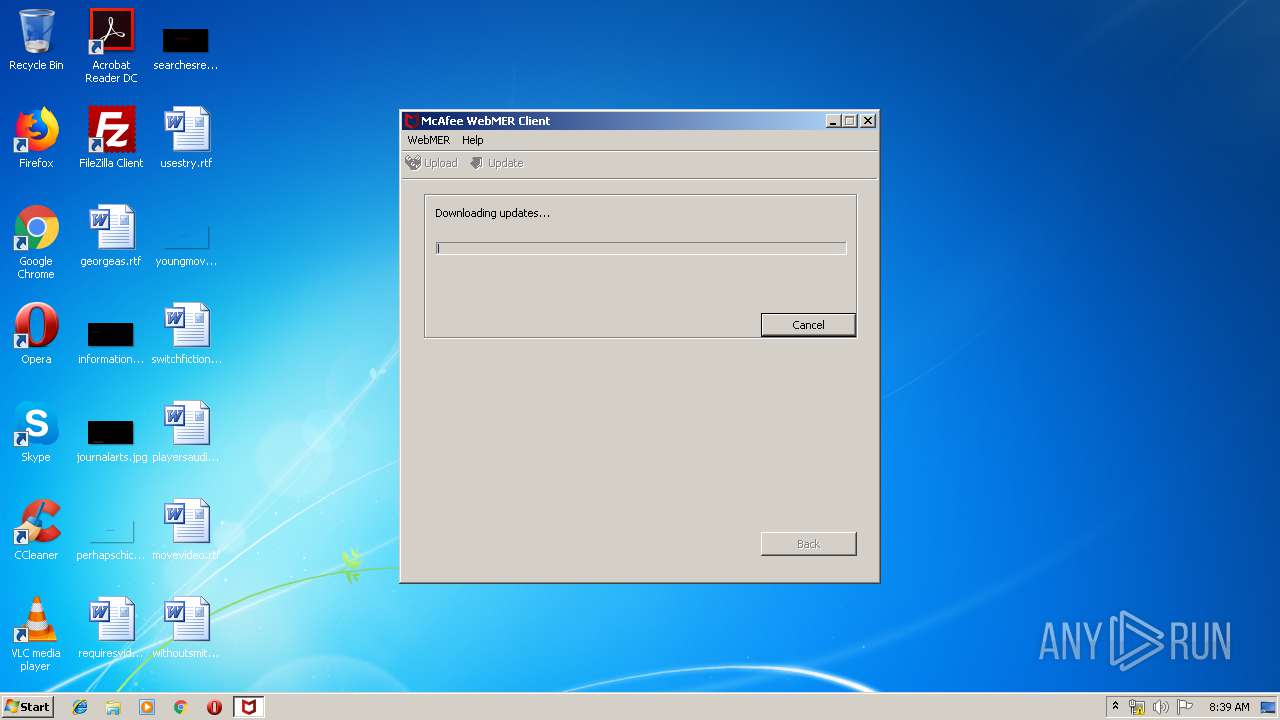
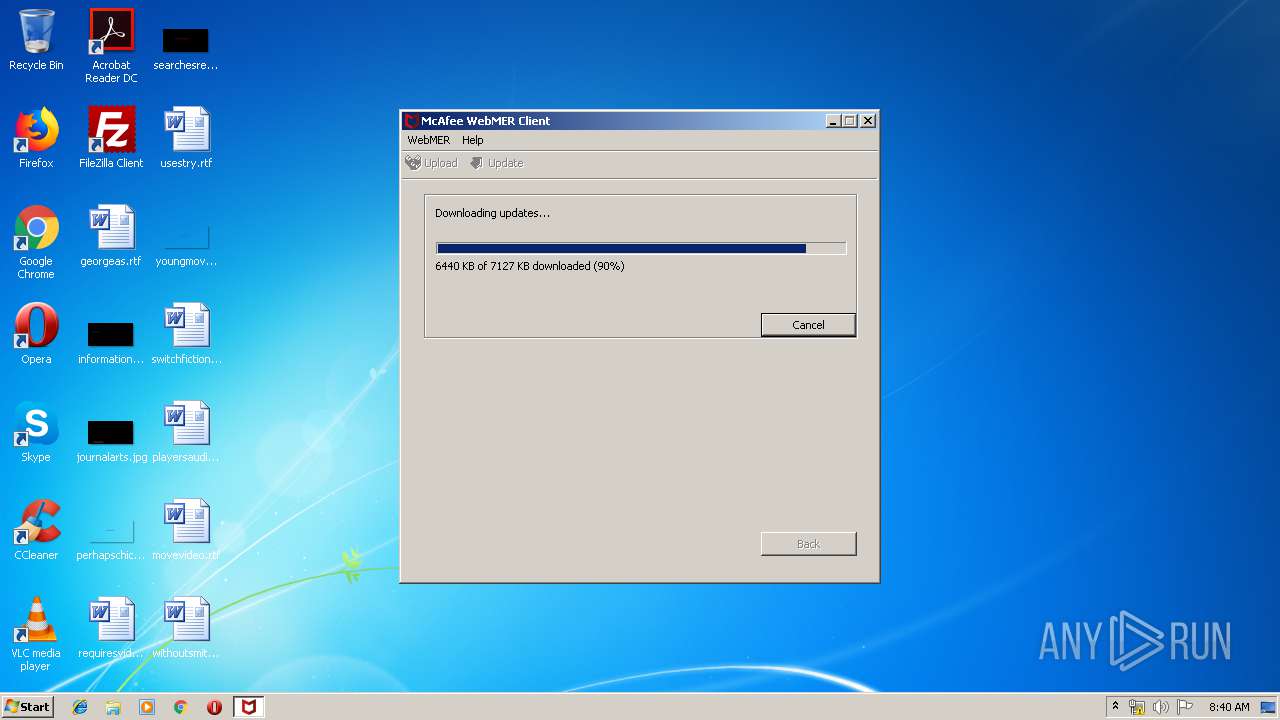
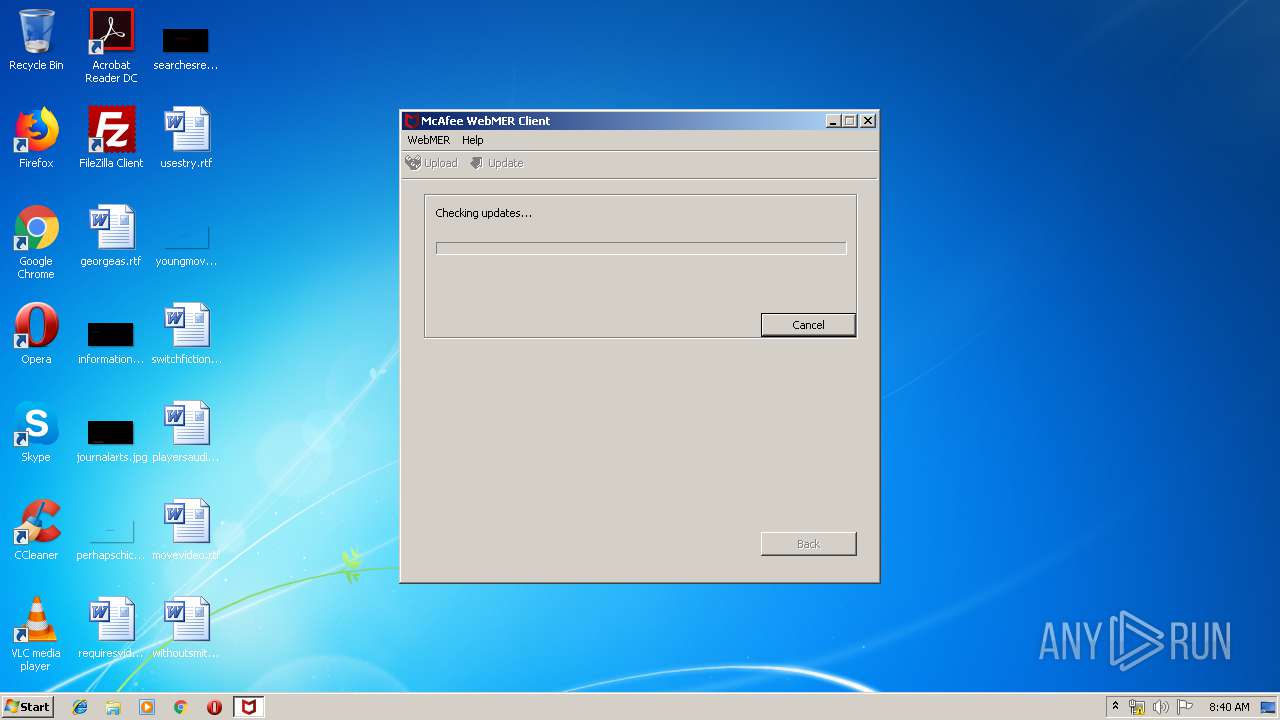
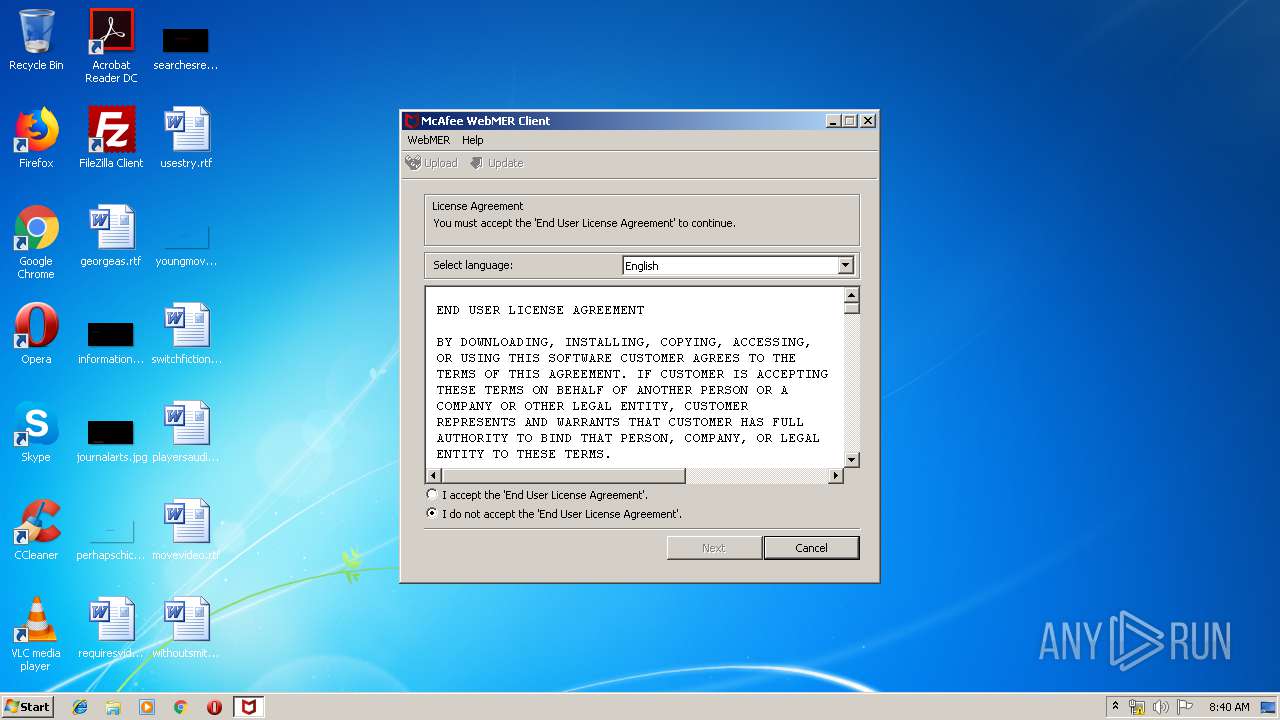
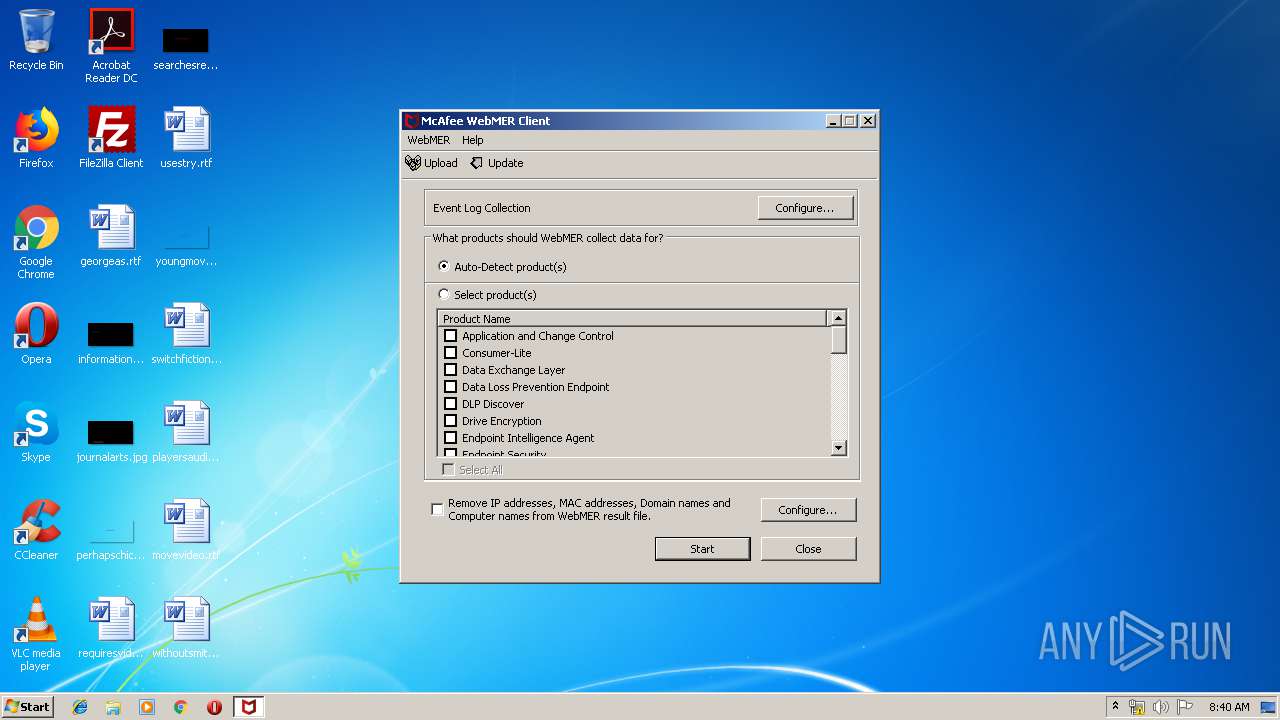
| File name: | MER.exe |
| Full analysis: | https://app.any.run/tasks/f0203894-fc51-45a9-a6be-e0a5c80480b9 |
| Verdict: | No threats detected |
| Analysis date: | July 26, 2019, 07:39:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 4A459686F7F56D3C8F07EDE44CE1A313 |
| SHA1: | 2C0D02648FAC397D3864A96ABB01354E72851772 |
| SHA256: | 417A36A10336F8F6B9571020F5DC37D01E627BBA51CFD0BE2C0DD6D4A8880050 |
| SSDEEP: | 196608:auYZUtrXmYh2w3TRMovUAwyAXxF6IjEEEbiTT:aalmYX3TRN8ADAXxF6QT |
MALICIOUS
Application was dropped or rewritten from another process
- WebMERClient.exe (PID: 2460)
- MER.exe (PID: 3324)
- WebMERClient.exe (PID: 2056)
Loads dropped or rewritten executable
- WebMERClient.exe (PID: 2460)
- WebMERClient.exe (PID: 2056)
SUSPICIOUS
Creates files in the program directory
- WebMERClient.exe (PID: 2460)
Executable content was dropped or overwritten
- MER.exe (PID: 3864)
- WebMERClient.exe (PID: 2460)
- MER.exe (PID: 3324)
Reads internet explorer settings
- WebMERClient.exe (PID: 2460)
- WebMERClient.exe (PID: 2056)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (43.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (29.8) |
| .exe | | | Generic Win/DOS Executable (13.2) |
| .exe | | | DOS Executable Generic (13.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:01:23 11:50:36+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 2048 |
| InitializedDataSize: | 7286272 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x13e8 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.0.0.0 |
| ProductVersionNumber: | 4.0.0.0 |
| FileFlagsMask: | 0x0017 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | McAfee LLC |
| FileDescription: | McMERExtractor Application |
| FileVersion: | 4, 0, 0, 0 |
| InternalName: | McMERExtractor |
| LegalCopyright: | Copyright ©2019 McAfee LLC. All Rights Reserved. |
| OriginalFileName: | McMERExtractor.exe |
| ProductName: | McAfee WebMER |
| ProductVersion: | 4.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 23-Jan-2019 10:50:36 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | McAfee LLC |
| FileDescription: | McMERExtractor Application |
| FileVersion: | 4, 0, 0, 0 |
| InternalName: | McMERExtractor |
| LegalCopyright: | Copyright ©2019 McAfee LLC. All Rights Reserved. |
| OriginalFilename: | McMERExtractor.exe |
| ProductName: | McAfee WebMER |
| ProductVersion: | 4.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 23-Jan-2019 10:50:36 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000063A | 0x00000800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 4.99267 |
.rdata | 0x00002000 | 0x00000558 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.30576 |
.rsrc | 0x00003000 | 0x006F2610 | 0x006F2800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.99574 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.12085 | 1156 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 4.20067 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
{78DB5B78-681D-4866-88EF-768934BF6DFA} | 7.99529 | 6942750 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
{88A41E31-9C18-4471-9C2D-AC728A17B054} | 7.99842 | 333458 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
KERNEL32.dll |
SETUPAPI.dll |
SHELL32.dll |
USER32.dll |
Total processes
43
Monitored processes
5
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1712 | "C:\Users\admin\AppData\Local\Temp\MER.exe" | C:\Users\admin\AppData\Local\Temp\MER.exe | — | explorer.exe | |||||||||||
User: admin Company: McAfee LLC Integrity Level: MEDIUM Description: McMERExtractor Application Exit code: 3221226540 Version: 4, 0, 0, 0 Modules
| |||||||||||||||
| 2056 | "C:\Users\admin\AppData\Local\Temp\WebMERClient.exe" /extractor "C:\Users\admin\AppData\Local\Temp\MER.exe" /proc 3324 C:\Users\admin\AppData\Local\Temp\MER.exe /wait2 | C:\Users\admin\AppData\Local\Temp\WebMERClient.exe | MER.exe | ||||||||||||
User: admin Company: McAfee LLC Integrity Level: HIGH Description: WebMERClient Module Exit code: 0 Version: 4, 0, 0, 0 Modules
| |||||||||||||||
| 2460 | "C:\Users\admin\AppData\Local\Temp\WebMERClient.exe" /extractor "C:\Users\admin\AppData\Local\Temp\MER.exe" /proc 3864 "C:\Users\admin\AppData\Local\Temp\MER.exe" | C:\Users\admin\AppData\Local\Temp\WebMERClient.exe | MER.exe | ||||||||||||
User: admin Company: McAfee LLC Integrity Level: HIGH Description: WebMERClient Module Exit code: 0 Version: 4, 0, 0, 0 Modules
| |||||||||||||||
| 3324 | C:\Users\admin\AppData\Local\Temp\MER.exe /wait2 | C:\Users\admin\AppData\Local\Temp\MER.exe | WebMERClient.exe | ||||||||||||
User: admin Company: McAfee LLC Integrity Level: HIGH Description: McMERExtractor Application Exit code: 0 Version: 4, 0, 0, 0 Modules
| |||||||||||||||
| 3864 | "C:\Users\admin\AppData\Local\Temp\MER.exe" | C:\Users\admin\AppData\Local\Temp\MER.exe | explorer.exe | ||||||||||||
User: admin Company: McAfee LLC Integrity Level: HIGH Description: McMERExtractor Application Exit code: 0 Version: 4, 0, 0, 0 Modules
| |||||||||||||||
Total events
248
Read events
197
Write events
50
Delete events
1
Modification events
| (PID) Process: | (2460) WebMERClient.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2460) WebMERClient.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2460) WebMERClient.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WebMERClient_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2460) WebMERClient.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WebMERClient_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2460) WebMERClient.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WebMERClient_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2460) WebMERClient.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WebMERClient_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2460) WebMERClient.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WebMERClient_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2460) WebMERClient.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WebMERClient_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2460) WebMERClient.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WebMERClient_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2460) WebMERClient.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WebMERClient_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
10
Suspicious files
43
Text files
4
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3864 | MER.exe | C:\Users\admin\AppData\Local\Temp\WebMERClientCompressed.tgz | — | |
MD5:— | SHA256:— | |||
| 2460 | WebMERClient.exe | C:\Users\admin\AppData\Local\Temp\{97F069FD-8C1D-49CD-A7B9-6A9CFAF975F4} | — | |
MD5:— | SHA256:— | |||
| 2460 | WebMERClient.exe | C:\Users\admin\AppData\Local\Temp\{B2E075EA-9EF9-4451-9664-4FC406CF032D} | — | |
MD5:— | SHA256:— | |||
| 2460 | WebMERClient.exe | C:\Users\admin\AppData\Local\Temp\WebMERProc.txt | — | |
MD5:— | SHA256:— | |||
| 3324 | MER.exe | C:\Users\admin\AppData\Local\Temp\WebMERClientCompressed.tgz | — | |
MD5:— | SHA256:— | |||
| 2056 | WebMERClient.exe | C:\Users\admin\AppData\Local\Temp\{1D88B6F9-8350-4C3C-8134-88C77A3CD2C3} | — | |
MD5:— | SHA256:— | |||
| 2056 | WebMERClient.exe | C:\Users\admin\AppData\Local\Temp\{2672F5CF-2A3B-4C43-9395-1E6081642A7D} | — | |
MD5:— | SHA256:— | |||
| 2460 | WebMERClient.exe | C:\Users\admin\AppData\Local\Temp\English_RemoteMER.htm | html | |
MD5:— | SHA256:— | |||
| 2460 | WebMERClient.exe | C:\Users\admin\AppData\Local\Temp\English_eula.htm | html | |
MD5:— | SHA256:— | |||
| 2460 | WebMERClient.exe | C:\ProgramData\McAfee\WebMER\MER.xml | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2460 | WebMERClient.exe | 161.69.13.31:443 | mer.mcafee.com | McAfee, Inc. | US | unknown |
2056 | WebMERClient.exe | 161.69.13.31:443 | mer.mcafee.com | McAfee, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
mer.mcafee.com |
| suspicious |