| download: | /my_list/s/ac2439d58e872e3102d8fb3113d7c25e.m3u8 |
| Full analysis: | https://app.any.run/tasks/8a8f0211-0525-4426-94c7-7ccf9e232a71 |
| Verdict: | Malicious activity |
| Analysis date: | August 10, 2024, 14:52:30 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | M3U playlist, ASCII text |
| MD5: | 17226EFA7D4F0DB9A66DD944EE946648 |
| SHA1: | 70C967BF825565EEC2B3C1D44B3993FEAD4884A7 |
| SHA256: | 4191B39C77768550D4930E87A5B7D1D7EB3124D1F53F1C2263485DFEDC482E89 |
| SSDEEP: | 6:PsvjLe2sEG3LXxd/T0d/tFSwAvM/iYJdInG0dvS:PsPen/W/LSwCM/tJdIX6 |
MALICIOUS
No malicious indicators.SUSPICIOUS
There is functionality for taking screenshot (YARA)
- vlc.exe (PID: 6384)
Connects to the server without a host name
- vlc.exe (PID: 6384)
INFO
May use AI service
- vlc.exe (PID: 6384)
Checks supported languages
- vlc.exe (PID: 6384)
Reads the computer name
- vlc.exe (PID: 6384)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .m3u | | | Extended M3U playlist (100) |
|---|
Total processes
132
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 6384 | "C:\Program Files\VideoLAN\VLC\vlc.exe" --started-from-file C:\Users\admin\AppData\Local\Temp\ac2439d58e872e3102d8fb3113d7c25e.m3u8.m3u | C:\Program Files\VideoLAN\VLC\vlc.exe | explorer.exe | ||||||||||||
User: admin Company: VideoLAN Integrity Level: MEDIUM Description: VLC media player Version: 3.0.11 Modules
| |||||||||||||||
Total events
2 250
Read events
2 250
Write events
0
Delete events
0
Modification events
Executable files
1
Suspicious files
0
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6384 | vlc.exe | C:\Users\admin\AppData\Roaming\vlc\vlc-qt-interface.ini.dh6384 | ini | |
MD5:71F227191ECFE1E9A197B5E3EB085118 | SHA256:6305067AC6AFC72768DCC8FFAC9A6512C019AB118F6418A5FF55C8779AA980CF | |||
| 6384 | vlc.exe | C:\Users\admin\AppData\Roaming\vlc\vlc-qt-interface.ini.ZP6384 | text | |
MD5:71F227191ECFE1E9A197B5E3EB085118 | SHA256:6305067AC6AFC72768DCC8FFAC9A6512C019AB118F6418A5FF55C8779AA980CF | |||
| 6384 | vlc.exe | C:\Users\admin\AppData\Roaming\vlc\vlc-qt-interface.ini | ini | |
MD5:71F227191ECFE1E9A197B5E3EB085118 | SHA256:6305067AC6AFC72768DCC8FFAC9A6512C019AB118F6418A5FF55C8779AA980CF | |||
| 6384 | vlc.exe | C:\Users\admin\AppData\Roaming\vlc\vlc-qt-interface.ini.lock | text | |
MD5:D225C18033C459B0C81506E9CFDDF8C6 | SHA256:4F7426B3FBDF8C2A026DB0F606787179CE5B4C425227A4FE582A9DBAA83058AE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
53
TCP/UDP connections
68
DNS requests
19
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
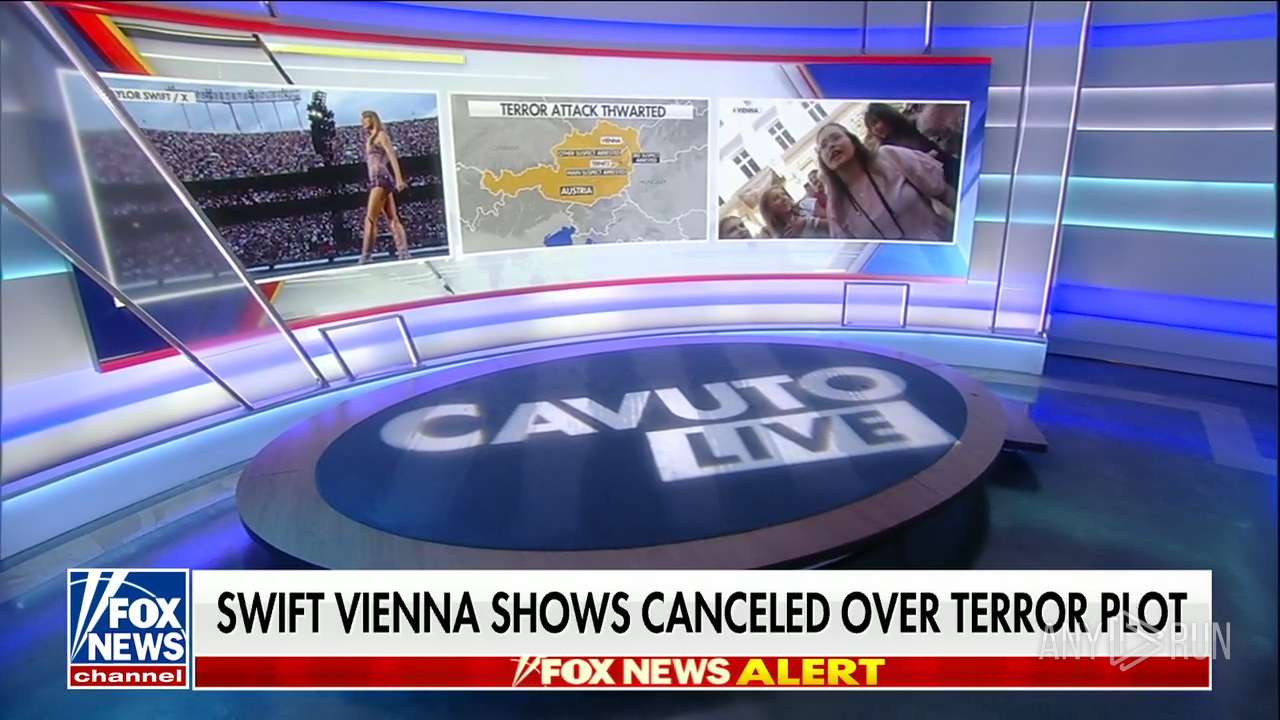
6384 | vlc.exe | GET | 302 | 143.244.60.97:80 | http://fl2.moveonjoy.com/FOX_News_Channel/index.m3u8?checkedby:iptvcat.com | US | text | 87 b | unknown |
6384 | vlc.exe | GET | 206 | 212.102.60.231:80 | http://212.102.60.231:80/FOX_News_Channel/index.m3u8?checkedby%3Aiptvcat.com | US | text | 206 b | unknown |
6384 | vlc.exe | GET | 206 | 212.102.60.231:80 | http://212.102.60.231:80/FOX_News_Channel/tracks-v1a1/mono.m3u8?checkedby%3Aiptvcat.com | US | text | 303 b | unknown |
6384 | vlc.exe | GET | 200 | 212.102.60.231:80 | http://212.102.60.231/FOX_News_Channel/tracks-v1a1/2024/08/10/14/52/15-05606.ts | US | binary | 1.09 Mb | unknown |
6384 | vlc.exe | GET | 200 | 212.102.60.231:80 | http://212.102.60.231/FOX_News_Channel/tracks-v1a1/2024/08/10/14/52/21-05072.ts | US | binary | 1.17 Mb | unknown |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 313 b | whitelisted |
6384 | vlc.exe | GET | 200 | 212.102.60.231:80 | http://212.102.60.231/FOX_News_Channel/tracks-v1a1/2024/08/10/14/52/26-05339.ts | US | binary | 1.23 Mb | unknown |
1568 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
6936 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | whitelisted |
6384 | vlc.exe | GET | 206 | 212.102.60.231:80 | http://212.102.60.231:80/FOX_News_Channel/tracks-v1a1/mono.m3u8?checkedby%3Aiptvcat.com | US | text | 303 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3140 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1076 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6384 | vlc.exe | 143.244.60.97:80 | fl2.moveonjoy.com | Datacamp Limited | US | unknown |
6384 | vlc.exe | 212.102.60.231:80 | — | Datacamp Limited | US | unknown |
3140 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5336 | SearchApp.exe | 92.123.104.63:443 | www.bing.com | Akamai International B.V. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
fl2.moveonjoy.com |
| unknown |
www.bing.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
th.bing.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
Threats
Process | Message |
|---|---|
vlc.exe | main libvlc debug: VLC media player - 3.0.11 Vetinari
|
vlc.exe | main libvlc debug: Copyright © 1996-2020 the VideoLAN team
|
vlc.exe | main libvlc debug: revision 3.0.11-0-gdc0c5ced72
|
vlc.exe | main libvlc debug: configured with ../extras/package/win32/../../../configure '--enable-update-check' '--enable-lua' '--enable-faad' '--enable-flac' '--enable-theora' '--enable-avcodec' '--enable-merge-ffmpeg' '--enable-dca' '--enable-mpc' '--enable-libass' '--enable-schroedinger' '--enable-realrtsp' '--enable-live555' '--enable-dvdread' '--enable-shout' '--enable-goom' '--enable-caca' '--enable-qt' '--enable-skins2' '--enable-sse' '--enable-mmx' '--enable-libcddb' '--enable-zvbi' '--disable-telx' '--enable-nls' '--host=x86_64-w64-mingw32' '--with-breakpad=https://win.crashes.videolan.org' 'host_alias=x86_64-w64-mingw32' 'PKG_CONFIG_LIBDIR=/home/jenkins/workspace/vlc-release/windows/vlc-release-win32-x64/contrib/x86_64-w64-mingw32/lib/pkgconfig'
|
vlc.exe | main libvlc debug: using multimedia timers as clock source
|
vlc.exe | main libvlc debug: min period: 1 ms, max period: 1000000 ms
|
vlc.exe | main libvlc debug: searching plug-in modules
|
vlc.exe | main libvlc debug: loading plugins cache file C:\Program Files\VideoLAN\VLC\plugins\plugins.dat
|
vlc.exe | main libvlc debug: recursively browsing `C:\Program Files\VideoLAN\VLC\plugins'
|
vlc.exe | main libvlc debug: plug-ins loaded: 494 modules
|