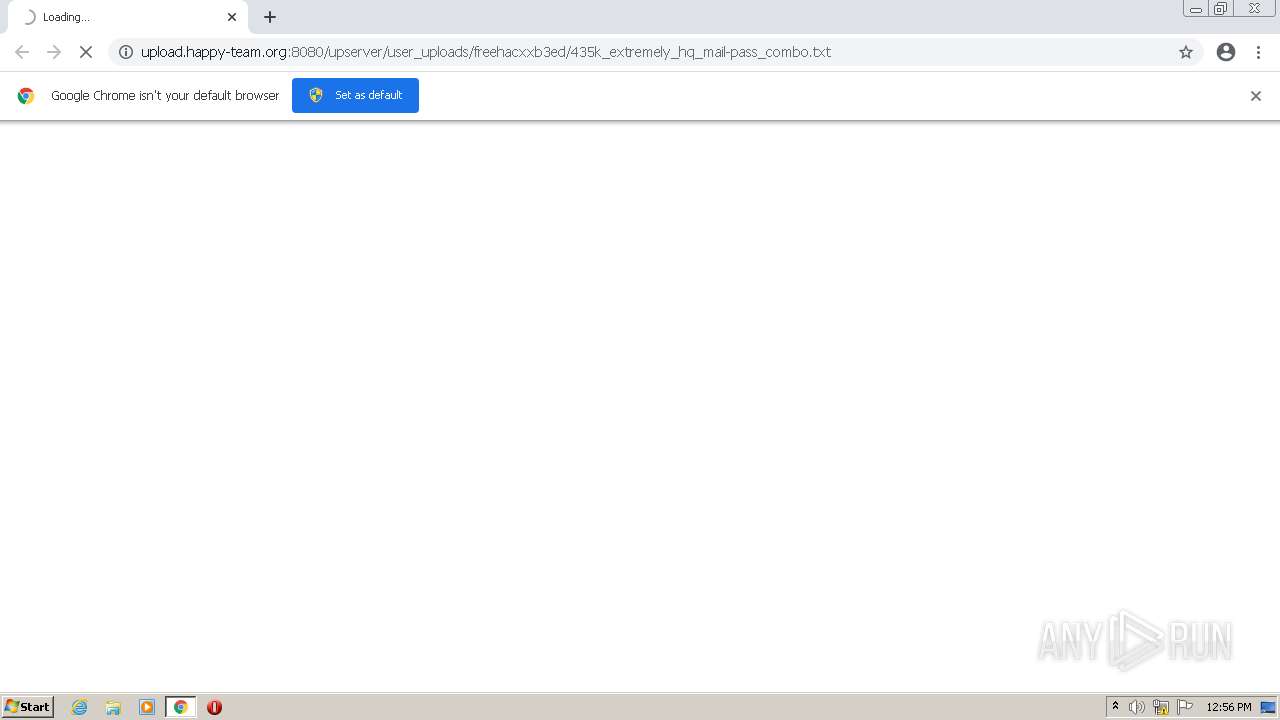
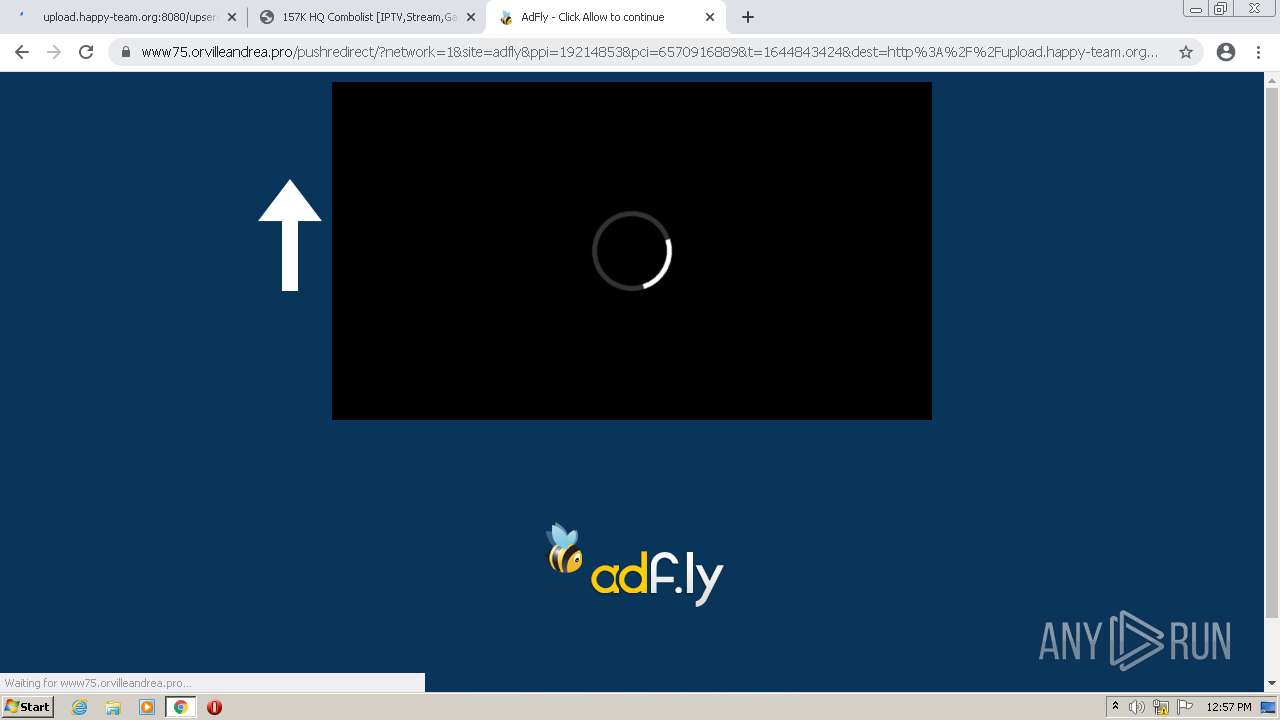
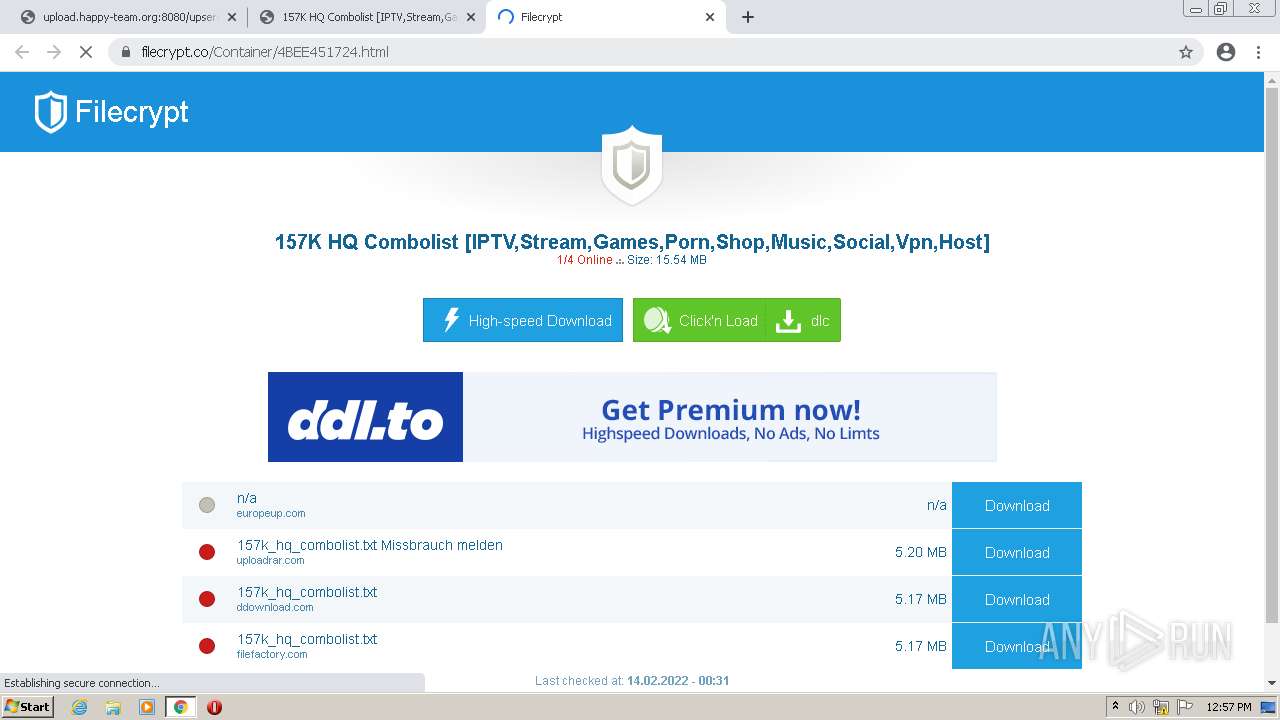
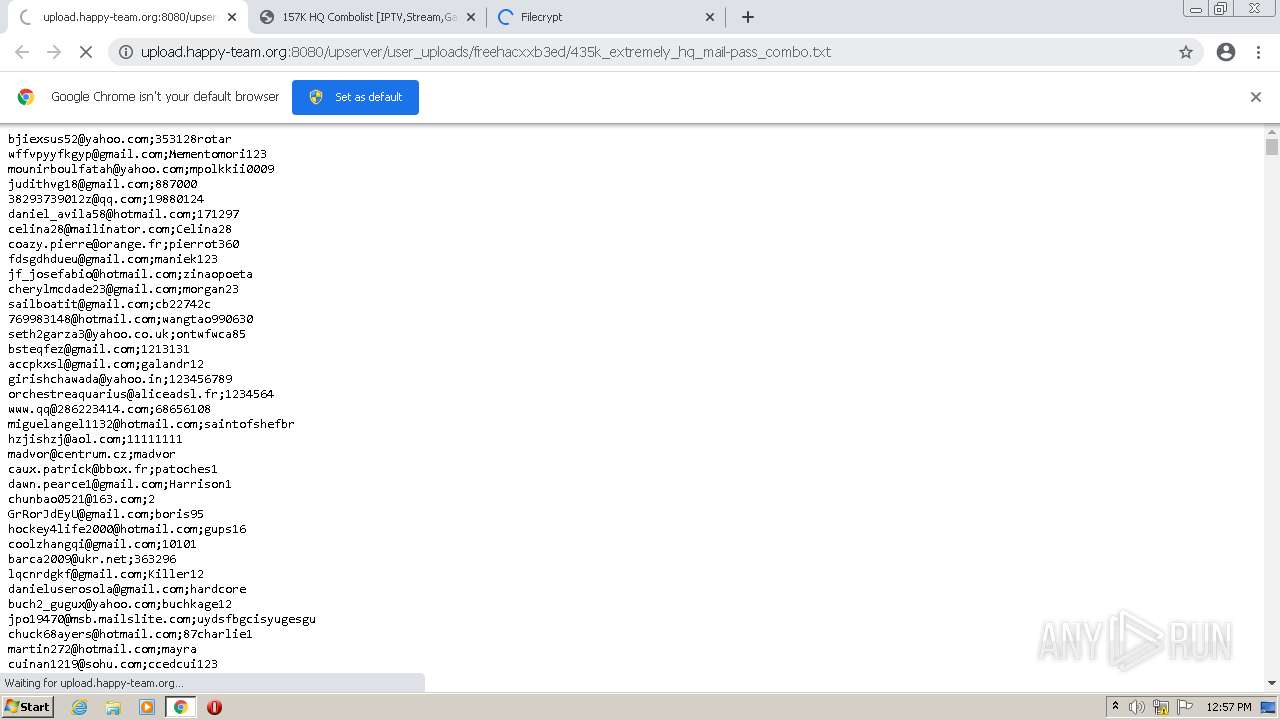
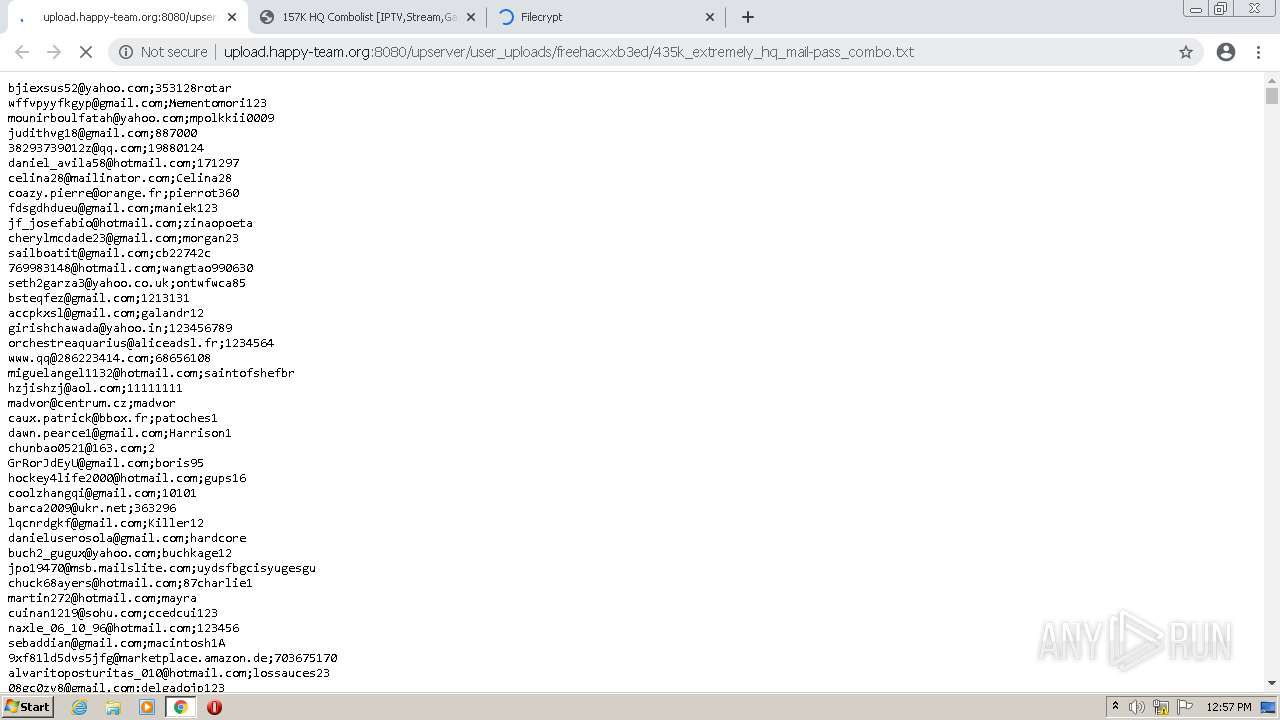
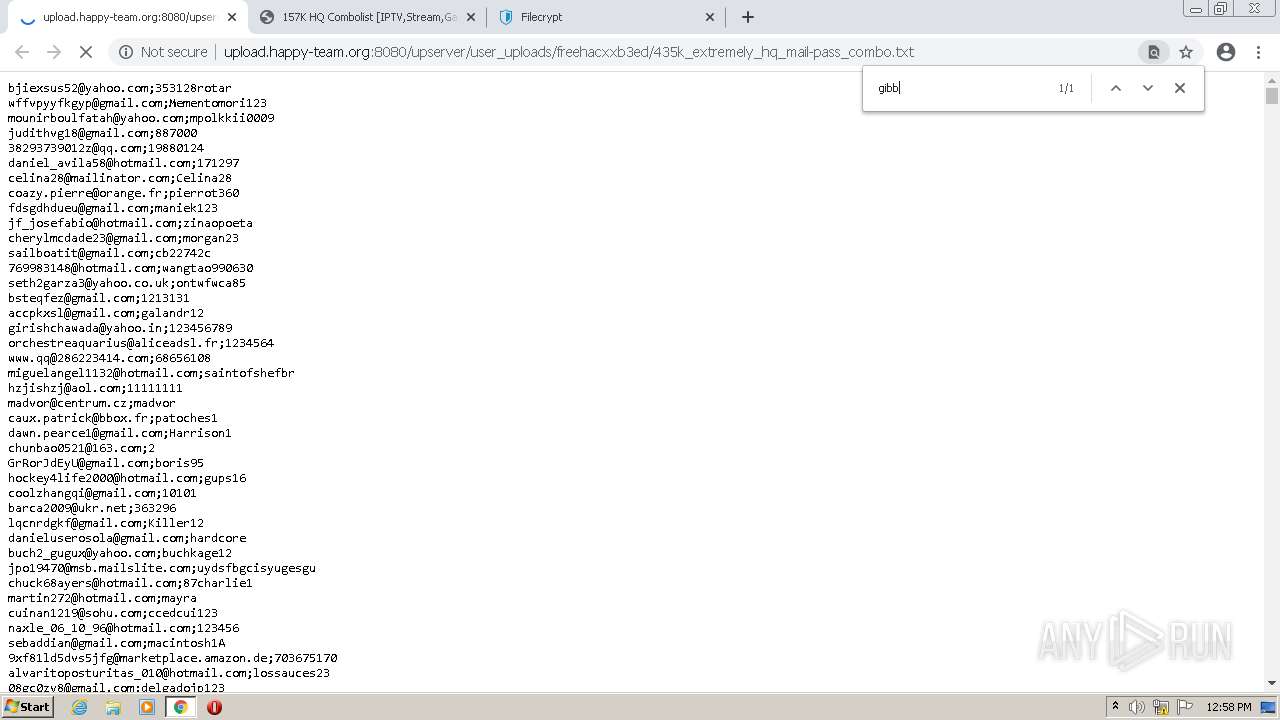
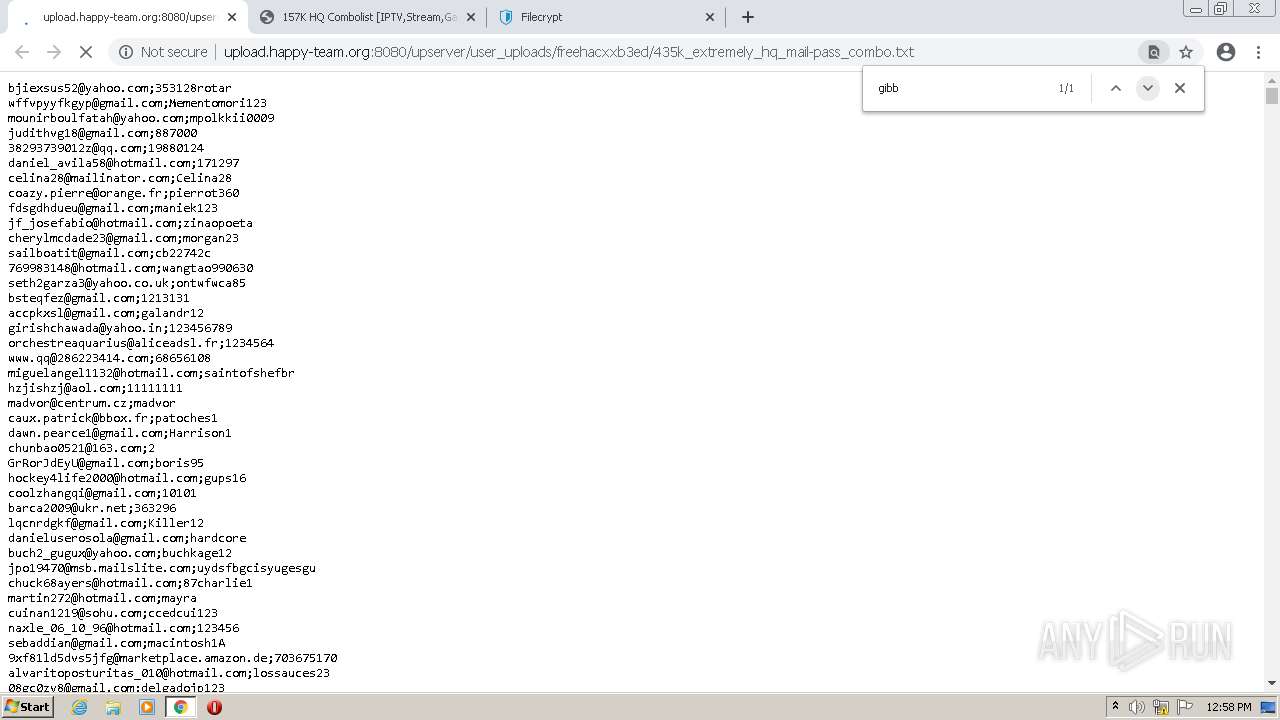
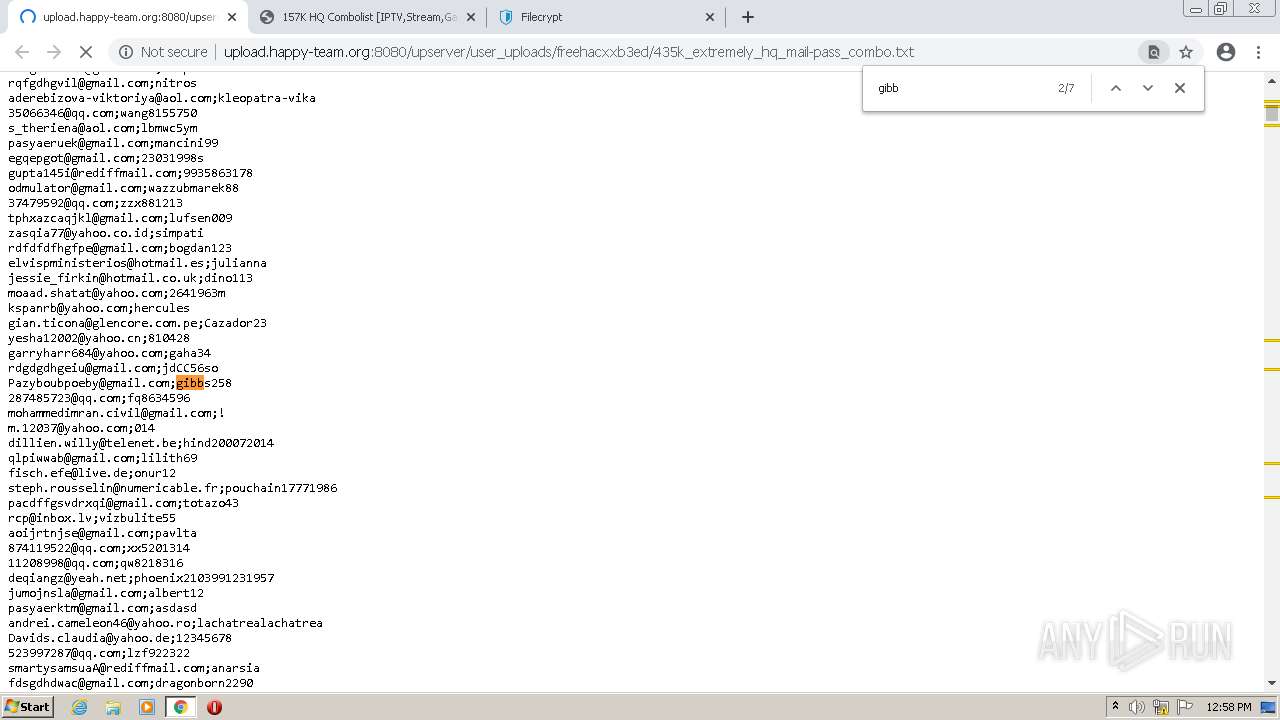
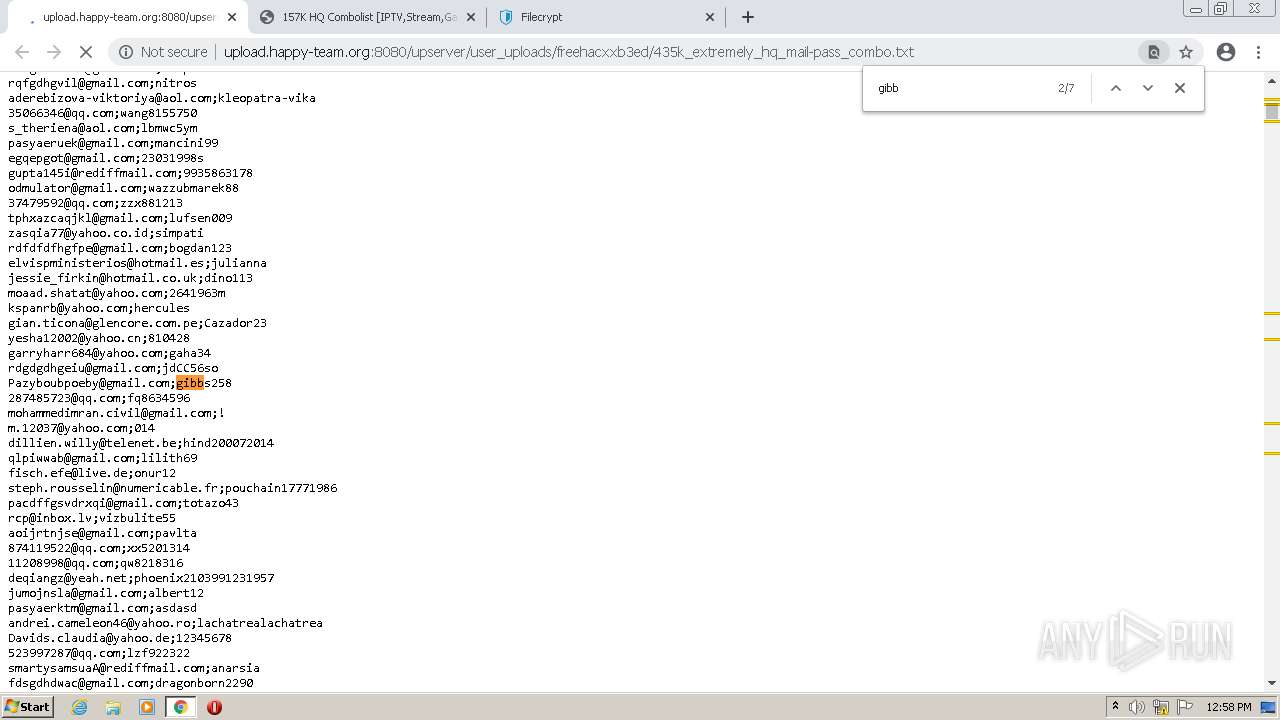
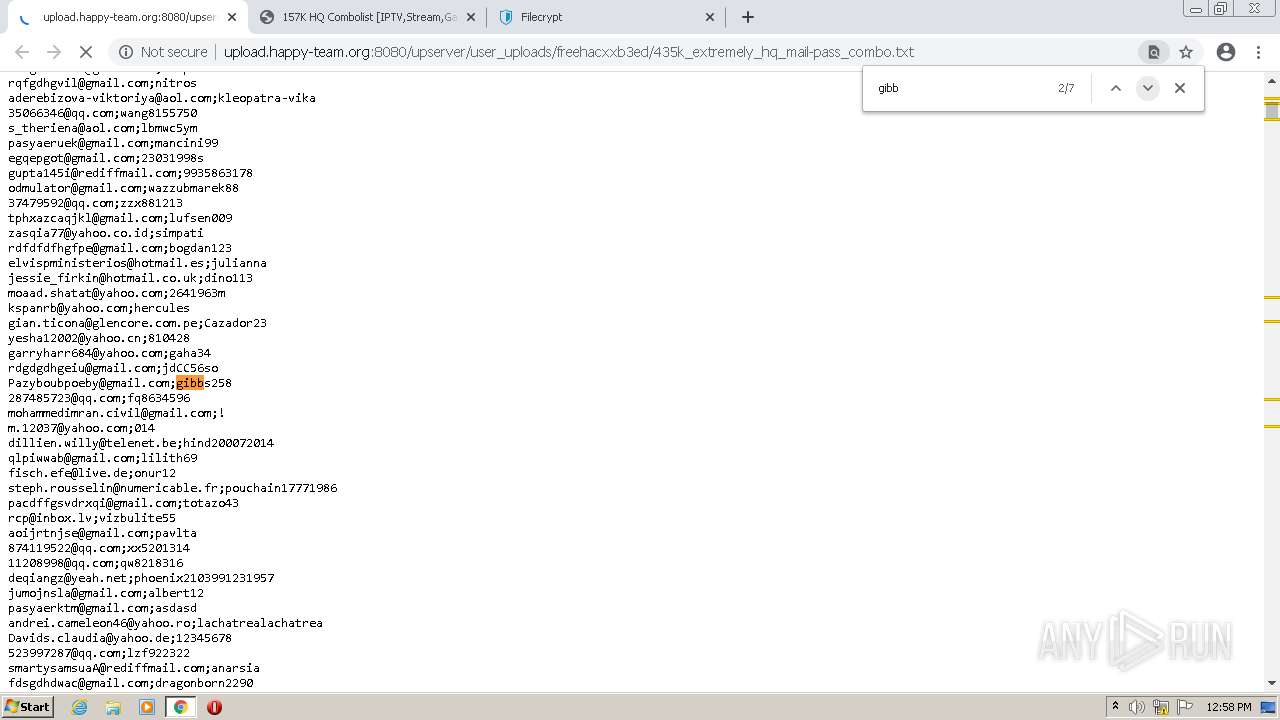
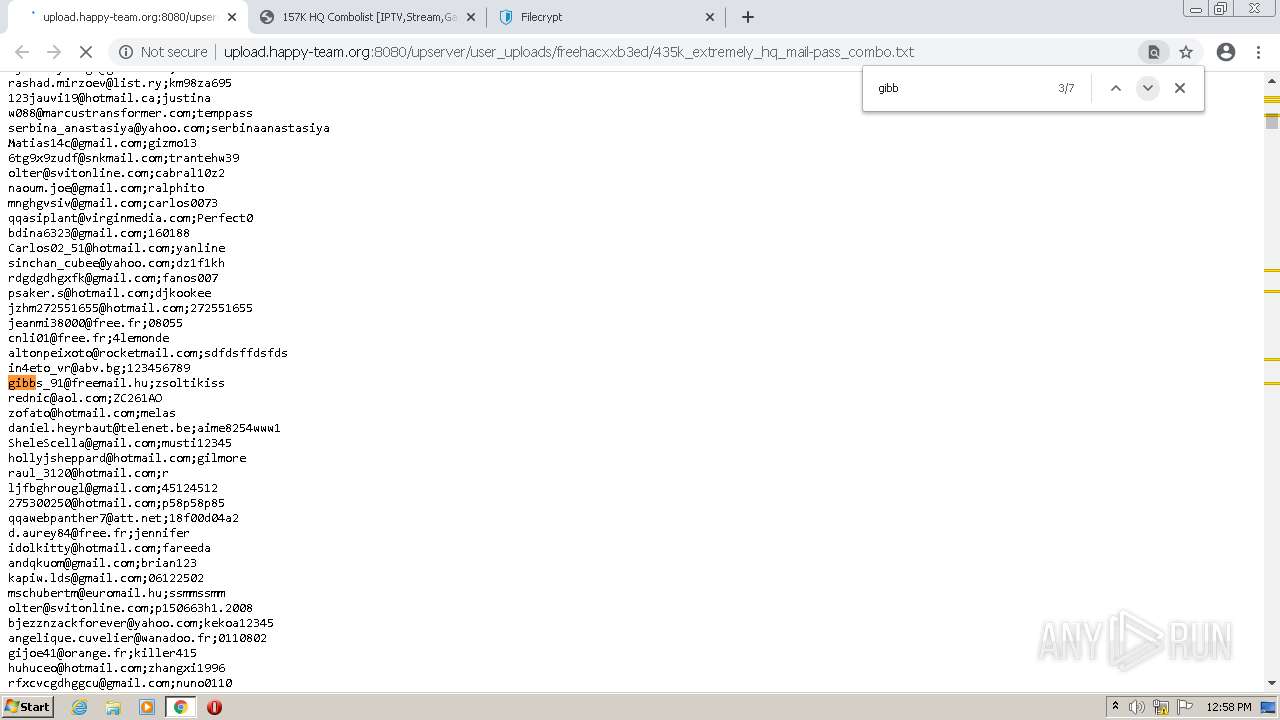
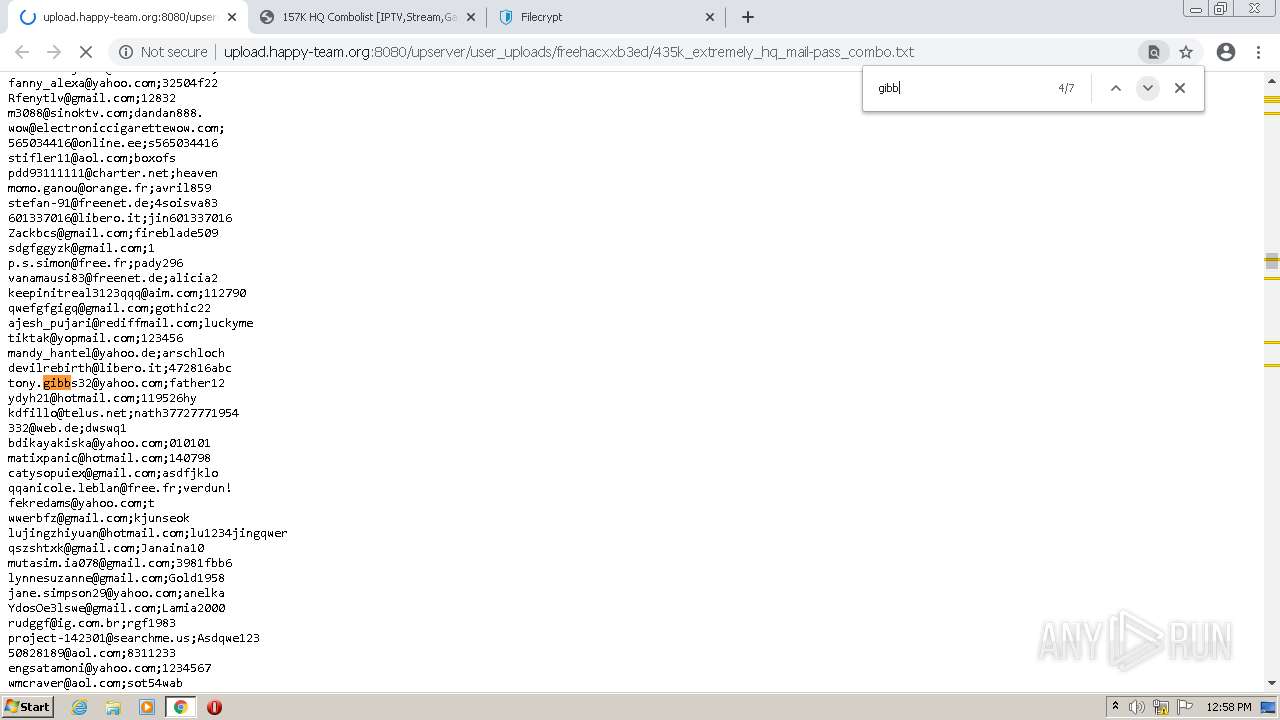
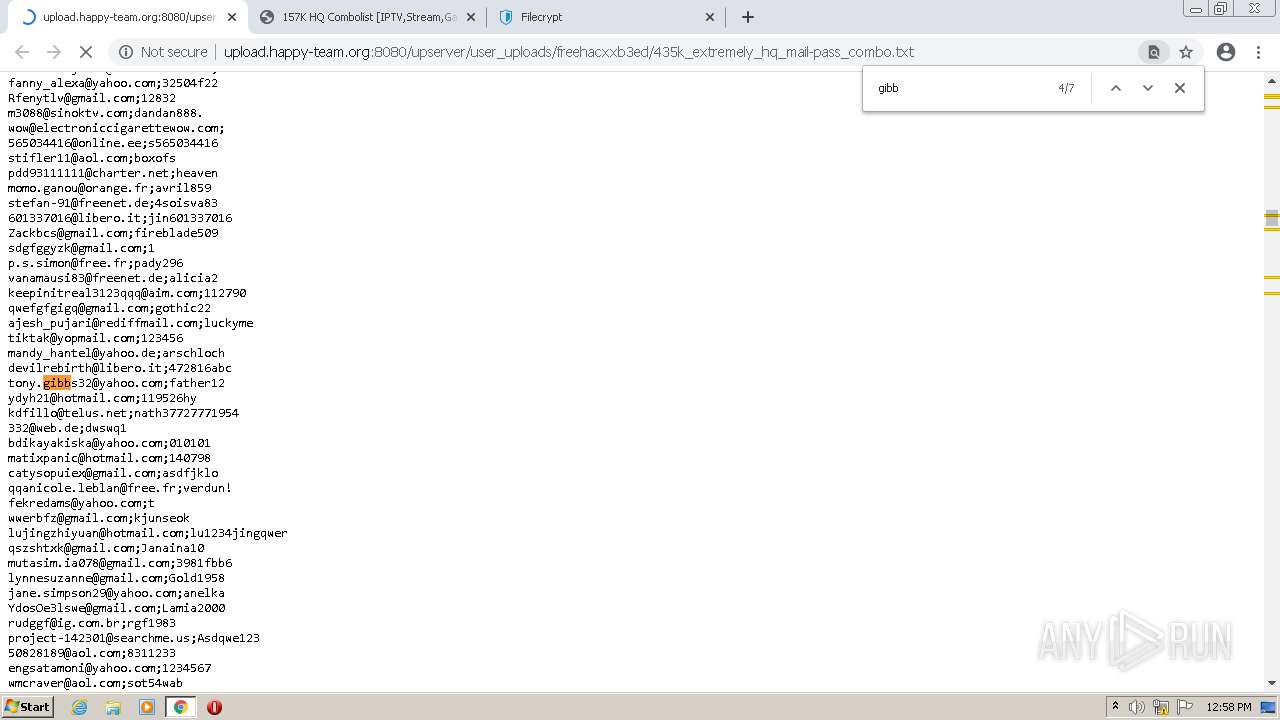
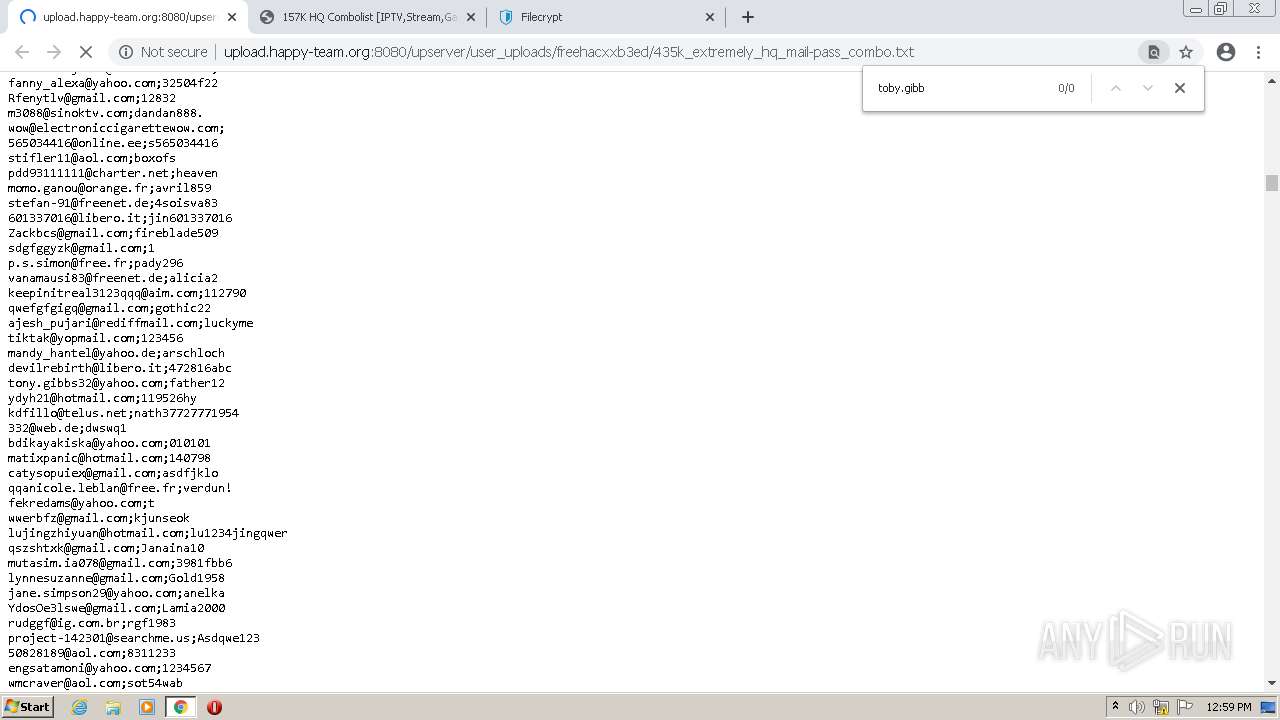
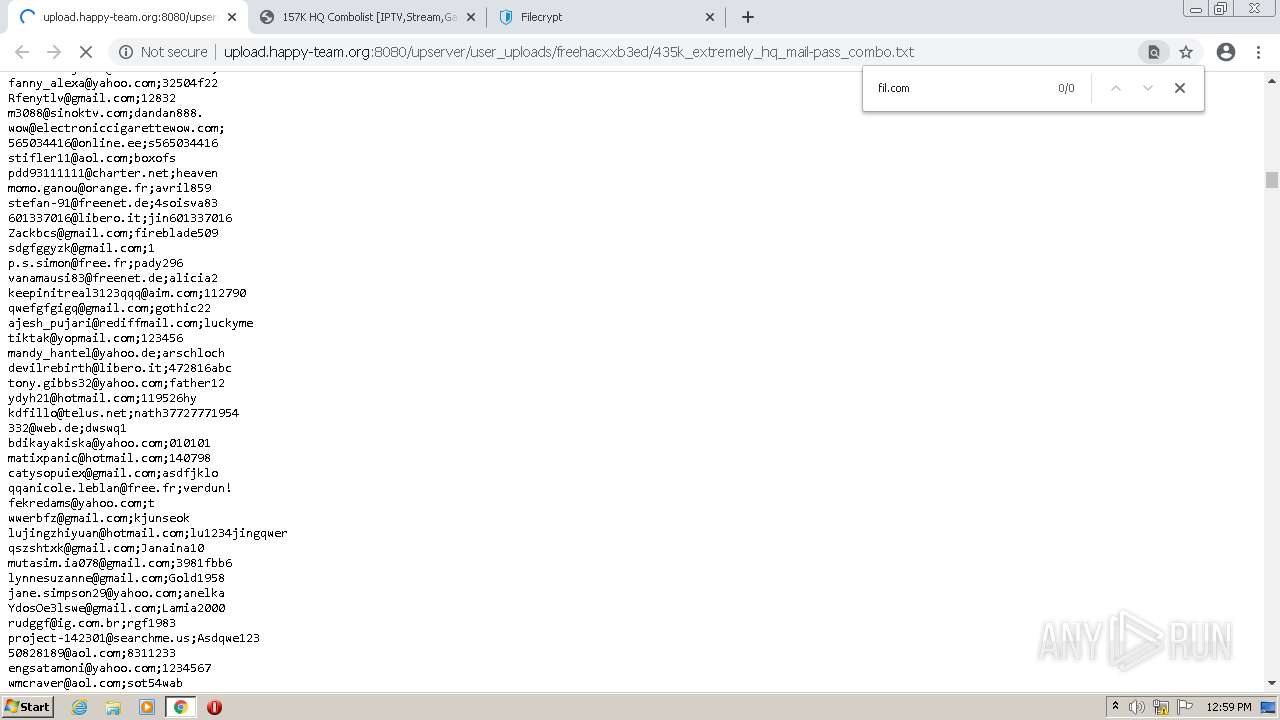
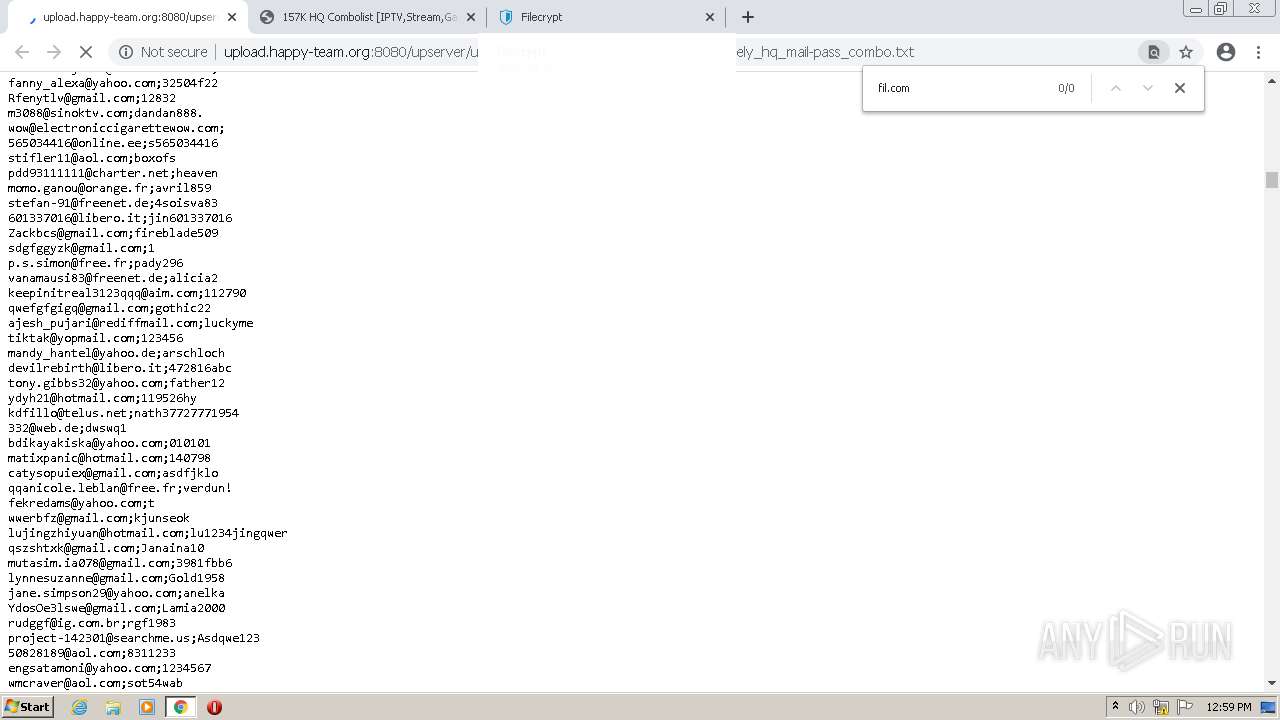
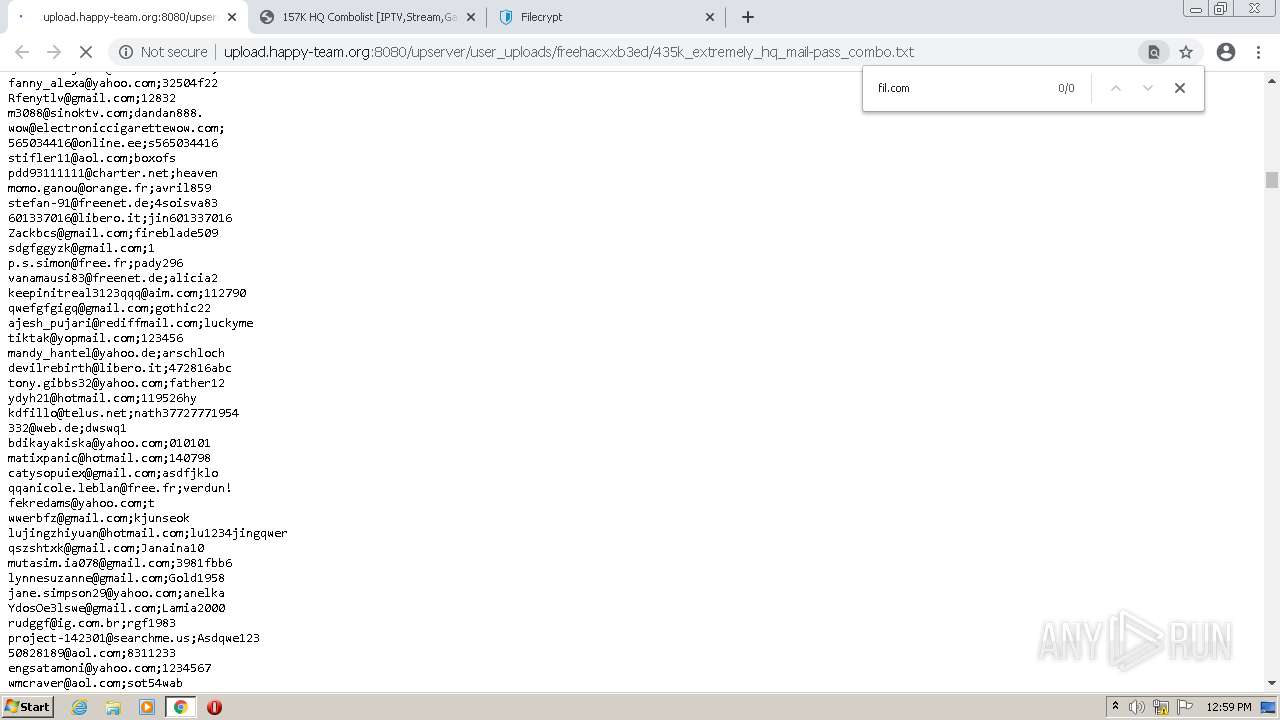
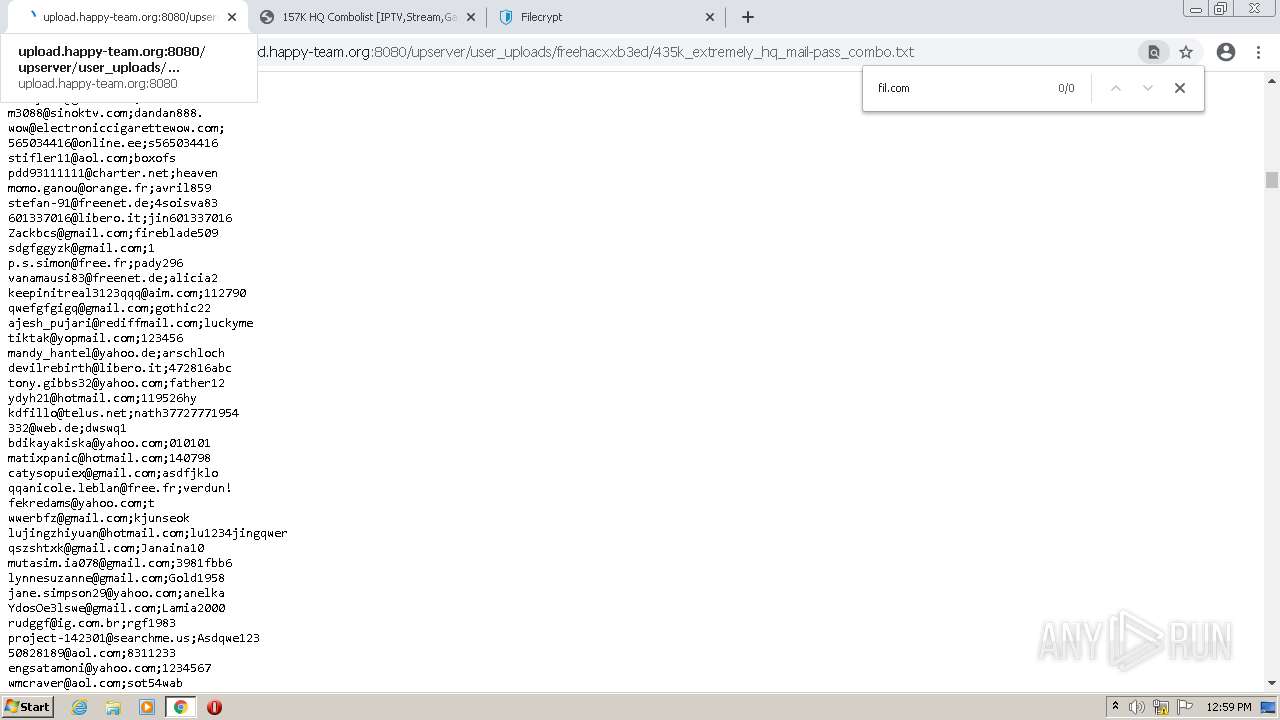
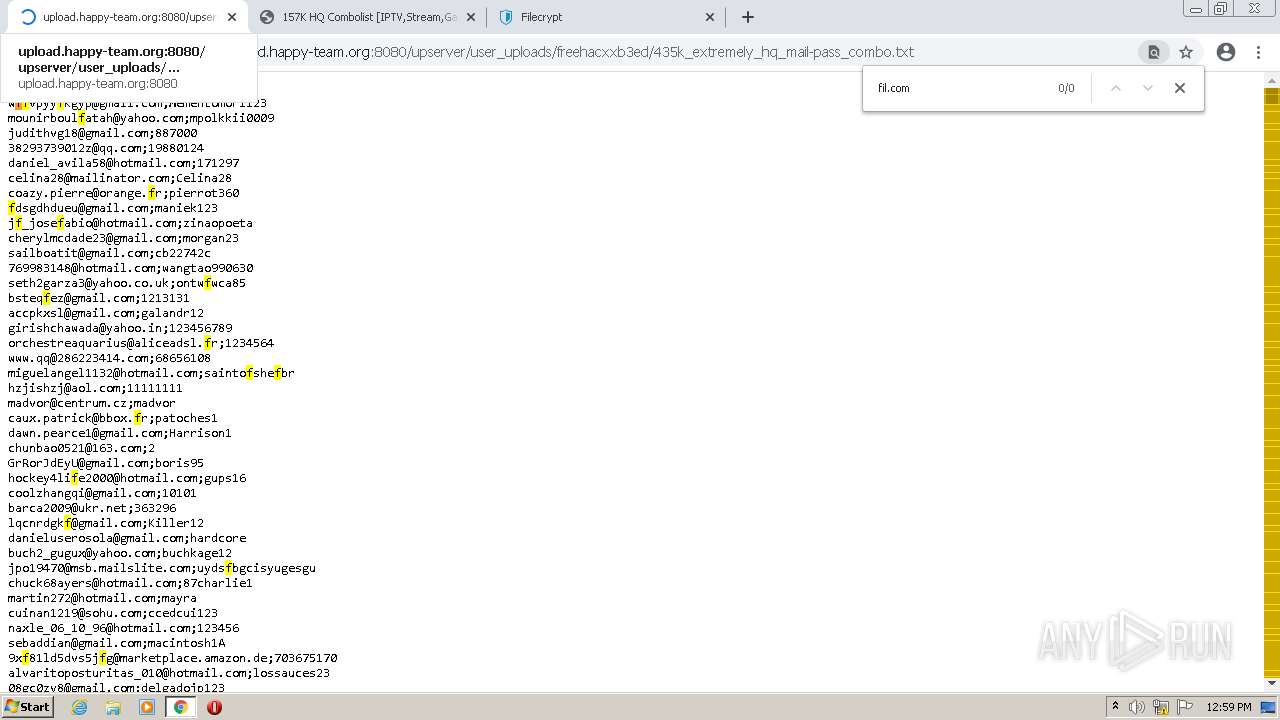
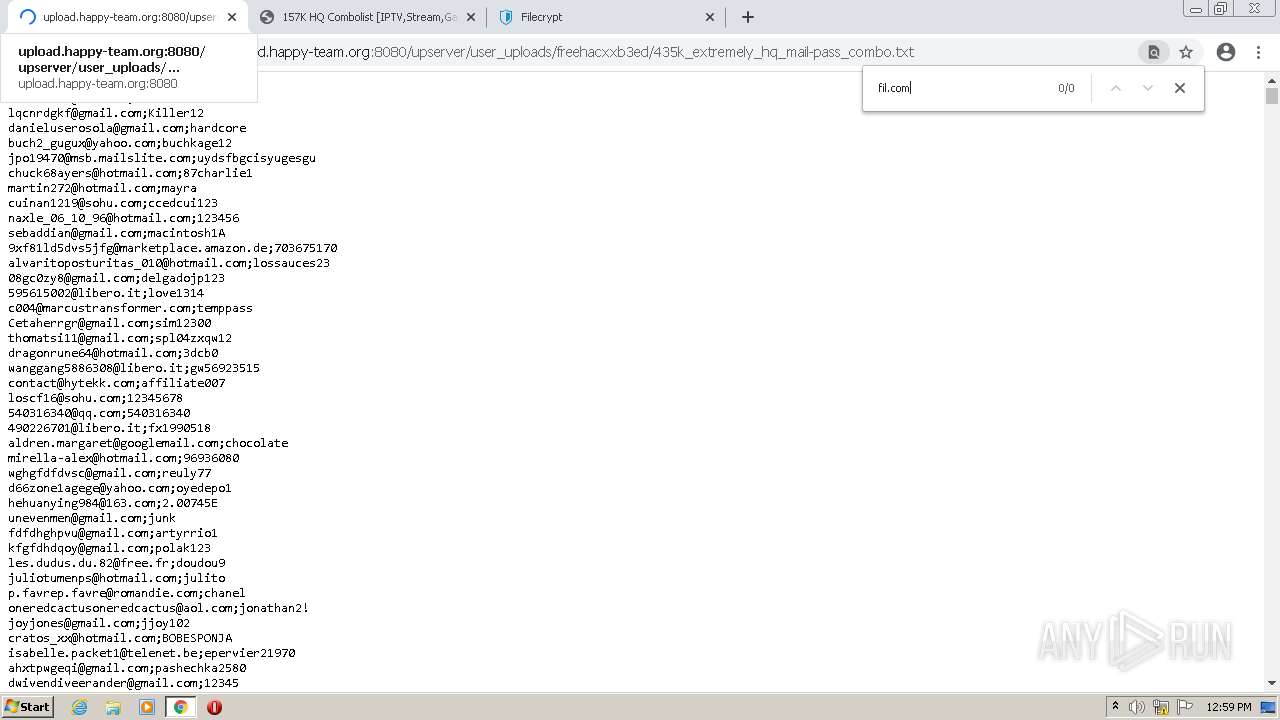
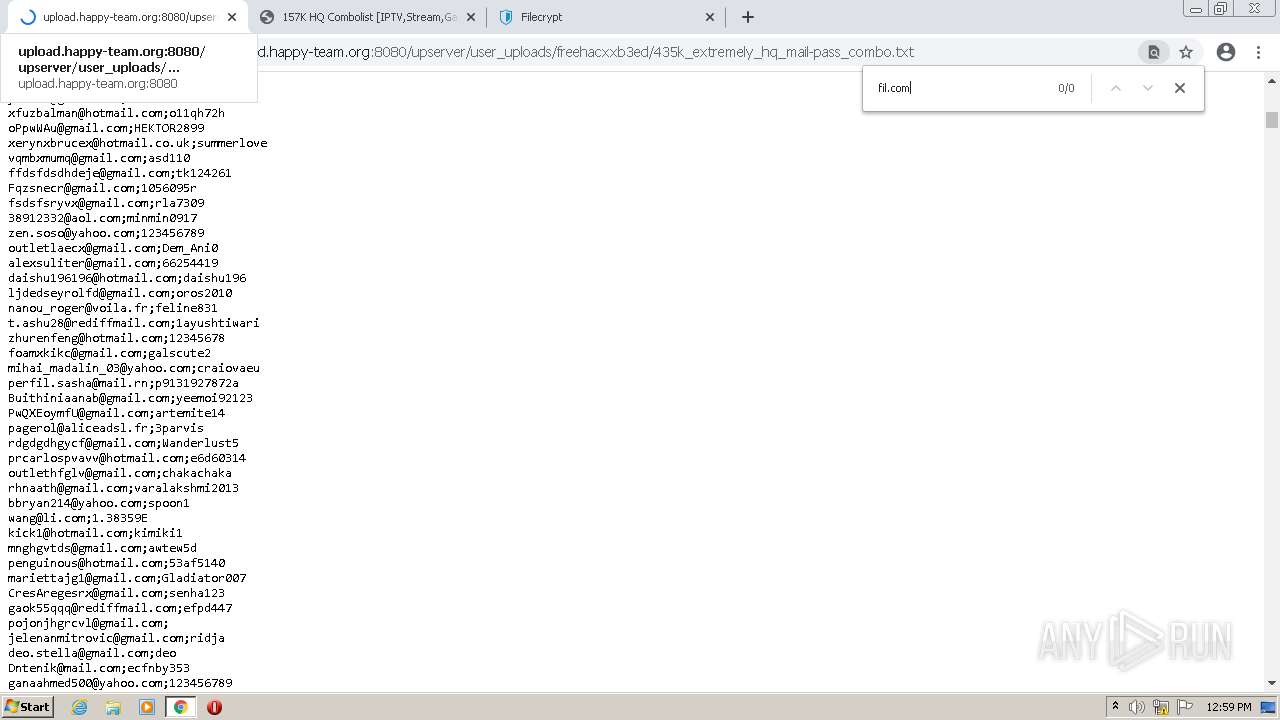
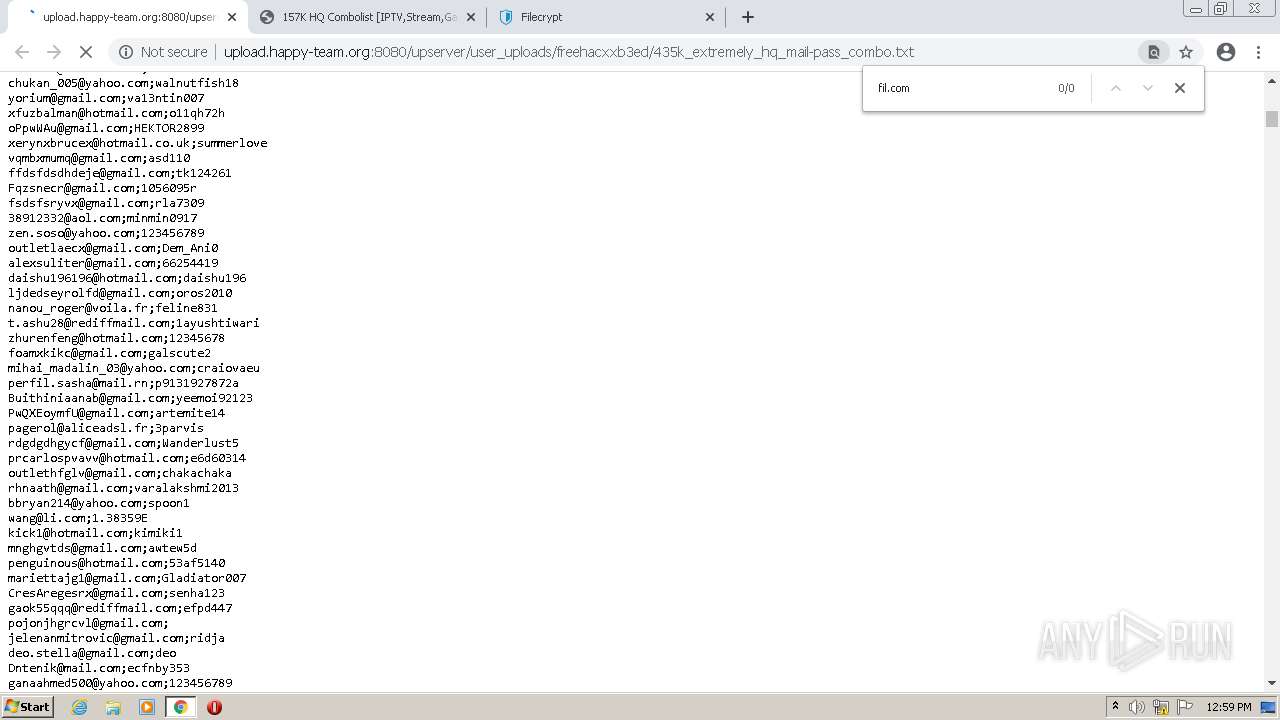
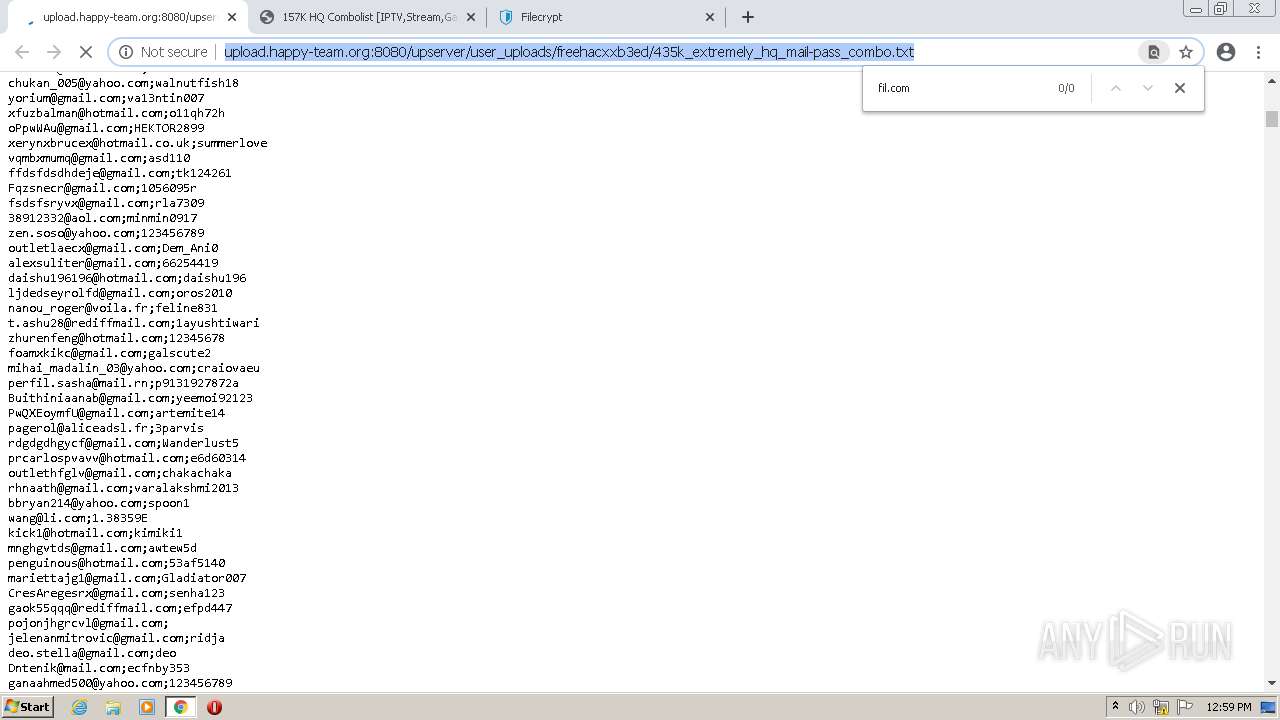
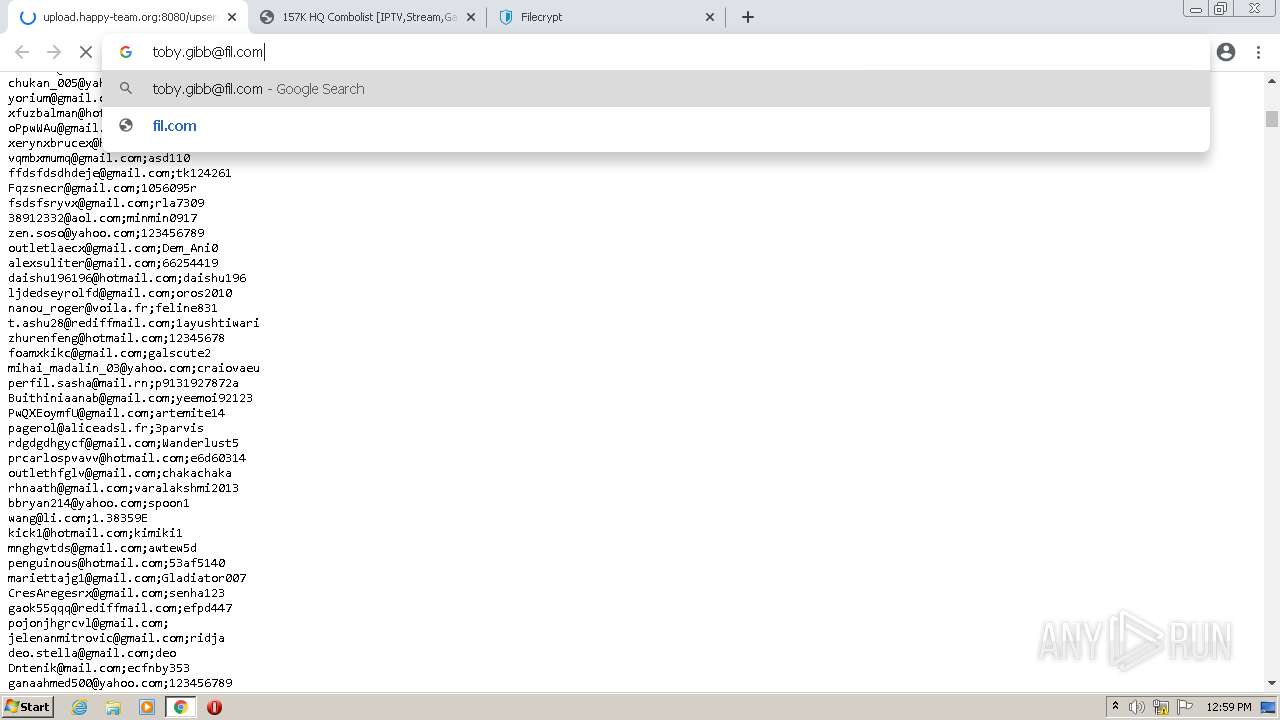
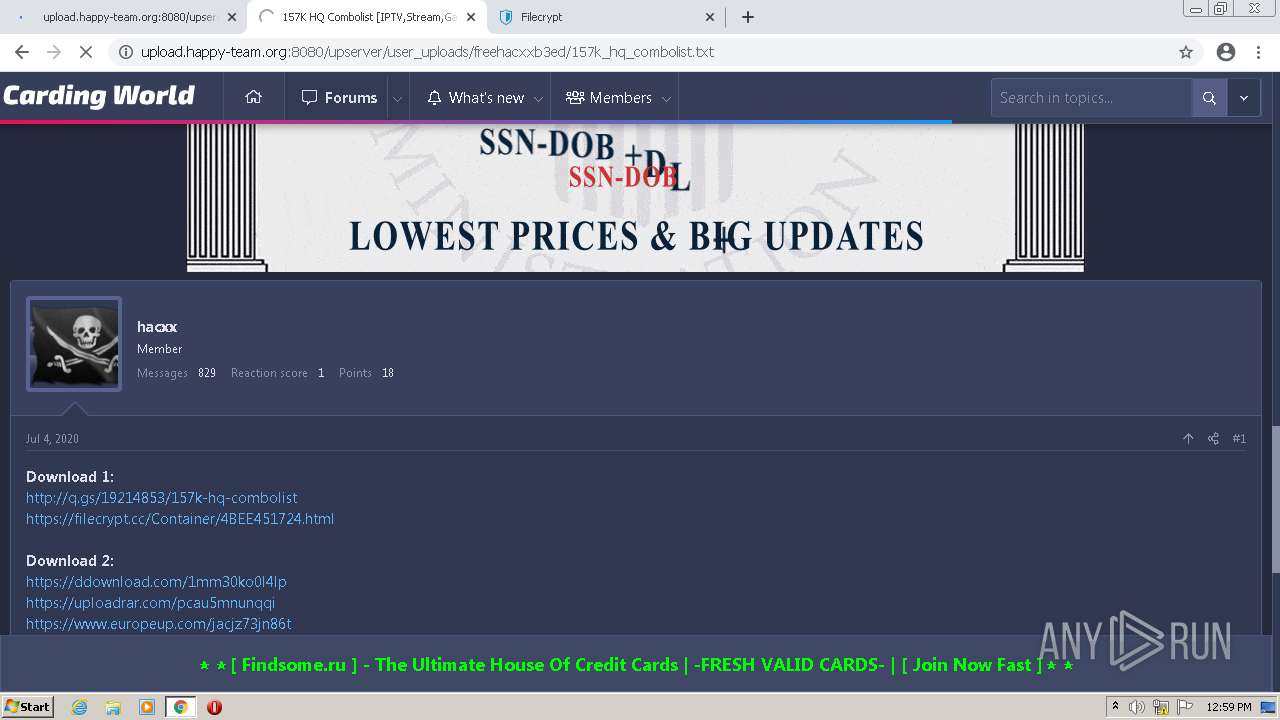
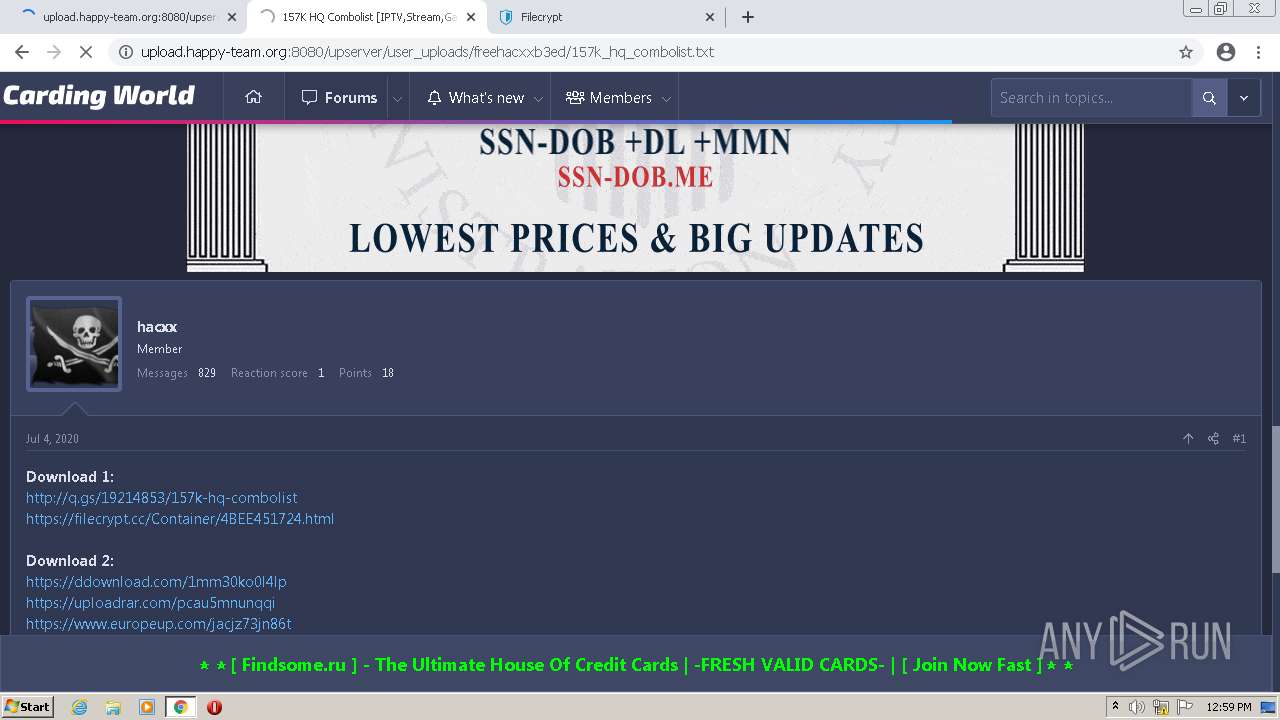
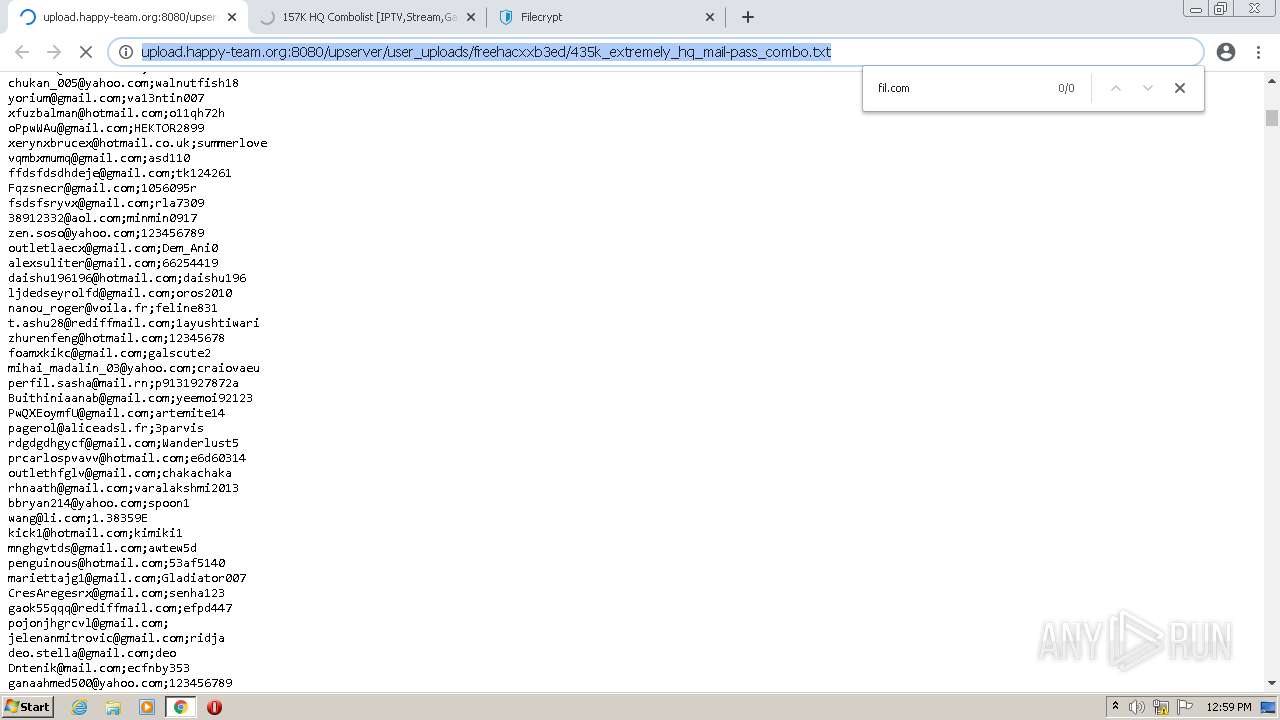
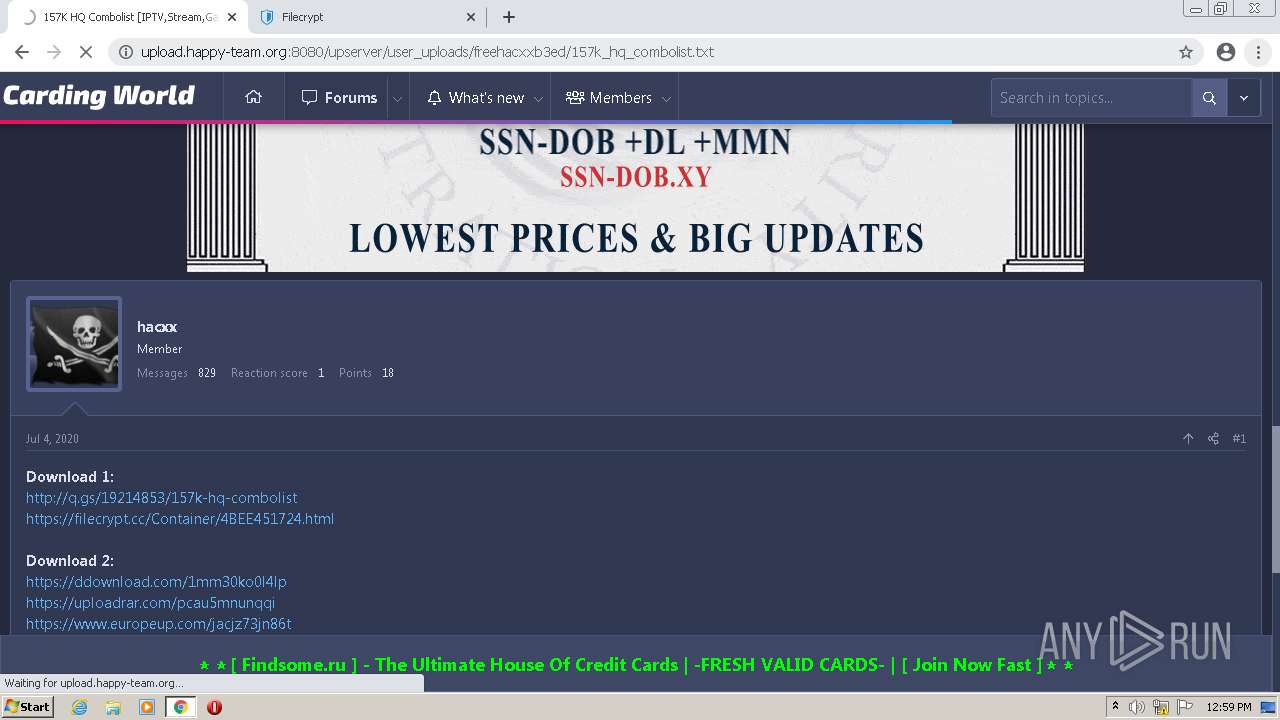
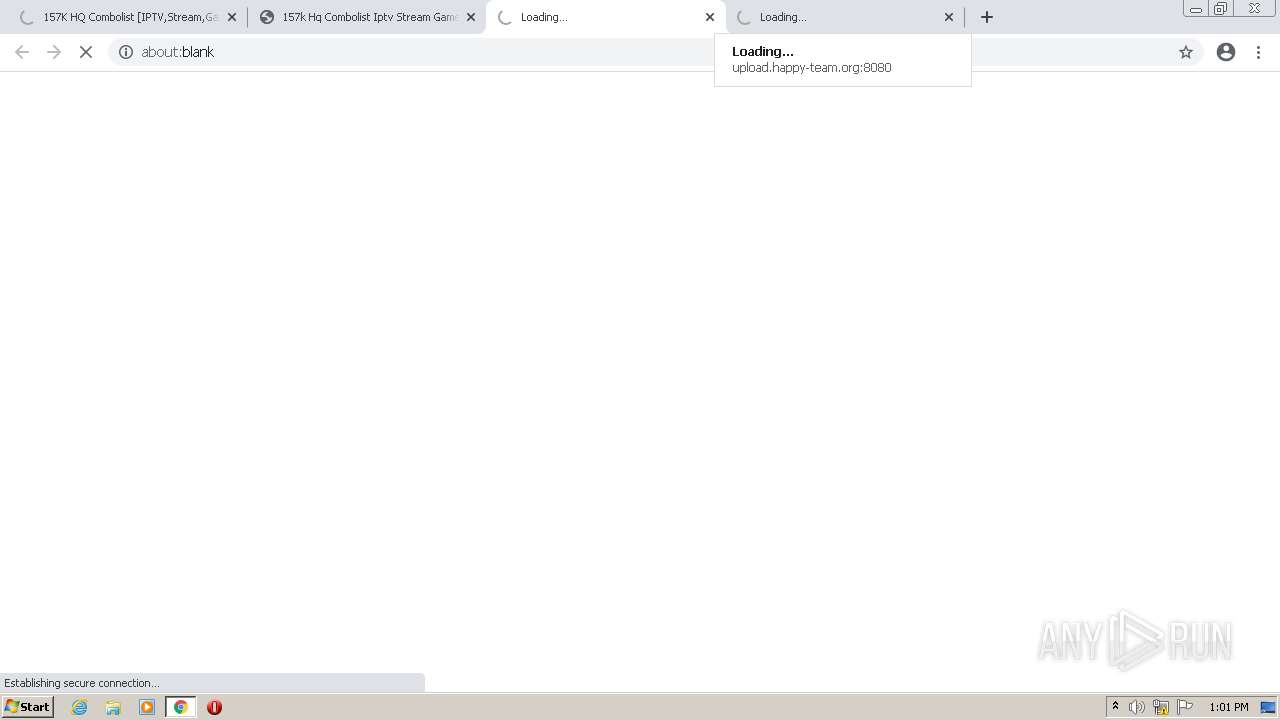
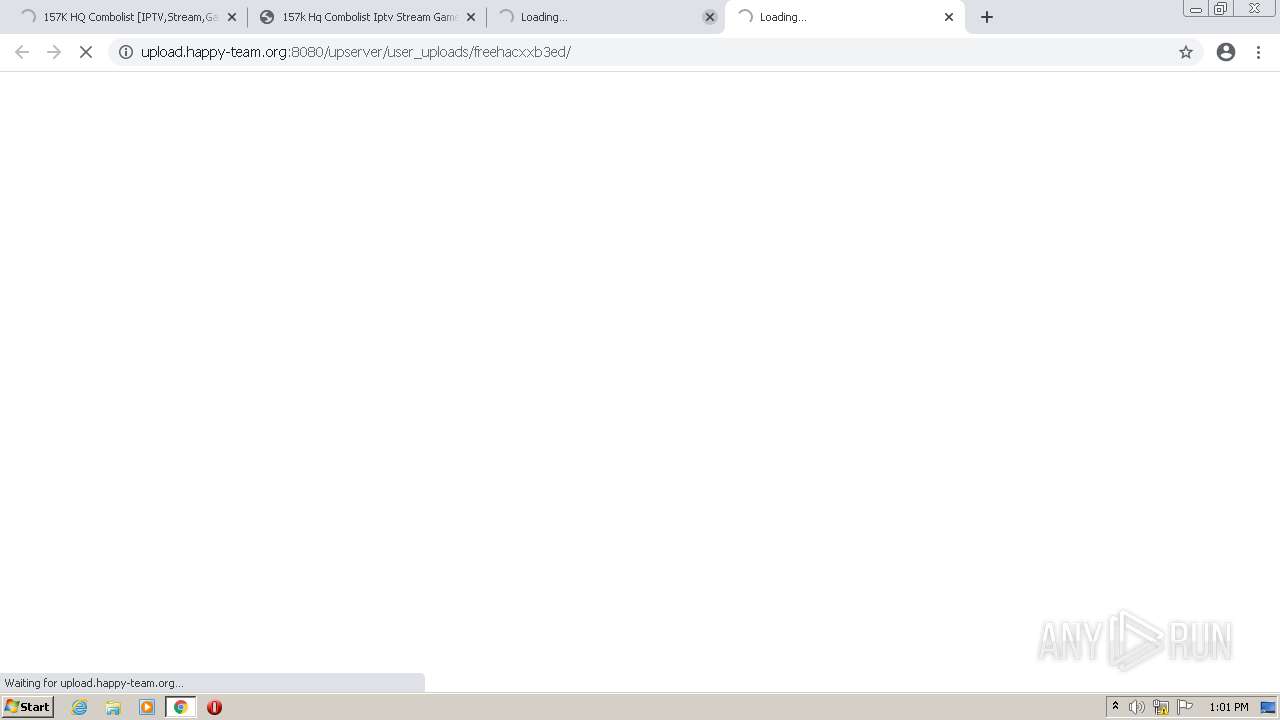
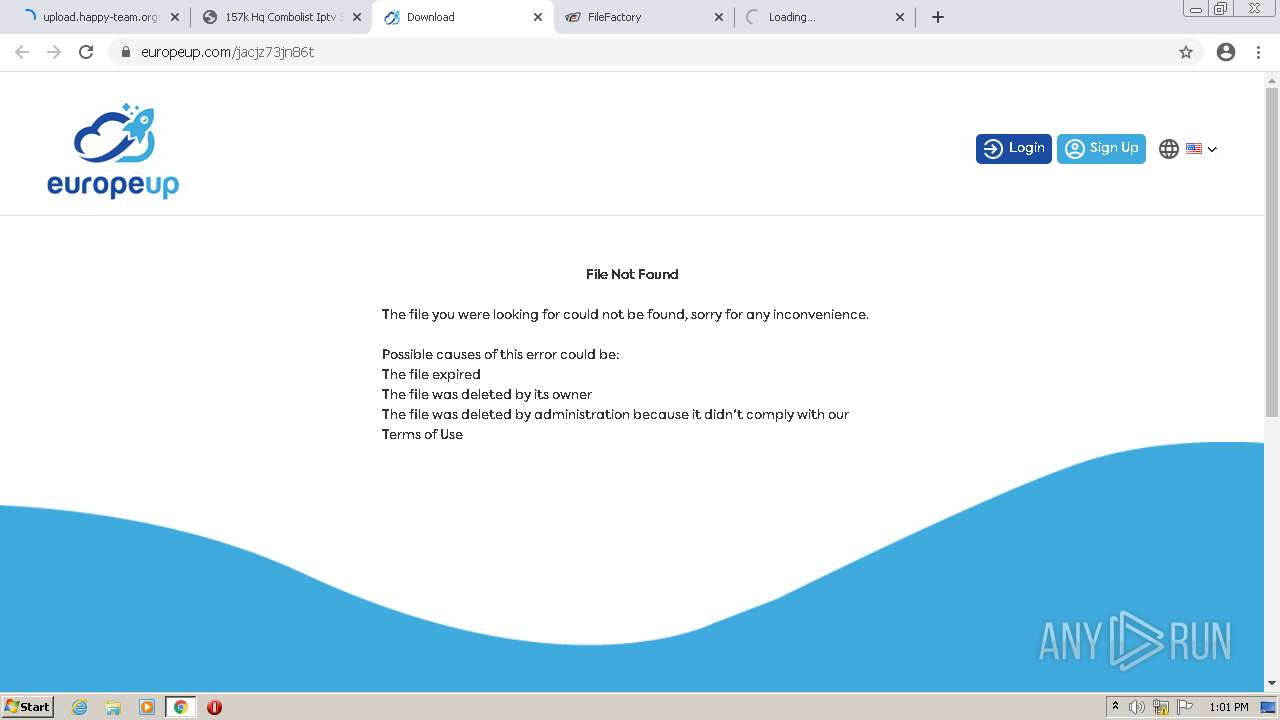
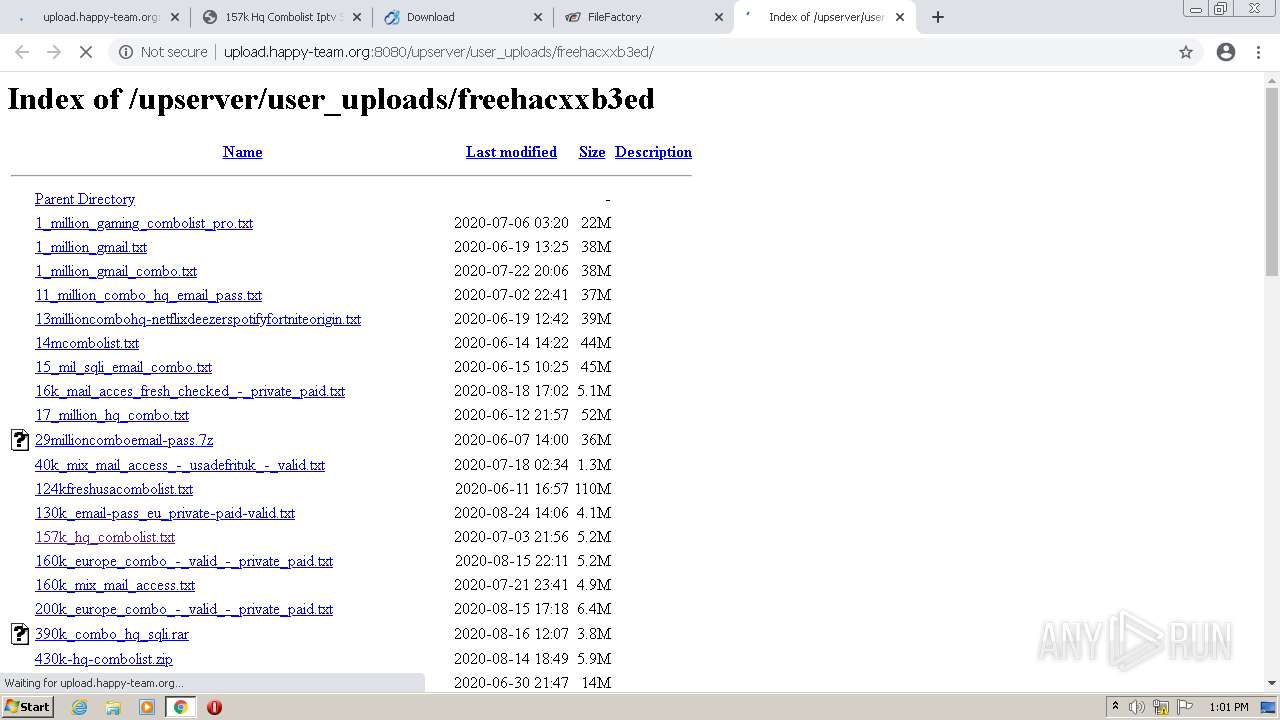
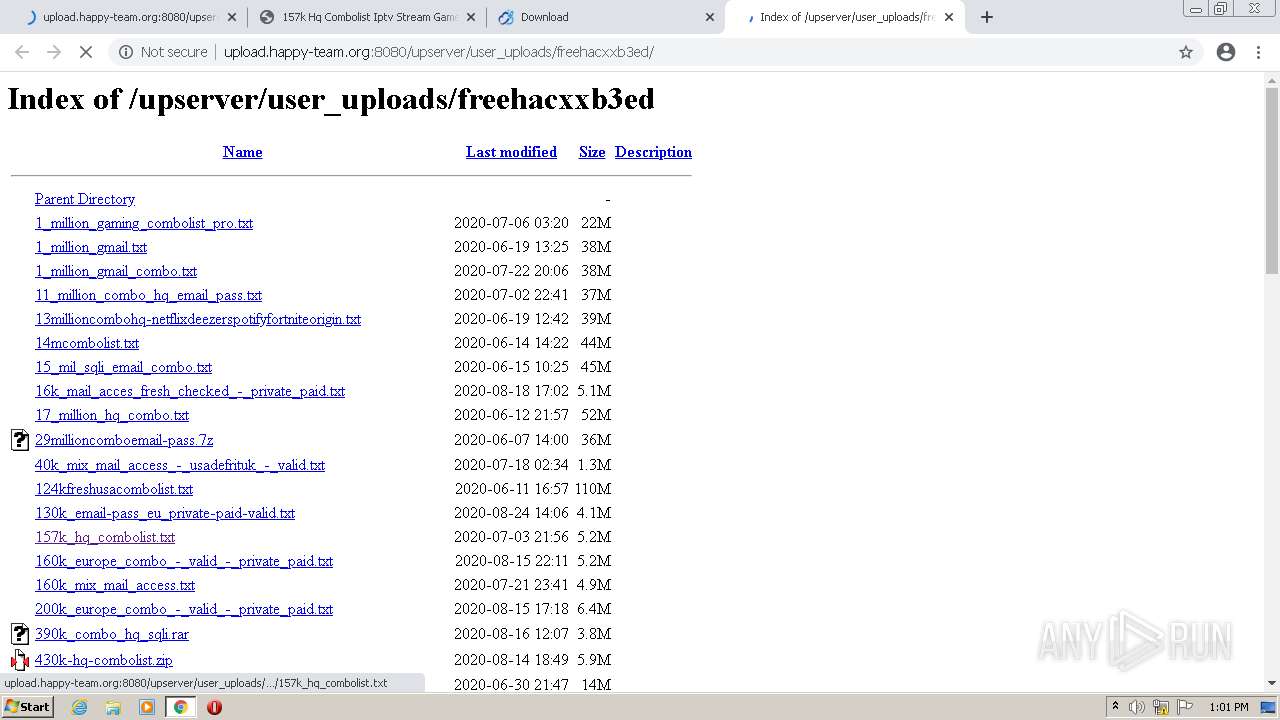
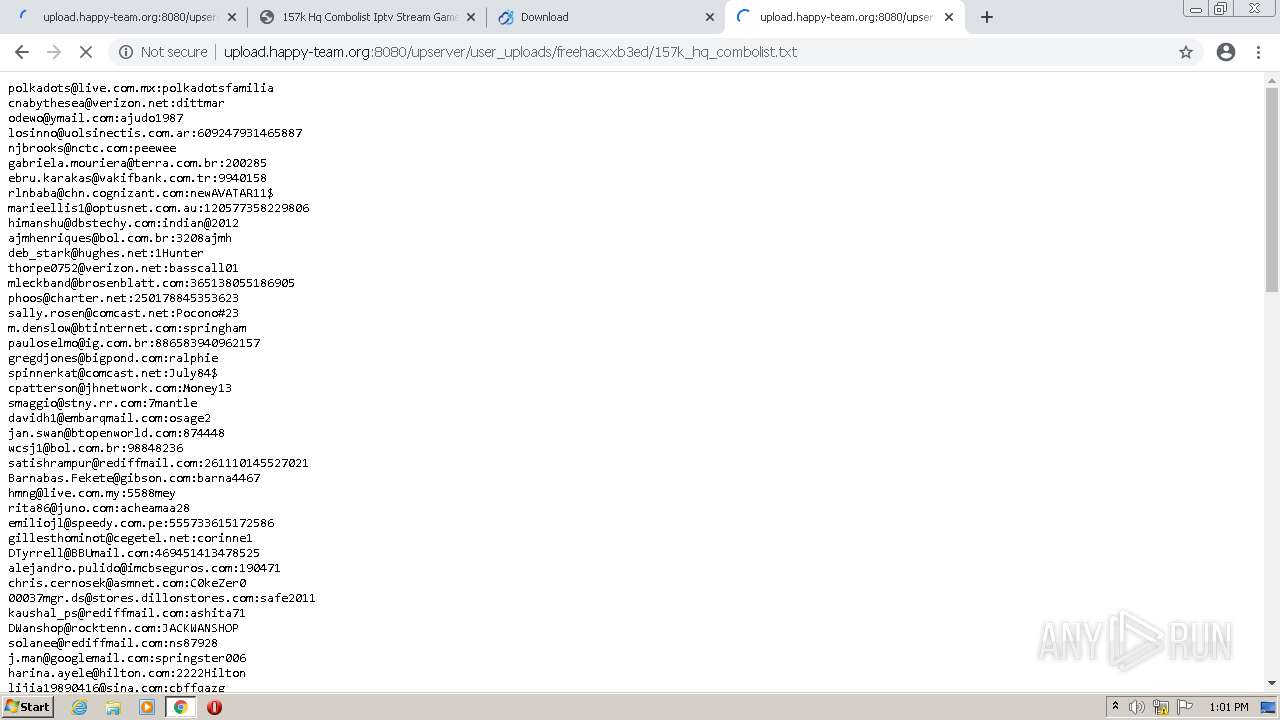
| URL: | http://upload.happy-team.org:8080/upserver/user_uploads/freehacxxb3ed/435k_extremely_hq_mail-pass_combo.txt |
| Full analysis: | https://app.any.run/tasks/25c53551-dfbc-47cb-a28a-5bebc89b16ec |
| Verdict: | Malicious activity |
| Analysis date: | February 14, 2022, 12:56:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 8826E73AA2EBF963000D9C43AAAFCACB |
| SHA1: | 451888E54B96C1C0F6AD17AC7E7F3E058961E932 |
| SHA256: | 4237B35560A00754943514197F3E17C155539A2662D7C79DC860ECFF38143719 |
| SSDEEP: | 3:N1KL2Ec5k+rsEVE+0ZDNeSLv3kLKlTn:CiEdas+hLKlT |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Checks supported languages
- chrome.exe (PID: 872)
- chrome.exe (PID: 3972)
- chrome.exe (PID: 1096)
- chrome.exe (PID: 3748)
- chrome.exe (PID: 2080)
- chrome.exe (PID: 2096)
- chrome.exe (PID: 2456)
- chrome.exe (PID: 984)
- chrome.exe (PID: 2244)
- chrome.exe (PID: 2832)
- chrome.exe (PID: 4040)
- chrome.exe (PID: 1144)
- chrome.exe (PID: 3692)
- chrome.exe (PID: 3216)
- chrome.exe (PID: 3272)
- chrome.exe (PID: 1588)
- chrome.exe (PID: 2568)
- chrome.exe (PID: 2952)
- chrome.exe (PID: 568)
- chrome.exe (PID: 2076)
- chrome.exe (PID: 3852)
- chrome.exe (PID: 2712)
- chrome.exe (PID: 876)
- chrome.exe (PID: 3080)
- chrome.exe (PID: 356)
- chrome.exe (PID: 3996)
- chrome.exe (PID: 2384)
- chrome.exe (PID: 3640)
- chrome.exe (PID: 3556)
- chrome.exe (PID: 3868)
- chrome.exe (PID: 3140)
- chrome.exe (PID: 3444)
- chrome.exe (PID: 2908)
- chrome.exe (PID: 188)
- chrome.exe (PID: 2888)
- chrome.exe (PID: 3236)
- chrome.exe (PID: 3548)
- chrome.exe (PID: 2152)
- chrome.exe (PID: 3668)
- chrome.exe (PID: 3624)
- chrome.exe (PID: 2764)
Reads the hosts file
- chrome.exe (PID: 872)
- chrome.exe (PID: 3748)
Reads the computer name
- chrome.exe (PID: 872)
- chrome.exe (PID: 3972)
- chrome.exe (PID: 3748)
- chrome.exe (PID: 2244)
- chrome.exe (PID: 356)
- chrome.exe (PID: 3852)
- chrome.exe (PID: 876)
- chrome.exe (PID: 3236)
- chrome.exe (PID: 2384)
Application launched itself
- chrome.exe (PID: 872)
Reads settings of System Certificates
- chrome.exe (PID: 3748)
Creates files in the user directory
- chrome.exe (PID: 872)
Reads the date of Windows installation
- chrome.exe (PID: 3852)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
76
Monitored processes
41
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 188 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,11373123984495570394,12710461487532574670,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=36 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2608 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 356 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=audio.mojom.AudioService --field-trial-handle=1040,11373123984495570394,12710461487532574670,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=audio --mojo-platform-channel-handle=3808 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 568 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,11373123984495570394,12710461487532574670,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3660 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 872 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "http://upload.happy-team.org:8080/upserver/user_uploads/freehacxxb3ed/435k_extremely_hq_mail-pass_combo.txt" | C:\Program Files\Google\Chrome\Application\chrome.exe | Explorer.EXE | |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 876 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1040,11373123984495570394,12710461487532574670,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=4688 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 984 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1040,11373123984495570394,12710461487532574670,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3544 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 1096 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x71abd988,0x71abd998,0x71abd9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 1144 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,11373123984495570394,12710461487532574670,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2208 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 1588 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,11373123984495570394,12710461487532574670,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3968 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 2076 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,11373123984495570394,12710461487532574670,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=23 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3980 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
91
Text files
177
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 872 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-620A517F-368.pma | — | |
MD5:— | SHA256:— | |||
| 872 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\dbddae8d-49ec-497d-a286-bb877e8047fd.tmp | text | |
MD5:— | SHA256:— | |||
| 872 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 872 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
| 872 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Extension State\LOG.old~RF13ee1c.TMP | text | |
MD5:D097F8EB2230B3F32C41C5D75790508C | SHA256:ADDF87D20CD455CFB4AACB6B76719629C0277A4CF70B496343047BB73ABBAEF5 | |||
| 872 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 872 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF13e746.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
| 872 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RF13e821.TMP | text | |
MD5:109A25C32EE1132ECD6D9F3ED9ADF01A | SHA256:DA6028DB9485C65E683643658326F02B1D0A1566DE14914EF28E5248EB94F0DD | |||
| 872 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 872 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Extension Settings\pkedcjkdefgpdelpbcmbmeomcjbeemfm\LOG.old | text | |
MD5:5202CA4D6AF0C37DAEC0D528CC7F2986 | SHA256:8F5B8FF94B14C36EA0CBE8FA0A4D165A632B45F834BBB7239E1A6CF6685F256C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
65
TCP/UDP connections
159
DNS requests
94
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
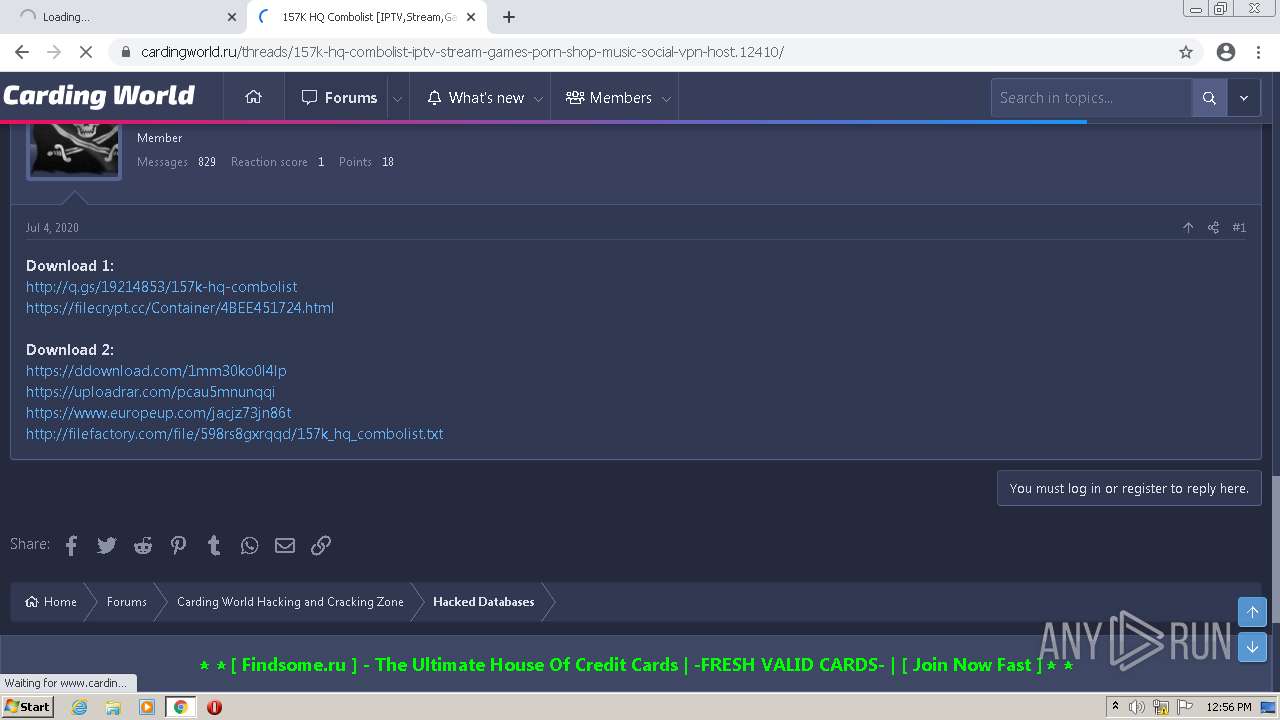
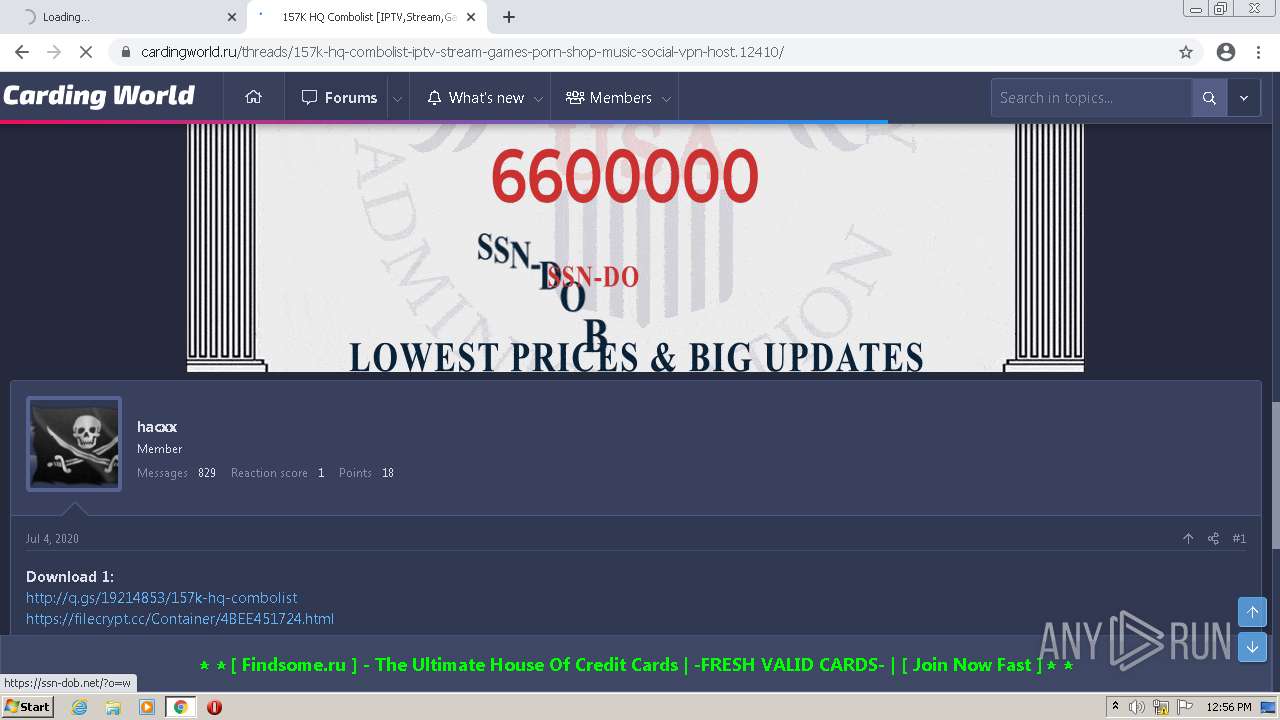
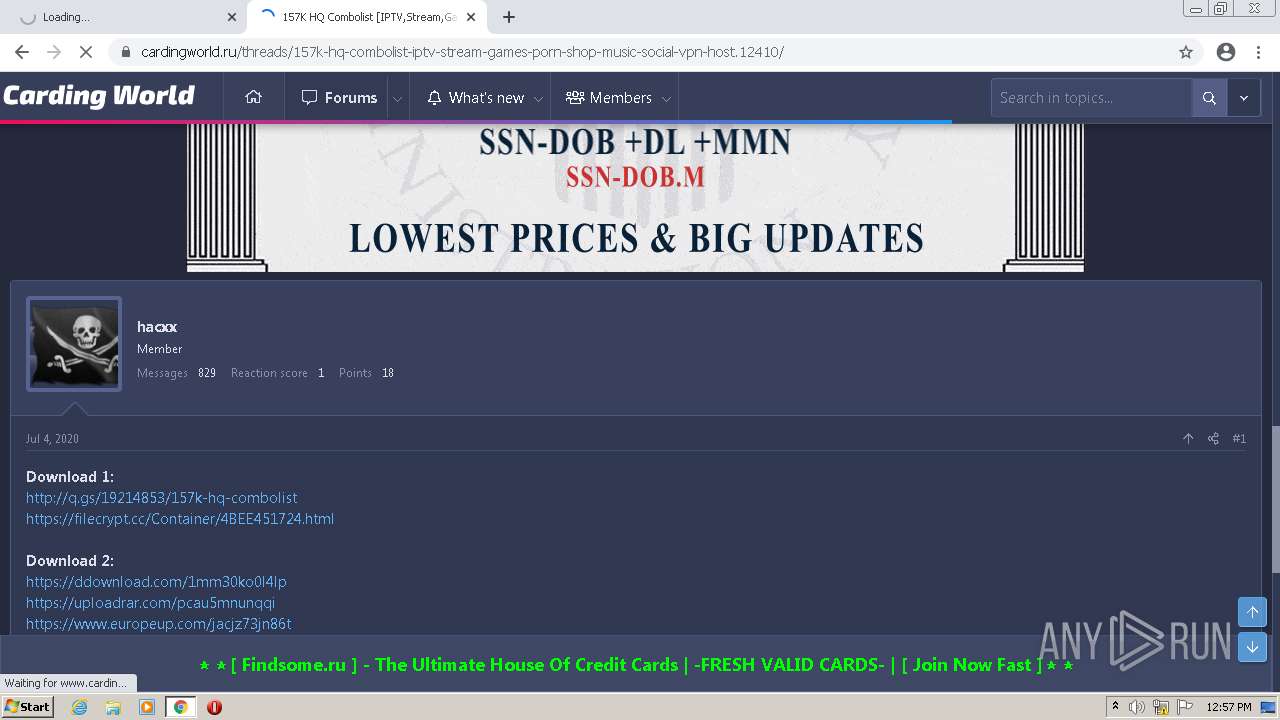
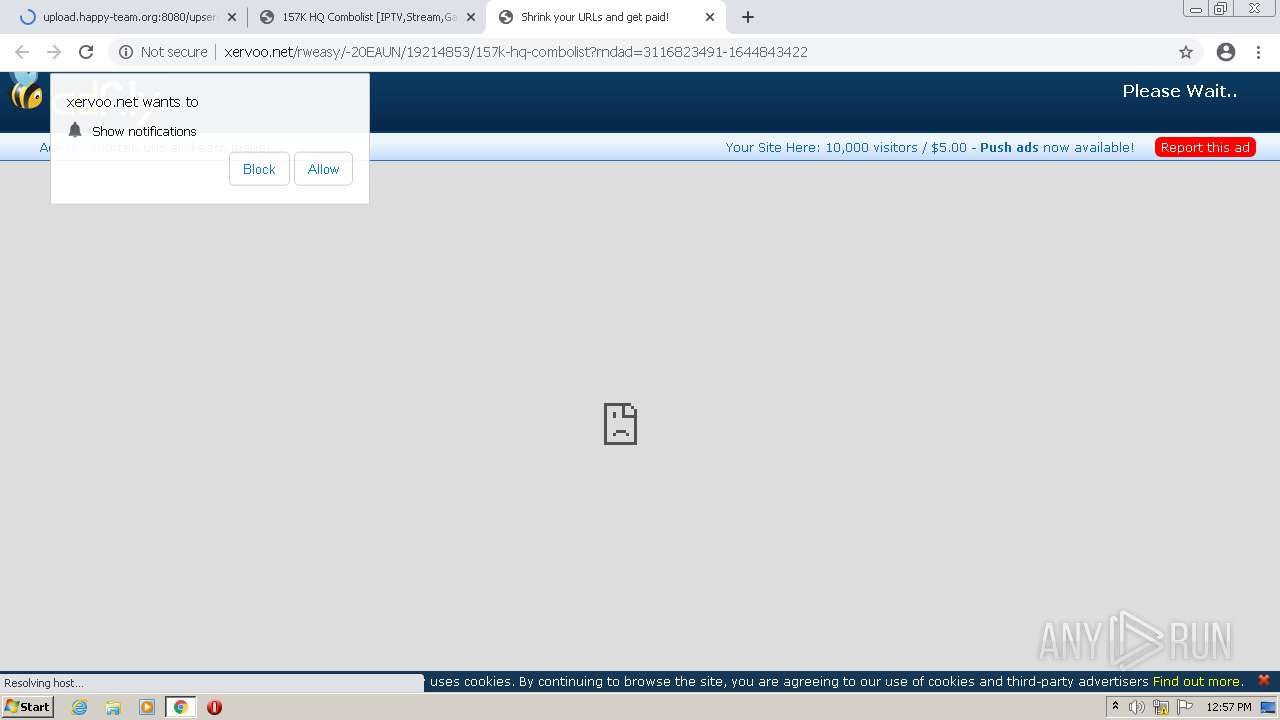
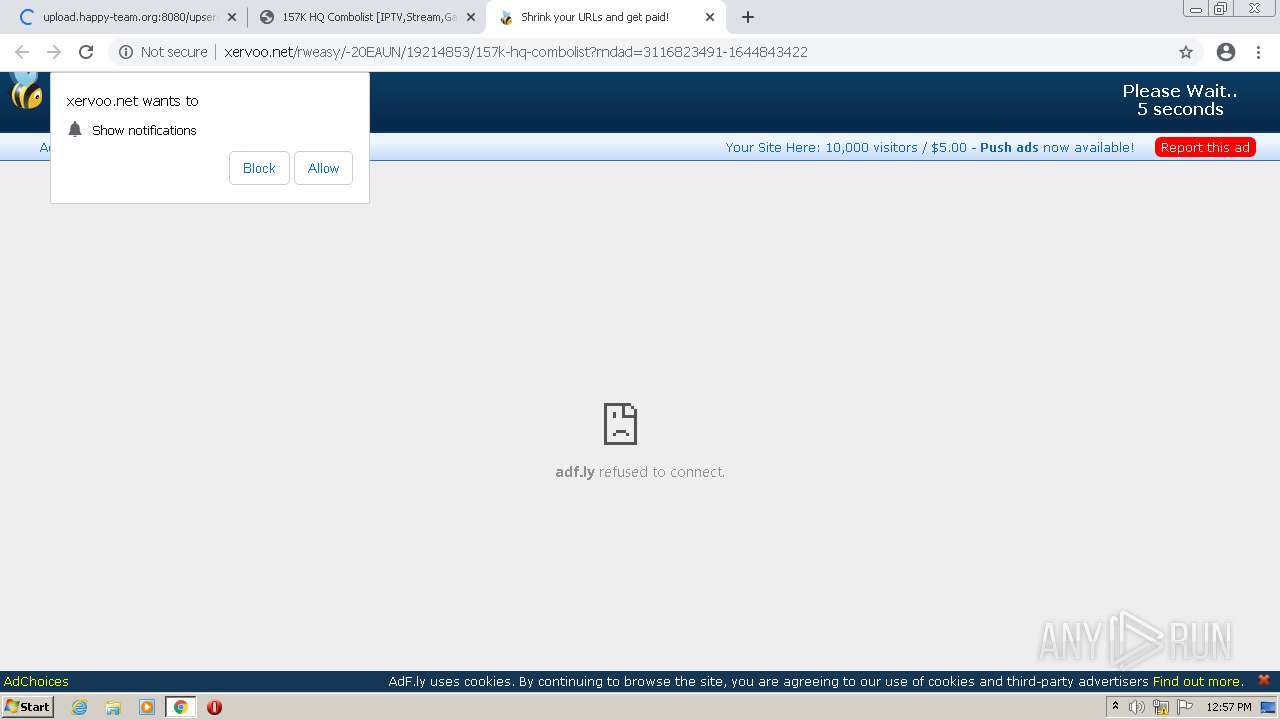
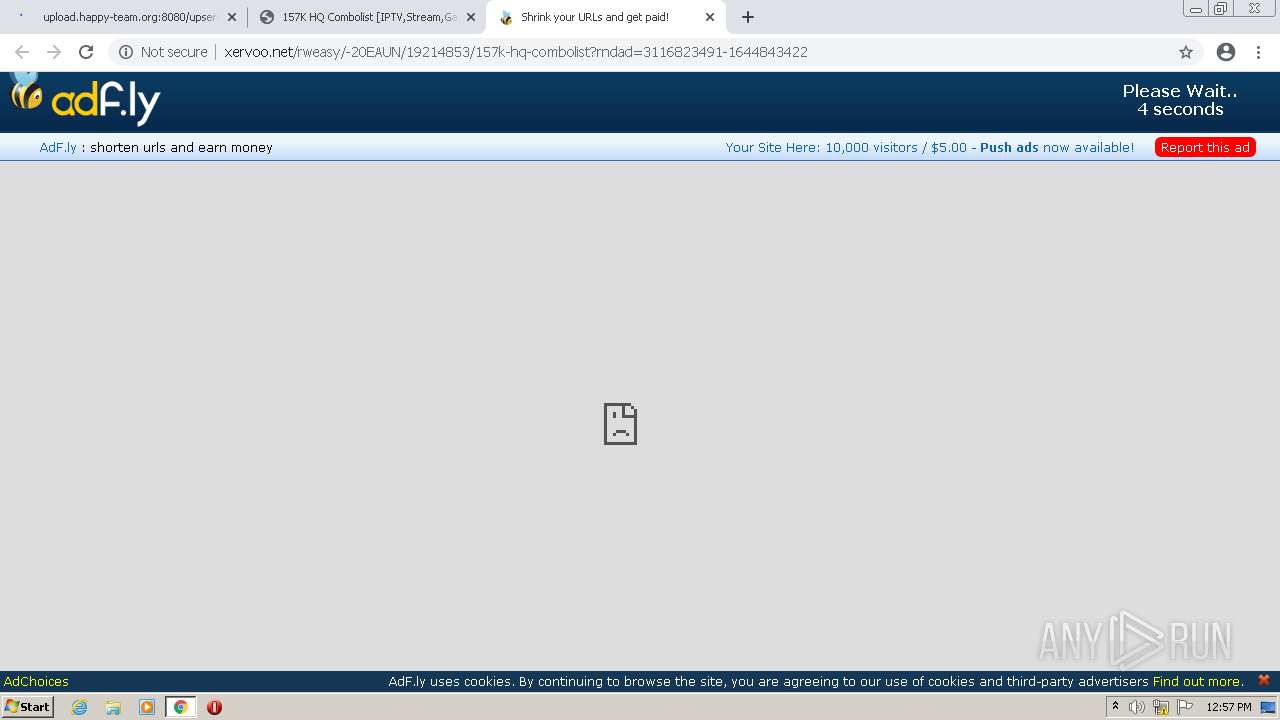
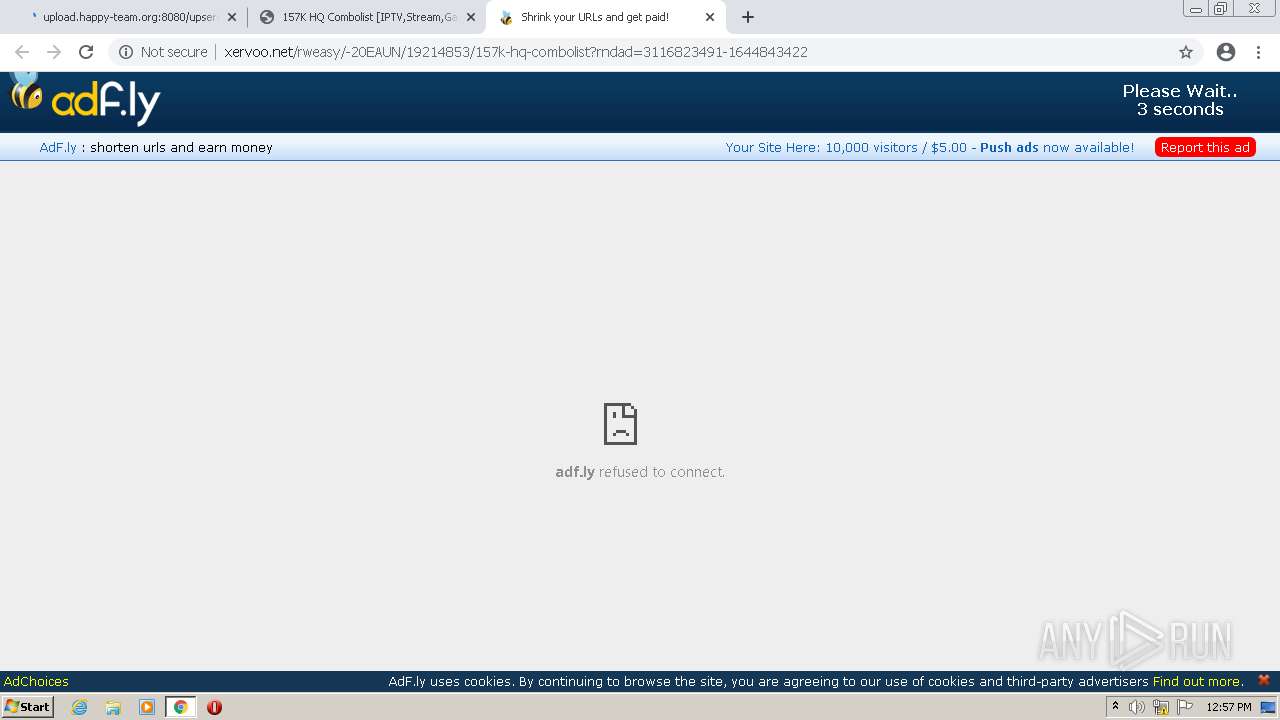
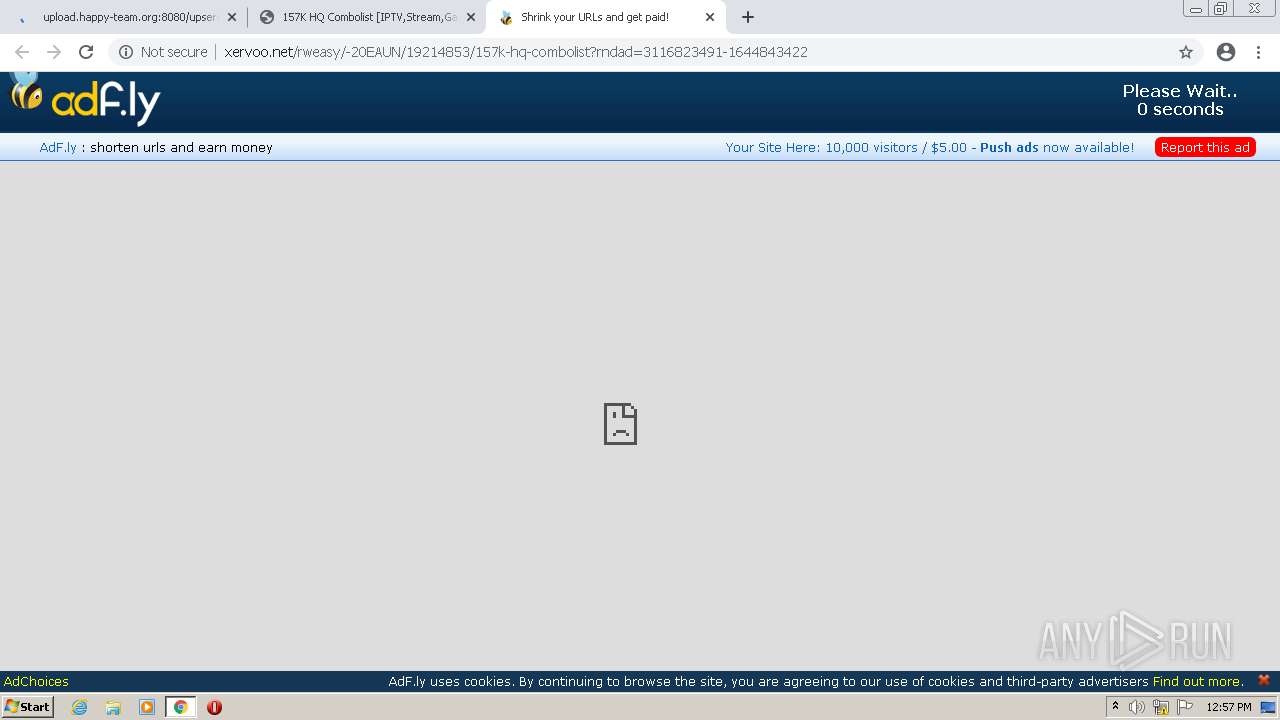
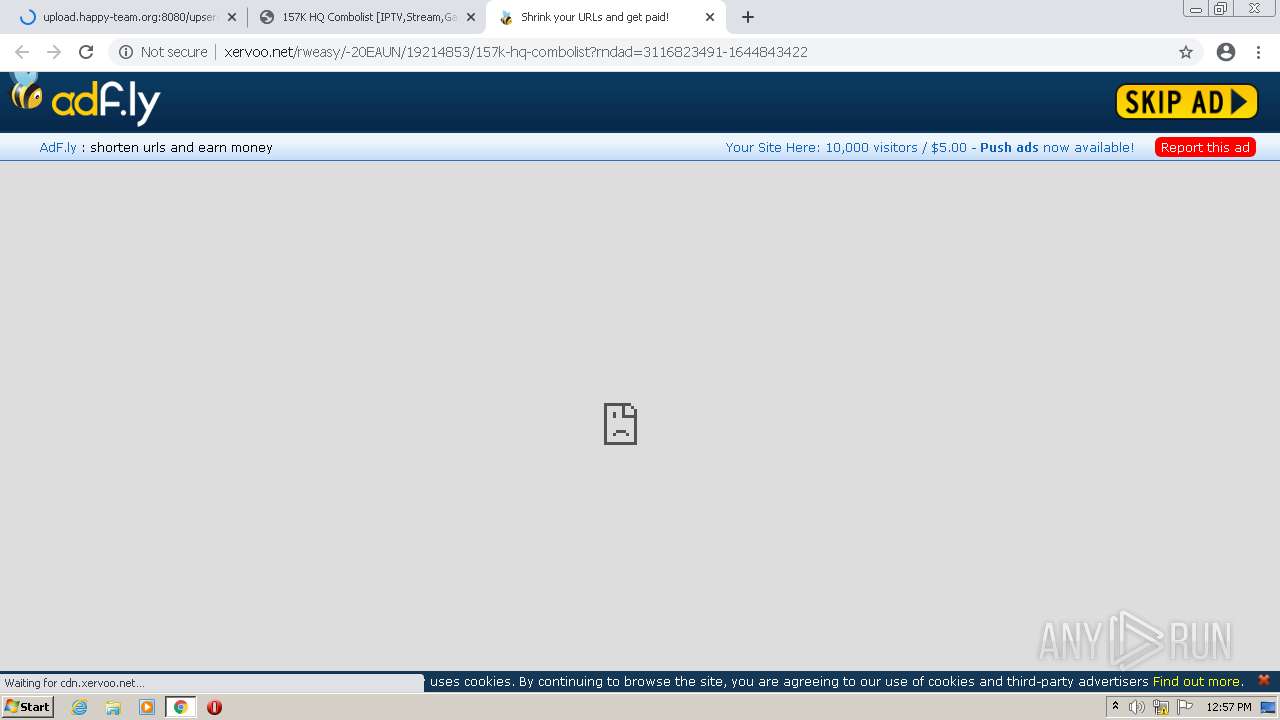
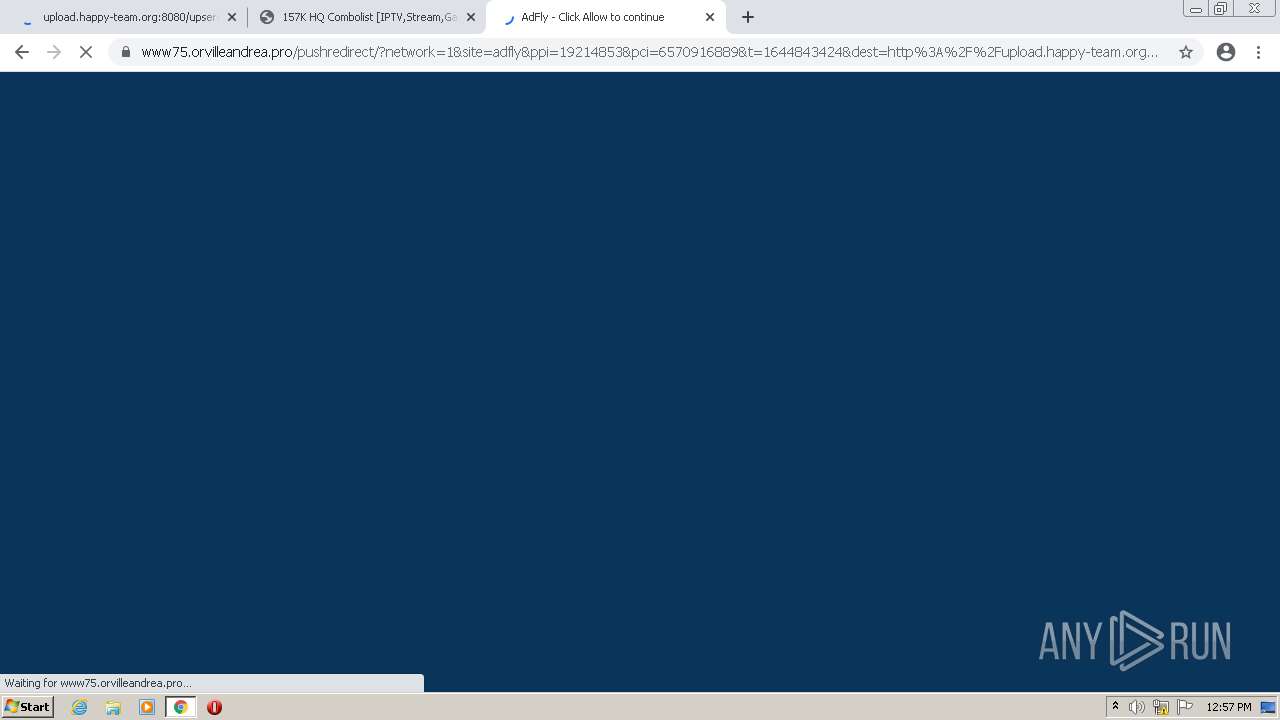
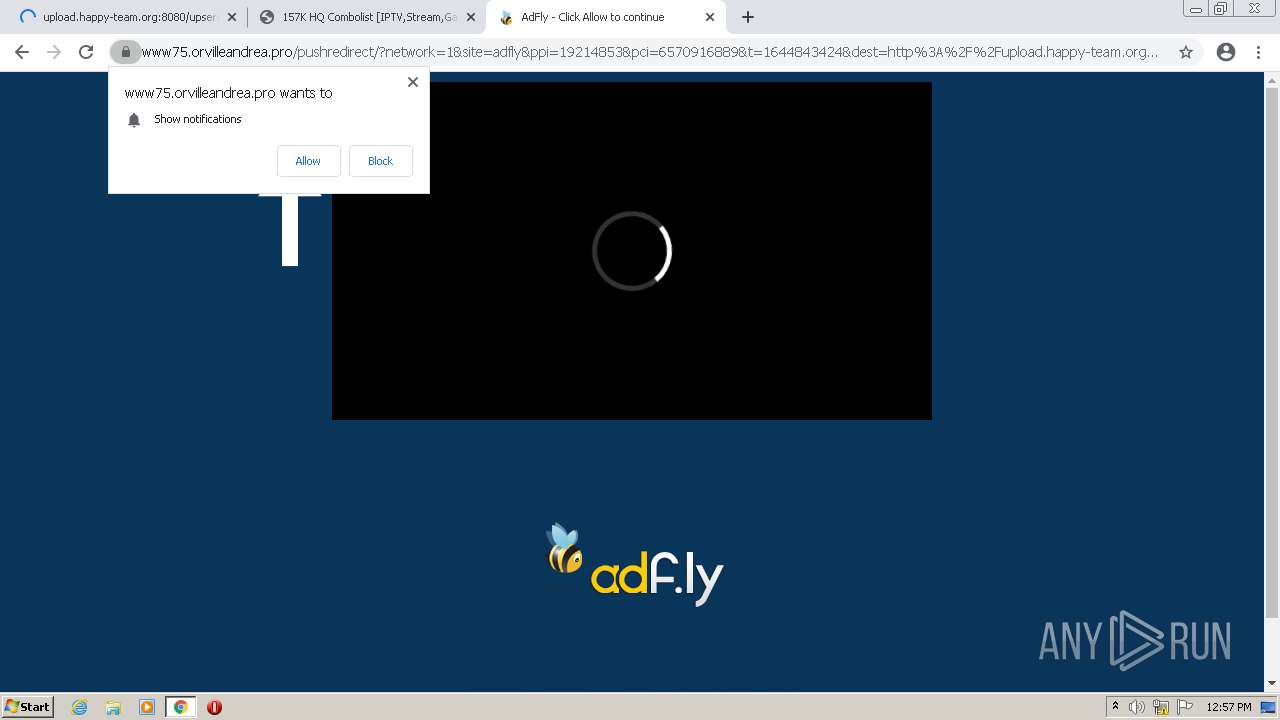
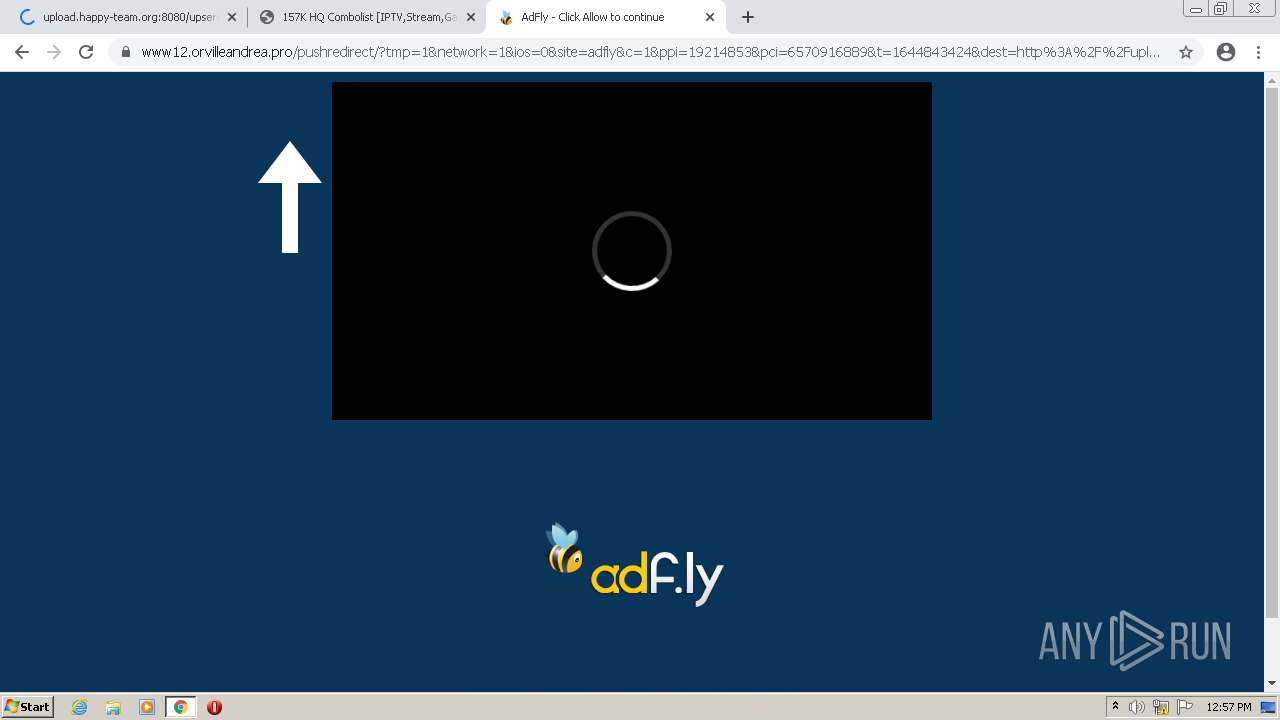
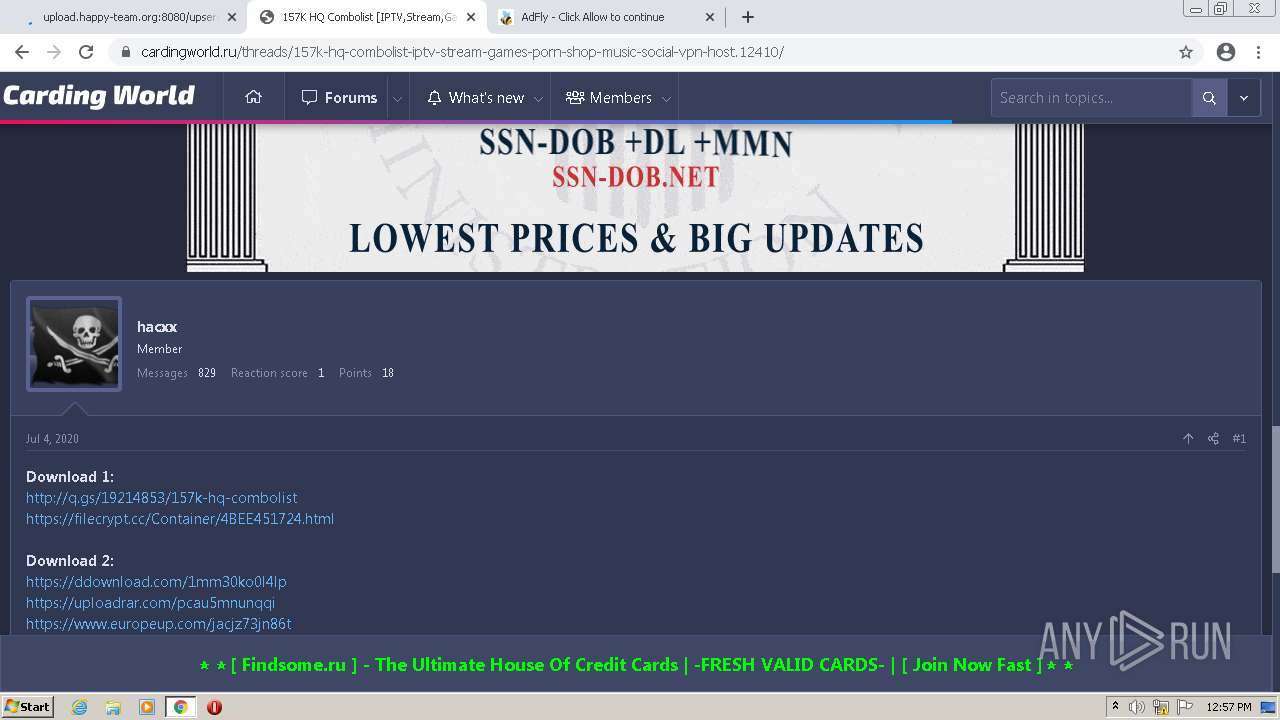
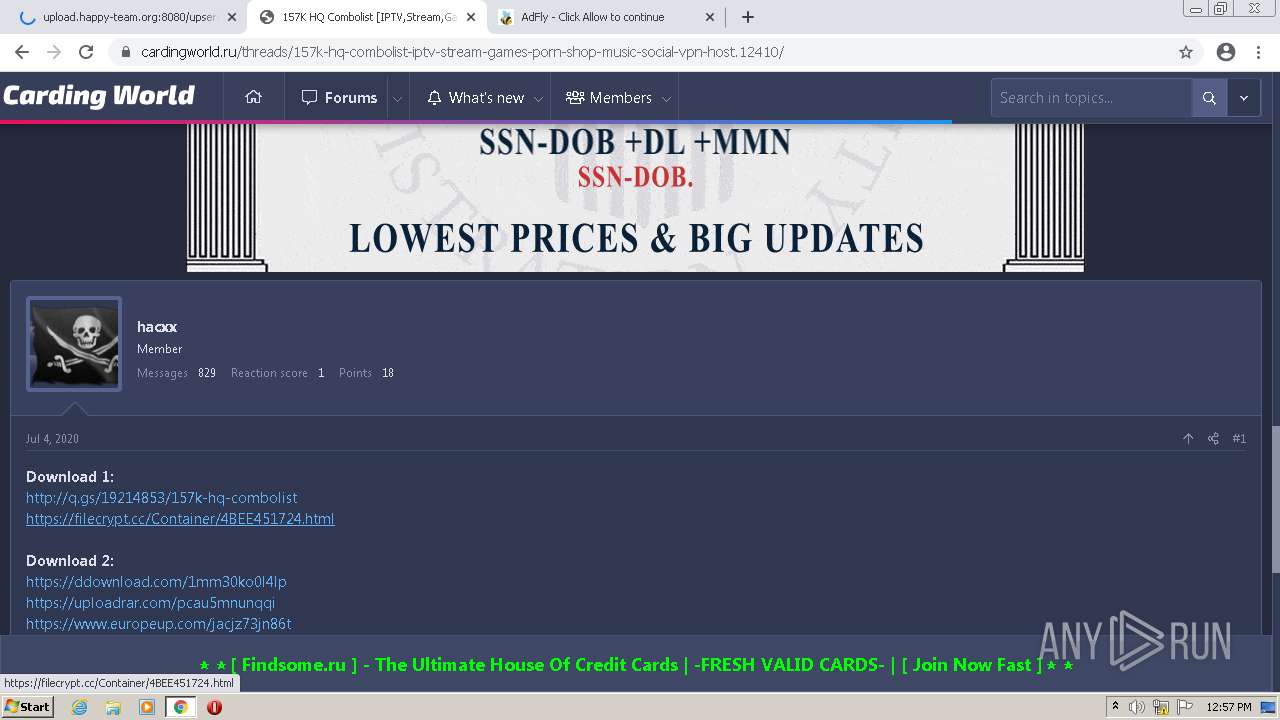
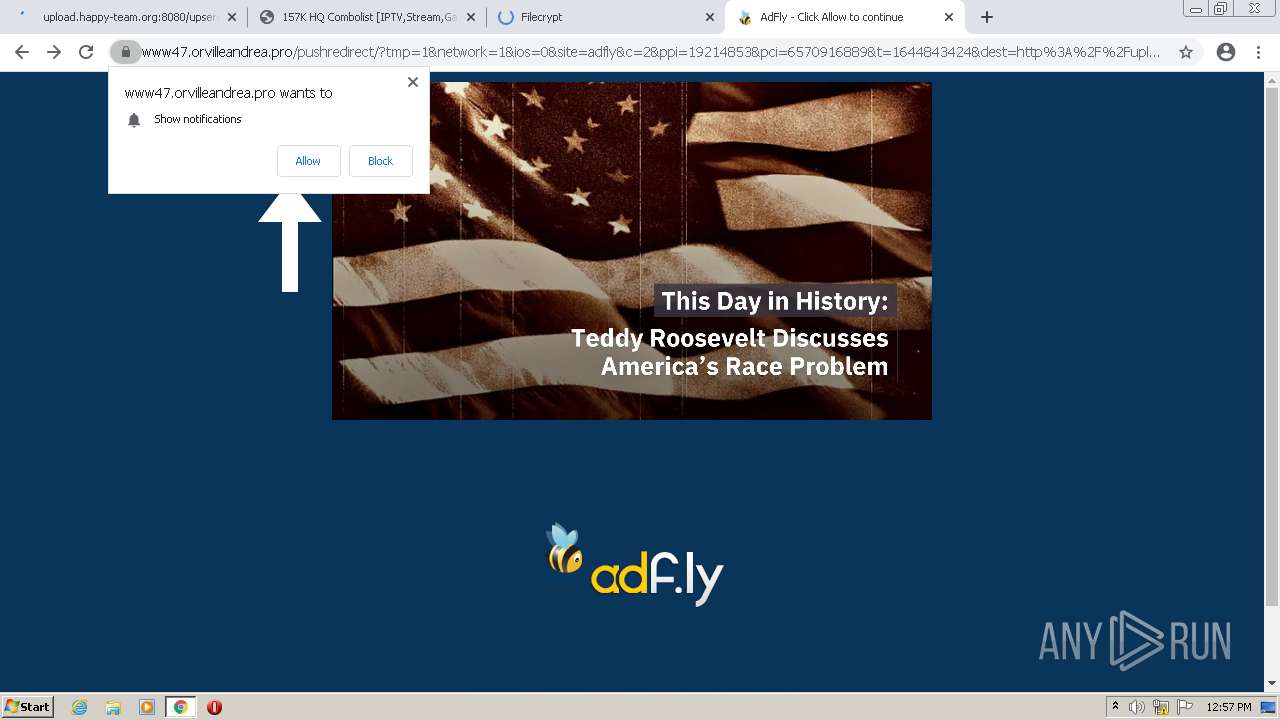
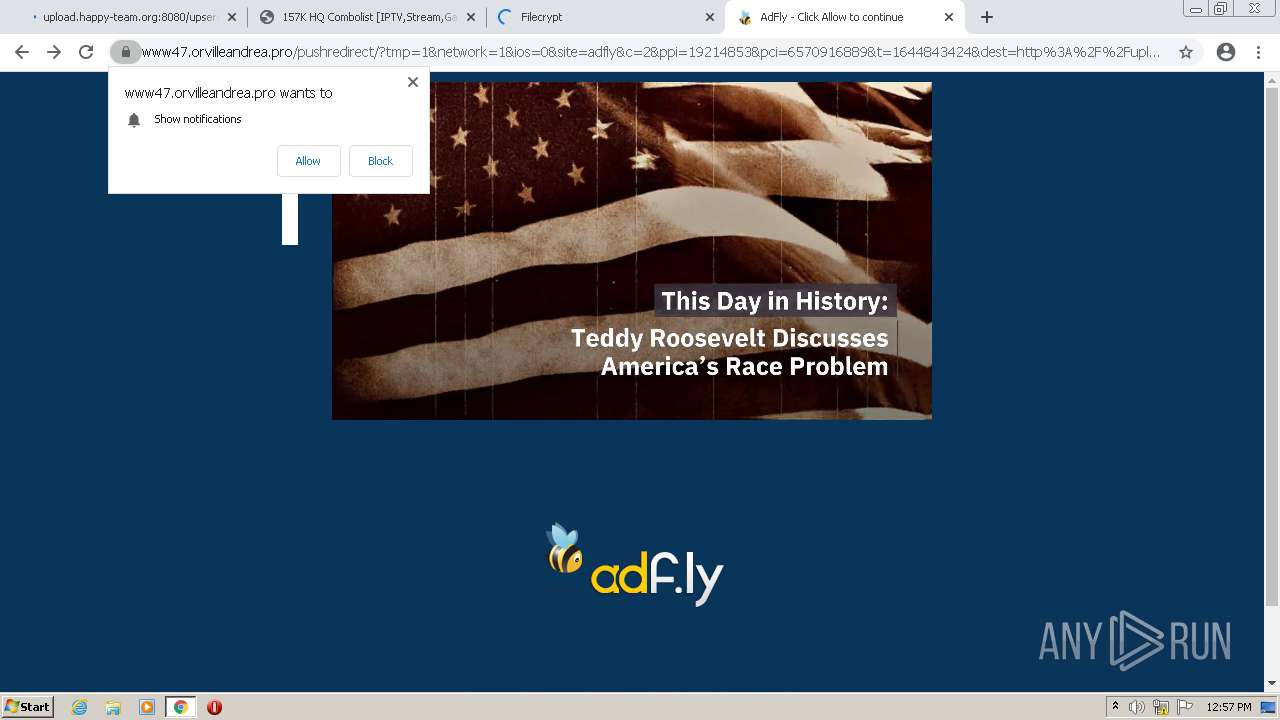
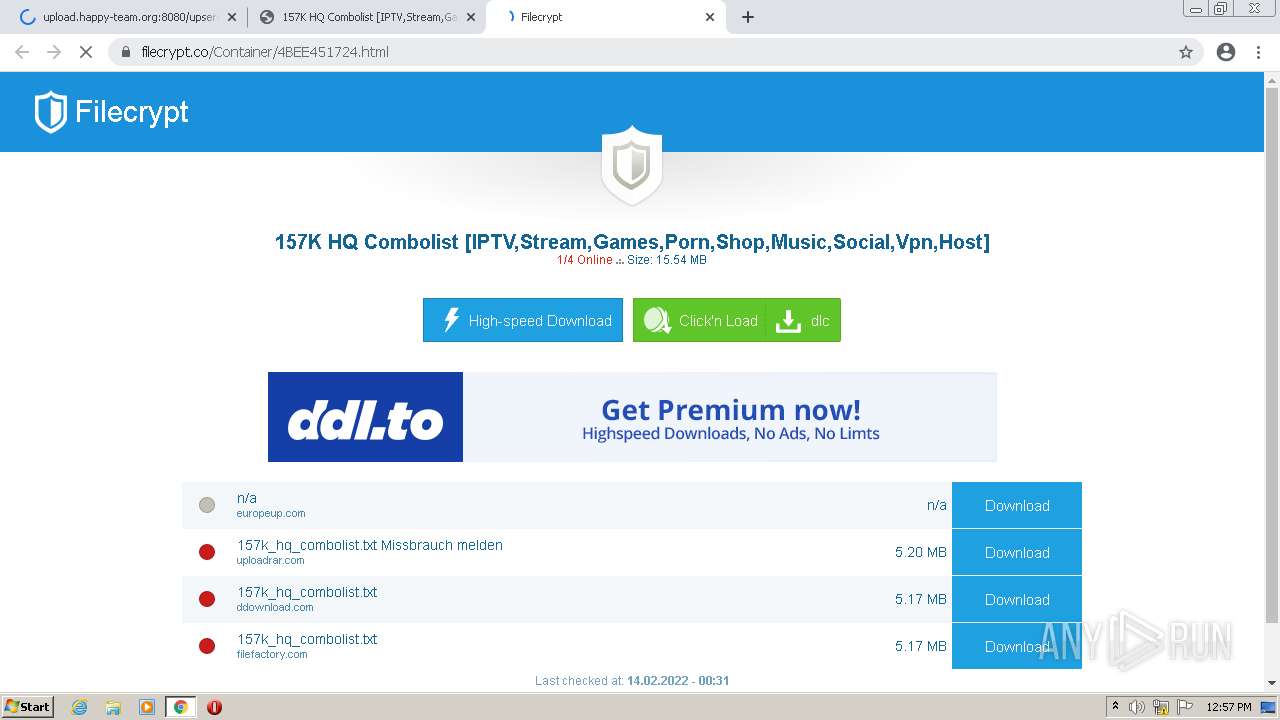
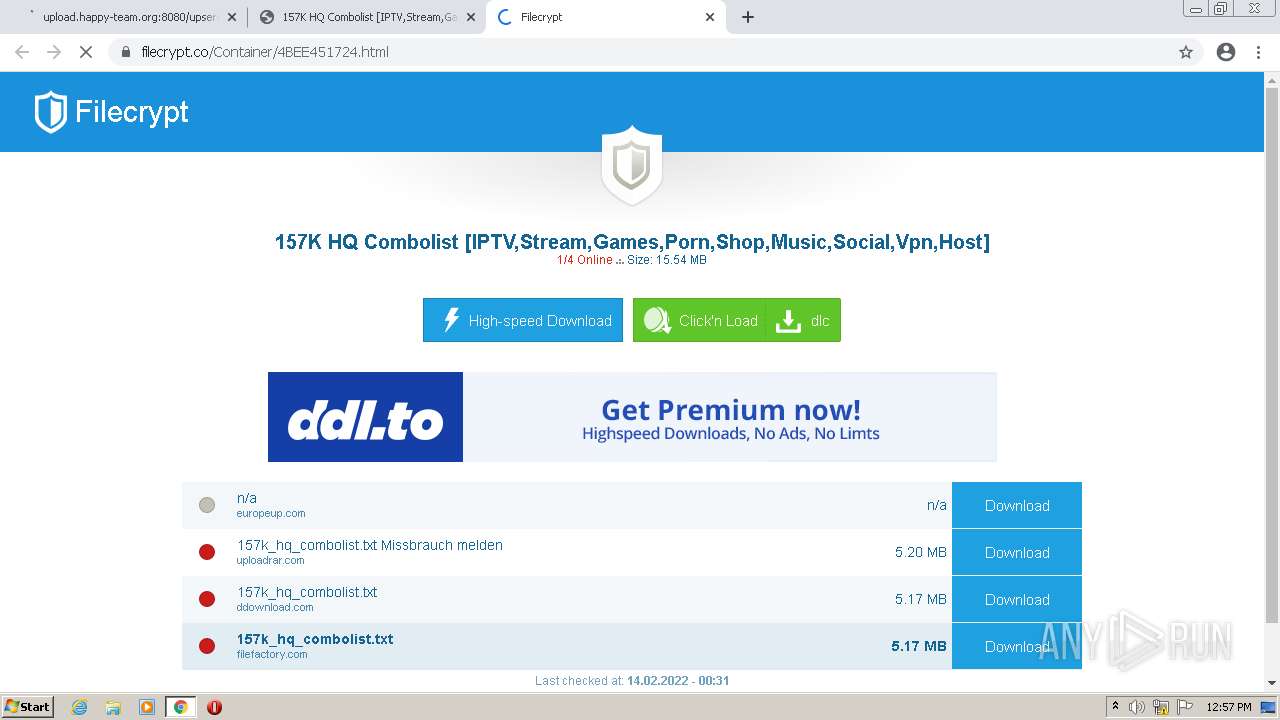
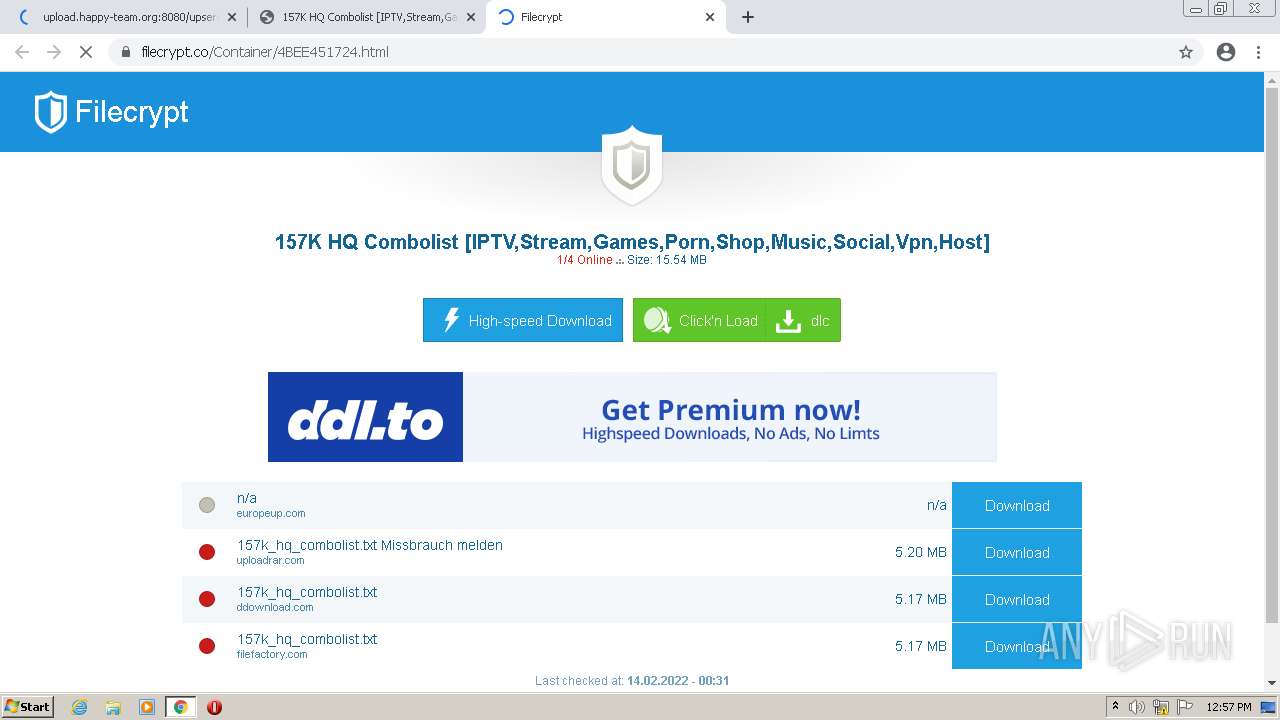
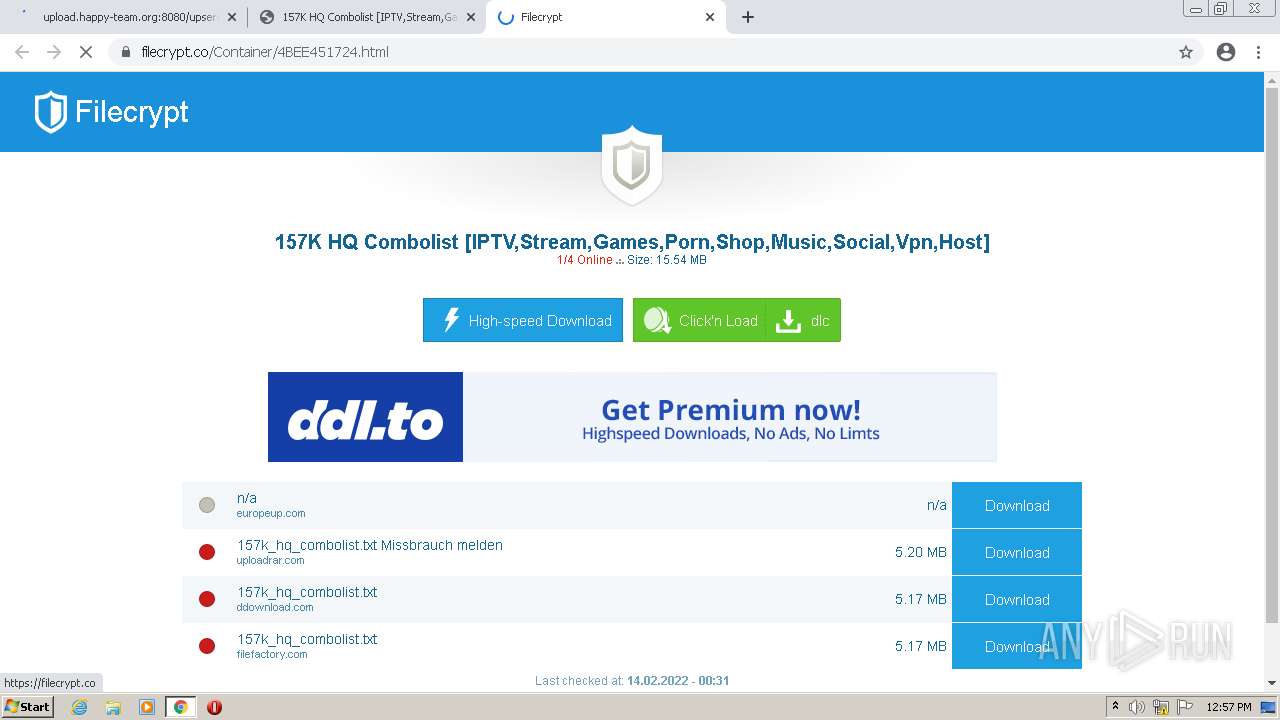
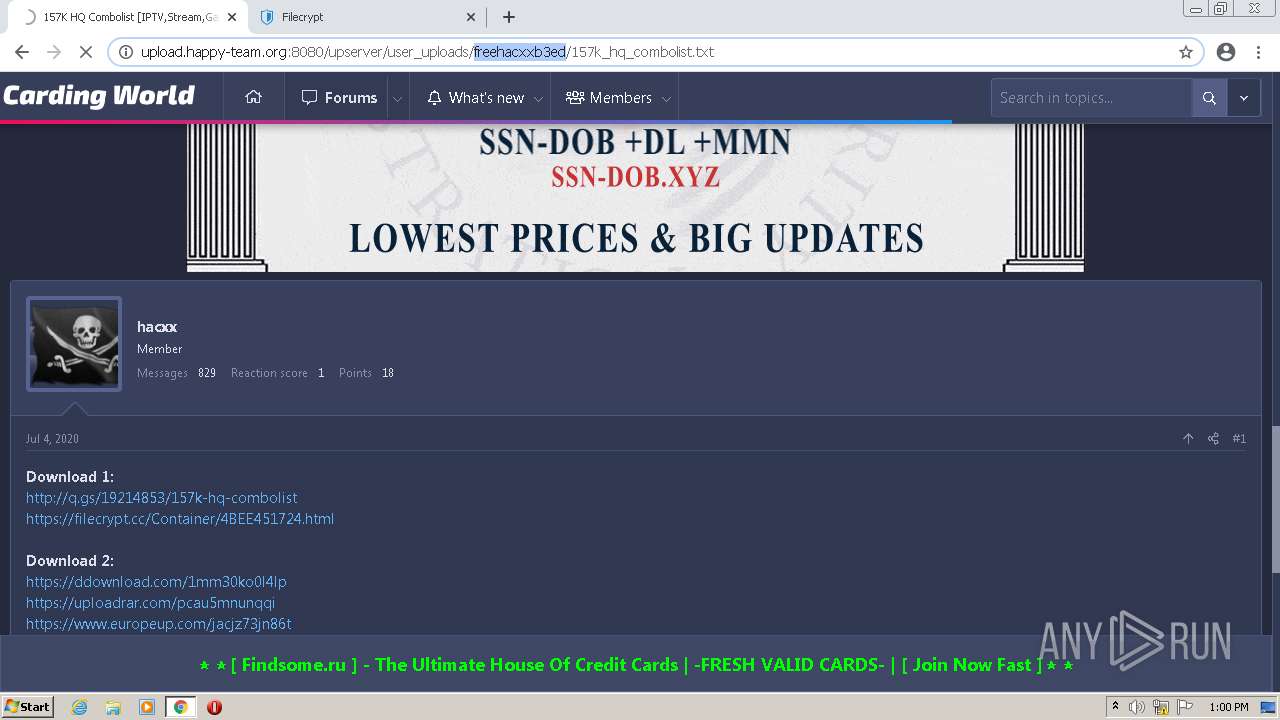
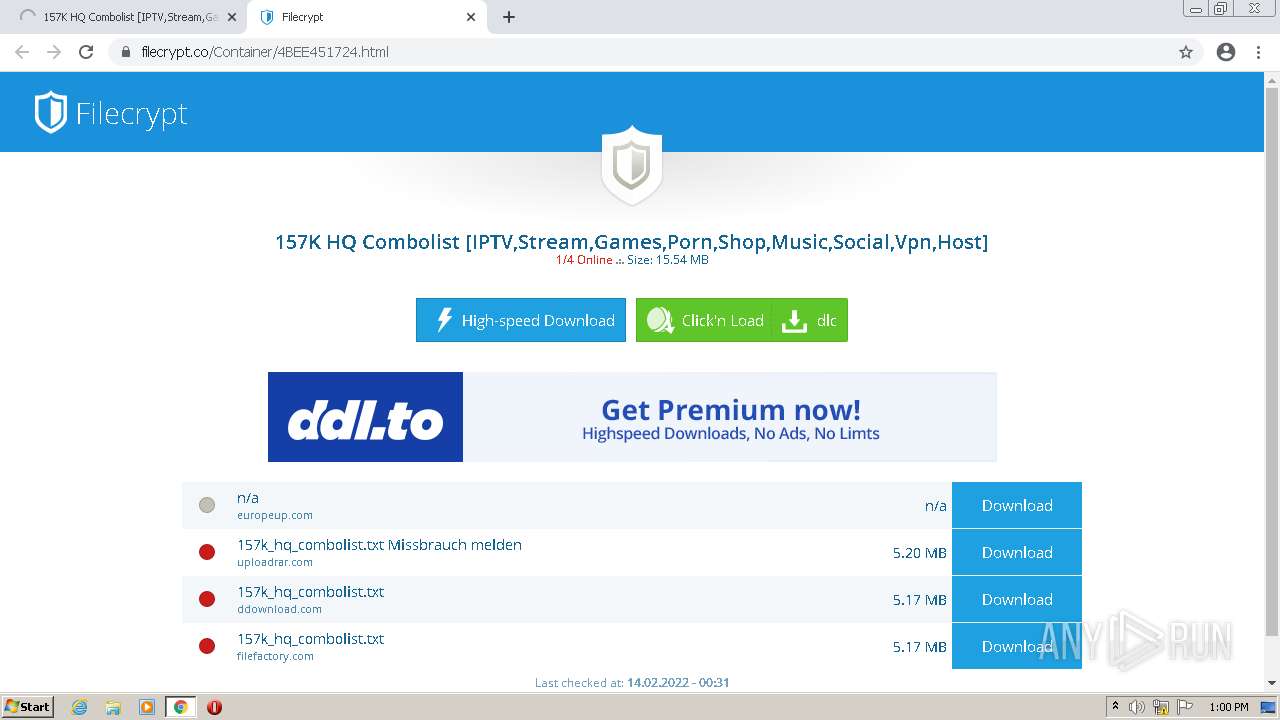
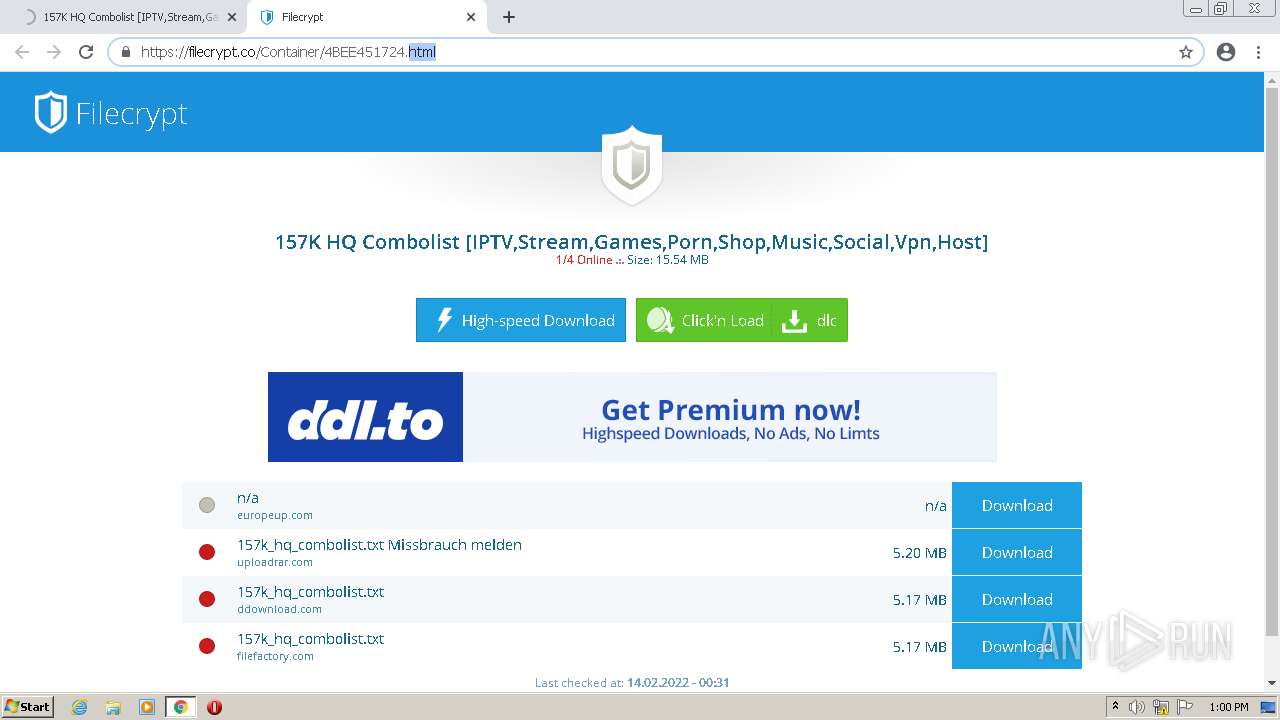
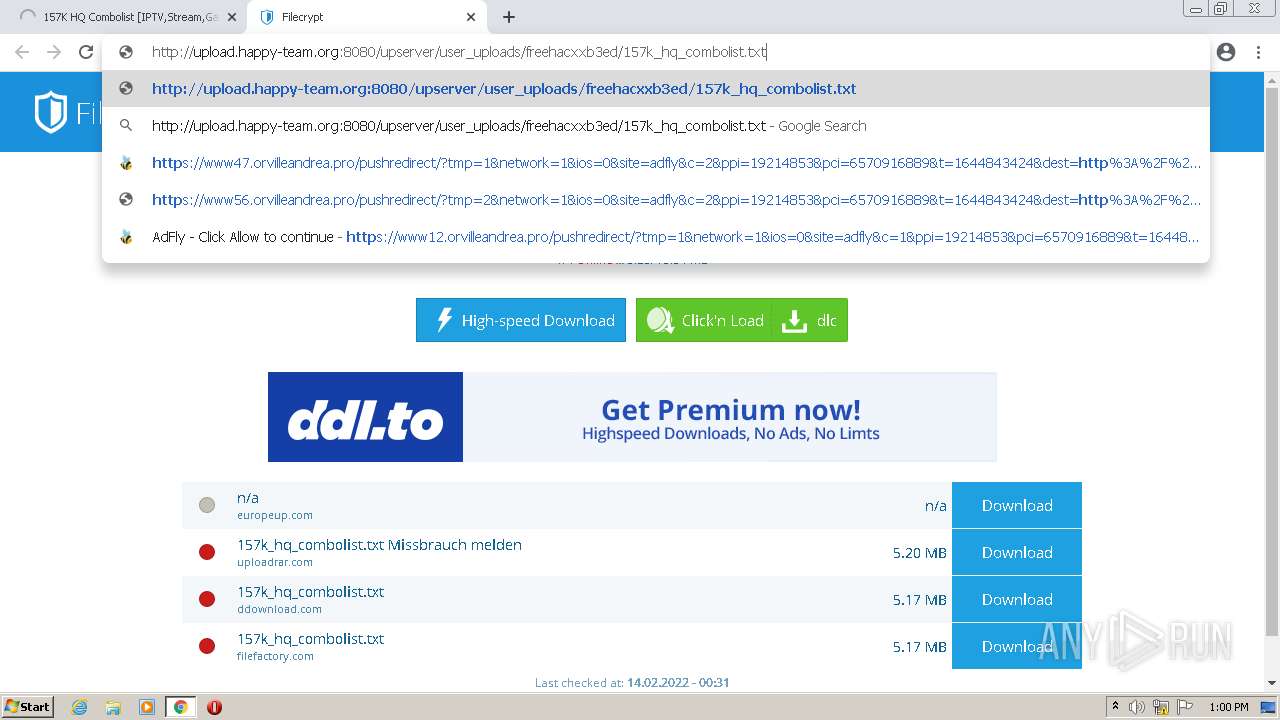
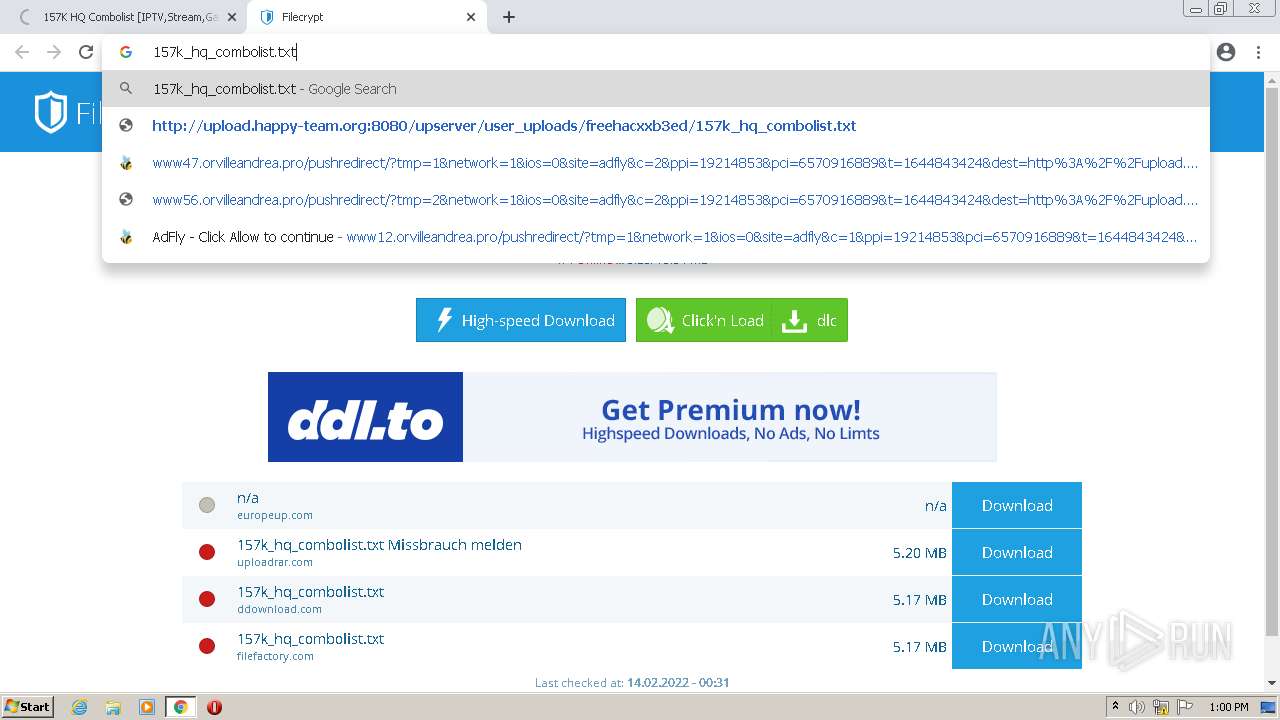
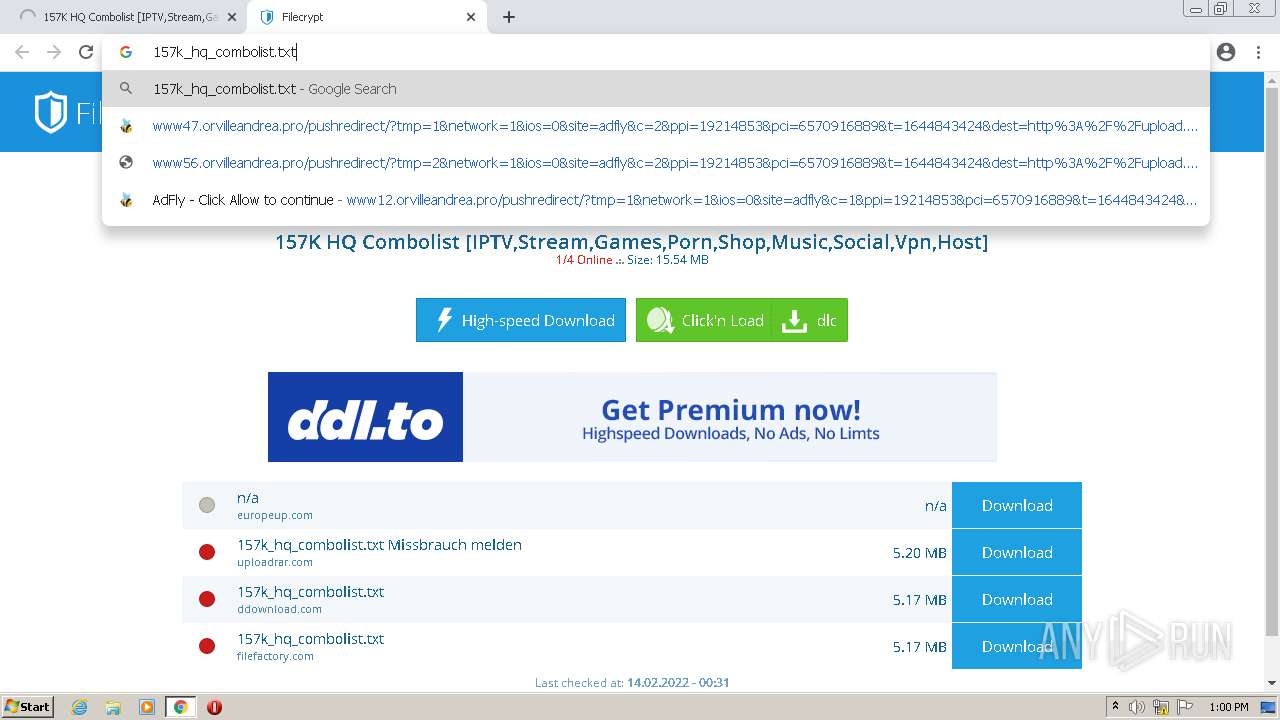
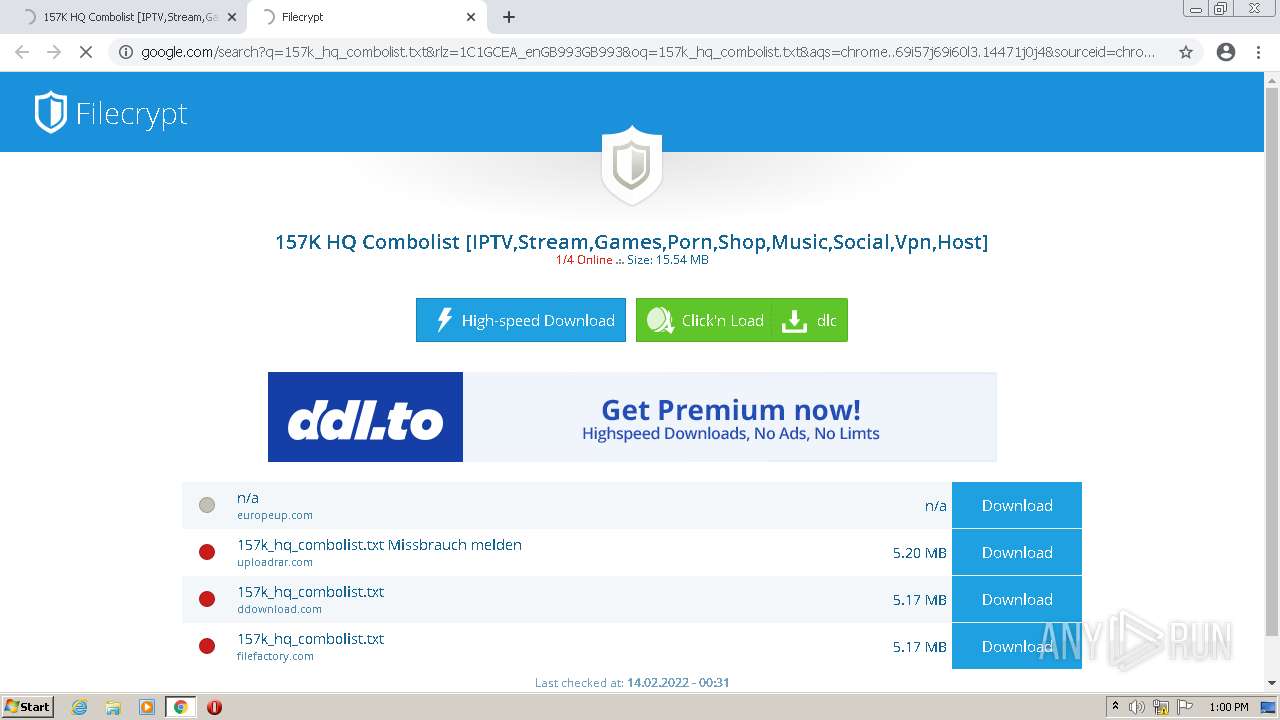
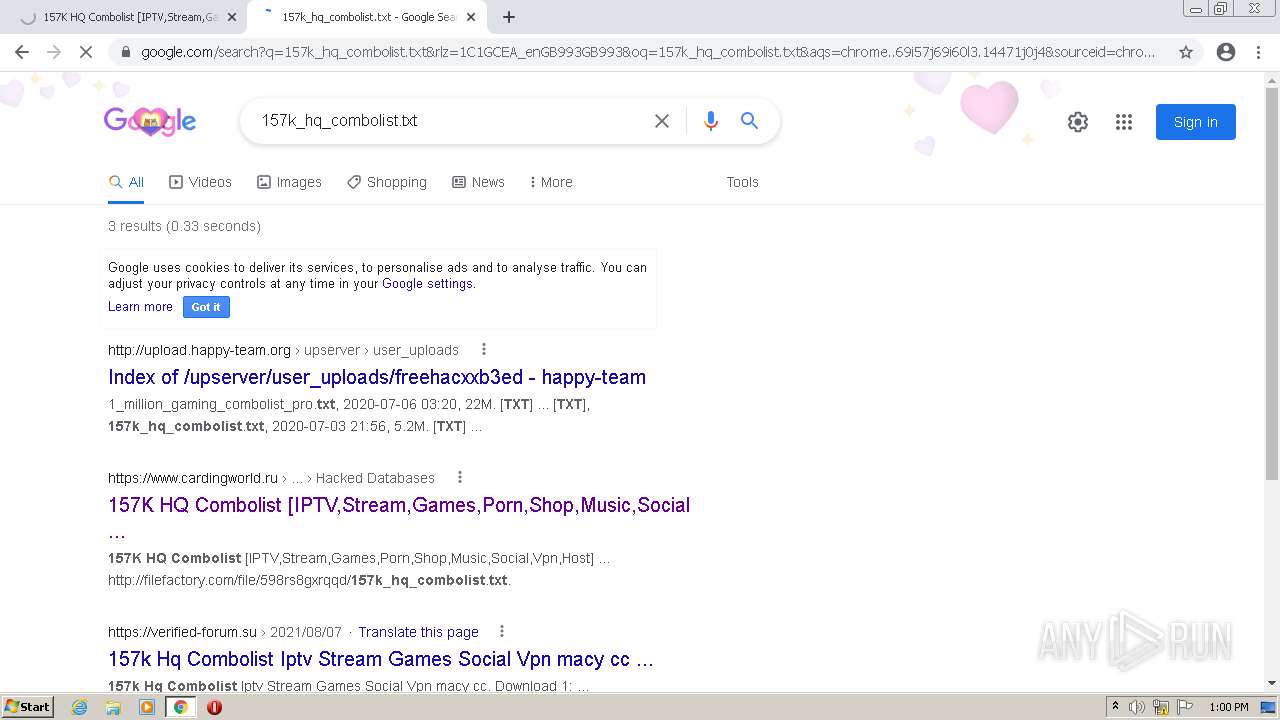
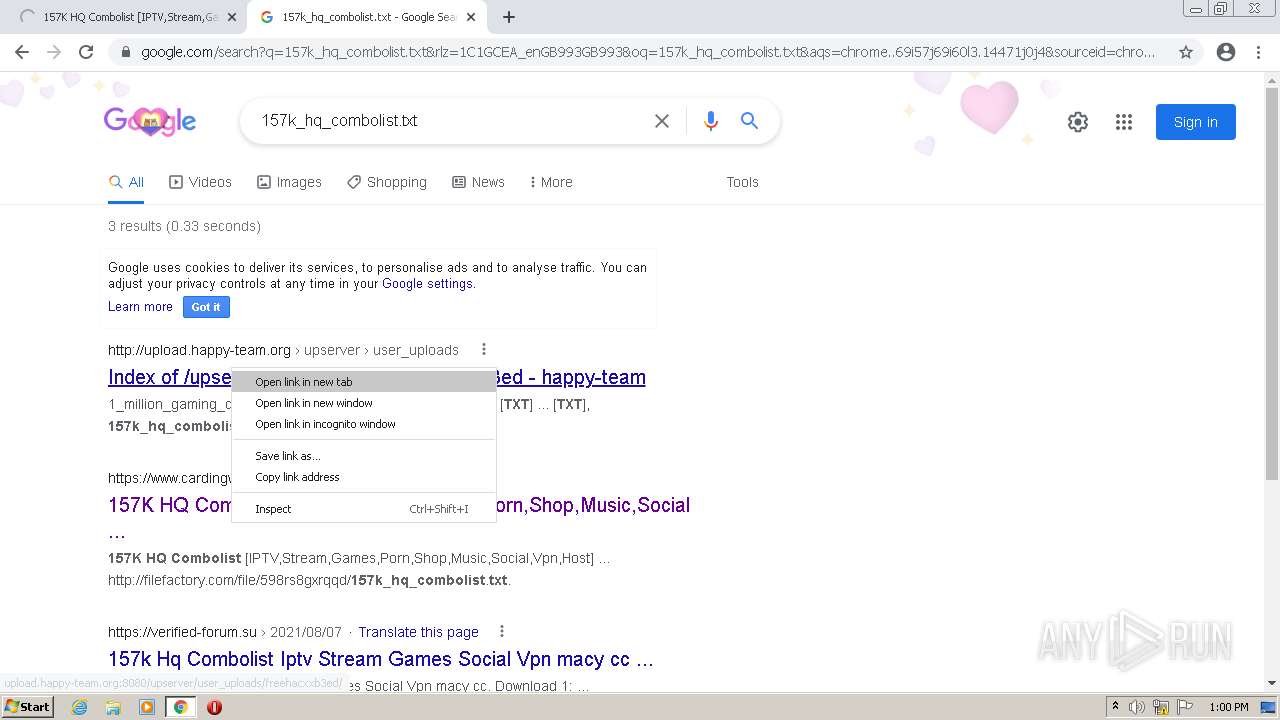
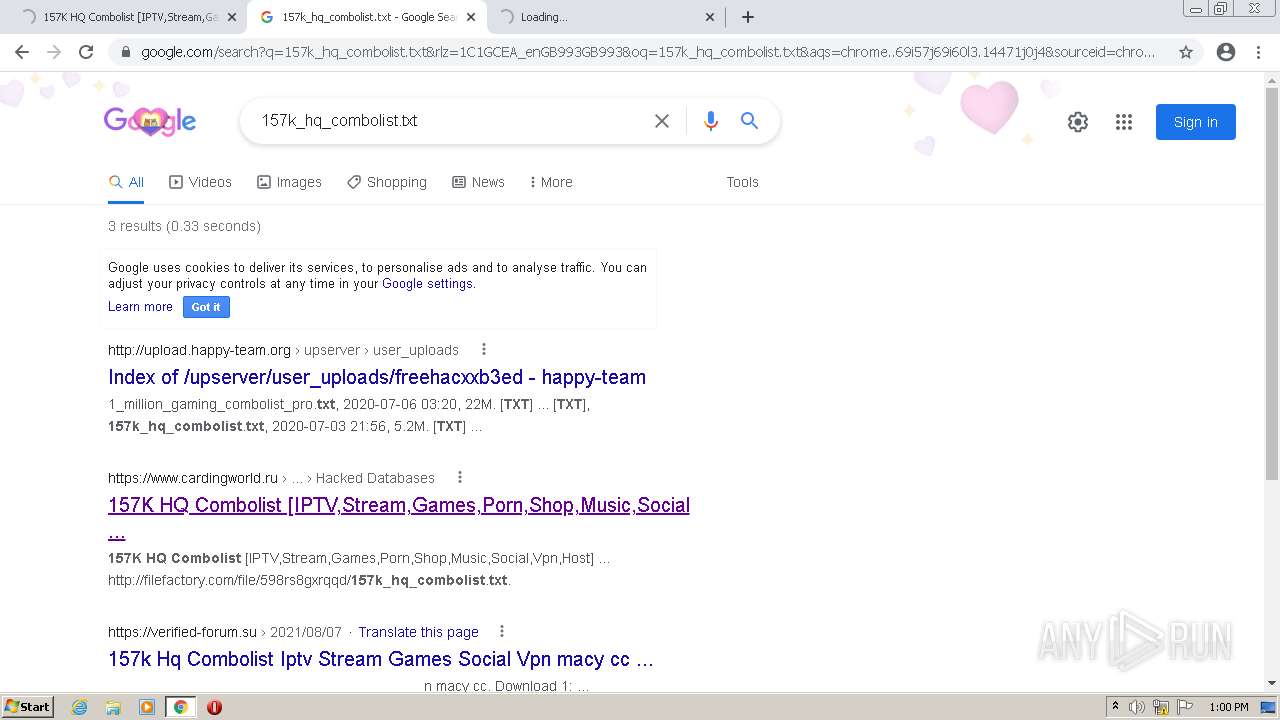
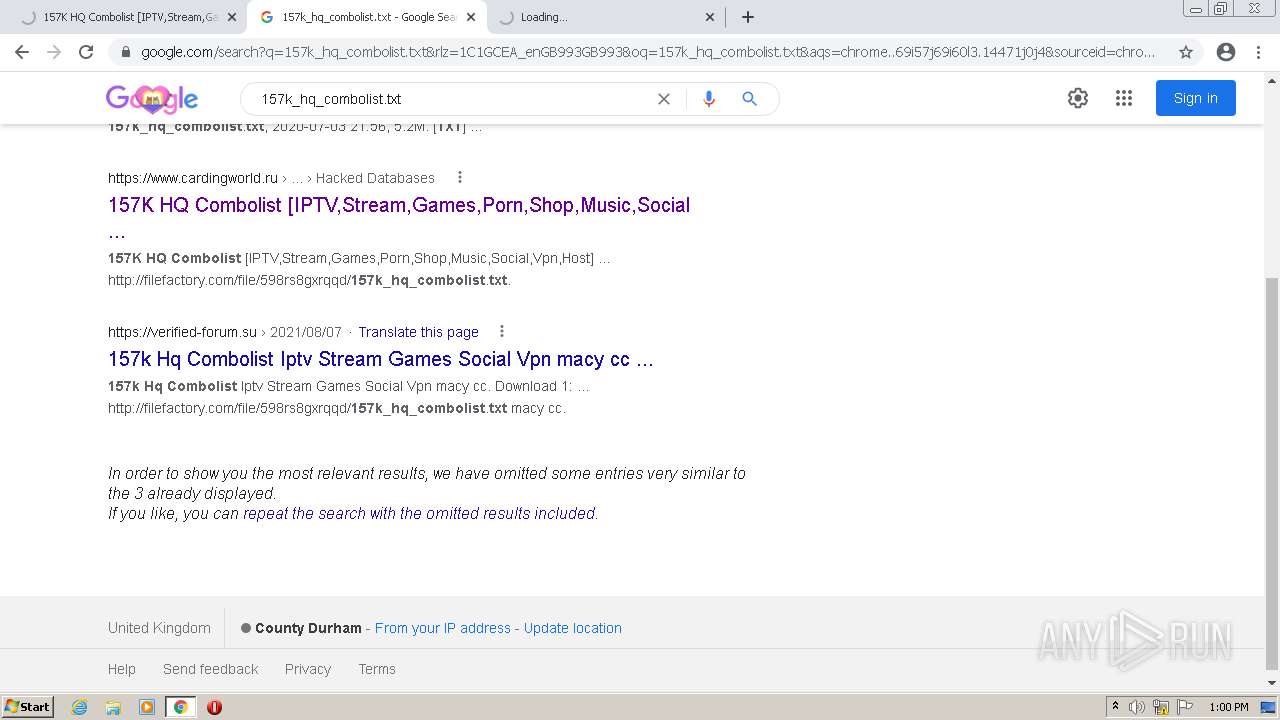
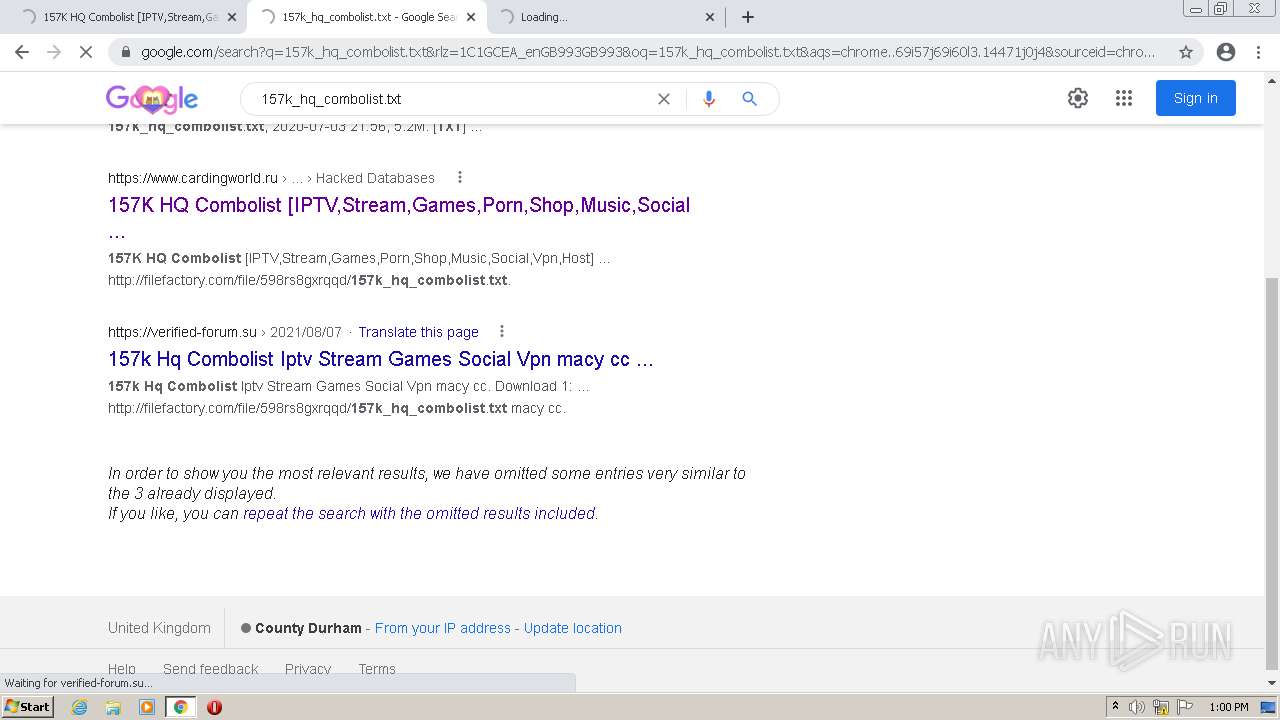
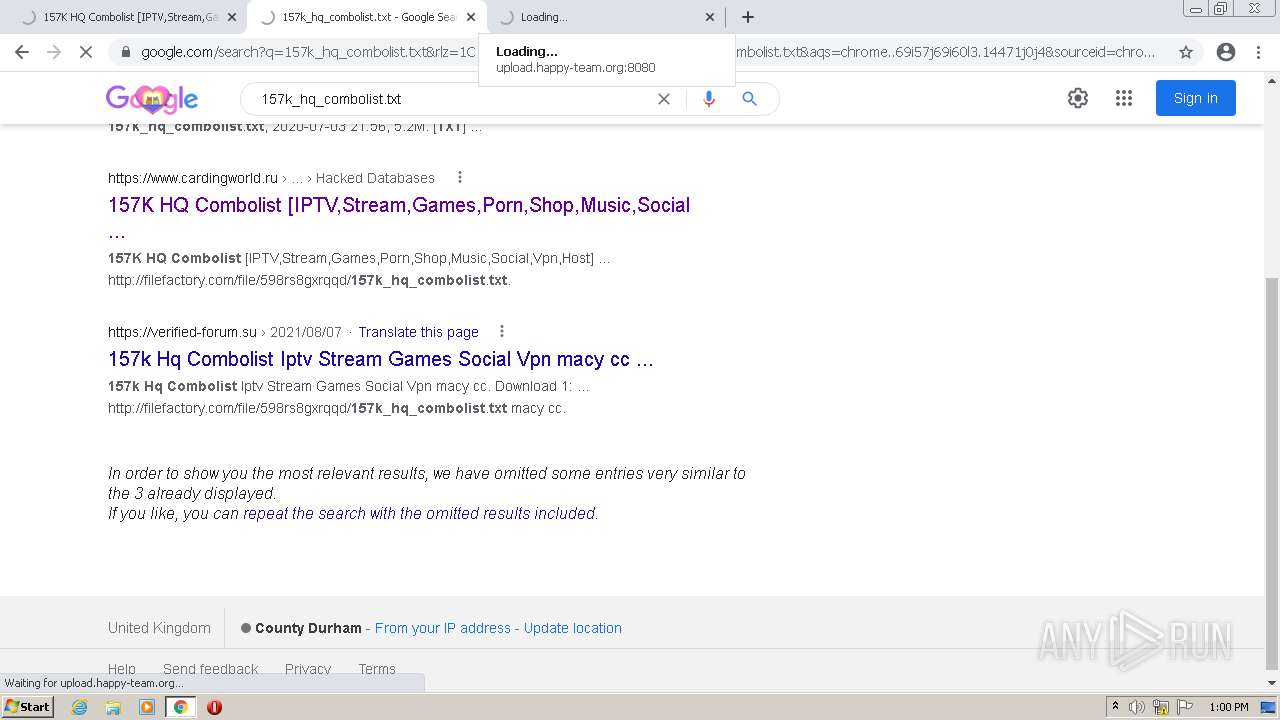
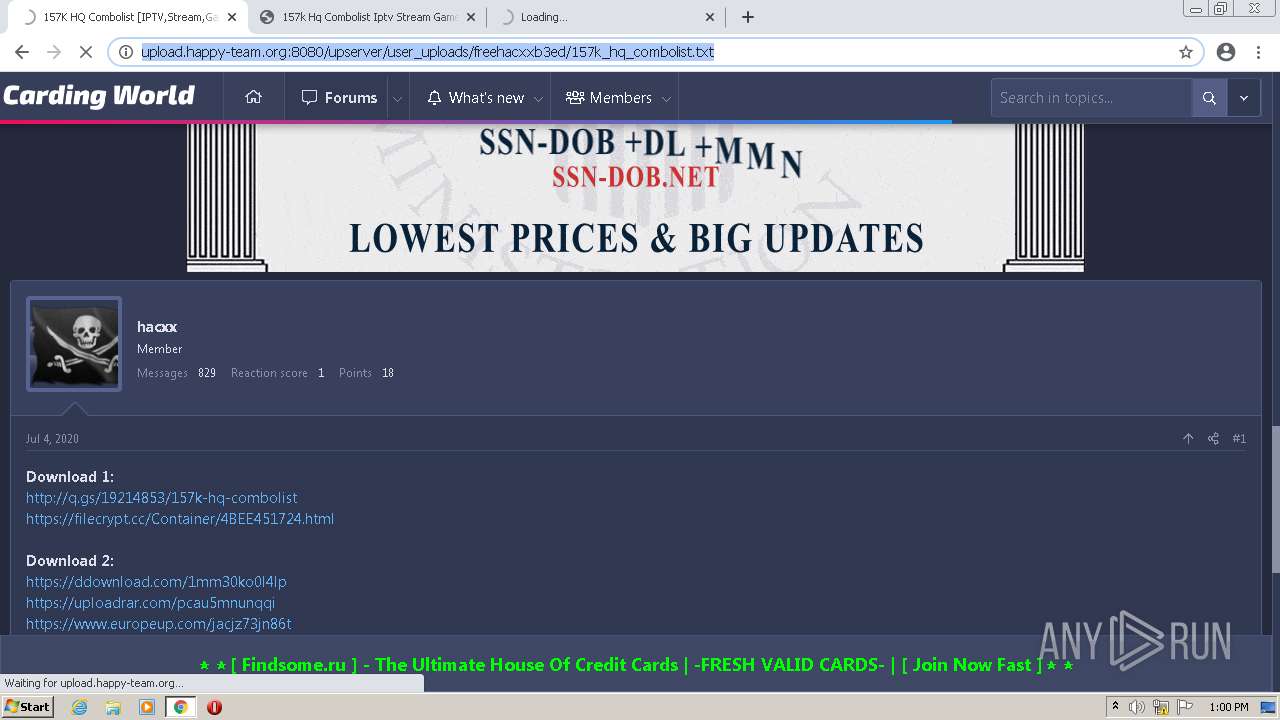
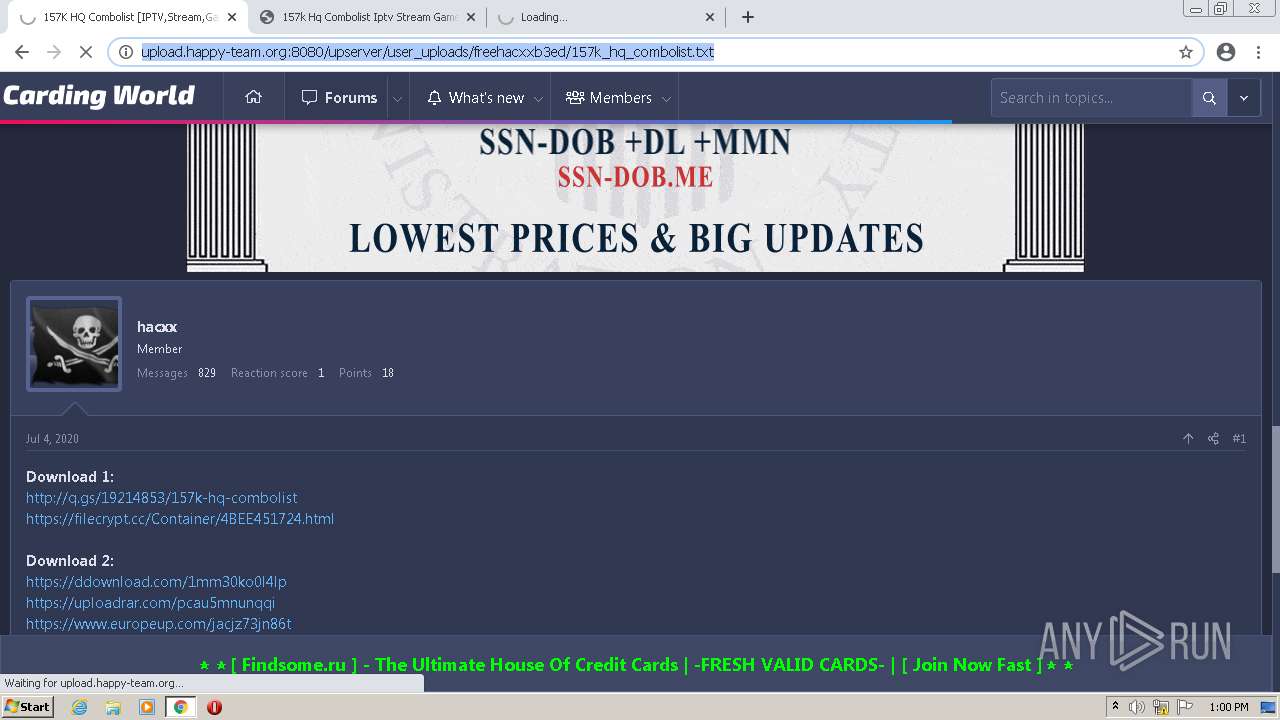
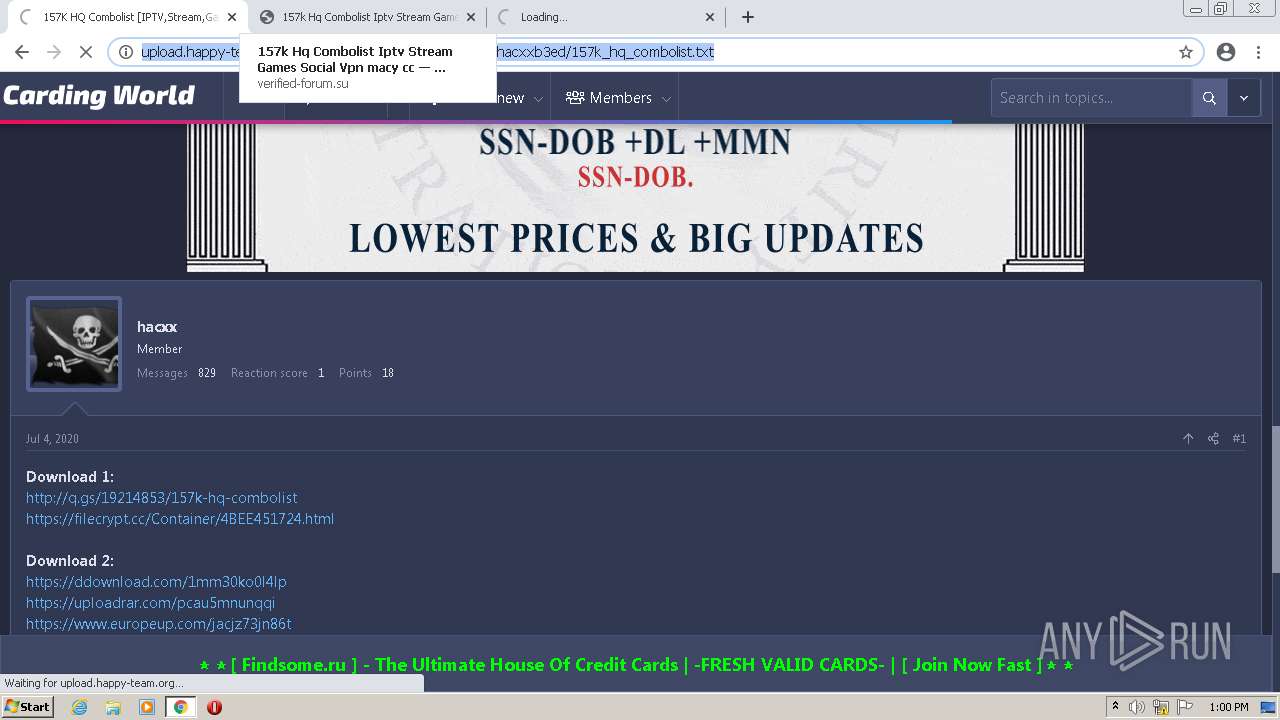
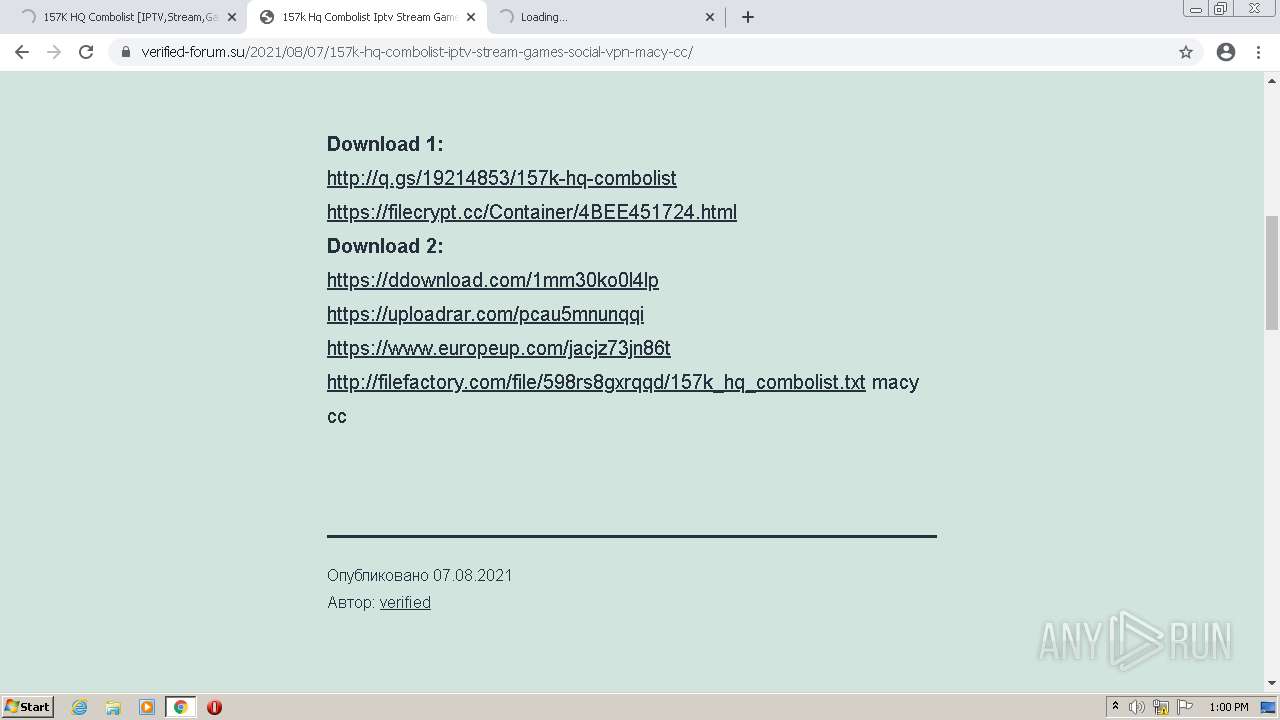
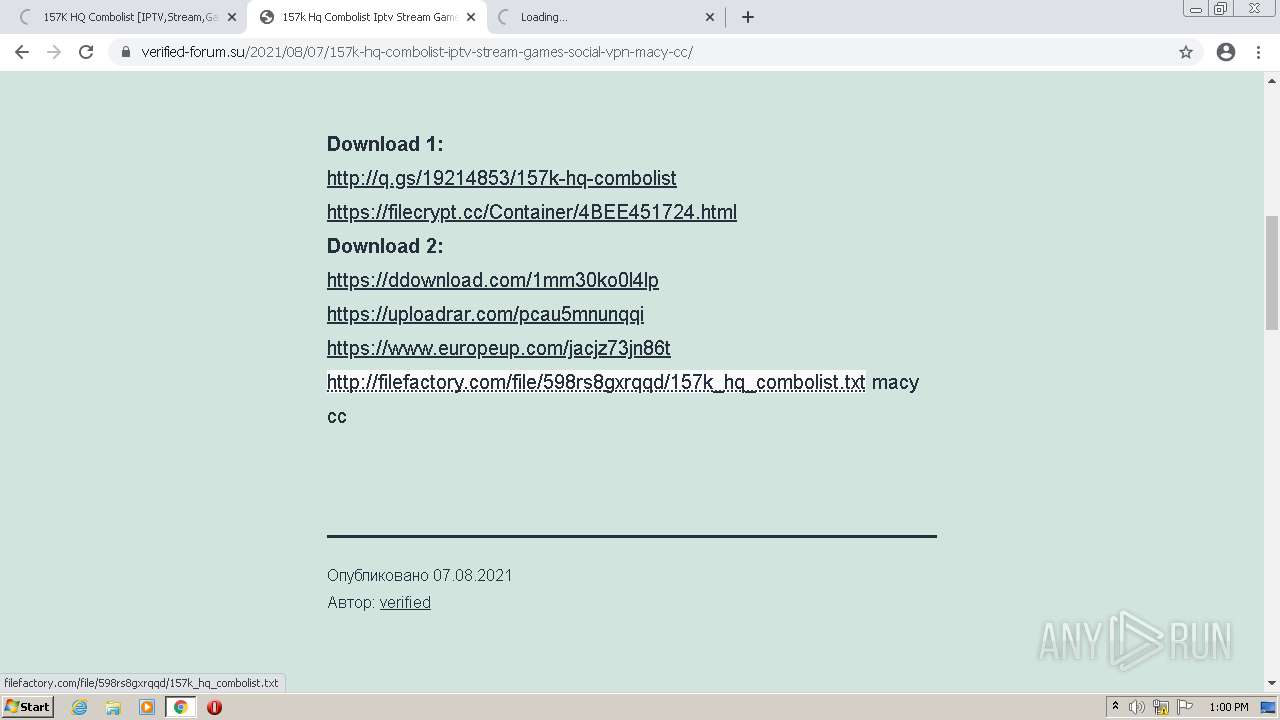
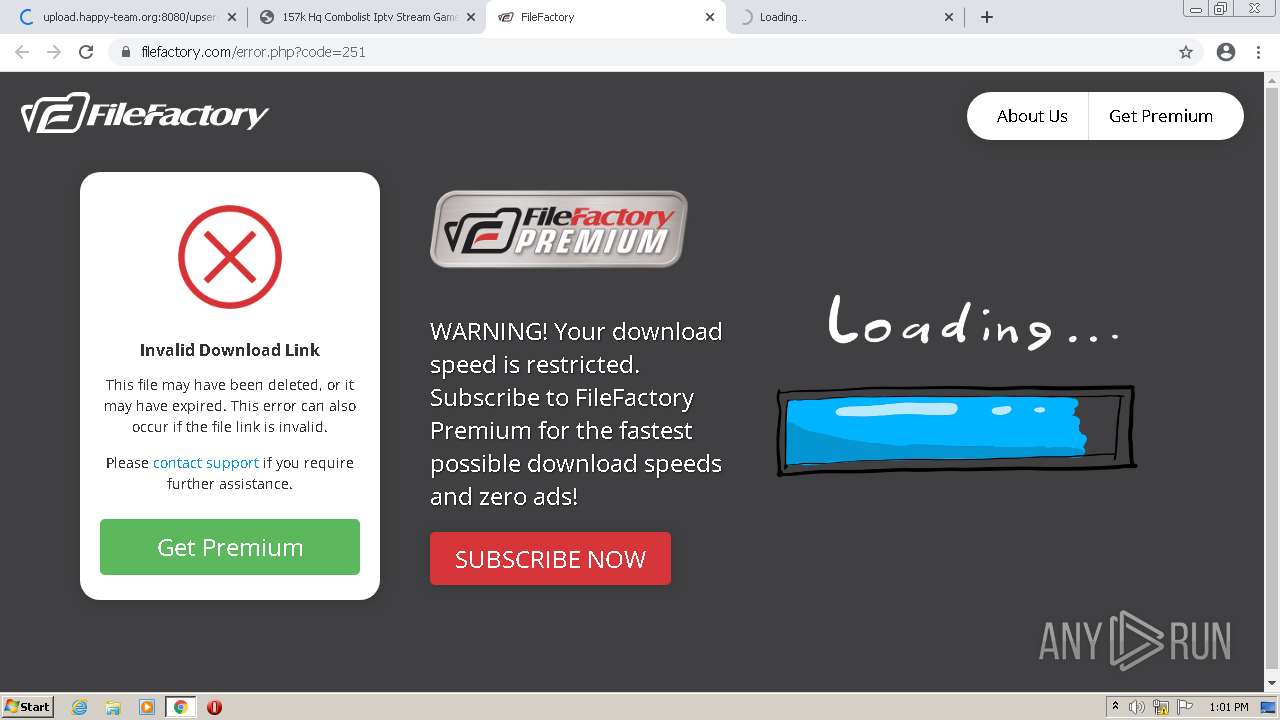
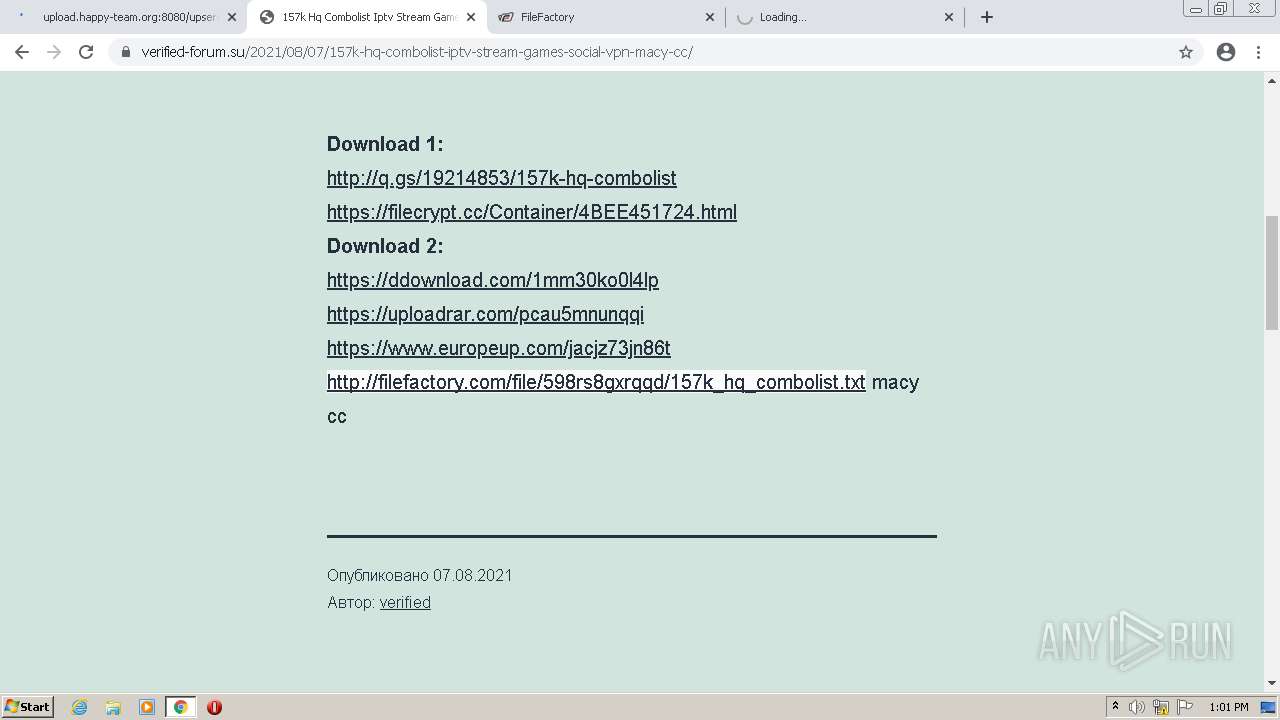
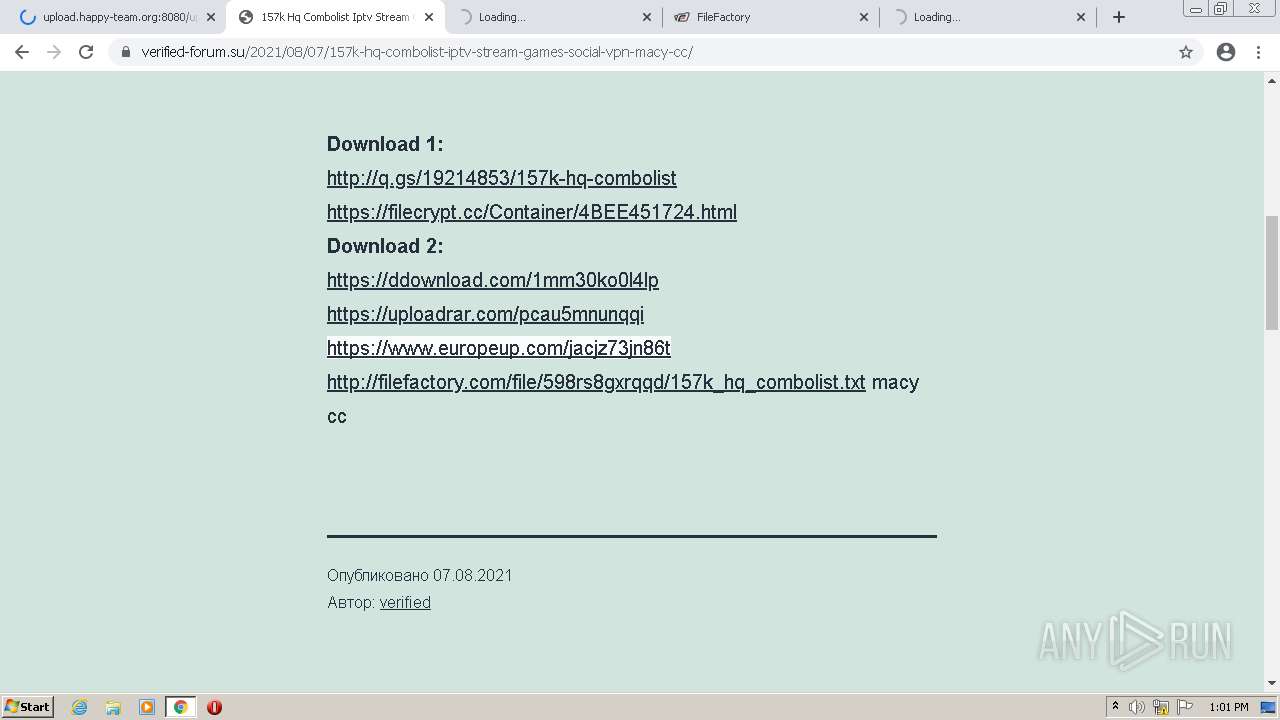
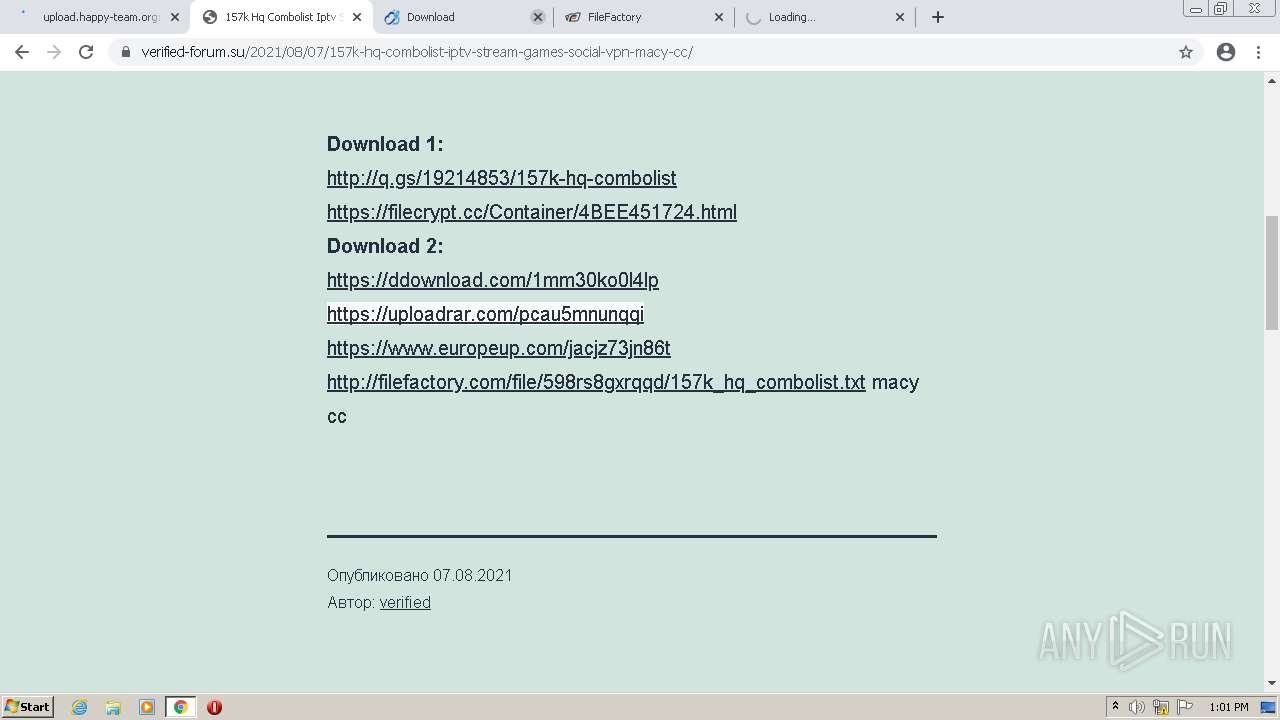
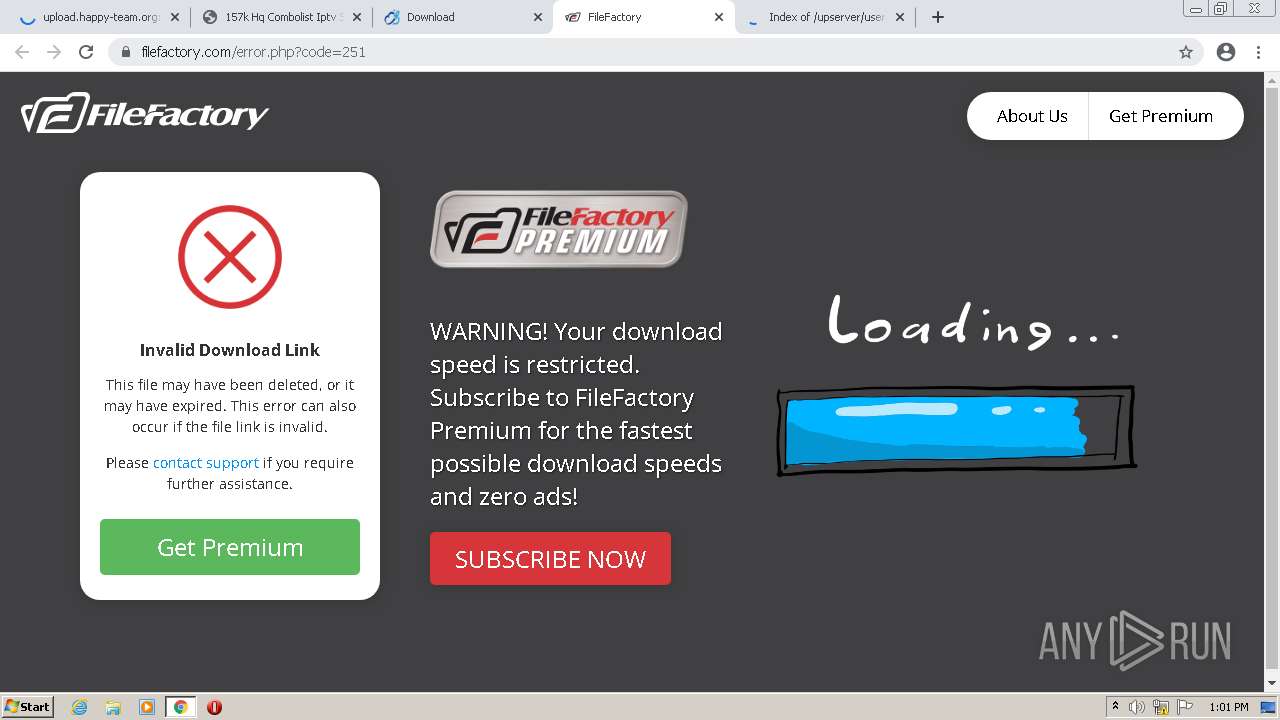
— | — | GET | 301 | 104.21.84.133:80 | http://q.gs/19214853/157k-hq-combolist | US | — | — | suspicious |
3748 | chrome.exe | GET | 200 | 172.67.151.162:80 | http://cdn.xervoo.net/static/js/view117_bidshow.js | US | compressed | 3.93 Kb | suspicious |
3748 | chrome.exe | GET | 200 | 172.67.151.162:80 | http://cdn.xervoo.net/static/js/amvn.js | US | compressed | 81.0 Kb | suspicious |
3748 | chrome.exe | GET | 200 | 104.21.12.44:80 | http://xervoo.net/rweasy/-20EAUN/19214853/157k-hq-combolist?rndad=3116823491-1644843422 | US | html | 5.25 Kb | suspicious |
3748 | chrome.exe | GET | 200 | 178.199.232.193:8080 | http://upload.happy-team.org:8080/upserver/user_uploads/freehacxxb3ed/435k_extremely_hq_mail-pass_combo.txt | CH | text | 6.22 Mb | suspicious |
3748 | chrome.exe | GET | 200 | 172.67.151.162:80 | http://cdn.xervoo.net/static/js/main.js | US | compressed | 667 b | suspicious |
3748 | chrome.exe | GET | 200 | 172.67.151.162:80 | http://cdn.xervoo.net/static/image/logo_fb2.png | US | image | 6.14 Kb | suspicious |
3748 | chrome.exe | GET | 200 | 172.67.151.162:80 | http://cdn.xervoo.net/static/image/ad_top_bg2.png?&ad_box_=1 | US | image | 156 b | suspicious |
3748 | chrome.exe | GET | 200 | 172.67.151.162:80 | http://cdn.xervoo.net/static/image/ahl6532.gif | US | image | 3.15 Kb | suspicious |
3748 | chrome.exe | GET | 200 | 104.21.12.44:80 | http://xervoo.net/js/display.js | US | compressed | 5.64 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3748 | chrome.exe | 142.250.185.142:443 | clients2.google.com | Google Inc. | US | whitelisted |
3748 | chrome.exe | 178.199.232.193:8080 | upload.happy-team.org | Swisscom (Switzerland) Ltd | CH | suspicious |
3748 | chrome.exe | 142.250.186.100:443 | www.google.com | Google Inc. | US | whitelisted |
3748 | chrome.exe | 172.217.23.109:443 | accounts.google.com | Google Inc. | US | suspicious |
3748 | chrome.exe | 142.250.186.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
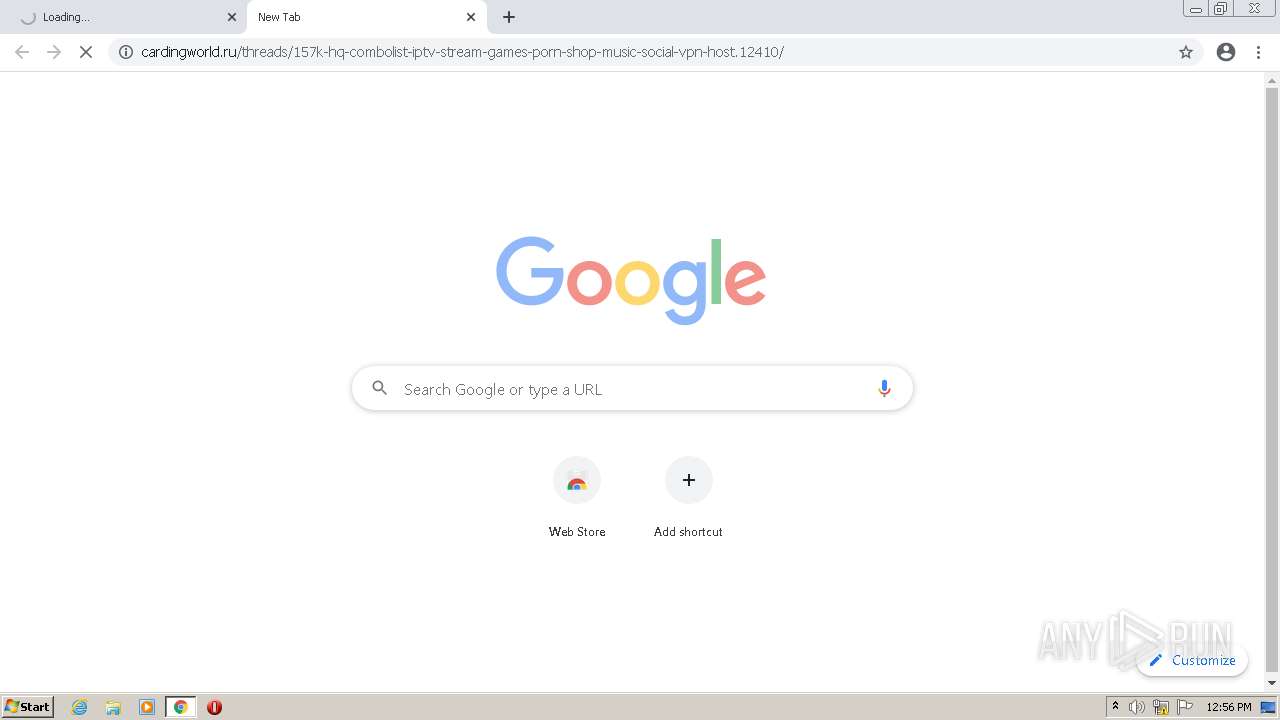
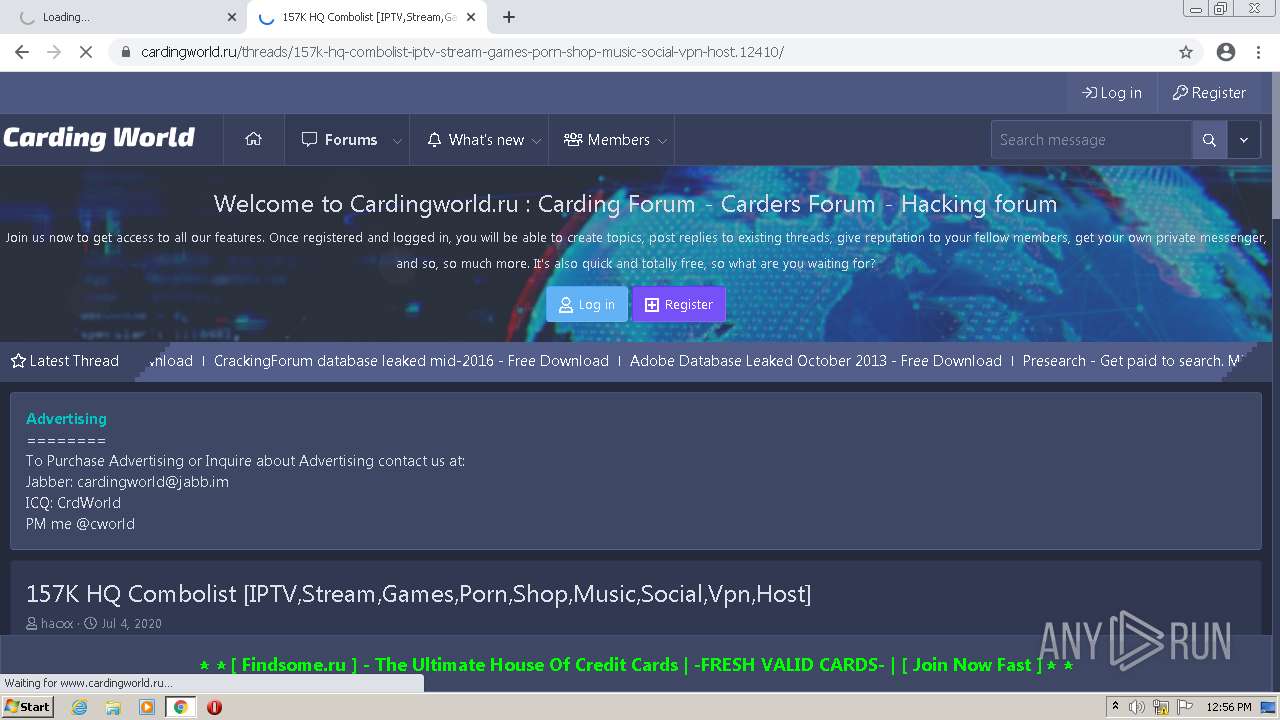
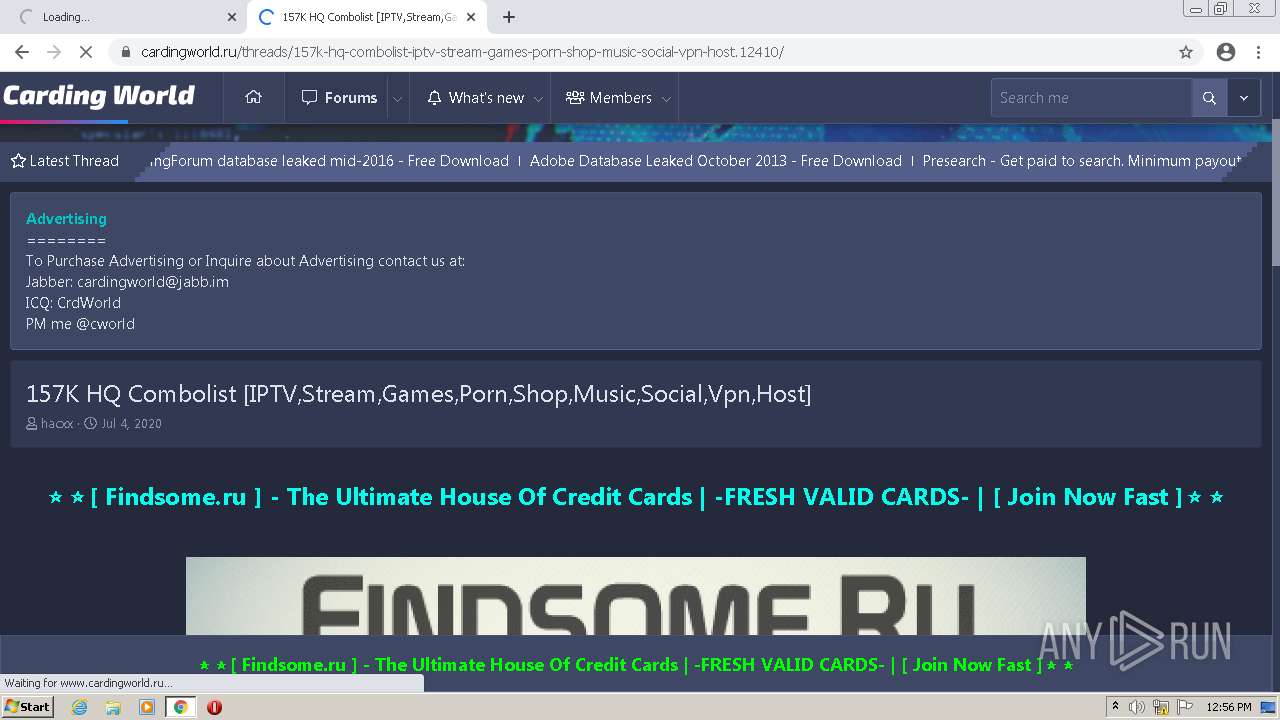
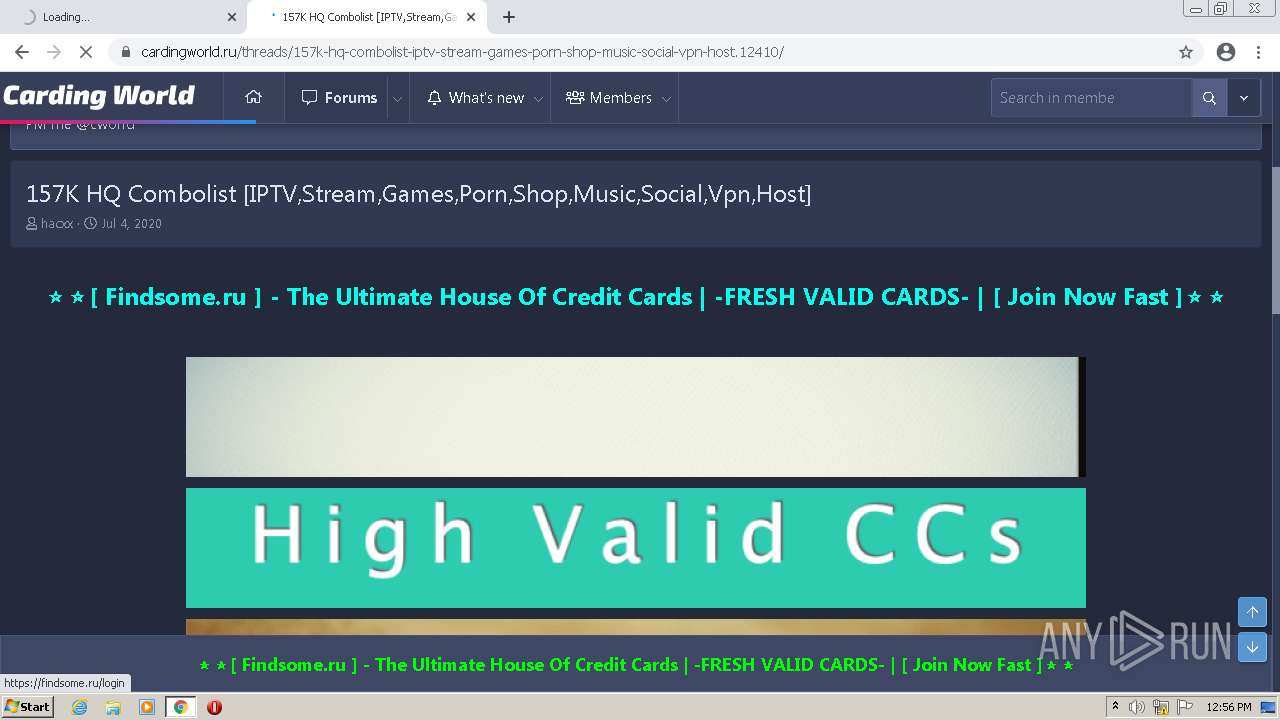
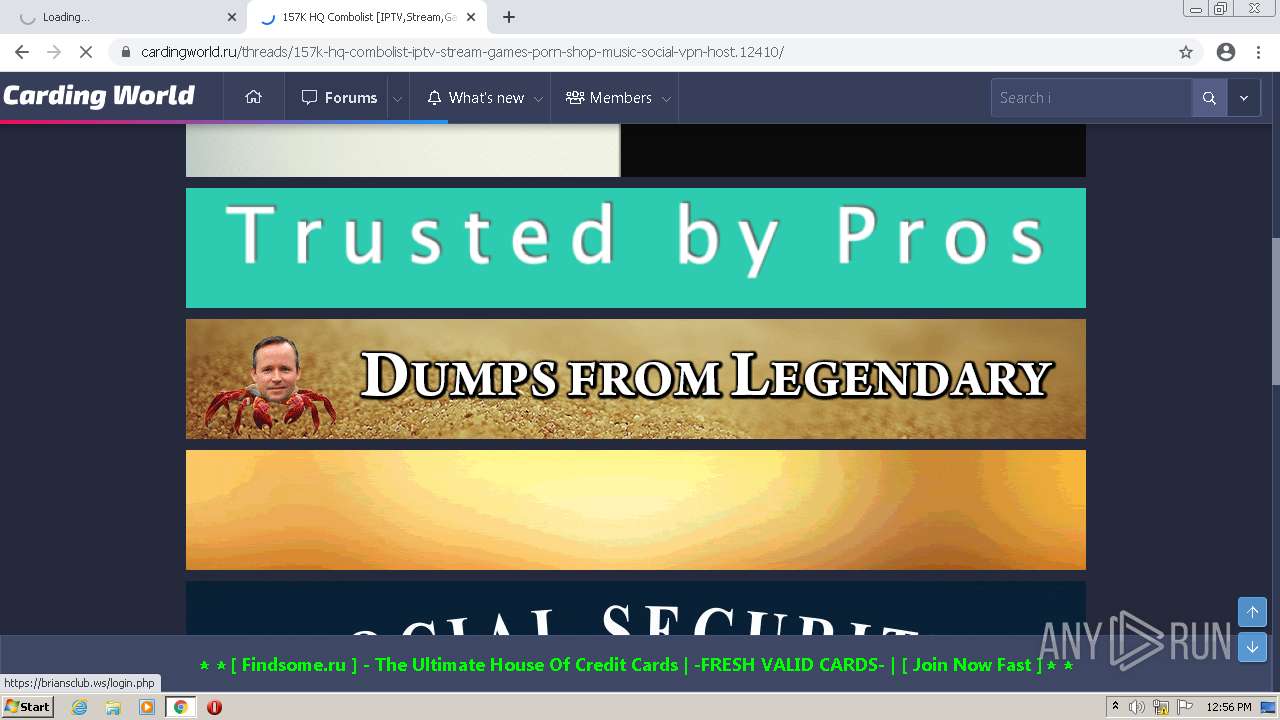
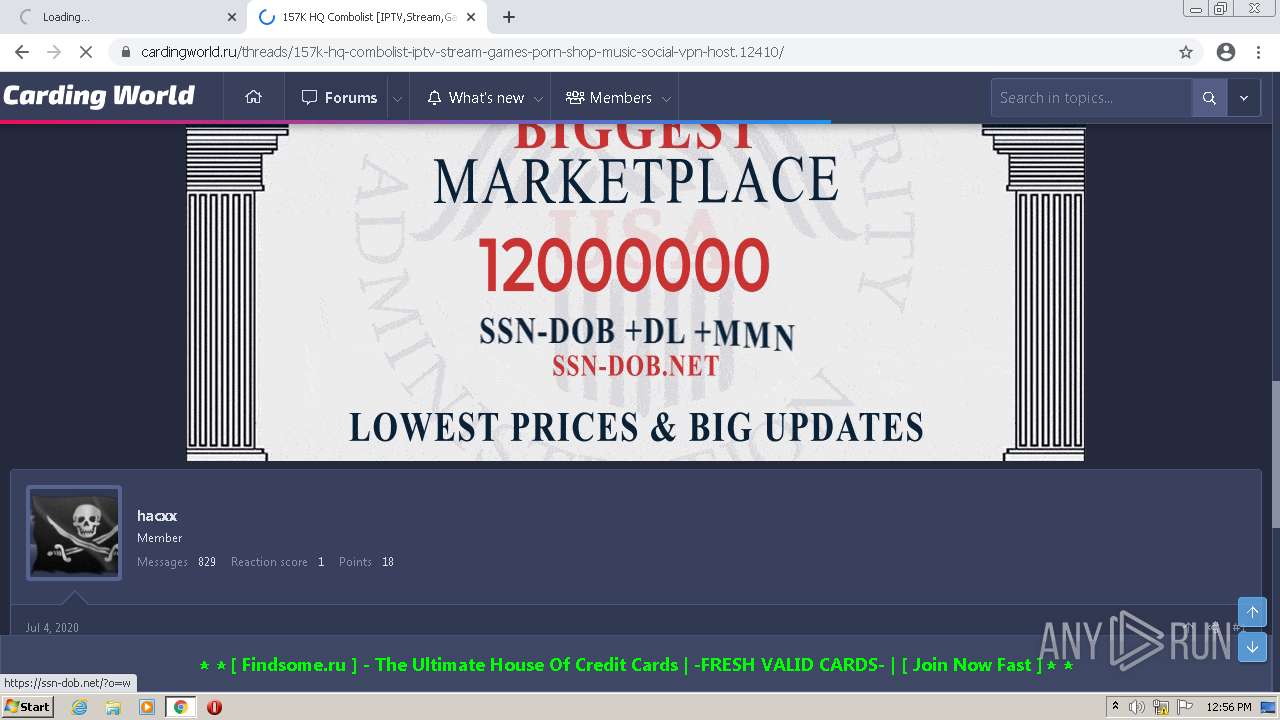
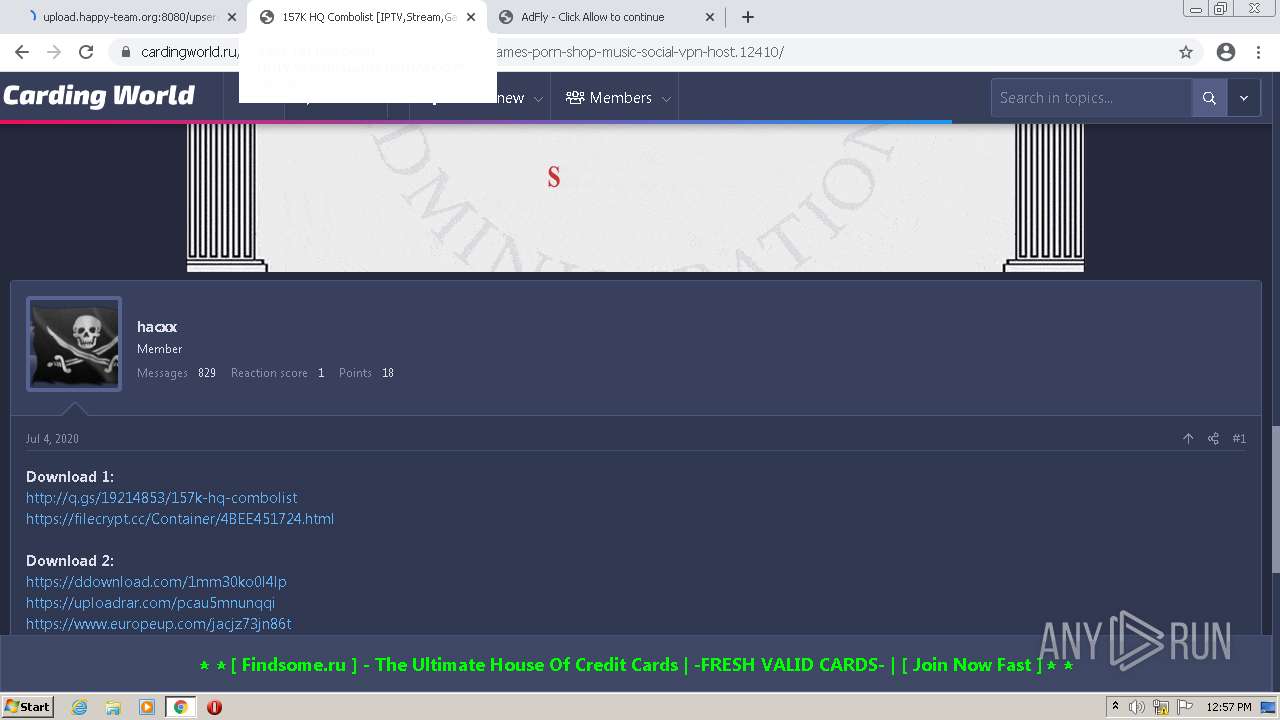
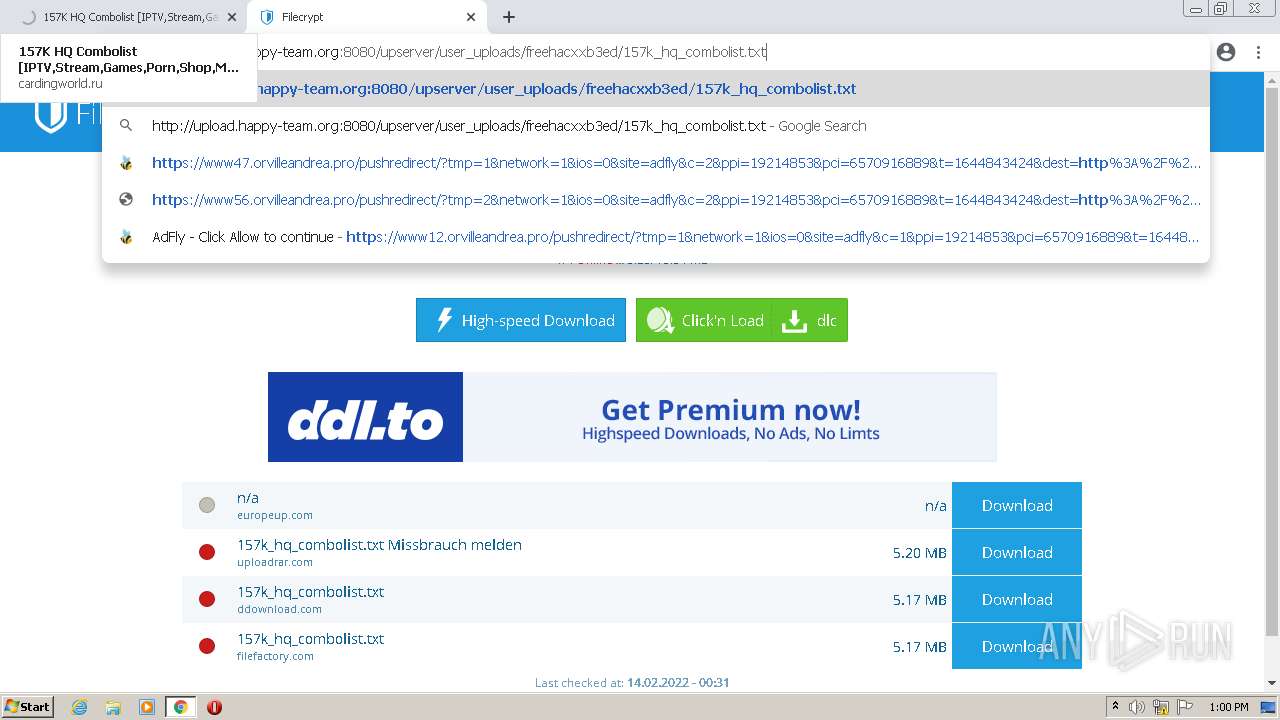
3748 | chrome.exe | 188.114.97.7:443 | www.cardingworld.ru | Cloudflare Inc | US | malicious |
3748 | chrome.exe | 2.16.106.163:80 | ctldl.windowsupdate.com | Akamai International B.V. | — | whitelisted |
3748 | chrome.exe | 142.250.186.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3748 | chrome.exe | 172.217.18.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3748 | chrome.exe | 142.250.181.238:443 | apis.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clients2.google.com |
| whitelisted |
upload.happy-team.org |
| suspicious |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
www.cardingworld.ru |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3748 | chrome.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
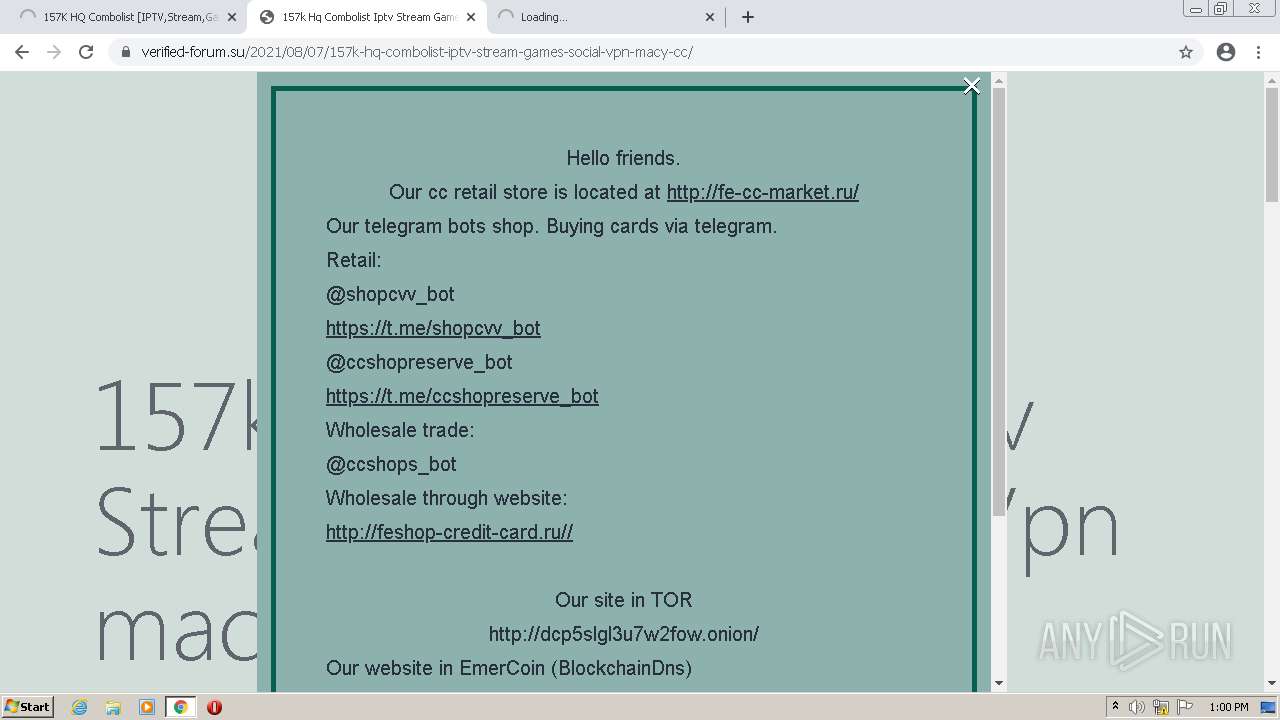
— | — | Potentially Bad Traffic | ET DNS Query for .cc TLD |
3748 | chrome.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
3748 | chrome.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
3748 | chrome.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
— | — | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
3748 | chrome.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
3748 | chrome.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |