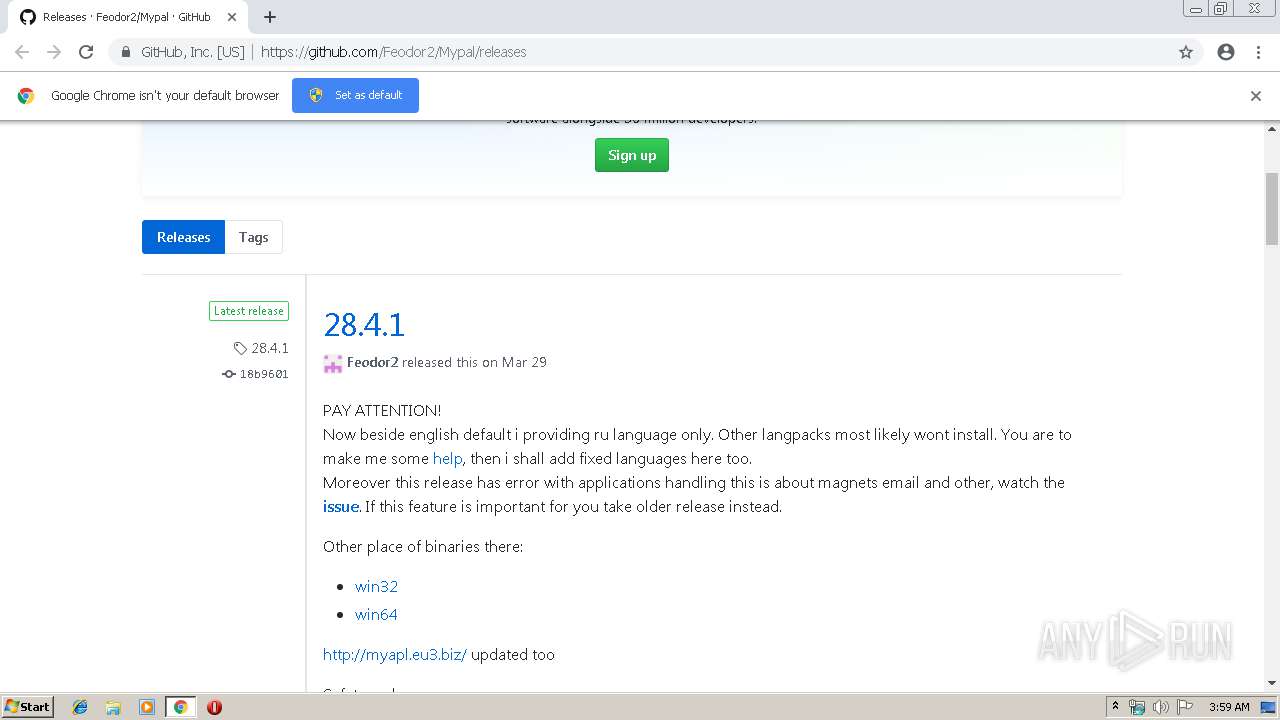
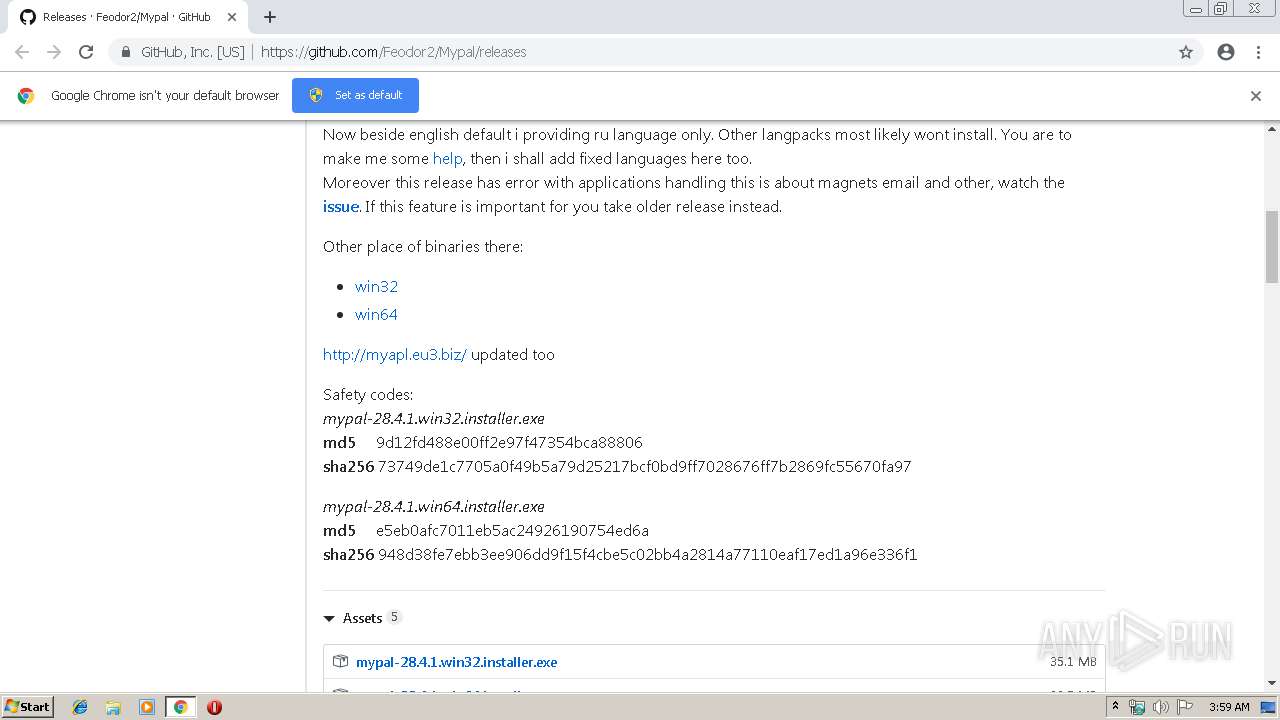
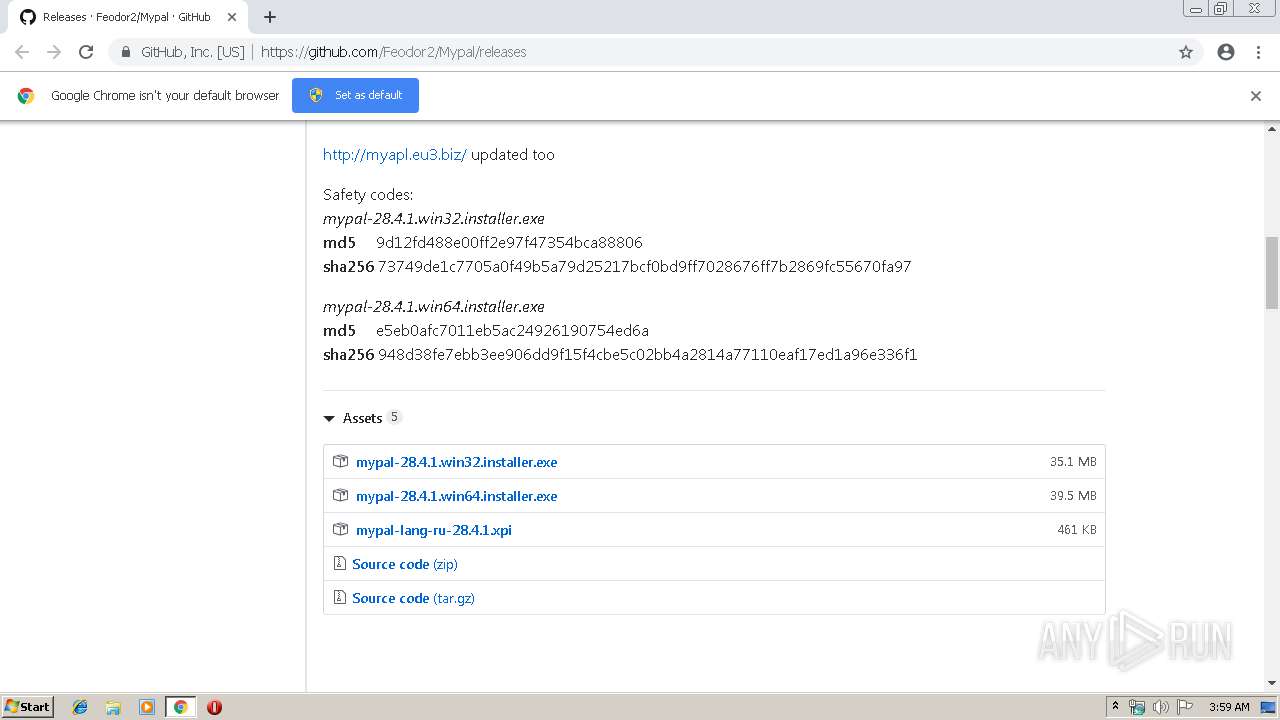
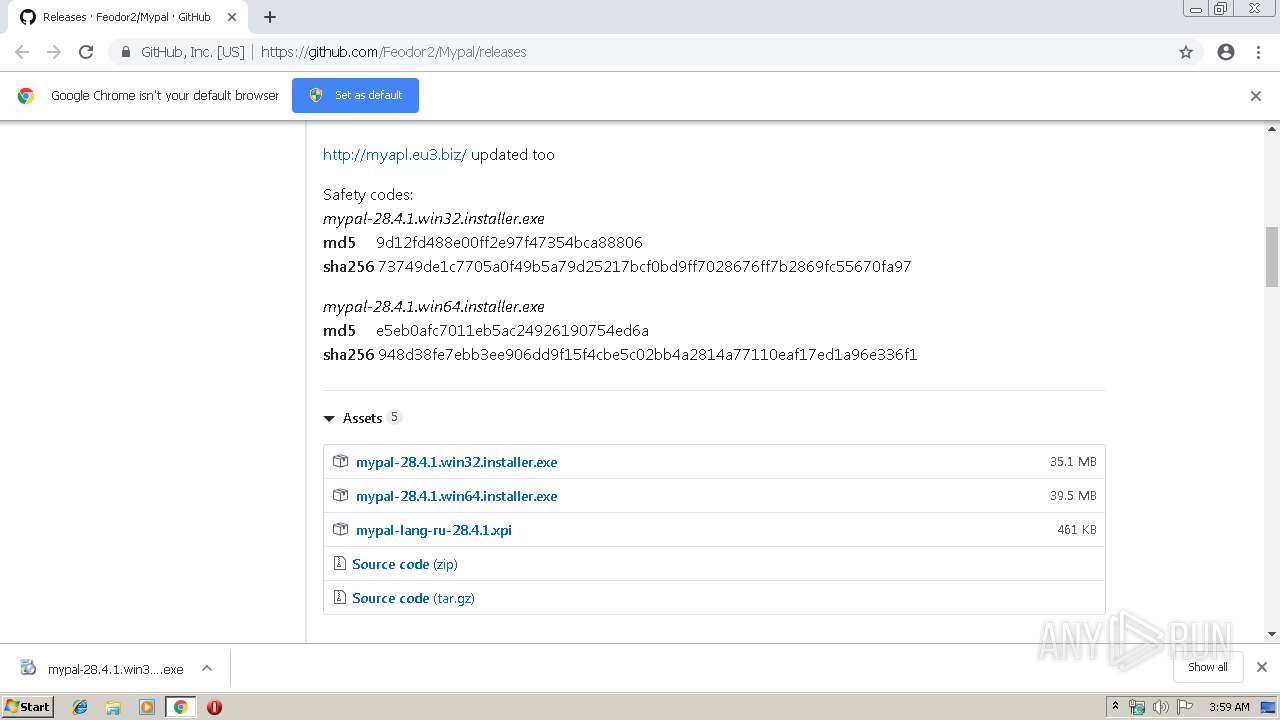
| URL: | https://github.com/Feodor2/Mypal/releases |
| Full analysis: | https://app.any.run/tasks/4761543d-07ed-4918-9d82-a1172077fd88 |
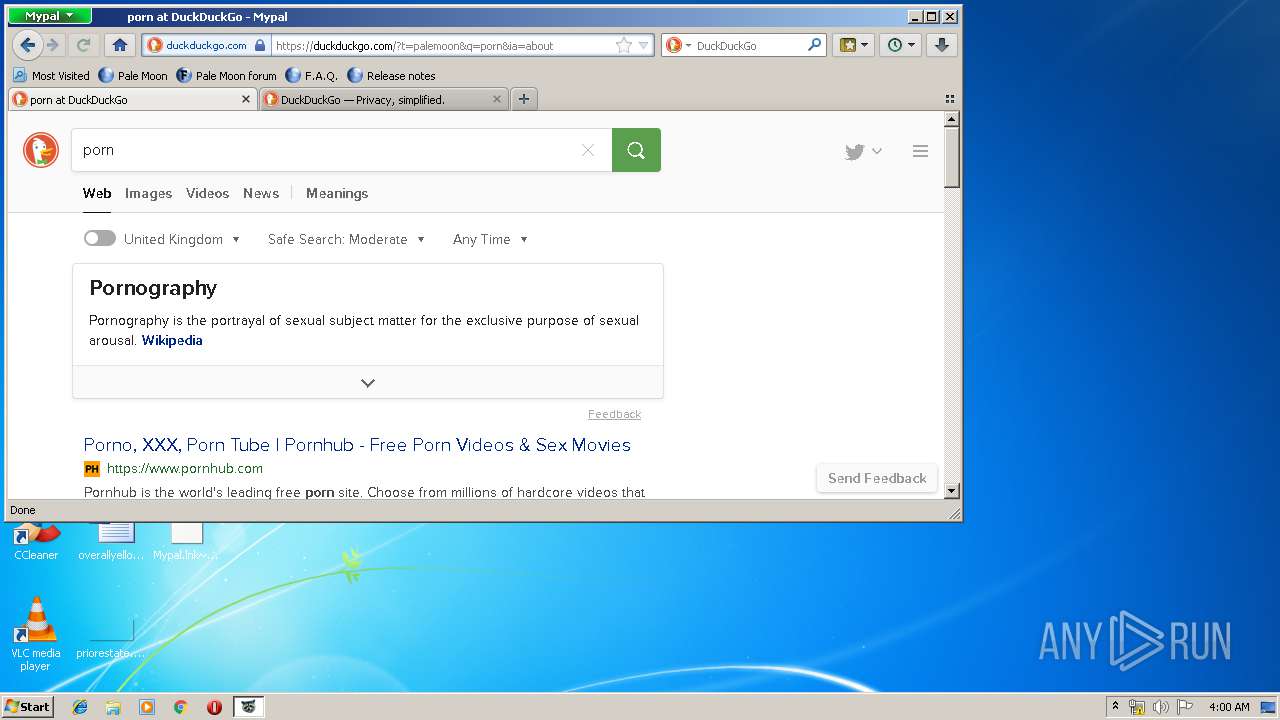
| Verdict: | Malicious activity |
| Analysis date: | May 03, 2019, 02:58:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 334F520B627E82170A4D6EE78F821EFE |
| SHA1: | 307D7AB1969BFC526F89225F943939A9D58DF64D |
| SHA256: | 42230C2E94327BA37EFDC0E638081F5582B073F4FBD1450F60FD02C3E9B8B062 |
| SSDEEP: | 3:N8tEdMK8qoYn:2u6Bqpn |
MALICIOUS
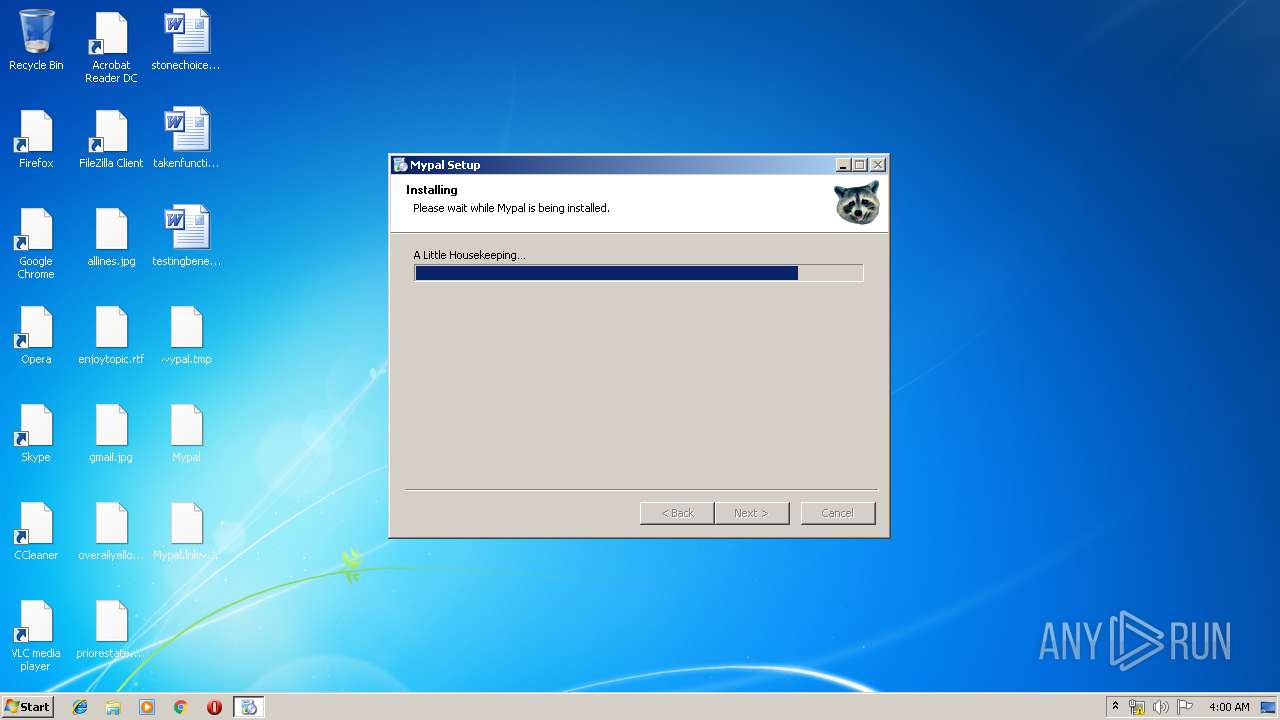
Application was dropped or rewritten from another process
- mypal-28.4.1.win32.installer.exe (PID: 2276)
- setup.exe (PID: 3688)
- setup.exe (PID: 2712)
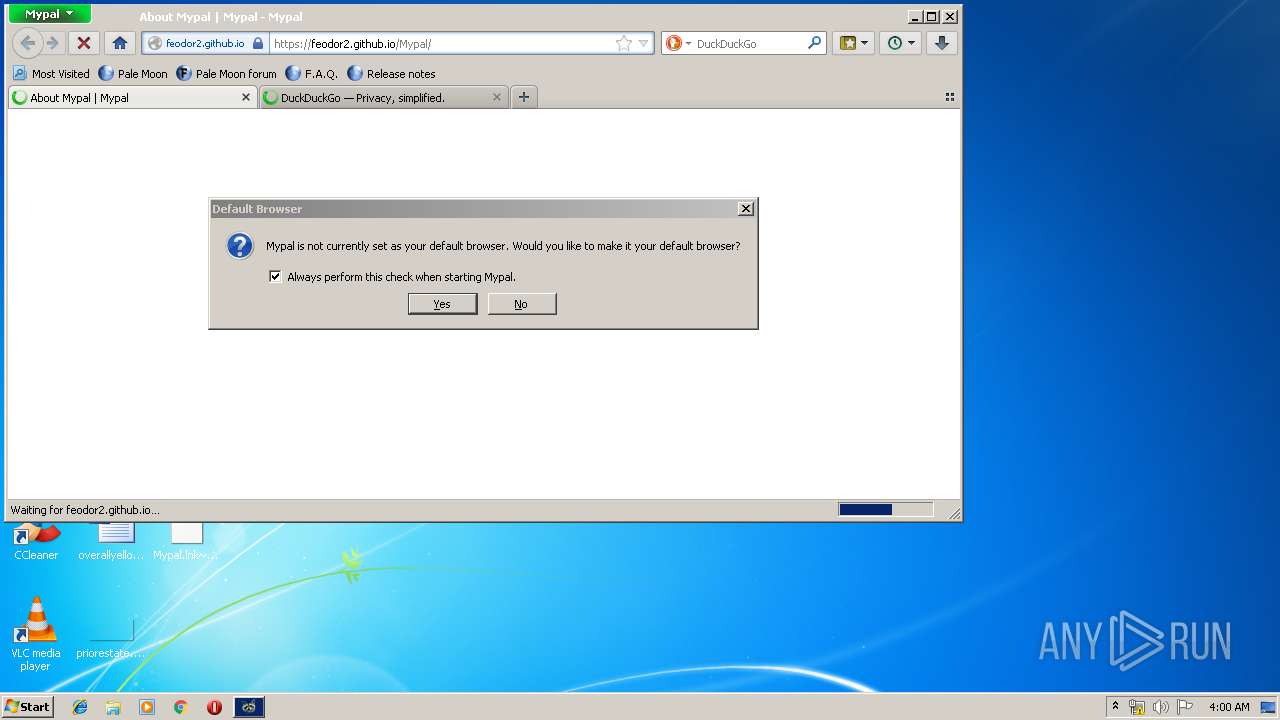
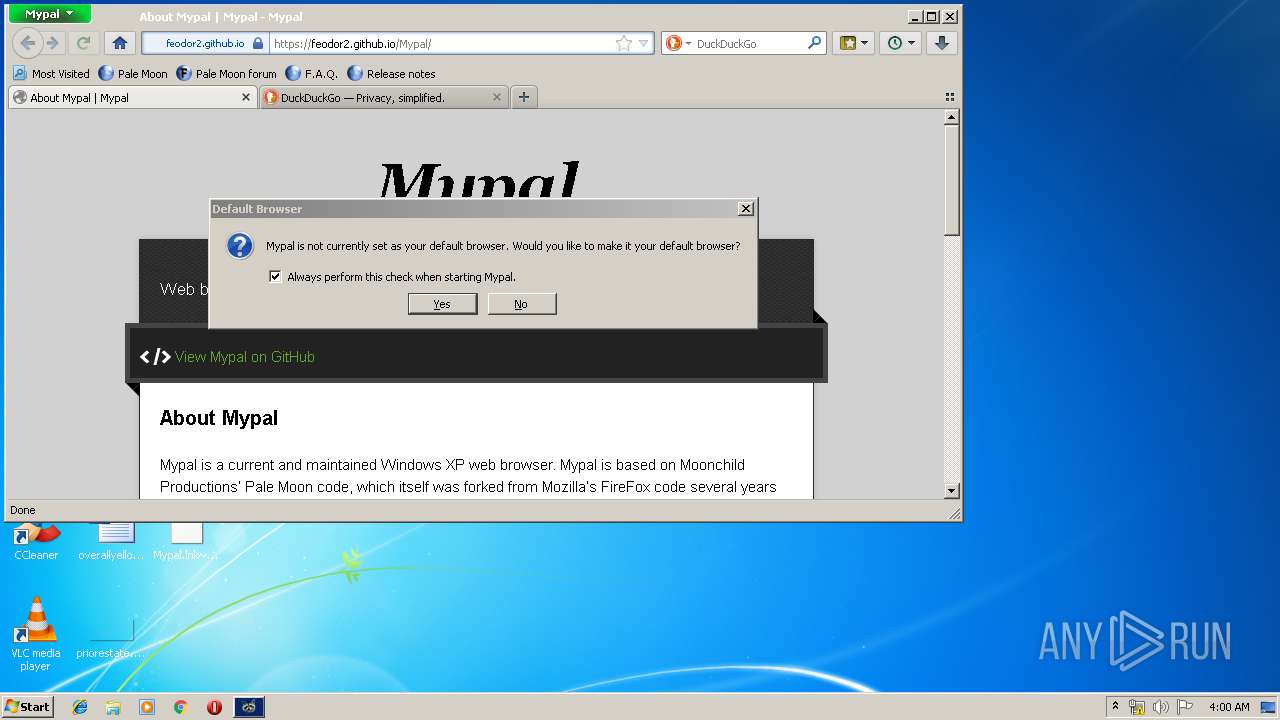
- mypal.exe (PID: 3384)
- helper.exe (PID: 3296)
Loads dropped or rewritten executable
- setup.exe (PID: 3688)
- setup.exe (PID: 2712)
- mypal.exe (PID: 3384)
- helper.exe (PID: 3296)
SUSPICIOUS
Executable content was dropped or overwritten
- setup.exe (PID: 3688)
- chrome.exe (PID: 2836)
- mypal-28.4.1.win32.installer.exe (PID: 2276)
- setup.exe (PID: 2712)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2836)
Application launched itself
- setup.exe (PID: 3688)
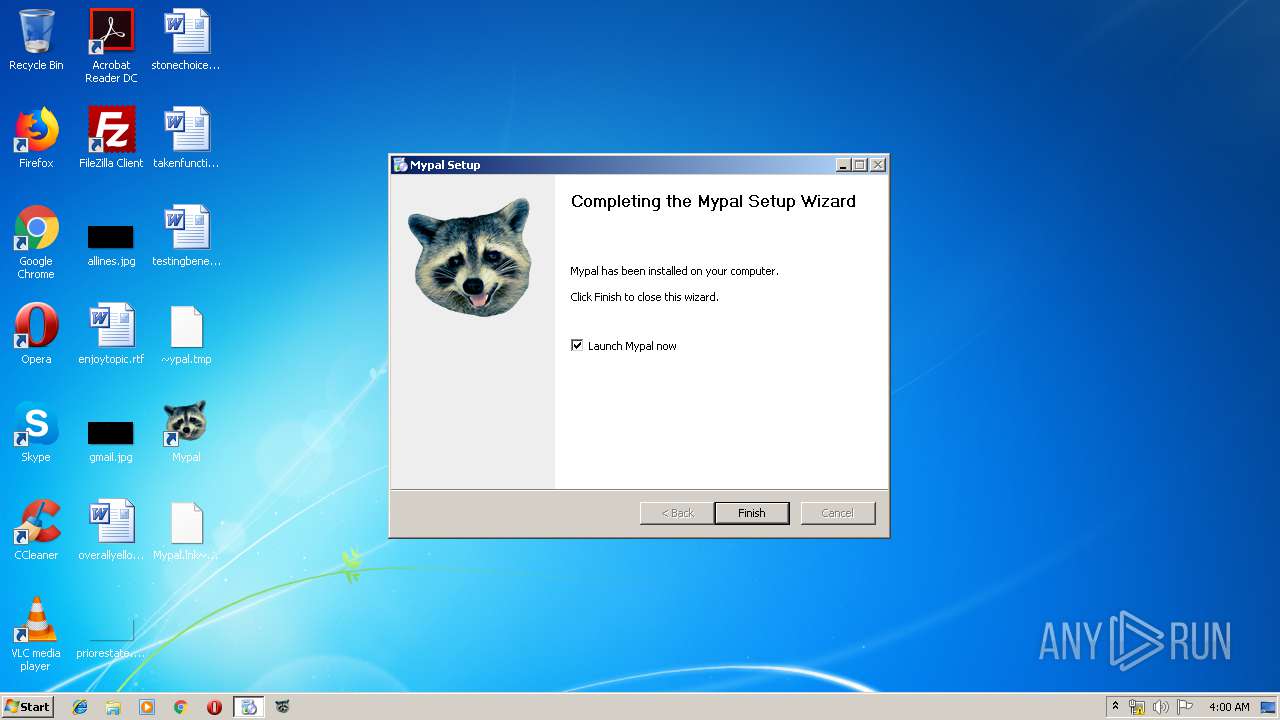
Creates a software uninstall entry
- setup.exe (PID: 2712)
Modifies the open verb of a shell class
- setup.exe (PID: 2712)
- setup.exe (PID: 3688)
- helper.exe (PID: 3296)
Creates files in the program directory
- setup.exe (PID: 2712)
Creates files in the user directory
- setup.exe (PID: 3688)
- mypal.exe (PID: 3384)
Reads CPU info
- mypal.exe (PID: 3384)
INFO
Application launched itself
- chrome.exe (PID: 2836)
Reads settings of System Certificates
- chrome.exe (PID: 2836)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
58
Monitored processes
24
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2220 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=948,2043283896163928293,11372168043744989382,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13573132960977978459 --mojo-platform-channel-handle=3968 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2248 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=948,2043283896163928293,11372168043744989382,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1375859776770222719 --mojo-platform-channel-handle=3844 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
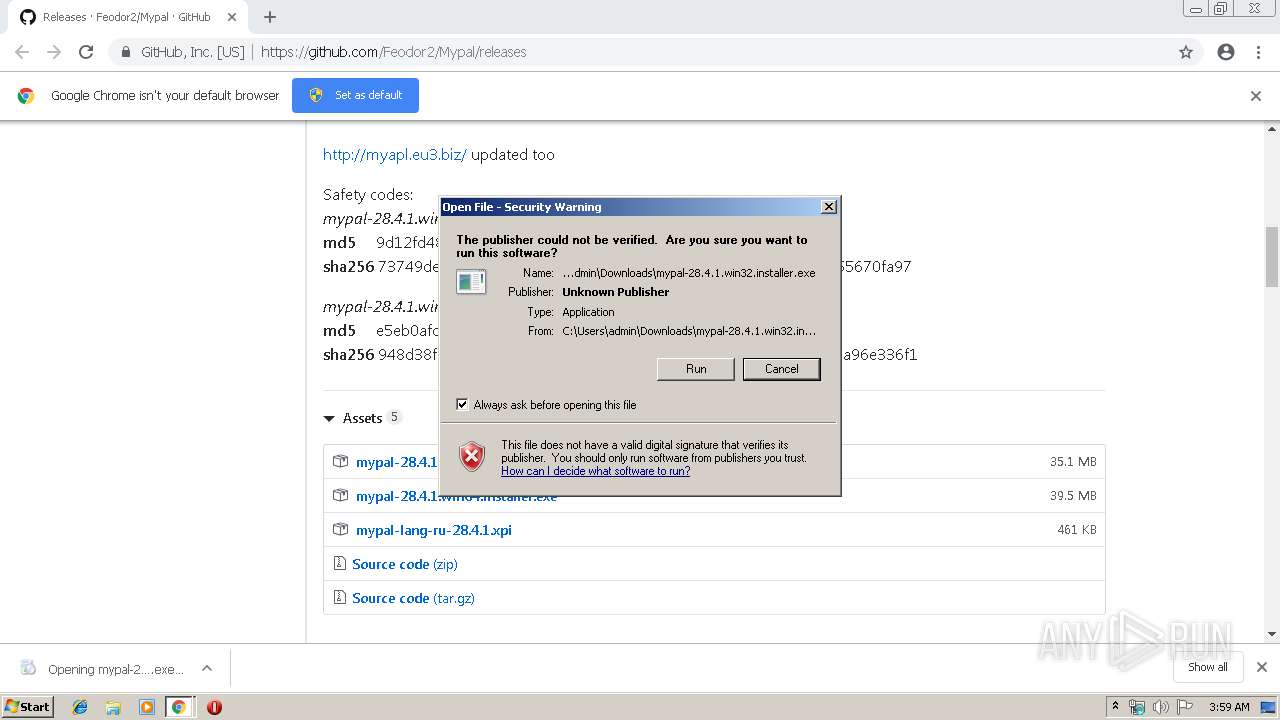
| 2276 | "C:\Users\admin\Downloads\mypal-28.4.1.win32.installer.exe" | C:\Users\admin\Downloads\mypal-28.4.1.win32.installer.exe | chrome.exe | ||||||||||||
User: admin Company: Moonchild Productions Integrity Level: MEDIUM Description: Pale Moon Exit code: 0 Version: 4.42 Modules
| |||||||||||||||
| 2316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=948,2043283896163928293,11372168043744989382,131072 --enable-features=PasswordImport --service-pipe-token=1880553255772174789 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1880553255772174789 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1976 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2440 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=948,2043283896163928293,11372168043744989382,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=943905590470586048 --mojo-platform-channel-handle=4160 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2592 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=948,2043283896163928293,11372168043744989382,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1276853428581346281 --mojo-platform-channel-handle=3884 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2660 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2840 --on-initialized-event-handle=308 --parent-handle=312 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2712 | "C:\Users\admin\AppData\Local\Temp\7zSC41E.tmp\setup.exe" /UAC:40188 /NCRC | C:\Users\admin\AppData\Local\Temp\7zSC41E.tmp\setup.exe | setup.exe | ||||||||||||
User: admin Company: Feodor2 Integrity Level: HIGH Description: Mypal Installer Exit code: 0 Version: 28.4.1 Modules
| |||||||||||||||
| 2828 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=948,2043283896163928293,11372168043744989382,131072 --enable-features=PasswordImport --service-pipe-token=3879561177585130948 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3879561177585130948 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1984 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2836 | "C:\Program Files\Google\Chrome\Application\chrome.exe" https://github.com/Feodor2/Mypal/releases | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
1 975
Read events
1 665
Write events
291
Delete events
19
Modification events
| (PID) Process: | (2836) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2836) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2836) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2836) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2836) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2660) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2836-13201325935879125 |
Value: 259 | |||
| (PID) Process: | (2836) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2836) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2836) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (2836) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
138
Suspicious files
141
Text files
456
Unknown types
54
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2836 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2836 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2836 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2836 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2836 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2836 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\f09571fa-2708-4c6e-8fcf-5d14353fca84.tmp | — | |
MD5:— | SHA256:— | |||
| 2836 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2836 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT | — | |
MD5:— | SHA256:— | |||
| 2836 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2836 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
77
DNS requests
112
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2836 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRJ9L2KGL92BpjF3kAtaDtxauTmhgQUPdNQpdagre7zSmAKZdMh1Pj41g8CEAoGMEJ%2FW7ztaVc5ZZO2RR8%3D | US | der | 471 b | whitelisted |
3384 | mypal.exe | POST | 200 | 195.138.255.24:80 | http://ocsp.comodoca.com/ | DE | der | 471 b | whitelisted |
2836 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
2836 | chrome.exe | GET | 302 | 172.217.22.46:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 504 b | whitelisted |
2836 | chrome.exe | GET | 200 | 173.194.5.185:80 | http://r3---sn-aigl6n7z.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.92.25.173&mm=28&mn=sn-aigl6n7z&ms=nvh&mt=1556852253&mv=m&pl=24&shardbypass=yes | US | crx | 842 Kb | whitelisted |
3384 | mypal.exe | POST | 200 | 2.16.186.27:80 | http://ocsp.int-x3.letsencrypt.org/ | unknown | der | 527 b | whitelisted |
3384 | mypal.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3384 | mypal.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3384 | mypal.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3384 | mypal.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2836 | chrome.exe | 216.58.207.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
2836 | chrome.exe | 172.217.22.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2836 | chrome.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2836 | chrome.exe | 140.82.118.4:443 | github.com | — | US | malicious |
2836 | chrome.exe | 185.199.108.154:443 | github.githubassets.com | GitHub, Inc. | NL | suspicious |
2836 | chrome.exe | 172.217.22.42:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2836 | chrome.exe | 151.101.0.133:443 | avatars2.githubusercontent.com | Fastly | US | malicious |
2836 | chrome.exe | 34.230.200.137:443 | collector.githubapp.com | Amazon.com, Inc. | US | unknown |
2836 | chrome.exe | 172.217.16.174:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
2836 | chrome.exe | 172.217.22.46:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
github.com |
| malicious |
accounts.google.com |
| shared |
ocsp.digicert.com |
| whitelisted |
github.githubassets.com |
| whitelisted |
avatars2.githubusercontent.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
avatars0.githubusercontent.com |
| whitelisted |
avatars1.githubusercontent.com |
| whitelisted |
avatars3.githubusercontent.com |
| whitelisted |