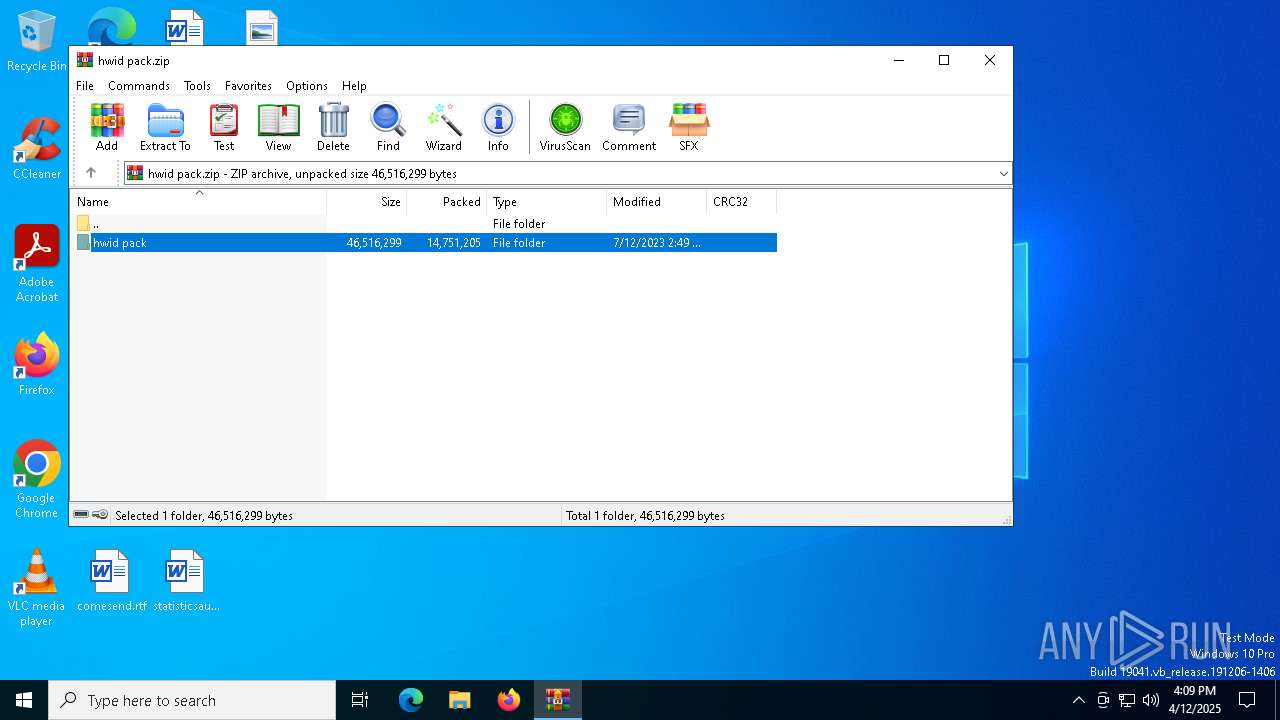
| File name: | hwid pack.zip |
| Full analysis: | https://app.any.run/tasks/38fdaefa-d8f7-4e5c-a69f-aa77e7111e71 |
| Verdict: | Malicious activity |
| Analysis date: | April 12, 2025, 16:09:11 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | 734C14A94F1778E506606804D3566594 |
| SHA1: | 8CBD6A9C512EDAAB288A0FD24C7C2D7D71C3999D |
| SHA256: | 41CAEB1DAB6AB9DA4571B88CD0A0A2B3A21CE305909358E538A04F988D4A139F |
| SSDEEP: | 196608:ELlI5+lEzBGc3CqWeo/X/Mbw4+OPexK4Ux:GNYBG1DXQwXBBq |
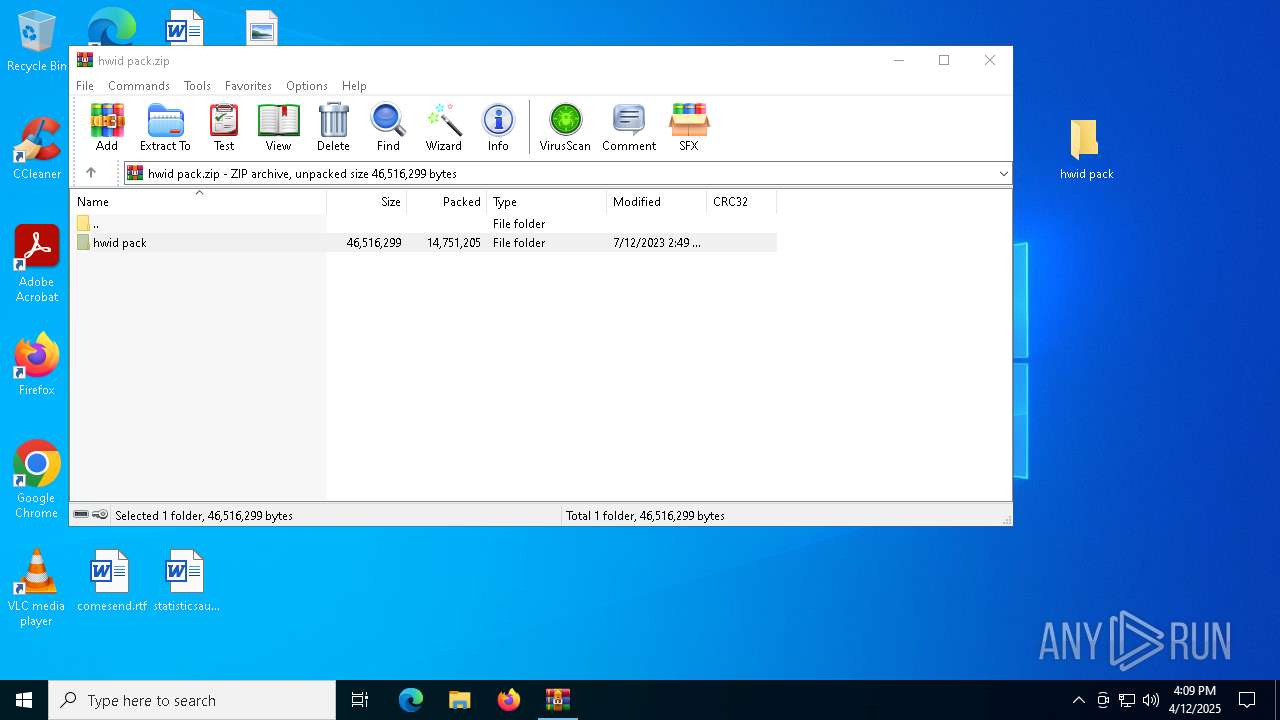
MALICIOUS
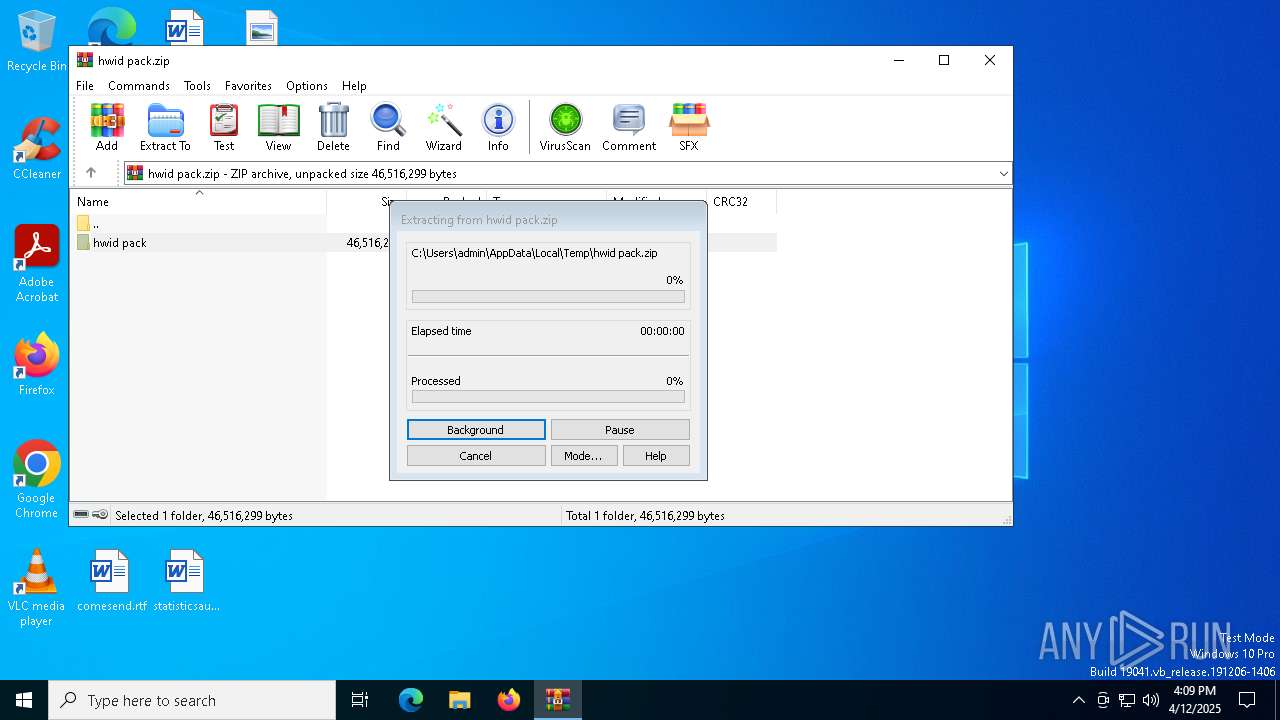
Generic archive extractor
- WinRAR.exe (PID: 7692)
Vulnerable driver has been detected
- WinRAR.exe (PID: 7692)
SUSPICIOUS
Drops a system driver (possible attempt to evade defenses)
- WinRAR.exe (PID: 7692)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7692)
The sample compiled with english language support
- WinRAR.exe (PID: 7692)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2023:07:11 19:49:08 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | hwid pack/ |
Total processes
128
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 7692 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\hwid pack.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
Total events
1 626
Read events
1 618
Write events
8
Delete events
0
Modification events
| (PID) Process: | (7692) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7692) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7692) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7692) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\hwid pack.zip | |||
| (PID) Process: | (7692) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7692) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7692) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7692) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
19
Suspicious files
6
Text files
51
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7692 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7692.48101\hwid pack\MacSetup.exe | executable | |
MD5:A7C8CF1D50EBE630A7D0C47686A0ABBF | SHA256:A453B3EA8D8133531FAD26B18701C694C324CC201E3069D07E99F0E100908C1A | |||
| 7692 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7692.48101\hwid pack\HardDisk.exe | executable | |
MD5:C20E96D4E616CE333C19A1C15A1CC137 | SHA256:2C141C06F7DF57F11EF2C62F2A96093484A65DF47065B1A475C53784AF0E2664 | |||
| 7692 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7692.48101\hwid pack\serial changer\AMIDEWIN.EXE | executable | |
MD5:182EC3A59BD847FB1BC3E12A41D48FA6 | SHA256:948DBD2BC128F8DC08267E110020FEE3FF5DE17CF4AAEF89372DE29623AF96FA | |||
| 7692 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7692.48101\hwid pack\serial changer\UCOREW64.SYS | executable | |
MD5:A17C58C0582EE560C72F60764ED63224 | SHA256:A7C8F4FAF3CBB088CAC7753D81F8EC4C38CCB97CD9DA817741F49272E8D01200 | |||
| 7692 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7692.48101\hwid pack\serial changer\amifldrv64.sys | executable | |
MD5:785045F8B25CD2E937DDC6B09DEBE01A | SHA256:37073E42FFA0322500F90CD7E3C8D02C4CDD695D31C77E81560ABEC20BFB68BA | |||
| 7692 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7692.48101\hwid pack\serial changer\UCOREVXD.VXD | executable | |
MD5:211B3CDA6EE0F7A8C86FFC2E5177020D | SHA256:0C30287DEB78A25A4037FC3201062DDF880B06EA436550D83F47FB7FCAC7DCF4 | |||
| 7692 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7692.48101\hwid pack\uninstall\lang\arabic.ini | text | |
MD5:6371CB8DF44E5227A0038E79EA7719E9 | SHA256:E434E5A76D2937EE9D05281454A51741C886AF67D04601D3B7145FE0134E75BF | |||
| 7692 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7692.48101\hwid pack\monitor serial\CRU.exe | executable | |
MD5:0F69AF48C32613F73C6ACB87A7D18661 | SHA256:0351A943CA93558FF36F74C3F0C768DCEB724E833E282ABCF1BE5B2E71D5C67B | |||
| 7692 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7692.48101\hwid pack\monitor serial\reset-all.exe | executable | |
MD5:3D47586C62BF61DAC639D8CC1BF43EE7 | SHA256:70639C195430AFB92799D711ED784406BFDFD04C648D5F3E4D9873DA0063660B | |||
| 7692 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7692.48101\hwid pack\monitor serial\Info.txt | text | |
MD5:DF95ACFBA3051D021EC94E47726BBD07 | SHA256:61350CE9D700627A156845DFEE77C44703280B16FD30BC1C216BFFC1CC82C0A1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
17
DNS requests
11
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.164.32:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8172 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8172 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.16.164.32:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6544 | svchost.exe | 40.126.32.68:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
8172 | SIHClient.exe | 172.202.163.200:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | GB | whitelisted |
8172 | SIHClient.exe | 23.52.120.96:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |