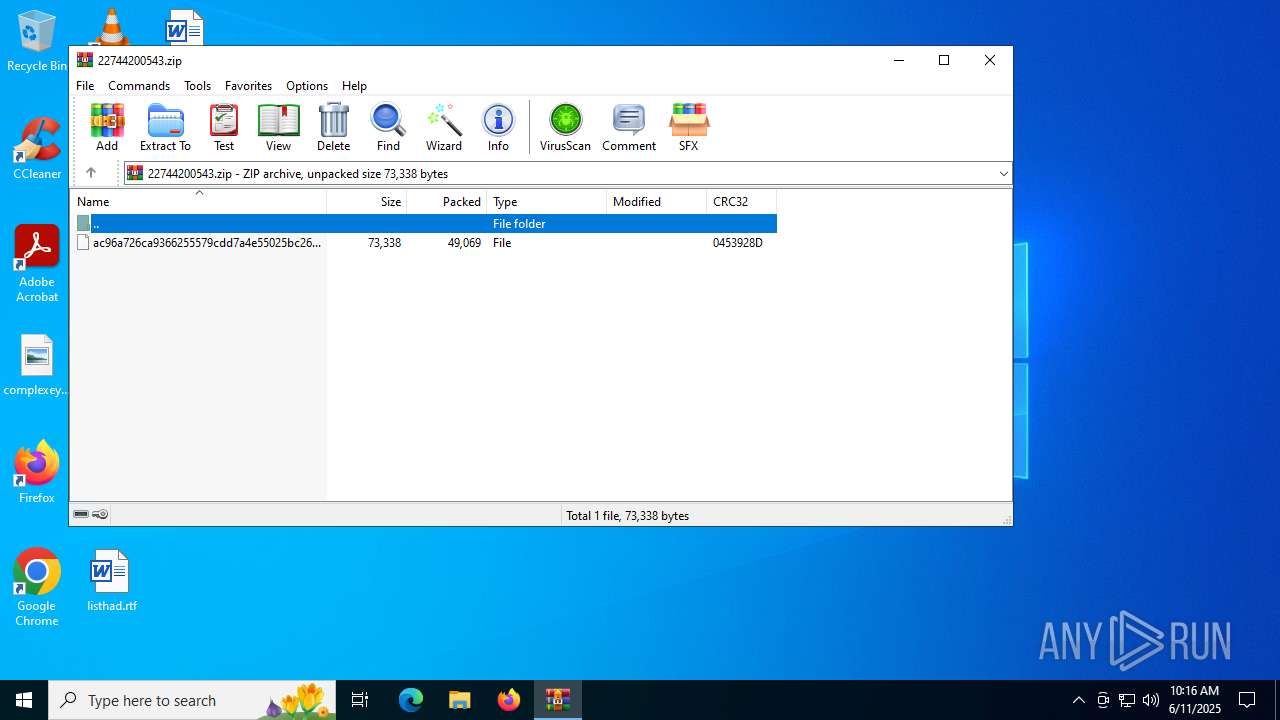
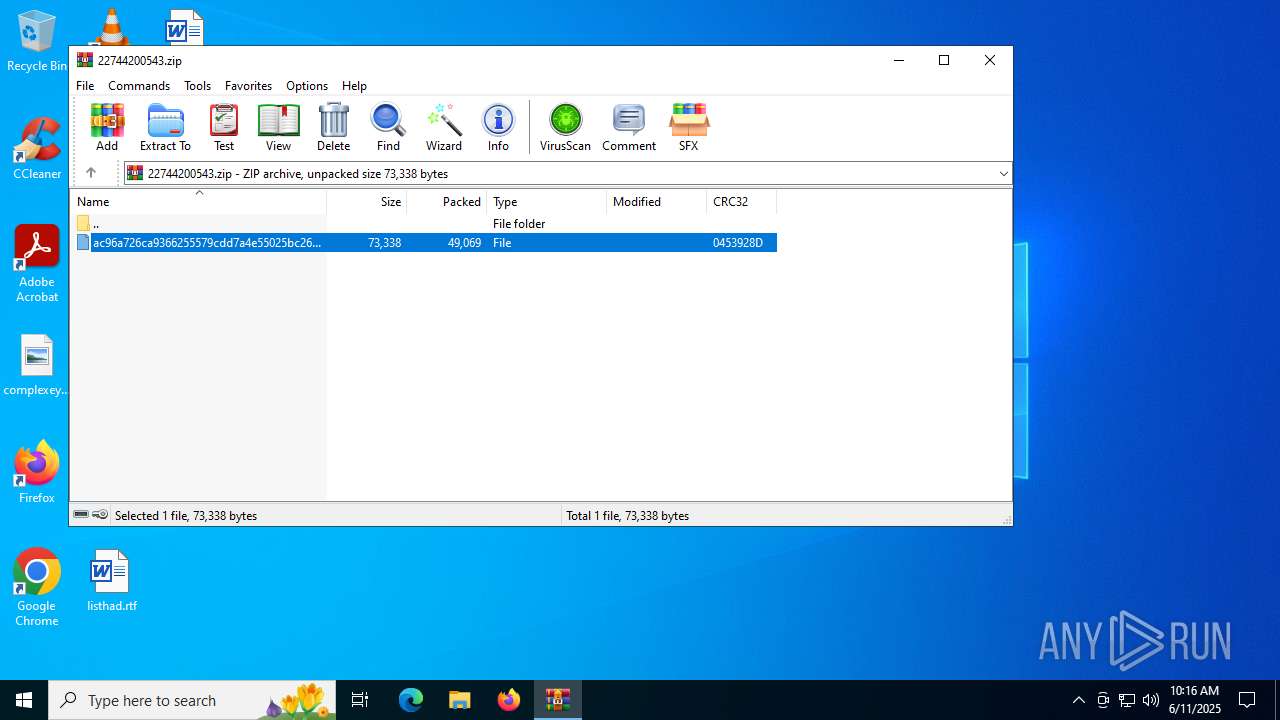
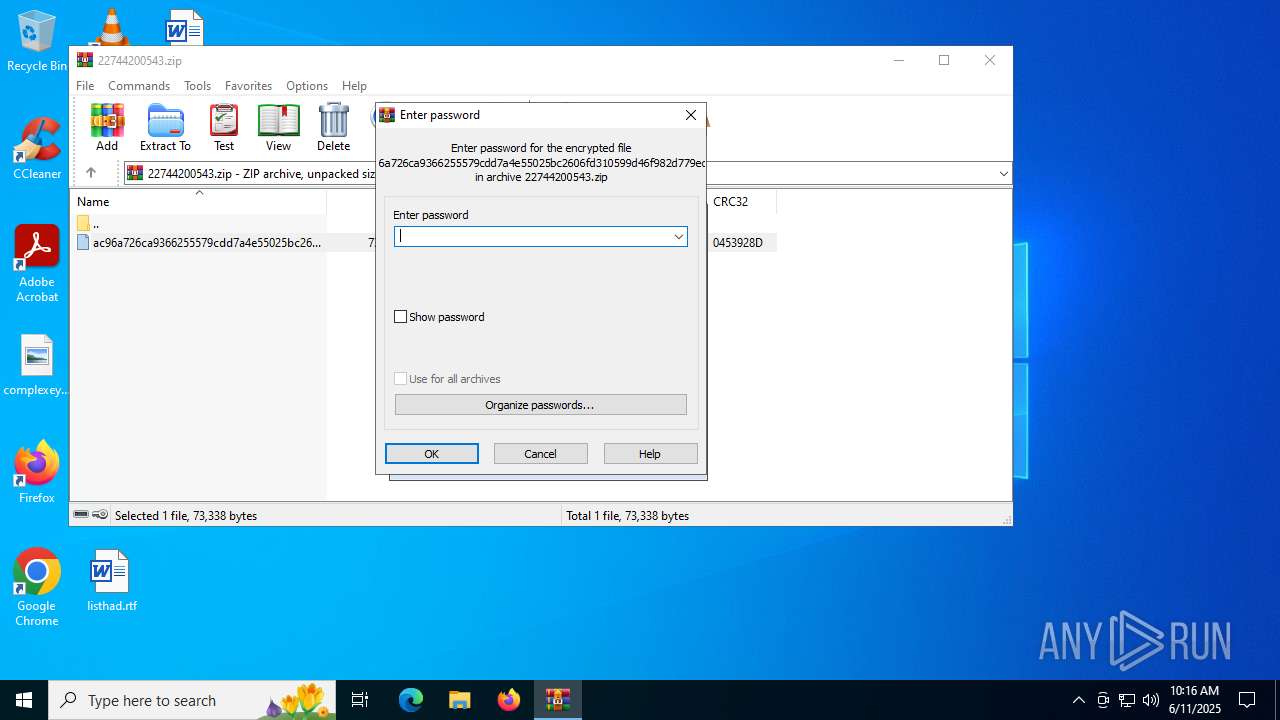
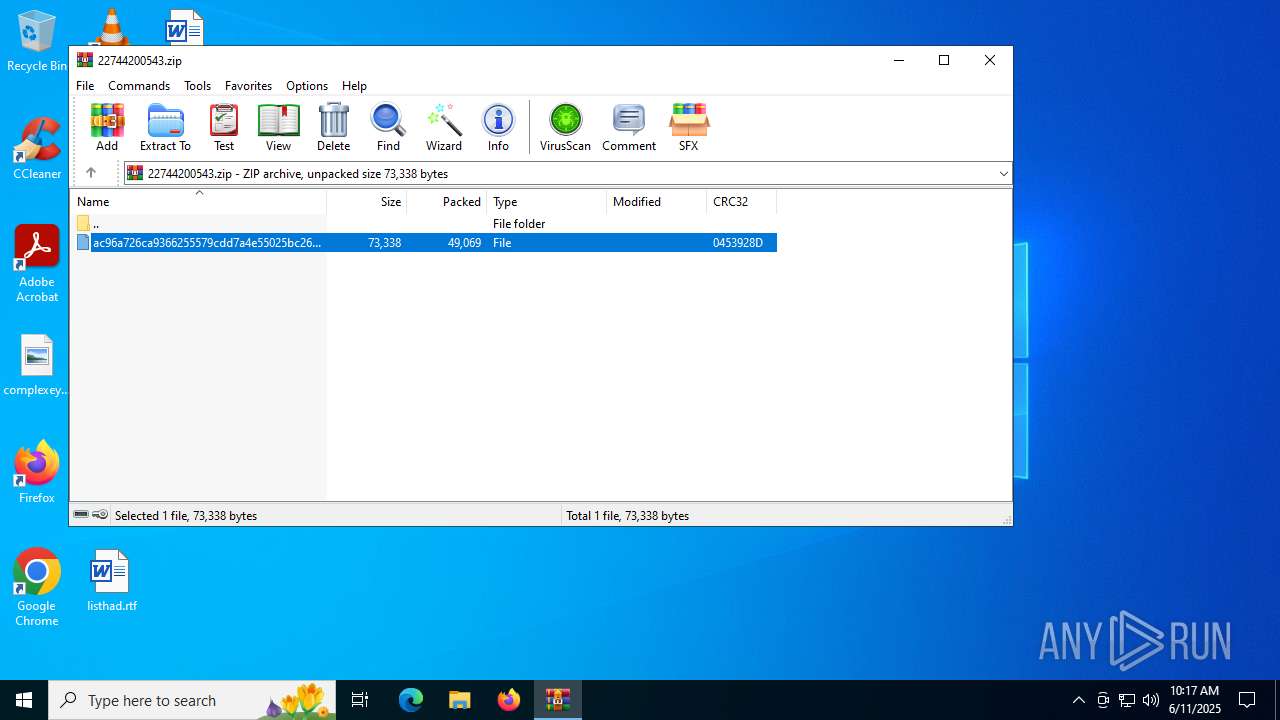
| File name: | 22744200543.zip |
| Full analysis: | https://app.any.run/tasks/c6a372de-68ac-4419-b144-e64fdd5a0725 |
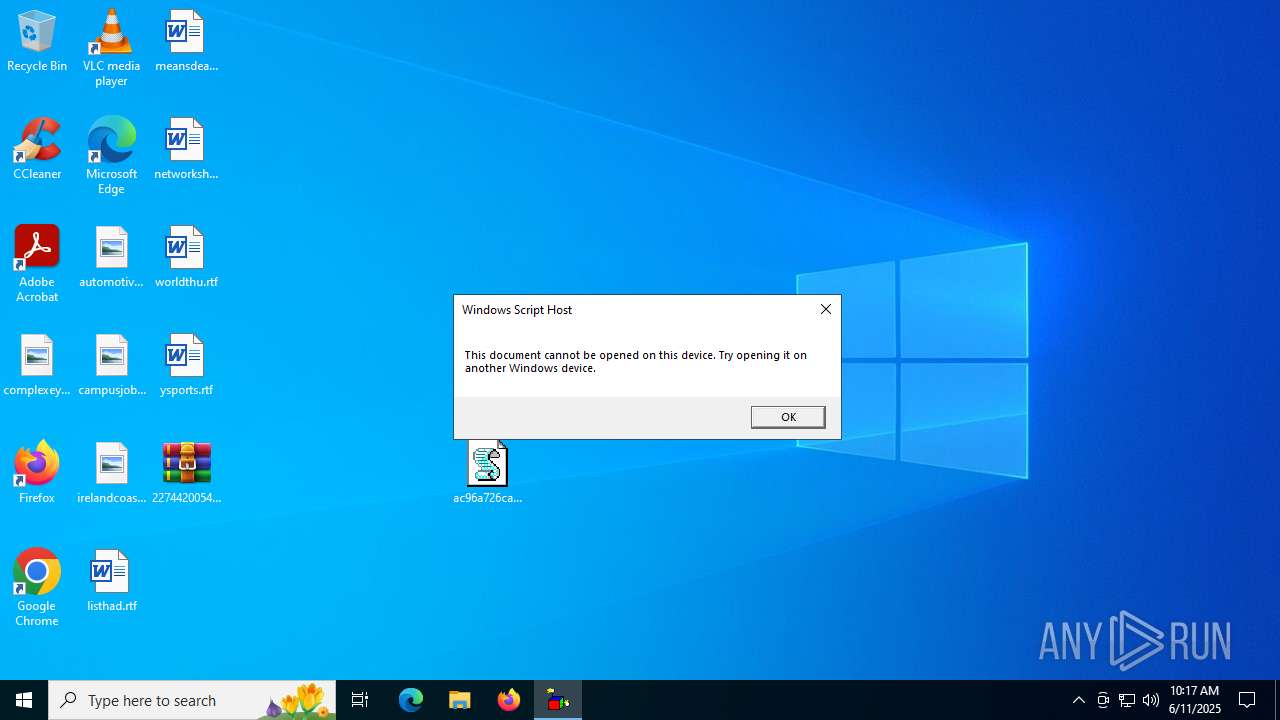
| Verdict: | Malicious activity |
| Analysis date: | June 11, 2025, 10:16:49 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 93BC53EA2E2E960F2BABC1EB30CA2DCD |
| SHA1: | FDD9977513075F1064C92A843358367598DD59F0 |
| SHA256: | 42028633E9EACE9201693E3828E0D9B1456EF72A34207BA60D68DCC1F7ABBCDE |
| SSDEEP: | 768:LcJkt5KKncuPJDiY/qtdR8VgoqOwymL1YSCs4+2tw56T8ibJVEDC8ovJ5mTNN3zv:P/KKncM7eoqnvbN6gkVE28OsP8RzAr |
MALICIOUS
Accesses environment variables (SCRIPT)
- wscript.exe (PID: 2144)
- wscript.exe (PID: 5712)
Checks whether a specified folder exists (SCRIPT)
- wscript.exe (PID: 7020)
Deletes a file (SCRIPT)
- wscript.exe (PID: 7020)
- wscript.exe (PID: 2144)
- wscript.exe (PID: 5712)
Creates a new folder (SCRIPT)
- wscript.exe (PID: 7020)
Changes Windows Defender settings
- wscript.exe (PID: 7020)
Adds process to the Windows Defender exclusion list
- wscript.exe (PID: 7020)
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 2144)
- wscript.exe (PID: 5712)
Uses Task Scheduler to run other applications
- wscript.exe (PID: 7020)
Opens a text file (SCRIPT)
- wscript.exe (PID: 7020)
- wscript.exe (PID: 5712)
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 5712)
Opens an HTTP connection (SCRIPT)
- wscript.exe (PID: 5712)
Sends HTTP request (SCRIPT)
- wscript.exe (PID: 5712)
Gets a file object corresponding to the file in a specified path (SCRIPT)
- wscript.exe (PID: 5712)
Gets TEMP folder path (SCRIPT)
- wscript.exe (PID: 5712)
Adds path to the Windows Defender exclusion list
- wscript.exe (PID: 7020)
SUSPICIOUS
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 2144)
- wscript.exe (PID: 7020)
- wscript.exe (PID: 5712)
Gets full path of the running script (SCRIPT)
- wscript.exe (PID: 2144)
- wscript.exe (PID: 7020)
Application launched itself
- wscript.exe (PID: 2144)
Runs shell command (SCRIPT)
- wscript.exe (PID: 2144)
- wscript.exe (PID: 7020)
- wscript.exe (PID: 5712)
Writes binary data to a Stream object (SCRIPT)
- wscript.exe (PID: 7020)
- wscript.exe (PID: 5712)
Likely accesses (executes) a file from the Public directory
- powershell.exe (PID: 1760)
- schtasks.exe (PID: 6104)
- ntdlg.exe (PID: 7056)
- wscript.exe (PID: 5712)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 7020)
Script adds exclusion process to Windows Defender
- wscript.exe (PID: 7020)
Checks whether a specific file exists (SCRIPT)
- wscript.exe (PID: 2144)
- wscript.exe (PID: 5712)
Uses WMI to retrieve WMI-managed resources (SCRIPT)
- wscript.exe (PID: 5712)
Creates a Stream, which may work with files, input/output devices, pipes, or TCP/IP sockets (SCRIPT)
- wscript.exe (PID: 5712)
Saves data to a binary file (SCRIPT)
- wscript.exe (PID: 5712)
Executable content was dropped or overwritten
- wscript.exe (PID: 5712)
The process executes via Task Scheduler
- wscript.exe (PID: 5712)
Executes WMI query (SCRIPT)
- wscript.exe (PID: 5712)
Connects to unusual port
- ntdlg.exe (PID: 7056)
Reads data from a binary Stream object (SCRIPT)
- wscript.exe (PID: 5712)
Script adds exclusion path to Windows Defender
- wscript.exe (PID: 7020)
INFO
Manual execution by a user
- wscript.exe (PID: 2144)
Self-termination (SCRIPT)
- wscript.exe (PID: 2144)
- wscript.exe (PID: 7020)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 5708)
- powershell.exe (PID: 4520)
- powershell.exe (PID: 1760)
- powershell.exe (PID: 4688)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 4520)
- powershell.exe (PID: 4688)
- powershell.exe (PID: 1760)
- powershell.exe (PID: 5708)
Checks proxy server information
- wscript.exe (PID: 5712)
- slui.exe (PID: 5960)
Reads the computer name
- ntdlg.exe (PID: 7056)
Checks supported languages
- ntdlg.exe (PID: 7056)
- curl.exe (PID: 5884)
Creates files or folders in the user directory
- ntdlg.exe (PID: 7056)
Execution of CURL command
- wscript.exe (PID: 5712)
Create files in a temporary directory
- curl.exe (PID: 5884)
Reads Internet Explorer settings
- wscript.exe (PID: 5712)
Reads the software policy settings
- slui.exe (PID: 5960)
Reads the machine GUID from the registry
- ntdlg.exe (PID: 7056)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:00:00 00:00:00 |
| ZipCRC: | 0x0453928d |
| ZipCompressedSize: | 49069 |
| ZipUncompressedSize: | 73338 |
| ZipFileName: | ac96a726ca9366255579cdd7a4e55025bc2606fd310599d46f982d779ec77a22 |
Total processes
165
Monitored processes
19
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1604 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\22744200543.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1760 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -Command "Add-MpPreference -ExclusionPath 'C:\Users\Public\controller\'" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1948 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2144 | "C:\WINDOWS\System32\WScript.exe" "C:\Users\admin\Desktop\ac96a726ca9366255579cdd7a4e55025bc2606fd310599d46f982d779ec77a22.wsf" | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 2148 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3644 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | ntdlg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4224 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | curl.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4372 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4520 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -Command "Add-MpPreference -ExclusionProcess 'C:\Windows\System32\clip.exe'" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4688 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -Command "Add-MpPreference -ExclusionPath 'C:\Users\admin\Desktop\ac96a726ca9366255579cdd7a4e55025bc2606fd310599d46f982d779ec77a22.wsf'" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
32 838
Read events
32 814
Write events
24
Delete events
0
Modification events
| (PID) Process: | (1604) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (1604) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (1604) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (1604) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\22744200543.zip | |||
| (PID) Process: | (1604) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1604) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1604) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1604) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1604) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (1604) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
Executable files
2
Suspicious files
4
Text files
31
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7020 | wscript.exe | C:\Windows\System32\wsf_admin_test.tmp | text | |
MD5:A5EA0AD9260B1550A14CC58D2C39B03D | SHA256:F1B2F662800122BED0FF255693DF89C4487FBDCF453D3524A42D4EC20C3D9C04 | |||
| 1604 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb1604.32706\ac96a726ca9366255579cdd7a4e55025bc2606fd310599d46f982d779ec77a22 | binary | |
MD5:3449121CA740E3B7AB353735C8263D7A | SHA256:AC96A726CA9366255579CDD7A4E55025BC2606FD310599D46F982D779EC77A22 | |||
| 7020 | wscript.exe | C:\Users\Public\ELEV | text | |
MD5:A5EA0AD9260B1550A14CC58D2C39B03D | SHA256:F1B2F662800122BED0FF255693DF89C4487FBDCF453D3524A42D4EC20C3D9C04 | |||
| 7020 | wscript.exe | C:\Users\Public\controller\controller.xml | xml | |
MD5:6C4A29AEA80E5BF23160D92E1F0F5A6B | SHA256:3F3D3C176FDD830CDA773731831004C4285CDFD92D71BECE14ED4D30DAB25463 | |||
| 5708 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_qgr3q4ia.pxq.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4520 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_r2muaz5b.xyt.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1760 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_4bju22c0.vl1.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4688 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_oboxzbth.fkk.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5708 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_amspilbs.4du.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4688 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_kfp2ulp1.xx3.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
37
DNS requests
25
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5552 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5552 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
3576 | svchost.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5712 | wscript.exe | GET | 200 | 3.167.227.102:80 | http://r10.c.lencr.org/73.crl | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 23.209.209.135:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
1512 | backgroundTaskHost.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
888 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5552 | SIHClient.exe | 20.12.23.50:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7056 | ntdlg.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 218 |
7056 | ntdlg.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 686 |
7056 | ntdlg.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 201 |
7056 | ntdlg.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 251 |
7056 | ntdlg.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 251 |