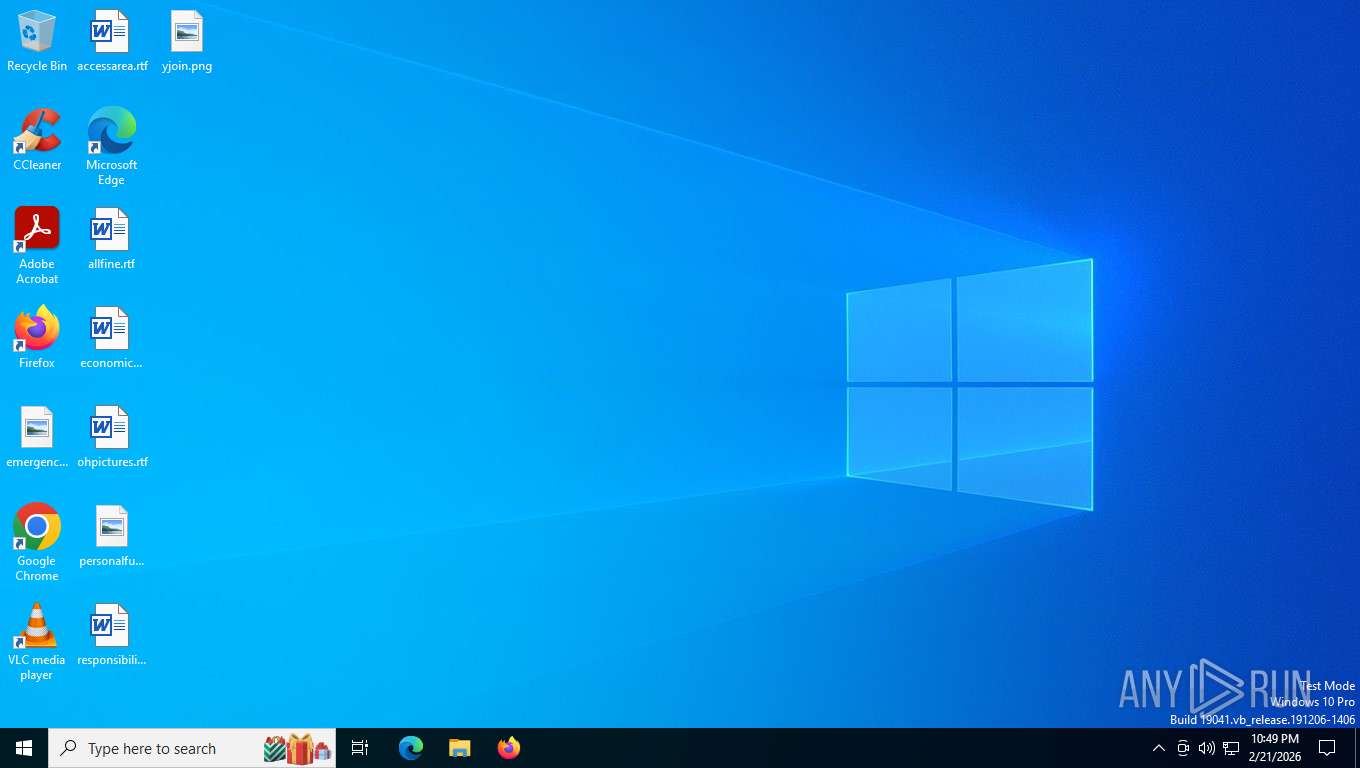
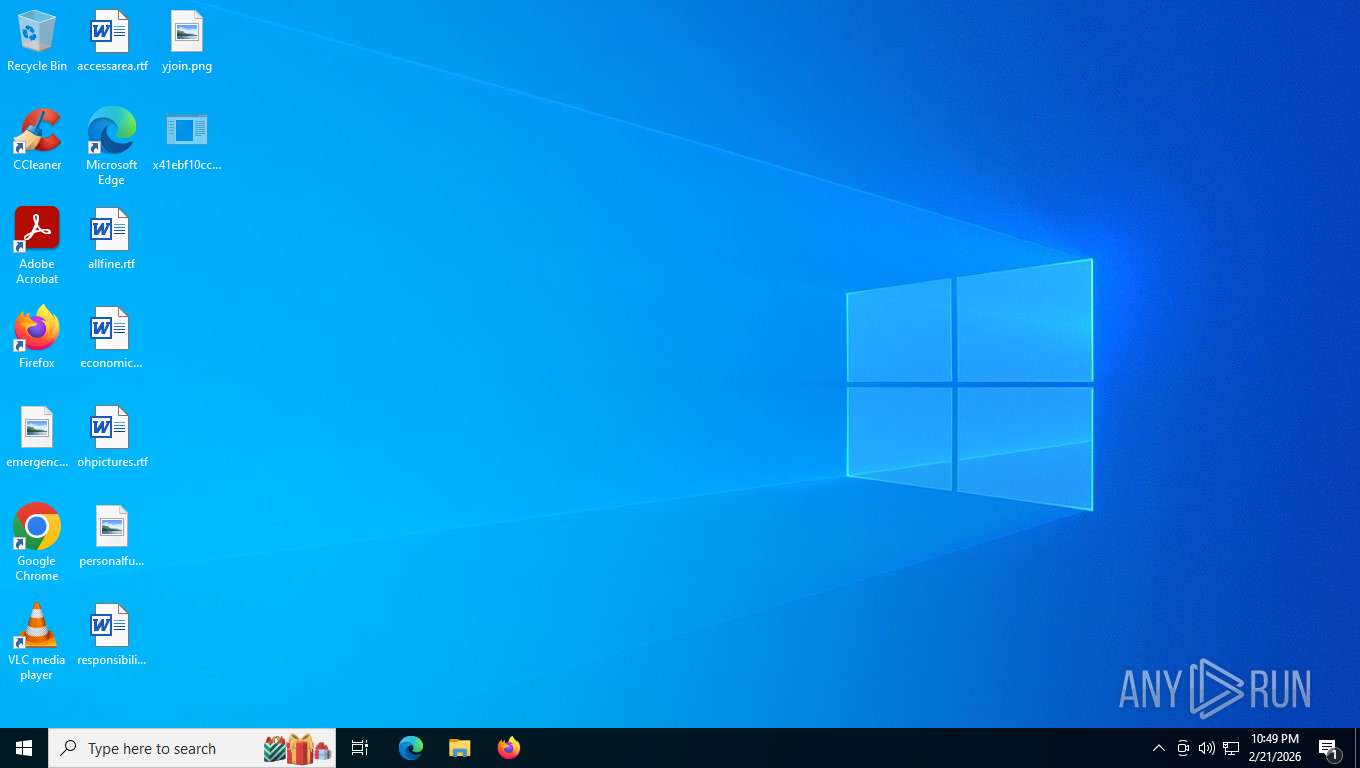
| File name: | x41ebf10cc350632f6f702e609cbb6ef067faa7b67209074484a6c18da55477b8.exe |
| Full analysis: | https://app.any.run/tasks/1d38e6a3-0a89-4235-af81-7256f2b78766 |
| Verdict: | Malicious activity |
| Threats: | DCrat, also known as Dark Crystal RAT, is a remote access trojan (RAT), which was first introduced in 2018. It is a modular malware that can be customized to perform different tasks. For instance, it can steal passwords, crypto wallet information, hijack Telegram and Steam accounts, and more. Attackers may use a variety of methods to distribute DCrat, but phishing email campaigns are the most common. |
| Analysis date: | February 22, 2026, 03:49:35 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 4 sections |
| MD5: | 3A3BC0697094B94814F58EBF3BB6D97F |
| SHA1: | 855073AE59B0DC767AF2A0813F2FD0709D655171 |
| SHA256: | 41EBF10CC350632F6F702E609CBB6EF067FAA7B67209074484A6C18DA55477B8 |
| SSDEEP: | 98304:hAfpO5iGuEfKpLDNX5LcBNO/M2AEqm6CnKdVdQbzQg+CrsqGXHDaNQcEBakTt5Jv:hr |
MALICIOUS
UAC/LUA settings modification
- x41ebf10cc350632f6f702e609cbb6ef067faa7b67209074484a6c18da55477b8.exe (PID: 2564)
- x41ebf10cc350632f6f702e609cbb6ef067faa7b67209074484a6c18da55477b8.exe (PID: 8640)
DCRAT mutex has been found
- x41ebf10cc350632f6f702e609cbb6ef067faa7b67209074484a6c18da55477b8.exe (PID: 8640)
Changes the autorun value in the registry
- x41ebf10cc350632f6f702e609cbb6ef067faa7b67209074484a6c18da55477b8.exe (PID: 8640)
Changes Windows Defender settings
- x41ebf10cc350632f6f702e609cbb6ef067faa7b67209074484a6c18da55477b8.exe (PID: 8640)
DCRAT has been detected (YARA)
- wininit.exe (PID: 7832)
Adds path to the Windows Defender exclusion list
- x41ebf10cc350632f6f702e609cbb6ef067faa7b67209074484a6c18da55477b8.exe (PID: 8640)
SUSPICIOUS
Starts CMD.EXE for commands execution
- x41ebf10cc350632f6f702e609cbb6ef067faa7b67209074484a6c18da55477b8.exe (PID: 2564)
Modifies hosts file to alter network resolution
- x41ebf10cc350632f6f702e609cbb6ef067faa7b67209074484a6c18da55477b8.exe (PID: 8640)
The process creates files with name similar to system file names
- x41ebf10cc350632f6f702e609cbb6ef067faa7b67209074484a6c18da55477b8.exe (PID: 8640)
Executed via WMI
- schtasks.exe (PID: 2780)
- schtasks.exe (PID: 9136)
- schtasks.exe (PID: 7956)
- schtasks.exe (PID: 32)
- schtasks.exe (PID: 1136)
- schtasks.exe (PID: 1784)
- schtasks.exe (PID: 1116)
- schtasks.exe (PID: 6940)
- schtasks.exe (PID: 8800)
- schtasks.exe (PID: 4424)
- schtasks.exe (PID: 7076)
- schtasks.exe (PID: 7280)
- schtasks.exe (PID: 5896)
- schtasks.exe (PID: 4404)
- schtasks.exe (PID: 7248)
- schtasks.exe (PID: 8416)
- schtasks.exe (PID: 2688)
- schtasks.exe (PID: 5588)
- schtasks.exe (PID: 772)
- schtasks.exe (PID: 7620)
- schtasks.exe (PID: 1684)
- schtasks.exe (PID: 9088)
- schtasks.exe (PID: 7532)
- schtasks.exe (PID: 4936)
- schtasks.exe (PID: 4636)
- schtasks.exe (PID: 2448)
- schtasks.exe (PID: 4020)
- schtasks.exe (PID: 7228)
- schtasks.exe (PID: 6568)
- schtasks.exe (PID: 7856)
- schtasks.exe (PID: 5600)
- schtasks.exe (PID: 796)
- schtasks.exe (PID: 5728)
- schtasks.exe (PID: 6728)
- schtasks.exe (PID: 8860)
- schtasks.exe (PID: 2600)
- schtasks.exe (PID: 6320)
- schtasks.exe (PID: 2288)
- schtasks.exe (PID: 7104)
- schtasks.exe (PID: 6108)
- schtasks.exe (PID: 7568)
- schtasks.exe (PID: 4728)
- schtasks.exe (PID: 144)
- schtasks.exe (PID: 7624)
- schtasks.exe (PID: 6784)
Creates scheduled task with highest privileges
- schtasks.exe (PID: 2780)
- schtasks.exe (PID: 32)
- schtasks.exe (PID: 9136)
- schtasks.exe (PID: 1136)
- schtasks.exe (PID: 1116)
- schtasks.exe (PID: 8800)
- schtasks.exe (PID: 7076)
- schtasks.exe (PID: 5896)
- schtasks.exe (PID: 4404)
- schtasks.exe (PID: 8416)
- schtasks.exe (PID: 772)
- schtasks.exe (PID: 5588)
- schtasks.exe (PID: 1684)
- schtasks.exe (PID: 7532)
- schtasks.exe (PID: 9088)
- schtasks.exe (PID: 7248)
- schtasks.exe (PID: 2448)
- schtasks.exe (PID: 7228)
- schtasks.exe (PID: 8860)
- schtasks.exe (PID: 7856)
- schtasks.exe (PID: 6568)
- schtasks.exe (PID: 5728)
- schtasks.exe (PID: 796)
- schtasks.exe (PID: 144)
- schtasks.exe (PID: 2600)
- schtasks.exe (PID: 2288)
- schtasks.exe (PID: 7104)
- schtasks.exe (PID: 4728)
- schtasks.exe (PID: 7568)
- schtasks.exe (PID: 7624)
Executable content was dropped or overwritten
- x41ebf10cc350632f6f702e609cbb6ef067faa7b67209074484a6c18da55477b8.exe (PID: 8640)
Script adds exclusion path to Windows Defender
- x41ebf10cc350632f6f702e609cbb6ef067faa7b67209074484a6c18da55477b8.exe (PID: 8640)
Starts POWERSHELL.EXE for commands execution
- x41ebf10cc350632f6f702e609cbb6ef067faa7b67209074484a6c18da55477b8.exe (PID: 8640)
Starts itself from another location
- x41ebf10cc350632f6f702e609cbb6ef067faa7b67209074484a6c18da55477b8.exe (PID: 8640)
INFO
Checks supported languages
- x41ebf10cc350632f6f702e609cbb6ef067faa7b67209074484a6c18da55477b8.exe (PID: 2564)
- x41ebf10cc350632f6f702e609cbb6ef067faa7b67209074484a6c18da55477b8.exe (PID: 8640)
- dllhost.exe (PID: 8028)
- SppExtComObj.exe (PID: 8492)
- wininit.exe (PID: 3664)
- Memory Compression.exe (PID: 1944)
- OfficeClickToRun.exe (PID: 3152)
- OfficeClickToRun.exe (PID: 8668)
- conhost.exe (PID: 5012)
- dllhost.exe (PID: 7876)
- Memory Compression.exe (PID: 7244)
- x41ebf10cc350632f6f702e609cbb6ef067faa7b67209074484a6c18da55477b8.exe (PID: 4516)
- cmd.exe (PID: 6828)
- SppExtComObj.exe (PID: 7824)
- wininit.exe (PID: 7832)
- cmd.exe (PID: 7360)
- x41ebf10cc350632f6f702e609cbb6ef067faa7b67209074484a6c18da55477b8.exe (PID: 5304)
- dllhost.exe (PID: 6500)
- ctfmon.exe (PID: 1188)
- conhost.exe (PID: 7212)
- csrss.exe (PID: 8408)
- csrss.exe (PID: 9188)
- dllhost.exe (PID: 8468)
- ctfmon.exe (PID: 7280)
- wininit.exe (PID: 3332)
The sample compiled with english language support
- x41ebf10cc350632f6f702e609cbb6ef067faa7b67209074484a6c18da55477b8.exe (PID: 2564)
- x41ebf10cc350632f6f702e609cbb6ef067faa7b67209074484a6c18da55477b8.exe (PID: 8640)
Process checks whether UAC notifications are on
- x41ebf10cc350632f6f702e609cbb6ef067faa7b67209074484a6c18da55477b8.exe (PID: 2564)
- x41ebf10cc350632f6f702e609cbb6ef067faa7b67209074484a6c18da55477b8.exe (PID: 8640)
Reads the machine GUID from the registry
- x41ebf10cc350632f6f702e609cbb6ef067faa7b67209074484a6c18da55477b8.exe (PID: 2564)
- x41ebf10cc350632f6f702e609cbb6ef067faa7b67209074484a6c18da55477b8.exe (PID: 8640)
- dllhost.exe (PID: 8028)
- SppExtComObj.exe (PID: 8492)
- wininit.exe (PID: 3664)
- Memory Compression.exe (PID: 1944)
- dllhost.exe (PID: 7876)
- Memory Compression.exe (PID: 7244)
- OfficeClickToRun.exe (PID: 8668)
- OfficeClickToRun.exe (PID: 3152)
- SppExtComObj.exe (PID: 7824)
- x41ebf10cc350632f6f702e609cbb6ef067faa7b67209074484a6c18da55477b8.exe (PID: 4516)
- cmd.exe (PID: 6828)
- conhost.exe (PID: 5012)
- conhost.exe (PID: 7212)
- cmd.exe (PID: 7360)
- dllhost.exe (PID: 6500)
- x41ebf10cc350632f6f702e609cbb6ef067faa7b67209074484a6c18da55477b8.exe (PID: 5304)
- wininit.exe (PID: 7832)
- ctfmon.exe (PID: 1188)
- csrss.exe (PID: 9188)
- dllhost.exe (PID: 8468)
- csrss.exe (PID: 8408)
- ctfmon.exe (PID: 7280)
- wininit.exe (PID: 3332)
Reads the computer name
- x41ebf10cc350632f6f702e609cbb6ef067faa7b67209074484a6c18da55477b8.exe (PID: 2564)
- x41ebf10cc350632f6f702e609cbb6ef067faa7b67209074484a6c18da55477b8.exe (PID: 8640)
- dllhost.exe (PID: 8028)
- Memory Compression.exe (PID: 1944)
- SppExtComObj.exe (PID: 8492)
- wininit.exe (PID: 3664)
- OfficeClickToRun.exe (PID: 3152)
- OfficeClickToRun.exe (PID: 8668)
- Memory Compression.exe (PID: 7244)
- dllhost.exe (PID: 7876)
- SppExtComObj.exe (PID: 7824)
- x41ebf10cc350632f6f702e609cbb6ef067faa7b67209074484a6c18da55477b8.exe (PID: 4516)
- cmd.exe (PID: 6828)
- wininit.exe (PID: 7832)
- conhost.exe (PID: 5012)
- conhost.exe (PID: 7212)
- cmd.exe (PID: 7360)
- x41ebf10cc350632f6f702e609cbb6ef067faa7b67209074484a6c18da55477b8.exe (PID: 5304)
- dllhost.exe (PID: 6500)
- csrss.exe (PID: 8408)
- csrss.exe (PID: 9188)
- dllhost.exe (PID: 8468)
- ctfmon.exe (PID: 7280)
- ctfmon.exe (PID: 1188)
- wininit.exe (PID: 3332)
Reads security settings of Internet Explorer
- x41ebf10cc350632f6f702e609cbb6ef067faa7b67209074484a6c18da55477b8.exe (PID: 2564)
- x41ebf10cc350632f6f702e609cbb6ef067faa7b67209074484a6c18da55477b8.exe (PID: 8640)
Process checks computer location settings
- x41ebf10cc350632f6f702e609cbb6ef067faa7b67209074484a6c18da55477b8.exe (PID: 2564)
- x41ebf10cc350632f6f702e609cbb6ef067faa7b67209074484a6c18da55477b8.exe (PID: 8640)
Creates files in the program directory
- x41ebf10cc350632f6f702e609cbb6ef067faa7b67209074484a6c18da55477b8.exe (PID: 8640)
Launching a file from a Registry key
- x41ebf10cc350632f6f702e609cbb6ef067faa7b67209074484a6c18da55477b8.exe (PID: 8640)
Manual execution by a user
- dllhost.exe (PID: 8028)
- SppExtComObj.exe (PID: 8492)
- wininit.exe (PID: 3664)
- Memory Compression.exe (PID: 1944)
- OfficeClickToRun.exe (PID: 3152)
- Memory Compression.exe (PID: 7244)
- conhost.exe (PID: 5012)
- dllhost.exe (PID: 7876)
- OfficeClickToRun.exe (PID: 8668)
- cmd.exe (PID: 6828)
- wininit.exe (PID: 7832)
- SppExtComObj.exe (PID: 7824)
- x41ebf10cc350632f6f702e609cbb6ef067faa7b67209074484a6c18da55477b8.exe (PID: 4516)
- cmd.exe (PID: 7360)
- x41ebf10cc350632f6f702e609cbb6ef067faa7b67209074484a6c18da55477b8.exe (PID: 5304)
- dllhost.exe (PID: 6500)
- ctfmon.exe (PID: 1188)
- conhost.exe (PID: 7212)
- csrss.exe (PID: 8408)
- csrss.exe (PID: 9188)
- dllhost.exe (PID: 8468)
- ctfmon.exe (PID: 7280)
.NET Reactor protector has been detected
- wininit.exe (PID: 7832)
Drops script file
- powershell.exe (PID: 7120)
- powershell.exe (PID: 5152)
- powershell.exe (PID: 144)
- powershell.exe (PID: 1352)
- powershell.exe (PID: 6320)
- powershell.exe (PID: 5528)
- powershell.exe (PID: 1960)
- powershell.exe (PID: 5424)
- powershell.exe (PID: 8264)
- powershell.exe (PID: 1860)
- powershell.exe (PID: 6628)
- powershell.exe (PID: 7296)
- powershell.exe (PID: 7620)
- powershell.exe (PID: 7988)
- powershell.exe (PID: 8700)
- powershell.exe (PID: 7856)
There is functionality for taking screenshot (YARA)
- wininit.exe (PID: 7832)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 5528)
- powershell.exe (PID: 5152)
- powershell.exe (PID: 7988)
- powershell.exe (PID: 6628)
- powershell.exe (PID: 144)
- powershell.exe (PID: 8264)
- powershell.exe (PID: 7296)
- powershell.exe (PID: 1860)
- powershell.exe (PID: 6320)
- powershell.exe (PID: 1352)
- powershell.exe (PID: 1960)
- powershell.exe (PID: 8700)
- powershell.exe (PID: 7620)
- powershell.exe (PID: 5424)
- powershell.exe (PID: 7120)
- powershell.exe (PID: 7856)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 5528)
- powershell.exe (PID: 5424)
- powershell.exe (PID: 144)
- powershell.exe (PID: 1860)
- powershell.exe (PID: 7620)
- powershell.exe (PID: 7296)
- powershell.exe (PID: 6320)
- powershell.exe (PID: 1352)
- powershell.exe (PID: 8700)
- powershell.exe (PID: 1960)
- powershell.exe (PID: 7856)
- powershell.exe (PID: 5152)
- powershell.exe (PID: 7120)
- powershell.exe (PID: 8264)
- powershell.exe (PID: 6628)
- powershell.exe (PID: 7988)
Checks proxy server information
- slui.exe (PID: 9620)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
DcRat
(PID) Process(7832) wininit.exe
C2 (1)http://batyatj6.beget.tech/a4f88cb8.php
Options
MutexDCR_MUTEX-lXdarsMtTvN6gvLVC7rX
Debugfalse
ServerConfigReplacementTable
0<
1$
5@
6
9(
p)
l^
N_
a;
Y&
d|
i.
W>
H#
k,
R*
Z~
m%
S`
I!
A-
PluginConfigReplacementTable
1%
2`
3_
5^
Q>
X;
B(
F,
r*
T.
U|
R$
d@
C~
E
G-
H!
J<
V#
n&
Z)
GetWebcamsfalse
SleepTimeout5
InactivityTimeout2
CacheStorageRegistry
AutoRunFull
StealerConfig
savebrowsersdatatosinglefiletrue
ignorepartiallyemptydatatrue
cookiestrue
passwordstrue
formstrue
cctrue
historytrue
telegramtrue
steamtrue
discordtrue
filezillatrue
screenshottrue
clipboardtrue
sysinfotrue
searchpath%UsersFolder% - Fast
StealerEnabledtrue
StealerOptionsfalse
SelfDeletefalse
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:07:13 22:47:16+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 104448 |
| InitializedDataSize: | 1973248 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xcd2f |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.15.2.0 |
| ProductVersionNumber: | 5.15.2.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| FileVersion: | 5.15.2.0 |
| OriginalFileName: | libGLESv2.dll |
| ProductName: | libGLESv2 |
| ProductVersion: | 5.15.2.0 |
Total processes
245
Monitored processes
105
Malicious processes
4
Suspicious processes
30
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 32 | schtasks.exe /create /tn "OfficeClickToRun" /sc ONLOGON /tr "'C:\Windows\Resources\Themes\OfficeClickToRun.exe'" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 144 | schtasks.exe /create /tn "SearchApp" /sc ONLOGON /tr "'C:\Windows\LiveKernelReports\SearchApp.exe'" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 144 | "powershell" -Command Add-MpPreference -ExclusionPath 'C:\found.000\dir0001.chk\cmd.exe' | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | x41ebf10cc350632f6f702e609cbb6ef067faa7b67209074484a6c18da55477b8.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 772 | schtasks.exe /create /tn "winrshost" /sc ONLOGON /tr "'C:\Recovery\Logs\winrshost.exe'" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 796 | schtasks.exe /create /tn "dllhost" /sc ONLOGON /tr "'C:\found.000\dir0000.chk\dllhost.exe'" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1116 | schtasks.exe /create /tn "wininitw" /sc MINUTE /mo 10 /tr "'C:\Program Files\rempl\Logs\wininit.exe'" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1136 | schtasks.exe /create /tn "OfficeClickToRunO" /sc MINUTE /mo 10 /tr "'C:\Windows\Resources\Themes\OfficeClickToRun.exe'" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1188 | "C:\Program Files\Windows Defender\Offline\ctfmon.exe" | C:\Program Files\Windows Defender\Offline\ctfmon.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 5.15.2.0 Modules
| |||||||||||||||
| 1352 | "powershell" -Command Add-MpPreference -ExclusionPath 'C:\Program Files (x86)\Mozilla Maintenance Service\x41ebf10cc350632f6f702e609cbb6ef067faa7b67209074484a6c18da55477b8.exe' | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | x41ebf10cc350632f6f702e609cbb6ef067faa7b67209074484a6c18da55477b8.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1656 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
92 911
Read events
92 871
Write events
40
Delete events
0
Modification events
| (PID) Process: | (2564) x41ebf10cc350632f6f702e609cbb6ef067faa7b67209074484a6c18da55477b8.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | EnableLUA |
Value: 0 | |||
| (PID) Process: | (8640) x41ebf10cc350632f6f702e609cbb6ef067faa7b67209074484a6c18da55477b8.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | EnableLUA |
Value: 0 | |||
| (PID) Process: | (8640) x41ebf10cc350632f6f702e609cbb6ef067faa7b67209074484a6c18da55477b8.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | ConsentPromptBehaviorAdmin |
Value: 0 | |||
| (PID) Process: | (8640) x41ebf10cc350632f6f702e609cbb6ef067faa7b67209074484a6c18da55477b8.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | PromptOnSecureDesktop |
Value: 0 | |||
| (PID) Process: | (8640) x41ebf10cc350632f6f702e609cbb6ef067faa7b67209074484a6c18da55477b8.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\9b90c88d90d65a05eea12d70abda15b8 |
| Operation: | write | Name: | 9b90c88d90d65a05eea12d70abda15b8 |
Value: 9b90c88d90d65a05eea12d70abda15b8 | |||
| (PID) Process: | (8640) x41ebf10cc350632f6f702e609cbb6ef067faa7b67209074484a6c18da55477b8.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Action Center\Checks\{C8E6F269-B90A-4053-A3BE-499AFCEC98C4}.check.0 |
| Operation: | write | Name: | CheckSetting |
Value: 23004100430042006C006F00620000000000000000000000010000000000000000000000 | |||
| (PID) Process: | (8640) x41ebf10cc350632f6f702e609cbb6ef067faa7b67209074484a6c18da55477b8.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | dllhost |
Value: "C:\Program Files\Common Files\Services\dllhost.exe" | |||
| (PID) Process: | (8640) x41ebf10cc350632f6f702e609cbb6ef067faa7b67209074484a6c18da55477b8.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | dllhost |
Value: "C:\Program Files\Common Files\Services\dllhost.exe" | |||
| (PID) Process: | (8640) x41ebf10cc350632f6f702e609cbb6ef067faa7b67209074484a6c18da55477b8.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | OfficeClickToRun |
Value: "C:\Windows\Resources\Themes\OfficeClickToRun.exe" | |||
| (PID) Process: | (8640) x41ebf10cc350632f6f702e609cbb6ef067faa7b67209074484a6c18da55477b8.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | OfficeClickToRun |
Value: "C:\Windows\Resources\Themes\OfficeClickToRun.exe" | |||
Executable files
24
Suspicious files
0
Text files
0
Unknown types
112
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8640 | x41ebf10cc350632f6f702e609cbb6ef067faa7b67209074484a6c18da55477b8.exe | C:\Program Files\rempl\Logs\wininit.exe | executable | |
MD5:3A3BC0697094B94814F58EBF3BB6D97F | SHA256:41EBF10CC350632F6F702E609CBB6EF067FAA7B67209074484A6C18DA55477B8 | |||
| 8640 | x41ebf10cc350632f6f702e609cbb6ef067faa7b67209074484a6c18da55477b8.exe | C:\Program Files\Reference Assemblies\SppExtComObj.exe | executable | |
MD5:3A3BC0697094B94814F58EBF3BB6D97F | SHA256:41EBF10CC350632F6F702E609CBB6EF067FAA7B67209074484A6C18DA55477B8 | |||
| 8640 | x41ebf10cc350632f6f702e609cbb6ef067faa7b67209074484a6c18da55477b8.exe | C:\Program Files\Reference Assemblies\e1ef82546f0b02 | binary | |
MD5:F2CA21BA6457B127ACB2613A396A510B | SHA256:4819A16C68462B4F4A412DDC266B54C1A7F525B3F95C8850057D1B1F82954279 | |||
| 8640 | x41ebf10cc350632f6f702e609cbb6ef067faa7b67209074484a6c18da55477b8.exe | C:\Program Files\Mozilla Firefox\gmp-clearkey\0.1\1a5d5b8dcee3d8 | binary | |
MD5:0E9FCBB2D4AAD2891A6EDBF0323316F5 | SHA256:D6547EC1E34148F3A30FE3AA3D1A57082ACEF53BF29FC2B7E47B924493470609 | |||
| 8640 | x41ebf10cc350632f6f702e609cbb6ef067faa7b67209074484a6c18da55477b8.exe | C:\Windows\Resources\Themes\e6c9b481da804f | binary | |
MD5:6F4EDBA5DBA2E37E7C41847AEE21F294 | SHA256:87818F2666E2879108A65E34C91989420013ACAC8A9A59FC7D1418153DA1F81E | |||
| 8640 | x41ebf10cc350632f6f702e609cbb6ef067faa7b67209074484a6c18da55477b8.exe | C:\Program Files (x86)\Mozilla Maintenance Service\x41ebf10cc350632f6f702e609cbb6ef067faa7b67209074484a6c18da55477b8.exe | executable | |
MD5:3A3BC0697094B94814F58EBF3BB6D97F | SHA256:41EBF10CC350632F6F702E609CBB6EF067FAA7B67209074484A6C18DA55477B8 | |||
| 8640 | x41ebf10cc350632f6f702e609cbb6ef067faa7b67209074484a6c18da55477b8.exe | C:\Recovery\Logs\winrshost.exe | executable | |
MD5:3A3BC0697094B94814F58EBF3BB6D97F | SHA256:41EBF10CC350632F6F702E609CBB6EF067FAA7B67209074484A6C18DA55477B8 | |||
| 8640 | x41ebf10cc350632f6f702e609cbb6ef067faa7b67209074484a6c18da55477b8.exe | C:\Windows\Prefetch\cmd.exe | executable | |
MD5:3A3BC0697094B94814F58EBF3BB6D97F | SHA256:41EBF10CC350632F6F702E609CBB6EF067FAA7B67209074484A6C18DA55477B8 | |||
| 8640 | x41ebf10cc350632f6f702e609cbb6ef067faa7b67209074484a6c18da55477b8.exe | C:\Program Files\Common Files\Services\5940a34987c991 | binary | |
MD5:91BC1FFB35157CC2D644AE409DD3F9FA | SHA256:C1D07BD6D36D09652E40EEECF9F74DD043B2EFA210C25B9F8E1ECAC21CAC8A06 | |||
| 8640 | x41ebf10cc350632f6f702e609cbb6ef067faa7b67209074484a6c18da55477b8.exe | C:\Recovery\Logs\c6e63a1ebc0cef | binary | |
MD5:C608891A1B8B86DA68A875D71EFE693B | SHA256:7E93BBAE1628A9D27EBDEA9720D83FCF9823C182DA15B3BEC3A01F7B18E4799A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
24
DNS requests
11
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
3348 | svchost.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 72.246.29.11:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3348 | svchost.exe | GET | 200 | 72.246.29.11:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 200 | 72.246.29.11:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4196 | slui.exe | POST | 500 | 48.192.1.65:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | binary | 512 b | whitelisted |
— | — | POST | 500 | 48.192.1.65:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | binary | 512 b | whitelisted |
3292 | svchost.exe | GET | 200 | 72.246.29.11:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Time-Stamp%20PCA%202010(1).crl | unknown | — | — | whitelisted |
3292 | svchost.exe | GET | 200 | 72.246.29.11:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
3348 | svchost.exe | 23.216.77.28:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 23.216.77.28:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
6768 | MoUsoCoreWorker.exe | 23.216.77.28:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 72.246.29.11:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
3348 | svchost.exe | 72.246.29.11:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 72.246.29.11:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
3348 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |