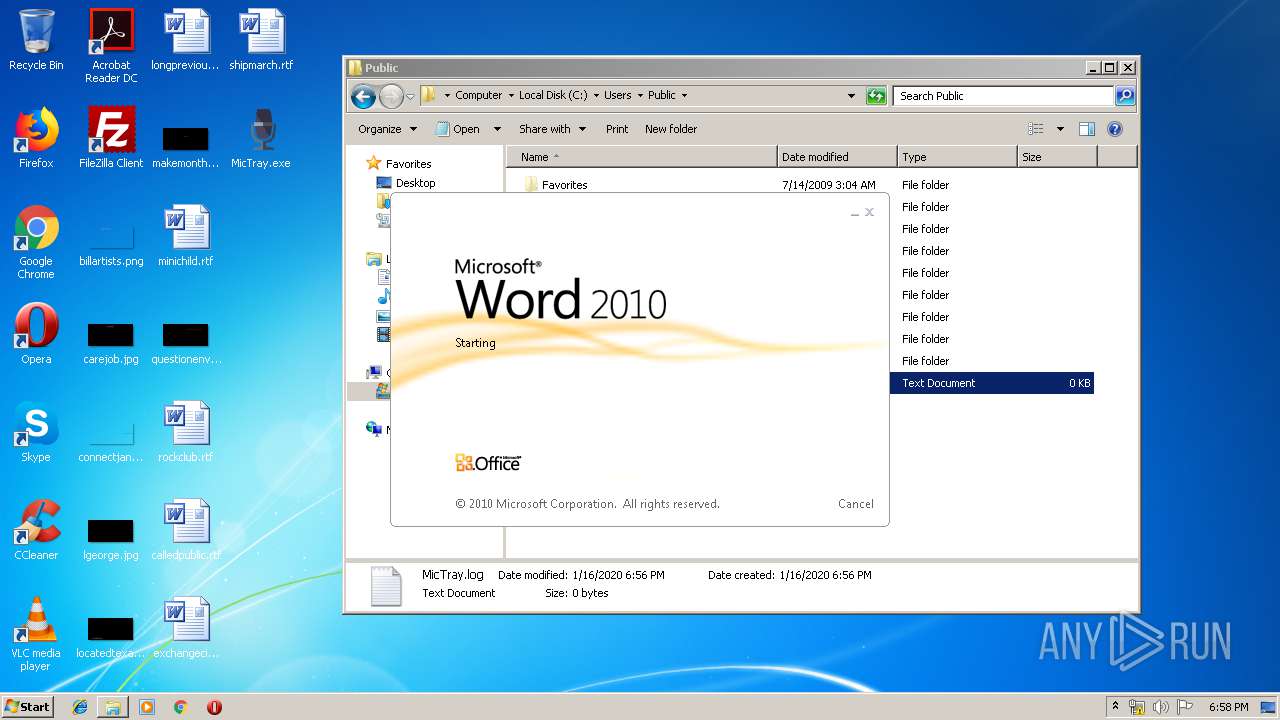
| File name: | MicTray.exe |
| Full analysis: | https://app.any.run/tasks/73b2e604-4ba3-4730-b29d-ea8b0b92f174 |
| Verdict: | Malicious activity |
| Analysis date: | January 16, 2020, 18:55:58 |
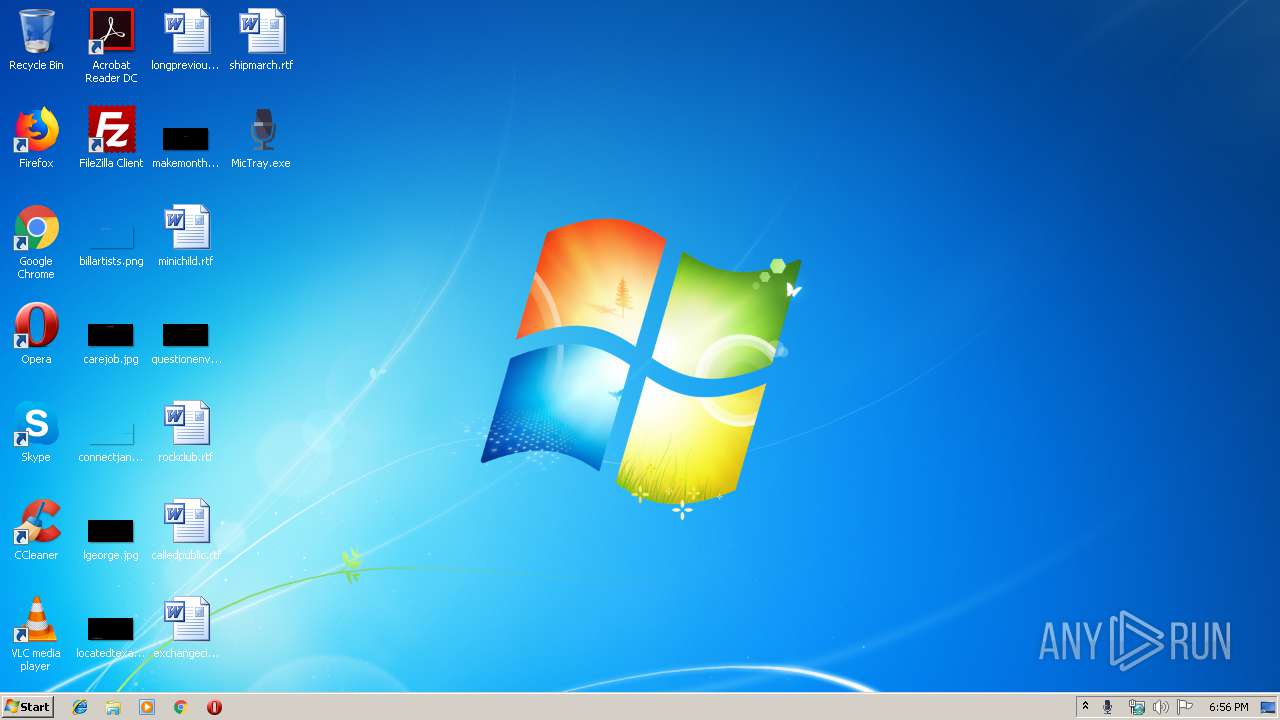
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 9650414C7D12076A4DF97B65F8F64D44 |
| SHA1: | 805FD148266EE74B23609AEDACE7D51953B613BF |
| SHA256: | 417BDFB818BC344219CD835808C903B02B70AB7C3D6A5104C900CAED1C5F24F6 |
| SSDEEP: | 49152:rIUUoXHHNAdhwth4RJSm96ZMsFmWU9q6LLdNTNeyF6:rHUoXHtAdKtgJSm96ZM6U9pLLdNTN16 |
MALICIOUS
No malicious indicators.SUSPICIOUS
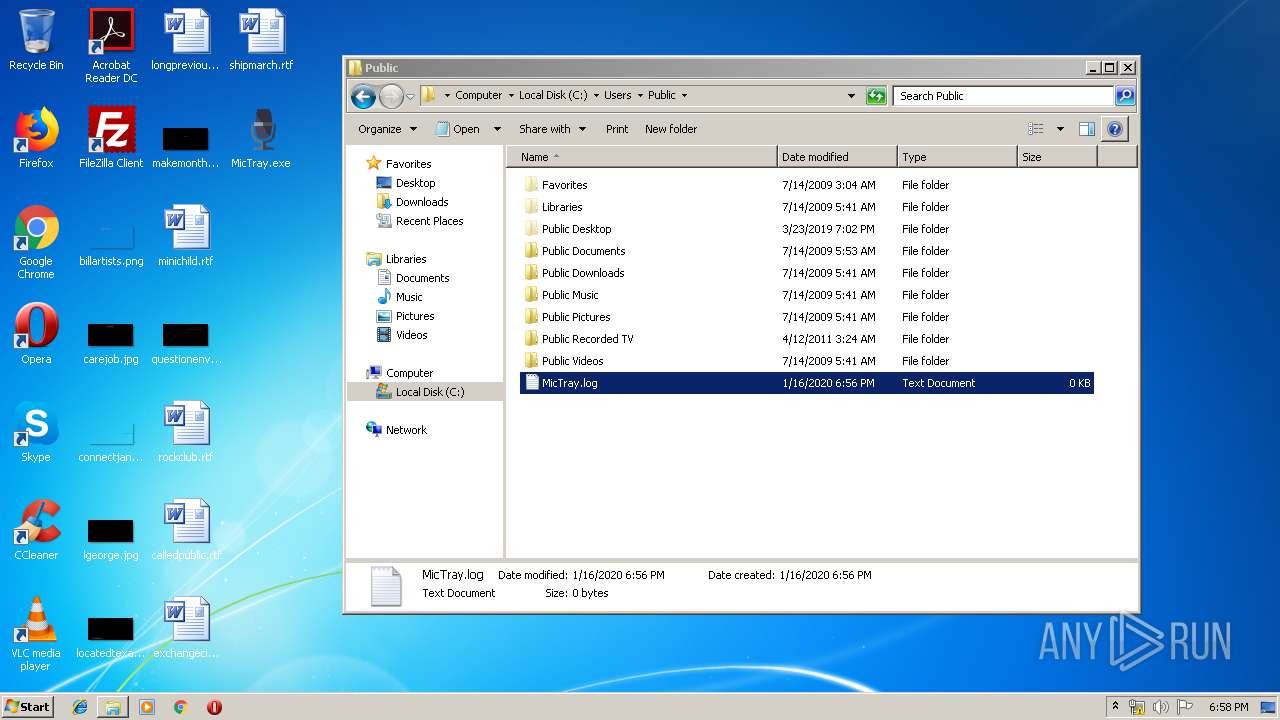
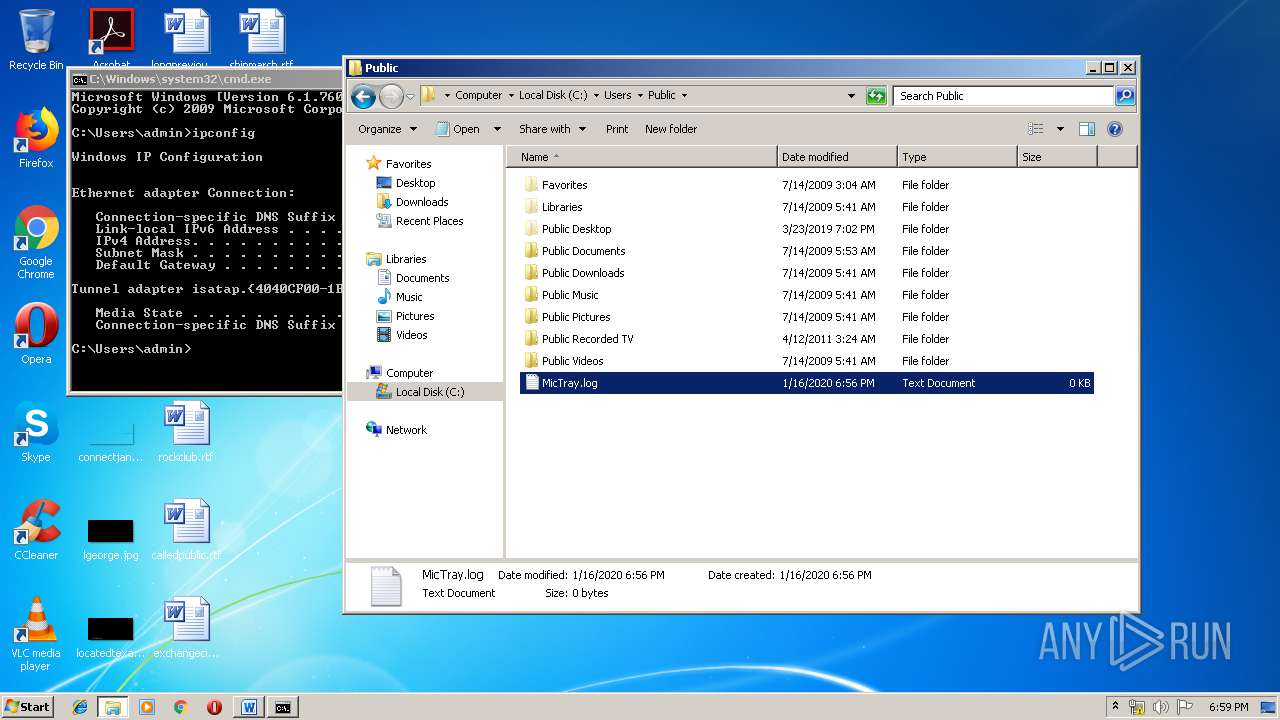
Creates files in the program directory
- firefox.exe (PID: 3000)
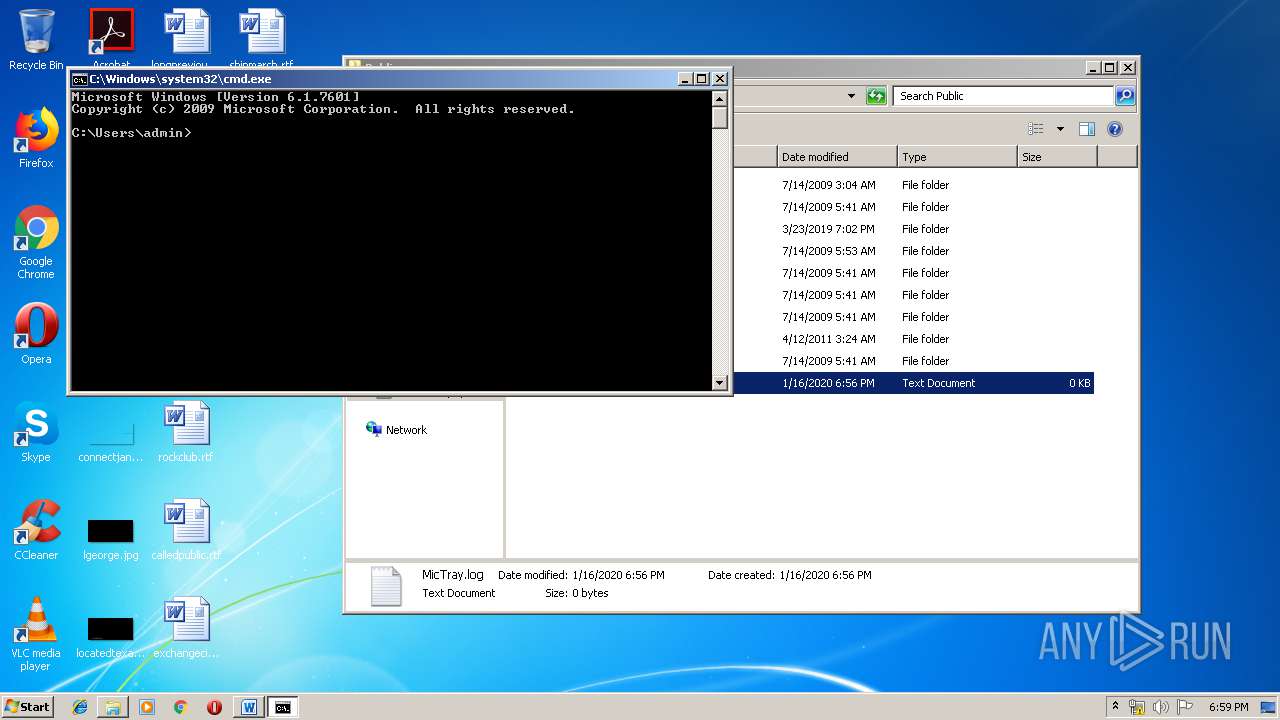
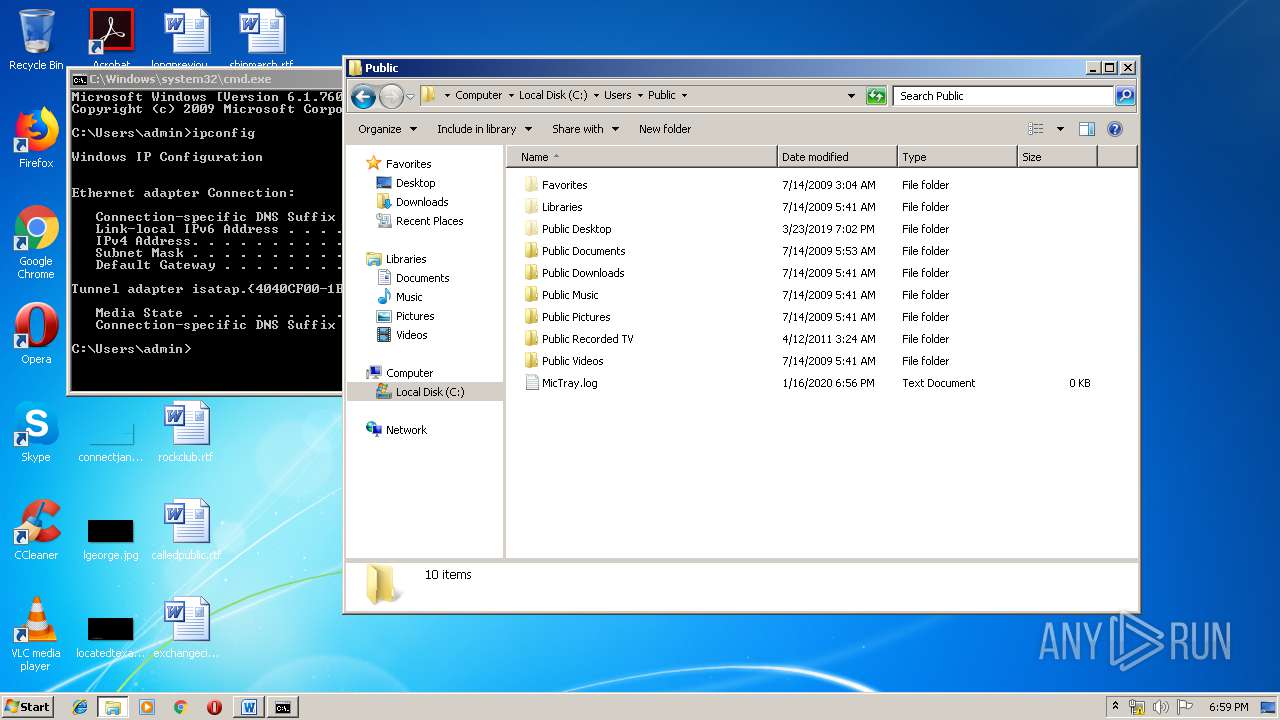
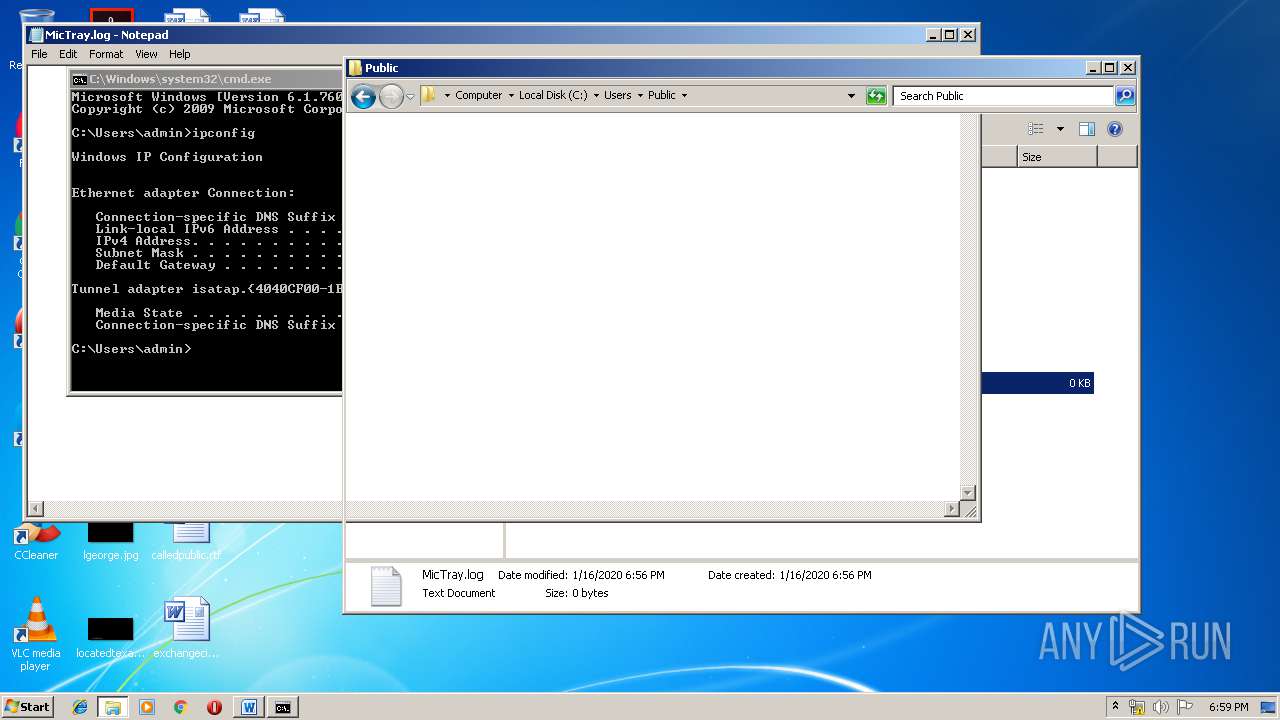
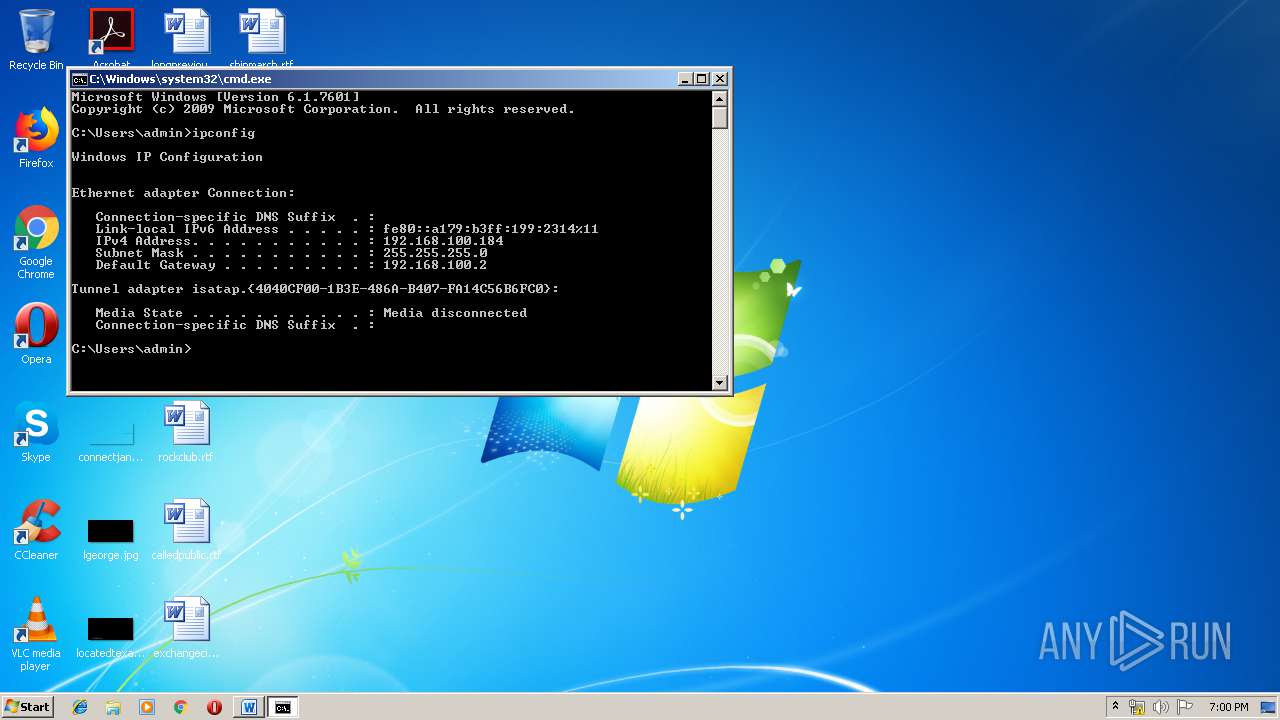
Uses IPCONFIG.EXE to discover IP address
- cmd.exe (PID: 3280)
INFO
Application launched itself
- firefox.exe (PID: 3000)
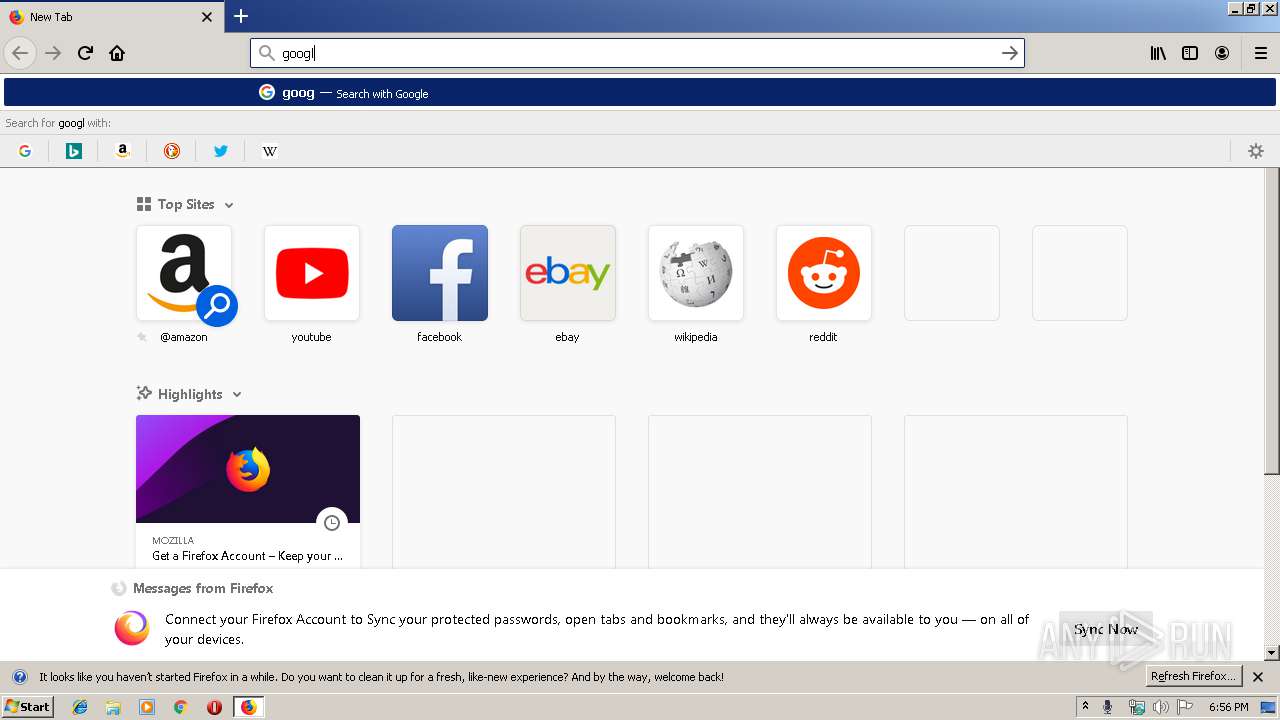
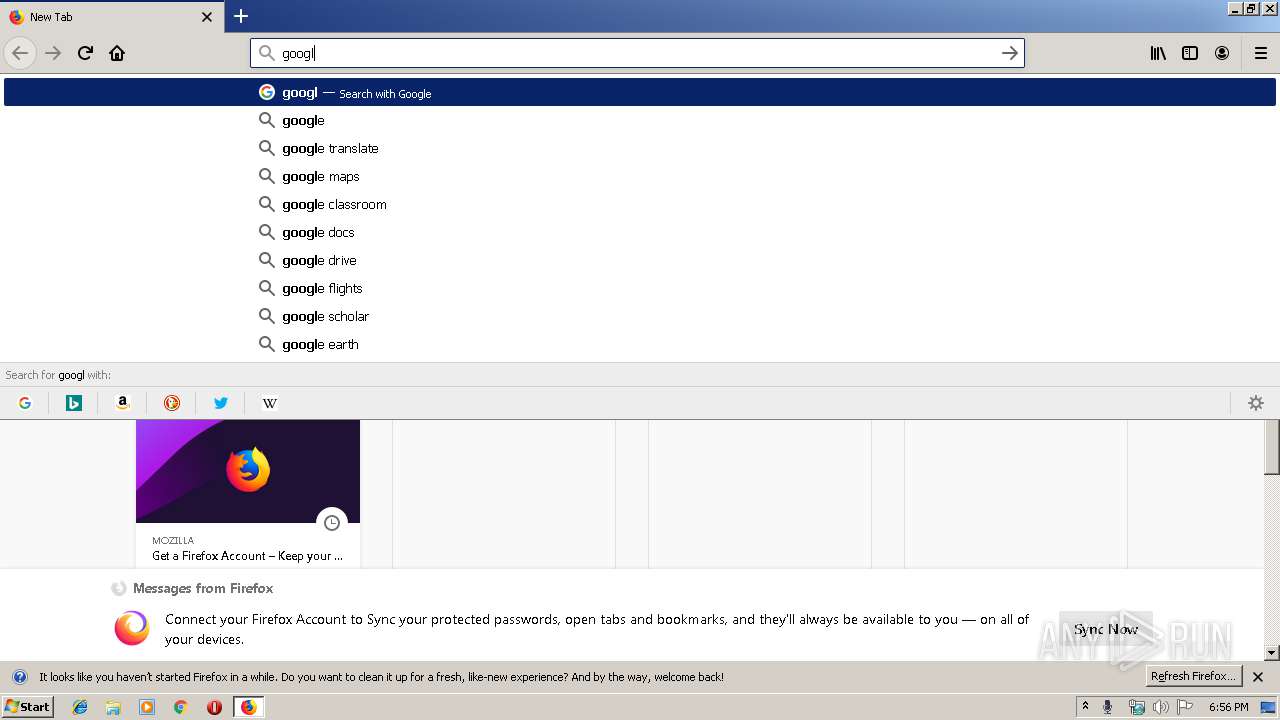
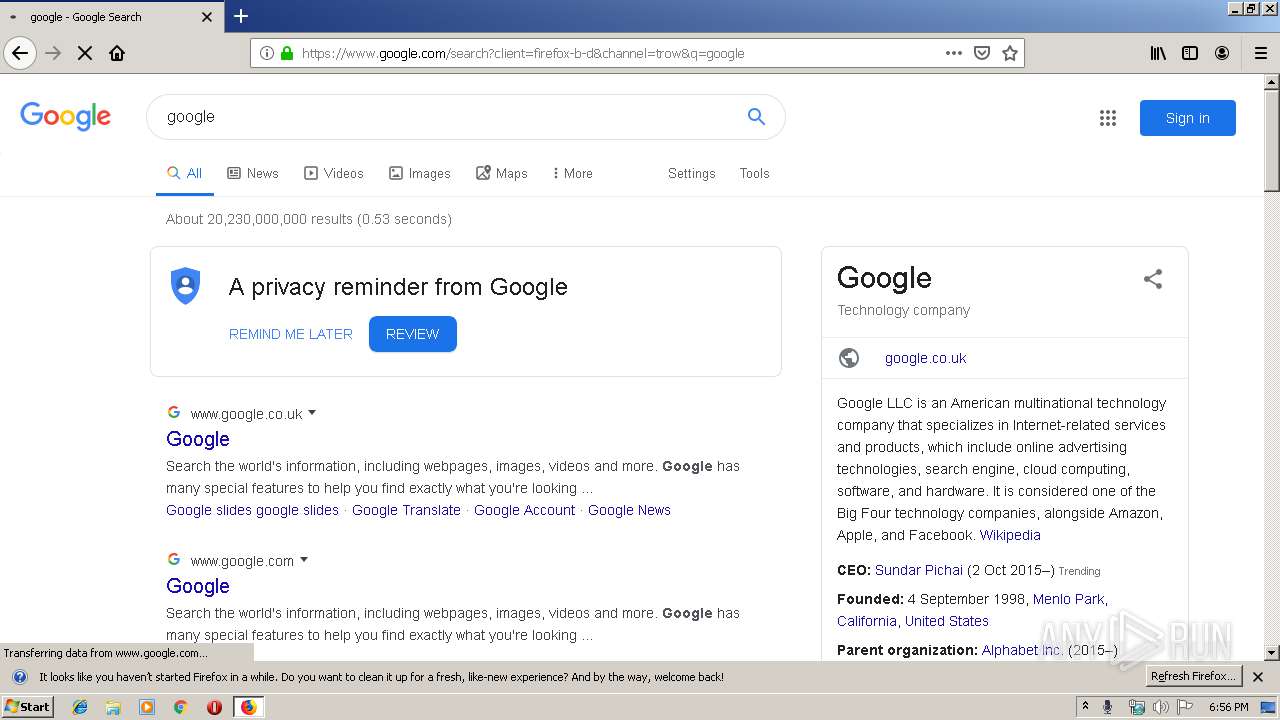
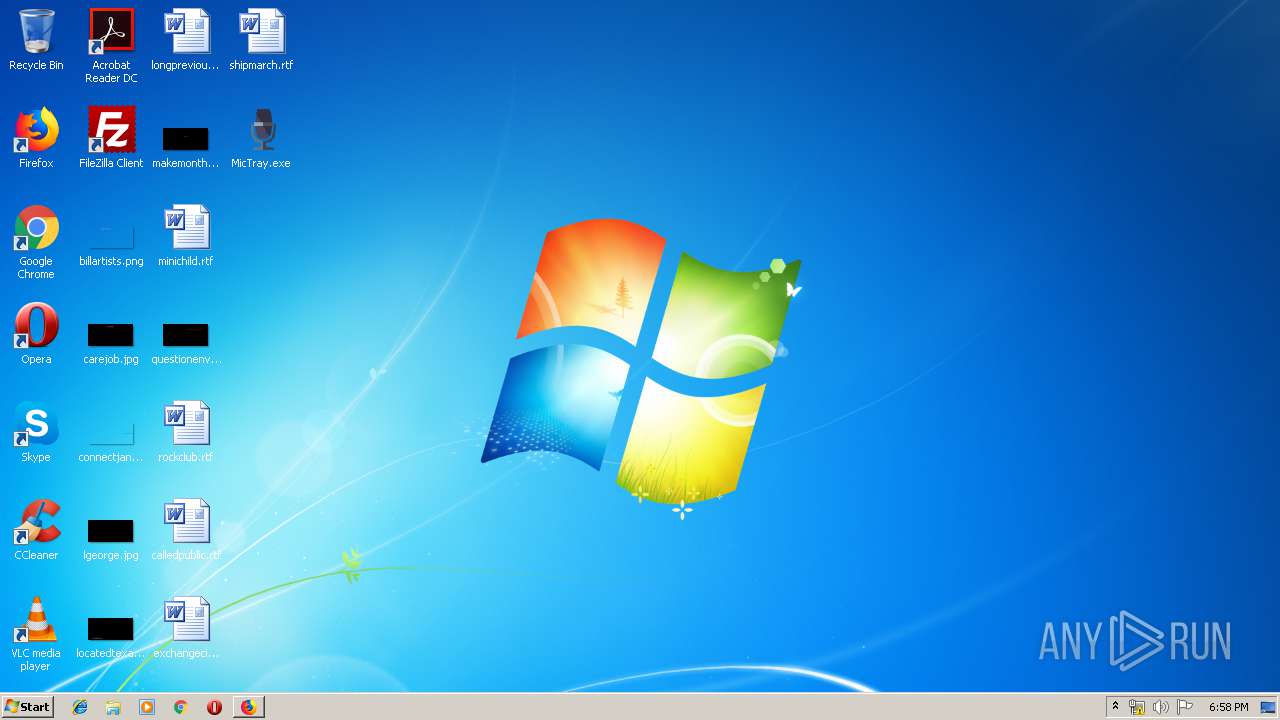
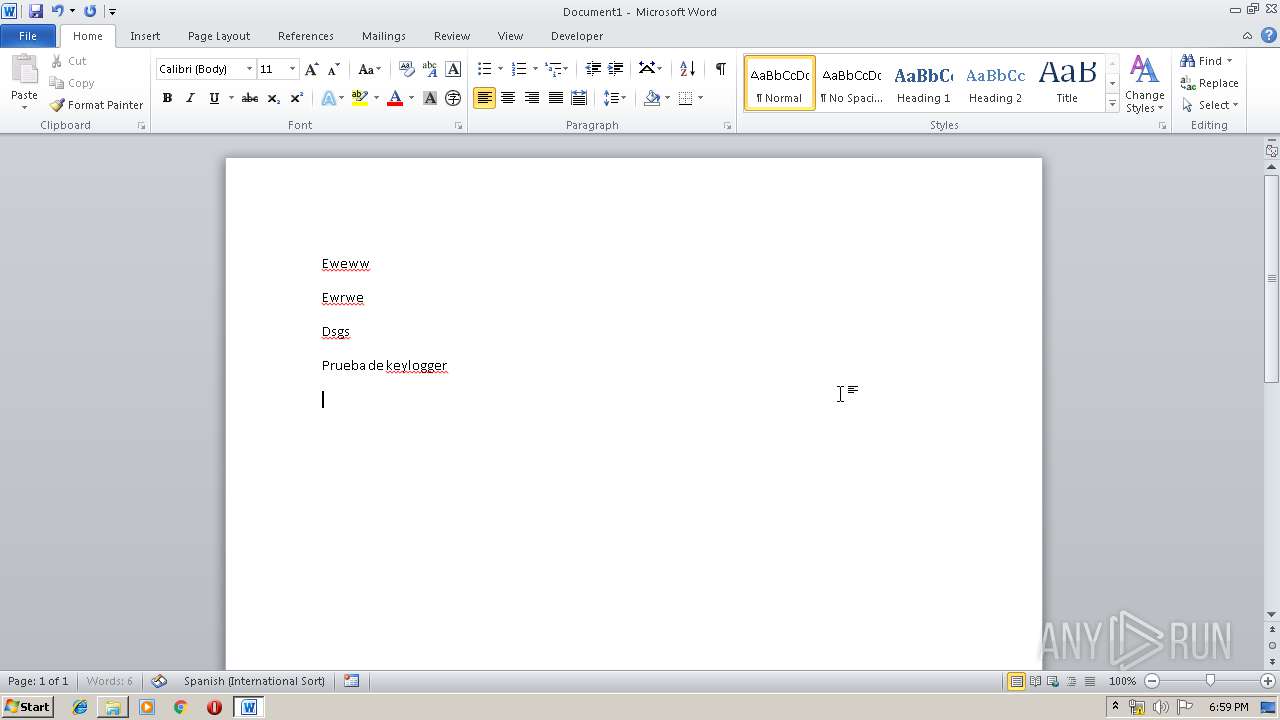
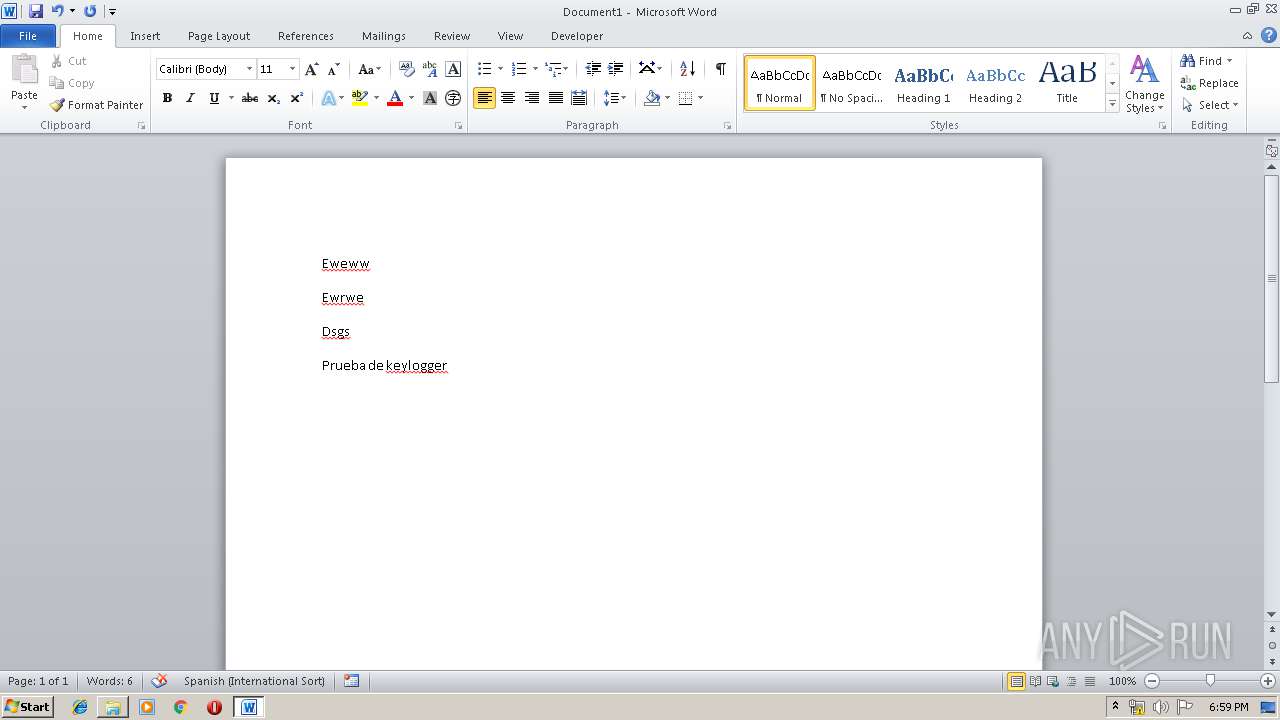
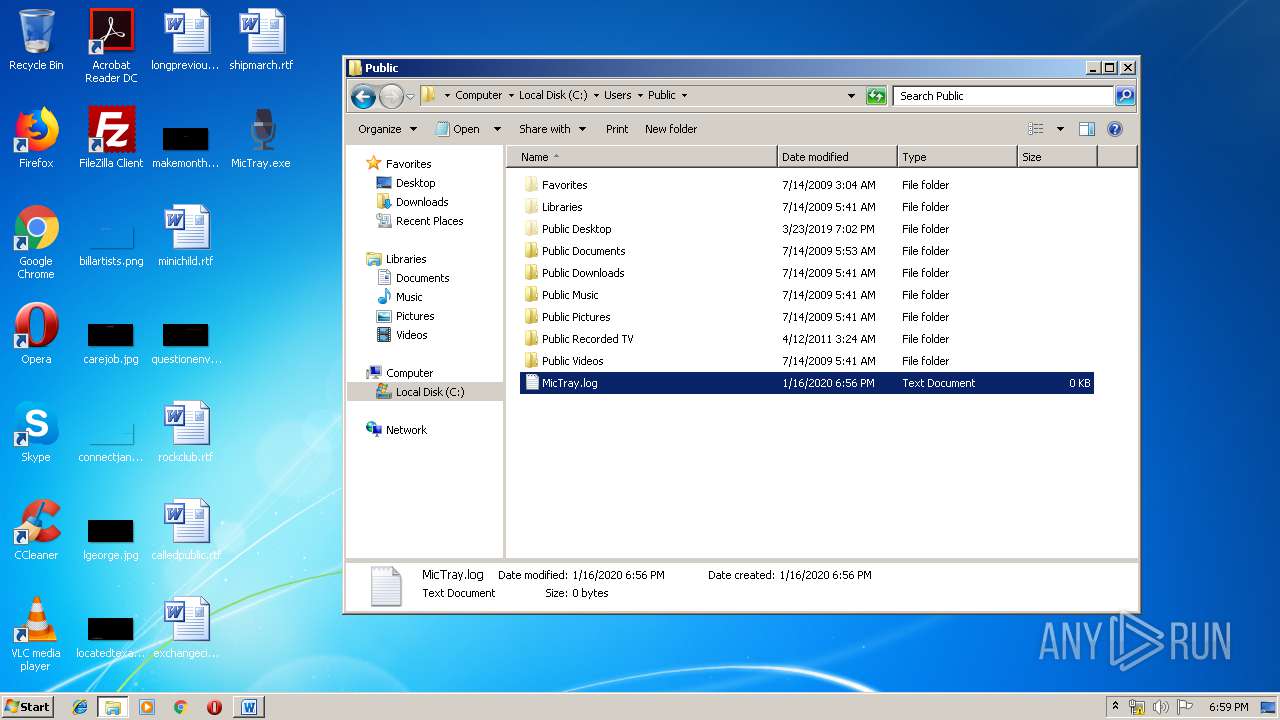
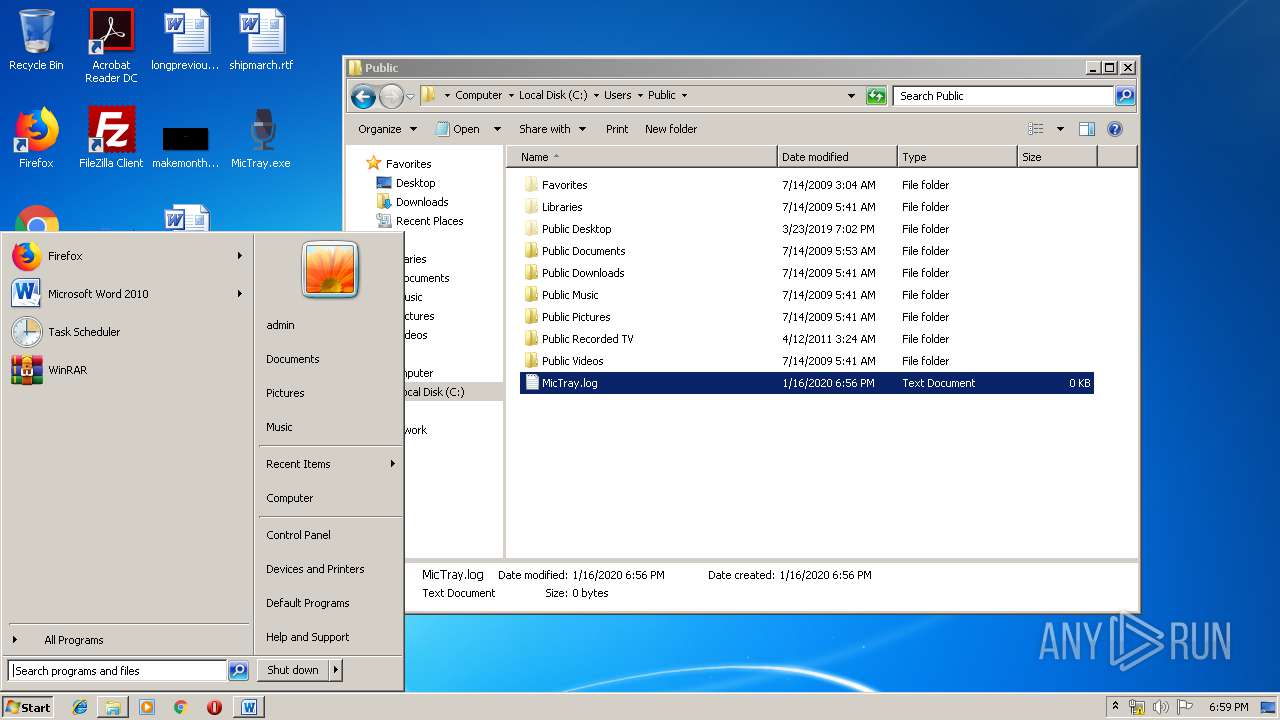
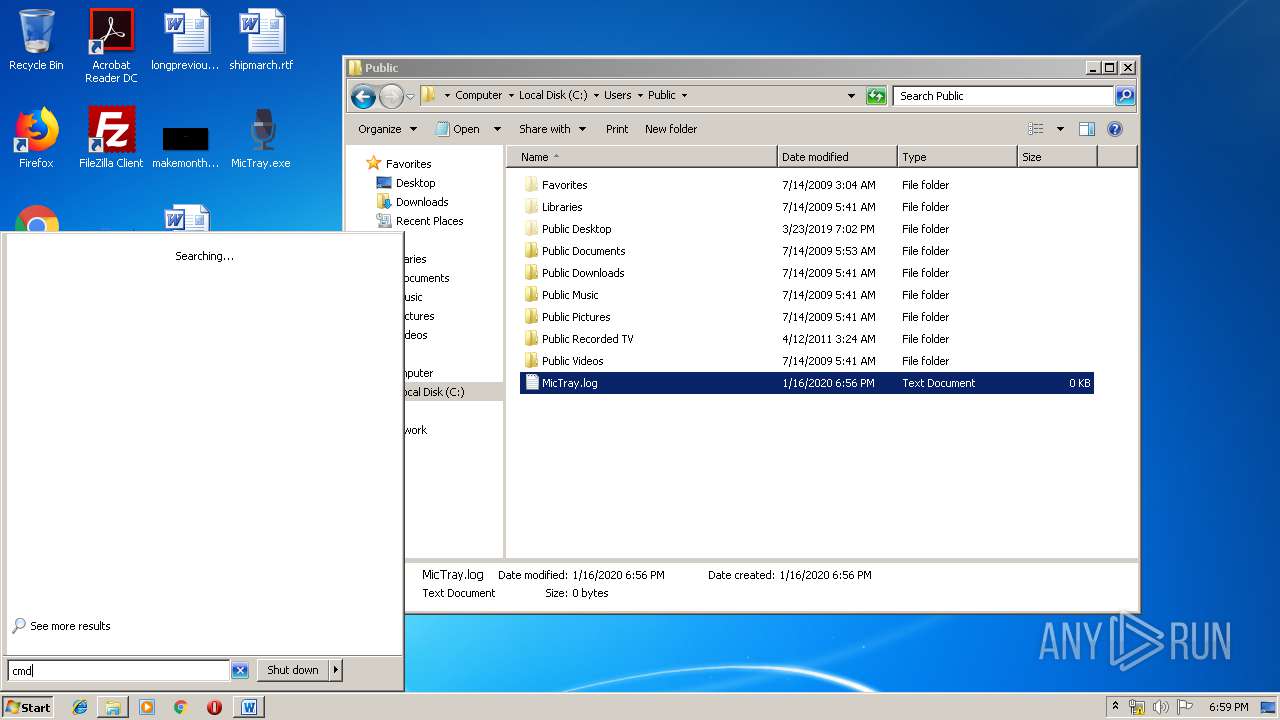
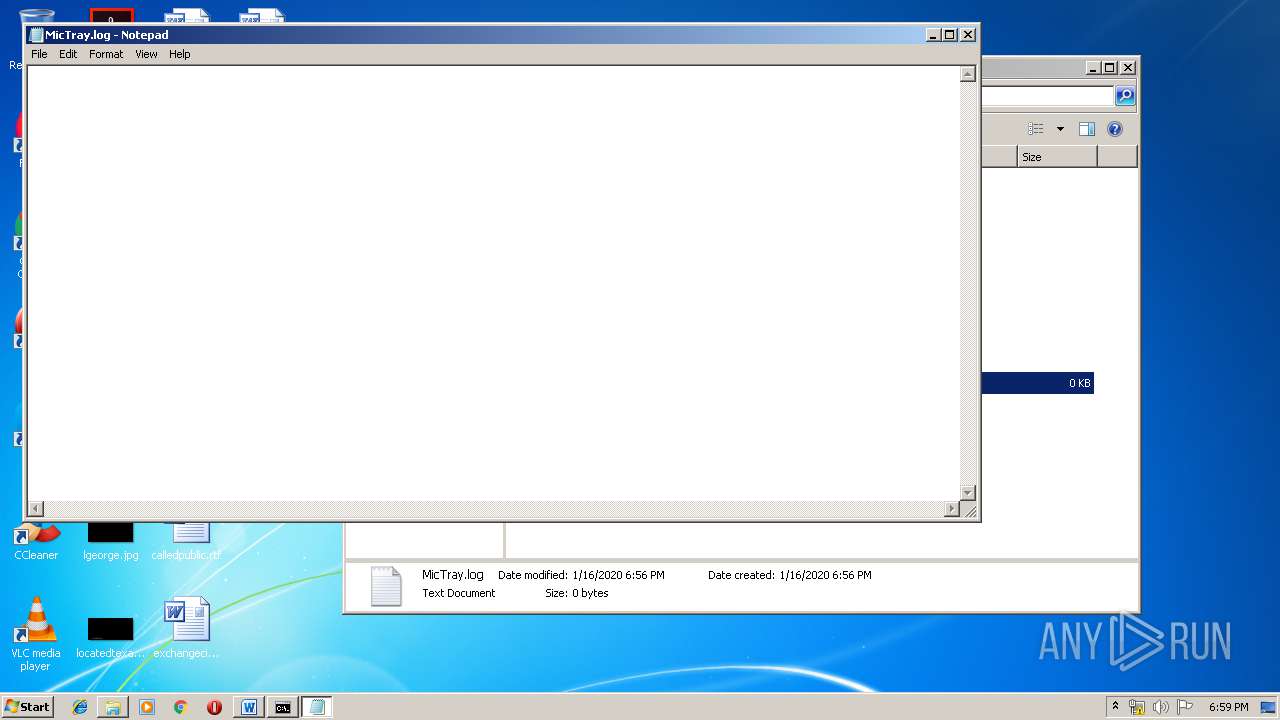
Manual execution by user
- NOTEPAD.EXE (PID: 3708)
- NOTEPAD.EXE (PID: 2928)
- cmd.exe (PID: 3280)
- NOTEPAD.EXE (PID: 3952)
- firefox.exe (PID: 2520)
- explorer.exe (PID: 3608)
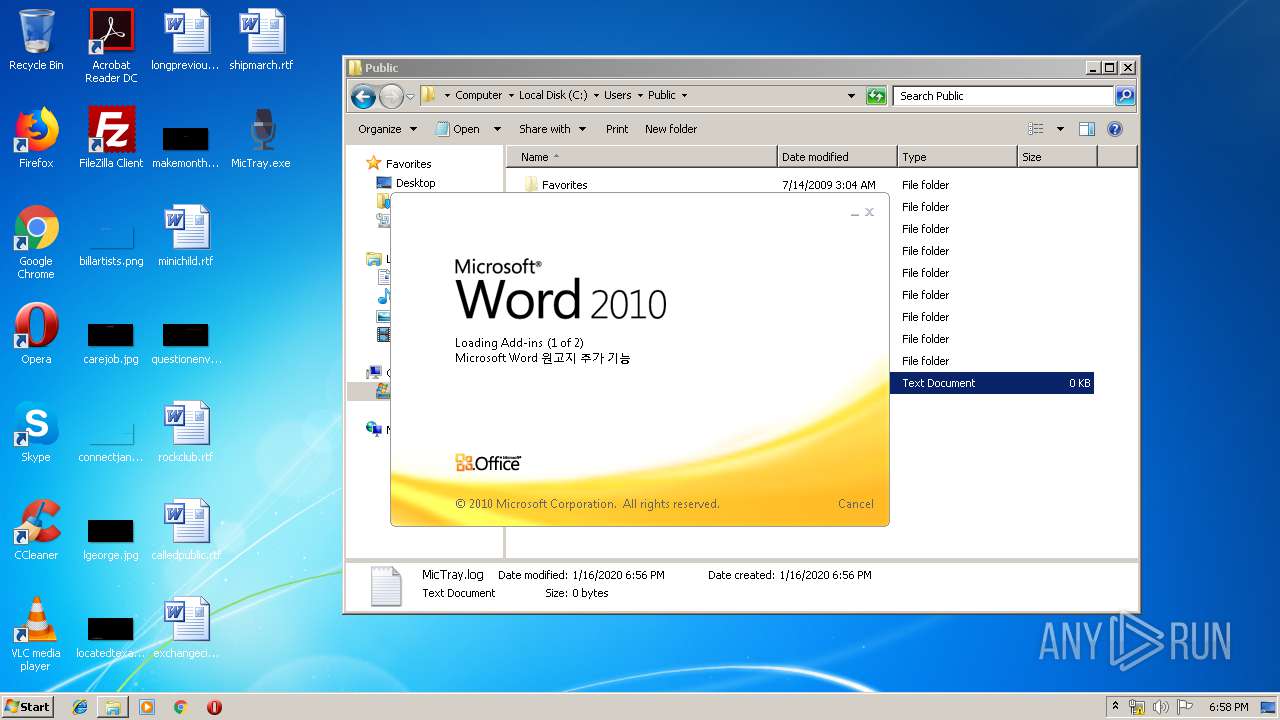
- WINWORD.EXE (PID: 3856)
Reads CPU info
- firefox.exe (PID: 3000)
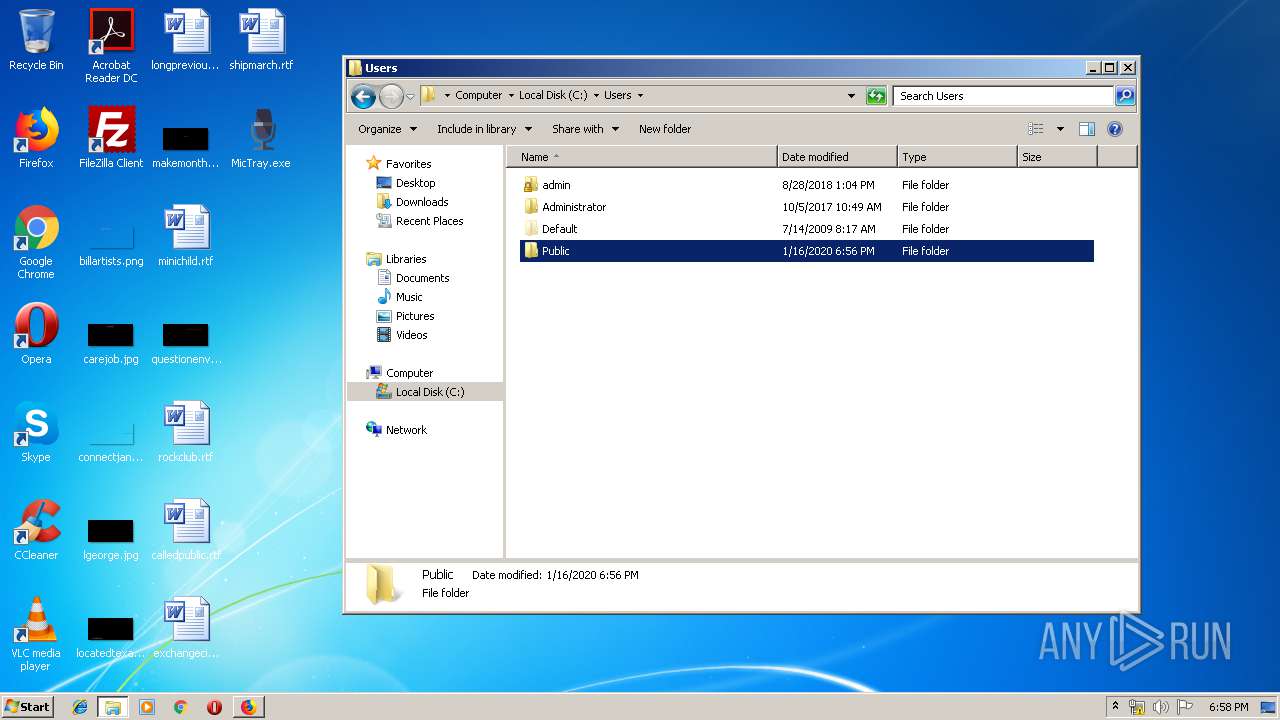
Creates files in the user directory
- WINWORD.EXE (PID: 3856)
- firefox.exe (PID: 3000)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3856)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2015:12:24 08:50:16+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 1423360 |
| InitializedDataSize: | 581120 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x12bc4d |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.31 |
| ProductVersionNumber: | 1.0.0.31 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | Chinese (Traditional) |
| CharacterSet: | Unicode |
| CompanyName: | Conexant |
| FileDescription: | mic tray icon |
| FileVersion: | 1.0.0.31 |
| LegalCopyright: | Copyright (C) 2014 |
| ProductVersion: | 1.0.0.31 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 24-Dec-2015 07:50:16 |
| Detected languages: |
|
| CompanyName: | Conexant |
| FileDescription: | mic tray icon |
| FileVersion: | 1.0.0.31 |
| LegalCopyright: | Copyright (C) 2014 |
| ProductVersion: | 1.0.0.31 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000120 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 24-Dec-2015 07:50:16 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0015B649 | 0x0015B800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.53607 |
.rdata | 0x0015D000 | 0x00053C06 | 0x00053E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.99903 |
.data | 0x001B1000 | 0x0000F240 | 0x00006E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.76203 |
.rsrc | 0x001C1000 | 0x0000C960 | 0x0000CA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.18518 |
.reloc | 0x001CE000 | 0x0001E094 | 0x0001E200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.48487 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.12107 | 796 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 2.82175 | 16936 | UNKNOWN | Chinese - Taiwan | RT_ICON |
3 | 3.02695 | 308 | UNKNOWN | English - United States | RT_CURSOR |
4 | 2.74274 | 180 | UNKNOWN | English - United States | RT_CURSOR |
5 | 2.34038 | 308 | UNKNOWN | English - United States | RT_CURSOR |
6 | 2.34004 | 308 | UNKNOWN | English - United States | RT_CURSOR |
7 | 2.51649 | 308 | UNKNOWN | English - United States | RT_CURSOR |
8 | 2.45401 | 308 | UNKNOWN | English - United States | RT_CURSOR |
9 | 2.34864 | 308 | UNKNOWN | English - United States | RT_CURSOR |
10 | 2.34505 | 308 | UNKNOWN | English - United States | RT_CURSOR |
Imports
ADVAPI32.dll |
GDI32.dll |
HID.DLL |
IMM32.dll |
KERNEL32.dll |
MSIMG32.dll |
OLEACC.dll |
OLEAUT32.dll |
SETUPAPI.dll |
SHELL32.dll |
Total processes
56
Monitored processes
15
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 964 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3000.20.935526780\1519307785" -childID 3 -isForBrowser -prefsHandle 3676 -prefMapHandle 3680 -prefsLen 7195 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3000 "\\.\pipe\gecko-crash-server-pipe.3000" 3692 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 1016 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3000.3.1224719219\362013761" -childID 1 -isForBrowser -prefsHandle 1720 -prefMapHandle 1716 -prefsLen 1 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3000 "\\.\pipe\gecko-crash-server-pipe.3000" 1740 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 1560 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3000.13.1613448670\1968549445" -childID 2 -isForBrowser -prefsHandle 2688 -prefMapHandle 2816 -prefsLen 5996 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3000 "\\.\pipe\gecko-crash-server-pipe.3000" 2836 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 2040 | ipconfig | C:\Windows\system32\ipconfig.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: IP Configuration Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2484 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3000.0.1908957727\1925516971" -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3000 "\\.\pipe\gecko-crash-server-pipe.3000" 1184 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 1 Version: 68.0.1 Modules
| |||||||||||||||
| 2520 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
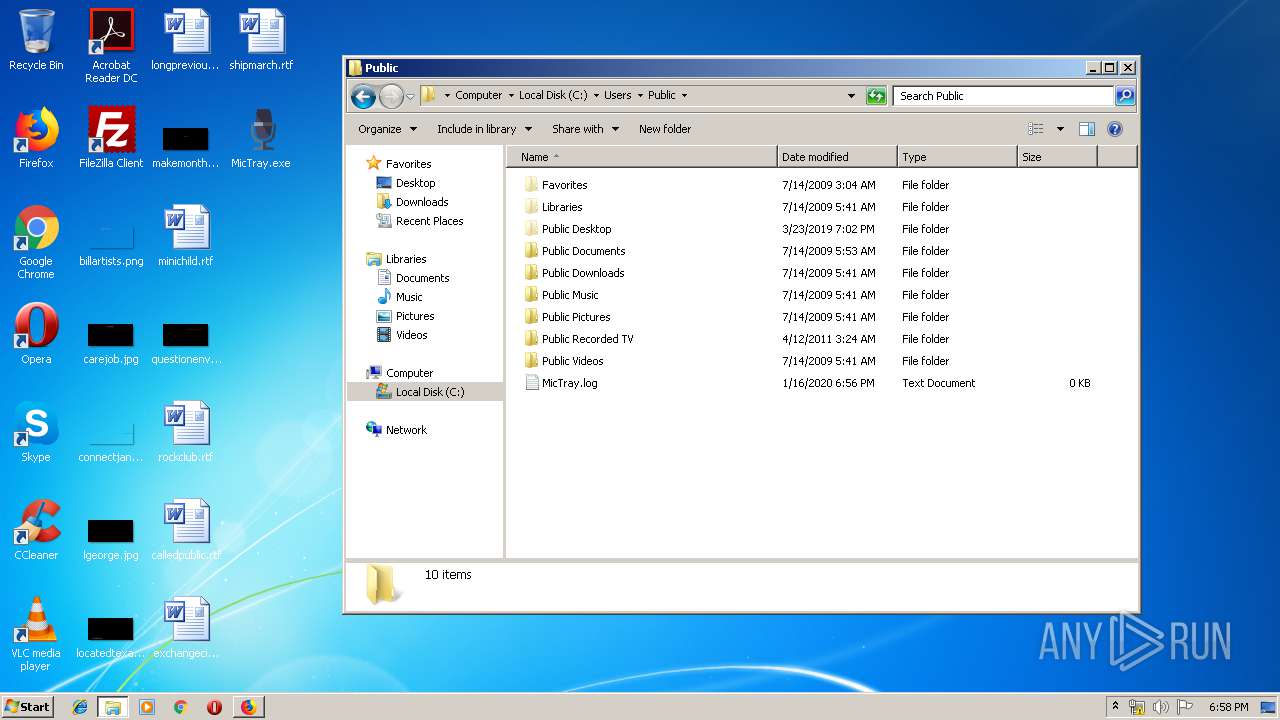
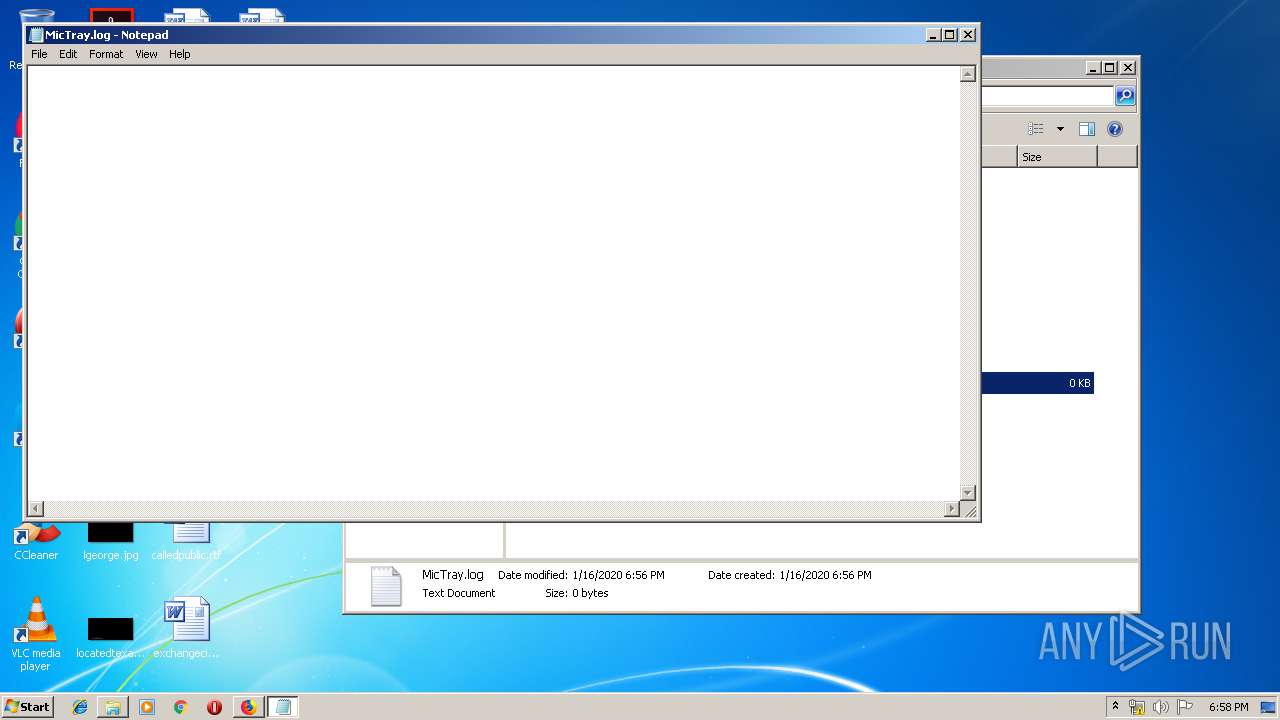
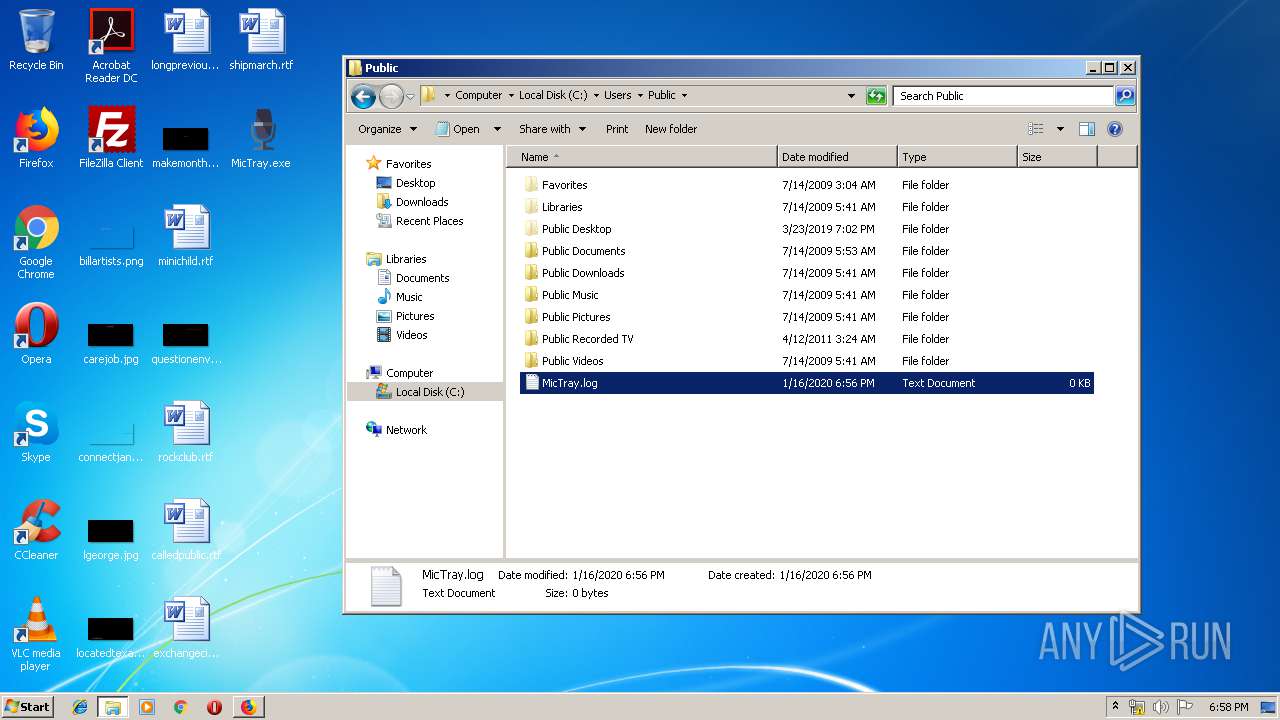
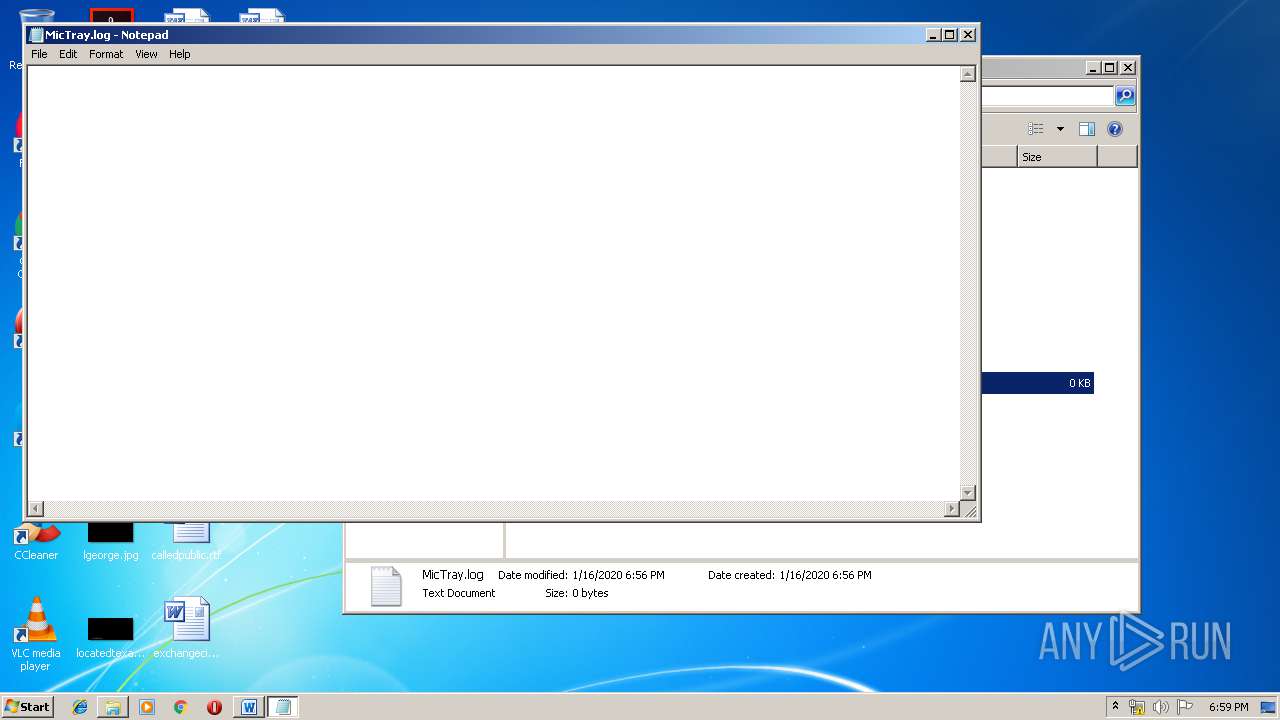
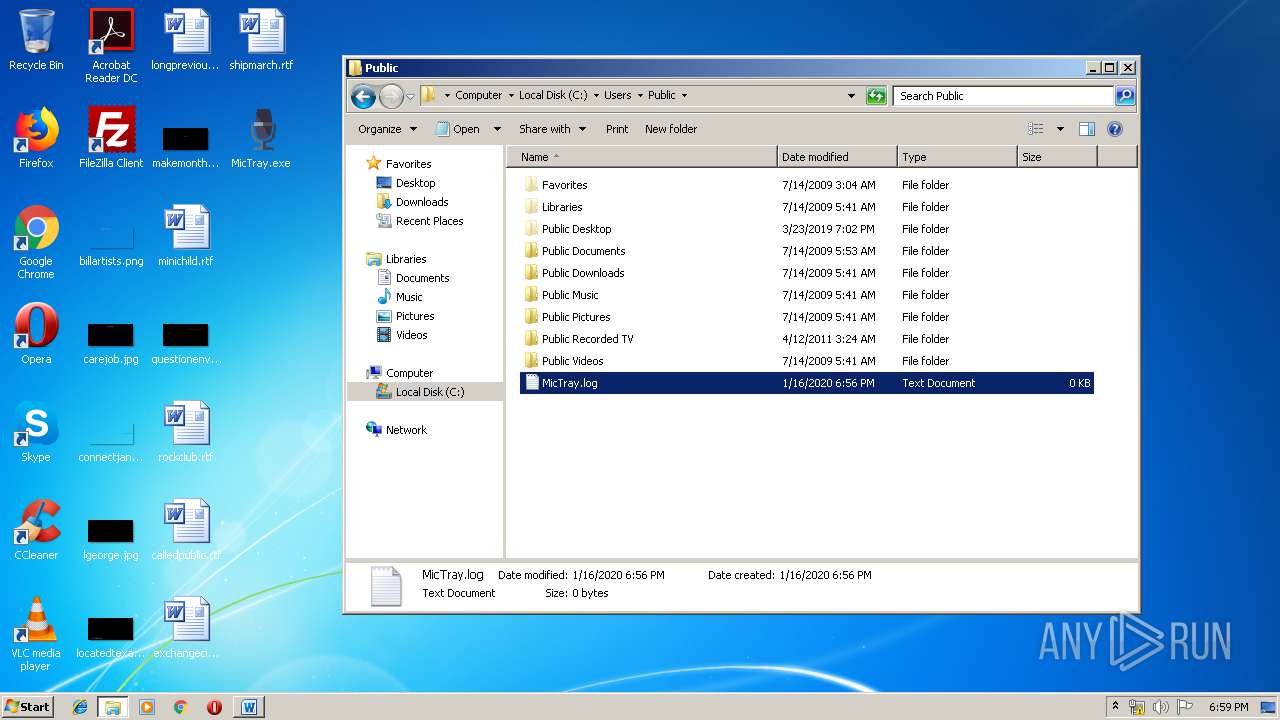
| 2928 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\Public\MicTray.log | C:\Windows\system32\NOTEPAD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2996 | "C:\Users\admin\Desktop\MicTray.exe" | C:\Users\admin\Desktop\MicTray.exe | — | explorer.exe | |||||||||||
User: admin Company: Conexant Integrity Level: MEDIUM Description: mic tray icon Exit code: 0 Version: 1.0.0.31 Modules
| |||||||||||||||
| 3000 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 3280 | "C:\Windows\system32\cmd.exe" | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 967
Read events
1 245
Write events
554
Delete events
168
Modification events
| (PID) Process: | (2520) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: 0BB62D1A03000000 | |||
| (PID) Process: | (3000) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: 0B8F301A03000000 | |||
| (PID) Process: | (3000) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 1 | |||
| (PID) Process: | (3000) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3000) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000092000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3708) NOTEPAD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosX |
Value: 22 | |||
| (PID) Process: | (3708) NOTEPAD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosY |
Value: 22 | |||
| (PID) Process: | (3708) NOTEPAD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosDX |
Value: 960 | |||
| (PID) Process: | (3708) NOTEPAD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosDY |
Value: 501 | |||
| (PID) Process: | (3316) pingsender.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
Executable files
0
Suspicious files
297
Text files
147
Unknown types
151
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3000 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 3000 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 3000 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
| 3000 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\search.json.mozlz4.tmp | — | |
MD5:— | SHA256:— | |||
| 3000 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\urlCache-current.bin | binary | |
MD5:— | SHA256:— | |||
| 3000 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs.js | text | |
MD5:— | SHA256:— | |||
| 3000 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\base-track-digest256.sbstore | binary | |
MD5:— | SHA256:— | |||
| 3000 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\search.json.mozlz4 | jsonlz4 | |
MD5:— | SHA256:— | |||
| 3000 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\allow-flashallow-digest256.sbstore | binary | |
MD5:D886A47C89D9C49C795DA345BC236990 | SHA256:A03C5E2656D2F292BF5794C8EEB8D223CD6BA4F4BFB2ED1F325460E879D0BCF7 | |||
| 3000 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
27
TCP/UDP connections
126
DNS requests
229
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3000 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
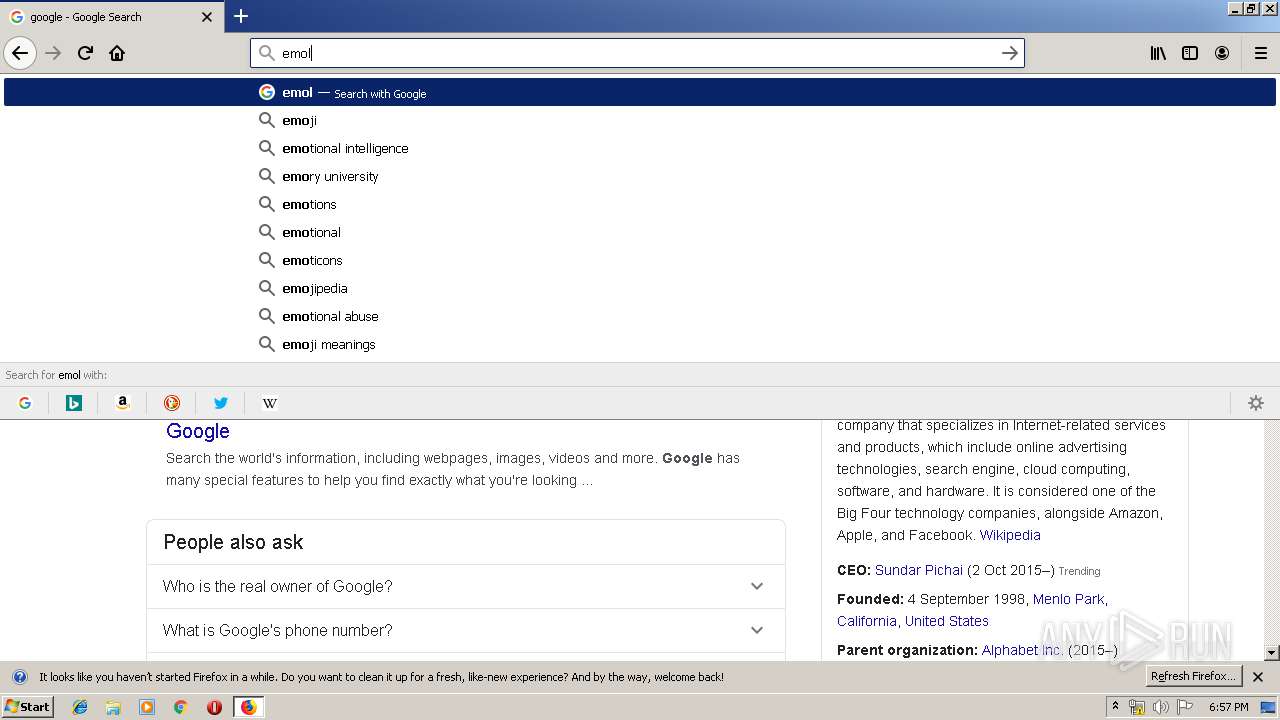
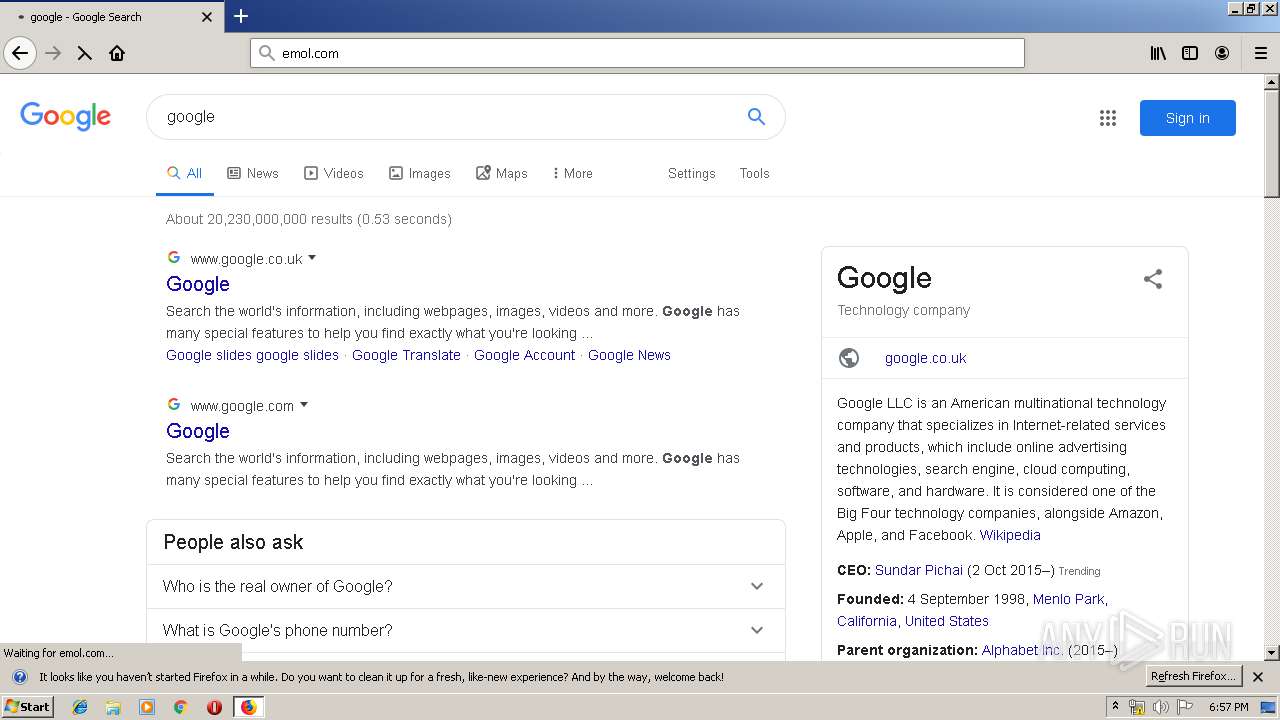
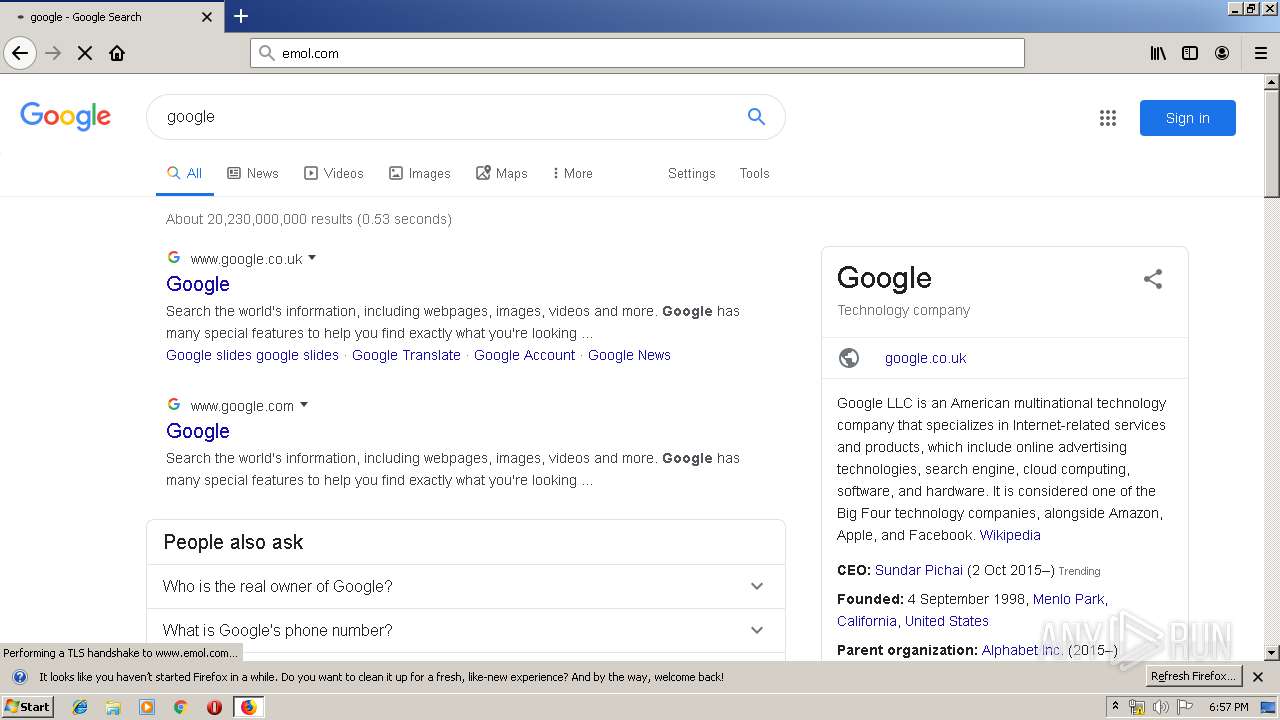
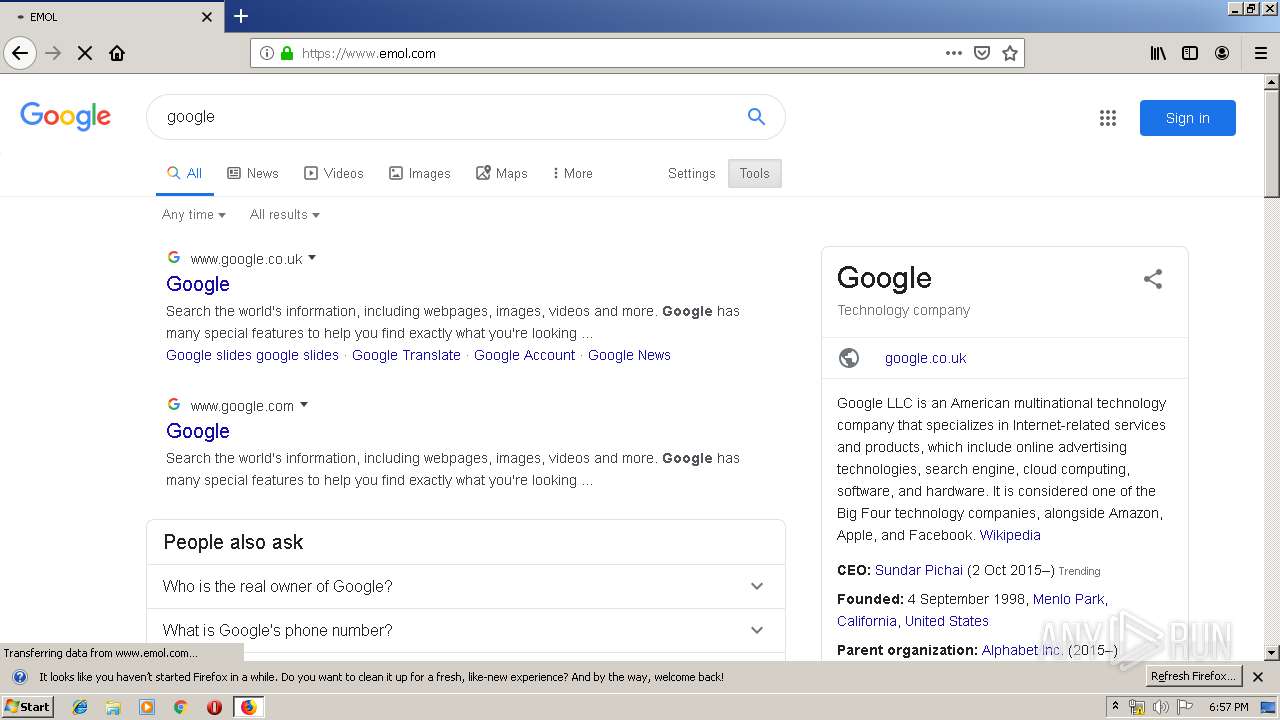
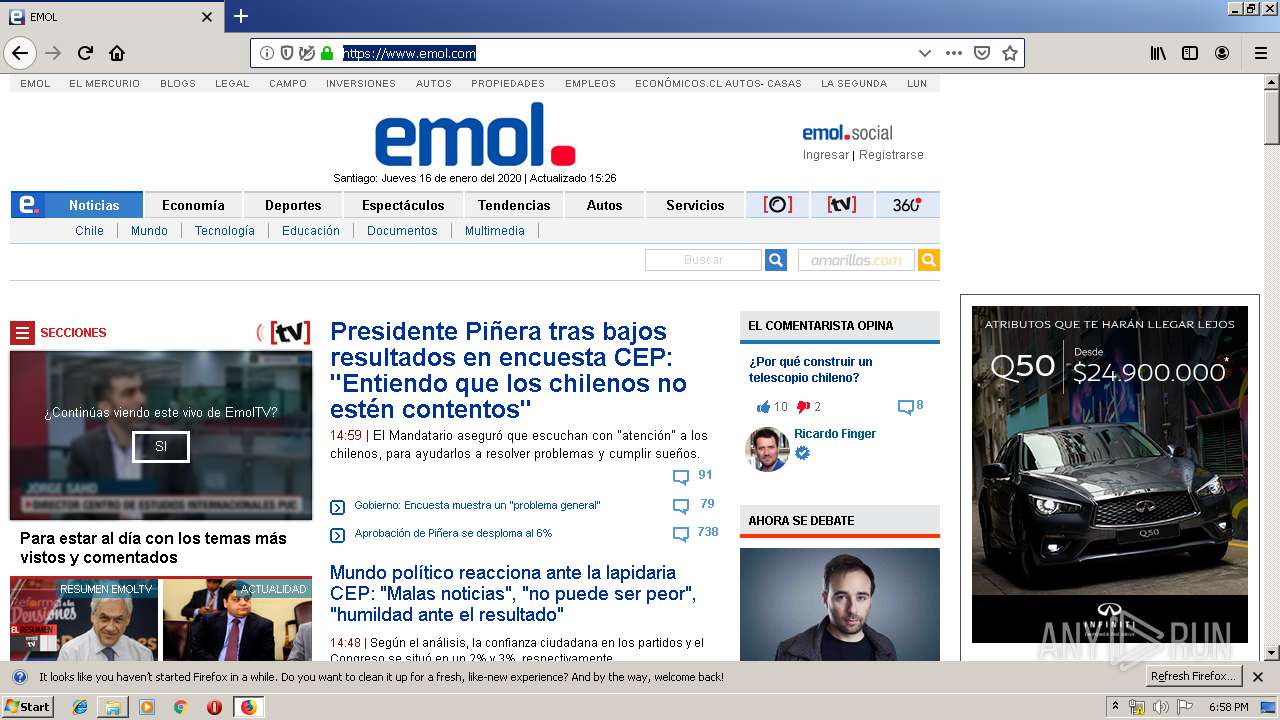
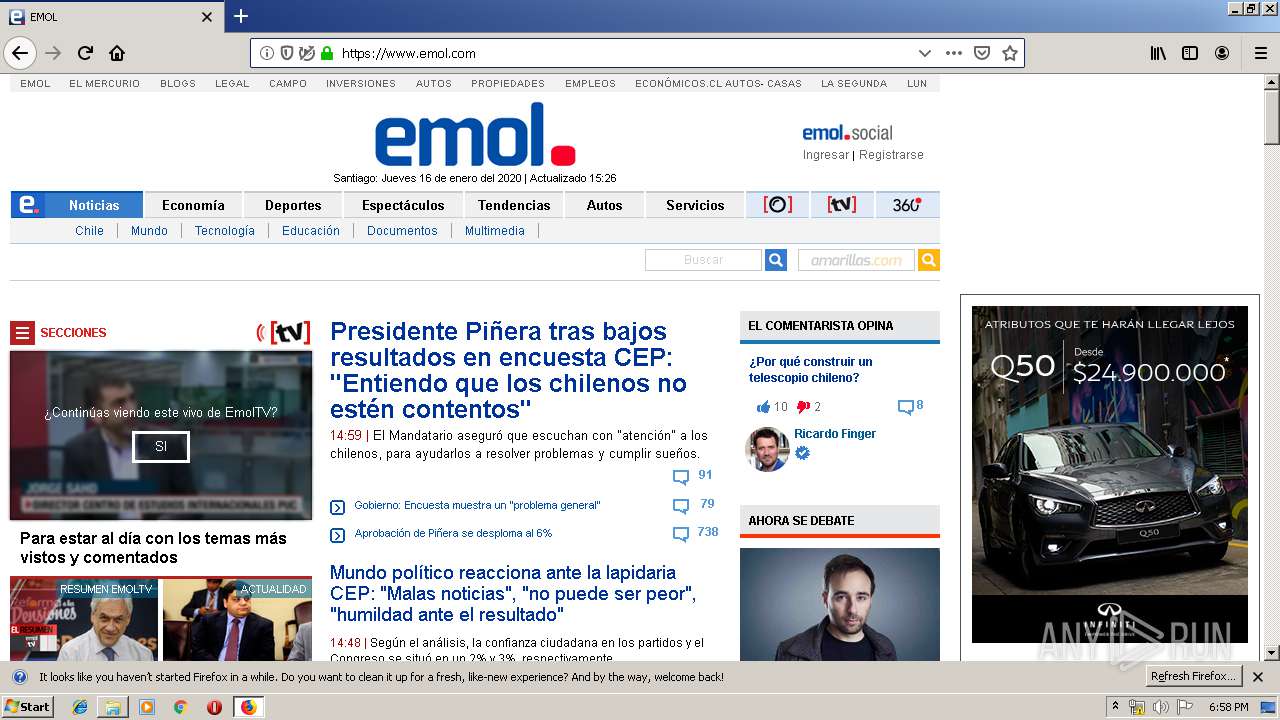
3000 | firefox.exe | GET | 301 | 200.12.20.60:80 | http://emol.com/ | CL | — | — | whitelisted |
3000 | firefox.exe | POST | 200 | 216.58.206.3:80 | http://ocsp.pki.goog/gts1o1 | US | der | 472 b | whitelisted |
3000 | firefox.exe | POST | 200 | 2.21.242.227:80 | http://ocsp.int-x3.letsencrypt.org/ | NL | der | 527 b | whitelisted |
3000 | firefox.exe | POST | 200 | 216.58.206.3:80 | http://ocsp.pki.goog/gts1o1 | US | der | 472 b | whitelisted |
3000 | firefox.exe | POST | 200 | 216.58.206.3:80 | http://ocsp.pki.goog/gts1o1 | US | der | 472 b | whitelisted |
3000 | firefox.exe | POST | 200 | 216.58.206.3:80 | http://ocsp.pki.goog/gts1o1 | US | der | 472 b | whitelisted |
3000 | firefox.exe | POST | 200 | 2.21.242.227:80 | http://ocsp.int-x3.letsencrypt.org/ | NL | der | 527 b | whitelisted |
3000 | firefox.exe | POST | 200 | 216.58.206.3:80 | http://ocsp.pki.goog/gts1o1 | US | der | 471 b | whitelisted |
3000 | firefox.exe | POST | 200 | 151.139.128.14:80 | http://ocsp.comodoca4.com/ | US | der | 279 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3000 | firefox.exe | 2.16.186.50:80 | detectportal.firefox.com | Akamai International B.V. | — | whitelisted |
3000 | firefox.exe | 143.204.214.76:443 | content-signature-2.cdn.mozilla.net | — | US | suspicious |
3000 | firefox.exe | 54.148.67.145:443 | tiles.services.mozilla.com | Amazon.com, Inc. | US | unknown |
3000 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3000 | firefox.exe | 172.217.22.110:443 | www.youtube.com | Google Inc. | US | whitelisted |
3000 | firefox.exe | 172.217.22.10:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3000 | firefox.exe | 143.204.214.123:443 | firefox.settings.services.mozilla.com | — | US | suspicious |
3000 | firefox.exe | 216.58.207.36:443 | www.google.com | Google Inc. | US | whitelisted |
3000 | firefox.exe | 216.58.206.3:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3000 | firefox.exe | 172.217.18.3:443 | www.google.co.uk | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
detectportal.firefox.com |
| whitelisted |
a1089.dscd.akamai.net |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
push.services.mozilla.com |
| whitelisted |
autopush.prod.mozaws.net |
| whitelisted |
snippets.cdn.mozilla.net |
| whitelisted |
d228z91au11ukj.cloudfront.net |
| whitelisted |
tiles.services.mozilla.com |
| whitelisted |
tiles.r53-2.services.mozilla.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
3000 | firefox.exe | Generic Protocol Command Decode | SURICATA STREAM CLOSEWAIT FIN out of window |