| File name: | http://r5---sn-hpa7zned.gvt1.com/edgedl/chrome-remote-desktop/chromeremotedesktophost-79.0.3945.10.msi?cms_redirect=yes&mip=185. |
| Full analysis: | https://app.any.run/tasks/63e390ac-e38c-4f55-8635-1a522441ec54 |
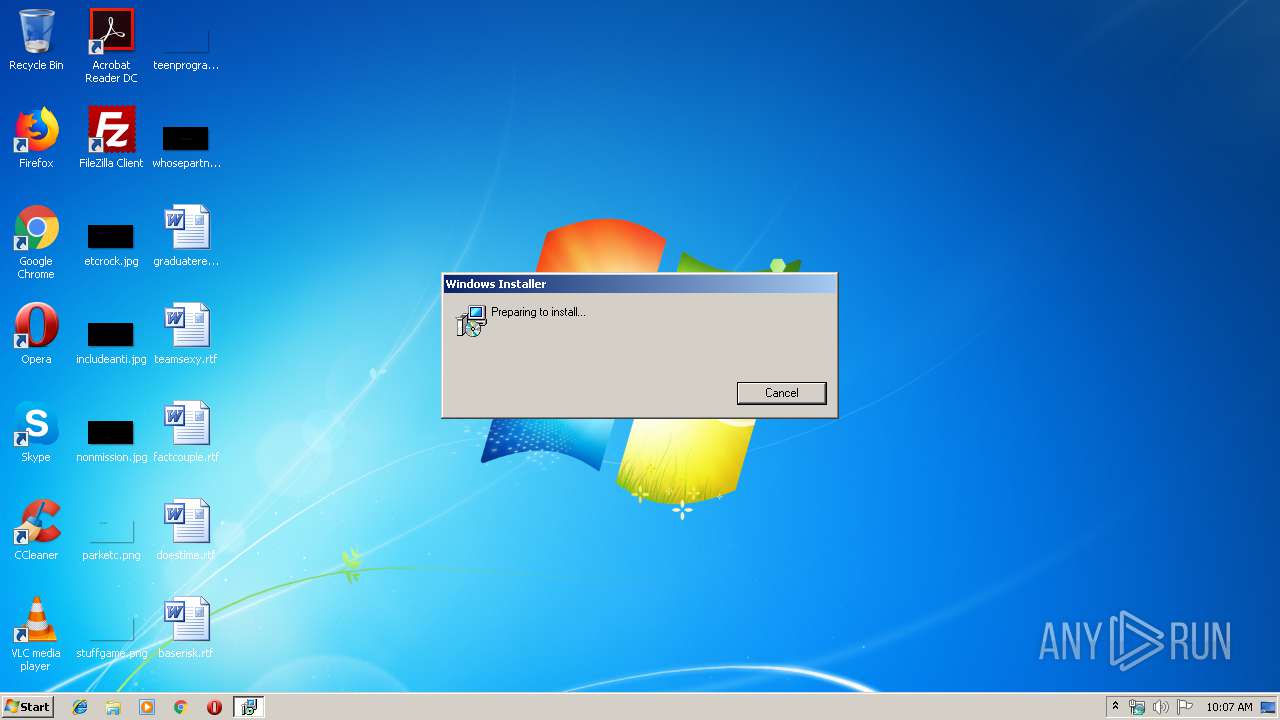
| Verdict: | Suspicious activity |
| Analysis date: | December 06, 2019, 10:06:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, MSI Installer, Code page: 1252, Title: Installation Database, Subject: Chrome Remote Desktop Host Package, Author: Google Inc., Keywords: Installer, Comments: Chrome Remote Desktop Host Package, Template: Intel;1033, Revision Number: {F2750C87-E6C1-4468-A5E5-524BC86ABAF0}, Create Time/Date: Fri Oct 25 04:51:22 2019, Last Saved Time/Date: Fri Oct 25 04:51:22 2019, Number of Pages: 200, Number of Words: 2, Name of Creating Application: Windows Installer XML Toolset (3.8.1128.0), Security: 2 |
| MD5: | 725A6F3713EC55551A9CADC2563E0FD2 |
| SHA1: | F7C3DA660AE2604420CCEF051D9D7F828E2AAAB4 |
| SHA256: | 41E04408C00CE998ED3A3199257E0D9E1B1F6DB595542F3FAFC054F05914751E |
| SSDEEP: | 393216:In5KJLXq6yBW1W9GMynCeHLvRXTQYbWxbQZ:InGoQU4We7BTlbWxU |
MALICIOUS
Changes settings of System certificates
- msiexec.exe (PID: 2492)
Loads dropped or rewritten executable
- services.exe (PID: 448)
SUSPICIOUS
Executed as Windows Service
- vssvc.exe (PID: 2108)
Executable content was dropped or overwritten
- msiexec.exe (PID: 3140)
Creates COM task schedule object
- msiexec.exe (PID: 3140)
Creates or modifies windows services
- services.exe (PID: 448)
INFO
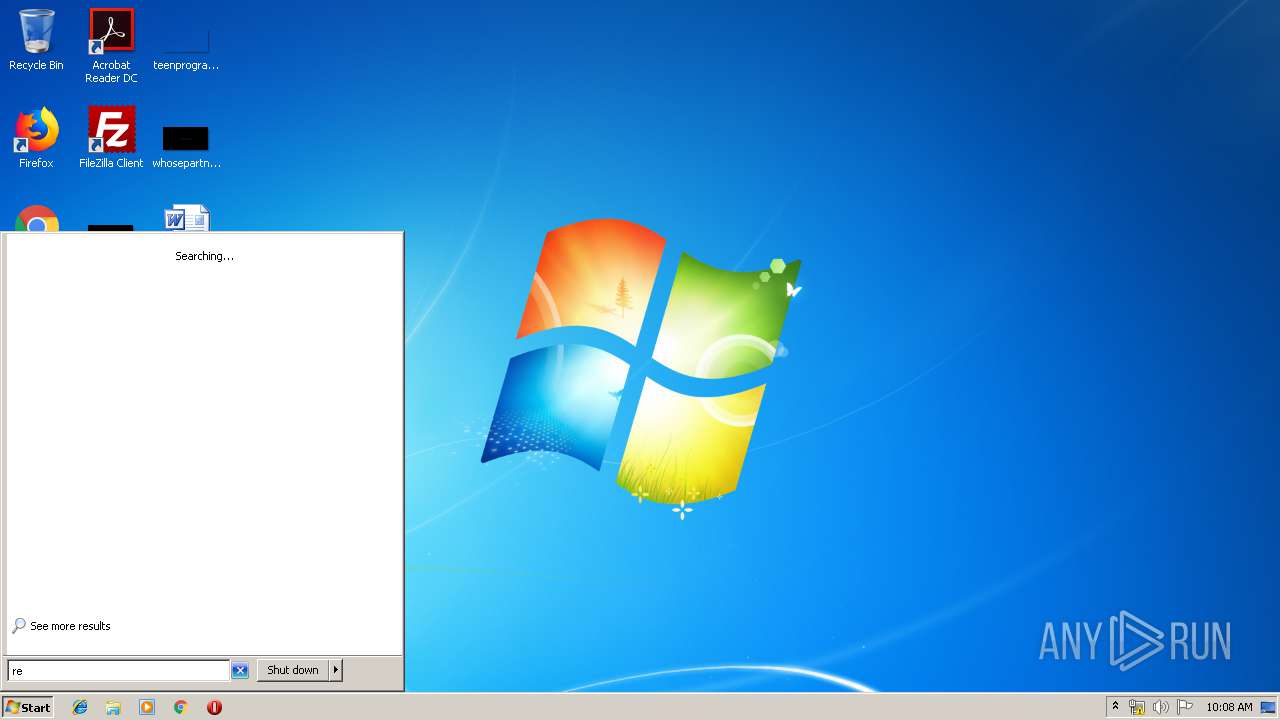
Searches for installed software
- msiexec.exe (PID: 3140)
Creates files in the program directory
- msiexec.exe (PID: 3140)
Low-level read access rights to disk partition
- vssvc.exe (PID: 2108)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 3016)
- MsiExec.exe (PID: 2080)
Application launched itself
- msiexec.exe (PID: 3140)
Creates a software uninstall entry
- msiexec.exe (PID: 3140)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (98.5) |
|---|---|---|
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| Title: | Installation Database |
| Subject: | Chrome Remote Desktop Host Package |
| Author: | Google Inc. |
| Keywords: | Installer |
| Comments: | Chrome Remote Desktop Host Package |
| Template: | Intel;1033 |
| RevisionNumber: | {F2750C87-E6C1-4468-A5E5-524BC86ABAF0} |
| CreateDate: | 2019:10:25 03:51:22 |
| ModifyDate: | 2019:10:25 03:51:22 |
| Pages: | 200 |
| Words: | 2 |
| Software: | Windows Installer XML Toolset (3.8.1128.0) |
| Security: | Read-only recommended |
Total processes
41
Monitored processes
7
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 448 | C:\Windows\system32\services.exe | C:\Windows\System32\services.exe | — | wininit.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Services and Controller app Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2080 | C:\Windows\system32\MsiExec.exe -Embedding 5EFC35DCA71BE05C96C7439B4B2EEA31 M Global\MSI0000 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2108 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2492 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\cb0ed14e-8b89-4c4e-ae4e-16e36259a258.msi" | C:\Windows\System32\msiexec.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2532 | C:\Windows\system32\MsiExec.exe -Embedding A1A854346EB7BBD5205ED0810381AA9F C | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3016 | C:\Windows\system32\MsiExec.exe -Embedding D08EB053DE71B2F485CF204027223871 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3140 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
834
Read events
494
Write events
328
Delete events
12
Modification events
| (PID) Process: | (2492) msiexec.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2492) msiexec.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\p2pcollab.dll,-8042 |
Value: Peer to Peer Trust | |||
| (PID) Process: | (2492) msiexec.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\qagentrt.dll,-10 |
Value: System Health Authentication | |||
| (PID) Process: | (2492) msiexec.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dnsapi.dll,-103 |
Value: Domain Name System (DNS) Server Trust | |||
| (PID) Process: | (2492) msiexec.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\fveui.dll,-843 |
Value: BitLocker Drive Encryption | |||
| (PID) Process: | (2492) msiexec.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\fveui.dll,-844 |
Value: BitLocker Data Recovery Agent | |||
| (PID) Process: | (2492) msiexec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\SystemCertificates\CA\Certificates\EAB040689A0D805B5D6FD654FC168CFF00B78BE3 |
| Operation: | write | Name: | Blob |
Value: 030000000100000014000000EAB040689A0D805B5D6FD654FC168CFF00B78BE31400000001000000140000005379BF5AAA2B4ACF5480E1D89BC09DF2B20366CB040000000100000010000000DB78CBD190952735D940BC80AC2432C00F0000000100000030000000435FE6564241D6B3828352EF9BE443D511C21F0AFB325C4038A5820F00D87774A8EF2193DDAAE065B2572FAF2BF0EE63190000000100000010000000EA6089055218053DD01E37E1D806EEDF18000000010000001000000045ED9BBC5E43D3B9ECD63C060DB78E5C20000000010000007B050000308205773082045FA003020102021013EA28705BF4ECED0C36630980614336300D06092A864886F70D01010C0500306F310B300906035504061302534531143012060355040A130B416464547275737420414231263024060355040B131D41646454727573742045787465726E616C20545450204E6574776F726B312230200603550403131941646454727573742045787465726E616C20434120526F6F74301E170D3030303533303130343833385A170D3230303533303130343833385A308188310B3009060355040613025553311330110603550408130A4E6577204A6572736579311430120603550407130B4A65727365792043697479311E301C060355040A131554686520555345525452555354204E6574776F726B312E302C06035504031325555345525472757374205253412043657274696669636174696F6E20417574686F7269747930820222300D06092A864886F70D01010105000382020F003082020A028202010080126517360EC3DB08B3D0AC570D76EDCD27D34CAD508361E2AA204D092D6409DCCE899FCC3DA9ECF6CFC1DCF1D3B1D67B3728112B47DA39C6BC3A19B45FA6BD7D9DA36342B676F2A93B2B91F8E26FD0EC162090093EE2E874C918B491D46264DB7FA306F188186A90223CBCFE13F087147BF6E41F8ED4E451C61167460851CB8614543FBC33FE7E6C9CFF169D18BD518E35A6A766C87267DB2166B1D49B7803C0503AE8CCF0DCBC9E4CFEAF0596351F575AB7FFCEF93DB72CB6F654DDC8E7123A4DAE4C8AB75C9AB4B7203DCA7F2234AE7E3B68660144E7014E46539B3360F794BE5337907343F332C353EFDBAAFE744E69C76B8C6093DEC4C70CDFE132AECC933B517895678BEE3D56FE0CD0690F1B0FF325266B336DF76E47FA7343E57E0EA566B1297C3284635589C40DC19354301913ACD37D37A7EB5D3A6C355CDB41D712DAA9490BDFD8808A0993628EB566CF2588CD84B8B13FA4390FD9029EEB124C957CF36B05A95E1683CCB867E2E8139DCC5B82D34CB3ED5BFFDEE573AC233B2D00BF3555740949D849581A7F9236E651920EF3267D1C4D17BCC9EC4326D0BF415F40A94444F499E757879E501F5754A83EFD74632FB1506509E658422E431A4CB4F0254759FA041E93D426464A5081B2DEBE78B7FC6715E1C957841E0F63D6E962BAD65F552EEA5CC62808042539B80E2BA9F24C971C073F0D52F5EDEF2F820F0203010001A381F43081F1301F0603551D23041830168014ADBD987A34B426F7FAC42654EF03BDE024CB541A301D0603551D0E041604145379BF5AAA2B4ACF5480E1D89BC09DF2B20366CB300E0603551D0F0101FF040403020186300F0603551D130101FF040530030101FF30110603551D20040A300830060604551D200030440603551D1F043D303B3039A037A0358633687474703A2F2F63726C2E7573657274727573742E636F6D2F416464547275737445787465726E616C4341526F6F742E63726C303506082B0601050507010104293027302506082B060105050730018619687474703A2F2F6F6373702E7573657274727573742E636F6D300D06092A864886F70D01010C050003820101009365F63783950F5EC3821C1FD677E73C8AC0AA09F0E90B26F1E0C26A75A1C779C9B95260C829120EF0AD03D609C476DFE5A68195A746DA8257A99592C5B68F03226C3377C17B32176E07CE5A14413A05241BF614063BA825240EBBCC2A75DDB970413F7CD0633621071F46FF60A491E167BCDE1F7E1914C9636791EA67076BB48F8BC06E437DC3A1806CB21EBC53857DDC90A1A4BC2DEF4672573505BFBB46BB6E6D3799B6FF239291C66E40F88F2956EA5FD55F1453ACF04F61EAF722CCA7560BE2B8341F26D97B1905683FBA3CD43806A2D3E68F0EE3B4716D4042C584B440952BF465A04879F61D8163969D4F75E0F87CE48EA9D1F2AD8AB38CC721CDC2EF | |||
| (PID) Process: | (3140) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 40000000000000001CFD46EB1CACD501440C000054090000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3140) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 40000000000000001CFD46EB1CACD501440C000054090000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2108) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000005C4893EB1CACD5013C080000EC020000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
9
Suspicious files
5
Text files
5
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2492 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\CabC4D1.tmp | — | |
MD5:— | SHA256:— | |||
| 2492 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\TarC4D2.tmp | — | |
MD5:— | SHA256:— | |||
| 2492 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\CabC4E3.tmp | — | |
MD5:— | SHA256:— | |||
| 2492 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\TarC4E4.tmp | — | |
MD5:— | SHA256:— | |||
| 2492 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\CabC4F4.tmp | — | |
MD5:— | SHA256:— | |||
| 2492 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\TarC4F5.tmp | — | |
MD5:— | SHA256:— | |||
| 2492 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSID2C2.tmp | — | |
MD5:— | SHA256:— | |||
| 3140 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 3140 | msiexec.exe | C:\Windows\Installer\3a046a.msi | — | |
MD5:— | SHA256:— | |||
| 2108 | vssvc.exe | C: | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2492 | msiexec.exe | 91.199.212.52:80 | crt.usertrust.com | Comodo CA Ltd | GB | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crt.usertrust.com |
| whitelisted |