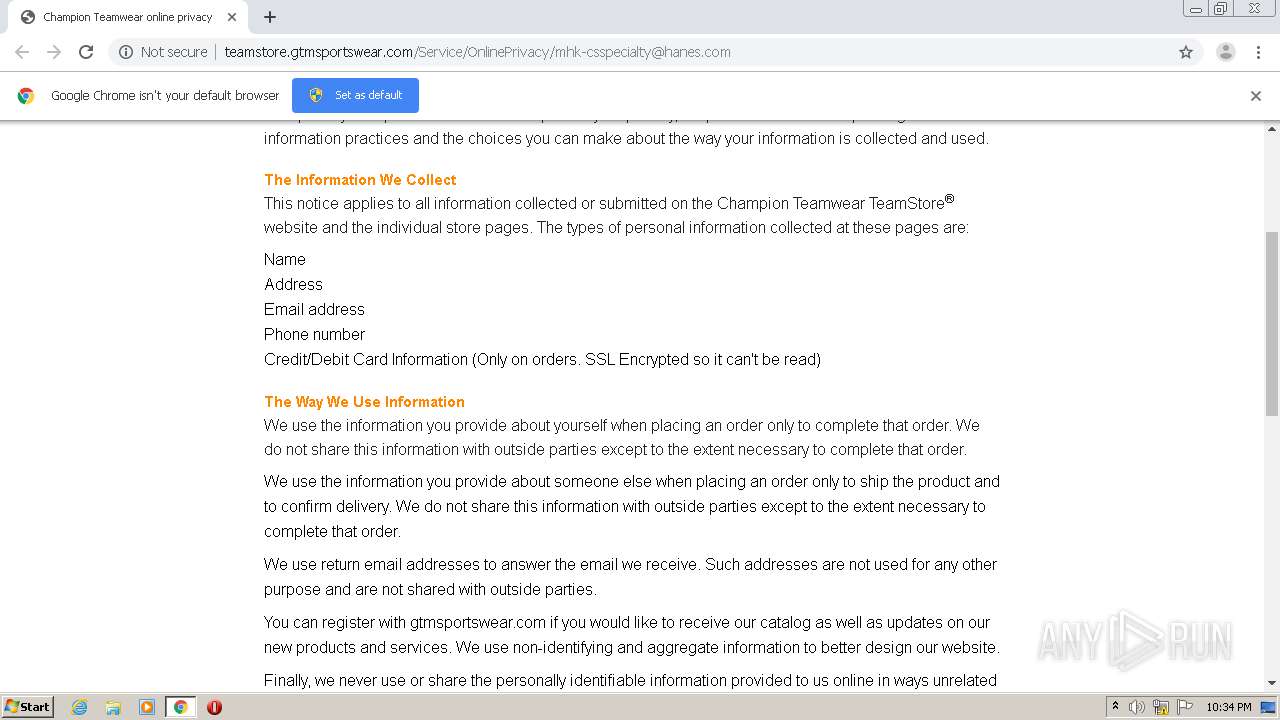
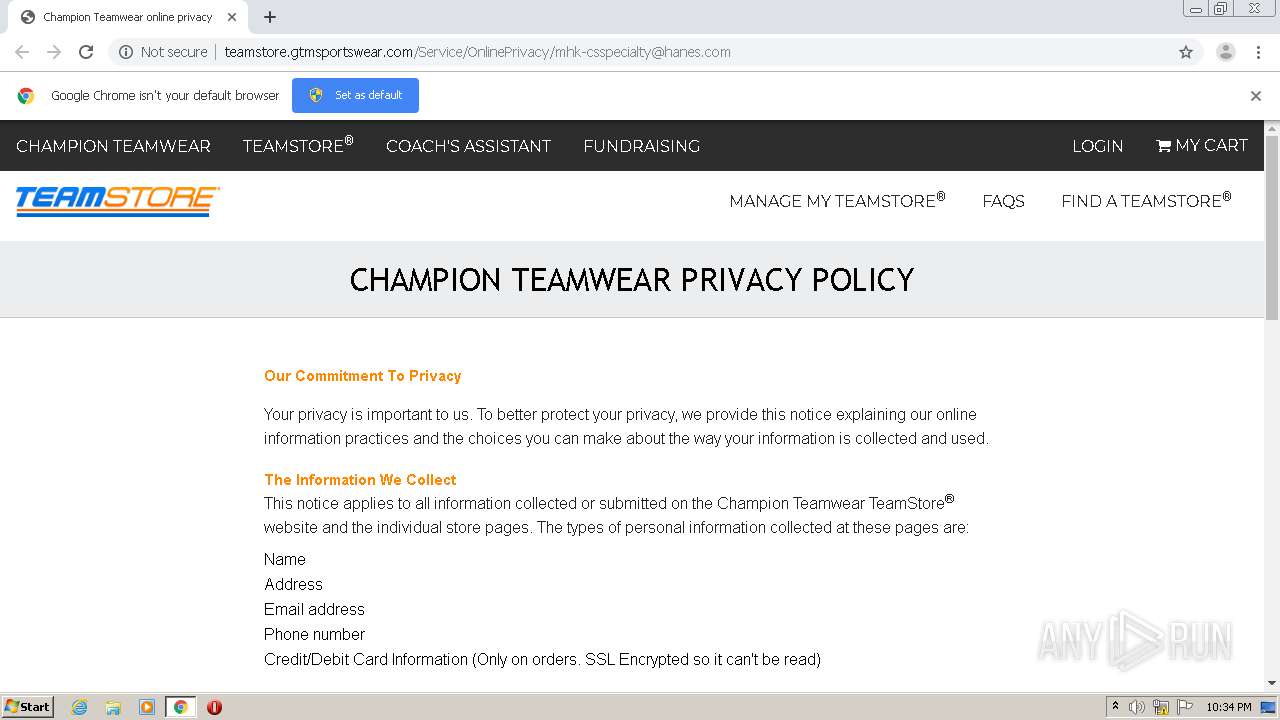
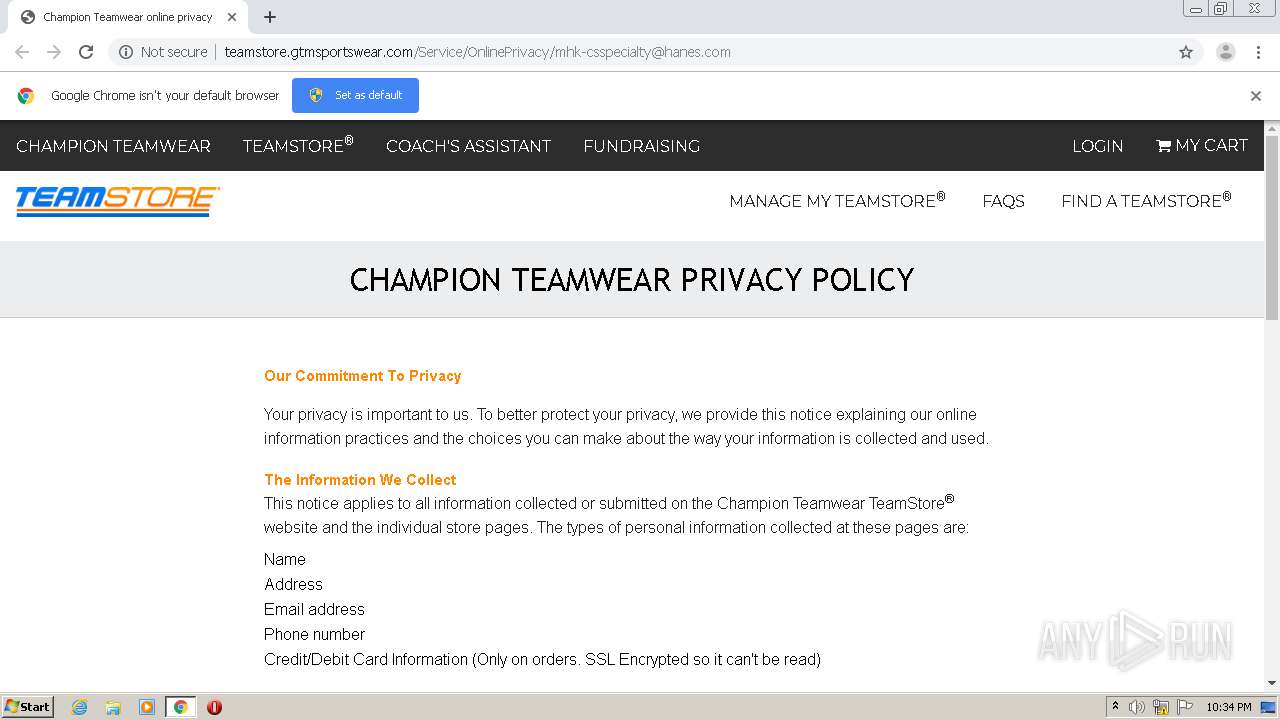
| URL: | http://teamstore.gtmsportswear.com/Service/OnlinePrivacy/mhk-csspecialty@hanes.com |
| Full analysis: | https://app.any.run/tasks/778ab615-44e0-414b-bb11-04d846beb863 |
| Verdict: | Malicious activity |
| Analysis date: | October 18, 2020, 21:33:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | B4D59A606DC66E92202A8540997F35C1 |
| SHA1: | 1A62CFE1F789041760D4C941DE210C211883B3F6 |
| SHA256: | 418F72D56426DCE304D3BB3D172FF85332CFE01A031692EEA31402A02808FA85 |
| SSDEEP: | 3:N1KKAzeCIBEp4WS0OSqMUndI:CKieCFp4n0O4UndI |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 2472)
Reads the hosts file
- chrome.exe (PID: 2472)
- chrome.exe (PID: 3820)
Reads settings of System Certificates
- chrome.exe (PID: 3820)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
48
Monitored processes
12
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 612 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=992,16734274377982927941,8283593752668918451,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=18273400684284800593 --mojo-platform-channel-handle=1008 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2008 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,16734274377982927941,8283593752668918451,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1293808073197165591 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2140 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2176 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,16734274377982927941,8283593752668918451,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=12166599533531780621 --mojo-platform-channel-handle=2728 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2228 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,16734274377982927941,8283593752668918451,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3489176987610481306 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2496 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2472 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://teamstore.gtmsportswear.com/Service/OnlinePrivacy/mhk-csspecialty@hanes.com" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2488 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2364 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2652 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,16734274377982927941,8283593752668918451,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11718431099103341650 --mojo-platform-channel-handle=3408 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3384 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,16734274377982927941,8283593752668918451,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=9814733474586286827 --mojo-platform-channel-handle=3412 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3620 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,16734274377982927941,8283593752668918451,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4422755733415322677 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2256 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3820 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,16734274377982927941,8283593752668918451,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=4937712581649303701 --mojo-platform-channel-handle=1668 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
621
Read events
558
Write events
59
Delete events
4
Modification events
| (PID) Process: | (2472) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2472) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2472) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2472) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2472) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2488) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2472-13247530435934500 |
Value: 259 | |||
| (PID) Process: | (2472) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2472) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2472) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2472) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
48
Text files
61
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F8CB4C4-9A8.pma | — | |
MD5:— | SHA256:— | |||
| 2472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\e7811a96-39d9-4ebc-a18b-5271a87f9106.tmp | — | |
MD5:— | SHA256:— | |||
| 2472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT | — | |
MD5:— | SHA256:— | |||
| 2472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF2d4069.TMP | text | |
MD5:— | SHA256:— | |||
| 2472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF2d4069.TMP | text | |
MD5:— | SHA256:— | |||
| 2472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
37
TCP/UDP connections
49
DNS requests
39
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3820 | chrome.exe | GET | 200 | 64.6.121.5:80 | http://teamstore.gtmsportswear.com/system.conf.js | US | text | 631 b | unknown |
3820 | chrome.exe | GET | 200 | 64.6.121.5:80 | http://teamstore.gtmsportswear.com/Content/default.css?1602274667519 | US | text | 71.8 Kb | unknown |
3820 | chrome.exe | GET | 200 | 64.6.121.5:80 | http://teamstore.gtmsportswear.com/Service/OnlinePrivacy/mhk-csspecialty@hanes.com | US | html | 6.01 Kb | unknown |
3820 | chrome.exe | GET | 200 | 64.6.121.5:80 | http://teamstore.gtmsportswear.com/Content/gtm_main.css?1602274667519 | US | text | 77.1 Kb | unknown |
3820 | chrome.exe | GET | 200 | 64.6.121.5:80 | http://teamstore.gtmsportswear.com/Scripts/iframeTools.js | US | text | 3.22 Kb | unknown |
3820 | chrome.exe | GET | 200 | 64.6.121.5:80 | http://teamstore.gtmsportswear.com/lib/traceur/traceur.min.js | US | text | 304 Kb | unknown |
3820 | chrome.exe | GET | 200 | 64.6.121.5:80 | http://teamstore.gtmsportswear.com/images/bg-html.png | US | image | 1.02 Kb | unknown |
3820 | chrome.exe | GET | 200 | 64.6.121.5:80 | http://teamstore.gtmsportswear.com/Scripts/jquery.validate.unobtrusive.js | US | text | 4.27 Kb | unknown |
3820 | chrome.exe | GET | 200 | 64.6.121.5:80 | http://teamstore.gtmsportswear.com/Content/Site.css?1602274667519 | US | text | 3.11 Kb | unknown |
3820 | chrome.exe | GET | 200 | 64.6.121.5:80 | http://teamstore.gtmsportswear.com/Content/default-responsive.css?1602274667519 | US | text | 178 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3820 | chrome.exe | 64.6.121.5:80 | teamstore.gtmsportswear.com | WTC Communications, Inc. | US | unknown |
3820 | chrome.exe | 172.217.16.195:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3820 | chrome.exe | 172.217.22.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3820 | chrome.exe | 94.31.29.32:443 | cdn.trackjs.com | netDNA | GB | suspicious |
3820 | chrome.exe | 216.58.212.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3820 | chrome.exe | 23.111.11.71:443 | a.omappapi.com | netDNA | US | unknown |
3820 | chrome.exe | 151.101.2.109:443 | cdn.polyfill.io | Fastly | US | suspicious |
3820 | chrome.exe | 216.58.207.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
3820 | chrome.exe | 172.217.16.174:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
— | — | 99.86.7.62:443 | api.omappapi.com | AT&T Services, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
teamstore.gtmsportswear.com |
| unknown |
accounts.google.com |
| shared |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
cdn.polyfill.io |
| whitelisted |
cdn.trackjs.com |
| whitelisted |
a.omappapi.com |
| whitelisted |
az416426.vo.msecnd.net |
| whitelisted |
championteamwear.com |
| unknown |