| File name: | QuickSeeSetup_officialwebsite.exe |
| Full analysis: | https://app.any.run/tasks/9b7109a5-ef86-4bfb-970f-5b225036e197 |
| Verdict: | Malicious activity |
| Analysis date: | January 20, 2022, 15:55:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 1AD0E7D02CB760E43C108C352F14D0D0 |
| SHA1: | 3E4A48333FDE9F4592CD4630490CE4B402F74962 |
| SHA256: | 4250123027509D712B144FB4BBE9598960E8F9C6B30F6E27C90770EE691D4545 |
| SSDEEP: | 393216:tIu84UdVEy9qMBNLtk+LKD5Ymo0iI+14Z8oO+skjull:tIu84UdVEy9qMBN9mSQu43O+skj2l |
MALICIOUS
Loads dropped or rewritten executable
- QuickSeeSetup_officialwebsite.exe (PID: 2752)
- regsvr32.exe (PID: 2920)
- QuickSeeTray.exe (PID: 2300)
- QuickSeeImg.exe (PID: 3344)
- QuickSeeImg.exe (PID: 960)
- Explorer.EXE (PID: 964)
- svchost.exe (PID: 872)
Drops executable file immediately after starts
- QuickSeeSetup_officialwebsite.exe (PID: 2752)
Application was dropped or rewritten from another process
- QuickHelper.exe (PID: 3492)
- QuickSeeTray.exe (PID: 2300)
- QuickSeeImg.exe (PID: 3344)
- guardhp.exe (PID: 2088)
- QuickSeeImg.exe (PID: 960)
Registers / Runs the DLL via REGSVR32.EXE
- QuickSeeSetup_officialwebsite.exe (PID: 2752)
Changes settings of System certificates
- QuickSeeSetup_officialwebsite.exe (PID: 2752)
Loads the Task Scheduler COM API
- QuickSeeTray.exe (PID: 2300)
Actions looks like stealing of personal data
- Explorer.EXE (PID: 964)
Steals credentials from Web Browsers
- Explorer.EXE (PID: 964)
SUSPICIOUS
Reads the computer name
- QuickSeeSetup_officialwebsite.exe (PID: 2752)
- QuickSeeTray.exe (PID: 2300)
- QuickSeeImg.exe (PID: 960)
- unsecapp.exe (PID: 2804)
- guardhp.exe (PID: 2088)
- QuickHelper.exe (PID: 3492)
Drops a file with a compile date too recent
- QuickSeeSetup_officialwebsite.exe (PID: 2752)
Creates a software uninstall entry
- QuickSeeSetup_officialwebsite.exe (PID: 2752)
- QuickSeeTray.exe (PID: 2300)
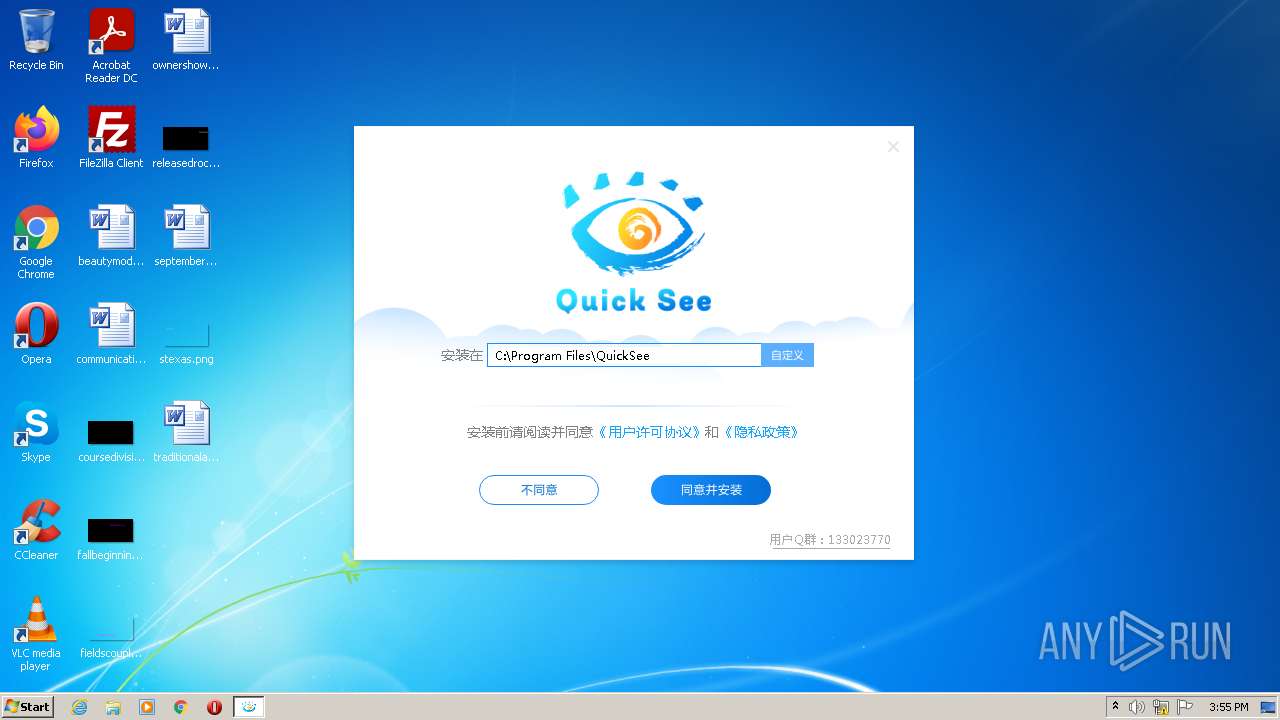
Creates a directory in Program Files
- QuickSeeSetup_officialwebsite.exe (PID: 2752)
- QuickSeeTray.exe (PID: 2300)
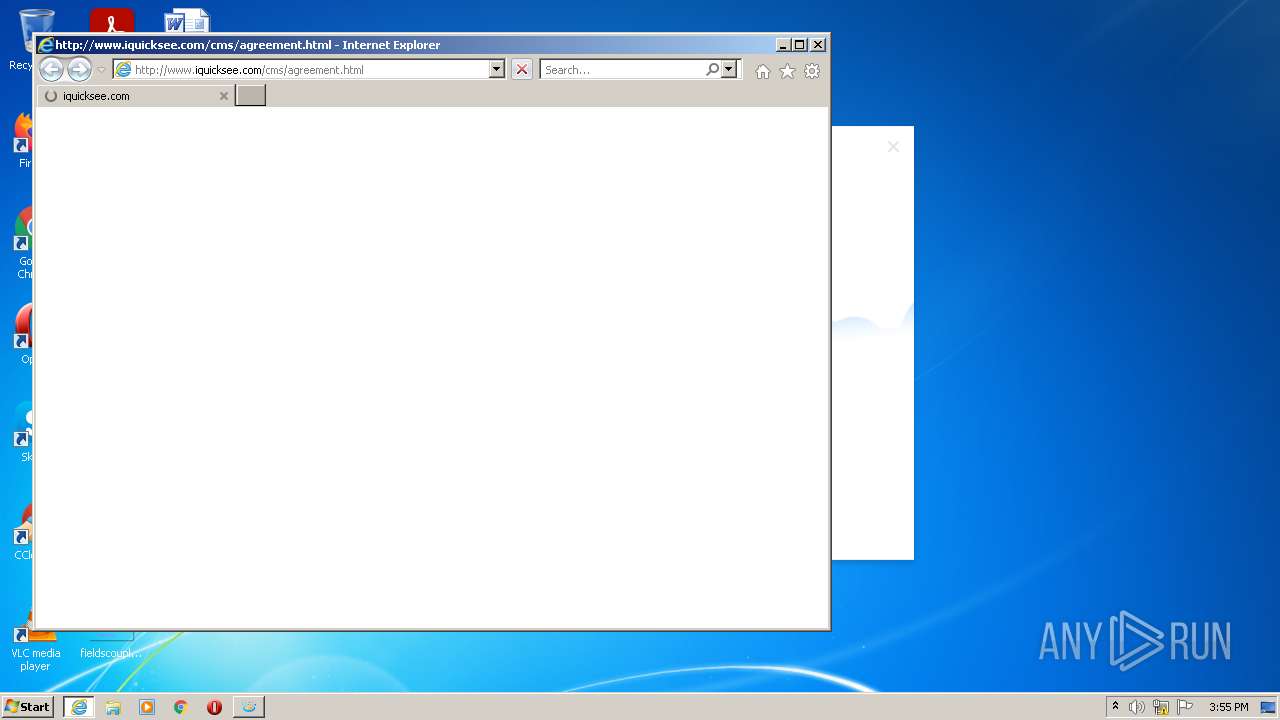
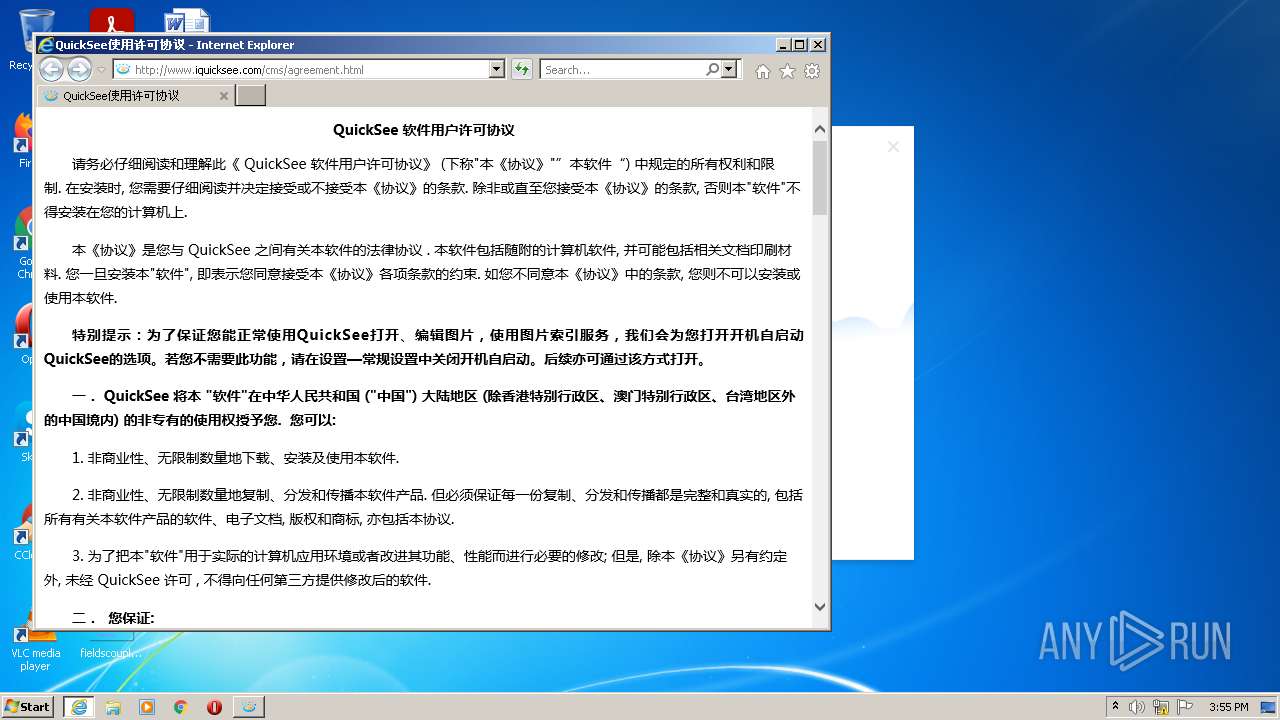
Starts Internet Explorer
- QuickSeeSetup_officialwebsite.exe (PID: 2752)
Creates files in the user directory
- QuickSeeSetup_officialwebsite.exe (PID: 2752)
- QuickSeeTray.exe (PID: 2300)
- QuickSeeImg.exe (PID: 3344)
- Explorer.EXE (PID: 964)
- guardhp.exe (PID: 2088)
Checks supported languages
- QuickSeeSetup_officialwebsite.exe (PID: 2752)
- QuickHelper.exe (PID: 3492)
- QuickSeeTray.exe (PID: 2300)
- QuickSeeImg.exe (PID: 960)
- QuickSeeImg.exe (PID: 3344)
- guardhp.exe (PID: 2088)
- unsecapp.exe (PID: 2804)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 528)
Creates files in the program directory
- QuickSeeSetup_officialwebsite.exe (PID: 2752)
- QuickSeeTray.exe (PID: 2300)
Executable content was dropped or overwritten
- QuickSeeSetup_officialwebsite.exe (PID: 2752)
Drops a file that was compiled in debug mode
- QuickSeeSetup_officialwebsite.exe (PID: 2752)
Creates or modifies windows services
- QuickSeeSetup_officialwebsite.exe (PID: 2752)
Reads default file associations for system extensions
- Explorer.EXE (PID: 964)
- QuickSeeImg.exe (PID: 960)
Adds / modifies Windows certificates
- QuickSeeSetup_officialwebsite.exe (PID: 2752)
Changes default file association
- QuickSeeImg.exe (PID: 3344)
Executed via COM
- unsecapp.exe (PID: 2804)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 2920)
INFO
Reads the computer name
- iexplore.exe (PID: 528)
- iexplore.exe (PID: 3812)
- regsvr32.exe (PID: 2920)
Checks supported languages
- iexplore.exe (PID: 528)
- iexplore.exe (PID: 3812)
- regsvr32.exe (PID: 2920)
Checks Windows Trust Settings
- QuickSeeSetup_officialwebsite.exe (PID: 2752)
- iexplore.exe (PID: 3812)
- QuickSeeTray.exe (PID: 2300)
- guardhp.exe (PID: 2088)
- Explorer.EXE (PID: 964)
Application launched itself
- iexplore.exe (PID: 3812)
Changes internet zones settings
- iexplore.exe (PID: 3812)
Reads settings of System Certificates
- QuickSeeSetup_officialwebsite.exe (PID: 2752)
- iexplore.exe (PID: 3812)
- QuickSeeTray.exe (PID: 2300)
- guardhp.exe (PID: 2088)
- Explorer.EXE (PID: 964)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 528)
Reads internet explorer settings
- iexplore.exe (PID: 528)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| ProductVersion: | 1.2121.1085.1229 |
|---|---|
| ProductName: | QuickSee |
| OriginalFileName: | install.exe |
| LegalCopyright: | Copyright (C) 2011-2020 |
| InternalName: | install.exe |
| FileVersion: | 1.2121.1085.1229 |
| FileDescription: | QuickSee安装程序 |
| CharacterSet: | Unicode |
| LanguageCode: | Chinese (Simplified) |
| FileSubtype: | - |
| ObjectFileType: | Dynamic link library |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.2121.1085.1229 |
| FileVersionNumber: | 1.2121.1085.1229 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x7d1fb |
| UninitializedDataSize: | - |
| InitializedDataSize: | 3323392 |
| CodeSize: | 1225216 |
| LinkerVersion: | 14.16 |
| PEType: | PE32 |
| TimeStamp: | 2021:12:03 08:18:39+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 03-Dec-2021 07:18:39 |
| Detected languages: |
|
| Debug artifacts: |
|
| FileDescription: | QuickSee安装程序 |
| FileVersion: | 1.2121.1085.1229 |
| InternalName: | install.exe |
| LegalCopyright: | Copyright (C) 2011-2020 |
| OriginalFilename: | install.exe |
| ProductName: | QuickSee |
| ProductVersion: | 1.2121.1085.1229 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000148 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 03-Dec-2021 07:18:39 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0012B1E1 | 0x0012B200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.52114 |
.rdata | 0x0012D000 | 0x000408BE | 0x00040A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.06423 |
.data | 0x0016E000 | 0x0000D008 | 0x00007C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.88488 |
.rsrc | 0x0017C000 | 0x002D49A0 | 0x002D4A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.06884 |
.reloc | 0x00451000 | 0x0000E42C | 0x0000E600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.64382 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.33204 | 1053 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 2.51784 | 67624 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 2.7764 | 38056 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 2.90417 | 21640 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 2.94388 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 3.242 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
14 | 2.37277 | 80 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
127 | 7.94378 | 5246 | Latin 1 / Western European | Chinese - PRC | PNG |
128 | 2.93999 | 90 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
203 | 7.99801 | 600500 | Latin 1 / Western European | Chinese - PRC | DLL_7Z |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
IPHLPAPI.DLL |
KERNEL32.dll |
OLEAUT32.dll |
PSAPI.DLL |
SETUPAPI.dll |
SHELL32.dll |
SHLWAPI.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
InstallEntryW | 1 | 0x00034EE0 |
_BasicEntry@12 | 2 | 0x00034E70 |
_Start@4 | 3 | 0x00034D20 |
Total processes
57
Monitored processes
13
Malicious processes
8
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 528 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3812 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 872 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\system32\svchost.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 960 | "C:\Program Files\QuickSee\QuickSeeImg.exe" --from=tray --focus | C:\Program Files\QuickSee\QuickSeeImg.exe | QuickSeeTray.exe | ||||||||||||
User: admin Company: ???????????? Integrity Level: HIGH Description: QuickSee Exit code: 0 Version: 1.2121.1085.1229 Modules
| |||||||||||||||
| 964 | C:\Windows\Explorer.EXE | C:\Windows\Explorer.EXE | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2088 | "C:\Program Files\QuickSee\Utils\guardhp.exe" /Pid=kantu | C:\Program Files\QuickSee\Utils\guardhp.exe | QuickSeeTray.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.5021.1020.1231 Modules
| |||||||||||||||
| 2300 | "C:\Program Files\QuickSee\QuickSeeTray.exe" --from=newinstall /try_now --show=4 | C:\Program Files\QuickSee\QuickSeeTray.exe | QuickSeeSetup_officialwebsite.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.2121.1085.1230 Modules
| |||||||||||||||
| 2752 | "C:\Users\admin\AppData\Local\Temp\QuickSeeSetup_officialwebsite.exe" | C:\Users\admin\AppData\Local\Temp\QuickSeeSetup_officialwebsite.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Description: QuickSee???? Exit code: 1 Version: 1.2121.1085.1229 Modules
| |||||||||||||||
| 2804 | C:\Windows\system32\wbem\unsecapp.exe -Embedding | C:\Windows\system32\wbem\unsecapp.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Sink to receive asynchronous callbacks for WMI client application Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 2920 | "C:\Windows\System32\regsvr32.exe" /s /i "C:\Program Files\QuickSee\QsShell.dll" | C:\Windows\System32\regsvr32.exe | — | QuickSeeSetup_officialwebsite.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3344 | "C:\Program Files\QuickSee\QuickSeeImg.exe" /install | C:\Program Files\QuickSee\QuickSeeImg.exe | — | QuickSeeTray.exe | |||||||||||
User: admin Company: ???????????? Integrity Level: HIGH Description: QuickSee Exit code: 0 Version: 1.2121.1085.1229 Modules
| |||||||||||||||
Total events
32 569
Read events
31 183
Write events
1 377
Delete events
9
Modification events
| (PID) Process: | (2752) QuickSeeSetup_officialwebsite.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Session Manager |
| Operation: | write | Name: | PendingFileRenameOperations |
Value: \??\C:\Users\admin\AppData\Local\Temp\netul.dll | |||
| (PID) Process: | (2752) QuickSeeSetup_officialwebsite.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\360Safe\Liveup |
| Operation: | write | Name: | mid |
Value: 98fbba90914e8b88d84161065028cd94932bcb5b0e661cb98a0e05d326c3fcd9 | |||
| (PID) Process: | (2752) QuickSeeSetup_officialwebsite.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\ComMaster |
| Operation: | write | Name: | m2 |
Value: 0df2acc0e9a4e42dc278db3d0cbafd6a76b4ffda2bf4 | |||
| (PID) Process: | (2752) QuickSeeSetup_officialwebsite.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\QuickSeeSetup_officialwebsite_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2752) QuickSeeSetup_officialwebsite.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\QuickSeeSetup_officialwebsite_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2752) QuickSeeSetup_officialwebsite.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\QuickSeeSetup_officialwebsite_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (2752) QuickSeeSetup_officialwebsite.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\QuickSeeSetup_officialwebsite_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (2752) QuickSeeSetup_officialwebsite.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\QuickSeeSetup_officialwebsite_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2752) QuickSeeSetup_officialwebsite.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\QuickSeeSetup_officialwebsite_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2752) QuickSeeSetup_officialwebsite.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
Executable files
77
Suspicious files
17
Text files
66
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2752 | QuickSeeSetup_officialwebsite.exe | C:\Users\admin\AppData\Local\Temp\{1CB95822-1AFC-42e4-832E-C75756ADC148}.tf | binary | |
MD5:— | SHA256:— | |||
| 2752 | QuickSeeSetup_officialwebsite.exe | C:\ProgramData\{36B0ADC0-E1DF-4f09-A92F-29EC62575496}.tmp\{9FA1921A-2322-46d2-9AAB-EDCB3592D81C}.tf | binary | |
MD5:— | SHA256:— | |||
| 2752 | QuickSeeSetup_officialwebsite.exe | C:\ProgramData\{36B0ADC0-E1DF-4f09-A92F-29EC62575496}.tmp\plugin\Basic.tpi | executable | |
MD5:— | SHA256:— | |||
| 2752 | QuickSeeSetup_officialwebsite.exe | C:\Users\admin\AppData\Local\Temp\{C2C4CB90-B091-4b19-939A-B29EE8257EAA}.tmp | compressed | |
MD5:— | SHA256:— | |||
| 2752 | QuickSeeSetup_officialwebsite.exe | C:\Users\admin\AppData\Local\Temp\{10E14A13-9F68-4f46-BEA7-9B3143848DEF}.tf | binary | |
MD5:— | SHA256:— | |||
| 2752 | QuickSeeSetup_officialwebsite.exe | C:\ProgramData\{36B0ADC0-E1DF-4f09-A92F-29EC62575496}.tmp\plugin\RunExtention.tpi | executable | |
MD5:— | SHA256:— | |||
| 2752 | QuickSeeSetup_officialwebsite.exe | C:\Users\admin\AppData\Local\Temp\{8C0010A1-CDA7-40b6-81A3-39FE02AF2D20}.tmp\QUICKSEE.LDSPRJ | xml | |
MD5:— | SHA256:— | |||
| 2752 | QuickSeeSetup_officialwebsite.exe | C:\Users\admin\AppData\Local\Temp\{F98D7921-1FDB-4633-B04F-8A32CA356050}.tmp\7z.dll | executable | |
MD5:— | SHA256:— | |||
| 2752 | QuickSeeSetup_officialwebsite.exe | C:\ProgramData\{36B0ADC0-E1DF-4f09-A92F-29EC62575496}.tmp\language\cn_simp.ini | text | |
MD5:— | SHA256:— | |||
| 2752 | QuickSeeSetup_officialwebsite.exe | C:\ProgramData\{36B0ADC0-E1DF-4f09-A92F-29EC62575496}.tmp\plugin\Misc.tpi | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
28
TCP/UDP connections
36
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
528 | iexplore.exe | GET | 200 | 182.92.195.97:80 | http://www.iquicksee.com/favicon.ico | CN | image | 16.5 Kb | unknown |
964 | Explorer.EXE | GET | 200 | 47.117.76.201:80 | http://s.ludashi.com/url2?&mid=98fbba90914e8b88d84161065028cd94&type=hpl&action=hpl_run&pid=kantu_officialwebsite&modver=2.5021.1025.1224&appver=1.2121.1085.1229 | CN | — | — | suspicious |
2752 | QuickSeeSetup_officialwebsite.exe | GET | 200 | 182.92.195.97:80 | http://www.iquicksee.com/channel/Commonapi?pid=officialwebsite&from=officialwebsite&ver=1.2121.1085.1229&osver=6.1.7601&instime=20220120155543 | CN | text | 268 b | unknown |
3812 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
964 | Explorer.EXE | GET | 200 | 101.226.28.204:80 | http://cdn-file.ludashi.com/pc/hao/external.dat?t=15 | CN | text | 172 b | suspicious |
2752 | QuickSeeSetup_officialwebsite.exe | GET | 200 | 106.15.201.26:80 | http://s.iquicksee.com/quicksee?pid=officialwebsite&type=installpkg&action=svc&app=kantu&appver=1.2121.1085.1229&mid=98fbba90914e8b88d84161065028cd94&mid2=0df2acc0e9a4e42dc278db3d0cbafd6a76b4ffda2bf4 | CN | text | 2 b | suspicious |
2752 | QuickSeeSetup_officialwebsite.exe | GET | 200 | 106.15.201.26:80 | http://s.iquicksee.com/quicksee?pid=officialwebsite&type=installpkg&action=enter&app=kantu&appver=1.2121.1085.1229&mid=98fbba90914e8b88d84161065028cd94&mid2=0df2acc0e9a4e42dc278db3d0cbafd6a76b4ffda2bf4 | CN | text | 2 b | suspicious |
2752 | QuickSeeSetup_officialwebsite.exe | POST | 200 | 115.28.112.133:80 | http://l.public.iquicksee.com/pc/udkantu/dogSun | CN | text | 216 b | unknown |
2752 | QuickSeeSetup_officialwebsite.exe | GET | 200 | 106.15.201.26:80 | http://s.iquicksee.com/quicksee?pid=officialwebsite&type=installpkg&action=run&app=kantu&appver=1.2121.1085.1229&mid=98fbba90914e8b88d84161065028cd94&mid2=0df2acc0e9a4e42dc278db3d0cbafd6a76b4ffda2bf4 | CN | text | 2 b | suspicious |
2300 | QuickSeeTray.exe | GET | 200 | 106.15.201.26:80 | http://s.iquicksee.com/quicksee?pid=officialwebsite&mid=98fbba90914e8b88d84161065028cd94&mid2=0df2acc0e9a4e42dc278db3d0cbafd6a76b4ffda2bf4&appver=1.2121.1085.1229&modver=1.2121.1085.1230&type=operate&action=run_newinstall&app=kantu | CN | text | 2 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
528 | iexplore.exe | 182.92.195.97:80 | www.iquicksee.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
2752 | QuickSeeSetup_officialwebsite.exe | 106.15.201.26:80 | s.iquicksee.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
3492 | QuickHelper.exe | 106.15.201.26:80 | s.iquicksee.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
3812 | iexplore.exe | 2.16.106.171:80 | ctldl.windowsupdate.com | Akamai International B.V. | — | whitelisted |
4 | System | 106.15.201.26:80 | s.iquicksee.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
2300 | QuickSeeTray.exe | 182.92.195.97:80 | www.iquicksee.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
3812 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2752 | QuickSeeSetup_officialwebsite.exe | 182.92.195.97:80 | www.iquicksee.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
2752 | QuickSeeSetup_officialwebsite.exe | 115.28.112.133:80 | l.public.iquicksee.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
2300 | QuickSeeTray.exe | 106.15.201.26:80 | s.iquicksee.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.iquicksee.com |
| unknown |
l.public.iquicksee.com |
| unknown |
s.iquicksee.com |
| unknown |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
cdn-file.iquicksee.com |
| malicious |
cdn-file.ludashi.com |
| suspicious |
s.ludashi.com |
| suspicious |