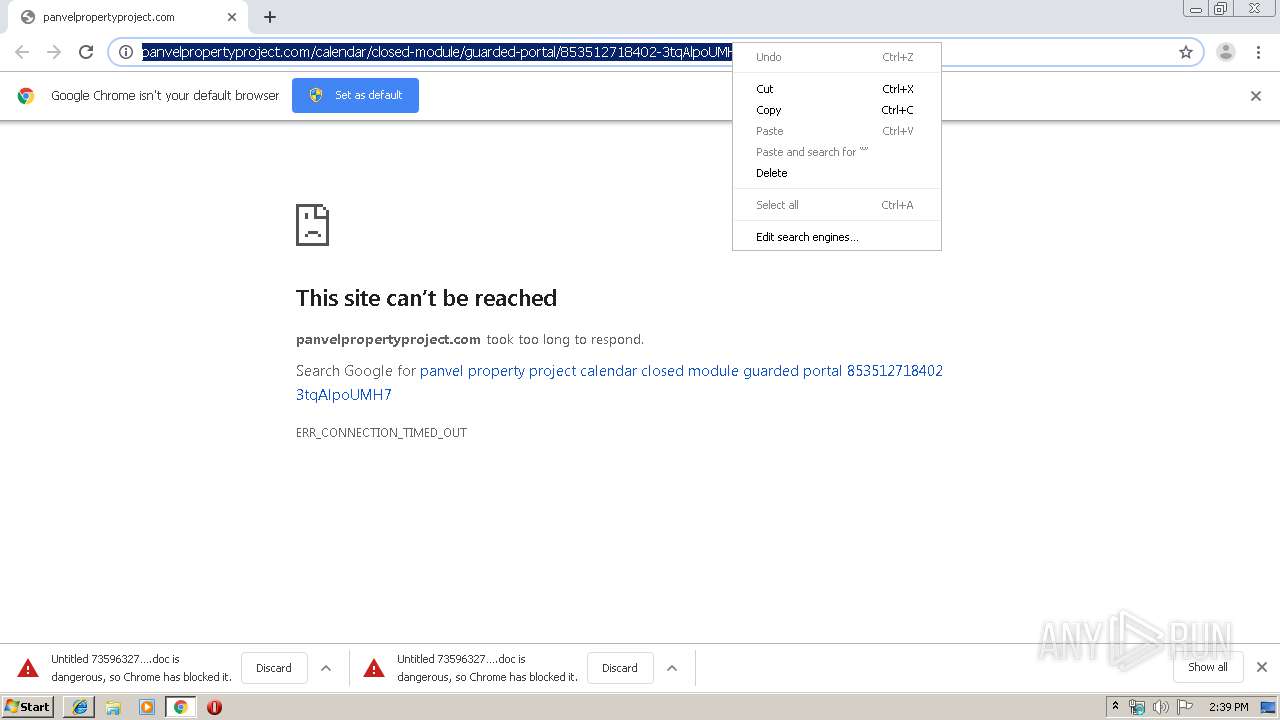
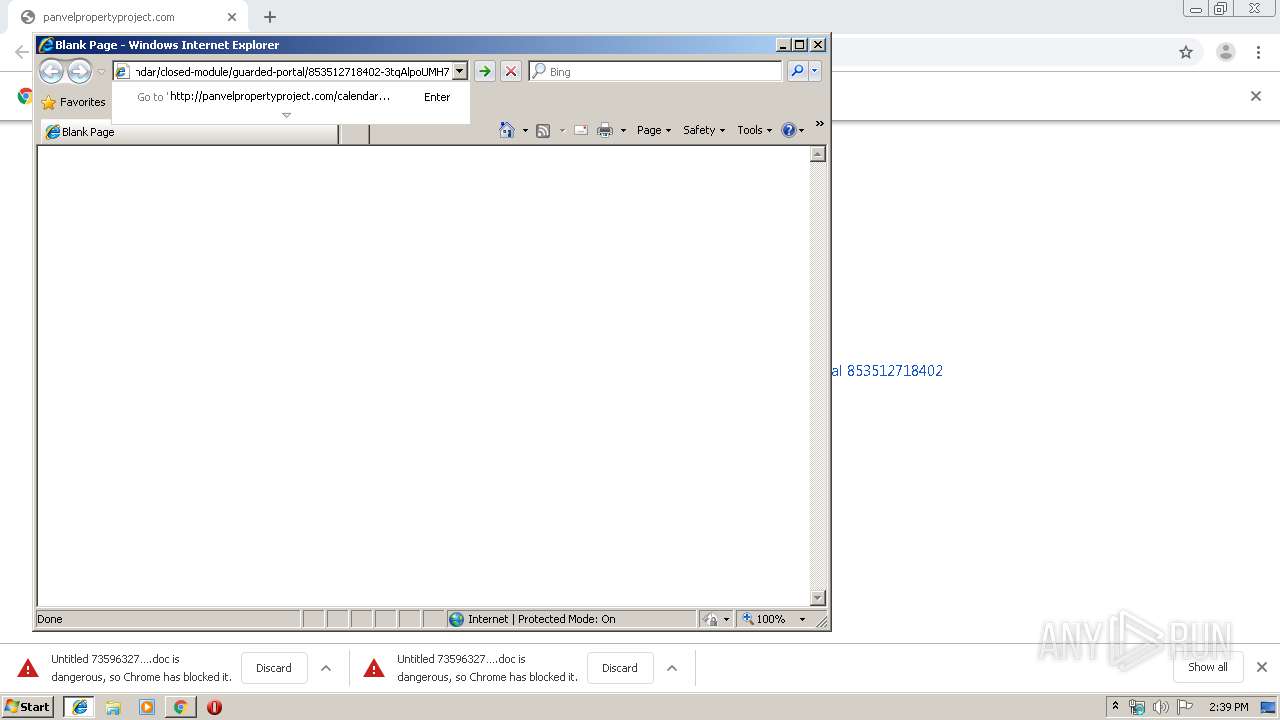
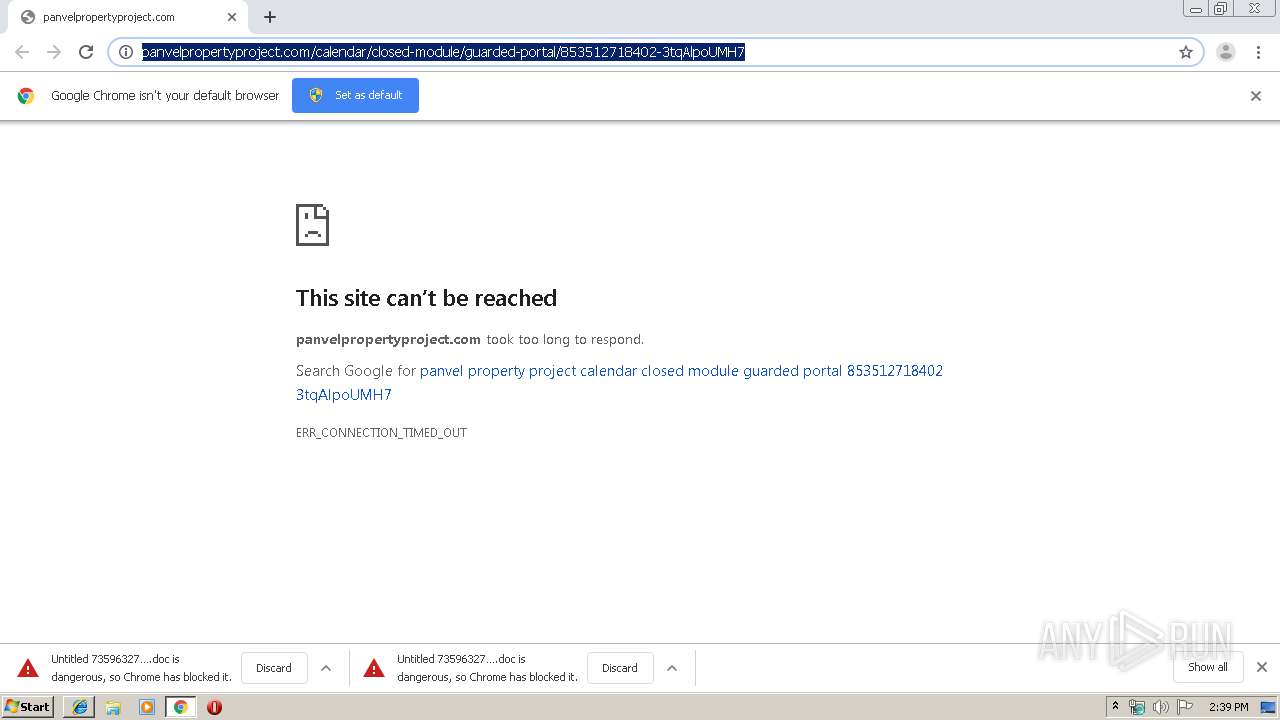
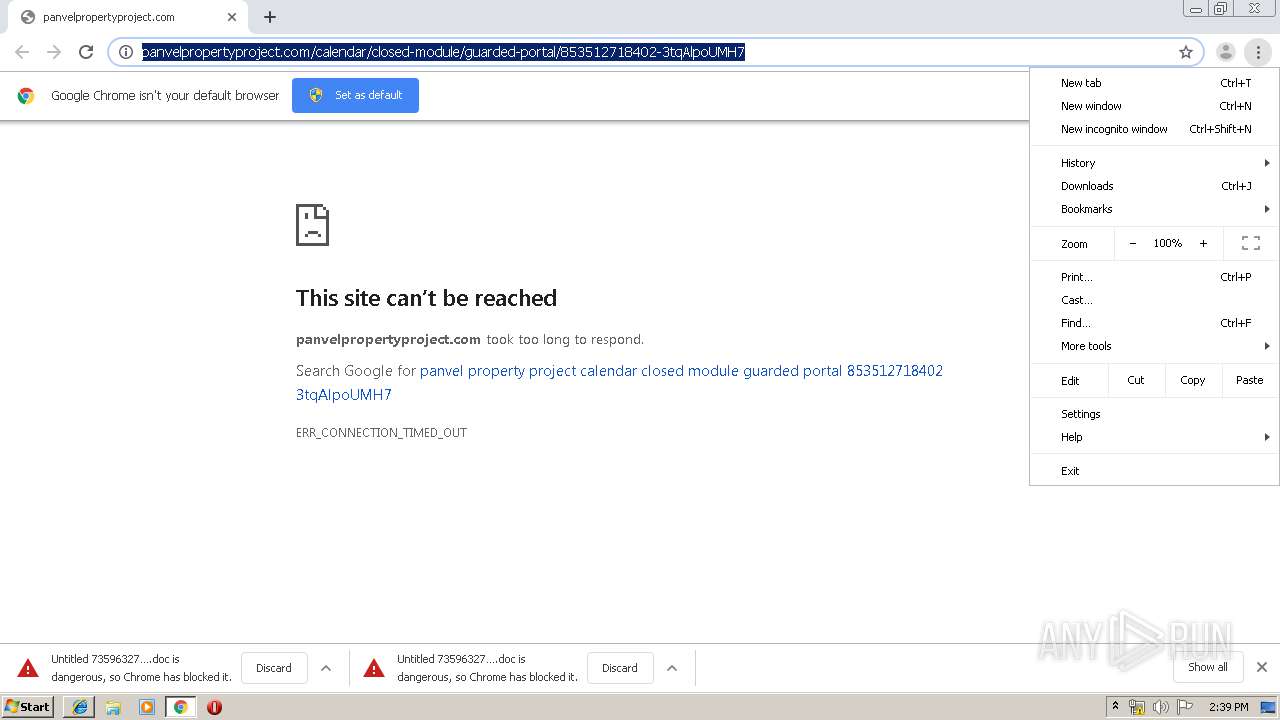
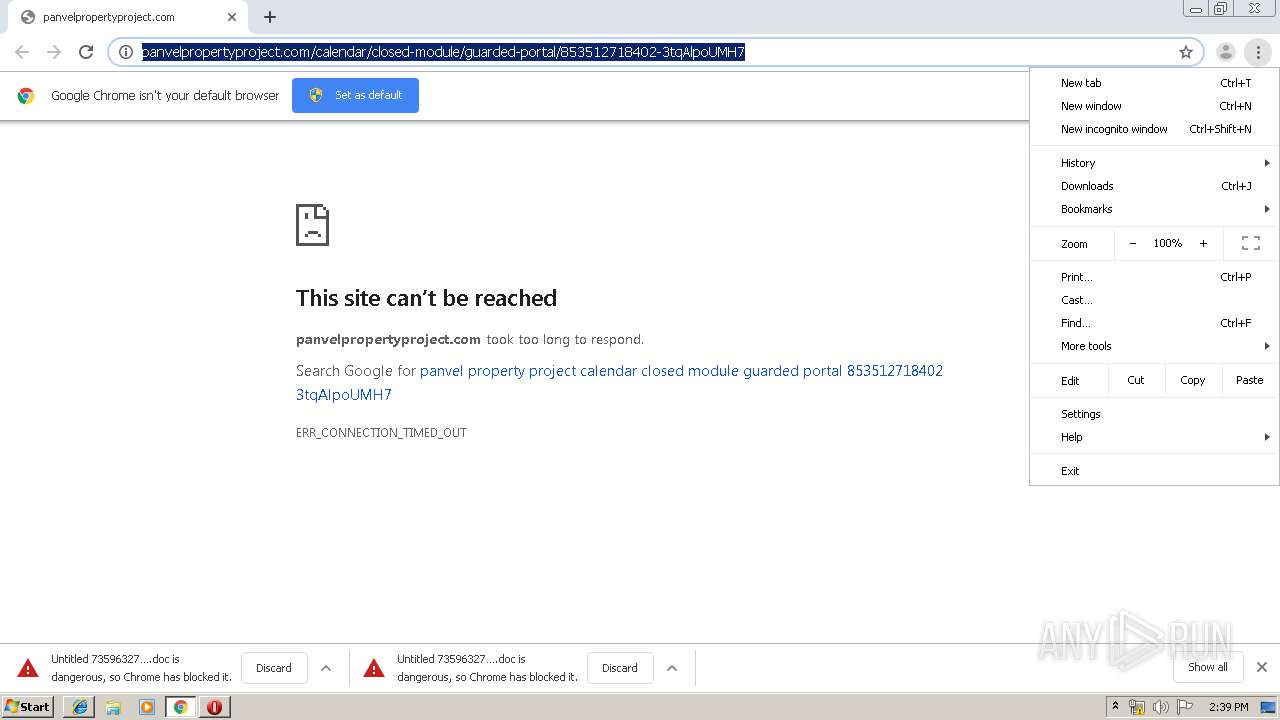
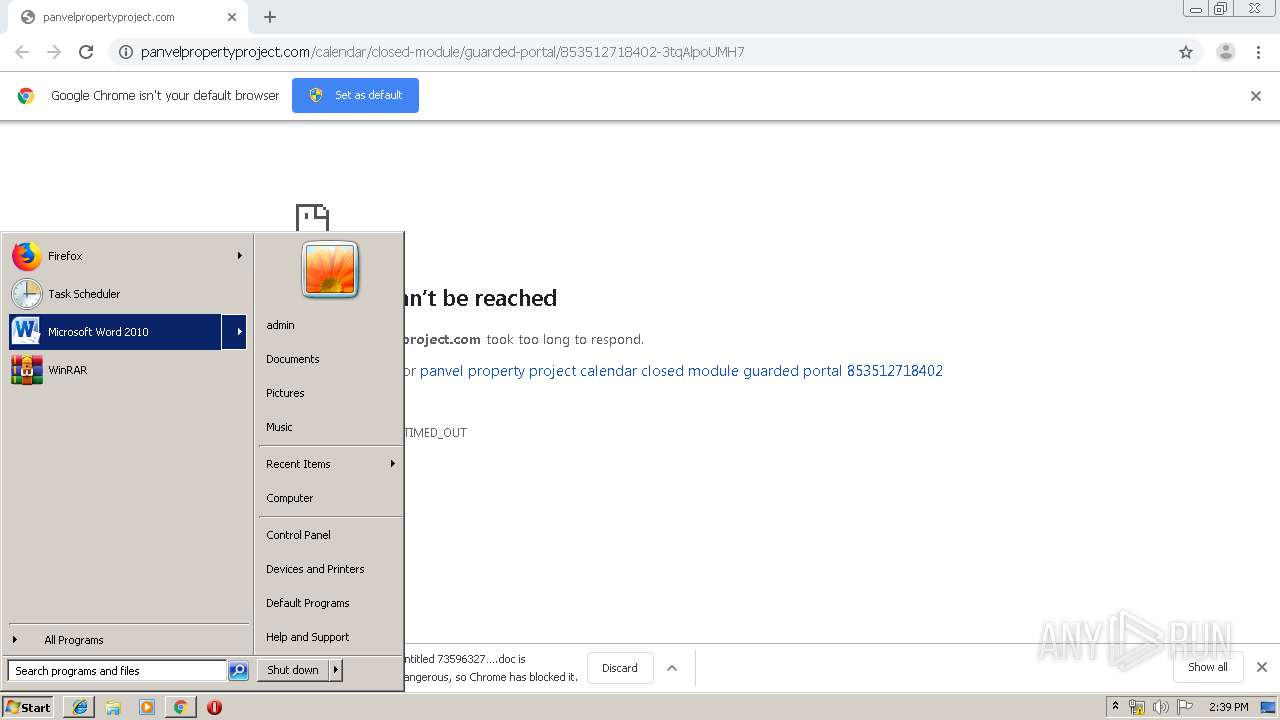
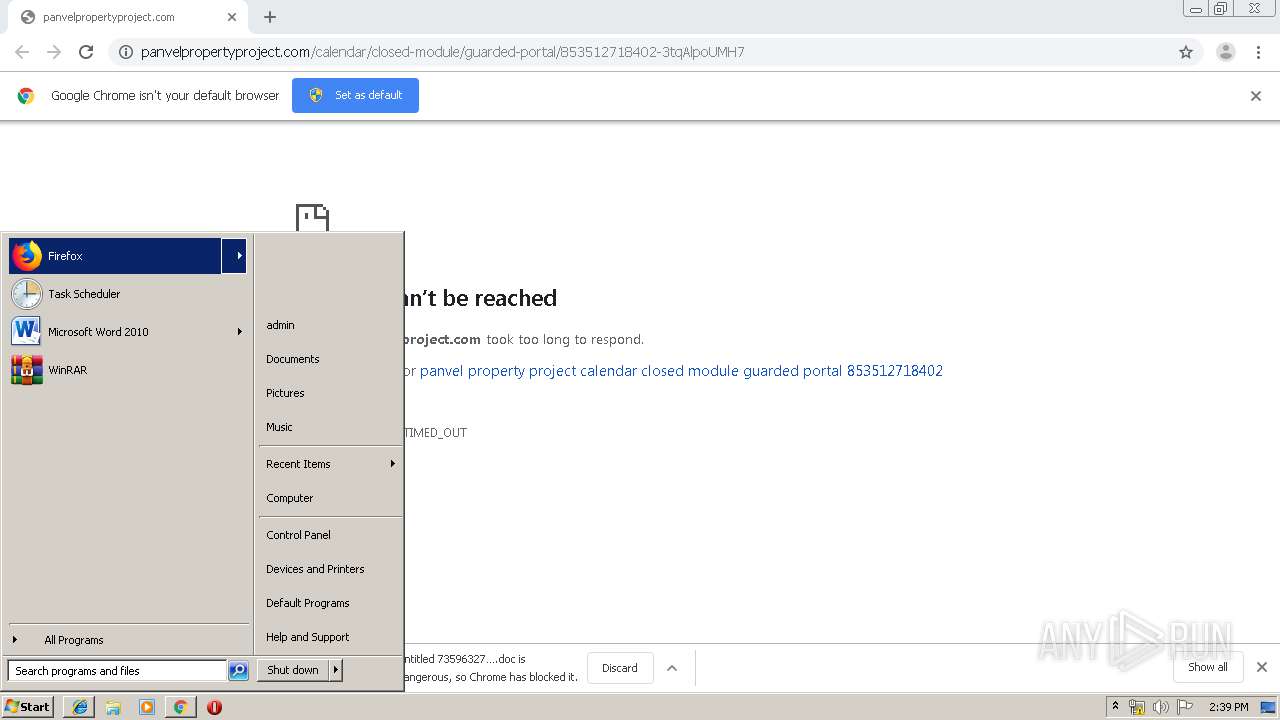
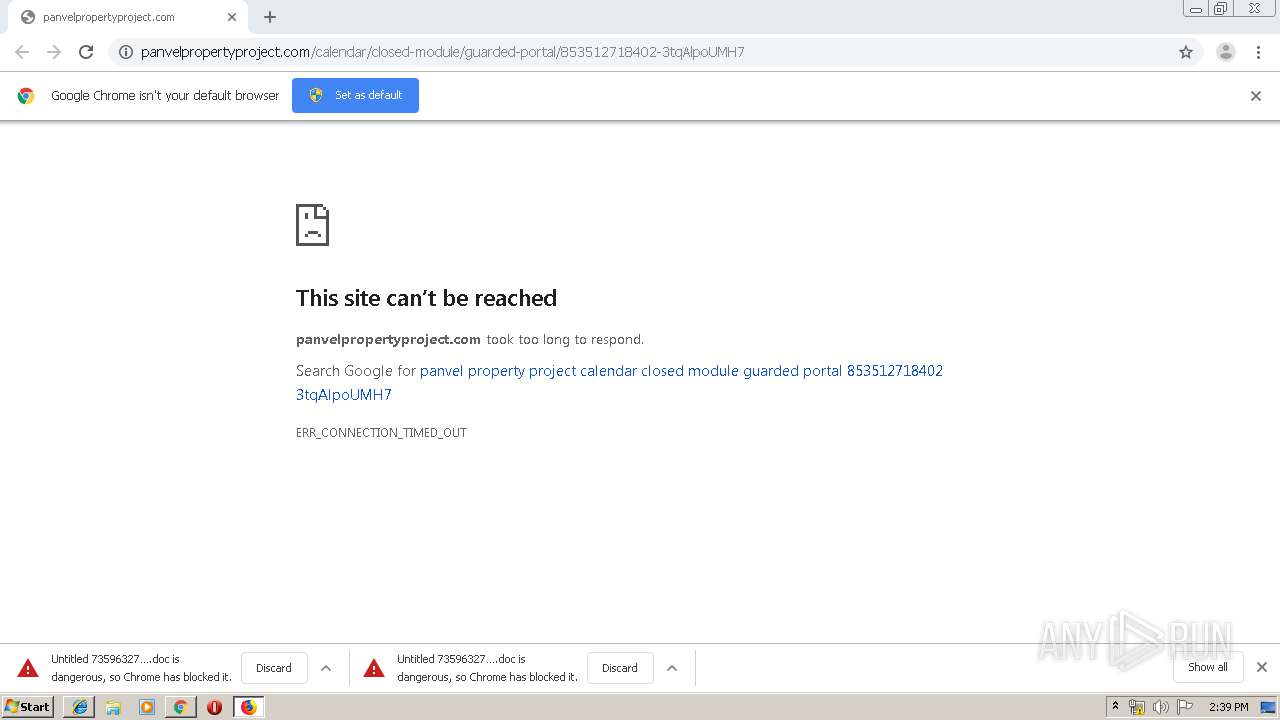
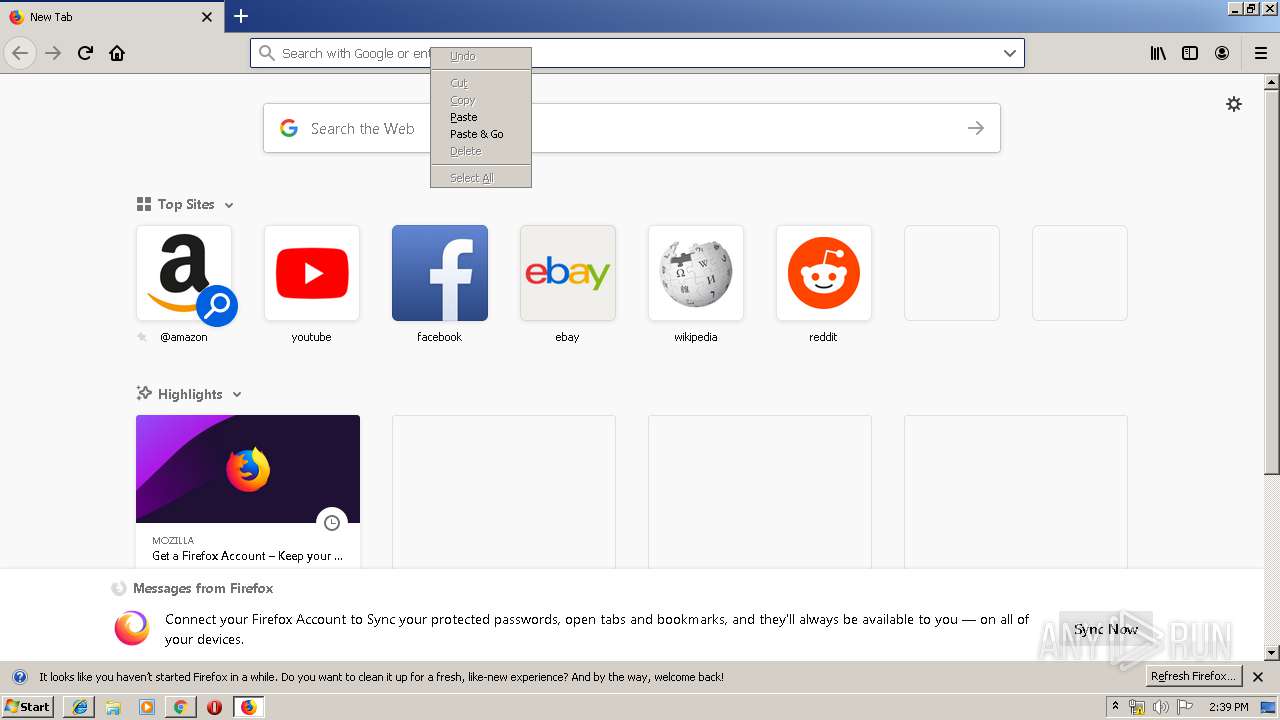
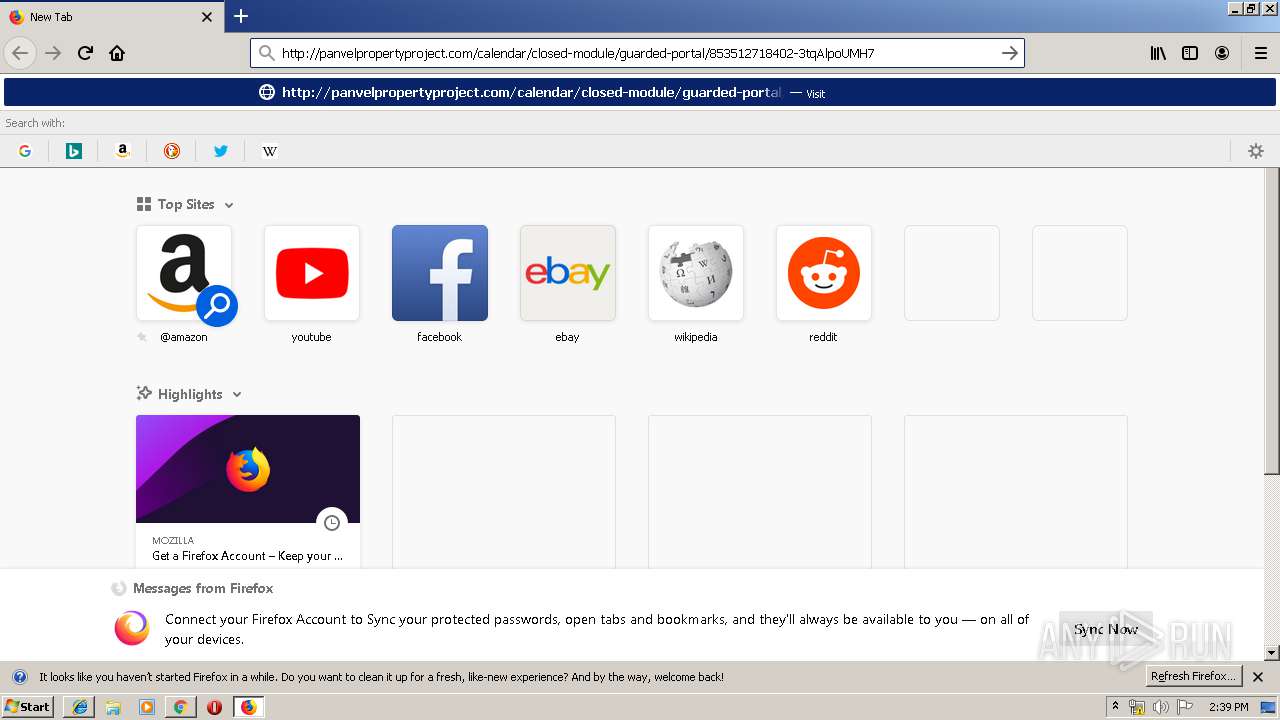
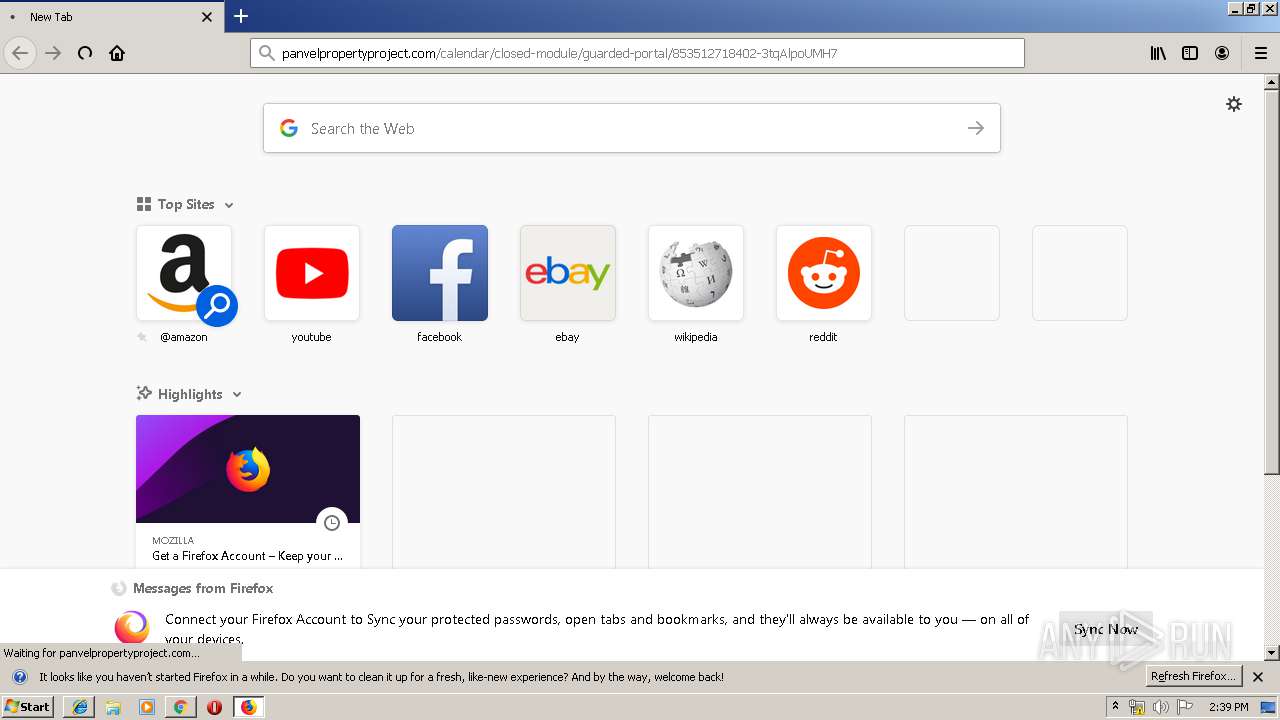
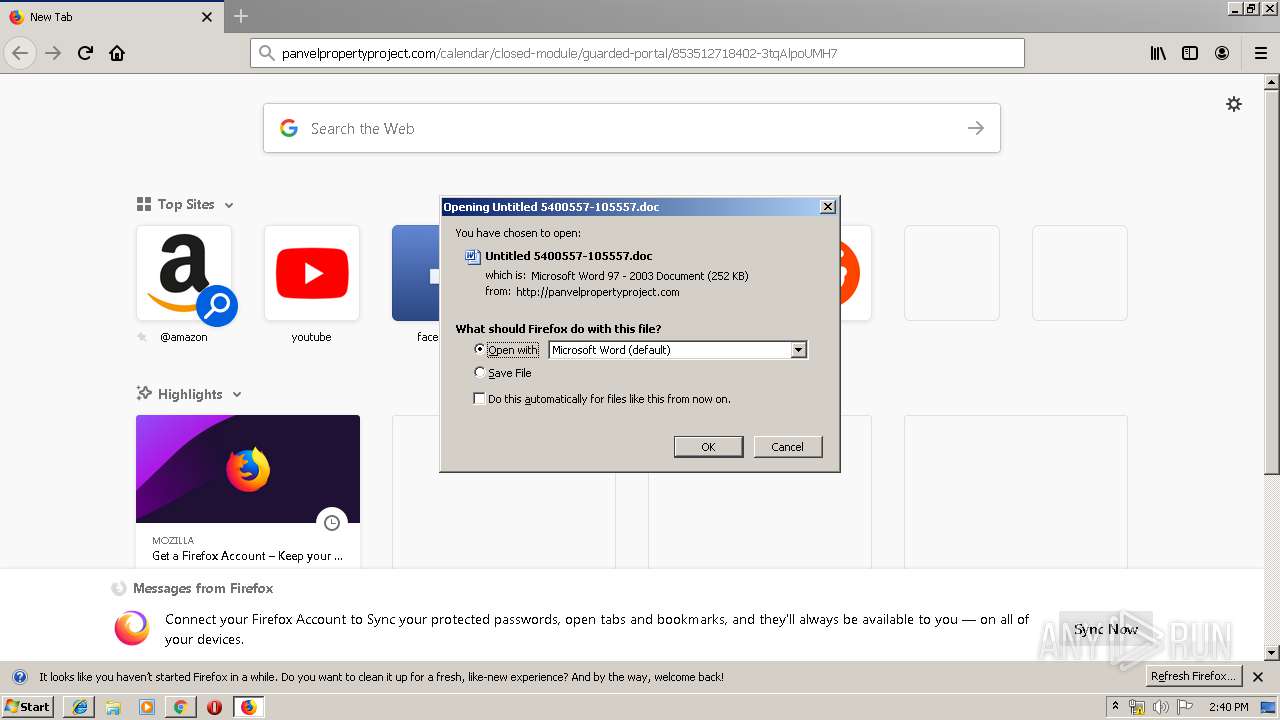
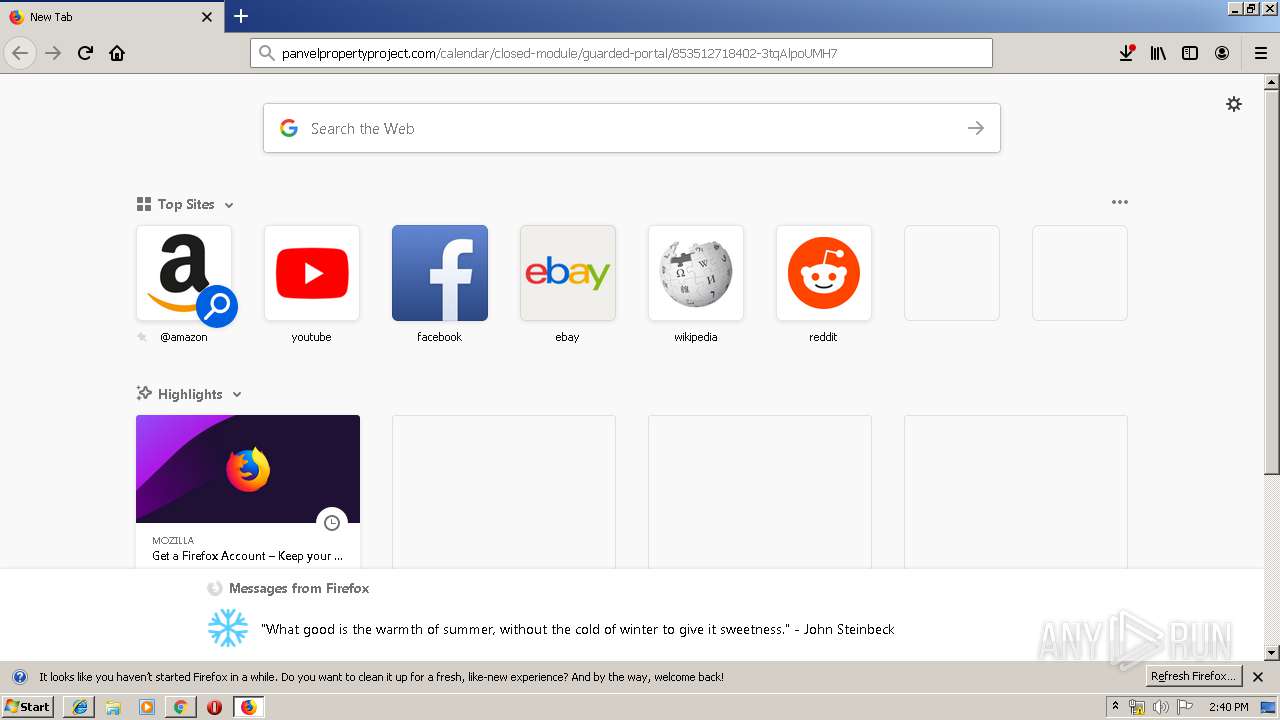
| URL: | http://panvelpropertyproject.com/calendar/closed-module/guarded-portal/853512718402-3tqAlpoUMH7 |
| Full analysis: | https://app.any.run/tasks/4ada16cb-1b4a-4dc4-aa30-bea47d1101ad |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | January 17, 2020, 14:38:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 8AC1096EB0DE7C5D983CB16055494163 |
| SHA1: | 764F480ED0FD2597EAE63AD9264C042E044711EC |
| SHA256: | 42553666C668365E4E0C6E45BEE4A8BF77967CEA3BF29190A3A6D72C2FD8886E |
| SSDEEP: | 3:N1KOELIVXpeUtyKjI3W1BxjBkoQEESECUhyAV8g:CODVXAUtZU3W1Bt/pt9g |
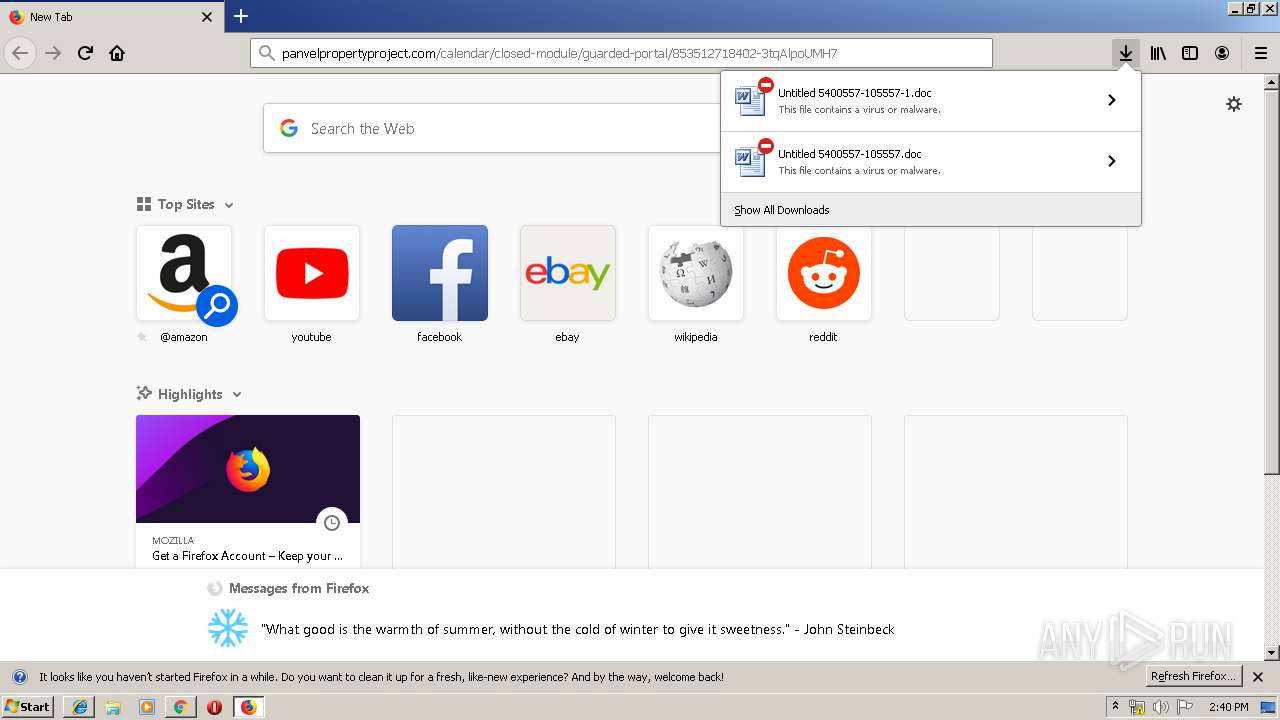
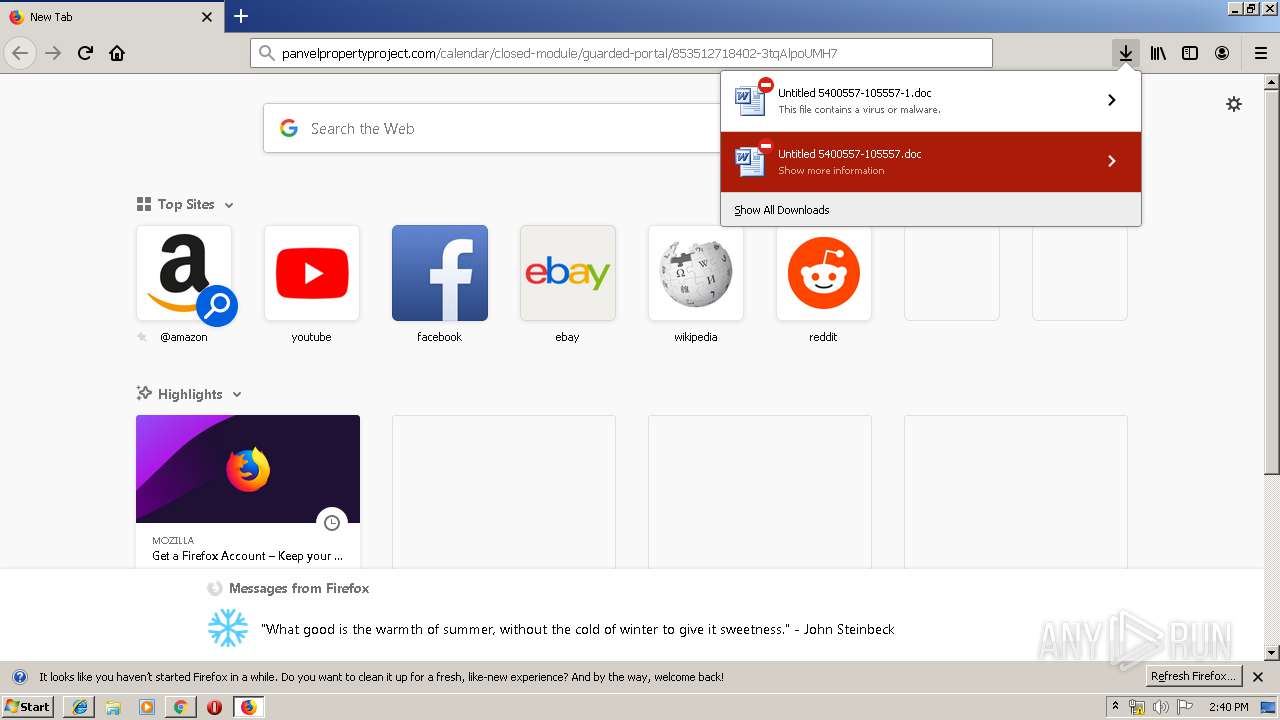
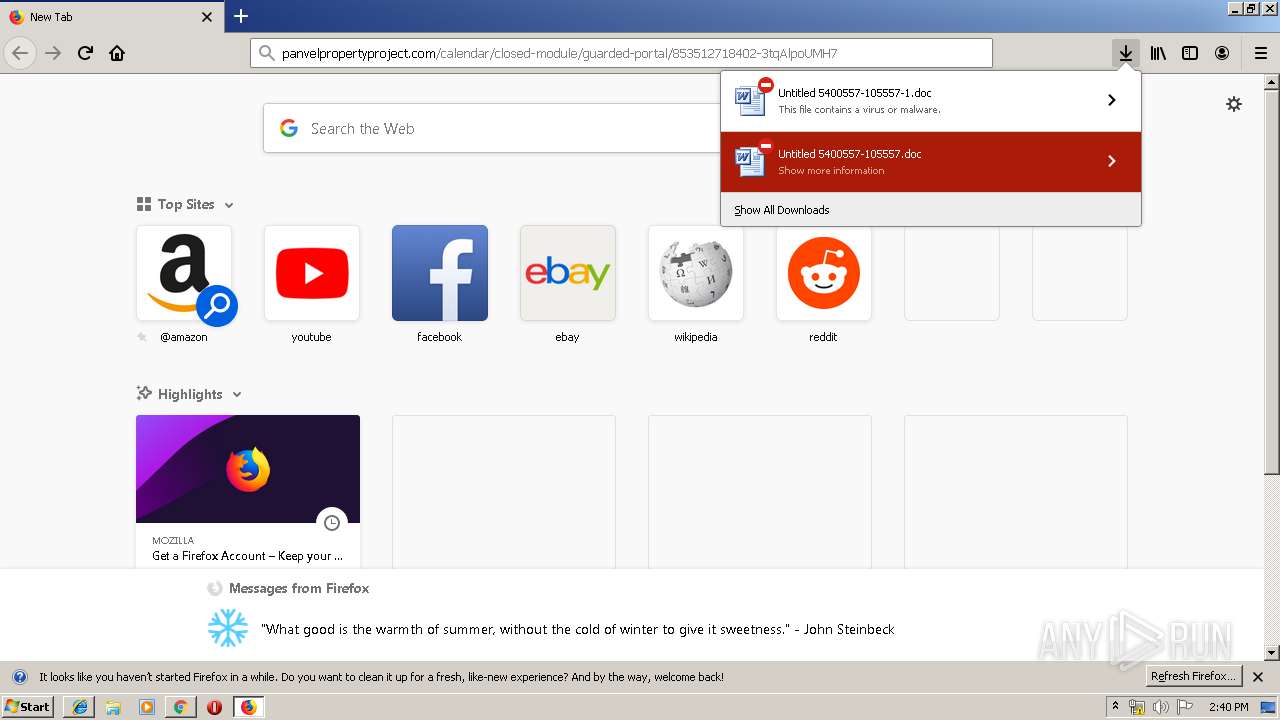
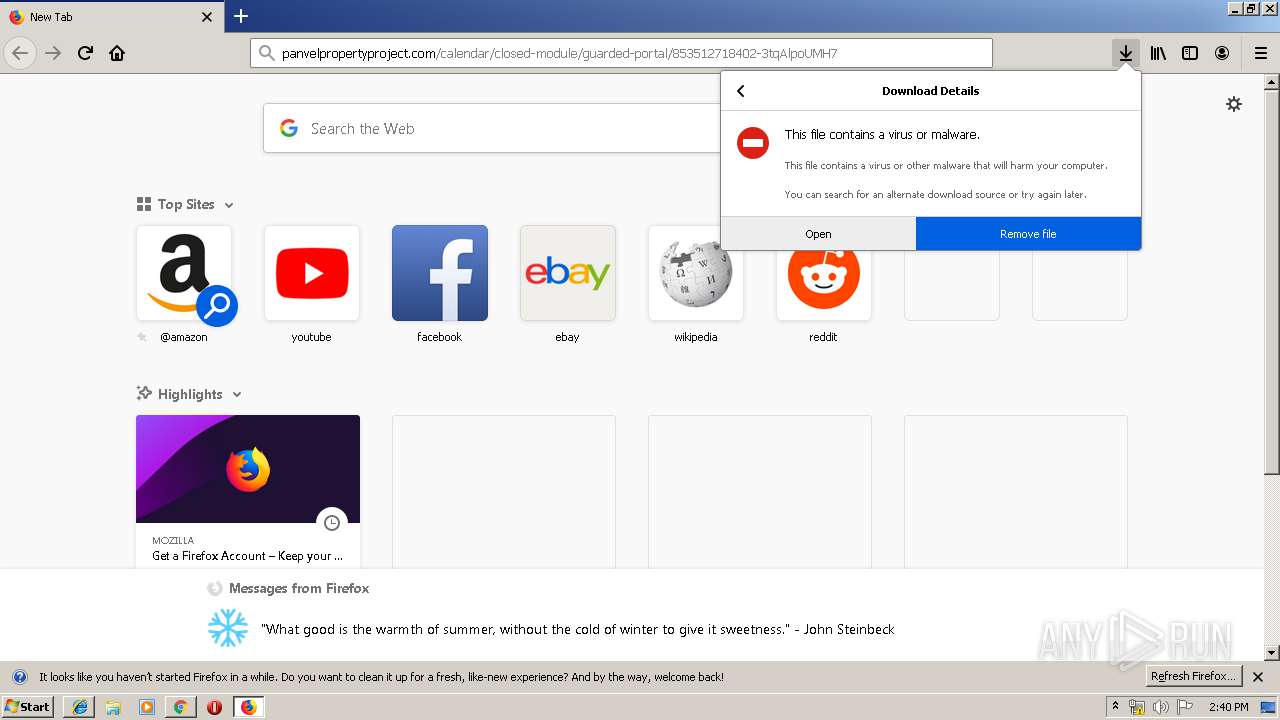
MALICIOUS
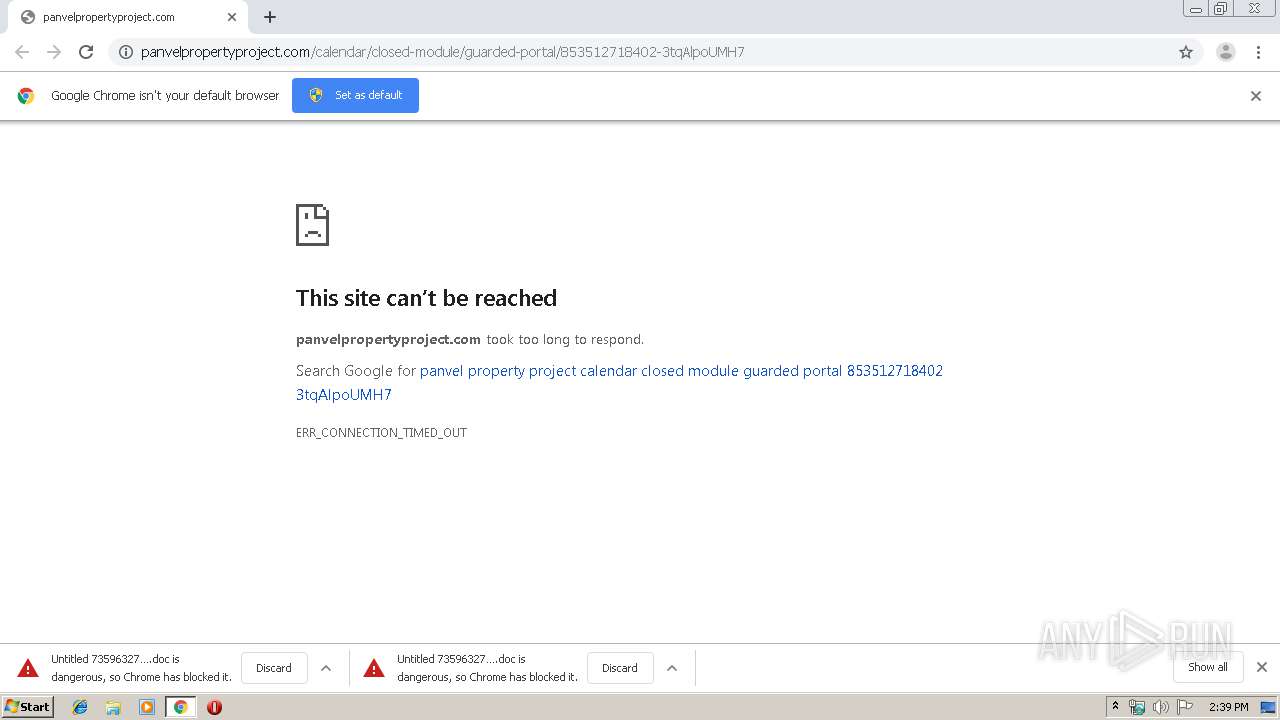
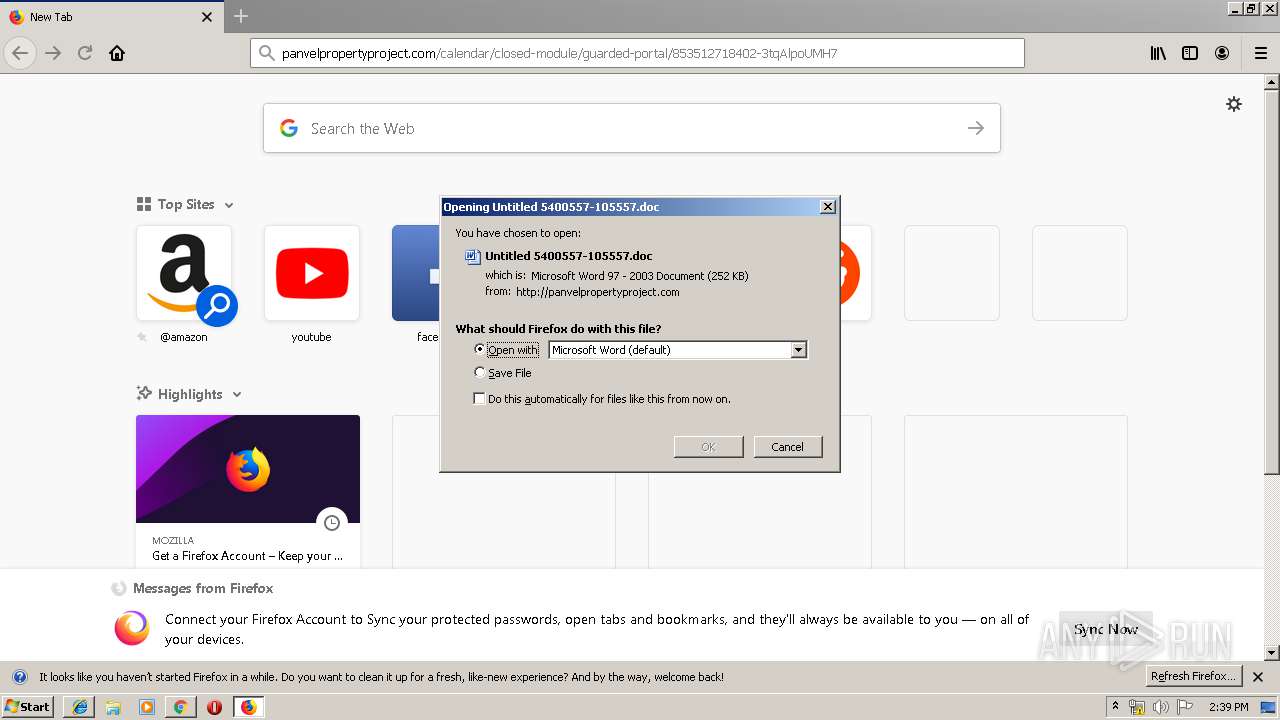
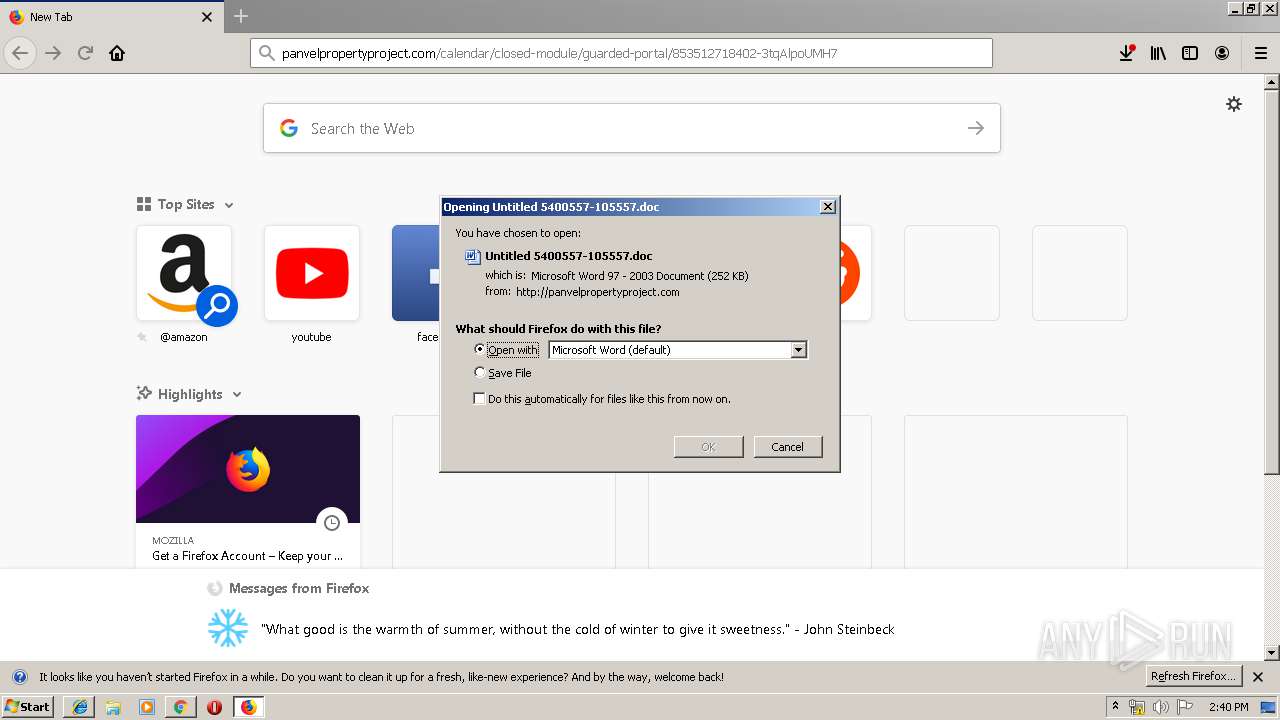
Drops known malicious document
- chrome.exe (PID: 600)
- chrome.exe (PID: 3960)
- iexplore.exe (PID: 912)
- firefox.exe (PID: 1948)
- WINWORD.EXE (PID: 3520)
- WINWORD.EXE (PID: 2428)
Application was dropped or rewritten from another process
- 900.exe (PID: 3504)
- serialfunc.exe (PID: 940)
- serialfunc.exe (PID: 3076)
- 900.exe (PID: 3440)
Downloads executable files from the Internet
- Powershell.exe (PID: 3892)
Emotet process was detected
- 900.exe (PID: 3504)
EMOTET was detected
- serialfunc.exe (PID: 3076)
Connects to CnC server
- serialfunc.exe (PID: 3076)
Changes the autorun value in the registry
- serialfunc.exe (PID: 3076)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 600)
Application launched itself
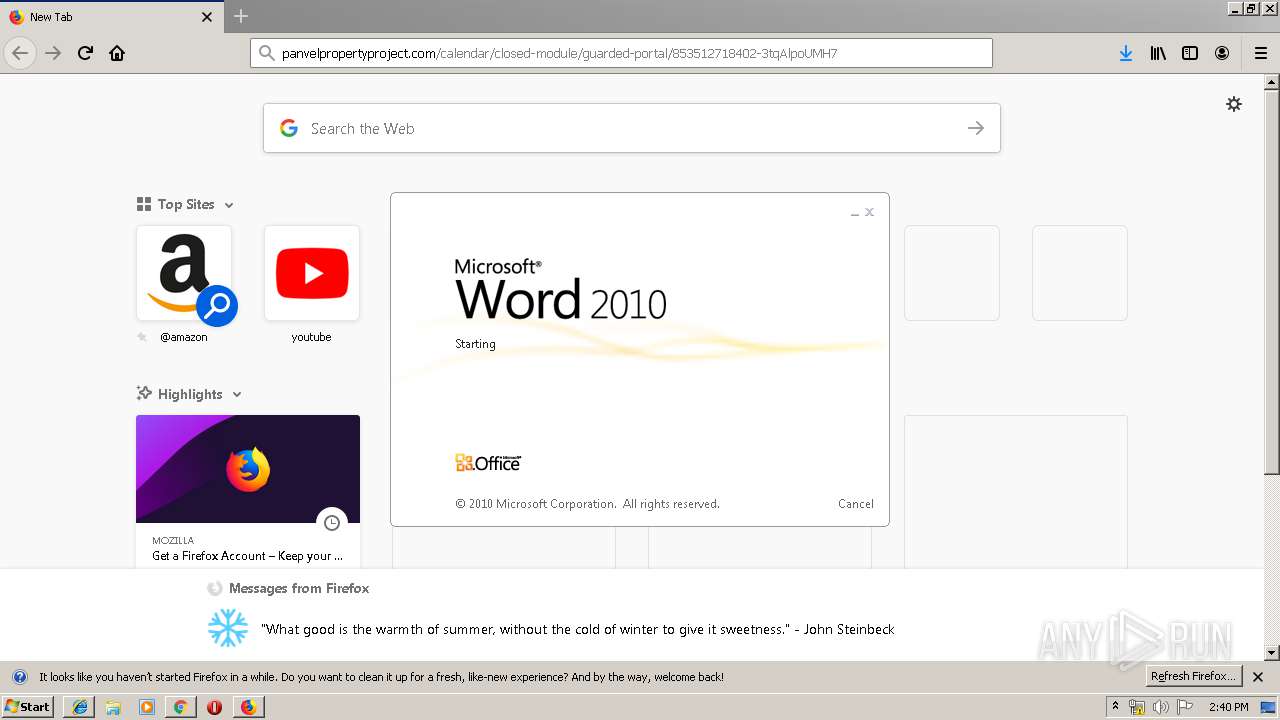
- WINWORD.EXE (PID: 2428)
- WINWORD.EXE (PID: 3520)
- serialfunc.exe (PID: 940)
Starts Microsoft Office Application
- WINWORD.EXE (PID: 2428)
- firefox.exe (PID: 1948)
- WINWORD.EXE (PID: 3520)
Creates files in the program directory
- firefox.exe (PID: 1948)
Executed via WMI
- Powershell.exe (PID: 3892)
PowerShell script executed
- Powershell.exe (PID: 3892)
Executable content was dropped or overwritten
- Powershell.exe (PID: 3892)
- 900.exe (PID: 3504)
Creates files in the user directory
- Powershell.exe (PID: 3892)
Connects to unusual port
- serialfunc.exe (PID: 3076)
Connects to SMTP port
- serialfunc.exe (PID: 3076)
Connects to server without host name
- serialfunc.exe (PID: 3076)
Starts itself from another location
- 900.exe (PID: 3504)
INFO
Reads the hosts file
- chrome.exe (PID: 600)
- chrome.exe (PID: 3960)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 600)
- chrome.exe (PID: 3960)
- firefox.exe (PID: 1948)
- WINWORD.EXE (PID: 3520)
- WINWORD.EXE (PID: 2428)
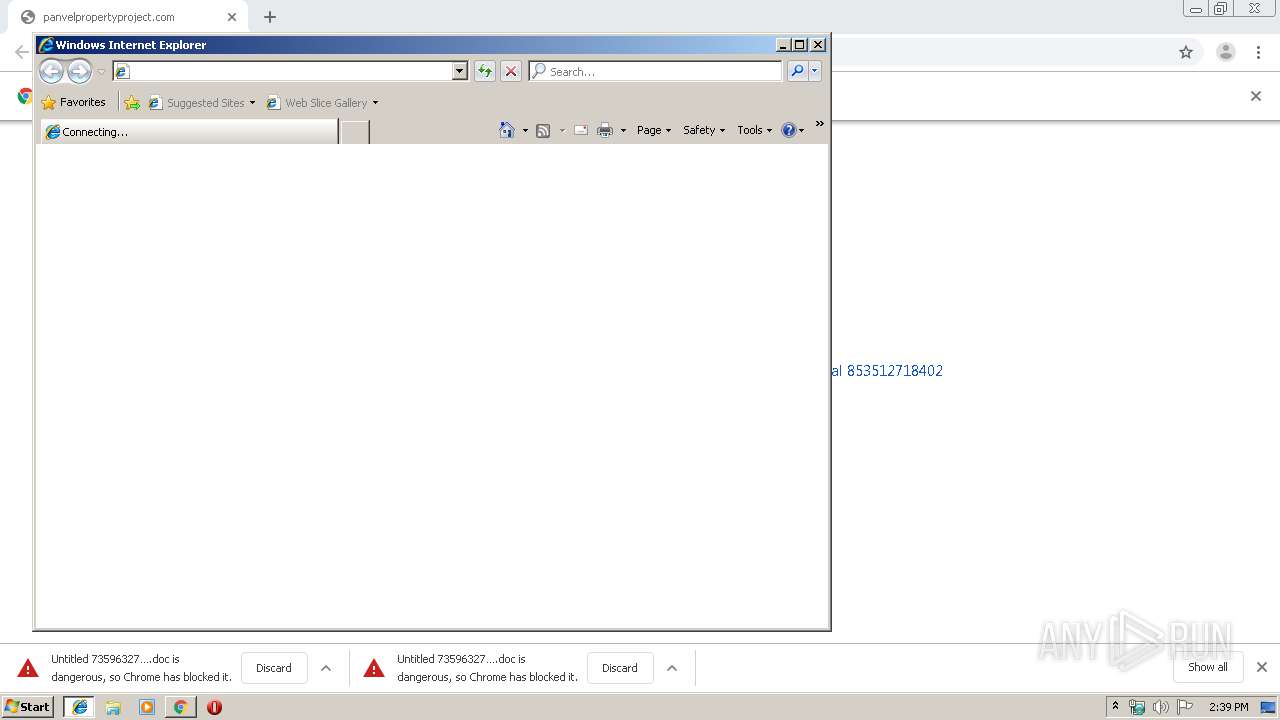
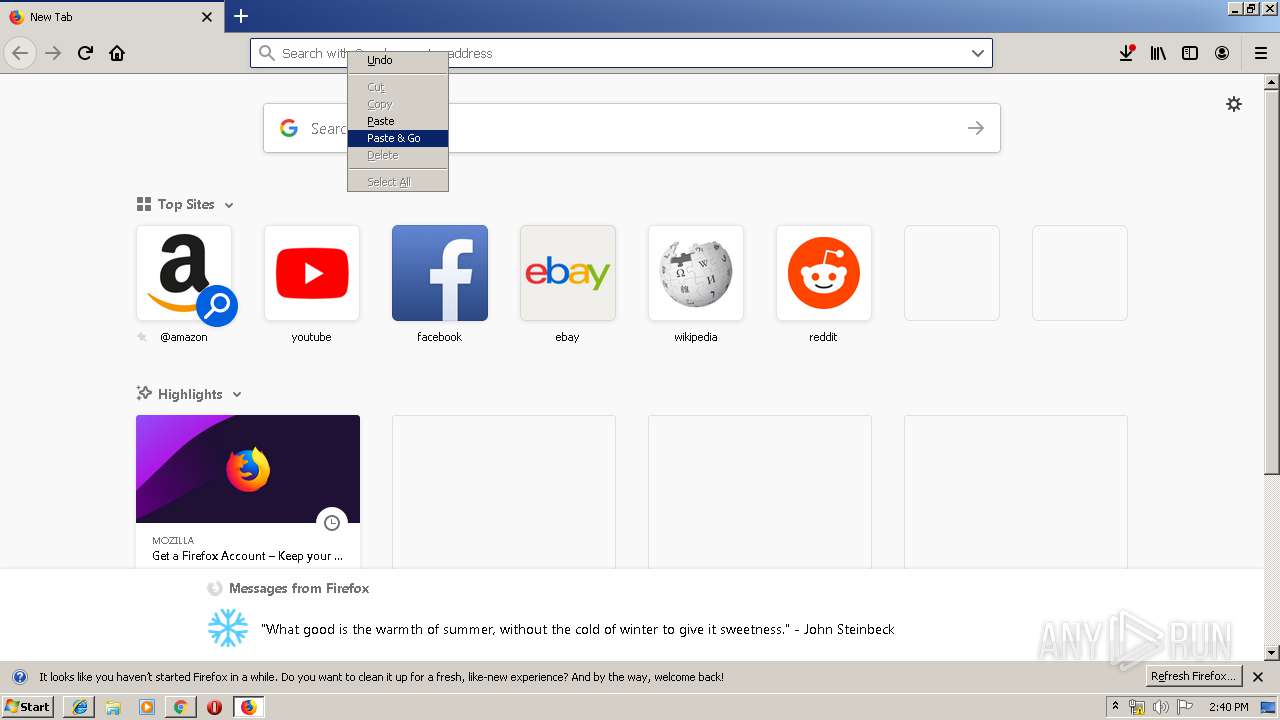
Manual execution by user
- iexplore.exe (PID: 3972)
- firefox.exe (PID: 520)
Application launched itself
- iexplore.exe (PID: 3972)
- firefox.exe (PID: 520)
- firefox.exe (PID: 1948)
- chrome.exe (PID: 600)
Creates files in the user directory
- iexplore.exe (PID: 912)
- firefox.exe (PID: 1948)
- WINWORD.EXE (PID: 2428)
- WINWORD.EXE (PID: 3520)
Reads Internet Cache Settings
- iexplore.exe (PID: 912)
- firefox.exe (PID: 1948)
Reads internet explorer settings
- iexplore.exe (PID: 912)
Changes internet zones settings
- iexplore.exe (PID: 3972)
Reads CPU info
- firefox.exe (PID: 1948)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3520)
- WINWORD.EXE (PID: 2148)
- WINWORD.EXE (PID: 3196)
- WINWORD.EXE (PID: 2428)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
93
Monitored processes
53
Malicious processes
12
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 284 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=980,2362764329789182552,18086670521994703777,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14942424741950183458 --mojo-platform-channel-handle=3312 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 408 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=980,2362764329789182552,18086670521994703777,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12092881899138057498 --mojo-platform-channel-handle=3420 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 496 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=1584 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 520 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 600 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://panvelpropertyproject.com/calendar/closed-module/guarded-portal/853512718402-3tqAlpoUMH7" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 656 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=980,2362764329789182552,18086670521994703777,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4931028413865610234 --mojo-platform-channel-handle=3452 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 912 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3972 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 932 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=980,2362764329789182552,18086670521994703777,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2277346951865802546 --mojo-platform-channel-handle=4832 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 940 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | 900.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: PromptEdit_Demo MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 976 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=980,2362764329789182552,18086670521994703777,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15253656041214645788 --mojo-platform-channel-handle=3260 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
6 866
Read events
5 349
Write events
1 345
Delete events
172
Modification events
| (PID) Process: | (600) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (600) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (600) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (600) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (600) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (496) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 600-13223745520179875 |
Value: 259 | |||
| (PID) Process: | (600) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (600) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (600) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (600) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
2
Suspicious files
115
Text files
359
Unknown types
60
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 600 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\b5b2781d-25ca-4e44-852f-ecfee0b7caa7.tmp | — | |
MD5:— | SHA256:— | |||
| 600 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 600 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 600 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 600 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 600 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 600 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 600 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 600 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 600 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF39968d.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
28
TCP/UDP connections
106
DNS requests
174
Threats
38
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3960 | chrome.exe | GET | 200 | 52.172.39.101:80 | http://panvelpropertyproject.com/calendar/closed-module/guarded-portal/853512718402-3tqAlpoUMH7/ | IN | document | 251 Kb | suspicious |
3960 | chrome.exe | GET | 200 | 52.172.39.101:80 | http://panvelpropertyproject.com/calendar/closed-module/guarded-portal/853512718402-3tqAlpoUMH7/ | IN | document | 251 Kb | suspicious |
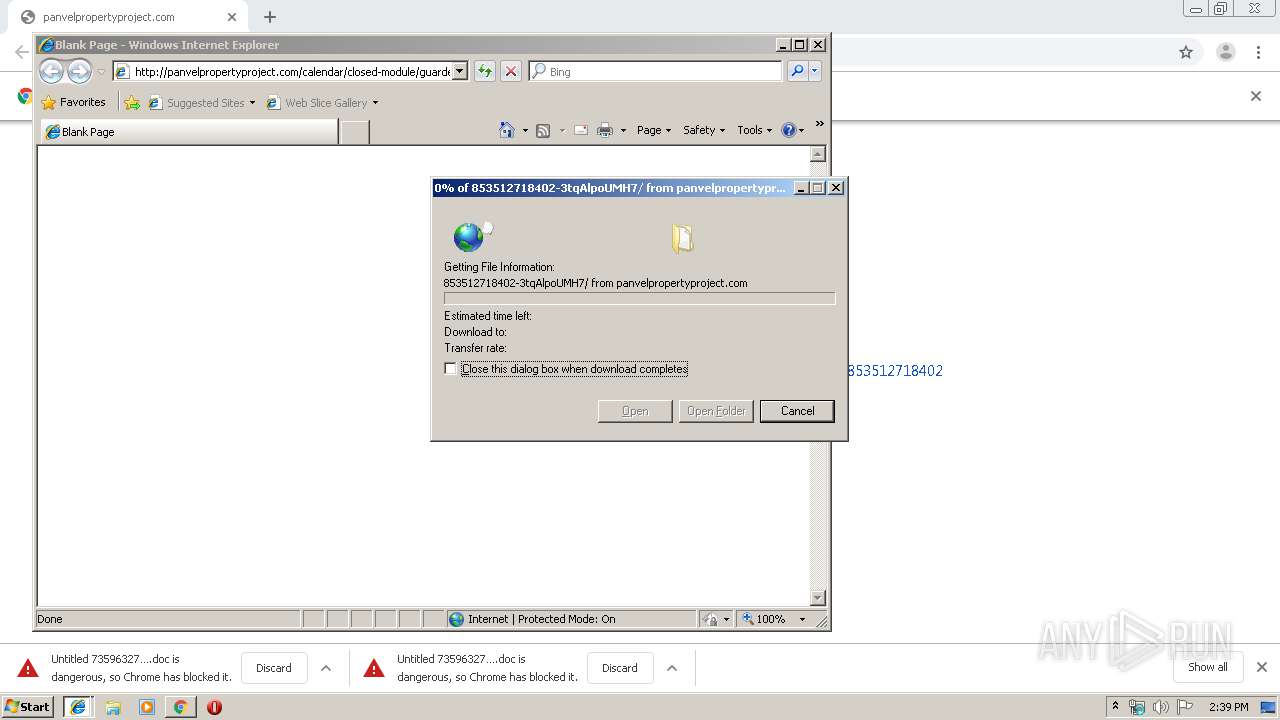
912 | iexplore.exe | GET | 301 | 52.172.39.101:80 | http://panvelpropertyproject.com/calendar/closed-module/guarded-portal/853512718402-3tqAlpoUMH7 | IN | html | 219 b | suspicious |
1948 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
1948 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
1948 | firefox.exe | GET | 301 | 52.172.39.101:80 | http://panvelpropertyproject.com/calendar/closed-module/guarded-portal/853512718402-3tqAlpoUMH7 | IN | html | 219 b | suspicious |
912 | iexplore.exe | GET | 200 | 52.172.39.101:80 | http://panvelpropertyproject.com/calendar/closed-module/guarded-portal/853512718402-3tqAlpoUMH7/ | IN | document | 251 Kb | suspicious |
1948 | firefox.exe | GET | 200 | 52.172.39.101:80 | http://panvelpropertyproject.com/calendar/closed-module/guarded-portal/853512718402-3tqAlpoUMH7/ | IN | document | 252 Kb | suspicious |
3960 | chrome.exe | GET | 302 | 172.217.22.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 515 b | whitelisted |
1948 | firefox.exe | POST | 200 | 172.217.18.163:80 | http://ocsp.pki.goog/gts1o1 | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3960 | chrome.exe | 172.217.18.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3960 | chrome.exe | 52.172.39.101:80 | panvelpropertyproject.com | Microsoft Corporation | IN | suspicious |
3960 | chrome.exe | 172.217.18.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
3960 | chrome.exe | 172.217.16.196:443 | www.google.com | Google Inc. | US | whitelisted |
3960 | chrome.exe | 172.217.22.67:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3960 | chrome.exe | 172.217.16.131:443 | www.google.co.uk | Google Inc. | US | whitelisted |
3960 | chrome.exe | 172.217.23.138:443 | www.googleapis.com | Google Inc. | US | whitelisted |
3960 | chrome.exe | 172.217.23.142:443 | clients2.google.com | Google Inc. | US | whitelisted |
3960 | chrome.exe | 172.217.21.193:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
3960 | chrome.exe | 173.194.5.185:80 | r3---sn-aigl6n7z.gvt1.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
panvelpropertyproject.com |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
www.google.co.uk |
| whitelisted |
www.googleapis.com |
| whitelisted |
clients2.google.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3960 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] Download DOC file with VBAScript |
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1948 | firefox.exe | Misc activity | SUSPICIOUS [PTsecurity] Download DOC file with VBAScript |
912 | iexplore.exe | Misc activity | SUSPICIOUS [PTsecurity] Download DOC file with VBAScript |
3892 | Powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3892 | Powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3892 | Powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
3076 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M5 |
3076 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M6 |