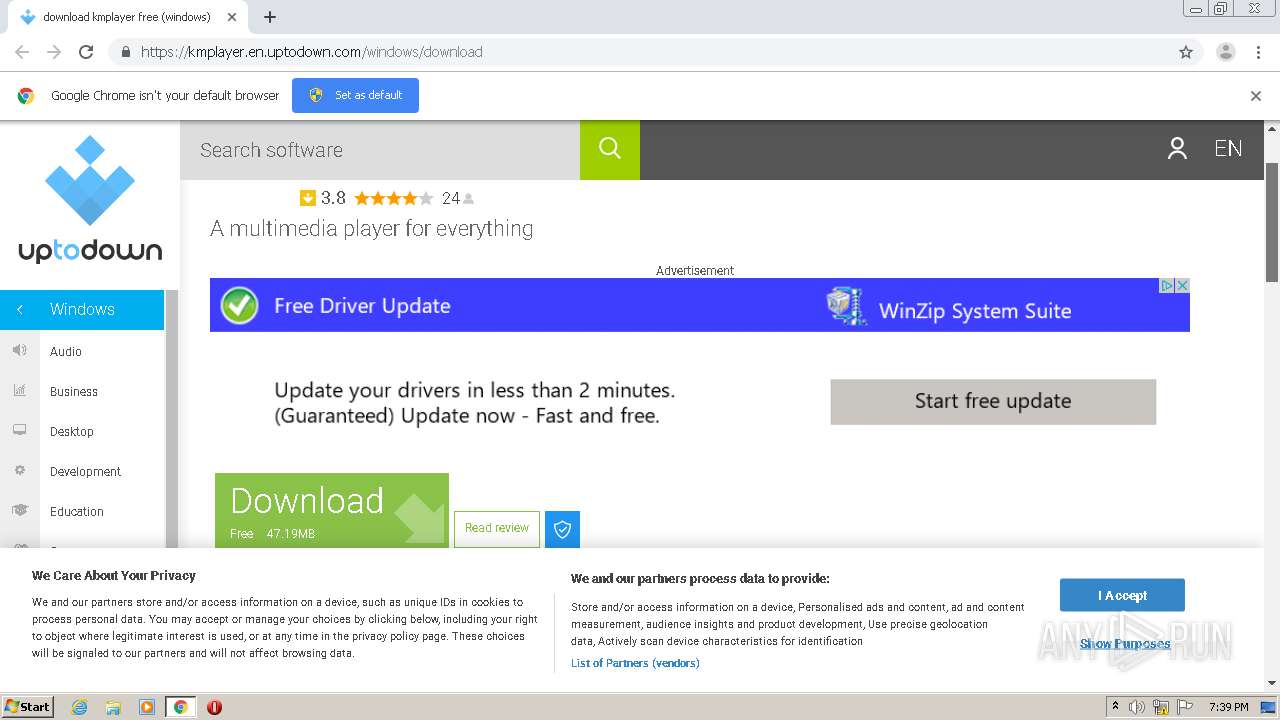
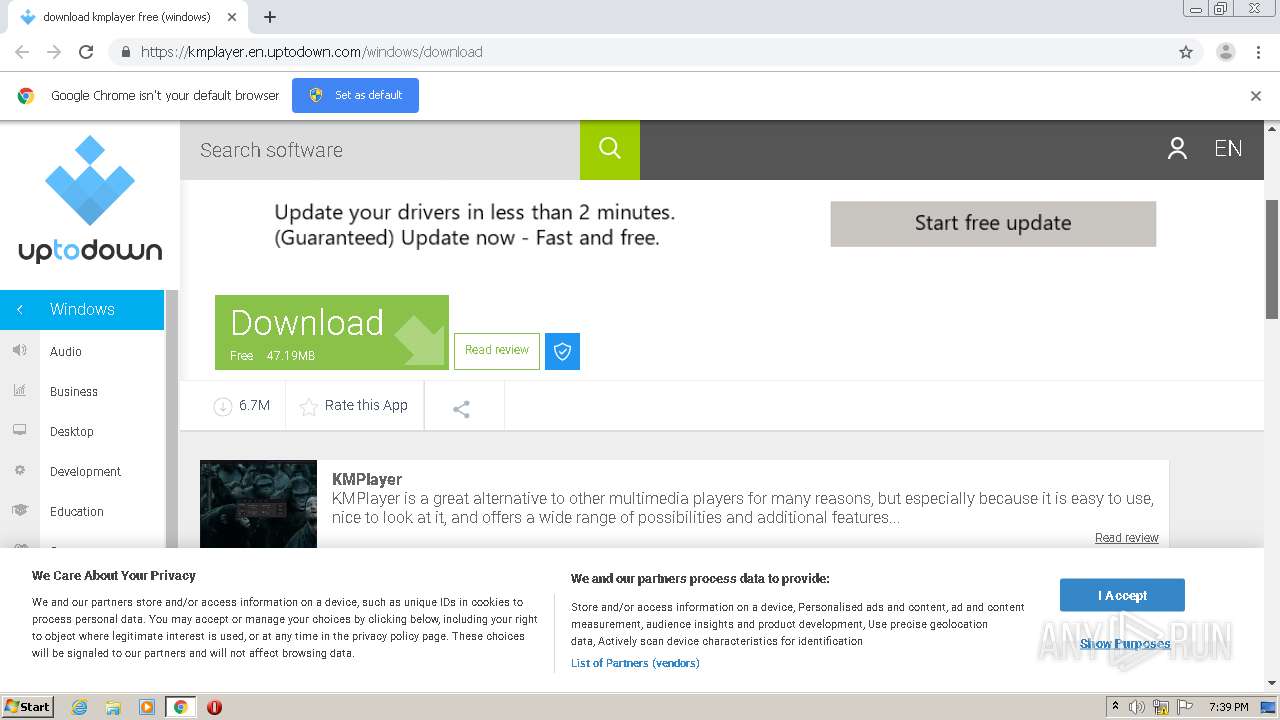
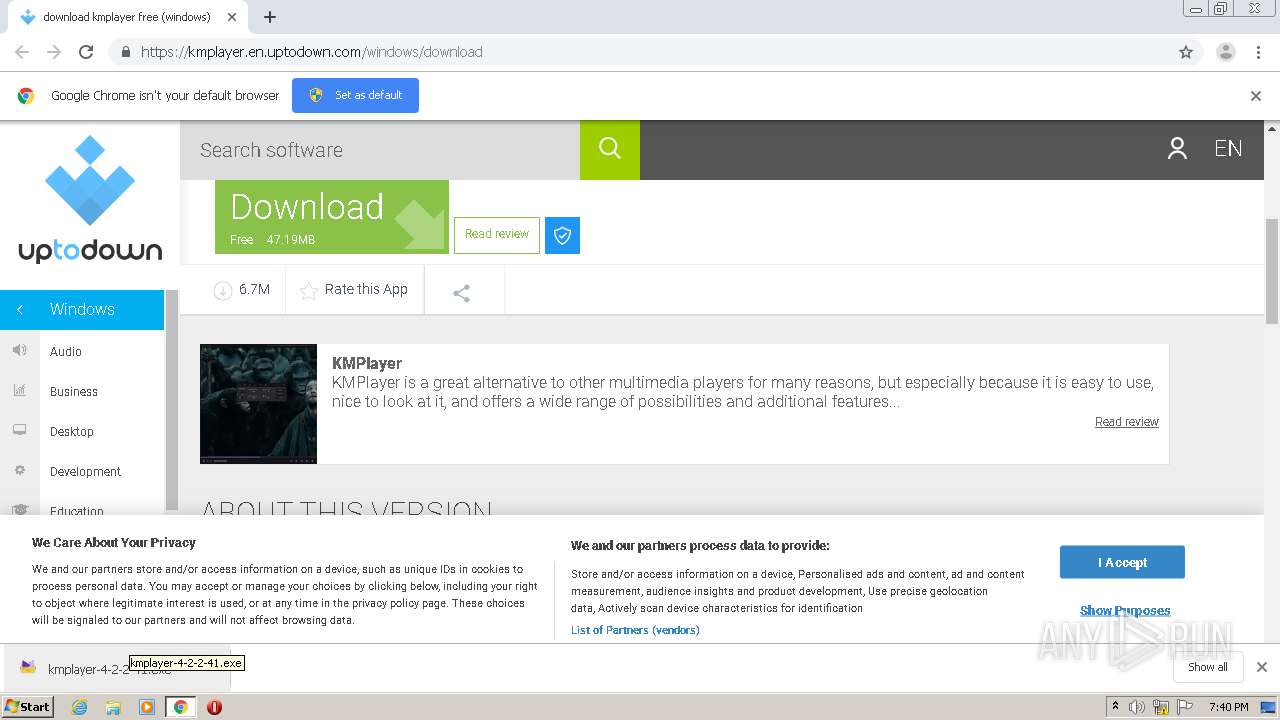
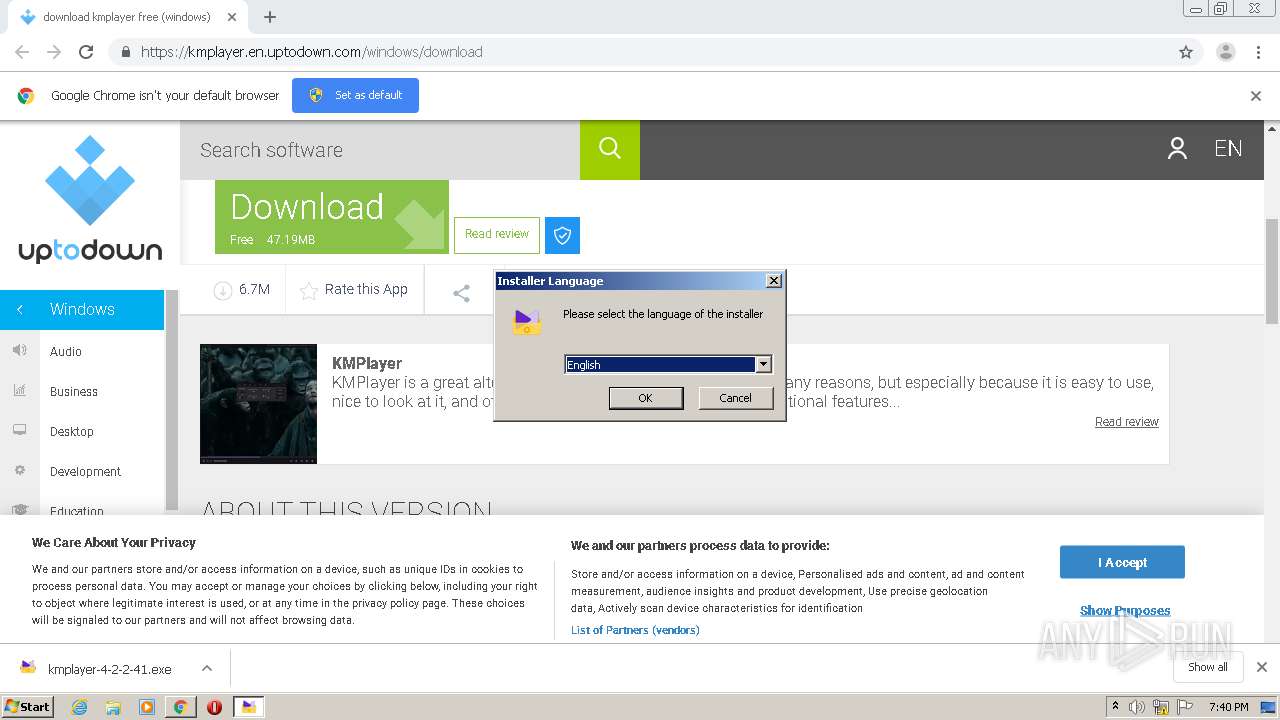
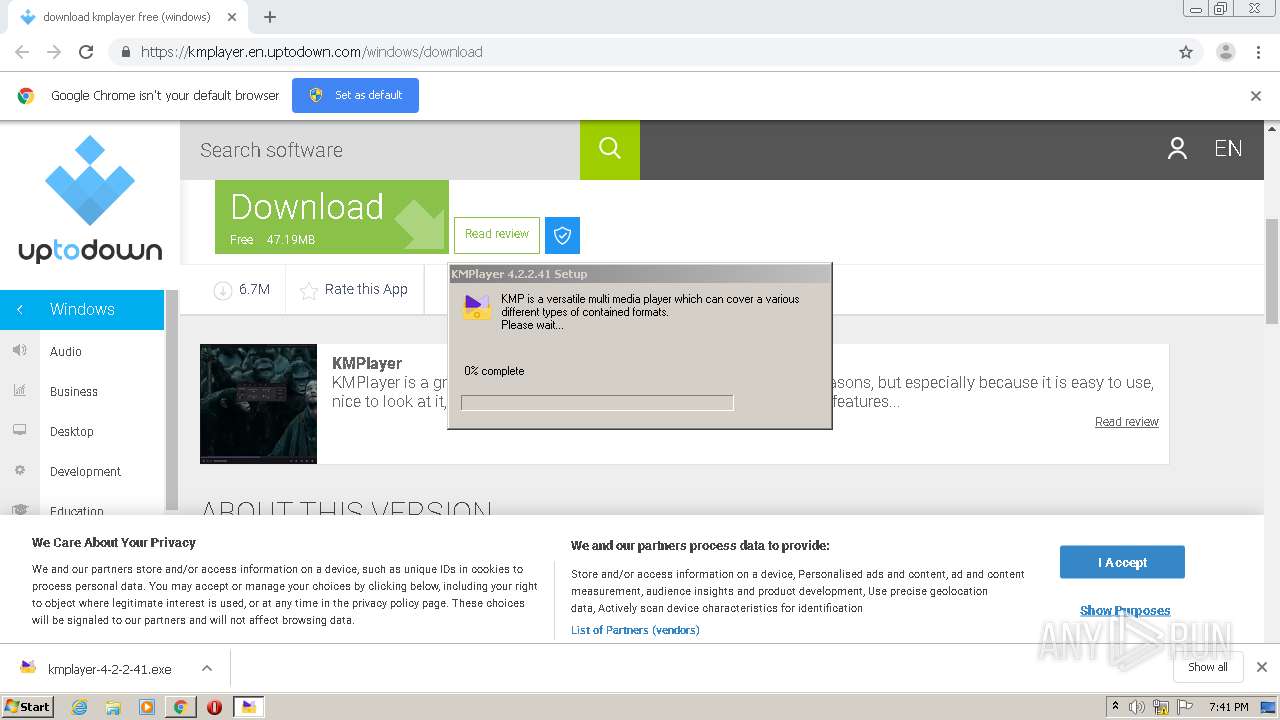
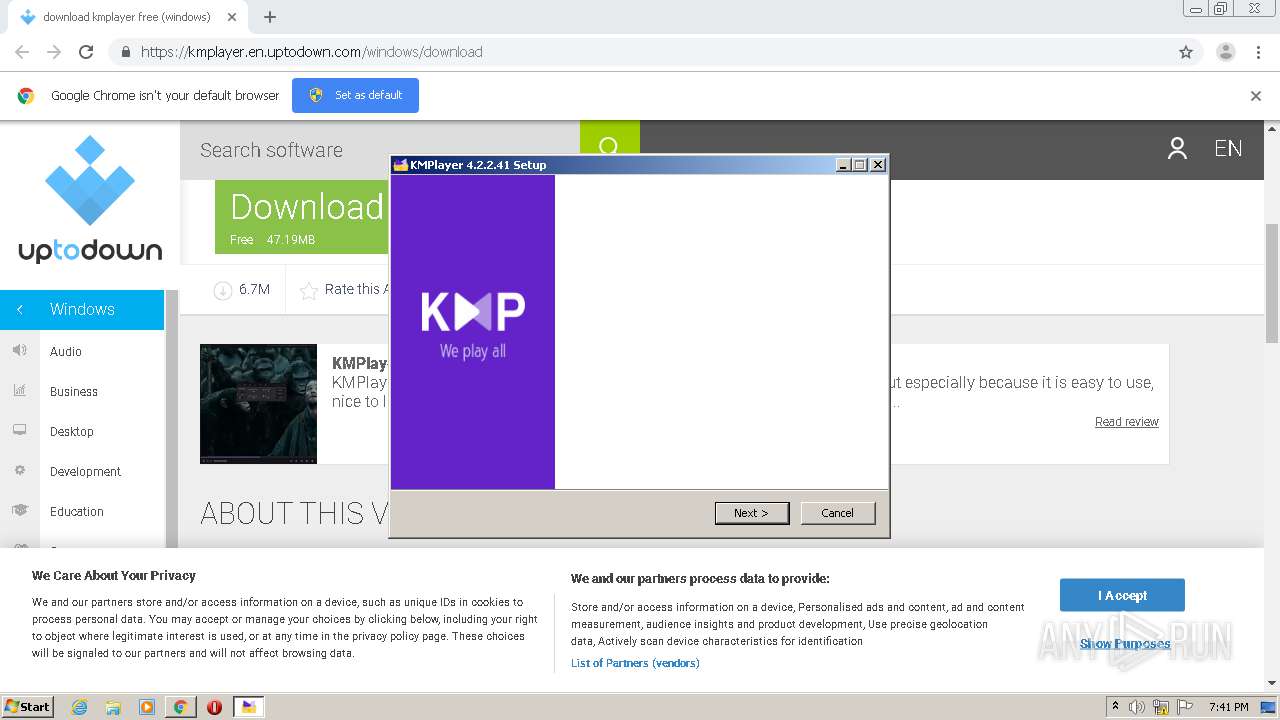
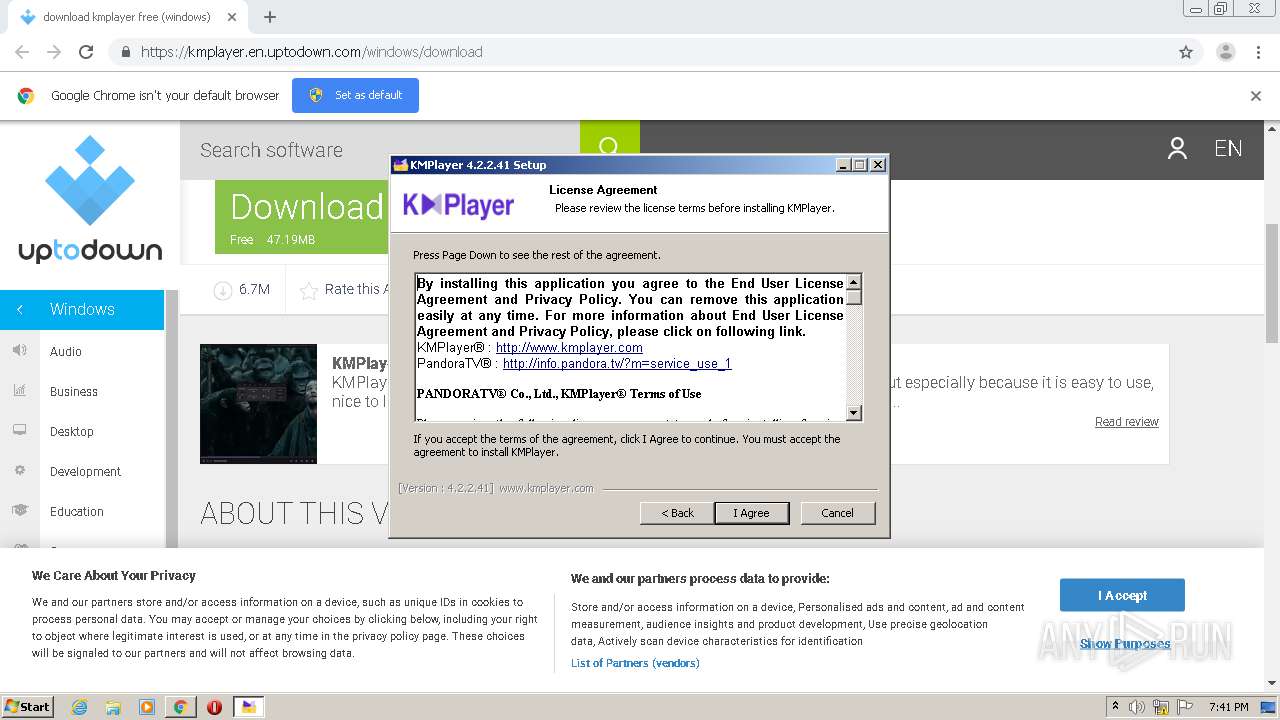
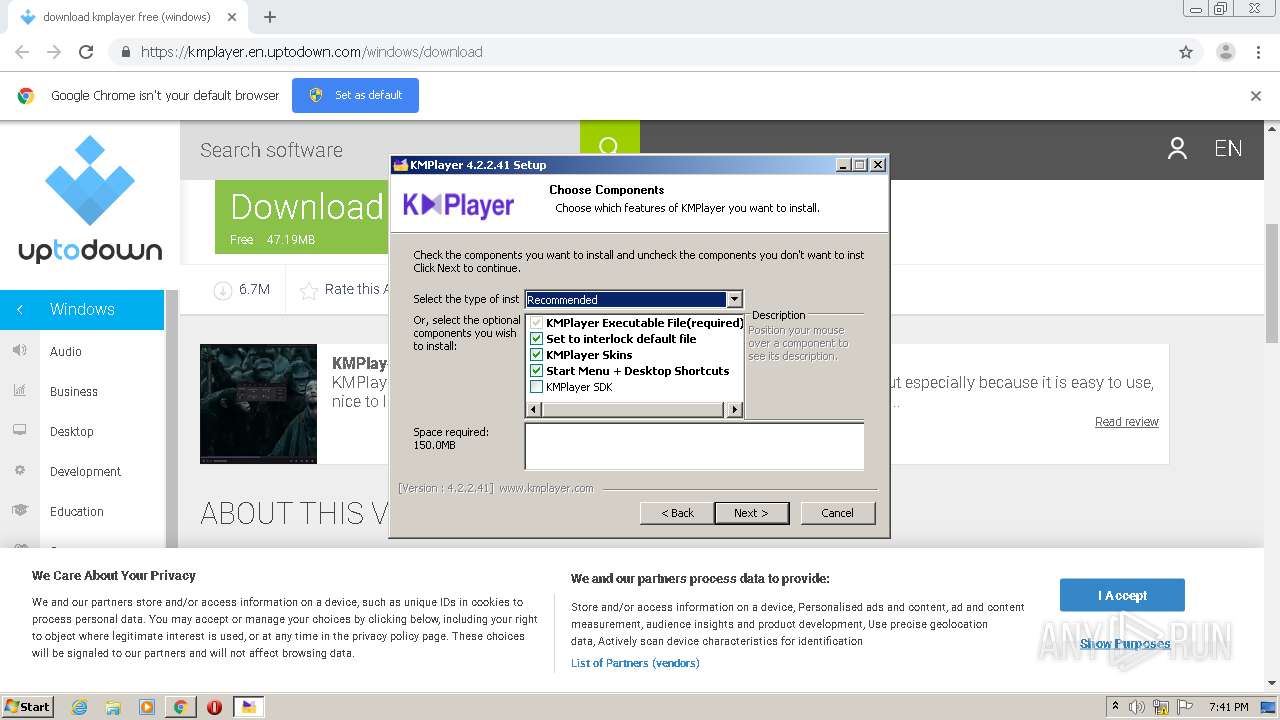
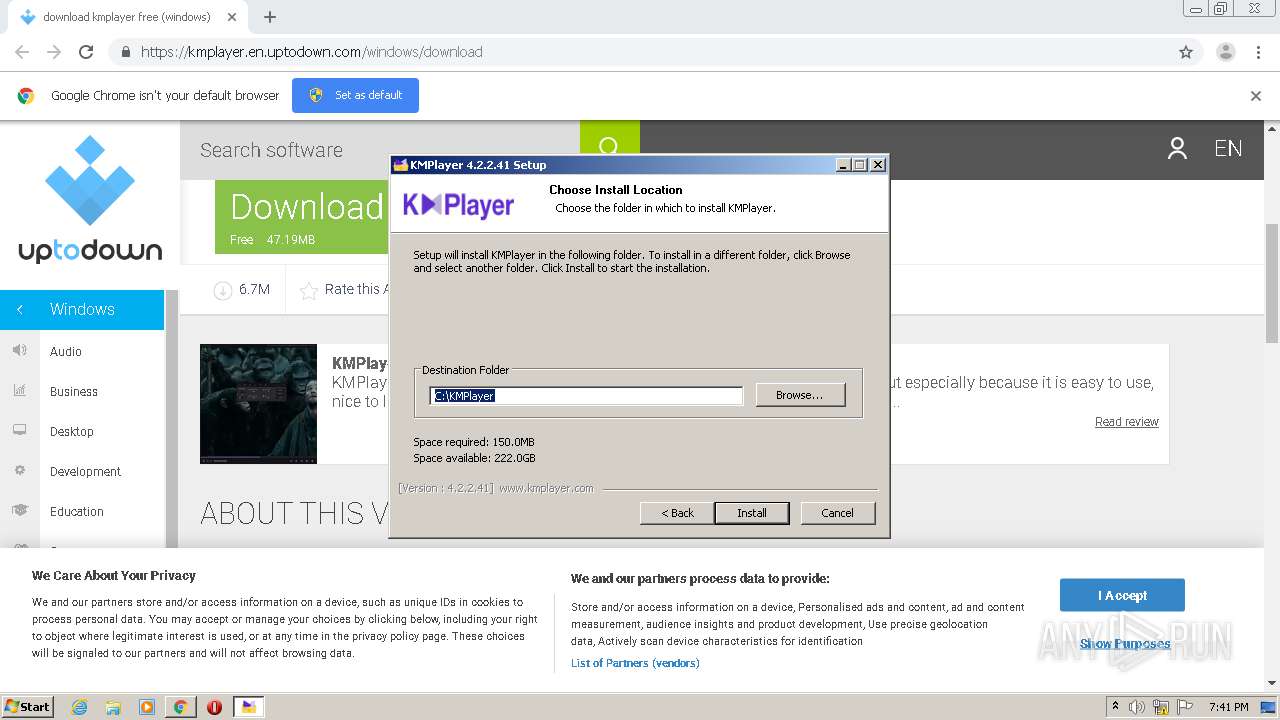
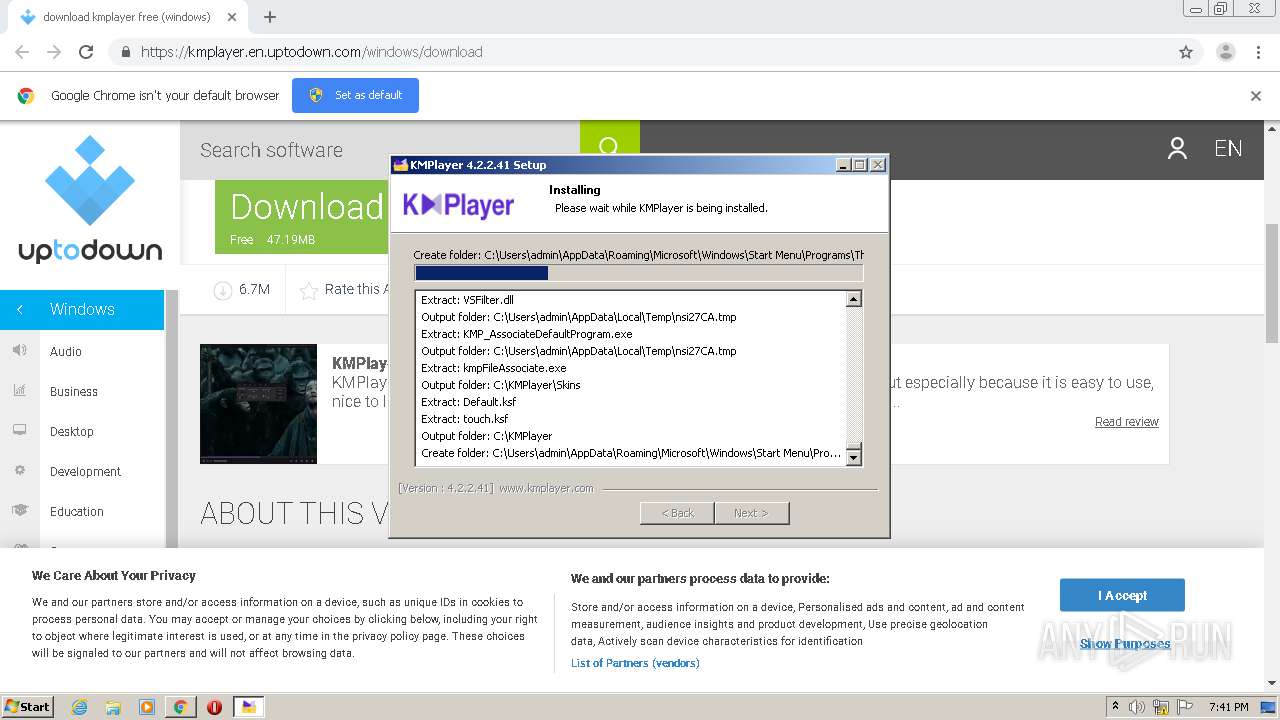
| URL: | https://kmplayer.en.uptodown.com/windows/download |
| Full analysis: | https://app.any.run/tasks/ac84ea31-5d7b-41ee-9687-c6a1d4f9ca62 |
| Verdict: | Malicious activity |
| Analysis date: | September 01, 2020, 18:38:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 90114B7A0C06AB9AA74887E3B06A3C7F |
| SHA1: | 59DA6E4773F4B1689E259768AF026CBE37803778 |
| SHA256: | 42465CAFDACFEEA28227583B7211F27F57AA19DFCF0383A0716C66ED8246A81F |
| SSDEEP: | 3:N8N4cAb5Vsbd3SMjKM:2qcAbLU3SpM |
MALICIOUS
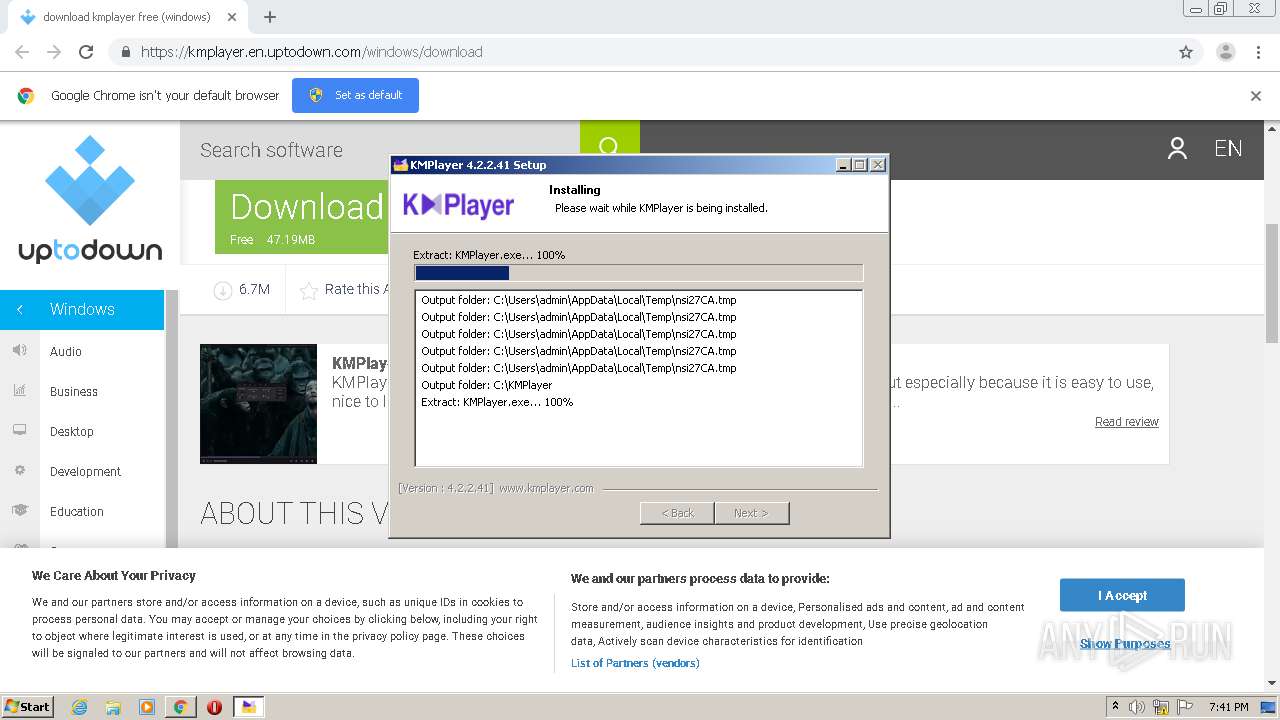
Application was dropped or rewritten from another process
- kmplayer-4-2-2-41.exe (PID: 3924)
- kmplayer-4-2-2-41.exe (PID: 3520)
- KMPlayer.exe (PID: 944)
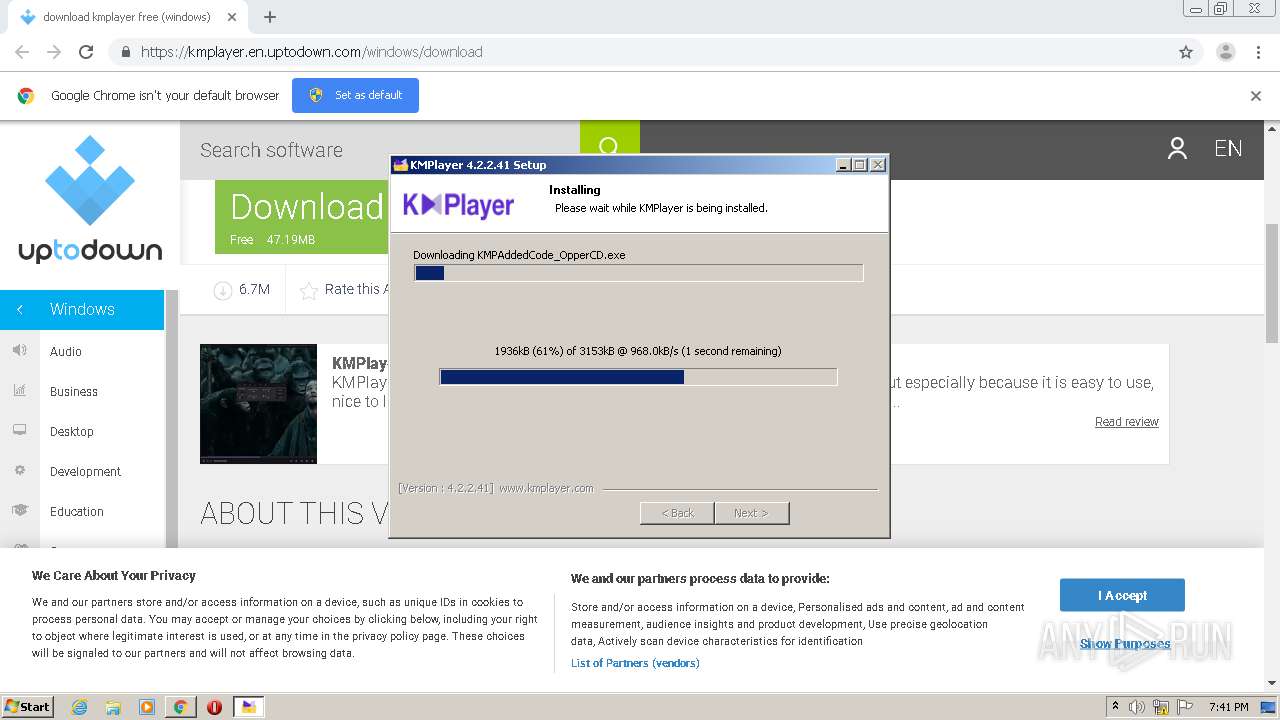
- KMPAddedCode_OpperCD.exe (PID: 1256)
- pin2taskbar.exe (PID: 2948)
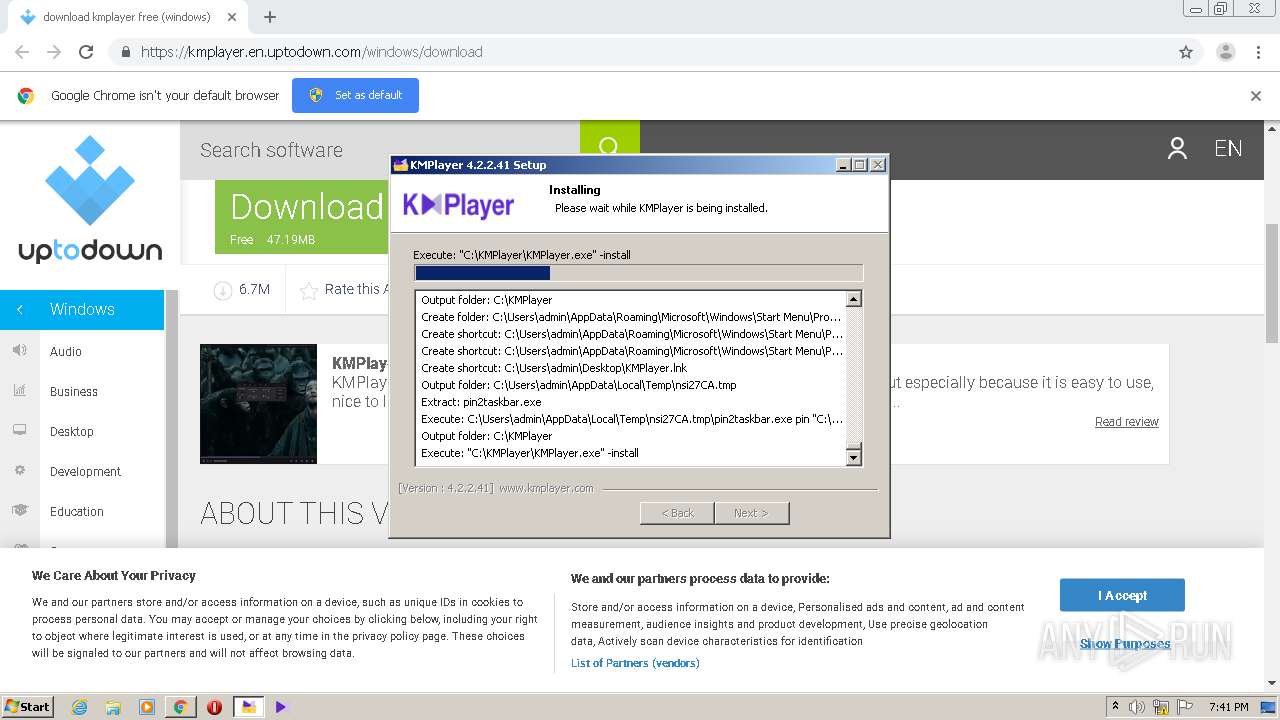
Loads dropped or rewritten executable
- kmplayer-4-2-2-41.exe (PID: 3520)
- KMPlayer.exe (PID: 944)
- KMPAddedCode_OpperCD.exe (PID: 1256)
Actions looks like stealing of personal data
- KMPAddedCode_OpperCD.exe (PID: 1256)
Downloads executable files from the Internet
- kmplayer-4-2-2-41.exe (PID: 3520)
SUSPICIOUS
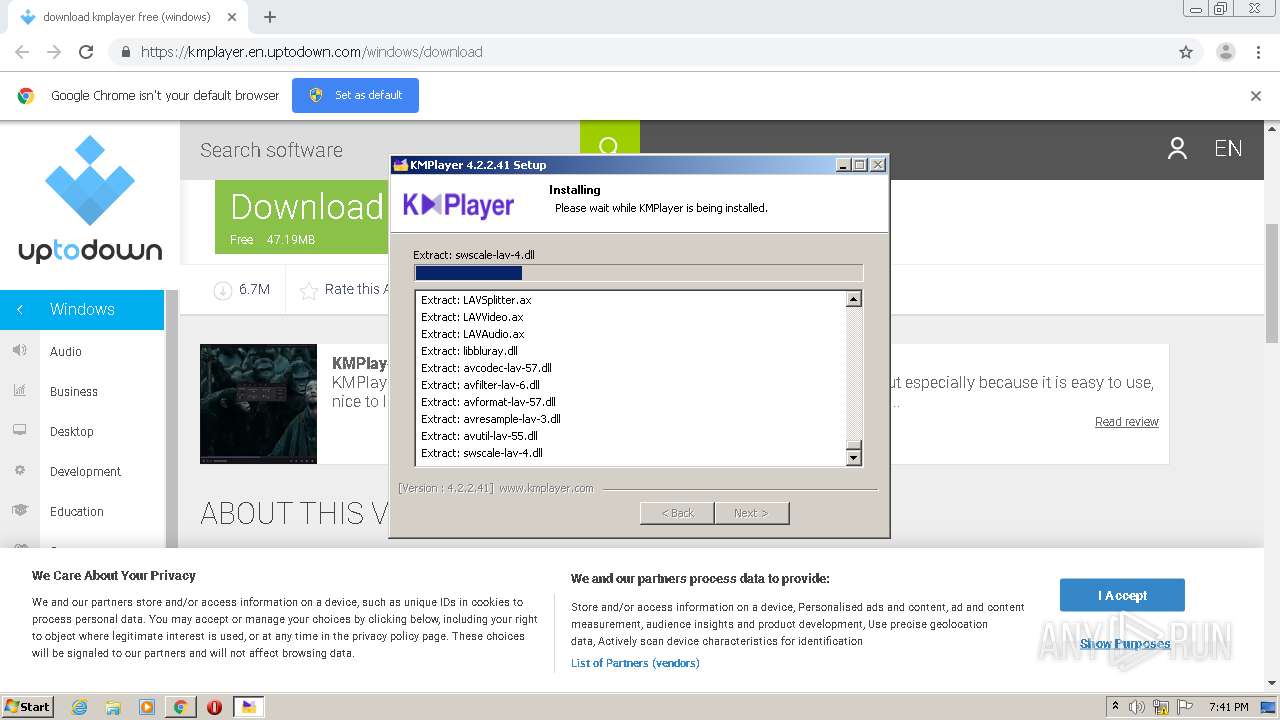
Executable content was dropped or overwritten
- chrome.exe (PID: 2984)
- kmplayer-4-2-2-41.exe (PID: 3520)
- KMPAddedCode_OpperCD.exe (PID: 1256)
Reads Internet Cache Settings
- kmplayer-4-2-2-41.exe (PID: 3520)
- KMPlayer.exe (PID: 944)
- KMPAddedCode_OpperCD.exe (PID: 1256)
Changes IE settings (feature browser emulation)
- kmplayer-4-2-2-41.exe (PID: 3520)
- KMPlayer.exe (PID: 944)
Creates a software uninstall entry
- kmplayer-4-2-2-41.exe (PID: 3520)
Creates COM task schedule object
- kmplayer-4-2-2-41.exe (PID: 3520)
Creates files in the user directory
- kmplayer-4-2-2-41.exe (PID: 3520)
- pin2taskbar.exe (PID: 2948)
Reads internet explorer settings
- KMPAddedCode_OpperCD.exe (PID: 1256)
Reads Environment values
- KMPAddedCode_OpperCD.exe (PID: 1256)
Creates files in the program directory
- KMPAddedCode_OpperCD.exe (PID: 1256)
INFO
Reads the hosts file
- chrome.exe (PID: 2916)
- chrome.exe (PID: 2984)
Application launched itself
- chrome.exe (PID: 2984)
Reads settings of System Certificates
- chrome.exe (PID: 2984)
Reads Internet Cache Settings
- chrome.exe (PID: 2984)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
63
Monitored processes
21
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 944 | "C:\KMPlayer\KMPlayer.exe" -install | C:\KMPlayer\KMPlayer.exe | kmplayer-4-2-2-41.exe | ||||||||||||
User: admin Company: PandoraTV Integrity Level: HIGH Description: The KMPlayer Exit code: 0 Version: 4.2.2.41 Modules
| |||||||||||||||
| 1256 | "C:\Users\admin\AppData\Local\Temp\nsi27CA.tmp\KMPAddedCode_OpperCD.exe" | C:\Users\admin\AppData\Local\Temp\nsi27CA.tmp\KMPAddedCode_OpperCD.exe | kmplayer-4-2-2-41.exe | ||||||||||||
User: admin Company: Rol Integrity Level: HIGH Description: Sokahedah Setup Exit code: 0 Version: 4.5.1.5 Modules
| |||||||||||||||
| 1352 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1008,17075170090500430546,10614464752322525468,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=16318434215740236080 --mojo-platform-channel-handle=3276 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1448 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,17075170090500430546,10614464752322525468,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7760867422458376326 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2504 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1676 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,17075170090500430546,10614464752322525468,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=7477435277058026364 --mojo-platform-channel-handle=3136 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1732 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x717fa9d0,0x717fa9e0,0x717fa9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2536 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,17075170090500430546,10614464752322525468,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=692514043317144801 --mojo-platform-channel-handle=3008 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2704 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,17075170090500430546,10614464752322525468,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8535021125424072731 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3400 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2744 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1008,17075170090500430546,10614464752322525468,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=13013829800836568776 --mojo-platform-channel-handle=1044 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2916 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,17075170090500430546,10614464752322525468,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=17298194057131404495 --mojo-platform-channel-handle=1656 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 258
Read events
1 726
Write events
528
Delete events
4
Modification events
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3236) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2984-13243459126843750 |
Value: 259 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2832-13239195546717773 |
Value: 0 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
87
Suspicious files
70
Text files
224
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\5919f9bf-01c1-498f-961d-346c85c8bdac.tmp | — | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF1932af.TMP | text | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF193454.TMP | — | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF193260.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
65
DNS requests
37
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
944 | KMPlayer.exe | GET | — | 61.111.8.188:80 | http://log.kmplayer.com/kmp?env=(4.2.2.41)&mode=install&install=1&update=0 | KR | — | — | suspicious |
1256 | KMPAddedCode_OpperCD.exe | POST | 200 | 13.224.130.50:80 | http://static.henemicid-leh.com/ | US | binary | 881 Kb | shared |
3520 | kmplayer-4-2-2-41.exe | GET | 302 | 110.45.195.192:80 | http://update.kmpmedia.net/player/ini_goods/1/0 | KR | — | — | suspicious |
3520 | kmplayer-4-2-2-41.exe | GET | 302 | 110.45.195.192:80 | http://update.kmpmedia.net/player/goods/?sq=46&division=d | KR | — | — | suspicious |
1256 | KMPAddedCode_OpperCD.exe | POST | 200 | 13.227.150.53:80 | http://staging.henemicid-leh.com/ | US | — | — | shared |
3520 | kmplayer-4-2-2-41.exe | GET | 200 | 54.229.49.40:80 | http://www.bytetouruniverse.com/Gtbusfax84UZ8q2damWR_BZNW8_Cp6bYh04IuaIHwFdR+k6KaMQfjC6DsvFOmXDKtqwg2p8ObWI3+kNxqSnGGX_JPguVMwaIS5_eUPhvMmcPbB8IiJOGkkJazTOQq9MW325e33mbmfNox3+LbeEL9geblcgc9A==-Ow== | IE | executable | 3.08 Mb | suspicious |
3520 | kmplayer-4-2-2-41.exe | GET | 200 | 163.171.132.119:80 | http://cdn.kmplayer.com/KMP/player/ini/goods/old_00_unicode_20200207102938.7z | US | compressed | 4.73 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2916 | chrome.exe | 216.58.212.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
2916 | chrome.exe | 104.16.148.64:443 | cdn.cookielaw.org | Cloudflare Inc | US | unknown |
2916 | chrome.exe | 216.58.205.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2916 | chrome.exe | 216.58.205.228:443 | www.google.com | Google Inc. | US | whitelisted |
2916 | chrome.exe | 216.58.205.226:443 | www.googletagservices.com | Google Inc. | US | whitelisted |
2916 | chrome.exe | 216.58.212.130:443 | securepubads.g.doubleclick.net | Google Inc. | US | whitelisted |
2916 | chrome.exe | 172.217.22.46:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
2916 | chrome.exe | 216.58.208.46:443 | clients2.google.com | Google Inc. | US | whitelisted |
2916 | chrome.exe | 104.20.185.68:443 | geolocation.onetrust.com | Cloudflare Inc | US | shared |
2916 | chrome.exe | 74.125.206.155:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
kmplayer.en.uptodown.com |
| malicious |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
cdn.cookielaw.org |
| whitelisted |
stc.utdstc.com |
| suspicious |
www.googletagservices.com |
| whitelisted |
img.utdstc.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3520 | kmplayer-4-2-2-41.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
3520 | kmplayer-4-2-2-41.exe | Misc activity | SUSPICIOUS [PTsecurity] HTTP header - Sometimes used by hostile installer |
3520 | kmplayer-4-2-2-41.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
3520 | kmplayer-4-2-2-41.exe | Misc activity | SUSPICIOUS [PTsecurity] HTTP header - Sometimes used by hostile installer |
3520 | kmplayer-4-2-2-41.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
3520 | kmplayer-4-2-2-41.exe | Misc activity | SUSPICIOUS [PTsecurity] HTTP header - Sometimes used by hostile installer |
3520 | kmplayer-4-2-2-41.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
3520 | kmplayer-4-2-2-41.exe | Misc activity | SUSPICIOUS [PTsecurity] HTTP header - Sometimes used by hostile installer |
3520 | kmplayer-4-2-2-41.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3520 | kmplayer-4-2-2-41.exe | Misc activity | ET INFO EXE - Served Attached HTTP |