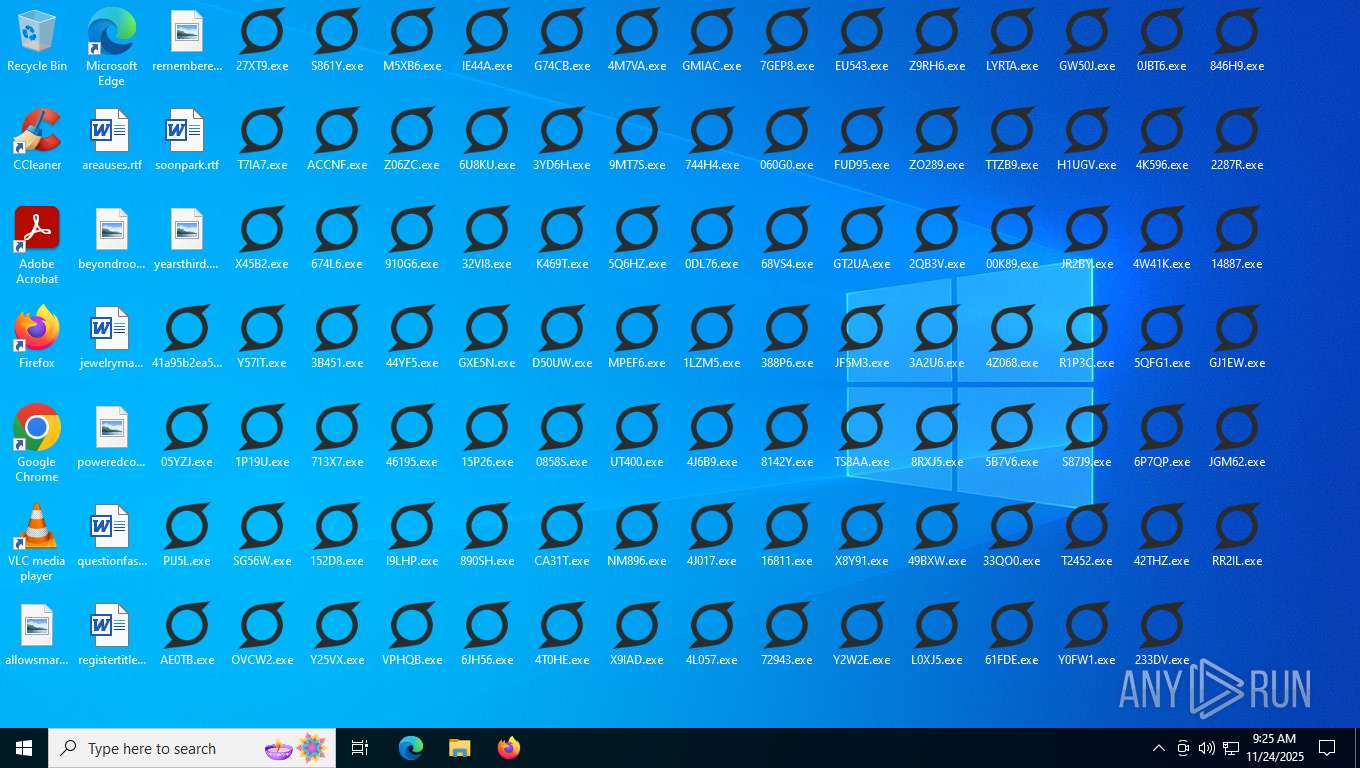
| File name: | 41a95b2ea5f1469a0b71cdf6cf7d3a4f922a50d0afe78479b4470c9b5ac1dd71.exe |
| Full analysis: | https://app.any.run/tasks/5ebe1406-6f45-44ec-bfab-b343b529ba93 |
| Verdict: | Malicious activity |
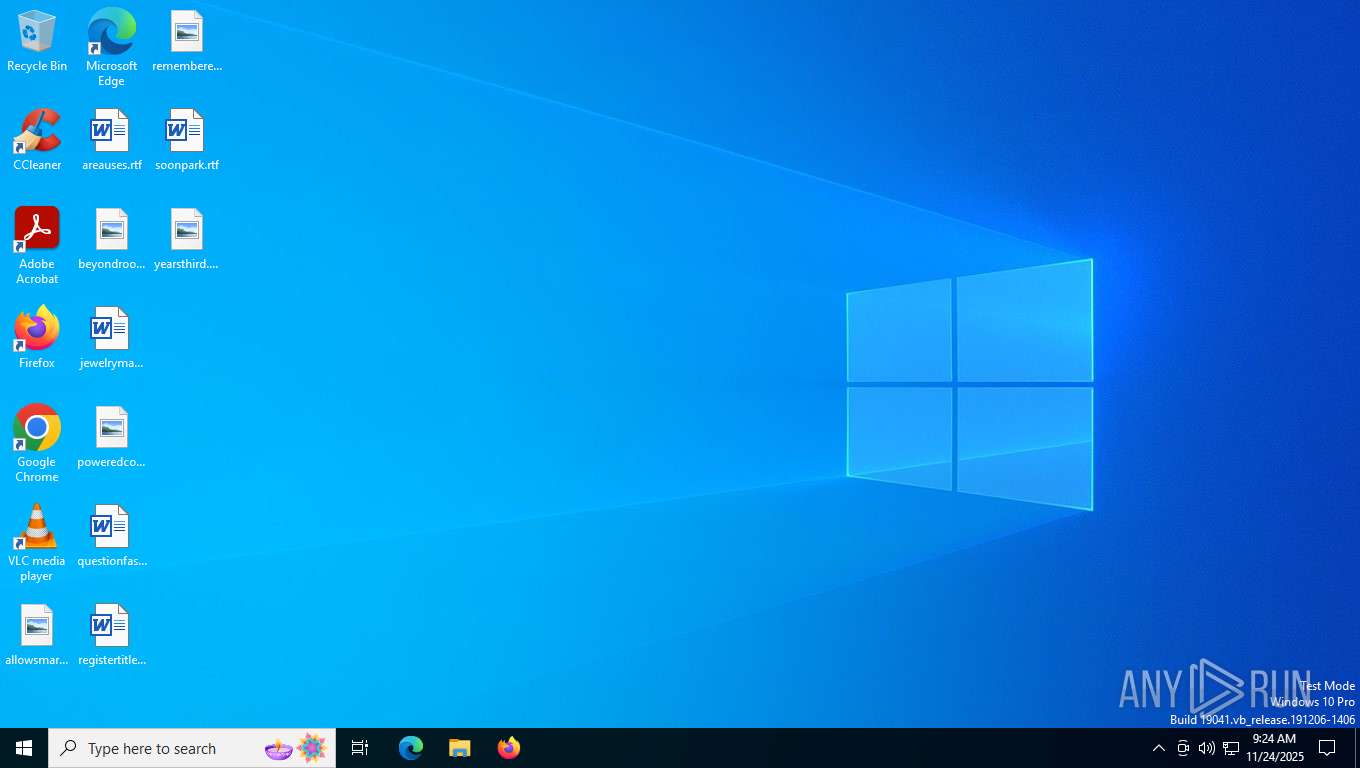
| Analysis date: | November 24, 2025, 09:24:39 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed, 5 sections |
| MD5: | D3ACCF7C9605A7E2111A59A4DA92B4EF |
| SHA1: | C4750D05E83432029FFDBF640B3B0F4605ADE661 |
| SHA256: | 41A95B2EA5F1469A0B71CDF6CF7D3A4F922A50D0AFE78479B4470C9B5AC1DD71 |
| SSDEEP: | 24576:MUKstWIP3Ymyne8H4wSeWgTTxZsasAY5S8zoPBNoEFZ9bpv:MUKstWIP3Ymyne8HJSeWgTTLsDAY48z6 |
MALICIOUS
No malicious indicators.SUSPICIOUS
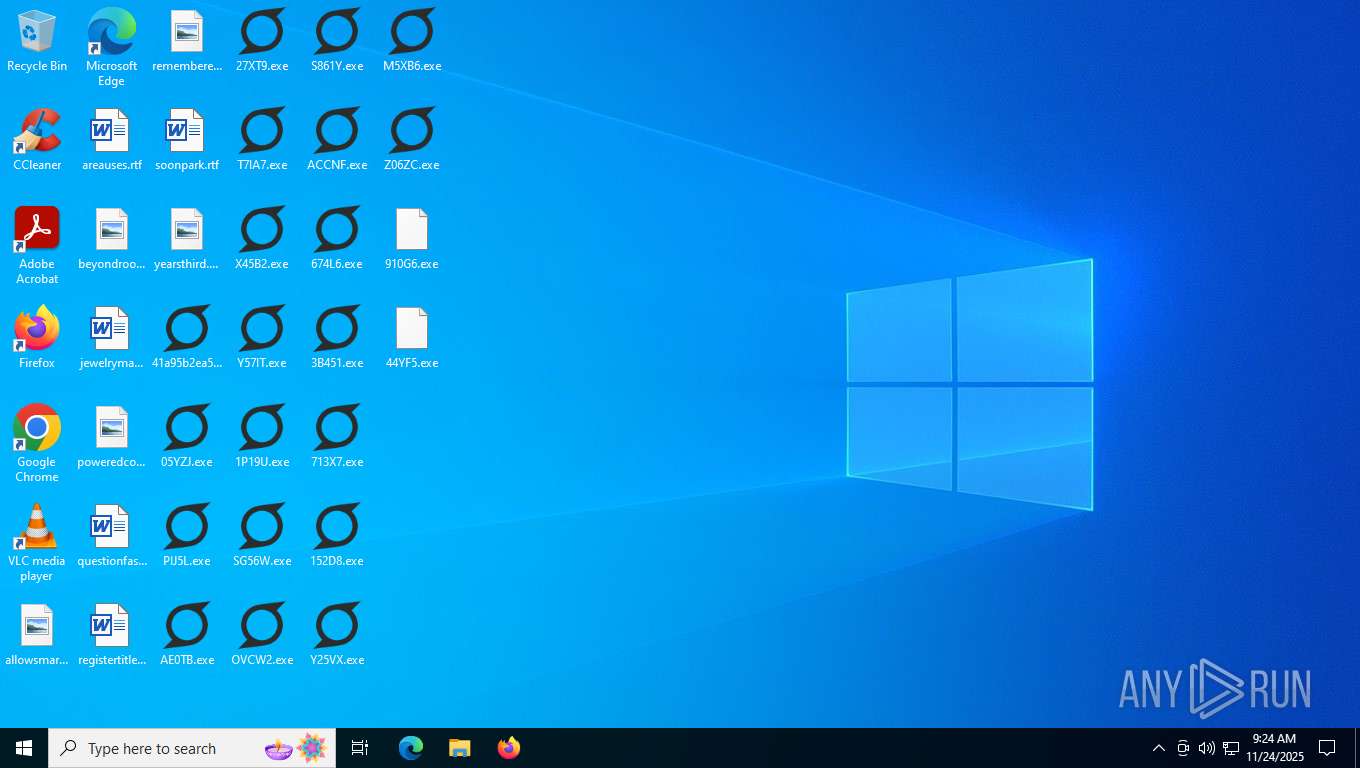
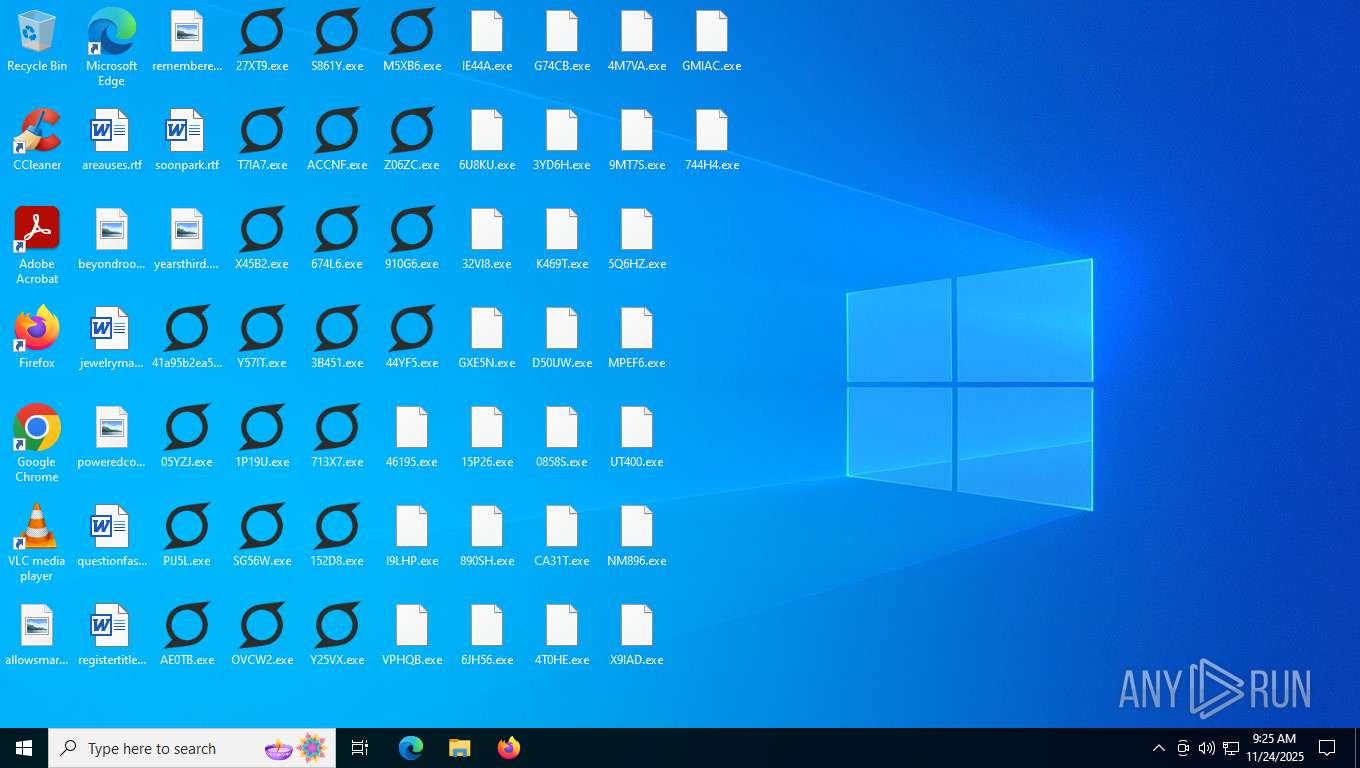
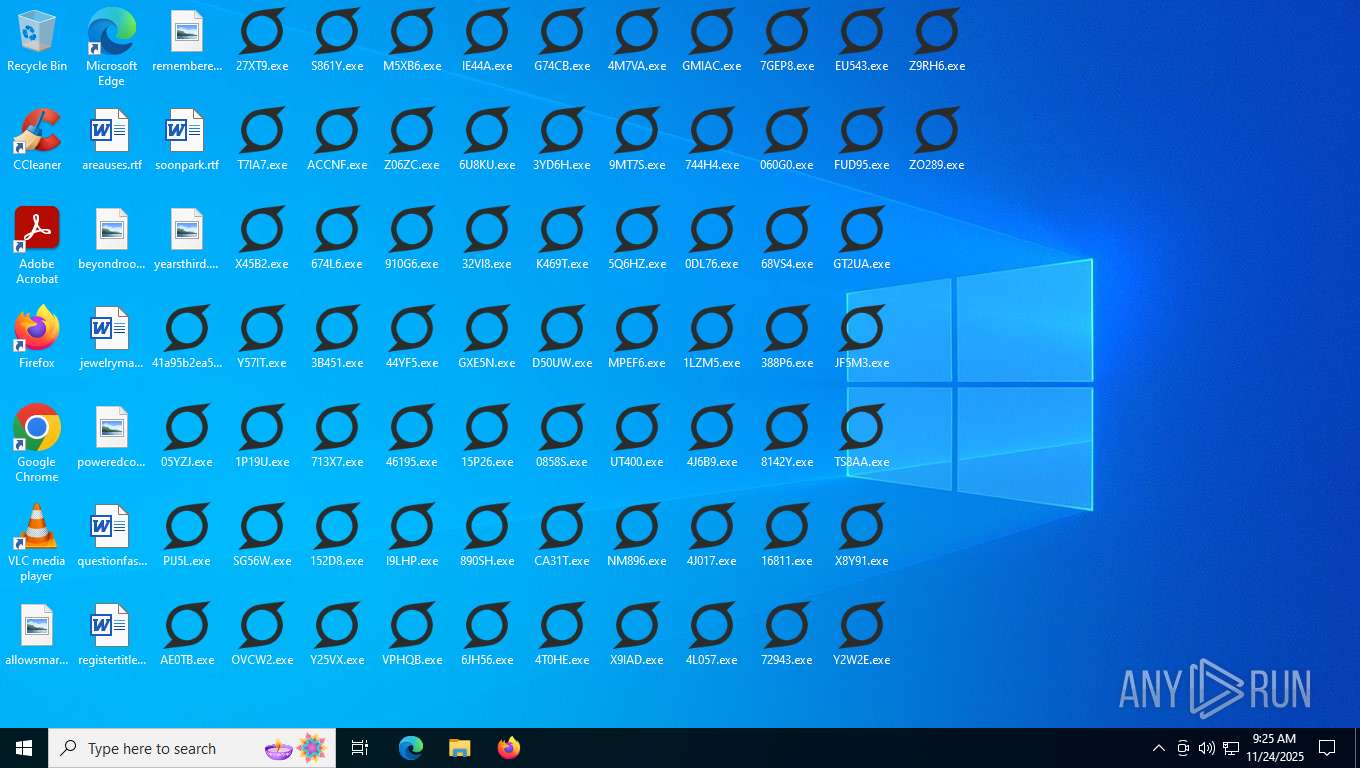
Executable content was dropped or overwritten
- 05YZJ.exe (PID: 7460)
- 41a95b2ea5f1469a0b71cdf6cf7d3a4f922a50d0afe78479b4470c9b5ac1dd71.exe (PID: 7412)
- PIJ5L.exe (PID: 7512)
- AE0TB.exe (PID: 7564)
- 27XT9.exe (PID: 7620)
- T7IA7.exe (PID: 7688)
- X45B2.exe (PID: 7764)
- Y57IT.exe (PID: 7888)
- 1P19U.exe (PID: 7976)
- SG56W.exe (PID: 8040)
- OVCW2.exe (PID: 8108)
- S861Y.exe (PID: 8160)
- 674L6.exe (PID: 1924)
- 3B451.exe (PID: 7436)
- ACCNF.exe (PID: 4104)
- 713X7.exe (PID: 7528)
- 152D8.exe (PID: 7580)
- Z06ZC.exe (PID: 7872)
- Y25VX.exe (PID: 7632)
- M5XB6.exe (PID: 7788)
- 44YF5.exe (PID: 7824)
- 46195.exe (PID: 8000)
- 910G6.exe (PID: 2344)
- I9LHP.exe (PID: 7976)
- VPHQB.exe (PID: 8040)
- IE44A.exe (PID: 8112)
- 6U8KU.exe (PID: 3236)
- 32VI8.exe (PID: 7240)
- 15P26.exe (PID: 4900)
- 890SH.exe (PID: 4220)
- GXE5N.exe (PID: 7492)
- G74CB.exe (PID: 7528)
- 3YD6H.exe (PID: 3400)
- K469T.exe (PID: 7640)
- 6JH56.exe (PID: 7436)
- D50UW.exe (PID: 7580)
- 0858S.exe (PID: 7740)
- CA31T.exe (PID: 7696)
- 4T0HE.exe (PID: 7476)
- 4M7VA.exe (PID: 7472)
- 9MT7S.exe (PID: 6356)
- 5Q6HZ.exe (PID: 4916)
- MPEF6.exe (PID: 7812)
- UT400.exe (PID: 892)
- NM896.exe (PID: 7796)
- X9IAD.exe (PID: 8020)
- GMIAC.exe (PID: 8076)
- 744H4.exe (PID: 8144)
- 16811.exe (PID: 2104)
- ZO289.exe (PID: 5868)
- 8142Y.exe (PID: 2740)
- TS8AA.exe (PID: 5244)
- Y2W2E.exe (PID: 5408)
- 7GEP8.exe (PID: 7460)
- 1LZM5.exe (PID: 5948)
- EU543.exe (PID: 7588)
- 4J6B9.exe (PID: 7608)
- 4L057.exe (PID: 1252)
- GT2UA.exe (PID: 4452)
- 68VS4.exe (PID: 7676)
- JF5M3.exe (PID: 3364)
- 0DL76.exe (PID: 7852)
- X8Y91.exe (PID: 5696)
- 388P6.exe (PID: 4592)
- 4J017.exe (PID: 3680)
- 060G0.exe (PID: 7872)
- Z9RH6.exe (PID: 8084)
- 49BXW.exe (PID: 8116)
- FUD95.exe (PID: 7960)
- 2QB3V.exe (PID: 8172)
- 3A2U6.exe (PID: 4064)
- 8RXJ5.exe (PID: 6728)
- LYRTA.exe (PID: 7252)
- TTZB9.exe (PID: 7480)
- L0XJ5.exe (PID: 6880)
- 33QO0.exe (PID: 7568)
- S87J9.exe (PID: 6260)
- 00K89.exe (PID: 7520)
- T2452.exe (PID: 3468)
- R1P3C.exe (PID: 7616)
- GW50J.exe (PID: 1276)
- JR2BY.exe (PID: 2408)
- 5B7V6.exe (PID: 7868)
- H1UGV.exe (PID: 7788)
- Y0FW1.exe (PID: 5656)
- 42THZ.exe (PID: 7992)
- 61FDE.exe (PID: 6452)
- RR2IL.exe (PID: 3332)
- 846H9.exe (PID: 8136)
- 5QFG1.exe (PID: 8040)
- 0JBT6.exe (PID: 4264)
- 2287R.exe (PID: 7796)
- 233DV.exe (PID: 4064)
- 4K596.exe (PID: 7612)
- 14887.exe (PID: 5712)
- GJ1EW.exe (PID: 7560)
- FDN4D.exe (PID: 7576)
- H4AMG.exe (PID: 1252)
- 4AL80.exe (PID: 7624)
- 8VT67.exe (PID: 7676)
- 135GH.exe (PID: 3100)
- 3PL9G.exe (PID: 5696)
- 9GGQ0.exe (PID: 7924)
- 44W55.exe (PID: 5224)
- 7N537.exe (PID: 3460)
- QQ9QW.exe (PID: 7916)
- 33C3V.exe (PID: 1140)
- 704N6.exe (PID: 8020)
- 29N30.exe (PID: 8092)
- CJ2BA.exe (PID: 6376)
- 9607X.exe (PID: 6776)
- 6N466.exe (PID: 7796)
- 936IC.exe (PID: 476)
- Y8FJ3.exe (PID: 4900)
- 6WNR9.exe (PID: 6676)
- RY1B7.exe (PID: 2852)
- I7J3C.exe (PID: 7460)
- HVF03.exe (PID: 4668)
- 45VQG.exe (PID: 7556)
- K4CPT.exe (PID: 5580)
- HA572.exe (PID: 5268)
- S9G16.exe (PID: 3100)
- I0C6M.exe (PID: 7708)
- W9FNS.exe (PID: 7768)
- 2WJ83.exe (PID: 7692)
- N0944.exe (PID: 5368)
- 384M8.exe (PID: 7852)
- LC3NX.exe (PID: 7840)
- W1UXJ.exe (PID: 7864)
- A1OW3.exe (PID: 2764)
- 1Z9YK.exe (PID: 8052)
- TLJU6.exe (PID: 5288)
- HA7IB.exe (PID: 5772)
- 1X968.exe (PID: 8180)
- 697GY.exe (PID: 5660)
- J159E.exe (PID: 8024)
- 7W936.exe (PID: 1948)
- REBR8.exe (PID: 7276)
- 2BS07.exe (PID: 2104)
- VJALT.exe (PID: 2944)
- F3AL2.exe (PID: 7536)
- 7ML00.exe (PID: 7436)
- 4N883.exe (PID: 5504)
- WT72A.exe (PID: 6260)
- 93465.exe (PID: 5040)
- IM8L2.exe (PID: 7700)
- 3O348.exe (PID: 7448)
- 8J424.exe (PID: 5704)
- 161WC.exe (PID: 7624)
- ZYG4A.exe (PID: 7676)
- M150Y.exe (PID: 7856)
- 15OE9.exe (PID: 7996)
- 5008Z.exe (PID: 5696)
- 72223.exe (PID: 4400)
- 1M300.exe (PID: 7352)
- 21JZY.exe (PID: 8128)
- 76I5W.exe (PID: 8044)
- JC7BE.exe (PID: 7976)
- SMWI4.exe (PID: 476)
- P37R8.exe (PID: 6776)
- RVL17.exe (PID: 6376)
- 1000T.exe (PID: 3944)
- VPOBX.exe (PID: 7664)
- 34C0T.exe (PID: 7484)
- USS5N.exe (PID: 7796)
- Z7QVP.exe (PID: 5244)
- GBJ33.exe (PID: 7516)
- QZ3E8.exe (PID: 8104)
- 3P7L5.exe (PID: 4452)
- 4T3G5.exe (PID: 4244)
- U758A.exe (PID: 7708)
- UB1D3.exe (PID: 7628)
- 3MQHV.exe (PID: 4668)
- P1ZQ3.exe (PID: 7784)
- 177WJ.exe (PID: 5580)
- DI9J0.exe (PID: 6164)
- SIN7D.exe (PID: 7816)
- 7D5SU.exe (PID: 7892)
- G587W.exe (PID: 7944)
- 7CQ7F.exe (PID: 2344)
- S87C9.exe (PID: 7348)
- 4SIOD.exe (PID: 7952)
- 70NQ3.exe (PID: 3076)
- 60Y4Y.exe (PID: 5376)
- 2AZV3.exe (PID: 2036)
- 1V809.exe (PID: 3984)
- 72MNC.exe (PID: 1576)
- 1S9LN.exe (PID: 4104)
- SAI99.exe (PID: 2880)
- YV5R1.exe (PID: 6676)
- N10GX.exe (PID: 7556)
- 13I69.exe (PID: 5408)
- GRW60.exe (PID: 7724)
- NPB62.exe (PID: 3956)
- 95XPK.exe (PID: 7572)
- 8UHII.exe (PID: 5268)
- D6350.exe (PID: 7836)
- 22032.exe (PID: 7748)
- PF509.exe (PID: 1136)
- 9N3CG.exe (PID: 7848)
- 9H1Q1.exe (PID: 3996)
- 4WQQE.exe (PID: 7788)
- 99141.exe (PID: 6264)
- WAJIF.exe (PID: 7820)
- 3VSS3.exe (PID: 2344)
- BLD7F.exe (PID: 3460)
- V9519.exe (PID: 7888)
- 1TL17.exe (PID: 8068)
- D3WN4.exe (PID: 8048)
- 35L5E.exe (PID: 4280)
- GOV5K.exe (PID: 3236)
- 94R76.exe (PID: 8152)
- C3HC9.exe (PID: 2312)
- I6B09.exe (PID: 6940)
- D96QW.exe (PID: 1080)
- KIXH4.exe (PID: 2760)
- 9PAFD.exe (PID: 7596)
- 9RM87.exe (PID: 7332)
- S07XZ.exe (PID: 1688)
- 460IW.exe (PID: 7380)
- 8G99B.exe (PID: 5948)
- 607S5.exe (PID: 7096)
- G3342.exe (PID: 2008)
- DA5TX.exe (PID: 7640)
- L0C14.exe (PID: 5040)
- BPCB1.exe (PID: 3996)
- JL3JW.exe (PID: 7880)
- 1T831.exe (PID: 1836)
- M3414.exe (PID: 7788)
- 5475W.exe (PID: 6252)
- WN8FW.exe (PID: 3680)
- J0Z4I.exe (PID: 7888)
- TAZN8.exe (PID: 8008)
- W9U53.exe (PID: 4280)
- 6Y84Z.exe (PID: 8068)
- 05NP7.exe (PID: 800)
- 0FKP5.exe (PID: 1384)
- YUIXG.exe (PID: 8048)
- FN8F2.exe (PID: 7492)
- 066PD.exe (PID: 4720)
- 505OB.exe (PID: 6504)
- 2541J.exe (PID: 7328)
- 9L57J.exe (PID: 1952)
- O1HB2.exe (PID: 7560)
- 2XSO0.exe (PID: 3568)
- 4E61L.exe (PID: 2900)
- 8SZ85.exe (PID: 7744)
- QI603.exe (PID: 7688)
- I59UD.exe (PID: 7784)
- 4TKS5.exe (PID: 5452)
- 022B9.exe (PID: 4884)
- DBR9D.exe (PID: 1284)
- C896I.exe (PID: 1520)
- B80HR.exe (PID: 7912)
- 2A5F5.exe (PID: 5704)
- 9E6N9.exe (PID: 7712)
- 07XOW.exe (PID: 4360)
- 0037G.exe (PID: 7824)
- MRL2Z.exe (PID: 7988)
- 9Y2AJ.exe (PID: 6964)
- 1746F.exe (PID: 7916)
- Y0JG0.exe (PID: 4784)
- 1B2N3.exe (PID: 8176)
- APF67.exe (PID: 8112)
- 1ZTZW.exe (PID: 4760)
- 89YII.exe (PID: 5956)
- 3U9HZ.exe (PID: 5500)
- H00P7.exe (PID: 7540)
- CX629.exe (PID: 1148)
- 0T70H.exe (PID: 2100)
- QGR2G.exe (PID: 1264)
- 31Z24.exe (PID: 7660)
- XQWA4.exe (PID: 7588)
- 90108.exe (PID: 3400)
- OY28S.exe (PID: 7580)
- 098VM.exe (PID: 2316)
- 1E928.exe (PID: 7736)
- QU316.exe (PID: 7864)
- 2DC97.exe (PID: 4452)
- VR3XP.exe (PID: 4916)
- 1T9QO.exe (PID: 7868)
- 4T6D5.exe (PID: 5392)
- 97R42.exe (PID: 7924)
- T8GF2.exe (PID: 6156)
- EXY1D.exe (PID: 5704)
- 54Y4E.exe (PID: 1252)
- F3JY5.exe (PID: 5584)
- YQU4Y.exe (PID: 7348)
- QYC88.exe (PID: 8144)
- 7UKT5.exe (PID: 8120)
- I1U0X.exe (PID: 8008)
- ZI8HO.exe (PID: 1540)
- 73A7I.exe (PID: 8176)
- T0YZ6.exe (PID: 2636)
- 5VOT0.exe (PID: 7796)
- B90C3.exe (PID: 5956)
- H2GM5.exe (PID: 8024)
- I4R98.exe (PID: 7664)
- 8M27C.exe (PID: 1148)
- M81O1.exe (PID: 7560)
- CF2W8.exe (PID: 7436)
- 567H4.exe (PID: 7100)
- 081VV.exe (PID: 7660)
- 4UNDC.exe (PID: 2580)
- N7886.exe (PID: 1248)
- L1V69.exe (PID: 7756)
- 90GQJ.exe (PID: 7616)
- 4BYIC.exe (PID: 7632)
- 58NY3.exe (PID: 7688)
- OSV3P.exe (PID: 7908)
- W5N73.exe (PID: 7784)
- 3CBUL.exe (PID: 3392)
- QS4B1.exe (PID: 5540)
- 6886X.exe (PID: 6164)
- S040W.exe (PID: 3148)
- C1304.exe (PID: 6740)
- W0VS1.exe (PID: 7992)
- 5W8TX.exe (PID: 7888)
- O870X.exe (PID: 4384)
- NV87C.exe (PID: 8128)
- E9437.exe (PID: 8124)
- 1GPF5.exe (PID: 5508)
- 1HMXM.exe (PID: 6728)
- 7L8F3.exe (PID: 7440)
- 623X2.exe (PID: 2164)
- 9FF6V.exe (PID: 272)
- X5X86.exe (PID: 2104)
- X11ZD.exe (PID: 7328)
- O29W1.exe (PID: 1952)
- 2EI6W.exe (PID: 7332)
- C5O6S.exe (PID: 3568)
- H83M9.exe (PID: 2512)
- F0FZI.exe (PID: 7436)
- 3ZQ3K.exe (PID: 2716)
- 3FC69.exe (PID: 7632)
- 04C2B.exe (PID: 7616)
- IH88U.exe (PID: 7688)
- 71H49.exe (PID: 1128)
- 65GW2.exe (PID: 1248)
- IXJU5.exe (PID: 7756)
- 385D5.exe (PID: 7908)
- 077UU.exe (PID: 3392)
- N71JV.exe (PID: 6164)
- 5056Z.exe (PID: 5540)
- YEZFT.exe (PID: 5356)
- 3A1N4.exe (PID: 6740)
- 284M4.exe (PID: 3156)
- 6I57G.exe (PID: 2344)
- Z41A7.exe (PID: 8008)
- J715A.exe (PID: 7348)
- 1B5H5.exe (PID: 6444)
- L38GI.exe (PID: 8116)
- 7PB1L.exe (PID: 2580)
- 8611J.exe (PID: 2724)
- L67FH.exe (PID: 8180)
- 0PC74.exe (PID: 7244)
- 4LU90.exe (PID: 2964)
- QQ68T.exe (PID: 1080)
- DRNIY.exe (PID: 7304)
- PKJU0.exe (PID: 7480)
- LJ7N7.exe (PID: 7108)
- 7NUST.exe (PID: 7528)
- 2GQCZ.exe (PID: 4896)
- 61596.exe (PID: 7484)
- Z4J88.exe (PID: 3468)
- 2LE92.exe (PID: 7644)
- RJB84.exe (PID: 932)
- YCU1Y.exe (PID: 660)
- 7609I.exe (PID: 7760)
- 4V6KD.exe (PID: 6048)
- 44710.exe (PID: 7256)
- 1R00P.exe (PID: 7768)
- ET5YL.exe (PID: 2700)
- 3W245.exe (PID: 6156)
- 961WF.exe (PID: 4916)
- FS121.exe (PID: 5392)
- 0U9KU.exe (PID: 1252)
- 2CVR6.exe (PID: 6236)
- A488N.exe (PID: 7924)
- 52N0T.exe (PID: 5704)
- Q0DQ6.exe (PID: 1924)
- ABDPY.exe (PID: 6300)
- QXK1G.exe (PID: 8076)
- 4BJR5.exe (PID: 8068)
- P3UW3.exe (PID: 8176)
- FEU1D.exe (PID: 1540)
- X8M1W.exe (PID: 2636)
- C9R03.exe (PID: 8036)
- T5YK7.exe (PID: 564)
- C895R.exe (PID: 3236)
- 3WB3H.exe (PID: 8172)
- P3Y56.exe (PID: 2820)
- 2L551.exe (PID: 6004)
- 6747G.exe (PID: 7464)
- 4W2V0.exe (PID: 4220)
- 061D6.exe (PID: 5124)
- 8BKZ6.exe (PID: 5192)
- 18K5D.exe (PID: 7656)
- K659K.exe (PID: 5712)
- 2X6H2.exe (PID: 5948)
- 937O9.exe (PID: 5912)
- F800M.exe (PID: 4140)
- YA25L.exe (PID: 7316)
- CT71M.exe (PID: 3320)
- F0A93.exe (PID: 5656)
- 4QQXF.exe (PID: 7444)
- 1OIL0.exe (PID: 6416)
- 553TU.exe (PID: 7840)
- N85R5.exe (PID: 8032)
- FV7Q7.exe (PID: 7344)
- 3W7ST.exe (PID: 7812)
- 0R1FD.exe (PID: 5368)
- N3P2Y.exe (PID: 3680)
- C678J.exe (PID: 5772)
- 5ZF77.exe (PID: 7984)
- 28FW7.exe (PID: 4360)
- J7Q9F.exe (PID: 3332)
- 9KX70.exe (PID: 4528)
- A7A9N.exe (PID: 8188)
- Z346S.exe (PID: 6988)
- 4NF77.exe (PID: 5892)
- 6Y9F1.exe (PID: 3020)
- JQ7P7.exe (PID: 476)
- M298O.exe (PID: 7792)
- LN85T.exe (PID: 7664)
- 8HVD8.exe (PID: 3236)
- SBNK3.exe (PID: 7232)
- I3FL1.exe (PID: 272)
- 9OV5D.exe (PID: 7328)
- M2PP1.exe (PID: 7564)
- NXKXZ.exe (PID: 7592)
- 2NL71.exe (PID: 4368)
- 1FA89.exe (PID: 5676)
- WZ5R9.exe (PID: 7896)
- 95A69.exe (PID: 7844)
- M04SW.exe (PID: 7724)
- Z4LWV.exe (PID: 4592)
- 6FWD5.exe (PID: 6452)
- 6I04B.exe (PID: 1844)
- 35VT6.exe (PID: 7628)
- 9NSM8.exe (PID: 7448)
- M70F6.exe (PID: 3680)
- 3769Y.exe (PID: 7940)
- 8672A.exe (PID: 7984)
- Y619C.exe (PID: 4360)
- ED3E5.exe (PID: 5368)
- J318B.exe (PID: 8144)
- G63HD.exe (PID: 5772)
- 3Z6S8.exe (PID: 564)
- 7D55V.exe (PID: 4528)
- 1185X.exe (PID: 7548)
- DC1YD.exe (PID: 4168)
- C89R8.exe (PID: 1504)
- 8K631.exe (PID: 3056)
- FA0M9.exe (PID: 404)
- 3D7SM.exe (PID: 6088)
- P53LK.exe (PID: 2820)
- LY9LH.exe (PID: 7100)
- X7J0M.exe (PID: 7508)
- T5FTO.exe (PID: 4996)
- L9FOD.exe (PID: 2576)
- V2YGW.exe (PID: 3956)
- NEQ55.exe (PID: 7460)
- H1U69.exe (PID: 3960)
- 1CJM1.exe (PID: 2564)
- WS76J.exe (PID: 1136)
- X0B43.exe (PID: 7740)
- G068C.exe (PID: 7720)
- IL89E.exe (PID: 7808)
- 9O8A7.exe (PID: 7848)
- T1V2X.exe (PID: 7900)
- 6506L.exe (PID: 5720)
- 9526M.exe (PID: 3392)
- 4X047.exe (PID: 7584)
- P7N86.exe (PID: 6164)
- TXW92.exe (PID: 7712)
- 5H918.exe (PID: 1252)
- JWIZ5.exe (PID: 8056)
- UHBE0.exe (PID: 3696)
- RS911.exe (PID: 3156)
- AYRAJ.exe (PID: 8092)
- TC027.exe (PID: 7960)
- K8UY7.exe (PID: 4280)
- 4C8M4.exe (PID: 8052)
- C919F.exe (PID: 1172)
- 16G78.exe (PID: 4720)
- 74274.exe (PID: 7604)
- D97EI.exe (PID: 5872)
- 12I31.exe (PID: 7508)
- 54KXP.exe (PID: 5884)
- 7C50O.exe (PID: 7612)
- D5234.exe (PID: 7540)
- 149RP.exe (PID: 7100)
- 78S5K.exe (PID: 4996)
- 2V531.exe (PID: 7524)
- 65918.exe (PID: 7460)
- Q20MZ.exe (PID: 3956)
- 0V85U.exe (PID: 2564)
- 15521.exe (PID: 3960)
- 93J3Q.exe (PID: 2576)
- WZ0C5.exe (PID: 7720)
- 0B581.exe (PID: 1136)
- 8J6V7.exe (PID: 7740)
- E6OTH.exe (PID: 7900)
- 0P2N0.exe (PID: 7848)
- 06BDB.exe (PID: 5720)
- 7442L.exe (PID: 3392)
- X90FV.exe (PID: 6164)
- H2N4X.exe (PID: 7808)
- 1MFY8.exe (PID: 7584)
- P5PAJ.exe (PID: 7712)
- 37SHD.exe (PID: 5604)
- 94T0F.exe (PID: 8056)
- J30H6.exe (PID: 4140)
- 5P20F.exe (PID: 4668)
- 3R6F8.exe (PID: 7444)
- 96QJ1.exe (PID: 3320)
- PZT68.exe (PID: 5656)
- J0TI0.exe (PID: 3364)
- R69OK.exe (PID: 8144)
- PP5S8.exe (PID: 3044)
- IYW45.exe (PID: 2100)
- 2CD2V.exe (PID: 692)
- 8KFU6.exe (PID: 7484)
- 5106J.exe (PID: 7380)
- FM69K.exe (PID: 5328)
- 5D328.exe (PID: 7312)
- GL5V3.exe (PID: 7520)
- 91204.exe (PID: 2972)
- 18G90.exe (PID: 5656)
- 3PG3X.exe (PID: 3320)
- Q3BHF.exe (PID: 3200)
- D1MY8.exe (PID: 6264)
- BO166.exe (PID: 6840)
- 251I1.exe (PID: 1284)
Reads security settings of Internet Explorer
- 41a95b2ea5f1469a0b71cdf6cf7d3a4f922a50d0afe78479b4470c9b5ac1dd71.exe (PID: 7412)
- 05YZJ.exe (PID: 7460)
- PIJ5L.exe (PID: 7512)
- AE0TB.exe (PID: 7564)
- 27XT9.exe (PID: 7620)
- T7IA7.exe (PID: 7688)
- Y57IT.exe (PID: 7888)
- 1P19U.exe (PID: 7976)
- X45B2.exe (PID: 7764)
- SG56W.exe (PID: 8040)
- OVCW2.exe (PID: 8108)
- S861Y.exe (PID: 8160)
- ACCNF.exe (PID: 4104)
- 674L6.exe (PID: 1924)
- 3B451.exe (PID: 7436)
- 713X7.exe (PID: 7528)
- 152D8.exe (PID: 7580)
- Z06ZC.exe (PID: 7872)
- Y25VX.exe (PID: 7632)
- M5XB6.exe (PID: 7788)
- 910G6.exe (PID: 2344)
- 44YF5.exe (PID: 7824)
- 46195.exe (PID: 8000)
- I9LHP.exe (PID: 7976)
- VPHQB.exe (PID: 8040)
- 32VI8.exe (PID: 7240)
- 6U8KU.exe (PID: 3236)
- IE44A.exe (PID: 8112)
- 15P26.exe (PID: 4900)
- 890SH.exe (PID: 4220)
- GXE5N.exe (PID: 7492)
- G74CB.exe (PID: 7528)
- 3YD6H.exe (PID: 3400)
- 6JH56.exe (PID: 7436)
- K469T.exe (PID: 7640)
- D50UW.exe (PID: 7580)
- 0858S.exe (PID: 7740)
- 4T0HE.exe (PID: 7476)
- 4M7VA.exe (PID: 7472)
- 9MT7S.exe (PID: 6356)
- CA31T.exe (PID: 7696)
- 5Q6HZ.exe (PID: 4916)
- MPEF6.exe (PID: 7812)
- UT400.exe (PID: 892)
- NM896.exe (PID: 7796)
- X9IAD.exe (PID: 8020)
- 744H4.exe (PID: 8144)
- 16811.exe (PID: 2104)
- ZO289.exe (PID: 5868)
- GMIAC.exe (PID: 8076)
- TS8AA.exe (PID: 5244)
- Y2W2E.exe (PID: 5408)
- 8142Y.exe (PID: 2740)
- 7GEP8.exe (PID: 7460)
- EU543.exe (PID: 7588)
- 1LZM5.exe (PID: 5948)
- GT2UA.exe (PID: 4452)
- 4J6B9.exe (PID: 7608)
- JF5M3.exe (PID: 3364)
- 68VS4.exe (PID: 7676)
- 4L057.exe (PID: 1252)
- 388P6.exe (PID: 4592)
- 0DL76.exe (PID: 7852)
- X8Y91.exe (PID: 5696)
- 4J017.exe (PID: 3680)
- 060G0.exe (PID: 7872)
- Z9RH6.exe (PID: 8084)
- 49BXW.exe (PID: 8116)
- FUD95.exe (PID: 7960)
- 72943.exe (PID: 5196)
- 2QB3V.exe (PID: 8172)
- 3A2U6.exe (PID: 4064)
- 8RXJ5.exe (PID: 6728)
- LYRTA.exe (PID: 7252)
- L0XJ5.exe (PID: 6880)
- TTZB9.exe (PID: 7480)
- 00K89.exe (PID: 7520)
- 33QO0.exe (PID: 7568)
- S87J9.exe (PID: 6260)
- T2452.exe (PID: 3468)
- R1P3C.exe (PID: 7616)
- GW50J.exe (PID: 1276)
- JR2BY.exe (PID: 2408)
- 5B7V6.exe (PID: 7868)
- 4Z068.exe (PID: 7680)
- Y0FW1.exe (PID: 5656)
- 6P7QP.exe (PID: 7940)
- 42THZ.exe (PID: 7992)
- H1UGV.exe (PID: 7788)
- RR2IL.exe (PID: 3332)
- 61FDE.exe (PID: 6452)
- 846H9.exe (PID: 8136)
- 233DV.exe (PID: 4064)
- 0JBT6.exe (PID: 4264)
- 2287R.exe (PID: 7796)
- JGM62.exe (PID: 7496)
- 5QFG1.exe (PID: 8040)
- 4K596.exe (PID: 7612)
- GJ1EW.exe (PID: 7560)
- 4W41K.exe (PID: 7668)
- FDN4D.exe (PID: 7576)
- 14887.exe (PID: 5712)
- H4AMG.exe (PID: 1252)
- 4AL80.exe (PID: 7624)
- 135GH.exe (PID: 3100)
- 3PL9G.exe (PID: 5696)
- 9GGQ0.exe (PID: 7924)
- 44W55.exe (PID: 5224)
- 8VT67.exe (PID: 7676)
- 7N537.exe (PID: 3460)
- QQ9QW.exe (PID: 7916)
- 33C3V.exe (PID: 1140)
- 704N6.exe (PID: 8020)
- 29N30.exe (PID: 8092)
- CJ2BA.exe (PID: 6376)
- 936IC.exe (PID: 476)
- 9607X.exe (PID: 6776)
- 6N466.exe (PID: 7796)
- 6WNR9.exe (PID: 6676)
- Y8FJ3.exe (PID: 4900)
- RY1B7.exe (PID: 2852)
- 45VQG.exe (PID: 7556)
- I7J3C.exe (PID: 7460)
- HVF03.exe (PID: 4668)
- I0C6M.exe (PID: 7708)
- K4CPT.exe (PID: 5580)
- HA572.exe (PID: 5268)
- S9G16.exe (PID: 3100)
- LC3NX.exe (PID: 7840)
- 2WJ83.exe (PID: 7692)
- W1UXJ.exe (PID: 7864)
- W9FNS.exe (PID: 7768)
- 384M8.exe (PID: 7852)
- A1OW3.exe (PID: 2764)
- N0944.exe (PID: 5368)
- 1Z9YK.exe (PID: 8052)
- HA7IB.exe (PID: 5772)
- TLJU6.exe (PID: 5288)
- 1X968.exe (PID: 8180)
- 697GY.exe (PID: 5660)
- 3G558.exe (PID: 2164)
- J159E.exe (PID: 8024)
- 7W936.exe (PID: 1948)
- REBR8.exe (PID: 7276)
- 2BS07.exe (PID: 2104)
- L5A71.exe (PID: 7332)
- VJALT.exe (PID: 2944)
- F3AL2.exe (PID: 7536)
- 4N883.exe (PID: 5504)
- WT72A.exe (PID: 6260)
- 7ML00.exe (PID: 7436)
- EX80H.exe (PID: 5900)
- 93465.exe (PID: 5040)
- IM8L2.exe (PID: 7700)
- 8J424.exe (PID: 5704)
- 161WC.exe (PID: 7624)
- ZYG4A.exe (PID: 7676)
- 3O348.exe (PID: 7448)
- 5008Z.exe (PID: 5696)
- M150Y.exe (PID: 7856)
- 15OE9.exe (PID: 7996)
- 72223.exe (PID: 4400)
- 1M300.exe (PID: 7352)
- 21JZY.exe (PID: 8128)
- 76I5W.exe (PID: 8044)
- JC7BE.exe (PID: 7976)
- SMWI4.exe (PID: 476)
- P37R8.exe (PID: 6776)
- RVL17.exe (PID: 6376)
- 1000T.exe (PID: 3944)
- VPOBX.exe (PID: 7664)
- USS5N.exe (PID: 7796)
- Z7QVP.exe (PID: 5244)
- GBJ33.exe (PID: 7516)
- 34C0T.exe (PID: 7484)
- QZ3E8.exe (PID: 8104)
- 3P7L5.exe (PID: 4452)
- 4T3G5.exe (PID: 4244)
- U758A.exe (PID: 7708)
- UB1D3.exe (PID: 7628)
- 3MQHV.exe (PID: 4668)
- DI9J0.exe (PID: 6164)
- P1ZQ3.exe (PID: 7784)
- 177WJ.exe (PID: 5580)
- 95758.exe (PID: 7904)
- SIN7D.exe (PID: 7816)
- 7D5SU.exe (PID: 7892)
- 7CQ7F.exe (PID: 2344)
- S87C9.exe (PID: 7348)
- G587W.exe (PID: 7944)
- 70NQ3.exe (PID: 3076)
- 4SIOD.exe (PID: 7952)
- 6V9N2.exe (PID: 7960)
- 1V809.exe (PID: 3984)
- 2AZV3.exe (PID: 2036)
- 2BNS9.exe (PID: 8108)
- 60Y4Y.exe (PID: 5376)
- 72MNC.exe (PID: 1576)
- 1S9LN.exe (PID: 4104)
- SAI99.exe (PID: 2880)
- 13I69.exe (PID: 5408)
- N10GX.exe (PID: 7556)
- YV5R1.exe (PID: 6676)
- 95XPK.exe (PID: 7572)
- GRW60.exe (PID: 7724)
- NPB62.exe (PID: 3956)
- 8UHII.exe (PID: 5268)
- D6350.exe (PID: 7836)
- 22032.exe (PID: 7748)
- 9H1Q1.exe (PID: 3996)
- PF509.exe (PID: 1136)
- 9N3CG.exe (PID: 7848)
- 4WQQE.exe (PID: 7788)
- WAJIF.exe (PID: 7820)
- 99141.exe (PID: 6264)
- 3VSS3.exe (PID: 2344)
- BLD7F.exe (PID: 3460)
- V9519.exe (PID: 7888)
- 35L5E.exe (PID: 4280)
- 1TL17.exe (PID: 8068)
- D3WN4.exe (PID: 8048)
- 94R76.exe (PID: 8152)
- GOV5K.exe (PID: 3236)
- C3HC9.exe (PID: 2312)
- D96QW.exe (PID: 1080)
- I6RV4.exe (PID: 2220)
- I6B09.exe (PID: 6940)
- KIXH4.exe (PID: 2760)
- 9PAFD.exe (PID: 7596)
- 9RM87.exe (PID: 7332)
- 460IW.exe (PID: 7380)
- S07XZ.exe (PID: 1688)
- 8G99B.exe (PID: 5948)
- DA5TX.exe (PID: 7640)
- 607S5.exe (PID: 7096)
- G3342.exe (PID: 2008)
- L0C14.exe (PID: 5040)
- BPCB1.exe (PID: 3996)
- JL3JW.exe (PID: 7880)
- 5475W.exe (PID: 6252)
- 1T831.exe (PID: 1836)
- M3414.exe (PID: 7788)
- WN8FW.exe (PID: 3680)
- J0Z4I.exe (PID: 7888)
- TAZN8.exe (PID: 8008)
- O30T9.exe (PID: 3460)
- 6Y84Z.exe (PID: 8068)
- W9U53.exe (PID: 4280)
- YUIXG.exe (PID: 8048)
- 05NP7.exe (PID: 800)
- 0FKP5.exe (PID: 1384)
- 066PD.exe (PID: 4720)
- 505OB.exe (PID: 6504)
- FN8F2.exe (PID: 7492)
- 2541J.exe (PID: 7328)
- 9L57J.exe (PID: 1952)
- K7LN5.exe (PID: 2740)
- 2XSO0.exe (PID: 3568)
- 4E61L.exe (PID: 2900)
- 1209L.exe (PID: 7668)
- O1HB2.exe (PID: 7560)
- 8SZ85.exe (PID: 7744)
- I9R07.exe (PID: 4668)
- QI603.exe (PID: 7688)
- I59UD.exe (PID: 7784)
- 4TKS5.exe (PID: 5452)
- DBR9D.exe (PID: 1284)
- 022B9.exe (PID: 4884)
- C896I.exe (PID: 1520)
- 2A5F5.exe (PID: 5704)
- B80HR.exe (PID: 7912)
- 9E6N9.exe (PID: 7712)
- 0037G.exe (PID: 7824)
- 1746F.exe (PID: 7916)
- MRL2Z.exe (PID: 7988)
- 9Y2AJ.exe (PID: 6964)
- 07XOW.exe (PID: 4360)
- Y0JG0.exe (PID: 4784)
- 1B2N3.exe (PID: 8176)
- 89YII.exe (PID: 5956)
- APF67.exe (PID: 8112)
- 1ZTZW.exe (PID: 4760)
- H00P7.exe (PID: 7540)
- CX629.exe (PID: 1148)
- 3U9HZ.exe (PID: 5500)
- 0T70H.exe (PID: 2100)
- QGR2G.exe (PID: 1264)
- 31Z24.exe (PID: 7660)
- XQWA4.exe (PID: 7588)
- 098VM.exe (PID: 2316)
- 90108.exe (PID: 3400)
- OY28S.exe (PID: 7580)
- QU316.exe (PID: 7864)
- 2DC97.exe (PID: 4452)
- 1E928.exe (PID: 7736)
- 1T9QO.exe (PID: 7868)
- VR3XP.exe (PID: 4916)
- 4T6D5.exe (PID: 5392)
- 97R42.exe (PID: 7924)
- T8GF2.exe (PID: 6156)
- 54Y4E.exe (PID: 1252)
- EXY1D.exe (PID: 5704)
- YQU4Y.exe (PID: 7348)
- F3JY5.exe (PID: 5584)
- 5AJX5.exe (PID: 2344)
- QYC88.exe (PID: 8144)
- 7UKT5.exe (PID: 8120)
- I1U0X.exe (PID: 8008)
- ZI8HO.exe (PID: 1540)
- 73A7I.exe (PID: 8176)
- T0YZ6.exe (PID: 2636)
- 5VOT0.exe (PID: 7796)
- H2GM5.exe (PID: 8024)
- B90C3.exe (PID: 5956)
- 8M27C.exe (PID: 1148)
- I4R98.exe (PID: 7664)
- YT95L.exe (PID: 7496)
- 567H4.exe (PID: 7100)
- M81O1.exe (PID: 7560)
- CF2W8.exe (PID: 7436)
- 081VV.exe (PID: 7660)
- 4UNDC.exe (PID: 2580)
- L1V69.exe (PID: 7756)
- N7886.exe (PID: 1248)
- 90GQJ.exe (PID: 7616)
- 58NY3.exe (PID: 7688)
- 4BYIC.exe (PID: 7632)
- W5N73.exe (PID: 7784)
- 3CBUL.exe (PID: 3392)
- OSV3P.exe (PID: 7908)
- 6886X.exe (PID: 6164)
- QS4B1.exe (PID: 5540)
- 3L9Y6.exe (PID: 5356)
- C1304.exe (PID: 6740)
- S040W.exe (PID: 3148)
- 5W8TX.exe (PID: 7888)
- W0VS1.exe (PID: 7992)
- NV87C.exe (PID: 8128)
- E9437.exe (PID: 8124)
- O870X.exe (PID: 4384)
- 623X2.exe (PID: 2164)
- 9T2X3.exe (PID: 6872)
- 1GPF5.exe (PID: 5508)
- 7L8F3.exe (PID: 7440)
- 1HMXM.exe (PID: 6728)
- 9FF6V.exe (PID: 272)
- X5X86.exe (PID: 2104)
- X11ZD.exe (PID: 7328)
- 2EI6W.exe (PID: 7332)
- H83M9.exe (PID: 2512)
- C5O6S.exe (PID: 3568)
- O29W1.exe (PID: 1952)
- 7PB1L.exe (PID: 2580)
- 65GW2.exe (PID: 1248)
- 3FC69.exe (PID: 7632)
- 04C2B.exe (PID: 7616)
- IH88U.exe (PID: 7688)
- 71H49.exe (PID: 1128)
- IXJU5.exe (PID: 7756)
- F0FZI.exe (PID: 7436)
- 385D5.exe (PID: 7908)
- 077UU.exe (PID: 3392)
- N71JV.exe (PID: 6164)
- 5056Z.exe (PID: 5540)
- YEZFT.exe (PID: 5356)
- 3A1N4.exe (PID: 6740)
- 284M4.exe (PID: 3156)
- 6I57G.exe (PID: 2344)
- J715A.exe (PID: 7348)
- Z41A7.exe (PID: 8008)
- 1B5H5.exe (PID: 6444)
- 3ZQ3K.exe (PID: 2716)
- L38GI.exe (PID: 8116)
- 8611J.exe (PID: 2724)
- L67FH.exe (PID: 8180)
- 0PC74.exe (PID: 7244)
- QQ68T.exe (PID: 1080)
- 4LU90.exe (PID: 2964)
- 61596.exe (PID: 7484)
- DRNIY.exe (PID: 7304)
- LJ7N7.exe (PID: 7108)
- PKJU0.exe (PID: 7480)
- 7NUST.exe (PID: 7528)
- 2GQCZ.exe (PID: 4896)
- 2LE92.exe (PID: 7644)
- RJB84.exe (PID: 932)
- Z4J88.exe (PID: 3468)
- 44710.exe (PID: 7256)
- 7609I.exe (PID: 7760)
- 961WF.exe (PID: 4916)
- YCU1Y.exe (PID: 660)
- 3W245.exe (PID: 6156)
- 1R00P.exe (PID: 7768)
- ET5YL.exe (PID: 2700)
- 4V6KD.exe (PID: 6048)
- FS121.exe (PID: 5392)
- A488N.exe (PID: 7924)
- 52N0T.exe (PID: 5704)
- 0U9KU.exe (PID: 1252)
- 2CVR6.exe (PID: 6236)
- ABDPY.exe (PID: 6300)
- Q0DQ6.exe (PID: 1924)
- 4BJR5.exe (PID: 8068)
- X8M1W.exe (PID: 2636)
- FEU1D.exe (PID: 1540)
- QXK1G.exe (PID: 8076)
- C9R03.exe (PID: 8036)
- C895R.exe (PID: 3236)
- P3Y56.exe (PID: 2820)
- T5YK7.exe (PID: 564)
- P3UW3.exe (PID: 8176)
- 2L551.exe (PID: 6004)
- 6747G.exe (PID: 7464)
- 061D6.exe (PID: 5124)
- K659K.exe (PID: 5712)
- 3WB3H.exe (PID: 8172)
- 4W2V0.exe (PID: 4220)
- 8BKZ6.exe (PID: 5192)
- 18K5D.exe (PID: 7656)
- 937O9.exe (PID: 5912)
- 2X6H2.exe (PID: 5948)
- YA25L.exe (PID: 7316)
- F800M.exe (PID: 4140)
- F0A93.exe (PID: 5656)
- 4QQXF.exe (PID: 7444)
- CT71M.exe (PID: 3320)
- 553TU.exe (PID: 7840)
- 1OIL0.exe (PID: 6416)
- N85R5.exe (PID: 8032)
- FV7Q7.exe (PID: 7344)
- 3W7ST.exe (PID: 7812)
- N3P2Y.exe (PID: 3680)
- 0R1FD.exe (PID: 5368)
- 28FW7.exe (PID: 4360)
- C678J.exe (PID: 5772)
- 5ZF77.exe (PID: 7984)
- 9KX70.exe (PID: 4528)
- J7Q9F.exe (PID: 3332)
- Z346S.exe (PID: 6988)
- 4NF77.exe (PID: 5892)
- A7A9N.exe (PID: 8188)
- 6Y9F1.exe (PID: 3020)
- JQ7P7.exe (PID: 476)
- M298O.exe (PID: 7792)
- 8HVD8.exe (PID: 3236)
- SBNK3.exe (PID: 7232)
- LN85T.exe (PID: 7664)
- I3FL1.exe (PID: 272)
- NXKXZ.exe (PID: 7592)
- M2PP1.exe (PID: 7564)
- 9OV5D.exe (PID: 7328)
- 2NL71.exe (PID: 4368)
- W1LKP.exe (PID: 7640)
- 1FA89.exe (PID: 5676)
- M04SW.exe (PID: 7724)
- WZ5R9.exe (PID: 7896)
- 95A69.exe (PID: 7844)
- 6I04B.exe (PID: 1844)
- Z4LWV.exe (PID: 4592)
- 6FWD5.exe (PID: 6452)
- 9NSM8.exe (PID: 7448)
- 35VT6.exe (PID: 7628)
- I5G1E.exe (PID: 2408)
- 3769Y.exe (PID: 7940)
- M70F6.exe (PID: 3680)
- Y619C.exe (PID: 4360)
- ED3E5.exe (PID: 5368)
- 8672A.exe (PID: 7984)
- G63HD.exe (PID: 5772)
- J318B.exe (PID: 8144)
- 7D55V.exe (PID: 4528)
- 3Z6S8.exe (PID: 564)
- 1185X.exe (PID: 7548)
- C89R8.exe (PID: 1504)
- DC1YD.exe (PID: 4168)
- FA0M9.exe (PID: 404)
- 8K631.exe (PID: 3056)
- 3D7SM.exe (PID: 6088)
- 57YAT.exe (PID: 4164)
- P53LK.exe (PID: 2820)
- 6VN85.exe (PID: 7540)
- B96M2.exe (PID: 7612)
- LY9LH.exe (PID: 7100)
- X7J0M.exe (PID: 7508)
- P21S1.exe (PID: 7524)
- T5FTO.exe (PID: 4996)
- V2YGW.exe (PID: 3956)
- L9FOD.exe (PID: 2576)
- NEQ55.exe (PID: 7460)
- 1CJM1.exe (PID: 2564)
- H1U69.exe (PID: 3960)
- G068C.exe (PID: 7720)
- WS76J.exe (PID: 1136)
- X0B43.exe (PID: 7740)
- T1V2X.exe (PID: 7900)
- IL89E.exe (PID: 7808)
- 9O8A7.exe (PID: 7848)
- 9526M.exe (PID: 3392)
- 6506L.exe (PID: 5720)
- 4X047.exe (PID: 7584)
- P7N86.exe (PID: 6164)
- 5H918.exe (PID: 1252)
- JWIZ5.exe (PID: 8056)
- TXW92.exe (PID: 7712)
- RS911.exe (PID: 3156)
- UHBE0.exe (PID: 3696)
- AYRAJ.exe (PID: 8092)
- K8UY7.exe (PID: 4280)
- 4C8M4.exe (PID: 8052)
- TC027.exe (PID: 7960)
- ARVV0.exe (PID: 5652)
- C919F.exe (PID: 1172)
- 16G78.exe (PID: 4720)
- 74274.exe (PID: 7604)
- D97EI.exe (PID: 5872)
- 54KXP.exe (PID: 5884)
- 12I31.exe (PID: 7508)
- D5234.exe (PID: 7540)
- 7C50O.exe (PID: 7612)
- 149RP.exe (PID: 7100)
- 78S5K.exe (PID: 4996)
- 2V531.exe (PID: 7524)
- Q20MZ.exe (PID: 3956)
- 65918.exe (PID: 7460)
- 0V85U.exe (PID: 2564)
- 15521.exe (PID: 3960)
- 93J3Q.exe (PID: 2576)
- WZ0C5.exe (PID: 7720)
- 0B581.exe (PID: 1136)
- 8J6V7.exe (PID: 7740)
- 0P2N0.exe (PID: 7848)
- E6OTH.exe (PID: 7900)
- 06BDB.exe (PID: 5720)
- 7442L.exe (PID: 3392)
- X90FV.exe (PID: 6164)
- H2N4X.exe (PID: 7808)
- 1MFY8.exe (PID: 7584)
- 4XL2Y.exe (PID: 1252)
- 37SHD.exe (PID: 5604)
- 94T0F.exe (PID: 8056)
- P5PAJ.exe (PID: 7712)
- 39119.exe (PID: 8052)
- CV758.exe (PID: 3696)
- 795BA.exe (PID: 8164)
- I386Z.exe (PID: 5652)
- V9JRJ.exe (PID: 4280)
- CRZG7.exe (PID: 7960)
- OI304.exe (PID: 1172)
- 840K8.exe (PID: 5884)
- 00IL4.exe (PID: 4720)
- 91MQJ.exe (PID: 7604)
- 3L324.exe (PID: 7108)
- 680P5.exe (PID: 7480)
- G19D2.exe (PID: 2104)
- 8HE62.exe (PID: 6972)
- 8023A.exe (PID: 6952)
- SL4W3.exe (PID: 2800)
- F0249.exe (PID: 7716)
- 047W6.exe (PID: 2972)
- 271RH.exe (PID: 7588)
- 5P20F.exe (PID: 4668)
- 9F6IY.exe (PID: 7316)
- G9379.exe (PID: 3200)
- 3R6F8.exe (PID: 7444)
- J30H6.exe (PID: 4140)
- 96QJ1.exe (PID: 3320)
- 4JH29.exe (PID: 2720)
- W57KL.exe (PID: 7448)
- PZT68.exe (PID: 5656)
- 5C9UK.exe (PID: 2408)
- J0TI0.exe (PID: 3364)
- W5R8O.exe (PID: 2804)
- 08F2R.exe (PID: 5480)
- Z0J96.exe (PID: 1656)
- QJPK5.exe (PID: 8000)
- TY934.exe (PID: 5584)
- 3RM64.exe (PID: 4360)
- 0S56I.exe (PID: 5772)
- MRA03.exe (PID: 564)
- R69OK.exe (PID: 8144)
- UPE07.exe (PID: 4528)
- 81OPC.exe (PID: 6464)
- N03U4.exe (PID: 5472)
- 4HLI3.exe (PID: 3544)
- PP5S8.exe (PID: 3044)
- K9BZO.exe (PID: 7552)
- V3P3S.exe (PID: 1144)
- 2CD2V.exe (PID: 692)
- IYW45.exe (PID: 2100)
- 8KFU6.exe (PID: 7484)
- FM69K.exe (PID: 5328)
- 5106J.exe (PID: 7380)
- 8K2KG.exe (PID: 8104)
- GL5V3.exe (PID: 7520)
- 5D328.exe (PID: 7312)
- 91204.exe (PID: 2972)
Reads the date of Windows installation
- 41a95b2ea5f1469a0b71cdf6cf7d3a4f922a50d0afe78479b4470c9b5ac1dd71.exe (PID: 7412)
- 05YZJ.exe (PID: 7460)
- PIJ5L.exe (PID: 7512)
- AE0TB.exe (PID: 7564)
- 27XT9.exe (PID: 7620)
- T7IA7.exe (PID: 7688)
- X45B2.exe (PID: 7764)
Starts itself from another location
- 41a95b2ea5f1469a0b71cdf6cf7d3a4f922a50d0afe78479b4470c9b5ac1dd71.exe (PID: 7412)
- 05YZJ.exe (PID: 7460)
- PIJ5L.exe (PID: 7512)
- AE0TB.exe (PID: 7564)
- 27XT9.exe (PID: 7620)
- T7IA7.exe (PID: 7688)
- Y57IT.exe (PID: 7888)
- X45B2.exe (PID: 7764)
- SG56W.exe (PID: 8040)
- OVCW2.exe (PID: 8108)
- 1P19U.exe (PID: 7976)
- ACCNF.exe (PID: 4104)
- 674L6.exe (PID: 1924)
- S861Y.exe (PID: 8160)
- 3B451.exe (PID: 7436)
- 713X7.exe (PID: 7528)
- 152D8.exe (PID: 7580)
- Y25VX.exe (PID: 7632)
- M5XB6.exe (PID: 7788)
- 910G6.exe (PID: 2344)
- 44YF5.exe (PID: 7824)
- 46195.exe (PID: 8000)
- Z06ZC.exe (PID: 7872)
- I9LHP.exe (PID: 7976)
- VPHQB.exe (PID: 8040)
- 6U8KU.exe (PID: 3236)
- 32VI8.exe (PID: 7240)
- IE44A.exe (PID: 8112)
- GXE5N.exe (PID: 7492)
- 15P26.exe (PID: 4900)
- 890SH.exe (PID: 4220)
- 6JH56.exe (PID: 7436)
- G74CB.exe (PID: 7528)
- 3YD6H.exe (PID: 3400)
- K469T.exe (PID: 7640)
- D50UW.exe (PID: 7580)
- 0858S.exe (PID: 7740)
- CA31T.exe (PID: 7696)
- 4T0HE.exe (PID: 7476)
- 4M7VA.exe (PID: 7472)
- 9MT7S.exe (PID: 6356)
- 5Q6HZ.exe (PID: 4916)
- MPEF6.exe (PID: 7812)
- UT400.exe (PID: 892)
- NM896.exe (PID: 7796)
- X9IAD.exe (PID: 8020)
- 744H4.exe (PID: 8144)
- 16811.exe (PID: 2104)
- GMIAC.exe (PID: 8076)
- ZO289.exe (PID: 5868)
- 8142Y.exe (PID: 2740)
- TS8AA.exe (PID: 5244)
- Y2W2E.exe (PID: 5408)
- 7GEP8.exe (PID: 7460)
- EU543.exe (PID: 7588)
- 1LZM5.exe (PID: 5948)
- 4J6B9.exe (PID: 7608)
- GT2UA.exe (PID: 4452)
- JF5M3.exe (PID: 3364)
- 68VS4.exe (PID: 7676)
- 4L057.exe (PID: 1252)
- X8Y91.exe (PID: 5696)
- 388P6.exe (PID: 4592)
- 0DL76.exe (PID: 7852)
- 060G0.exe (PID: 7872)
- 4J017.exe (PID: 3680)
- Z9RH6.exe (PID: 8084)
- 72943.exe (PID: 5196)
- FUD95.exe (PID: 7960)
- 49BXW.exe (PID: 8116)
- 2QB3V.exe (PID: 8172)
- 3A2U6.exe (PID: 4064)
- 8RXJ5.exe (PID: 6728)
- LYRTA.exe (PID: 7252)
- L0XJ5.exe (PID: 6880)
- TTZB9.exe (PID: 7480)
- 00K89.exe (PID: 7520)
- 33QO0.exe (PID: 7568)
- T2452.exe (PID: 3468)
- R1P3C.exe (PID: 7616)
- S87J9.exe (PID: 6260)
- GW50J.exe (PID: 1276)
- 4Z068.exe (PID: 7680)
- 5B7V6.exe (PID: 7868)
- JR2BY.exe (PID: 2408)
- Y0FW1.exe (PID: 5656)
- 61FDE.exe (PID: 6452)
- 6P7QP.exe (PID: 7940)
- 42THZ.exe (PID: 7992)
- H1UGV.exe (PID: 7788)
- 846H9.exe (PID: 8136)
- RR2IL.exe (PID: 3332)
- 233DV.exe (PID: 4064)
- 5QFG1.exe (PID: 8040)
- 2287R.exe (PID: 7796)
- JGM62.exe (PID: 7496)
- 0JBT6.exe (PID: 4264)
- GJ1EW.exe (PID: 7560)
- 4K596.exe (PID: 7612)
- 4W41K.exe (PID: 7668)
- FDN4D.exe (PID: 7576)
- 14887.exe (PID: 5712)
- 135GH.exe (PID: 3100)
- H4AMG.exe (PID: 1252)
- 4AL80.exe (PID: 7624)
- 8VT67.exe (PID: 7676)
- 3PL9G.exe (PID: 5696)
- 9GGQ0.exe (PID: 7924)
- 44W55.exe (PID: 5224)
- 7N537.exe (PID: 3460)
- QQ9QW.exe (PID: 7916)
- 704N6.exe (PID: 8020)
- 29N30.exe (PID: 8092)
- CJ2BA.exe (PID: 6376)
- 33C3V.exe (PID: 1140)
- 936IC.exe (PID: 476)
- 9607X.exe (PID: 6776)
- 6N466.exe (PID: 7796)
- RY1B7.exe (PID: 2852)
- Y8FJ3.exe (PID: 4900)
- 6WNR9.exe (PID: 6676)
- 45VQG.exe (PID: 7556)
- I7J3C.exe (PID: 7460)
- HVF03.exe (PID: 4668)
- I0C6M.exe (PID: 7708)
- K4CPT.exe (PID: 5580)
- HA572.exe (PID: 5268)
- S9G16.exe (PID: 3100)
- W1UXJ.exe (PID: 7864)
- W9FNS.exe (PID: 7768)
- 2WJ83.exe (PID: 7692)
- LC3NX.exe (PID: 7840)
- 384M8.exe (PID: 7852)
- A1OW3.exe (PID: 2764)
- TLJU6.exe (PID: 5288)
- N0944.exe (PID: 5368)
- HA7IB.exe (PID: 5772)
- 1Z9YK.exe (PID: 8052)
- J159E.exe (PID: 8024)
- 1X968.exe (PID: 8180)
- 697GY.exe (PID: 5660)
- 7W936.exe (PID: 1948)
- REBR8.exe (PID: 7276)
- 3G558.exe (PID: 2164)
- 2BS07.exe (PID: 2104)
- L5A71.exe (PID: 7332)
- VJALT.exe (PID: 2944)
- F3AL2.exe (PID: 7536)
- 7ML00.exe (PID: 7436)
- 4N883.exe (PID: 5504)
- WT72A.exe (PID: 6260)
- EX80H.exe (PID: 5900)
- 93465.exe (PID: 5040)
- IM8L2.exe (PID: 7700)
- 8J424.exe (PID: 5704)
- 161WC.exe (PID: 7624)
- 3O348.exe (PID: 7448)
- 5008Z.exe (PID: 5696)
- M150Y.exe (PID: 7856)
- ZYG4A.exe (PID: 7676)
- 72223.exe (PID: 4400)
- 1M300.exe (PID: 7352)
- 15OE9.exe (PID: 7996)
- 21JZY.exe (PID: 8128)
- 76I5W.exe (PID: 8044)
- JC7BE.exe (PID: 7976)
- RVL17.exe (PID: 6376)
- SMWI4.exe (PID: 476)
- P37R8.exe (PID: 6776)
- USS5N.exe (PID: 7796)
- 1000T.exe (PID: 3944)
- VPOBX.exe (PID: 7664)
- 34C0T.exe (PID: 7484)
- Z7QVP.exe (PID: 5244)
- GBJ33.exe (PID: 7516)
- 4T3G5.exe (PID: 4244)
- QZ3E8.exe (PID: 8104)
- 3P7L5.exe (PID: 4452)
- 3MQHV.exe (PID: 4668)
- 177WJ.exe (PID: 5580)
- UB1D3.exe (PID: 7628)
- DI9J0.exe (PID: 6164)
- U758A.exe (PID: 7708)
- P1ZQ3.exe (PID: 7784)
- 95758.exe (PID: 7904)
- SIN7D.exe (PID: 7816)
- 7D5SU.exe (PID: 7892)
- G587W.exe (PID: 7944)
- 7CQ7F.exe (PID: 2344)
- S87C9.exe (PID: 7348)
- 70NQ3.exe (PID: 3076)
- 4SIOD.exe (PID: 7952)
- 6V9N2.exe (PID: 7960)
- 1V809.exe (PID: 3984)
- 2AZV3.exe (PID: 2036)
- 2BNS9.exe (PID: 8108)
- 72MNC.exe (PID: 1576)
- 1S9LN.exe (PID: 4104)
- SAI99.exe (PID: 2880)
- 60Y4Y.exe (PID: 5376)
- 13I69.exe (PID: 5408)
- N10GX.exe (PID: 7556)
- YV5R1.exe (PID: 6676)
- 95XPK.exe (PID: 7572)
- NPB62.exe (PID: 3956)
- GRW60.exe (PID: 7724)
- 8UHII.exe (PID: 5268)
- 22032.exe (PID: 7748)
- D6350.exe (PID: 7836)
- 9H1Q1.exe (PID: 3996)
- 9N3CG.exe (PID: 7848)
- PF509.exe (PID: 1136)
- WAJIF.exe (PID: 7820)
- 4WQQE.exe (PID: 7788)
- 99141.exe (PID: 6264)
- 3VSS3.exe (PID: 2344)
- BLD7F.exe (PID: 3460)
- V9519.exe (PID: 7888)
- 35L5E.exe (PID: 4280)
- 1TL17.exe (PID: 8068)
- C3HC9.exe (PID: 2312)
- 94R76.exe (PID: 8152)
- D3WN4.exe (PID: 8048)
- D96QW.exe (PID: 1080)
- I6RV4.exe (PID: 2220)
- GOV5K.exe (PID: 3236)
- 9RM87.exe (PID: 7332)
- KIXH4.exe (PID: 2760)
- I6B09.exe (PID: 6940)
- 460IW.exe (PID: 7380)
- S07XZ.exe (PID: 1688)
- 9PAFD.exe (PID: 7596)
- DA5TX.exe (PID: 7640)
- 607S5.exe (PID: 7096)
- 8G99B.exe (PID: 5948)
- L0C14.exe (PID: 5040)
- BPCB1.exe (PID: 3996)
- G3342.exe (PID: 2008)
- 5475W.exe (PID: 6252)
- 1T831.exe (PID: 1836)
- JL3JW.exe (PID: 7880)
- WN8FW.exe (PID: 3680)
- J0Z4I.exe (PID: 7888)
- TAZN8.exe (PID: 8008)
- M3414.exe (PID: 7788)
- O30T9.exe (PID: 3460)
- W9U53.exe (PID: 4280)
- 6Y84Z.exe (PID: 8068)
- YUIXG.exe (PID: 8048)
- 05NP7.exe (PID: 800)
- 0FKP5.exe (PID: 1384)
- 505OB.exe (PID: 6504)
- 066PD.exe (PID: 4720)
- FN8F2.exe (PID: 7492)
- 2541J.exe (PID: 7328)
- 9L57J.exe (PID: 1952)
- K7LN5.exe (PID: 2740)
- O1HB2.exe (PID: 7560)
- 2XSO0.exe (PID: 3568)
- 4E61L.exe (PID: 2900)
- 8SZ85.exe (PID: 7744)
- I9R07.exe (PID: 4668)
- QI603.exe (PID: 7688)
- 1209L.exe (PID: 7668)
- I59UD.exe (PID: 7784)
- 4TKS5.exe (PID: 5452)
- 022B9.exe (PID: 4884)
- DBR9D.exe (PID: 1284)
- B80HR.exe (PID: 7912)
- C896I.exe (PID: 1520)
- 9E6N9.exe (PID: 7712)
- 0037G.exe (PID: 7824)
- 2A5F5.exe (PID: 5704)
- 1746F.exe (PID: 7916)
- MRL2Z.exe (PID: 7988)
- 07XOW.exe (PID: 4360)
- 9Y2AJ.exe (PID: 6964)
- Y0JG0.exe (PID: 4784)
- 1B2N3.exe (PID: 8176)
- 1ZTZW.exe (PID: 4760)
- APF67.exe (PID: 8112)
- 3U9HZ.exe (PID: 5500)
- H00P7.exe (PID: 7540)
- 89YII.exe (PID: 5956)
- 0T70H.exe (PID: 2100)
- QGR2G.exe (PID: 1264)
- CX629.exe (PID: 1148)
- 31Z24.exe (PID: 7660)
- XQWA4.exe (PID: 7588)
- 098VM.exe (PID: 2316)
- OY28S.exe (PID: 7580)
- 90108.exe (PID: 3400)
- 1E928.exe (PID: 7736)
- 2DC97.exe (PID: 4452)
- VR3XP.exe (PID: 4916)
- 1T9QO.exe (PID: 7868)
- QU316.exe (PID: 7864)
- T8GF2.exe (PID: 6156)
- 4T6D5.exe (PID: 5392)
- 54Y4E.exe (PID: 1252)
- EXY1D.exe (PID: 5704)
- 97R42.exe (PID: 7924)
- 5AJX5.exe (PID: 2344)
- YQU4Y.exe (PID: 7348)
- F3JY5.exe (PID: 5584)
- QYC88.exe (PID: 8144)
- 7UKT5.exe (PID: 8120)
- I1U0X.exe (PID: 8008)
- T0YZ6.exe (PID: 2636)
- 73A7I.exe (PID: 8176)
- ZI8HO.exe (PID: 1540)
- 5VOT0.exe (PID: 7796)
- B90C3.exe (PID: 5956)
- H2GM5.exe (PID: 8024)
- I4R98.exe (PID: 7664)
- YT95L.exe (PID: 7496)
- 8M27C.exe (PID: 1148)
- M81O1.exe (PID: 7560)
- 567H4.exe (PID: 7100)
- 081VV.exe (PID: 7660)
- 4UNDC.exe (PID: 2580)
- CF2W8.exe (PID: 7436)
- N7886.exe (PID: 1248)
- L1V69.exe (PID: 7756)
- 4BYIC.exe (PID: 7632)
- 90GQJ.exe (PID: 7616)
- 58NY3.exe (PID: 7688)
- W5N73.exe (PID: 7784)
- OSV3P.exe (PID: 7908)
- 3CBUL.exe (PID: 3392)
- 6886X.exe (PID: 6164)
- QS4B1.exe (PID: 5540)
- C1304.exe (PID: 6740)
- 3L9Y6.exe (PID: 5356)
- S040W.exe (PID: 3148)
- 5W8TX.exe (PID: 7888)
- W0VS1.exe (PID: 7992)
- O870X.exe (PID: 4384)
- E9437.exe (PID: 8124)
- 623X2.exe (PID: 2164)
- NV87C.exe (PID: 8128)
- 1HMXM.exe (PID: 6728)
- 1GPF5.exe (PID: 5508)
- 9T2X3.exe (PID: 6872)
- 9FF6V.exe (PID: 272)
- 7L8F3.exe (PID: 7440)
- X5X86.exe (PID: 2104)
- 2EI6W.exe (PID: 7332)
- X11ZD.exe (PID: 7328)
- H83M9.exe (PID: 2512)
- C5O6S.exe (PID: 3568)
- O29W1.exe (PID: 1952)
- F0FZI.exe (PID: 7436)
- 3ZQ3K.exe (PID: 2716)
- 65GW2.exe (PID: 1248)
- 7PB1L.exe (PID: 2580)
- IXJU5.exe (PID: 7756)
- 3FC69.exe (PID: 7632)
- IH88U.exe (PID: 7688)
- 385D5.exe (PID: 7908)
- 077UU.exe (PID: 3392)
- N71JV.exe (PID: 6164)
- 5056Z.exe (PID: 5540)
- YEZFT.exe (PID: 5356)
- 3A1N4.exe (PID: 6740)
- 284M4.exe (PID: 3156)
- 6I57G.exe (PID: 2344)
- J715A.exe (PID: 7348)
- Z41A7.exe (PID: 8008)
- 1B5H5.exe (PID: 6444)
- L67FH.exe (PID: 8180)
- 8611J.exe (PID: 2724)
- L38GI.exe (PID: 8116)
- 04C2B.exe (PID: 7616)
- 71H49.exe (PID: 1128)
- 4LU90.exe (PID: 2964)
- DRNIY.exe (PID: 7304)
- QQ68T.exe (PID: 1080)
- 0PC74.exe (PID: 7244)
- LJ7N7.exe (PID: 7108)
- 7NUST.exe (PID: 7528)
- PKJU0.exe (PID: 7480)
- 2GQCZ.exe (PID: 4896)
- 61596.exe (PID: 7484)
- Z4J88.exe (PID: 3468)
- 2LE92.exe (PID: 7644)
- RJB84.exe (PID: 932)
- 7609I.exe (PID: 7760)
- YCU1Y.exe (PID: 660)
- 44710.exe (PID: 7256)
- 1R00P.exe (PID: 7768)
- 4V6KD.exe (PID: 6048)
- ET5YL.exe (PID: 2700)
- 961WF.exe (PID: 4916)
- FS121.exe (PID: 5392)
- A488N.exe (PID: 7924)
- 3W245.exe (PID: 6156)
- 0U9KU.exe (PID: 1252)
- 52N0T.exe (PID: 5704)
- 2CVR6.exe (PID: 6236)
- QXK1G.exe (PID: 8076)
- C9R03.exe (PID: 8036)
- T5YK7.exe (PID: 564)
- Q0DQ6.exe (PID: 1924)
- 4BJR5.exe (PID: 8068)
- ABDPY.exe (PID: 6300)
- FEU1D.exe (PID: 1540)
- X8M1W.exe (PID: 2636)
- C895R.exe (PID: 3236)
- P3UW3.exe (PID: 8176)
- 6747G.exe (PID: 7464)
- 3WB3H.exe (PID: 8172)
- 2L551.exe (PID: 6004)
- P3Y56.exe (PID: 2820)
- 4W2V0.exe (PID: 4220)
- 061D6.exe (PID: 5124)
- 18K5D.exe (PID: 7656)
- K659K.exe (PID: 5712)
- 8BKZ6.exe (PID: 5192)
- 2X6H2.exe (PID: 5948)
- F800M.exe (PID: 4140)
- 937O9.exe (PID: 5912)
- YA25L.exe (PID: 7316)
- 4QQXF.exe (PID: 7444)
- CT71M.exe (PID: 3320)
- 1OIL0.exe (PID: 6416)
- 553TU.exe (PID: 7840)
- F0A93.exe (PID: 5656)
- 3W7ST.exe (PID: 7812)
- N85R5.exe (PID: 8032)
- 0R1FD.exe (PID: 5368)
- FV7Q7.exe (PID: 7344)
- N3P2Y.exe (PID: 3680)
- 28FW7.exe (PID: 4360)
- 5ZF77.exe (PID: 7984)
- J7Q9F.exe (PID: 3332)
- 9KX70.exe (PID: 4528)
- C678J.exe (PID: 5772)
- A7A9N.exe (PID: 8188)
- 4NF77.exe (PID: 5892)
- Z346S.exe (PID: 6988)
- JQ7P7.exe (PID: 476)
- 6Y9F1.exe (PID: 3020)
- LN85T.exe (PID: 7664)
- M298O.exe (PID: 7792)
- 8HVD8.exe (PID: 3236)
- I3FL1.exe (PID: 272)
- SBNK3.exe (PID: 7232)
- 9OV5D.exe (PID: 7328)
- NXKXZ.exe (PID: 7592)
- M2PP1.exe (PID: 7564)
- 2NL71.exe (PID: 4368)
- 1FA89.exe (PID: 5676)
- M04SW.exe (PID: 7724)
- WZ5R9.exe (PID: 7896)
- 95A69.exe (PID: 7844)
- W1LKP.exe (PID: 7640)
- 6I04B.exe (PID: 1844)
- Z4LWV.exe (PID: 4592)
- 35VT6.exe (PID: 7628)
- 6FWD5.exe (PID: 6452)
- 9NSM8.exe (PID: 7448)
- 3769Y.exe (PID: 7940)
- M70F6.exe (PID: 3680)
- I5G1E.exe (PID: 2408)
- ED3E5.exe (PID: 5368)
- 8672A.exe (PID: 7984)
- G63HD.exe (PID: 5772)
- J318B.exe (PID: 8144)
- Y619C.exe (PID: 4360)
- 3Z6S8.exe (PID: 564)
- 7D55V.exe (PID: 4528)
- DC1YD.exe (PID: 4168)
- C89R8.exe (PID: 1504)
- 8K631.exe (PID: 3056)
- 1185X.exe (PID: 7548)
- FA0M9.exe (PID: 404)
- 3D7SM.exe (PID: 6088)
- 57YAT.exe (PID: 4164)
- P53LK.exe (PID: 2820)
- X7J0M.exe (PID: 7508)
- 6VN85.exe (PID: 7540)
- B96M2.exe (PID: 7612)
- LY9LH.exe (PID: 7100)
- P21S1.exe (PID: 7524)
- T5FTO.exe (PID: 4996)
- V2YGW.exe (PID: 3956)
- NEQ55.exe (PID: 7460)
- 1CJM1.exe (PID: 2564)
- H1U69.exe (PID: 3960)
- L9FOD.exe (PID: 2576)
- G068C.exe (PID: 7720)
- WS76J.exe (PID: 1136)
- X0B43.exe (PID: 7740)
- 9O8A7.exe (PID: 7848)
- T1V2X.exe (PID: 7900)
- 6506L.exe (PID: 5720)
- 9526M.exe (PID: 3392)
- IL89E.exe (PID: 7808)
- 5H918.exe (PID: 1252)
- P7N86.exe (PID: 6164)
- JWIZ5.exe (PID: 8056)
- TXW92.exe (PID: 7712)
- 4X047.exe (PID: 7584)
- RS911.exe (PID: 3156)
- UHBE0.exe (PID: 3696)
- 4C8M4.exe (PID: 8052)
- AYRAJ.exe (PID: 8092)
- K8UY7.exe (PID: 4280)
- TC027.exe (PID: 7960)
- ARVV0.exe (PID: 5652)
- C919F.exe (PID: 1172)
- 16G78.exe (PID: 4720)
- 74274.exe (PID: 7604)
- D97EI.exe (PID: 5872)
- 54KXP.exe (PID: 5884)
- D5234.exe (PID: 7540)
- 7C50O.exe (PID: 7612)
- 12I31.exe (PID: 7508)
- 149RP.exe (PID: 7100)
- 78S5K.exe (PID: 4996)
- 2V531.exe (PID: 7524)
- Q20MZ.exe (PID: 3956)
- 65918.exe (PID: 7460)
- 0V85U.exe (PID: 2564)
- 15521.exe (PID: 3960)
- 93J3Q.exe (PID: 2576)
- WZ0C5.exe (PID: 7720)
- 8J6V7.exe (PID: 7740)
- E6OTH.exe (PID: 7900)
- 0B581.exe (PID: 1136)
- 0P2N0.exe (PID: 7848)
- 06BDB.exe (PID: 5720)
- 7442L.exe (PID: 3392)
- H2N4X.exe (PID: 7808)
- X90FV.exe (PID: 6164)
- 1MFY8.exe (PID: 7584)
- 4XL2Y.exe (PID: 1252)
- P5PAJ.exe (PID: 7712)
- 94T0F.exe (PID: 8056)
- CV758.exe (PID: 3696)
- 795BA.exe (PID: 8164)
- 37SHD.exe (PID: 5604)
- 39119.exe (PID: 8052)
- CRZG7.exe (PID: 7960)
- I386Z.exe (PID: 5652)
- V9JRJ.exe (PID: 4280)
- OI304.exe (PID: 1172)
- 00IL4.exe (PID: 4720)
- 91MQJ.exe (PID: 7604)
- G19D2.exe (PID: 2104)
- 3L324.exe (PID: 7108)
- 840K8.exe (PID: 5884)
- SL4W3.exe (PID: 2800)
- 8HE62.exe (PID: 6972)
- 8023A.exe (PID: 6952)
- 680P5.exe (PID: 7480)
- F0249.exe (PID: 7716)
- 047W6.exe (PID: 2972)
- 271RH.exe (PID: 7588)
- 5P20F.exe (PID: 4668)
- 9F6IY.exe (PID: 7316)
- G9379.exe (PID: 3200)
- J30H6.exe (PID: 4140)
- 3R6F8.exe (PID: 7444)
- 96QJ1.exe (PID: 3320)
- 4JH29.exe (PID: 2720)
- PZT68.exe (PID: 5656)
- J0TI0.exe (PID: 3364)
- W5R8O.exe (PID: 2804)
- W57KL.exe (PID: 7448)
- 5C9UK.exe (PID: 2408)
- QJPK5.exe (PID: 8000)
- TY934.exe (PID: 5584)
- 08F2R.exe (PID: 5480)
- 3RM64.exe (PID: 4360)
- 0S56I.exe (PID: 5772)
- Z0J96.exe (PID: 1656)
- MRA03.exe (PID: 564)
- R69OK.exe (PID: 8144)
- UPE07.exe (PID: 4528)
- 81OPC.exe (PID: 6464)
- N03U4.exe (PID: 5472)
- 4HLI3.exe (PID: 3544)
- V3P3S.exe (PID: 1144)
- PP5S8.exe (PID: 3044)
- K9BZO.exe (PID: 7552)
- IYW45.exe (PID: 2100)
- 8KFU6.exe (PID: 7484)
- 2CD2V.exe (PID: 692)
- 8K2KG.exe (PID: 8104)
- FM69K.exe (PID: 5328)
- GL5V3.exe (PID: 7520)
- 5106J.exe (PID: 7380)
- 5D328.exe (PID: 7312)
- Q3BHF.exe (PID: 3200)
- XHUDG.exe (PID: 4668)
- EP56H.exe (PID: 7316)
- 3OKVT.exe (PID: 7444)
- 3PG3X.exe (PID: 3320)
- 7YOQ4.exe (PID: 2720)
- 18G90.exe (PID: 5656)
- 91204.exe (PID: 2972)
- 80I4B.exe (PID: 4140)
- D1MY8.exe (PID: 6264)
- 2QUM2.exe (PID: 7872)
- BO166.exe (PID: 6840)
- 251I1.exe (PID: 1284)
- I3K71.exe (PID: 6640)
INFO
Checks supported languages
- 41a95b2ea5f1469a0b71cdf6cf7d3a4f922a50d0afe78479b4470c9b5ac1dd71.exe (PID: 7412)
- 05YZJ.exe (PID: 7460)
- PIJ5L.exe (PID: 7512)
- AE0TB.exe (PID: 7564)
- T7IA7.exe (PID: 7688)
- 27XT9.exe (PID: 7620)
- X45B2.exe (PID: 7764)
- Y57IT.exe (PID: 7888)
- 1P19U.exe (PID: 7976)
- OVCW2.exe (PID: 8108)
- SG56W.exe (PID: 8040)
- ACCNF.exe (PID: 4104)
- 674L6.exe (PID: 1924)
- 3B451.exe (PID: 7436)
- S861Y.exe (PID: 8160)
- 713X7.exe (PID: 7528)
- 152D8.exe (PID: 7580)
- Y25VX.exe (PID: 7632)
- Z06ZC.exe (PID: 7872)
- M5XB6.exe (PID: 7788)
- 44YF5.exe (PID: 7824)
- 46195.exe (PID: 8000)
- 910G6.exe (PID: 2344)
- VPHQB.exe (PID: 8040)
- IE44A.exe (PID: 8112)
- I9LHP.exe (PID: 7976)
- 32VI8.exe (PID: 7240)
- GXE5N.exe (PID: 7492)
- 6U8KU.exe (PID: 3236)
- 15P26.exe (PID: 4900)
- 890SH.exe (PID: 4220)
- 6JH56.exe (PID: 7436)
- G74CB.exe (PID: 7528)
- 3YD6H.exe (PID: 3400)
- K469T.exe (PID: 7640)
- D50UW.exe (PID: 7580)
- 0858S.exe (PID: 7740)
- CA31T.exe (PID: 7696)
- 4T0HE.exe (PID: 7476)
- 9MT7S.exe (PID: 6356)
- 4M7VA.exe (PID: 7472)
- 5Q6HZ.exe (PID: 4916)
- MPEF6.exe (PID: 7812)
- UT400.exe (PID: 892)
- NM896.exe (PID: 7796)
- X9IAD.exe (PID: 8020)
- GMIAC.exe (PID: 8076)
- 744H4.exe (PID: 8144)
- 16811.exe (PID: 2104)
- ZO289.exe (PID: 5868)
- 8142Y.exe (PID: 2740)
- Y2W2E.exe (PID: 5408)
- TS8AA.exe (PID: 5244)
- EU543.exe (PID: 7588)
- 1LZM5.exe (PID: 5948)
- 7GEP8.exe (PID: 7460)
- GT2UA.exe (PID: 4452)
- 4J6B9.exe (PID: 7608)
- 4L057.exe (PID: 1252)
- JF5M3.exe (PID: 3364)
- 68VS4.exe (PID: 7676)
- X8Y91.exe (PID: 5696)
- 388P6.exe (PID: 4592)
- 0DL76.exe (PID: 7852)
- 060G0.exe (PID: 7872)
- 4J017.exe (PID: 3680)
- 72943.exe (PID: 5196)
- Z9RH6.exe (PID: 8084)
- 49BXW.exe (PID: 8116)
- FUD95.exe (PID: 7960)
- 2QB3V.exe (PID: 8172)
- L0XJ5.exe (PID: 6880)
- 3A2U6.exe (PID: 4064)
- TTZB9.exe (PID: 7480)
- 8RXJ5.exe (PID: 6728)
- LYRTA.exe (PID: 7252)
- 00K89.exe (PID: 7520)
- 33QO0.exe (PID: 7568)
- S87J9.exe (PID: 6260)
- R1P3C.exe (PID: 7616)
- GW50J.exe (PID: 1276)
- T2452.exe (PID: 3468)
- JR2BY.exe (PID: 2408)
- 4Z068.exe (PID: 7680)
- 5B7V6.exe (PID: 7868)
- H1UGV.exe (PID: 7788)
- Y0FW1.exe (PID: 5656)
- 42THZ.exe (PID: 7992)
- 6P7QP.exe (PID: 7940)
- 61FDE.exe (PID: 6452)
- RR2IL.exe (PID: 3332)
- 5QFG1.exe (PID: 8040)
- 846H9.exe (PID: 8136)
- 233DV.exe (PID: 4064)
- 0JBT6.exe (PID: 4264)
- 2287R.exe (PID: 7796)
- 4K596.exe (PID: 7612)
- JGM62.exe (PID: 7496)
- GJ1EW.exe (PID: 7560)
- 4W41K.exe (PID: 7668)
- FDN4D.exe (PID: 7576)
- 14887.exe (PID: 5712)
- 135GH.exe (PID: 3100)
- H4AMG.exe (PID: 1252)
- 4AL80.exe (PID: 7624)
- 8VT67.exe (PID: 7676)
- 3PL9G.exe (PID: 5696)
- 44W55.exe (PID: 5224)
- 9GGQ0.exe (PID: 7924)
- 7N537.exe (PID: 3460)
- QQ9QW.exe (PID: 7916)
- 33C3V.exe (PID: 1140)
- 29N30.exe (PID: 8092)
- CJ2BA.exe (PID: 6376)
- 704N6.exe (PID: 8020)
- 9607X.exe (PID: 6776)
- 6N466.exe (PID: 7796)
- 936IC.exe (PID: 476)
- RY1B7.exe (PID: 2852)
- Y8FJ3.exe (PID: 4900)
- 6WNR9.exe (PID: 6676)
- 45VQG.exe (PID: 7556)
- I7J3C.exe (PID: 7460)
- HVF03.exe (PID: 4668)
- I0C6M.exe (PID: 7708)
- K4CPT.exe (PID: 5580)
- HA572.exe (PID: 5268)
- S9G16.exe (PID: 3100)
- W9FNS.exe (PID: 7768)
- 384M8.exe (PID: 7852)
- N0944.exe (PID: 5368)
- 2WJ83.exe (PID: 7692)
- LC3NX.exe (PID: 7840)
- HA7IB.exe (PID: 5772)
- W1UXJ.exe (PID: 7864)
- A1OW3.exe (PID: 2764)
- 1Z9YK.exe (PID: 8052)
- J159E.exe (PID: 8024)
- TLJU6.exe (PID: 5288)
- 1X968.exe (PID: 8180)
- 697GY.exe (PID: 5660)
- 7W936.exe (PID: 1948)
- REBR8.exe (PID: 7276)
- 3G558.exe (PID: 2164)
- L5A71.exe (PID: 7332)
- VJALT.exe (PID: 2944)
- F3AL2.exe (PID: 7536)
- 2BS07.exe (PID: 2104)
- 4N883.exe (PID: 5504)
- WT72A.exe (PID: 6260)
- EX80H.exe (PID: 5900)
- 7ML00.exe (PID: 7436)
- 93465.exe (PID: 5040)
- IM8L2.exe (PID: 7700)
- 3O348.exe (PID: 7448)
- 8J424.exe (PID: 5704)
- 161WC.exe (PID: 7624)
- ZYG4A.exe (PID: 7676)
- 5008Z.exe (PID: 5696)
- M150Y.exe (PID: 7856)
- JC7BE.exe (PID: 7976)
- 72223.exe (PID: 4400)
- 1M300.exe (PID: 7352)
- 15OE9.exe (PID: 7996)
- 76I5W.exe (PID: 8044)
- RVL17.exe (PID: 6376)
- 21JZY.exe (PID: 8128)
- SMWI4.exe (PID: 476)
- P37R8.exe (PID: 6776)
- USS5N.exe (PID: 7796)
- 1000T.exe (PID: 3944)
- VPOBX.exe (PID: 7664)
- Z7QVP.exe (PID: 5244)
- GBJ33.exe (PID: 7516)
- 4T3G5.exe (PID: 4244)
- 34C0T.exe (PID: 7484)
- QZ3E8.exe (PID: 8104)
- 3MQHV.exe (PID: 4668)
- 3P7L5.exe (PID: 4452)
- U758A.exe (PID: 7708)
- 177WJ.exe (PID: 5580)
- UB1D3.exe (PID: 7628)
- P1ZQ3.exe (PID: 7784)
- DI9J0.exe (PID: 6164)
- 95758.exe (PID: 7904)
- SIN7D.exe (PID: 7816)
- 7D5SU.exe (PID: 7892)
- 7CQ7F.exe (PID: 2344)
- G587W.exe (PID: 7944)
- S87C9.exe (PID: 7348)
- 4SIOD.exe (PID: 7952)
- 6V9N2.exe (PID: 7960)
- 1V809.exe (PID: 3984)
- 70NQ3.exe (PID: 3076)
- 60Y4Y.exe (PID: 5376)
- 2AZV3.exe (PID: 2036)
- 2BNS9.exe (PID: 8108)
- 72MNC.exe (PID: 1576)
- 1S9LN.exe (PID: 4104)
- SAI99.exe (PID: 2880)
- 13I69.exe (PID: 5408)
- YV5R1.exe (PID: 6676)
- N10GX.exe (PID: 7556)
- 95XPK.exe (PID: 7572)
- NPB62.exe (PID: 3956)
- GRW60.exe (PID: 7724)
- 22032.exe (PID: 7748)
- 8UHII.exe (PID: 5268)
- D6350.exe (PID: 7836)
- 9H1Q1.exe (PID: 3996)
- PF509.exe (PID: 1136)
- 9N3CG.exe (PID: 7848)
- WAJIF.exe (PID: 7820)
- 4WQQE.exe (PID: 7788)
- 99141.exe (PID: 6264)
- V9519.exe (PID: 7888)
- 35L5E.exe (PID: 4280)
- BLD7F.exe (PID: 3460)
- 3VSS3.exe (PID: 2344)
- 1TL17.exe (PID: 8068)
- D3WN4.exe (PID: 8048)
- 94R76.exe (PID: 8152)
- GOV5K.exe (PID: 3236)
- C3HC9.exe (PID: 2312)
- D96QW.exe (PID: 1080)
- I6RV4.exe (PID: 2220)
- I6B09.exe (PID: 6940)
- 9RM87.exe (PID: 7332)
- KIXH4.exe (PID: 2760)
- 9PAFD.exe (PID: 7596)
- 460IW.exe (PID: 7380)
- S07XZ.exe (PID: 1688)
- 8G99B.exe (PID: 5948)
- 607S5.exe (PID: 7096)
- G3342.exe (PID: 2008)
- DA5TX.exe (PID: 7640)
- L0C14.exe (PID: 5040)
- BPCB1.exe (PID: 3996)
- JL3JW.exe (PID: 7880)
- 5475W.exe (PID: 6252)
- 1T831.exe (PID: 1836)
- M3414.exe (PID: 7788)
- WN8FW.exe (PID: 3680)
- J0Z4I.exe (PID: 7888)
- TAZN8.exe (PID: 8008)
- W9U53.exe (PID: 4280)
- 6Y84Z.exe (PID: 8068)
- YUIXG.exe (PID: 8048)
- O30T9.exe (PID: 3460)
- 05NP7.exe (PID: 800)
- 0FKP5.exe (PID: 1384)
- 066PD.exe (PID: 4720)
- 505OB.exe (PID: 6504)
- FN8F2.exe (PID: 7492)
- K7LN5.exe (PID: 2740)
- 2541J.exe (PID: 7328)
- 9L57J.exe (PID: 1952)
- O1HB2.exe (PID: 7560)
- 4E61L.exe (PID: 2900)
- 1209L.exe (PID: 7668)
- 2XSO0.exe (PID: 3568)
- QI603.exe (PID: 7688)
- I9R07.exe (PID: 4668)
- I59UD.exe (PID: 7784)
- 8SZ85.exe (PID: 7744)
- 4TKS5.exe (PID: 5452)
- 022B9.exe (PID: 4884)
- DBR9D.exe (PID: 1284)
- C896I.exe (PID: 1520)
- B80HR.exe (PID: 7912)
- 2A5F5.exe (PID: 5704)
- 9E6N9.exe (PID: 7712)
- 0037G.exe (PID: 7824)
- 07XOW.exe (PID: 4360)
- MRL2Z.exe (PID: 7988)
- 1746F.exe (PID: 7916)
- Y0JG0.exe (PID: 4784)
- 1B2N3.exe (PID: 8176)
- 9Y2AJ.exe (PID: 6964)
- 89YII.exe (PID: 5956)
- APF67.exe (PID: 8112)
- 1ZTZW.exe (PID: 4760)
- H00P7.exe (PID: 7540)
- CX629.exe (PID: 1148)
- 3U9HZ.exe (PID: 5500)
- QGR2G.exe (PID: 1264)
- XQWA4.exe (PID: 7588)
- 0T70H.exe (PID: 2100)
- 90108.exe (PID: 3400)
- 31Z24.exe (PID: 7660)
- 098VM.exe (PID: 2316)
- OY28S.exe (PID: 7580)
- 1E928.exe (PID: 7736)
- 2DC97.exe (PID: 4452)
- VR3XP.exe (PID: 4916)
- T8GF2.exe (PID: 6156)
- QU316.exe (PID: 7864)
- 1T9QO.exe (PID: 7868)
- 97R42.exe (PID: 7924)
- 4T6D5.exe (PID: 5392)
- EXY1D.exe (PID: 5704)
- F3JY5.exe (PID: 5584)
- 54Y4E.exe (PID: 1252)
- YQU4Y.exe (PID: 7348)
- I1U0X.exe (PID: 8008)
- 5AJX5.exe (PID: 2344)
- QYC88.exe (PID: 8144)
- T0YZ6.exe (PID: 2636)
- 7UKT5.exe (PID: 8120)
- ZI8HO.exe (PID: 1540)
- 73A7I.exe (PID: 8176)
- 5VOT0.exe (PID: 7796)
- H2GM5.exe (PID: 8024)
- B90C3.exe (PID: 5956)
- YT95L.exe (PID: 7496)
- 8M27C.exe (PID: 1148)
- I4R98.exe (PID: 7664)
- M81O1.exe (PID: 7560)
- CF2W8.exe (PID: 7436)
- 567H4.exe (PID: 7100)
- 4UNDC.exe (PID: 2580)
- 081VV.exe (PID: 7660)
- L1V69.exe (PID: 7756)
- 4BYIC.exe (PID: 7632)
- N7886.exe (PID: 1248)
- 58NY3.exe (PID: 7688)
- 90GQJ.exe (PID: 7616)
- W5N73.exe (PID: 7784)
- 3CBUL.exe (PID: 3392)
- 6886X.exe (PID: 6164)
- OSV3P.exe (PID: 7908)
- QS4B1.exe (PID: 5540)
- 3L9Y6.exe (PID: 5356)
- S040W.exe (PID: 3148)
- C1304.exe (PID: 6740)
- 5W8TX.exe (PID: 7888)
- W0VS1.exe (PID: 7992)
- NV87C.exe (PID: 8128)
- E9437.exe (PID: 8124)
- O870X.exe (PID: 4384)
- 623X2.exe (PID: 2164)
- 9T2X3.exe (PID: 6872)
- 1GPF5.exe (PID: 5508)
- 1HMXM.exe (PID: 6728)
- 9FF6V.exe (PID: 272)
- 7L8F3.exe (PID: 7440)
- X5X86.exe (PID: 2104)
- X11ZD.exe (PID: 7328)
- O29W1.exe (PID: 1952)
- 2EI6W.exe (PID: 7332)
- C5O6S.exe (PID: 3568)
- H83M9.exe (PID: 2512)
- F0FZI.exe (PID: 7436)
- 3ZQ3K.exe (PID: 2716)
- 7PB1L.exe (PID: 2580)
- IXJU5.exe (PID: 7756)
- IH88U.exe (PID: 7688)
- 71H49.exe (PID: 1128)
- 3FC69.exe (PID: 7632)
- 04C2B.exe (PID: 7616)
- 385D5.exe (PID: 7908)
- 077UU.exe (PID: 3392)
- 5056Z.exe (PID: 5540)
- N71JV.exe (PID: 6164)
- YEZFT.exe (PID: 5356)
- 3A1N4.exe (PID: 6740)
- 284M4.exe (PID: 3156)
- J715A.exe (PID: 7348)
- 6I57G.exe (PID: 2344)
- Z41A7.exe (PID: 8008)
- 1B5H5.exe (PID: 6444)
- L38GI.exe (PID: 8116)
- 65GW2.exe (PID: 1248)
- L67FH.exe (PID: 8180)
- 8611J.exe (PID: 2724)
- 0PC74.exe (PID: 7244)
- 4LU90.exe (PID: 2964)
- DRNIY.exe (PID: 7304)
- 61596.exe (PID: 7484)
- LJ7N7.exe (PID: 7108)
- QQ68T.exe (PID: 1080)
- 2GQCZ.exe (PID: 4896)
- PKJU0.exe (PID: 7480)
- 7NUST.exe (PID: 7528)
- RJB84.exe (PID: 932)
- Z4J88.exe (PID: 3468)
- 2LE92.exe (PID: 7644)
- 7609I.exe (PID: 7760)
- 44710.exe (PID: 7256)
- YCU1Y.exe (PID: 660)
- 3W245.exe (PID: 6156)
- 961WF.exe (PID: 4916)
- ET5YL.exe (PID: 2700)
- 1R00P.exe (PID: 7768)
- 4V6KD.exe (PID: 6048)
- A488N.exe (PID: 7924)
- FS121.exe (PID: 5392)
- 0U9KU.exe (PID: 1252)
- 52N0T.exe (PID: 5704)
- 2CVR6.exe (PID: 6236)
- Q0DQ6.exe (PID: 1924)
- QXK1G.exe (PID: 8076)
- ABDPY.exe (PID: 6300)
- FEU1D.exe (PID: 1540)
- C9R03.exe (PID: 8036)
- P3UW3.exe (PID: 8176)
- X8M1W.exe (PID: 2636)
- C895R.exe (PID: 3236)
- 4BJR5.exe (PID: 8068)
- P3Y56.exe (PID: 2820)
- 3WB3H.exe (PID: 8172)
- T5YK7.exe (PID: 564)
- 2L551.exe (PID: 6004)
- 6747G.exe (PID: 7464)
- 4W2V0.exe (PID: 4220)
- K659K.exe (PID: 5712)
- 061D6.exe (PID: 5124)
- 18K5D.exe (PID: 7656)
- 8BKZ6.exe (PID: 5192)
- 937O9.exe (PID: 5912)
- 2X6H2.exe (PID: 5948)
- F800M.exe (PID: 4140)
- YA25L.exe (PID: 7316)
- F0A93.exe (PID: 5656)
- 4QQXF.exe (PID: 7444)
- CT71M.exe (PID: 3320)
- 553TU.exe (PID: 7840)
- 1OIL0.exe (PID: 6416)
- N85R5.exe (PID: 8032)
- FV7Q7.exe (PID: 7344)
- 3W7ST.exe (PID: 7812)
- 0R1FD.exe (PID: 5368)
- 5ZF77.exe (PID: 7984)
- N3P2Y.exe (PID: 3680)
- C678J.exe (PID: 5772)
- 28FW7.exe (PID: 4360)
- 4NF77.exe (PID: 5892)
- J7Q9F.exe (PID: 3332)
- 9KX70.exe (PID: 4528)
- Z346S.exe (PID: 6988)
- A7A9N.exe (PID: 8188)
- JQ7P7.exe (PID: 476)
- 6Y9F1.exe (PID: 3020)
- 8HVD8.exe (PID: 3236)
- LN85T.exe (PID: 7664)
- M298O.exe (PID: 7792)
- SBNK3.exe (PID: 7232)
- I3FL1.exe (PID: 272)
- 9OV5D.exe (PID: 7328)
- NXKXZ.exe (PID: 7592)
- M2PP1.exe (PID: 7564)
- 2NL71.exe (PID: 4368)
- W1LKP.exe (PID: 7640)
- 1FA89.exe (PID: 5676)
- 95A69.exe (PID: 7844)
- M04SW.exe (PID: 7724)
- WZ5R9.exe (PID: 7896)
- 6I04B.exe (PID: 1844)
- Z4LWV.exe (PID: 4592)
- 6FWD5.exe (PID: 6452)
- 35VT6.exe (PID: 7628)
- I5G1E.exe (PID: 2408)
- 9NSM8.exe (PID: 7448)
- 3769Y.exe (PID: 7940)
- M70F6.exe (PID: 3680)
- 8672A.exe (PID: 7984)
- ED3E5.exe (PID: 5368)
- J318B.exe (PID: 8144)
- 7D55V.exe (PID: 4528)
- Y619C.exe (PID: 4360)
- G63HD.exe (PID: 5772)
- 3Z6S8.exe (PID: 564)
- DC1YD.exe (PID: 4168)
- C89R8.exe (PID: 1504)
- 1185X.exe (PID: 7548)
- 8K631.exe (PID: 3056)
- FA0M9.exe (PID: 404)
- 57YAT.exe (PID: 4164)
- P53LK.exe (PID: 2820)
- 3D7SM.exe (PID: 6088)
- B96M2.exe (PID: 7612)
- LY9LH.exe (PID: 7100)
- X7J0M.exe (PID: 7508)
- 6VN85.exe (PID: 7540)
- T5FTO.exe (PID: 4996)
- P21S1.exe (PID: 7524)
- V2YGW.exe (PID: 3956)
- L9FOD.exe (PID: 2576)
- NEQ55.exe (PID: 7460)
- H1U69.exe (PID: 3960)
- X0B43.exe (PID: 7740)
- 1CJM1.exe (PID: 2564)
- WS76J.exe (PID: 1136)
- G068C.exe (PID: 7720)
- T1V2X.exe (PID: 7900)
- IL89E.exe (PID: 7808)
- 9O8A7.exe (PID: 7848)
- 9526M.exe (PID: 3392)
- P7N86.exe (PID: 6164)
- 6506L.exe (PID: 5720)
- 5H918.exe (PID: 1252)
- 4X047.exe (PID: 7584)
- JWIZ5.exe (PID: 8056)
- UHBE0.exe (PID: 3696)
- 4C8M4.exe (PID: 8052)
- RS911.exe (PID: 3156)
- TXW92.exe (PID: 7712)
- AYRAJ.exe (PID: 8092)
- K8UY7.exe (PID: 4280)
- TC027.exe (PID: 7960)
- ARVV0.exe (PID: 5652)
- 16G78.exe (PID: 4720)
- 74274.exe (PID: 7604)
- C919F.exe (PID: 1172)
- 54KXP.exe (PID: 5884)
- D97EI.exe (PID: 5872)
- 12I31.exe (PID: 7508)
- 7C50O.exe (PID: 7612)
- 149RP.exe (PID: 7100)
- D5234.exe (PID: 7540)
- 78S5K.exe (PID: 4996)
- 2V531.exe (PID: 7524)
- Q20MZ.exe (PID: 3956)
- 93J3Q.exe (PID: 2576)
- 65918.exe (PID: 7460)
- 15521.exe (PID: 3960)
- 8J6V7.exe (PID: 7740)
- 0V85U.exe (PID: 2564)
- WZ0C5.exe (PID: 7720)
- 0B581.exe (PID: 1136)
- E6OTH.exe (PID: 7900)
- H2N4X.exe (PID: 7808)
- 0P2N0.exe (PID: 7848)
- 7442L.exe (PID: 3392)
- 06BDB.exe (PID: 5720)
- 4XL2Y.exe (PID: 1252)
- 94T0F.exe (PID: 8056)
- X90FV.exe (PID: 6164)
- 1MFY8.exe (PID: 7584)
- P5PAJ.exe (PID: 7712)
- 37SHD.exe (PID: 5604)
- 39119.exe (PID: 8052)
- 795BA.exe (PID: 8164)
- V9JRJ.exe (PID: 4280)
- CV758.exe (PID: 3696)
- CRZG7.exe (PID: 7960)
- I386Z.exe (PID: 5652)
- 00IL4.exe (PID: 4720)
- 91MQJ.exe (PID: 7604)
- OI304.exe (PID: 1172)
- 840K8.exe (PID: 5884)
- 3L324.exe (PID: 7108)
- 680P5.exe (PID: 7480)
- G19D2.exe (PID: 2104)
- 8HE62.exe (PID: 6972)
- SL4W3.exe (PID: 2800)
- 8023A.exe (PID: 6952)
- 047W6.exe (PID: 2972)
- F0249.exe (PID: 7716)
- 271RH.exe (PID: 7588)
- 9F6IY.exe (PID: 7316)
- J30H6.exe (PID: 4140)
- 5P20F.exe (PID: 4668)
- G9379.exe (PID: 3200)
- 3R6F8.exe (PID: 7444)
- 96QJ1.exe (PID: 3320)
- PZT68.exe (PID: 5656)
- 4JH29.exe (PID: 2720)
- J0TI0.exe (PID: 3364)
- W57KL.exe (PID: 7448)
- W5R8O.exe (PID: 2804)
- 5C9UK.exe (PID: 2408)
- TY934.exe (PID: 5584)
- 08F2R.exe (PID: 5480)
- QJPK5.exe (PID: 8000)
- 0S56I.exe (PID: 5772)
- Z0J96.exe (PID: 1656)
- 3RM64.exe (PID: 4360)
- MRA03.exe (PID: 564)
- R69OK.exe (PID: 8144)
- UPE07.exe (PID: 4528)
- 81OPC.exe (PID: 6464)
- N03U4.exe (PID: 5472)
- K9BZO.exe (PID: 7552)
- 4HLI3.exe (PID: 3544)
- PP5S8.exe (PID: 3044)
- V3P3S.exe (PID: 1144)
- IYW45.exe (PID: 2100)
- 2CD2V.exe (PID: 692)
- 8KFU6.exe (PID: 7484)
- FM69K.exe (PID: 5328)
- 5106J.exe (PID: 7380)
- 8K2KG.exe (PID: 8104)
- 91204.exe (PID: 2972)
- GL5V3.exe (PID: 7520)
- 5D328.exe (PID: 7312)
- Q3BHF.exe (PID: 3200)
Reads the computer name
- 41a95b2ea5f1469a0b71cdf6cf7d3a4f922a50d0afe78479b4470c9b5ac1dd71.exe (PID: 7412)
- 05YZJ.exe (PID: 7460)
- PIJ5L.exe (PID: 7512)
- T7IA7.exe (PID: 7688)
- AE0TB.exe (PID: 7564)
- 27XT9.exe (PID: 7620)
- 1P19U.exe (PID: 7976)
- X45B2.exe (PID: 7764)
- Y57IT.exe (PID: 7888)
- SG56W.exe (PID: 8040)
- OVCW2.exe (PID: 8108)
- S861Y.exe (PID: 8160)
- 674L6.exe (PID: 1924)
- 3B451.exe (PID: 7436)
- ACCNF.exe (PID: 4104)
- 713X7.exe (PID: 7528)
- 152D8.exe (PID: 7580)
- Y25VX.exe (PID: 7632)
- Z06ZC.exe (PID: 7872)
- M5XB6.exe (PID: 7788)
- 44YF5.exe (PID: 7824)
- 46195.exe (PID: 8000)
- VPHQB.exe (PID: 8040)
- I9LHP.exe (PID: 7976)
- IE44A.exe (PID: 8112)
- 6U8KU.exe (PID: 3236)
- 32VI8.exe (PID: 7240)
- GXE5N.exe (PID: 7492)
- 15P26.exe (PID: 4900)
- 890SH.exe (PID: 4220)
- 6JH56.exe (PID: 7436)
- G74CB.exe (PID: 7528)
- 3YD6H.exe (PID: 3400)
- K469T.exe (PID: 7640)
- D50UW.exe (PID: 7580)
- 0858S.exe (PID: 7740)
- CA31T.exe (PID: 7696)
- 4T0HE.exe (PID: 7476)
- 4M7VA.exe (PID: 7472)
- 9MT7S.exe (PID: 6356)
- 5Q6HZ.exe (PID: 4916)
- UT400.exe (PID: 892)
- MPEF6.exe (PID: 7812)
- NM896.exe (PID: 7796)
- X9IAD.exe (PID: 8020)
- GMIAC.exe (PID: 8076)
- 910G6.exe (PID: 2344)
- 744H4.exe (PID: 8144)
- 16811.exe (PID: 2104)
- ZO289.exe (PID: 5868)
- 8142Y.exe (PID: 2740)
- TS8AA.exe (PID: 5244)
- Y2W2E.exe (PID: 5408)
- EU543.exe (PID: 7588)
- 1LZM5.exe (PID: 5948)
- 7GEP8.exe (PID: 7460)
- GT2UA.exe (PID: 4452)
- 4J6B9.exe (PID: 7608)
- 4L057.exe (PID: 1252)
- 68VS4.exe (PID: 7676)
- JF5M3.exe (PID: 3364)
- 0DL76.exe (PID: 7852)
- X8Y91.exe (PID: 5696)
- 388P6.exe (PID: 4592)
- 4J017.exe (PID: 3680)
- 72943.exe (PID: 5196)
- 060G0.exe (PID: 7872)
- Z9RH6.exe (PID: 8084)
- 49BXW.exe (PID: 8116)
- FUD95.exe (PID: 7960)
- 2QB3V.exe (PID: 8172)
- 3A2U6.exe (PID: 4064)
- L0XJ5.exe (PID: 6880)
- 8RXJ5.exe (PID: 6728)
- TTZB9.exe (PID: 7480)
- LYRTA.exe (PID: 7252)
- 00K89.exe (PID: 7520)
- 33QO0.exe (PID: 7568)
- S87J9.exe (PID: 6260)
- T2452.exe (PID: 3468)
- R1P3C.exe (PID: 7616)
- GW50J.exe (PID: 1276)
- 5B7V6.exe (PID: 7868)
- Y0FW1.exe (PID: 5656)
- JR2BY.exe (PID: 2408)
- 4Z068.exe (PID: 7680)
- H1UGV.exe (PID: 7788)
- RR2IL.exe (PID: 3332)
- 6P7QP.exe (PID: 7940)
- 61FDE.exe (PID: 6452)
- 846H9.exe (PID: 8136)
- 42THZ.exe (PID: 7992)
- 5QFG1.exe (PID: 8040)
- 2287R.exe (PID: 7796)
- GJ1EW.exe (PID: 7560)
- 233DV.exe (PID: 4064)
- 14887.exe (PID: 5712)
- JGM62.exe (PID: 7496)
- 4K596.exe (PID: 7612)
- 0JBT6.exe (PID: 4264)
- FDN4D.exe (PID: 7576)
- 135GH.exe (PID: 3100)
- 4W41K.exe (PID: 7668)
- H4AMG.exe (PID: 1252)
- 4AL80.exe (PID: 7624)
- 8VT67.exe (PID: 7676)
- 3PL9G.exe (PID: 5696)
- 9GGQ0.exe (PID: 7924)
- 44W55.exe (PID: 5224)
- 7N537.exe (PID: 3460)
- QQ9QW.exe (PID: 7916)
- 33C3V.exe (PID: 1140)
- 704N6.exe (PID: 8020)
- CJ2BA.exe (PID: 6376)
- 29N30.exe (PID: 8092)
- 9607X.exe (PID: 6776)
- 6N466.exe (PID: 7796)
- RY1B7.exe (PID: 2852)
- 936IC.exe (PID: 476)
- Y8FJ3.exe (PID: 4900)
- 6WNR9.exe (PID: 6676)
- I7J3C.exe (PID: 7460)
- HVF03.exe (PID: 4668)
- I0C6M.exe (PID: 7708)
- 45VQG.exe (PID: 7556)
- HA572.exe (PID: 5268)
- S9G16.exe (PID: 3100)
- K4CPT.exe (PID: 5580)
- W1UXJ.exe (PID: 7864)
- LC3NX.exe (PID: 7840)
- N0944.exe (PID: 5368)
- W9FNS.exe (PID: 7768)
- 2WJ83.exe (PID: 7692)
- 384M8.exe (PID: 7852)
- HA7IB.exe (PID: 5772)
- A1OW3.exe (PID: 2764)
- 1Z9YK.exe (PID: 8052)
- TLJU6.exe (PID: 5288)
- J159E.exe (PID: 8024)
- 697GY.exe (PID: 5660)
- 1X968.exe (PID: 8180)
- 3G558.exe (PID: 2164)
- 7W936.exe (PID: 1948)
- REBR8.exe (PID: 7276)
- 2BS07.exe (PID: 2104)
- L5A71.exe (PID: 7332)
- VJALT.exe (PID: 2944)
- F3AL2.exe (PID: 7536)
- 7ML00.exe (PID: 7436)
- 4N883.exe (PID: 5504)
- WT72A.exe (PID: 6260)
- 93465.exe (PID: 5040)
- IM8L2.exe (PID: 7700)
- 3O348.exe (PID: 7448)
- EX80H.exe (PID: 5900)
- 8J424.exe (PID: 5704)
- 161WC.exe (PID: 7624)
- ZYG4A.exe (PID: 7676)
- M150Y.exe (PID: 7856)
- 15OE9.exe (PID: 7996)
- 5008Z.exe (PID: 5696)
- 72223.exe (PID: 4400)
- 1M300.exe (PID: 7352)
- JC7BE.exe (PID: 7976)
- 76I5W.exe (PID: 8044)
- 21JZY.exe (PID: 8128)
- RVL17.exe (PID: 6376)
- P37R8.exe (PID: 6776)
- USS5N.exe (PID: 7796)
- SMWI4.exe (PID: 476)
- 1000T.exe (PID: 3944)
- VPOBX.exe (PID: 7664)
- 34C0T.exe (PID: 7484)
- Z7QVP.exe (PID: 5244)
- GBJ33.exe (PID: 7516)
- 3P7L5.exe (PID: 4452)
- 3MQHV.exe (PID: 4668)
- 4T3G5.exe (PID: 4244)
- QZ3E8.exe (PID: 8104)
- U758A.exe (PID: 7708)
- 177WJ.exe (PID: 5580)
- DI9J0.exe (PID: 6164)
- P1ZQ3.exe (PID: 7784)
- UB1D3.exe (PID: 7628)
- 95758.exe (PID: 7904)
- SIN7D.exe (PID: 7816)
- 7D5SU.exe (PID: 7892)
- G587W.exe (PID: 7944)
- 7CQ7F.exe (PID: 2344)
- S87C9.exe (PID: 7348)
- 4SIOD.exe (PID: 7952)
- 6V9N2.exe (PID: 7960)
- 1V809.exe (PID: 3984)
- 70NQ3.exe (PID: 3076)
- 2AZV3.exe (PID: 2036)
- 2BNS9.exe (PID: 8108)
- 60Y4Y.exe (PID: 5376)
- 72MNC.exe (PID: 1576)
- 1S9LN.exe (PID: 4104)
- SAI99.exe (PID: 2880)
- 13I69.exe (PID: 5408)
- YV5R1.exe (PID: 6676)
- N10GX.exe (PID: 7556)
- NPB62.exe (PID: 3956)
- GRW60.exe (PID: 7724)
- 95XPK.exe (PID: 7572)
- 8UHII.exe (PID: 5268)
- D6350.exe (PID: 7836)
- 22032.exe (PID: 7748)
- PF509.exe (PID: 1136)
- 9N3CG.exe (PID: 7848)
- WAJIF.exe (PID: 7820)
- 9H1Q1.exe (PID: 3996)
- 4WQQE.exe (PID: 7788)
- 99141.exe (PID: 6264)
- BLD7F.exe (PID: 3460)
- 3VSS3.exe (PID: 2344)
- V9519.exe (PID: 7888)
- 1TL17.exe (PID: 8068)
- D3WN4.exe (PID: 8048)
- 35L5E.exe (PID: 4280)
- 94R76.exe (PID: 8152)
- GOV5K.exe (PID: 3236)
- C3HC9.exe (PID: 2312)
- D96QW.exe (PID: 1080)
- I6RV4.exe (PID: 2220)
- I6B09.exe (PID: 6940)
- KIXH4.exe (PID: 2760)
- 9PAFD.exe (PID: 7596)
- 9RM87.exe (PID: 7332)
- S07XZ.exe (PID: 1688)
- 8G99B.exe (PID: 5948)
- 460IW.exe (PID: 7380)
- 607S5.exe (PID: 7096)
- G3342.exe (PID: 2008)
- DA5TX.exe (PID: 7640)
- BPCB1.exe (PID: 3996)
- JL3JW.exe (PID: 7880)
- L0C14.exe (PID: 5040)
- 5475W.exe (PID: 6252)
- 1T831.exe (PID: 1836)
- M3414.exe (PID: 7788)
- J0Z4I.exe (PID: 7888)
- TAZN8.exe (PID: 8008)
- WN8FW.exe (PID: 3680)
- O30T9.exe (PID: 3460)
- W9U53.exe (PID: 4280)
- 6Y84Z.exe (PID: 8068)
- 0FKP5.exe (PID: 1384)
- 066PD.exe (PID: 4720)
- YUIXG.exe (PID: 8048)
- 05NP7.exe (PID: 800)
- 505OB.exe (PID: 6504)
- FN8F2.exe (PID: 7492)
- 2541J.exe (PID: 7328)
- 9L57J.exe (PID: 1952)
- O1HB2.exe (PID: 7560)
- K7LN5.exe (PID: 2740)
- 2XSO0.exe (PID: 3568)
- 4E61L.exe (PID: 2900)
- 1209L.exe (PID: 7668)
- 8SZ85.exe (PID: 7744)
- I9R07.exe (PID: 4668)
- QI603.exe (PID: 7688)
- I59UD.exe (PID: 7784)
- 4TKS5.exe (PID: 5452)
- 022B9.exe (PID: 4884)
- DBR9D.exe (PID: 1284)
- C896I.exe (PID: 1520)
- B80HR.exe (PID: 7912)
- 2A5F5.exe (PID: 5704)
- 0037G.exe (PID: 7824)
- 07XOW.exe (PID: 4360)
- 9E6N9.exe (PID: 7712)
- 1746F.exe (PID: 7916)
- MRL2Z.exe (PID: 7988)
- 9Y2AJ.exe (PID: 6964)
- Y0JG0.exe (PID: 4784)
- 1B2N3.exe (PID: 8176)
- APF67.exe (PID: 8112)
- 1ZTZW.exe (PID: 4760)
- 89YII.exe (PID: 5956)
- H00P7.exe (PID: 7540)
- CX629.exe (PID: 1148)
- 3U9HZ.exe (PID: 5500)
- QGR2G.exe (PID: 1264)
- 0T70H.exe (PID: 2100)
- 31Z24.exe (PID: 7660)
- 90108.exe (PID: 3400)
- XQWA4.exe (PID: 7588)
- 098VM.exe (PID: 2316)
- OY28S.exe (PID: 7580)
- 1E928.exe (PID: 7736)
- QU316.exe (PID: 7864)
- 2DC97.exe (PID: 4452)
- VR3XP.exe (PID: 4916)
- 1T9QO.exe (PID: 7868)
- 4T6D5.exe (PID: 5392)
- 97R42.exe (PID: 7924)
- T8GF2.exe (PID: 6156)
- EXY1D.exe (PID: 5704)
- F3JY5.exe (PID: 5584)
- 54Y4E.exe (PID: 1252)
- 5AJX5.exe (PID: 2344)
- YQU4Y.exe (PID: 7348)
- QYC88.exe (PID: 8144)
- I1U0X.exe (PID: 8008)
- 7UKT5.exe (PID: 8120)
- ZI8HO.exe (PID: 1540)
- 73A7I.exe (PID: 8176)
- T0YZ6.exe (PID: 2636)
- 5VOT0.exe (PID: 7796)
- B90C3.exe (PID: 5956)
- H2GM5.exe (PID: 8024)
- YT95L.exe (PID: 7496)
- 8M27C.exe (PID: 1148)
- I4R98.exe (PID: 7664)
- M81O1.exe (PID: 7560)
- CF2W8.exe (PID: 7436)
- 567H4.exe (PID: 7100)
- 4UNDC.exe (PID: 2580)
- 081VV.exe (PID: 7660)
- N7886.exe (PID: 1248)
- L1V69.exe (PID: 7756)
- 4BYIC.exe (PID: 7632)
- 90GQJ.exe (PID: 7616)
- 58NY3.exe (PID: 7688)
- OSV3P.exe (PID: 7908)
- 3CBUL.exe (PID: 3392)
- W5N73.exe (PID: 7784)
- 6886X.exe (PID: 6164)
- QS4B1.exe (PID: 5540)
- 3L9Y6.exe (PID: 5356)
- S040W.exe (PID: 3148)
- C1304.exe (PID: 6740)
- W0VS1.exe (PID: 7992)
- E9437.exe (PID: 8124)
- 5W8TX.exe (PID: 7888)
- O870X.exe (PID: 4384)
- NV87C.exe (PID: 8128)
- 1GPF5.exe (PID: 5508)
- 9T2X3.exe (PID: 6872)
- 623X2.exe (PID: 2164)
- 1HMXM.exe (PID: 6728)
- 9FF6V.exe (PID: 272)
- 7L8F3.exe (PID: 7440)
- X5X86.exe (PID: 2104)
- X11ZD.exe (PID: 7328)
- O29W1.exe (PID: 1952)
- 2EI6W.exe (PID: 7332)
- H83M9.exe (PID: 2512)
- C5O6S.exe (PID: 3568)
- F0FZI.exe (PID: 7436)
- 65GW2.exe (PID: 1248)
- IXJU5.exe (PID: 7756)
- 04C2B.exe (PID: 7616)
- IH88U.exe (PID: 7688)
- 71H49.exe (PID: 1128)
- 077UU.exe (PID: 3392)
- 385D5.exe (PID: 7908)
- N71JV.exe (PID: 6164)
- YEZFT.exe (PID: 5356)
- 5056Z.exe (PID: 5540)
- 3A1N4.exe (PID: 6740)
- 284M4.exe (PID: 3156)
- 6I57G.exe (PID: 2344)
- J715A.exe (PID: 7348)
- Z41A7.exe (PID: 8008)
- 1B5H5.exe (PID: 6444)
- 3ZQ3K.exe (PID: 2716)
- L38GI.exe (PID: 8116)
- 7PB1L.exe (PID: 2580)
- 8611J.exe (PID: 2724)
- 3FC69.exe (PID: 7632)
- L67FH.exe (PID: 8180)
- 4LU90.exe (PID: 2964)
- 0PC74.exe (PID: 7244)
- QQ68T.exe (PID: 1080)
- LJ7N7.exe (PID: 7108)
- DRNIY.exe (PID: 7304)
- PKJU0.exe (PID: 7480)
- 2GQCZ.exe (PID: 4896)
- RJB84.exe (PID: 932)
- 61596.exe (PID: 7484)
- 7NUST.exe (PID: 7528)
- Z4J88.exe (PID: 3468)
- 2LE92.exe (PID: 7644)
- 7609I.exe (PID: 7760)
- 44710.exe (PID: 7256)
- 1R00P.exe (PID: 7768)
- ET5YL.exe (PID: 2700)
- 4V6KD.exe (PID: 6048)
- YCU1Y.exe (PID: 660)
- 961WF.exe (PID: 4916)
- 3W245.exe (PID: 6156)
- FS121.exe (PID: 5392)
- 52N0T.exe (PID: 5704)
- 0U9KU.exe (PID: 1252)
- A488N.exe (PID: 7924)
- 2CVR6.exe (PID: 6236)
- QXK1G.exe (PID: 8076)
- T5YK7.exe (PID: 564)
- Q0DQ6.exe (PID: 1924)
- 4BJR5.exe (PID: 8068)
- ABDPY.exe (PID: 6300)
- P3UW3.exe (PID: 8176)
- FEU1D.exe (PID: 1540)
- X8M1W.exe (PID: 2636)
- C9R03.exe (PID: 8036)
- P3Y56.exe (PID: 2820)
- 2L551.exe (PID: 6004)
- C895R.exe (PID: 3236)
- 6747G.exe (PID: 7464)
- 3WB3H.exe (PID: 8172)
- 4W2V0.exe (PID: 4220)
- 061D6.exe (PID: 5124)
- 18K5D.exe (PID: 7656)
- K659K.exe (PID: 5712)
- 8BKZ6.exe (PID: 5192)
- 937O9.exe (PID: 5912)
- 2X6H2.exe (PID: 5948)
- F800M.exe (PID: 4140)
- 4QQXF.exe (PID: 7444)
- YA25L.exe (PID: 7316)
- CT71M.exe (PID: 3320)
- 3W7ST.exe (PID: 7812)
- 1OIL0.exe (PID: 6416)
- F0A93.exe (PID: 5656)
- 553TU.exe (PID: 7840)
- FV7Q7.exe (PID: 7344)
- N85R5.exe (PID: 8032)
- 5ZF77.exe (PID: 7984)
- N3P2Y.exe (PID: 3680)
- 0R1FD.exe (PID: 5368)
- 28FW7.exe (PID: 4360)
- C678J.exe (PID: 5772)
- 9KX70.exe (PID: 4528)
- J7Q9F.exe (PID: 3332)
- A7A9N.exe (PID: 8188)
- Z346S.exe (PID: 6988)
- 4NF77.exe (PID: 5892)
- 6Y9F1.exe (PID: 3020)
- JQ7P7.exe (PID: 476)
- M298O.exe (PID: 7792)
- 8HVD8.exe (PID: 3236)
- SBNK3.exe (PID: 7232)
- 9OV5D.exe (PID: 7328)
- LN85T.exe (PID: 7664)
- I3FL1.exe (PID: 272)
- NXKXZ.exe (PID: 7592)
- M2PP1.exe (PID: 7564)
- 2NL71.exe (PID: 4368)
- W1LKP.exe (PID: 7640)
- 1FA89.exe (PID: 5676)
- WZ5R9.exe (PID: 7896)
- 6I04B.exe (PID: 1844)
- M04SW.exe (PID: 7724)
- 95A69.exe (PID: 7844)
- 6FWD5.exe (PID: 6452)
- Z4LWV.exe (PID: 4592)
- 35VT6.exe (PID: 7628)
- 9NSM8.exe (PID: 7448)
- M70F6.exe (PID: 3680)
- I5G1E.exe (PID: 2408)
- 3769Y.exe (PID: 7940)
- Y619C.exe (PID: 4360)
- ED3E5.exe (PID: 5368)
- 8672A.exe (PID: 7984)
- J318B.exe (PID: 8144)
- 7D55V.exe (PID: 4528)
- G63HD.exe (PID: 5772)
- 3Z6S8.exe (PID: 564)
- 1185X.exe (PID: 7548)
- DC1YD.exe (PID: 4168)
- C89R8.exe (PID: 1504)
- FA0M9.exe (PID: 404)
- P53LK.exe (PID: 2820)
- 8K631.exe (PID: 3056)
- 57YAT.exe (PID: 4164)
- 3D7SM.exe (PID: 6088)
- 6VN85.exe (PID: 7540)
- B96M2.exe (PID: 7612)
- LY9LH.exe (PID: 7100)
- X7J0M.exe (PID: 7508)
- T5FTO.exe (PID: 4996)
- P21S1.exe (PID: 7524)
- NEQ55.exe (PID: 7460)
- V2YGW.exe (PID: 3956)
- L9FOD.exe (PID: 2576)
- X0B43.exe (PID: 7740)
- 1CJM1.exe (PID: 2564)
- H1U69.exe (PID: 3960)
- G068C.exe (PID: 7720)
- WS76J.exe (PID: 1136)
- T1V2X.exe (PID: 7900)
- IL89E.exe (PID: 7808)
- 9O8A7.exe (PID: 7848)
- 9526M.exe (PID: 3392)
- P7N86.exe (PID: 6164)
- 6506L.exe (PID: 5720)
- 5H918.exe (PID: 1252)
- 4X047.exe (PID: 7584)
- TXW92.exe (PID: 7712)
- JWIZ5.exe (PID: 8056)
- RS911.exe (PID: 3156)
- UHBE0.exe (PID: 3696)
- K8UY7.exe (PID: 4280)
- TC027.exe (PID: 7960)
- 4C8M4.exe (PID: 8052)
- AYRAJ.exe (PID: 8092)
- ARVV0.exe (PID: 5652)
- 16G78.exe (PID: 4720)
- 74274.exe (PID: 7604)
- C919F.exe (PID: 1172)
- 54KXP.exe (PID: 5884)
- D97EI.exe (PID: 5872)
- 12I31.exe (PID: 7508)
- 7C50O.exe (PID: 7612)
- D5234.exe (PID: 7540)
- 149RP.exe (PID: 7100)
- 78S5K.exe (PID: 4996)
- 2V531.exe (PID: 7524)
- 93J3Q.exe (PID: 2576)
- 65918.exe (PID: 7460)
- Q20MZ.exe (PID: 3956)
- 15521.exe (PID: 3960)
- 0V85U.exe (PID: 2564)
- 0B581.exe (PID: 1136)
- 8J6V7.exe (PID: 7740)
- WZ0C5.exe (PID: 7720)
- E6OTH.exe (PID: 7900)
- H2N4X.exe (PID: 7808)
- 0P2N0.exe (PID: 7848)
- 06BDB.exe (PID: 5720)
- X90FV.exe (PID: 6164)
- 7442L.exe (PID: 3392)
- 4XL2Y.exe (PID: 1252)
- 1MFY8.exe (PID: 7584)
- P5PAJ.exe (PID: 7712)
- 37SHD.exe (PID: 5604)
- 94T0F.exe (PID: 8056)
- 39119.exe (PID: 8052)
- 795BA.exe (PID: 8164)
- CV758.exe (PID: 3696)
- CRZG7.exe (PID: 7960)
- I386Z.exe (PID: 5652)
- 00IL4.exe (PID: 4720)
- V9JRJ.exe (PID: 4280)
- OI304.exe (PID: 1172)
- 840K8.exe (PID: 5884)
- 91MQJ.exe (PID: 7604)
- 3L324.exe (PID: 7108)
- 680P5.exe (PID: 7480)
- G19D2.exe (PID: 2104)
- 8HE62.exe (PID: 6972)
- 8023A.exe (PID: 6952)
- SL4W3.exe (PID: 2800)
- 047W6.exe (PID: 2972)
- G9379.exe (PID: 3200)
- 271RH.exe (PID: 7588)
- F0249.exe (PID: 7716)
- 9F6IY.exe (PID: 7316)
- J30H6.exe (PID: 4140)
- 5P20F.exe (PID: 4668)
- 96QJ1.exe (PID: 3320)
- 3R6F8.exe (PID: 7444)
- 4JH29.exe (PID: 2720)
- W57KL.exe (PID: 7448)
- PZT68.exe (PID: 5656)
- 5C9UK.exe (PID: 2408)
- J0TI0.exe (PID: 3364)
- W5R8O.exe (PID: 2804)
- 08F2R.exe (PID: 5480)
- Z0J96.exe (PID: 1656)
- QJPK5.exe (PID: 8000)
- TY934.exe (PID: 5584)
- 3RM64.exe (PID: 4360)
- 0S56I.exe (PID: 5772)
- MRA03.exe (PID: 564)
- R69OK.exe (PID: 8144)
- UPE07.exe (PID: 4528)
- 81OPC.exe (PID: 6464)
- N03U4.exe (PID: 5472)
- 4HLI3.exe (PID: 3544)
- 8KFU6.exe (PID: 7484)
- PP5S8.exe (PID: 3044)
- K9BZO.exe (PID: 7552)
- V3P3S.exe (PID: 1144)
- IYW45.exe (PID: 2100)
- 2CD2V.exe (PID: 692)
- 5106J.exe (PID: 7380)
- FM69K.exe (PID: 5328)
- 8K2KG.exe (PID: 8104)
- 91204.exe (PID: 2972)
- 5D328.exe (PID: 7312)
- GL5V3.exe (PID: 7520)
- Q3BHF.exe (PID: 3200)
Process checks computer location settings
- 41a95b2ea5f1469a0b71cdf6cf7d3a4f922a50d0afe78479b4470c9b5ac1dd71.exe (PID: 7412)
- 05YZJ.exe (PID: 7460)
- PIJ5L.exe (PID: 7512)
- AE0TB.exe (PID: 7564)
- 27XT9.exe (PID: 7620)
- T7IA7.exe (PID: 7688)
- X45B2.exe (PID: 7764)
- Y57IT.exe (PID: 7888)
- 1P19U.exe (PID: 7976)
- SG56W.exe (PID: 8040)
- OVCW2.exe (PID: 8108)
- S861Y.exe (PID: 8160)
- ACCNF.exe (PID: 4104)
- 3B451.exe (PID: 7436)
- 674L6.exe (PID: 1924)
- 713X7.exe (PID: 7528)
- 152D8.exe (PID: 7580)
- Y25VX.exe (PID: 7632)
- M5XB6.exe (PID: 7788)
- 44YF5.exe (PID: 7824)
- 46195.exe (PID: 8000)
- Z06ZC.exe (PID: 7872)
- 910G6.exe (PID: 2344)
- I9LHP.exe (PID: 7976)
- VPHQB.exe (PID: 8040)
- 6U8KU.exe (PID: 3236)
- 32VI8.exe (PID: 7240)
- IE44A.exe (PID: 8112)
- GXE5N.exe (PID: 7492)
- 15P26.exe (PID: 4900)
- 890SH.exe (PID: 4220)
- 6JH56.exe (PID: 7436)
- G74CB.exe (PID: 7528)
- 3YD6H.exe (PID: 3400)
- K469T.exe (PID: 7640)
- D50UW.exe (PID: 7580)
- 0858S.exe (PID: 7740)
- 4T0HE.exe (PID: 7476)
- 4M7VA.exe (PID: 7472)
- CA31T.exe (PID: 7696)
- 5Q6HZ.exe (PID: 4916)
- MPEF6.exe (PID: 7812)
- 9MT7S.exe (PID: 6356)
- NM896.exe (PID: 7796)
- UT400.exe (PID: 892)
- X9IAD.exe (PID: 8020)
- 744H4.exe (PID: 8144)
- 16811.exe (PID: 2104)
- ZO289.exe (PID: 5868)
- GMIAC.exe (PID: 8076)
- TS8AA.exe (PID: 5244)
- Y2W2E.exe (PID: 5408)
- 8142Y.exe (PID: 2740)
- EU543.exe (PID: 7588)
- 7GEP8.exe (PID: 7460)
- GT2UA.exe (PID: 4452)
- 4J6B9.exe (PID: 7608)
- 1LZM5.exe (PID: 5948)
- 68VS4.exe (PID: 7676)
- 4L057.exe (PID: 1252)
- JF5M3.exe (PID: 3364)
- 388P6.exe (PID: 4592)
- 0DL76.exe (PID: 7852)
- X8Y91.exe (PID: 5696)
- 4J017.exe (PID: 3680)
- 060G0.exe (PID: 7872)
- FUD95.exe (PID: 7960)
- Z9RH6.exe (PID: 8084)
- 72943.exe (PID: 5196)
- 2QB3V.exe (PID: 8172)
- 3A2U6.exe (PID: 4064)
- 49BXW.exe (PID: 8116)
- 8RXJ5.exe (PID: 6728)
- LYRTA.exe (PID: 7252)
- L0XJ5.exe (PID: 6880)
- TTZB9.exe (PID: 7480)
- 00K89.exe (PID: 7520)
- 33QO0.exe (PID: 7568)
- T2452.exe (PID: 3468)
- R1P3C.exe (PID: 7616)
- GW50J.exe (PID: 1276)
- S87J9.exe (PID: 6260)
- JR2BY.exe (PID: 2408)
- 4Z068.exe (PID: 7680)
- 5B7V6.exe (PID: 7868)
- Y0FW1.exe (PID: 5656)
- 61FDE.exe (PID: 6452)
- 6P7QP.exe (PID: 7940)
- 42THZ.exe (PID: 7992)
- RR2IL.exe (PID: 3332)
- 5QFG1.exe (PID: 8040)
- 2287R.exe (PID: 7796)
- 846H9.exe (PID: 8136)
- 0JBT6.exe (PID: 4264)
- JGM62.exe (PID: 7496)
- 233DV.exe (PID: 4064)
- H1UGV.exe (PID: 7788)
- GJ1EW.exe (PID: 7560)
- 4K596.exe (PID: 7612)
- 4W41K.exe (PID: 7668)
- FDN4D.exe (PID: 7576)
- 14887.exe (PID: 5712)
- 4AL80.exe (PID: 7624)
- H4AMG.exe (PID: 1252)
- 135GH.exe (PID: 3100)
- 8VT67.exe (PID: 7676)
- 3PL9G.exe (PID: 5696)
- 9GGQ0.exe (PID: 7924)
- 44W55.exe (PID: 5224)
- 7N537.exe (PID: 3460)
- 33C3V.exe (PID: 1140)
- QQ9QW.exe (PID: 7916)
- 704N6.exe (PID: 8020)
- 29N30.exe (PID: 8092)
- CJ2BA.exe (PID: 6376)
- 936IC.exe (PID: 476)
- 9607X.exe (PID: 6776)
- 6N466.exe (PID: 7796)
- RY1B7.exe (PID: 2852)
- Y8FJ3.exe (PID: 4900)
- 6WNR9.exe (PID: 6676)
- I7J3C.exe (PID: 7460)
- HVF03.exe (PID: 4668)
- 45VQG.exe (PID: 7556)
- I0C6M.exe (PID: 7708)
- HA572.exe (PID: 5268)
- K4CPT.exe (PID: 5580)
- 2WJ83.exe (PID: 7692)
- S9G16.exe (PID: 3100)
- W9FNS.exe (PID: 7768)
- LC3NX.exe (PID: 7840)
- W1UXJ.exe (PID: 7864)
- 384M8.exe (PID: 7852)
- A1OW3.exe (PID: 2764)
- N0944.exe (PID: 5368)
- HA7IB.exe (PID: 5772)
- 1Z9YK.exe (PID: 8052)
- TLJU6.exe (PID: 5288)
- 1X968.exe (PID: 8180)
- 697GY.exe (PID: 5660)
- J159E.exe (PID: 8024)
- 7W936.exe (PID: 1948)
- REBR8.exe (PID: 7276)
- 2BS07.exe (PID: 2104)
- 3G558.exe (PID: 2164)
- L5A71.exe (PID: 7332)
- VJALT.exe (PID: 2944)
- F3AL2.exe (PID: 7536)
- 4N883.exe (PID: 5504)
- 7ML00.exe (PID: 7436)
- WT72A.exe (PID: 6260)
- EX80H.exe (PID: 5900)
- 93465.exe (PID: 5040)
- IM8L2.exe (PID: 7700)
- 8J424.exe (PID: 5704)
- 161WC.exe (PID: 7624)
- 3O348.exe (PID: 7448)
- 5008Z.exe (PID: 5696)
- M150Y.exe (PID: 7856)
- ZYG4A.exe (PID: 7676)
- 72223.exe (PID: 4400)
- 1M300.exe (PID: 7352)
- 15OE9.exe (PID: 7996)
- 21JZY.exe (PID: 8128)
- 76I5W.exe (PID: 8044)
- JC7BE.exe (PID: 7976)
- RVL17.exe (PID: 6376)
- P37R8.exe (PID: 6776)
- SMWI4.exe (PID: 476)
- VPOBX.exe (PID: 7664)
- USS5N.exe (PID: 7796)
- 1000T.exe (PID: 3944)
- Z7QVP.exe (PID: 5244)
- GBJ33.exe (PID: 7516)
- 34C0T.exe (PID: 7484)
- 4T3G5.exe (PID: 4244)
- 3P7L5.exe (PID: 4452)
- QZ3E8.exe (PID: 8104)
- 3MQHV.exe (PID: 4668)
- U758A.exe (PID: 7708)
- 177WJ.exe (PID: 5580)
- UB1D3.exe (PID: 7628)
- DI9J0.exe (PID: 6164)
- P1ZQ3.exe (PID: 7784)
- 95758.exe (PID: 7904)
- SIN7D.exe (PID: 7816)
- 7D5SU.exe (PID: 7892)
- G587W.exe (PID: 7944)
- 7CQ7F.exe (PID: 2344)
- S87C9.exe (PID: 7348)
- 70NQ3.exe (PID: 3076)
- 4SIOD.exe (PID: 7952)
- 6V9N2.exe (PID: 7960)
- 1V809.exe (PID: 3984)
- 2AZV3.exe (PID: 2036)
- 2BNS9.exe (PID: 8108)
- 60Y4Y.exe (PID: 5376)
- 1S9LN.exe (PID: 4104)
- 72MNC.exe (PID: 1576)
- SAI99.exe (PID: 2880)
- 13I69.exe (PID: 5408)
- YV5R1.exe (PID: 6676)
- N10GX.exe (PID: 7556)
- 95XPK.exe (PID: 7572)
- NPB62.exe (PID: 3956)
- GRW60.exe (PID: 7724)
- 22032.exe (PID: 7748)
- 8UHII.exe (PID: 5268)
- D6350.exe (PID: 7836)
- 9H1Q1.exe (PID: 3996)
- PF509.exe (PID: 1136)
- 9N3CG.exe (PID: 7848)
- WAJIF.exe (PID: 7820)
- 4WQQE.exe (PID: 7788)
- 99141.exe (PID: 6264)
- V9519.exe (PID: 7888)
- 3VSS3.exe (PID: 2344)
- BLD7F.exe (PID: 3460)
- 35L5E.exe (PID: 4280)
- 1TL17.exe (PID: 8068)
- 94R76.exe (PID: 8152)
- D3WN4.exe (PID: 8048)
- C3HC9.exe (PID: 2312)
- D96QW.exe (PID: 1080)
- I6RV4.exe (PID: 2220)
- GOV5K.exe (PID: 3236)
- 9RM87.exe (PID: 7332)
- 9PAFD.exe (PID: 7596)
- I6B09.exe (PID: 6940)
- KIXH4.exe (PID: 2760)
- 460IW.exe (PID: 7380)
- S07XZ.exe (PID: 1688)
- DA5TX.exe (PID: 7640)
- 607S5.exe (PID: 7096)
- 8G99B.exe (PID: 5948)
- L0C14.exe (PID: 5040)
- BPCB1.exe (PID: 3996)
- G3342.exe (PID: 2008)
- 5475W.exe (PID: 6252)
- M3414.exe (PID: 7788)
- 1T831.exe (PID: 1836)
- JL3JW.exe (PID: 7880)
- J0Z4I.exe (PID: 7888)
- WN8FW.exe (PID: 3680)
- TAZN8.exe (PID: 8008)
- O30T9.exe (PID: 3460)
- W9U53.exe (PID: 4280)
- 6Y84Z.exe (PID: 8068)
- YUIXG.exe (PID: 8048)
- 05NP7.exe (PID: 800)
- 0FKP5.exe (PID: 1384)
- 505OB.exe (PID: 6504)
- FN8F2.exe (PID: 7492)
- 066PD.exe (PID: 4720)
- 9L57J.exe (PID: 1952)
- K7LN5.exe (PID: 2740)
- 2541J.exe (PID: 7328)
- O1HB2.exe (PID: 7560)
- 2XSO0.exe (PID: 3568)
- 4E61L.exe (PID: 2900)
- 1209L.exe (PID: 7668)
- QI603.exe (PID: 7688)
- 8SZ85.exe (PID: 7744)
- I9R07.exe (PID: 4668)
- 4TKS5.exe (PID: 5452)
- 022B9.exe (PID: 4884)
- I59UD.exe (PID: 7784)
- C896I.exe (PID: 1520)
- 2A5F5.exe (PID: 5704)
- DBR9D.exe (PID: 1284)
- B80HR.exe (PID: 7912)
- 9E6N9.exe (PID: 7712)
- 0037G.exe (PID: 7824)
- 1746F.exe (PID: 7916)
- MRL2Z.exe (PID: 7988)
- 9Y2AJ.exe (PID: 6964)
- 07XOW.exe (PID: 4360)
- Y0JG0.exe (PID: 4784)
- 1B2N3.exe (PID: 8176)
- 1ZTZW.exe (PID: 4760)
- 89YII.exe (PID: 5956)
- APF67.exe (PID: 8112)
- H00P7.exe (PID: 7540)
- 3U9HZ.exe (PID: 5500)
- QGR2G.exe (PID: 1264)
- 0T70H.exe (PID: 2100)
- CX629.exe (PID: 1148)
- 31Z24.exe (PID: 7660)
- XQWA4.exe (PID: 7588)
- 098VM.exe (PID: 2316)
- 90108.exe (PID: 3400)
- OY28S.exe (PID: 7580)
- 2DC97.exe (PID: 4452)
- 1E928.exe (PID: 7736)
- 1T9QO.exe (PID: 7868)
- VR3XP.exe (PID: 4916)
- QU316.exe (PID: 7864)
- 4T6D5.exe (PID: 5392)
- 97R42.exe (PID: 7924)
- T8GF2.exe (PID: 6156)
- EXY1D.exe (PID: 5704)
- 54Y4E.exe (PID: 1252)
- 5AJX5.exe (PID: 2344)
- F3JY5.exe (PID: 5584)
- YQU4Y.exe (PID: 7348)
- 7UKT5.exe (PID: 8120)
- I1U0X.exe (PID: 8008)
- QYC88.exe (PID: 8144)
- T0YZ6.exe (PID: 2636)
- ZI8HO.exe (PID: 1540)
- 73A7I.exe (PID: 8176)
- H2GM5.exe (PID: 8024)
- 5VOT0.exe (PID: 7796)
- B90C3.exe (PID: 5956)
- I4R98.exe (PID: 7664)
- YT95L.exe (PID: 7496)
- 8M27C.exe (PID: 1148)
- 567H4.exe (PID: 7100)
- M81O1.exe (PID: 7560)
- CF2W8.exe (PID: 7436)
- 081VV.exe (PID: 7660)
- 4UNDC.exe (PID: 2580)
- N7886.exe (PID: 1248)
- L1V69.exe (PID: 7756)
- 90GQJ.exe (PID: 7616)
- 4BYIC.exe (PID: 7632)
- 58NY3.exe (PID: 7688)
- OSV3P.exe (PID: 7908)
- W5N73.exe (PID: 7784)
- 3CBUL.exe (PID: 3392)
- 6886X.exe (PID: 6164)
- QS4B1.exe (PID: 5540)
- C1304.exe (PID: 6740)
- 3L9Y6.exe (PID: 5356)
- S040W.exe (PID: 3148)
- W0VS1.exe (PID: 7992)
- 5W8TX.exe (PID: 7888)
- O870X.exe (PID: 4384)
- E9437.exe (PID: 8124)
- NV87C.exe (PID: 8128)
- 623X2.exe (PID: 2164)
- 9T2X3.exe (PID: 6872)
- 1HMXM.exe (PID: 6728)
- 1GPF5.exe (PID: 5508)
- 7L8F3.exe (PID: 7440)
- X5X86.exe (PID: 2104)
- X11ZD.exe (PID: 7328)
- 9FF6V.exe (PID: 272)
- 2EI6W.exe (PID: 7332)
- H83M9.exe (PID: 2512)
- C5O6S.exe (PID: 3568)
- O29W1.exe (PID: 1952)
- F0FZI.exe (PID: 7436)
- 3ZQ3K.exe (PID: 2716)
- 7PB1L.exe (PID: 2580)
- IXJU5.exe (PID: 7756)
- 04C2B.exe (PID: 7616)
- IH88U.exe (PID: 7688)
- 71H49.exe (PID: 1128)
- 385D5.exe (PID: 7908)
- 3FC69.exe (PID: 7632)
- 077UU.exe (PID: 3392)
- N71JV.exe (PID: 6164)
- 5056Z.exe (PID: 5540)
- YEZFT.exe (PID: 5356)
- 3A1N4.exe (PID: 6740)
- 284M4.exe (PID: 3156)
- 6I57G.exe (PID: 2344)
- J715A.exe (PID: 7348)
- Z41A7.exe (PID: 8008)
- L38GI.exe (PID: 8116)
- 1B5H5.exe (PID: 6444)
- 65GW2.exe (PID: 1248)
- L67FH.exe (PID: 8180)
- 8611J.exe (PID: 2724)
- 0PC74.exe (PID: 7244)
- 4LU90.exe (PID: 2964)
- DRNIY.exe (PID: 7304)
- QQ68T.exe (PID: 1080)
- LJ7N7.exe (PID: 7108)
- PKJU0.exe (PID: 7480)
- 61596.exe (PID: 7484)
- 7NUST.exe (PID: 7528)
- 2GQCZ.exe (PID: 4896)
- Z4J88.exe (PID: 3468)
- 2LE92.exe (PID: 7644)
- RJB84.exe (PID: 932)
- 7609I.exe (PID: 7760)
- YCU1Y.exe (PID: 660)
- 4V6KD.exe (PID: 6048)
- 961WF.exe (PID: 4916)
- 1R00P.exe (PID: 7768)
- 44710.exe (PID: 7256)
- A488N.exe (PID: 7924)
- FS121.exe (PID: 5392)
- ET5YL.exe (PID: 2700)
- 3W245.exe (PID: 6156)
- 0U9KU.exe (PID: 1252)
- 52N0T.exe (PID: 5704)
- 2CVR6.exe (PID: 6236)
- QXK1G.exe (PID: 8076)
- T5YK7.exe (PID: 564)
- Q0DQ6.exe (PID: 1924)
- ABDPY.exe (PID: 6300)
- X8M1W.exe (PID: 2636)
- 4BJR5.exe (PID: 8068)
- FEU1D.exe (PID: 1540)
- C9R03.exe (PID: 8036)
- P3UW3.exe (PID: 8176)
- C895R.exe (PID: 3236)
- 6747G.exe (PID: 7464)
- P3Y56.exe (PID: 2820)
- 2L551.exe (PID: 6004)
- 3WB3H.exe (PID: 8172)
- K659K.exe (PID: 5712)
- 4W2V0.exe (PID: 4220)
- 18K5D.exe (PID: 7656)
- 061D6.exe (PID: 5124)
- 2X6H2.exe (PID: 5948)
- 937O9.exe (PID: 5912)
- 8BKZ6.exe (PID: 5192)
- YA25L.exe (PID: 7316)
- F800M.exe (PID: 4140)
- CT71M.exe (PID: 3320)
- 4QQXF.exe (PID: 7444)
- 1OIL0.exe (PID: 6416)
- 553TU.exe (PID: 7840)
- F0A93.exe (PID: 5656)
- FV7Q7.exe (PID: 7344)
- 3W7ST.exe (PID: 7812)
- N85R5.exe (PID: 8032)
- N3P2Y.exe (PID: 3680)
- 0R1FD.exe (PID: 5368)
- 28FW7.exe (PID: 4360)
- 5ZF77.exe (PID: 7984)
- J7Q9F.exe (PID: 3332)
- C678J.exe (PID: 5772)
- 9KX70.exe (PID: 4528)
- A7A9N.exe (PID: 8188)
- Z346S.exe (PID: 6988)
- 4NF77.exe (PID: 5892)
- JQ7P7.exe (PID: 476)
- 6Y9F1.exe (PID: 3020)
- LN85T.exe (PID: 7664)
- 8HVD8.exe (PID: 3236)
- I3FL1.exe (PID: 272)
- SBNK3.exe (PID: 7232)
- M298O.exe (PID: 7792)
- NXKXZ.exe (PID: 7592)
- M2PP1.exe (PID: 7564)
- 9OV5D.exe (PID: 7328)
- 2NL71.exe (PID: 4368)
- W1LKP.exe (PID: 7640)
- 1FA89.exe (PID: 5676)
- M04SW.exe (PID: 7724)
- WZ5R9.exe (PID: 7896)
- 95A69.exe (PID: 7844)
- 6I04B.exe (PID: 1844)
- Z4LWV.exe (PID: 4592)
- 6FWD5.exe (PID: 6452)
- 9NSM8.exe (PID: 7448)
- 35VT6.exe (PID: 7628)
- 3769Y.exe (PID: 7940)
- M70F6.exe (PID: 3680)
- I5G1E.exe (PID: 2408)
- Y619C.exe (PID: 4360)
- ED3E5.exe (PID: 5368)
- 8672A.exe (PID: 7984)
- G63HD.exe (PID: 5772)
- J318B.exe (PID: 8144)
- 3Z6S8.exe (PID: 564)
- 7D55V.exe (PID: 4528)
- DC1YD.exe (PID: 4168)
- C89R8.exe (PID: 1504)
- FA0M9.exe (PID: 404)
- 1185X.exe (PID: 7548)
- 8K631.exe (PID: 3056)
- 57YAT.exe (PID: 4164)
- 3D7SM.exe (PID: 6088)
- P53LK.exe (PID: 2820)
- X7J0M.exe (PID: 7508)
- 6VN85.exe (PID: 7540)
- B96M2.exe (PID: 7612)
- T5FTO.exe (PID: 4996)
- P21S1.exe (PID: 7524)
- LY9LH.exe (PID: 7100)
- V2YGW.exe (PID: 3956)
- NEQ55.exe (PID: 7460)
- 1CJM1.exe (PID: 2564)
- H1U69.exe (PID: 3960)
- L9FOD.exe (PID: 2576)
- G068C.exe (PID: 7720)
- WS76J.exe (PID: 1136)
- X0B43.exe (PID: 7740)
- 9O8A7.exe (PID: 7848)
- T1V2X.exe (PID: 7900)
- 6506L.exe (PID: 5720)
- 9526M.exe (PID: 3392)
- IL89E.exe (PID: 7808)
- 4X047.exe (PID: 7584)
- P7N86.exe (PID: 6164)
- TXW92.exe (PID: 7712)
- 5H918.exe (PID: 1252)
- JWIZ5.exe (PID: 8056)
- RS911.exe (PID: 3156)
- UHBE0.exe (PID: 3696)
- K8UY7.exe (PID: 4280)
- 4C8M4.exe (PID: 8052)
- AYRAJ.exe (PID: 8092)
- TC027.exe (PID: 7960)
- ARVV0.exe (PID: 5652)
- C919F.exe (PID: 1172)
- 74274.exe (PID: 7604)
- 16G78.exe (PID: 4720)
- 12I31.exe (PID: 7508)
- 54KXP.exe (PID: 5884)
- D97EI.exe (PID: 5872)
- 7C50O.exe (PID: 7612)
- D5234.exe (PID: 7540)
- 149RP.exe (PID: 7100)
- 78S5K.exe (PID: 4996)
- 2V531.exe (PID: 7524)
- 65918.exe (PID: 7460)
- Q20MZ.exe (PID: 3956)
- 0V85U.exe (PID: 2564)
- 15521.exe (PID: 3960)
- 93J3Q.exe (PID: 2576)
- 8J6V7.exe (PID: 7740)
- WZ0C5.exe (PID: 7720)
- 0P2N0.exe (PID: 7848)
- 0B581.exe (PID: 1136)
- E6OTH.exe (PID: 7900)
- 06BDB.exe (PID: 5720)
- 7442L.exe (PID: 3392)
- H2N4X.exe (PID: 7808)
- 4XL2Y.exe (PID: 1252)
- X90FV.exe (PID: 6164)
- 1MFY8.exe (PID: 7584)
- P5PAJ.exe (PID: 7712)
- 94T0F.exe (PID: 8056)
- 37SHD.exe (PID: 5604)
- 795BA.exe (PID: 8164)
- 39119.exe (PID: 8052)
- CV758.exe (PID: 3696)
- CRZG7.exe (PID: 7960)
- I386Z.exe (PID: 5652)
- V9JRJ.exe (PID: 4280)
- 91MQJ.exe (PID: 7604)
- OI304.exe (PID: 1172)
- 00IL4.exe (PID: 4720)
- 3L324.exe (PID: 7108)
- 680P5.exe (PID: 7480)
- 840K8.exe (PID: 5884)
- G19D2.exe (PID: 2104)
- SL4W3.exe (PID: 2800)
- 8023A.exe (PID: 6952)
- 8HE62.exe (PID: 6972)
- F0249.exe (PID: 7716)
- 271RH.exe (PID: 7588)
- 047W6.exe (PID: 2972)
- 9F6IY.exe (PID: 7316)
- 5P20F.exe (PID: 4668)
- G9379.exe (PID: 3200)
- 96QJ1.exe (PID: 3320)
- J30H6.exe (PID: 4140)
- 3R6F8.exe (PID: 7444)
- 4JH29.exe (PID: 2720)
- W57KL.exe (PID: 7448)
- PZT68.exe (PID: 5656)
- W5R8O.exe (PID: 2804)
- 5C9UK.exe (PID: 2408)
- J0TI0.exe (PID: 3364)
- TY934.exe (PID: 5584)
- 08F2R.exe (PID: 5480)
- QJPK5.exe (PID: 8000)
- 3RM64.exe (PID: 4360)
- 0S56I.exe (PID: 5772)
- Z0J96.exe (PID: 1656)
- MRA03.exe (PID: 564)
- R69OK.exe (PID: 8144)
- UPE07.exe (PID: 4528)
- 81OPC.exe (PID: 6464)
- N03U4.exe (PID: 5472)
- 4HLI3.exe (PID: 3544)
- PP5S8.exe (PID: 3044)
- K9BZO.exe (PID: 7552)
- V3P3S.exe (PID: 1144)
- 2CD2V.exe (PID: 692)
- 8KFU6.exe (PID: 7484)
- IYW45.exe (PID: 2100)
- FM69K.exe (PID: 5328)
- 8K2KG.exe (PID: 8104)
- GL5V3.exe (PID: 7520)
- 5106J.exe (PID: 7380)
- 5D328.exe (PID: 7312)
- 91204.exe (PID: 2972)
Checks proxy server information
- slui.exe (PID: 5168)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (39.5) |
|---|---|---|
| .exe | | | UPX compressed Win32 Executable (38.7) |
| .dll | | | Win32 Dynamic Link Library (generic) (9.4) |
| .exe | | | Win32 Executable (generic) (6.4) |
| .exe | | | Generic Win/DOS Executable (2.8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 0000:00:00 00:00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 450560 |
| InitializedDataSize: | 150016 |
| UninitializedDataSize: | 802816 |
| EntryPoint: | 0x132be0 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
757
Monitored processes
613
Malicious processes
169
Suspicious processes
149
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | "C:\Users\admin\Desktop\9FF6V.exe" | C:\Users\admin\Desktop\9FF6V.exe | X5X86.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 272 | "C:\Users\admin\Desktop\I3FL1.exe" | C:\Users\admin\Desktop\I3FL1.exe | LN85T.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 404 | "C:\Users\admin\Desktop\FA0M9.exe" | C:\Users\admin\Desktop\FA0M9.exe | 8K631.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 476 | "C:\Users\admin\Desktop\936IC.exe" | C:\Users\admin\Desktop\936IC.exe | CJ2BA.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 476 | "C:\Users\admin\Desktop\SMWI4.exe" | C:\Users\admin\Desktop\SMWI4.exe | RVL17.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 476 | "C:\Users\admin\Desktop\JQ7P7.exe" | C:\Users\admin\Desktop\JQ7P7.exe | Z346S.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 564 | "C:\Users\admin\Desktop\T5YK7.exe" | C:\Users\admin\Desktop\T5YK7.exe | C9R03.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 564 | "C:\Users\admin\Desktop\3Z6S8.exe" | C:\Users\admin\Desktop\3Z6S8.exe | 7D55V.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 564 | "C:\Users\admin\Desktop\MRA03.exe" | C:\Users\admin\Desktop\MRA03.exe | — | UPE07.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 660 | "C:\Users\admin\Desktop\YCU1Y.exe" | C:\Users\admin\Desktop\YCU1Y.exe | 7609I.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
223 563
Read events
223 507
Write events
56
Delete events
0
Modification events
| (PID) Process: | (7460) 05YZJ.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (7460) 05YZJ.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (7460) 05YZJ.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (7460) 05YZJ.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (7412) 41a95b2ea5f1469a0b71cdf6cf7d3a4f922a50d0afe78479b4470c9b5ac1dd71.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (7412) 41a95b2ea5f1469a0b71cdf6cf7d3a4f922a50d0afe78479b4470c9b5ac1dd71.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (7412) 41a95b2ea5f1469a0b71cdf6cf7d3a4f922a50d0afe78479b4470c9b5ac1dd71.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (7412) 41a95b2ea5f1469a0b71cdf6cf7d3a4f922a50d0afe78479b4470c9b5ac1dd71.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (7512) PIJ5L.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (7512) PIJ5L.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
Executable files
535
Suspicious files
0
Text files
1
Unknown types
28
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7688 | T7IA7.exe | C:\Users\admin\Desktop\X45B2.exe | executable | |
MD5:7A09D74B6677D5A6C4853B027C1A07C6 | SHA256:AB058D4E876F72CE011ECC8113A0612C51DB597745FAF13DF310AE3D9DBAF812 | |||
| 7412 | 41a95b2ea5f1469a0b71cdf6cf7d3a4f922a50d0afe78479b4470c9b5ac1dd71.exe | C:\Users\admin\Desktop\05YZJ.exe | executable | |
MD5:304510B40A186DCDB19CE67C0F05C91C | SHA256:72D3B082783D3F38067A5C0145E1D42EC2EC5AC1048880145BFDE0F4BCFD1EBE | |||
| 7436 | 3B451.exe | C:\Users\admin\Desktop\713X7.exe | executable | |
MD5:F649DC0878B17CB35D0BC5EED2B13FEF | SHA256:70E01CDF6737AE5D85A7DBE8A071855D4087E44741E8BB1A29E89339068F0006 | |||
| 7632 | Y25VX.exe | C:\Users\admin\Desktop\M5XB6.exe | executable | |
MD5:887E0021A2A7CCCA5ACC1A51673BFB62 | SHA256:DAF61ECC64B98250A1DFAE0E7C6D22E7A4B335241866C630528FDEF328317F7F | |||
| 4104 | ACCNF.exe | C:\Users\admin\Desktop\674L6.exe | executable | |
MD5:BA82FF511E4DB143B61A9BF60305CCBC | SHA256:F7039B52F44803AF4866A33B51557C486BC397D50EE7801E2EFB299D70CCDE2C | |||
| 8160 | S861Y.exe | C:\Users\admin\Desktop\ACCNF.exe | executable | |
MD5:048CCDEF767FD655429075F3F667F0BB | SHA256:81577D1D296BD2F64AEBBF495EA3E14BD349059A4C13F73A4CA60A3E1568EBD4 | |||
| 7528 | 713X7.exe | C:\Users\admin\Desktop\152D8.exe | executable | |
MD5:DCE978A74CF5DFC216EF4A85327A09DB | SHA256:08F5512778FED50319FF07E5B858061806377BE5C2709A2B766417408A2CFF45 | |||
| 7788 | M5XB6.exe | C:\Users\admin\Desktop\Z06ZC.exe | executable | |
MD5:45B2B04C61363A81962E8DB506D625CA | SHA256:4EC8F3B12B212979578F26067C29B93D5A2AB2699B1D2E483F0E4822AD18C576 | |||
| 7872 | Z06ZC.exe | C:\Users\admin\Desktop\910G6.exe | executable | |
MD5:4ABFC4025E01DA4DF30343DC0DA6599D | SHA256:A6228402F6DB4A6A21AF3550A29A66DB2E008F8607F8D80CB2D57E8F397DB970 | |||
| 7512 | PIJ5L.exe | C:\Users\admin\Desktop\AE0TB.exe | executable | |
MD5:1BD0E0E029675686D22F94042568485B | SHA256:4E92A09016663996FE4A7746C21633993871FCF4319141569D8ADE36E5AA8541 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
31
TCP/UDP connections
50
DNS requests
19
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2564 | svchost.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4592 | RUXIMICS.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5596 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | POST | 200 | 40.126.32.136:443 | https://login.live.com/RST2.srf | unknown | xml | 11.1 Kb | unknown |
— | — | POST | 200 | 20.190.160.128:443 | https://login.live.com/RST2.srf | unknown | xml | 10.3 Kb | unknown |
— | — | POST | 200 | 20.190.160.67:443 | https://login.live.com/RST2.srf | unknown | xml | 10.3 Kb | unknown |
— | — | POST | 200 | 20.190.160.128:443 | https://login.live.com/RST2.srf | unknown | xml | 10.3 Kb | unknown |
— | — | POST | 200 | 40.126.32.136:443 | https://login.live.com/RST2.srf | unknown | xml | 11.0 Kb | unknown |
— | — | GET | 200 | 20.3.187.198:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | unknown | — | — | unknown |
— | — | GET | 200 | 74.179.77.204:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | compressed | 29.1 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2564 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5596 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4592 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 92.123.104.31:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2564 | svchost.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5596 | MoUsoCoreWorker.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4592 | RUXIMICS.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5596 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |