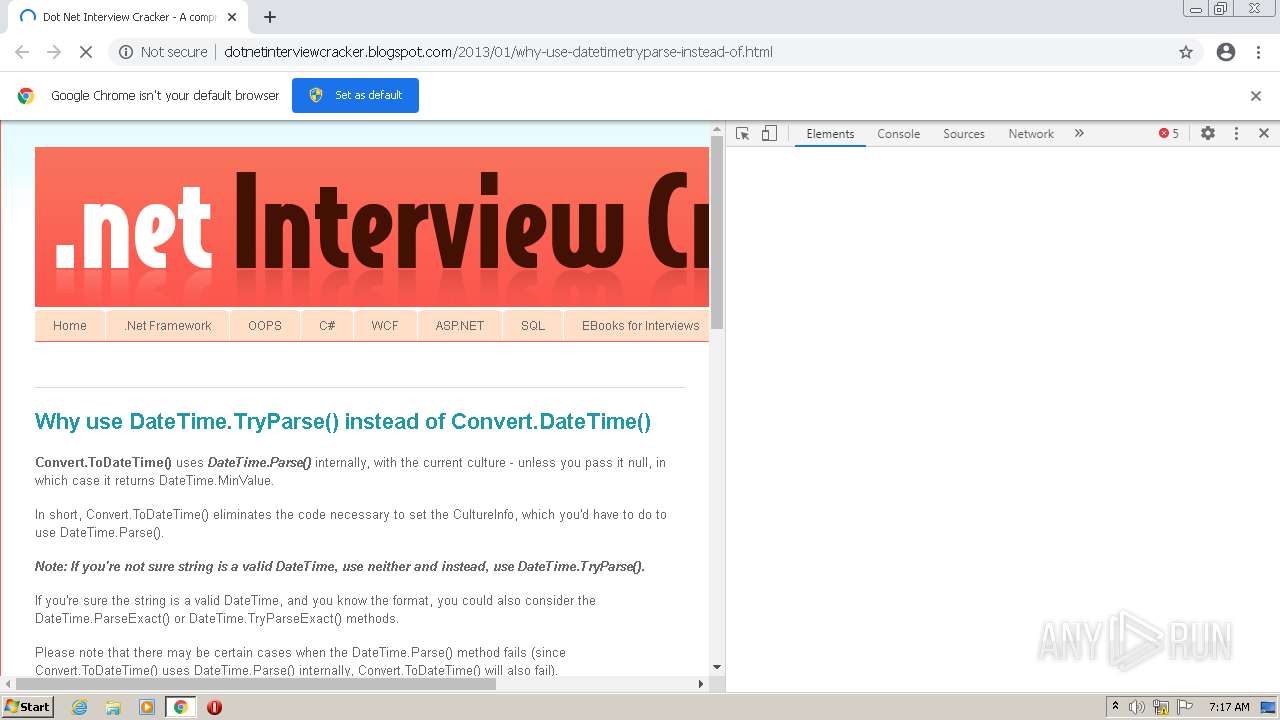
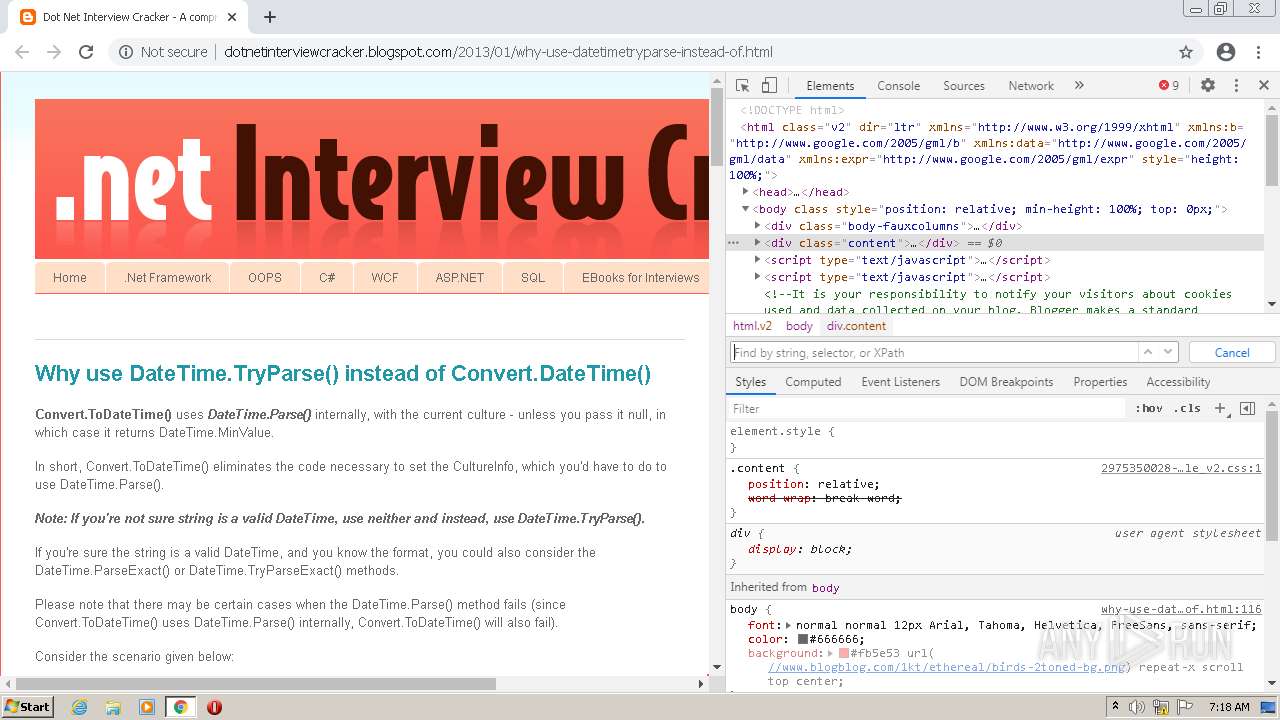
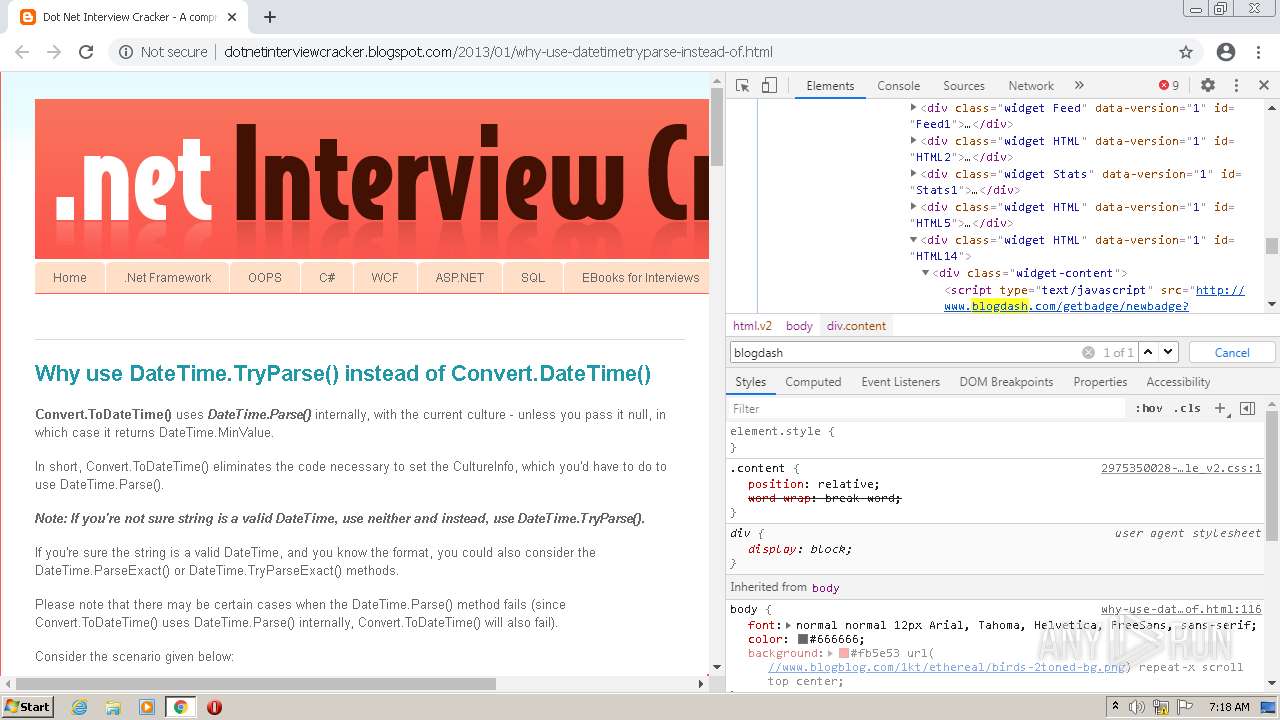
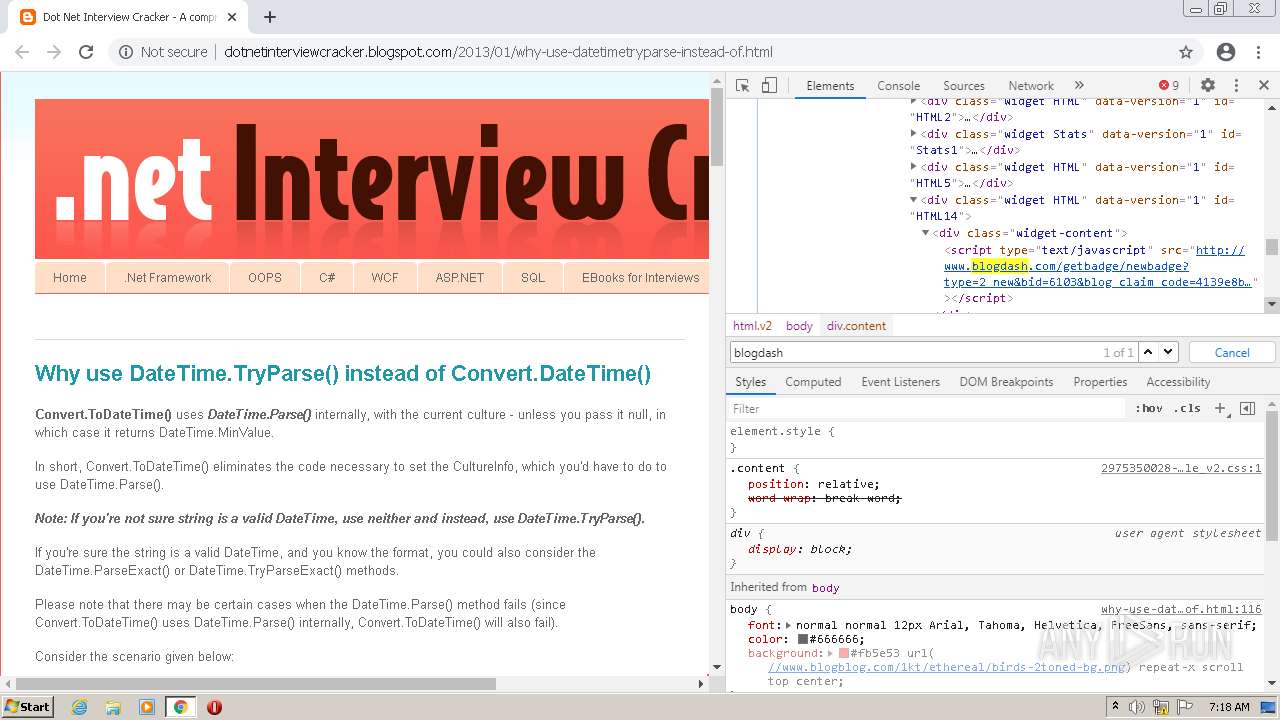
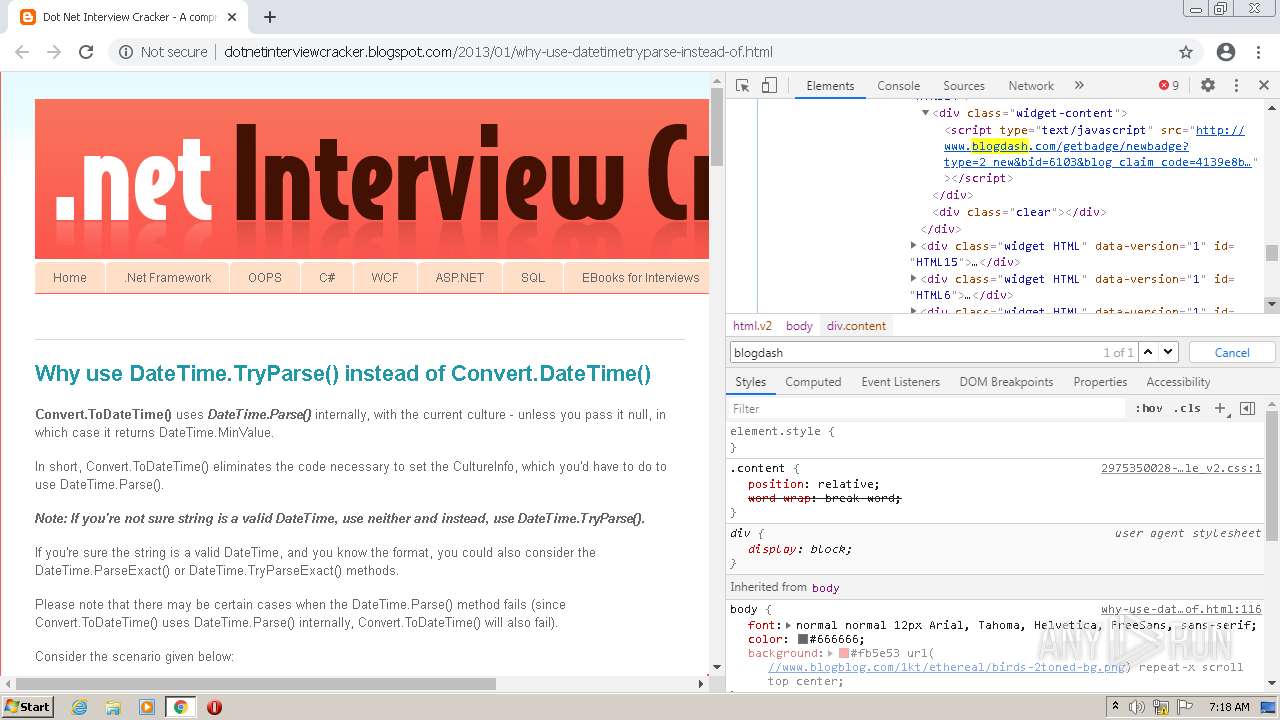
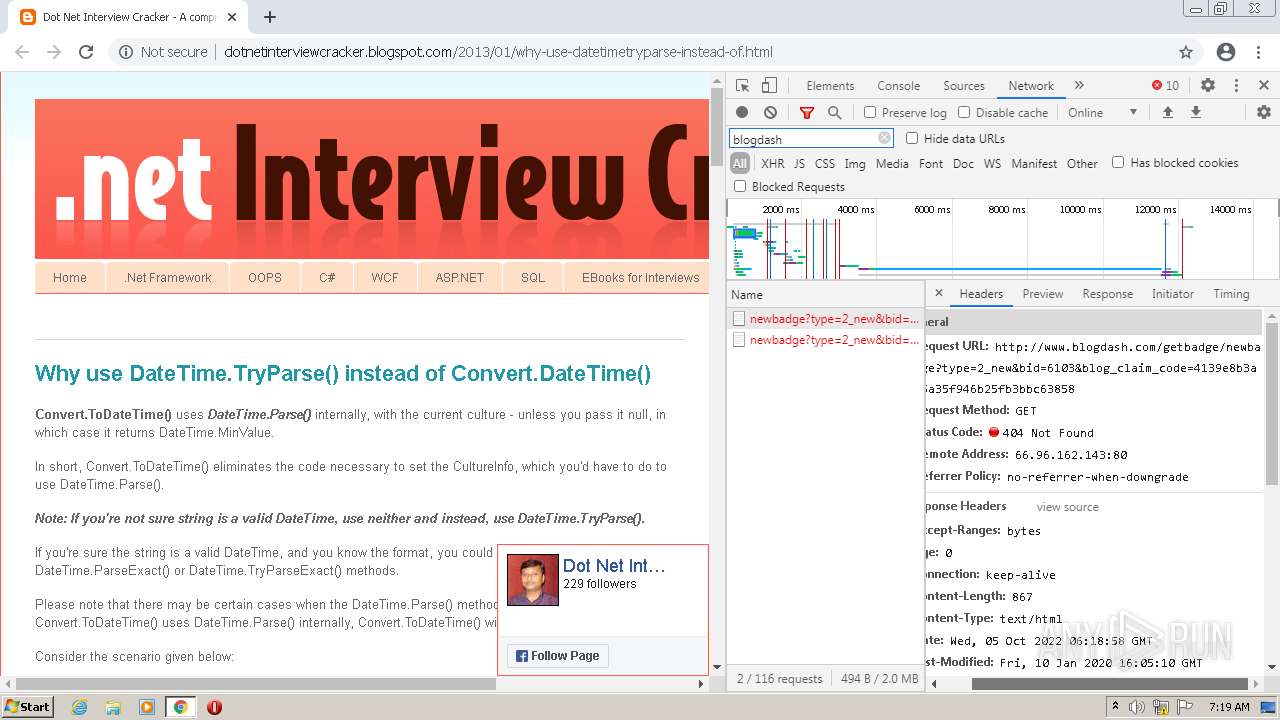
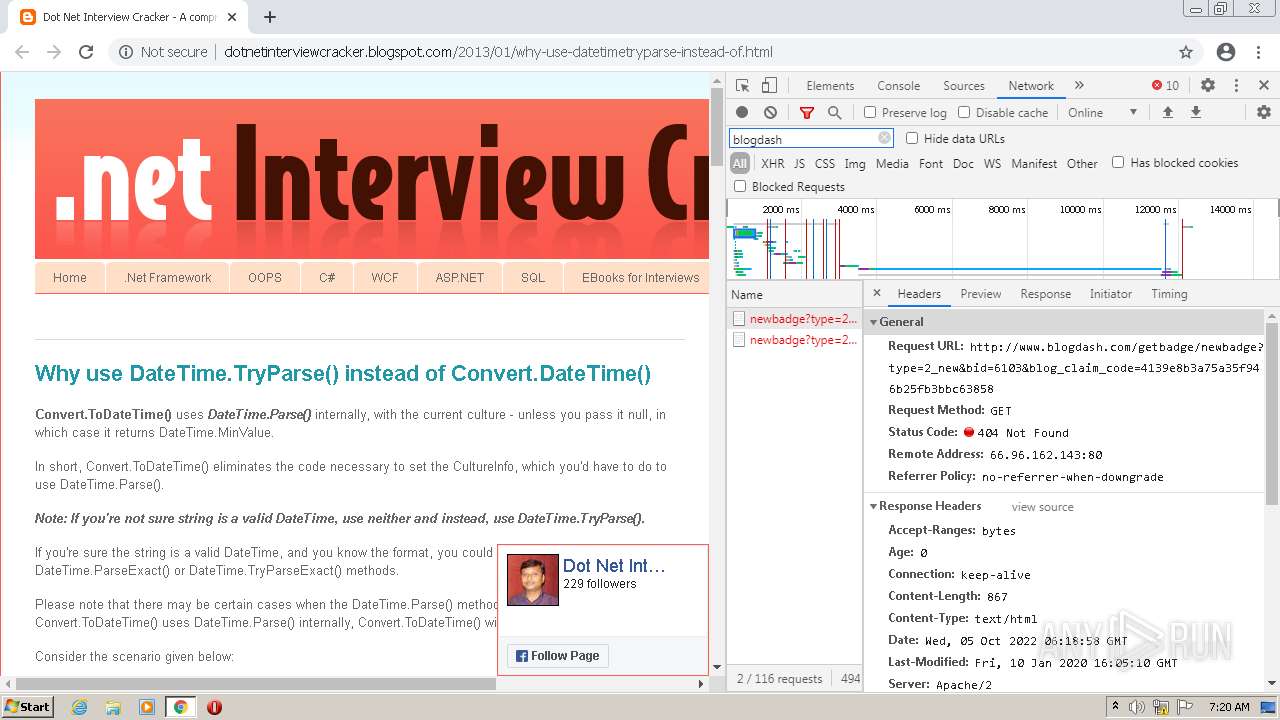
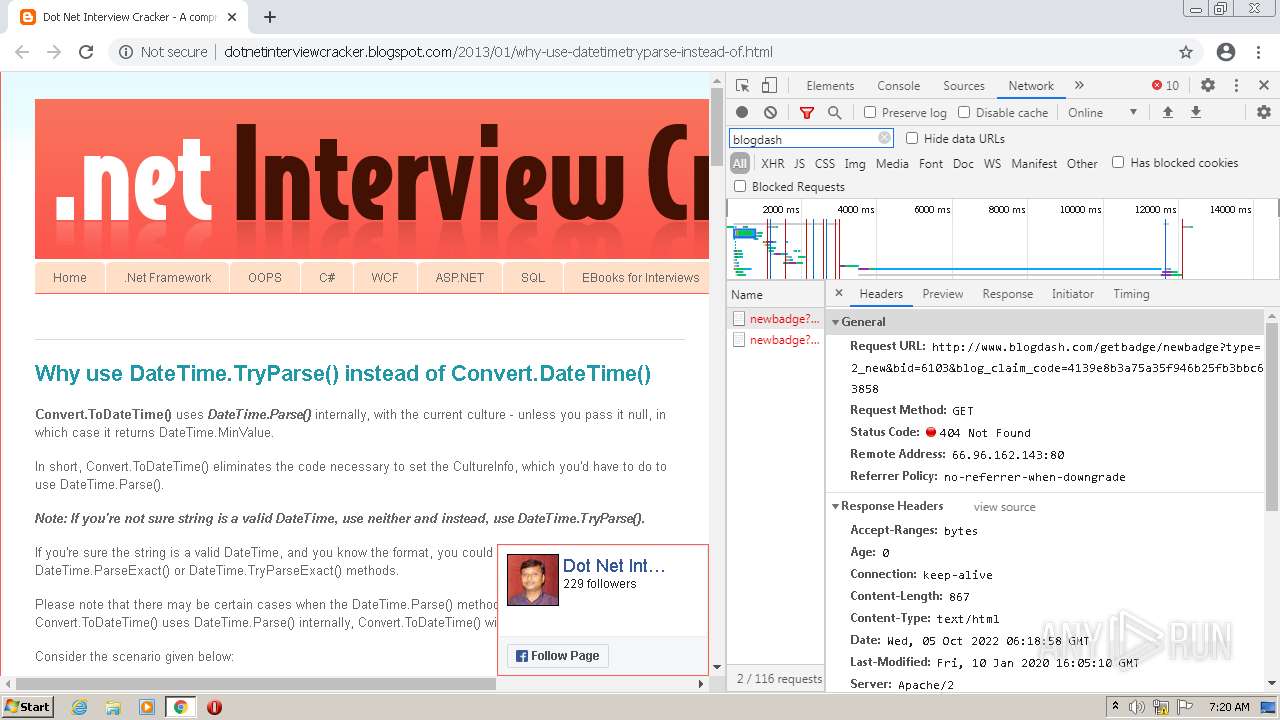
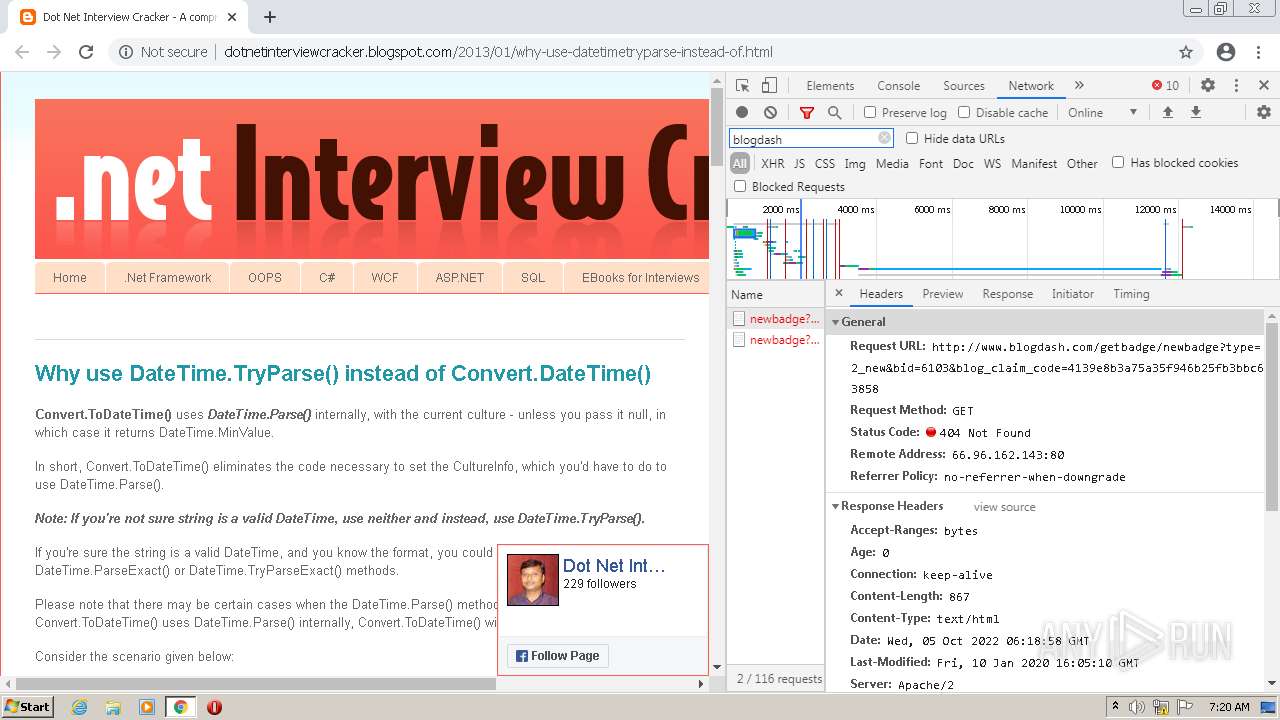
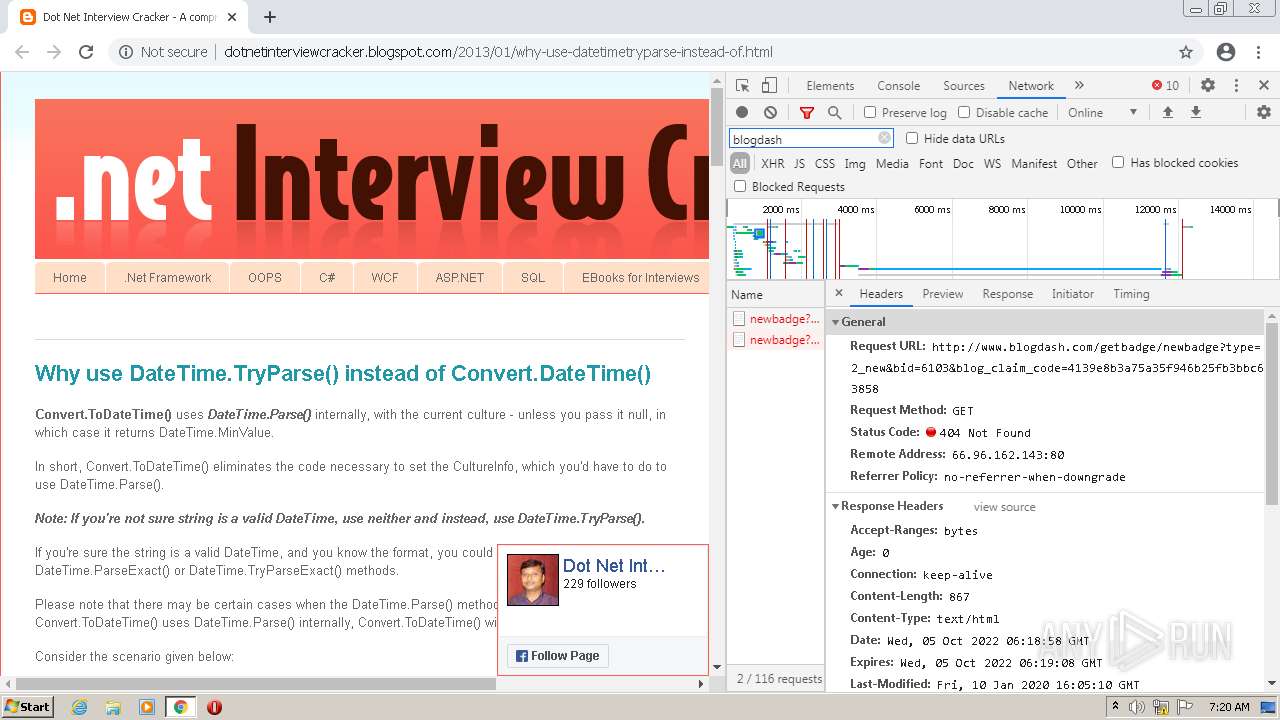
| URL: | http://dotnetinterviewcracker.blogspot.com/2013/01/why-use-datetimetryparse-instead-of.html |
| Full analysis: | https://app.any.run/tasks/fe2de281-fedc-4810-bf91-c41042f61721 |
| Verdict: | Malicious activity |
| Analysis date: | October 05, 2022, 06:17:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | B1A5F301B0C4598F9AF5D0CB925E6681 |
| SHA1: | BEA2813BDE008EB7630502AAD6072E1BF55BCEF9 |
| SHA256: | 416288E9E5148C815BFDE18D0503397C1B47E304117ADDC860CD5008794F857D |
| SSDEEP: | 3:N1KaKyRpSA3GSKMlK0cIyR0+XkEhL1KXNG:CaVR8GKrVR0+XVKdG |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 1656)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
65
Monitored processes
30
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1032,4273221337207610515,13837560531476211229,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3980 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 188 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,4273221337207610515,13837560531476211229,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2736 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,4273221337207610515,13837560531476211229,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1908 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 452 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1032,4273221337207610515,13837560531476211229,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=820 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 544 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,4273221337207610515,13837560531476211229,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2156 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1312 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1032,4273221337207610515,13837560531476211229,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3936 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1656 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "http://dotnetinterviewcracker.blogspot.com/2013/01/why-use-datetimetryparse-instead-of.html" | C:\Program Files\Google\Chrome\Application\chrome.exe | Explorer.EXE | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,4273221337207610515,13837560531476211229,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2780 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2056 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,4273221337207610515,13837560531476211229,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3552 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2136 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,4273221337207610515,13837560531476211229,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3524 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
13 140
Read events
13 032
Write events
103
Delete events
5
Modification events
| (PID) Process: | (1656) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1656) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1656) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1656) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1656) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1656) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1656) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1656) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1656) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (1656) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
1
Suspicious files
35
Text files
134
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1656 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-633D216F-678.pma | — | |
MD5:— | SHA256:— | |||
| 1656 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\3e5a62d2-c61c-407e-95db-b4a356ff46e3.tmp | text | |
MD5:— | SHA256:— | |||
| 1656 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 2828 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 1656 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFd9f5d.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
| 1656 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFd9f5d.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 1656 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RFd9f6d.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
| 1656 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 1656 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:995C92837E4775CAFFE387D51ADBA520 | SHA256:51247C3464FD988B72670002D01A57FBFF1348704D325DC8FF8817ED2459D0D9 | |||
| 1656 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
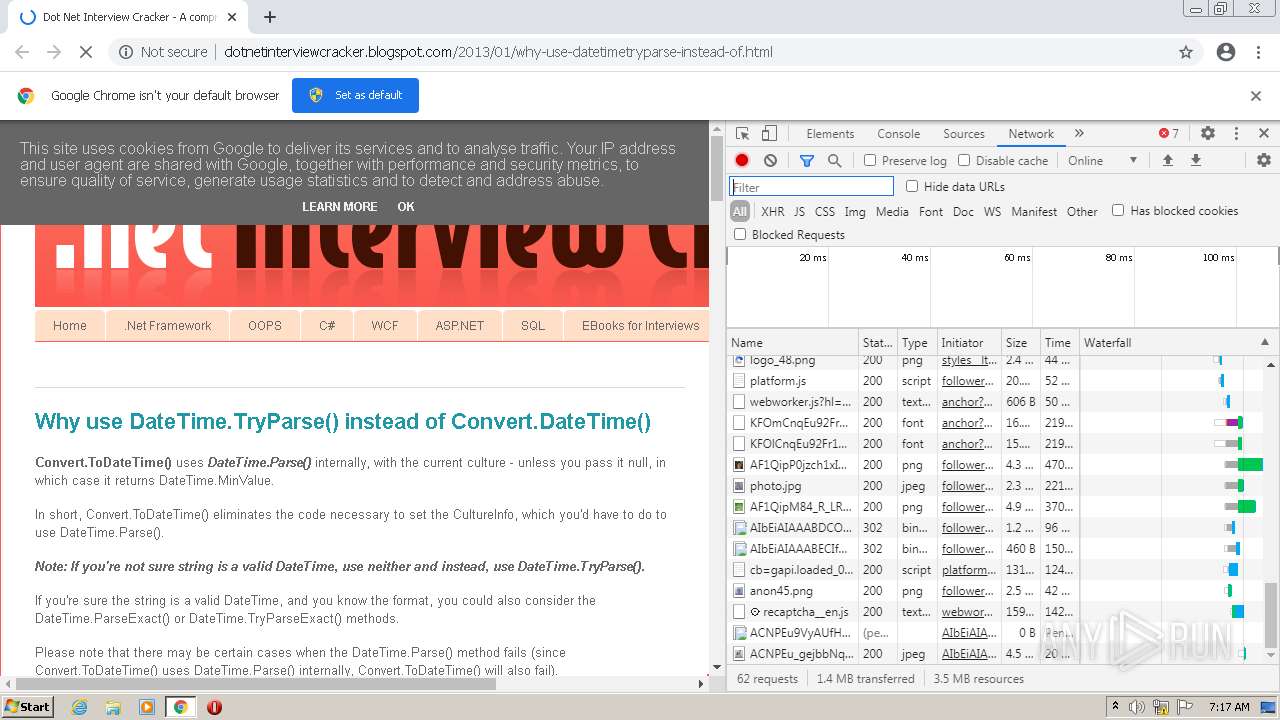
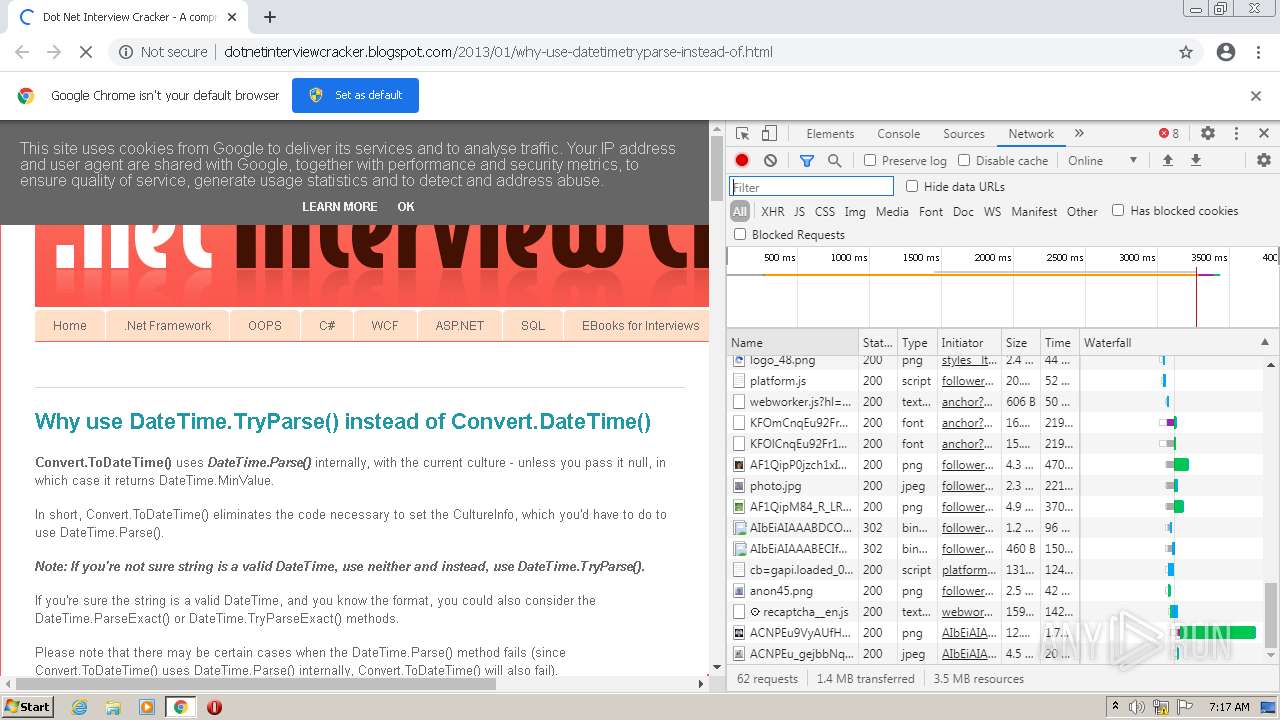
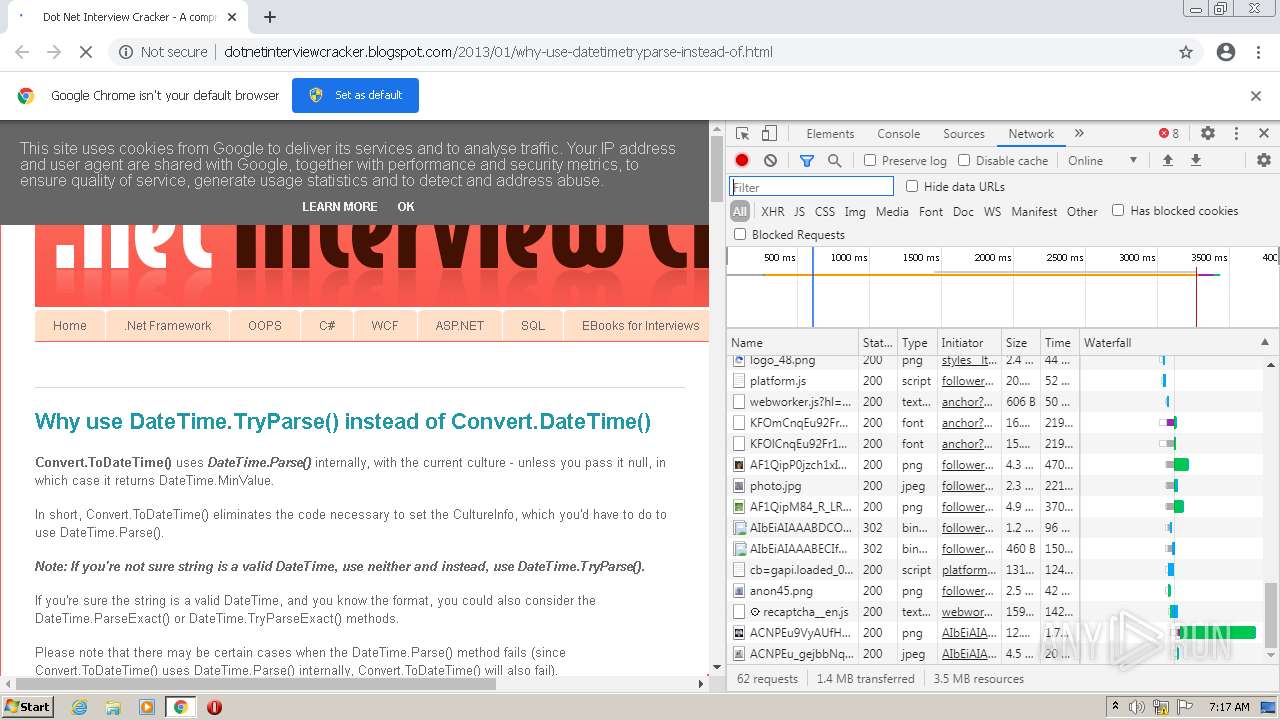
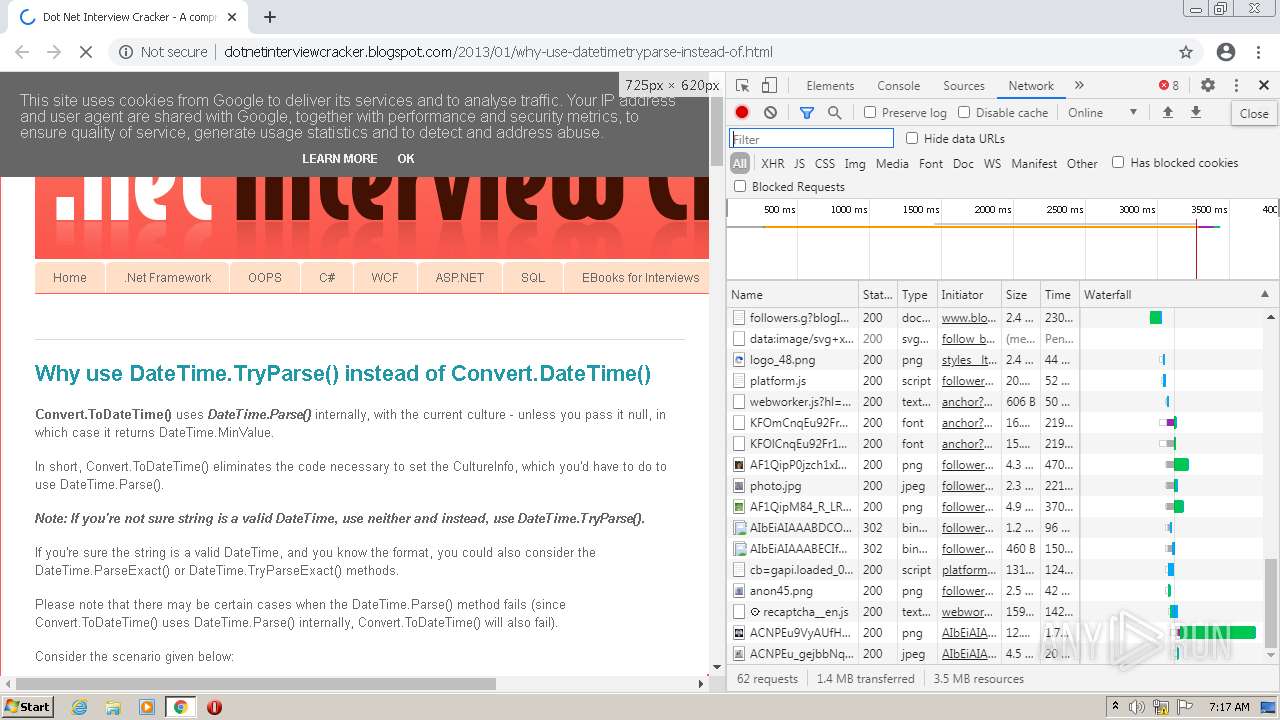
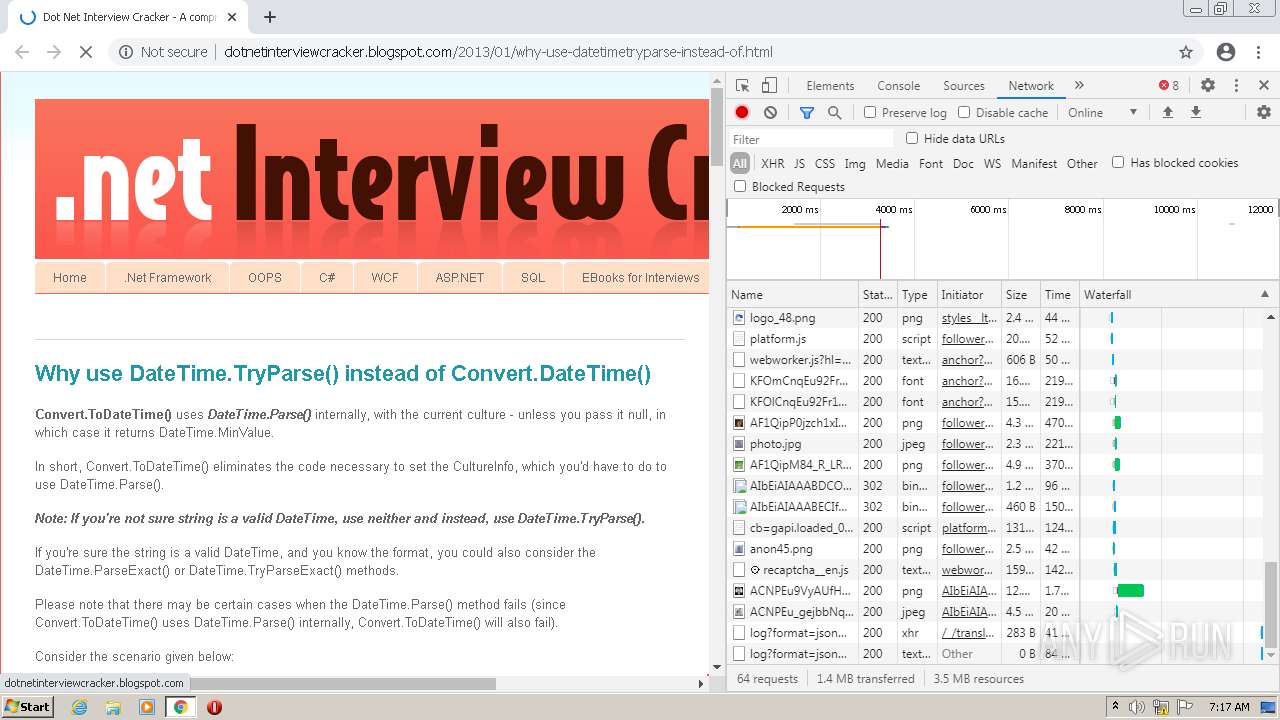
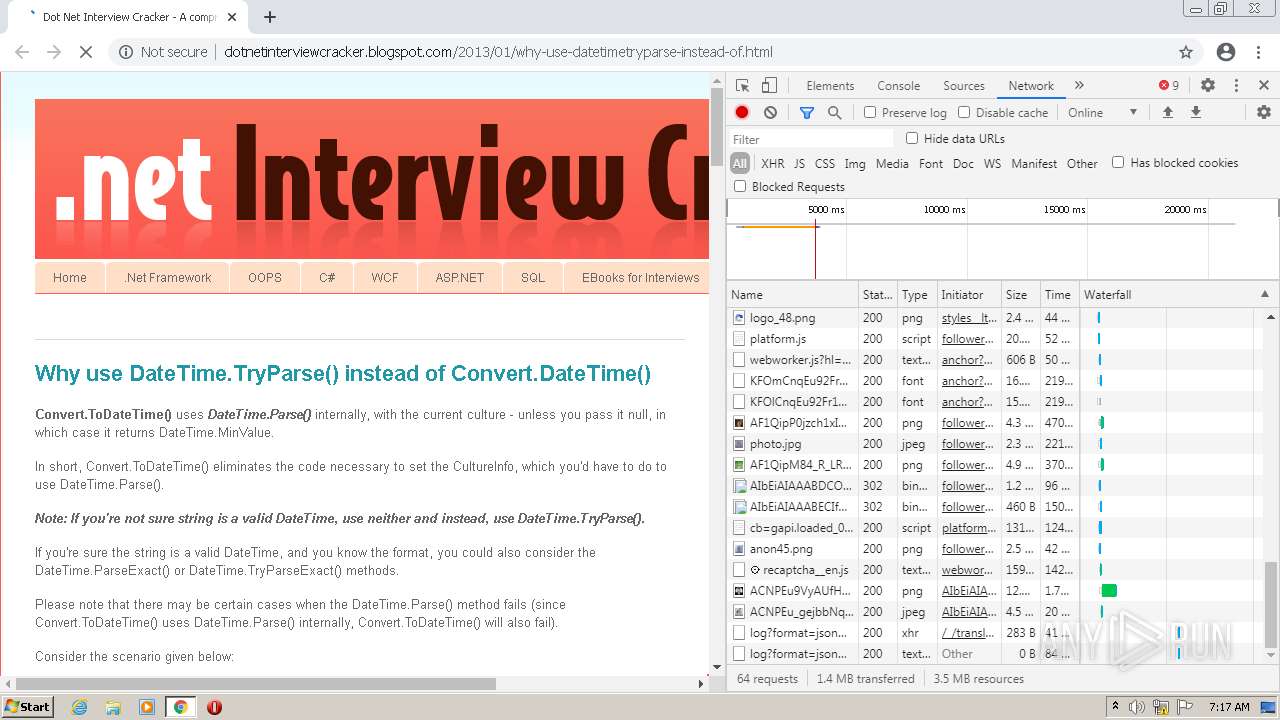
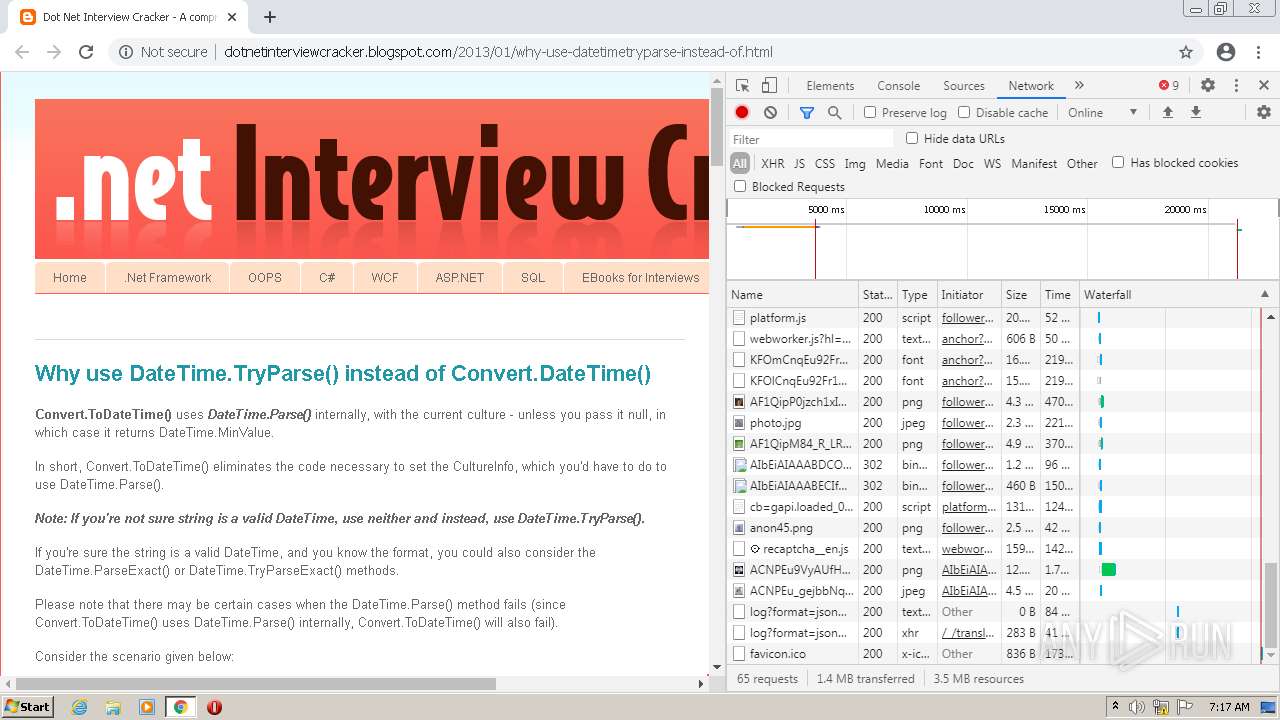
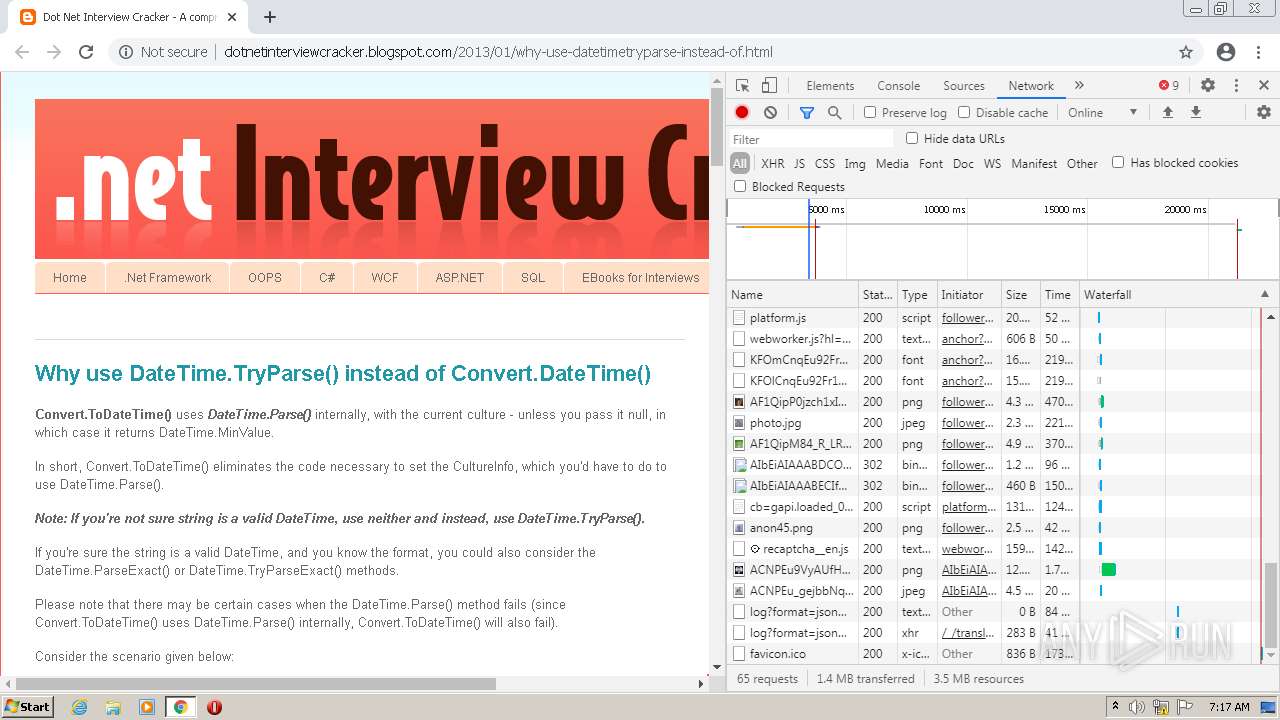
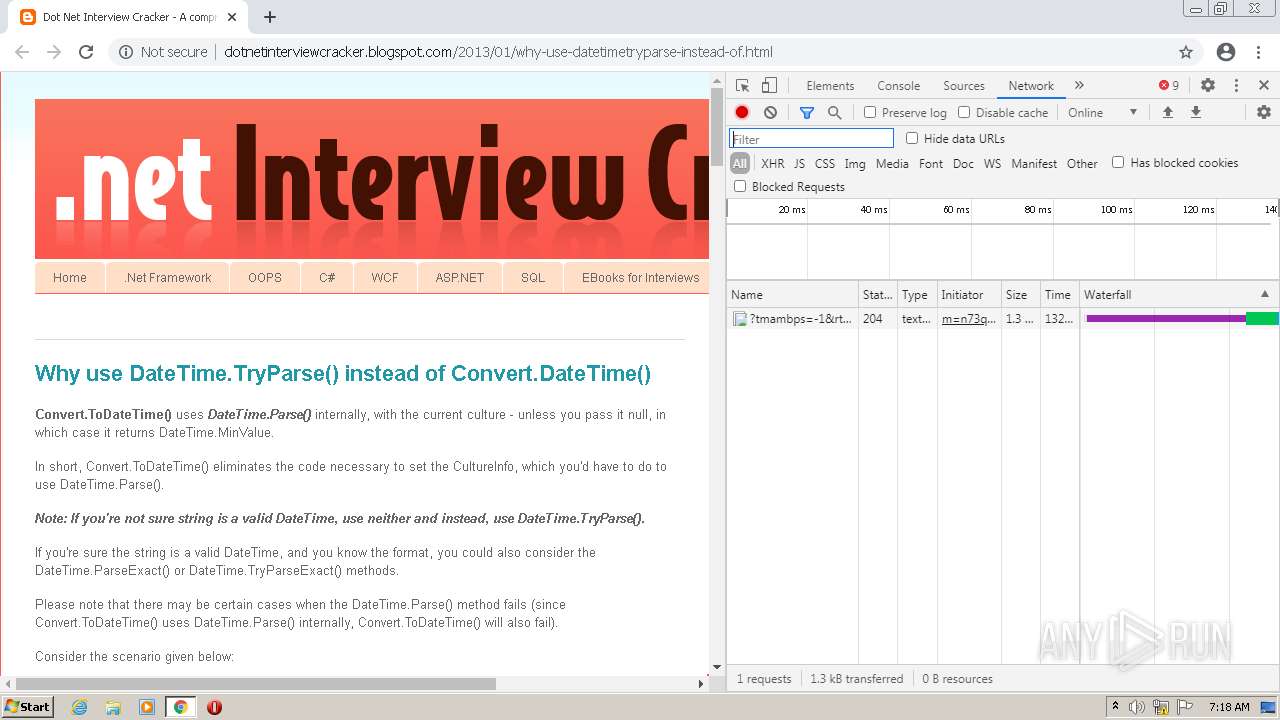
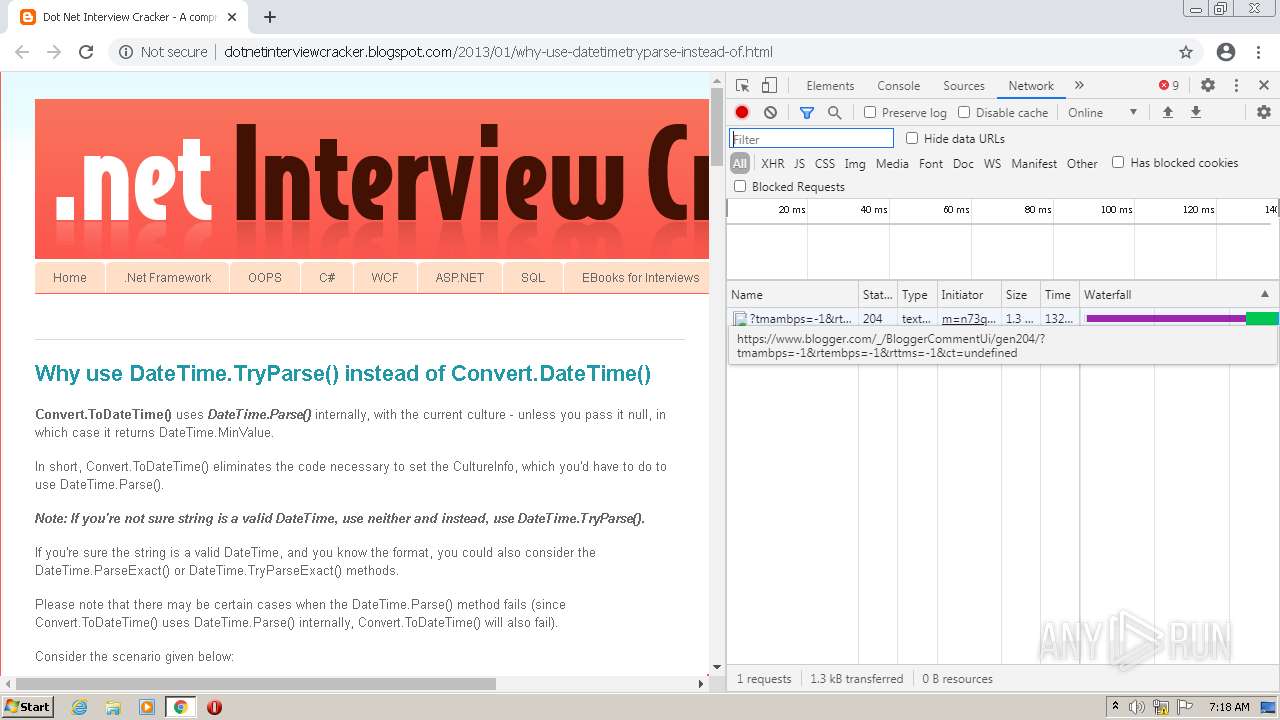
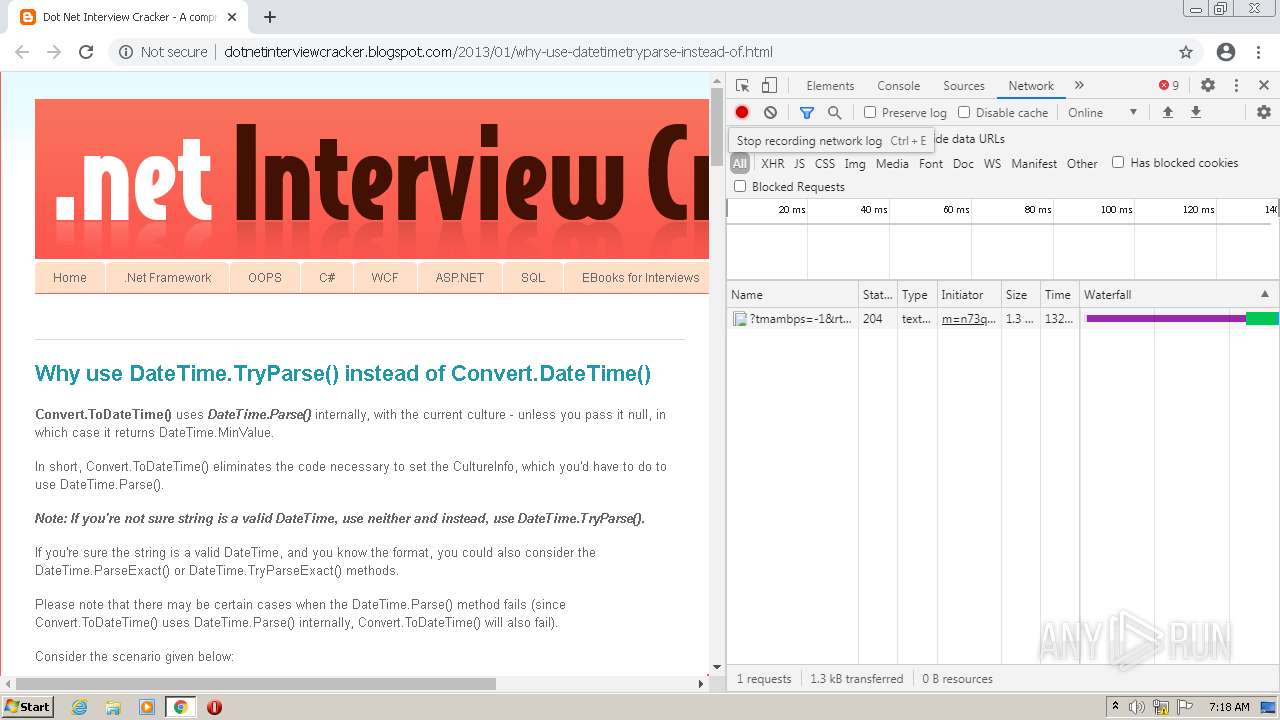
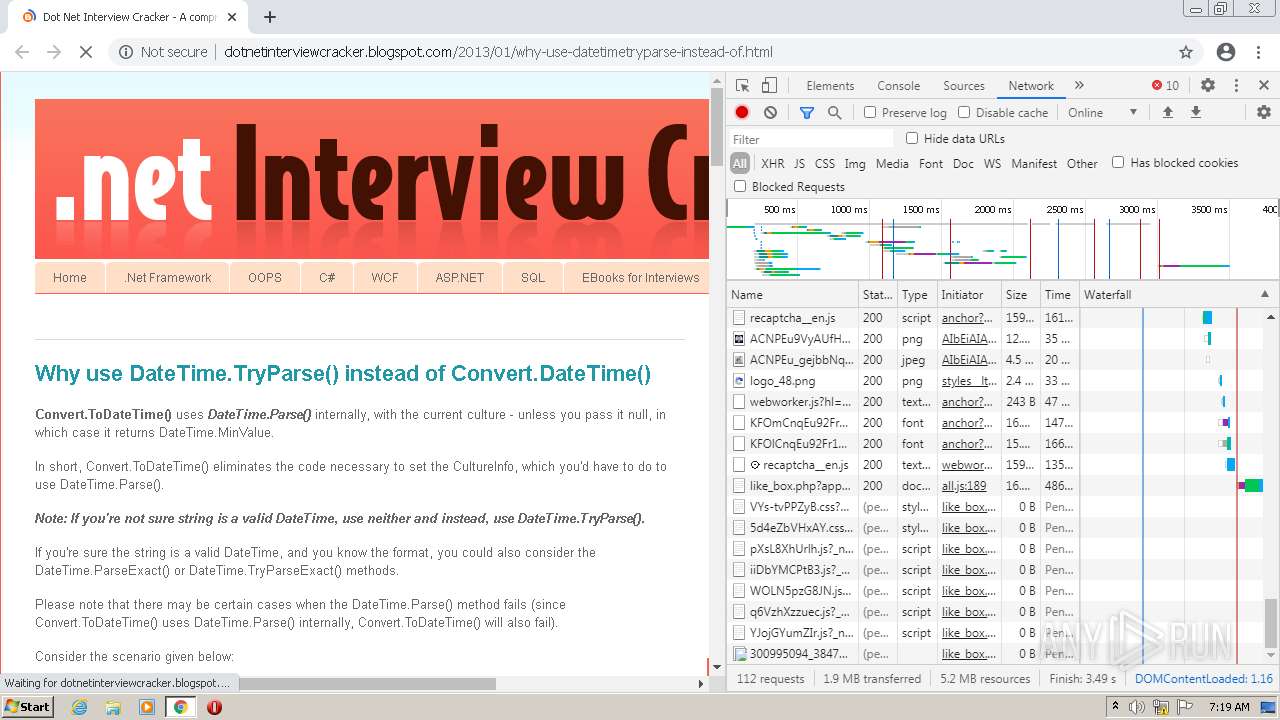
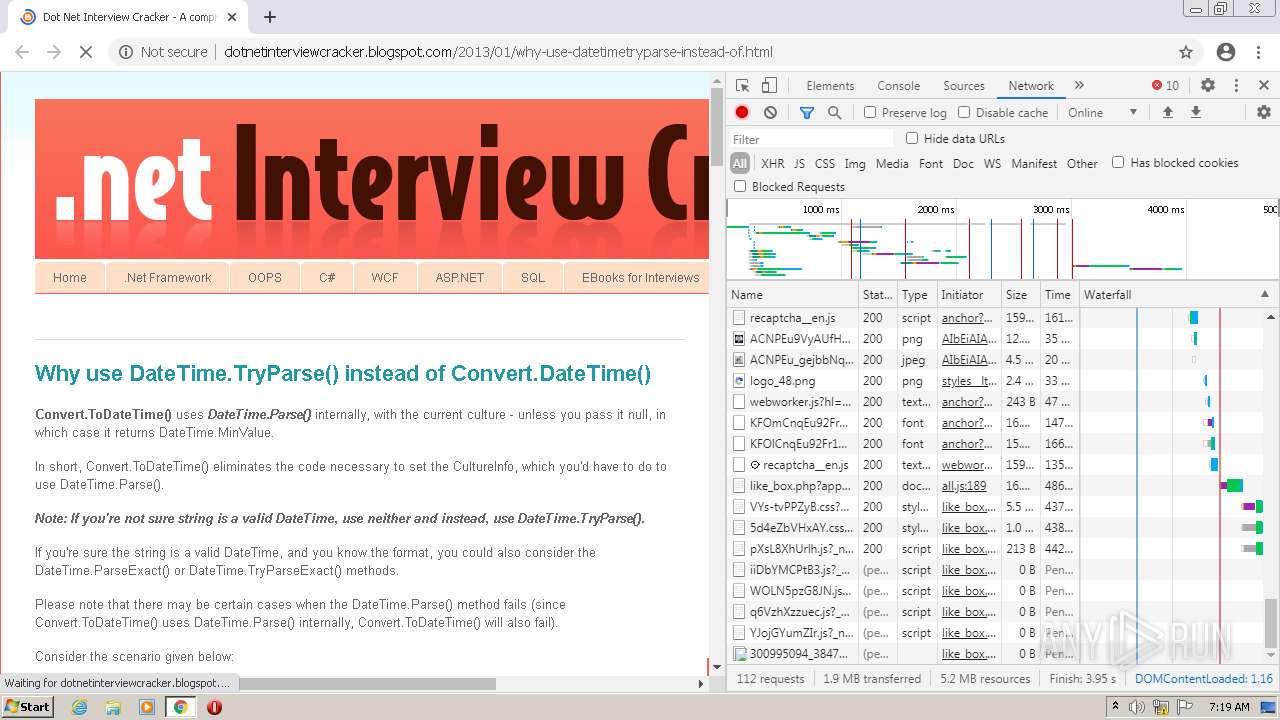
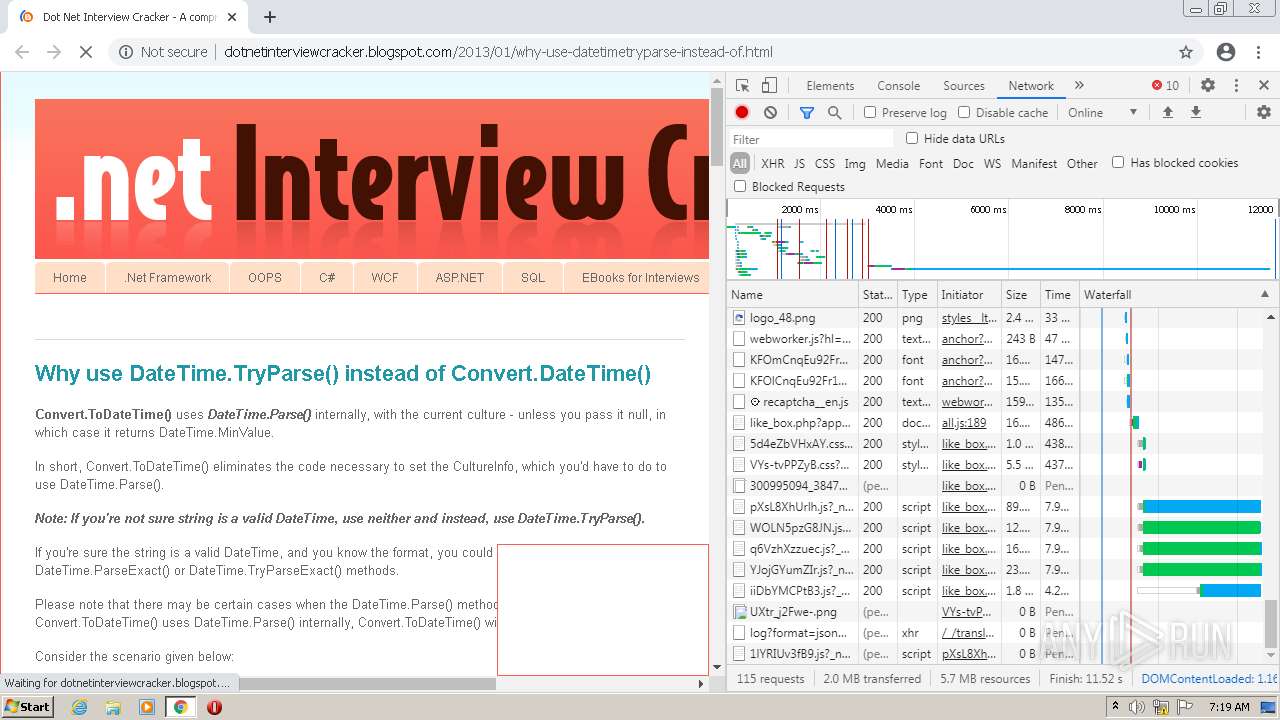
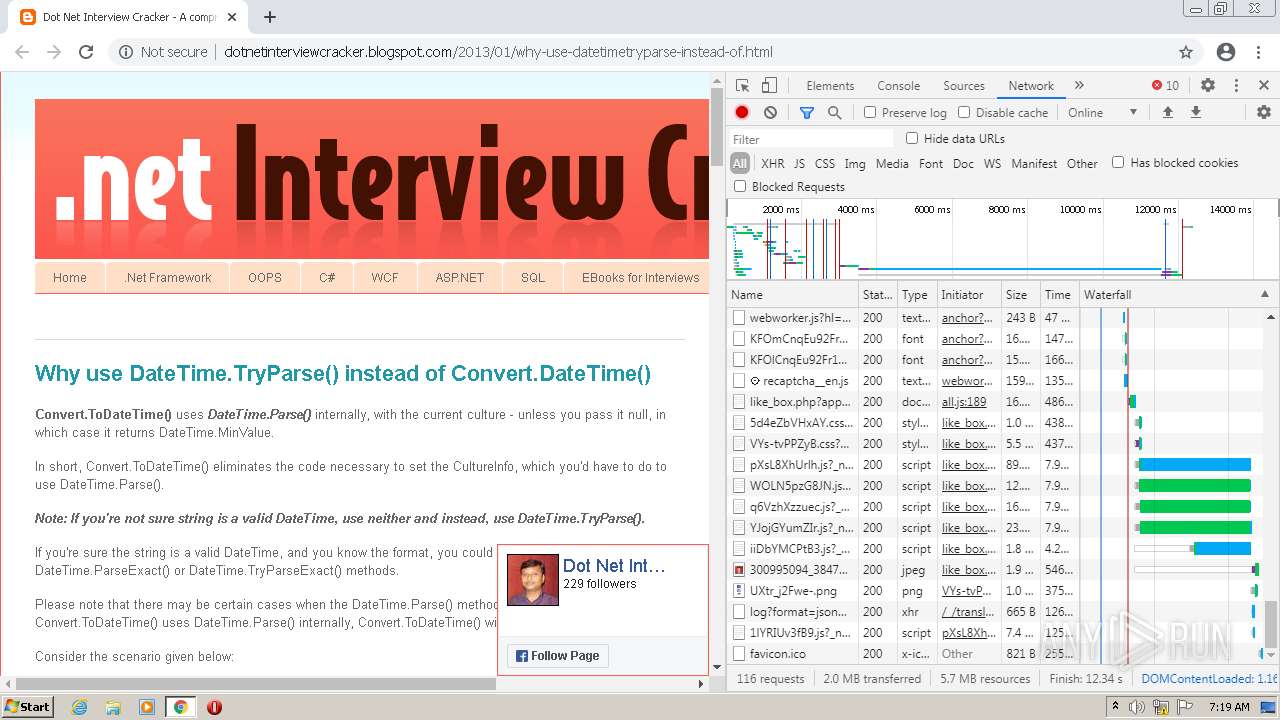
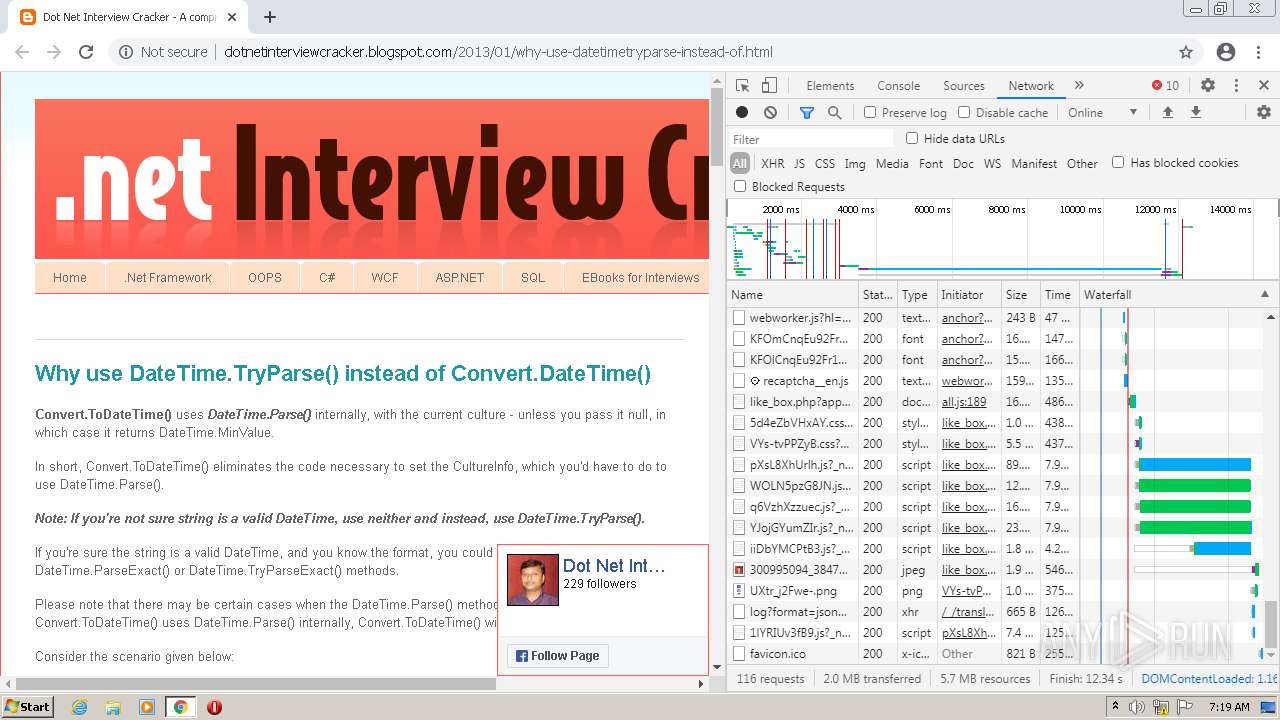
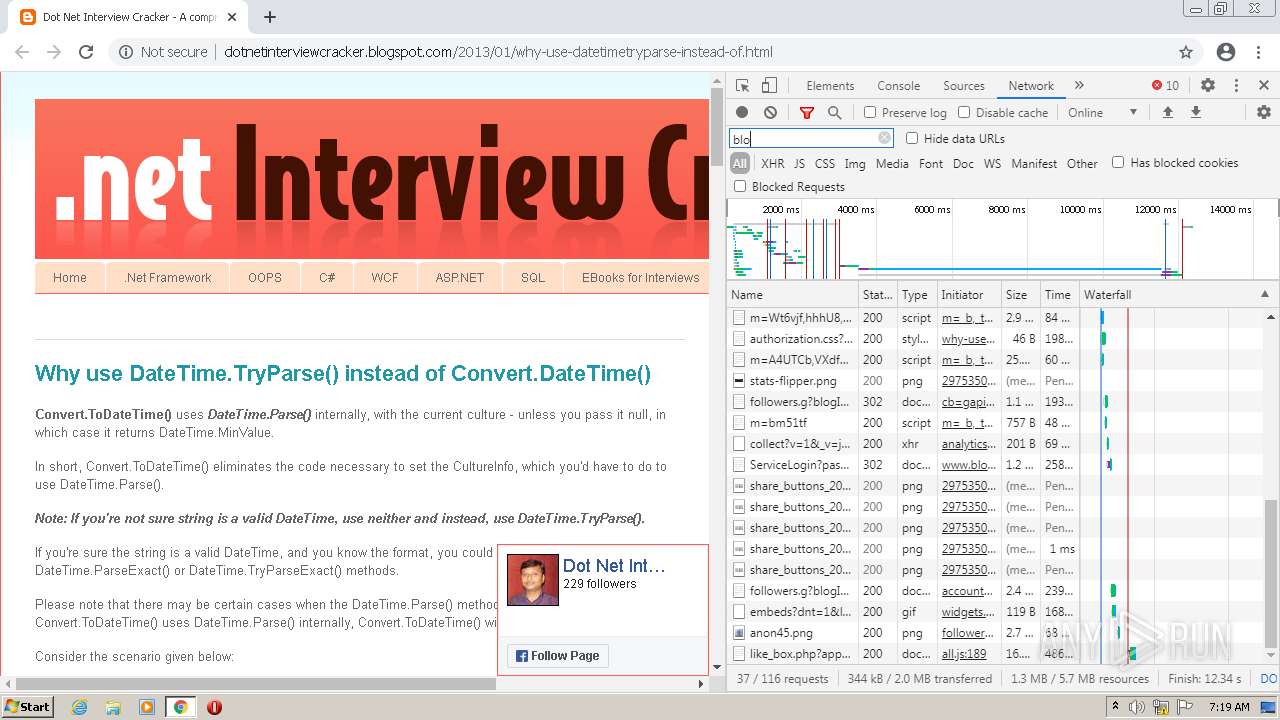
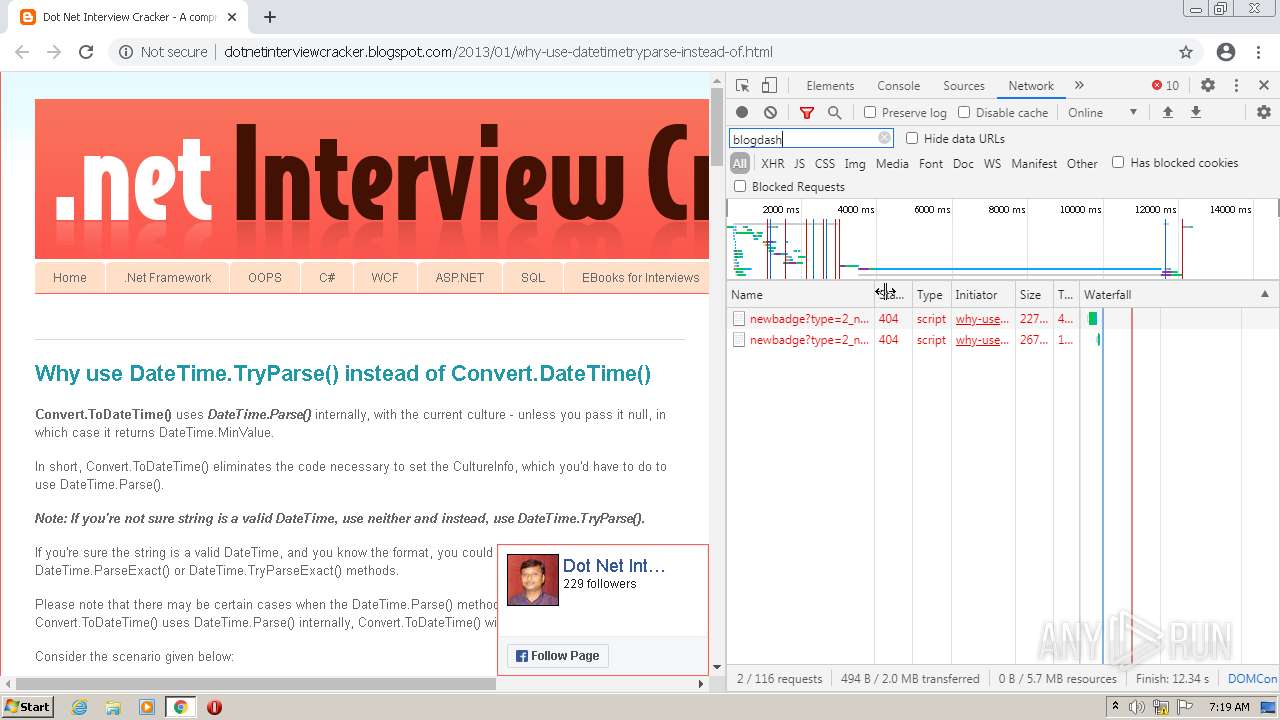
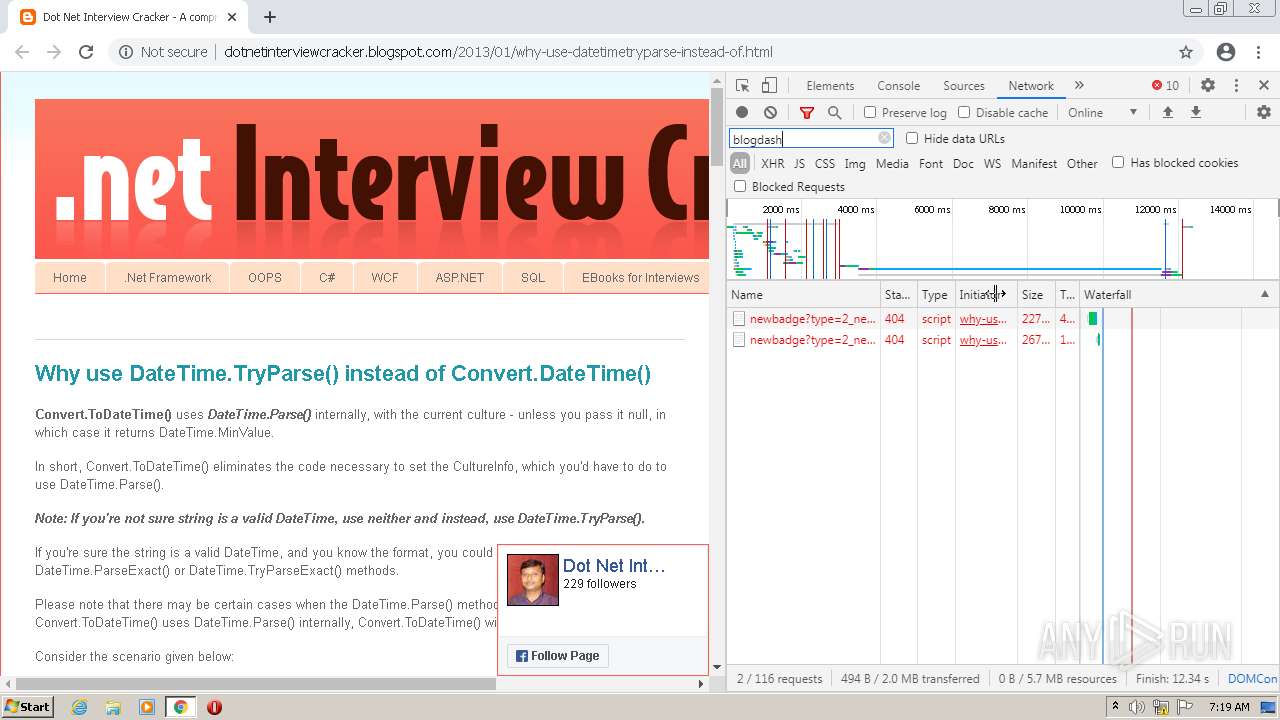
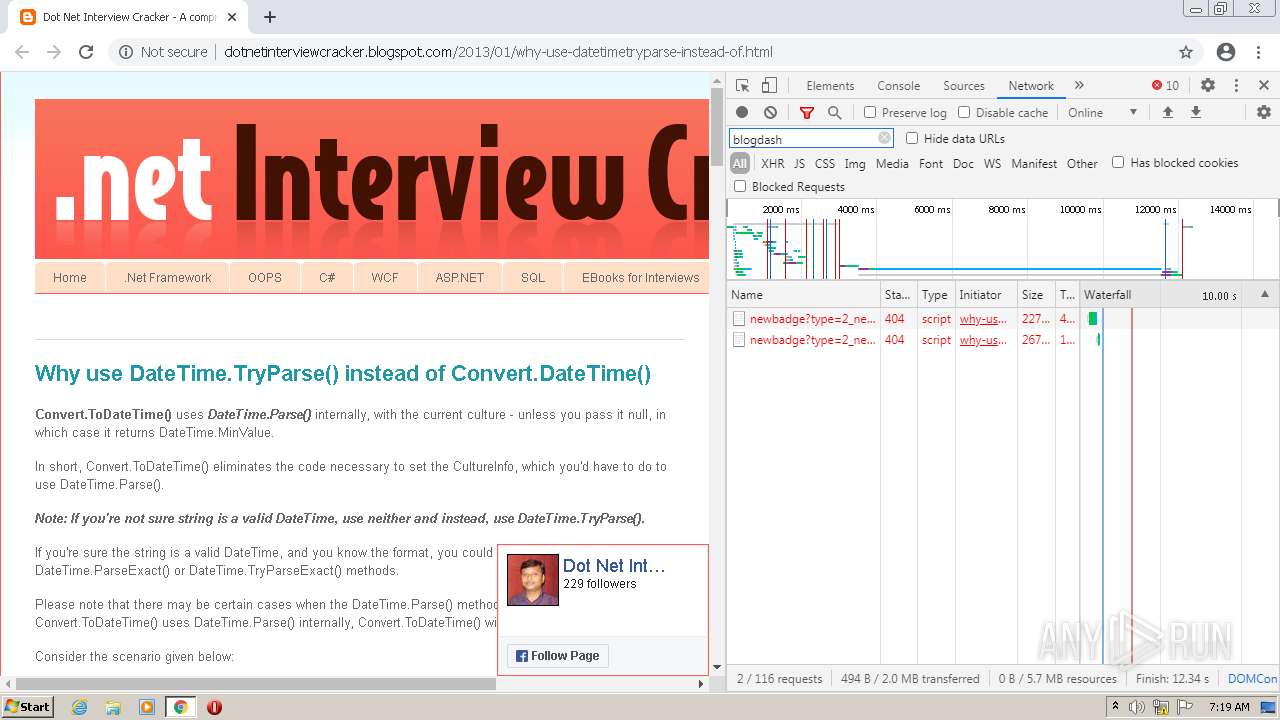
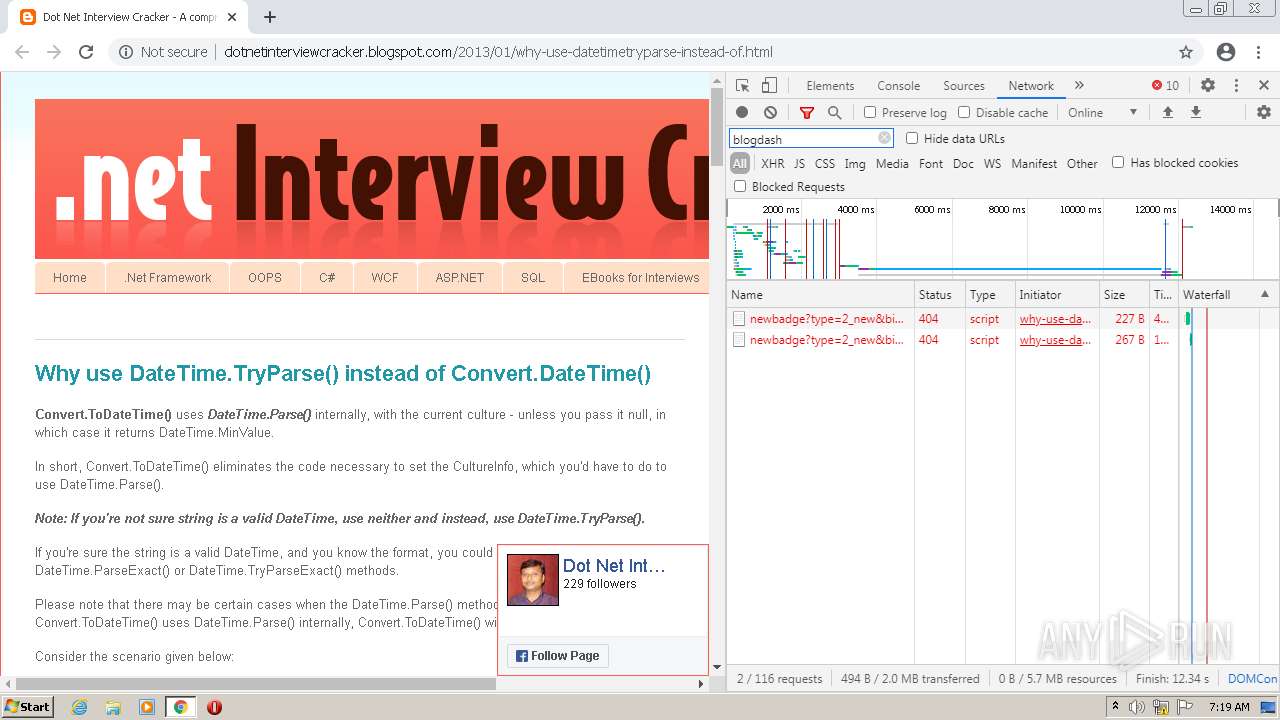
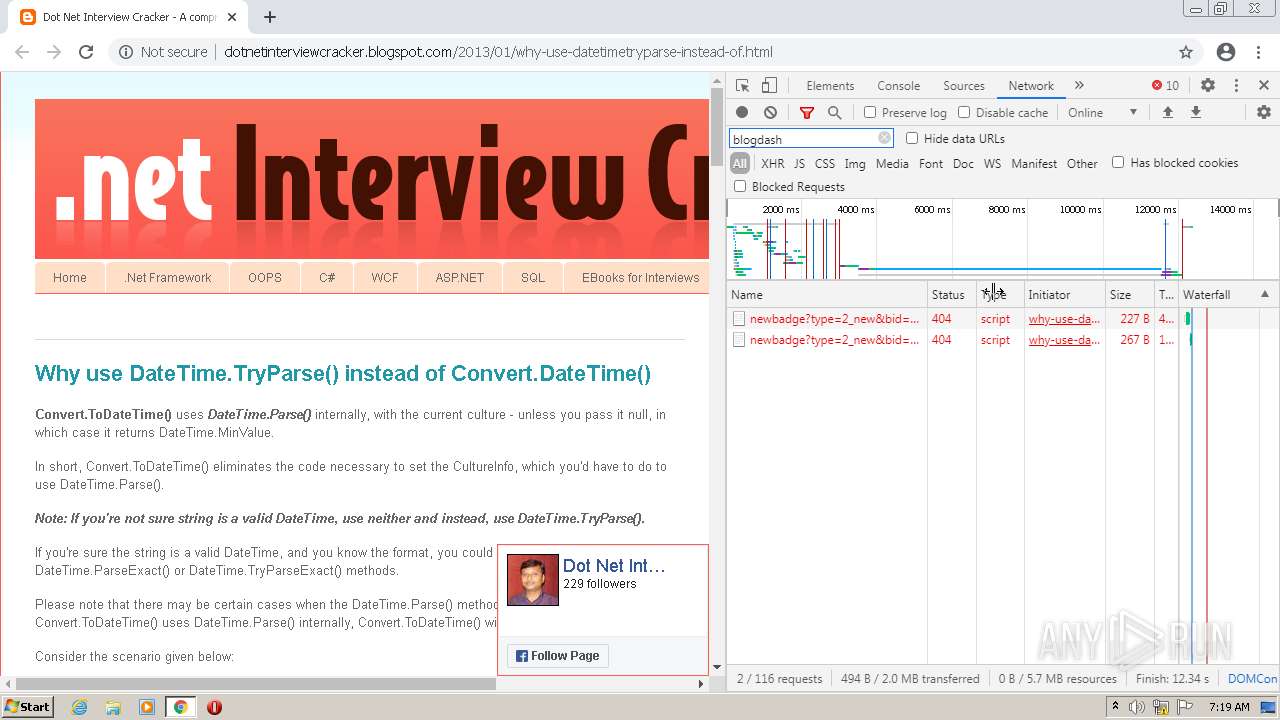
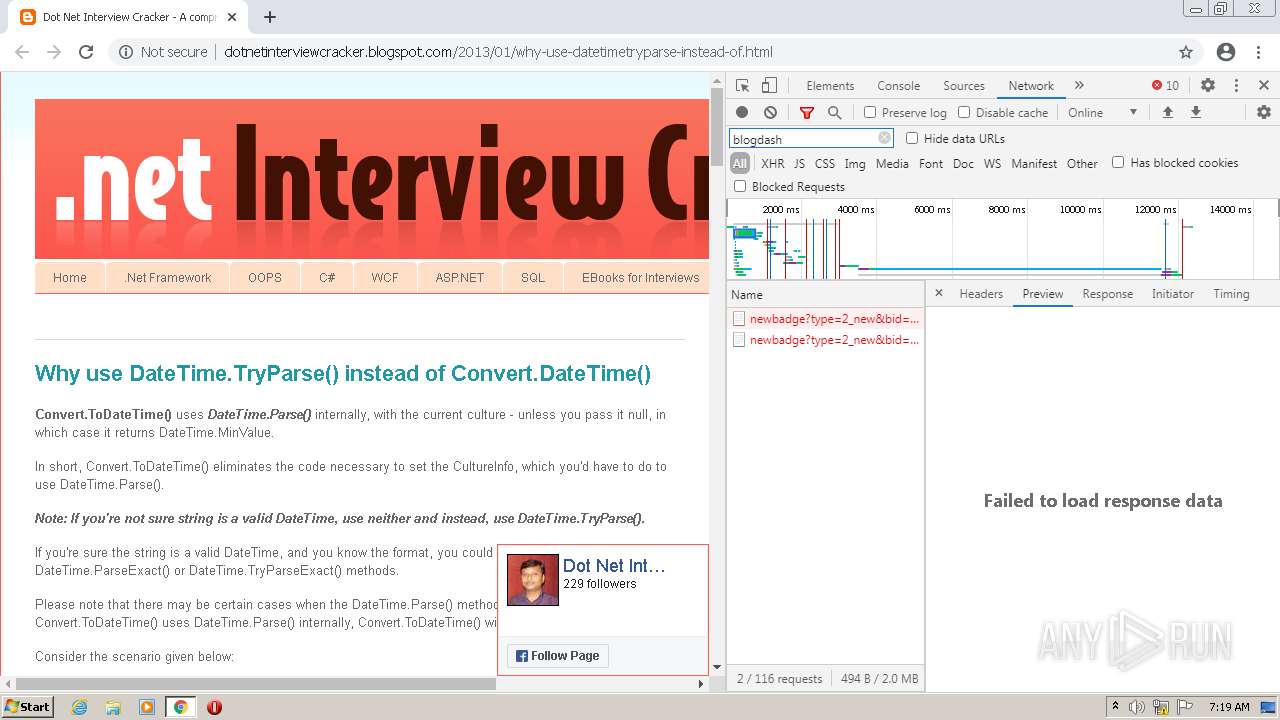
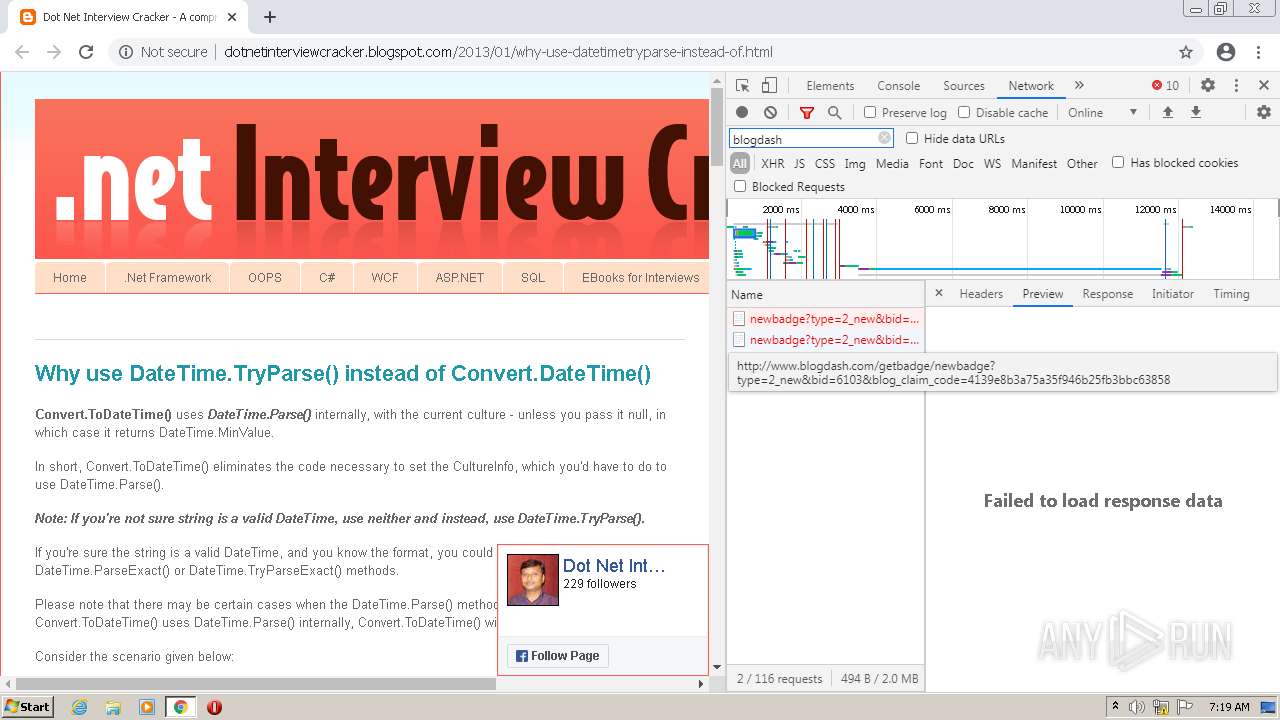
HTTP(S) requests
70
TCP/UDP connections
101
DNS requests
54
Threats
0
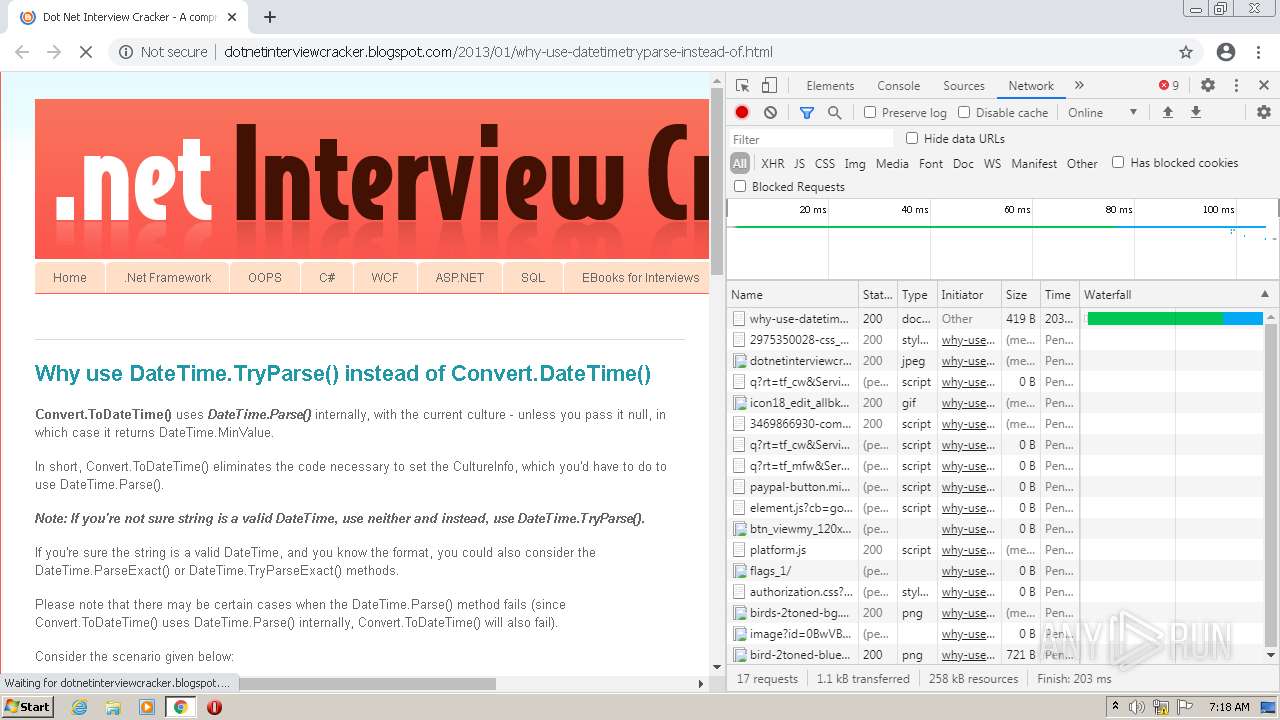
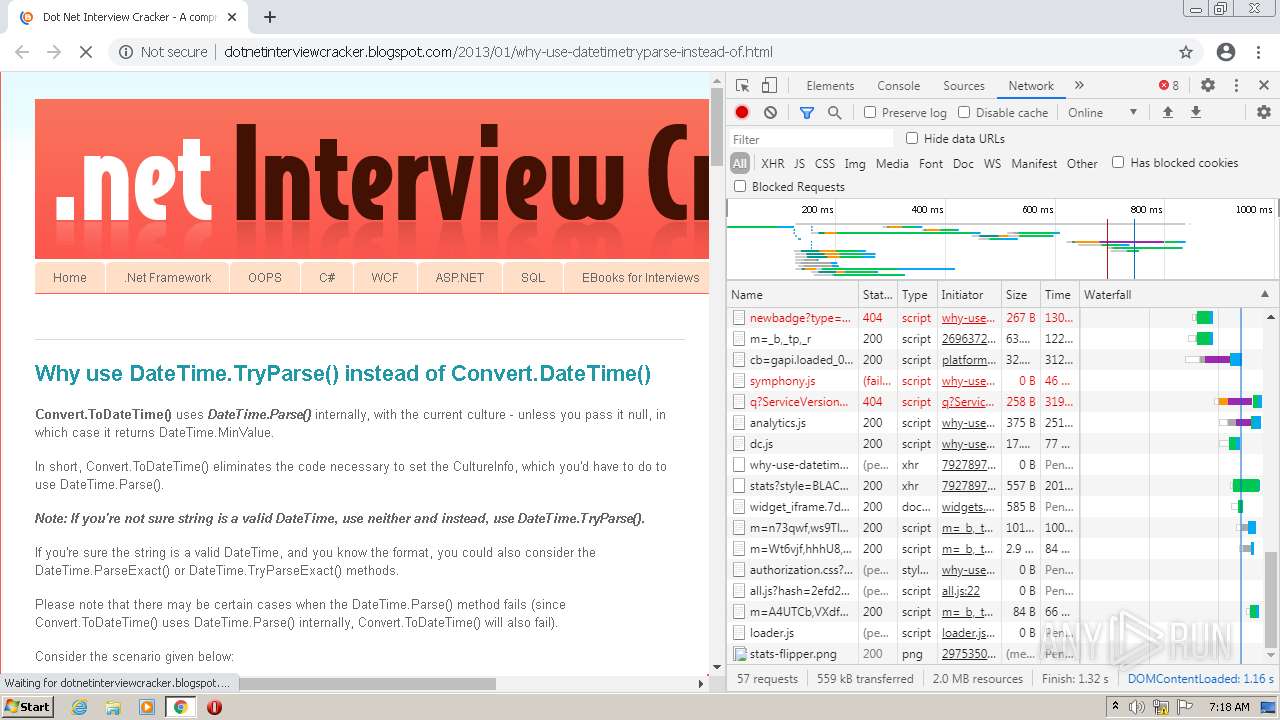
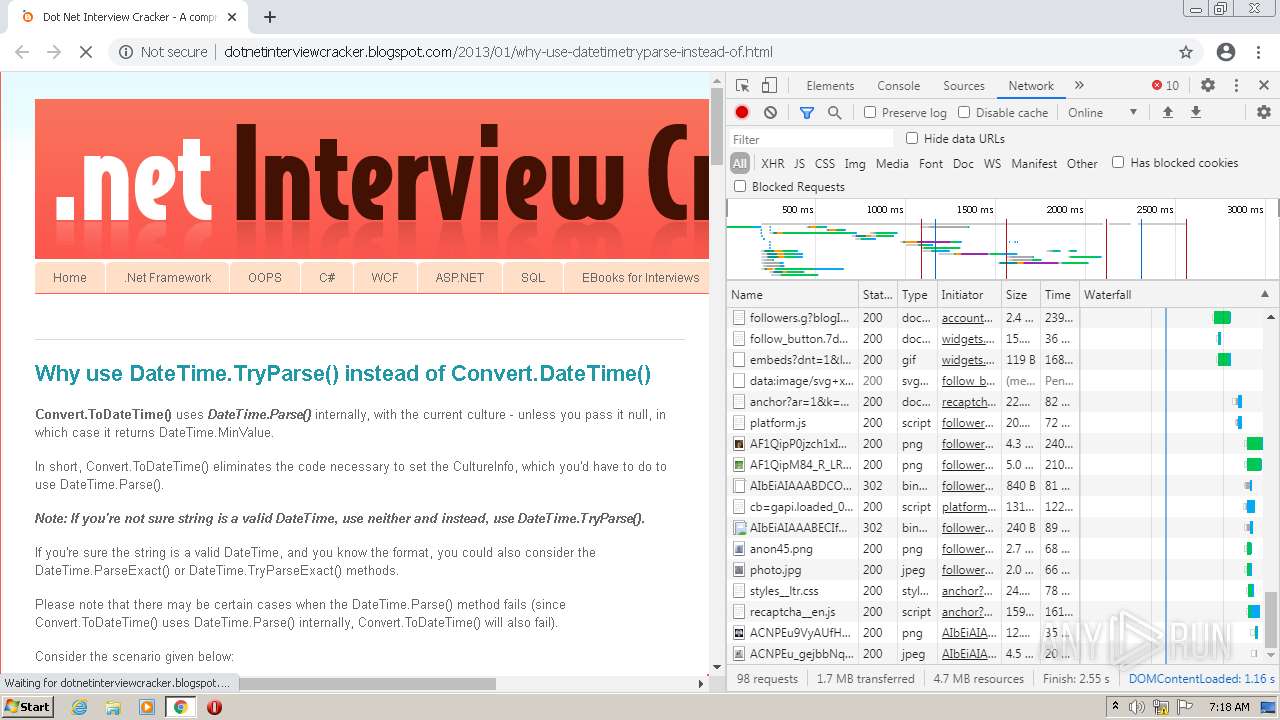
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3660 | chrome.exe | GET | 301 | 216.58.212.174:80 | http://translate.google.com/translate_a/element.js?cb=googleTranslateElementInit | US | — | — | whitelisted |
3660 | chrome.exe | GET | 301 | 13.107.42.14:80 | http://www.linkedin.com/img/webpromo/btn_viewmy_120x33.png | US | — | — | whitelisted |
3660 | chrome.exe | GET | 301 | 142.250.185.129:80 | http://themes.googleusercontent.com/image?id=0BwVBOzw_-hbMNjViMzQ0ZDEtMWU1NS00ZTBkLWFjY2EtZjM5YmU4OTA2MjBm | US | — | — | whitelisted |
3660 | chrome.exe | GET | 200 | 142.250.186.33:80 | http://dotnetinterviewcracker.blogspot.com/2013/01/why-use-datetimetryparse-instead-of.html | US | html | 18.4 Kb | suspicious |
3660 | chrome.exe | GET | 200 | 142.250.186.161:80 | http://1.bp.blogspot.com/-SZsBNL9O-c0/UJyV9EfOasI/AAAAAAAAATs/K2pX3zvZAV4/s929/dotnetinterviewcracker.jpg | US | image | 63.5 Kb | whitelisted |
3660 | chrome.exe | GET | 200 | 13.224.191.177:80 | http://z-in.amazon-adsystem.com/widgets/q?ServiceVersion=20070822&Operation=GetScript&ID=OneJS&WS=1&MarketPlace=IN | US | text | 7.80 Kb | unknown |
3660 | chrome.exe | GET | 200 | 66.154.110.218:80 | http://s09.flagcounter.com/count/IM9/bg_FFFFFF/txt_000000/border_CCCCCC/columns_3/maxflags_248/viewers_0/labels_1/pageviews_0/flags_1/ | US | image | 73.3 Kb | suspicious |
3660 | chrome.exe | GET | 200 | 88.99.85.235:80 | http://api.qrserver.com/v1/create-qr-code/?data=http%3A%2F%2Fdotnetinterviewcracker.blogspot.com&size=260x260&qzone=1&bgcolor=FA5B52&prov=goqrme | DE | image | 561 b | unknown |
3660 | chrome.exe | GET | 200 | 93.184.220.66:80 | http://platform.twitter.com/widgets.js | US | text | 28.5 Kb | whitelisted |
3660 | chrome.exe | GET | 200 | 172.217.16.201:80 | http://www.blogblog.com/1kt/ethereal/birds-2toned-bg.png | US | image | 486 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
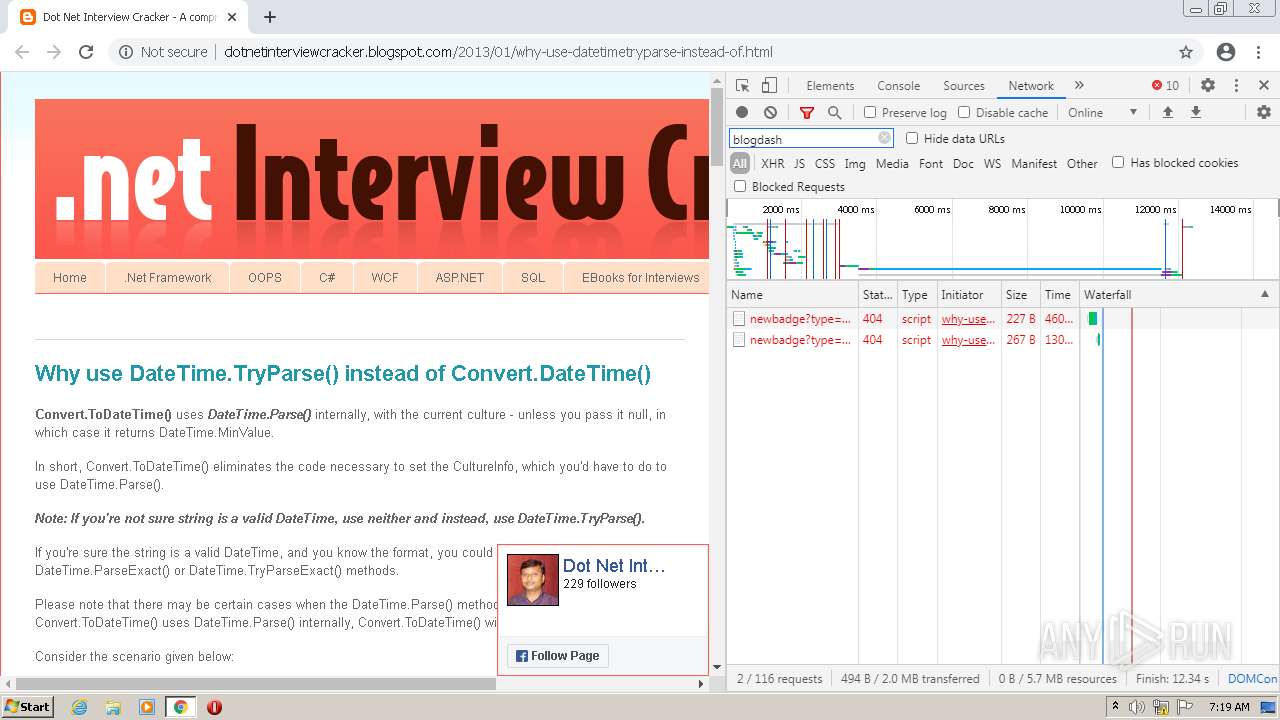
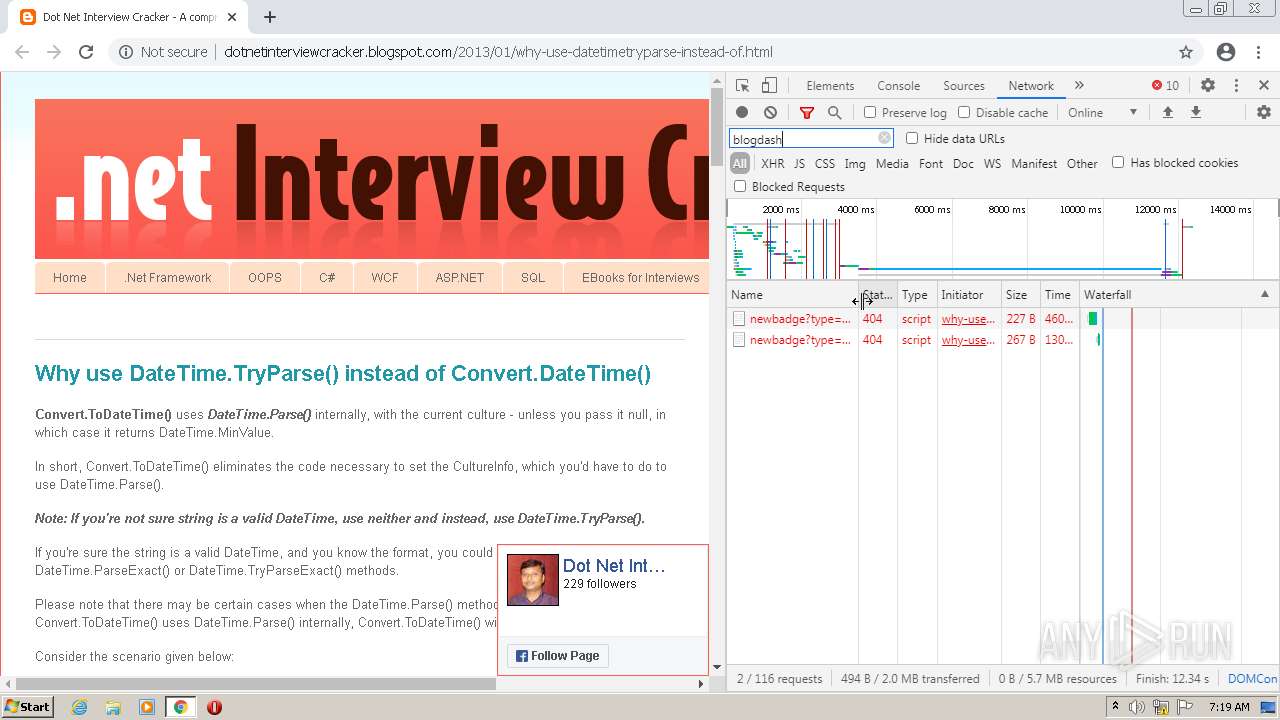
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3660 | chrome.exe | 142.250.186.110:443 | clients2.google.com | GOOGLE | US | whitelisted |
3660 | chrome.exe | 142.250.186.33:80 | dotnetinterviewcracker.blogspot.com | GOOGLE | US | whitelisted |
3660 | chrome.exe | 172.217.16.201:443 | www.blogger.com | GOOGLE | US | whitelisted |
3660 | chrome.exe | 142.250.186.161:80 | 1.bp.blogspot.com | GOOGLE | US | whitelisted |
3660 | chrome.exe | 52.95.118.186:80 | ws-in.amazon-adsystem.com | AMAZON-02 | IE | suspicious |
3660 | chrome.exe | 172.217.16.206:443 | apis.google.com | GOOGLE | US | whitelisted |
3660 | chrome.exe | 142.250.185.99:443 | www.gstatic.com | GOOGLE | US | whitelisted |
3660 | chrome.exe | 192.229.221.25:443 | www.paypalobjects.com | EDGECAST | US | suspicious |
3660 | chrome.exe | 216.58.212.174:80 | translate.google.com | GOOGLE | US | whitelisted |
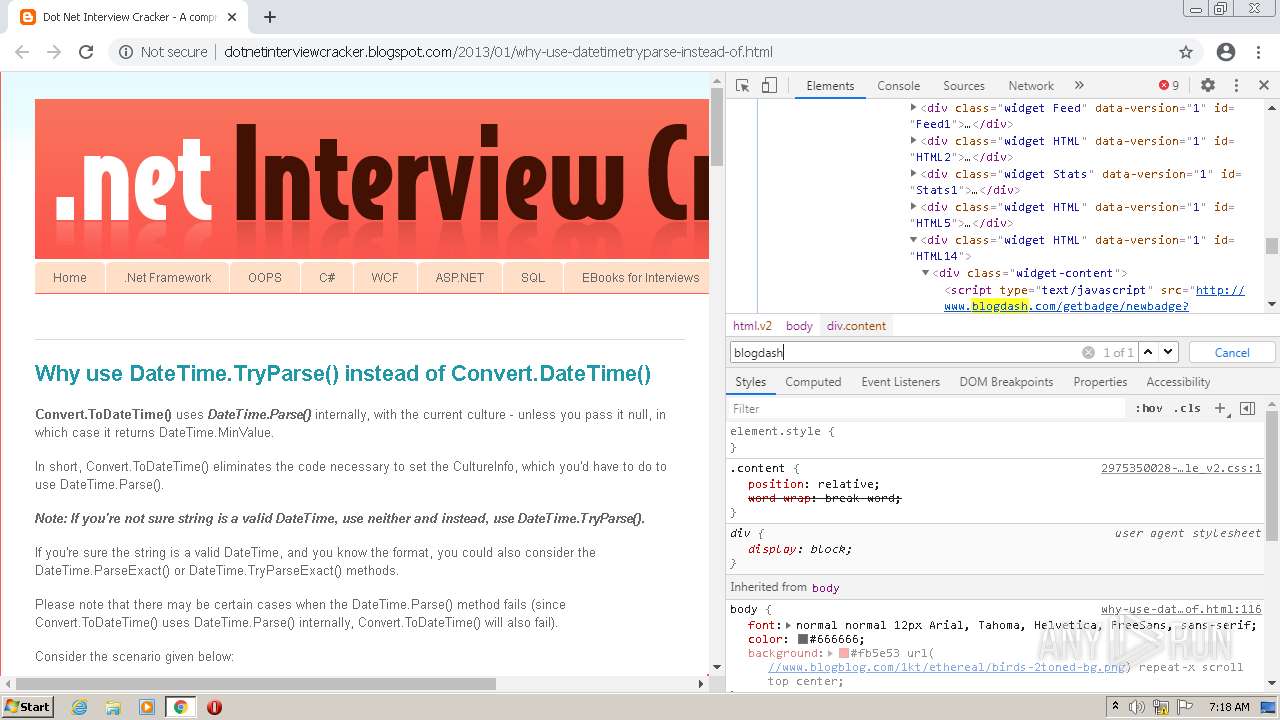
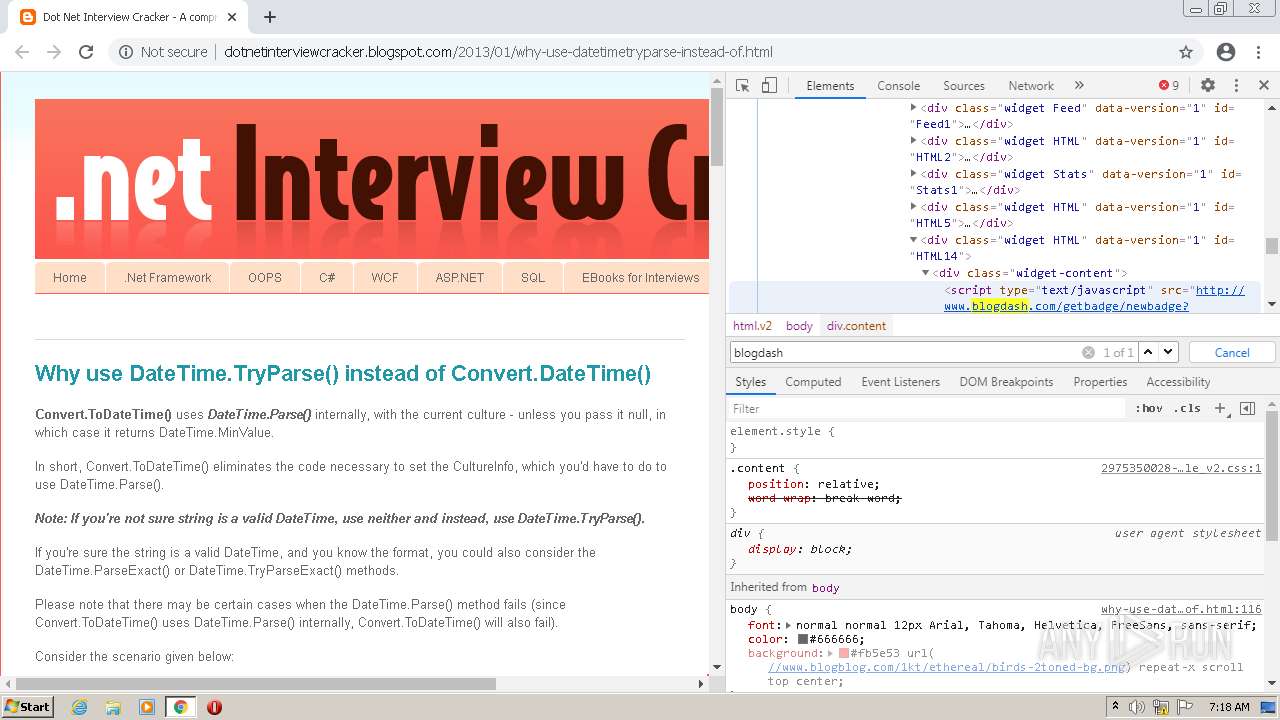
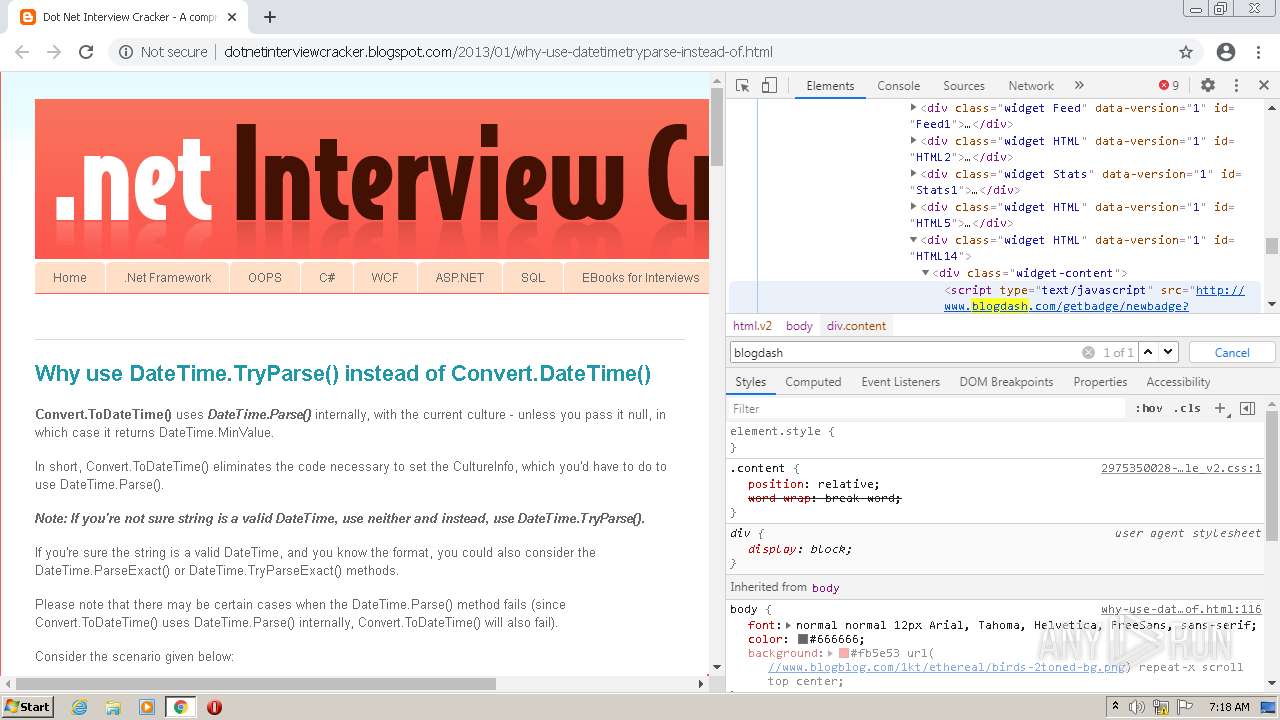
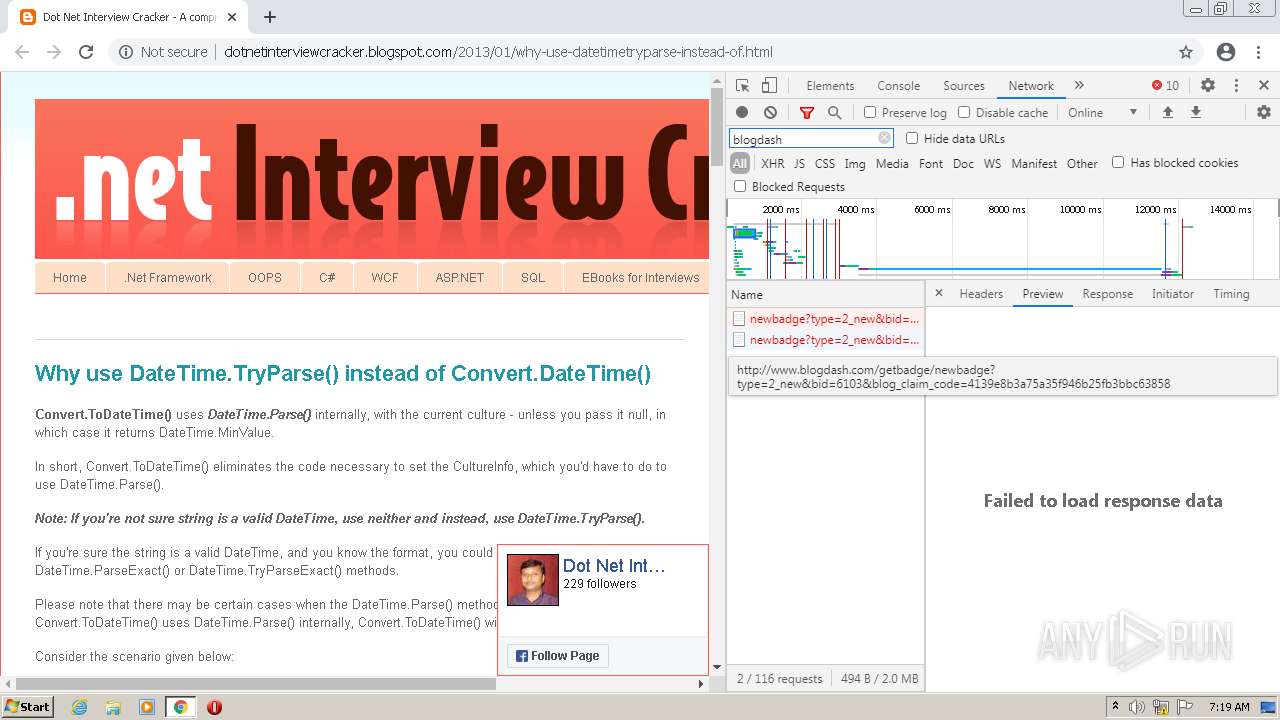
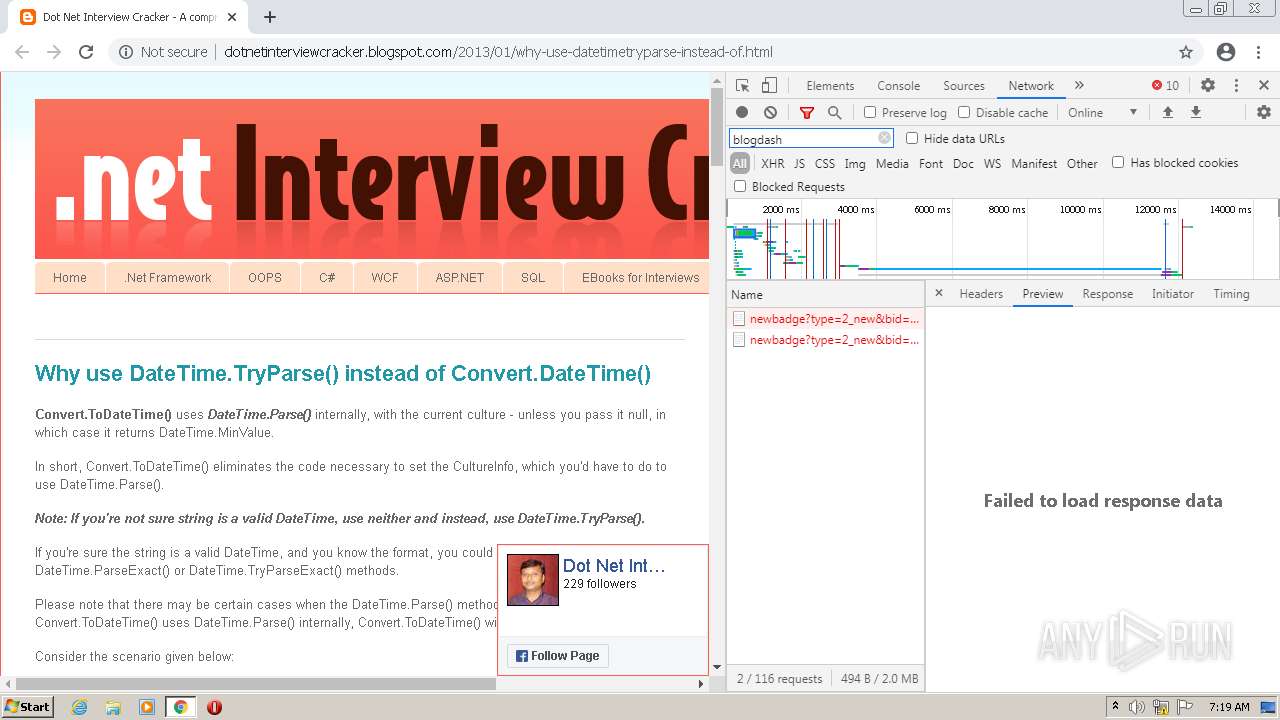
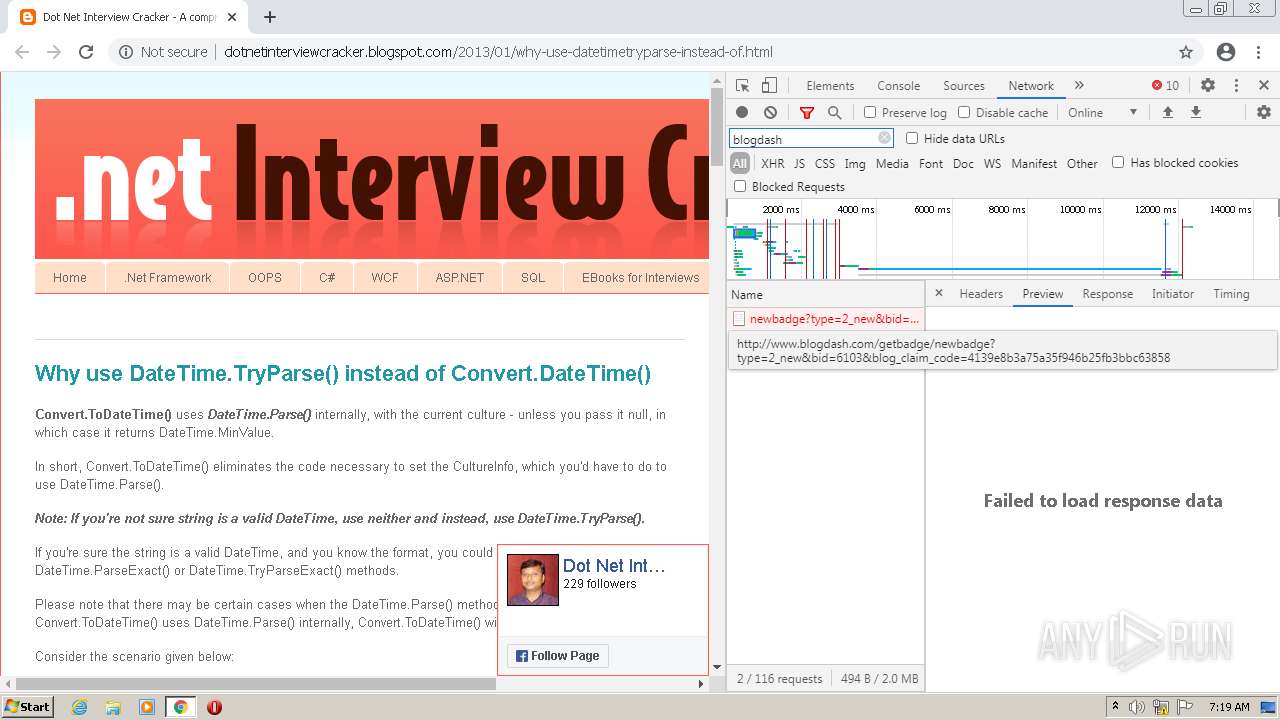
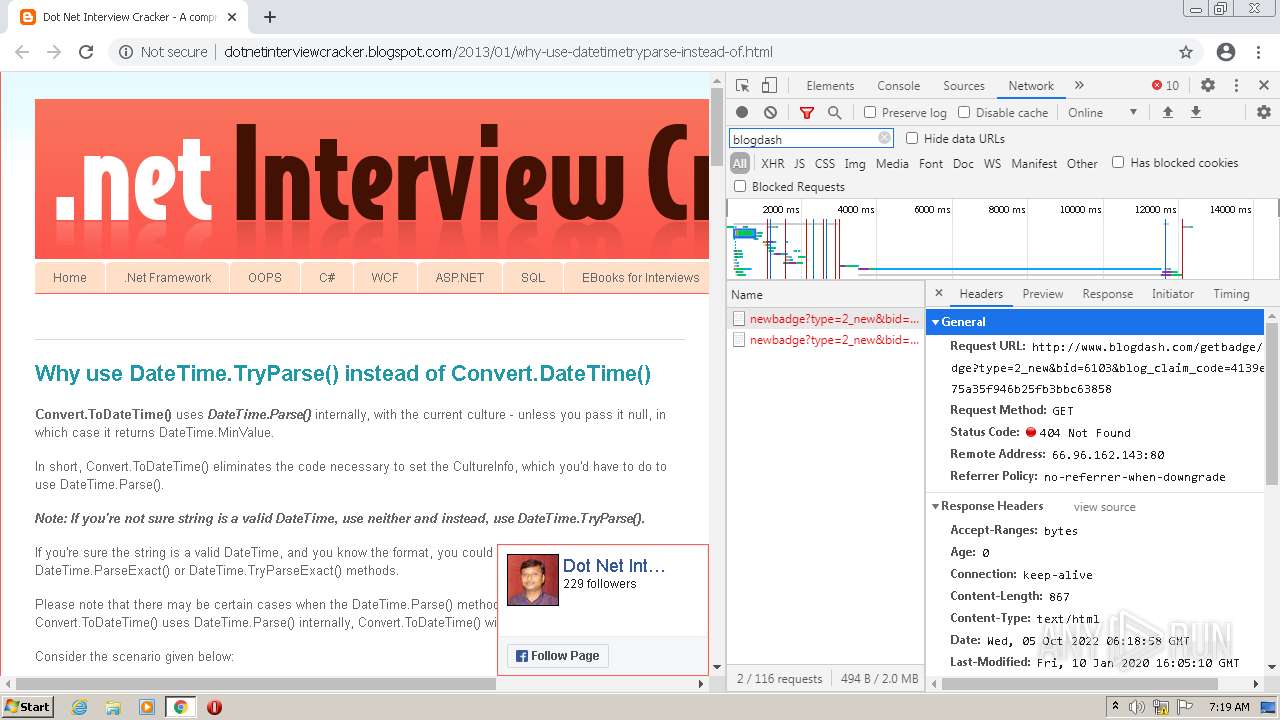
3660 | chrome.exe | 66.96.162.143:80 | www.blogdash.com | BIZLAND-SD | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clients2.google.com |
| whitelisted |
dotnetinterviewcracker.blogspot.com |
| suspicious |
accounts.google.com |
| shared |
www.blogger.com |
| shared |
1.bp.blogspot.com |
| whitelisted |
ws-in.amazon-adsystem.com |
| suspicious |
www.paypalobjects.com |
| whitelisted |
translate.google.com |
| whitelisted |
apis.google.com |
| whitelisted |
www.gstatic.com |
| whitelisted |