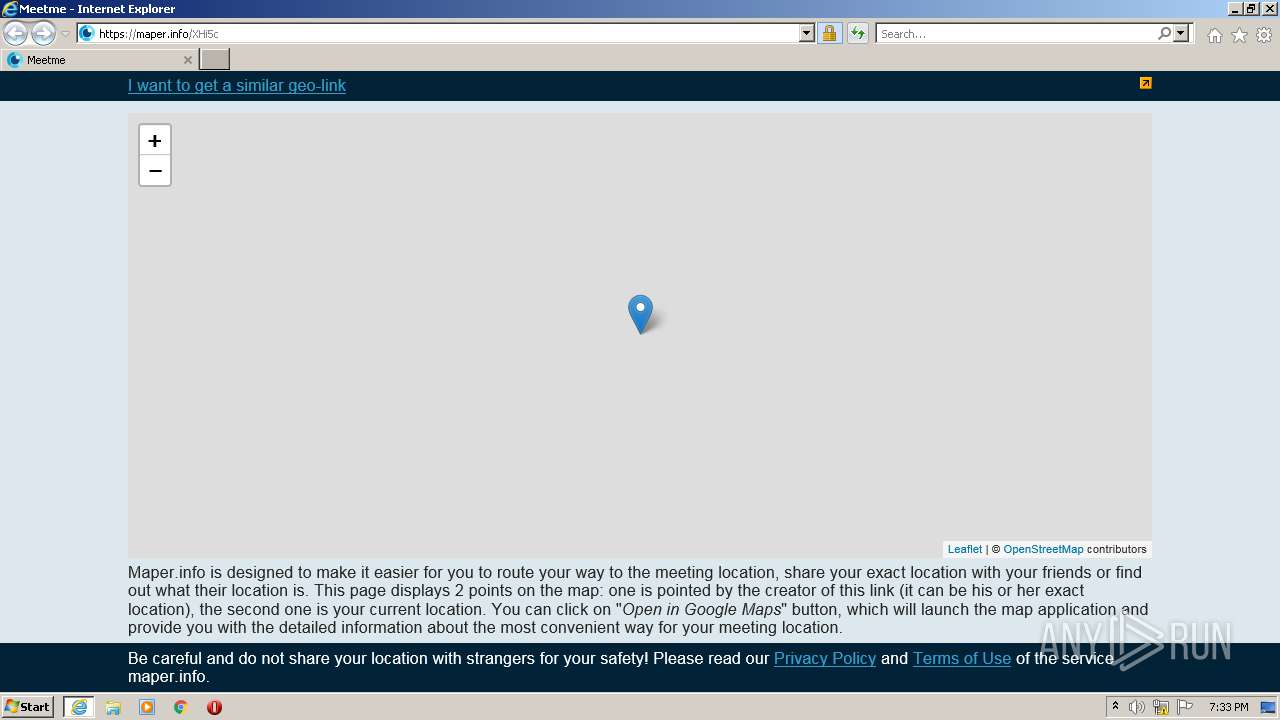
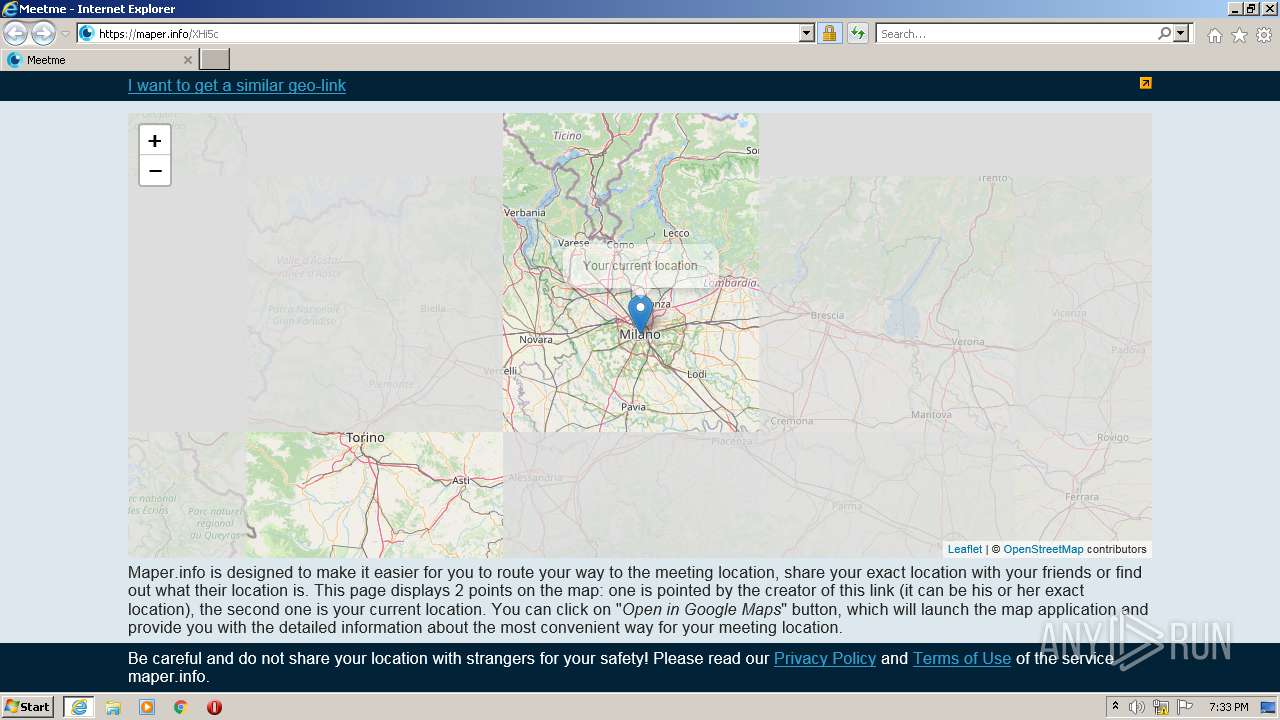
| URL: | https://maper.info/XHi5c |
| Full analysis: | https://app.any.run/tasks/52a9d044-878a-4c83-93c5-151c07255aae |
| Verdict: | Malicious activity |
| Analysis date: | November 24, 2021, 19:33:13 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 59FEEE3D953B223044AB1C1AE3D95646 |
| SHA1: | 185F8196FF0CB73FBEBB686F4193CF3E84850F10 |
| SHA256: | 4206A71F4DE2CC9D7574386539AC4597325B0EB6DD721923CDB41EB674DBACB5 |
| SSDEEP: | 3:N8em+Tn:2un |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3096)
Reads Environment values
- iexplore.exe (PID: 3096)
INFO
Checks supported languages
- iexplore.exe (PID: 2372)
- iexplore.exe (PID: 3096)
Reads the computer name
- iexplore.exe (PID: 2372)
- iexplore.exe (PID: 3096)
Checks Windows Trust Settings
- iexplore.exe (PID: 3096)
- iexplore.exe (PID: 2372)
Reads settings of System Certificates
- iexplore.exe (PID: 3096)
- iexplore.exe (PID: 2372)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2372)
Reads internet explorer settings
- iexplore.exe (PID: 3096)
Changes internet zones settings
- iexplore.exe (PID: 2372)
Application launched itself
- iexplore.exe (PID: 2372)
Creates files in the user directory
- iexplore.exe (PID: 3096)
Changes settings of System certificates
- iexplore.exe (PID: 2372)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
37
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2372 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://maper.info/XHi5c" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3096 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2372 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
16 585
Read events
16 468
Write events
115
Delete events
2
Modification events
| (PID) Process: | (2372) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2372) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 631718048 | |||
| (PID) Process: | (2372) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30925162 | |||
| (PID) Process: | (2372) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 931881798 | |||
| (PID) Process: | (2372) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30925162 | |||
| (PID) Process: | (2372) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2372) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2372) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2372) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2372) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
15
Text files
35
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3096 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\JBRLR9CF.txt | text | |
MD5:AB7F7B38728A58AB186D40548158719B | SHA256:07F1C5FC5984E0FD6853A0CAB7CBCF9A07A54248CC1AE31E50BEF1E9CE7F5996 | |||
| 3096 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | der | |
MD5:0AEF5A177E8B23FEF980F6F061EC00DA | SHA256:727A6AED72564CF0816C9B53DB4F17475D9AF58C71BE5723397045868CB8422D | |||
| 3096 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:986EB525373AF83BC508612FDFD2EA21 | SHA256:5F075EA09D14BEBEF6F4E1B5EE8AFACD6A0F34449BD8B5D4664CCC97E02A19CF | |||
| 3096 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_89854CA6A0F0936A4D2ECA78845CEA25 | der | |
MD5:5DA4F9F310192AB9011C3BFEC20E67B9 | SHA256:D00B02B055DBEE5D6698BF2A35934B2903FECDE8895D049BFAE5C230C959E6D1 | |||
| 3096 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B2FAF7692FD9FFBD64EDE317E42334BA_89854CA6A0F0936A4D2ECA78845CEA25 | binary | |
MD5:898F0E0C427DF328BD2946CF0DDE7BC2 | SHA256:387C446D32A57D7BF41EA3EECFDCFC0861B6DF1830BD9D936D4825C6D20D2761 | |||
| 3096 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarEAB2.tmp | cat | |
MD5:D99661D0893A52A0700B8AE68457351A | SHA256:BDD5111162A6FA25682E18FA74E37E676D49CAFCB5B7207E98E5256D1EF0D003 | |||
| 3096 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
| 3096 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabEAB1.tmp | compressed | |
MD5:ACAEDA60C79C6BCAC925EEB3653F45E0 | SHA256:6B0CECCF0103AFD89844761417C1D23ACC41F8AEBF3B7230765209B61EEE5658 | |||
| 3096 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:904CCAC054C9CF6FC2243490C93A98C1 | SHA256:DD7D7BE73A7D70049F968F37C2E80B121CFE93EE3A4E892F94709E38C0C6DD6B | |||
| 3096 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:D066E72B8FB37E5F58BBE8715DDE8EDB | SHA256:C14422CD2FE12DBD456703396B779C4DDF17483D148706C78FAAB52A9A796E7C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
50
DNS requests
20
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2372 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
3096 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEFZnHQTqT5lMbxCBR1nSdZQ%3D | US | der | 471 b | whitelisted |
3096 | iexplore.exe | GET | 200 | 104.18.20.226:80 | http://ocsp2.globalsign.com/rootr3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCEHgDGCDPAjbzpoUYuu%2B39wE%3D | US | der | 1.40 Kb | whitelisted |
3096 | iexplore.exe | GET | 200 | 104.18.30.182:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSr83eyJy3njhjVpn5bEpfc6MXawQQUOuEJhtTPGcKWdnRJdtzgNcZjY5oCEHJqaUWUuUGuV9euEAx07js%3D | US | der | 314 b | whitelisted |
3096 | iexplore.exe | GET | 200 | 8.248.149.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?c6b966393682f9ed | US | compressed | 4.70 Kb | whitelisted |
3096 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
3096 | iexplore.exe | GET | 200 | 104.89.32.83:80 | http://x1.c.lencr.org/ | NL | der | 717 b | whitelisted |
2372 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
3096 | iexplore.exe | GET | 200 | 8.248.149.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?5b810eac8f0d199b | US | compressed | 59.9 Kb | whitelisted |
3096 | iexplore.exe | GET | 200 | 8.248.149.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?e72579a577c34f84 | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3096 | iexplore.exe | 5.9.164.117:443 | maper.info | Hetzner Online GmbH | DE | malicious |
3096 | iexplore.exe | 104.89.32.83:80 | x1.c.lencr.org | Akamai Technologies, Inc. | NL | suspicious |
3096 | iexplore.exe | 104.16.126.175:443 | unpkg.com | Cloudflare Inc | US | shared |
2372 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3096 | iexplore.exe | 88.212.201.210:443 | counter.yadro.ru | United Network LLC | RU | suspicious |
3096 | iexplore.exe | 104.18.30.182:80 | ocsp.usertrust.com | Cloudflare Inc | US | suspicious |
3096 | iexplore.exe | 8.248.149.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
— | — | 151.139.128.14:80 | ocsp.comodoca.com | Highwinds Network Group, Inc. | US | suspicious |
3096 | iexplore.exe | 151.101.2.137:443 | a.tile.openstreetmap.org | Fastly | US | suspicious |
2372 | iexplore.exe | 5.9.164.117:443 | maper.info | Hetzner Online GmbH | DE | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
maper.info |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
unpkg.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
counter.yadro.ru |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3096 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY IP Logger Redirect Domain in SNI |
3096 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY IP Logger Redirect Domain in SNI |
2372 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY IP Logger Redirect Domain in SNI |
2372 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY IP Logger Redirect Domain in SNI |
4 ETPRO signatures available at the full report