| File name: | 1.exe |
| Full analysis: | https://app.any.run/tasks/d24cbea0-0a75-4dba-aab2-c14adb9bed97 |
| Verdict: | No threats detected |
| Analysis date: | March 26, 2019, 02:07:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | CC513A41C65F68523D2DB11725468C3F |
| SHA1: | E0EF8B95A9E1E7DF6F0DB0DE8620D7BB3CD20080 |
| SHA256: | 4248C7D5EFAC86FD8AB763C1F86E4E295C0AEDE3F80210B5CAB864BC8299AB75 |
| SSDEEP: | 49152:GRG5IlbCtDnDl1W70r/7KFnQ9p8S/nkb18hG6mKm:4G5IRCd+0XcnXAJQ64 |
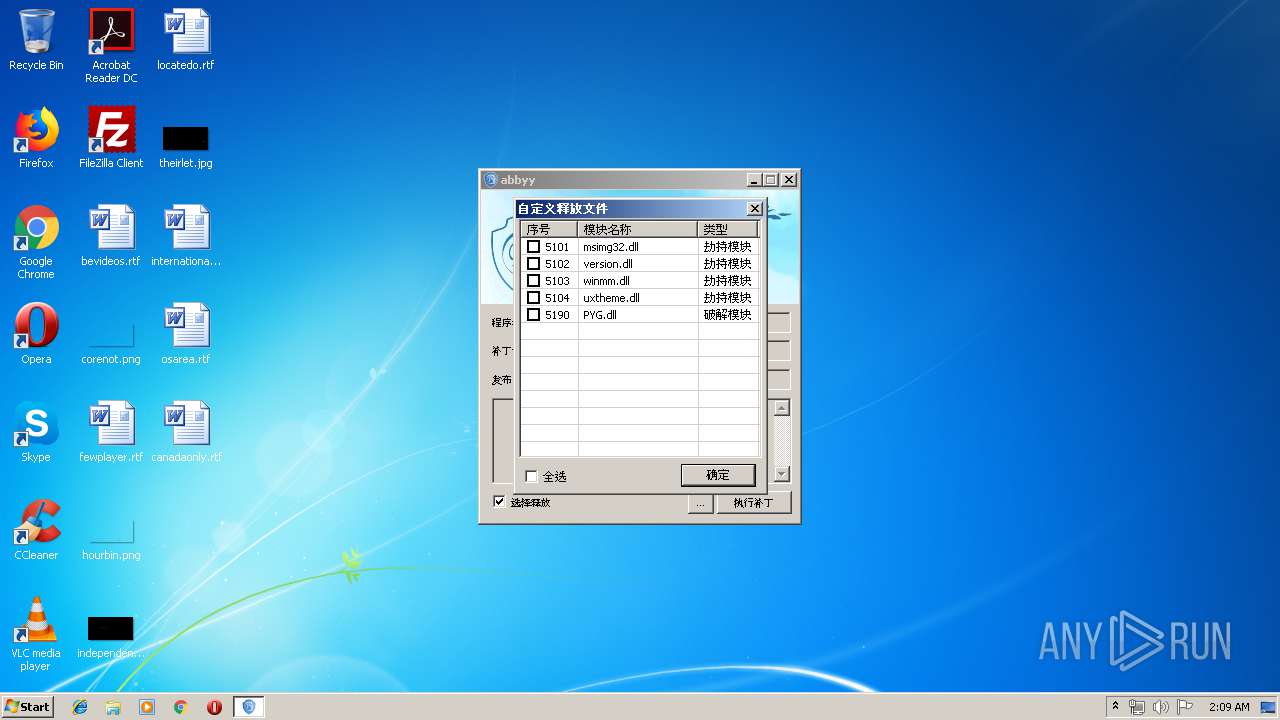
MALICIOUS
Loads dropped or rewritten executable
- 1.exe (PID: 1344)
SUSPICIOUS
Application launched itself
- 1.exe (PID: 1360)
Executable content was dropped or overwritten
- 1.exe (PID: 1360)
Reads internet explorer settings
- 1.exe (PID: 1360)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:05:01 14:05:31+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | - |
| InitializedDataSize: | - |
| UninitializedDataSize: | - |
| EntryPoint: | 0x273087 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.0.3.1005 |
| ProductVersionNumber: | 2.0.3.1005 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
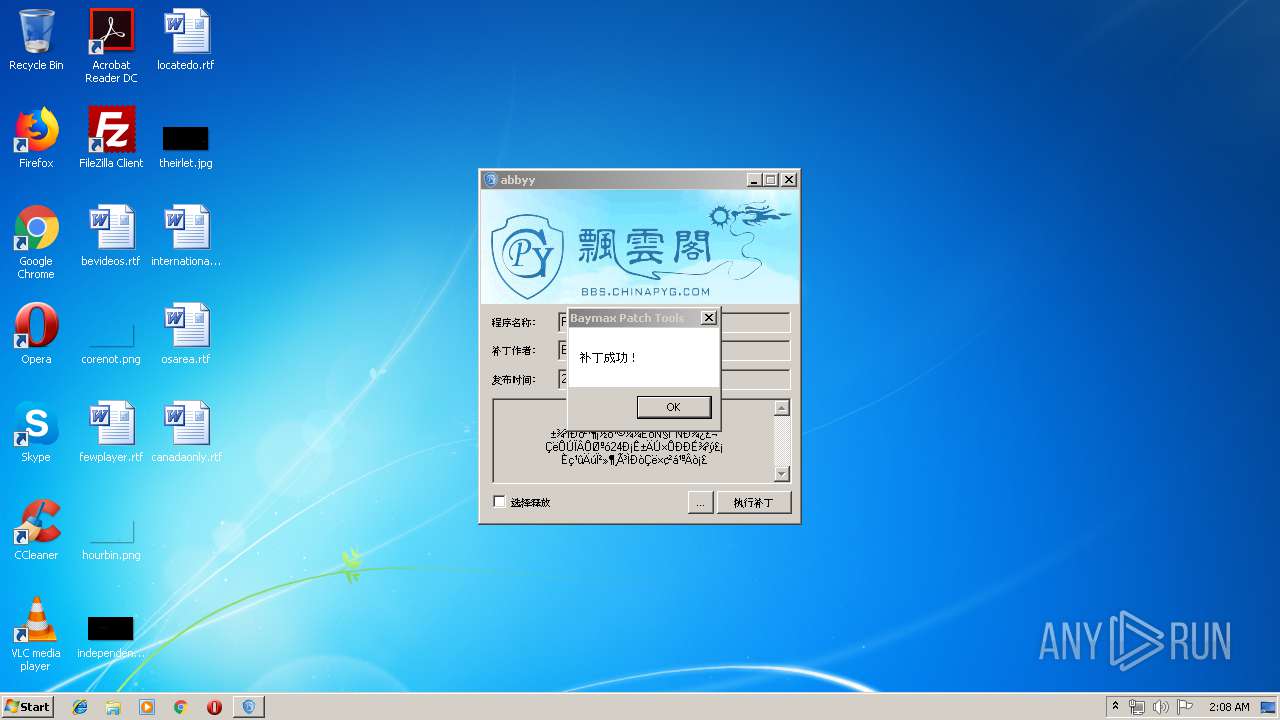
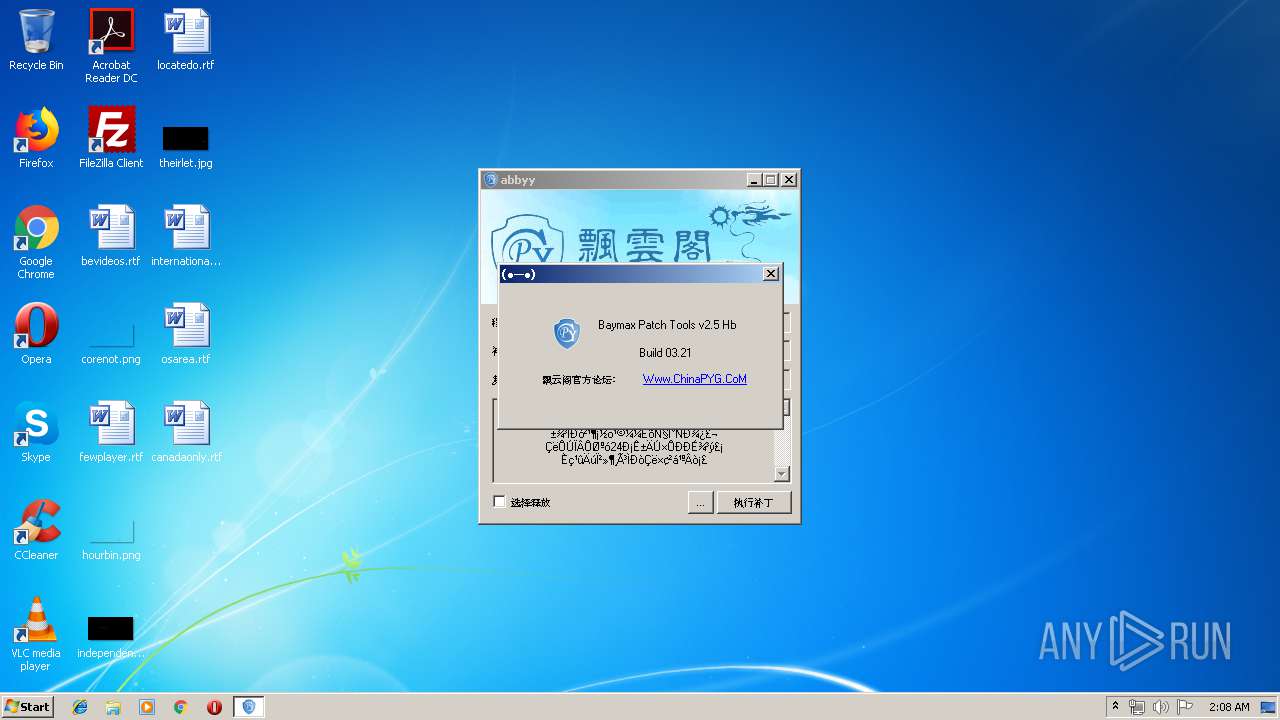
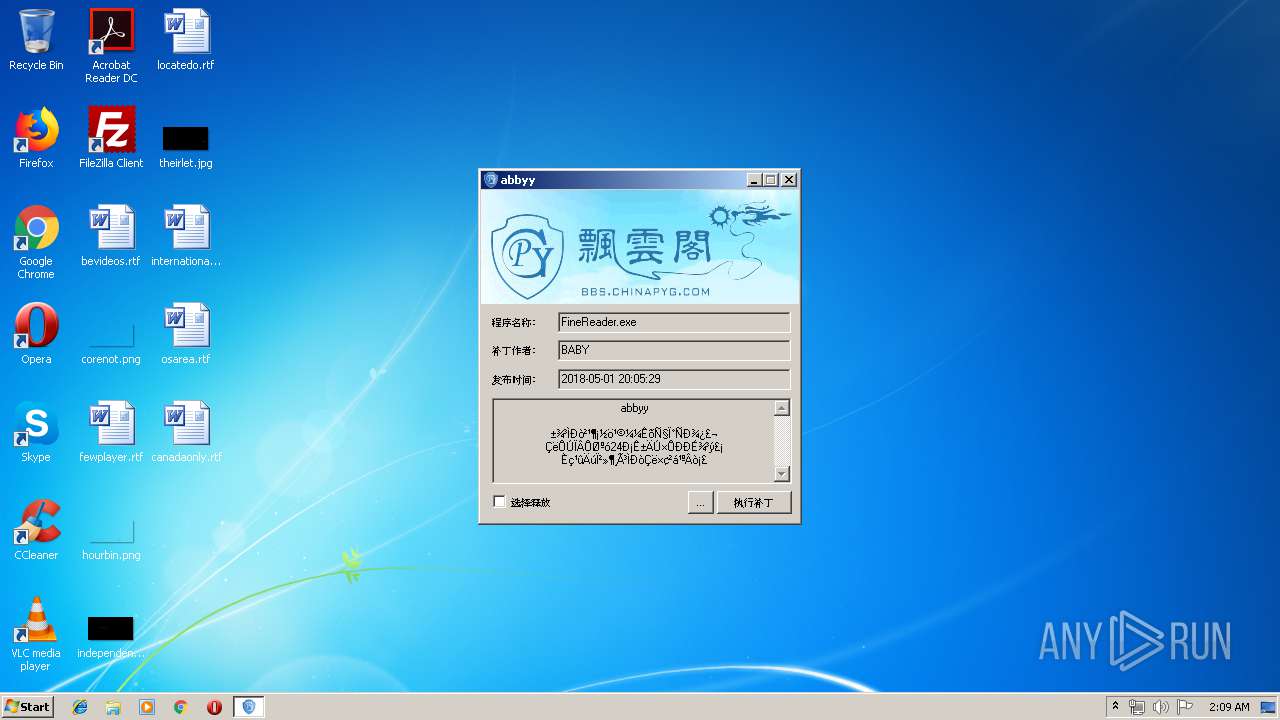
| Comments: | Www.ChinaPYG.CoM |
| CompanyName: | 飘云阁官方论坛 |
| FileDescription: | Baymax Patch Tools |
| FileVersion: | 2, 0, 3, 1005 |
| InternalName: | PatchUi.exe |
| LegalCopyright: | Copyright 2015 |
| OriginalFileName: | PatchUi.exe |
| ProductName: | PatchUi |
| ProductVersion: | 2, 0, 3, 1005 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-May-2018 12:05:31 |
| Detected languages: |
|
| Comments: | Www.ChinaPYG.CoM |
| CompanyName: | 飘云阁官方论坛 |
| FileDescription: | Baymax Patch Tools |
| FileVersion: | 2, 0, 3, 1005 |
| InternalName: | PatchUi.exe |
| LegalCopyright: | Copyright 2015 |
| OriginalFilename: | PatchUi.exe |
| ProductName: | PatchUi |
| ProductVersion: | 2, 0, 3, 1005 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 01-May-2018 12:05:31 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x001A4000 | 0x001A4000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.44305 |
.UPX | 0x0027F000 | 0x00001000 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.98306 |
.idata | 0x00275000 | 0x00002000 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_NOT_PAGED, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.00992 |
.rsrc | 0x00277000 | 0x00008000 | 0x00007200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.45512 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.02785 | 629 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 4.16426 | 2216 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
3 | 3.68913 | 1736 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
4 | 3.05281 | 1384 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
5 | 5.76511 | 9640 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
6 | 5.92826 | 4264 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
7 | 5.98476 | 2440 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
8 | 5.91618 | 1128 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
128 | 2.85812 | 118 | Latin 1 / Western European | Chinese - PRC | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
IPHLPAPI.DLL |
KERNEL32.dll |
MSVCRT.dll |
OLEAUT32.dll |
PSAPI.DLL |
SHELL32.dll |
Total processes
36
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
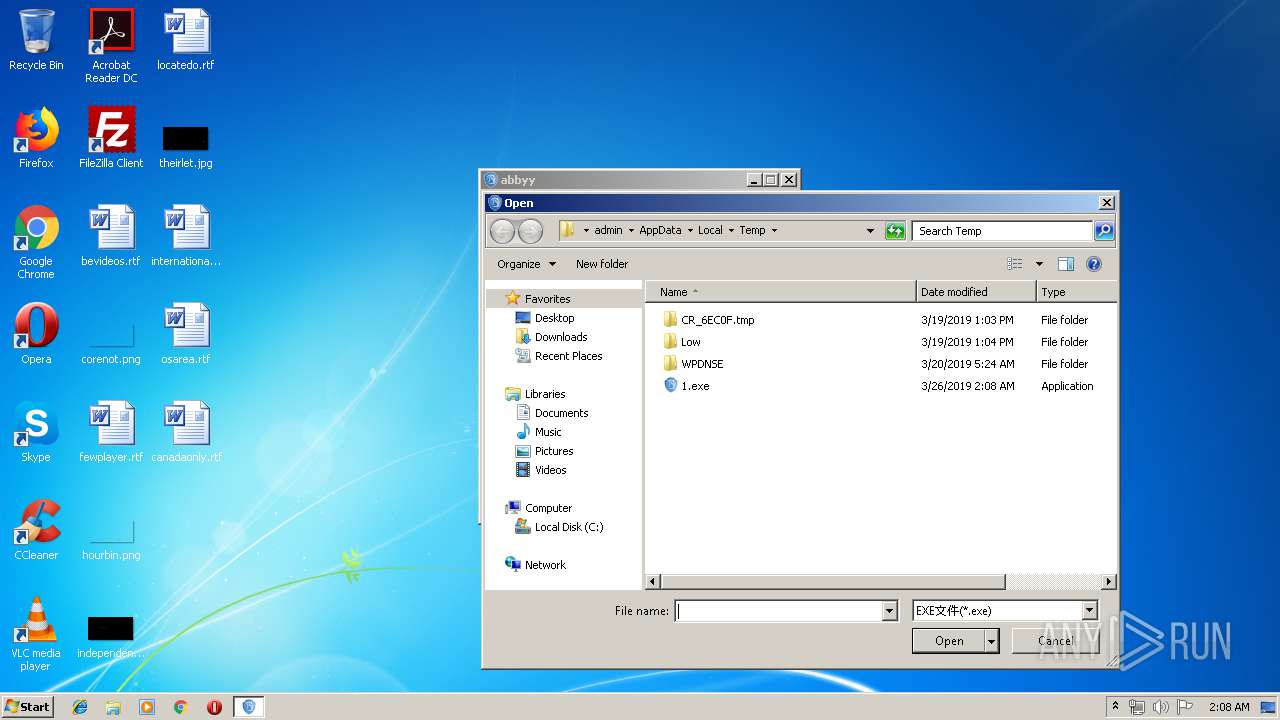
| 1208 | "C:\Users\admin\AppData\Local\Temp\1.exe" | C:\Users\admin\AppData\Local\Temp\1.exe | — | explorer.exe | |||||||||||
User: admin Company: 飘云阁官方论坛 Integrity Level: MEDIUM Description: Baymax Patch Tools Exit code: 3221226540 Version: 2, 0, 3, 1005 Modules
| |||||||||||||||
| 1344 | "C:\Users\admin\AppData\Local\Temp\1.exe" -baymax | C:\Users\admin\AppData\Local\Temp\1.exe | 1.exe | ||||||||||||
User: admin Company: 飘云阁官方论坛 Integrity Level: HIGH Description: Baymax Patch Tools Exit code: 4294967295 Version: 2, 0, 3, 1005 Modules
| |||||||||||||||
| 1360 | "C:\Users\admin\AppData\Local\Temp\1.exe" | C:\Users\admin\AppData\Local\Temp\1.exe | explorer.exe | ||||||||||||
User: admin Company: 飘云阁官方论坛 Integrity Level: HIGH Description: Baymax Patch Tools Exit code: 0 Version: 2, 0, 3, 1005 Modules
| |||||||||||||||
Total events
644
Read events
556
Write events
85
Delete events
3
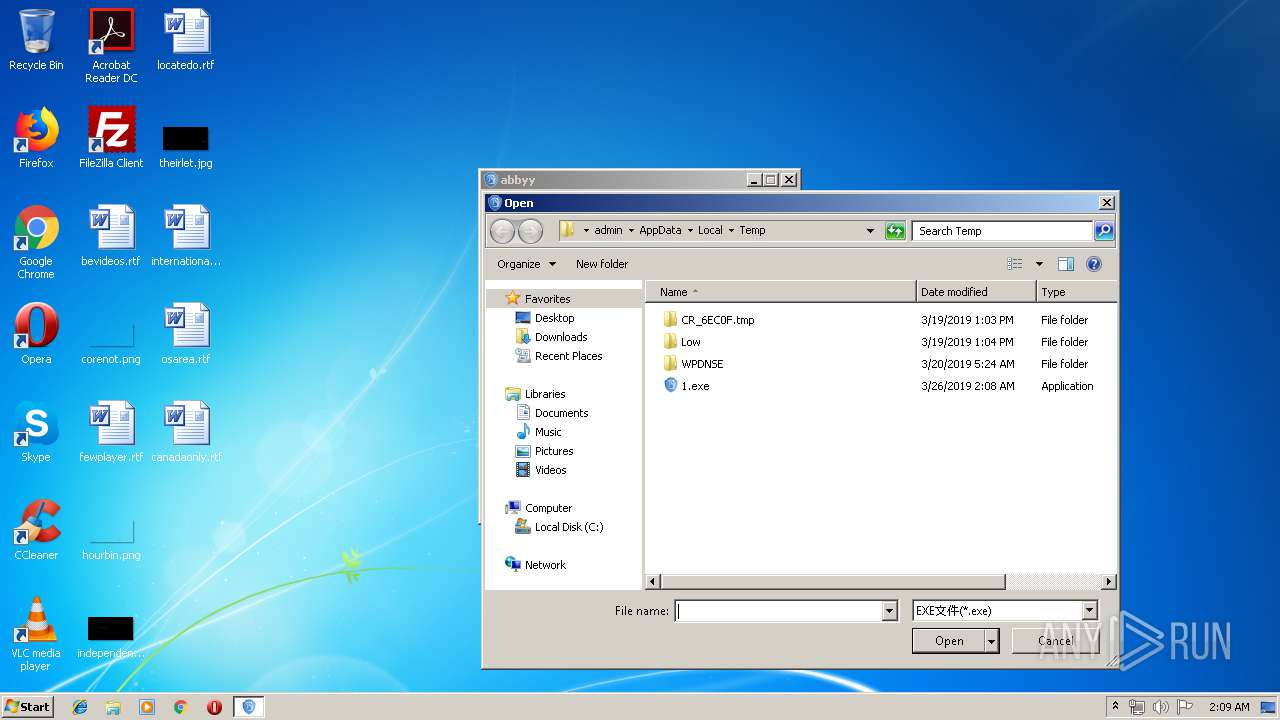
Modification events
| (PID) Process: | (1360) 1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\FirstFolder |
| Operation: | write | Name: | 0 |
Value: 43003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C0031002E00650078006500000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070000000 | |||
| (PID) Process: | (1360) 1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\FirstFolder |
| Operation: | write | Name: | MRUListEx |
Value: 00000000FFFFFFFF | |||
| (PID) Process: | (1360) 1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\LastVisitedPidlMRU |
| Operation: | write | Name: | MRUListEx |
Value: FFFFFFFF | |||
| (PID) Process: | (1360) 1.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (1360) 1.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 0700000000000000010000000200000006000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (1360) 1.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\7 |
| Operation: | write | Name: | MRUListEx |
Value: 0100000000000000FFFFFFFF | |||
| (PID) Process: | (1360) 1.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\7\1\0 |
| Operation: | write | Name: | 1 |
Value: 4A003100000000007A4E0811102054656D700000360008000400EFBE454B814A7A4E08112A00000090010000000002000000000000000000000000000000540065006D007000000014000000 | |||
| (PID) Process: | (1360) 1.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\7\1\0 |
| Operation: | write | Name: | MRUListEx |
Value: 0100000000000000FFFFFFFF | |||
| (PID) Process: | (1360) 1.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 0202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (1360) 1.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\7\1\0\1 |
| Operation: | write | Name: | NodeSlot |
Value: 95 | |||
Executable files
5
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1360 | 1.exe | C:\Users\admin\AppData\Local\Temp\uxtheme.dll | executable | |
MD5:— | SHA256:— | |||
| 1360 | 1.exe | C:\Users\admin\AppData\Local\Temp\msimg32.dll | executable | |
MD5:F994A511B6EB1A92CC2676049C646F7B | SHA256:CF84497EBFBD390CA18B5A3C66866A37A2AA4D5C993165DFD11B87B8916CF062 | |||
| 1360 | 1.exe | C:\Users\admin\AppData\Local\Temp\winmm.dll | executable | |
MD5:93DF90916B6144FB9CED19F55421C73F | SHA256:7248876F24E9D06D875E52EAD1EA85F385B021A43495D89ECFA2D7EE57B97A36 | |||
| 1360 | 1.exe | C:\Users\admin\AppData\Local\Temp\PYG.dll | executable | |
MD5:4684264D219456CC2A86F4EDD9904DF4 | SHA256:BF0C2A7630FC96C3905C3B731DB0196552E0C3150BB09DD23FF231630E5A28FC | |||
| 1360 | 1.exe | C:\Users\admin\AppData\Local\Temp\version.dll | executable | |
MD5:0C7E47850C98857C937218359541D13E | SHA256:9AA229E14A15FC551610E503EE310A01C87275580F10D27E3BFA3D0A003FC67C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
1.exe | [NSDLL]version.dll Has Auto Inject ... |
1.exe | -baymax |
1.exe | -baymax |
1.exe | NS_INJECT_FIND Module |