| File name: | Asphalt 8 Airborne Trainer New.exe |
| Full analysis: | https://app.any.run/tasks/cab120b0-1018-4720-84dd-bd9f9fc2f2d0 |
| Verdict: | Malicious activity |
| Analysis date: | August 02, 2024, 15:25:46 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | DA52EE7D16AD70047E41C9005B693C31 |
| SHA1: | 78EEFF1081CA88364F047596D8B8A8BADB821DF0 |
| SHA256: | 424EBEB7182D370CB27D3A17C1EB1CCE13285C799E283F3BB6FC94E84BBE5C94 |
| SSDEEP: | 1536:dBlli2iLR9nk7RBog5KG6JkOiVPL+09ME5LBtJD64uQgCd7R9HEdOpkkNRBog5KF:Pi2izE57miVj+J6pHdJkdO557N/K |
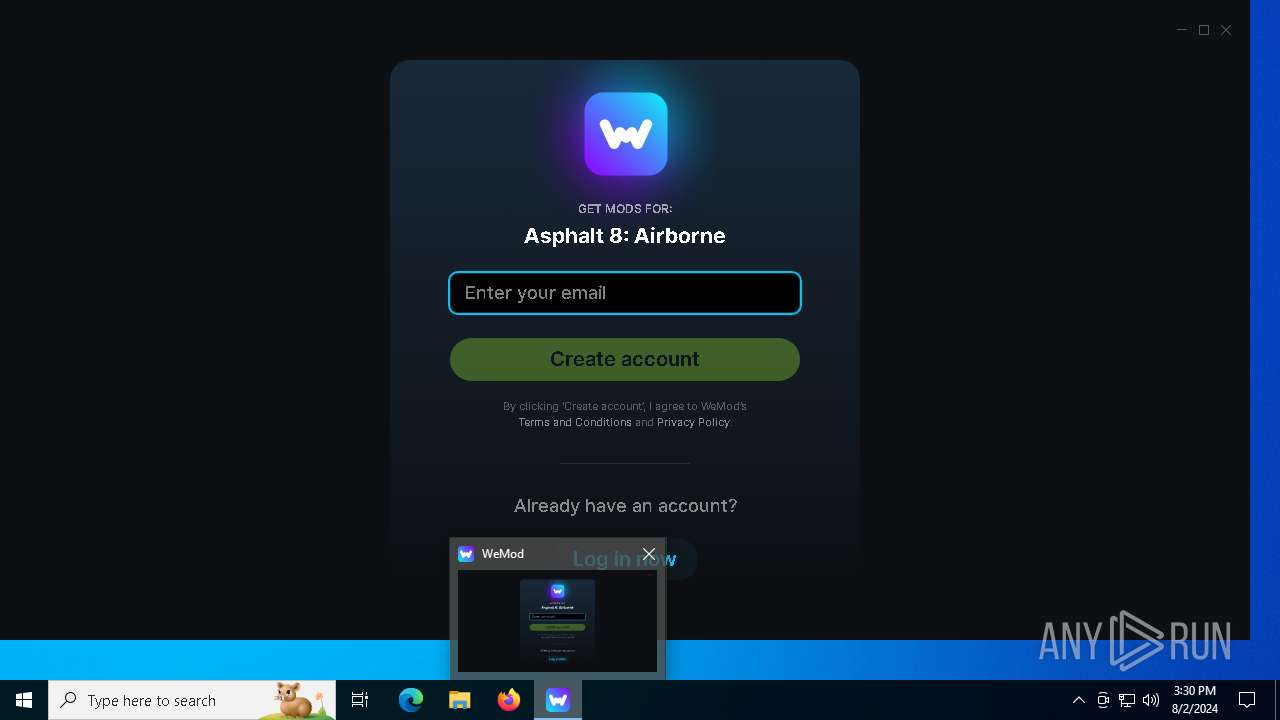
MALICIOUS
Drops the executable file immediately after the start
- Asphalt 8 Airborne Trainer New.exe (PID: 6296)
- Update.exe (PID: 6772)
- WeMod-Setup-638582091671773071.exe (PID: 6756)
Scans artifacts that could help determine the target
- Asphalt 8 Airborne Trainer New.exe (PID: 6296)
SUSPICIOUS
Reads security settings of Internet Explorer
- Asphalt 8 Airborne Trainer New.exe (PID: 6296)
- Update.exe (PID: 6772)
- Update.exe (PID: 6612)
- WeModAuxiliaryService.exe (PID: 3044)
Reads Microsoft Outlook installation path
- Asphalt 8 Airborne Trainer New.exe (PID: 6296)
Checks Windows Trust Settings
- Asphalt 8 Airborne Trainer New.exe (PID: 6296)
- WeModAuxiliaryService.exe (PID: 3044)
Process drops legitimate windows executable
- Update.exe (PID: 6772)
Executable content was dropped or overwritten
- Update.exe (PID: 6772)
- WeMod-Setup-638582091671773071.exe (PID: 6756)
Reads Internet Explorer settings
- Asphalt 8 Airborne Trainer New.exe (PID: 6296)
Creates a software uninstall entry
- Update.exe (PID: 6772)
Searches for installed software
- Update.exe (PID: 6772)
Reads the date of Windows installation
- Update.exe (PID: 6772)
- Asphalt 8 Airborne Trainer New.exe (PID: 6296)
- Update.exe (PID: 6612)
Application launched itself
- WeMod.exe (PID: 2092)
Found regular expressions for crypto-addresses (YARA)
- WeMod.exe (PID: 1184)
INFO
Checks supported languages
- Asphalt 8 Airborne Trainer New.exe (PID: 6296)
- Update.exe (PID: 6772)
- WeMod-Setup-638582091671773071.exe (PID: 6756)
- WeMod.exe (PID: 6928)
- Update.exe (PID: 1124)
- squirrel.exe (PID: 6168)
- Update.exe (PID: 6612)
- WeMod.exe (PID: 2092)
- WeMod.exe (PID: 1184)
- Update.exe (PID: 5988)
- WeModAuxiliaryService.exe (PID: 3044)
- WeMod.exe (PID: 7156)
- WeMod.exe (PID: 3848)
- TextInputHost.exe (PID: 5372)
- WeMod.exe (PID: 6388)
- identity_helper.exe (PID: 7800)
Checks proxy server information
- Asphalt 8 Airborne Trainer New.exe (PID: 6296)
- Update.exe (PID: 6772)
- WeMod.exe (PID: 2092)
- Update.exe (PID: 5988)
- WeModAuxiliaryService.exe (PID: 3044)
Reads the machine GUID from the registry
- Asphalt 8 Airborne Trainer New.exe (PID: 6296)
- Update.exe (PID: 6772)
- squirrel.exe (PID: 6168)
- Update.exe (PID: 1124)
- Update.exe (PID: 6612)
- Update.exe (PID: 5988)
- WeMod.exe (PID: 2092)
- WeModAuxiliaryService.exe (PID: 3044)
- WeMod.exe (PID: 6388)
Reads the computer name
- Asphalt 8 Airborne Trainer New.exe (PID: 6296)
- Update.exe (PID: 6772)
- Update.exe (PID: 1124)
- squirrel.exe (PID: 6168)
- WeMod.exe (PID: 2092)
- Update.exe (PID: 6612)
- WeMod.exe (PID: 3848)
- Update.exe (PID: 5988)
- WeModAuxiliaryService.exe (PID: 3044)
- WeMod.exe (PID: 7156)
- TextInputHost.exe (PID: 5372)
- WeMod.exe (PID: 6388)
- identity_helper.exe (PID: 7800)
Reads the software policy settings
- Asphalt 8 Airborne Trainer New.exe (PID: 6296)
- Update.exe (PID: 6772)
- WeModAuxiliaryService.exe (PID: 3044)
- Update.exe (PID: 5988)
Creates files or folders in the user directory
- Asphalt 8 Airborne Trainer New.exe (PID: 6296)
- Update.exe (PID: 6772)
- WeMod-Setup-638582091671773071.exe (PID: 6756)
- squirrel.exe (PID: 6168)
- Update.exe (PID: 1124)
- WeMod.exe (PID: 2092)
- Update.exe (PID: 6612)
- WeMod.exe (PID: 3848)
- Update.exe (PID: 5988)
- WeModAuxiliaryService.exe (PID: 3044)
- WeMod.exe (PID: 6388)
Process checks Internet Explorer phishing filters
- Asphalt 8 Airborne Trainer New.exe (PID: 6296)
Create files in a temporary directory
- Update.exe (PID: 6772)
- Asphalt 8 Airborne Trainer New.exe (PID: 6296)
- WeMod.exe (PID: 2092)
- Update.exe (PID: 5988)
Disables trace logs
- Asphalt 8 Airborne Trainer New.exe (PID: 6296)
- Update.exe (PID: 6772)
- Update.exe (PID: 5988)
Reads Environment values
- Asphalt 8 Airborne Trainer New.exe (PID: 6296)
- WeMod.exe (PID: 6928)
- Update.exe (PID: 6772)
- WeMod.exe (PID: 2092)
- Update.exe (PID: 5988)
- identity_helper.exe (PID: 7800)
Reads product name
- WeMod.exe (PID: 6928)
- WeMod.exe (PID: 2092)
Process checks computer location settings
- Update.exe (PID: 6772)
- Asphalt 8 Airborne Trainer New.exe (PID: 6296)
- Update.exe (PID: 6612)
- WeMod.exe (PID: 1184)
- WeMod.exe (PID: 2092)
Reads CPU info
- WeMod.exe (PID: 2092)
Manual execution by a user
- firefox.exe (PID: 6724)
- msedge.exe (PID: 6816)
Application launched itself
- firefox.exe (PID: 6724)
- firefox.exe (PID: 6820)
- msedge.exe (PID: 6816)
Reads Microsoft Office registry keys
- msedge.exe (PID: 6816)
- firefox.exe (PID: 6820)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2045:04:11 17:40:35+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 103936 |
| InitializedDataSize: | 28160 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1b4ae |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 8.0.0.0 |
| ProductVersionNumber: | 8.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | WeMod Setup |
| CompanyName: | WeMod LLC |
| FileDescription: | WeMod Setup |
| FileVersion: | 8.0.0.0 |
| InternalName: | WeMod-Setup.exe |
| LegalCopyright: | Copyright © WeMod LLC 2022 |
| LegalTrademarks: | - |
| OriginalFileName: | WeMod-Setup.exe |
| ProductName: | WeMod |
| ProductVersion: | 8.0.0.0 |
| AssemblyVersion: | 8.0.0.0 |
Total processes
188
Monitored processes
45
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 240 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=1916 -parentBuildID 20240213221259 -prefsHandle 1852 -prefMapHandle 1844 -prefsLen 30537 -prefMapSize 244343 -appDir "C:\Program Files\Mozilla Firefox\browser" - {8d2c7572-b546-4662-bfb0-0767a5d2d294} 6820 "\\.\pipe\gecko-crash-server-pipe.6820" 209929e1a10 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 320 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5464 -childID 3 -isForBrowser -prefsHandle 5456 -prefMapHandle 5452 -prefsLen 31169 -prefMapSize 244343 -jsInitHandle 1512 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {a491fb15-23ac-4689-920d-ca96d421339f} 6820 "\\.\pipe\gecko-crash-server-pipe.6820" 2099989af50 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 1124 | C:\Users\admin\AppData\Local\WeMod\Update.exe --createShortcut WeMod.exe | C:\Users\admin\AppData\Local\WeMod\Update.exe | — | WeMod.exe | |||||||||||
User: admin Company: GitHub Integrity Level: MEDIUM Description: Update Exit code: 0 Version: 2.0.1.53 Modules
| |||||||||||||||
| 1184 | "C:\Users\admin\AppData\Local\WeMod\app-9.8.0\WeMod.exe" --type=renderer --user-data-dir="C:\Users\admin\AppData\Roaming\WeMod" --app-user-model-id=com.squirrel.WeMod.WeMod --app-path="C:\Users\admin\AppData\Local\WeMod\app-9.8.0\resources\app.asar" --no-sandbox --no-zygote --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --field-trial-handle=2464,i,3641959511973666931,9242461001987769470,262144 --enable-features=kWebSQLAccess --disable-features=SpareRendererForSitePerProcess,WinDelaySpellcheckServiceInit,WinRetrieveSuggestionsOnlyOnDemand --variations-seed-version --mojo-platform-channel-handle=2520 /prefetch:1 | C:\Users\admin\AppData\Local\WeMod\app-9.8.0\WeMod.exe | WeMod.exe | ||||||||||||
User: admin Company: WeMod Integrity Level: MEDIUM Description: WeMod - Cheats and Mods Version: 9.8.0 Modules
| |||||||||||||||
| 1776 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2628 --field-trial-handle=2060,i,5508734483876610182,16836549359151961011,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1944 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=2052 --field-trial-handle=2060,i,5508734483876610182,16836549359151961011,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2064 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x304,0x308,0x30c,0x300,0x380,0x7fffcd2b5fd8,0x7fffcd2b5fe4,0x7fffcd2b5ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2092 | "C:\Users\admin\AppData\Local\WeMod\app-9.8.0\WeMod.exe" wemod://titles/30304?gameId=30890&_inst=mk06zz6UY3yAX1ff | C:\Users\admin\AppData\Local\WeMod\app-9.8.0\WeMod.exe | — | Update.exe | |||||||||||
User: admin Company: WeMod Integrity Level: MEDIUM Description: WeMod - Cheats and Mods Version: 9.8.0 Modules
| |||||||||||||||
| 2264 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=2592 --field-trial-handle=2060,i,5508734483876610182,16836549359151961011,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 3044 | C:\Users\admin\AppData\Local\WeMod\app-9.8.0\resources\app.asar.unpacked\static\unpacked\auxiliary\WeModAuxiliaryService.exe WeMod\Support_1722612448785_Out | C:\Users\admin\AppData\Local\WeMod\app-9.8.0\resources\app.asar.unpacked\static\unpacked\auxiliary\WeModAuxiliaryService.exe | WeMod.exe | ||||||||||||
User: admin Company: WeMod LLC Integrity Level: MEDIUM Description: WeMod Version: 7.2.0.0 Modules
| |||||||||||||||
Total events
43 965
Read events
43 768
Write events
173
Delete events
24
Modification events
| (PID) Process: | (6296) Asphalt 8 Airborne Trainer New.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6296) Asphalt 8 Airborne Trainer New.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6296) Asphalt 8 Airborne Trainer New.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6296) Asphalt 8 Airborne Trainer New.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (6296) Asphalt 8 Airborne Trainer New.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6296) Asphalt 8 Airborne Trainer New.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6296) Asphalt 8 Airborne Trainer New.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6296) Asphalt 8 Airborne Trainer New.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Asphalt 8 Airborne Trainer New_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6296) Asphalt 8 Airborne Trainer New.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Asphalt 8 Airborne Trainer New_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6296) Asphalt 8 Airborne Trainer New.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Asphalt 8 Airborne Trainer New_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
25
Suspicious files
447
Text files
118
Unknown types
19
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6296 | Asphalt 8 Airborne Trainer New.exe | C:\Users\admin\AppData\Local\Temp\WeMod-Setup-638582091671773071.exe | — | |
MD5:— | SHA256:— | |||
| 6756 | WeMod-Setup-638582091671773071.exe | C:\Users\admin\AppData\Local\SquirrelTemp\WeMod-9.8.0-full.nupkg | — | |
MD5:— | SHA256:— | |||
| 6772 | Update.exe | C:\Users\admin\AppData\Local\WeMod\packages\WeMod-9.8.0-full.nupkg | — | |
MD5:— | SHA256:— | |||
| 6296 | Asphalt 8 Airborne Trainer New.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:9990EC810CD6A0FA03215FA2C1C966E0 | SHA256:9B74609BFD1B8AE3531932BAA47A05F1EDEAED7AE2DA2A61EDA9A44271A5105A | |||
| 6772 | Update.exe | C:\Users\admin\AppData\Local\WeMod\app-9.8.0\chrome_200_percent.pak | binary | |
MD5:77088F98A0F7EA522795BAEC5C930D03 | SHA256:83D9243037B2F7E62D0FDFCE19CA72E488C18E9691961E2D191E84FB3F2F7A5D | |||
| 6772 | Update.exe | C:\Users\admin\AppData\Local\WeMod\app-9.8.0\icudtl.dat | — | |
MD5:— | SHA256:— | |||
| 6772 | Update.exe | C:\Users\admin\AppData\Local\WeMod\app-9.8.0\d3dcompiler_47.dll | executable | |
MD5:A7B7470C347F84365FFE1B2072B4F95C | SHA256:AF7B99BE1B8770C0E4D18E43B04E81D11BDEB667FA6B07ADE7A88F4C5676BF9A | |||
| 6756 | WeMod-Setup-638582091671773071.exe | C:\Users\admin\AppData\Local\SquirrelTemp\Update.exe | executable | |
MD5:807A97BA81B43E0D8B4D4FBE21937398 | SHA256:08B481219F081C6F4358DB776D4A273DB280EF29B8D50B8E81875FFDB860BAF9 | |||
| 6296 | Asphalt 8 Airborne Trainer New.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\AH8CR9J5\Inter-Black-14a450a3d2[1].woff | binary | |
MD5:14A450A3D2FD191FCEFA23B273BAAF14 | SHA256:95201F343A7EC66DBF5F9316A1E1A16AE65BEC02B4243F5B645CC6D484E42267 | |||
| 6296 | Asphalt 8 Airborne Trainer New.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\Inter-Medium-5ce3e4db96[1].woff | woff | |
MD5:5CE3E4DB9634913232403F166B2447DE | SHA256:68D52E74E8171DDB2C94CA60A2596DC8A46407320449881FD09369DBC317624C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
145
DNS requests
189
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6864 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 313 b | whitelisted |
6896 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | whitelisted |
3044 | WeModAuxiliaryService.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | US | binary | 471 b | whitelisted |
3044 | WeModAuxiliaryService.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | US | binary | 727 b | whitelisted |
3044 | WeModAuxiliaryService.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEA2LpfdFcSPbdVFa0X9jdfU%3D | US | binary | 727 b | whitelisted |
6820 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | US | text | 8 b | whitelisted |
6820 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | US | text | 90 b | whitelisted |
6820 | firefox.exe | POST | 200 | 216.58.206.35:80 | http://o.pki.goog/wr2 | US | binary | 472 b | unknown |
6820 | firefox.exe | POST | 200 | 184.24.77.57:80 | http://r10.o.lencr.org/ | DE | binary | 504 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1784 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2680 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6296 | Asphalt 8 Airborne Trainer New.exe | 104.22.42.75:443 | api.wemod.com | CLOUDFLARENET | — | unknown |
6296 | Asphalt 8 Airborne Trainer New.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1784 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
5336 | SearchApp.exe | 104.126.37.177:443 | www.bing.com | Akamai International B.V. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
api.wemod.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
th.bing.com |
| whitelisted |
storage-cdn.wemod.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1776 | msedge.exe | Misc activity | SUSPICIOUS [ANY.RUN] Tracking Service (.popin .cc) |
1776 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
1776 | msedge.exe | Misc activity | SUSPICIOUS [ANY.RUN] Tracking Service (.popin .cc) |
1776 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |