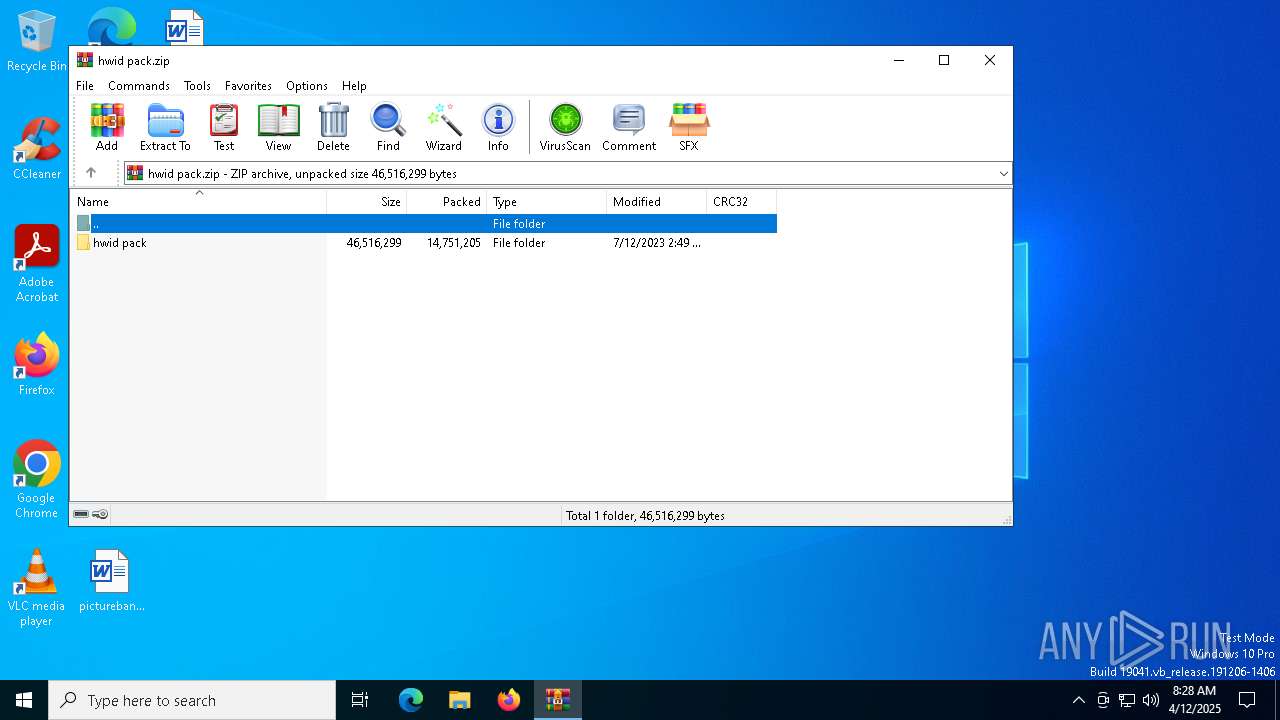
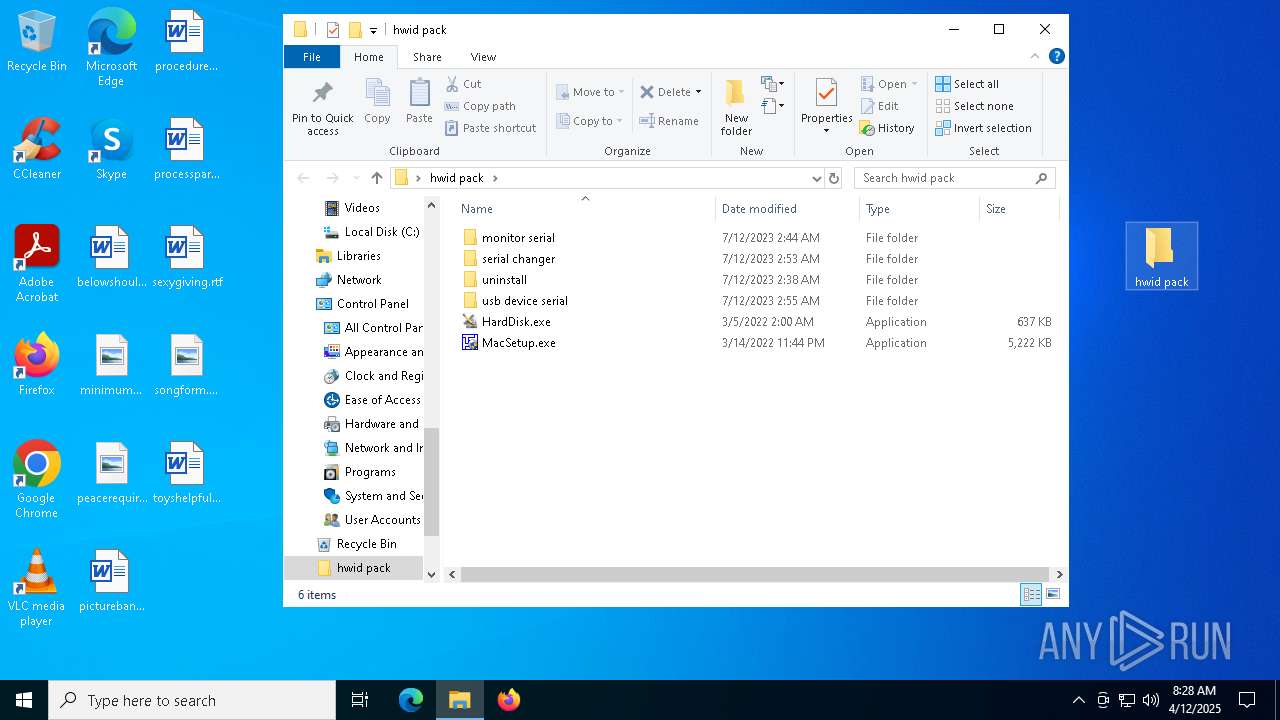
| File name: | hwid pack.zip |
| Full analysis: | https://app.any.run/tasks/f5e3c643-ef31-4b3d-a0ae-db4d8f505217 |
| Verdict: | Malicious activity |
| Analysis date: | April 12, 2025, 08:28:08 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | 734C14A94F1778E506606804D3566594 |
| SHA1: | 8CBD6A9C512EDAAB288A0FD24C7C2D7D71C3999D |
| SHA256: | 41CAEB1DAB6AB9DA4571B88CD0A0A2B3A21CE305909358E538A04F988D4A139F |
| SSDEEP: | 196608:ELlI5+lEzBGc3CqWeo/X/Mbw4+OPexK4Ux:GNYBG1DXQwXBBq |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 6184)
Vulnerable driver has been detected
- WinRAR.exe (PID: 6184)
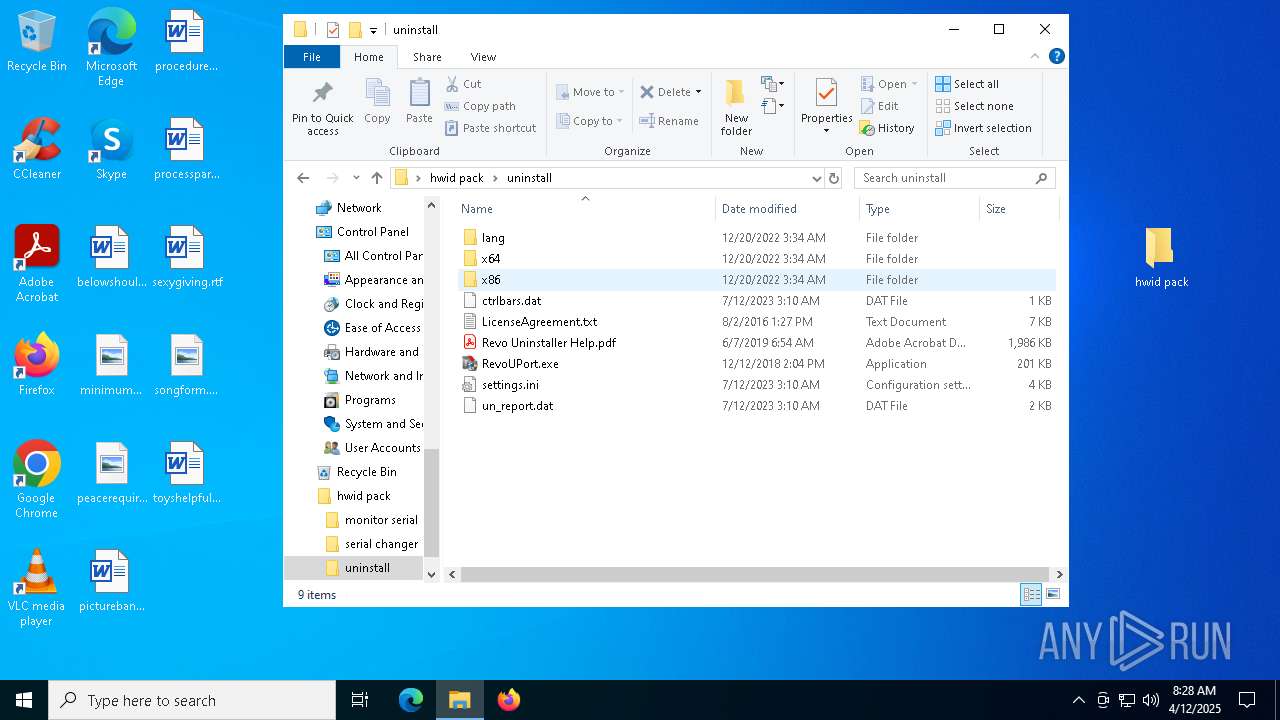
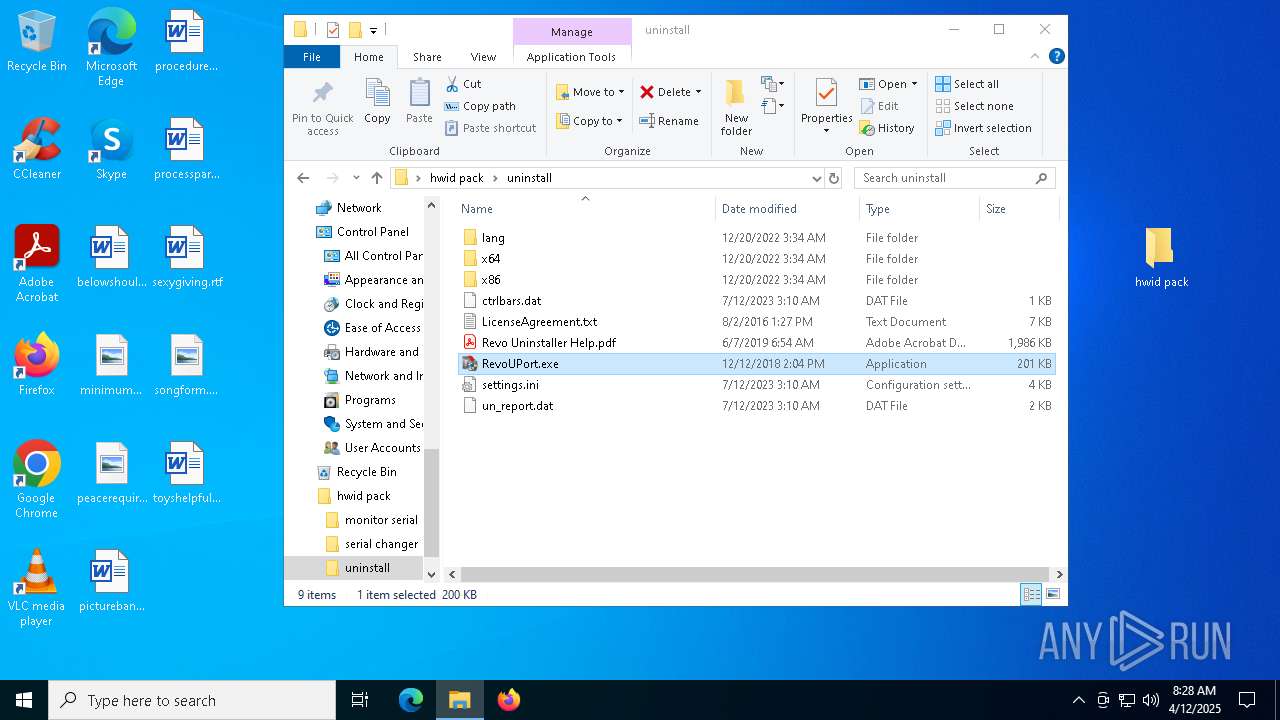
Executing a file with an untrusted certificate
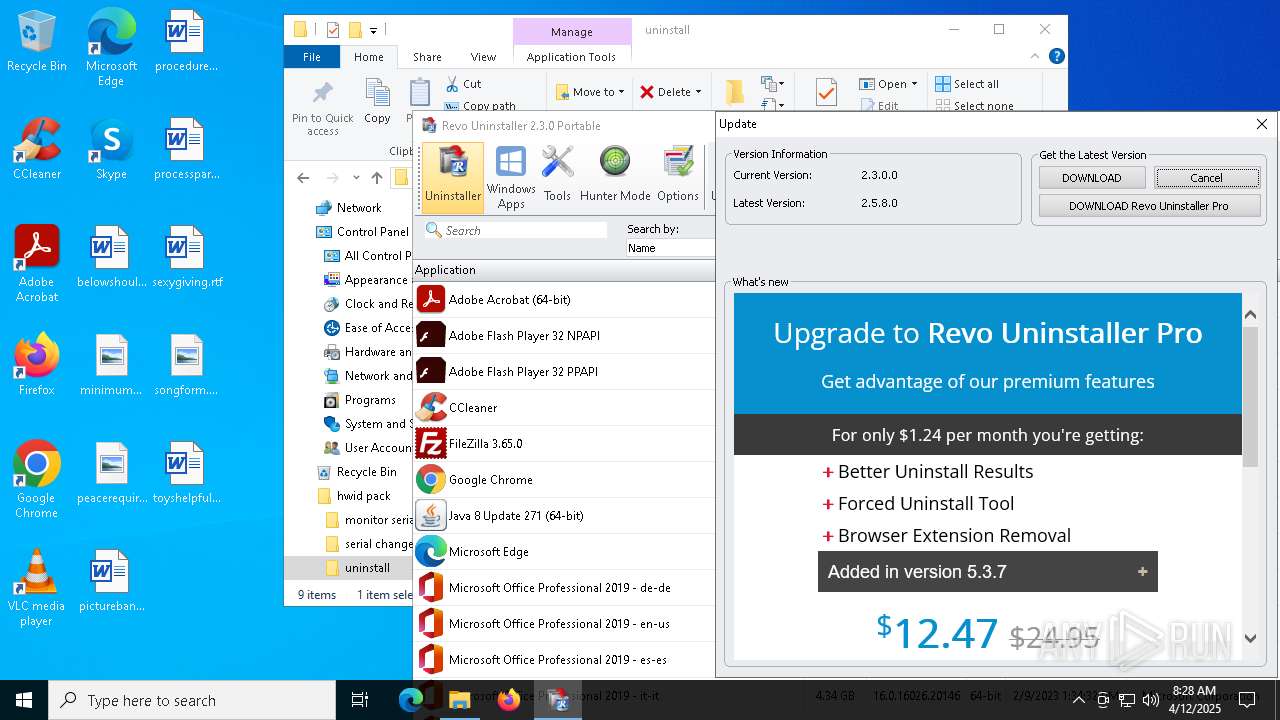
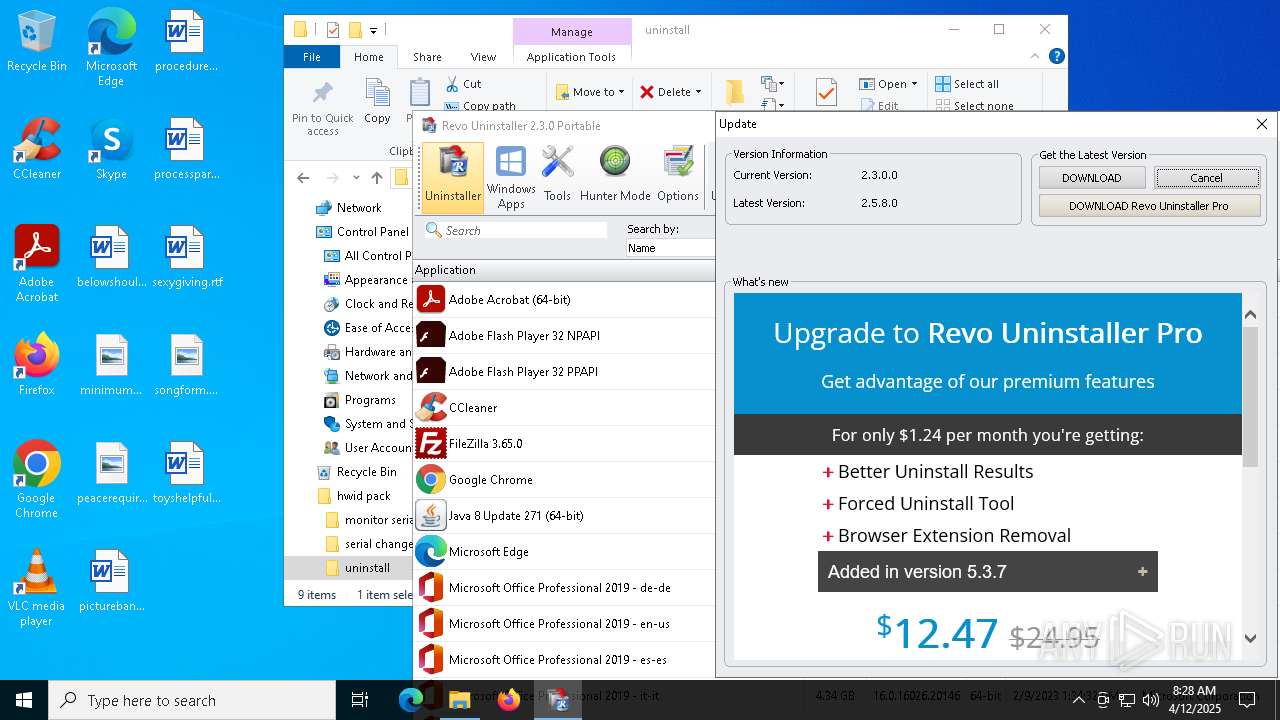
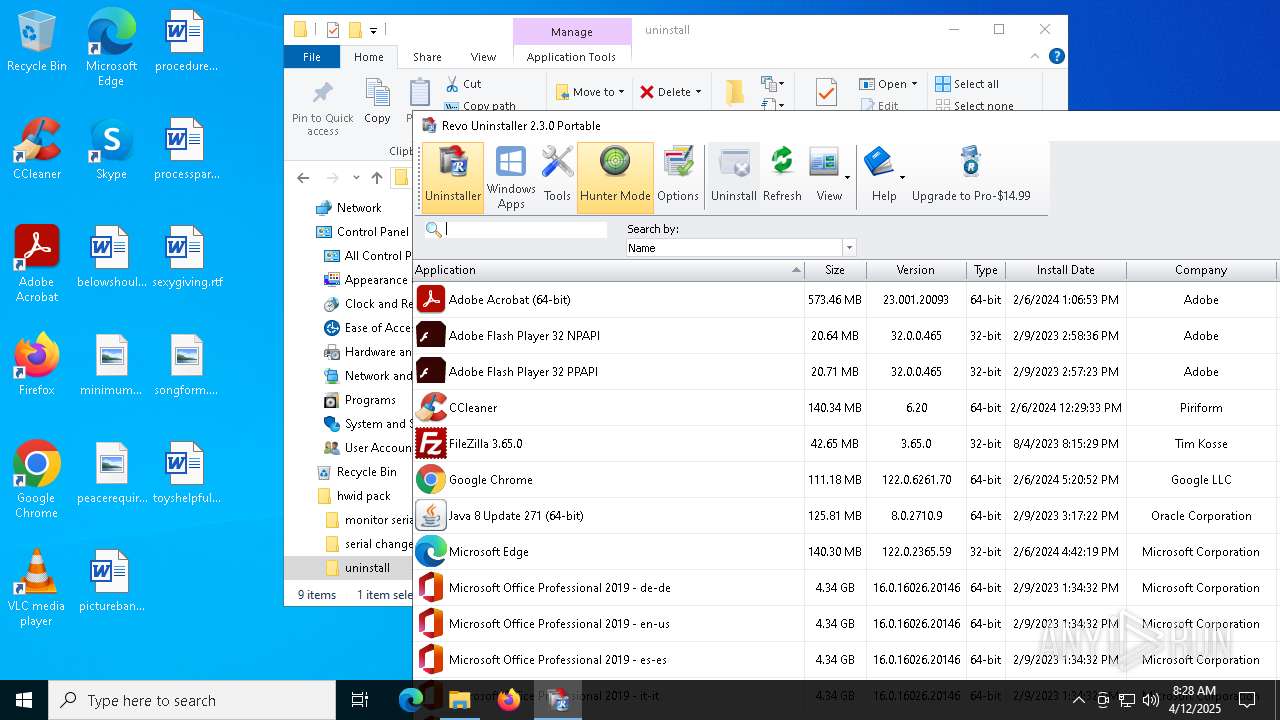
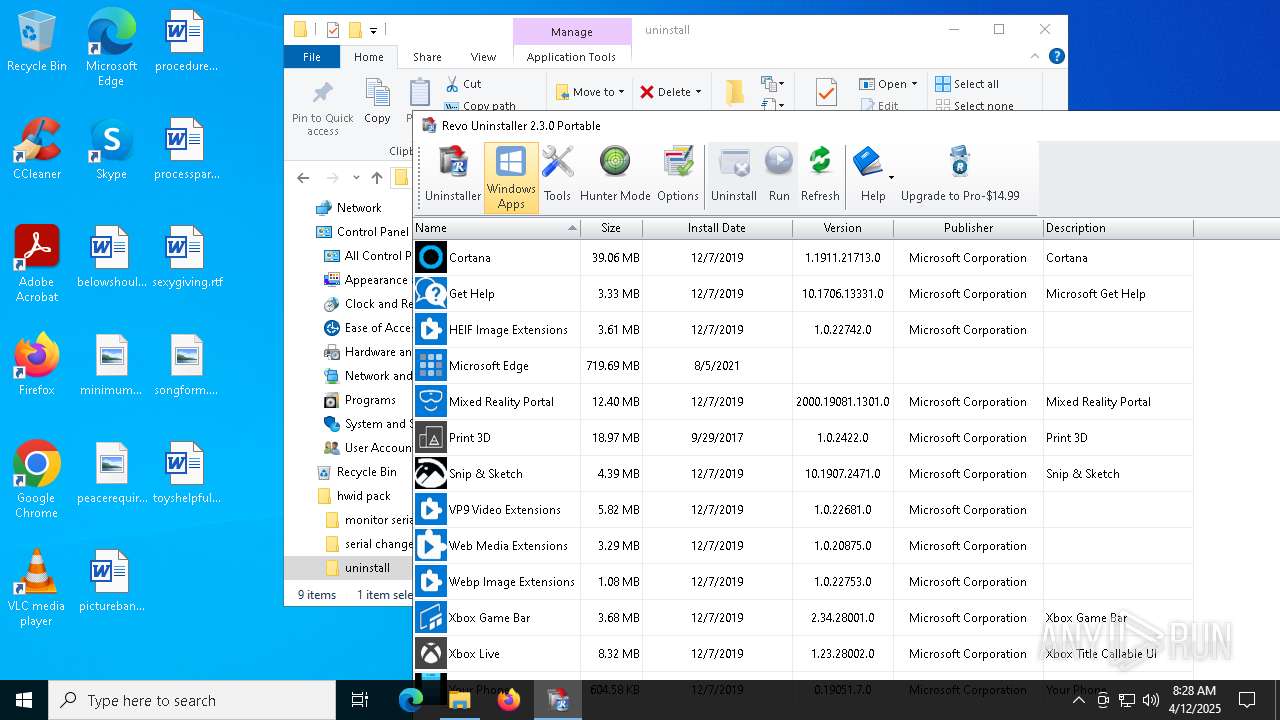
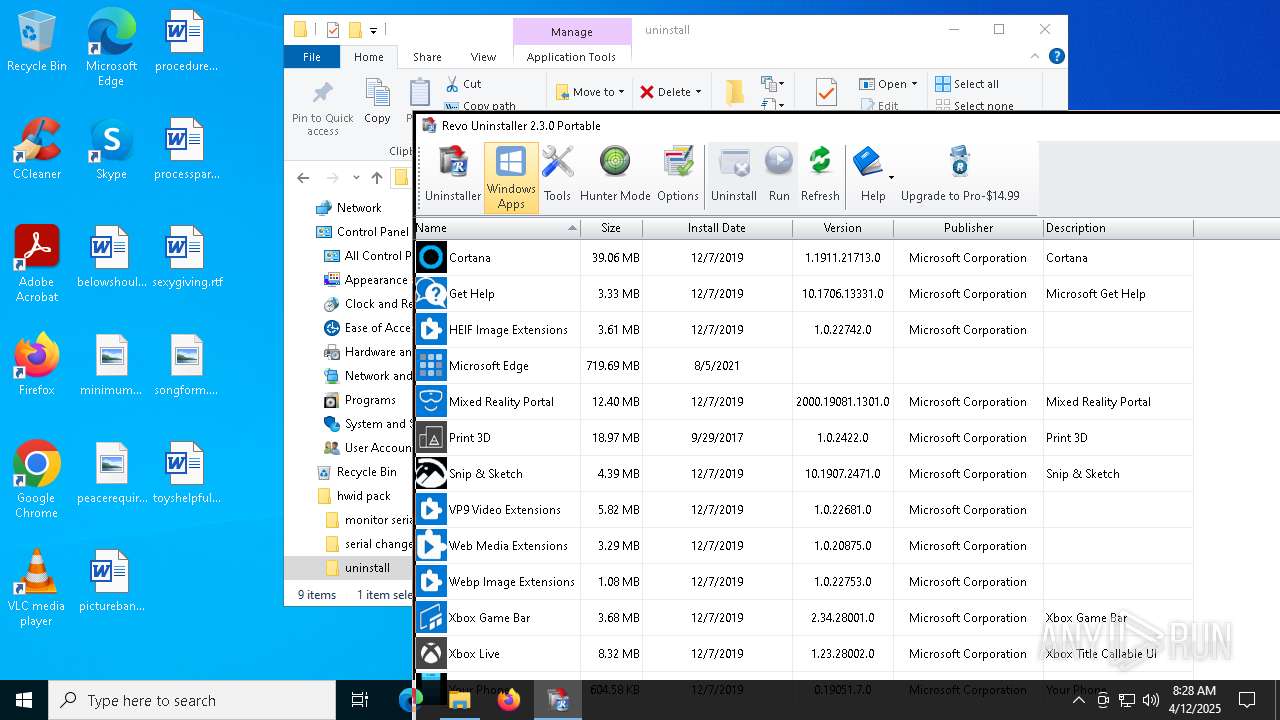
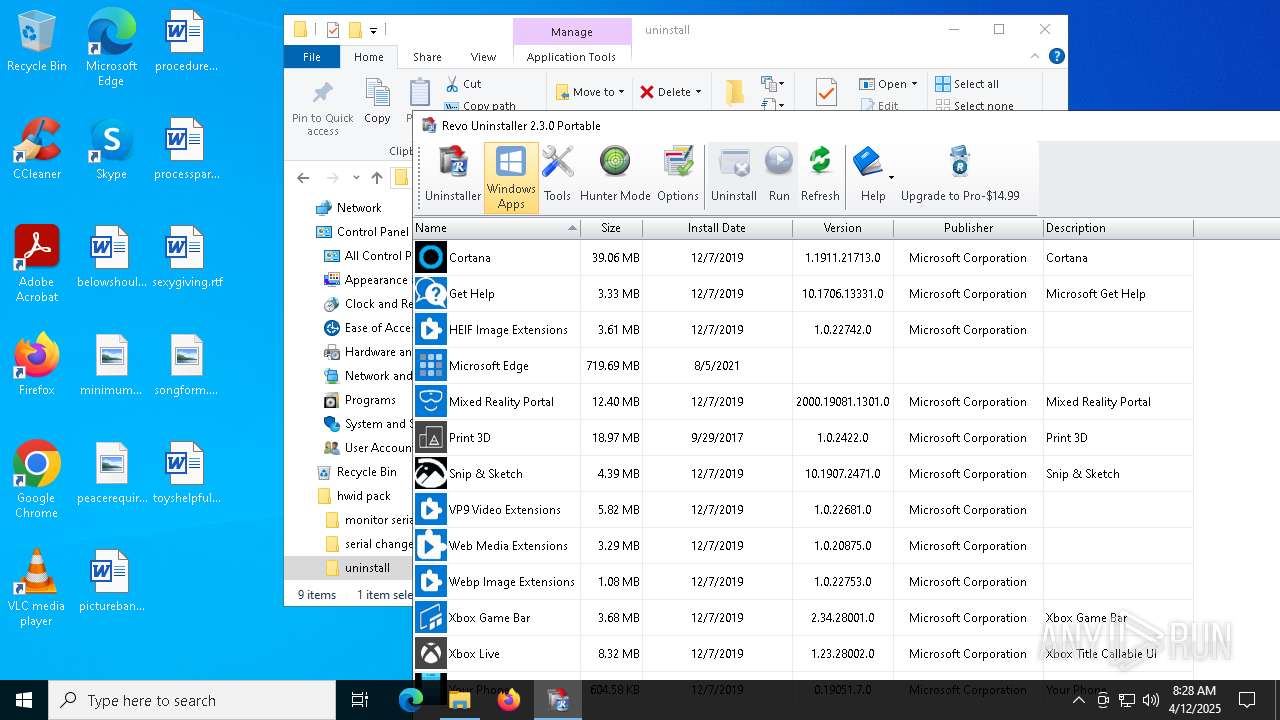
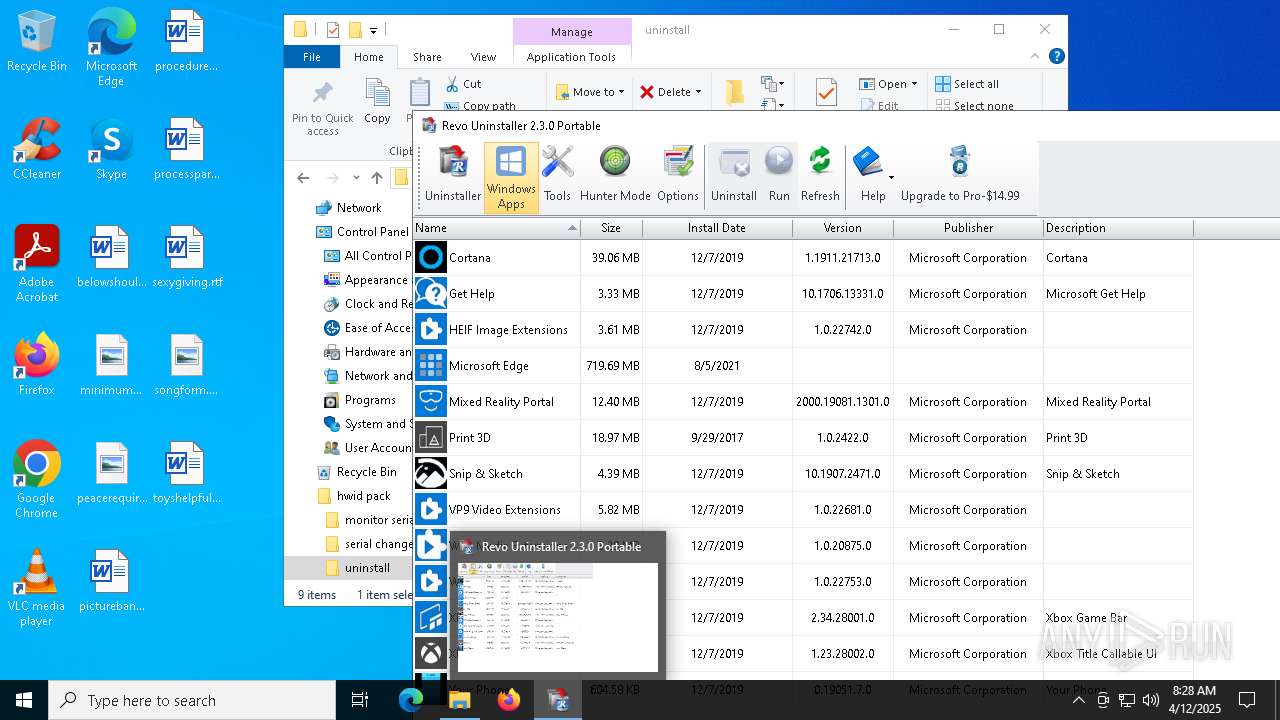
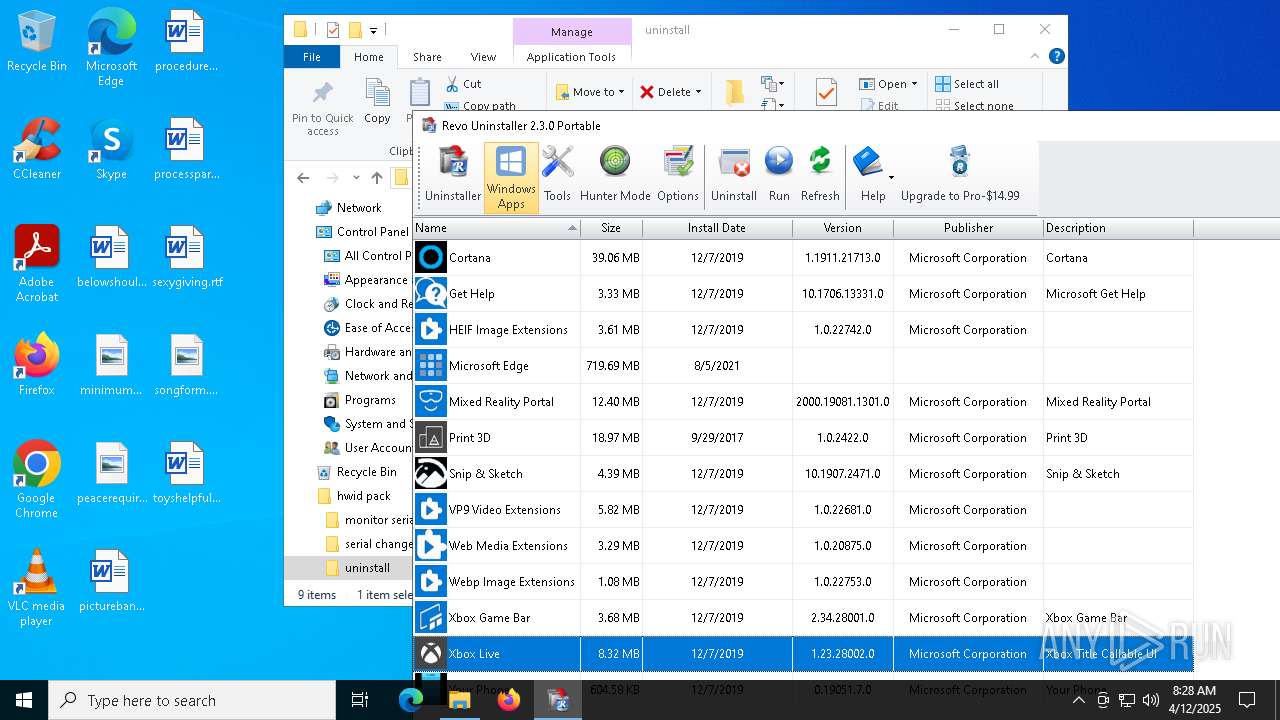
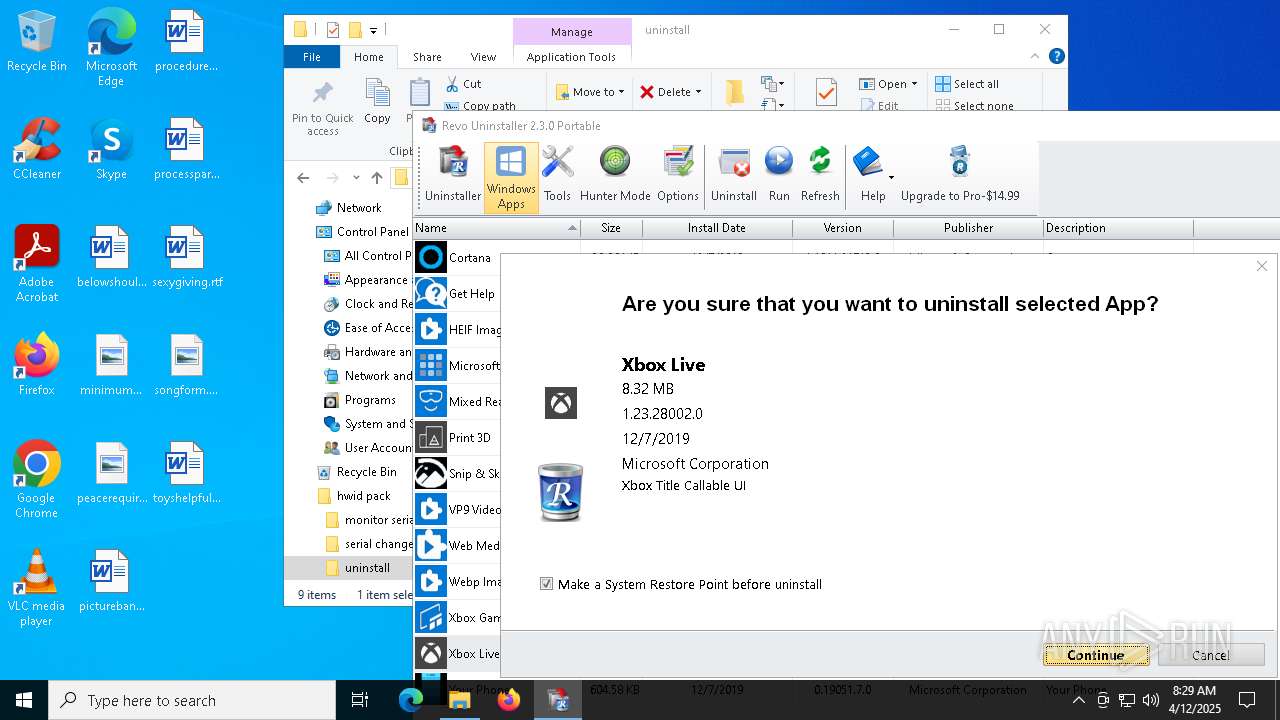
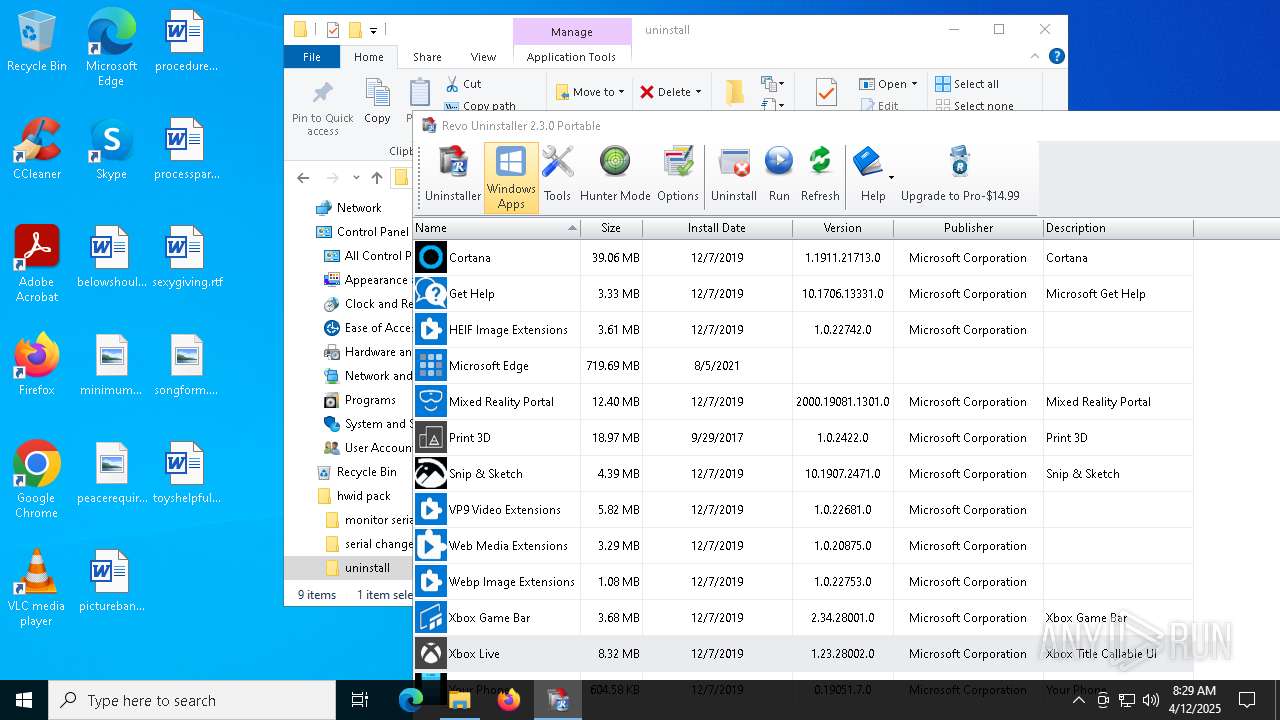
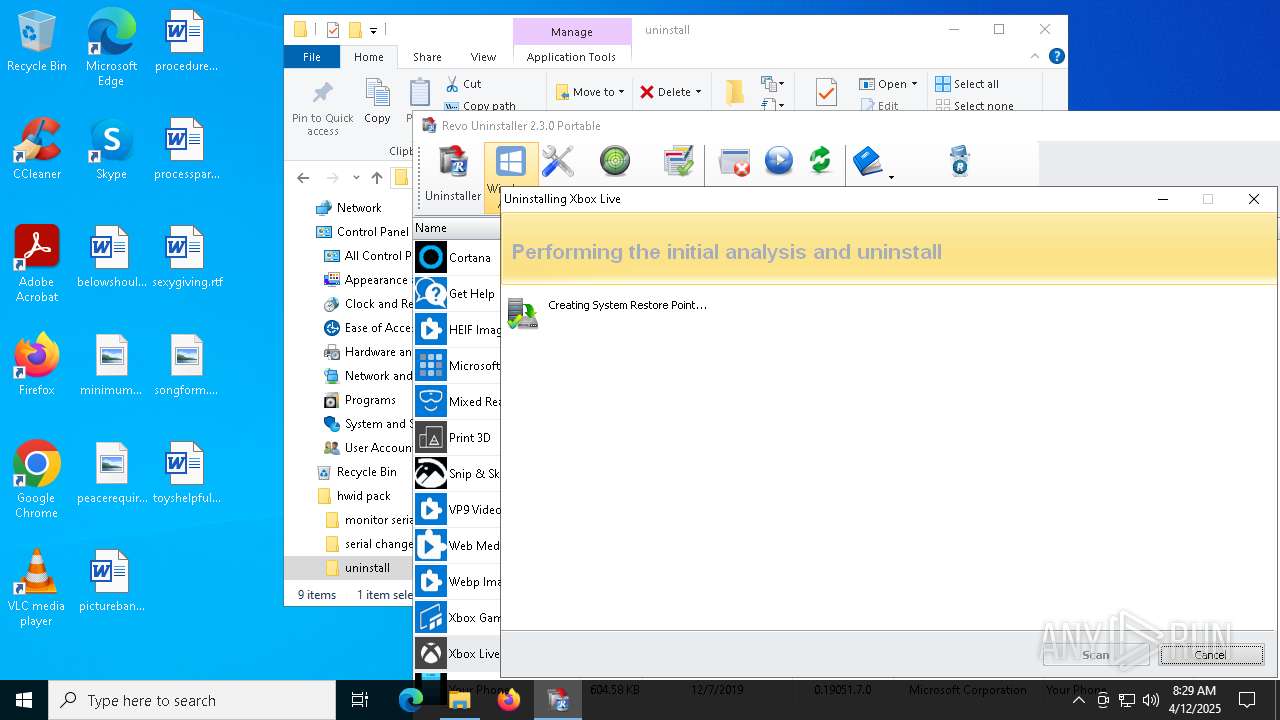
- RevoUn.exe (PID: 6148)
SUSPICIOUS
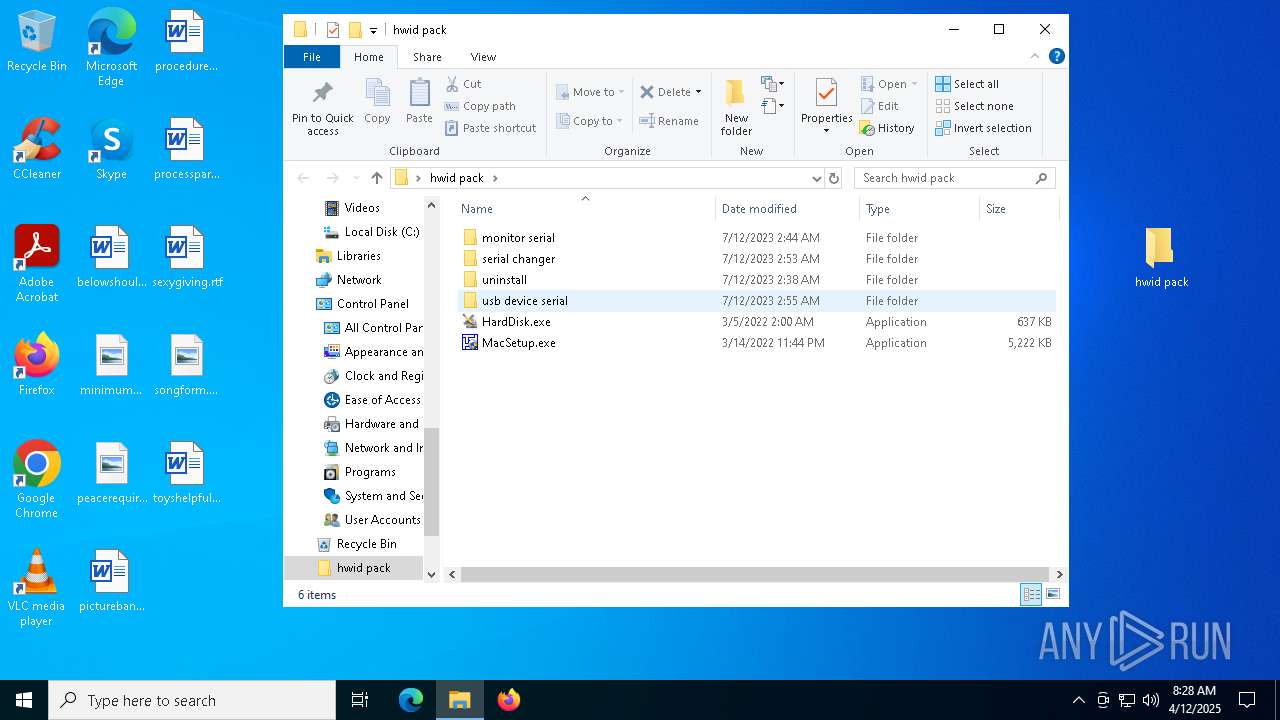
Drops a system driver (possible attempt to evade defenses)
- WinRAR.exe (PID: 6184)
Reads security settings of Internet Explorer
- RevoUn.exe (PID: 6148)
Reads Microsoft Outlook installation path
- RevoUn.exe (PID: 6148)
Reads Internet Explorer settings
- RevoUn.exe (PID: 6148)
Executes as Windows Service
- VSSVC.exe (PID: 300)
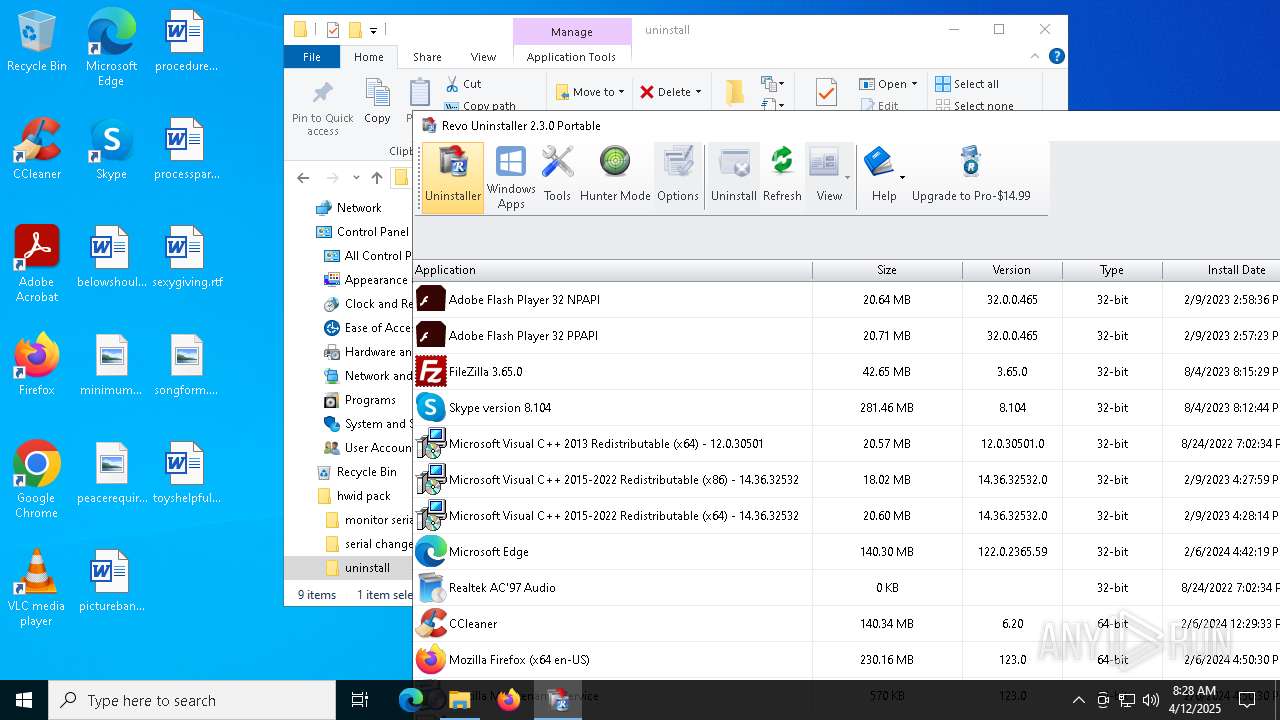
Searches for installed software
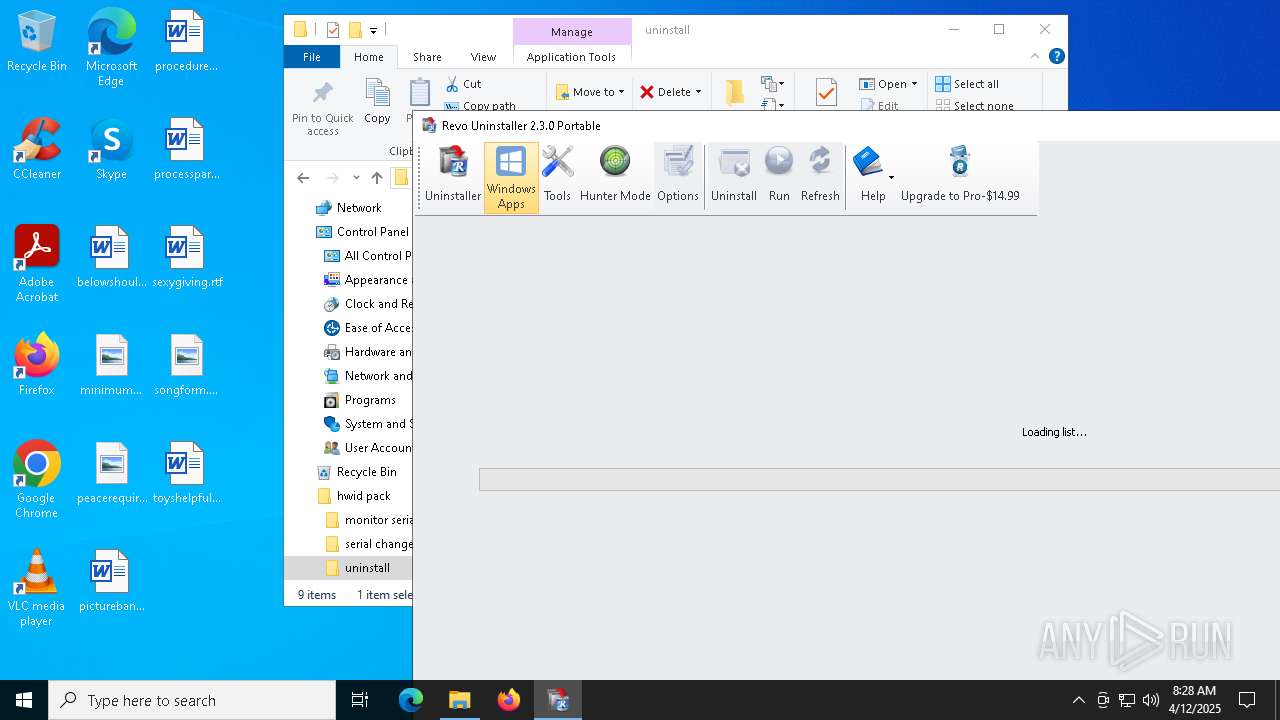
- RevoUn.exe (PID: 6148)
- dllhost.exe (PID: 6540)
INFO
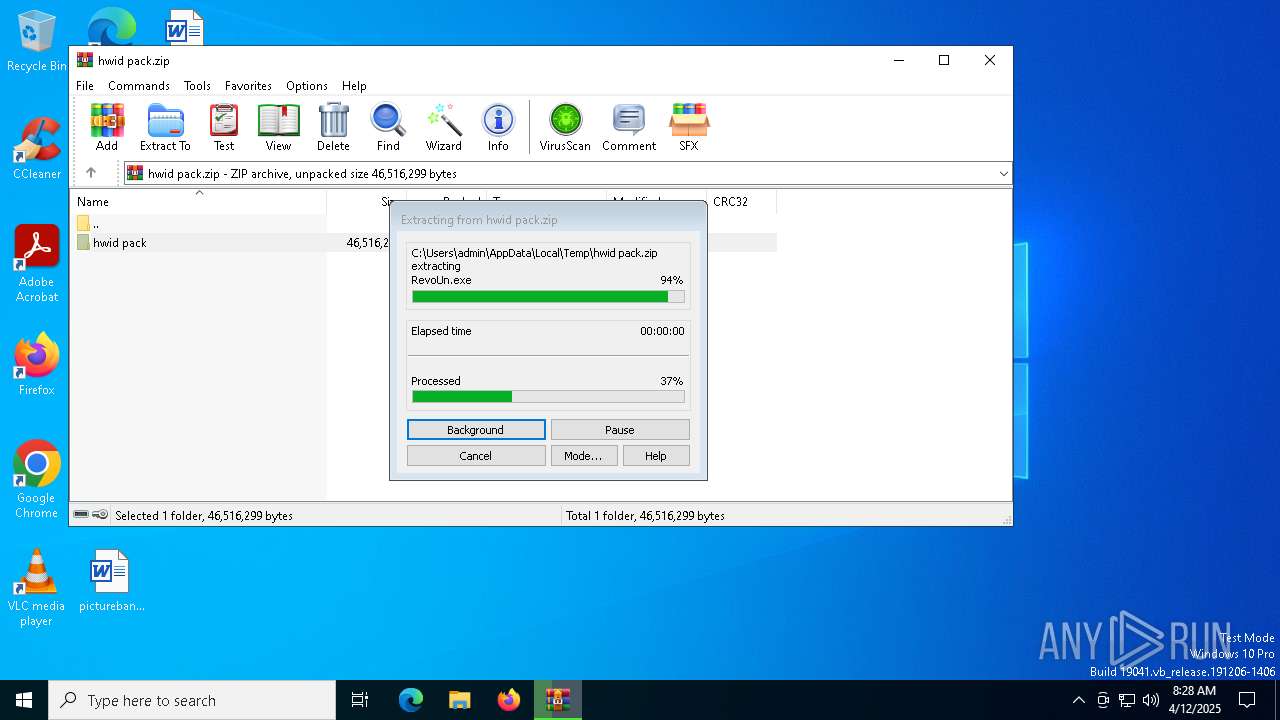
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6184)
The sample compiled with english language support
- WinRAR.exe (PID: 6184)
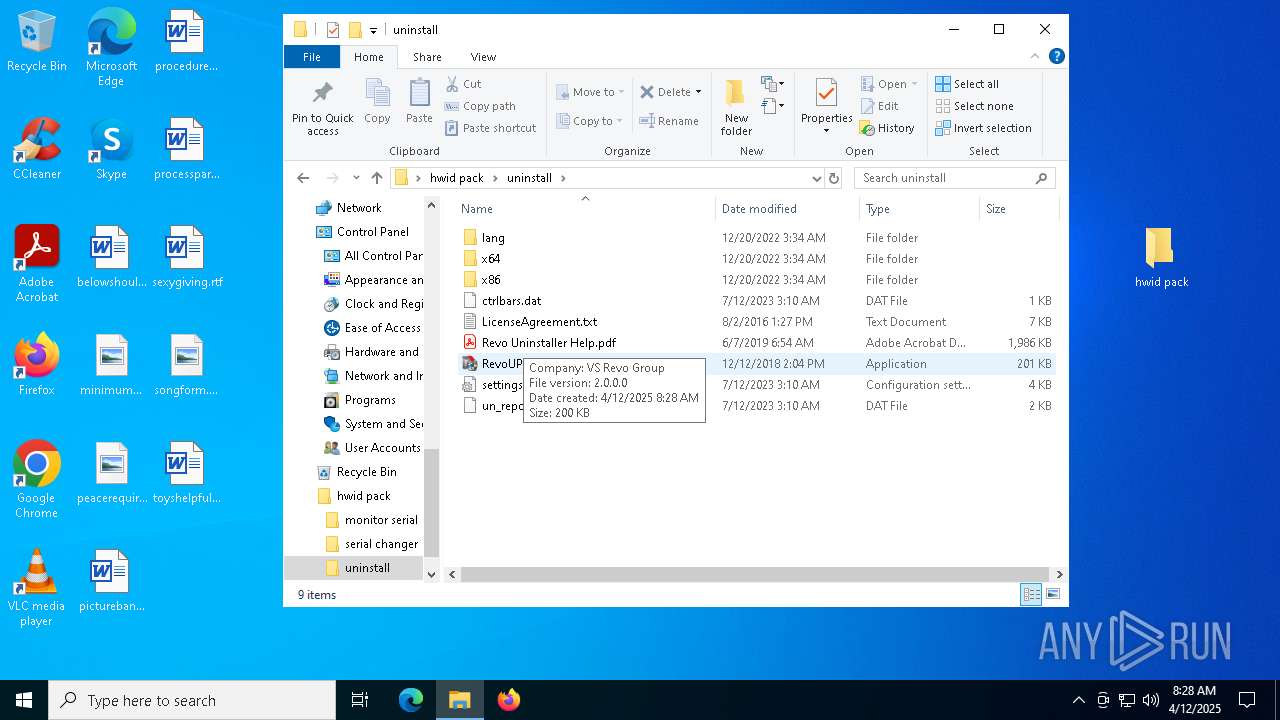
Manual execution by a user
- RevoUPort.exe (PID: 1056)
- RevoUPort.exe (PID: 3180)
Checks supported languages
- RevoUPort.exe (PID: 3180)
- RevoUn.exe (PID: 6148)
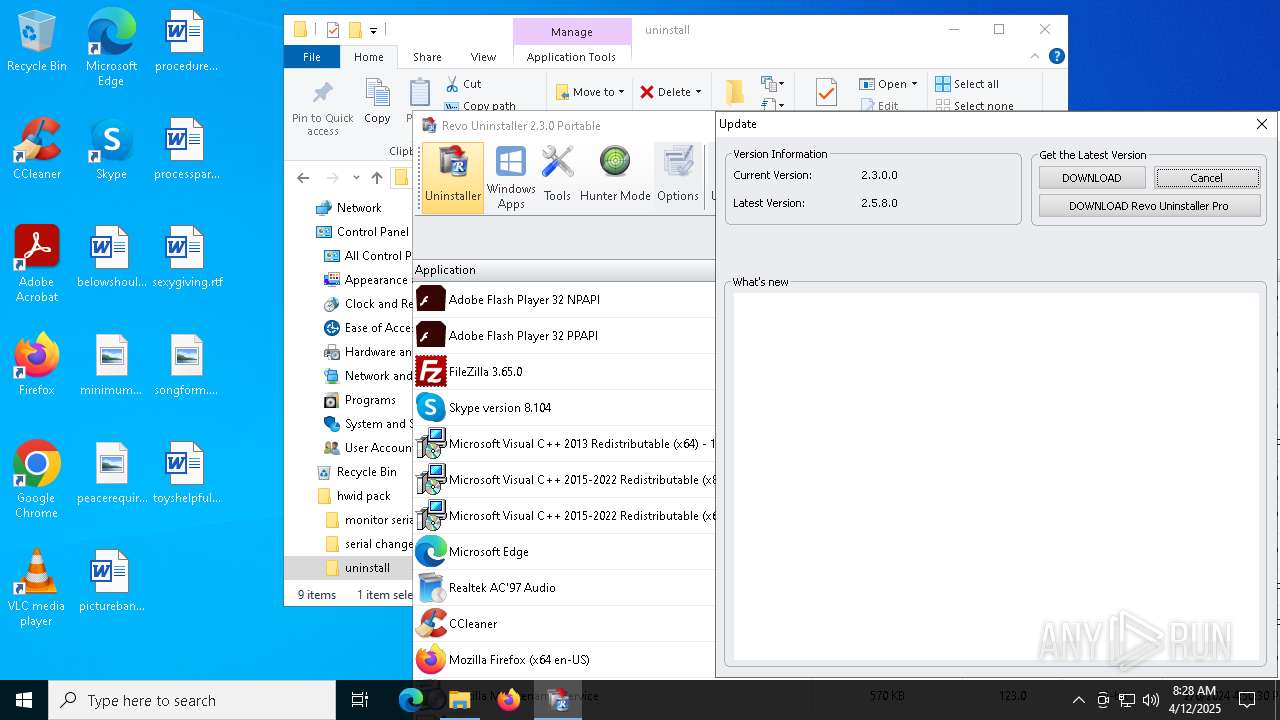
Checks proxy server information
- RevoUn.exe (PID: 6148)
Reads the computer name
- RevoUn.exe (PID: 6148)
Local mutex for internet shortcut management
- RevoUn.exe (PID: 6148)
Reads the software policy settings
- RevoUn.exe (PID: 6148)
Reads the machine GUID from the registry
- RevoUn.exe (PID: 6148)
Create files in a temporary directory
- RevoUn.exe (PID: 6148)
Creates files or folders in the user directory
- RevoUn.exe (PID: 6148)
Process checks computer location settings
- RevoUn.exe (PID: 6148)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2023:07:11 19:49:08 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | hwid pack/ |
Total processes
138
Monitored processes
7
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1056 | "C:\Users\admin\Desktop\hwid pack\uninstall\RevoUPort.exe" | C:\Users\admin\Desktop\hwid pack\uninstall\RevoUPort.exe | — | explorer.exe | |||||||||||
User: admin Company: VS Revo Group Integrity Level: MEDIUM Exit code: 3221226540 Version: 2, 0, 0, 0 Modules
| |||||||||||||||
| 1180 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3180 | "C:\Users\admin\Desktop\hwid pack\uninstall\RevoUPort.exe" | C:\Users\admin\Desktop\hwid pack\uninstall\RevoUPort.exe | explorer.exe | ||||||||||||
User: admin Company: VS Revo Group Integrity Level: HIGH Exit code: 0 Version: 2, 0, 0, 0 Modules
| |||||||||||||||
| 6148 | "C:\Users\admin\Desktop\hwid pack\uninstall\x64\RevoUn.exe" | C:\Users\admin\Desktop\hwid pack\uninstall\x64\RevoUn.exe | RevoUPort.exe | ||||||||||||
User: admin Company: VS Revo Group Integrity Level: HIGH Description: Revo Uninstaller Version: 2.3.0.0 Modules
| |||||||||||||||
| 6184 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\hwid pack.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 6540 | C:\WINDOWS\system32\DllHost.exe /Processid:{F32D97DF-E3E5-4CB9-9E3E-0EB5B4E49801} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
7 750
Read events
7 552
Write events
172
Delete events
26
Modification events
| (PID) Process: | (6184) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6184) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6184) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6184) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\hwid pack.zip | |||
| (PID) Process: | (6184) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6184) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6184) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6184) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6184) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
| (PID) Process: | (6184) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
Executable files
19
Suspicious files
24
Text files
56
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
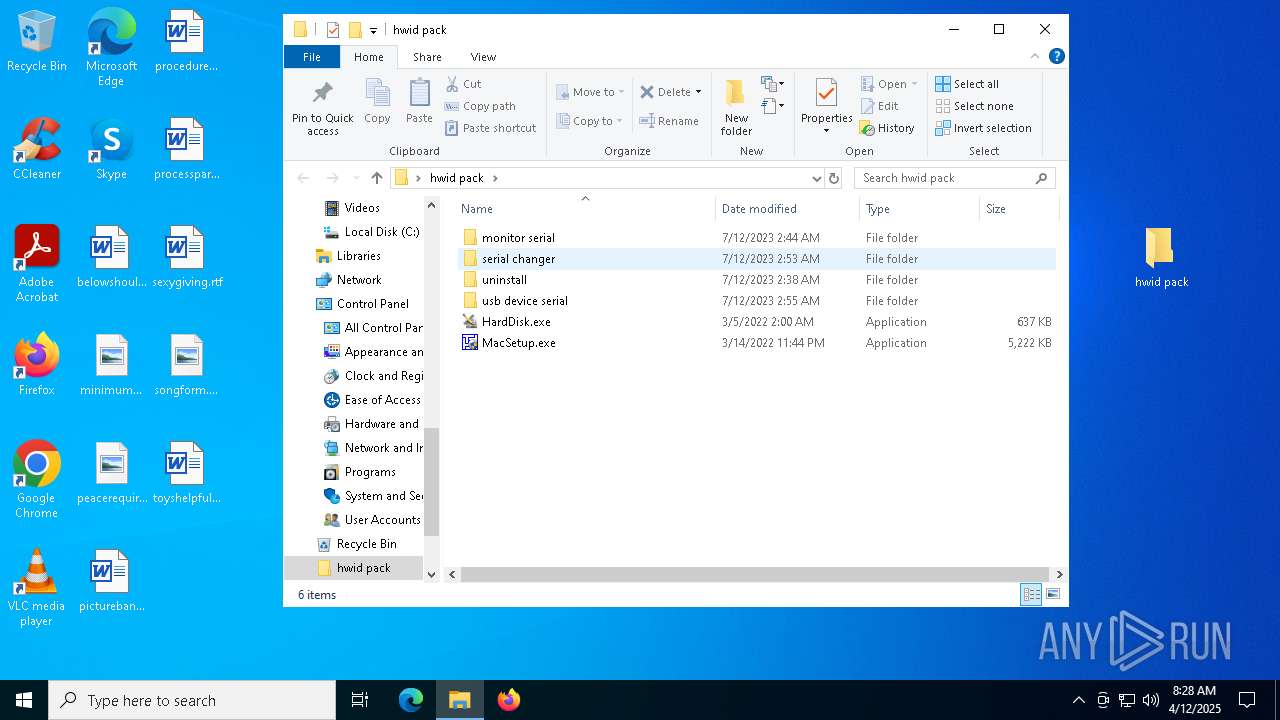
| 6184 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6184.31354\hwid pack\serial changer\amifldrv64.sys | executable | |
MD5:785045F8B25CD2E937DDC6B09DEBE01A | SHA256:37073E42FFA0322500F90CD7E3C8D02C4CDD695D31C77E81560ABEC20BFB68BA | |||
| 6184 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6184.31354\hwid pack\serial changer\AMIDEWIN.EXE | executable | |
MD5:182EC3A59BD847FB1BC3E12A41D48FA6 | SHA256:948DBD2BC128F8DC08267E110020FEE3FF5DE17CF4AAEF89372DE29623AF96FA | |||
| 6184 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6184.31354\hwid pack\monitor serial\Info.txt | text | |
MD5:DF95ACFBA3051D021EC94E47726BBD07 | SHA256:61350CE9D700627A156845DFEE77C44703280B16FD30BC1C216BFFC1CC82C0A1 | |||
| 6184 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6184.31354\hwid pack\MacSetup.exe | executable | |
MD5:A7C8CF1D50EBE630A7D0C47686A0ABBF | SHA256:A453B3EA8D8133531FAD26B18701C694C324CC201E3069D07E99F0E100908C1A | |||
| 6184 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6184.31354\hwid pack\serial changer\README.txt | text | |
MD5:0E28E605E0988892043002E8D6FA719B | SHA256:1541F150F12295D926578FC8920F2F398D046BDDA66BC3026BF2533BBA07666B | |||
| 6184 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6184.31354\hwid pack\monitor serial\restart64.exe | executable | |
MD5:297AA19BADE534A791D053CA190B74AD | SHA256:5F779BB822AEDAF5BD11693CDF73F6C7C3342F37371A78C07C2ACA1E15DBFD00 | |||
| 6184 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6184.31354\hwid pack\serial changer\AMIDEWINx64.EXE | executable | |
MD5:6A6505B2413D2C7B16C6D059448DB9E5 | SHA256:53E3B72F8EB13ACF3CB69D4CB124E8DC64FC541555C3C95CC8003B8046853955 | |||
| 6184 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6184.31354\hwid pack\serial changer\UCOREDLL.DLL | executable | |
MD5:8370F3114924ED6C53741DE7A253625A | SHA256:78A4D8E5E8C33793E5A2020325D3A49E92E4826167742E93179BDACBF167B409 | |||
| 6184 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6184.31354\hwid pack\serial changer\UCORESYS.SYS | executable | |
MD5:9555D36FB21B993E5C4B98C2FC2B3671 | SHA256:FD6F56189CD723B32FC06392867FCD5128E63D8B5801E4F7A83523F820531981 | |||
| 6184 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6184.31354\hwid pack\uninstall\lang\albanian.ini | text | |
MD5:29D9BADF9A370C44D849F83D84370A24 | SHA256:7497147AFF5C43B779BAD6868C34930230BD1E93D6F725D37BCFB047DC15E7CA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
24
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6148 | RevoUn.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAFnjx%2FviCJV2LCnDmt7siA%3D | unknown | — | — | whitelisted |
6148 | RevoUn.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTWEwdftt6hG98BgtOX4dN8bpJVCQQUak5Qv5honVt7IHXUWQF5SGaSMgYCEAMrS8jhZ%2BfydwpiiyxF8aA%3D | unknown | — | — | whitelisted |
6148 | RevoUn.exe | GET | 200 | 142.250.186.67:80 | http://c.pki.goog/r/r4.crl | unknown | — | — | whitelisted |
6148 | RevoUn.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | unknown | — | — | whitelisted |
6148 | RevoUn.exe | GET | 200 | 142.250.186.67:80 | http://c.pki.goog/r/gsr1.crl | unknown | — | — | whitelisted |
6148 | RevoUn.exe | GET | 200 | 142.250.186.67:80 | http://o.pki.goog/we2/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTuMJxAT2trYla0jia%2F5EUSmLrk3QQUdb7Ed66J9kQ3fc%2BxaB8dGuvcNFkCEHGvPPlOXde9CQBZ60wQP4Y%3D | unknown | — | — | whitelisted |
6148 | RevoUn.exe | GET | 200 | 142.250.186.67:80 | http://o.pki.goog/we2/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTuMJxAT2trYla0jia%2F5EUSmLrk3QQUdb7Ed66J9kQ3fc%2BxaB8dGuvcNFkCEQC9ZcgYQ%2FurORDkqLZcs5MY | unknown | — | — | whitelisted |
1388 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1388 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6148 | RevoUn.exe | 146.20.152.114:443 | www.revouninstaller.com | RACKSPACE | US | whitelisted |
6148 | RevoUn.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
6148 | RevoUn.exe | 23.45.97.130:443 | 791448185ff546d6838b-efb466af81ecd558bdca51a0b78387ec.ssl.cf1.rackcdn.com | AKAMAI-AS | DE | whitelisted |
6148 | RevoUn.exe | 142.250.184.234:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
www.revouninstaller.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
791448185ff546d6838b-efb466af81ecd558bdca51a0b78387ec.ssl.cf1.rackcdn.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
f057a20f961f56a72089-b74530d2d26278124f446233f95622ef.ssl.cf1.rackcdn.com |
| whitelisted |
c.pki.goog |
| whitelisted |