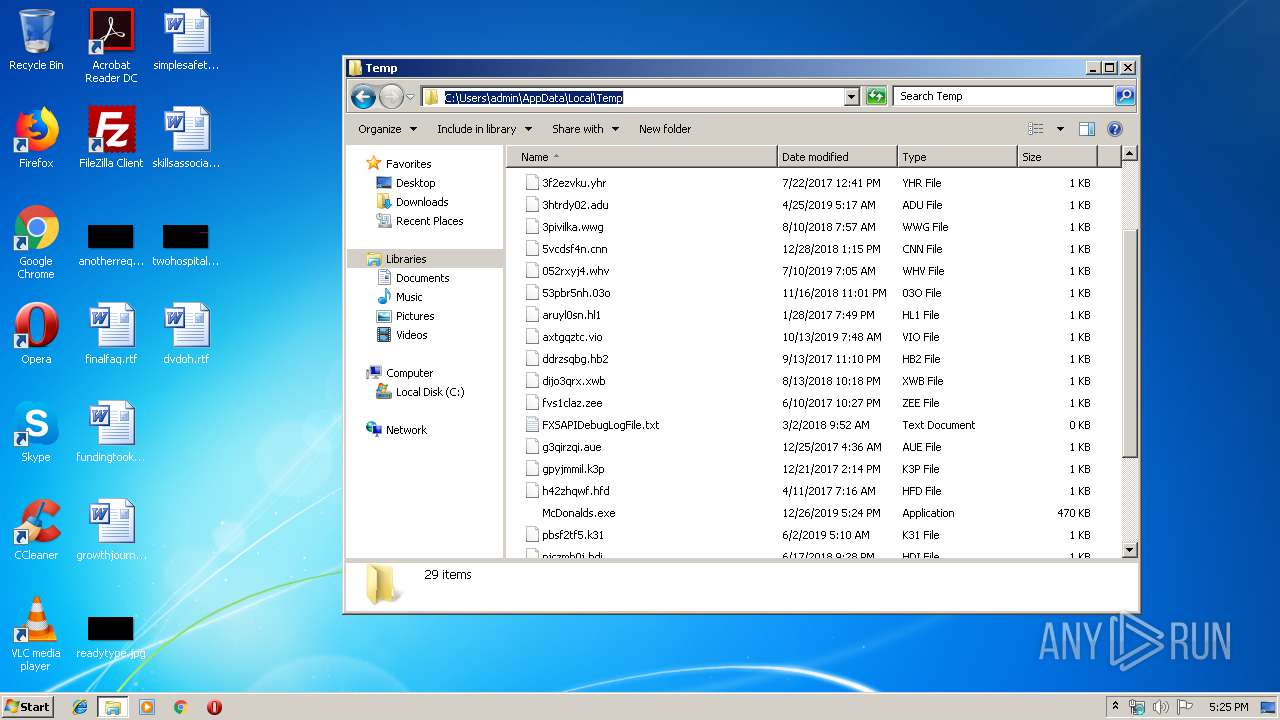
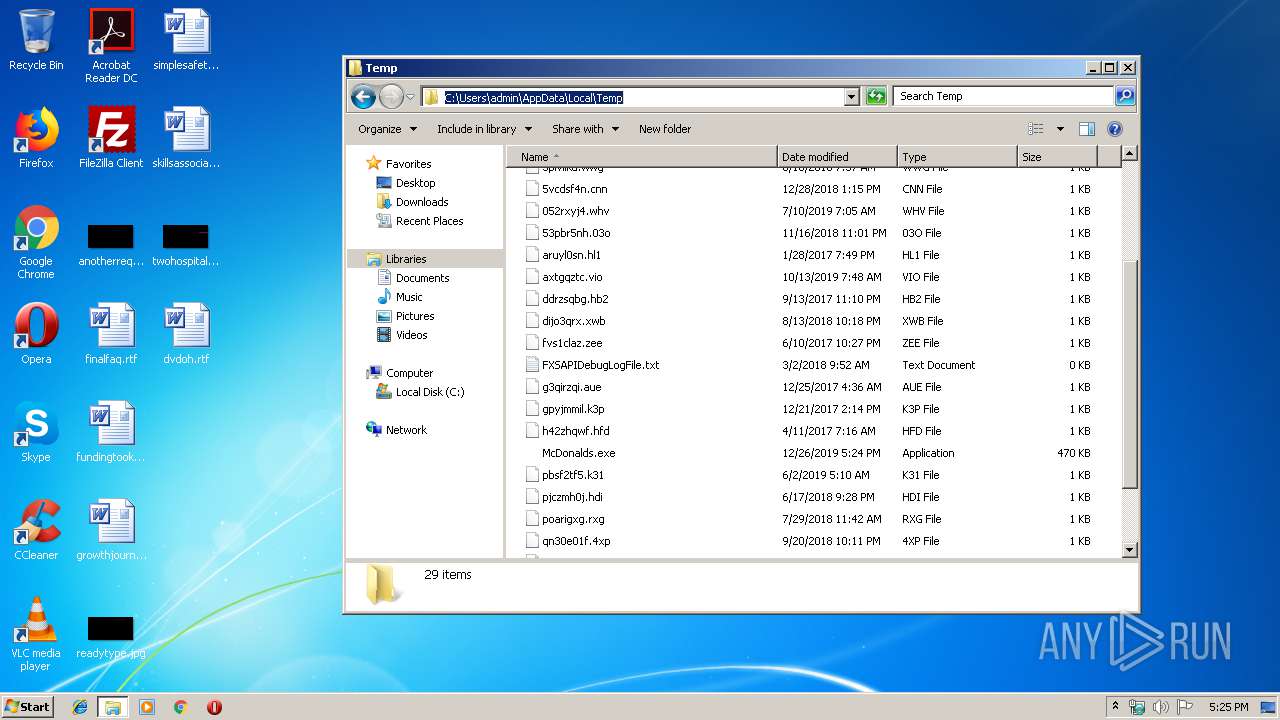
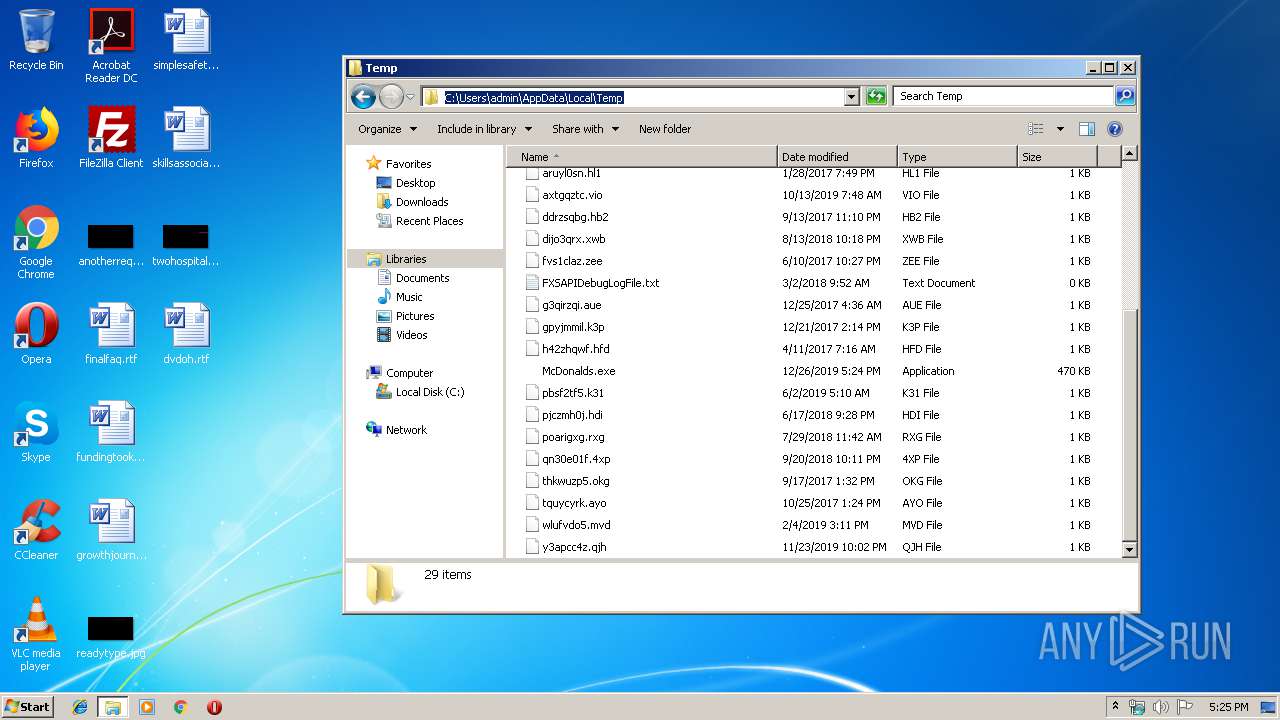
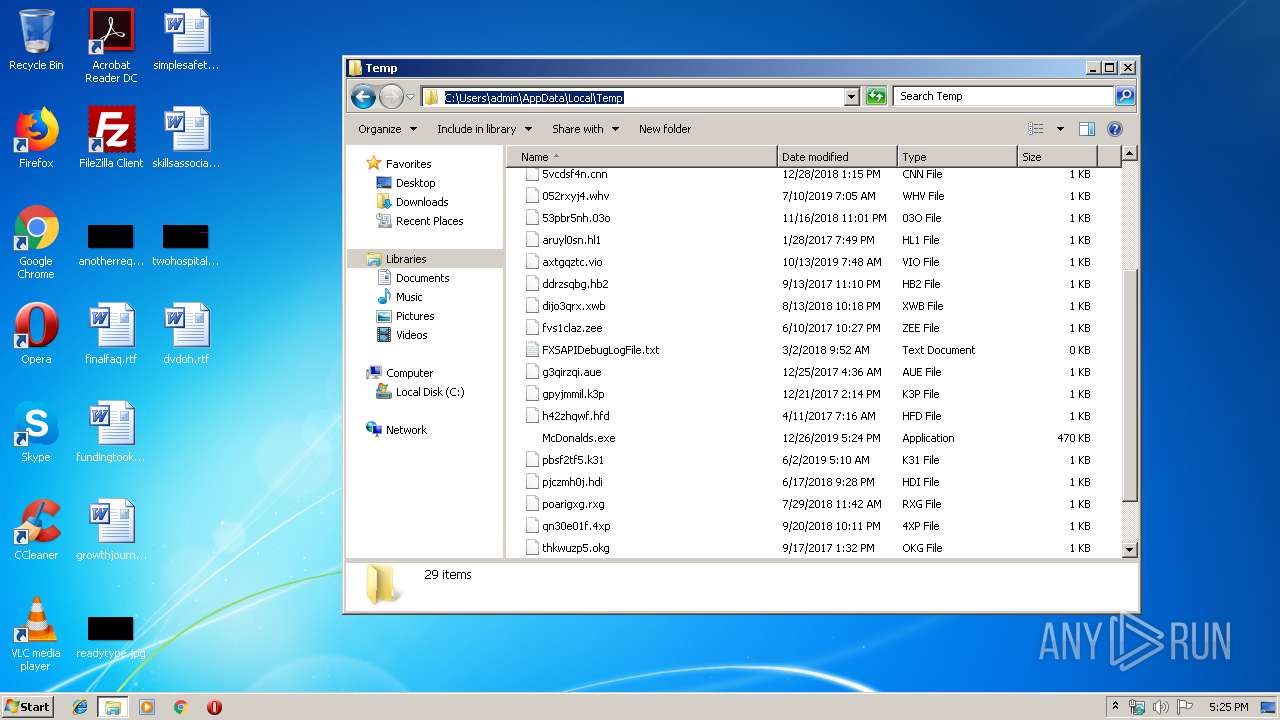
| File name: | McDonalds.exe |
| Full analysis: | https://app.any.run/tasks/313e3ab5-70d8-4bb4-8087-4b24f162312f |
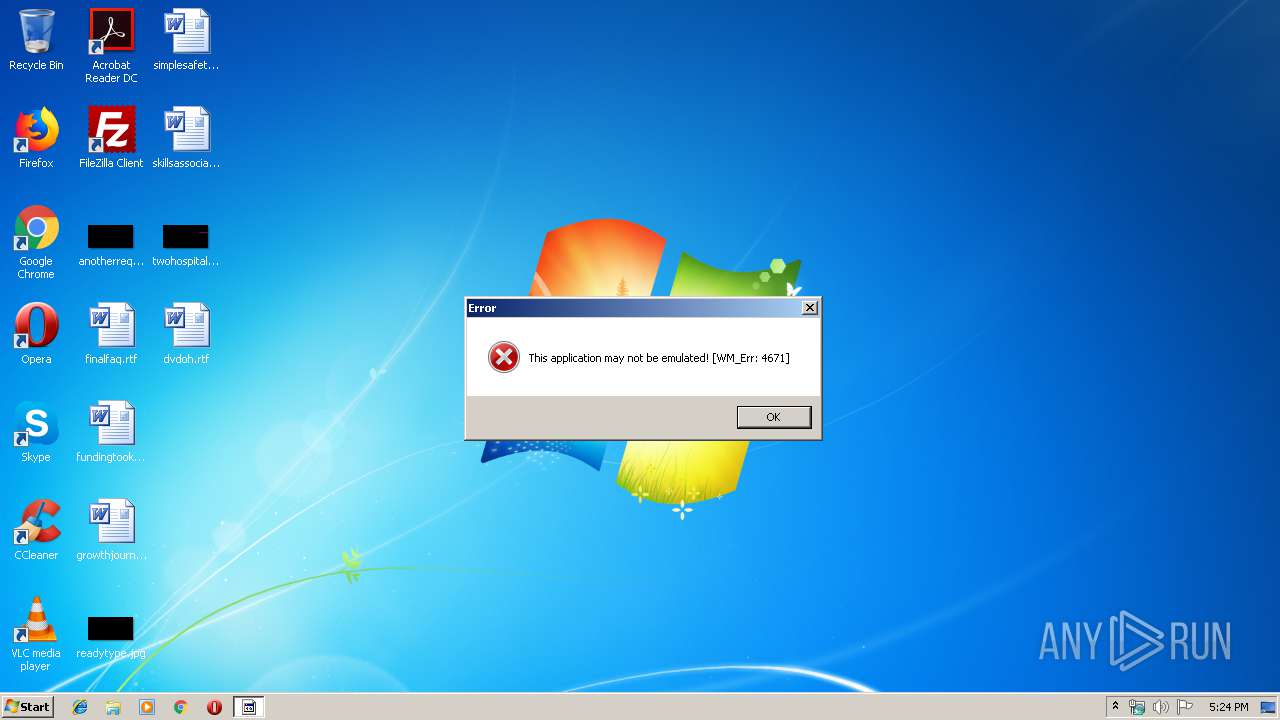
| Verdict: | Malicious activity |
| Analysis date: | December 26, 2019, 17:24:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 7ABAD3E8C2CC19D549F38D8696C7B3EB |
| SHA1: | 872CA1FD0FB209041B04433DA3DF40AA3EF6C4D0 |
| SHA256: | 41EA6377FA1A8F8058D580FE1A6026158CFCF9B6A5AEAEB4C300477A1296A84D |
| SSDEEP: | 6144:R9WCfbPmAuC8vLFM7e6KJZzx2/tKi78Y/e9/6XS56wq2ddDFJbtJr8XvjKpR:R9dfuG36ZzxwPWyXhwXTD/zYfjk |
MALICIOUS
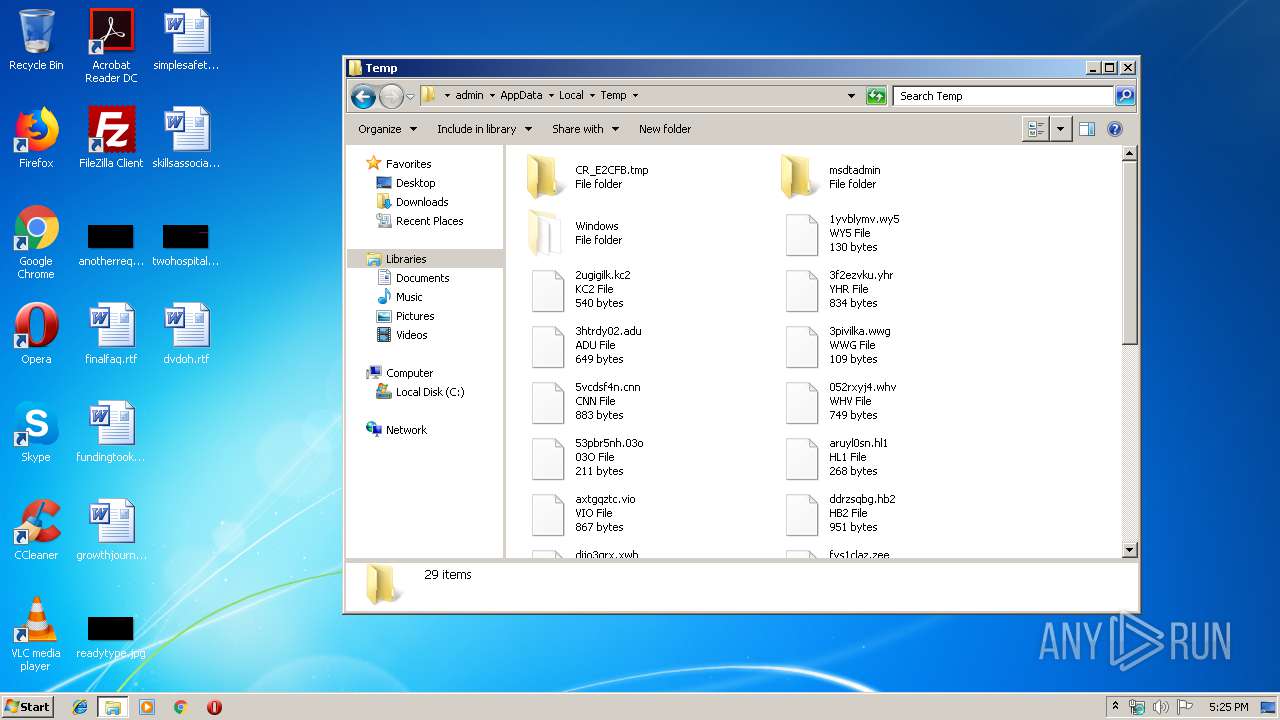
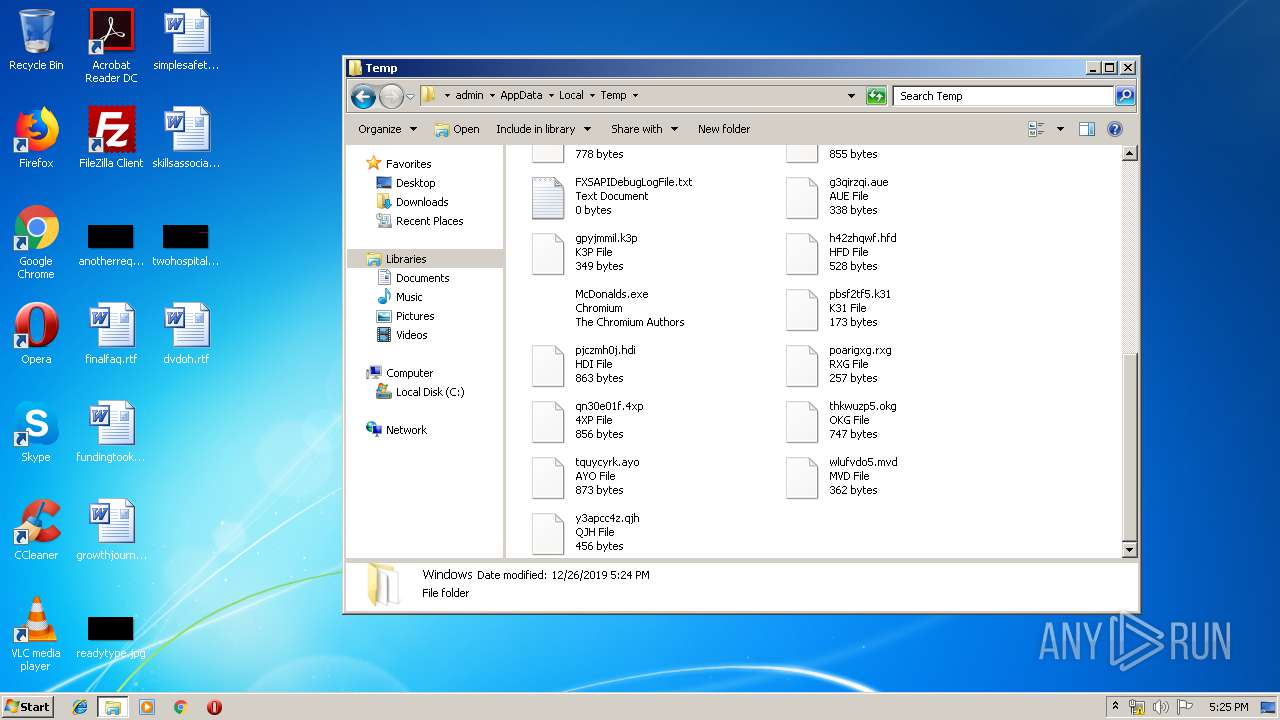
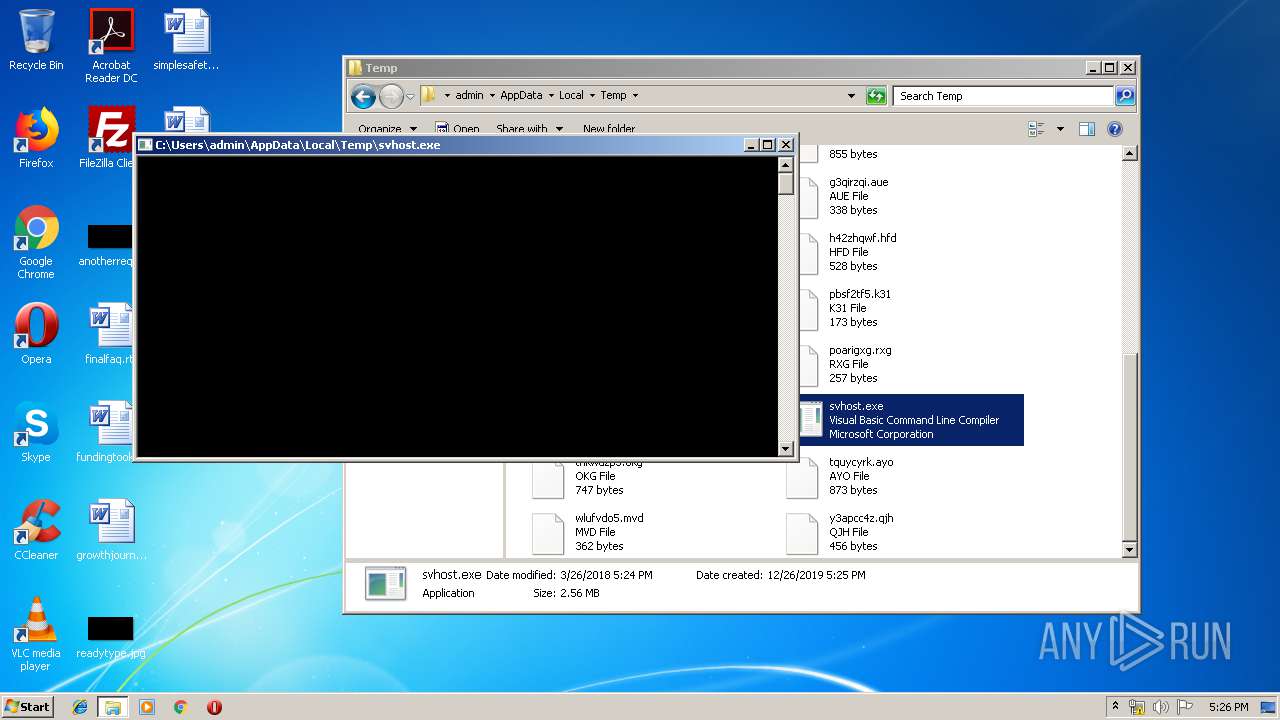
Application was dropped or rewritten from another process
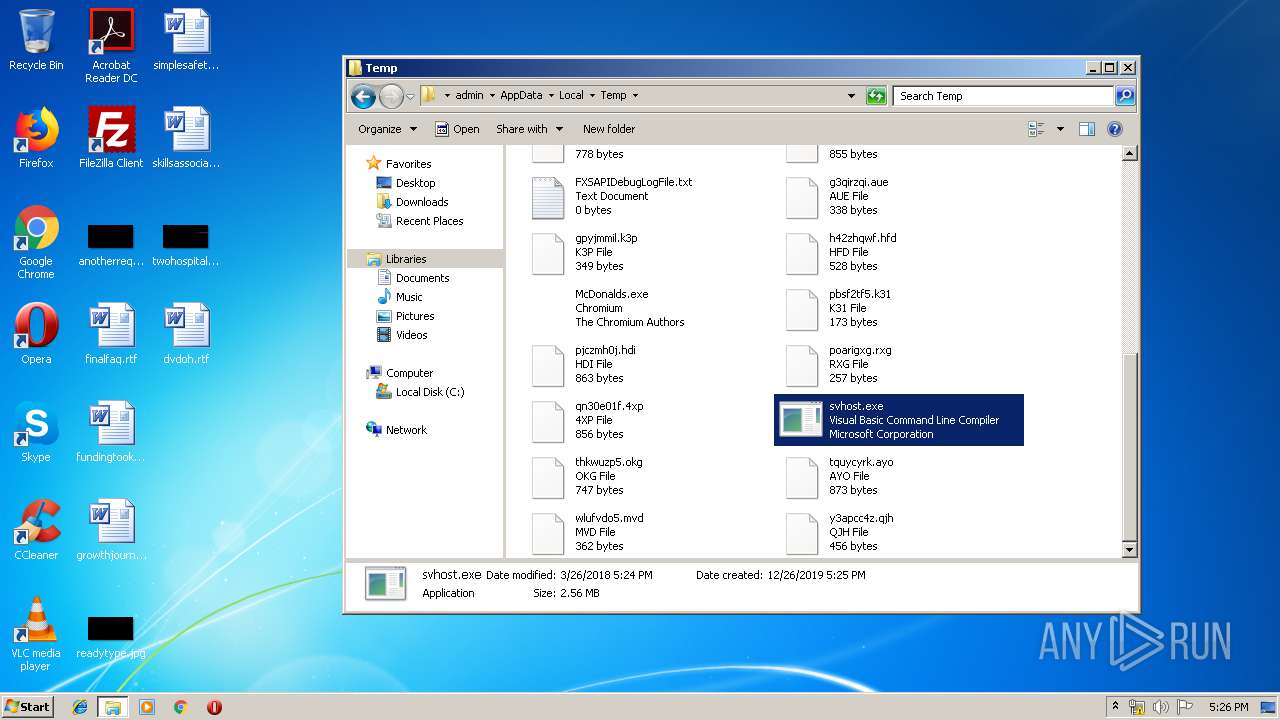
- svhost.exe (PID: 2140)
- svhost.exe (PID: 1296)
- svhost.exe (PID: 1472)
- svhost.exe (PID: 4088)
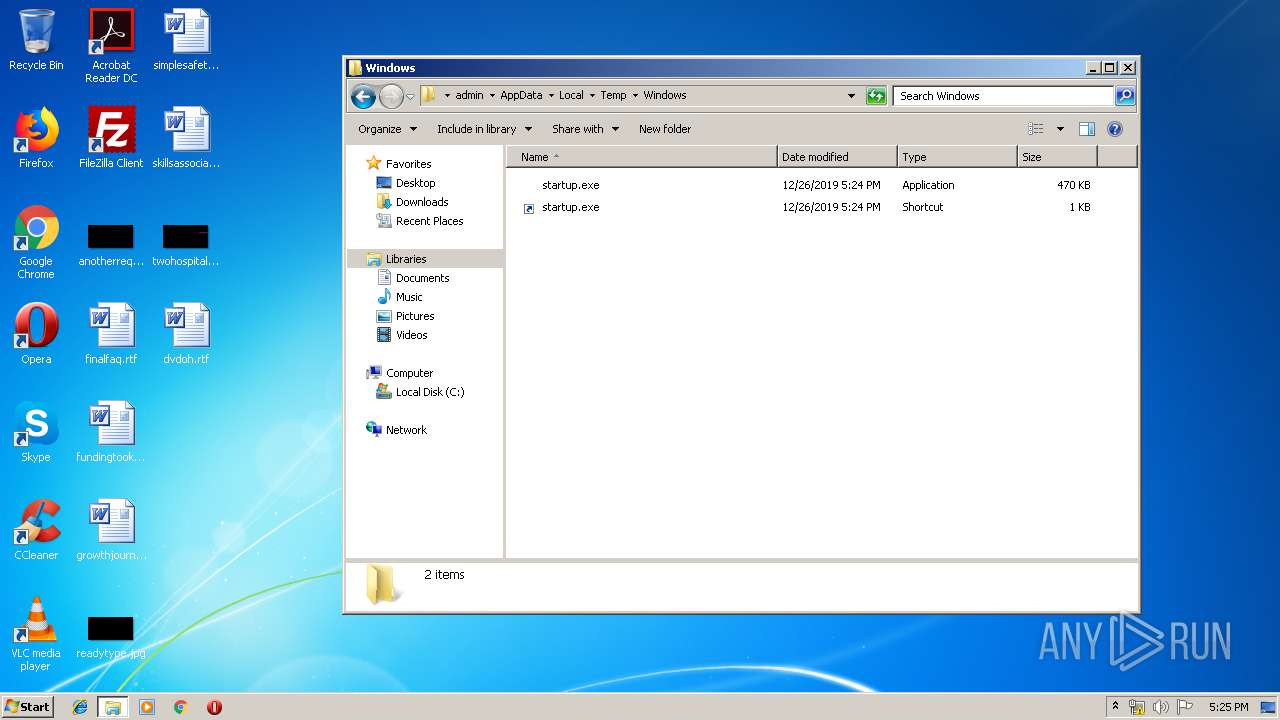
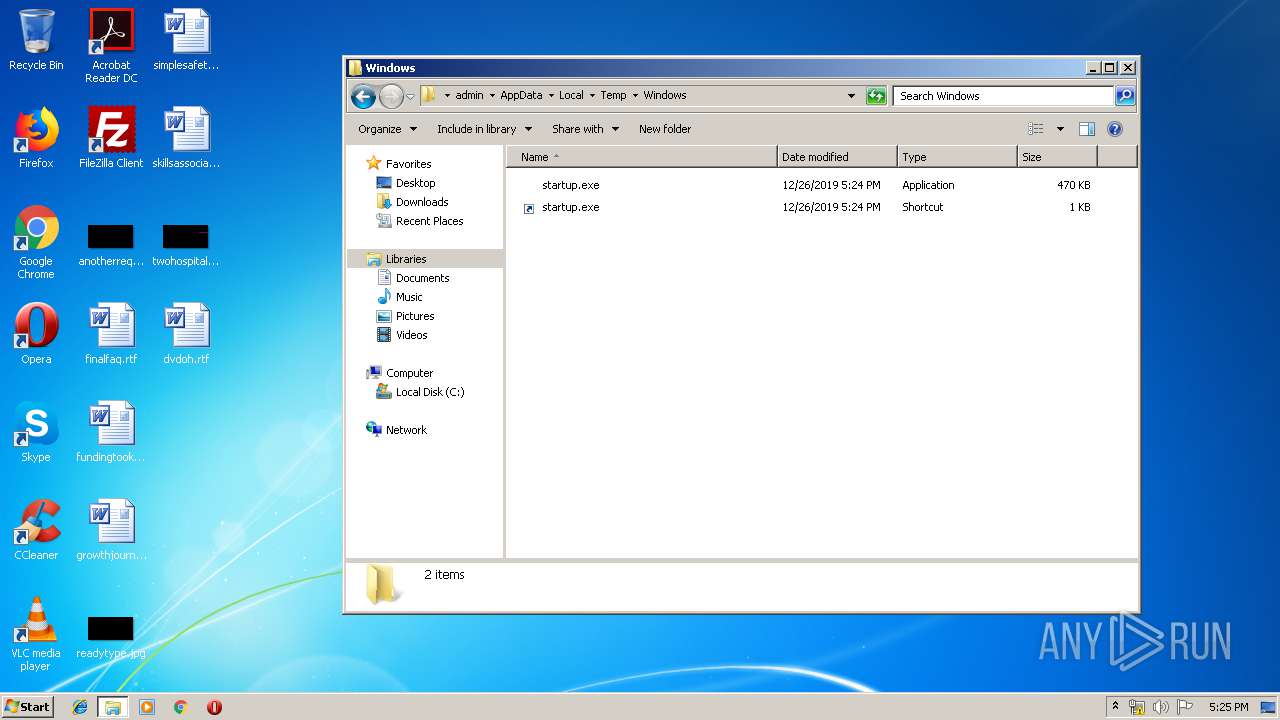
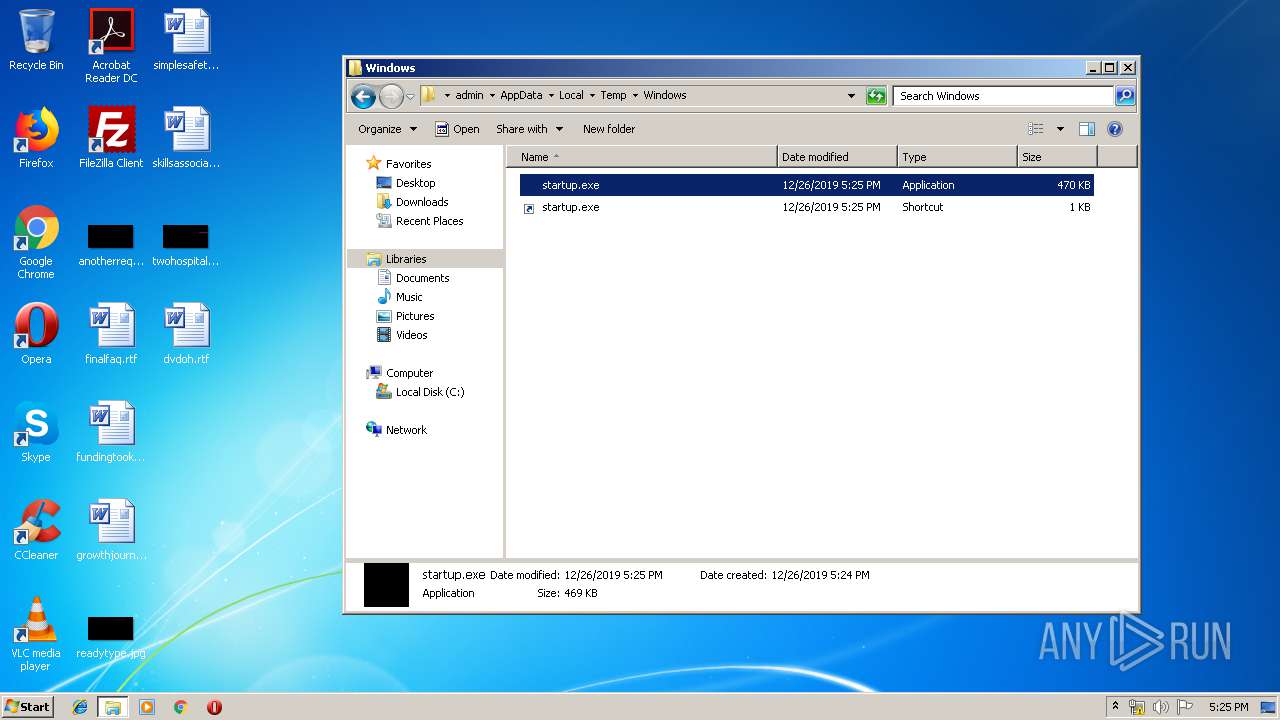
Writes to a start menu file
- McDonalds.exe (PID: 944)
- startup.exe (PID: 2280)
- McDonalds.exe (PID: 2376)
SUSPICIOUS
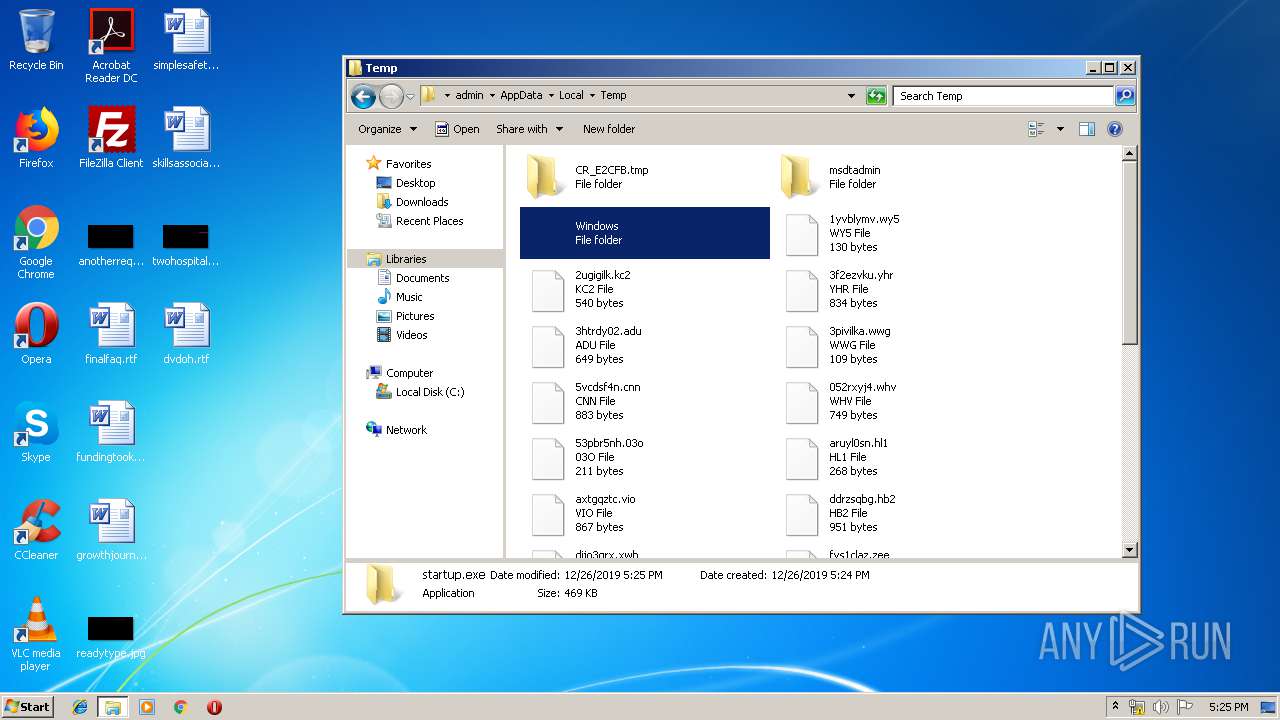
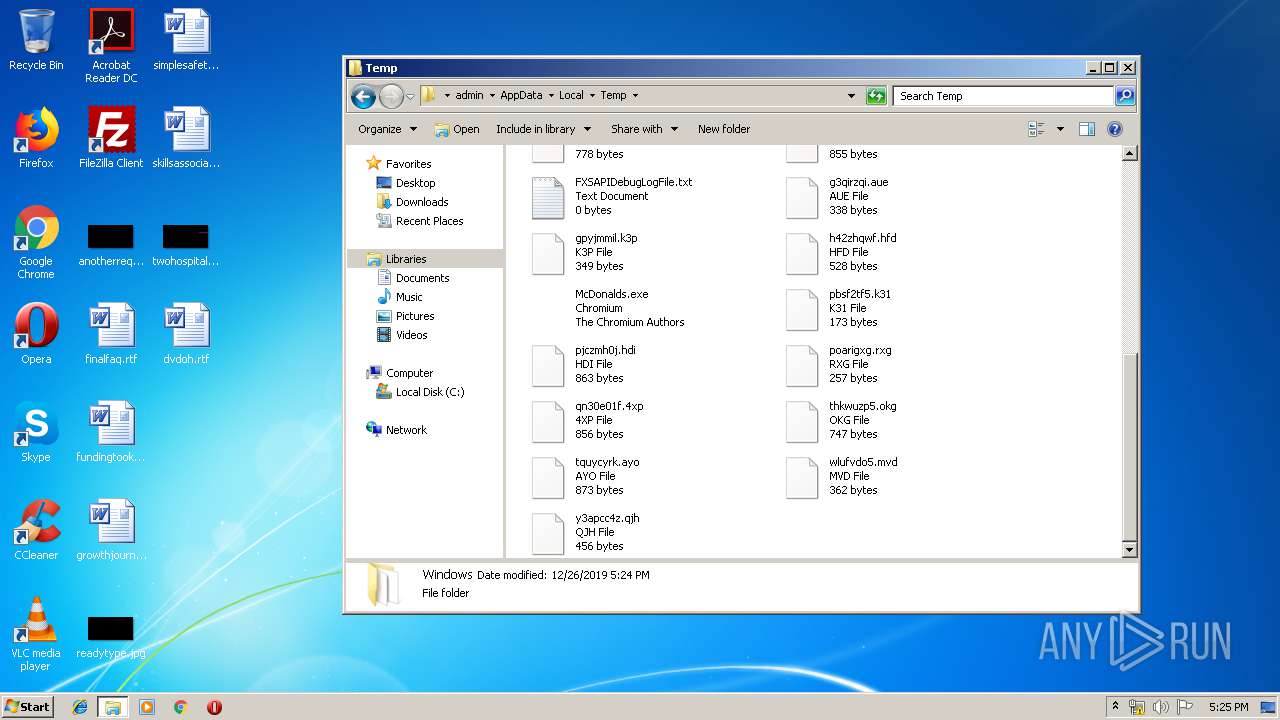
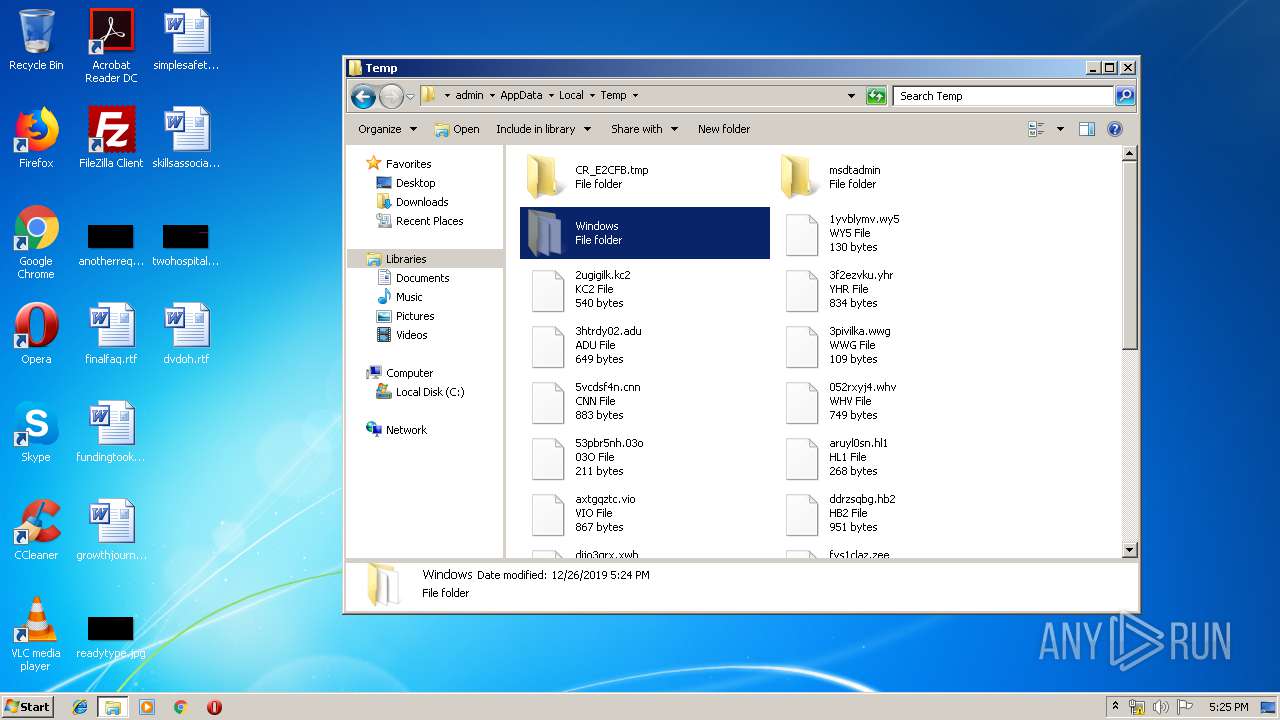
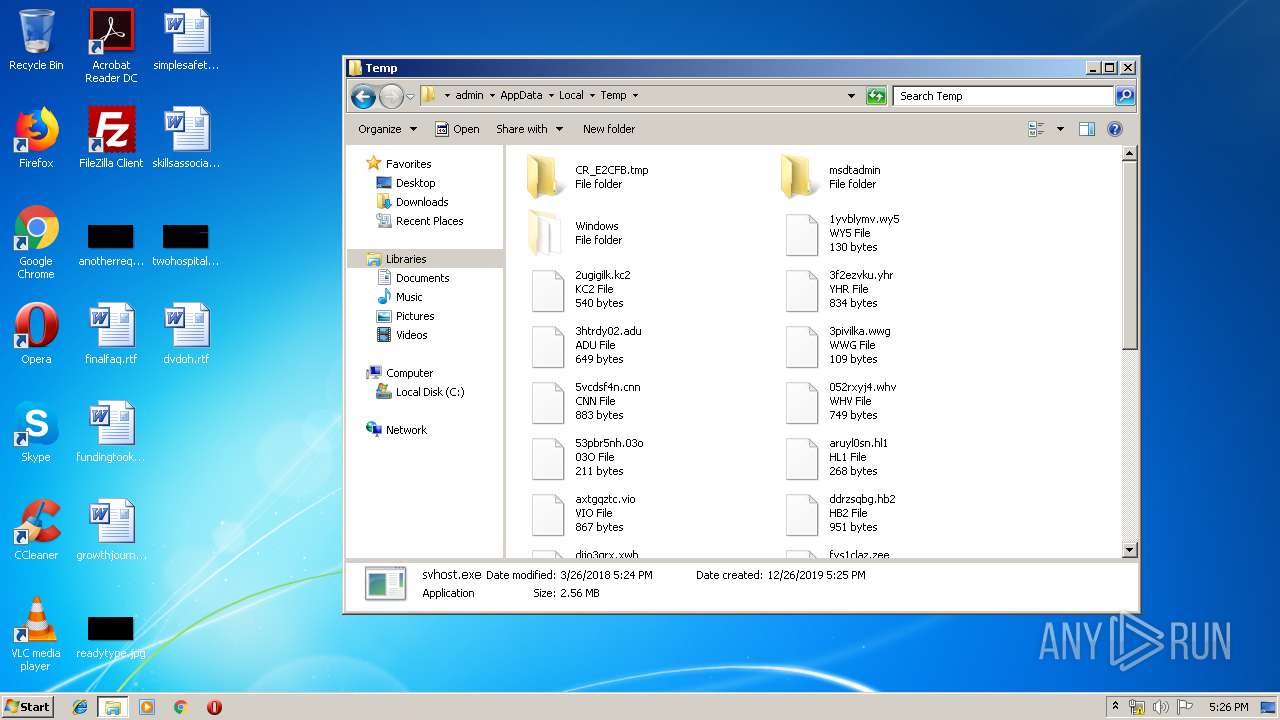
Executable content was dropped or overwritten
- cmd.exe (PID: 2168)
- McDonalds.exe (PID: 944)
- svhost.exe (PID: 2140)
- startup.exe (PID: 2280)
- svhost.exe (PID: 1296)
- cmd.exe (PID: 3504)
- McDonalds.exe (PID: 2376)
Starts CMD.EXE for commands execution
- McDonalds.exe (PID: 944)
- svhost.exe (PID: 2140)
- startup.exe (PID: 2280)
- svhost.exe (PID: 1296)
- McDonalds.exe (PID: 2376)
Creates files in the user directory
- McDonalds.exe (PID: 944)
INFO
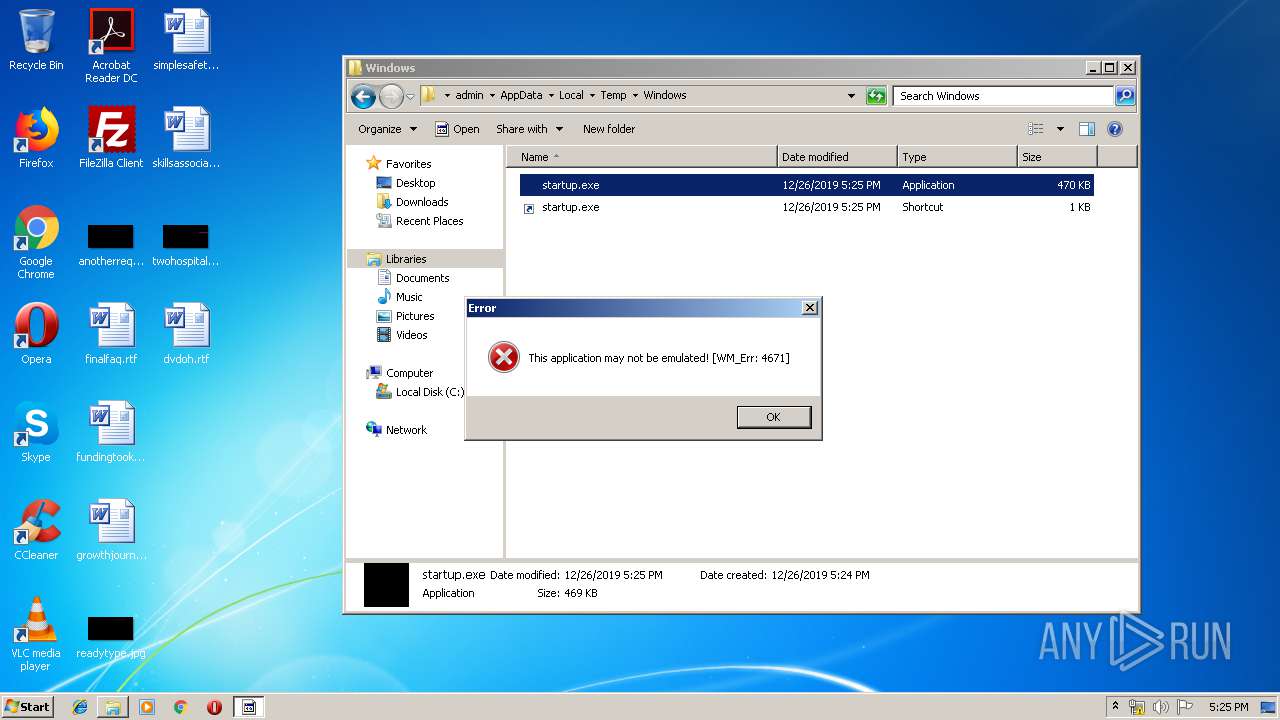
Manual execution by user
- explorer.exe (PID: 3084)
- startup.exe (PID: 2280)
- McDonalds.exe (PID: 2376)
- svhost.exe (PID: 4088)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:12:26 01:47:47+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 476672 |
| InitializedDataSize: | 3584 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x76556 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 78.0.3904.108 |
| ProductVersionNumber: | 78.0.3904.108 |
| FileFlagsMask: | 0x0017 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | The Chromium Authors |
| FileDescription: | Chromium |
| FileVersion: | 78.0.3904.108 |
| InternalName: | chrome_exe |
| LegalCopyright: | Copyright 2019 The Chromium Authors. All rights reserved. |
| OriginalFileName: | chrome.exe |
| ProductName: | Chromium |
| ProductVersion: | 78.0.3904.108 |
| CompanyShortName: | The Chromium Authors |
| ProductShortName: | Chromium |
| LastChange: | 4b26898a39ee037623a72fcfb77279fce0e7d648-refs/branch-heads/3904@{#889} |
| OfficialBuild: | - |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 26-Dec-2019 00:47:47 |
| Detected languages: |
|
| CompanyName: | The Chromium Authors |
| FileDescription: | Chromium |
| FileVersion: | 78.0.3904.108 |
| InternalName: | chrome_exe |
| LegalCopyright: | Copyright 2019 The Chromium Authors. All rights reserved. |
| OriginalFilename: | chrome.exe |
| ProductName: | Chromium |
| ProductVersion: | 78.0.3904.108 |
| CompanyShortName: | The Chromium Authors |
| ProductShortName: | Chromium |
| LastChange: | 4b26898a39ee037623a72fcfb77279fce0e7d648-refs/branch-heads/3904@{#889} |
| Official Build: | 0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 26-Dec-2019 00:47:47 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x0007455C | 0x00074600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.80027 |
.rsrc | 0x00078000 | 0x00000A8E | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.37139 |
.reloc | 0x0007A000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
Imports
mscoree.dll |
Total processes
63
Monitored processes
16
Malicious processes
0
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 944 | "C:\Users\admin\AppData\Local\Temp\McDonalds.exe" | C:\Users\admin\AppData\Local\Temp\McDonalds.exe | explorer.exe | ||||||||||||
User: admin Company: The Chromium Authors Integrity Level: MEDIUM Description: Chromium Exit code: 0 Version: 78.0.3904.108 Modules
| |||||||||||||||
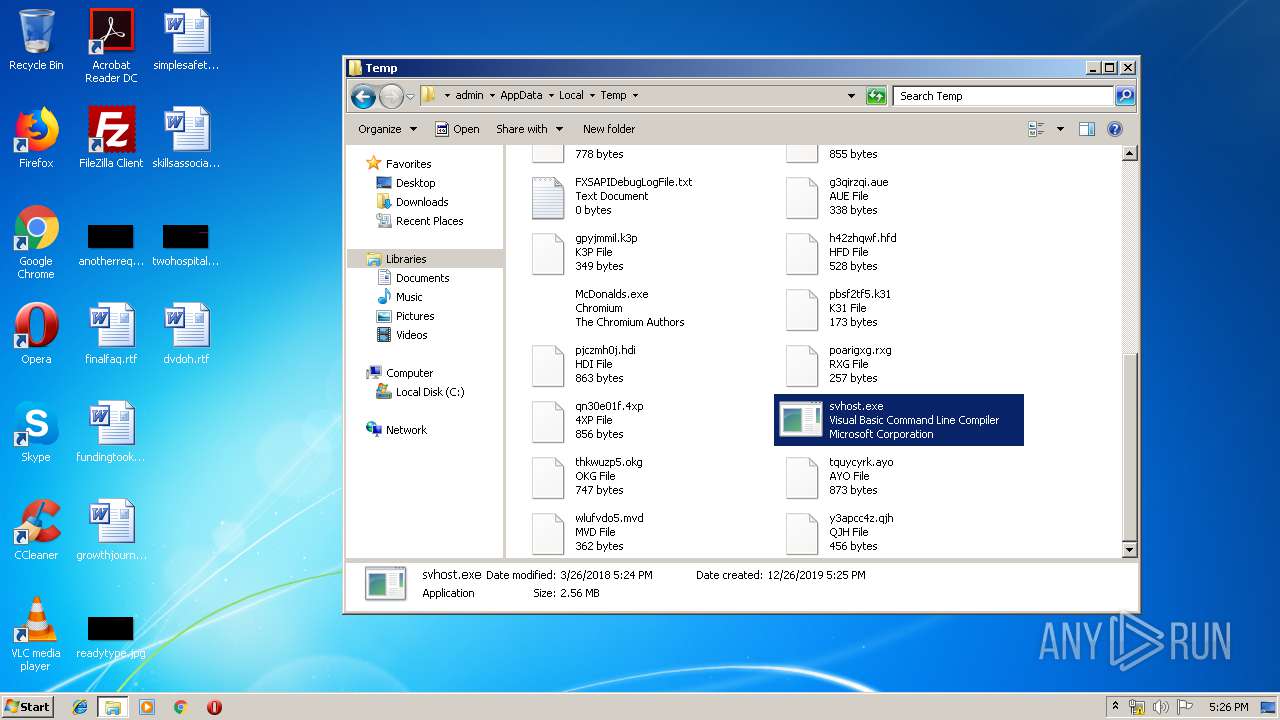
| 1296 | "C:\Users\admin\AppData\Local\Temp\svhost.exe" | C:\Users\admin\AppData\Local\Temp\svhost.exe | startup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 14.7.3062.0 Modules
| |||||||||||||||
| 1472 | "C:\Users\admin\AppData\Local\Temp\svhost.exe" | C:\Users\admin\AppData\Local\Temp\svhost.exe | — | McDonalds.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 3221225496 Version: 14.7.3062.0 Modules
| |||||||||||||||
| 1532 | "C:\Windows\System32\cmd.exe" /c echo [zoneTransfer]ZoneID = 2 > %temp%\Windows\startup.exe:Zone.Identifier | C:\Windows\System32\cmd.exe | — | McDonalds.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1892 | "C:\Windows\System32\cmd.exe" /c echo [zoneTransfer]ZoneID = 2 > %temp%\Windows\startup.exe:Zone.Identifier | C:\Windows\System32\cmd.exe | — | startup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2140 | "C:\Users\admin\AppData\Local\Temp\svhost.exe" | C:\Users\admin\AppData\Local\Temp\svhost.exe | McDonalds.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 14.7.3062.0 Modules
| |||||||||||||||
| 2168 | "C:\Windows\System32\cmd.exe" /c copy "C:/Users/admin/AppData/Local/Temp/McDonalds.exe" "%temp%\Windows\startup.exe" /Y | C:\Windows\System32\cmd.exe | McDonalds.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2280 | "C:\Users\admin\AppData\Local\Temp\Windows\startup.exe" | C:\Users\admin\AppData\Local\Temp\Windows\startup.exe | explorer.exe | ||||||||||||
User: admin Company: The Chromium Authors Integrity Level: MEDIUM Description: Chromium Exit code: 0 Version: 78.0.3904.108 Modules
| |||||||||||||||
| 2376 | "C:\Users\admin\AppData\Local\Temp\McDonalds.exe" | C:\Users\admin\AppData\Local\Temp\McDonalds.exe | explorer.exe | ||||||||||||
User: admin Company: The Chromium Authors Integrity Level: MEDIUM Description: Chromium Exit code: 0 Version: 78.0.3904.108 Modules
| |||||||||||||||
| 2840 | cmd /c ""C:\Users\admin\AppData\Local\Temp\89UdIBRuIJ3rwkXm.bat" " | C:\Windows\system32\cmd.exe | — | svhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 985
Read events
1 965
Write events
20
Delete events
0
Modification events
| (PID) Process: | (944) McDonalds.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (944) McDonalds.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2140) svhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2140) svhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2280) startup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2280) startup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1296) svhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1296) svhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2376) McDonalds.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2376) McDonalds.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
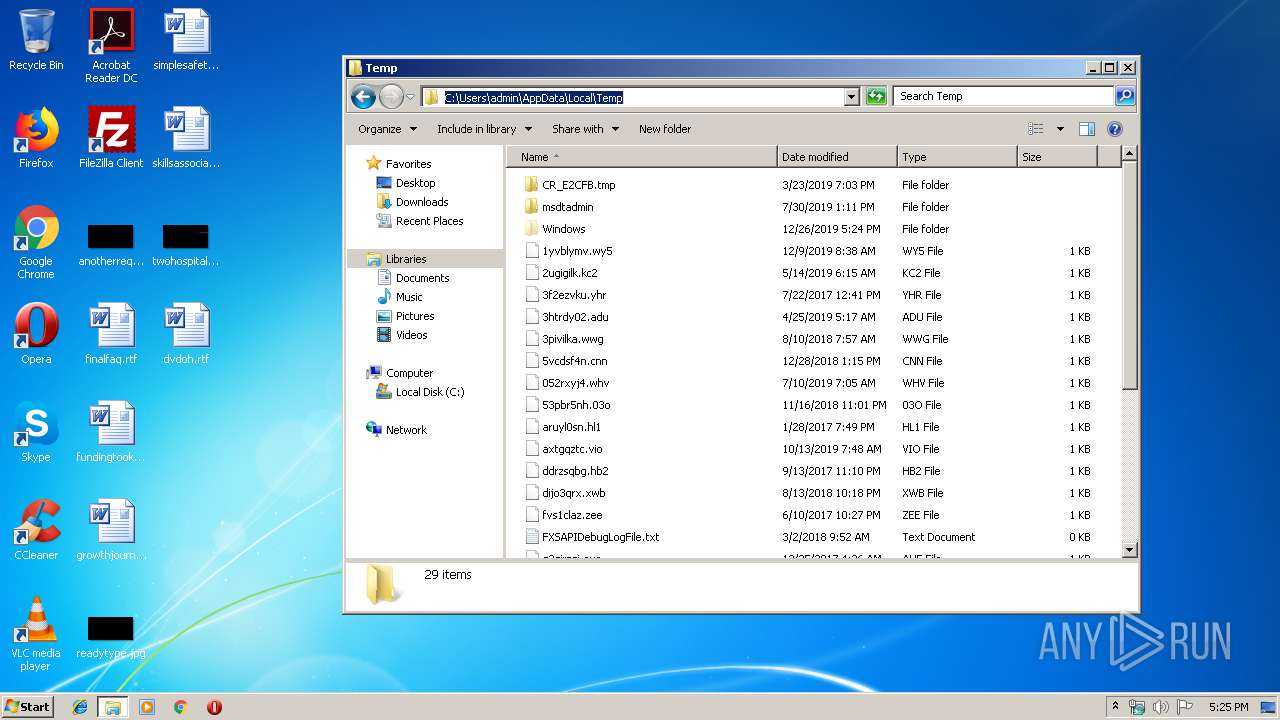
Executable files
7
Suspicious files
0
Text files
5
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1296 | svhost.exe | C:\Users\admin\AppData\Local\Temp\89UdIBRuIJ3rwkXm.bat | text | |
MD5:E1CCCC4A0747D9084D3515605CFFF707 | SHA256:8F6C20DC7B8477652EF3B1FB8814AA79EADD8709080A9A9CA15589AFF3151802 | |||
| 944 | McDonalds.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\startup.exe.lnk | lnk | |
MD5:27C596819E0A42D27257D9417FD57584 | SHA256:FC73F0A39F9DF4F257CBE57681CE9FCC086ACF663BCB257EE9AFCC66FEE9CA98 | |||
| 2376 | McDonalds.exe | C:\Users\admin\AppData\Local\Temp\Windows\startup.exe.lnk | lnk | |
MD5:2E4F9D365AD729E9EFD24CCDCA9A2190 | SHA256:3C99DA97D394B4092D8F28745944E610B72B435107534E69A70E6D3D60F287F7 | |||
| 2376 | McDonalds.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\startup.exe.lnk | lnk | |
MD5:27C596819E0A42D27257D9417FD57584 | SHA256:FC73F0A39F9DF4F257CBE57681CE9FCC086ACF663BCB257EE9AFCC66FEE9CA98 | |||
| 1532 | cmd.exe | C:\Users\admin\AppData\Local\Temp\Windows\startup.exe:Zone.Identifier | text | |
MD5:130A75A932A2FE57BFEA6A65B88DA8F6 | SHA256:F2B79CAE559D6772AFC1C2ED9468988178F8B6833D5028A15DEA73CE47D0196E | |||
| 2280 | startup.exe | C:\Users\admin\AppData\Local\Temp\Windows\startup.exe.lnk | lnk | |
MD5:2E4F9D365AD729E9EFD24CCDCA9A2190 | SHA256:3C99DA97D394B4092D8F28745944E610B72B435107534E69A70E6D3D60F287F7 | |||
| 2140 | svhost.exe | C:\Users\admin\AppData\Local\Temp\vQTfPuHO11aXIITM.bat | text | |
MD5:18B621A09AA817ABDE8D7315A5314CBC | SHA256:A8F0A1BA2DA57157C820A95A7014A19E58AACCEE14994485019AF60C1FB65371 | |||
| 2280 | startup.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\startup.exe.lnk | lnk | |
MD5:27C596819E0A42D27257D9417FD57584 | SHA256:FC73F0A39F9DF4F257CBE57681CE9FCC086ACF663BCB257EE9AFCC66FEE9CA98 | |||
| 944 | McDonalds.exe | C:\Users\admin\AppData\Local\Temp\Windows\startup.exe.lnk | lnk | |
MD5:2E4F9D365AD729E9EFD24CCDCA9A2190 | SHA256:3C99DA97D394B4092D8F28745944E610B72B435107534E69A70E6D3D60F287F7 | |||
| 1296 | svhost.exe | C:\Users\admin\AppData\Local\Temp\89UdIBRuIJ3rwkXm | executable | |
MD5:1F7BCCC57D21A4BFEDDAAFE514CFD74D | SHA256:D4CB7377E8275ED47E499AB0D7EE47167829A5931BA41AA5790593595A7E1061 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report