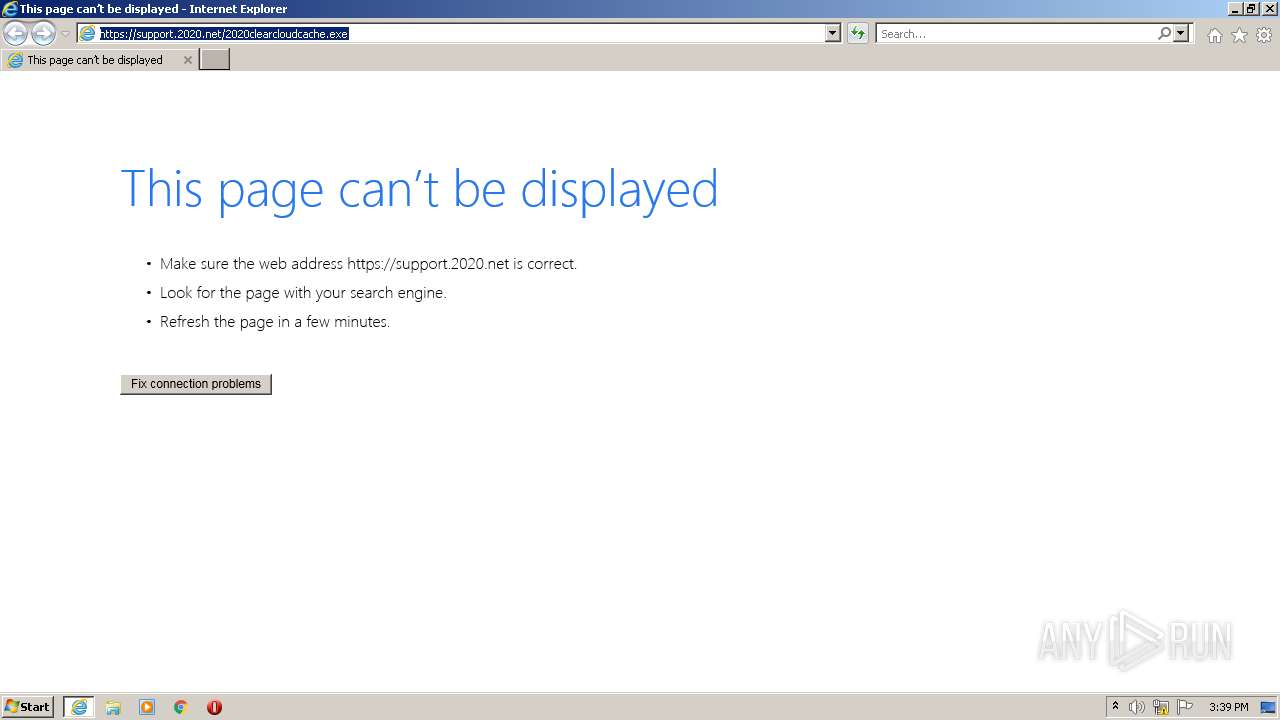
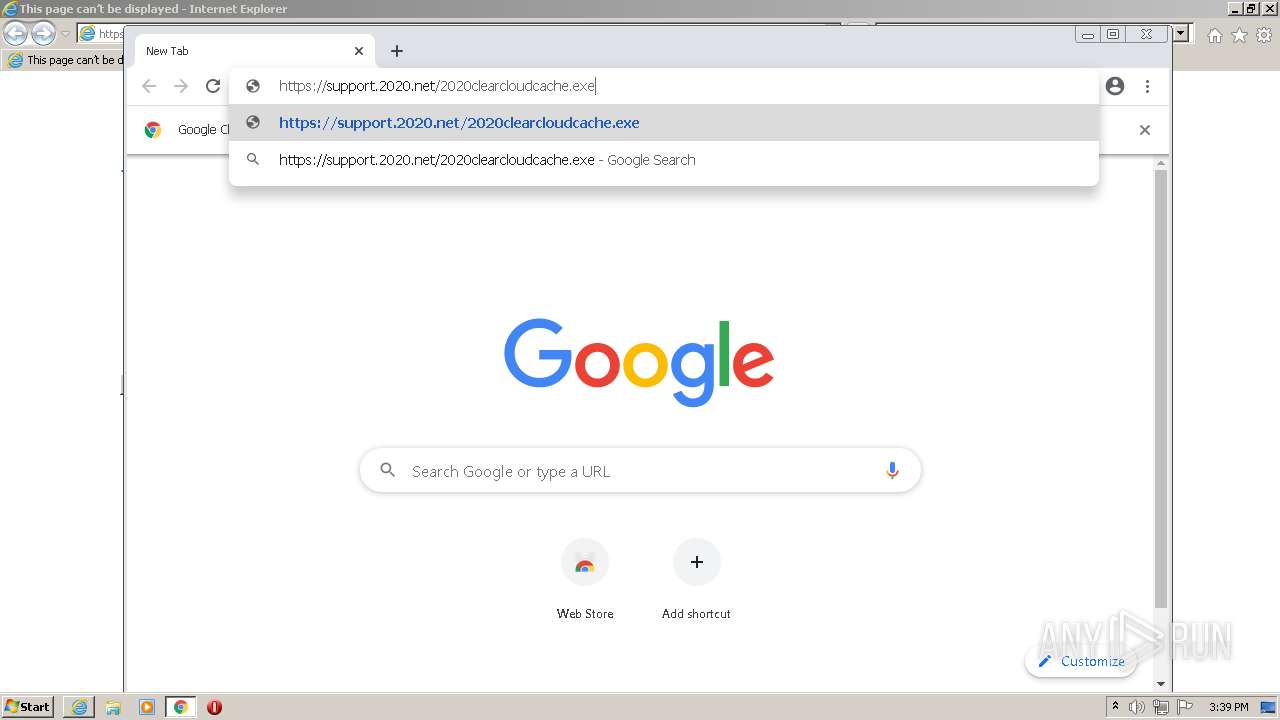
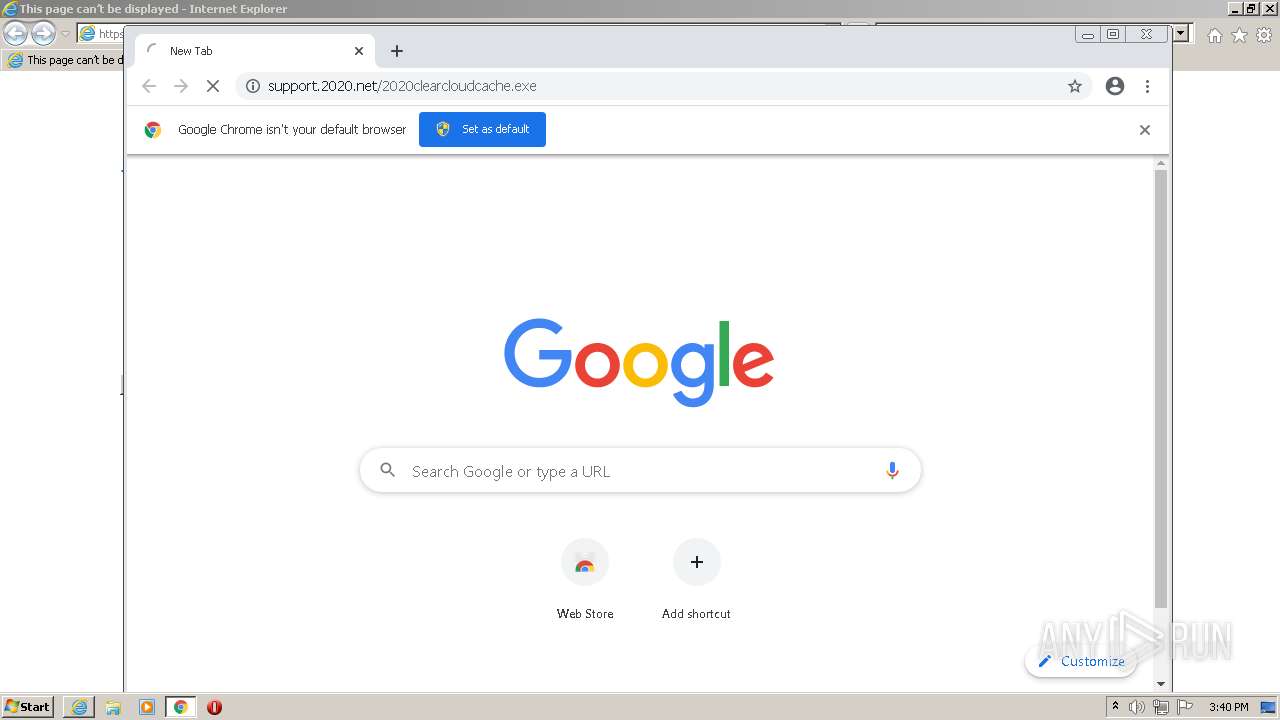
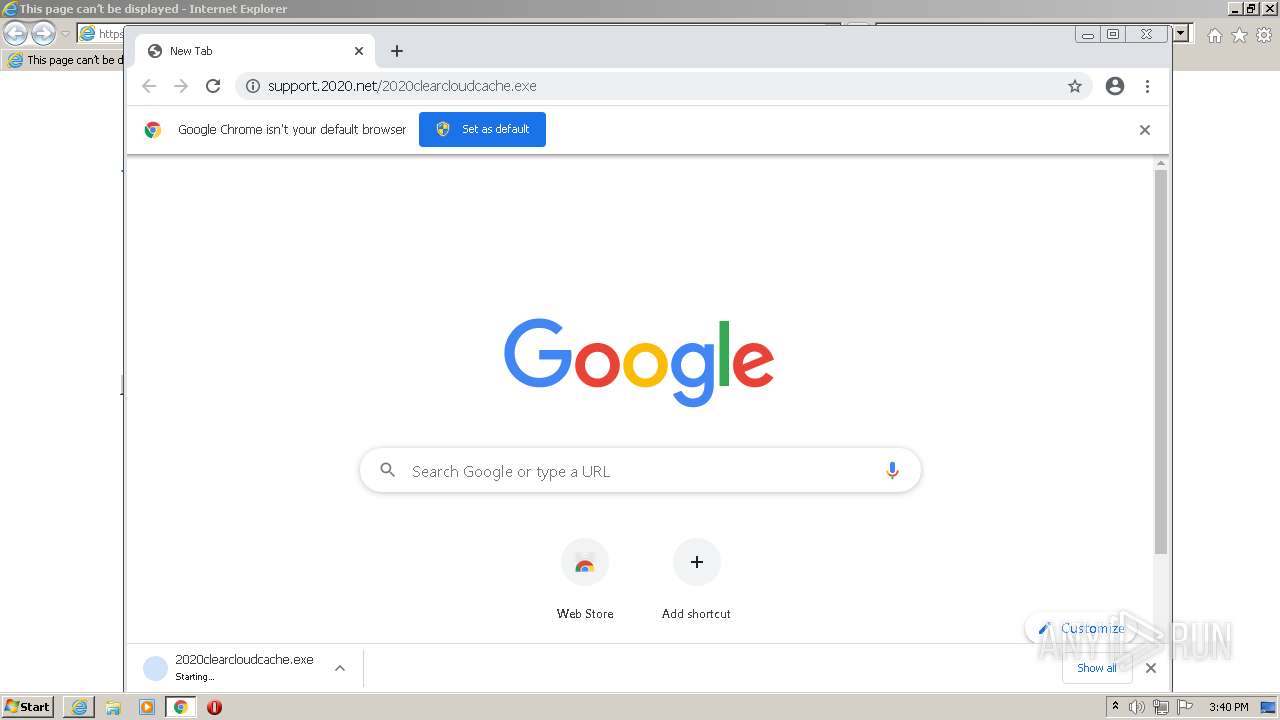
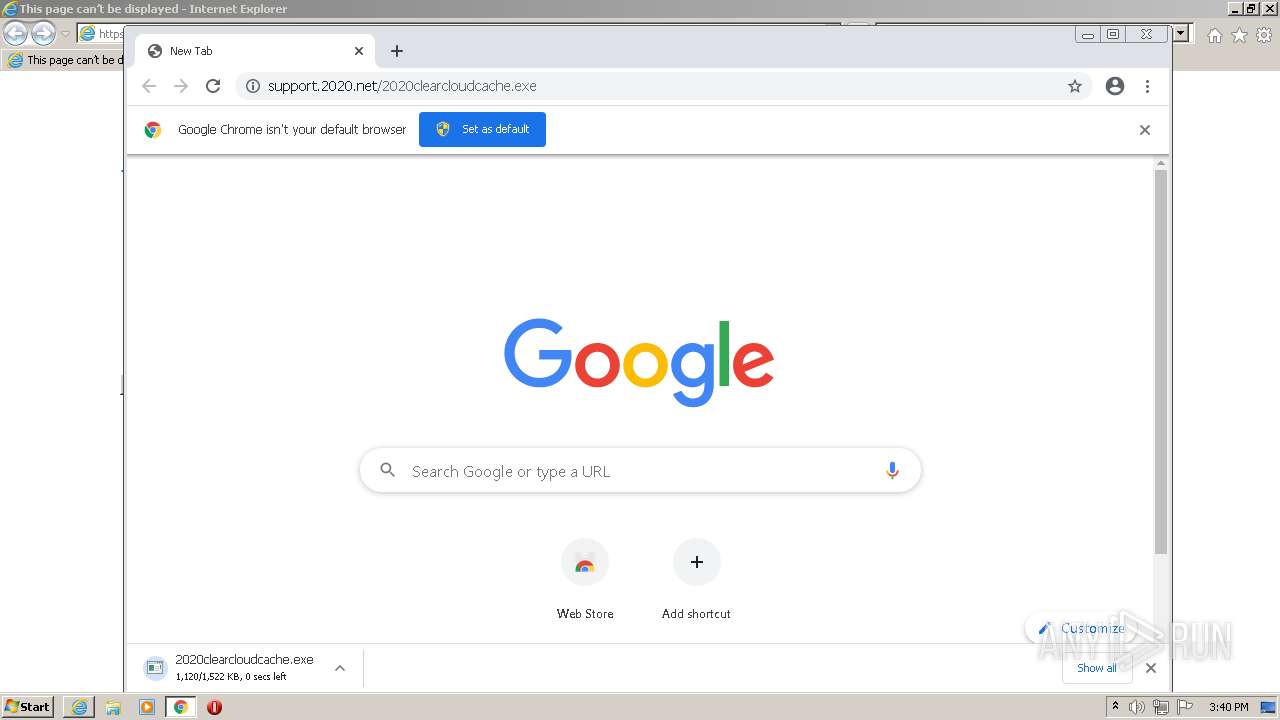
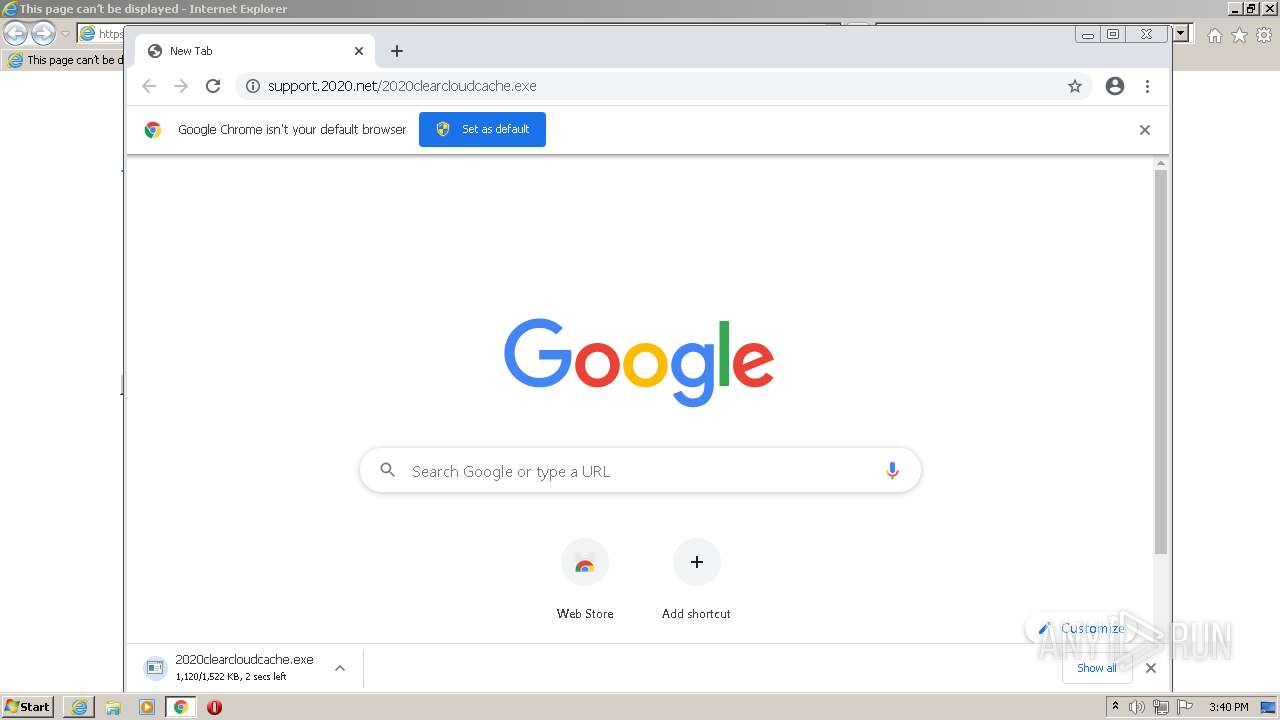
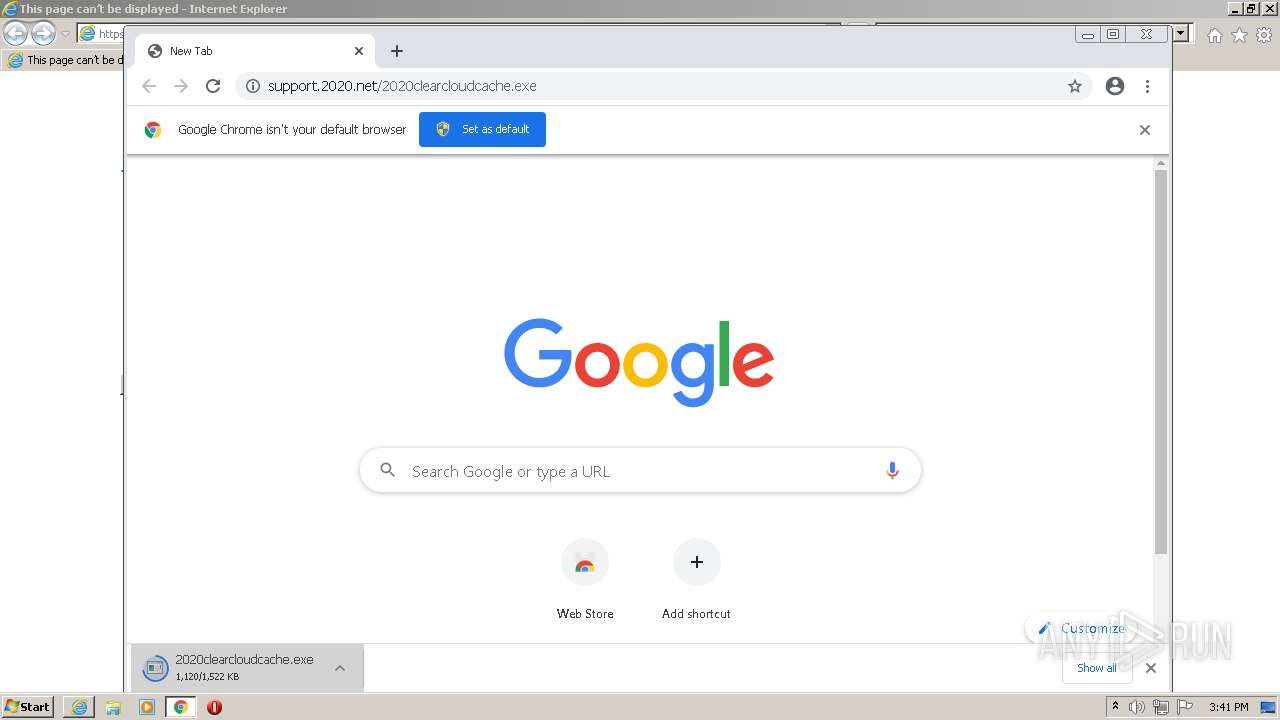
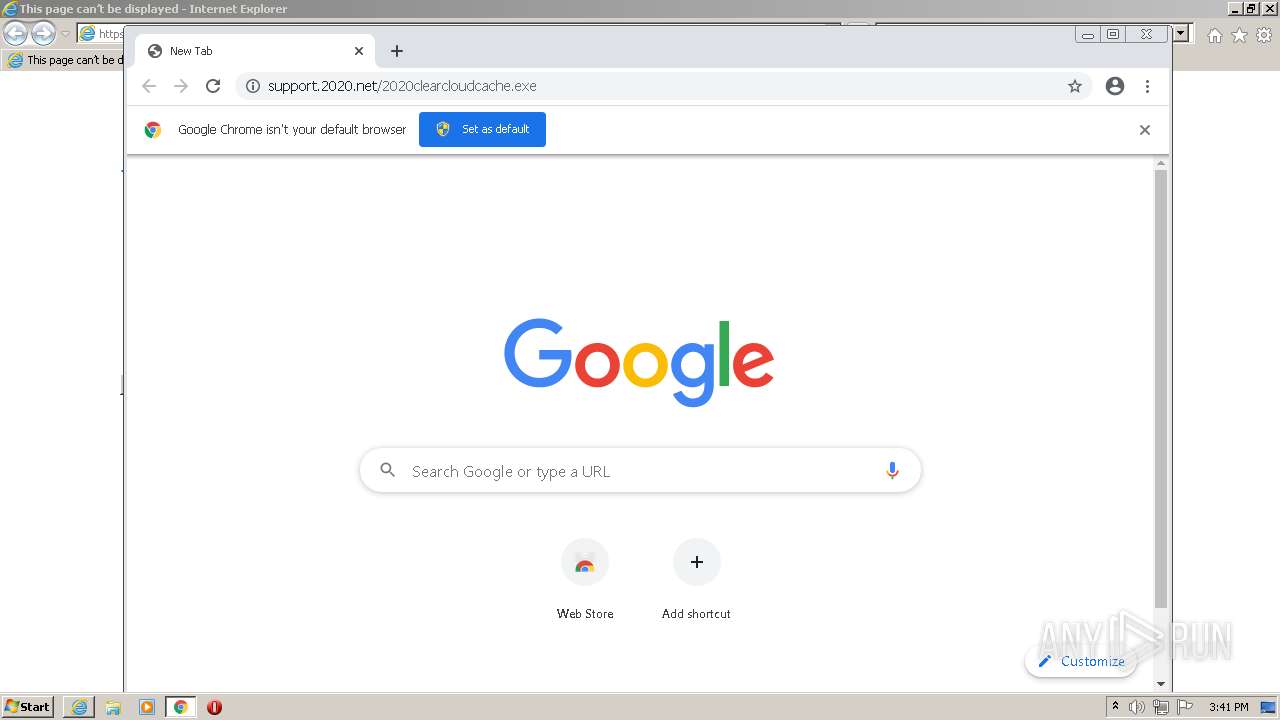
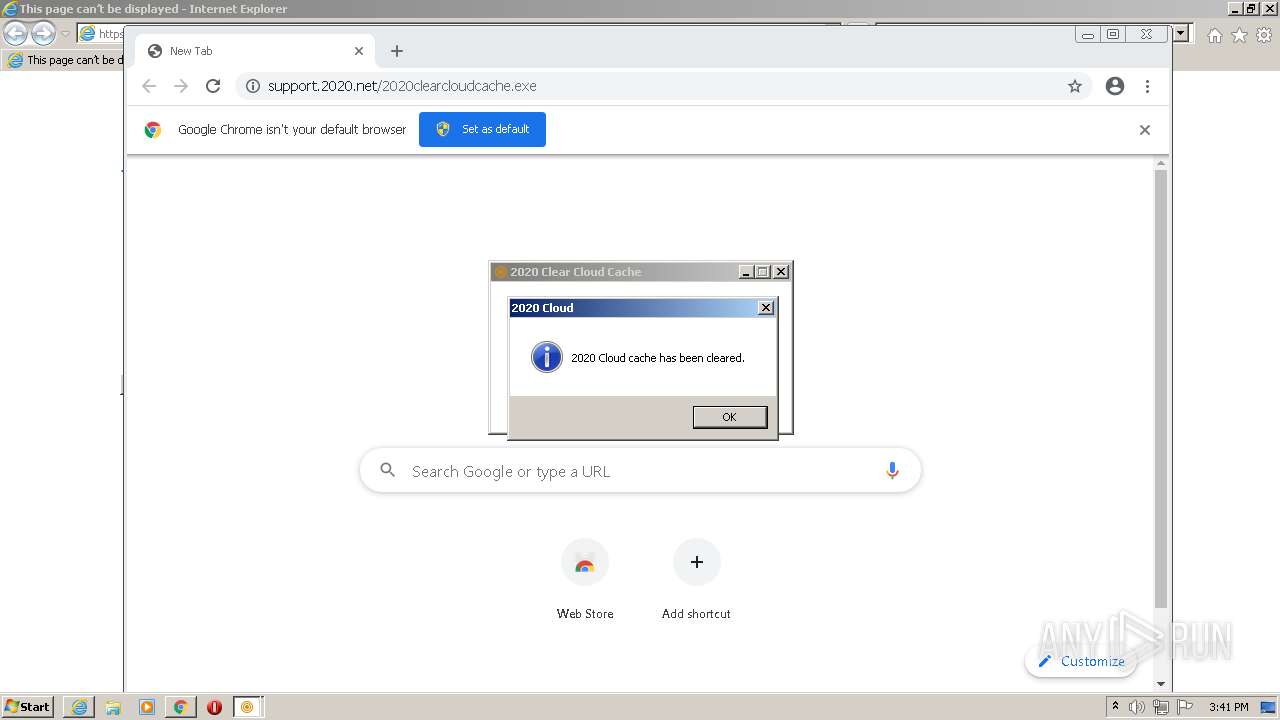
| URL: | https://support.2020.net/2020clearcloudcache.exe |
| Full analysis: | https://app.any.run/tasks/05a8144d-e0b9-48cf-8571-ac37a5d6fc4d |
| Verdict: | Malicious activity |
| Analysis date: | May 17, 2022, 14:39:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | BB75BBCB12C731C4240DB830DE8060D9 |
| SHA1: | E9B9D2C9033698FBB603AD2F0815D89AEFC2BCDE |
| SHA256: | 4195F145915D2A6D336CCE8F622FE2865D8EA13A4CAF76DF69CDB35B038252CB |
| SSDEEP: | 3:N8dCBLtdA23eB9XAn:2wBLIZB9XAn |
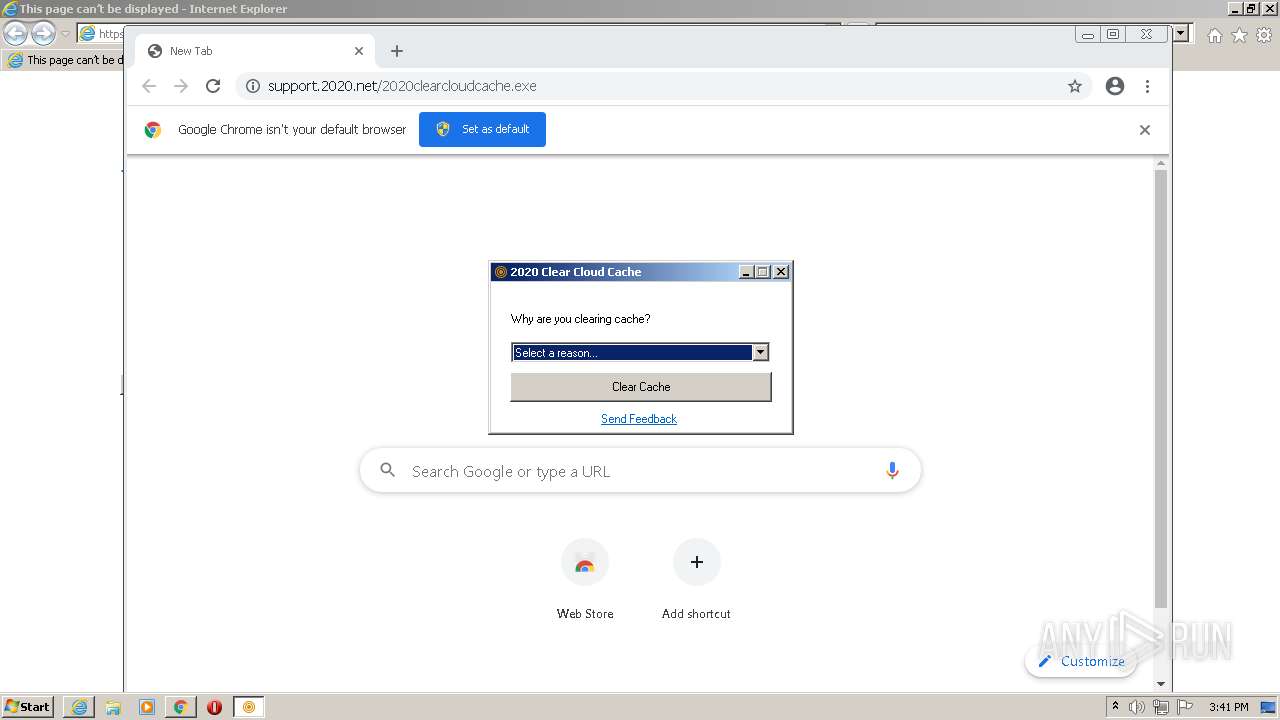
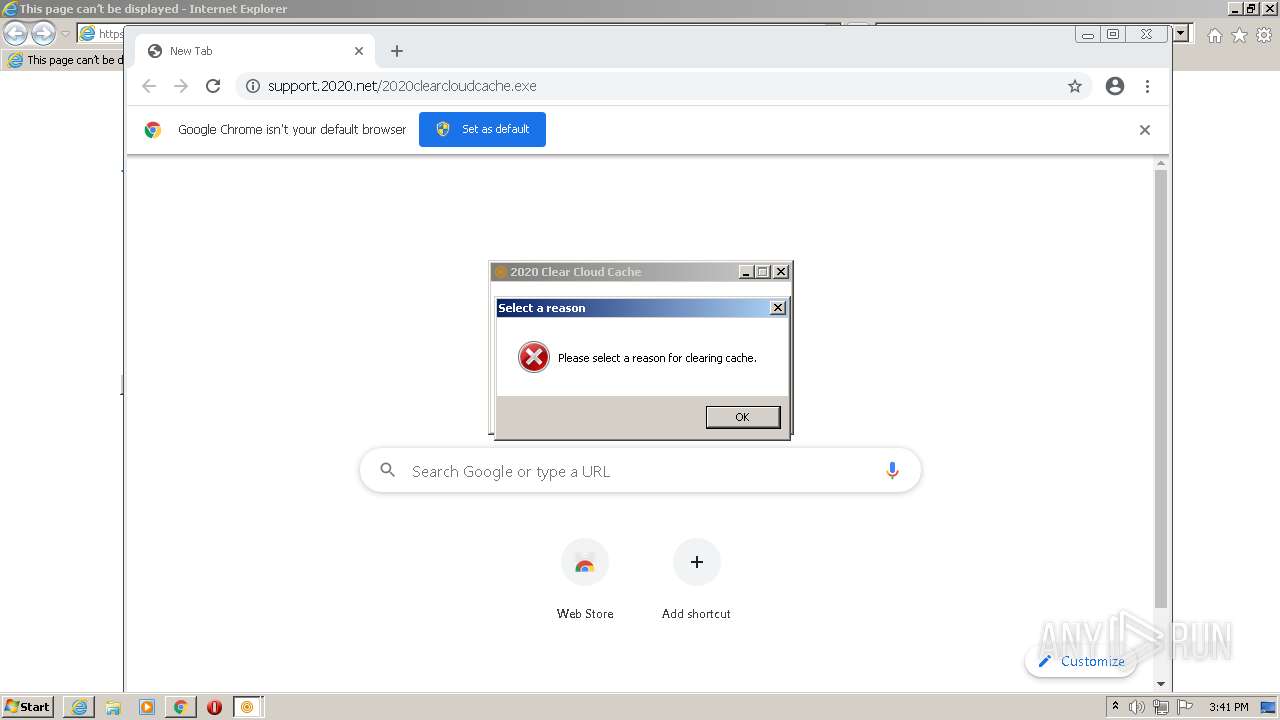
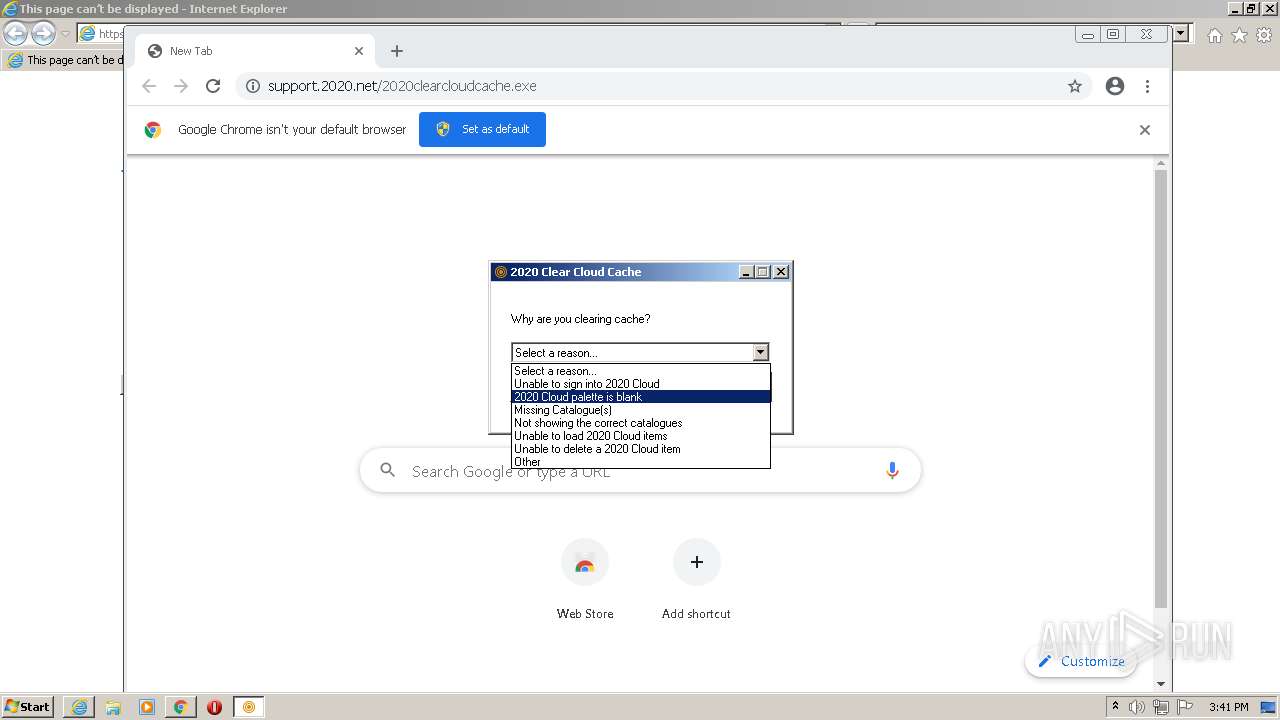
MALICIOUS
Drops executable file immediately after starts
- chrome.exe (PID: 1804)
- chrome.exe (PID: 3520)
Application was dropped or rewritten from another process
- 2020clearcloudcache.exe (PID: 2208)
- 2020clearcloudcache.exe (PID: 1096)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2912)
- iexplore.exe (PID: 2340)
- iexplore.exe (PID: 876)
- iexplore.exe (PID: 3624)
Executable content was dropped or overwritten
- chrome.exe (PID: 1804)
- chrome.exe (PID: 3520)
Modifies files in Chrome extension folder
- chrome.exe (PID: 1804)
Drops a file with a compile date too recent
- chrome.exe (PID: 3520)
- chrome.exe (PID: 1804)
Checks supported languages
- 2020clearcloudcache.exe (PID: 2208)
- 2020clearcloudcache.exe (PID: 1096)
Reads mouse settings
- 2020clearcloudcache.exe (PID: 2208)
- 2020clearcloudcache.exe (PID: 1096)
Reads the computer name
- 2020clearcloudcache.exe (PID: 2208)
- 2020clearcloudcache.exe (PID: 1096)
Application launched itself
- 2020clearcloudcache.exe (PID: 2208)
Executed via COM
- iexplore.exe (PID: 3108)
INFO
Checks supported languages
- iexplore.exe (PID: 1000)
- iexplore.exe (PID: 2912)
- chrome.exe (PID: 3520)
- chrome.exe (PID: 1804)
- chrome.exe (PID: 304)
- chrome.exe (PID: 3484)
- chrome.exe (PID: 3652)
- chrome.exe (PID: 1068)
- chrome.exe (PID: 916)
- chrome.exe (PID: 3120)
- chrome.exe (PID: 4080)
- chrome.exe (PID: 3600)
- chrome.exe (PID: 712)
- chrome.exe (PID: 1536)
- chrome.exe (PID: 2040)
- chrome.exe (PID: 1012)
- chrome.exe (PID: 4068)
- chrome.exe (PID: 3460)
- chrome.exe (PID: 3972)
- chrome.exe (PID: 3192)
- chrome.exe (PID: 3428)
- chrome.exe (PID: 1536)
- chrome.exe (PID: 2720)
- chrome.exe (PID: 568)
- iexplore.exe (PID: 3108)
- iexplore.exe (PID: 2340)
- iexplore.exe (PID: 876)
- iexplore.exe (PID: 3624)
- chrome.exe (PID: 116)
Reads the computer name
- iexplore.exe (PID: 2912)
- chrome.exe (PID: 1804)
- chrome.exe (PID: 3484)
- iexplore.exe (PID: 1000)
- chrome.exe (PID: 3520)
- chrome.exe (PID: 3652)
- chrome.exe (PID: 4080)
- chrome.exe (PID: 4068)
- chrome.exe (PID: 3460)
- chrome.exe (PID: 3192)
- chrome.exe (PID: 3972)
- chrome.exe (PID: 1536)
- chrome.exe (PID: 568)
- iexplore.exe (PID: 3108)
- iexplore.exe (PID: 2340)
- iexplore.exe (PID: 876)
- iexplore.exe (PID: 3624)
Changes internet zones settings
- iexplore.exe (PID: 1000)
- iexplore.exe (PID: 3108)
Application launched itself
- iexplore.exe (PID: 1000)
- chrome.exe (PID: 1804)
- iexplore.exe (PID: 3108)
Reads settings of System Certificates
- iexplore.exe (PID: 1000)
- chrome.exe (PID: 3520)
- chrome.exe (PID: 1804)
- iexplore.exe (PID: 876)
- iexplore.exe (PID: 2340)
- iexplore.exe (PID: 3624)
- iexplore.exe (PID: 3108)
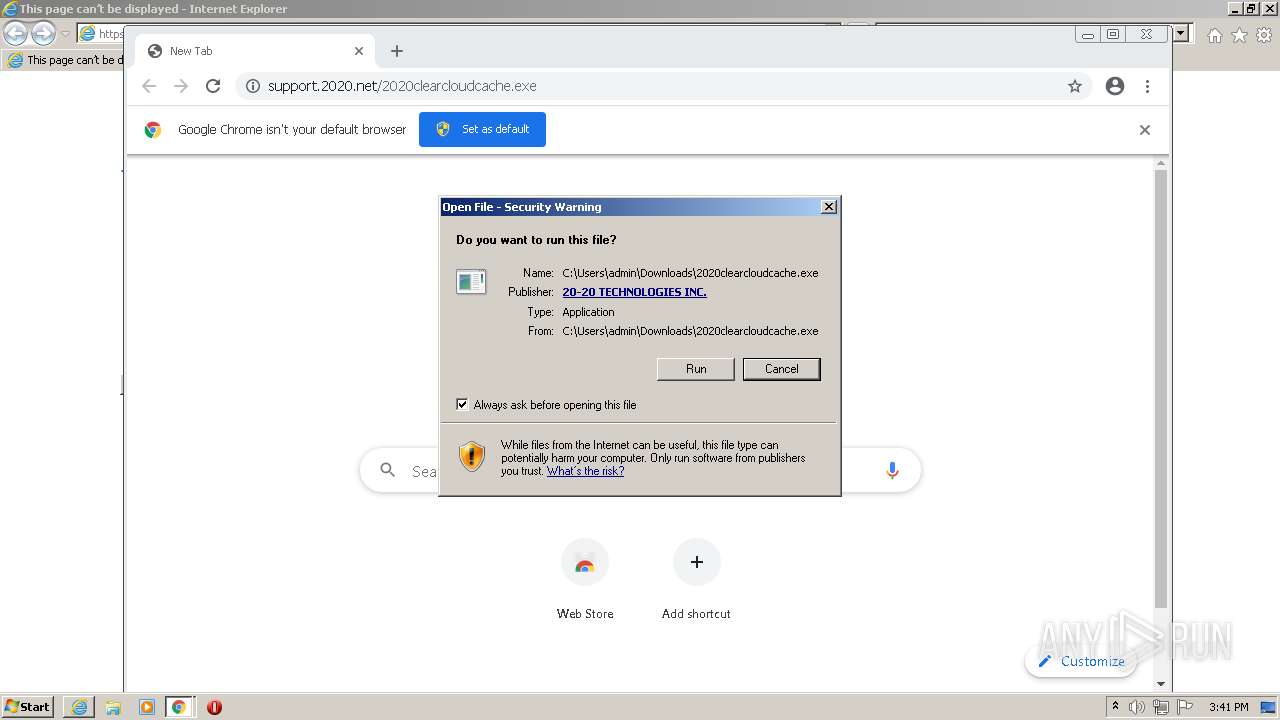
Manual execution by user
- chrome.exe (PID: 1804)
Reads the hosts file
- chrome.exe (PID: 3520)
- chrome.exe (PID: 1804)
Checks Windows Trust Settings
- iexplore.exe (PID: 1000)
- chrome.exe (PID: 1804)
- iexplore.exe (PID: 876)
- iexplore.exe (PID: 2340)
- iexplore.exe (PID: 3624)
- iexplore.exe (PID: 3108)
Reads internet explorer settings
- iexplore.exe (PID: 2912)
- iexplore.exe (PID: 2340)
- iexplore.exe (PID: 876)
- iexplore.exe (PID: 3624)
Creates files in the user directory
- iexplore.exe (PID: 1000)
- iexplore.exe (PID: 876)
Reads the date of Windows installation
- chrome.exe (PID: 3972)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2340)
Changes settings of System certificates
- iexplore.exe (PID: 2340)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
72
Monitored processes
31
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --field-trial-handle=1052,4136502380782065010,5016144197317449606,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=1224 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 304 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6e56d988,0x6e56d998,0x6e56d9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 568 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1052,4136502380782065010,5016144197317449606,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=4032 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 712 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,4136502380782065010,5016144197317449606,131072 --enable-features=PasswordImport --lang=en-US --instant-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1936 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 876 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3108 CREDAT:537610 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 916 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,4136502380782065010,5016144197317449606,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1904 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1000 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://support.2020.net/2020clearcloudcache.exe" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1012 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,4136502380782065010,5016144197317449606,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3188 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1068 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,4136502380782065010,5016144197317449606,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2248 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1096 | "C:\Users\admin\Downloads\2020clearcloudcache.exe" ! | C:\Users\admin\Downloads\2020clearcloudcache.exe | 2020clearcloudcache.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: 2020 Clear Cloud Cache Exit code: 0 Version: 2.0.0.3 Modules
| |||||||||||||||
Total events
46 456
Read events
45 894
Write events
551
Delete events
11
Modification events
| (PID) Process: | (1000) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (1000) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (1000) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30960123 | |||
| (PID) Process: | (1000) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (1000) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30960123 | |||
| (PID) Process: | (1000) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1000) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1000) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1000) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1000) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
4
Suspicious files
130
Text files
143
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1804 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-6283B3AB-70C.pma | — | |
MD5:— | SHA256:— | |||
| 1000 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:9120B5FBC3A9B08D7513C11933B16E5E | SHA256:1E6E798D664A209751A9D3B345FEFFEBDB4B27EDAC18E182B492FE637EF6D30D | |||
| 1000 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:013889ED18205FDFC42D77439AA8BE5F | SHA256:9F8E38B887BF339E88E4C5A11D38D91C5123BB16A2904EE302A6FC0107B09B05 | |||
| 1000 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | der | |
MD5:461878113201B1B6A1E6FB596DBF9E23 | SHA256:3C914BDE72BBC1D4C13788F9BE2E5DF64AF834394460D381ABFEA42E28F3E4A8 | |||
| 1000 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:7CBB6D9F4FD8F04352A30619BA0AF7BF | SHA256:CAD7607E0BD8DCFAFE85B064683A912499C75930FCA1B23FD7CBF20328E7629C | |||
| 1000 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | binary | |
MD5:99C1F1E106AEF13D5BED2E6DA3AED8A1 | SHA256:DA329B117F57FC9BCBECFB3CA8925724B70E6F9B9665555EB9893E4DFA0A1016 | |||
| 304 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 1000 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 1000 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\urlblockindex[2].bin | binary | |
MD5:FA518E3DFAE8CA3A0E495460FD60C791 | SHA256:775853600060162C4B4E5F883F9FD5A278E61C471B3EE1826396B6D129499AA7 | |||
| 1000 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\favicon[2].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
71
DNS requests
32
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1096 | 2020clearcloudcache.exe | GET | 301 | 23.100.55.220:80 | http://support.2020.net/dashboardcontent/versiondata/ccc.txt | IE | html | 194 b | suspicious |
1000 | iexplore.exe | GET | 200 | 23.216.77.80:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?c9717ba240406512 | US | compressed | 4.70 Kb | whitelisted |
1096 | 2020clearcloudcache.exe | GET | 200 | 20.38.100.129:80 | http://pubfilexfer2020prod.z20.web.core.windows.net/dashboardcontent/versiondata/ccc.txt | US | text | 24 b | suspicious |
2340 | iexplore.exe | GET | 301 | 23.100.55.220:80 | http://support.2020.net/apps/stats/2020clearcloudcache.exe.html | IE | html | 194 b | suspicious |
2340 | iexplore.exe | GET | 200 | 20.38.100.129:80 | http://pubfilexfer2020prod.z20.web.core.windows.net/apps/stats/2020clearcloudcache.exe.html | US | html | 526 b | suspicious |
3520 | chrome.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | crx | 242 Kb | whitelisted |
2340 | iexplore.exe | GET | 200 | 142.250.186.163:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
1000 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
1000 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
3624 | iexplore.exe | GET | 200 | 142.250.184.206:80 | http://crls.pki.goog/gts1c3/QOvJ0N1sT2A.crl | US | der | 12.0 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2912 | iexplore.exe | 23.100.55.220:443 | support.2020.net | Microsoft Corporation | IE | suspicious |
— | — | 131.253.33.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
— | — | 152.199.19.161:443 | r20swj13mr.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3520 | chrome.exe | 142.250.186.110:443 | clients2.google.com | Google Inc. | US | whitelisted |
3520 | chrome.exe | 142.250.184.196:443 | www.google.com | Google Inc. | US | whitelisted |
3520 | chrome.exe | 142.250.185.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3520 | chrome.exe | 142.250.186.97:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
3520 | chrome.exe | 142.250.181.227:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1000 | iexplore.exe | 152.199.19.161:443 | r20swj13mr.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
— | — | 23.100.55.220:443 | support.2020.net | Microsoft Corporation | IE | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
support.2020.net |
| suspicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2912 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2912 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2912 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2912 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2912 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3520 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM TIMEWAIT ACK with wrong seq |
1096 | 2020clearcloudcache.exe | Potential Corporate Privacy Violation | ET POLICY Autoit Windows Automation tool User-Agent in HTTP Request - Possibly Hostile |
1096 | 2020clearcloudcache.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
3520 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM TIMEWAIT ACK with wrong seq |
1096 | 2020clearcloudcache.exe | Potential Corporate Privacy Violation | ET POLICY Autoit Windows Automation tool User-Agent in HTTP Request - Possibly Hostile |