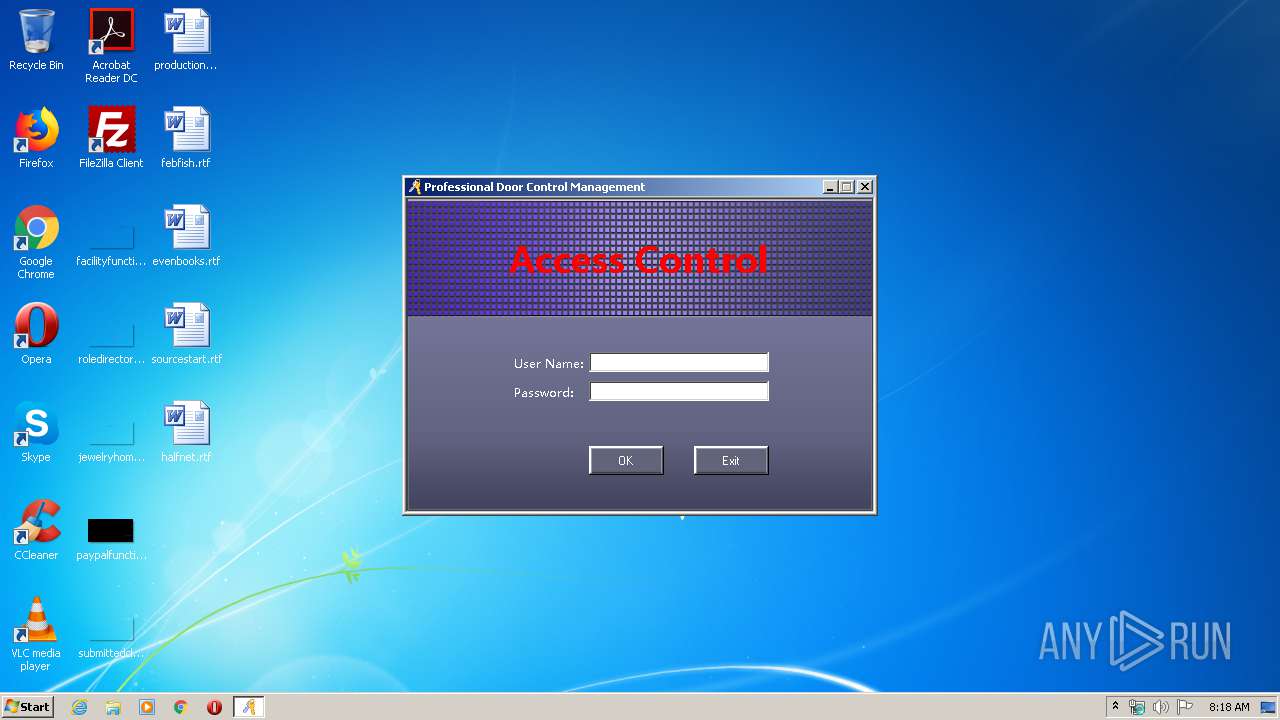
| File name: | n3000.exe |
| Full analysis: | https://app.any.run/tasks/0081dcc2-a8e6-42fb-aa33-f442f859c338 |
| Verdict: | Suspicious activity |
| Analysis date: | February 27, 2020, 08:17:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | B1255F07368AF7BAA07A6AFA655E269E |
| SHA1: | 8F211296E5A1403F23F1DF0502A4DB90C3B7F9A0 |
| SHA256: | 419F4064808351D1245A1D3A0673136FFCFEE79757F11BD6304F4B4A59768458 |
| SSDEEP: | 98304:Vl5XgS2PbdCsmGylUZrYefbeuT21tDtfd:D5X4zdj9ZPbv2Tpd |
MALICIOUS
Loads dropped or rewritten executable
- n3000.exe (PID: 3364)
SUSPICIOUS
Executable content was dropped or overwritten
- n3000.exe (PID: 3364)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:07:23 11:51:06+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 3709440 |
| InitializedDataSize: | 69632 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x38b96e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 8.1.93.19055 |
| ProductVersionNumber: | 8.1.93.19055 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
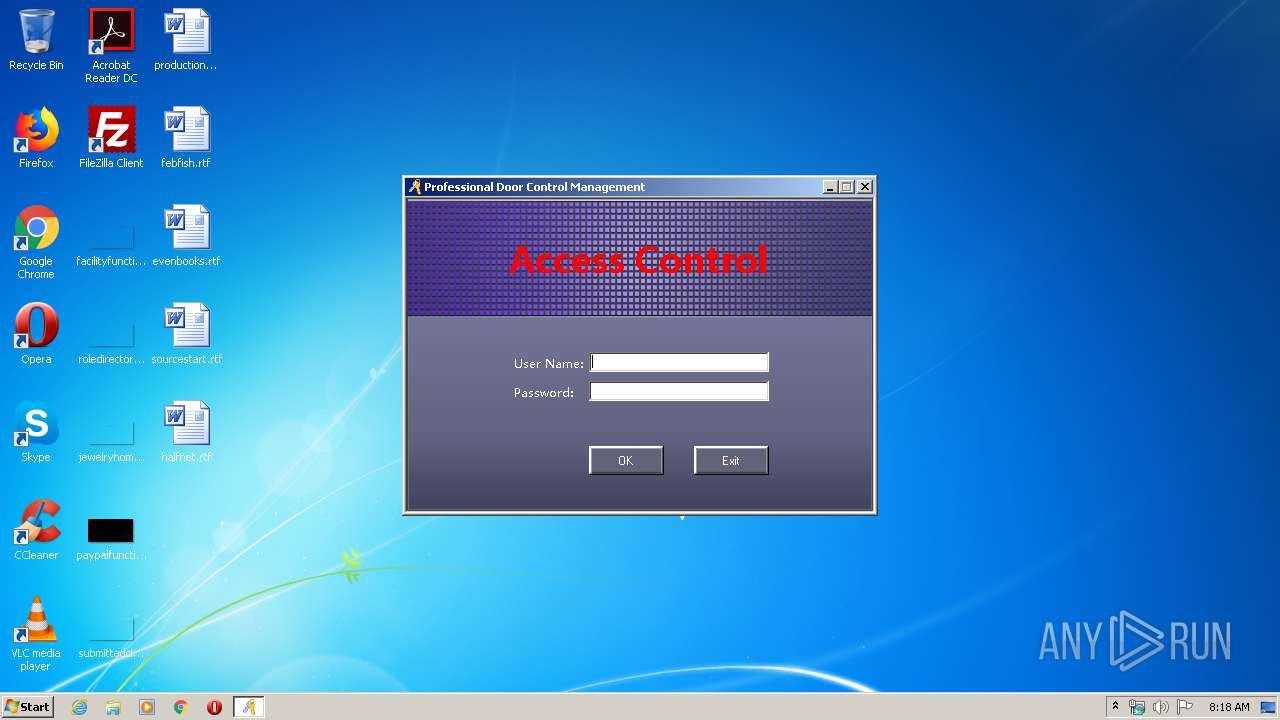
| CompanyName: | CSN |
| FileDescription: | N3000 |
| FileVersion: | 8.1.93.19055 |
| InternalName: | N3000.exe |
| LegalCopyright: | Copyright © 2010 CSN |
| OriginalFileName: | N3000.exe |
| ProductName: | N3000 |
| ProductVersion: | 8.1.93.19055 |
| AssemblyVersion: | 8.1.93.19055 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 23-Jul-2019 09:51:06 |
| CompanyName: | CSN |
| FileDescription: | N3000 |
| FileVersion: | 8.1.93.19055 |
| InternalName: | N3000.exe |
| LegalCopyright: | Copyright © 2010 CSN |
| OriginalFilename: | N3000.exe |
| ProductName: | N3000 |
| ProductVersion: | 8.1.93.19055 |
| Assembly Version: | 8.1.93.19055 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 23-Jul-2019 09:51:06 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x00389974 | 0x00389A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.99861 |
.rsrc | 0x0038C000 | 0x00010C08 | 0x00010E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.0981 |
.reloc | 0x0039E000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.40958 | 740 | UNKNOWN | UNKNOWN | RT_VERSION |
2 | 3.094 | 67624 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.16096 | 20 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
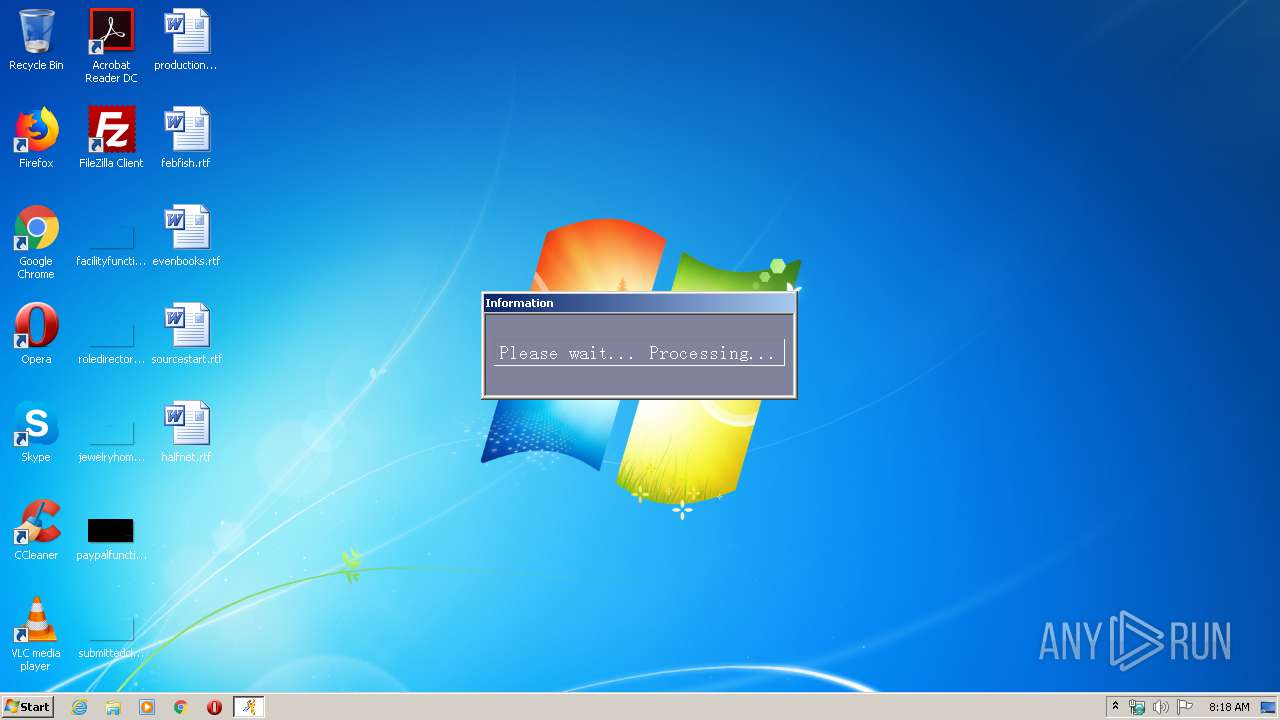
Total processes
33
Monitored processes
1
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3364 | "C:\Users\admin\AppData\Local\Temp\n3000.exe" | C:\Users\admin\AppData\Local\Temp\n3000.exe | explorer.exe | ||||||||||||
User: admin Company: CSN Integrity Level: MEDIUM Description: N3000 Exit code: 0 Version: 8.1.93.19055 Modules
| |||||||||||||||
Total events
18
Read events
18
Write events
0
Delete events
0
Modification events
Executable files
2
Suspicious files
1
Text files
15
Unknown types
21
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3364 | n3000.exe | C:\Users\admin\AppData\Local\Temp\iCCard3000.mdb.gz | — | |
MD5:— | SHA256:— | |||
| 3364 | n3000.exe | C:\Users\admin\AppData\Local\Temp\iCCard3000.ldb | — | |
MD5:— | SHA256:— | |||
| 3364 | n3000.exe | C:\Users\admin\AppData\Local\Temp\n3k_log.log | text | |
MD5:— | SHA256:— | |||
| 3364 | n3000.exe | C:\Users\admin\AppData\Local\Temp\n3k_cust.xml | text | |
MD5:— | SHA256:— | |||
| 3364 | n3000.exe | C:\Users\admin\AppData\Local\Temp\iCCard3000.mdb | mdb | |
MD5:350CAF5C9B3A7000C45F0F85C35D7E8B | SHA256:B787DDB5E871D91DCA0D875076576CF898FABF12090D7AACAF70B680324FC9DB | |||
| 3364 | n3000.exe | C:\Users\admin\AppData\Local\Temp\n3k_comm.dll | executable | |
MD5:BD219E7C2B0C3959188A43CDA5BFB2D4 | SHA256:FC38BFFABD3046E50C227BDF6E6A4098F52AE331D83DB7CB11DD75F0D8AB65B0 | |||
| 3364 | n3000.exe | C:\Users\admin\AppData\Local\Temp\Interop.jro.dll | executable | |
MD5:CB4797DA62D066B83A8234AB948C70D0 | SHA256:E88021BB92DB981249E71D9C450B4812C966DDCE4136BEB25F7F9B46150A3EE8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
n3000.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
n3000.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|