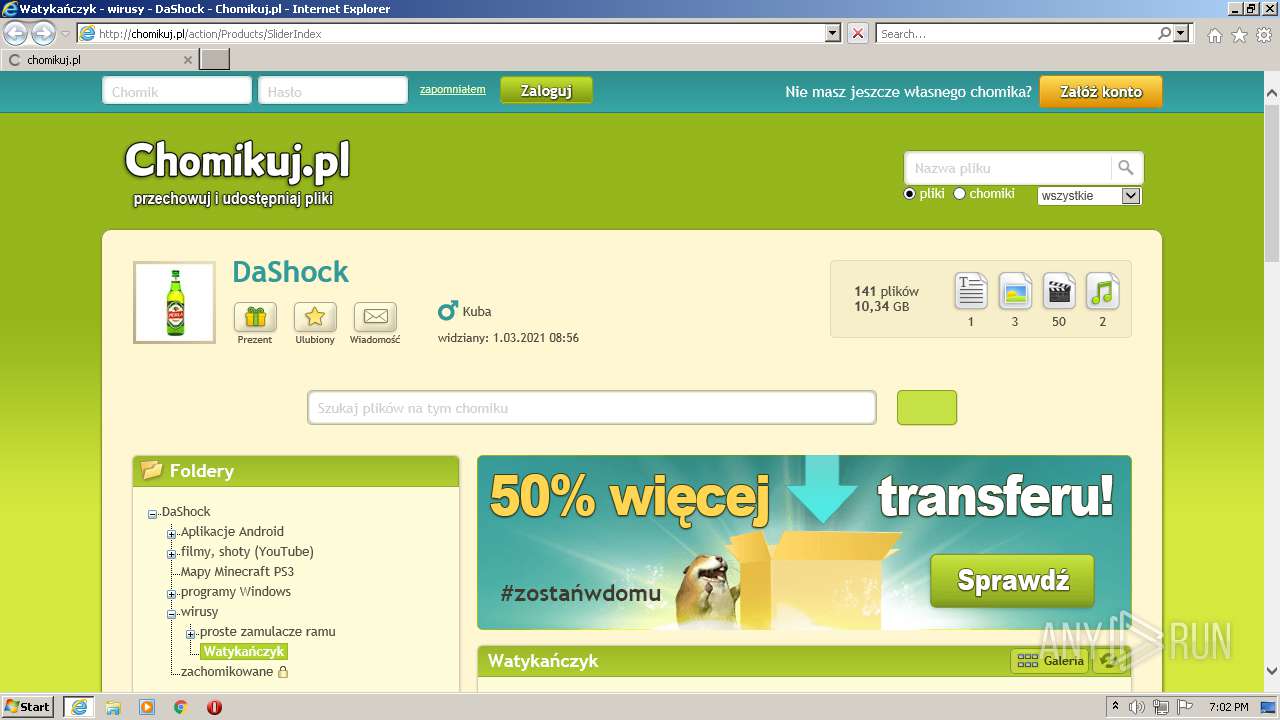
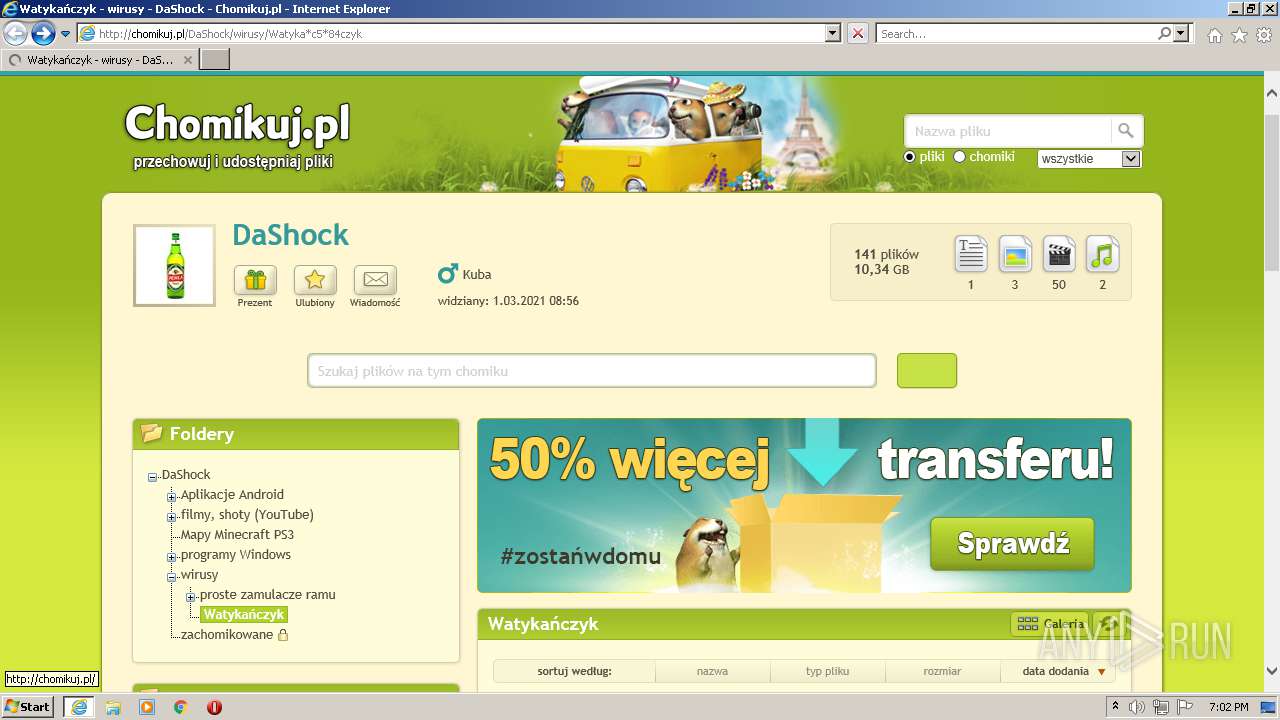
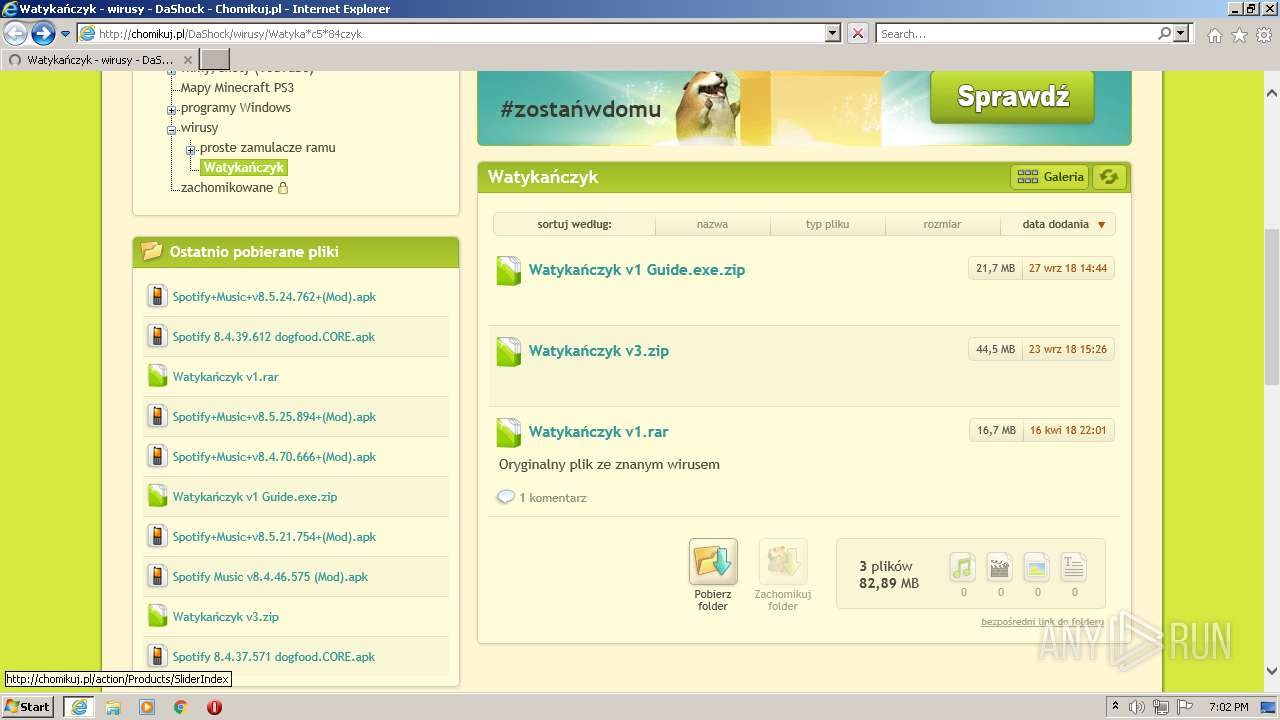
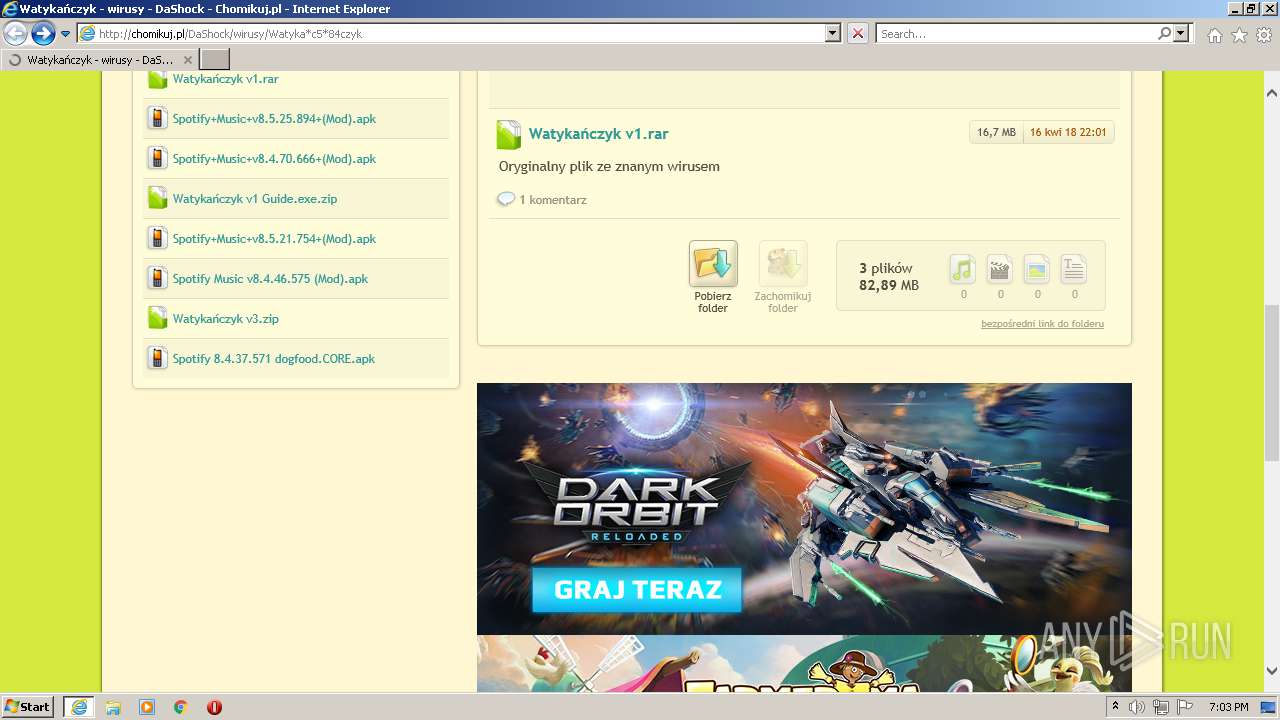
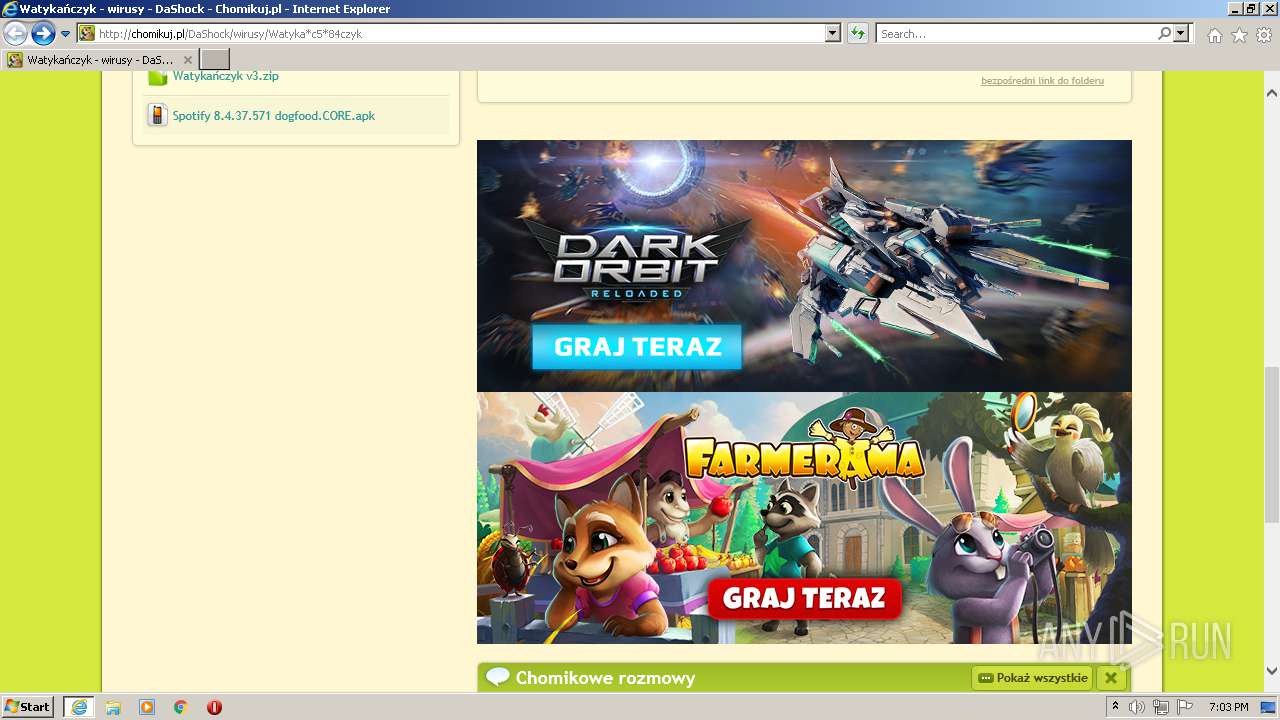
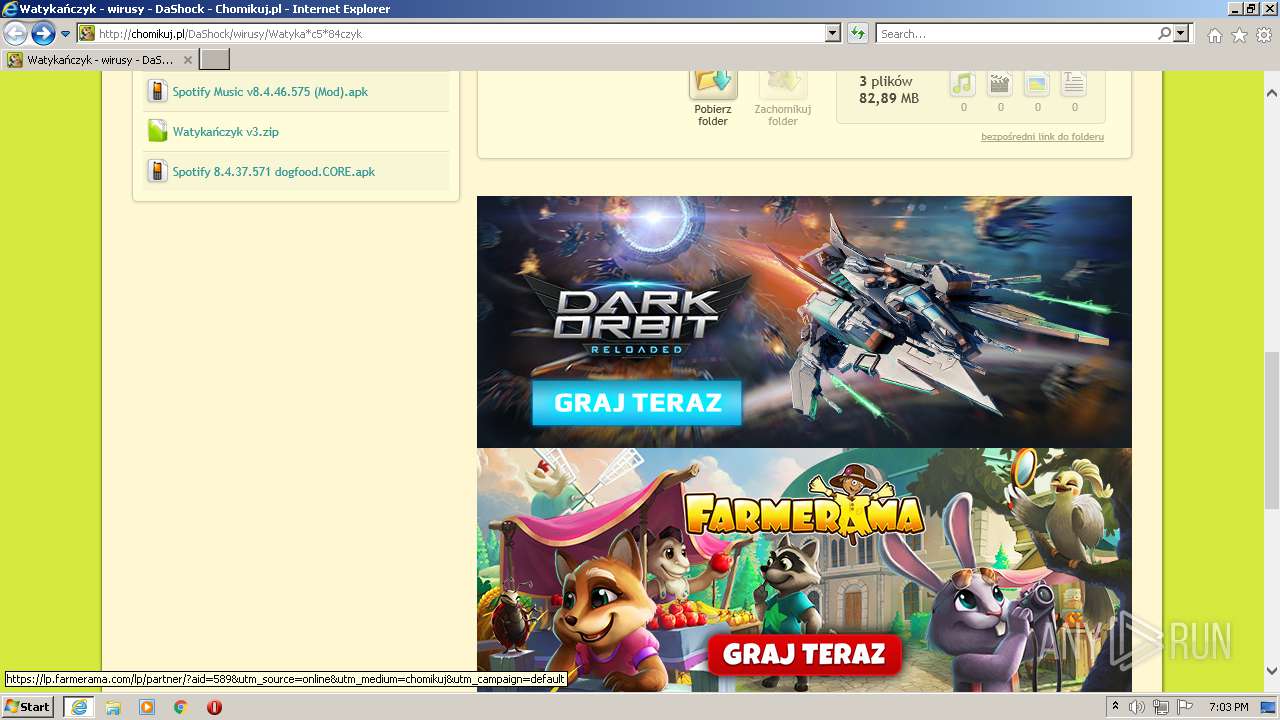
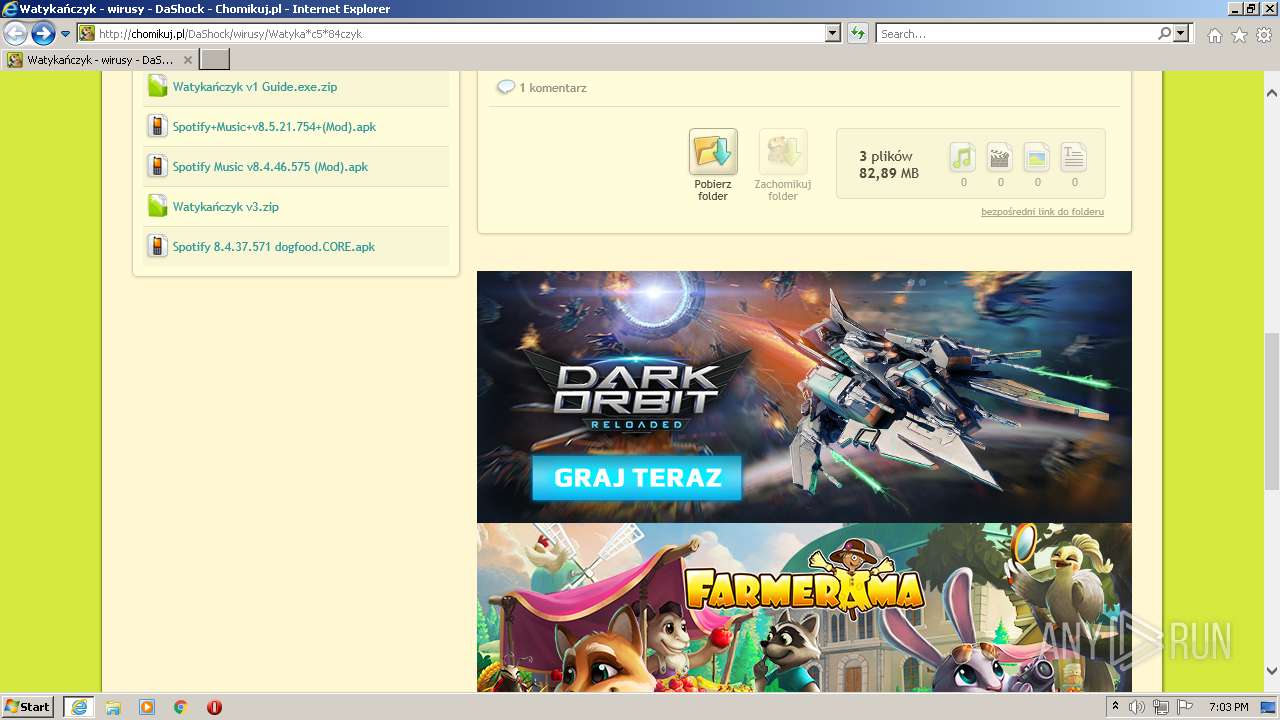
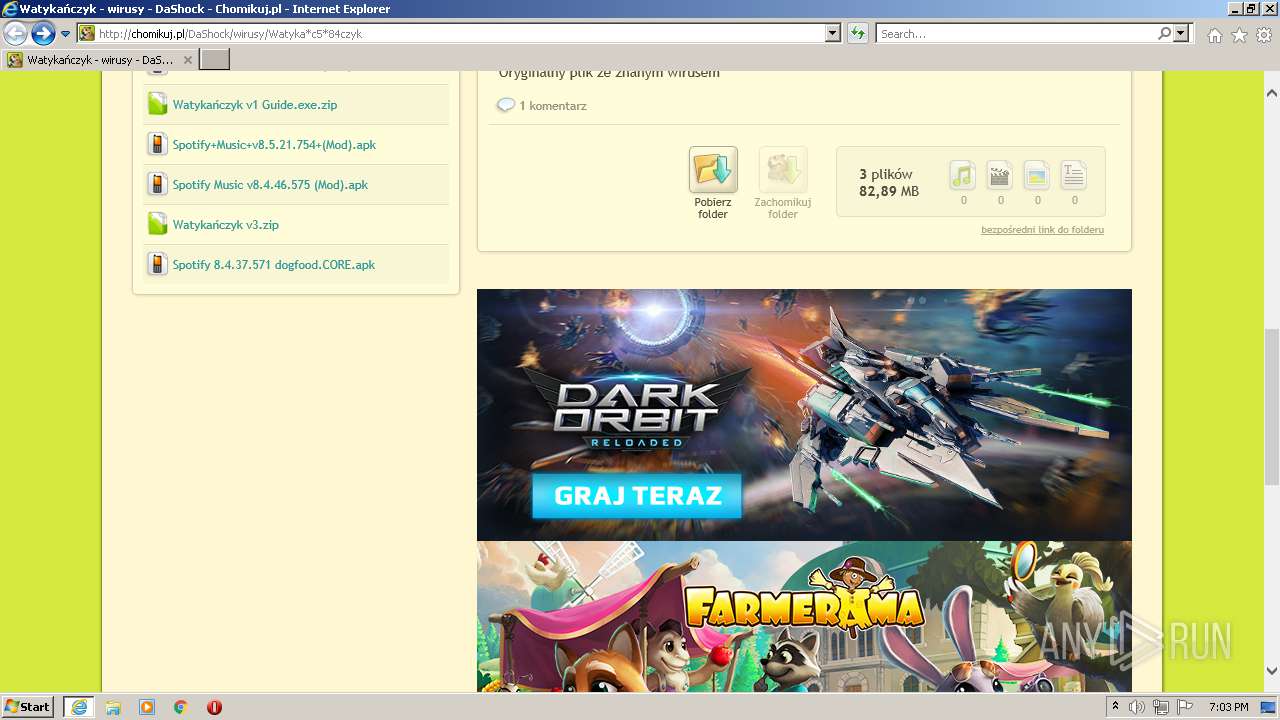
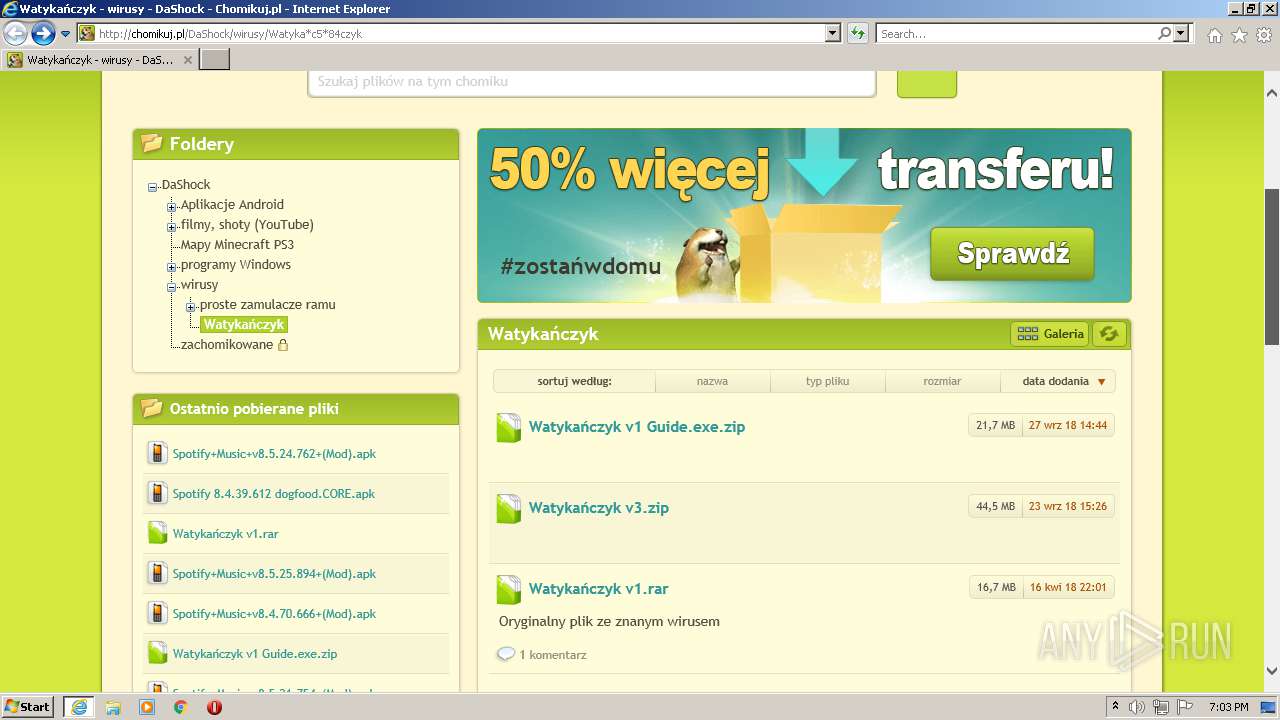
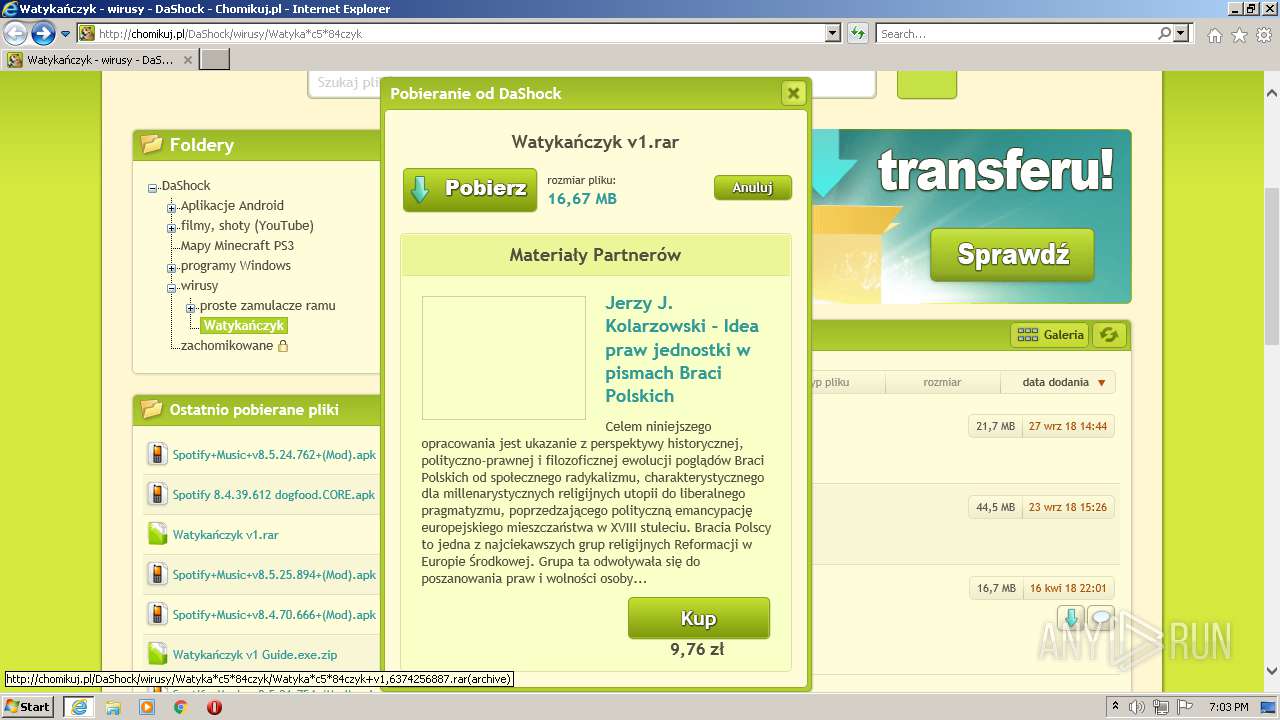
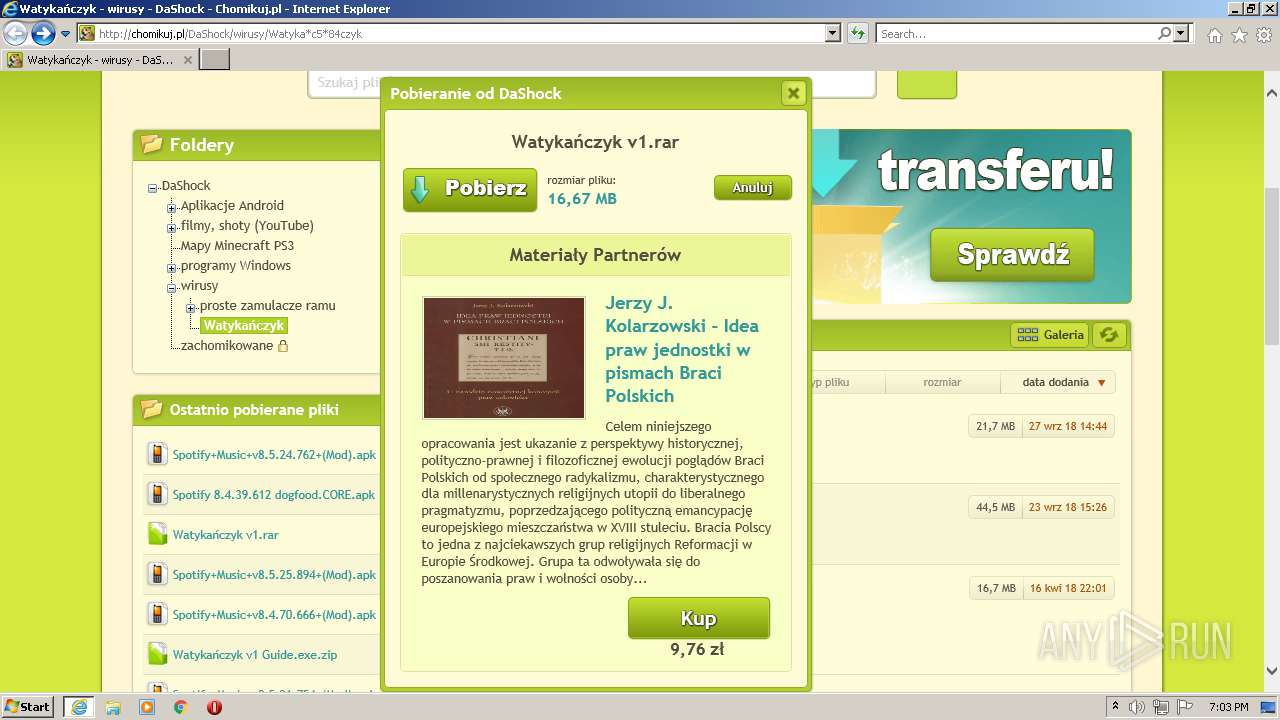
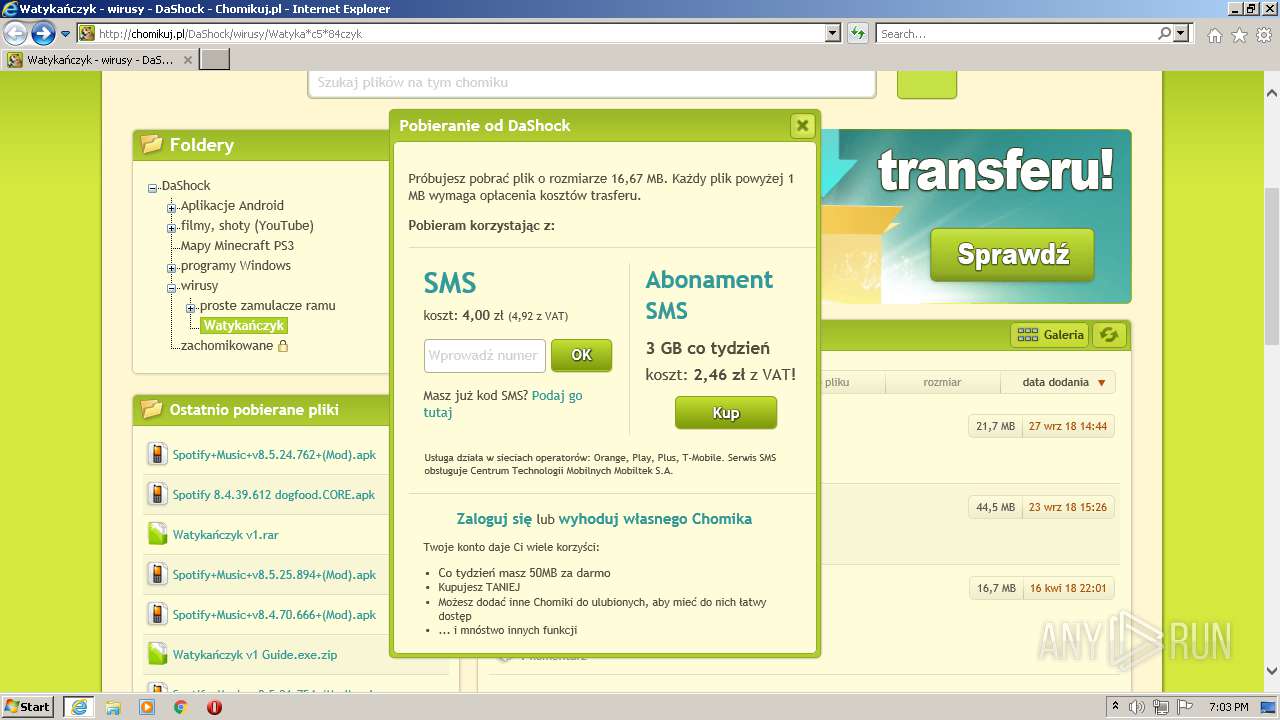
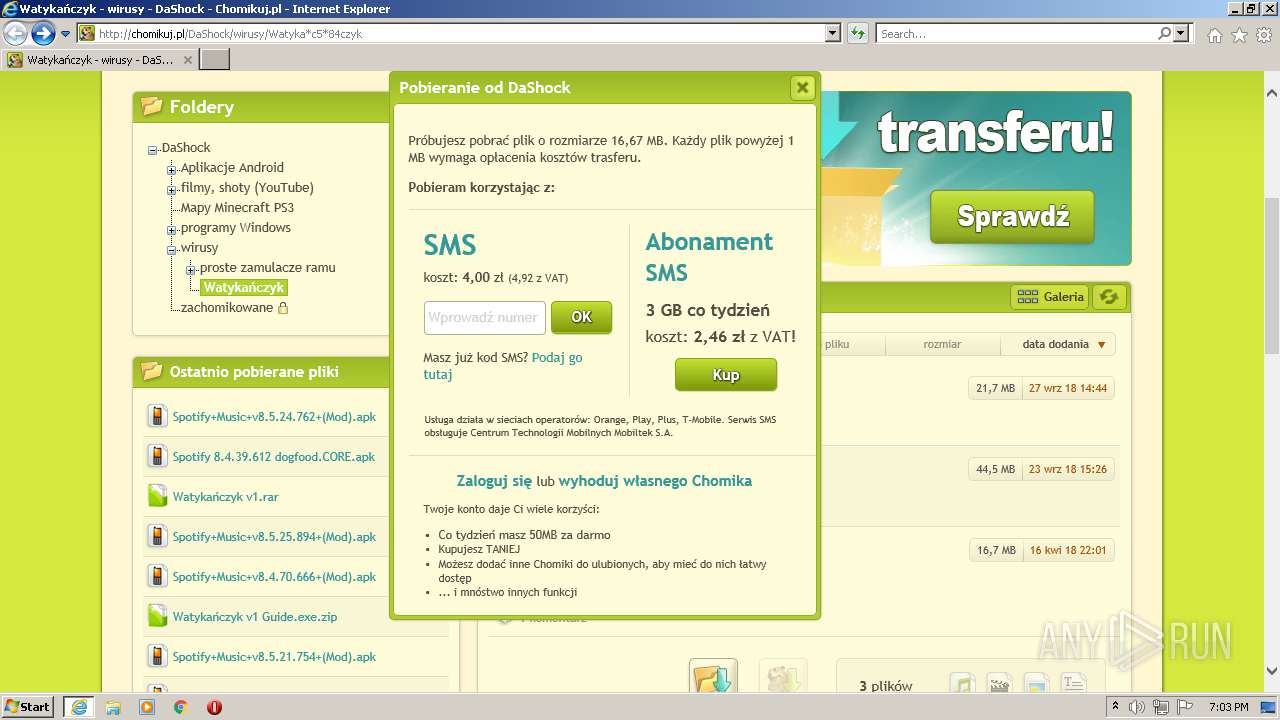
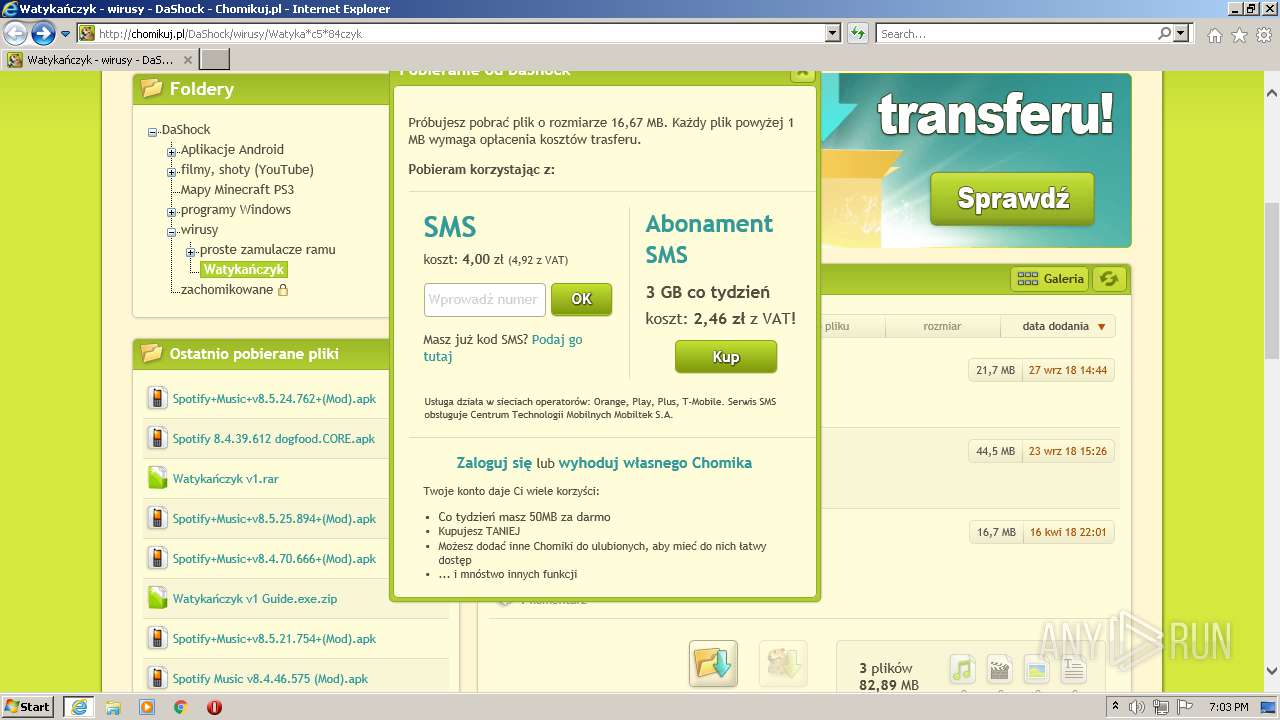
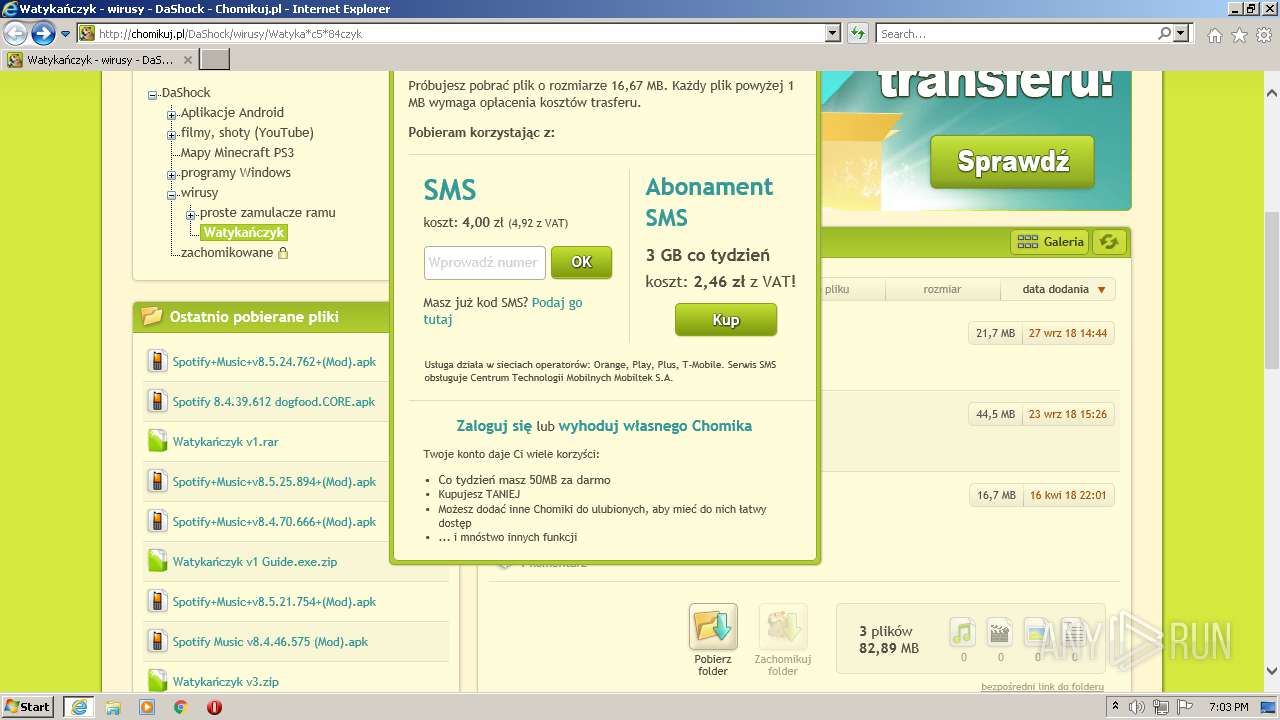
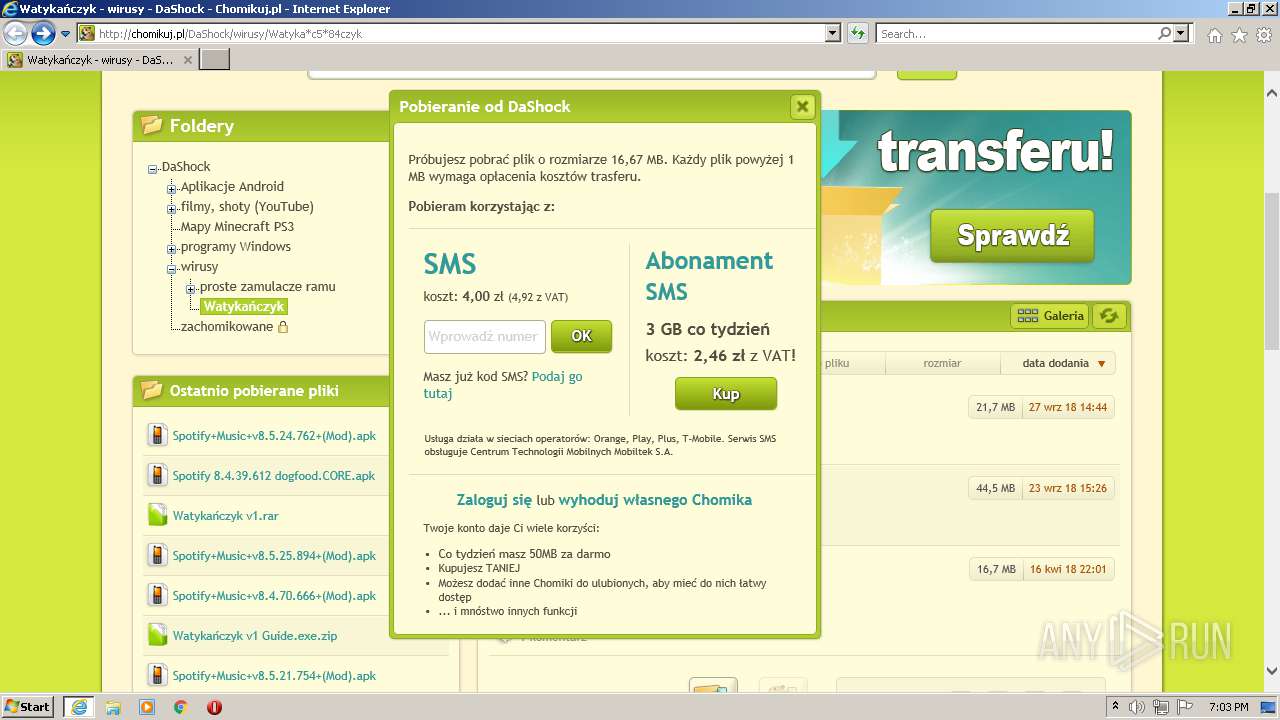
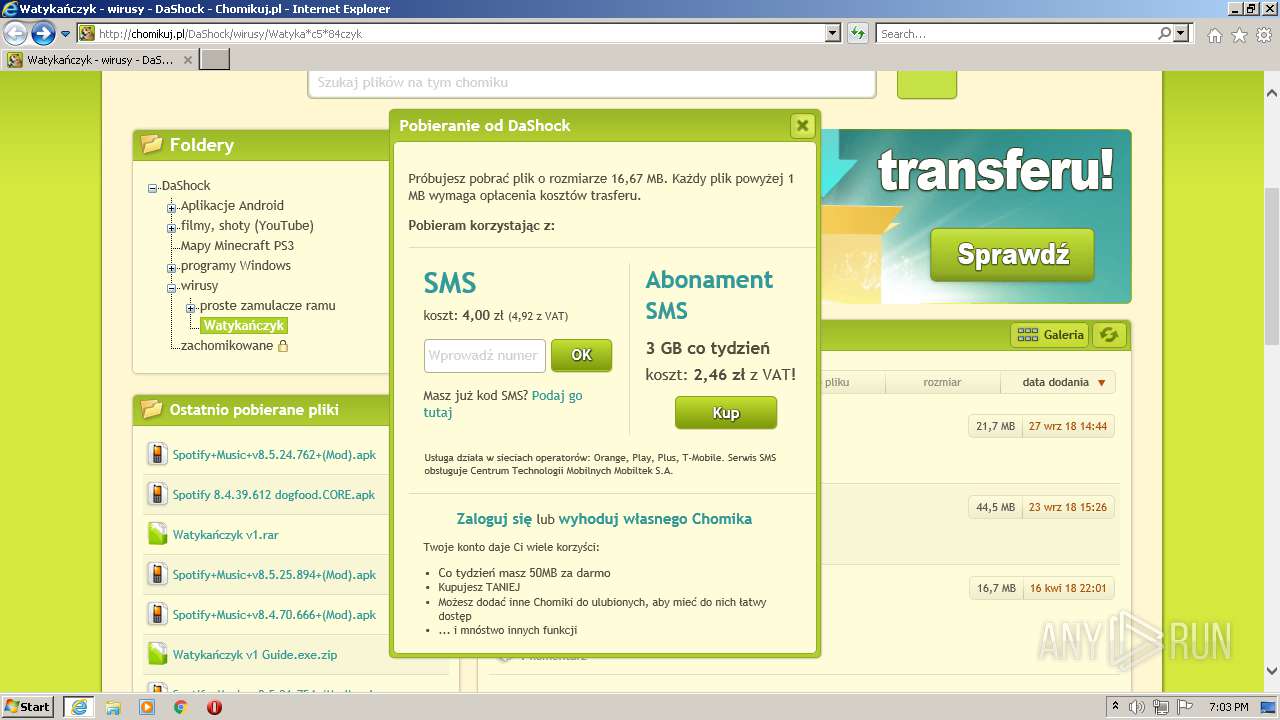
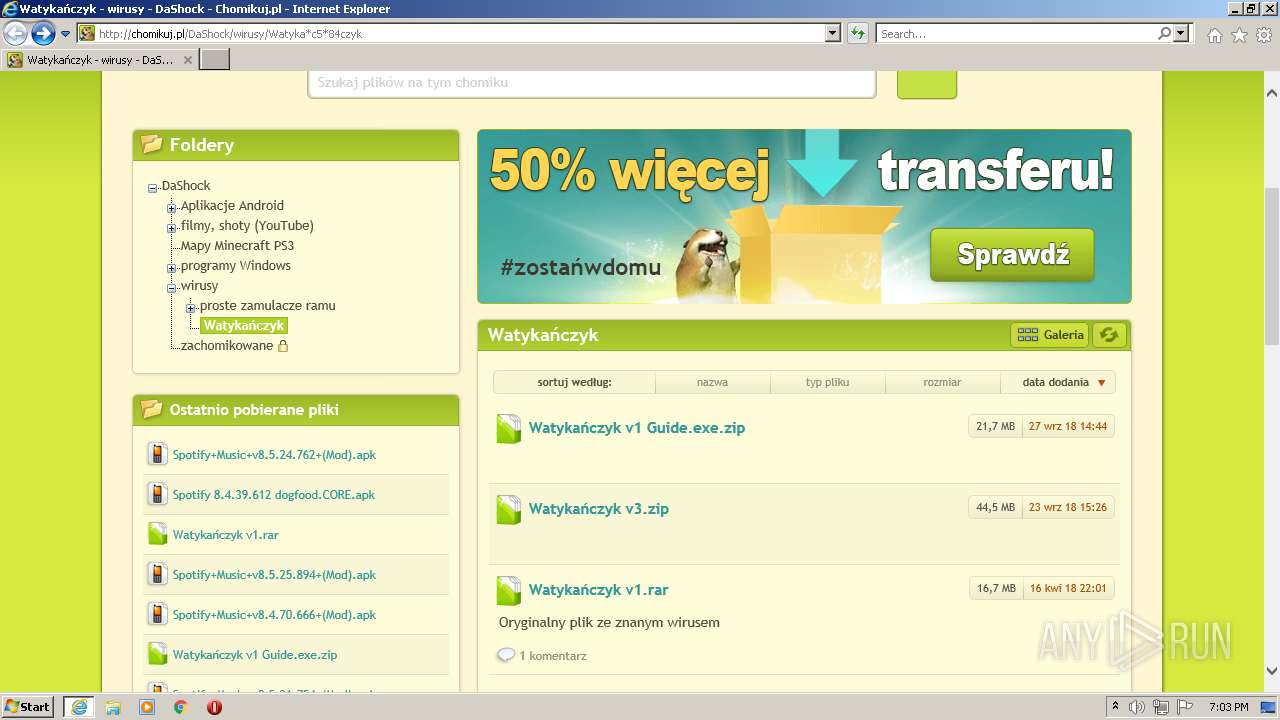
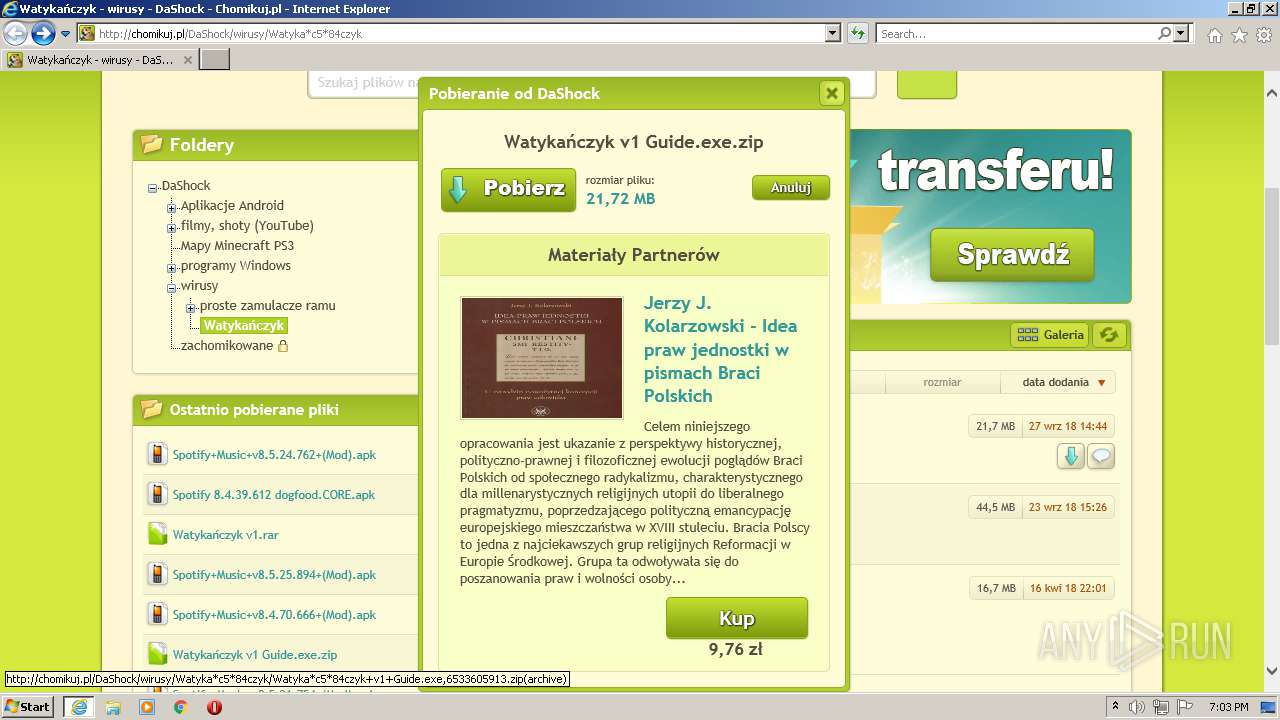
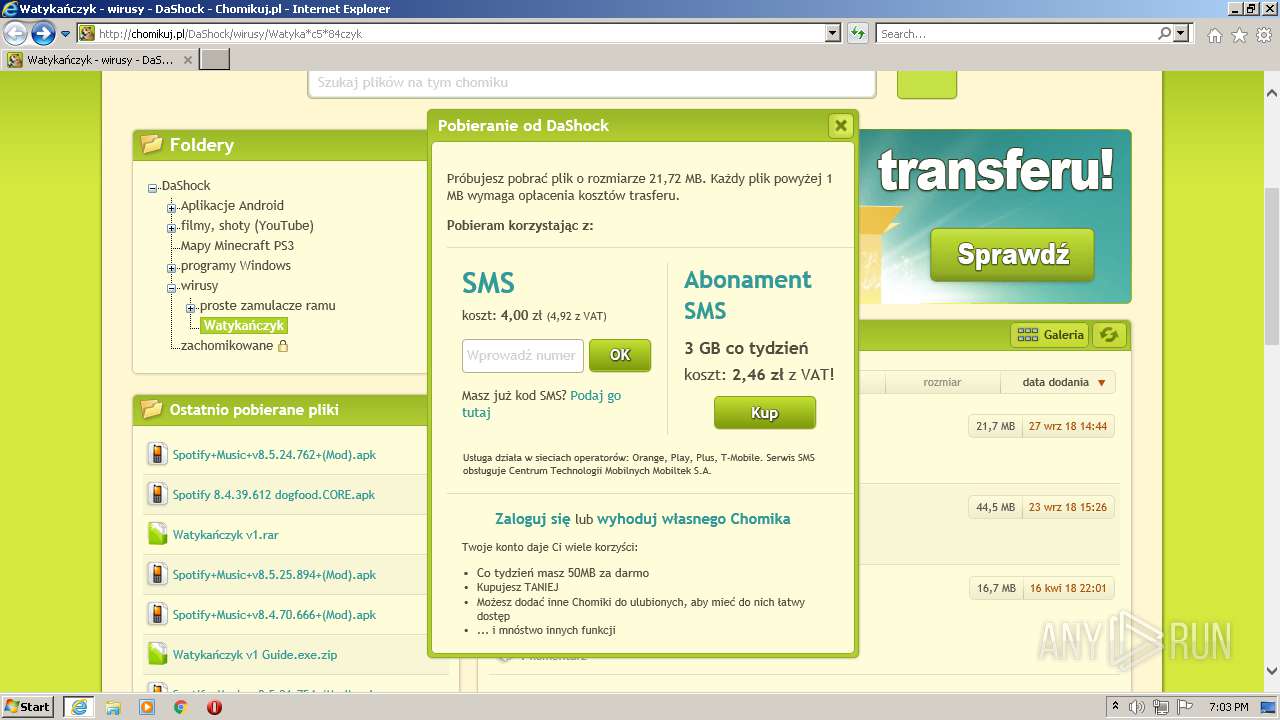
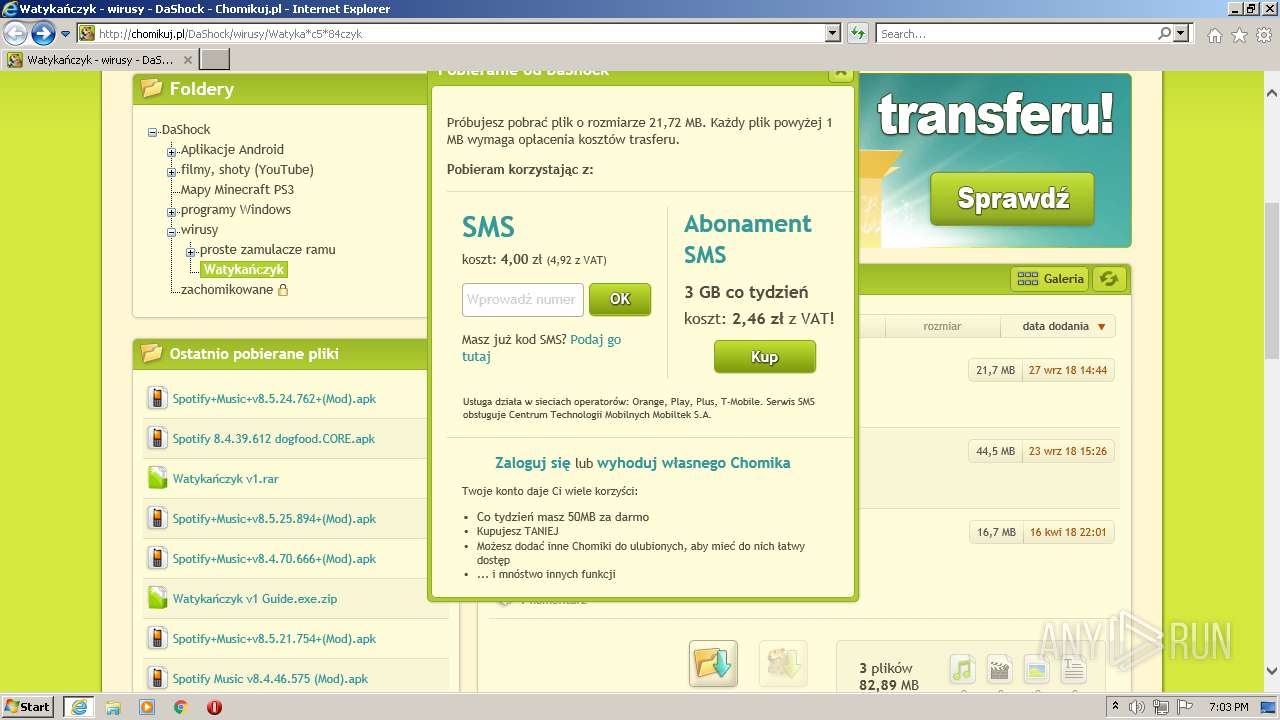
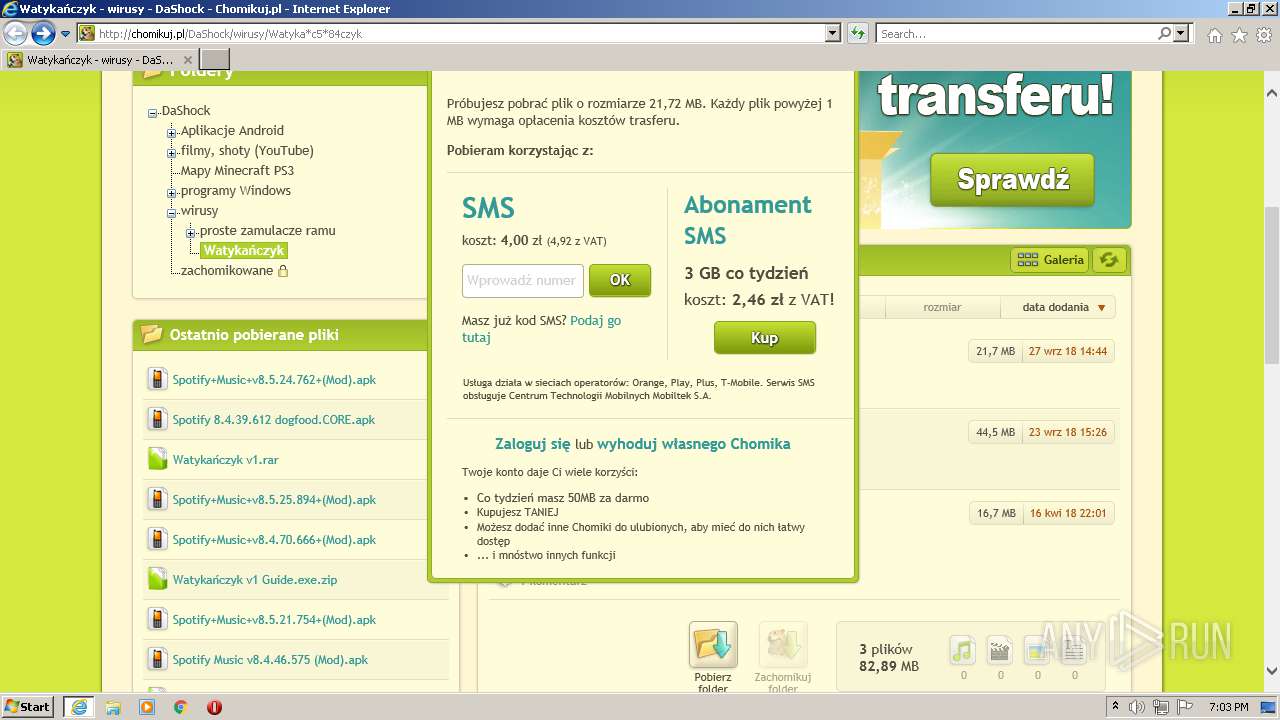
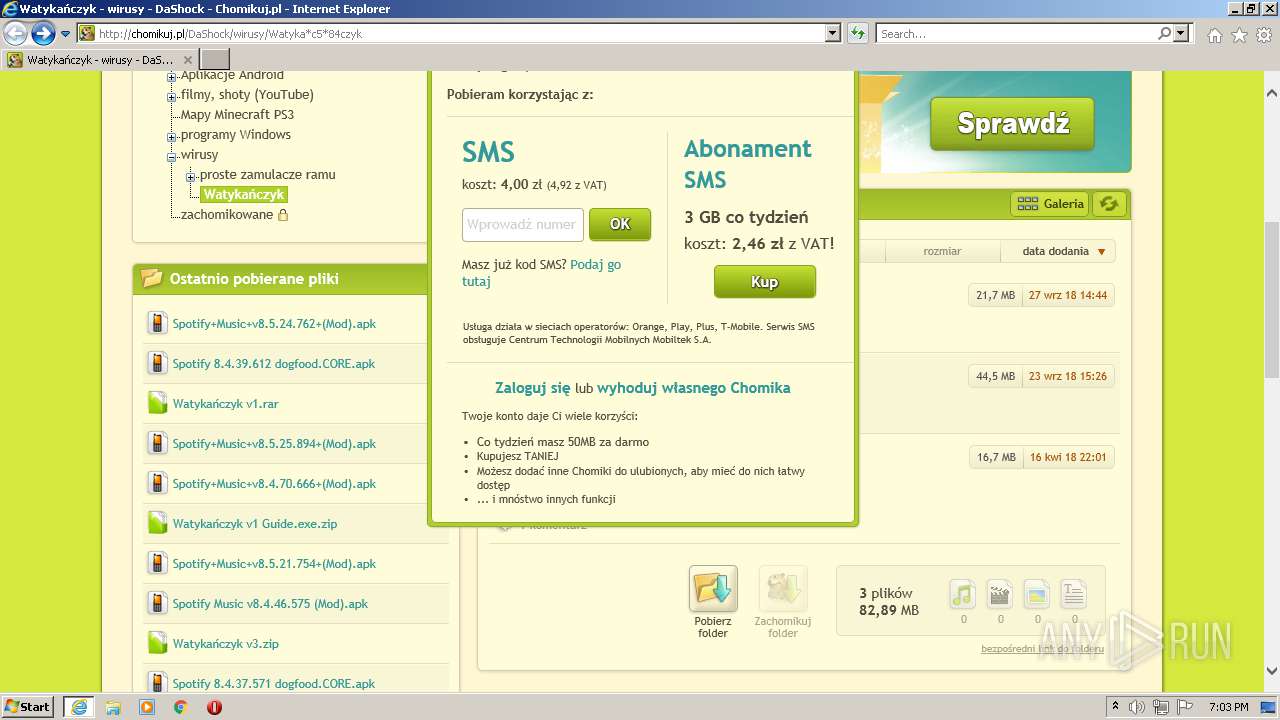
| URL: | http://chomikuj.pl/DaShock/wirusy/Watyka*c5*84czyk |
| Full analysis: | https://app.any.run/tasks/7bae83c2-2623-4c3b-a11f-57e184b10385 |
| Verdict: | Malicious activity |
| Analysis date: | May 22, 2021, 18:02:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | CF83E179B9911BFE236014D800397E77 |
| SHA1: | 97DB68F2C8A2D8AA69594AD70A94C7D90339D2FB |
| SHA256: | 422F7E117C21B4739FFA869A1D405EF102BEA21419F22E2B550A0EF3ACF8BF4B |
| SSDEEP: | 3:N1KdNKtzVJK3mWQbpR4n:CcXCmWQbpR4n |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 4028)
Reads the computer name
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 2020)
Creates files in the user directory
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 2020)
Checks supported languages
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 2020)
Executed via COM
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 2020)
INFO
Checks supported languages
- iexplore.exe (PID: 1984)
- iexplore.exe (PID: 4028)
Changes internet zones settings
- iexplore.exe (PID: 1984)
Reads the computer name
- iexplore.exe (PID: 1984)
- iexplore.exe (PID: 4028)
Application launched itself
- iexplore.exe (PID: 1984)
Creates files in the user directory
- iexplore.exe (PID: 4028)
- iexplore.exe (PID: 1984)
Checks Windows Trust Settings
- iexplore.exe (PID: 4028)
- iexplore.exe (PID: 1984)
Reads settings of System Certificates
- iexplore.exe (PID: 4028)
- iexplore.exe (PID: 1984)
Reads internet explorer settings
- iexplore.exe (PID: 4028)
Reads CPU info
- iexplore.exe (PID: 4028)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
37
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1984 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://chomikuj.pl/DaShock/wirusy/Watyka*c5*84czyk" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2020 | C:\Windows\system32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Integrity Level: MEDIUM Description: Adobe� Flash� Player Installer/Uninstaller 32.0 r0 Exit code: 0 Version: 32,0,0,453 Modules
| |||||||||||||||
| 4028 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1984 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
24 943
Read events
24 746
Write events
197
Delete events
0
Modification events
| (PID) Process: | (1984) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (1984) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (1984) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30887732 | |||
| (PID) Process: | (1984) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (1984) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30887732 | |||
| (PID) Process: | (1984) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1984) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1984) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1984) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1984) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
27
Text files
225
Unknown types
34
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4028 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\WCZ7U9HG.txt | text | |
MD5:— | SHA256:— | |||
| 4028 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\7GMBTRY9.txt | text | |
MD5:— | SHA256:— | |||
| 4028 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\877bbd1b6e[1].css | text | |
MD5:— | SHA256:— | |||
| 4028 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\Watyka_c5_84czyk[1].htm | html | |
MD5:— | SHA256:— | |||
| 4028 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\7594286262,75x75,PL[1].jpg | image | |
MD5:— | SHA256:— | |||
| 4028 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\fa469fce2f[1].css | text | |
MD5:FA469FCE2F97863C7A3AC538C28E428A | SHA256:396774AE0EC80A8C72115F414938330D849355FA95D32D766141828CCB314F9E | |||
| 4028 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\friend_profile,PL[1].jpg | image | |
MD5:597F99EE3A5F945B0B50E83C49D93E04 | SHA256:8F16C8FC1E370AC2B165850B6C33DDA0B11DF376629A8C1B51C350549C9C0481 | |||
| 4028 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\bf0a4be460[1].css | text | |
MD5:BF0A4BE46078F1743A82C30466A37BFA | SHA256:18BD3E06B0A356A4BA0C77DA0FD5FDA87C893003B6A7438E3EC762D571383305 | |||
| 4028 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\0ba441af03[1].css | text | |
MD5:0BA441AF032D5EF63E242CAE7EE8394A | SHA256:A2E26D3D58729CAD05DD5E23DD25657E375F8807AEE2876F6DCDDAB10AED3180 | |||
| 4028 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\d3705ebd1d[1].css | text | |
MD5:D3705EBD1D883C26086190DFFAF18D42 | SHA256:B9AAFA4A7EB7C5CA6E9978C145FA0A1F245B287B70F28FF2EA82FB0E579CDB39 | |||
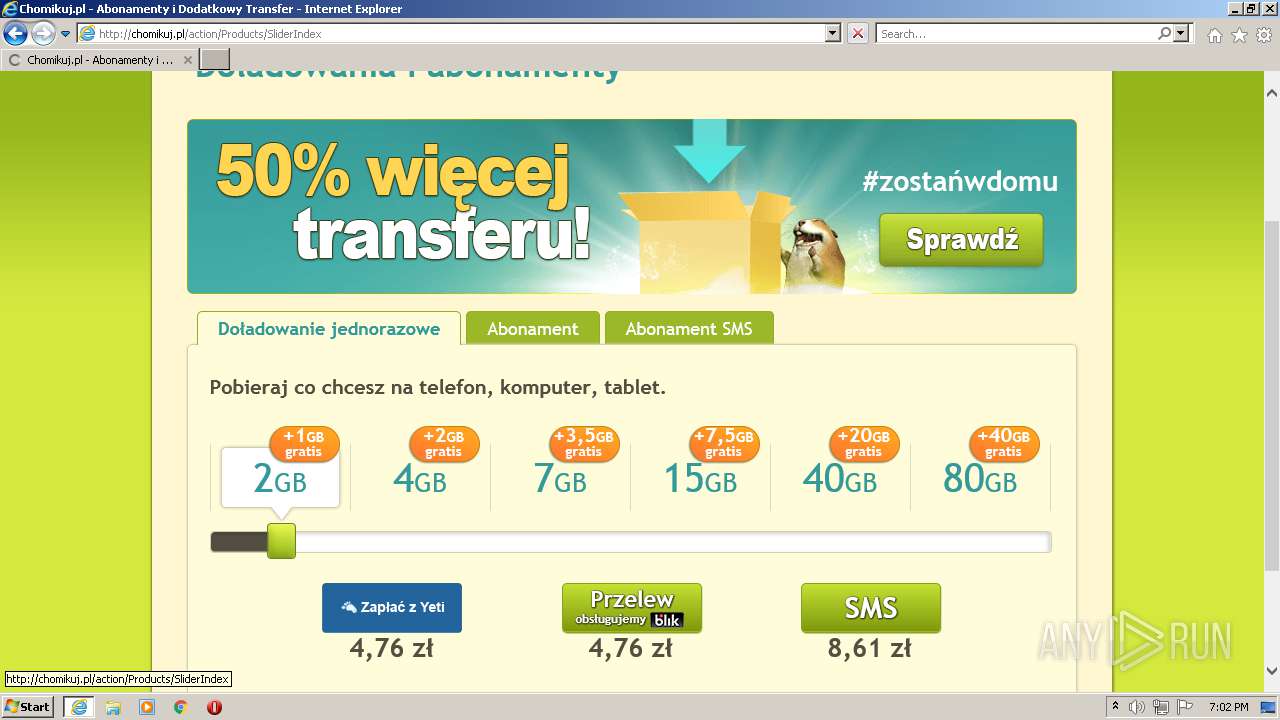
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
200
TCP/UDP connections
113
DNS requests
43
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4028 | iexplore.exe | GET | 200 | 185.11.128.206:80 | http://pro.hit.gemius.pl/gstream.js | PL | text | 7.85 Kb | whitelisted |
4028 | iexplore.exe | GET | 200 | 172.67.160.221:80 | http://x4.static-chomikuj.pl/res/877bbd1b6e.css | US | text | 23.5 Kb | malicious |
4028 | iexplore.exe | GET | 200 | 104.21.89.144:80 | http://profile.static-chomikuj.pl/7594286262,75x75,PL.jpg | US | image | 1.60 Kb | malicious |
4028 | iexplore.exe | GET | 200 | 172.67.160.221:80 | http://x4.static-chomikuj.pl/res/cc8041919e.css | US | compressed | 2.83 Kb | malicious |
4028 | iexplore.exe | GET | 200 | 172.67.160.221:80 | http://x4.static-chomikuj.pl/res/17f7a16296.js | US | html | 278 Kb | malicious |
4028 | iexplore.exe | GET | 200 | 104.22.25.70:80 | http://chomikuj.pl/DaShock/wirusy/Watyka*c5*84czyk | US | html | 10.5 Kb | whitelisted |
4028 | iexplore.exe | GET | 200 | 172.67.160.221:80 | http://x4.static-chomikuj.pl/res/d3705ebd1d.css | US | text | 868 b | malicious |
4028 | iexplore.exe | GET | 200 | 172.67.160.221:80 | http://x4.static-chomikuj.pl/res/414bb6ae50.css | US | text | 11.4 Kb | malicious |
4028 | iexplore.exe | GET | 200 | 172.67.160.221:80 | http://x4.static-chomikuj.pl/res/bf0a4be460.css | US | text | 1.15 Kb | malicious |
4028 | iexplore.exe | GET | 200 | 172.67.160.221:80 | http://x4.static-chomikuj.pl/res/0ba441af03.css | US | text | 12.9 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4028 | iexplore.exe | 104.22.25.70:80 | chomikuj.pl | Cloudflare Inc | US | suspicious |
4028 | iexplore.exe | 185.11.128.206:80 | pro.hit.gemius.pl | Data Invest sp. z o.o. S.K.A | PL | unknown |
4028 | iexplore.exe | 142.250.185.100:443 | www.google.com | Google Inc. | US | whitelisted |
4028 | iexplore.exe | 172.67.160.221:80 | x4.static-chomikuj.pl | — | US | unknown |
4028 | iexplore.exe | 91.224.220.19:443 | www.yetipay.pl | Hosteam S.c. Tomasz Groszewski Bartosz Waszak Lukasz Groszewski | PL | suspicious |
4028 | iexplore.exe | 104.21.89.144:80 | x4.static-chomikuj.pl | Cloudflare Inc | US | suspicious |
4028 | iexplore.exe | 104.21.89.144:443 | x4.static-chomikuj.pl | Cloudflare Inc | US | suspicious |
4028 | iexplore.exe | 66.102.1.156:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
4028 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
4028 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
chomikuj.pl |
| whitelisted |
x4.static-chomikuj.pl |
| malicious |
pro.hit.gemius.pl |
| whitelisted |
www.google.com |
| malicious |
www.yetipay.pl |
| whitelisted |
profile.static-chomikuj.pl |
| malicious |
static-chomikuj.pl |
| malicious |
stats.g.doubleclick.net |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |