| File name: | ADISyncSetup.exe |
| Full analysis: | https://app.any.run/tasks/586fbf3b-586a-4fcf-8e73-2b455d18e258 |
| Verdict: | Malicious activity |
| Analysis date: | March 24, 2025, 18:27:53 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 8 sections |
| MD5: | FCB763A85FDD5C9806F16DD21B0F33D9 |
| SHA1: | C09C2DFC2BD07652ADF60F5991C901E01D5078E2 |
| SHA256: | 41D5DB8766525836DA935C917CF7064C8CBA5C4CA45EB8704496887DD05E94BB |
| SSDEEP: | 98304:RVrrgNaaTQuBGuG2EGadXTXzGGcesWnIDoFXKUYmsXP16FFn2KIpvVVNXkSmp9aD:RQN |
MALICIOUS
Executing a file with an untrusted certificate
- InstallerHelper.exe (PID: 8132)
- adisync.exe (PID: 2136)
- adsopmanager.exe (PID: 2644)
- ADISyncSetup.exe (PID: 1312)
- ADISyncSetup.exe (PID: 668)
SUSPICIOUS
Starts CMD.EXE for commands execution
- InstallerHandler.exe (PID: 4920)
- InstallerHelper.exe (PID: 8132)
Searches for installed software
- InstallerHandler.exe (PID: 4920)
- rundll32.exe (PID: 7592)
Uses RUNDLL32.EXE to load library
- msiexec.exe (PID: 7400)
- msiexec.exe (PID: 7968)
Executable content was dropped or overwritten
- rundll32.exe (PID: 7592)
- rundll32.exe (PID: 7464)
- rundll32.exe (PID: 7760)
- rundll32.exe (PID: 7684)
- rundll32.exe (PID: 7948)
- ADISyncSetup.exe (PID: 1312)
Executes as Windows Service
- VSSVC.exe (PID: 7292)
- adsopmanager.exe (PID: 2644)
There is functionality for taking screenshot (YARA)
- ADISyncSetup.exe (PID: 1312)
Windows service management via SC.EXE
- sc.exe (PID: 8148)
Starts SC.EXE for service management
- cmd.exe (PID: 4268)
INFO
The sample compiled with english language support
- ADISyncSetup.exe (PID: 1312)
Create files in a temporary directory
- msiexec.exe (PID: 7256)
- rundll32.exe (PID: 7464)
- rundll32.exe (PID: 7592)
- ADISyncSetup.exe (PID: 1312)
Reads the computer name
- InstallerHandler.exe (PID: 4920)
- msiexec.exe (PID: 7320)
- msiexec.exe (PID: 7400)
- InstallerHelper.exe (PID: 8132)
Creates files or folders in the user directory
- msiexec.exe (PID: 7256)
- BackgroundTransferHost.exe (PID: 2384)
Executable content was dropped or overwritten
- msiexec.exe (PID: 7256)
- msiexec.exe (PID: 7320)
Checks supported languages
- msiexec.exe (PID: 7320)
- msiexec.exe (PID: 7400)
- ADISyncSetup.exe (PID: 1312)
- msiexec.exe (PID: 7264)
- InstallerHandler.exe (PID: 4920)
Application launched itself
- msiexec.exe (PID: 7320)
Manages system restore points
- SrTasks.exe (PID: 1056)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 2384)
- BackgroundTransferHost.exe (PID: 7000)
- BackgroundTransferHost.exe (PID: 7828)
Reads the machine GUID from the registry
- adsopmanager.exe (PID: 2644)
- InstallerHandler.exe (PID: 4920)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (3.6) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (1.6) |
| .exe | | | DOS Executable Generic (1.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2022:01:15 05:02:00+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 2881536 |
| InitializedDataSize: | 2545152 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x223301 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.10.6.346 |
| ProductVersionNumber: | 1.10.6.346 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | - |
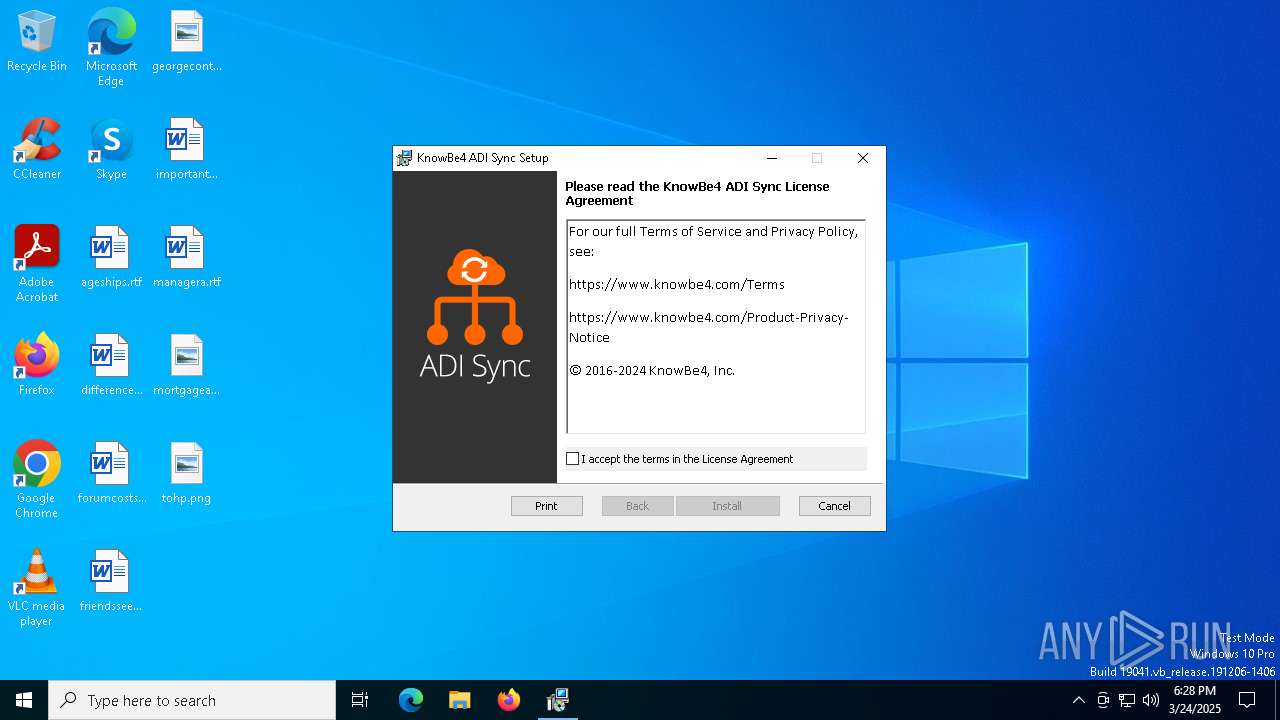
| CompanyName: | KnowBe4, Inc. |
| FileDescription: | KnowBe4 ADI Sync |
| FileVersion: | 1.10.6.346 |
| InternalName: | - |
| LegalCopyright: | Copyright (C) KnowBe4, Inc. |
| LegalTrademarks: | All Rights Reserved |
| OLESelfRegister: | - |
| OriginalFileName: | - |
| PrivateBuild: | - |
| ProductName: | KnowBe4 ADI Sync |
| ProductVersion: | 1.10.6.346 |
| SpecialBuild: | - |
Total processes
170
Monitored processes
34
Malicious processes
7
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 668 | "C:\Users\admin\AppData\Local\Temp\ADISyncSetup.exe" | C:\Users\admin\AppData\Local\Temp\ADISyncSetup.exe | — | explorer.exe | |||||||||||
User: admin Company: KnowBe4, Inc. Integrity Level: MEDIUM Description: KnowBe4 ADI Sync Exit code: 3221226540 Version: 1.10.6.346 Modules
| |||||||||||||||
| 1056 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1312 | "C:\Users\admin\AppData\Local\Temp\ADISyncSetup.exe" | C:\Users\admin\AppData\Local\Temp\ADISyncSetup.exe | explorer.exe | ||||||||||||
User: admin Company: KnowBe4, Inc. Integrity Level: HIGH Description: KnowBe4 ADI Sync Version: 1.10.6.346 Modules
| |||||||||||||||
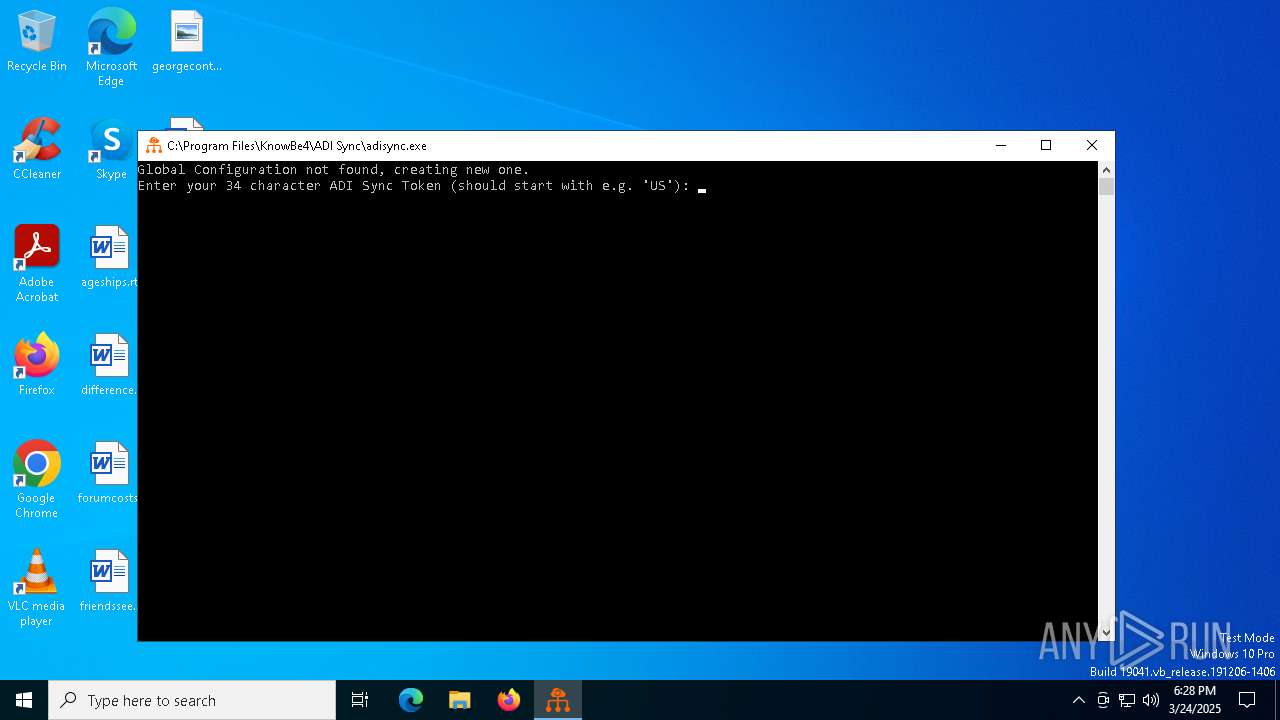
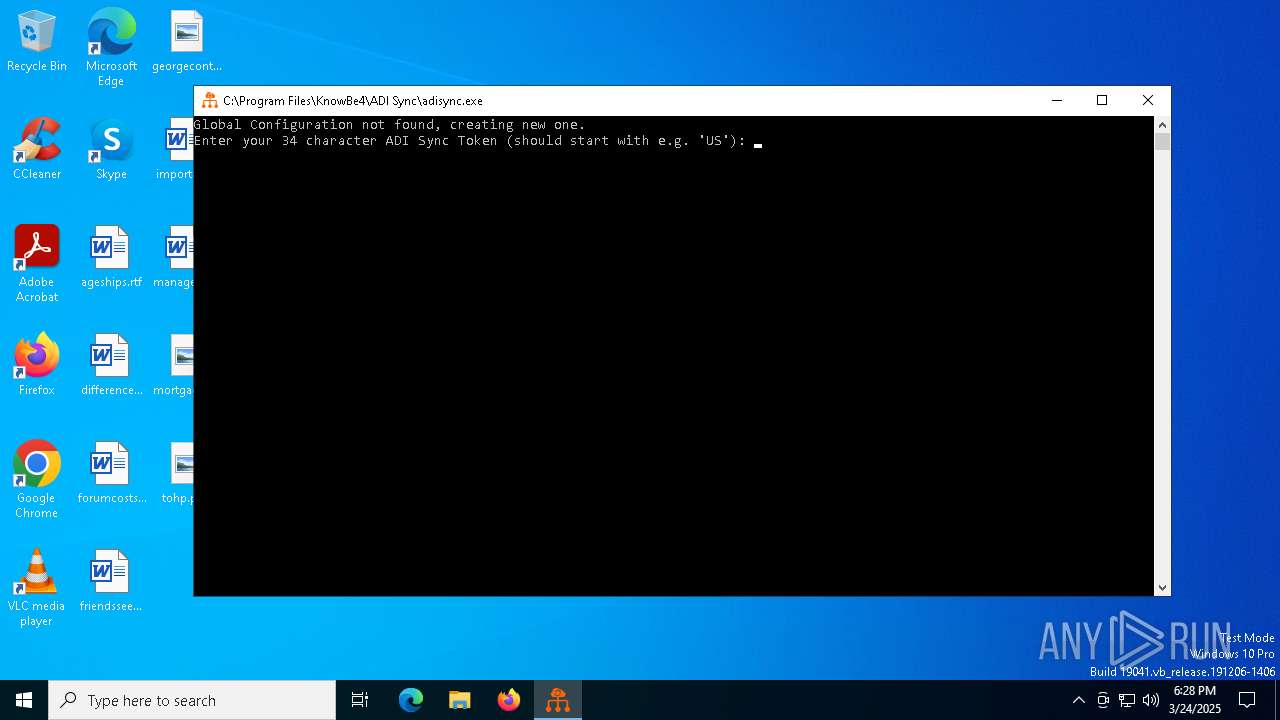
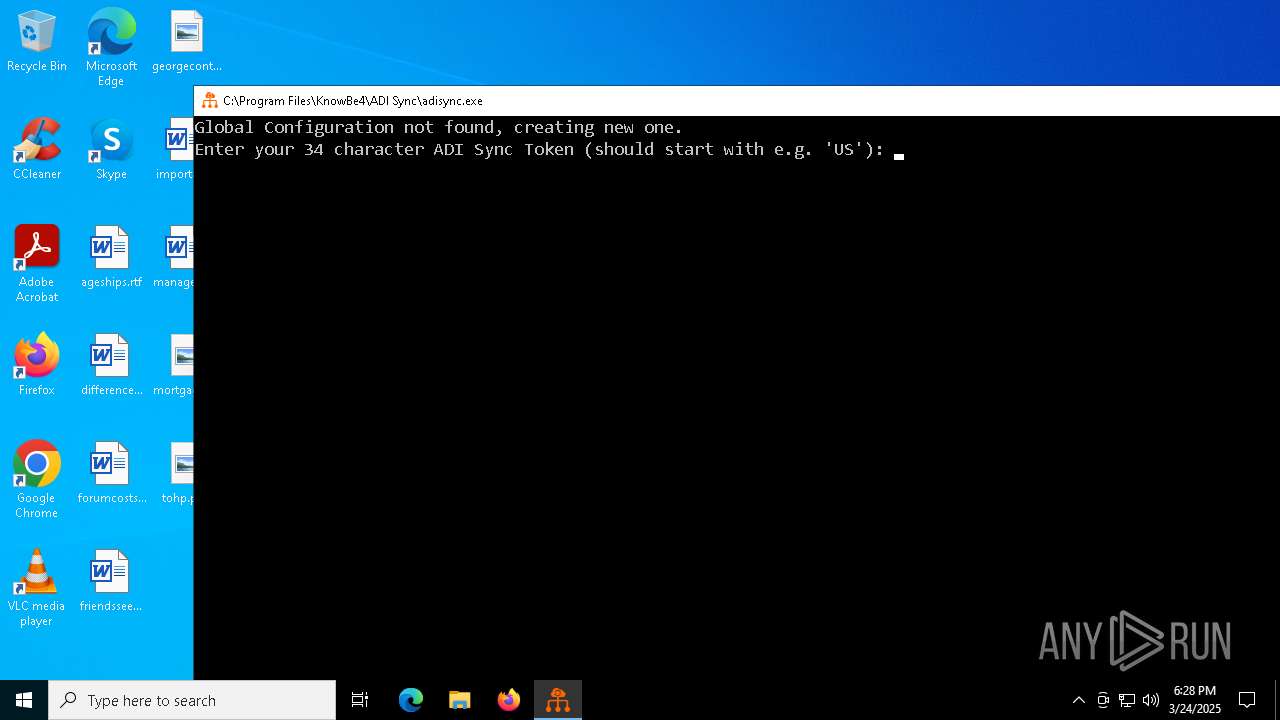
| 2136 | "C:\Program Files\KnowBe4\ADI Sync\adisync.exe" config --install | C:\Program Files\KnowBe4\ADI Sync\adisync.exe | — | msiexec.exe | |||||||||||
User: admin Integrity Level: HIGH Description: ADI Sync Version: 1.10.6.346 Modules
| |||||||||||||||
| 2384 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2644 | "C:\Program Files\KnowBe4\ADI Sync\adsopmanager.exe" | C:\Program Files\KnowBe4\ADI Sync\adsopmanager.exe | — | services.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Description: OpManager Version: 1.10.6.346 Modules
| |||||||||||||||
| 4112 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4268 | "cmd.exe" /c sc.exe start adsopmanager | C:\Windows\System32\cmd.exe | — | InstallerHelper.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4920 | C:\Users\admin\AppData\Local\Temp\{B3A5157B-1F07-49FA-BC5D-C3AFBCF1536A}\InstallerHandler.exe /L*v "C:\Users\admin\AppData\Local\Temp\adsinstaller.log" | C:\Users\admin\AppData\Local\Temp\{B3A5157B-1F07-49FA-BC5D-C3AFBCF1536A}\InstallerHandler.exe | — | ADISyncSetup.exe | |||||||||||
User: admin Integrity Level: HIGH Description: InstallerHandler Version: 1.0.0.0 Modules
| |||||||||||||||
| 5324 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | adisync.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
14 074
Read events
13 783
Write events
274
Delete events
17
Modification events
| (PID) Process: | (7000) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7000) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7000) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2384) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2384) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2384) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (7320) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 48000000000000008C379083EA9CDB01981C000010150000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7320) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000529B9283EA9CDB01981C000010150000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7356) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7356) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
Executable files
66
Suspicious files
28
Text files
15
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1312 | ADISyncSetup.exe | C:\Users\admin\AppData\Local\Temp\DVCAF3.tmp | image | |
MD5:1A2FDECE59714CD7A59B2354B8402C67 | SHA256:0912175D9A556EB372E836D2675EE591A1F0D971C63E4D22DDBC245C7B5C954C | |||
| 1312 | ADISyncSetup.exe | C:\Users\admin\AppData\Local\Temp\{B3A5157B-1F07-49FA-BC5D-C3AFBCF1536A}\Branding.dll | executable | |
MD5:2F023CA6B1743EC13C2BFB3986D67384 | SHA256:9454B87CC0E704FF7DC8AE4E1FCE0EAADF3D467813E271FD1A6C876E6935AD71 | |||
| 1312 | ADISyncSetup.exe | C:\Users\admin\AppData\Local\Temp\{B3A5157B-1F07-49FA-BC5D-C3AFBCF1536A}\Common.dll | executable | |
MD5:104BA4EFAE7ADE9860867E4D8863A6FA | SHA256:AF75A7CBB8C47D3B6117E76FA4C1EF41BF65A21C25A7AA5874DE4C80EE91D9EB | |||
| 1312 | ADISyncSetup.exe | C:\Users\admin\AppData\Local\Temp\{B3A5157B-1F07-49FA-BC5D-C3AFBCF1536A}\ADISyncSetup.msi | executable | |
MD5:608FFD77FA6635DAD58D28C7BC040C7B | SHA256:AA303A5CE674151354202A44AE1333BC5E4FD697C234FFD91D24E440349E5953 | |||
| 7256 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\26C212D9399727259664BDFCA073966E_C5856A5EB1E3B74AE8014850A678CDBF | binary | |
MD5:F80B80DF393DD9FA5681DAF04DC95970 | SHA256:3ADB671CEA304AA57ABD1C22BD6BAA3E28BA75EC794DD48D9DEB6E53E113C43B | |||
| 1312 | ADISyncSetup.exe | C:\Users\admin\AppData\Local\Temp\{B3A5157B-1F07-49FA-BC5D-C3AFBCF1536A}\Newtonsoft.Json.dll | executable | |
MD5:195FFB7167DB3219B217C4FD439EEDD6 | SHA256:E1E27AF7B07EEEDF5CE71A9255F0422816A6FC5849A483C6714E1B472044FA9D | |||
| 7256 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\3EC49180A59F0C351C30F112AD97CFA5_A73CB184BD71EAE4966B5FD3D77BFB68 | binary | |
MD5:6FBB80E63C265ADC18F7B818F50AE4C5 | SHA256:6874DEE9D482914692093AB5A37C1AD5246FBAFB56B3E61D9EFCC9B8E2A4F502 | |||
| 7256 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\26C212D9399727259664BDFCA073966E_C5856A5EB1E3B74AE8014850A678CDBF | binary | |
MD5:014B71D89AB6F26A402D9D80A09623B2 | SHA256:314438E138008E5CD679470AAADC5F180CF1C6866463AF568DEC986246B7C3DE | |||
| 1312 | ADISyncSetup.exe | C:\Users\admin\AppData\Local\Temp\{B3A5157B-1F07-49FA-BC5D-C3AFBCF1536A}\Pinvoke.dll | executable | |
MD5:2ECD8B813F35DE43CEE980EBB932A9AE | SHA256:CE55EF1CCED24167DACB7D25F0D71DC2D4848CFED1218F41BF53B089A5CBEF3F | |||
| 7464 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSID2E2.tmp-0\CAWithoutDependencies.dll | executable | |
MD5:2611C1086E4D0117304EB58EE3F065E5 | SHA256:15A02F9E2DDC3853BAD489EC5F21AC1098BC818E447232F9F93F7DC37921A42B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
31
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7256 | msiexec.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEA%2B4p0C5FY0DUUO8WdnwQCk%3D | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5736 | backgroundTaskHost.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
2384 | BackgroundTransferHost.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5728 | SIHClient.exe | GET | 200 | 23.209.214.100:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5728 | SIHClient.exe | GET | 200 | 23.209.214.100:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7256 | msiexec.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSE67Nbq3jfQQg8yXEpbmqLTNn7XwQUm1%2BwNrqdBq4ZJ73AoCLAi4s4d%2B0CEAeYPdJxBHT%2FSn3SEFireVY%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 20.190.159.75:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 23.54.109.203:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
7256 | msiexec.exe | 23.54.109.203:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5736 | backgroundTaskHost.exe | 20.223.35.26:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5736 | backgroundTaskHost.exe | 23.54.109.203:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |
www.bing.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |