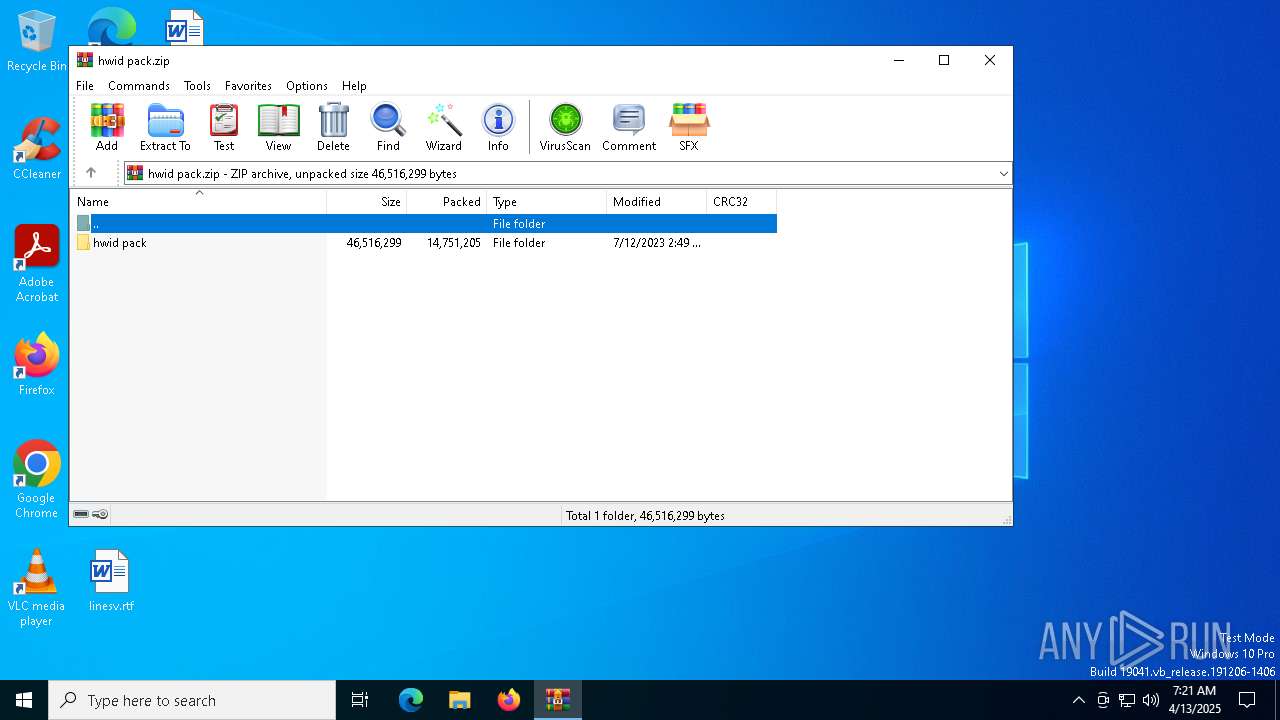
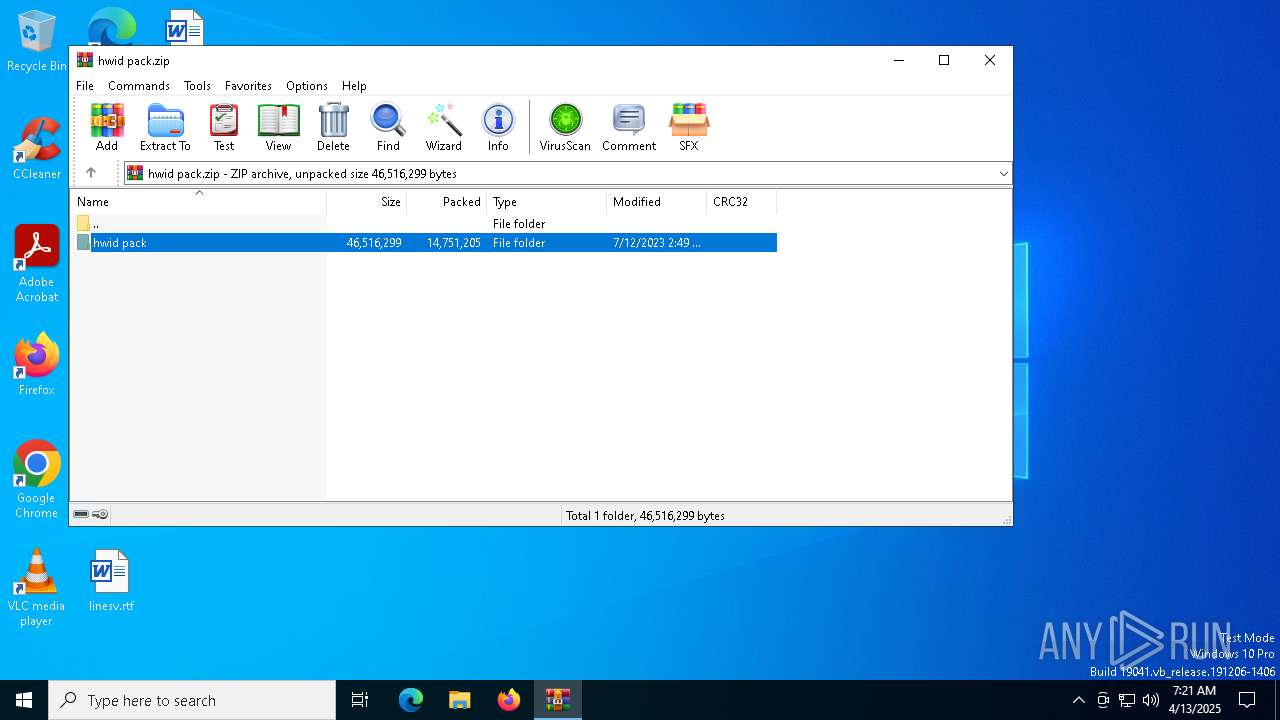
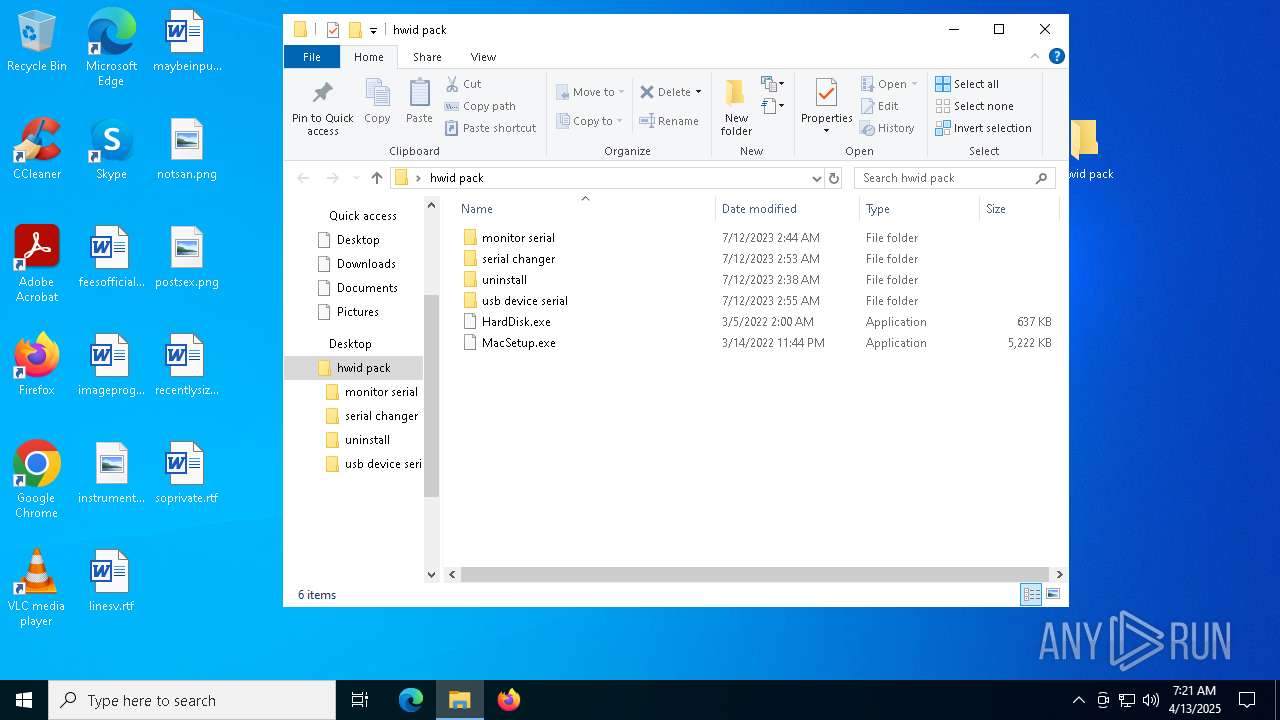
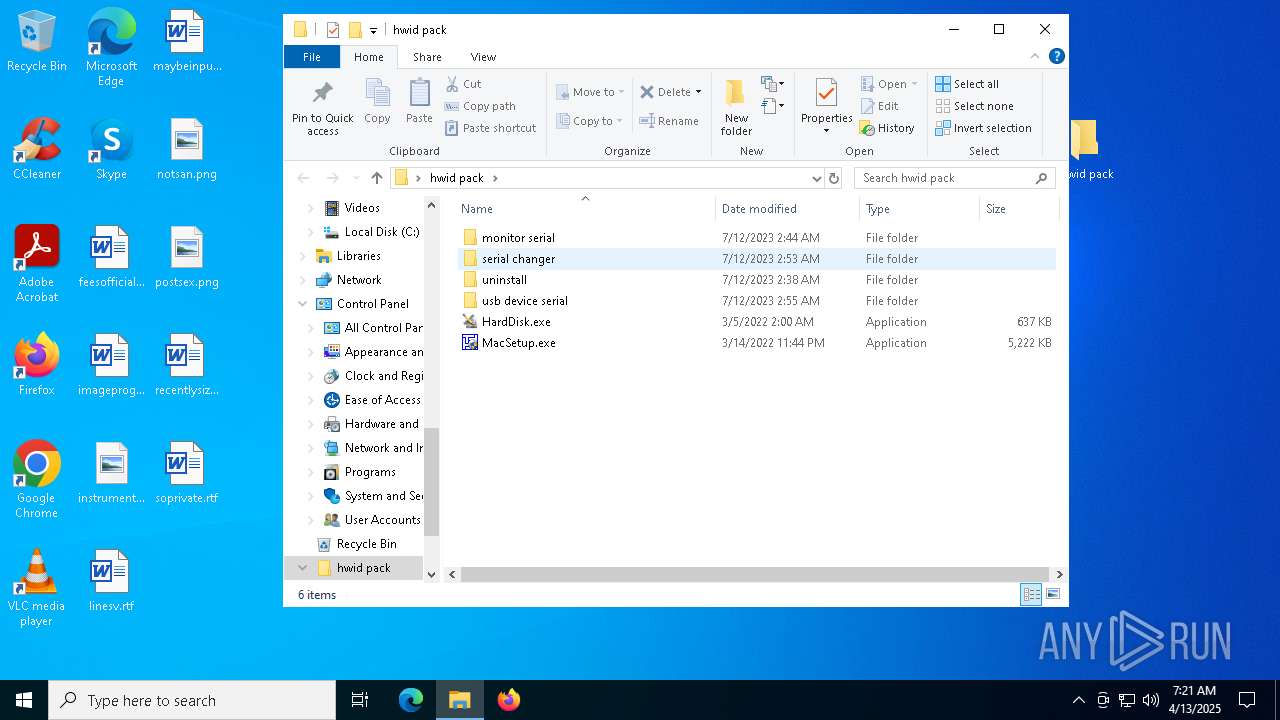
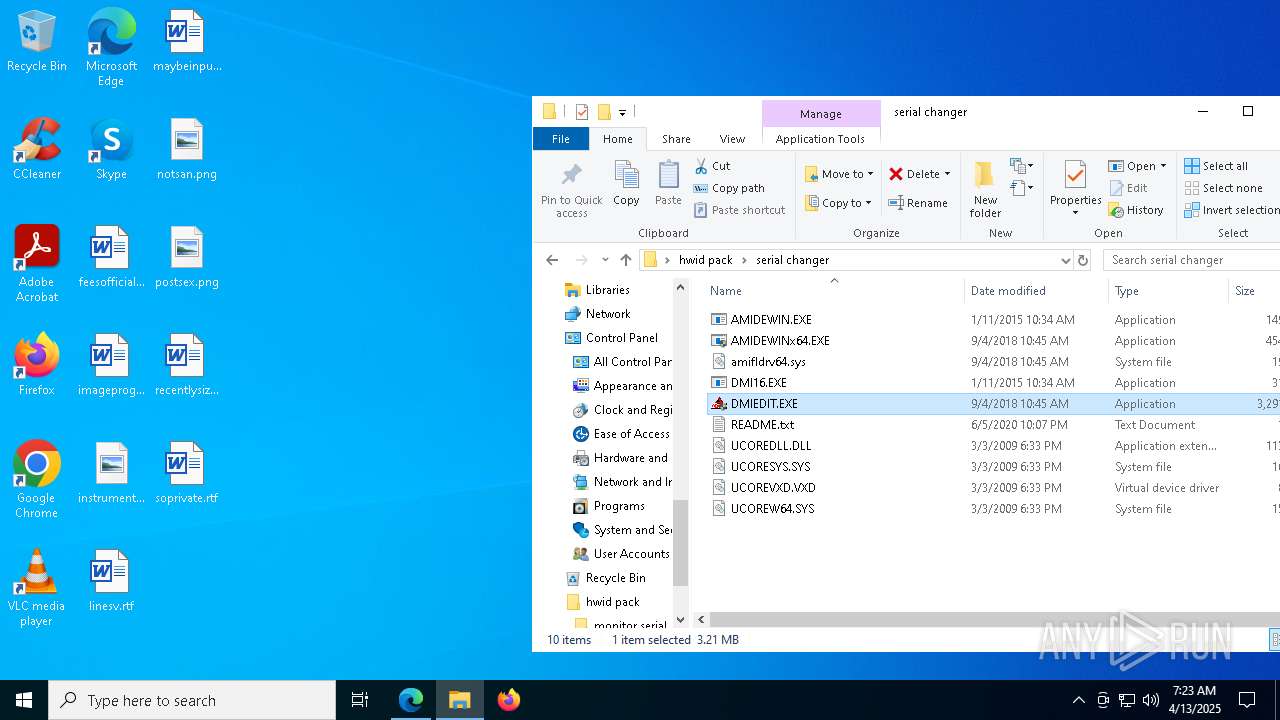
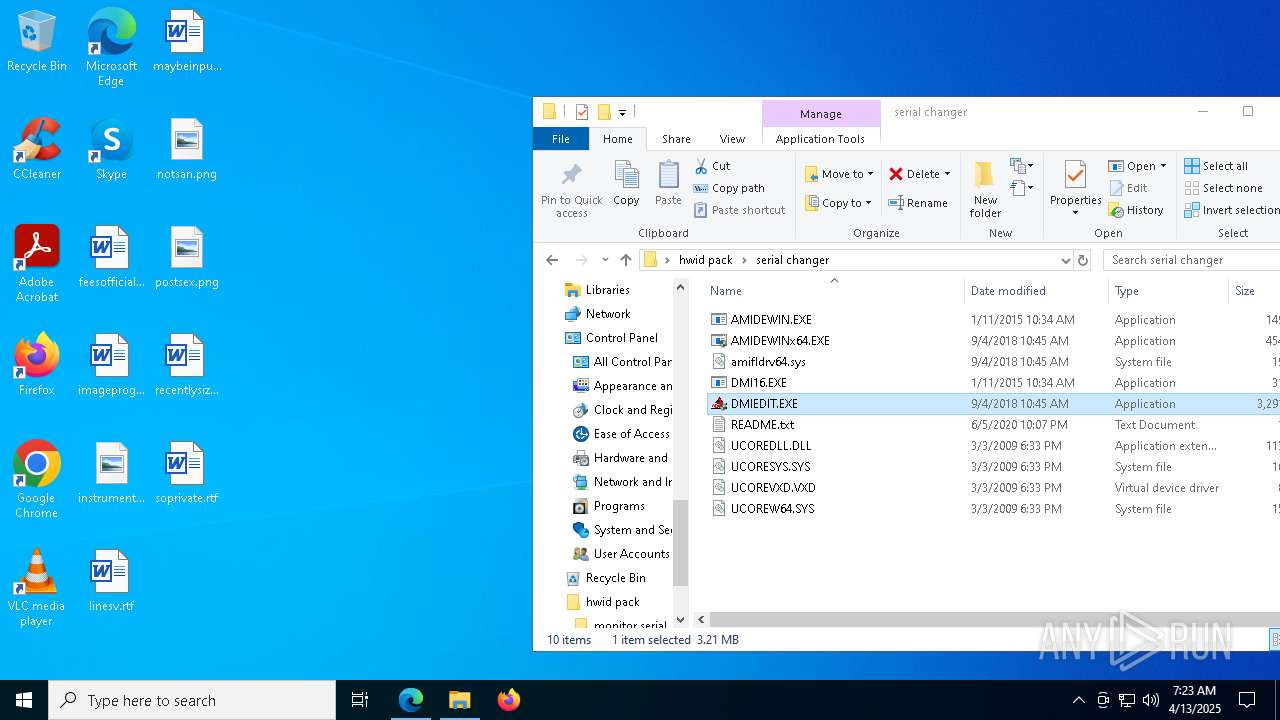
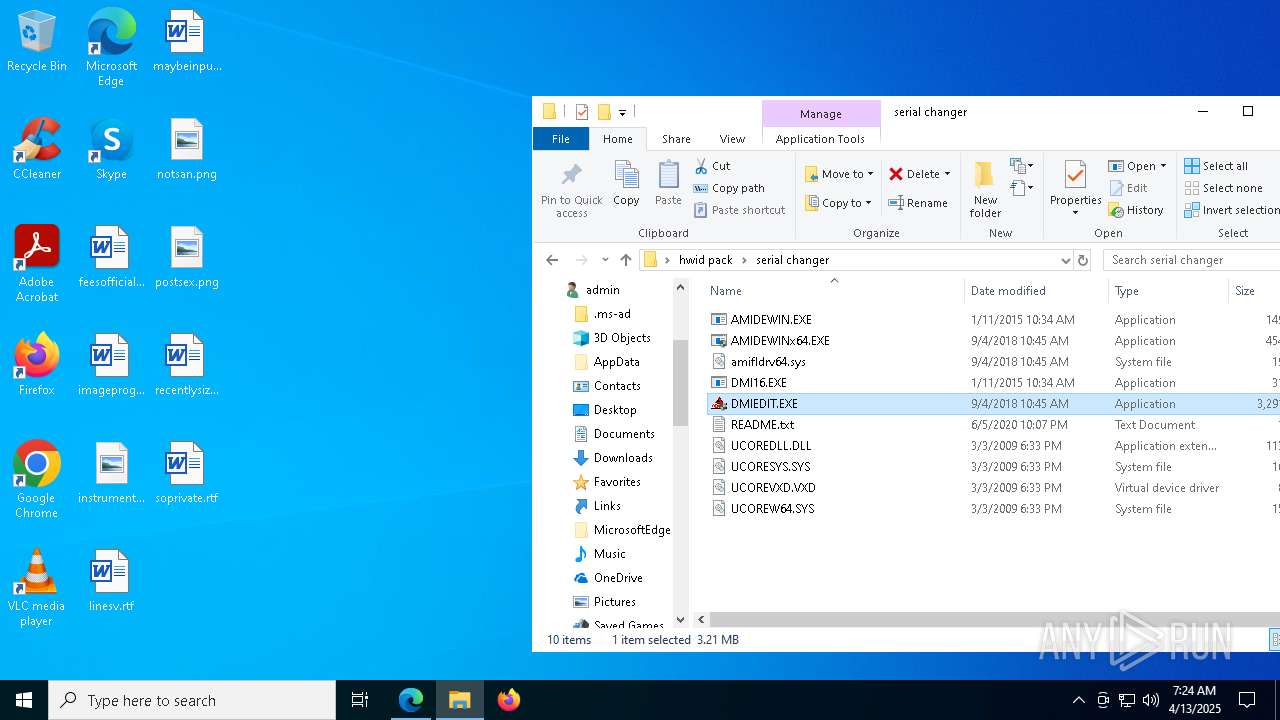
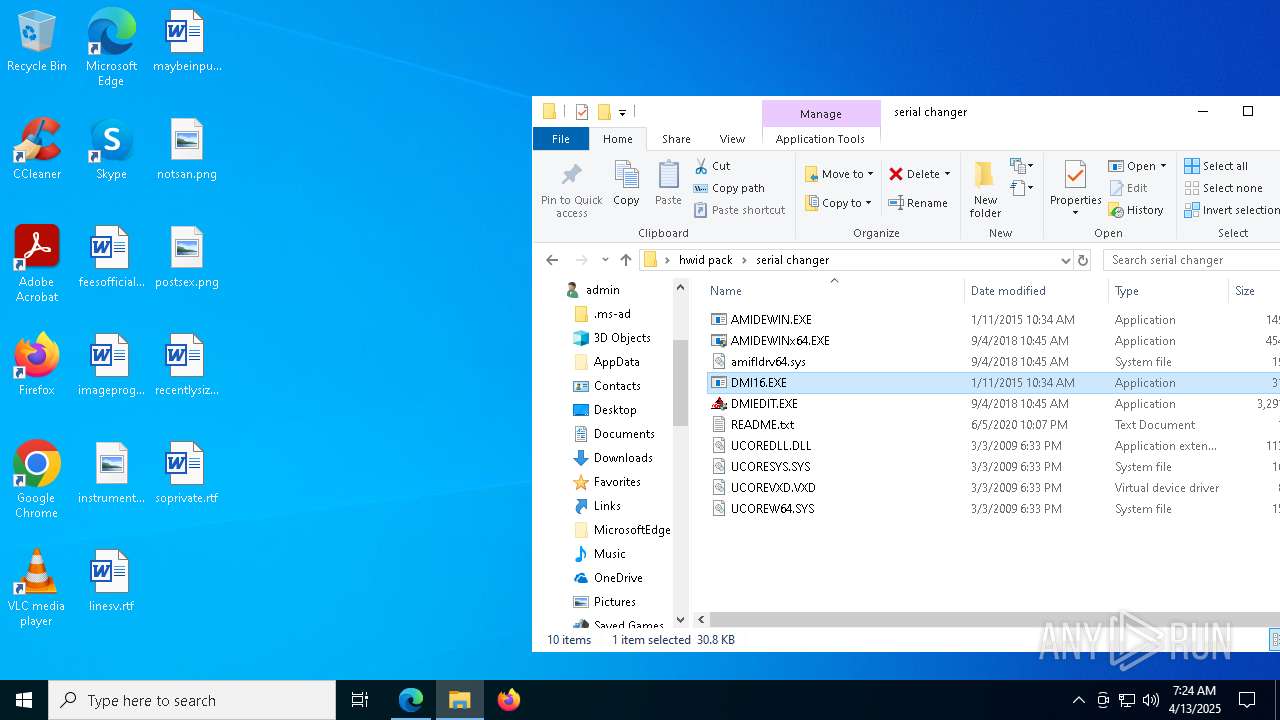
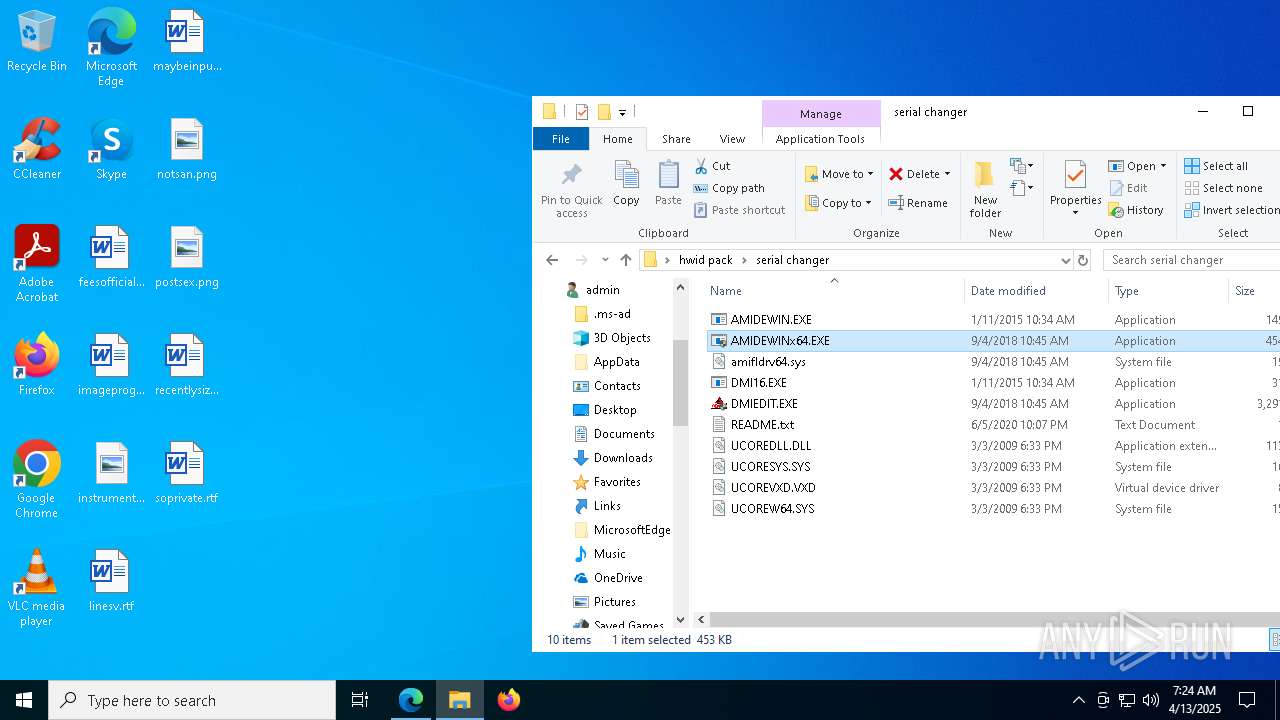
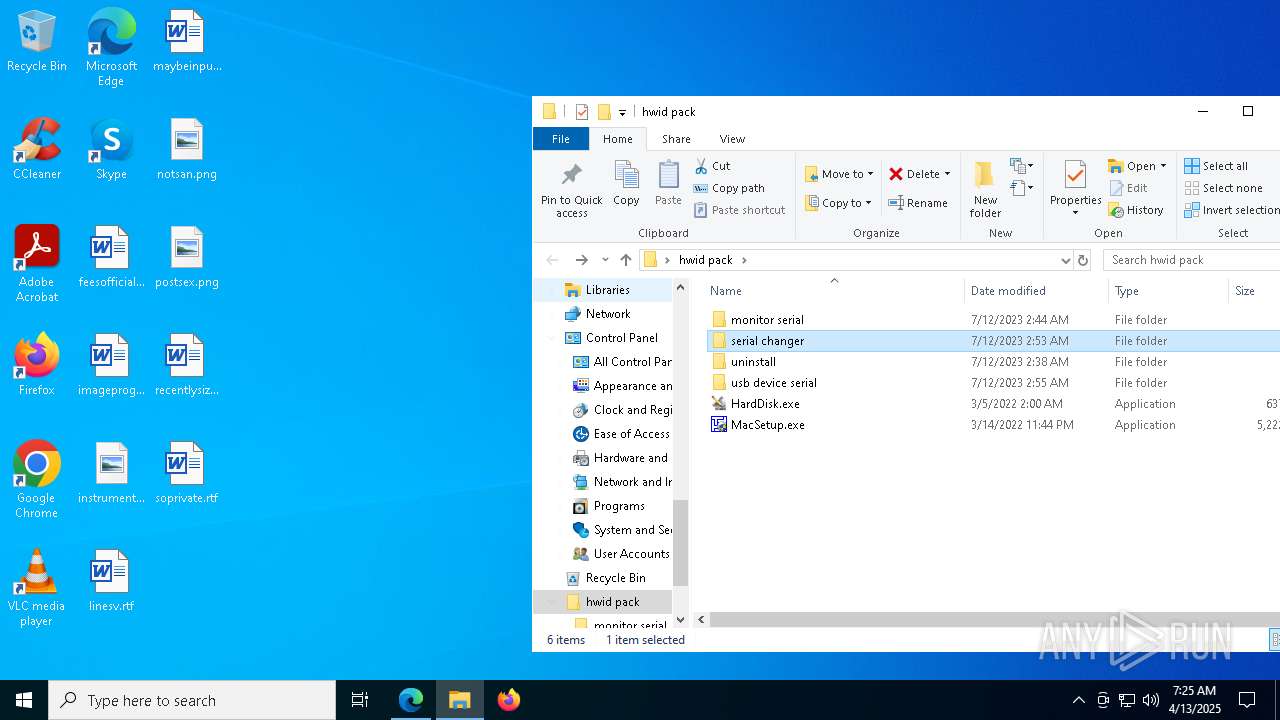
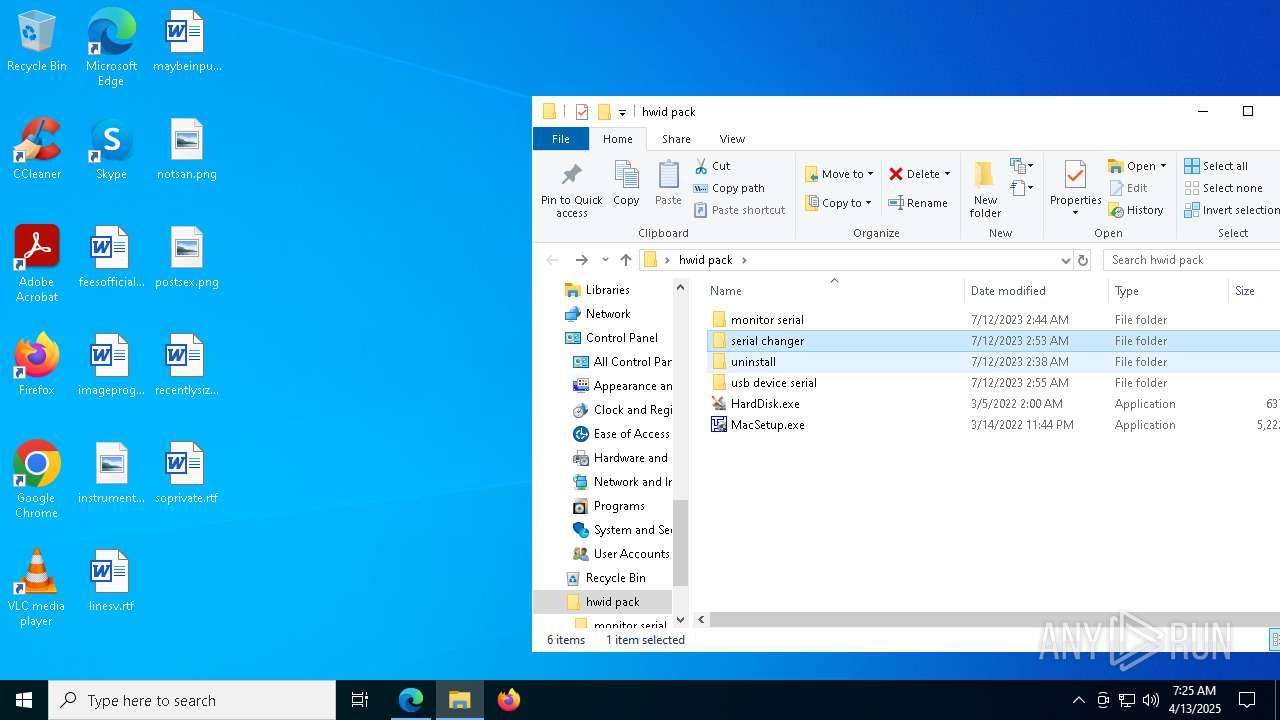
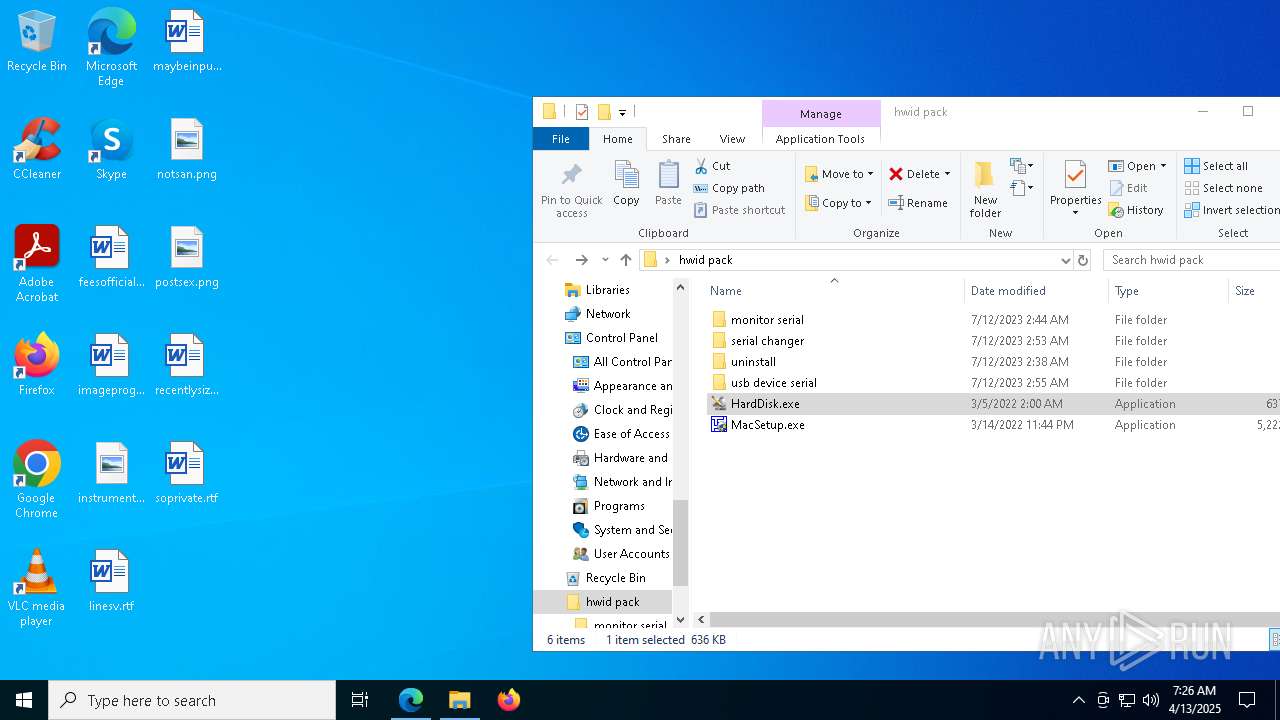
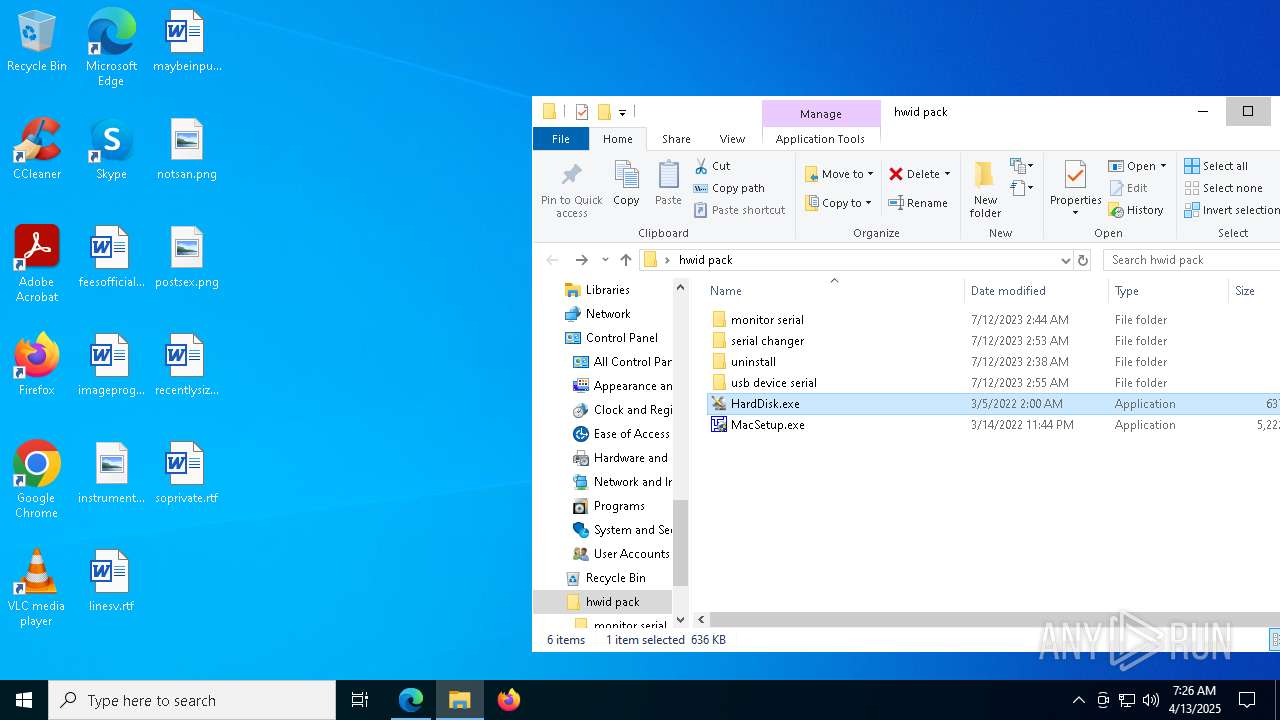
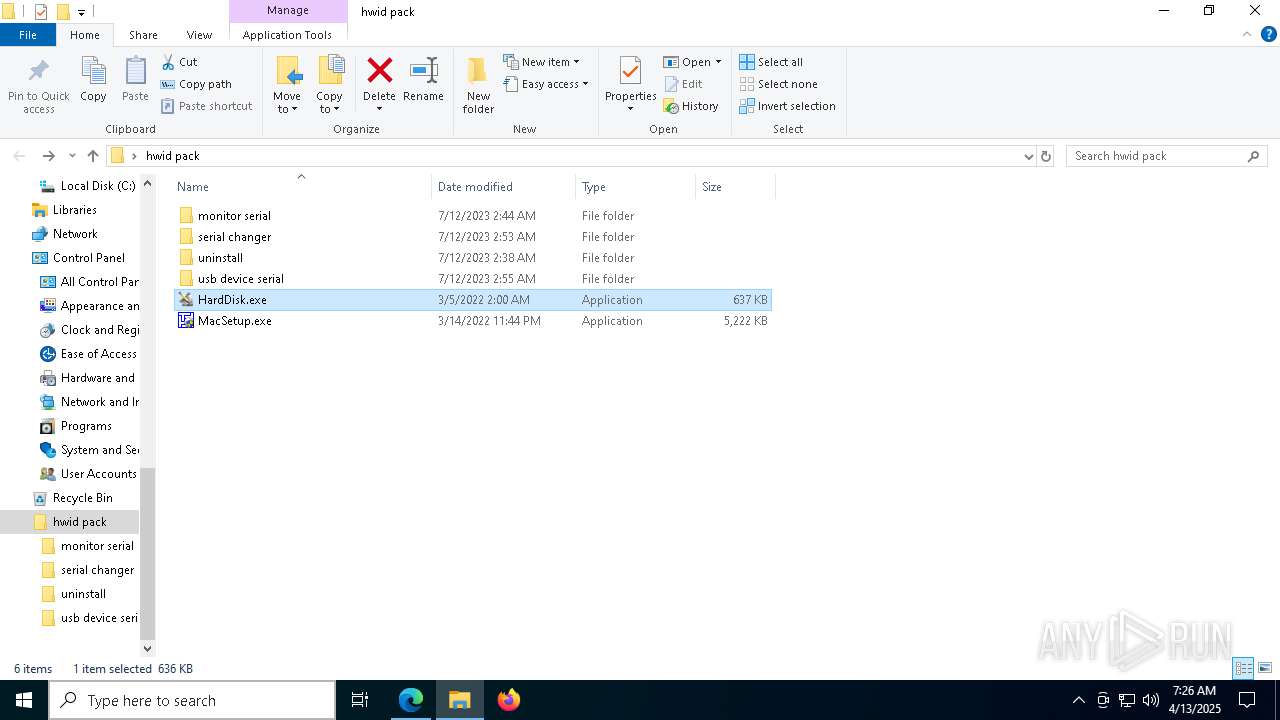
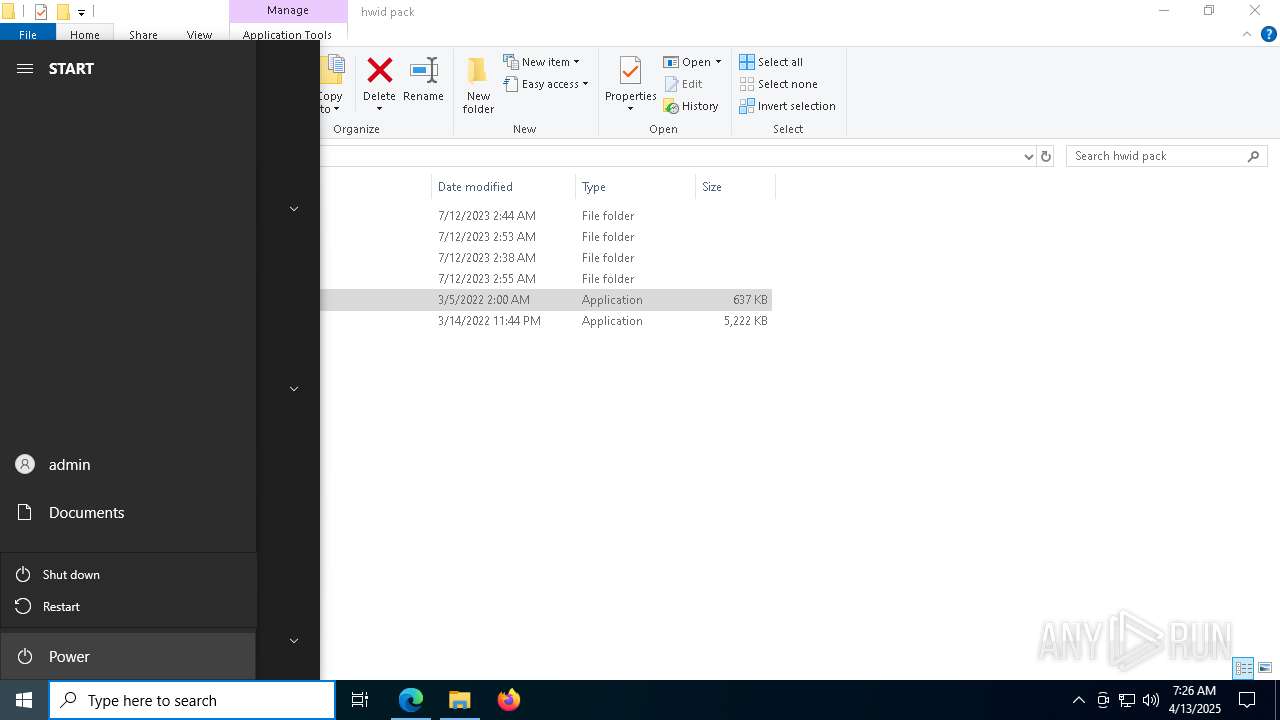
| File name: | hwid pack.zip |
| Full analysis: | https://app.any.run/tasks/5ef38e1e-ef06-4742-8f28-80e54f7012cc |
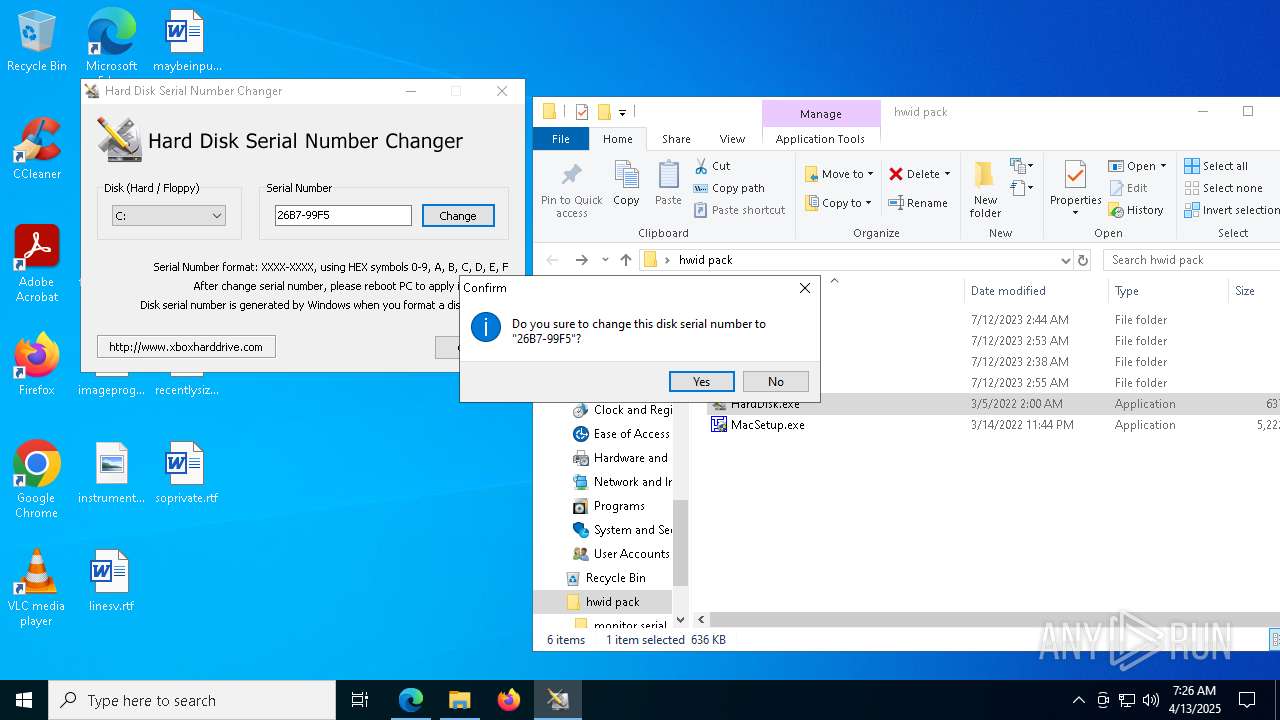
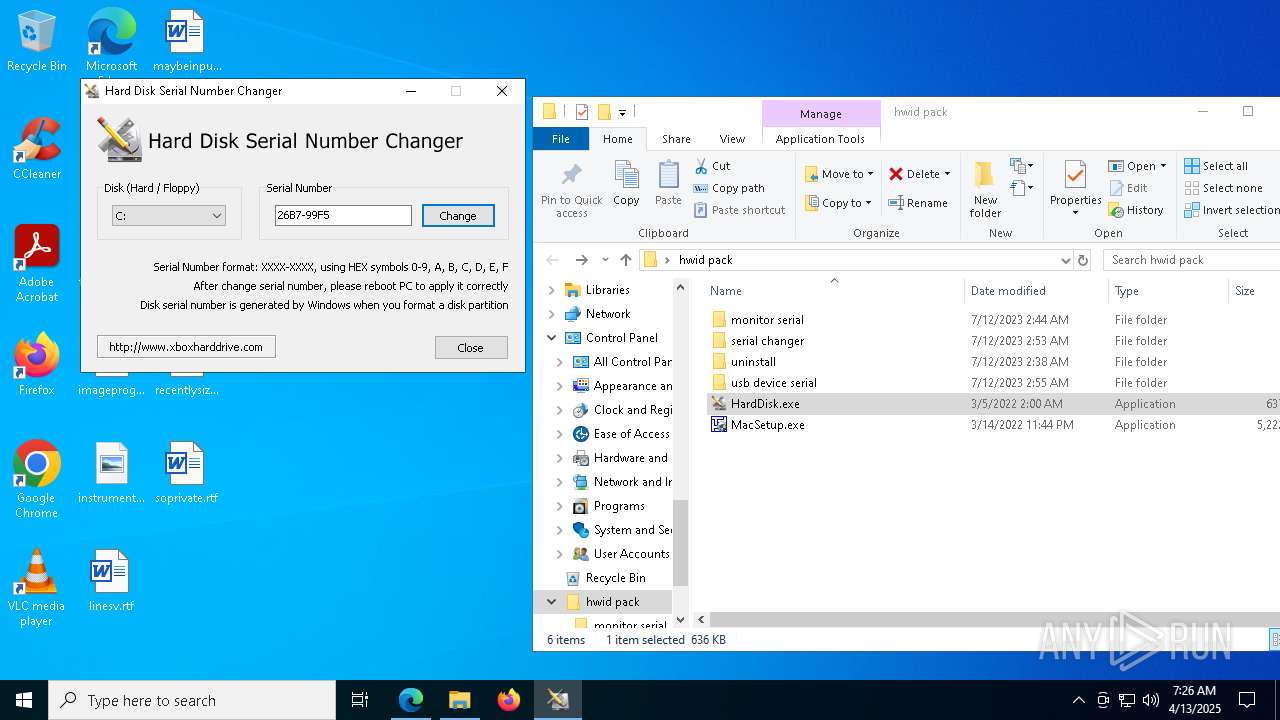
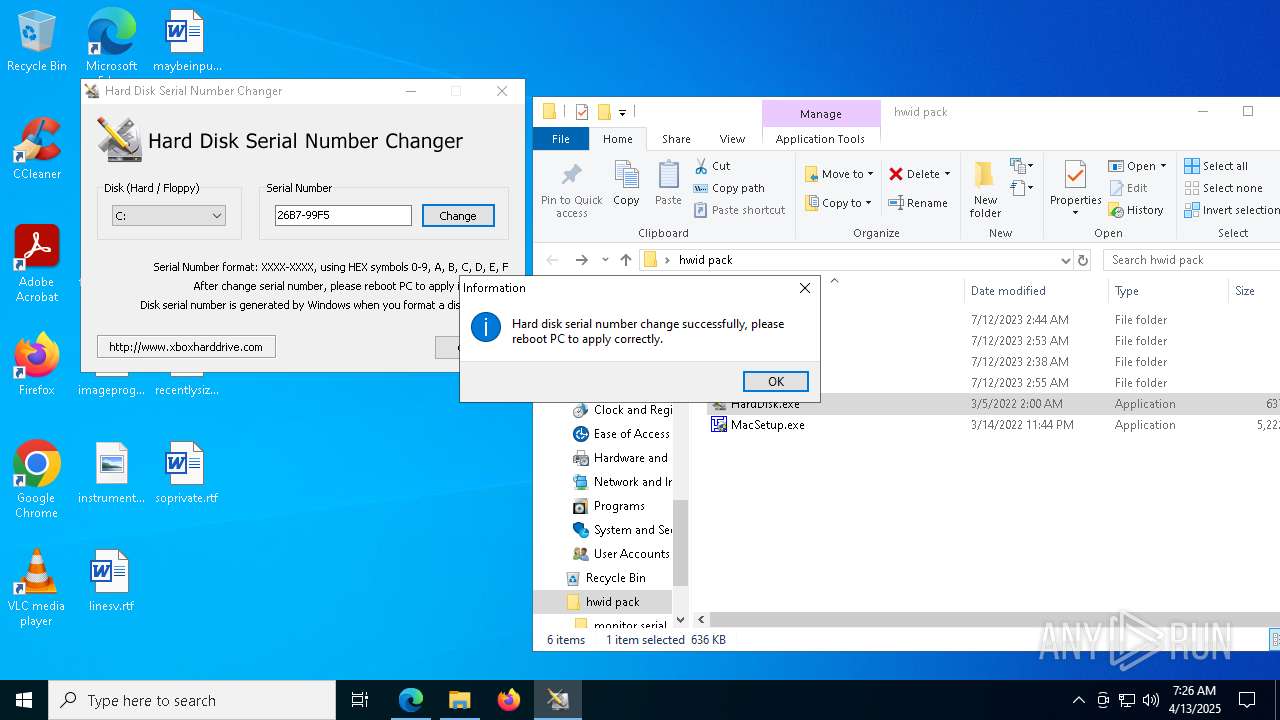
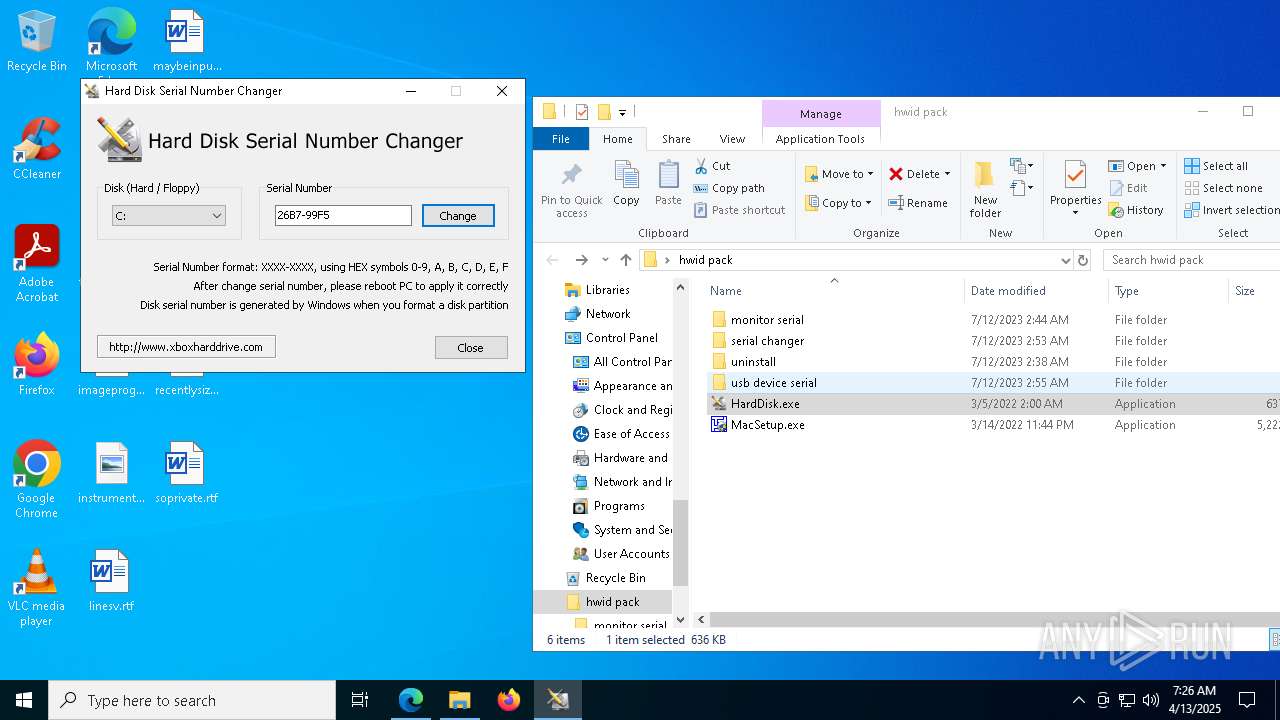
| Verdict: | Malicious activity |
| Analysis date: | April 13, 2025, 07:21:30 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | 734C14A94F1778E506606804D3566594 |
| SHA1: | 8CBD6A9C512EDAAB288A0FD24C7C2D7D71C3999D |
| SHA256: | 41CAEB1DAB6AB9DA4571B88CD0A0A2B3A21CE305909358E538A04F988D4A139F |
| SSDEEP: | 196608:ELlI5+lEzBGc3CqWeo/X/Mbw4+OPexK4Ux:GNYBG1DXQwXBBq |
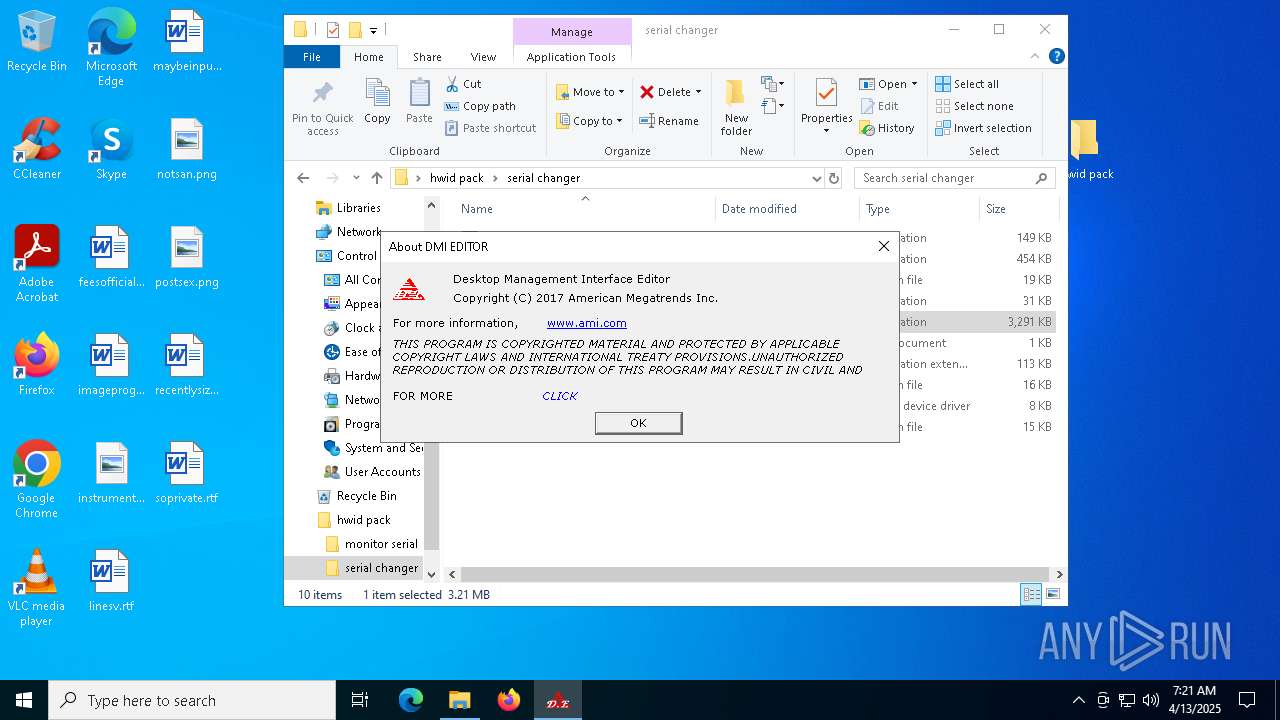
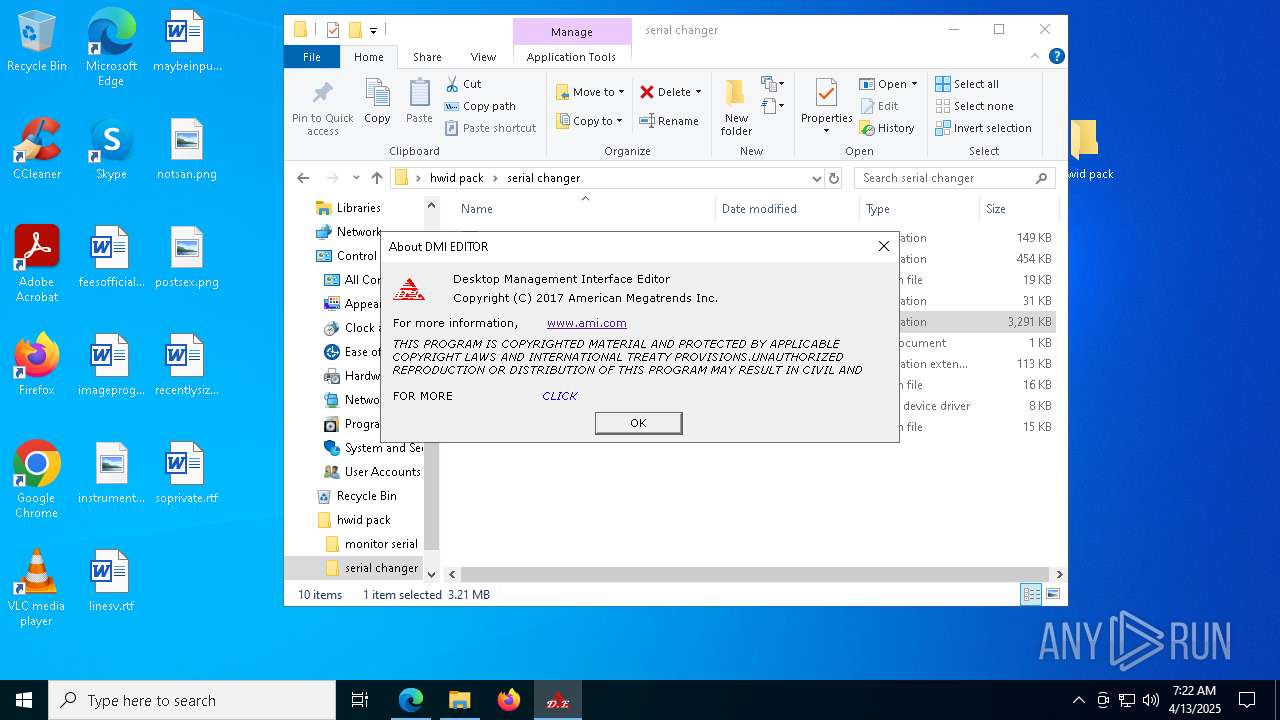
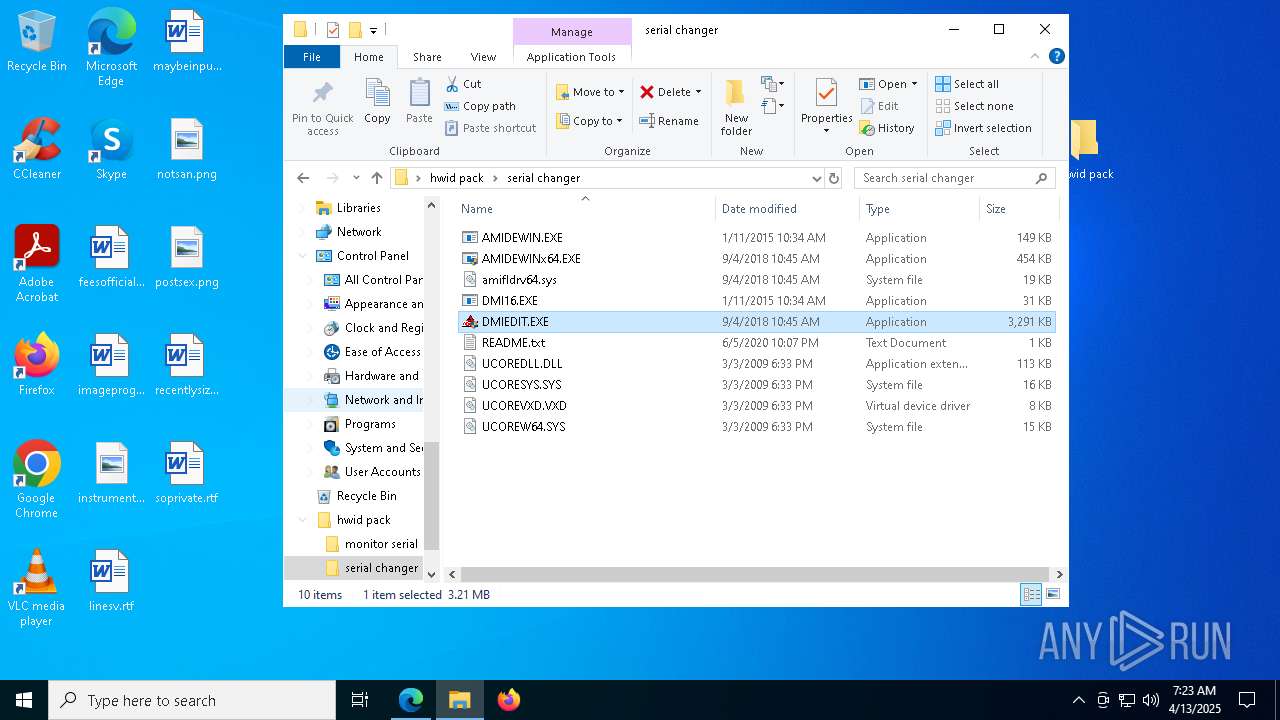
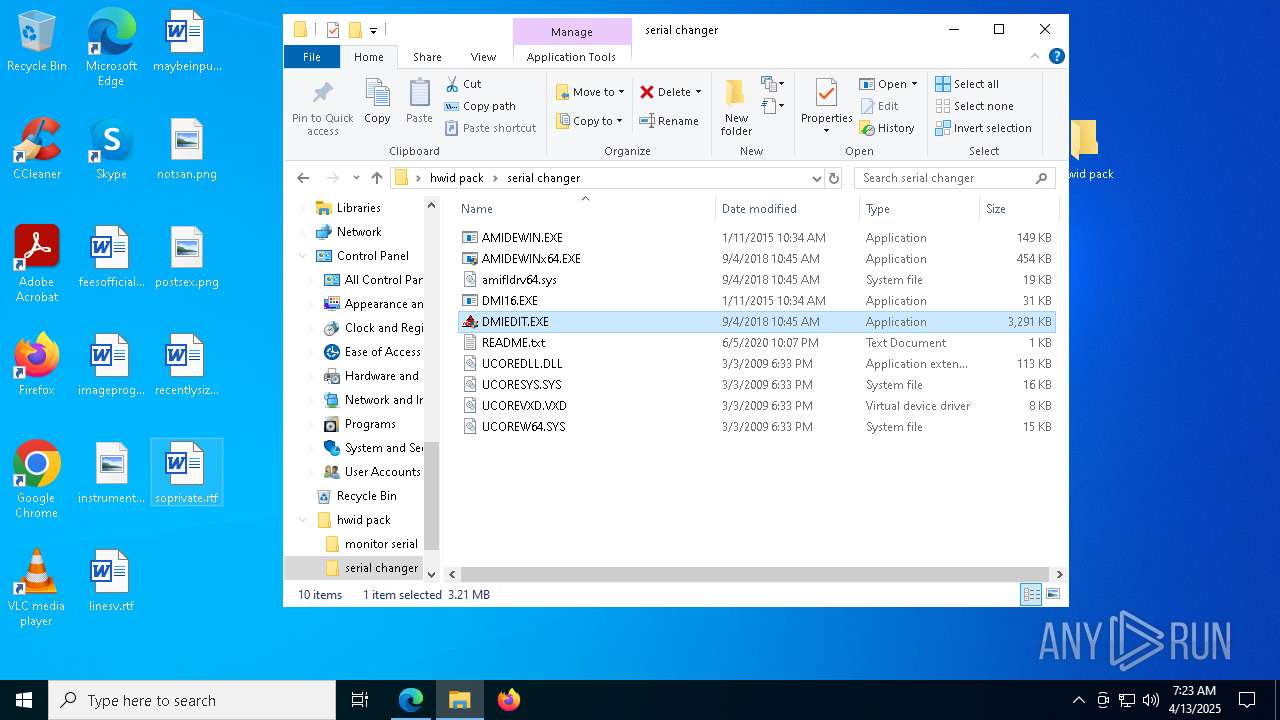
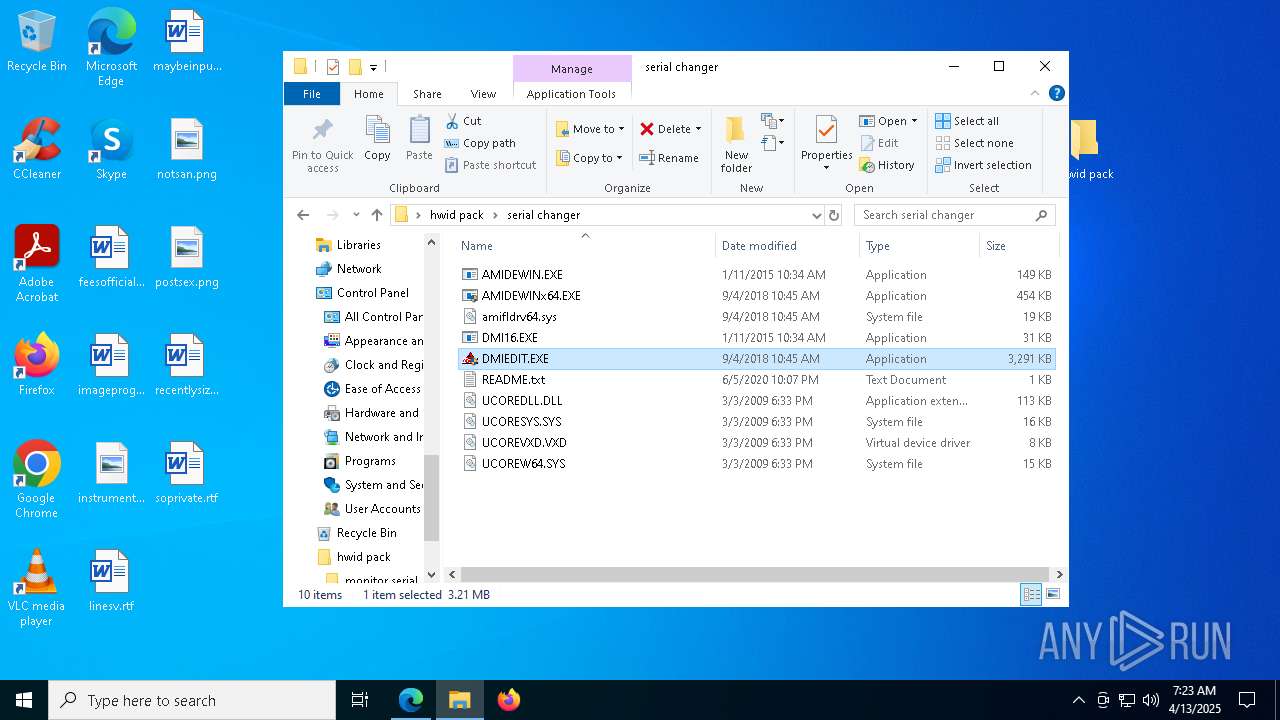
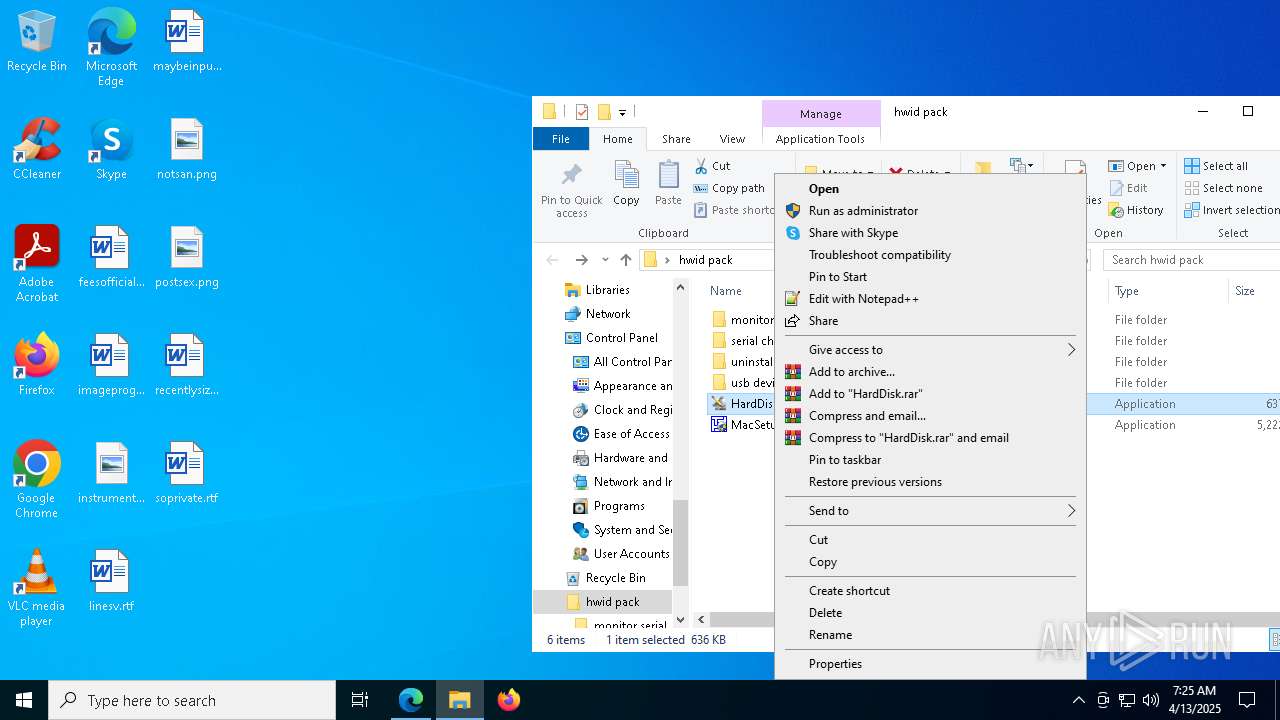
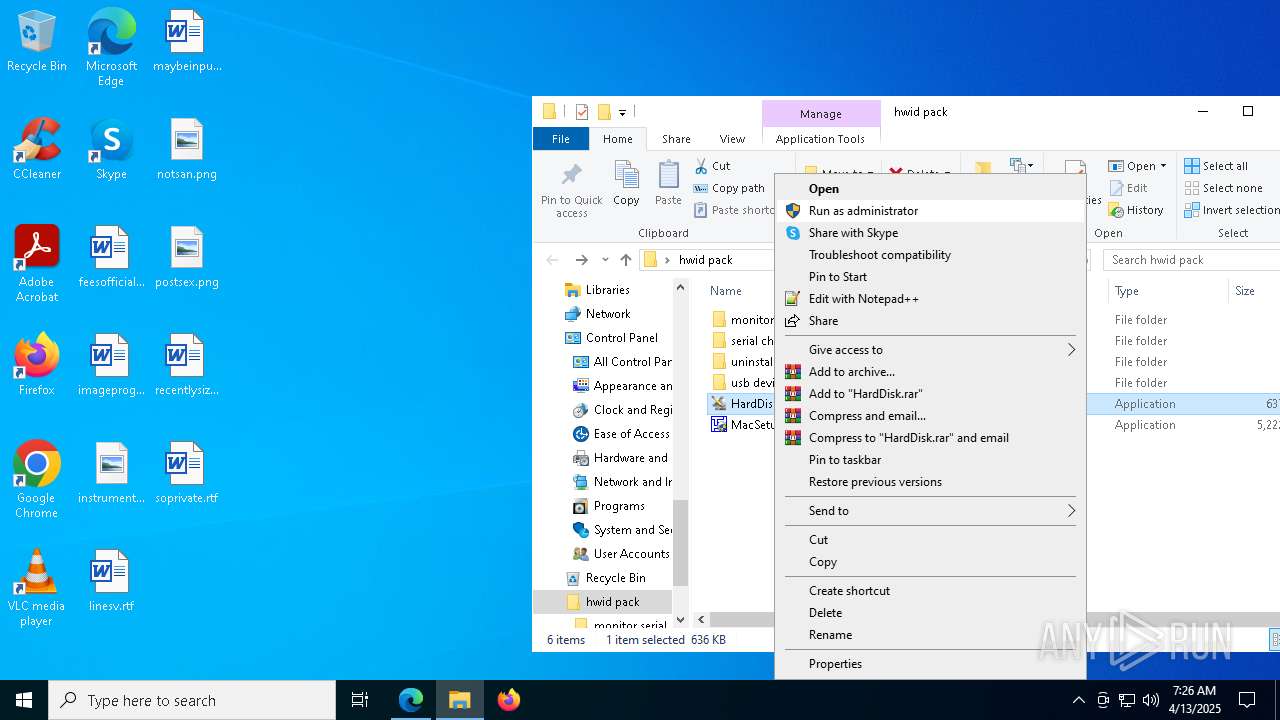
MALICIOUS
Vulnerable driver has been detected
- WinRAR.exe (PID: 3896)
SUSPICIOUS
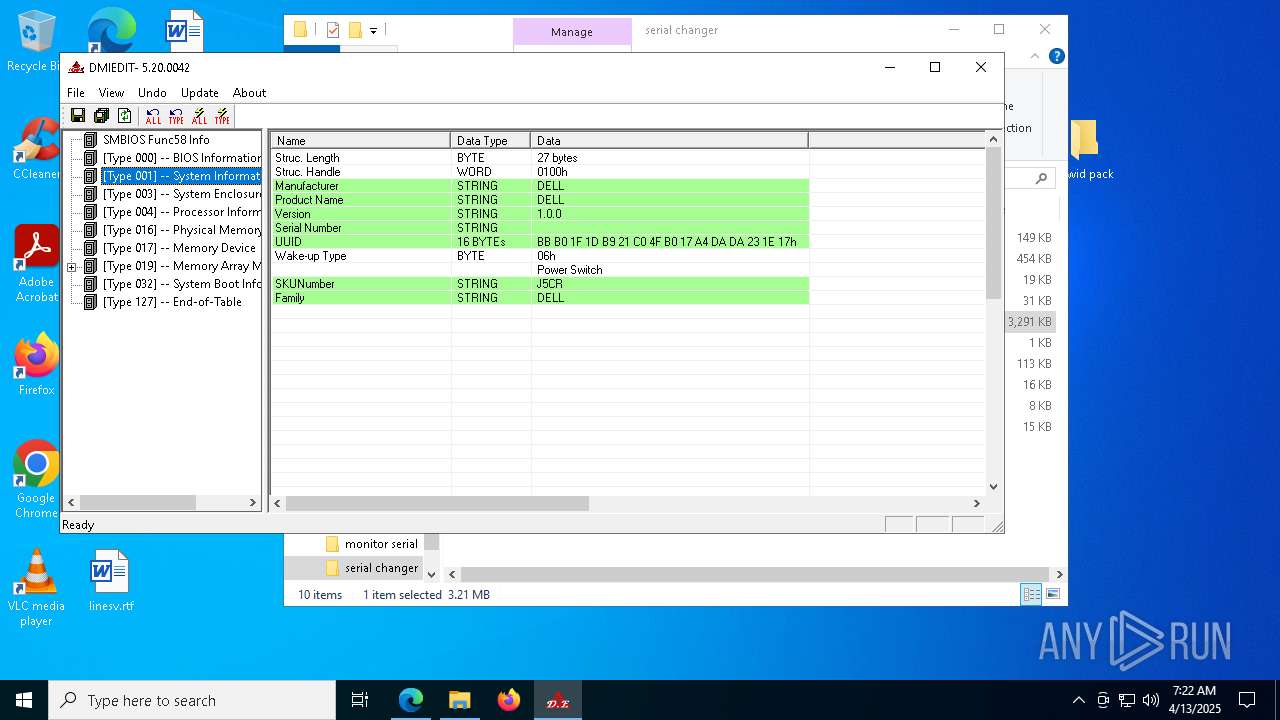
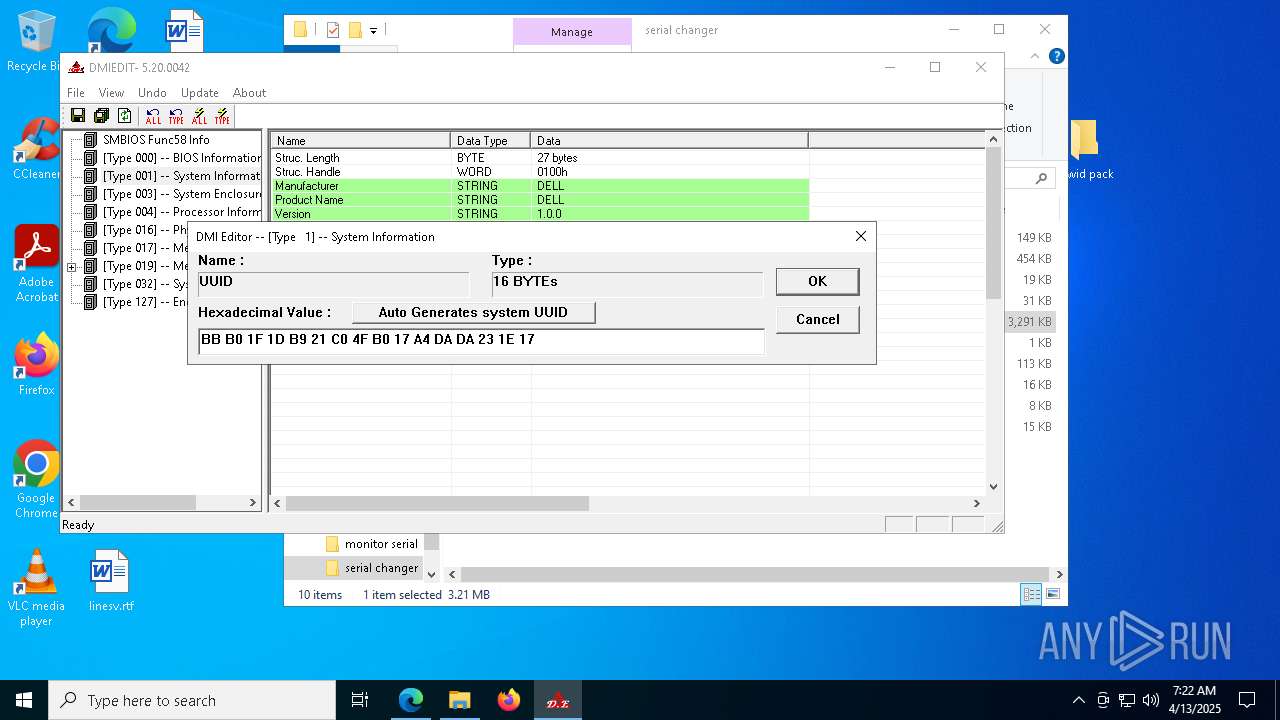
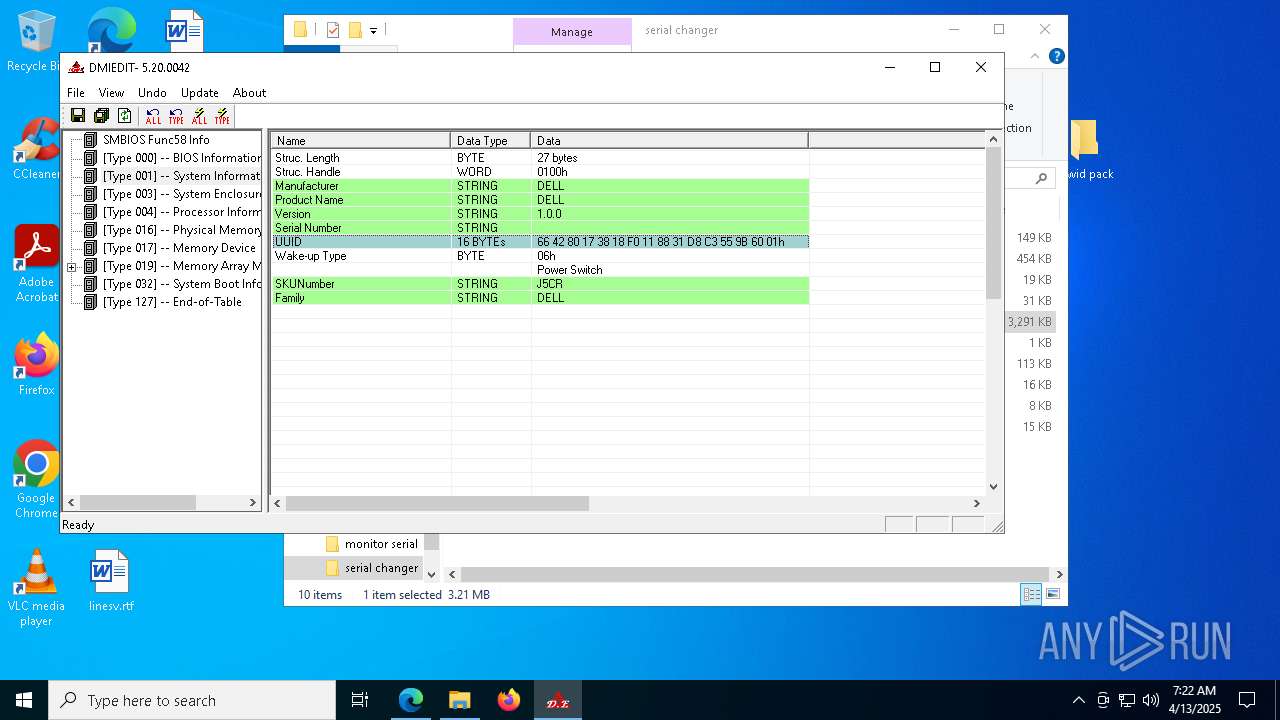
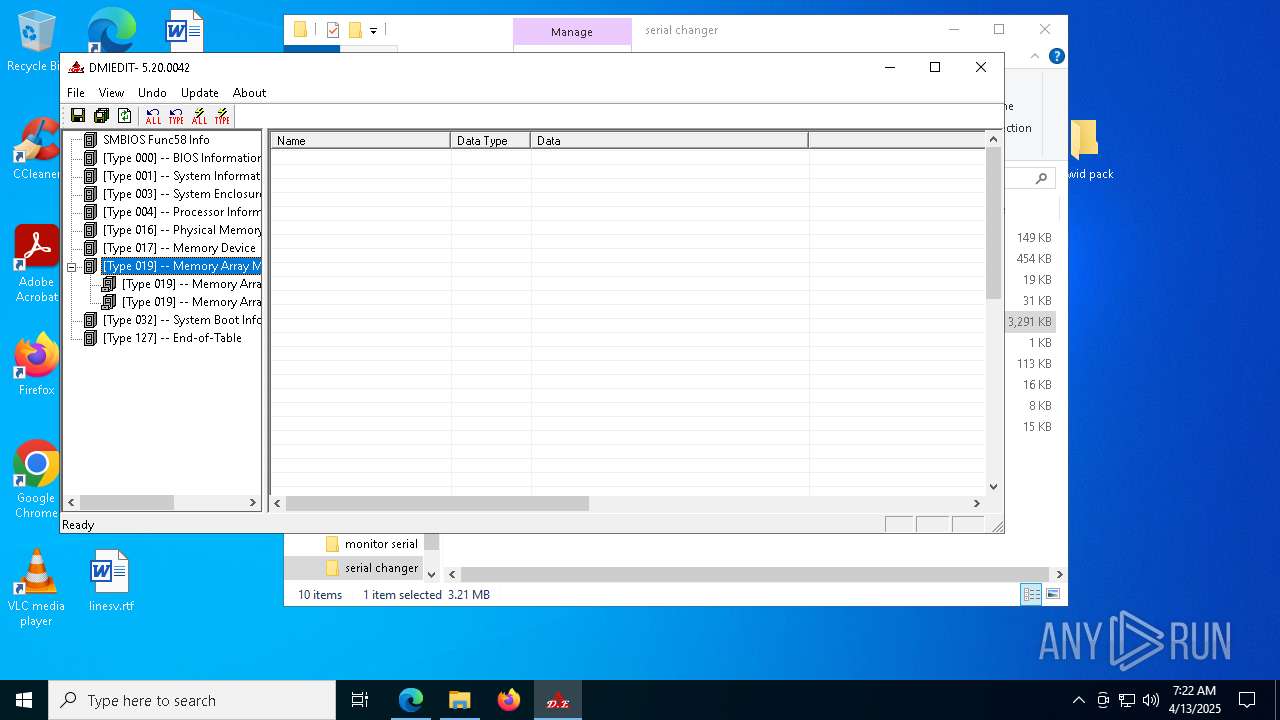
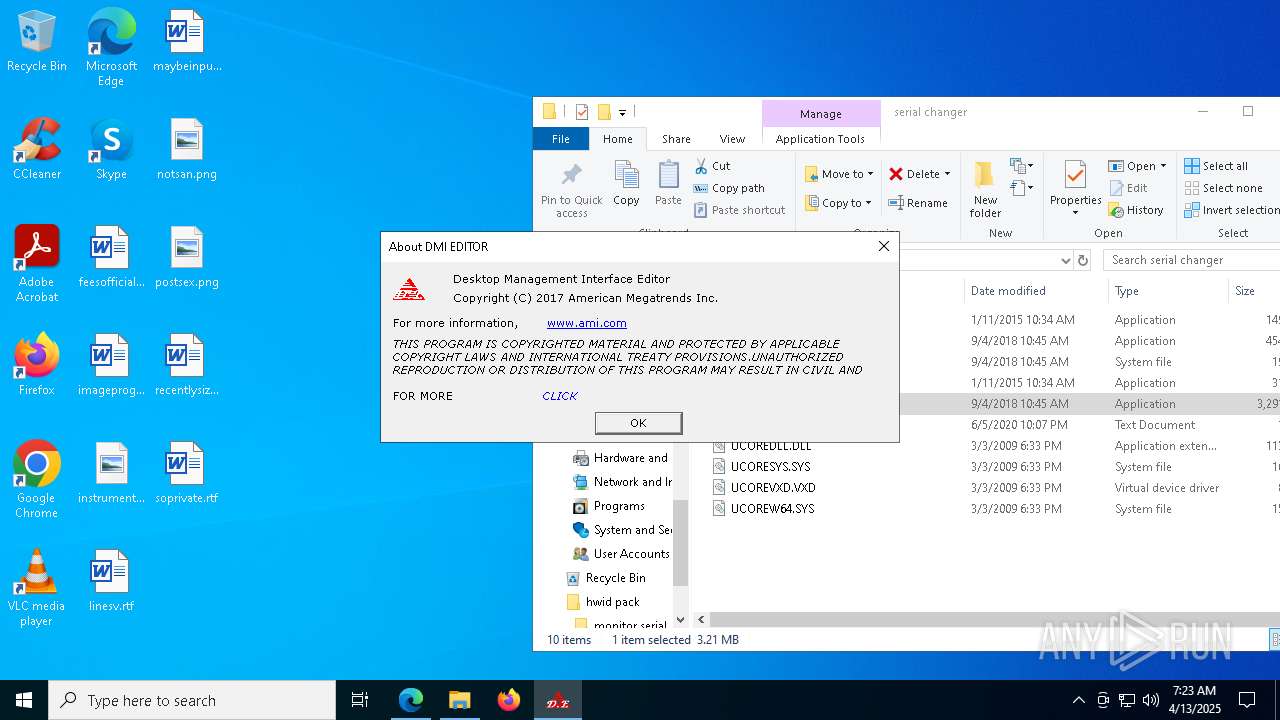
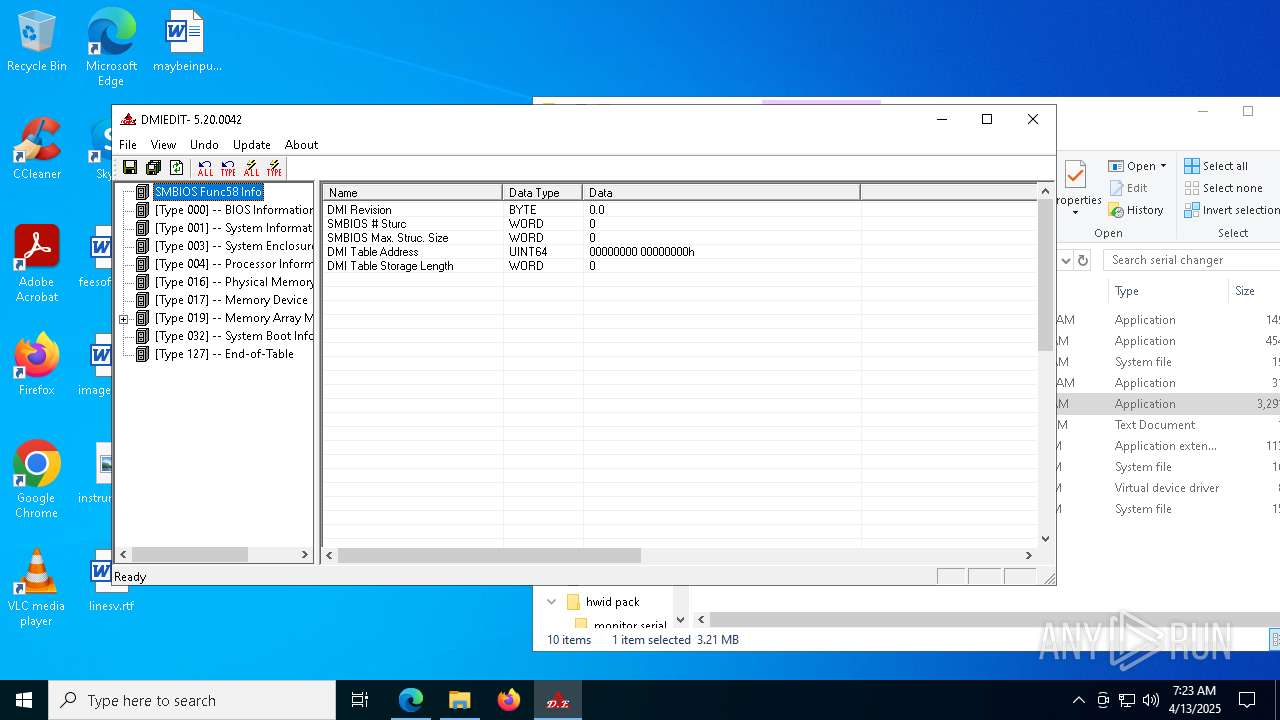
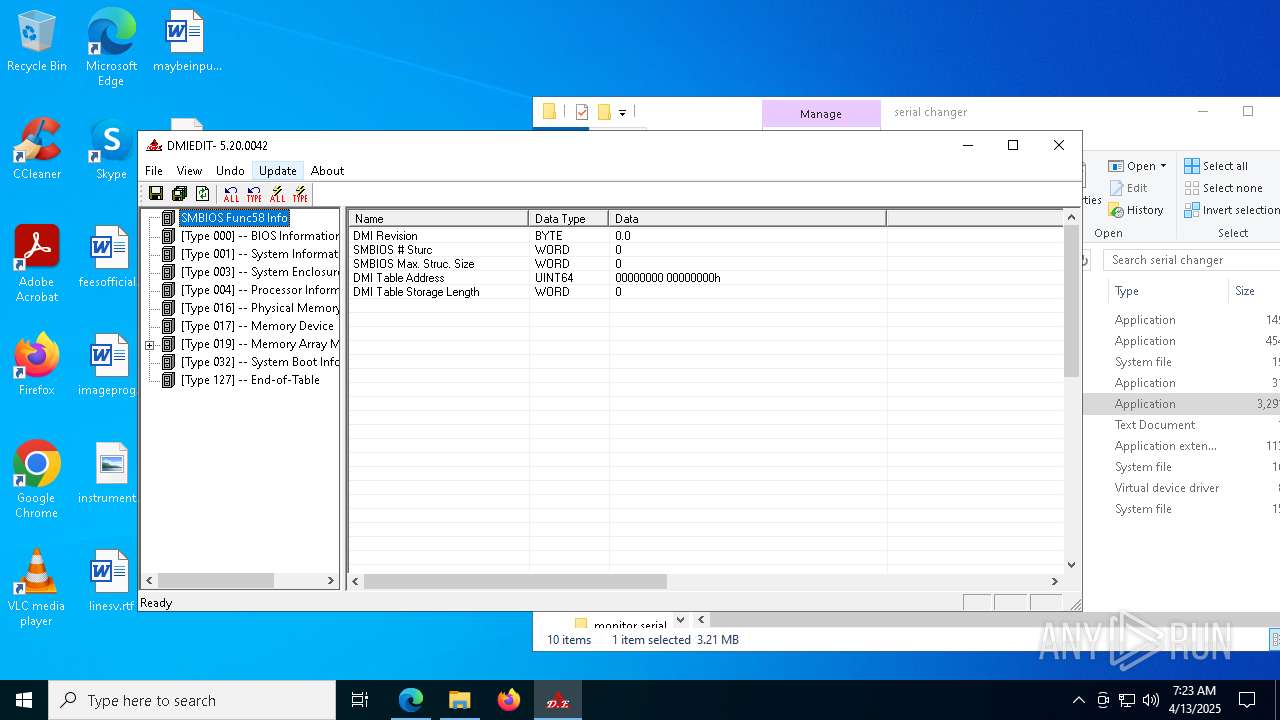
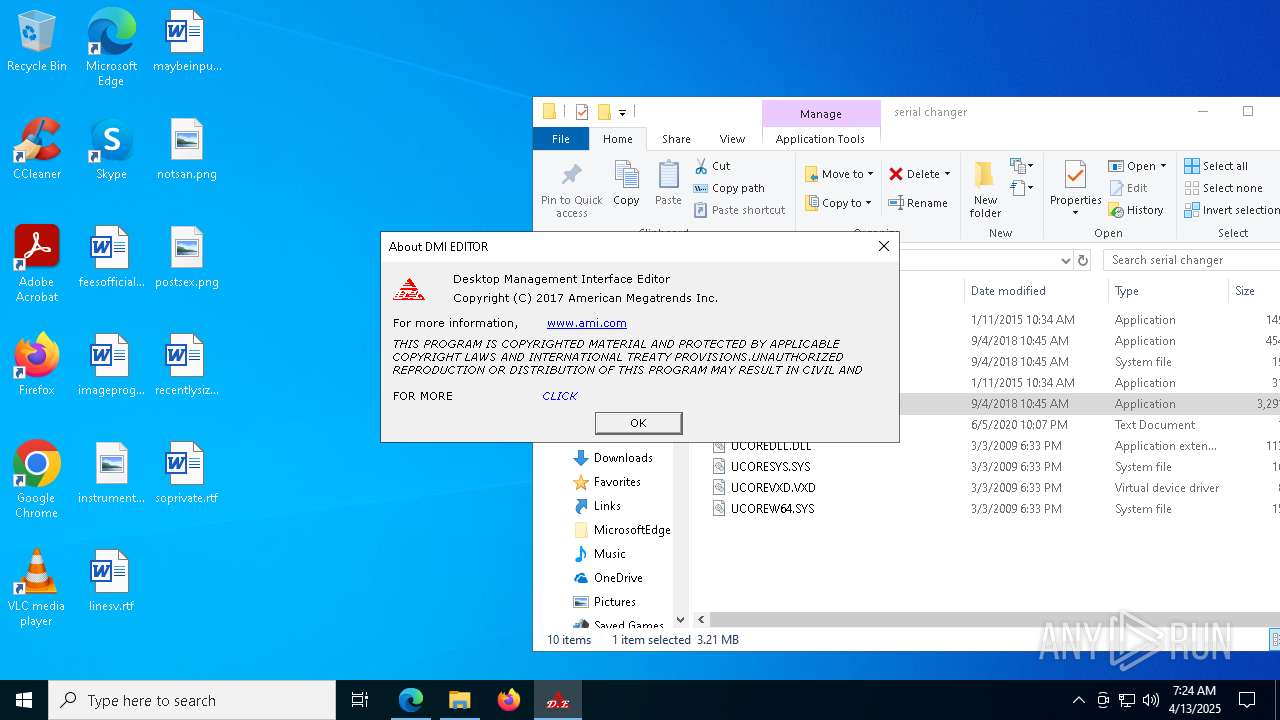
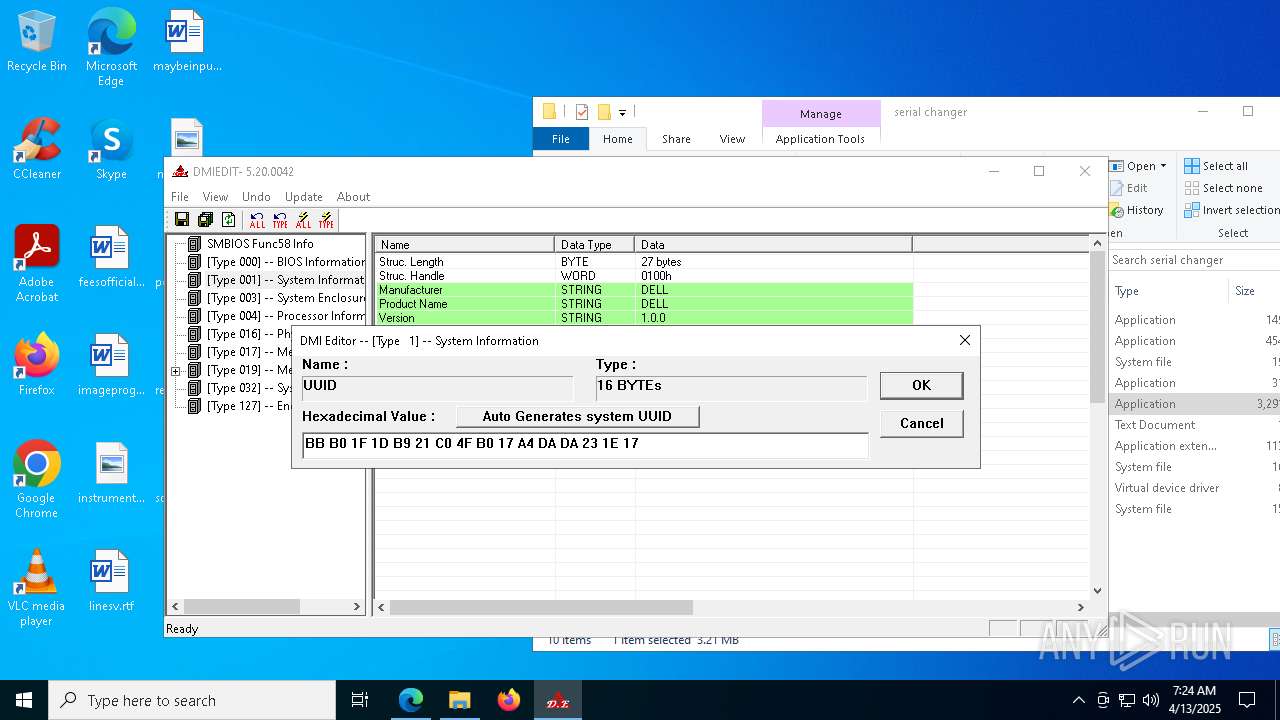
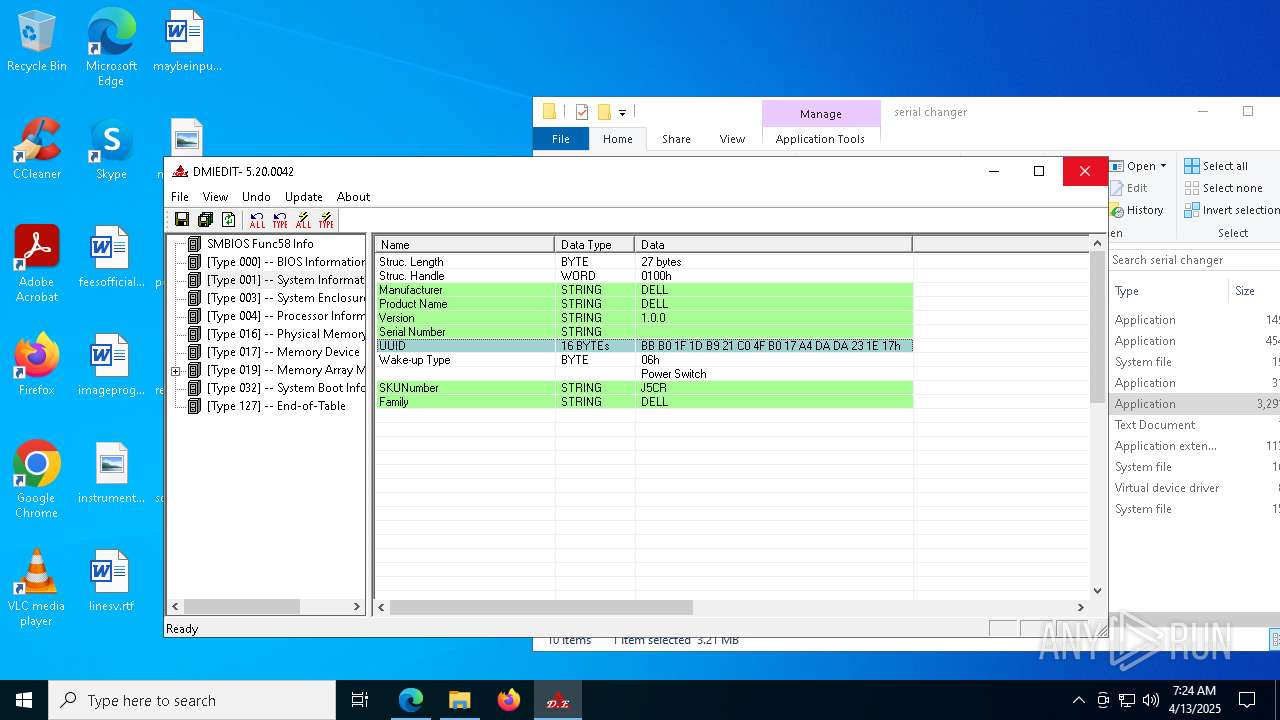
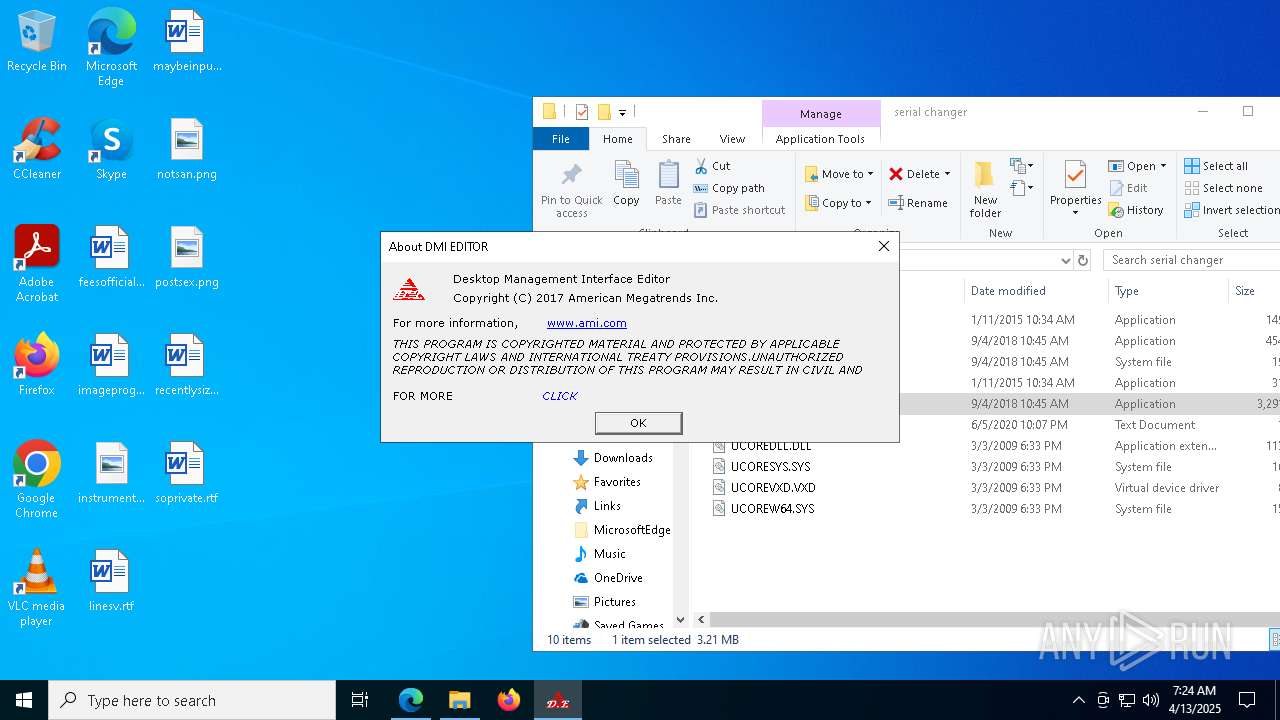
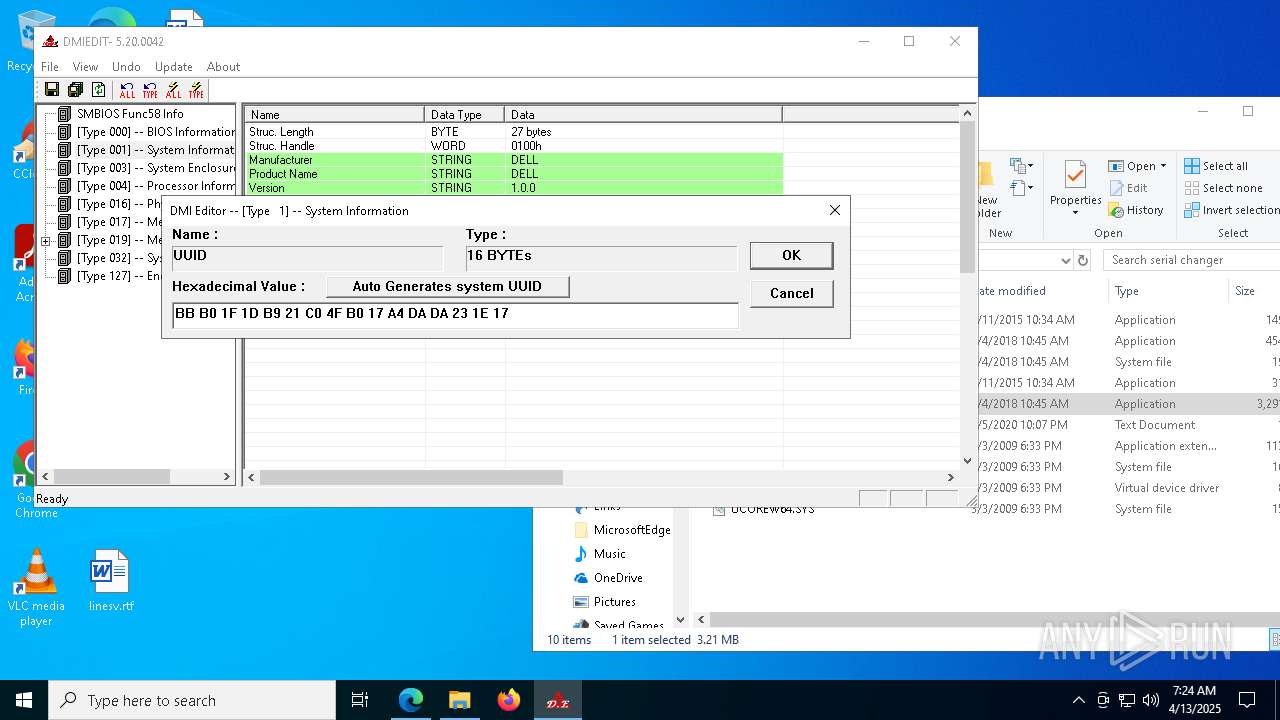
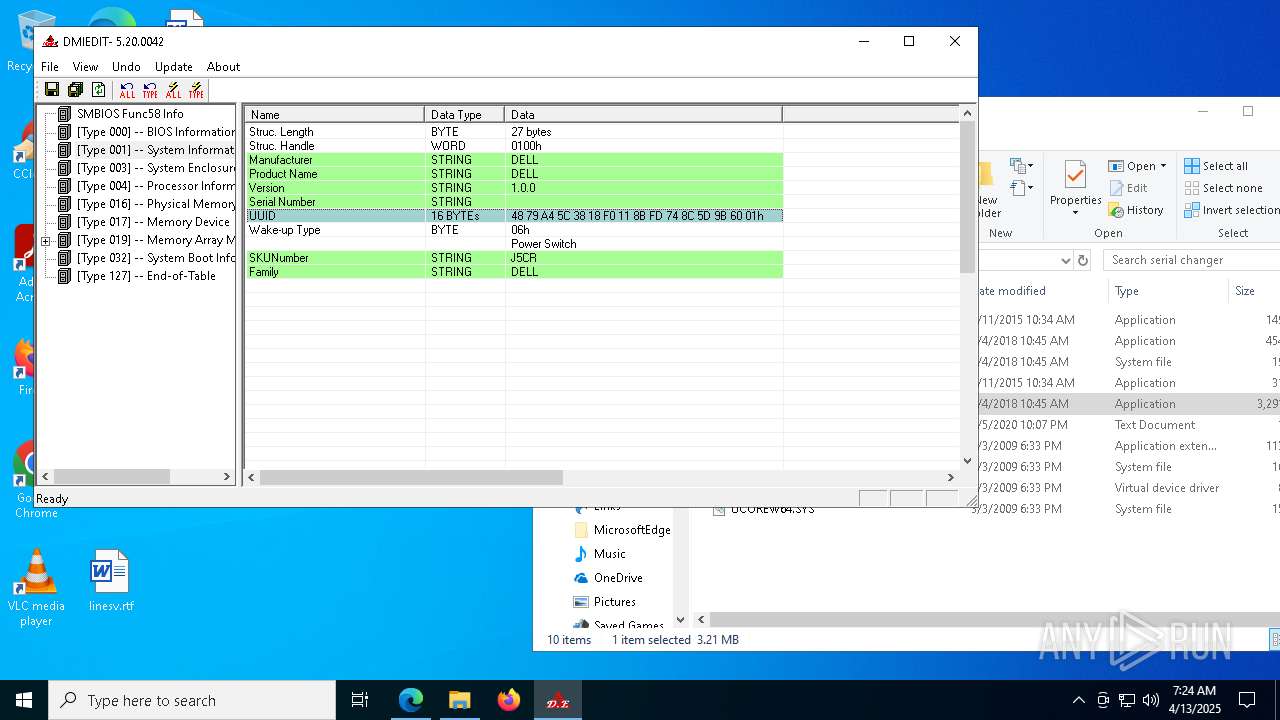
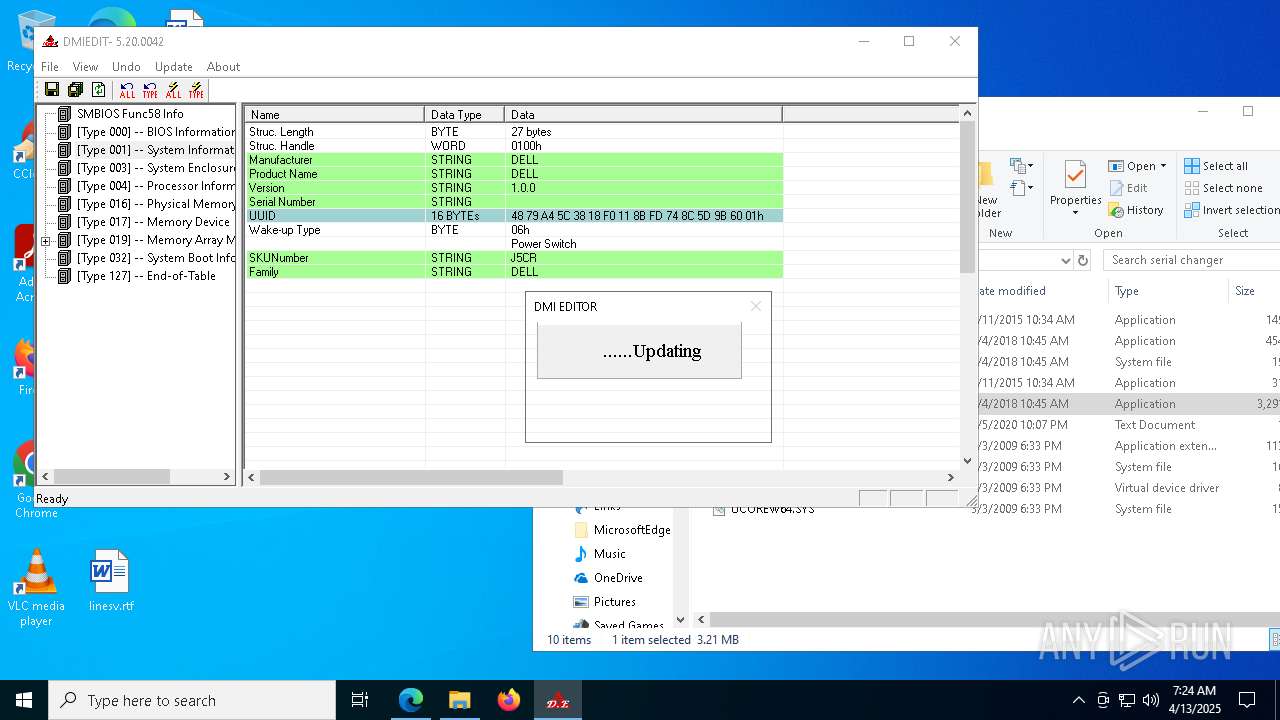
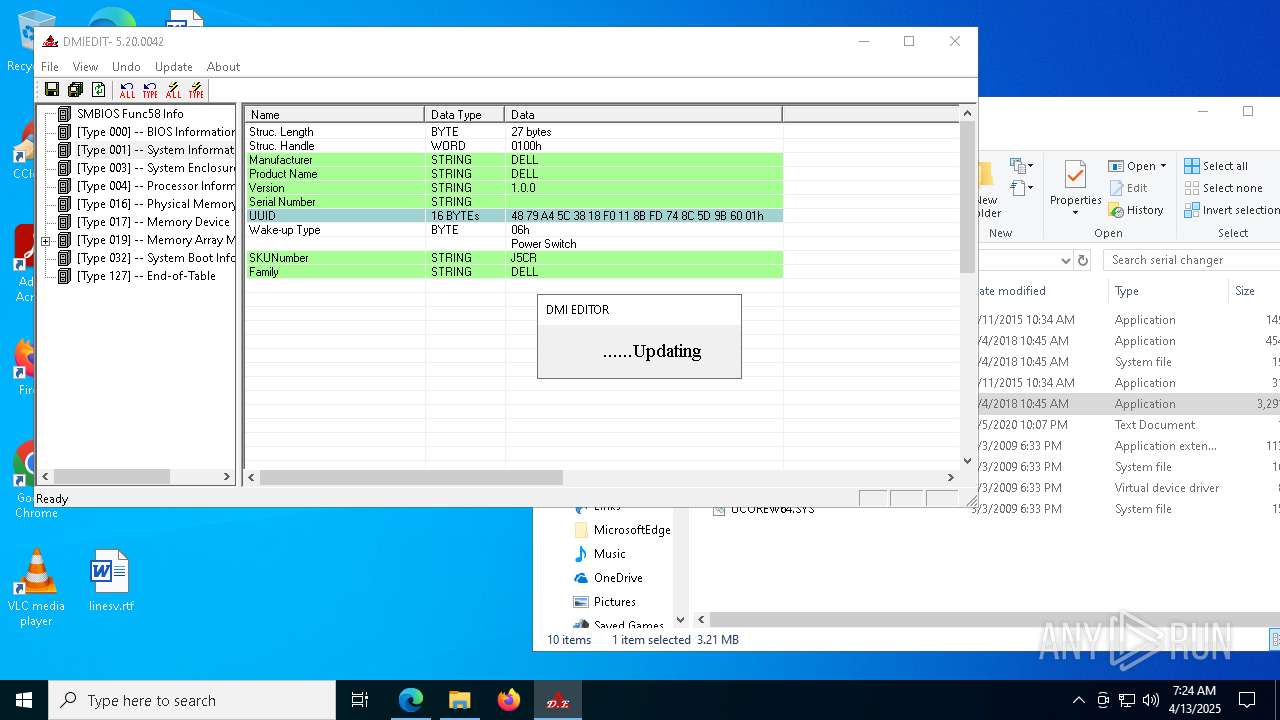
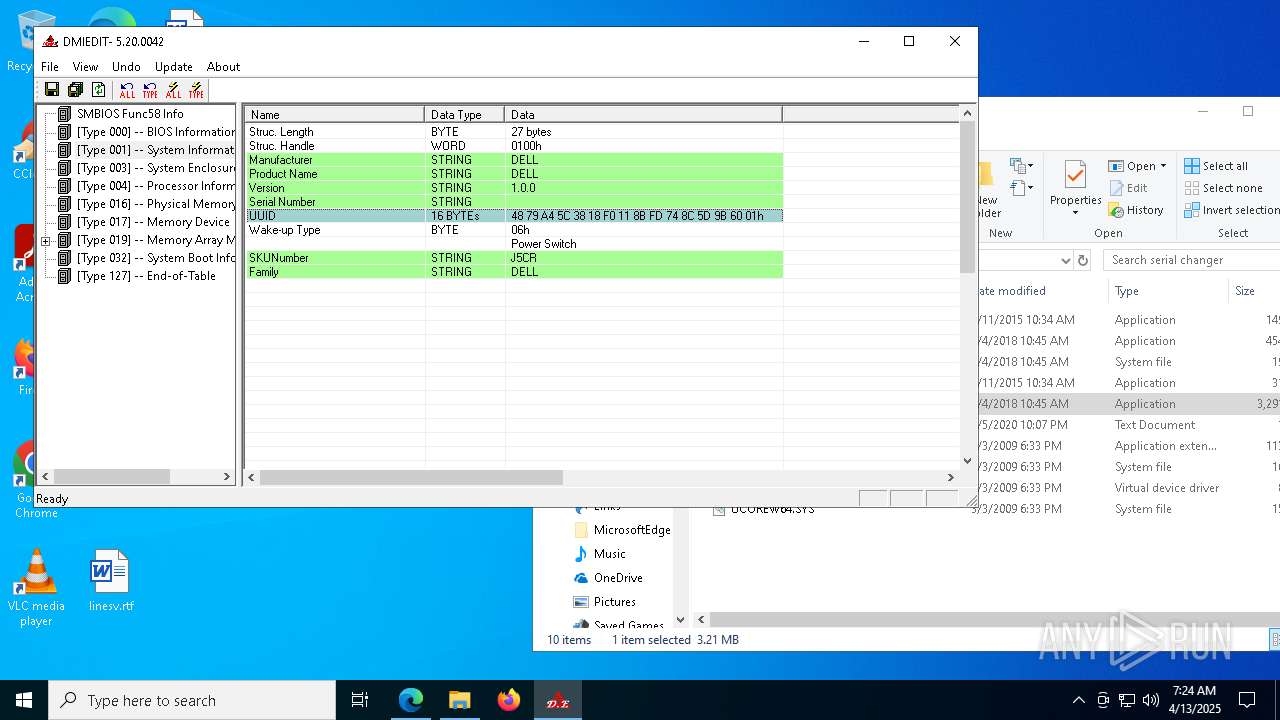
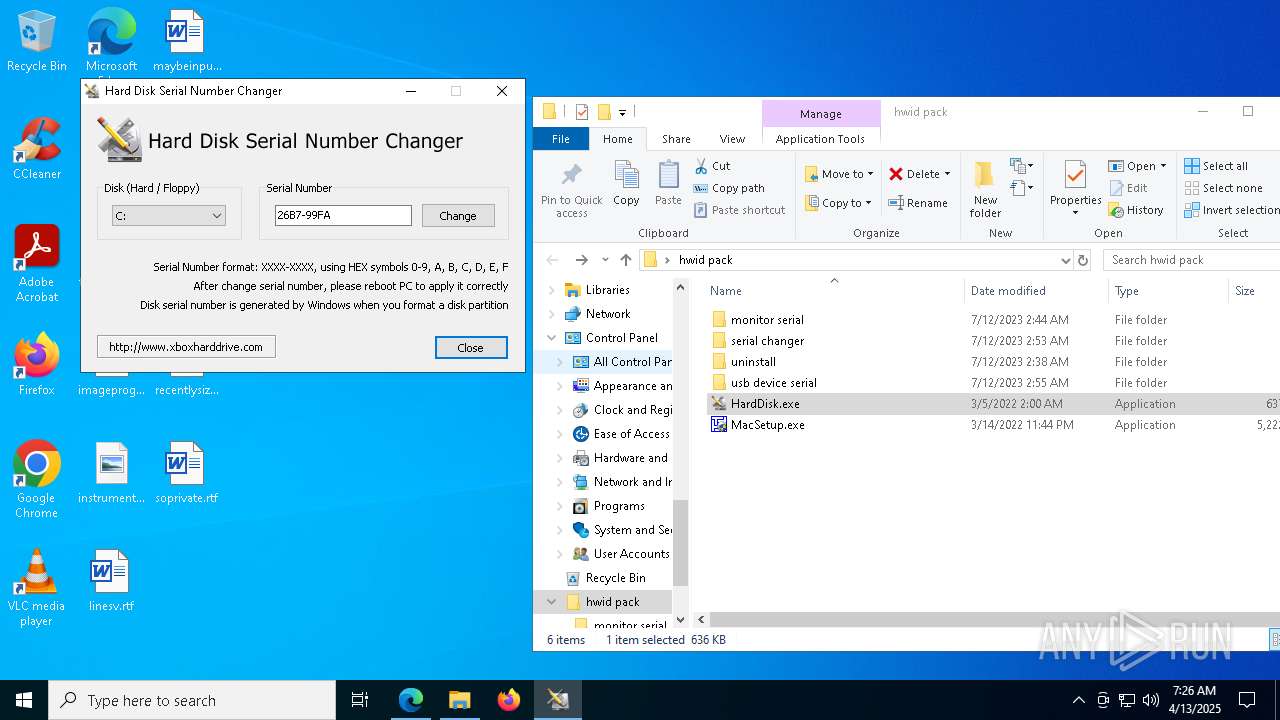
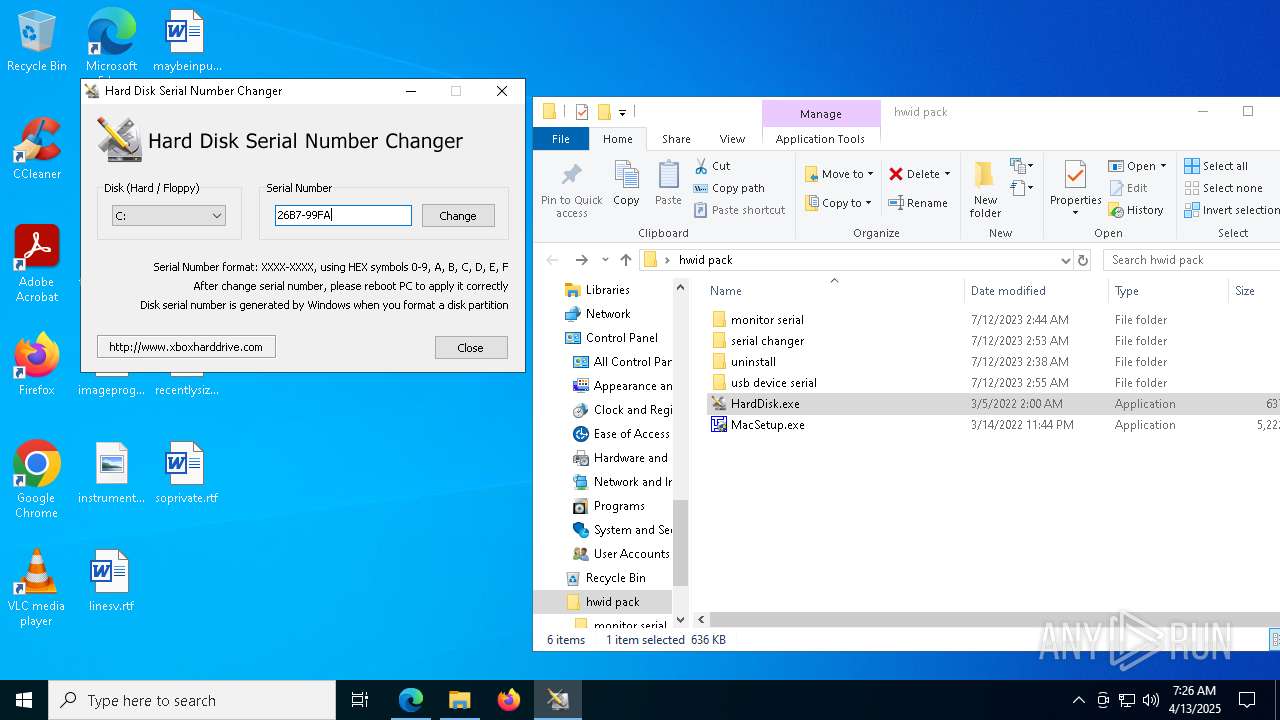
Reads security settings of Internet Explorer
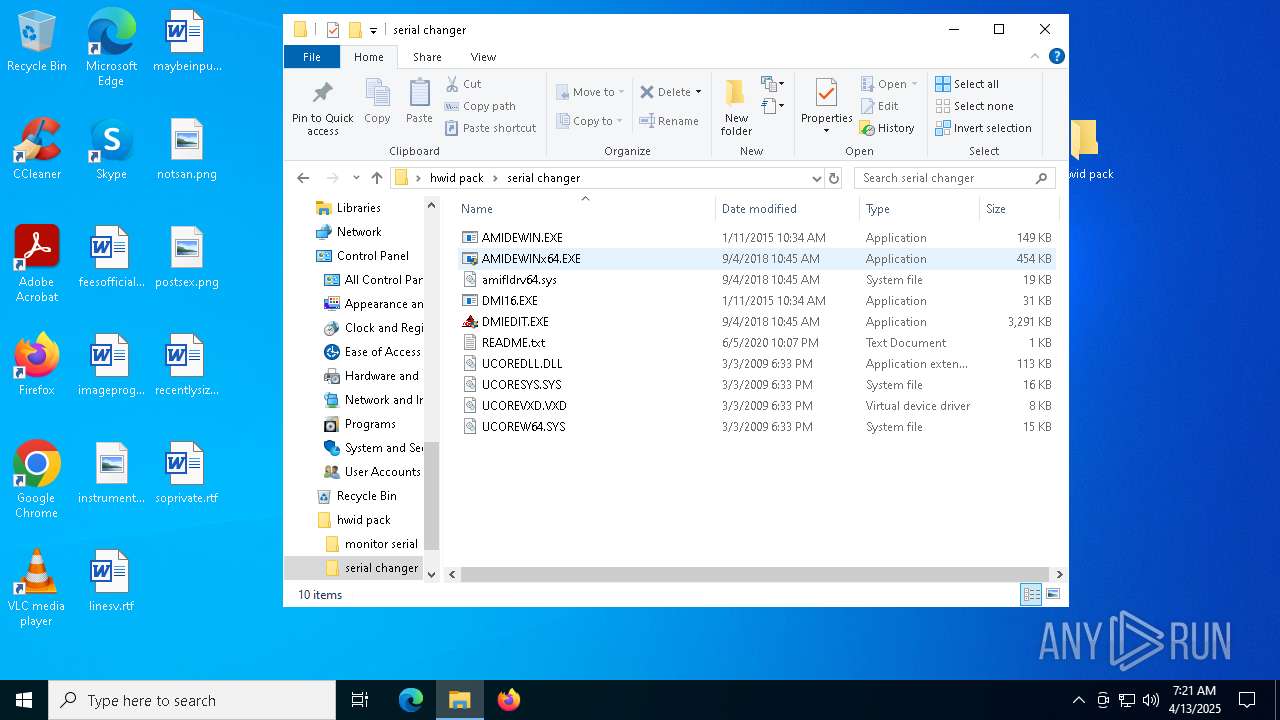
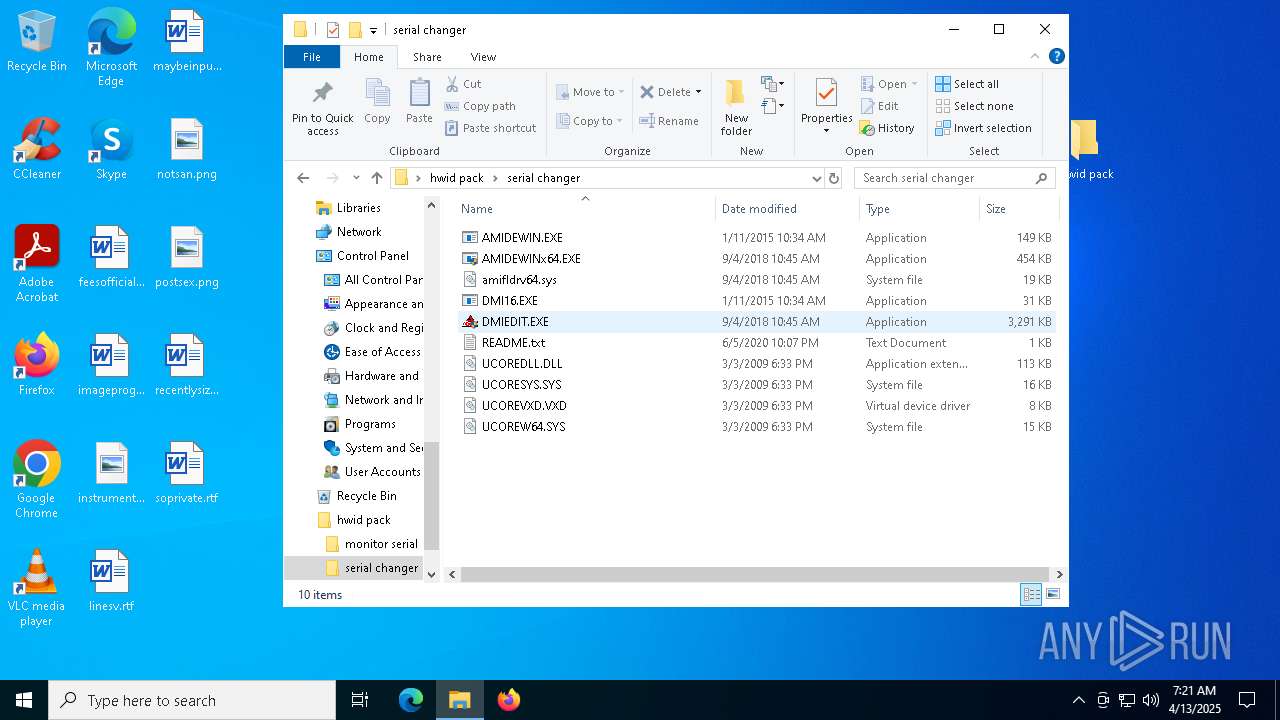
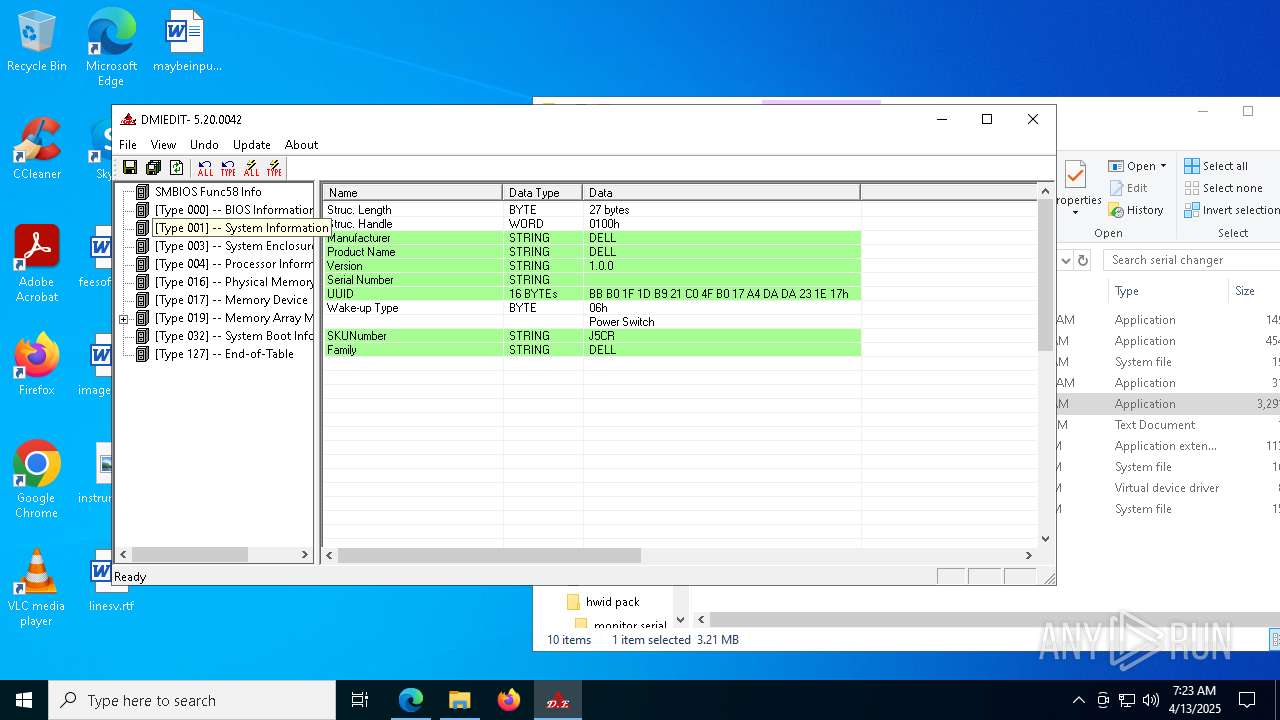
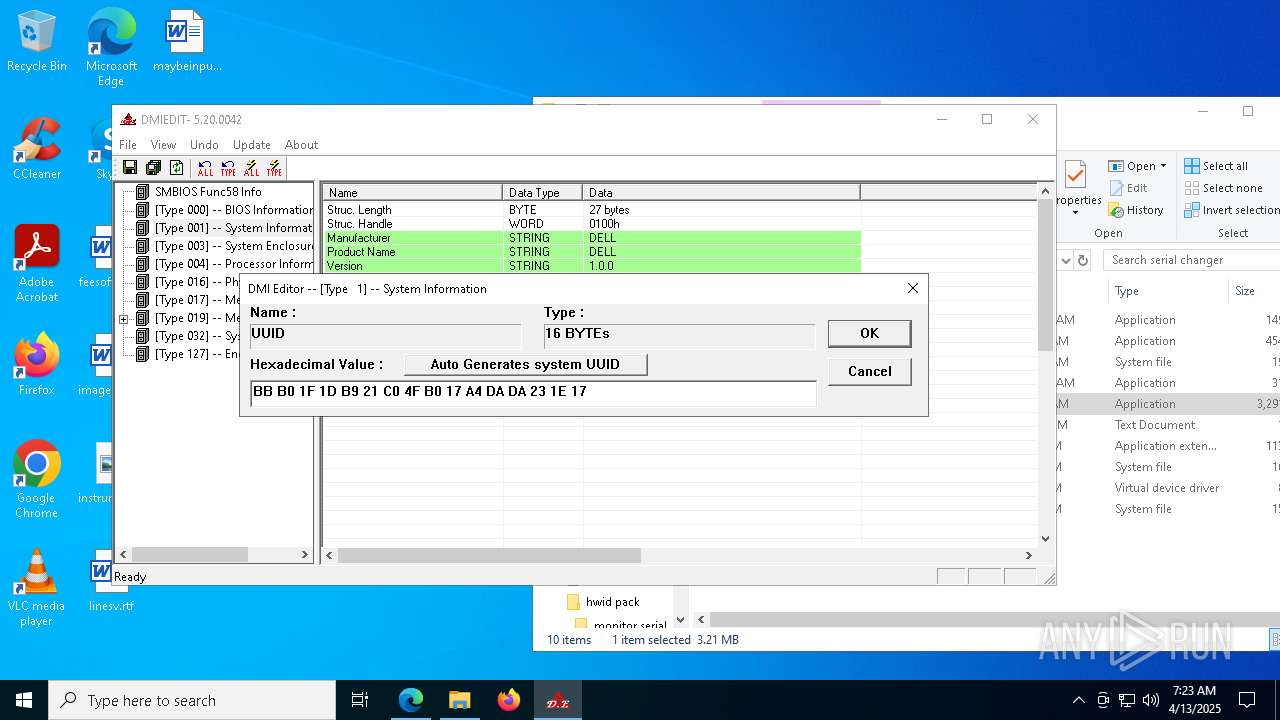
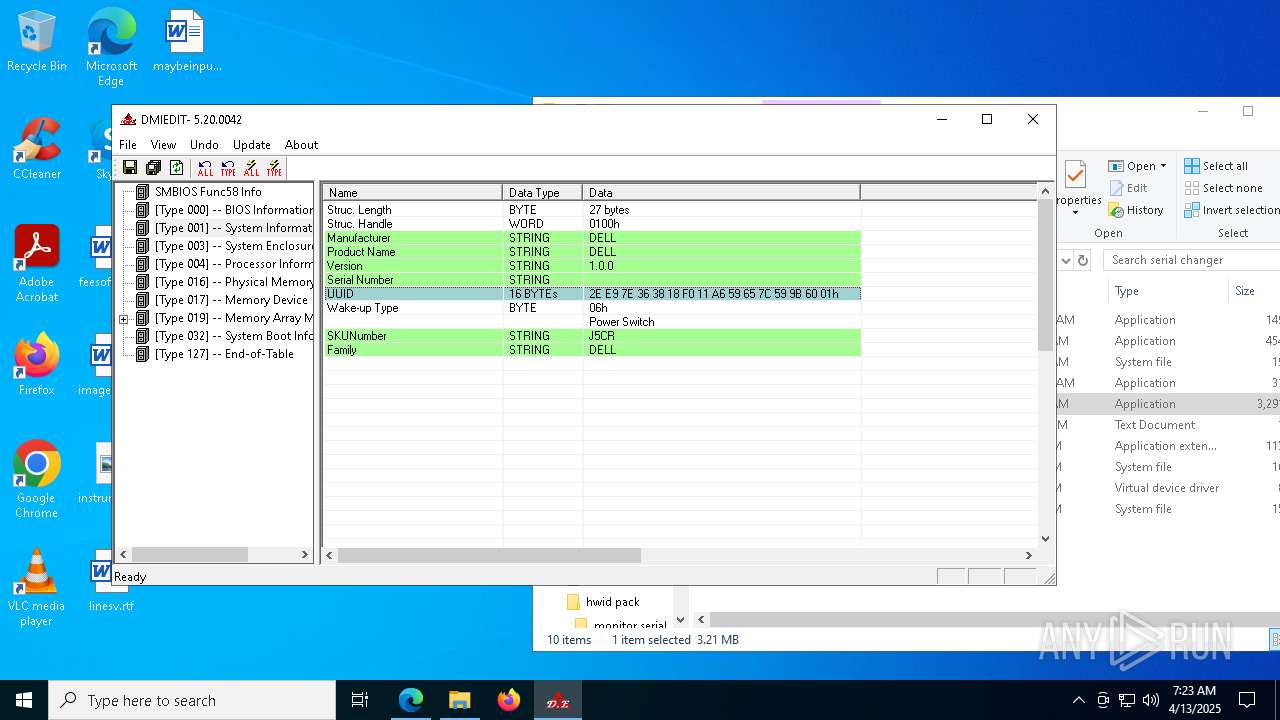
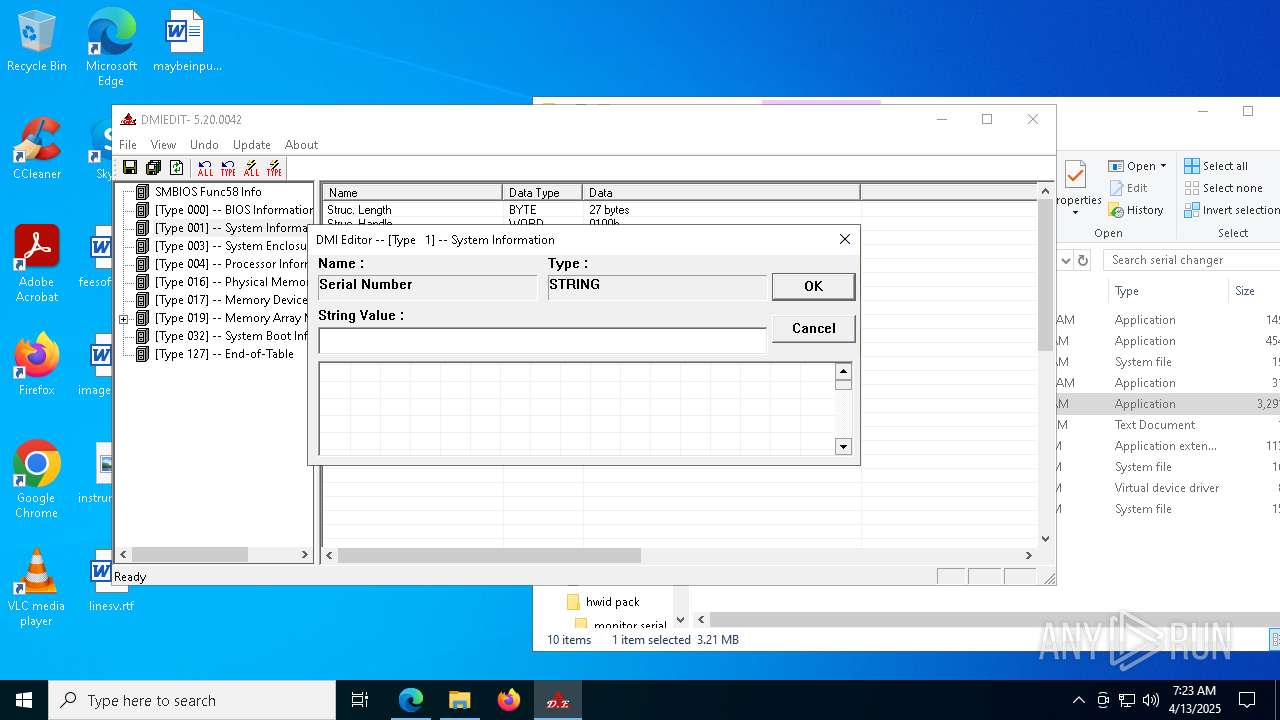
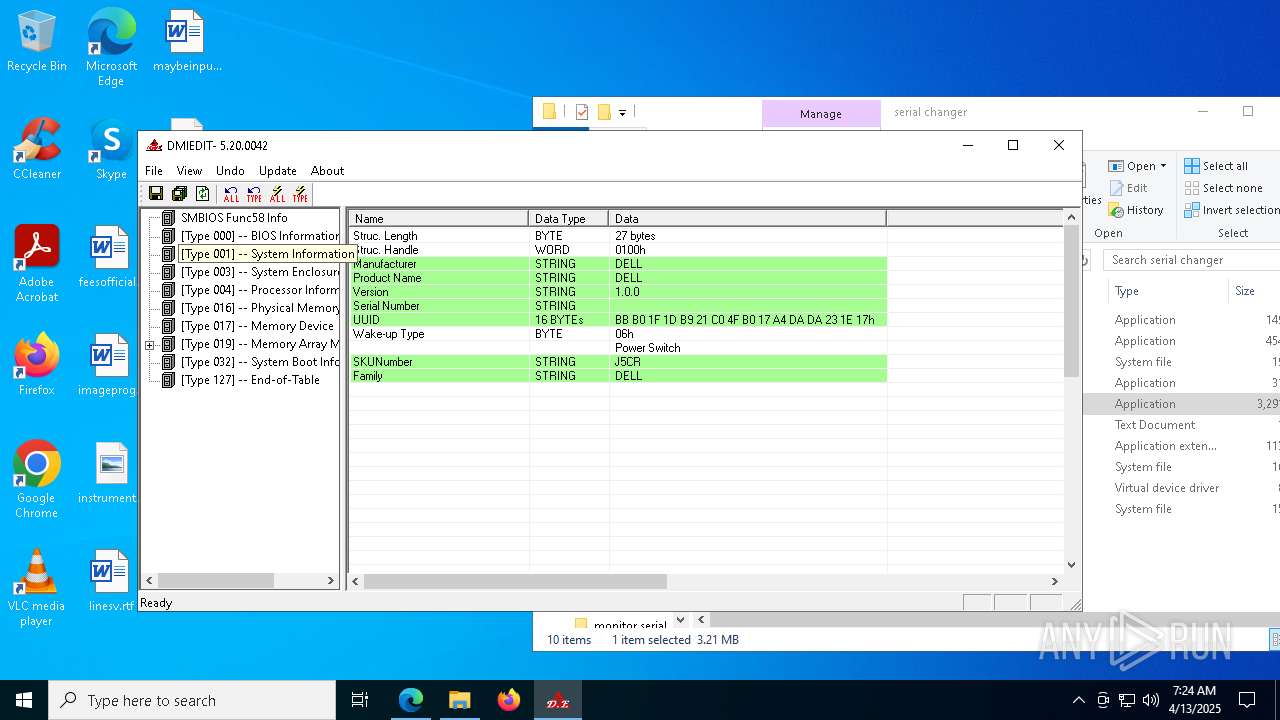
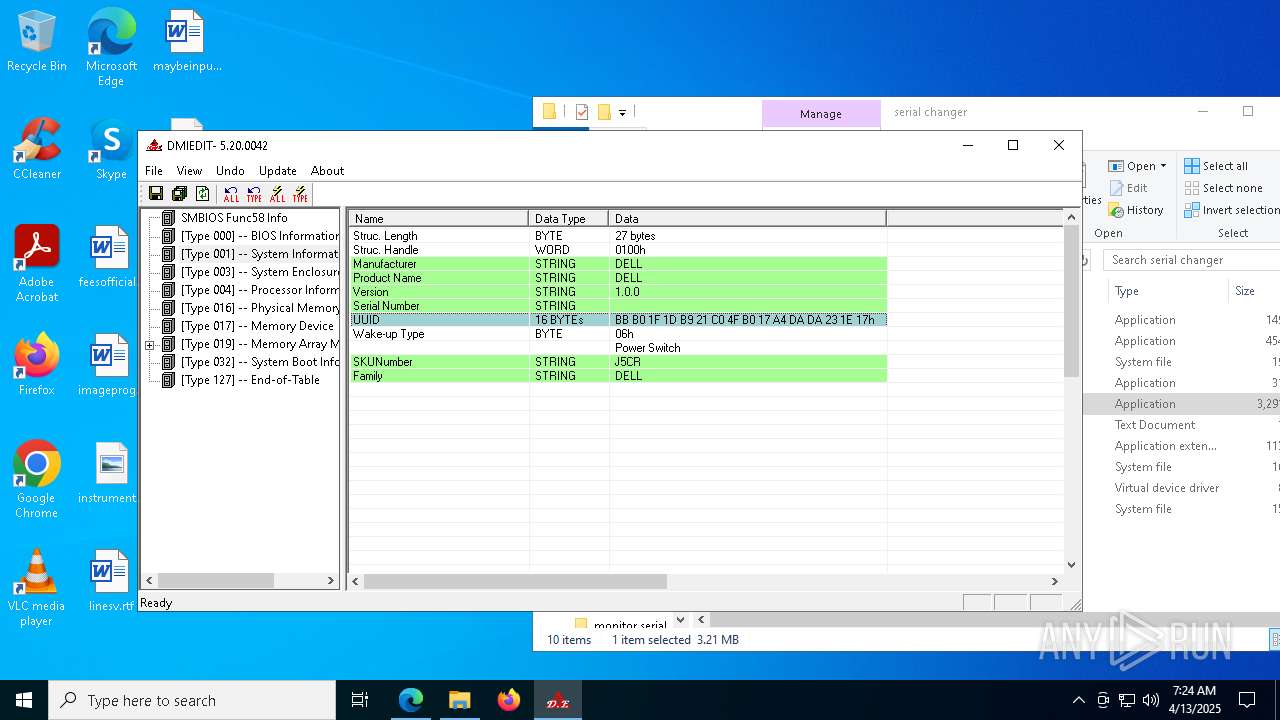
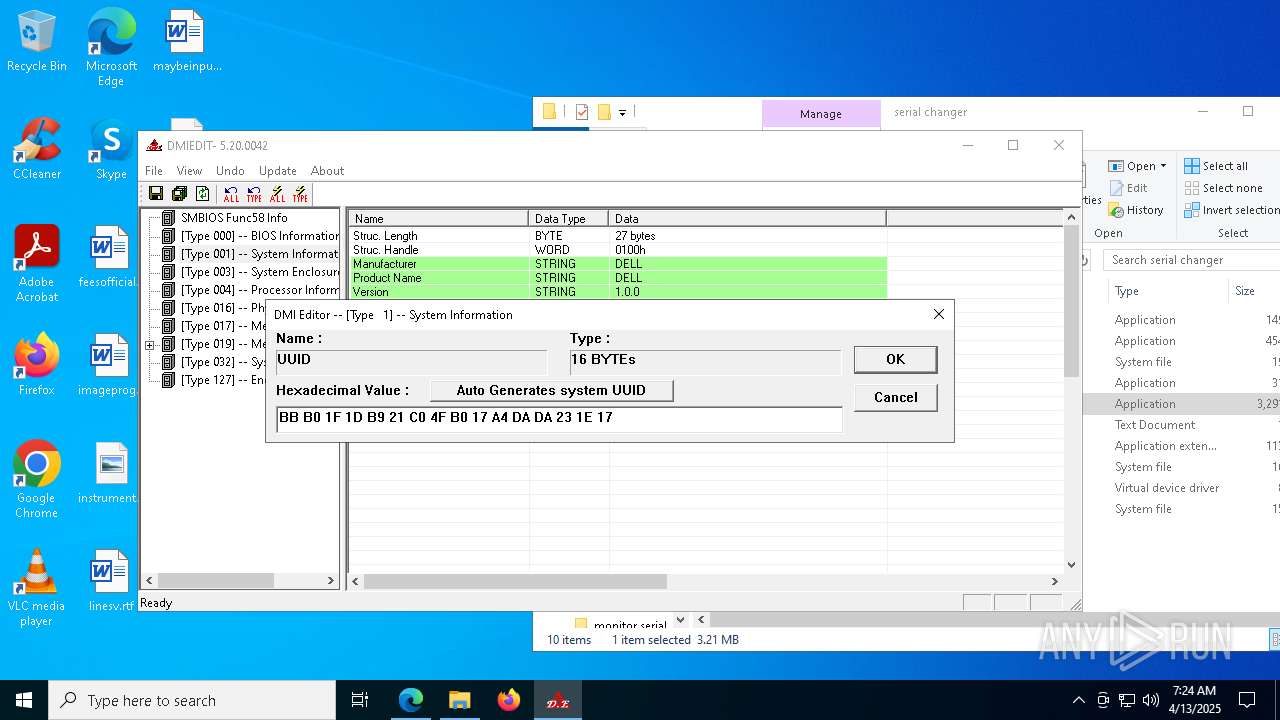
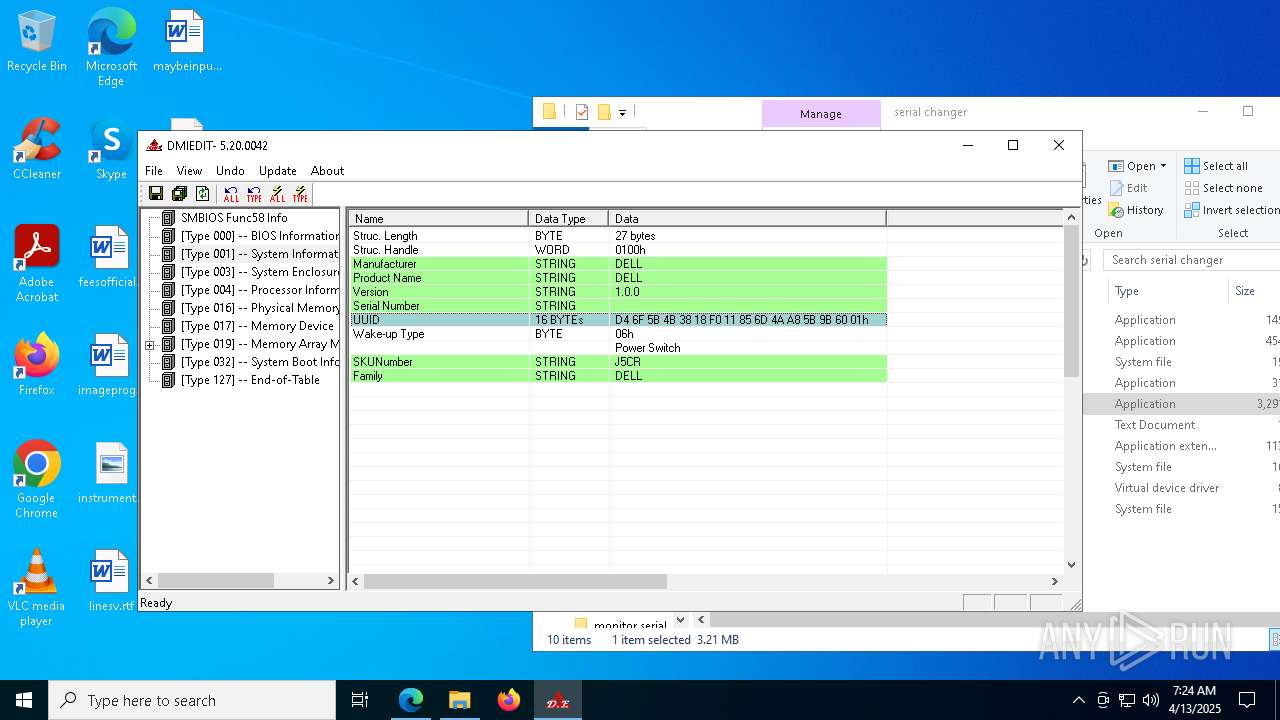
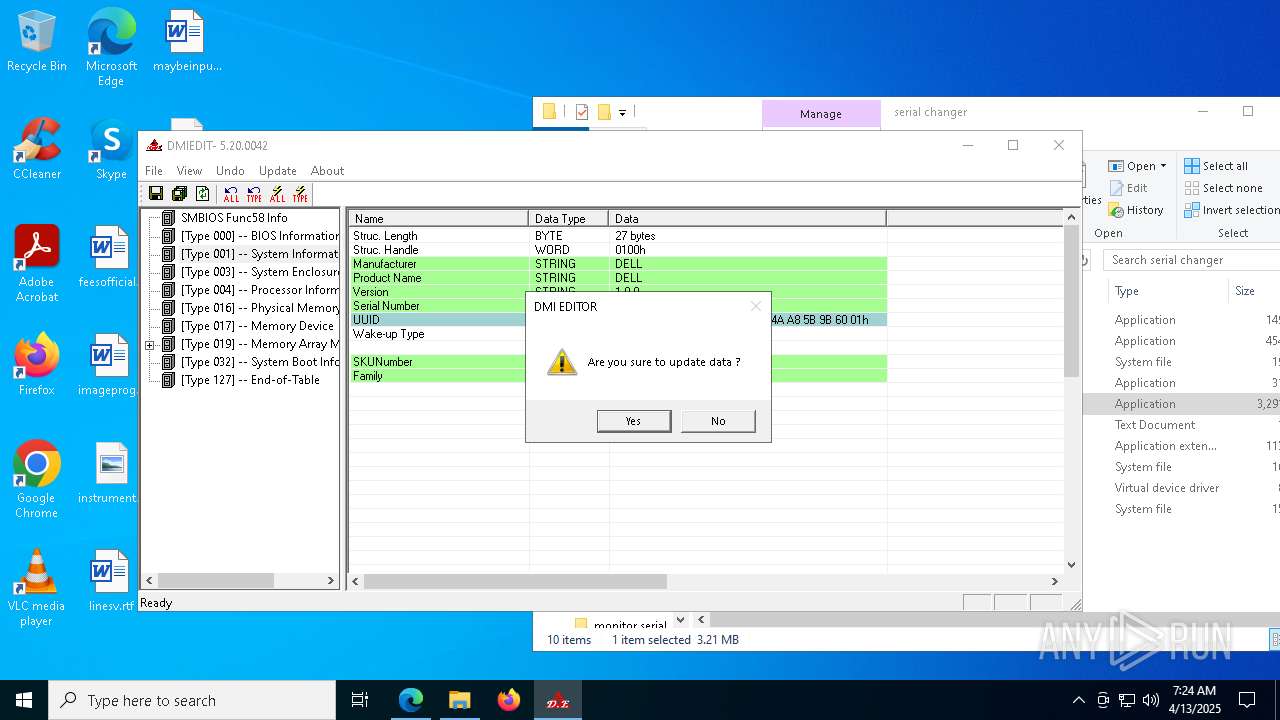
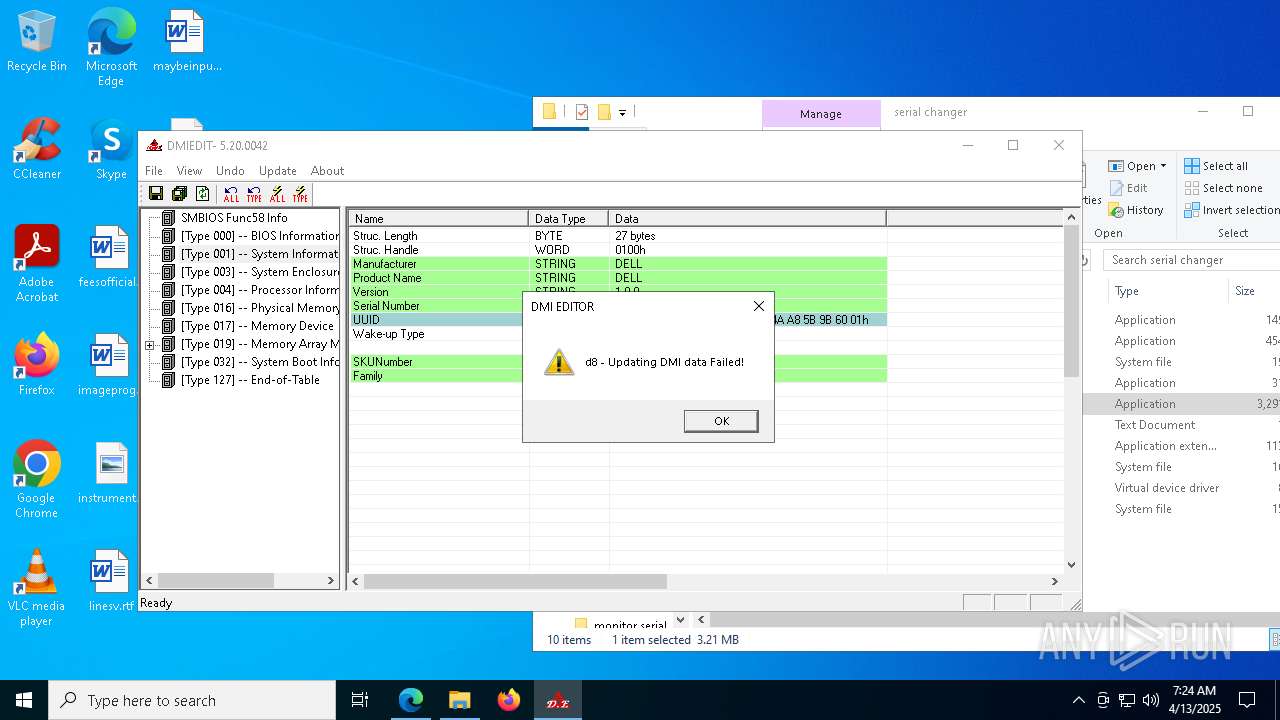
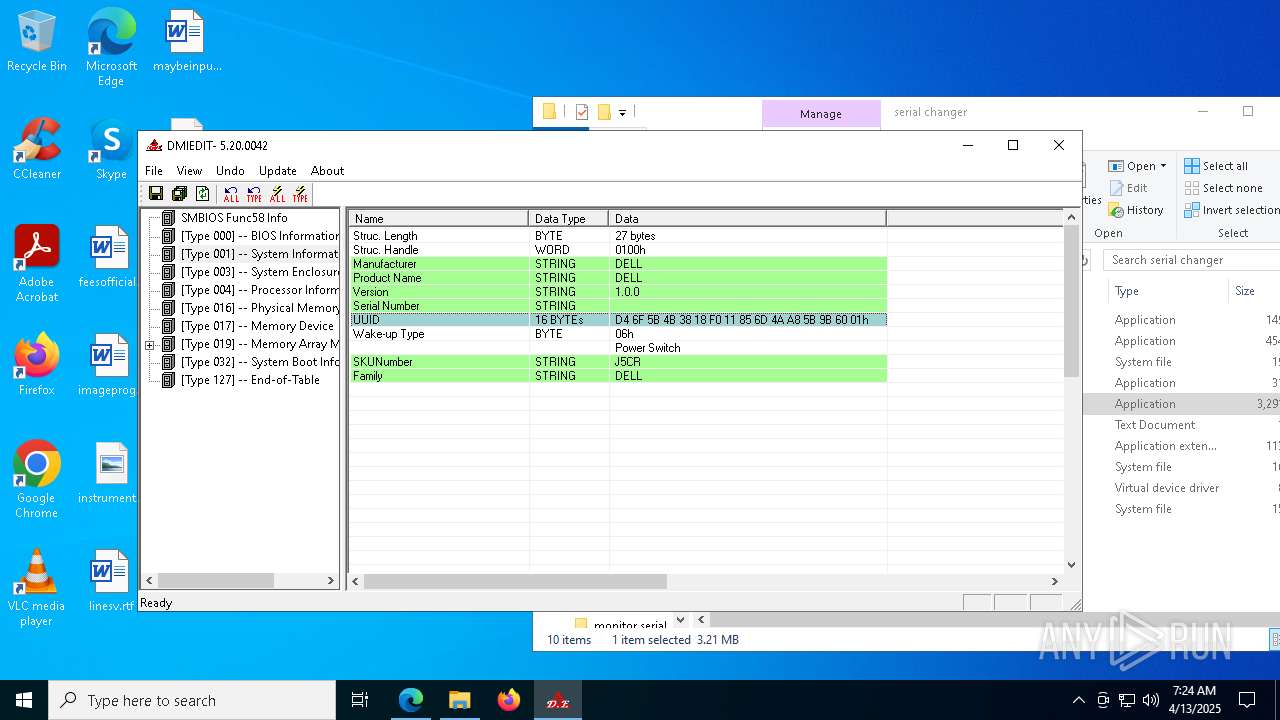
- DMIEDIT.EXE (PID: 5416)
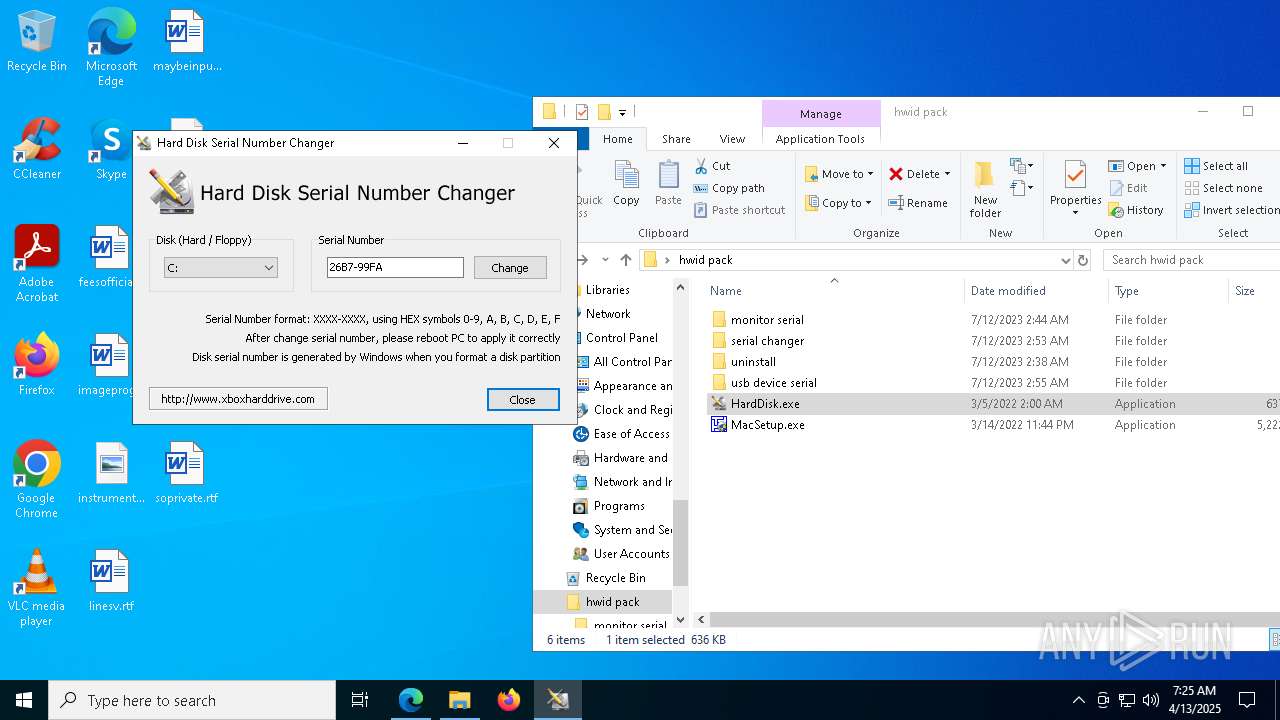
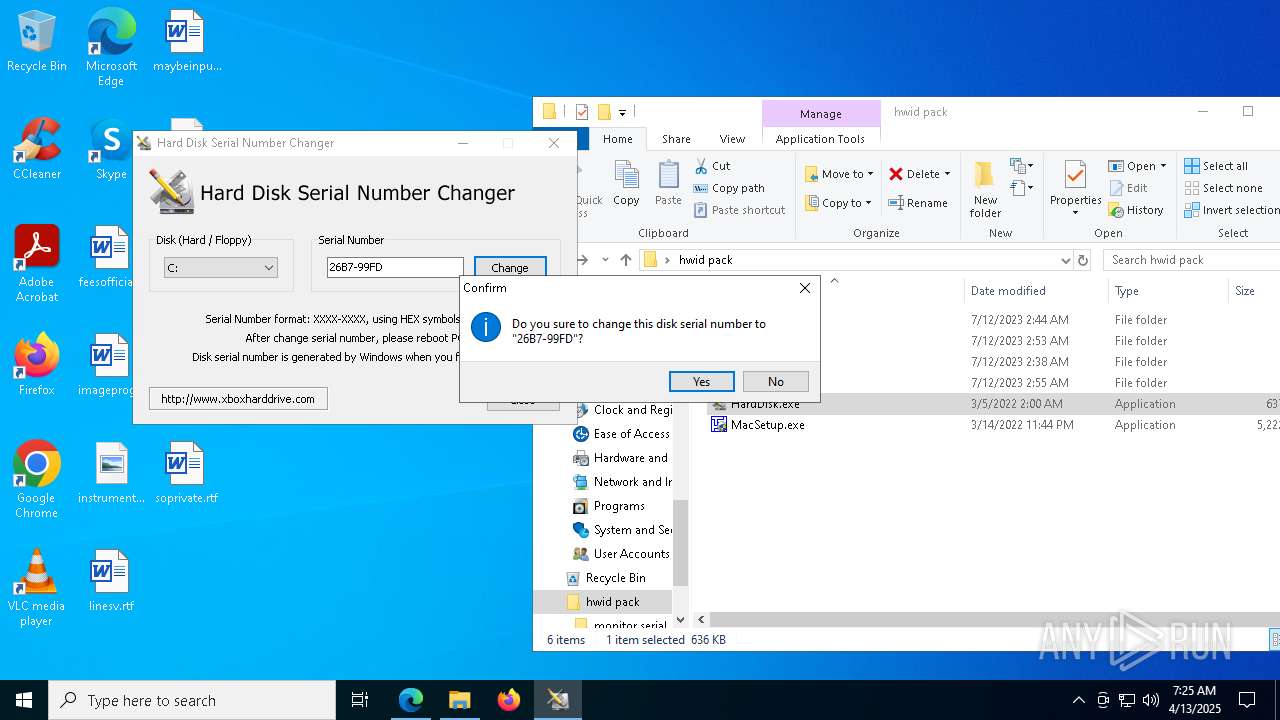
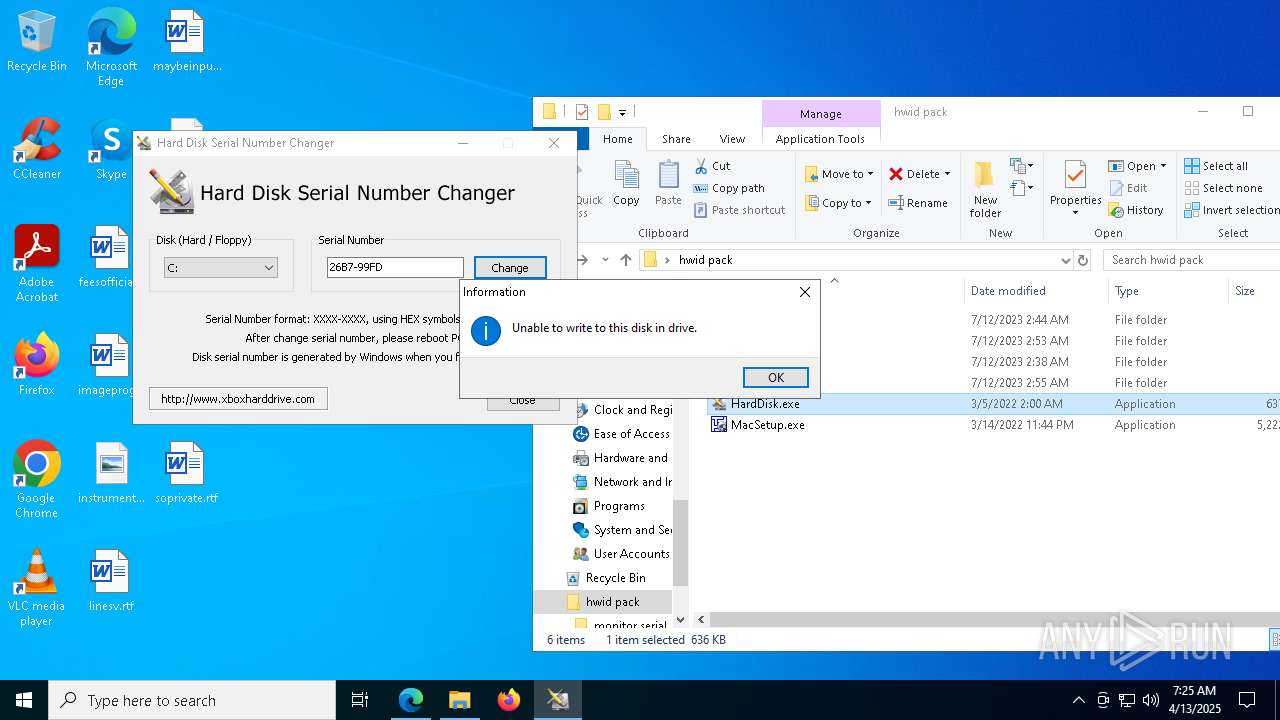
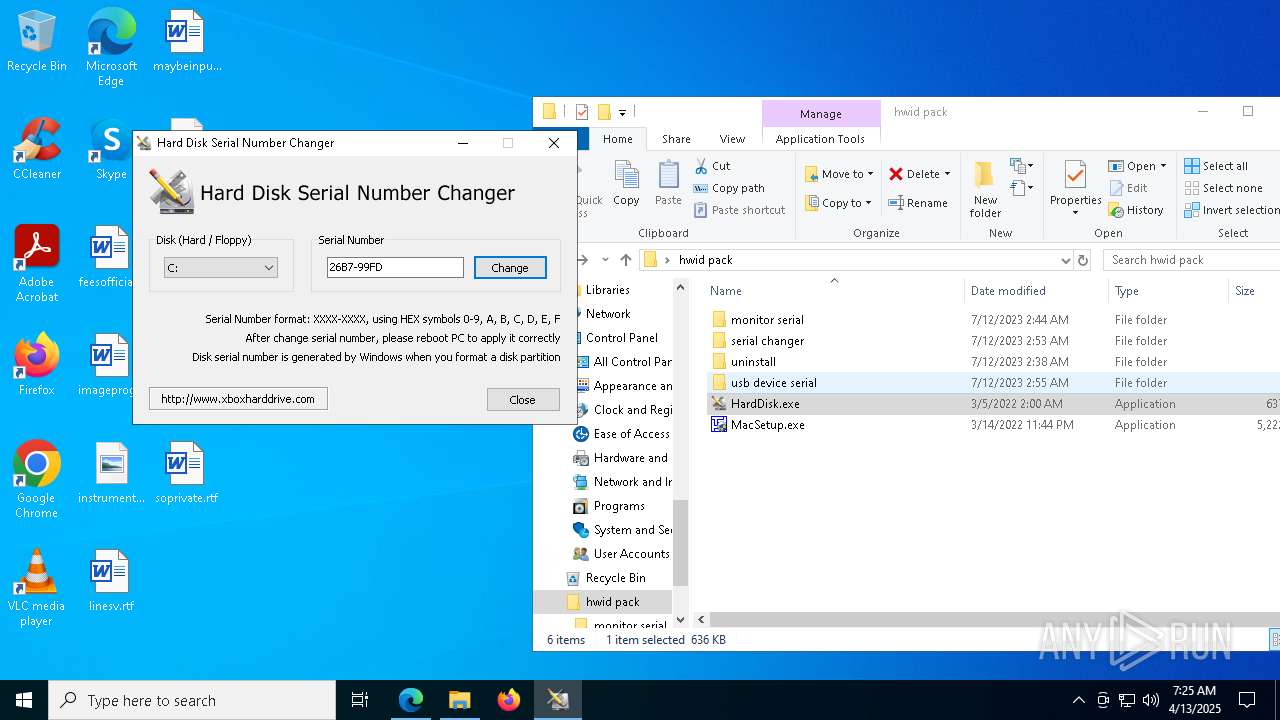
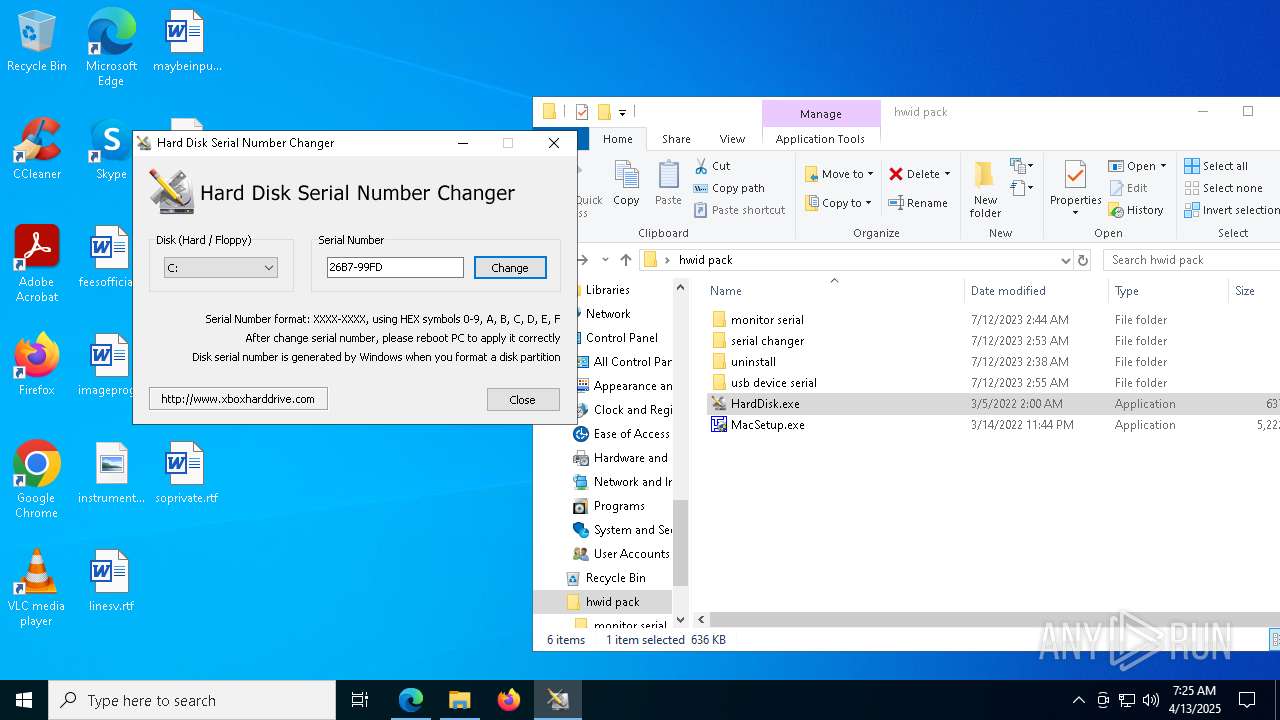
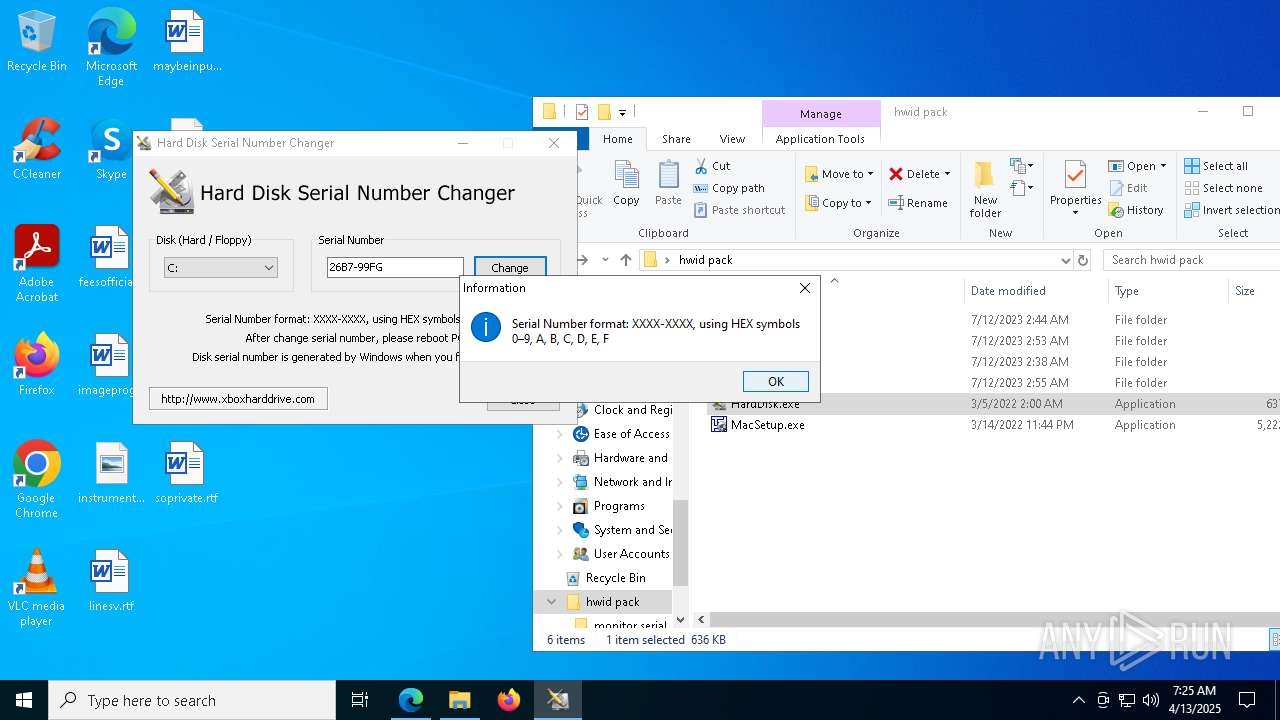
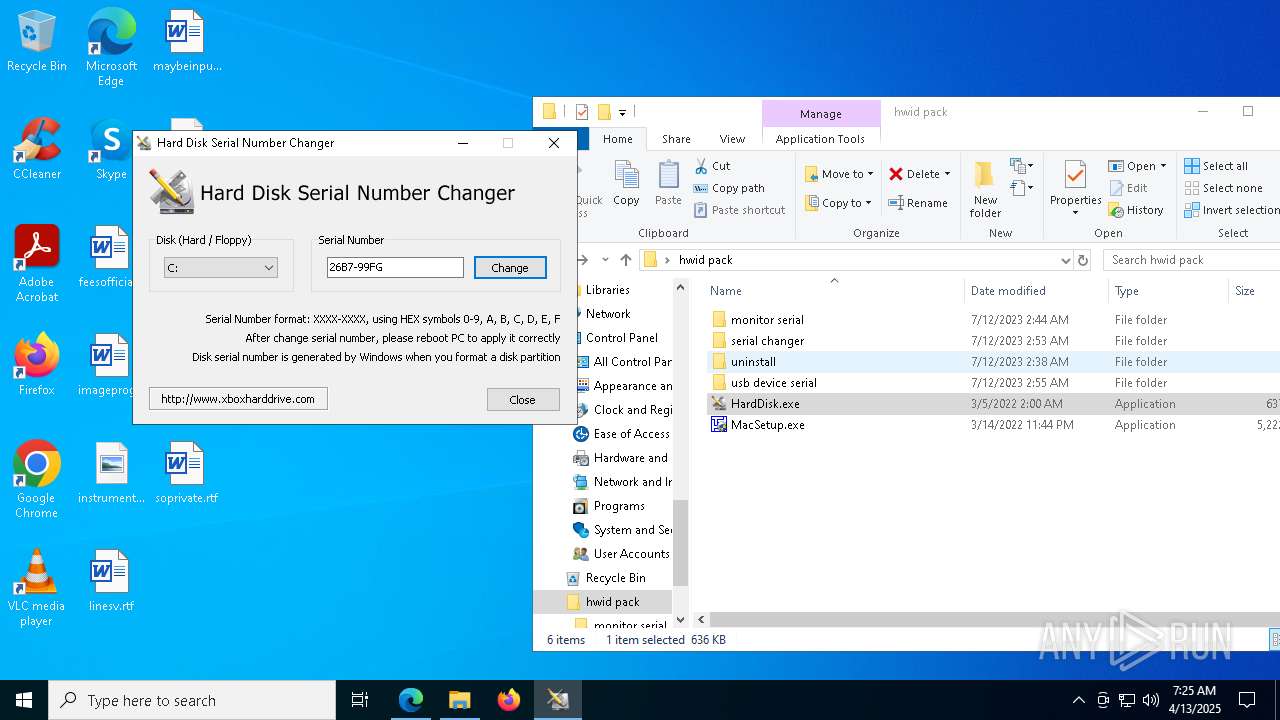
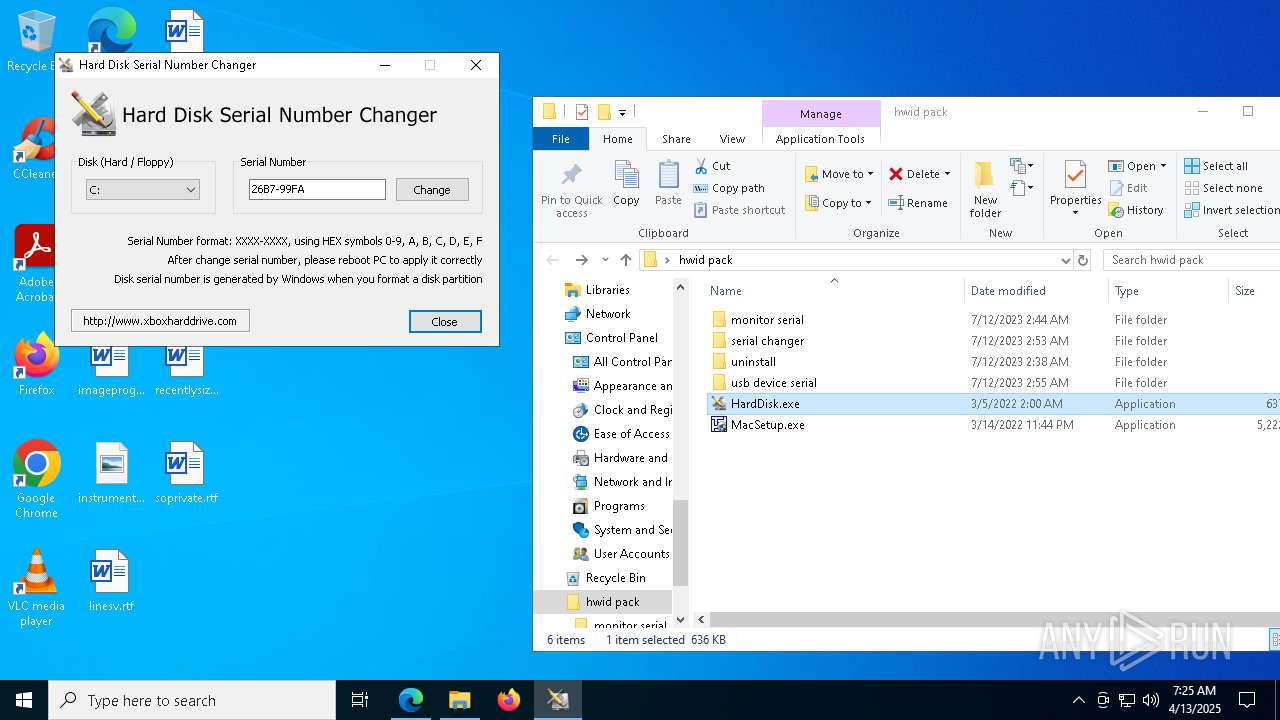
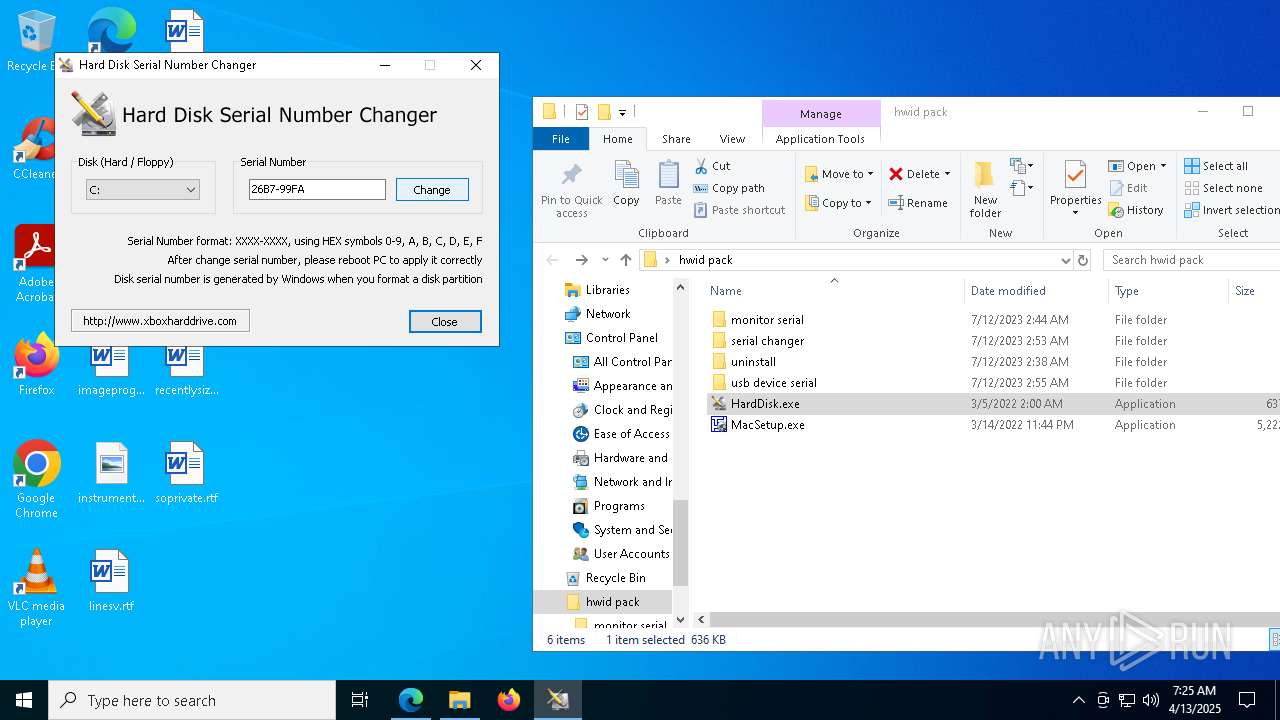
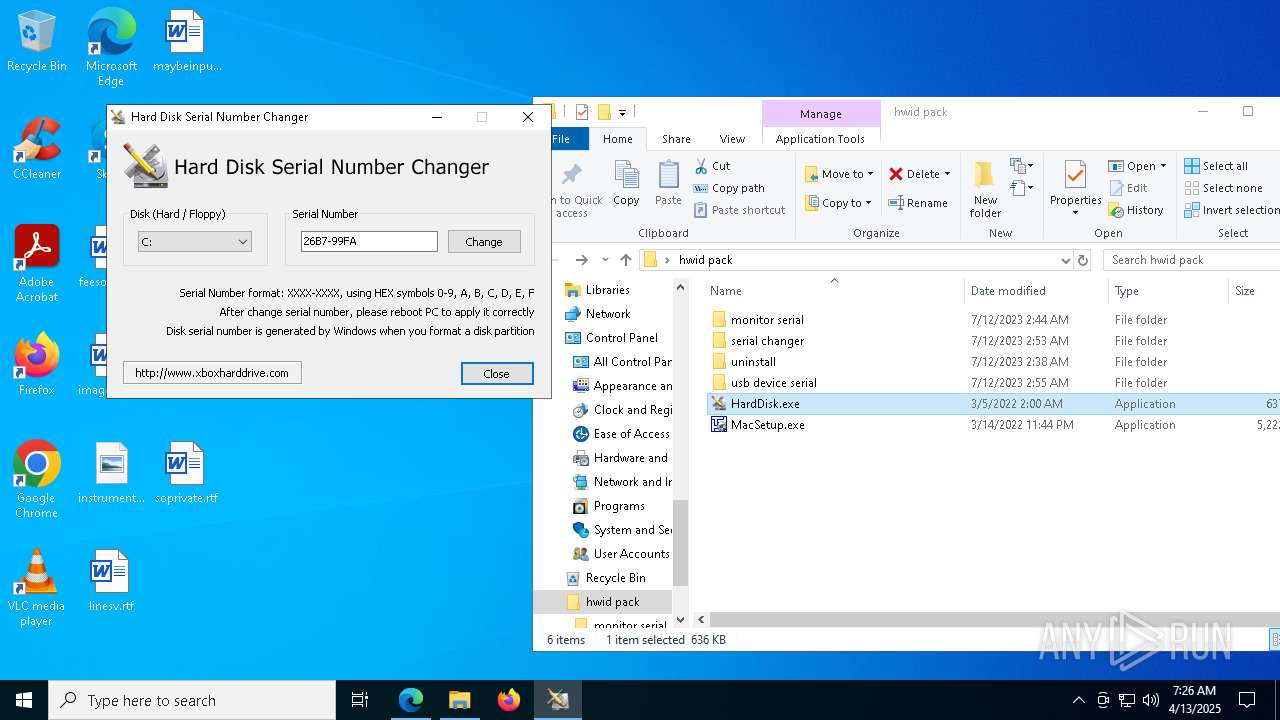
- HardDisk.exe (PID: 7912)
There is functionality for taking screenshot (YARA)
- DMIEDIT.EXE (PID: 5416)
- DMIEDIT.EXE (PID: 5504)
- DMIEDIT.EXE (PID: 7276)
- HardDisk.exe (PID: 7912)
- DMIEDIT.EXE (PID: 7212)
- HardDisk.exe (PID: 1244)
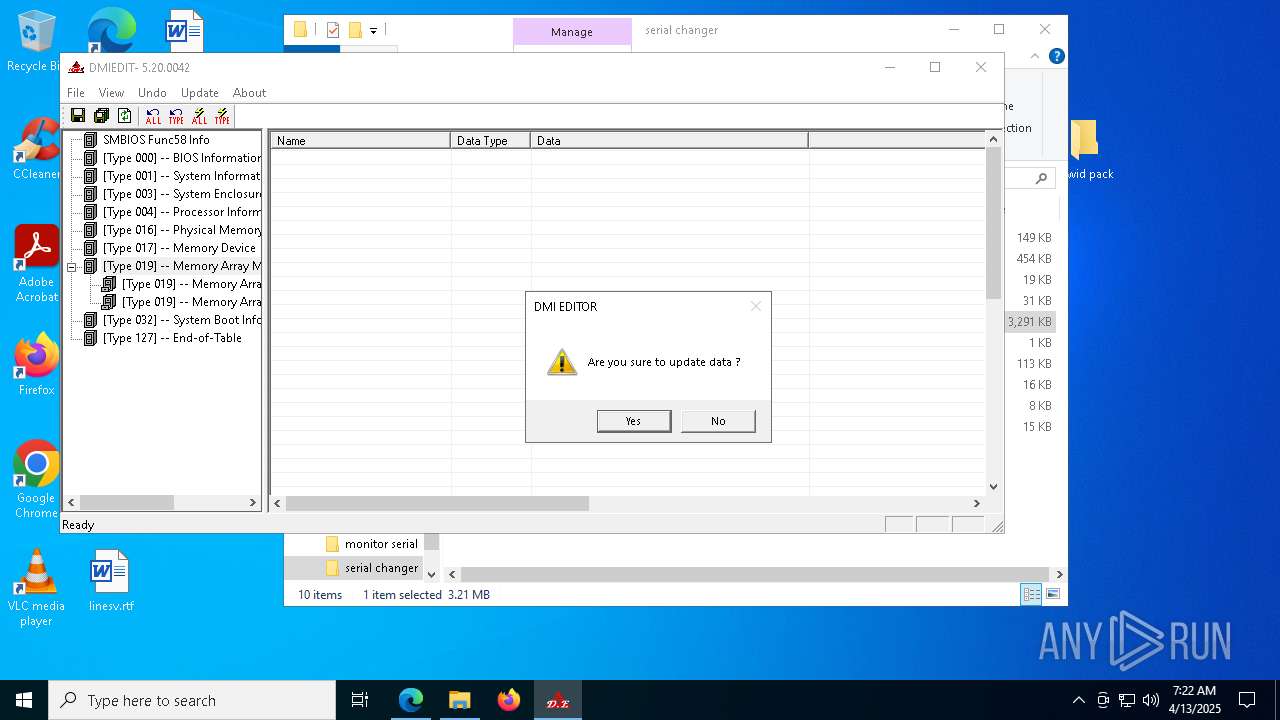
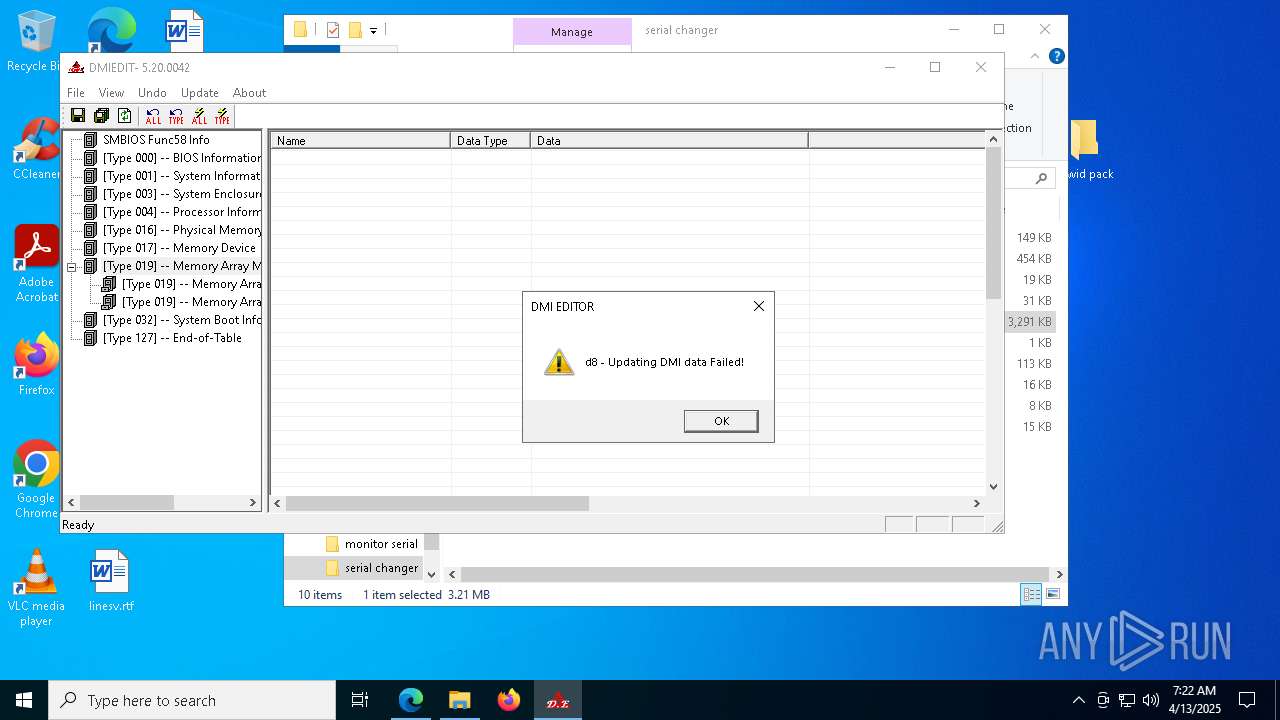
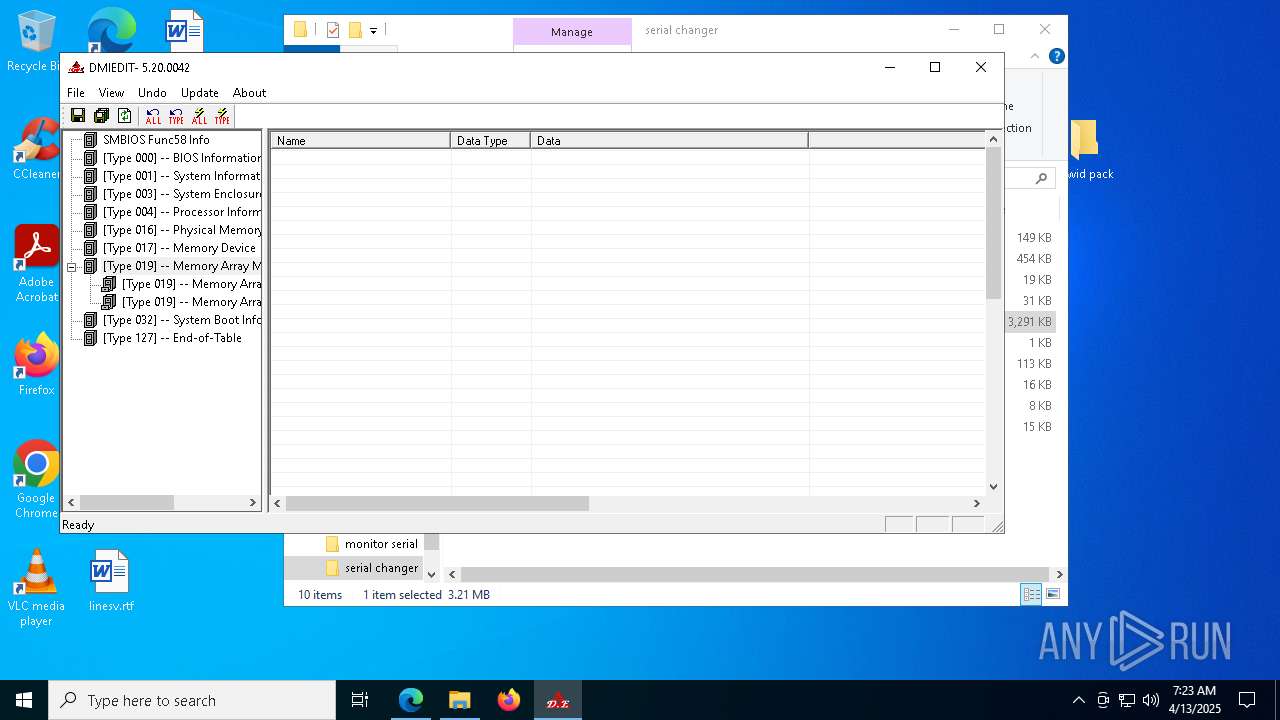
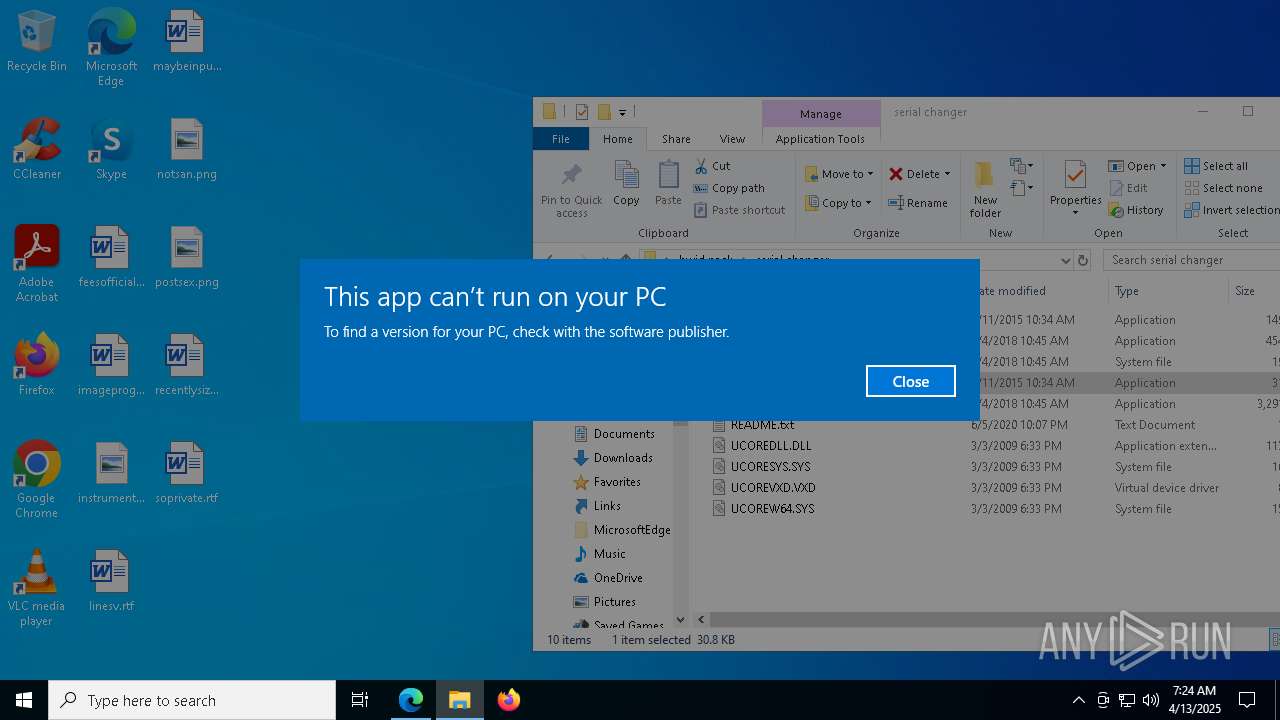
Executes application which crashes
- DMIEDIT.EXE (PID: 5416)
- DMIEDIT.EXE (PID: 5504)
- DMIEDIT.EXE (PID: 7276)
- DMIEDIT.EXE (PID: 7212)
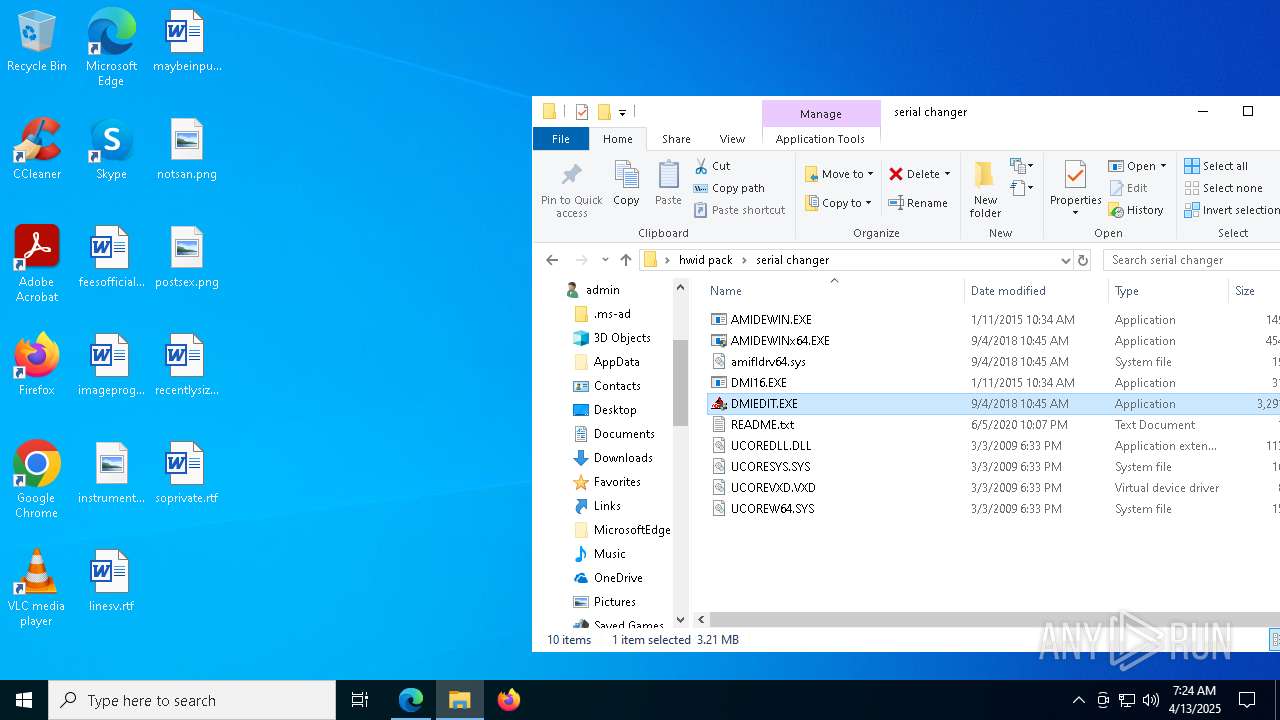
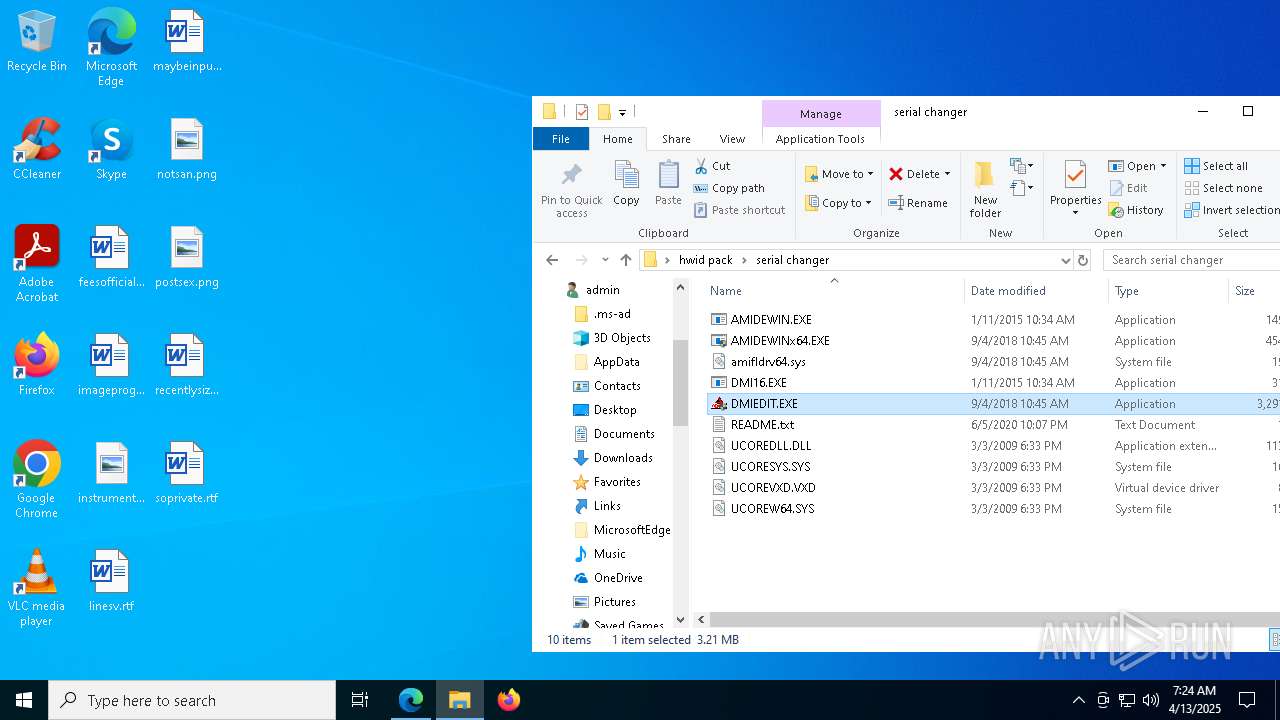
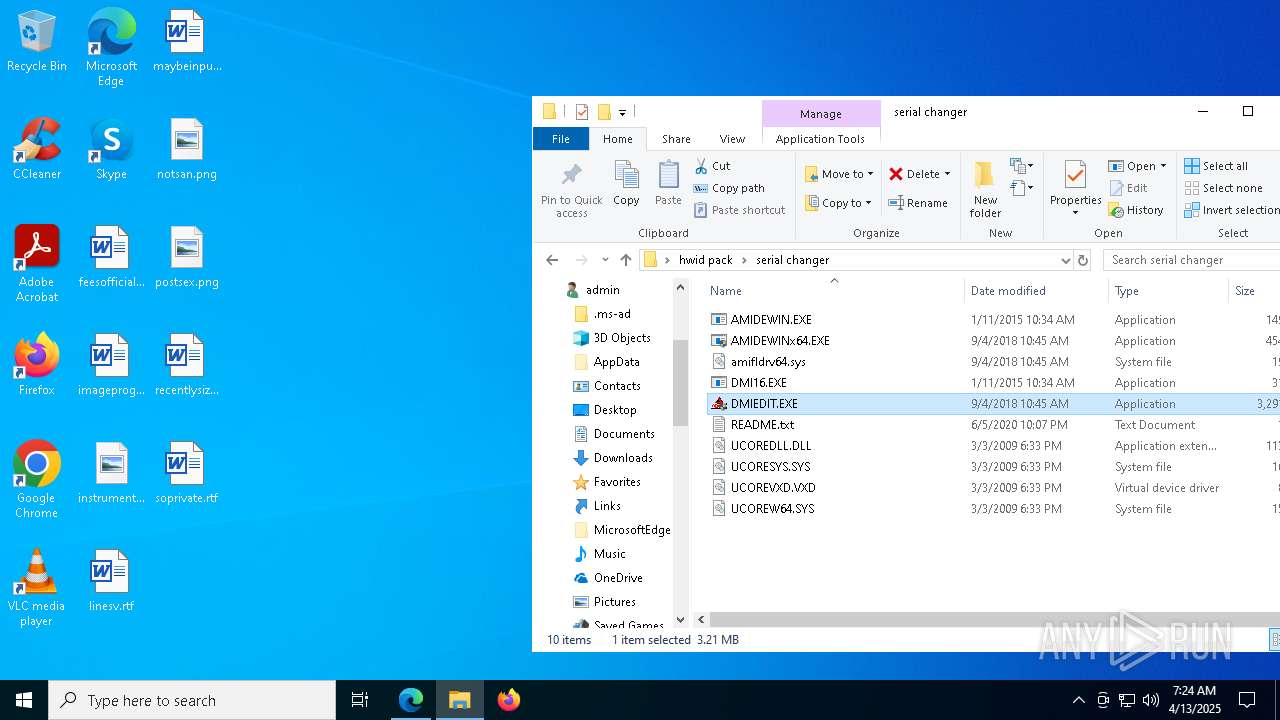
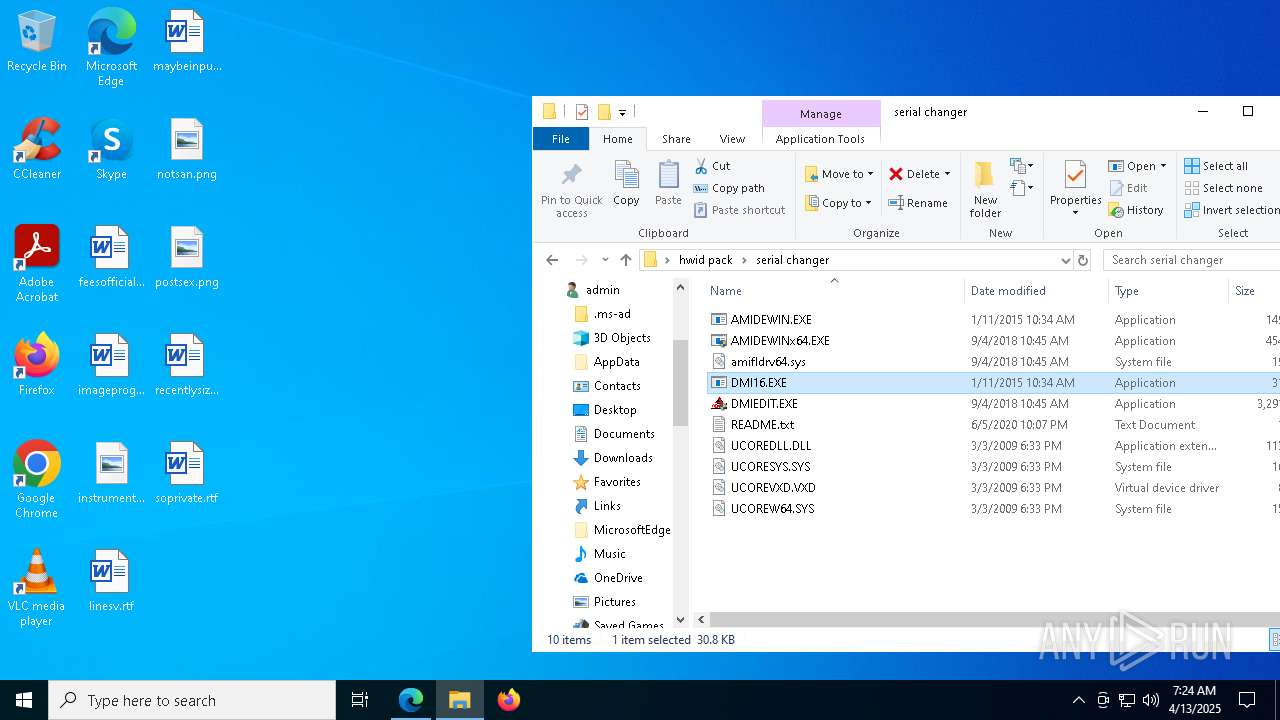
Drops a system driver (possible attempt to evade defenses)
- WinRAR.exe (PID: 3896)
INFO
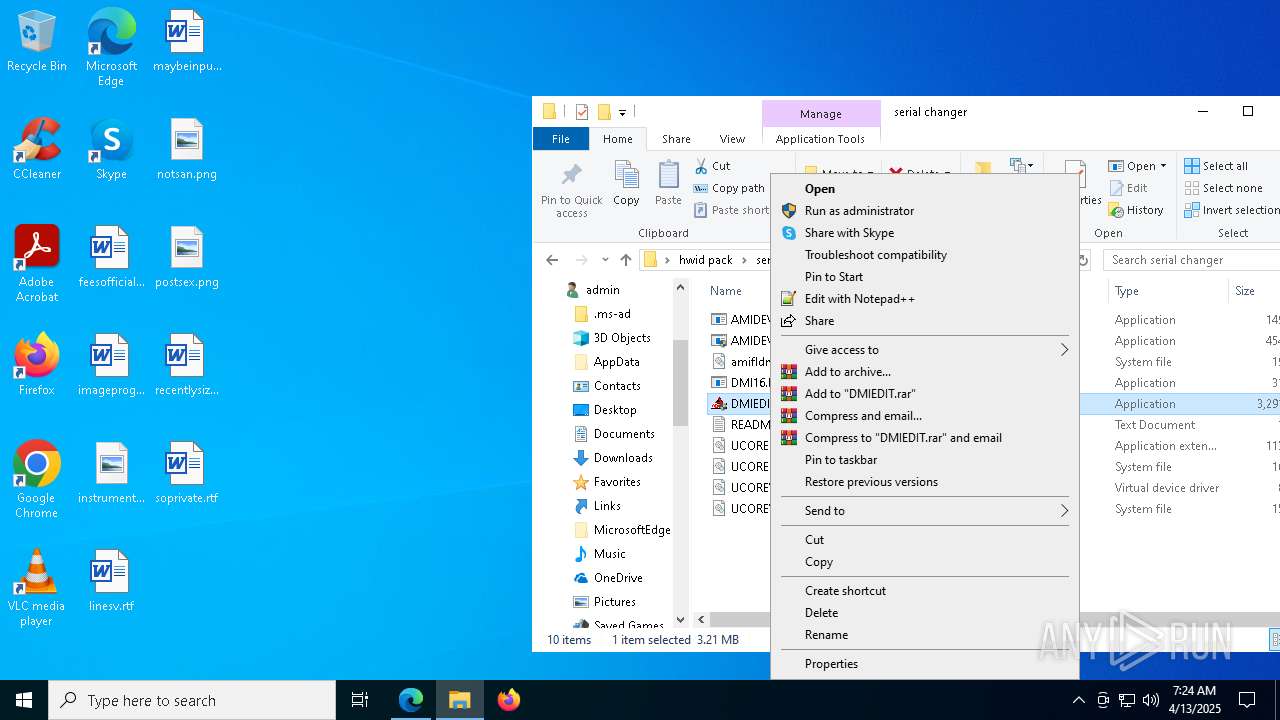
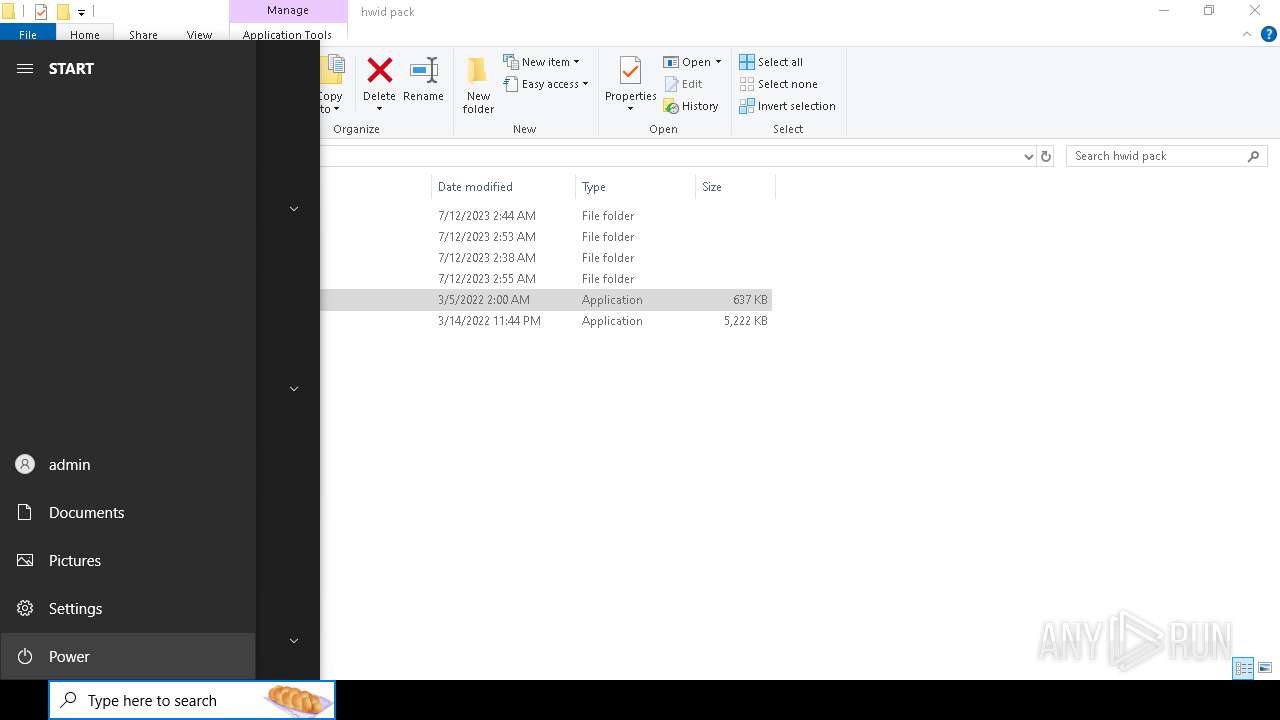
Manual execution by a user
- msedge.exe (PID: 6080)
- DMIEDIT.EXE (PID: 7280)
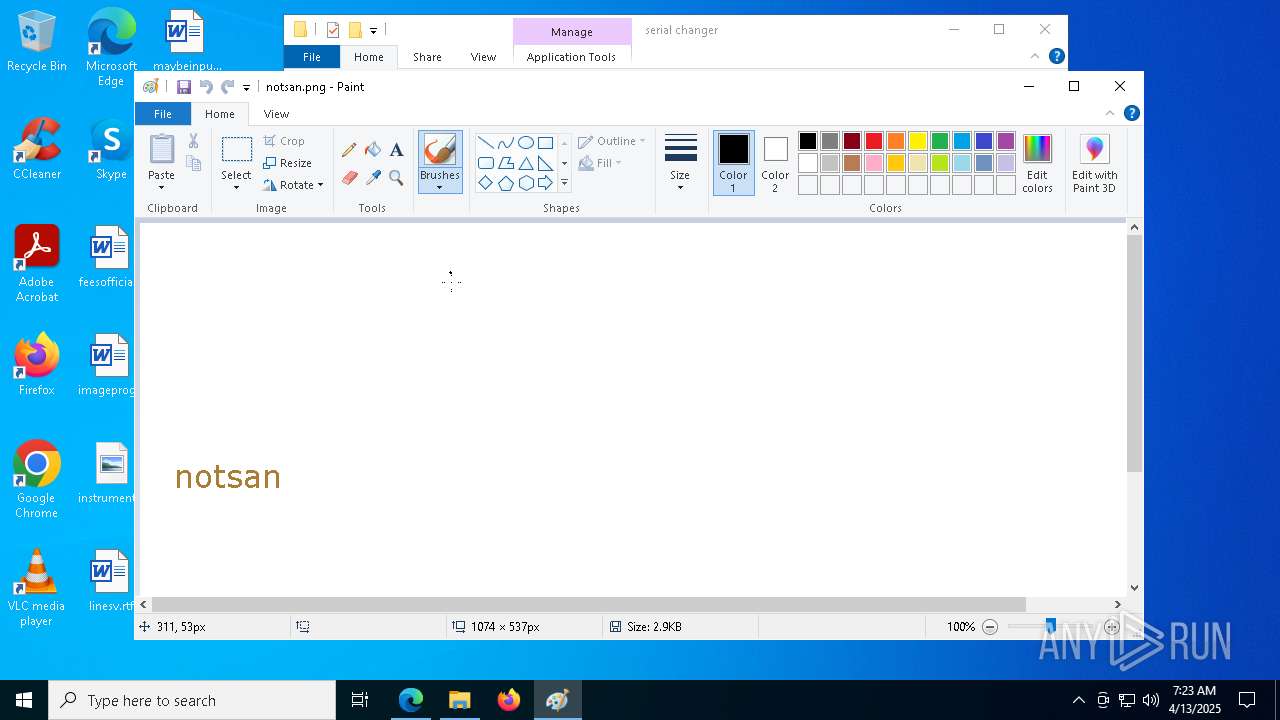
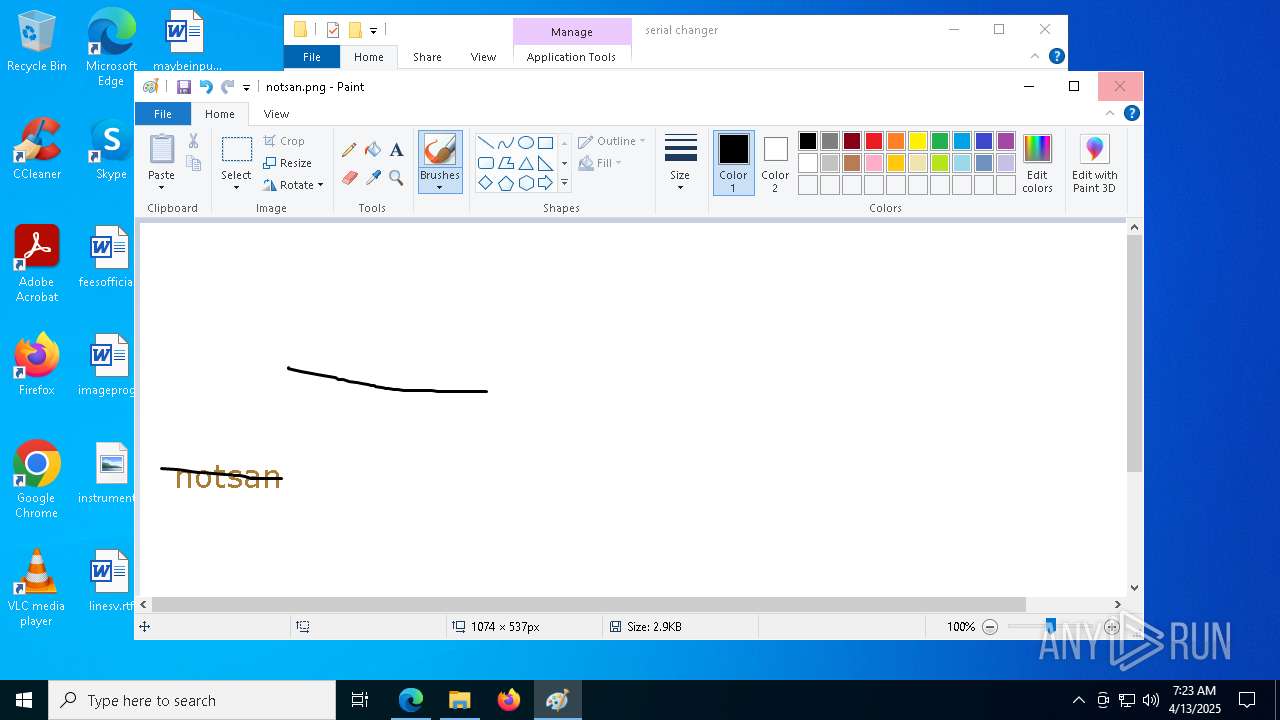
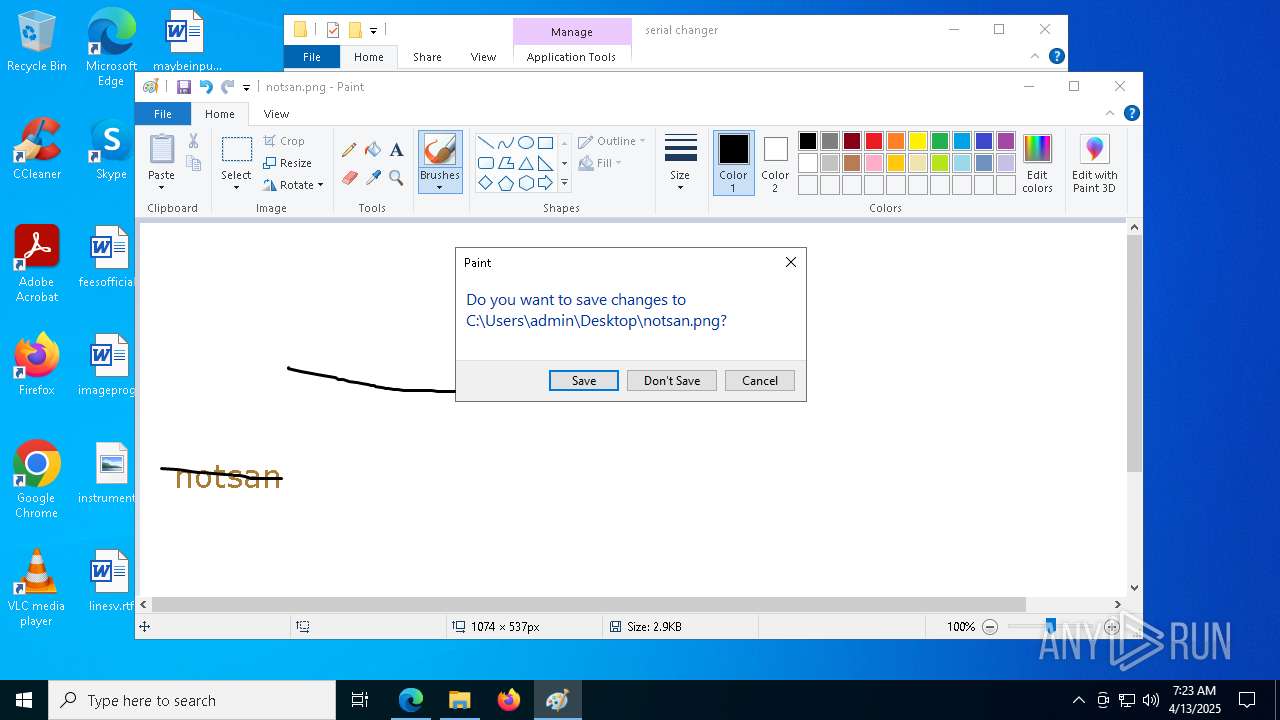
- mspaint.exe (PID: 8068)
- DMIEDIT.EXE (PID: 7276)
- DMIEDIT.EXE (PID: 8040)
- DMIEDIT.EXE (PID: 5280)
- DMIEDIT.EXE (PID: 5504)
- DMIEDIT.EXE (PID: 904)
- DMIEDIT.EXE (PID: 5416)
- DMIEDIT.EXE (PID: 7212)
- DMIEDIT.EXE (PID: 516)
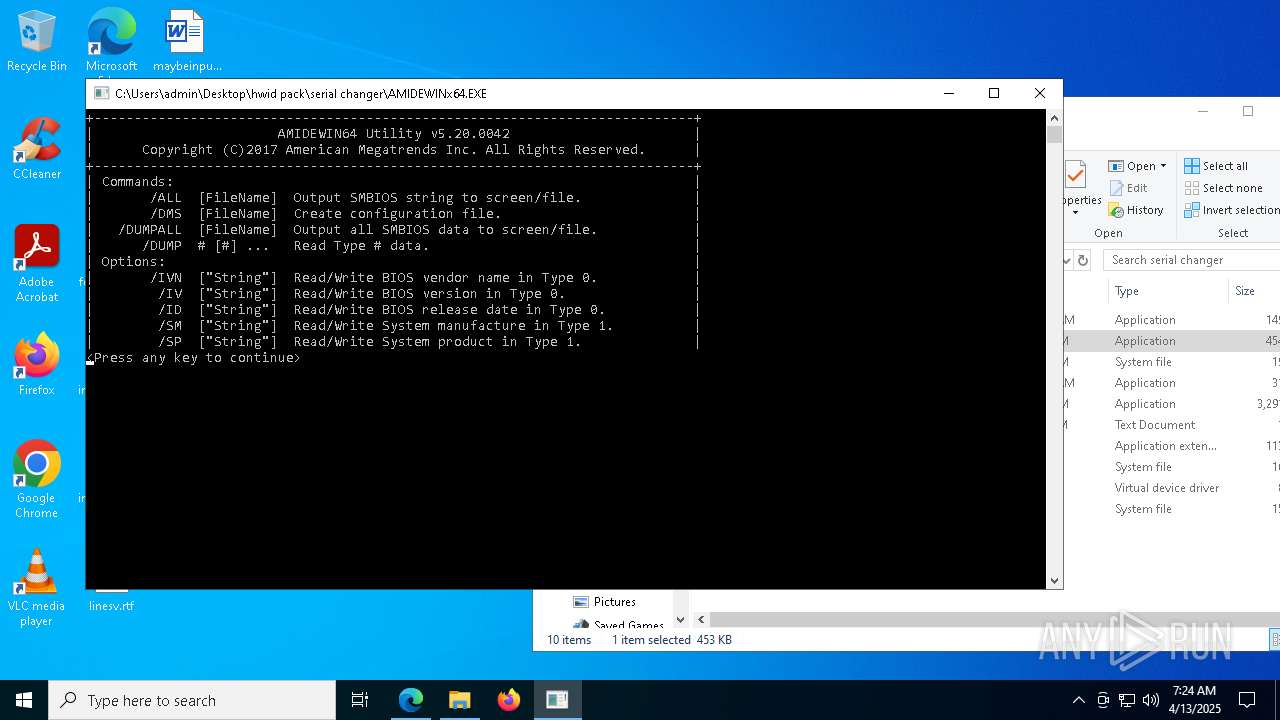
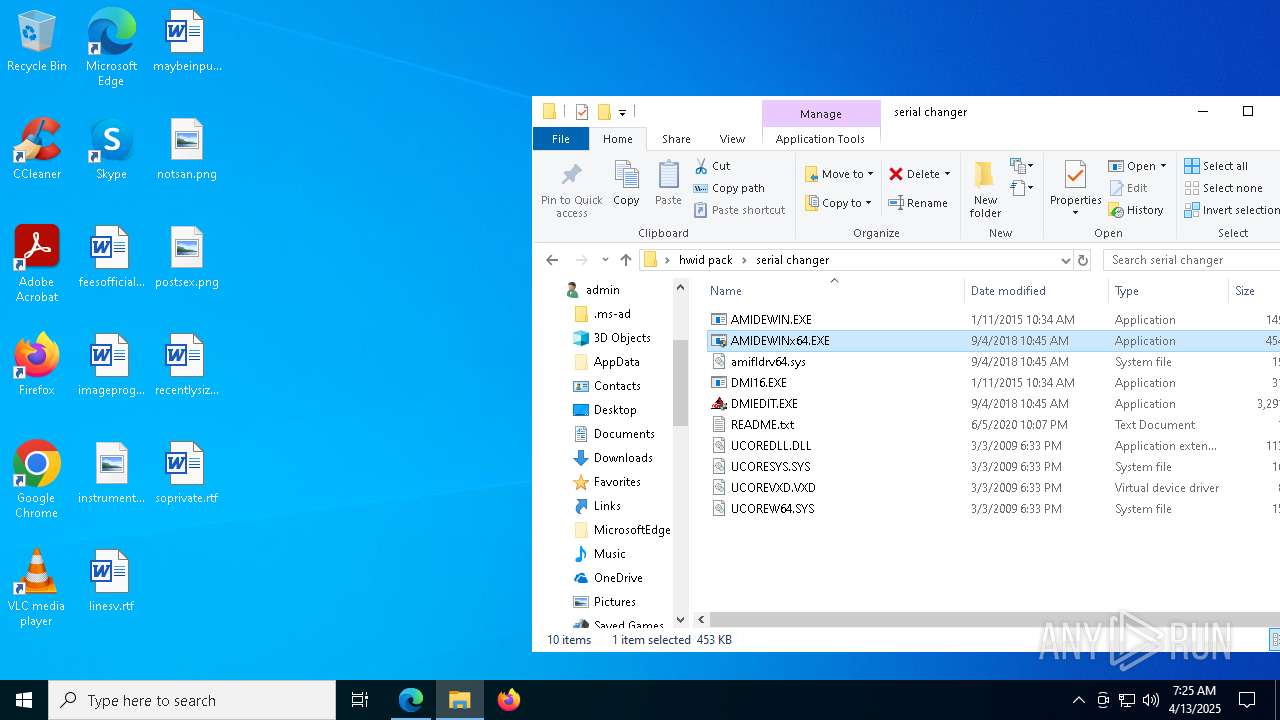
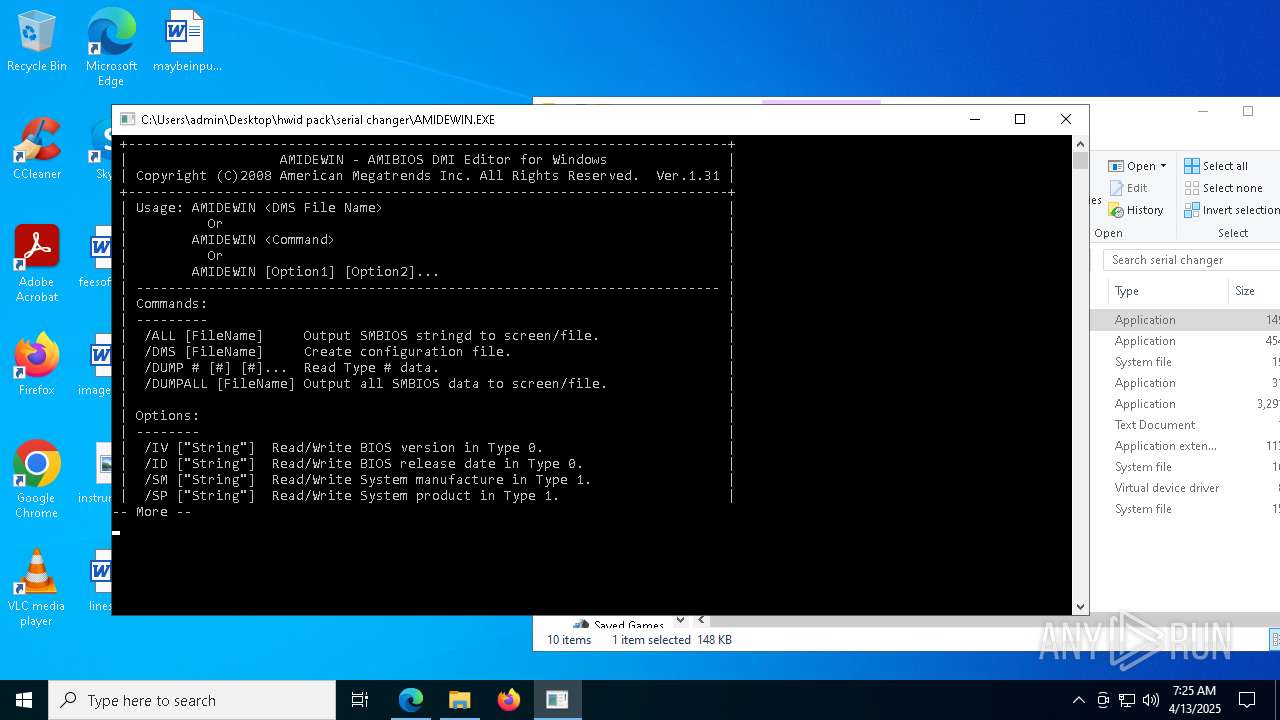
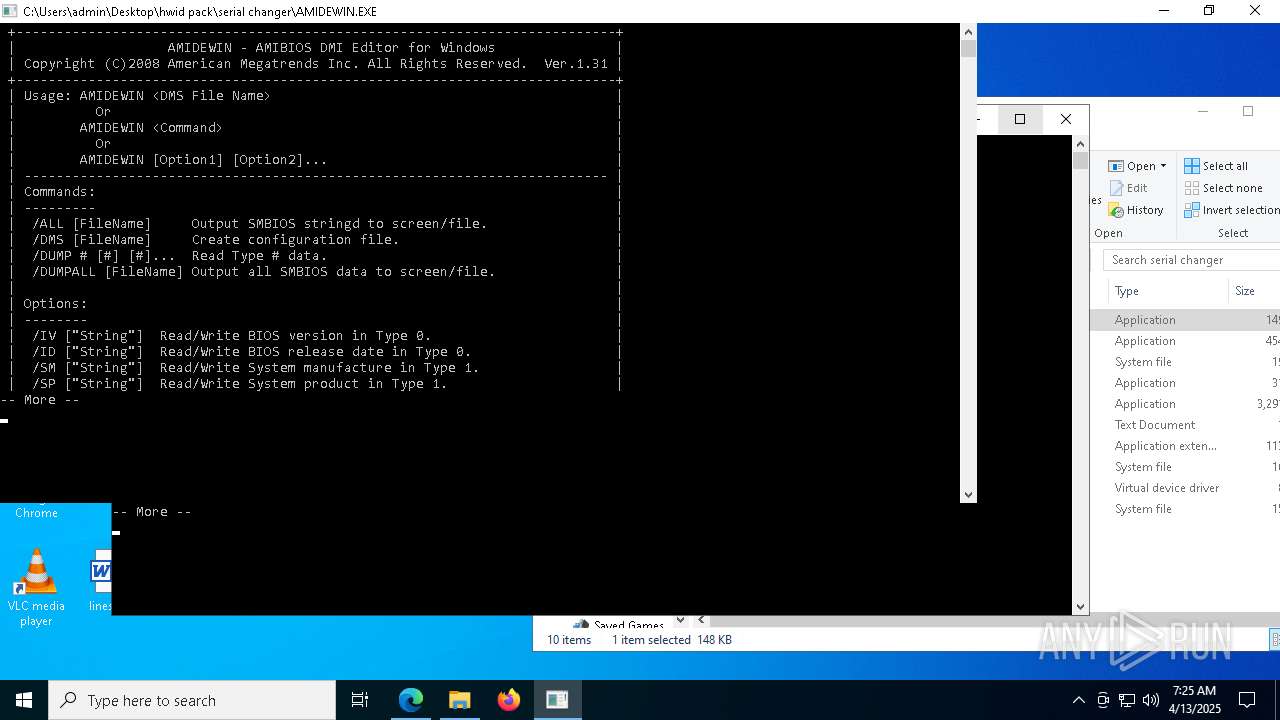
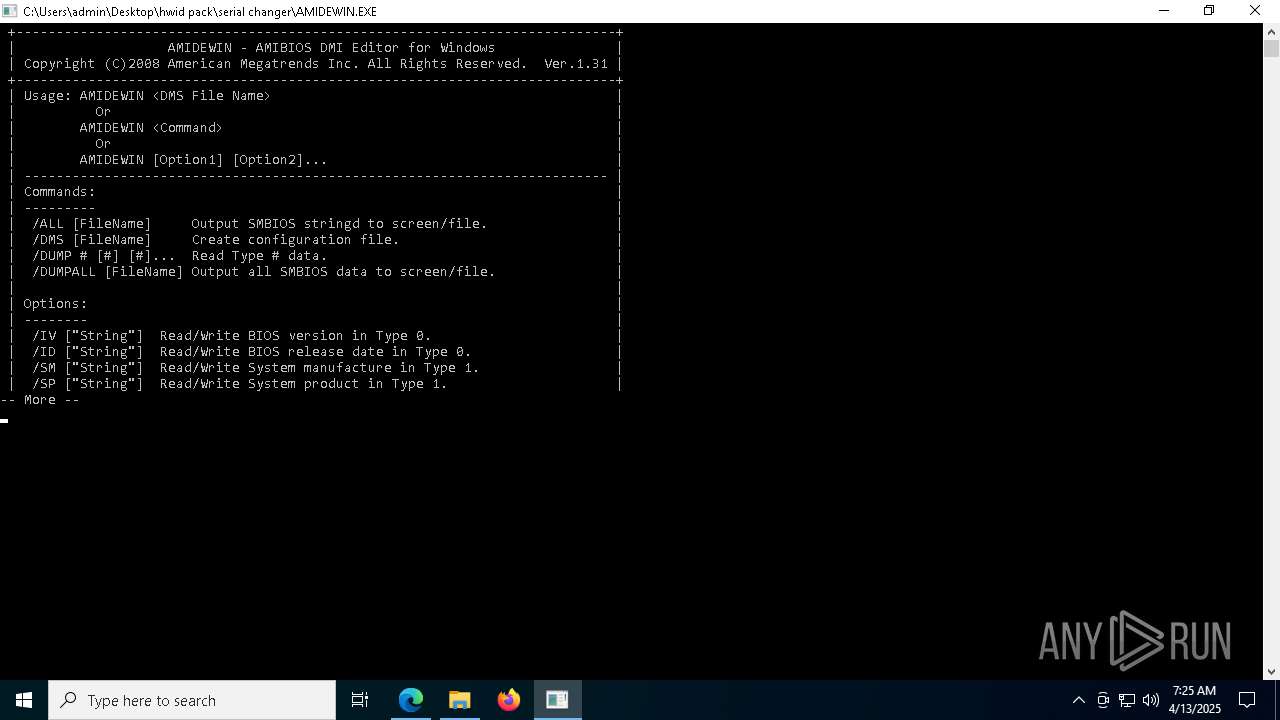
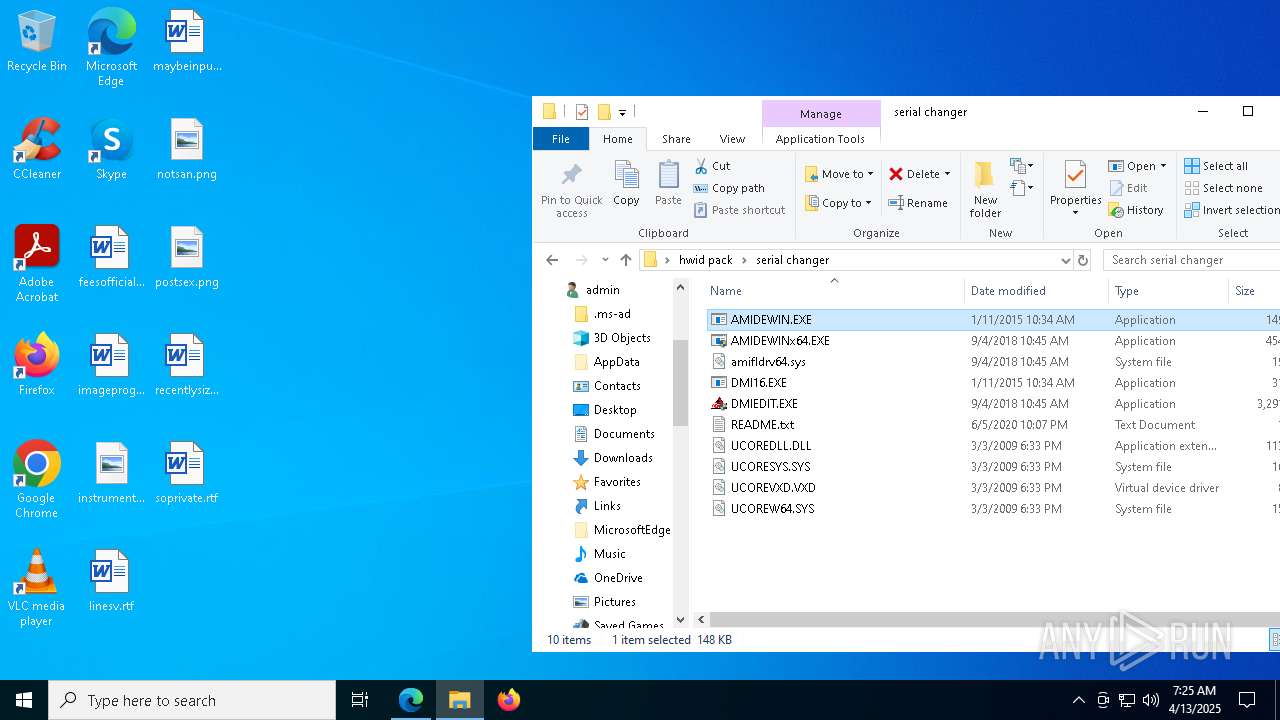
- AMIDEWINx64.EXE (PID: 7636)
- AMIDEWIN.EXE (PID: 7596)
- AMIDEWINx64.EXE (PID: 4212)
- HardDisk.exe (PID: 7912)
- HardDisk.exe (PID: 7372)
- HardDisk.exe (PID: 1244)
- HardDisk.exe (PID: 4200)
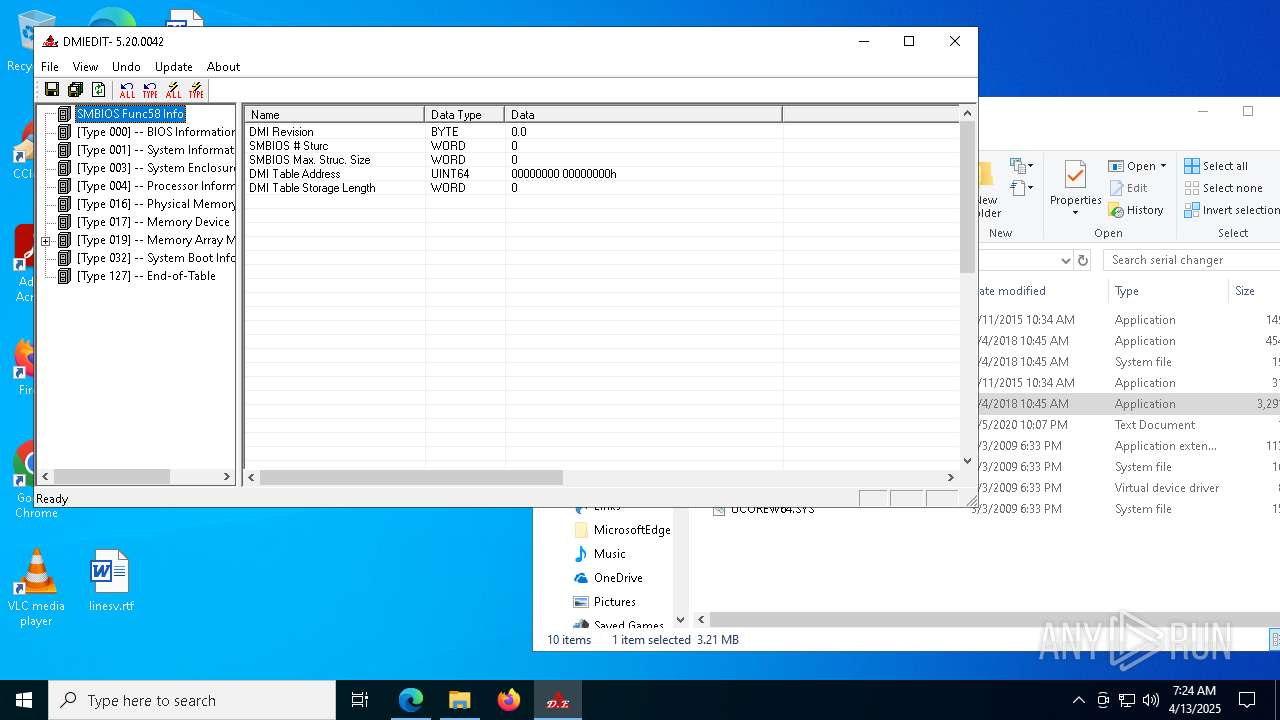
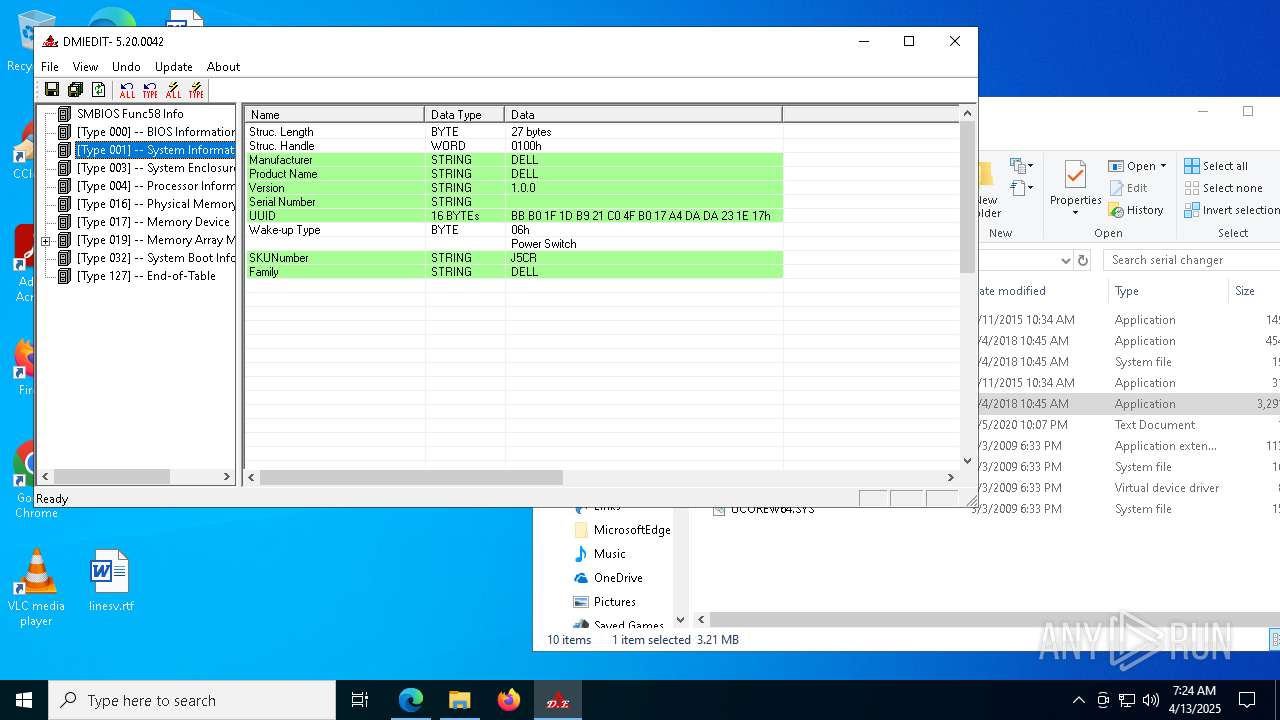
Checks supported languages
- DMIEDIT.EXE (PID: 5416)
- identity_helper.exe (PID: 8164)
- DMIEDIT.EXE (PID: 7276)
- DMIEDIT.EXE (PID: 5504)
- DMIEDIT.EXE (PID: 516)
- AMIDEWIN.EXE (PID: 7596)
- AMIDEWINx64.EXE (PID: 4212)
- HardDisk.exe (PID: 7912)
- DMIEDIT.EXE (PID: 7212)
- identity_helper.exe (PID: 4056)
- HardDisk.exe (PID: 7372)
- HardDisk.exe (PID: 1244)
- HardDisk.exe (PID: 4200)
Reads Environment values
- identity_helper.exe (PID: 8164)
- identity_helper.exe (PID: 4056)
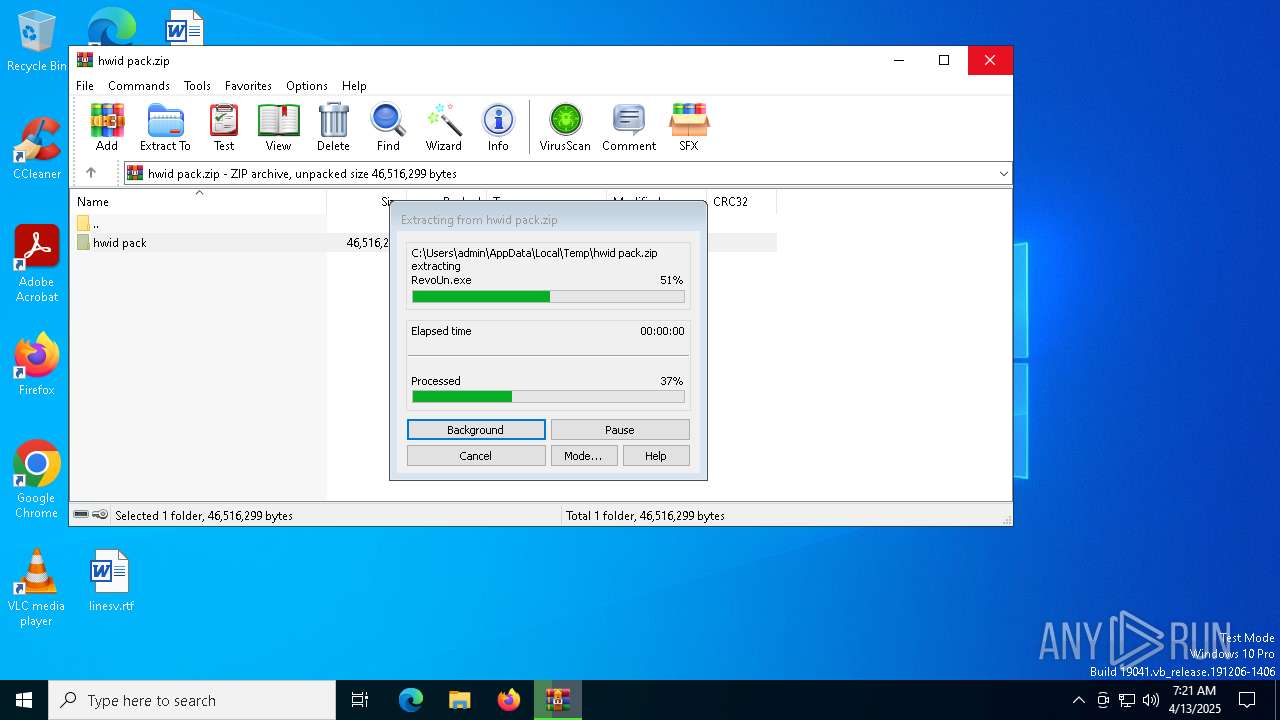
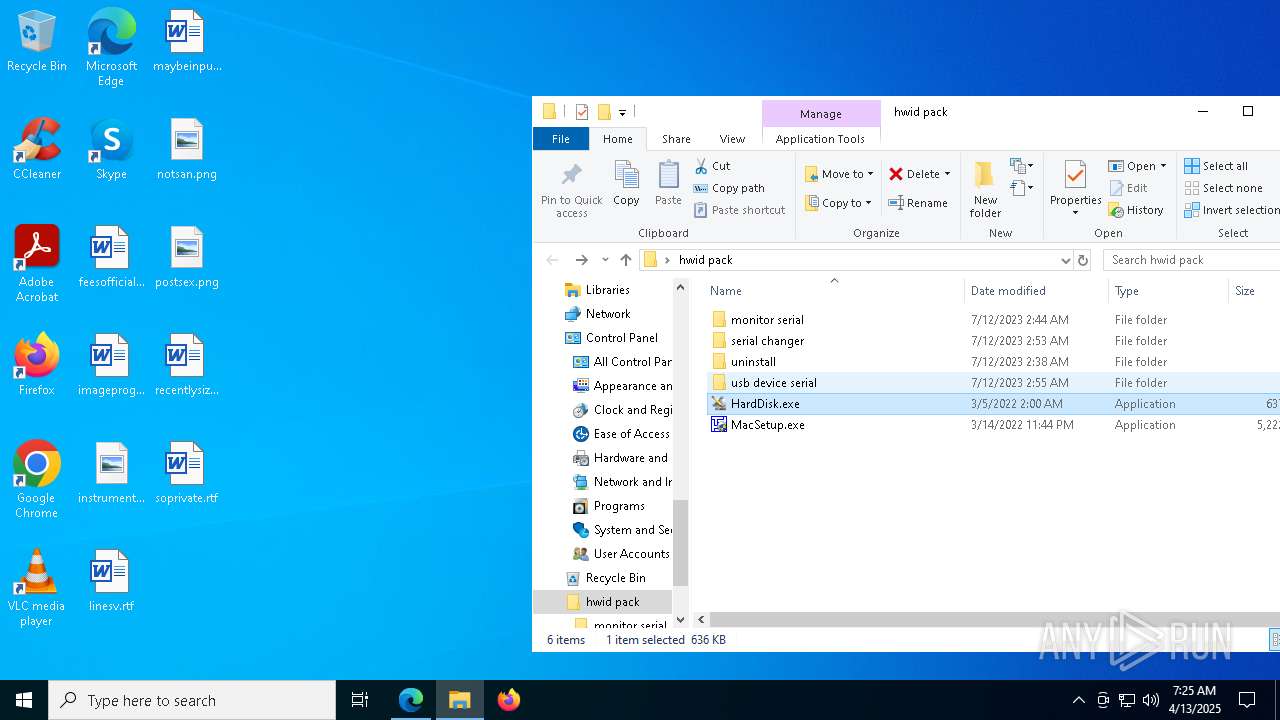
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3896)
The sample compiled with english language support
- WinRAR.exe (PID: 3896)
Application launched itself
- msedge.exe (PID: 3300)
- msedge.exe (PID: 6080)
- msedge.exe (PID: 5956)
Creates files or folders in the user directory
- WerFault.exe (PID: 7468)
- WerFault.exe (PID: 2896)
- WerFault.exe (PID: 6072)
- WerFault.exe (PID: 3396)
Reads the computer name
- identity_helper.exe (PID: 8164)
- DMIEDIT.EXE (PID: 7276)
- DMIEDIT.EXE (PID: 5504)
- DMIEDIT.EXE (PID: 5416)
- DMIEDIT.EXE (PID: 516)
- AMIDEWINx64.EXE (PID: 4212)
- HardDisk.exe (PID: 7912)
- DMIEDIT.EXE (PID: 7212)
- identity_helper.exe (PID: 4056)
- HardDisk.exe (PID: 7372)
- HardDisk.exe (PID: 1244)
- HardDisk.exe (PID: 4200)
Checks proxy server information
- slui.exe (PID: 4300)
Reads the software policy settings
- slui.exe (PID: 4300)
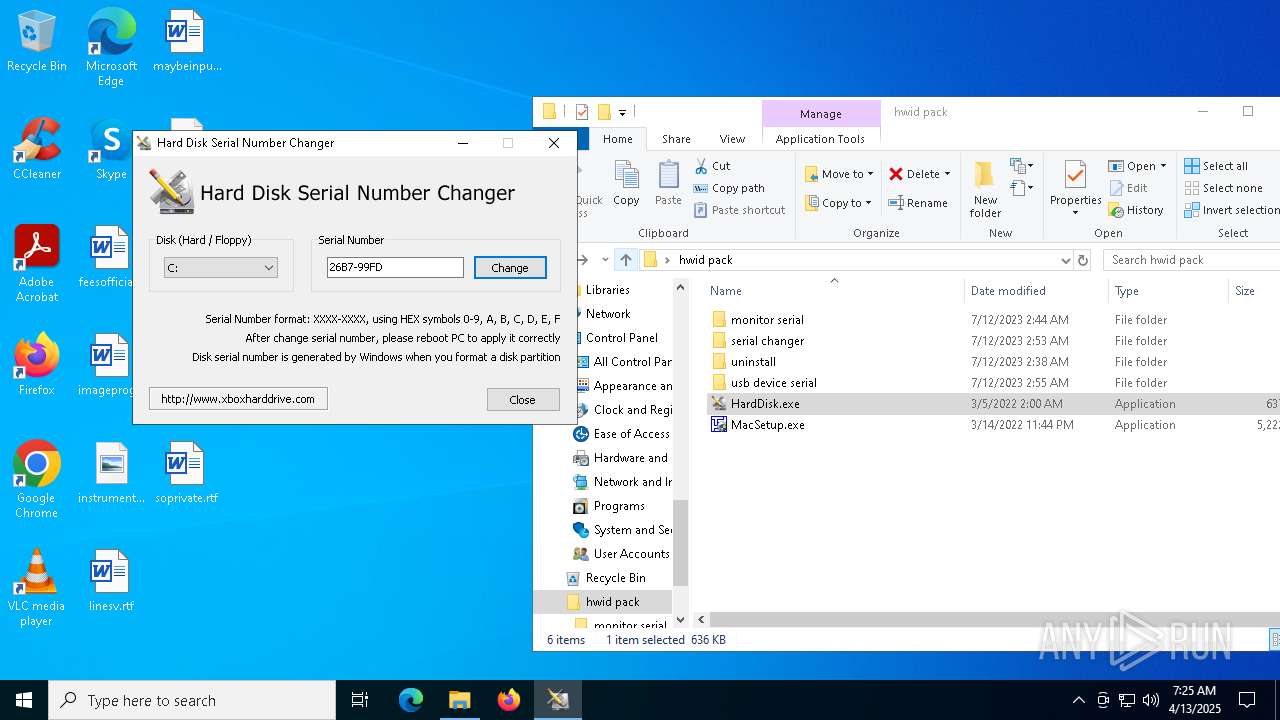
Compiled with Borland Delphi (YARA)
- HardDisk.exe (PID: 7912)
- HardDisk.exe (PID: 1244)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2023:07:11 19:49:08 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | hwid pack/ |
Total processes
268
Monitored processes
116
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 436 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=2620 --field-trial-handle=2344,i,4280044006243932732,16471422888268518074,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
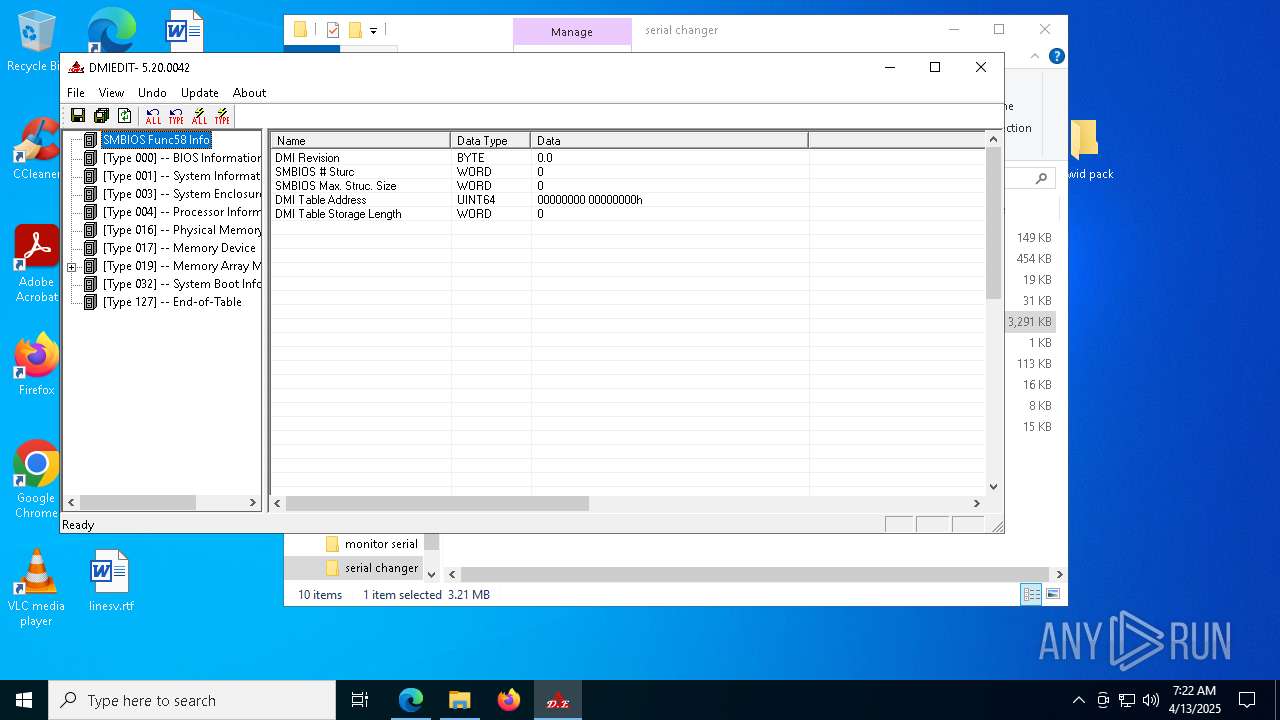
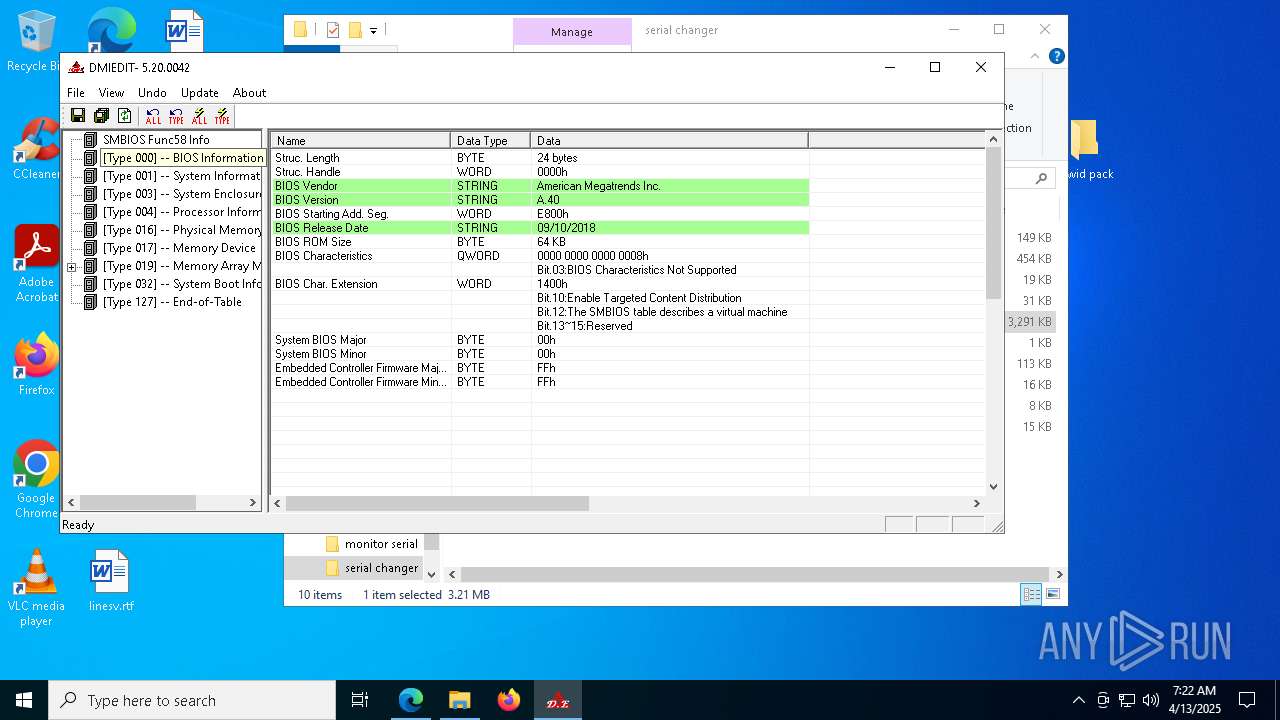
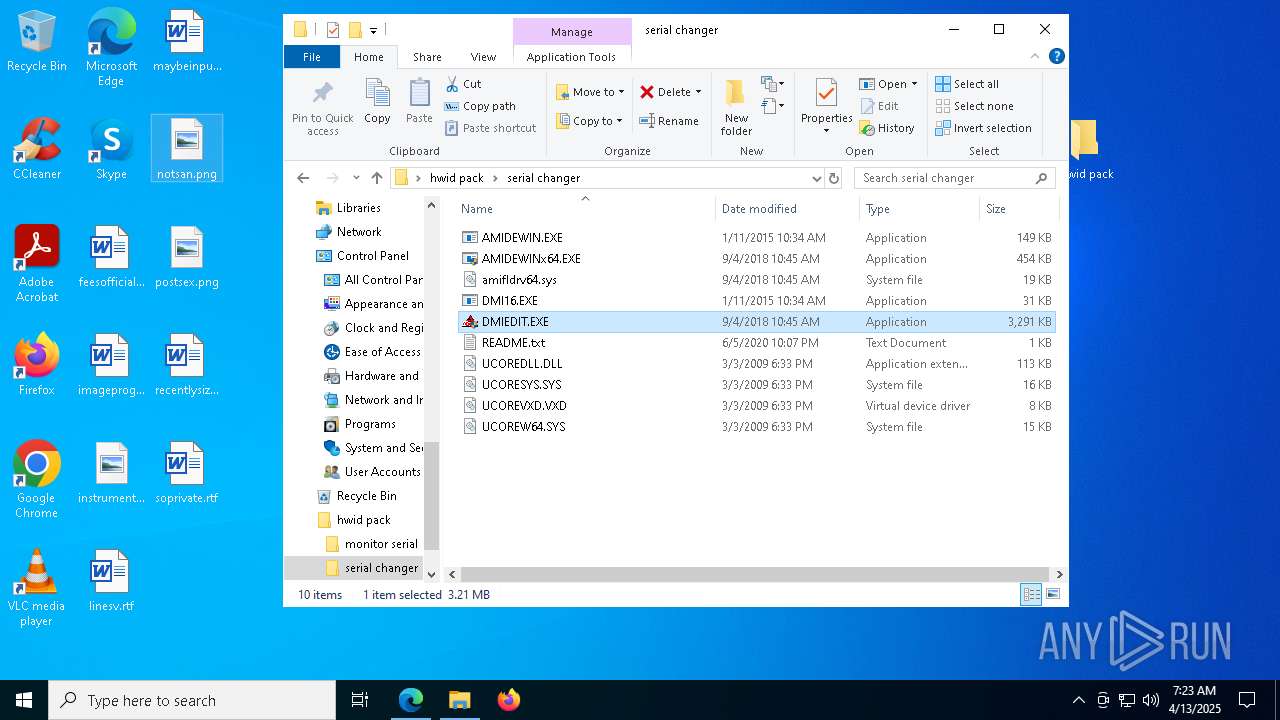
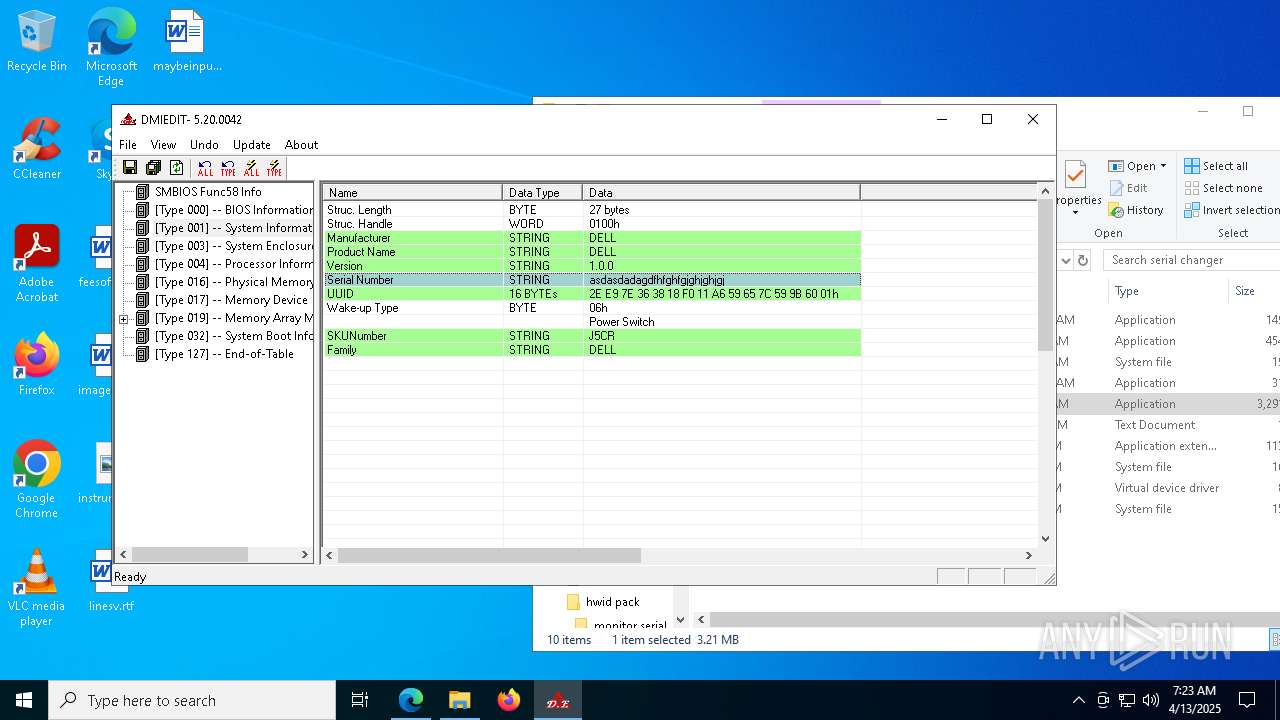
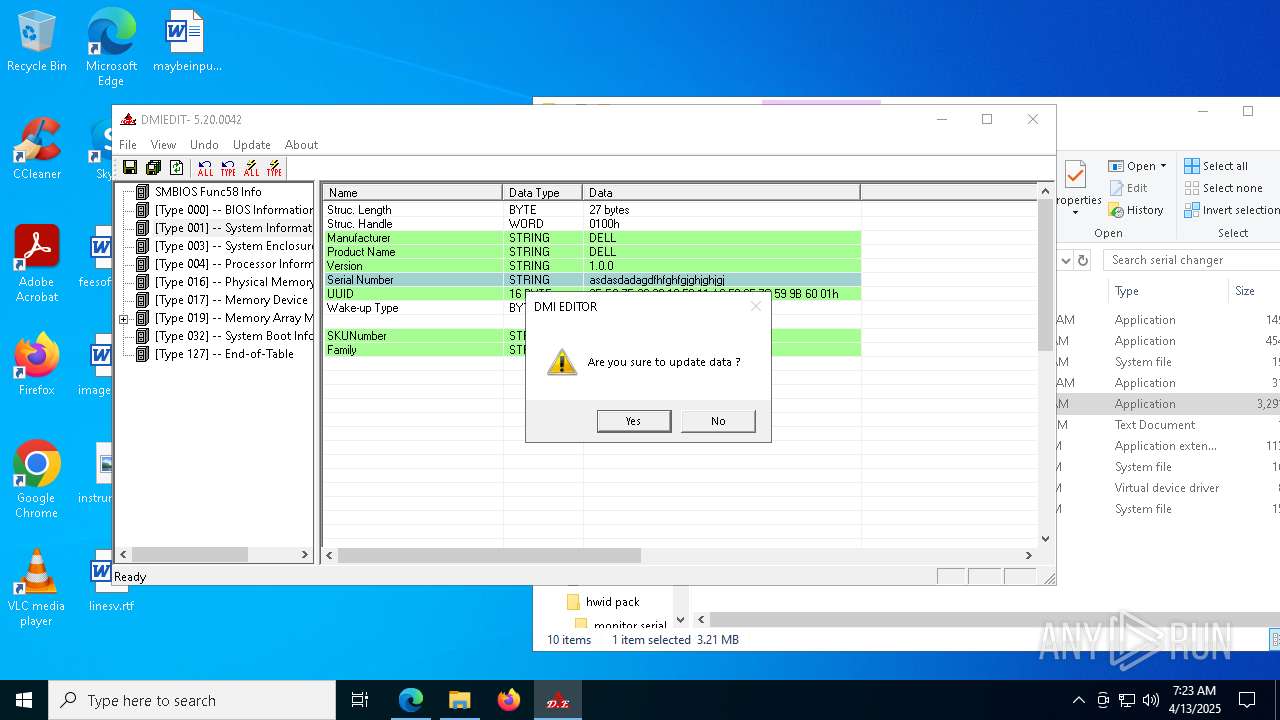
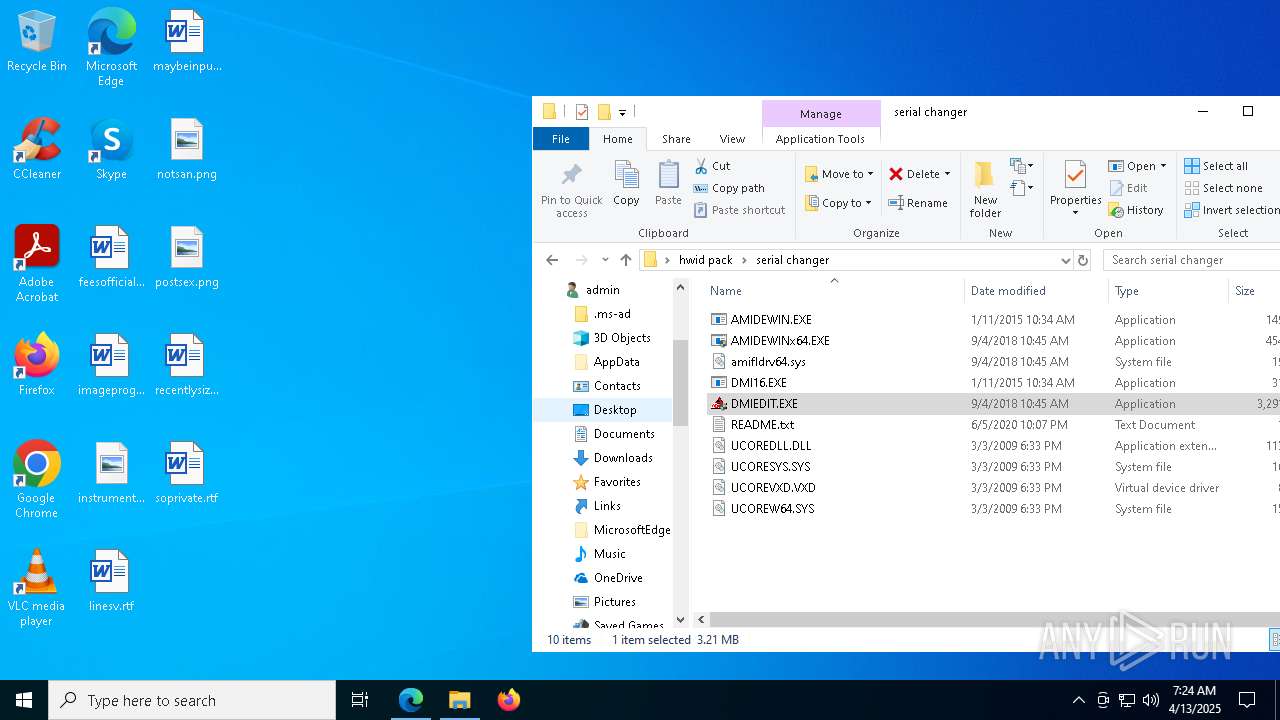
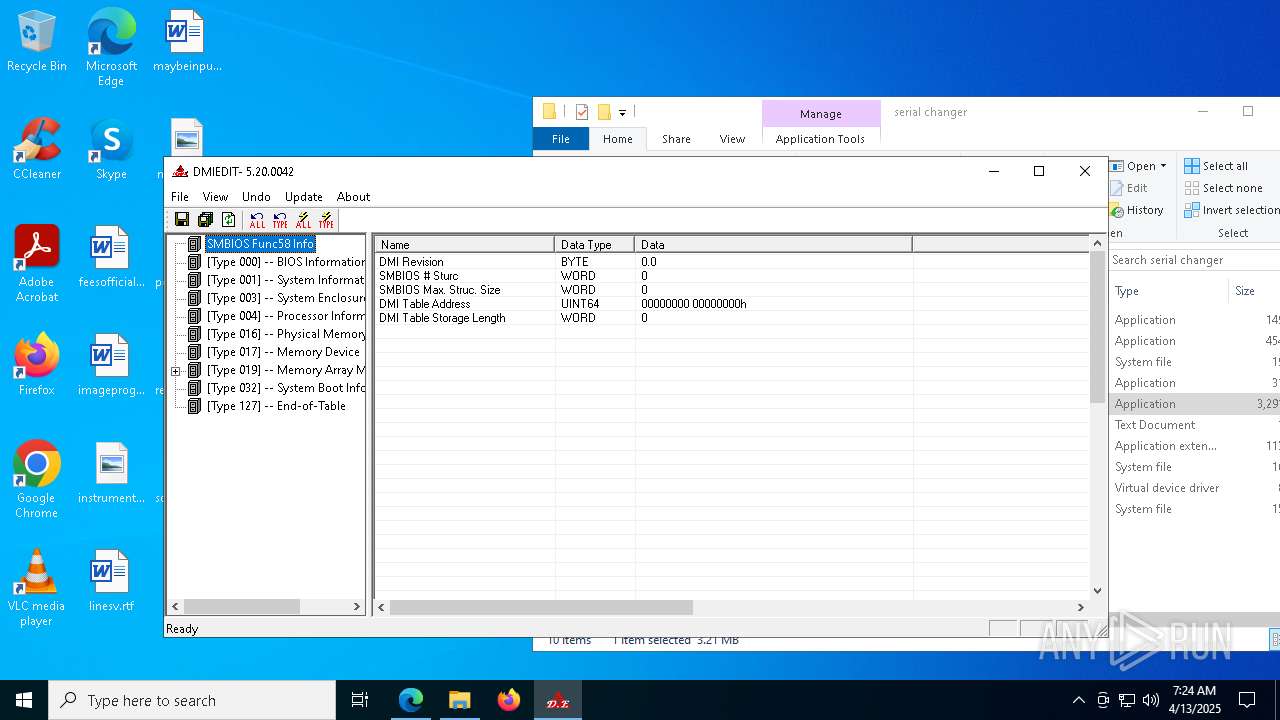
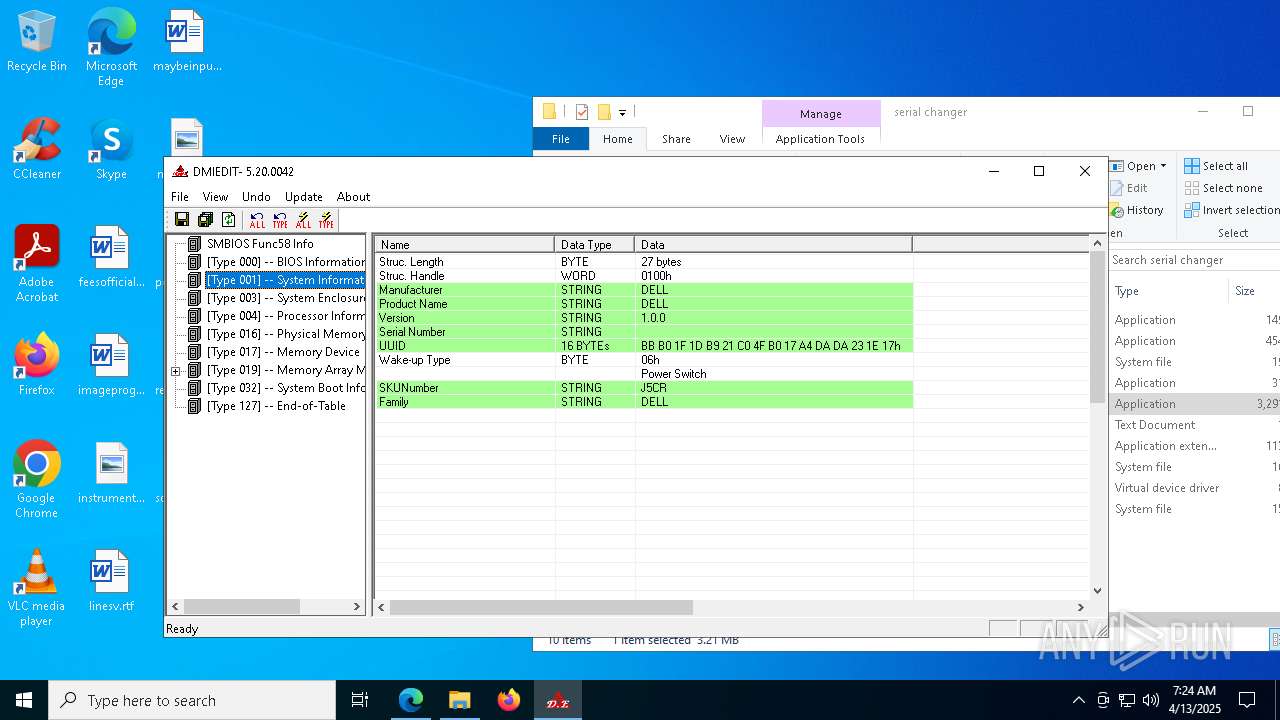
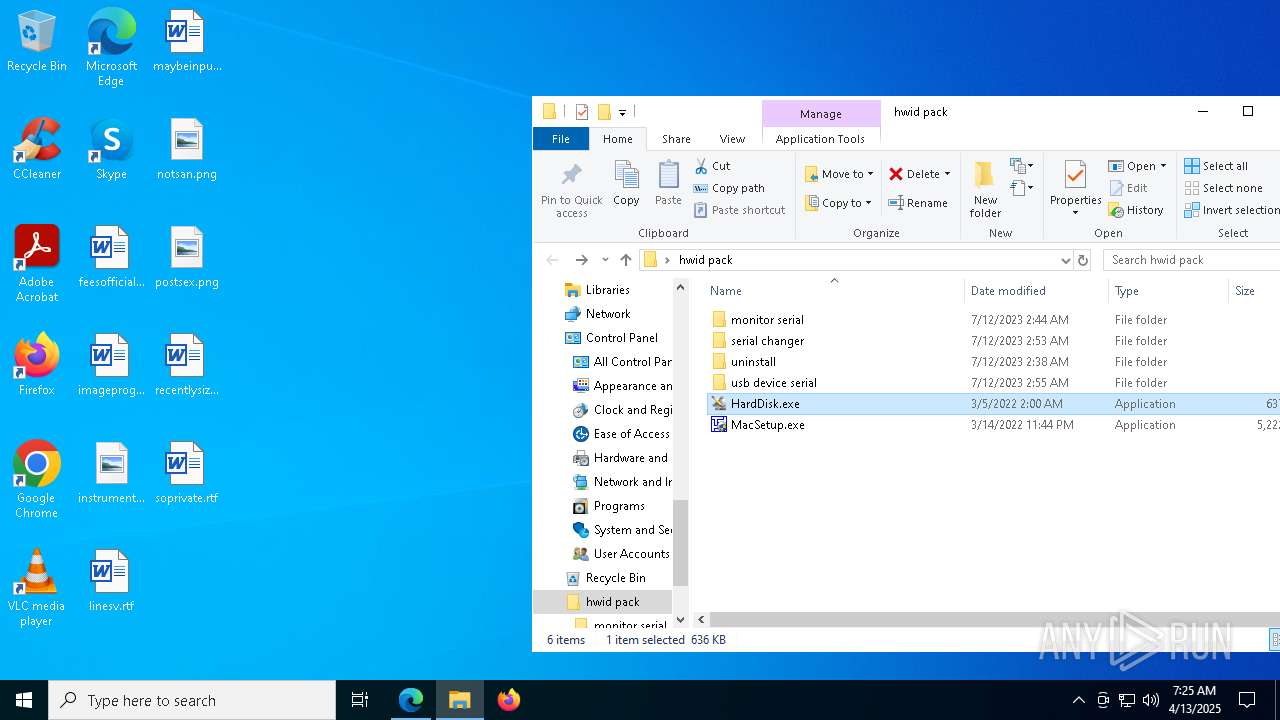
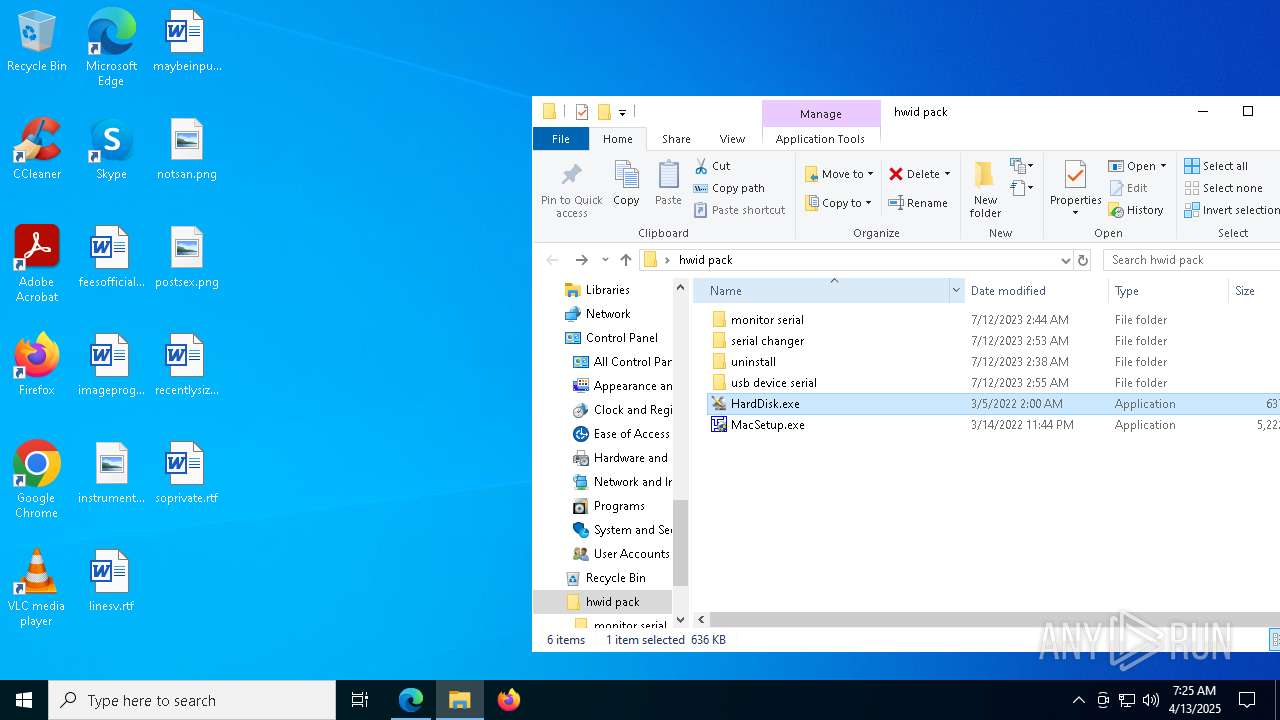
| 516 | "C:\Users\admin\Desktop\hwid pack\serial changer\DMIEDIT.EXE" | C:\Users\admin\Desktop\hwid pack\serial changer\DMIEDIT.EXE | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: DMI EDITOR/Windows MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 684 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7304 --field-trial-handle=2344,i,4280044006243932732,16471422888268518074,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 780 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --extension-process --renderer-sub-type=extension --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=48 --mojo-platform-channel-handle=3852 --field-trial-handle=2344,i,4280044006243932732,16471422888268518074,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 864 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3580 --field-trial-handle=2516,i,7509422746029035785,11471766331847810064,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 904 | "C:\Users\admin\Desktop\hwid pack\serial changer\DMIEDIT.EXE" | C:\Users\admin\Desktop\hwid pack\serial changer\DMIEDIT.EXE | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: DMI EDITOR/Windows MFC Application Exit code: 3221226540 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 1040 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=2068 --field-trial-handle=2344,i,4280044006243932732,16471422888268518074,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
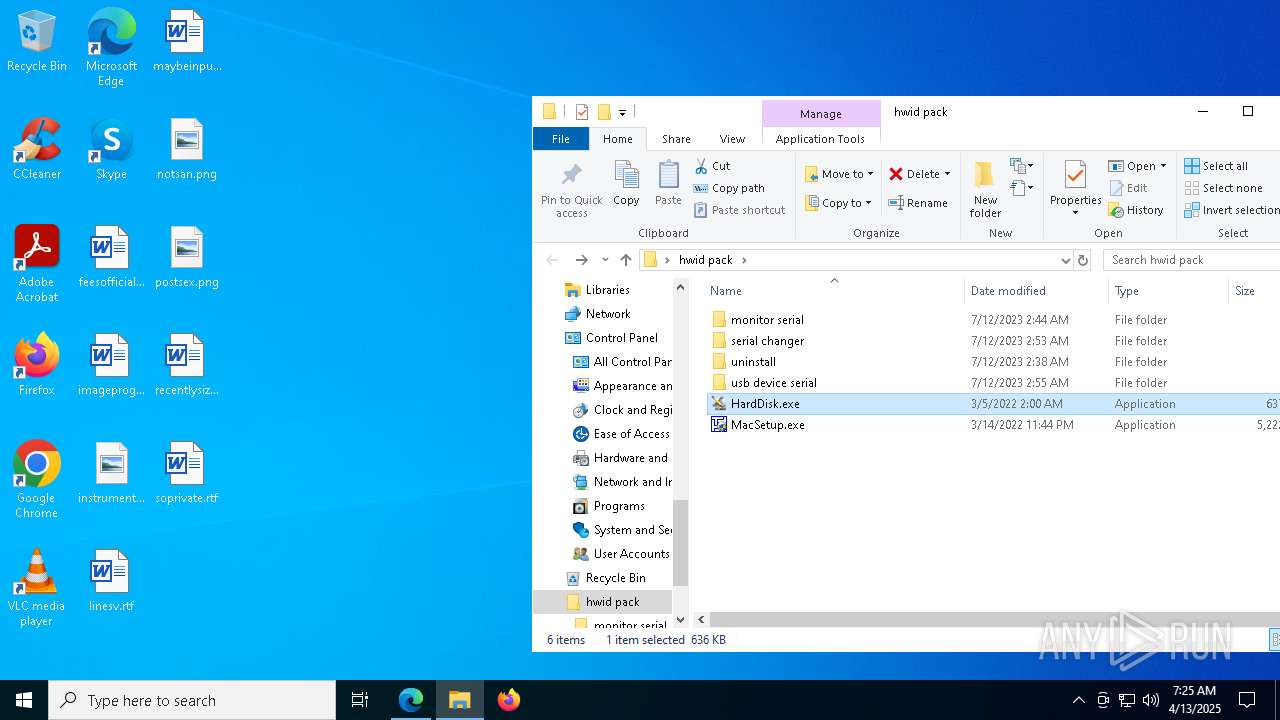
| 1244 | "C:\Users\admin\Desktop\hwid pack\HardDisk.exe" | C:\Users\admin\Desktop\hwid pack\HardDisk.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2092 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=51 --mojo-platform-channel-handle=7344 --field-trial-handle=2344,i,4280044006243932732,16471422888268518074,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2096 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2332 --field-trial-handle=2252,i,10242095243841477916,14947390882041280880,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
19 948
Read events
19 801
Write events
134
Delete events
13
Modification events
| (PID) Process: | (3896) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (3896) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (3896) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (3896) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\hwid pack.zip | |||
| (PID) Process: | (3896) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3896) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3896) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3896) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3896) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
| (PID) Process: | (3896) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
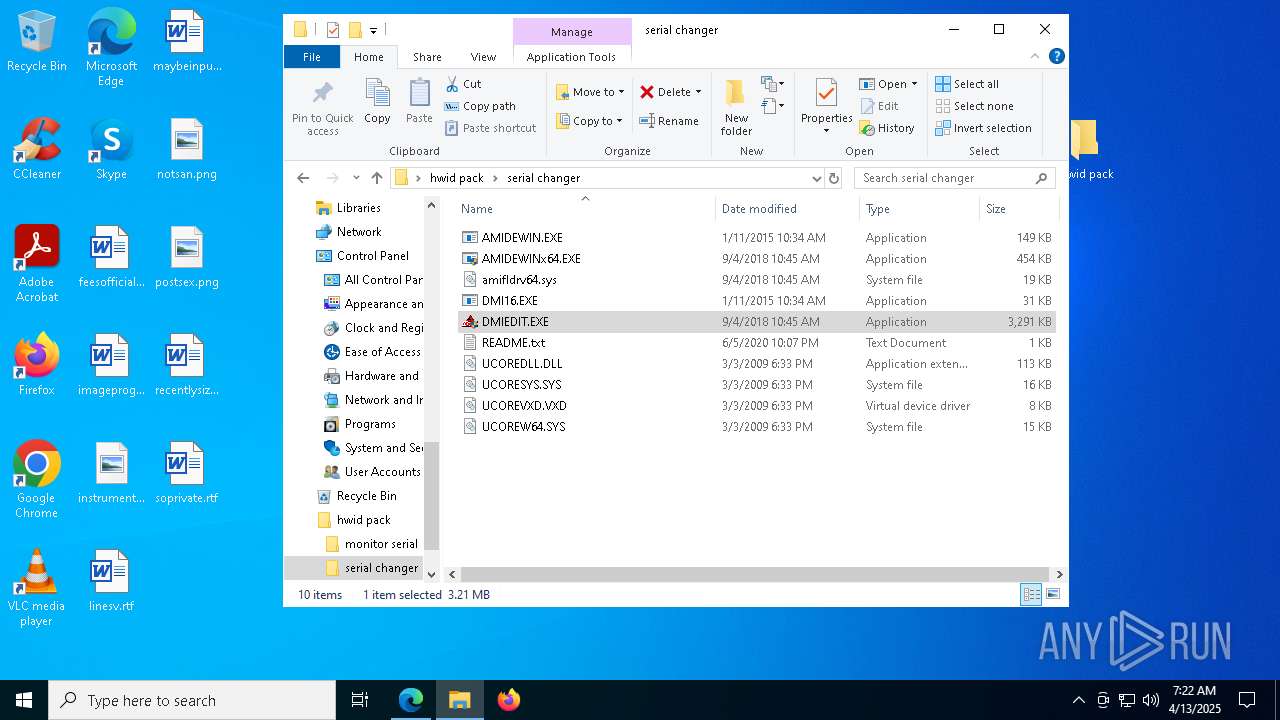
Executable files
41
Suspicious files
614
Text files
178
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3896 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3896.21751\hwid pack\monitor serial\CRU.exe | executable | |
MD5:0F69AF48C32613F73C6ACB87A7D18661 | SHA256:0351A943CA93558FF36F74C3F0C768DCEB724E833E282ABCF1BE5B2E71D5C67B | |||
| 3896 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3896.21751\hwid pack\HardDisk.exe | executable | |
MD5:C20E96D4E616CE333C19A1C15A1CC137 | SHA256:2C141C06F7DF57F11EF2C62F2A96093484A65DF47065B1A475C53784AF0E2664 | |||
| 3896 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3896.21751\hwid pack\monitor serial\reset-all.exe | executable | |
MD5:3D47586C62BF61DAC639D8CC1BF43EE7 | SHA256:70639C195430AFB92799D711ED784406BFDFD04C648D5F3E4D9873DA0063660B | |||
| 3896 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3896.21751\hwid pack\MacSetup.exe | executable | |
MD5:A7C8CF1D50EBE630A7D0C47686A0ABBF | SHA256:A453B3EA8D8133531FAD26B18701C694C324CC201E3069D07E99F0E100908C1A | |||
| 3896 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3896.21751\hwid pack\monitor serial\restart64.exe | executable | |
MD5:297AA19BADE534A791D053CA190B74AD | SHA256:5F779BB822AEDAF5BD11693CDF73F6C7C3342F37371A78C07C2ACA1E15DBFD00 | |||
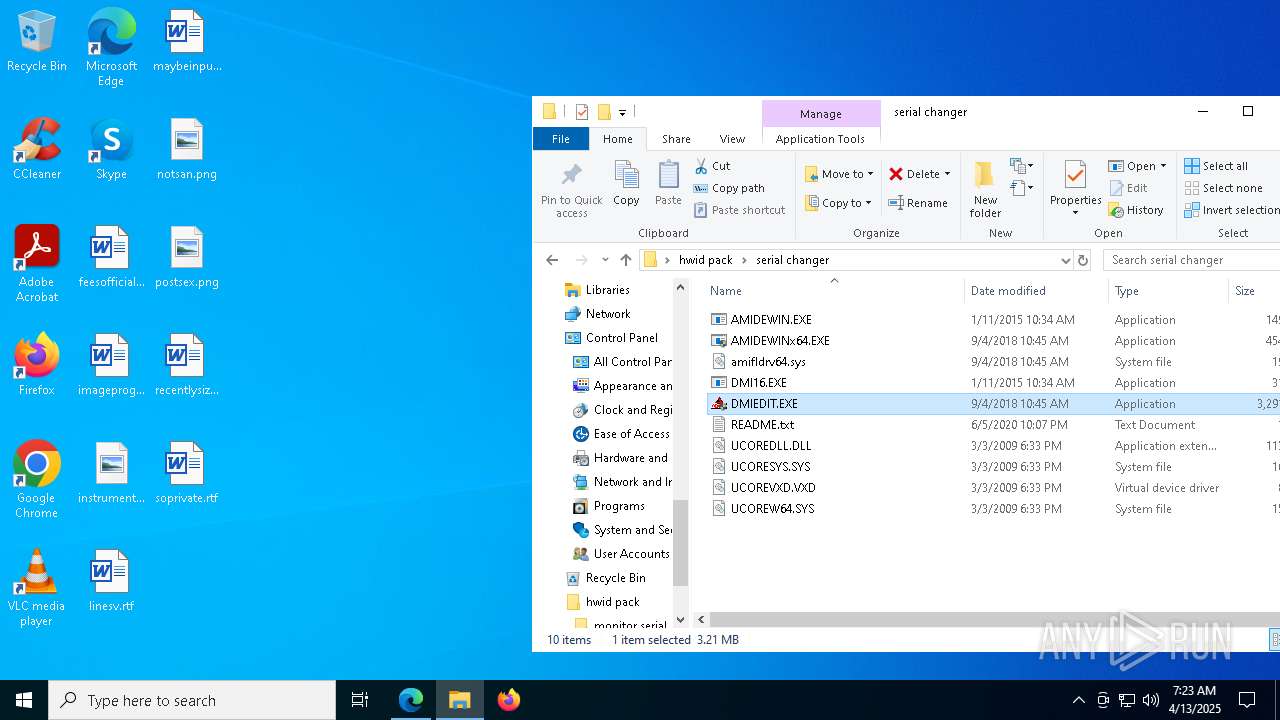
| 3896 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3896.21751\hwid pack\serial changer\UCOREW64.SYS | executable | |
MD5:A17C58C0582EE560C72F60764ED63224 | SHA256:A7C8F4FAF3CBB088CAC7753D81F8EC4C38CCB97CD9DA817741F49272E8D01200 | |||
| 3896 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3896.21751\hwid pack\monitor serial\Info.txt | text | |
MD5:DF95ACFBA3051D021EC94E47726BBD07 | SHA256:61350CE9D700627A156845DFEE77C44703280B16FD30BC1C216BFFC1CC82C0A1 | |||
| 3896 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3896.21751\hwid pack\serial changer\UCOREDLL.DLL | executable | |
MD5:8370F3114924ED6C53741DE7A253625A | SHA256:78A4D8E5E8C33793E5A2020325D3A49E92E4826167742E93179BDACBF167B409 | |||
| 3896 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3896.21751\hwid pack\uninstall\lang\albanian.ini | text | |
MD5:29D9BADF9A370C44D849F83D84370A24 | SHA256:7497147AFF5C43B779BAD6868C34930230BD1E93D6F725D37BCFB047DC15E7CA | |||
| 3896 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3896.21751\hwid pack\serial changer\amifldrv64.sys | executable | |
MD5:785045F8B25CD2E937DDC6B09DEBE01A | SHA256:37073E42FFA0322500F90CD7E3C8D02C4CDD695D31C77E81560ABEC20BFB68BA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
37
TCP/UDP connections
166
DNS requests
205
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.18:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7852 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7852 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7700 | svchost.exe | HEAD | 200 | 23.48.23.27:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1744954407&P2=404&P3=2&P4=ihF8AynDFD65nb5KS2MiqgTg4l7mkMuM9IiHTmSsMFboMr4p9ML4pnzYjHrLqAcmcukSSZee5dh5Pwive9f8IQ%3d%3d | unknown | — | — | whitelisted |
7700 | svchost.exe | GET | 206 | 23.48.23.27:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1744954407&P2=404&P3=2&P4=ihF8AynDFD65nb5KS2MiqgTg4l7mkMuM9IiHTmSsMFboMr4p9ML4pnzYjHrLqAcmcukSSZee5dh5Pwive9f8IQ%3d%3d | unknown | — | — | whitelisted |
7700 | svchost.exe | GET | 206 | 23.48.23.27:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1744954407&P2=404&P3=2&P4=ihF8AynDFD65nb5KS2MiqgTg4l7mkMuM9IiHTmSsMFboMr4p9ML4pnzYjHrLqAcmcukSSZee5dh5Pwive9f8IQ%3d%3d | unknown | — | — | whitelisted |
7700 | svchost.exe | GET | 206 | 23.48.23.27:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1744954407&P2=404&P3=2&P4=ihF8AynDFD65nb5KS2MiqgTg4l7mkMuM9IiHTmSsMFboMr4p9ML4pnzYjHrLqAcmcukSSZee5dh5Pwive9f8IQ%3d%3d | unknown | — | — | whitelisted |
7700 | svchost.exe | GET | 200 | 23.48.23.27:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/cf34b06a-2f53-4bd0-9d11-b58cf2e820a4?P1=1744954408&P2=404&P3=2&P4=cH9jjpVLI2KXHn7r5LYW5FvICg%2fyA%2bVPugYSqDjyvfNyLX3WcKdGr8oelAX1HIEJUHA6EvZ%2bsdOBt9lDx8r3WQ%3d%3d | unknown | — | — | whitelisted |
7700 | svchost.exe | GET | 206 | 23.48.23.27:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1744954407&P2=404&P3=2&P4=ihF8AynDFD65nb5KS2MiqgTg4l7mkMuM9IiHTmSsMFboMr4p9ML4pnzYjHrLqAcmcukSSZee5dh5Pwive9f8IQ%3d%3d | unknown | — | — | whitelisted |
7700 | svchost.exe | HEAD | 200 | 23.48.23.27:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/cf34b06a-2f53-4bd0-9d11-b58cf2e820a4?P1=1744954408&P2=404&P3=2&P4=cH9jjpVLI2KXHn7r5LYW5FvICg%2fyA%2bVPugYSqDjyvfNyLX3WcKdGr8oelAX1HIEJUHA6EvZ%2bsdOBt9lDx8r3WQ%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.18:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6512 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6080 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6512 | msedge.exe | 141.193.213.21:443 | www.ami.com | — | — | whitelisted |
6512 | msedge.exe | 142.250.184.195:443 | fonts.gstatic.com | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
www.ami.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |