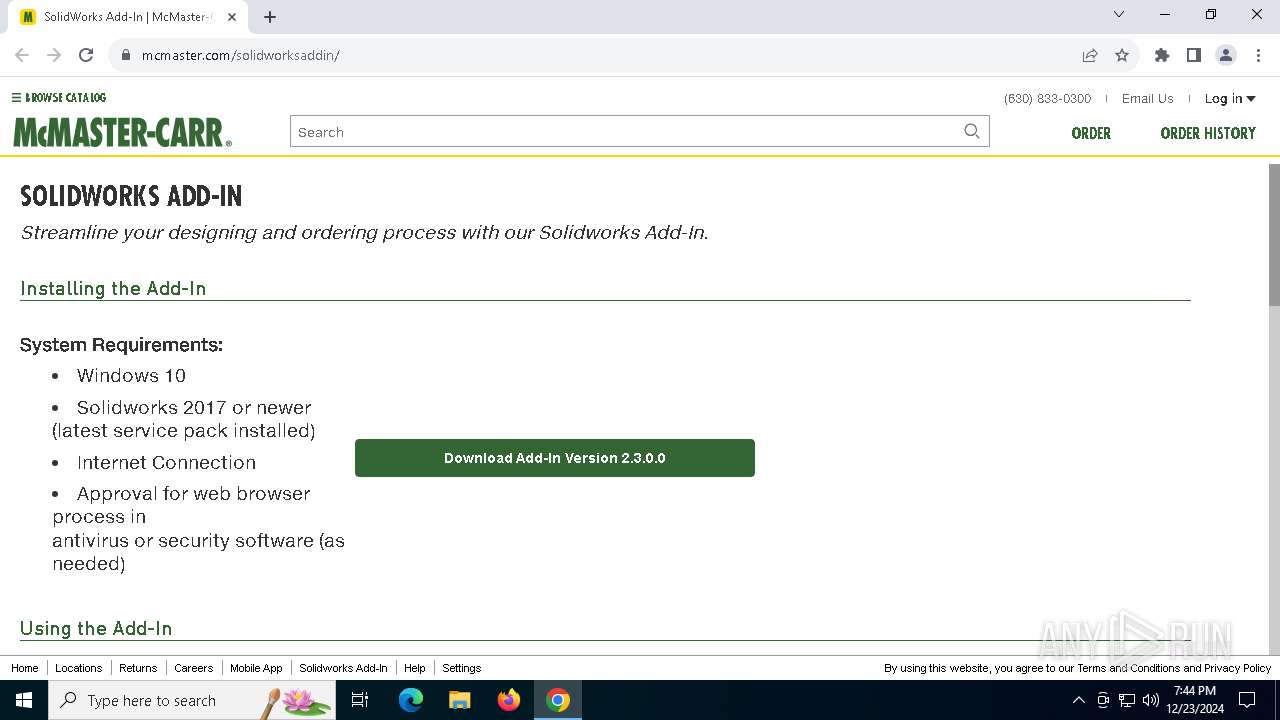
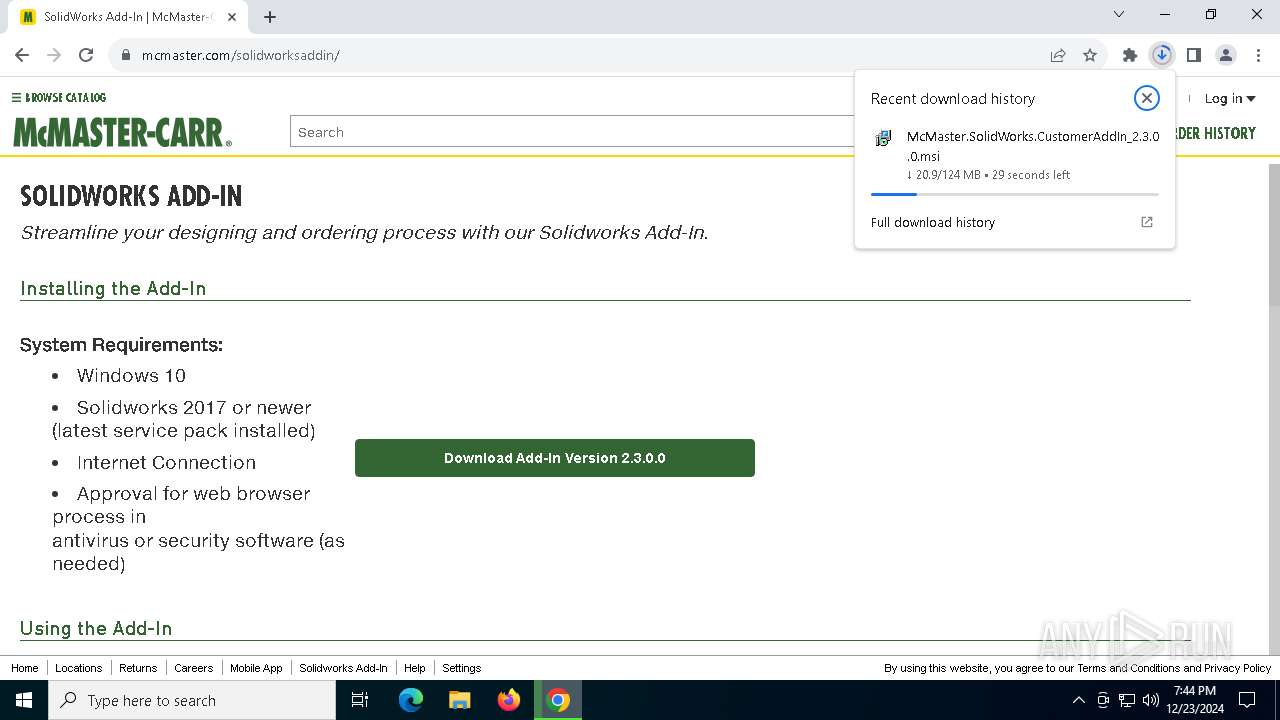
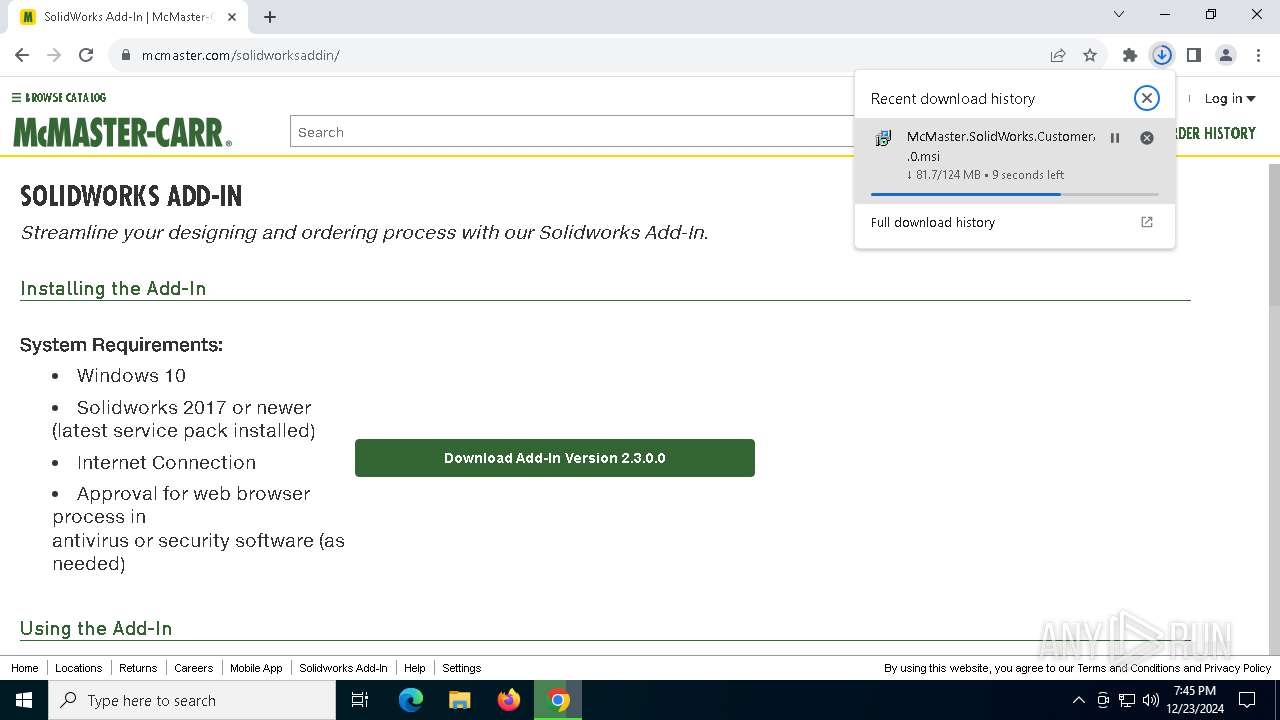
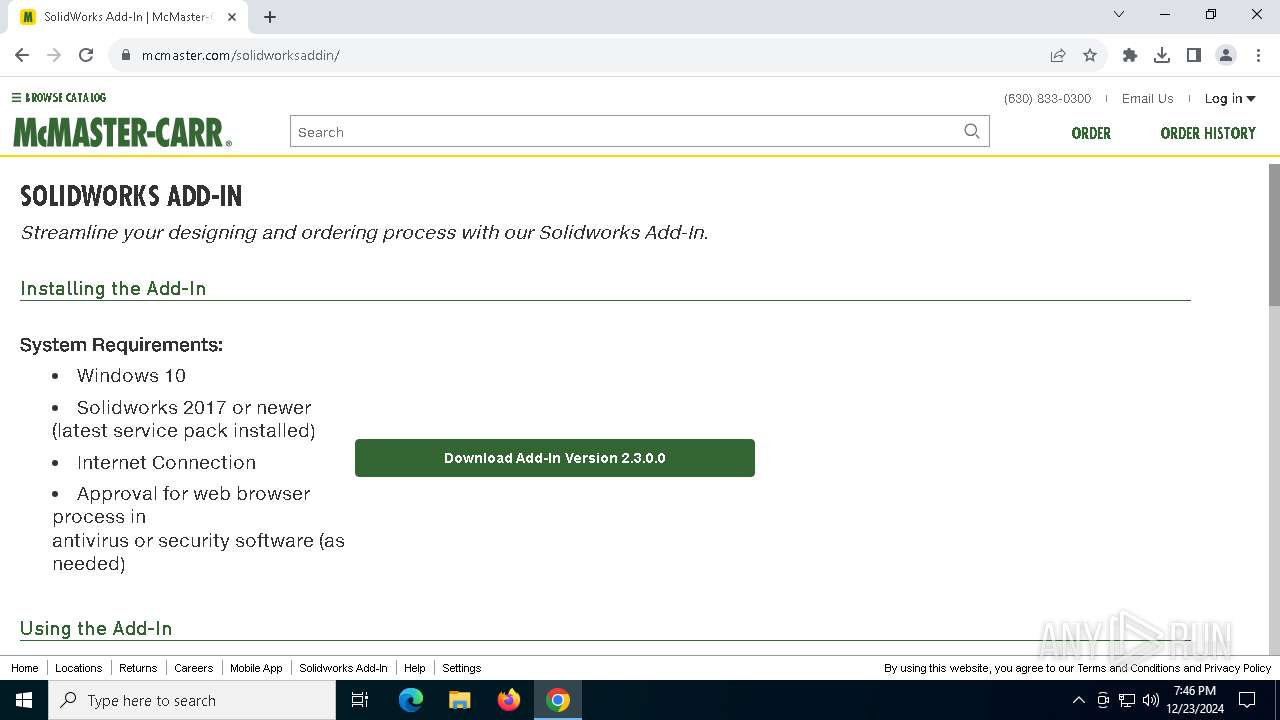
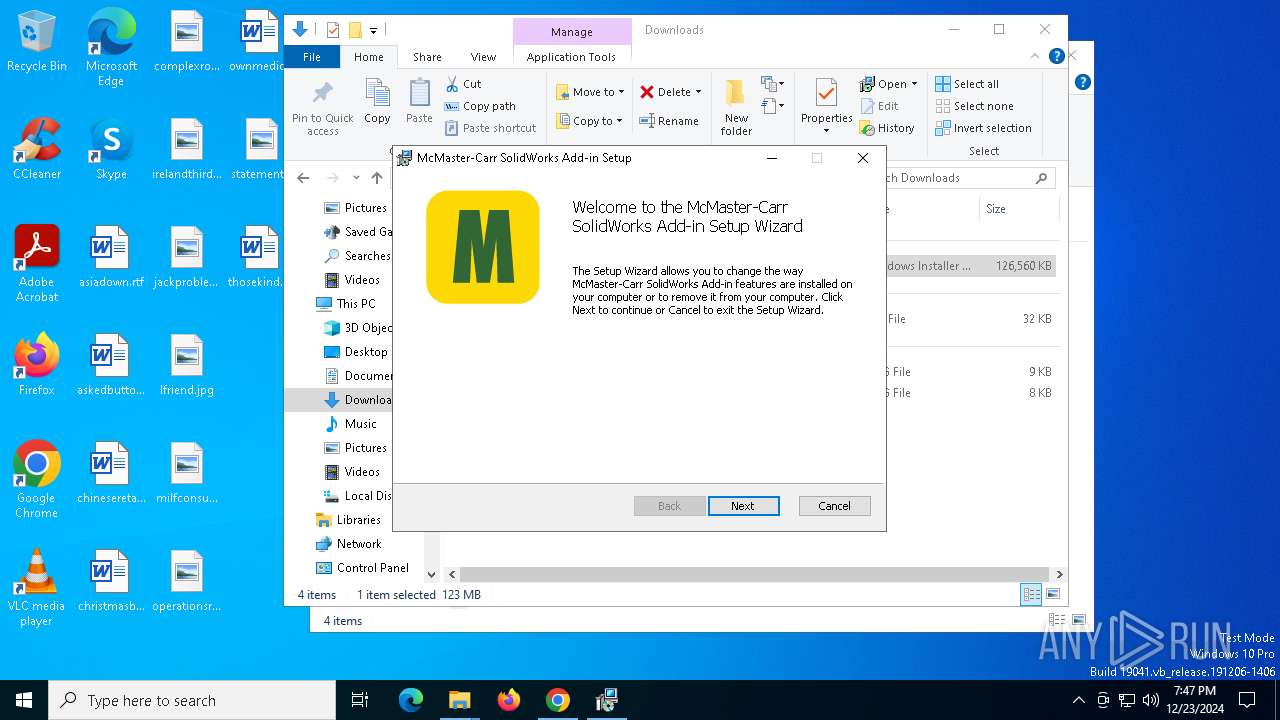
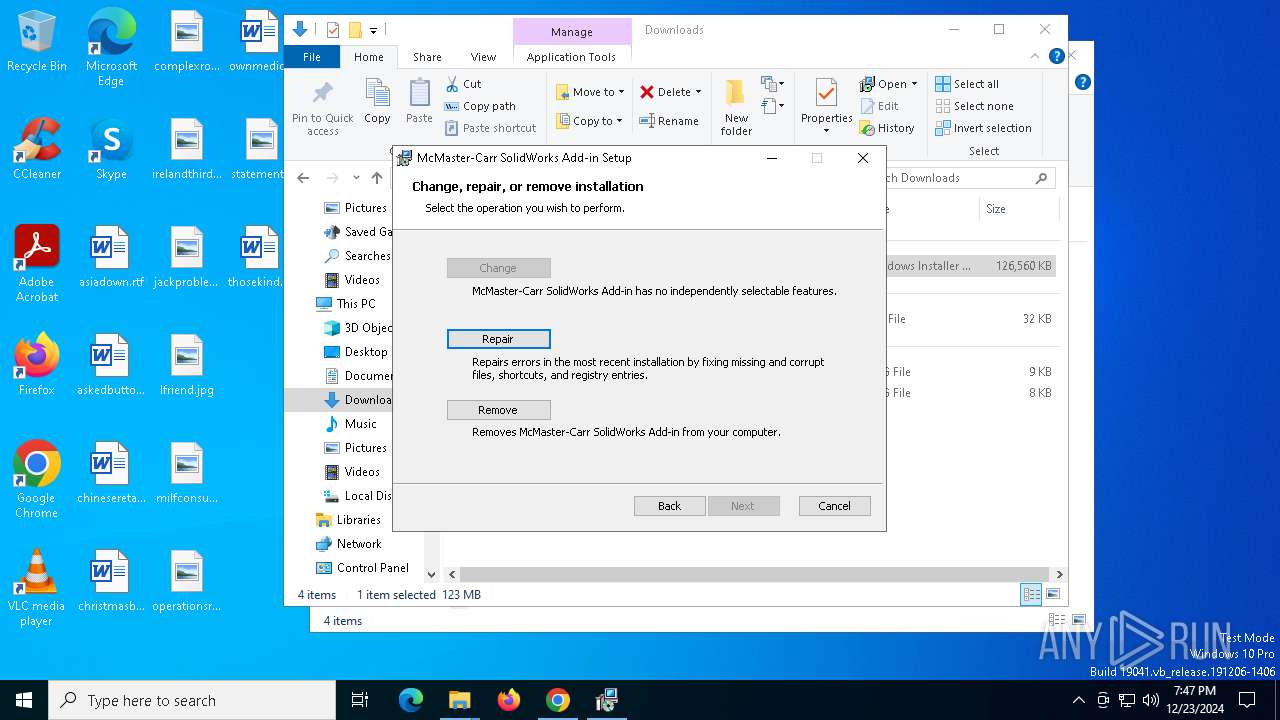
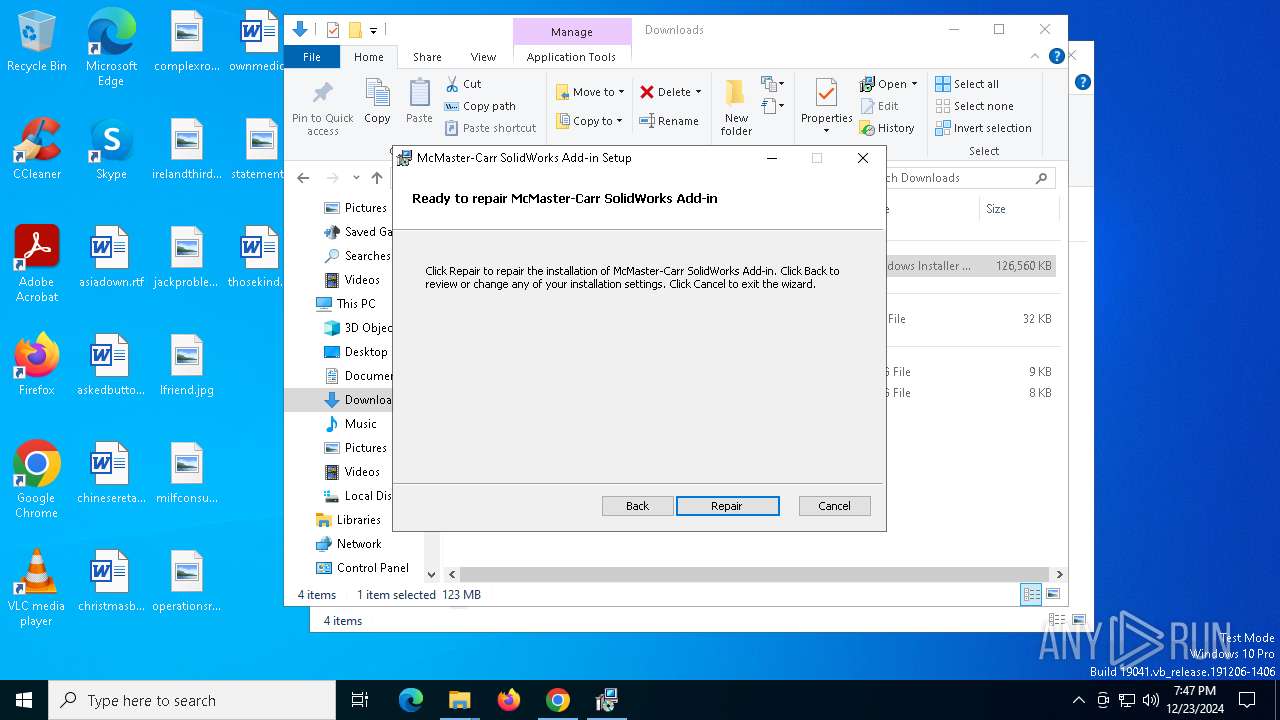
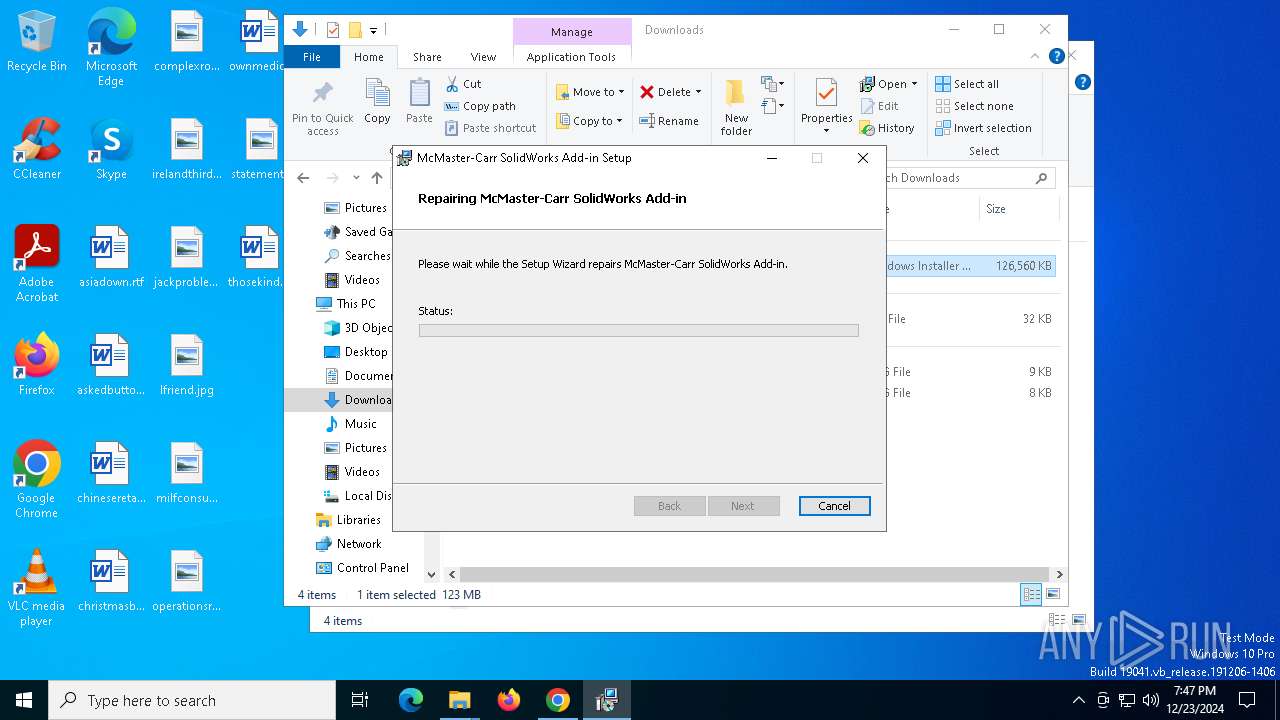
| URL: | https://www.mcmaster.com/solidworksaddin/ |
| Full analysis: | https://app.any.run/tasks/6294ba47-8dcd-4718-8589-45c1a944ba7d |
| Verdict: | Malicious activity |
| Analysis date: | December 23, 2024, 19:44:29 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MD5: | 24A6612641DD08FBEA4120BC1AB419C6 |
| SHA1: | E6D331C4768C6C855C79489D745AEB423EC1CAE6 |
| SHA256: | 417E8BF07721529B3E7EFC14DDCEDFCDAF8E17DAD76239CFA722A11387CF0172 |
| SSDEEP: | 3:N8DSLM+p9saBM+:2OLM+TBM+ |
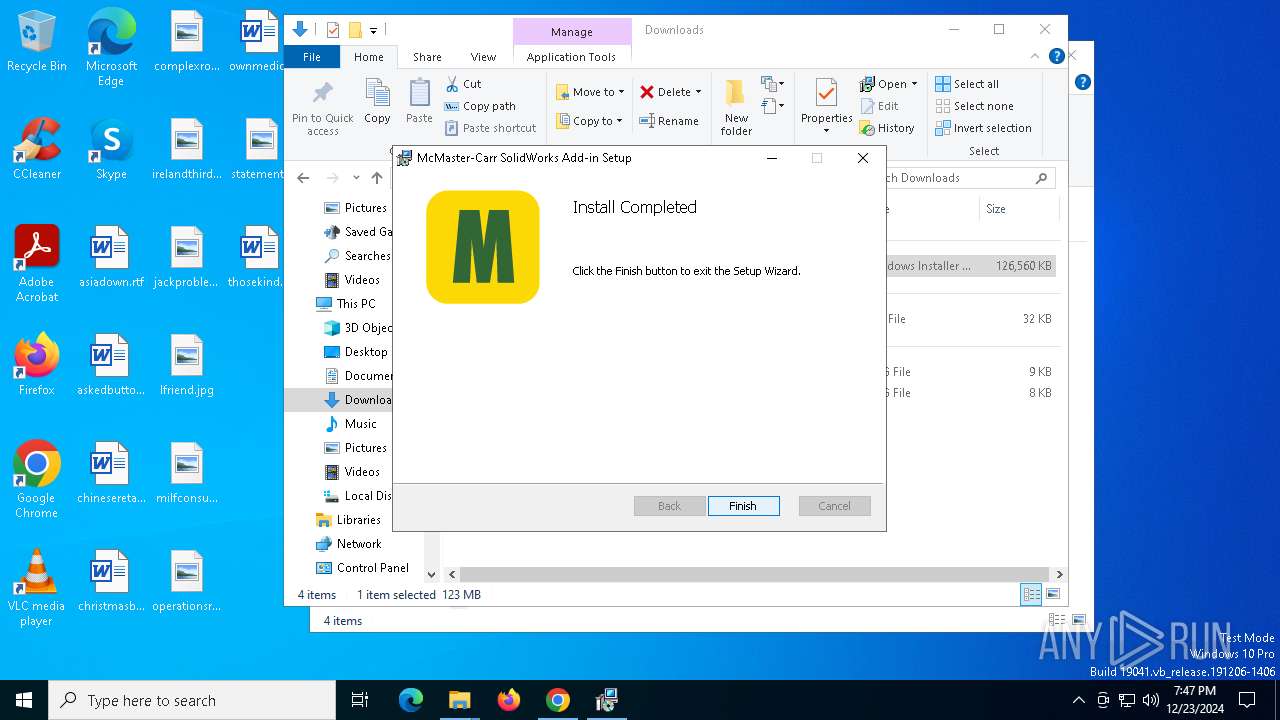
MALICIOUS
No malicious indicators.SUSPICIOUS
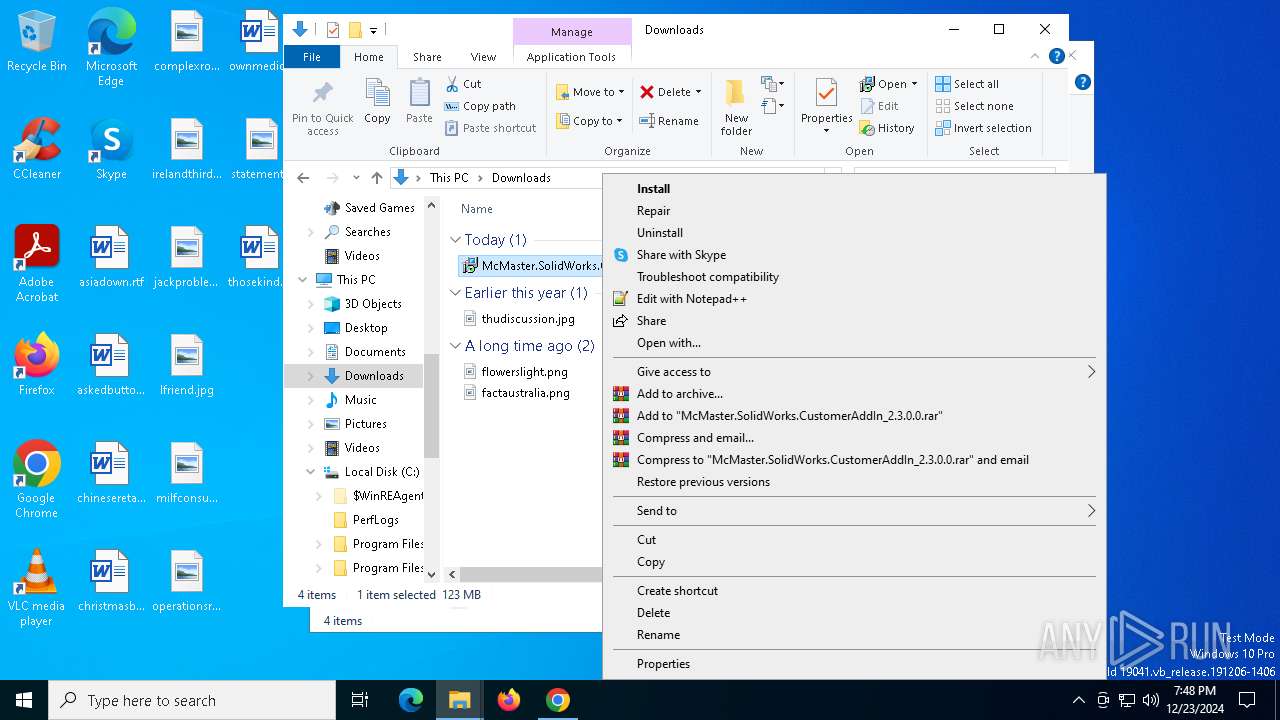
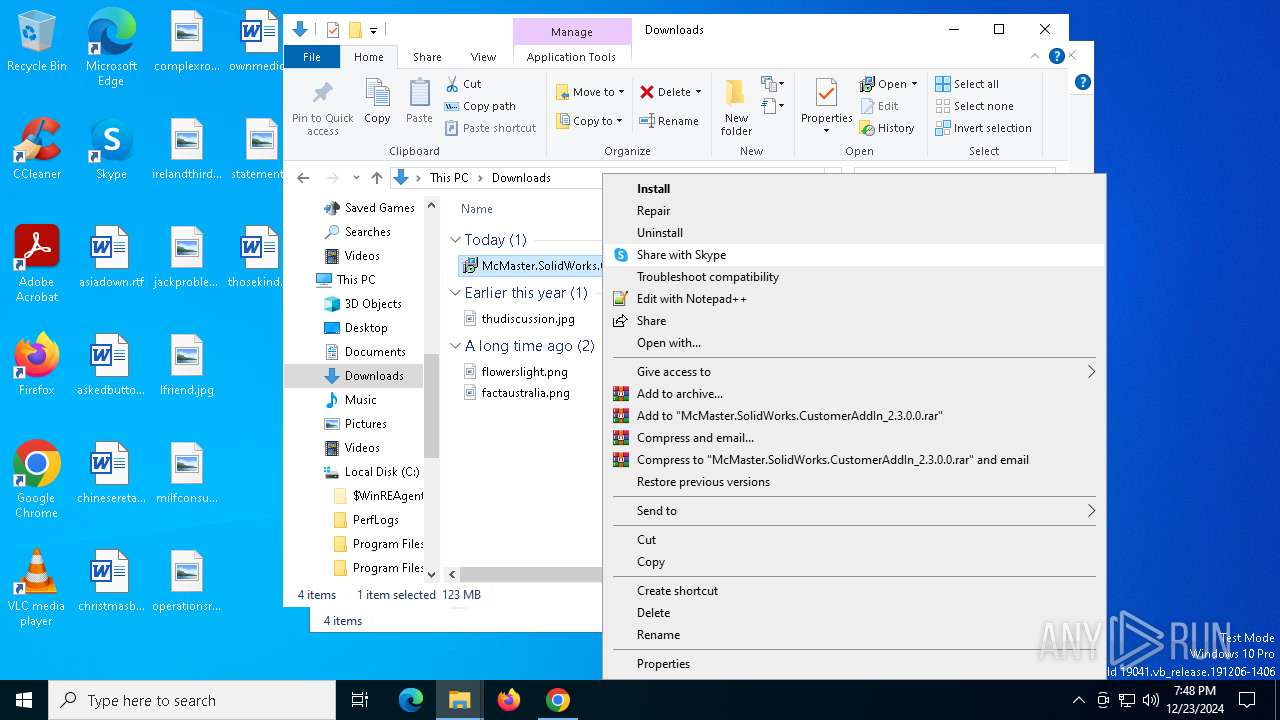
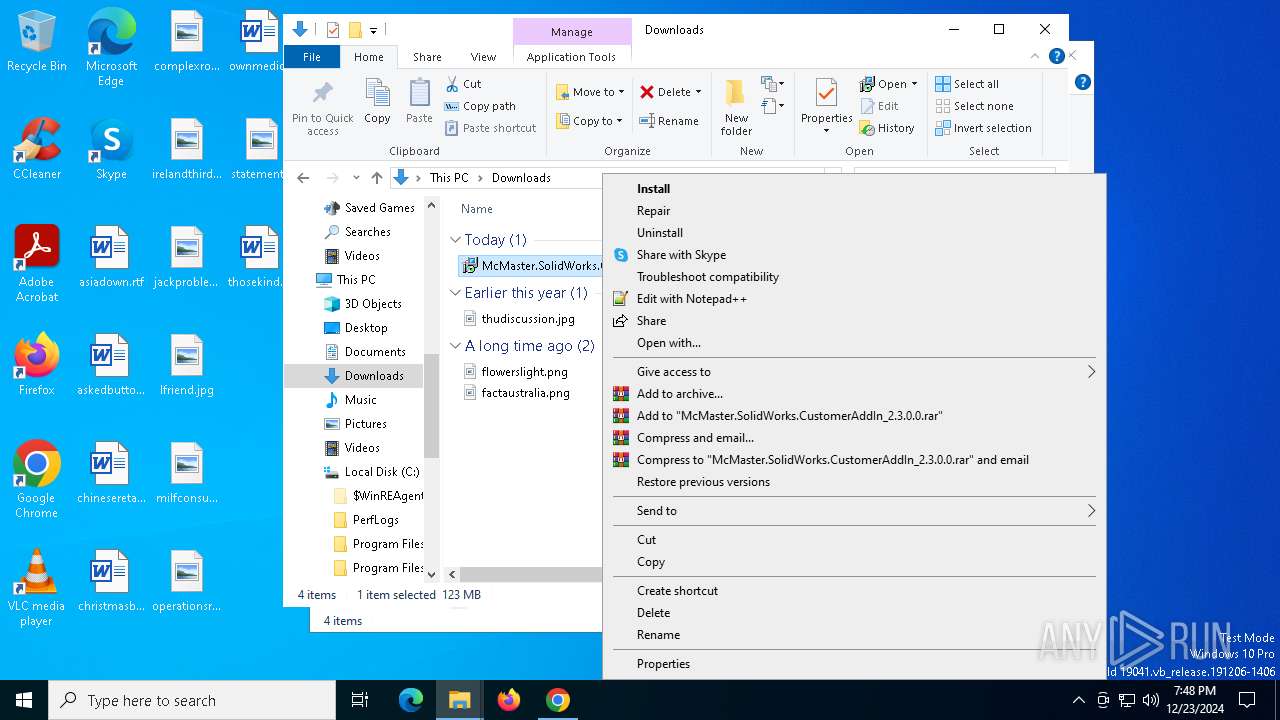
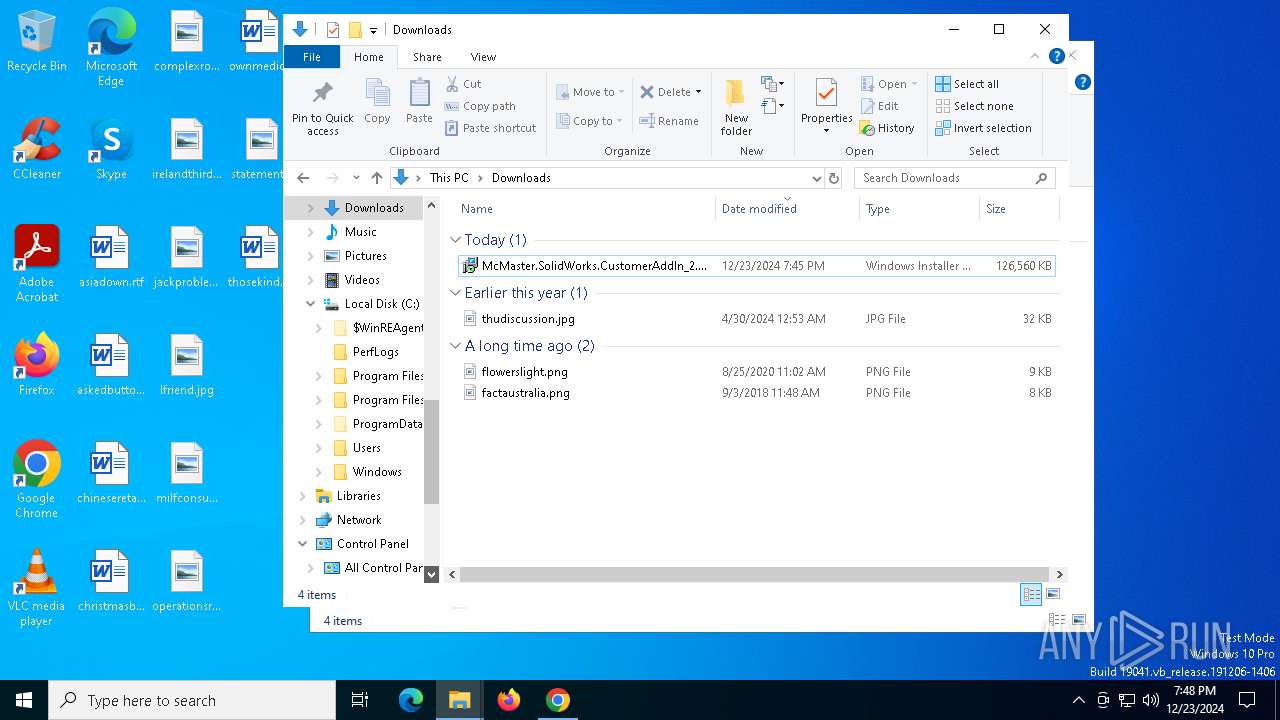
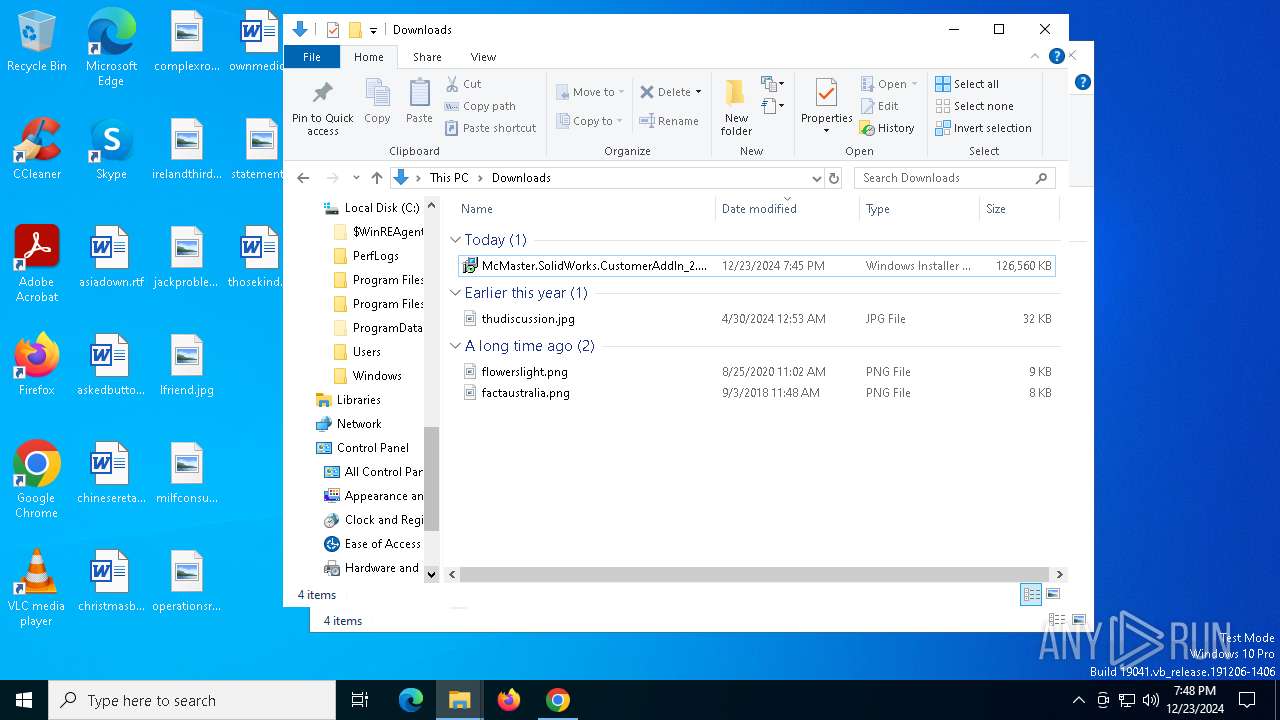
Executable content was dropped or overwritten
- rundll32.exe (PID: 2292)
- rundll32.exe (PID: 6820)
- rundll32.exe (PID: 420)
- rundll32.exe (PID: 6528)
- rundll32.exe (PID: 4628)
- rundll32.exe (PID: 5876)
- rundll32.exe (PID: 716)
- rundll32.exe (PID: 3816)
- rundll32.exe (PID: 5300)
- rundll32.exe (PID: 7148)
- rundll32.exe (PID: 6788)
Executes as Windows Service
- VSSVC.exe (PID: 4468)
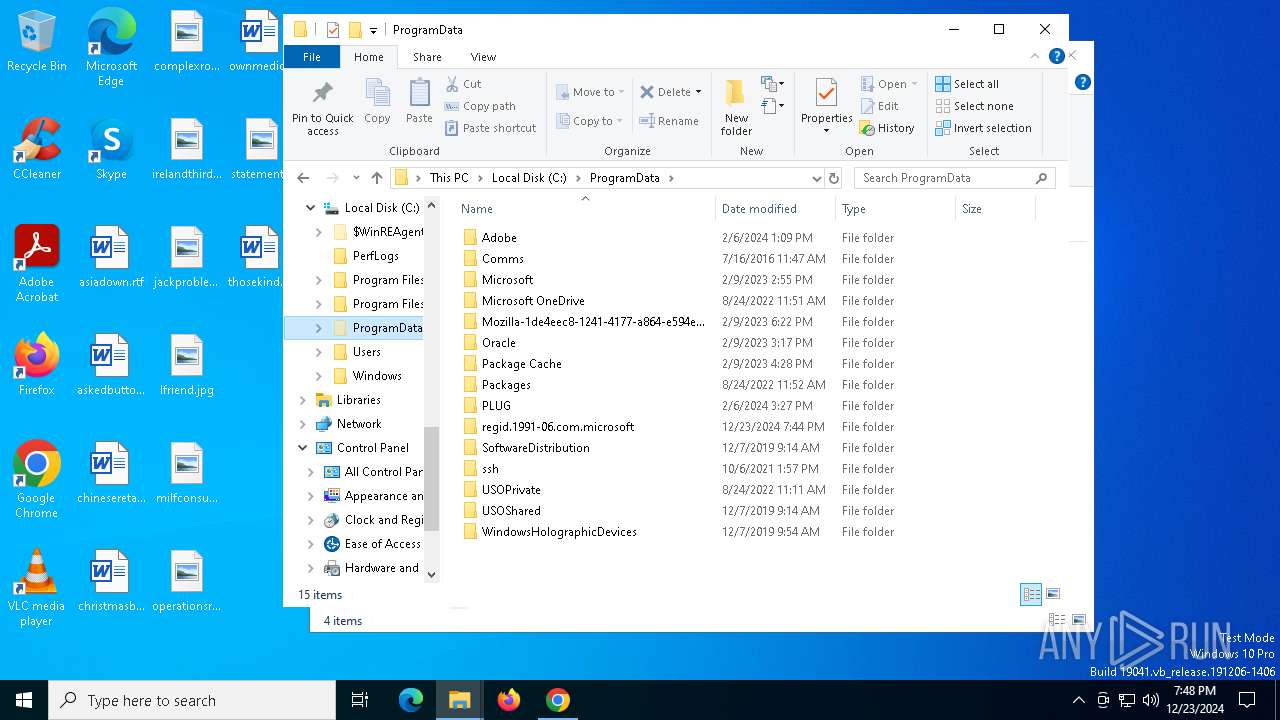
Creates/Modifies COM task schedule object
- msiexec.exe (PID: 7132)
INFO
Application launched itself
- chrome.exe (PID: 3544)
Reads the machine GUID from the registry
- SearchApp.exe (PID: 5064)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 5452)
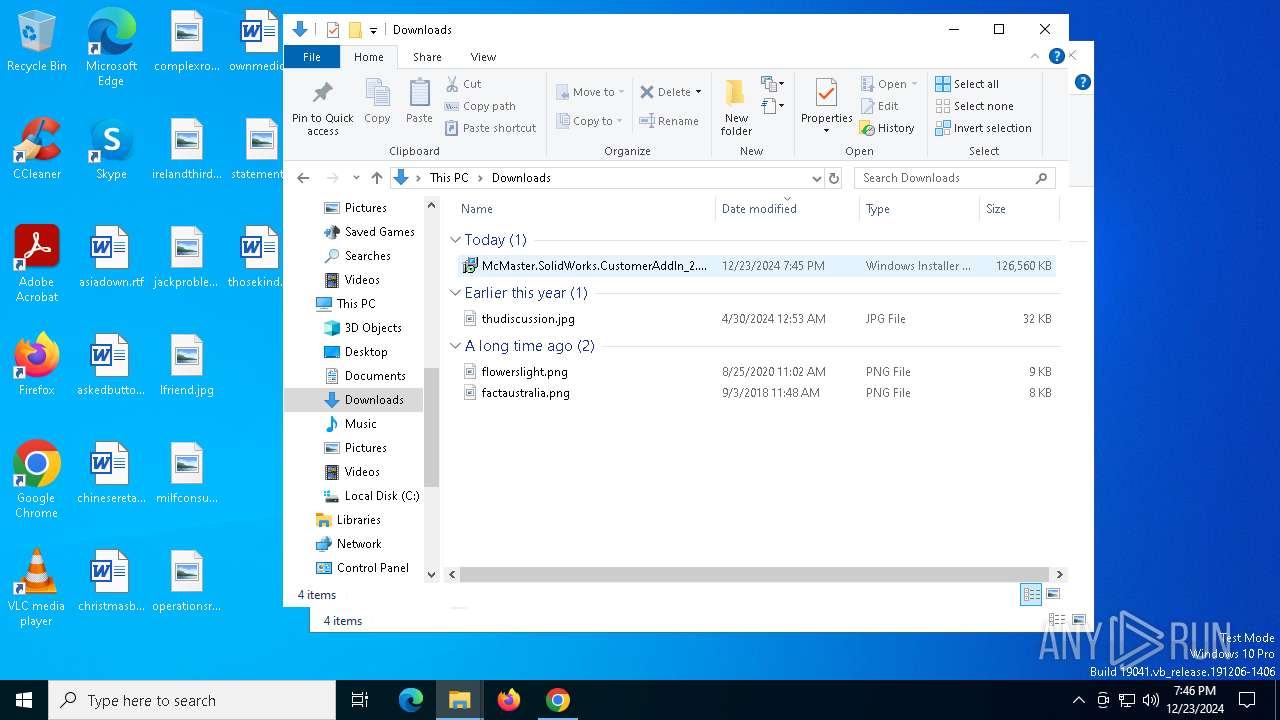
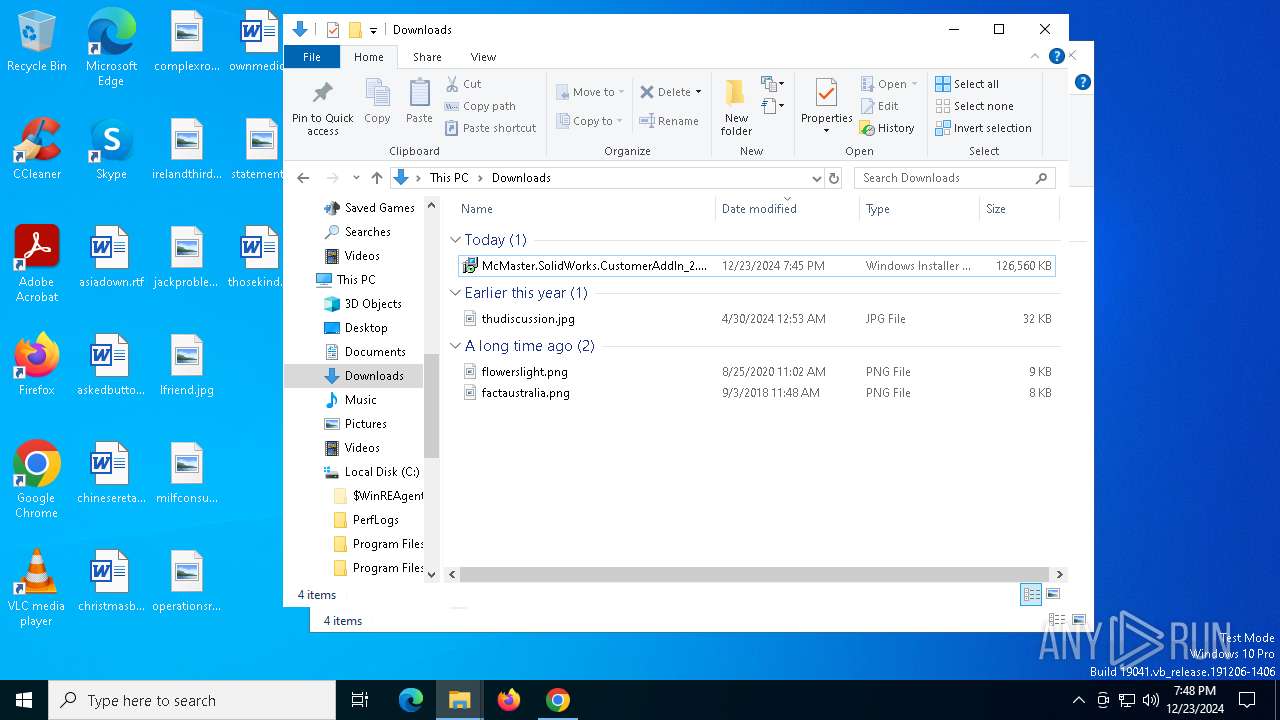
The process uses the downloaded file
- chrome.exe (PID: 6880)
- chrome.exe (PID: 3544)
Reads the computer name
- msiexec.exe (PID: 7132)
- msiexec.exe (PID: 2452)
- msiexec.exe (PID: 6416)
- msiexec.exe (PID: 5764)
Reads Microsoft Office registry keys
- chrome.exe (PID: 3544)
Checks supported languages
- msiexec.exe (PID: 2452)
- msiexec.exe (PID: 7132)
- msiexec.exe (PID: 6416)
- SearchApp.exe (PID: 5064)
- msiexec.exe (PID: 5764)
- msiexec.exe (PID: 6876)
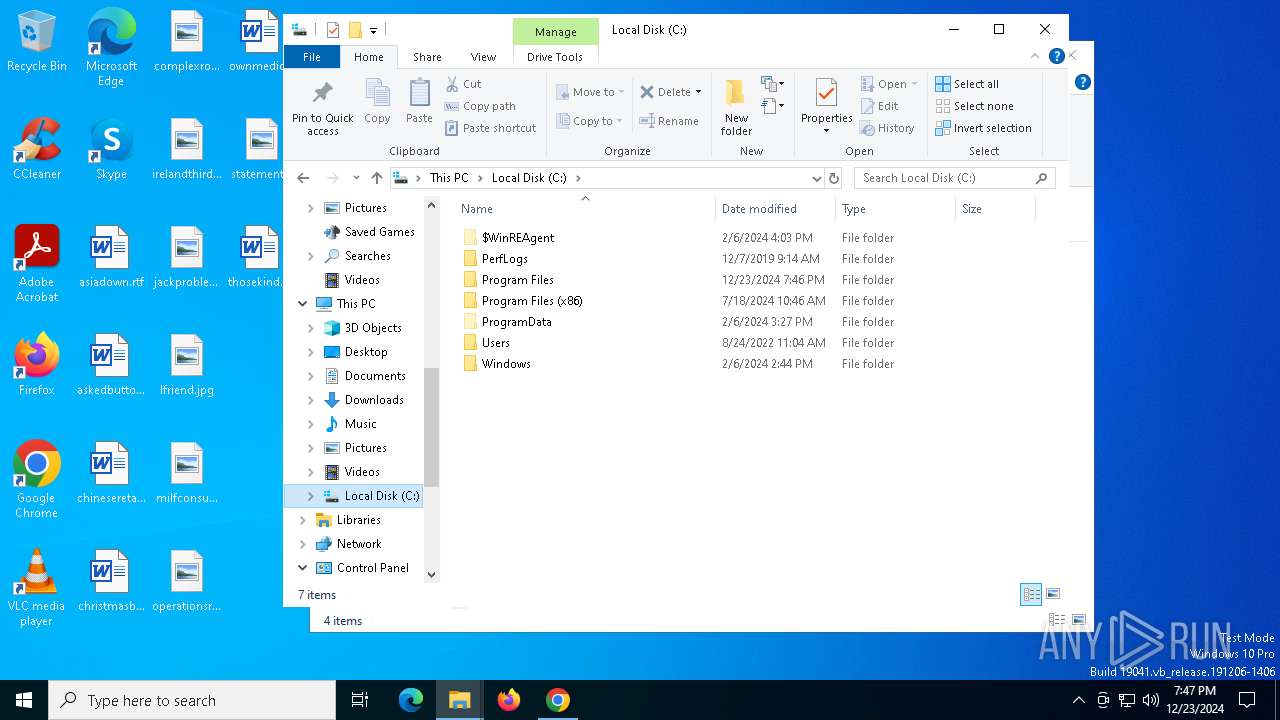
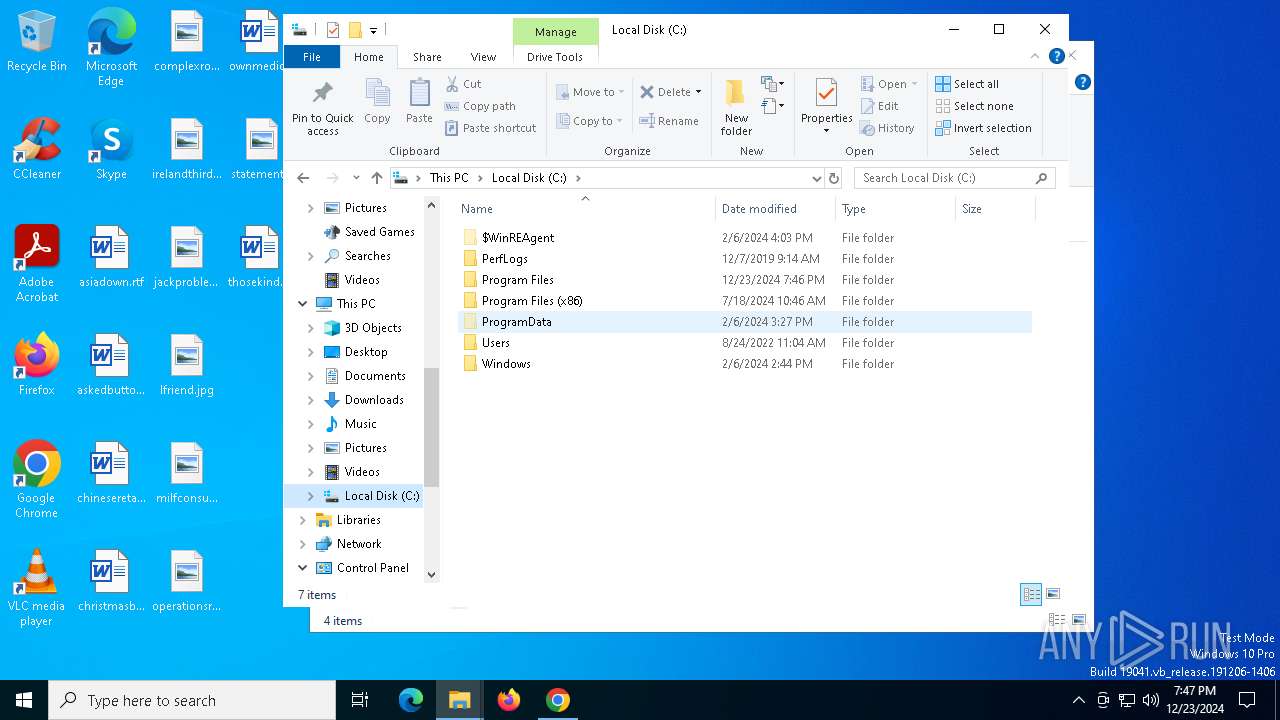
Executable content was dropped or overwritten
- msiexec.exe (PID: 5452)
- msiexec.exe (PID: 7132)
- chrome.exe (PID: 3864)
- msiexec.exe (PID: 6904)
- chrome.exe (PID: 2428)
Create files in a temporary directory
- rundll32.exe (PID: 2292)
- rundll32.exe (PID: 6820)
- rundll32.exe (PID: 4628)
- rundll32.exe (PID: 716)
Reads the software policy settings
- SearchApp.exe (PID: 5064)
- rundll32.exe (PID: 2292)
- msiexec.exe (PID: 5452)
- msiexec.exe (PID: 7132)
- rundll32.exe (PID: 5876)
- rundll32.exe (PID: 5300)
Creates files or folders in the user directory
- rundll32.exe (PID: 2292)
Checks proxy server information
- rundll32.exe (PID: 2292)
- rundll32.exe (PID: 5876)
Disables trace logs
- rundll32.exe (PID: 2292)
- rundll32.exe (PID: 5876)
The sample compiled with english language support
- msiexec.exe (PID: 7132)
- chrome.exe (PID: 2428)
- chrome.exe (PID: 3864)
Manages system restore points
- SrTasks.exe (PID: 1220)
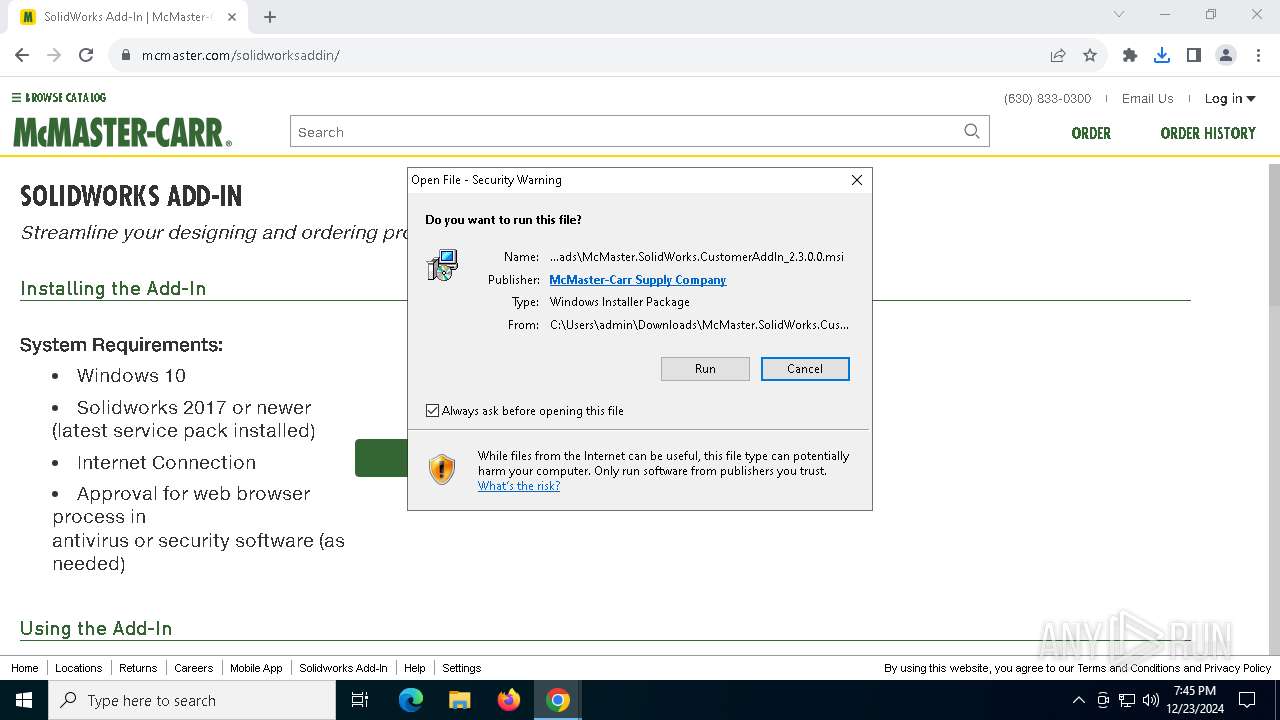
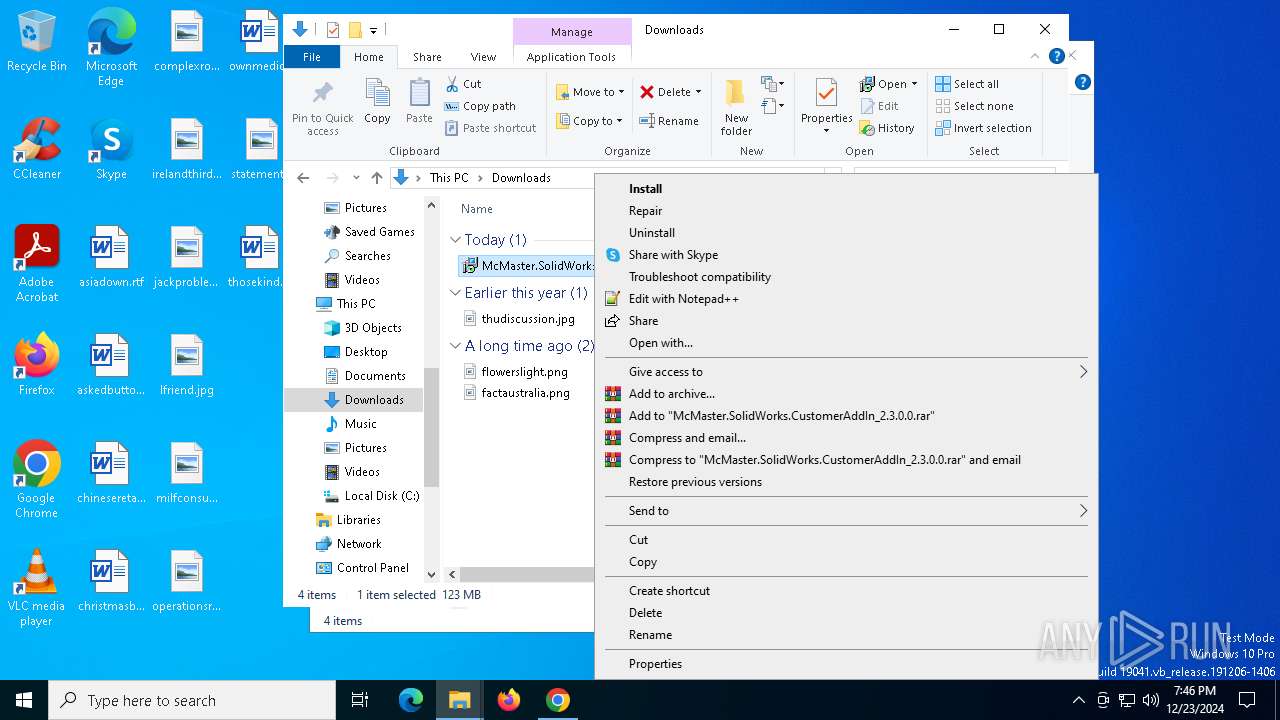
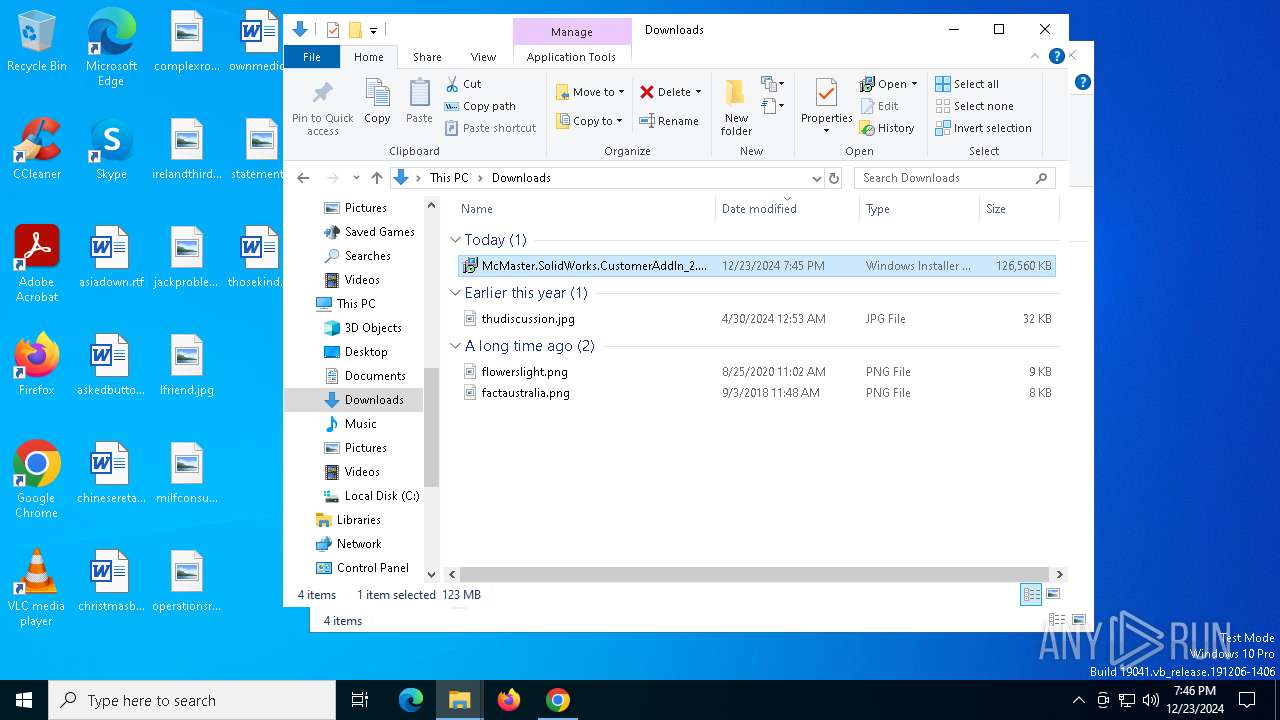
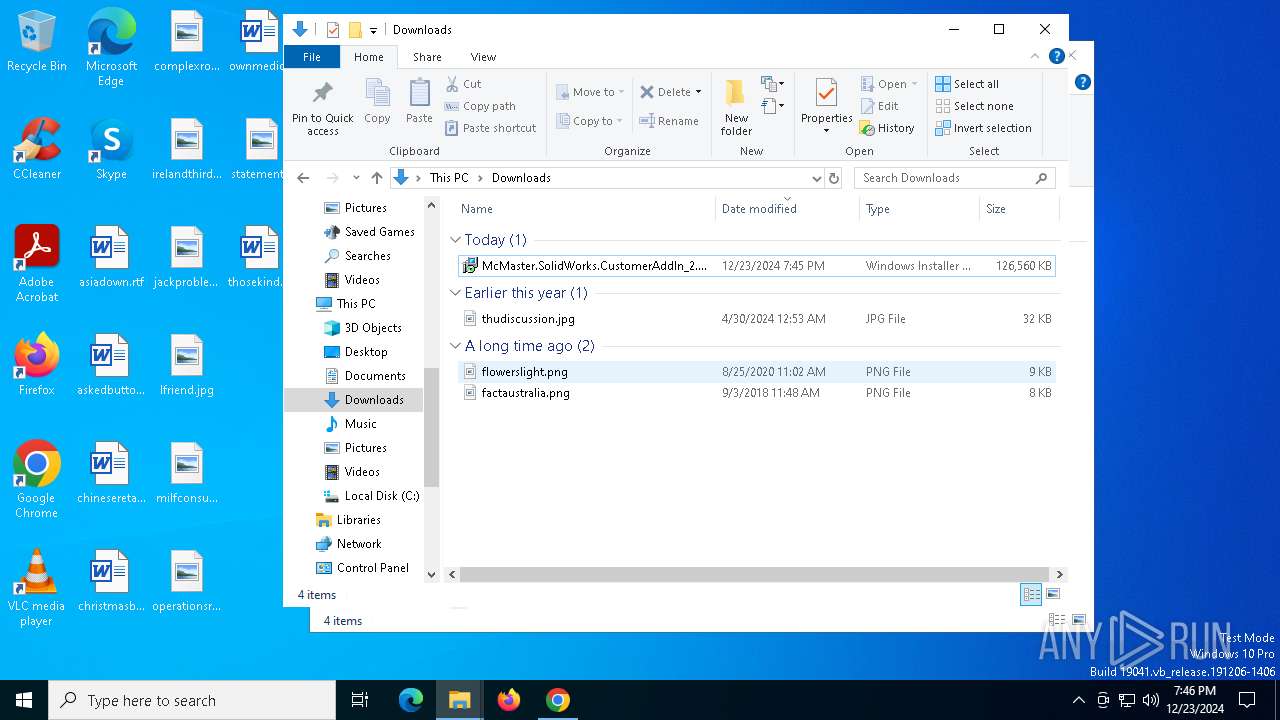
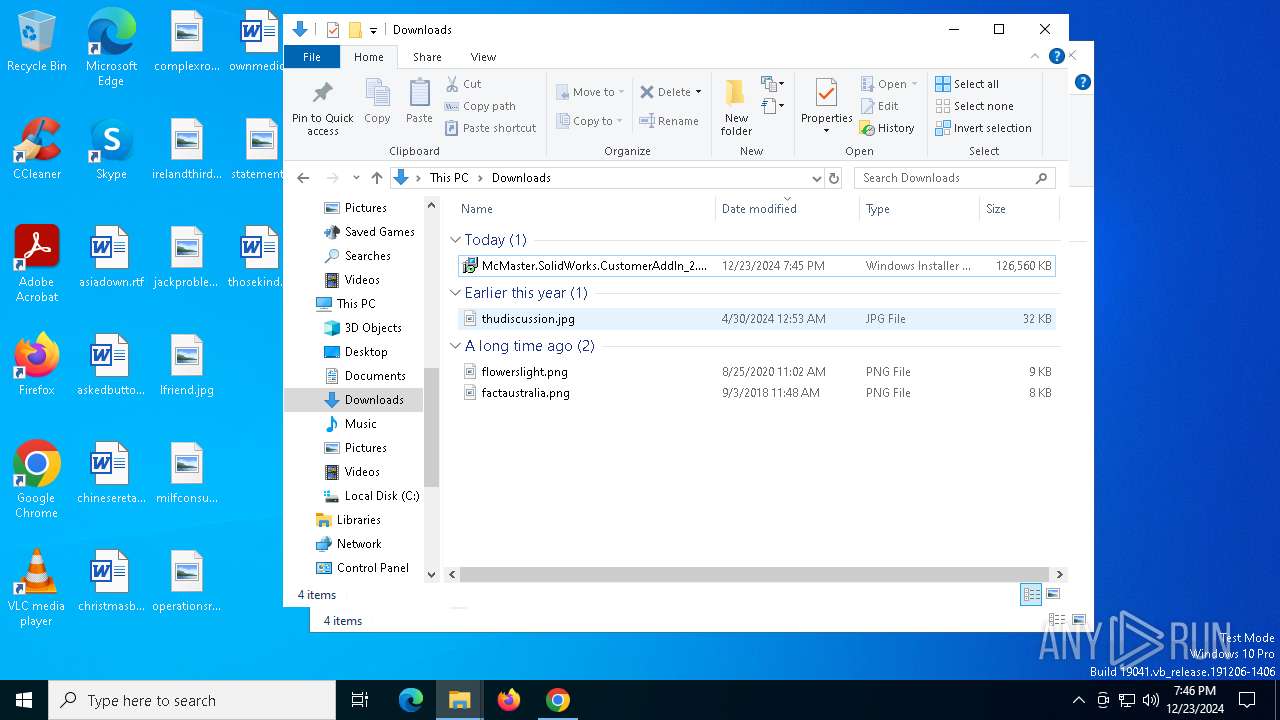
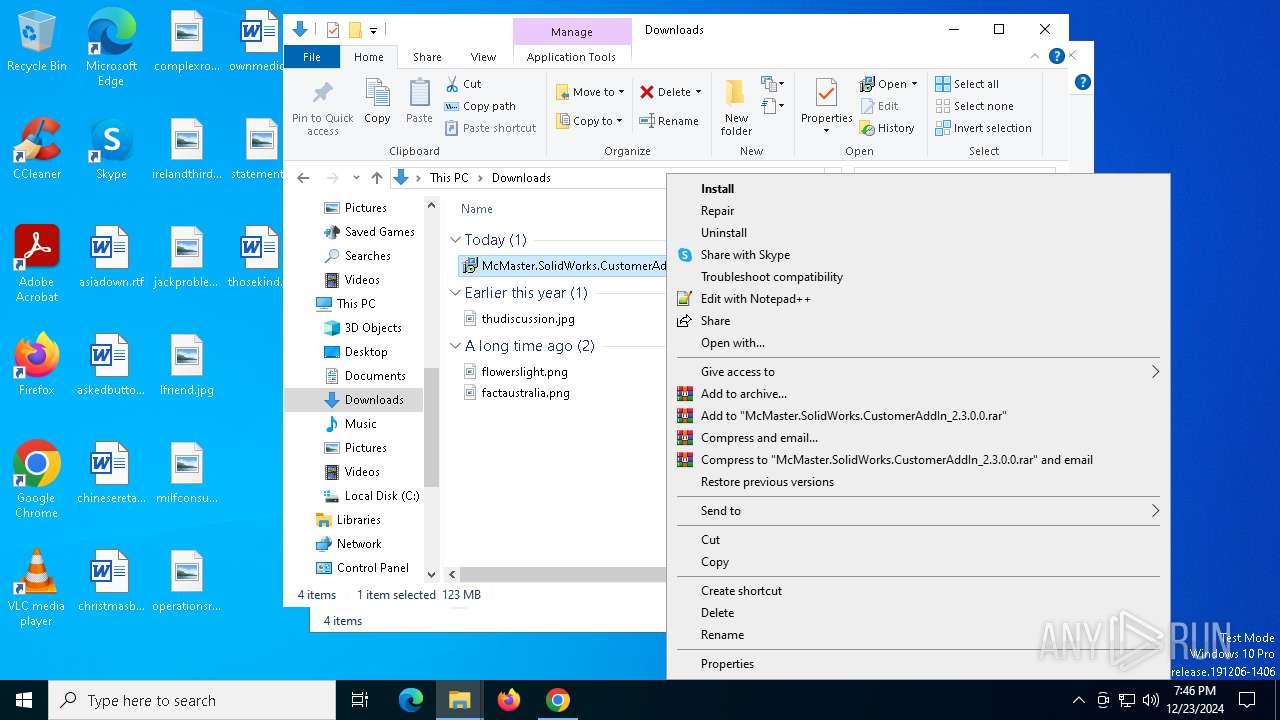
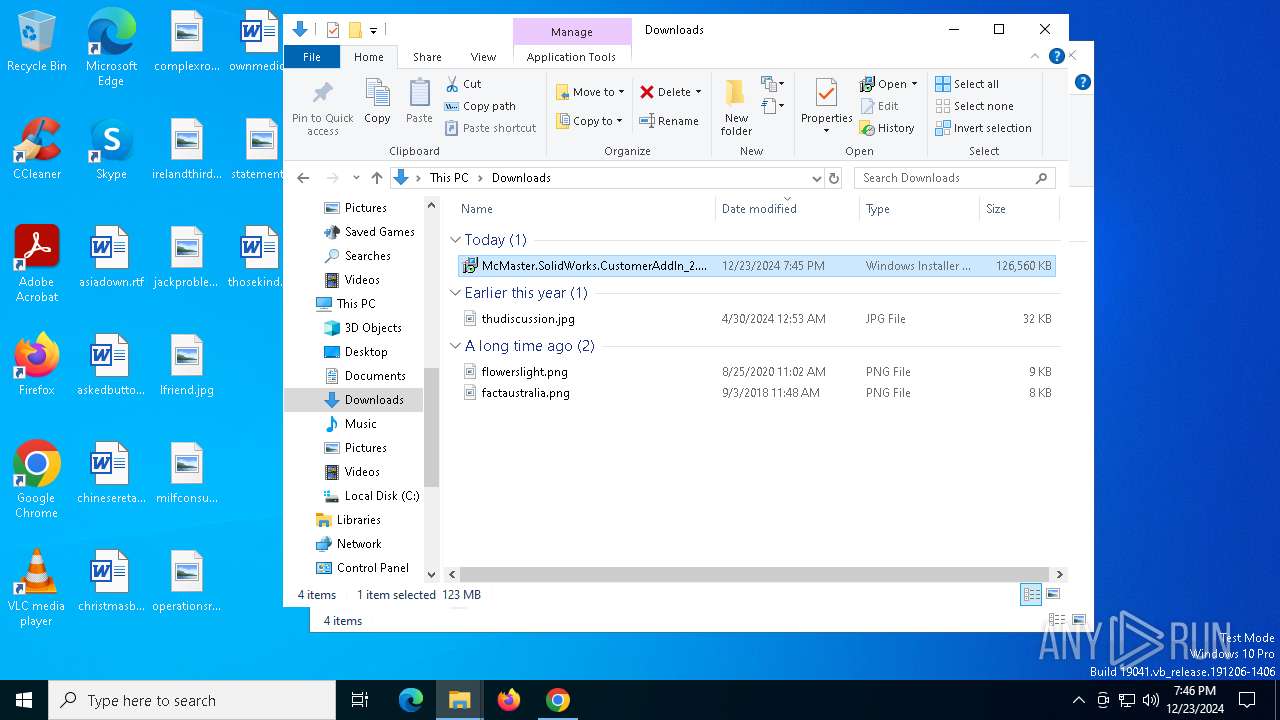
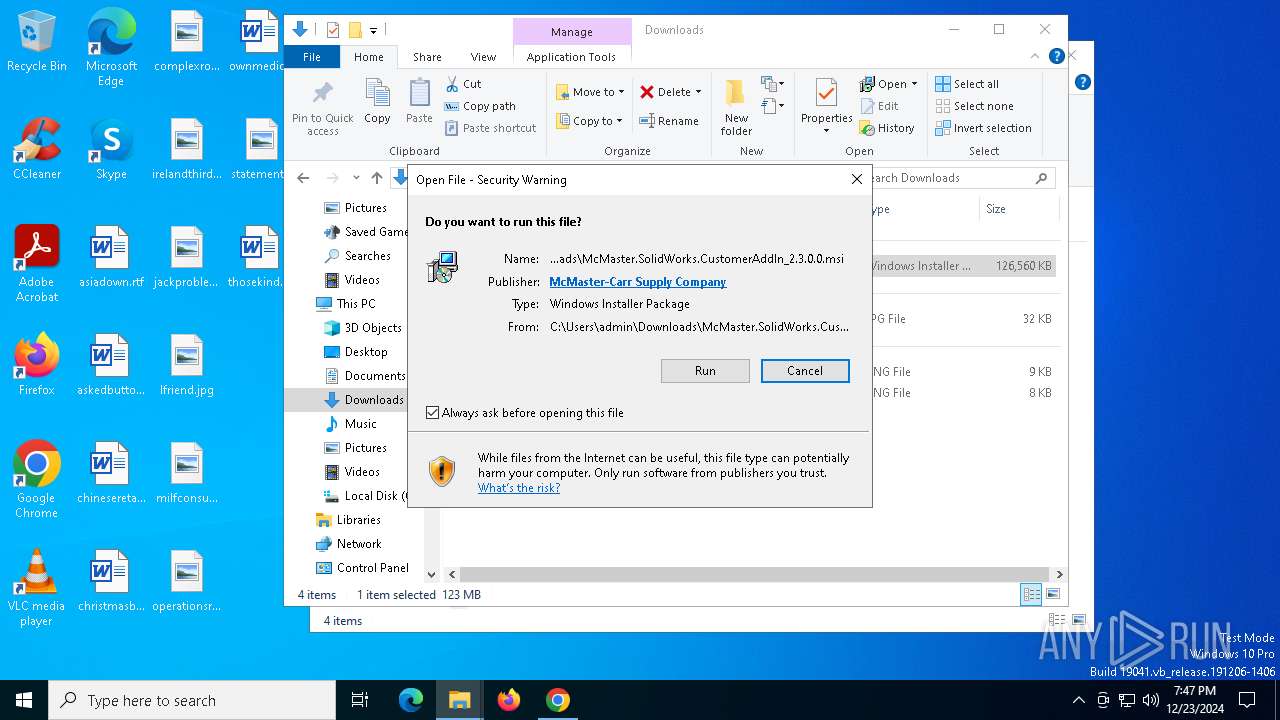
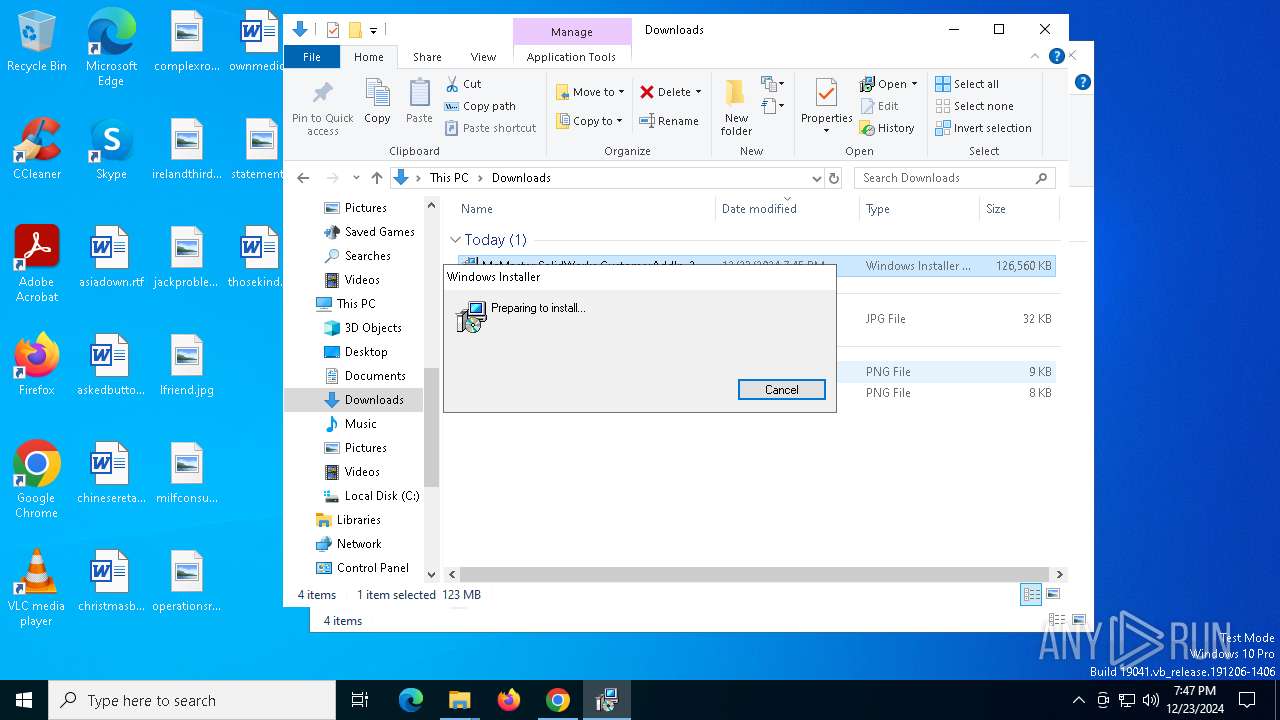
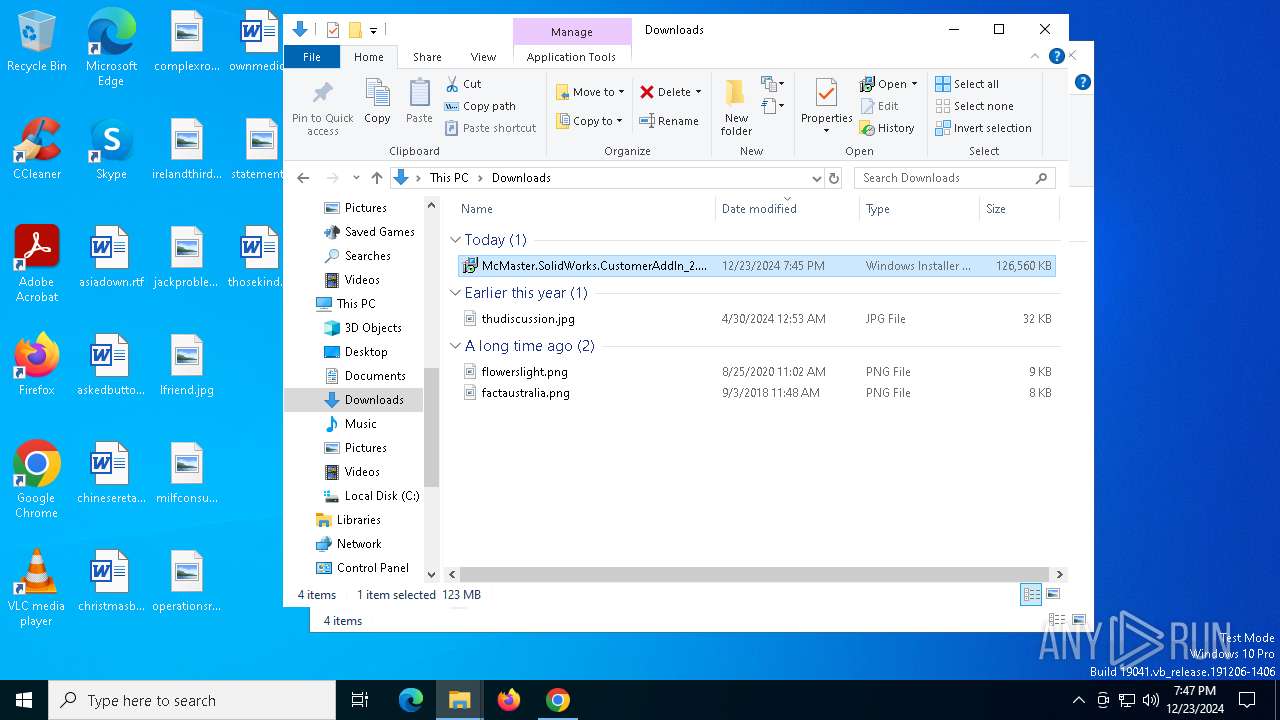
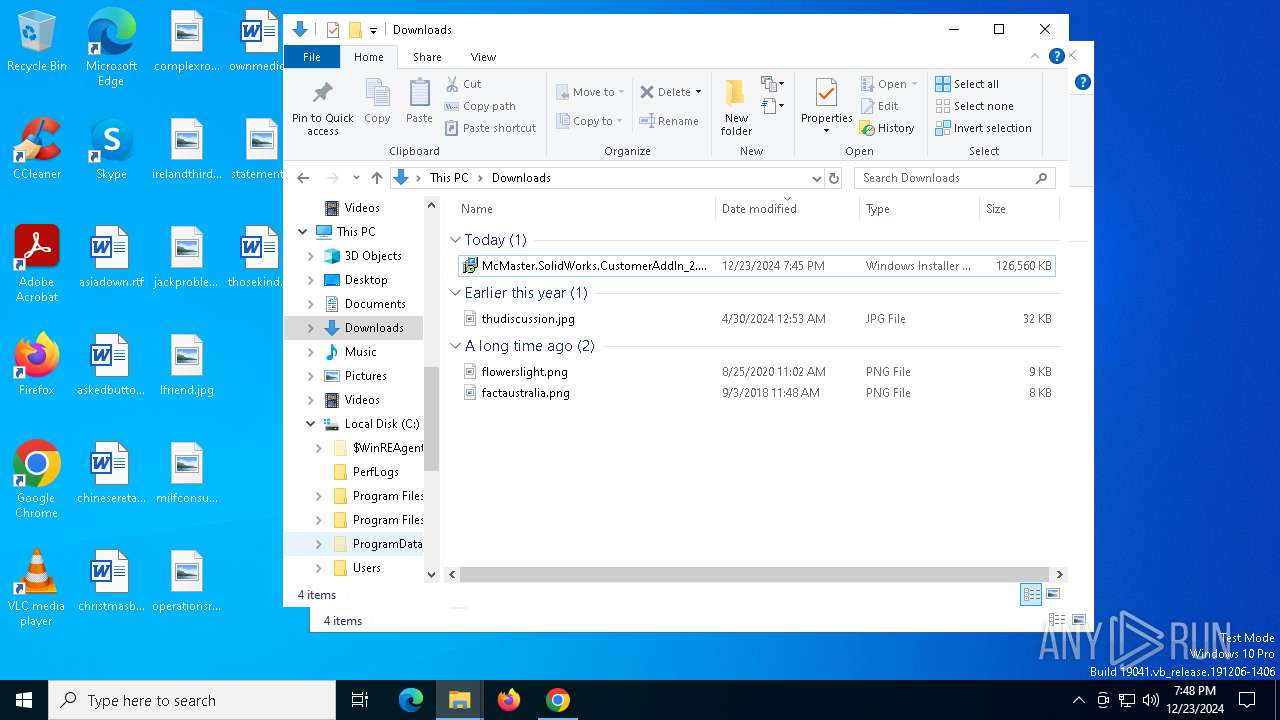
Manual execution by a user
- msiexec.exe (PID: 6904)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
176
Monitored processes
41
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 420 | rundll32.exe "C:\WINDOWS\Installer\MSIEB7A.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_1371046 7 McMaster.SolidWorks.LocalADAccountTranslation!McMaster.SolidWorks.LocalADAccountTranslation.CustomActions.TranslateSidToName | C:\Windows\SysWOW64\rundll32.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 716 | rundll32.exe "C:\WINDOWS\Installer\MSIFE66.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_1441421 28 McMaster.SolidWorks.LocalADAccountTranslation!McMaster.SolidWorks.LocalADAccountTranslation.CustomActions.TranslateSidToName | C:\Windows\SysWOW64\rundll32.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 836 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4584 --field-trial-handle=1888,i,1280208631492244885,2064077681512428139,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1220 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2292 | rundll32.exe "C:\Users\admin\AppData\Local\Temp\MSI7771.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_1341328 3 McMaster.SolidWorks.LoggingCustomActions!McMaster.SolidWorks.LoggingCustomActions.CustomActions.LogInstallStart | C:\Windows\SysWOW64\rundll32.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2428 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=6060 --field-trial-handle=1888,i,1280208631492244885,2064077681512428139,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2452 | C:\Windows\syswow64\MsiExec.exe -Embedding 1318B87B07336FAF0CE301AA4695A770 C | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3544 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking --disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints "https://www.mcmaster.com/solidworksaddin/" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 3816 | rundll32.exe "C:\WINDOWS\Installer\MSIFCDE.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_1441125 23 McMaster.SolidWorks.LocalADAccountTranslation!McMaster.SolidWorks.LocalADAccountTranslation.CustomActions.TranslateSidToName | C:\Windows\SysWOW64\rundll32.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3864 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5696 --field-trial-handle=1888,i,1280208631492244885,2064077681512428139,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
Total events
29 010
Read events
28 012
Write events
959
Delete events
39
Modification events
| (PID) Process: | (3544) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3544) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3544) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3544) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3544) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (5064) SearchApp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Feeds\DSB |
| Operation: | write | Name: | DynamicText |
Value: | |||
| (PID) Process: | (5064) SearchApp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Feeds\DSB |
| Operation: | write | Name: | DynamicTextTruncated |
Value: | |||
| (PID) Process: | (5064) SearchApp.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.search_cw5n1h2txyewy\Internet Explorer\DOMStorage\bing.com |
| Operation: | write | Name: | Total |
Value: 51220 | |||
| (PID) Process: | (5064) SearchApp.exe | Key: | \REGISTRY\A\{ee080948-b2ea-145a-6870-f9164b908eb9}\LocalState\DynamicSearchBox |
| Operation: | write | Name: | TelemetryID |
Value: 0000A550F21E7355DB01 | |||
| (PID) Process: | (6880) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 0100000000000000BF265D307355DB01 | |||
Executable files
56
Suspicious files
198
Text files
60
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF13709f.TMP | — | |
MD5:— | SHA256:— | |||
| 3544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF1370af.TMP | — | |
MD5:— | SHA256:— | |||
| 3544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF1370af.TMP | — | |
MD5:— | SHA256:— | |||
| 3544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF1370be.TMP | — | |
MD5:— | SHA256:— | |||
| 3544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF1370be.TMP | — | |
MD5:— | SHA256:— | |||
| 3544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
39
TCP/UDP connections
81
DNS requests
64
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2624 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7040 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
2624 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5404 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/cxmnq7ci5es7kes4fruun62via_2024.12.17.1202/ggkkehgbnfjpeggfpleeakpidbkibbmn_2024.12.17.1202_all_adhesfd5wpyhstvspdj4hmgltslq.crx3 | unknown | — | — | whitelisted |
3544 | chrome.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEAznjKUiqYL%2FBqOflmNFLzs%3D | unknown | — | — | whitelisted |
5404 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/cxmnq7ci5es7kes4fruun62via_2024.12.17.1202/ggkkehgbnfjpeggfpleeakpidbkibbmn_2024.12.17.1202_all_adhesfd5wpyhstvspdj4hmgltslq.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 2.23.209.179:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
4712 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
876 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3544 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6320 | chrome.exe | 108.177.15.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
6320 | chrome.exe | 104.102.49.219:443 | www.mcmaster.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.mcmaster.com |
| whitelisted |
accounts.google.com |
| whitelisted |
images1.mcmaster.com |
| whitelisted |
www1.mcmaster.com |
| whitelisted |
www2.mcmaster.com |
| whitelisted |
www.google.com |
| whitelisted |