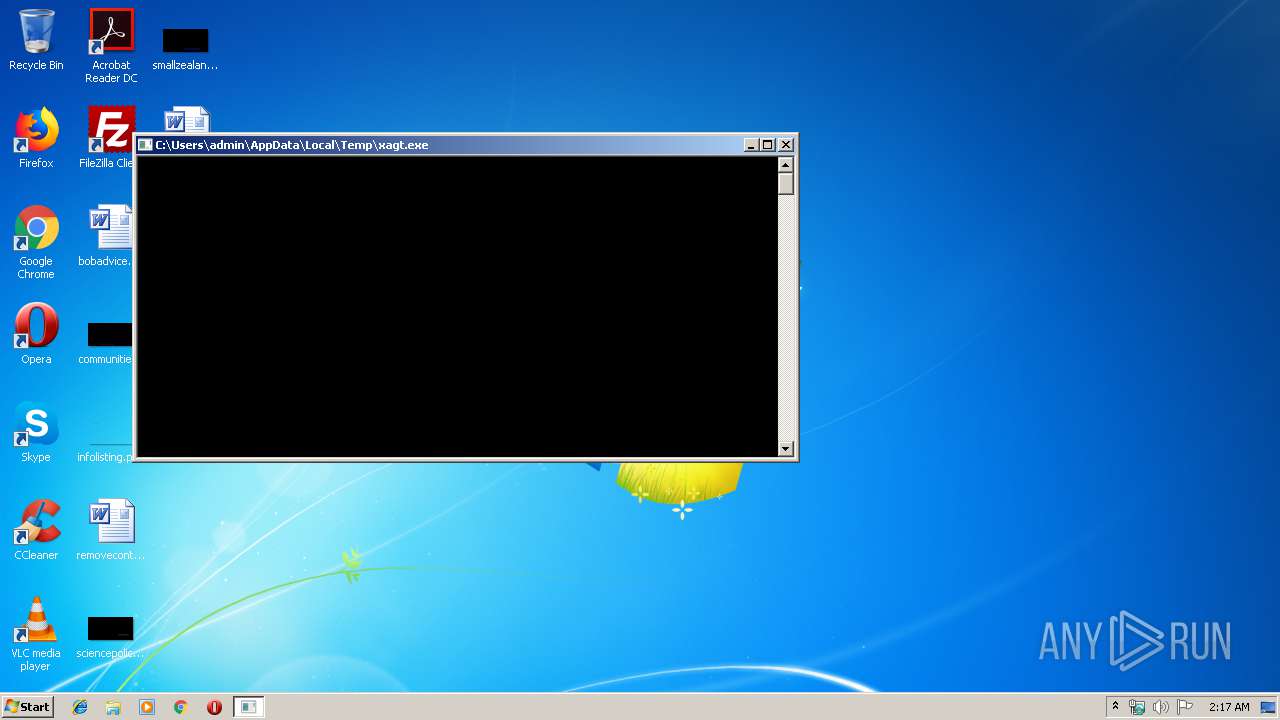
| File name: | xagt.exe |
| Full analysis: | https://app.any.run/tasks/80cadd23-a0dd-4a0c-8e00-b1989b985e37 |
| Verdict: | Malicious activity |
| Analysis date: | October 31, 2019, 02:16:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | 757E4C2FFE7F5B21FB237180B44F203F |
| SHA1: | 9AC34C875199E58257AC6BC8B3563421949C0355 |
| SHA256: | 422451FD1D983769AC057B70F64991E3E777D347F68B5FE37F15EBF373CCF2E6 |
| SSDEEP: | 393216:WnY3Ek73HSivZbxo91XflezvlPivGV/GlYsnZ:WY3o91XUij |
MALICIOUS
Loads dropped or rewritten executable
- xagt.exe (PID: 2208)
SUSPICIOUS
Creates files in the program directory
- xagt.exe (PID: 2208)
Executable content was dropped or overwritten
- xagt.exe (PID: 2208)
Creates files in the driver directory
- xagt.exe (PID: 2208)
Creates files in the Windows directory
- xagt.exe (PID: 2208)
Creates or modifies windows services
- xagt.exe (PID: 2208)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (28.3) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (generic) (27.3) |
| .exe | | | Win32 Executable MS Visual C++ (generic) (20.5) |
| .exe | | | Win64 Executable (generic) (18.1) |
| .exe | | | Win32 Executable (generic) (2.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:01:02 16:09:21+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 3513344 |
| InitializedDataSize: | 12110336 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2be3ab |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 22.41.5.6171 |
| ProductVersionNumber: | 22.41.5.6171 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| FileVersion: | 22.41.5 |
| ProductVersion: | 22.41.5 |
| CompanyName: | FireEye Inc. |
| LegalCopyright: | Copyright © 2016, FireEye Inc. |
| ProductName: | FireEye Agent |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 02-Jan-2017 15:09:21 |
| Detected languages: |
|
| Debug artifacts: |
|
| FileVersion: | 22.41.5 |
| ProductVersion: | 22.41.5 |
| CompanyName: | FireEye Inc. |
| LegalCopyright: | Copyright © 2016, FireEye Inc. |
| ProductName: | FireEye Agent |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 02-Jan-2017 15:09:21 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00359A59 | 0x00359C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.55272 |
.rdata | 0x0035B000 | 0x00A82372 | 0x00A82400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.71708 |
.data | 0x00DDE000 | 0x000E20E0 | 0x000DC400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.57606 |
.tls | 0x00EC1000 | 0x00000011 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00EC2000 | 0x00000720 | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.1487 |
.reloc | 0x00EC3000 | 0x0002D7A4 | 0x0002D800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.67354 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.95512 | 1122 | Latin 1 / Western European | English - United States | RT_MANIFEST |
Imports
ADVAPI32.dll |
CRYPT32.dll |
IPHLPAPI.DLL |
KERNEL32.dll |
LIBEAY32.dll (delay-loaded) |
NETAPI32.dll |
PSAPI.DLL |
RPCRT4.dll |
SETUPAPI.dll |
SHELL32.dll |
Total processes
39
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2208 | "C:\Users\admin\AppData\Local\Temp\xagt.exe" | C:\Users\admin\AppData\Local\Temp\xagt.exe | explorer.exe | ||||||||||||
User: admin Company: FireEye Inc. Integrity Level: HIGH Exit code: 3221225477 Version: 22.41.5 Modules
| |||||||||||||||
| 3456 | "C:\Users\admin\AppData\Local\Temp\xagt.exe" | C:\Users\admin\AppData\Local\Temp\xagt.exe | — | explorer.exe | |||||||||||
User: admin Company: FireEye Inc. Integrity Level: MEDIUM Exit code: 3221226540 Version: 22.41.5 Modules
| |||||||||||||||
Total events
19
Read events
7
Write events
12
Delete events
0
Modification events
| (PID) Process: | (2208) xagt.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\FeKern |
| Operation: | write | Name: | DisplayName |
Value: FeKern | |||
| (PID) Process: | (2208) xagt.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\FeKern |
| Operation: | write | Name: | ErrorControl |
Value: 1 | |||
| (PID) Process: | (2208) xagt.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\FeKern |
| Operation: | write | Name: | Type |
Value: 2 | |||
| (PID) Process: | (2208) xagt.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\FeKern |
| Operation: | write | Name: | Start |
Value: 3 | |||
| (PID) Process: | (2208) xagt.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\FeKern |
| Operation: | write | Name: | ImagePath |
Value: \SystemRoot\System32\drivers\FeKern.sys | |||
| (PID) Process: | (2208) xagt.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\FeKern |
| Operation: | write | Name: | DependsOnService |
Value: FltMgr | |||
| (PID) Process: | (2208) xagt.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\FeKern |
| Operation: | write | Name: | Group |
Value: FSFilter Activity Monitor | |||
| (PID) Process: | (2208) xagt.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\GroupOrderList |
| Operation: | write | Name: | FSFilter Activity Monitor |
Value: 020000000200000001000000 | |||
| (PID) Process: | (2208) xagt.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\FeKern |
| Operation: | write | Name: | Tag |
Value: 2 | |||
| (PID) Process: | (2208) xagt.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\FeKern\Instances |
| Operation: | write | Name: | DefaultInstance |
Value: FeKern | |||
Executable files
5
Suspicious files
2
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2208 | xagt.exe | C:\ProgramData\FireEye\xagt\main.db-journal | — | |
MD5:— | SHA256:— | |||
| 2208 | xagt.exe | C:\Users\admin\AppData\Local\Temp\ssleay32.dll | executable | |
MD5:021BE6EF93EB6C2505956D863DDB067D | SHA256:3F6BD8AE646745684AB736B535740A5D0BE26E7A4B14F9F54C06DD631D10C14E | |||
| 2208 | xagt.exe | C:\Users\admin\AppData\Local\Temp\audits.dll | executable | |
MD5:E61A0465994A3D176E65A0D228BE0A71 | SHA256:3E2471DE486F95D300E119B0403F3BFB0C608E3D8254728D5F95F0D11E032F01 | |||
| 2208 | xagt.exe | C:\ProgramData\FireEye\xagt\xacs\xamky | binary | |
MD5:3902987934C321AD9E003B36593323FF | SHA256:4CF370BC0F462465EFDEBEA472AD815227C0991809282C1C219162B3C9225474 | |||
| 2208 | xagt.exe | C:\ProgramData\FireEye\xagt\main.db | binary | |
MD5:DED503C55111580027BC4CE109413E74 | SHA256:52B2BFF0BB0EC59C8F191663842A15497E9B5509BAA1D8DD04FB4C4C754DDBEB | |||
| 2208 | xagt.exe | C:\Windows\System32\drivers\FeKern.sys | executable | |
MD5:6E2B8A188DDA27AB35D94406012E74CB | SHA256:6081CFDFF62F8B46DC101E0817D93E650472453A097CEF38674FB84B8180B57F | |||
| 2208 | xagt.exe | C:\Users\admin\AppData\Local\Temp\libeay32.dll | executable | |
MD5:8DA8C6D7A1B1B8D8BF02F9DC1FB0A139 | SHA256:74B8A42C9030FE26BC7E8A9DD0157F2D96E8490D940C464310CD4CEC46474379 | |||
| 2208 | xagt.exe | C:\Users\admin\AppData\Local\Temp\msvcr120.dll | executable | |
MD5:034CCADC1C073E4216E9466B720F9849 | SHA256:86E39B5995AF0E042FCDAA85FE2AEFD7C9DDC7AD65E6327BD5E7058BC3AB615F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
xagt.exe | CreateFile for \\.\fekern_00 succeeded with error : 0
|
xagt.exe | SendDeviceIoctl for test IOCTL returned status : 0
|