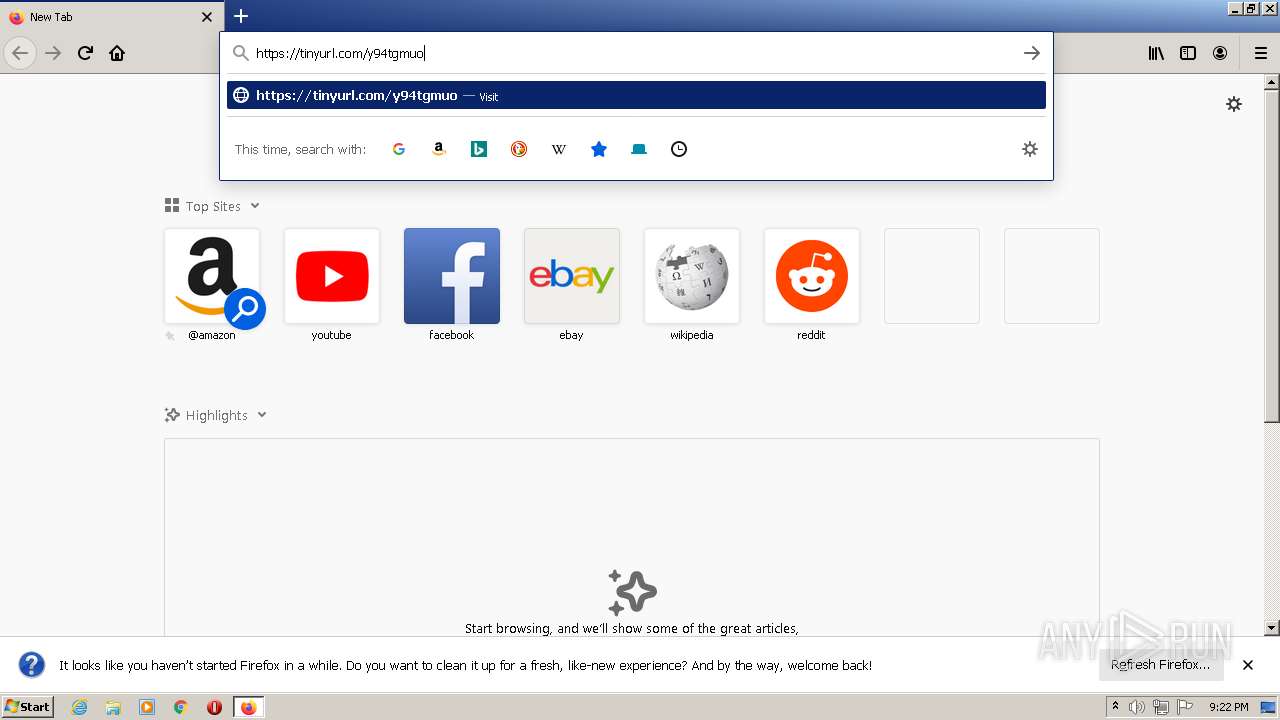
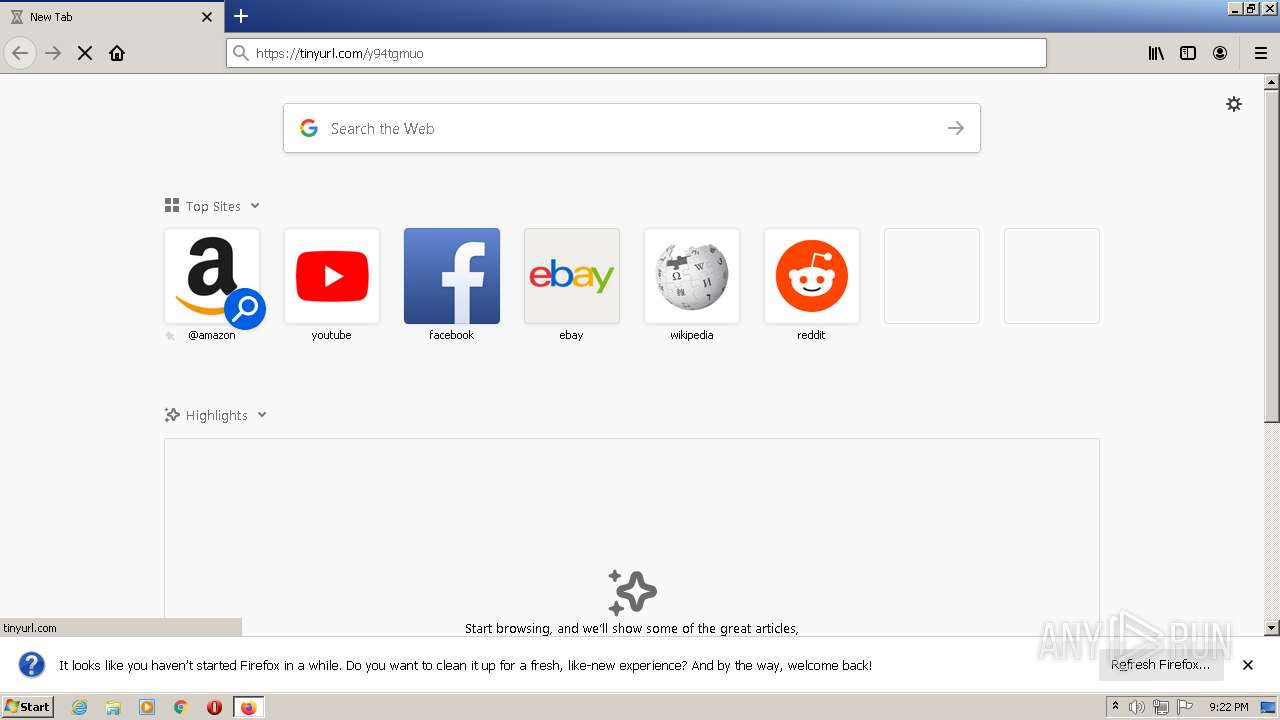
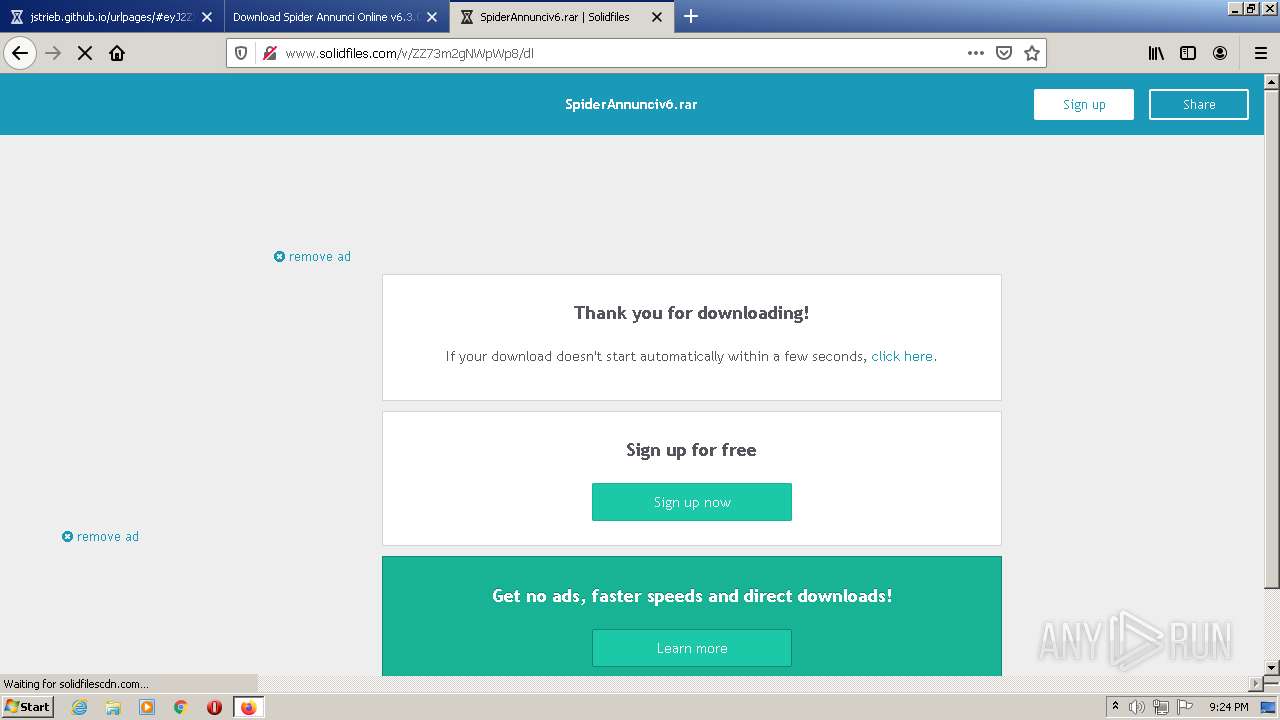
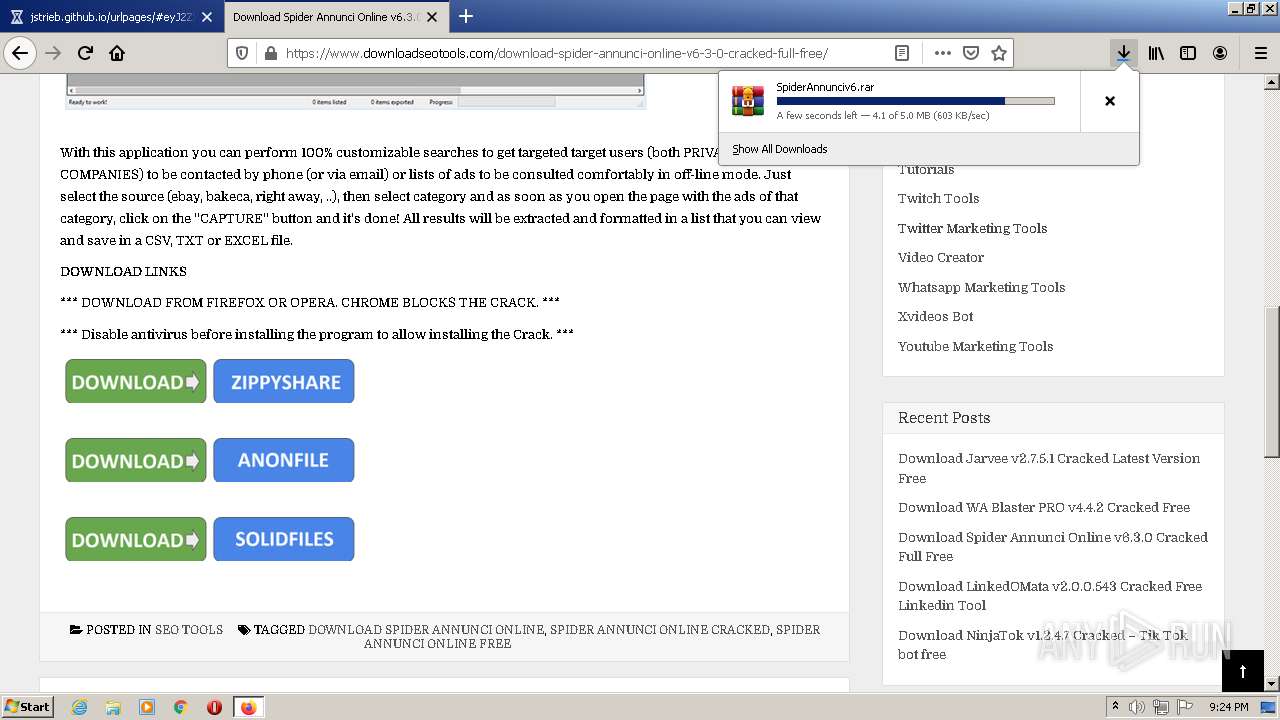
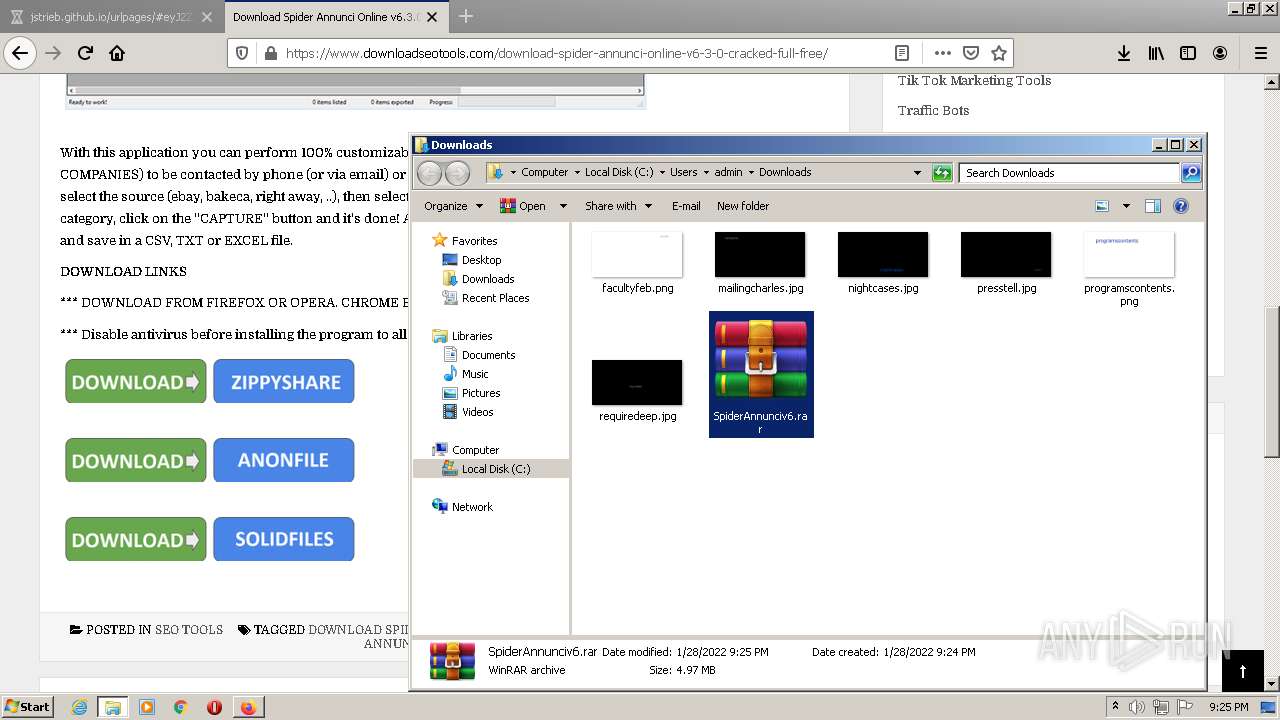
| URL: | https://tinyurl.com/y94tgmuo |
| Full analysis: | https://app.any.run/tasks/5e83bede-b862-4cd7-adc2-8770875063e7 |
| Verdict: | Malicious activity |
| Analysis date: | January 28, 2022, 21:22:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | F2E992005E0A8A51C71CDE4891028222 |
| SHA1: | 4F7E0F36DDB06B1EE7A820A7F8112B21B502CDDE |
| SHA256: | 415EEE619F306D6FD53286F62043903BF22603A0ABA4CE58982B650B2B5BA6EC |
| SSDEEP: | 3:N8EzLdIHb4:2Endsb4 |
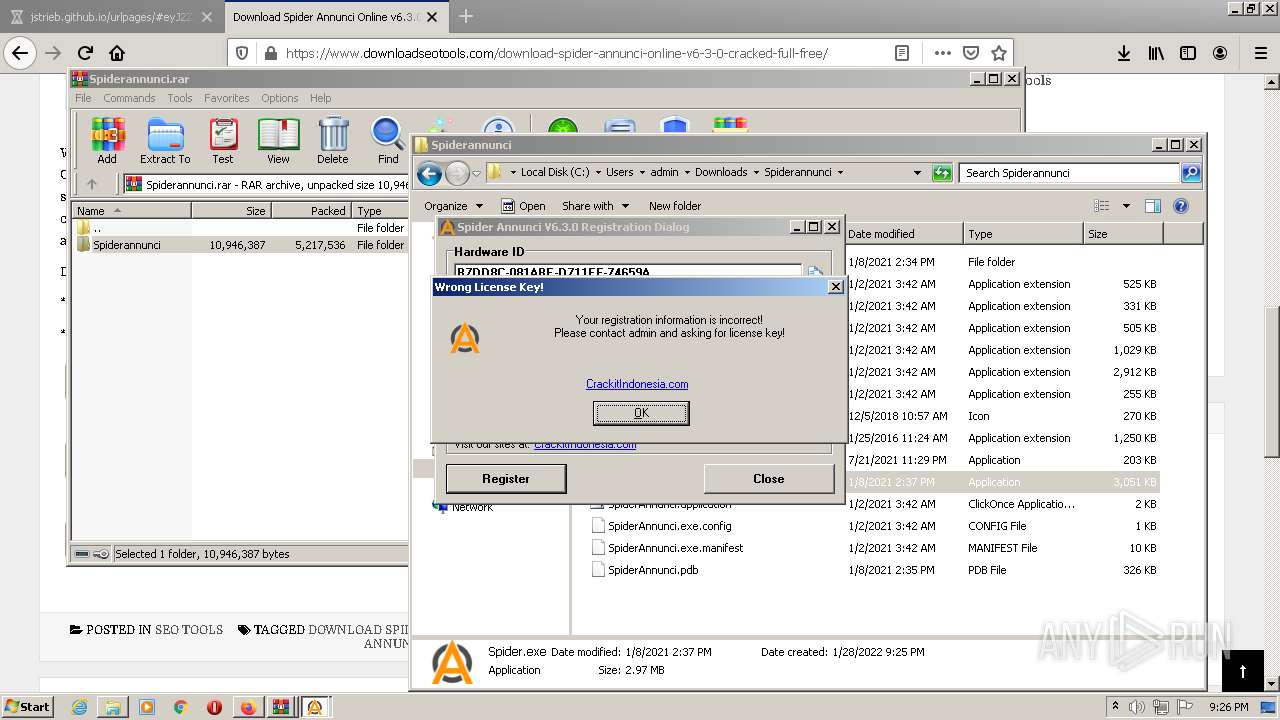
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 2836)
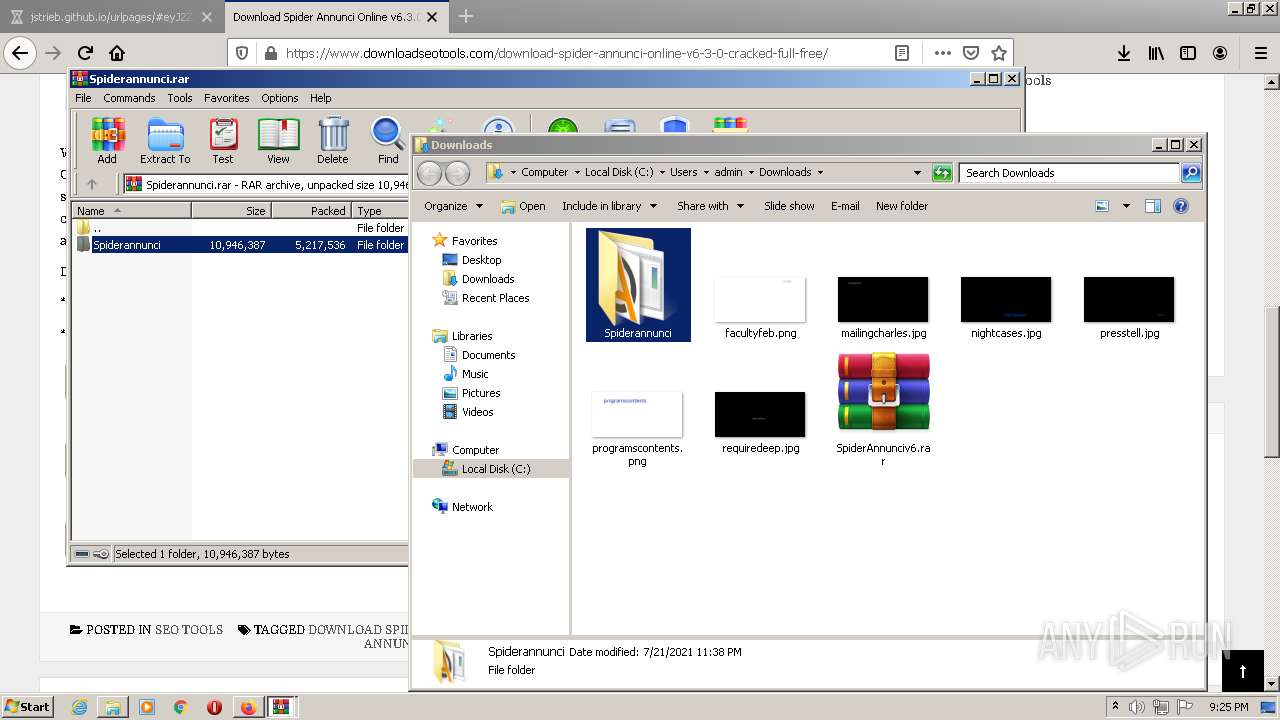
Application was dropped or rewritten from another process
- Spider.exe (PID: 1872)
- Spider.exe (PID: 1760)
SUSPICIOUS
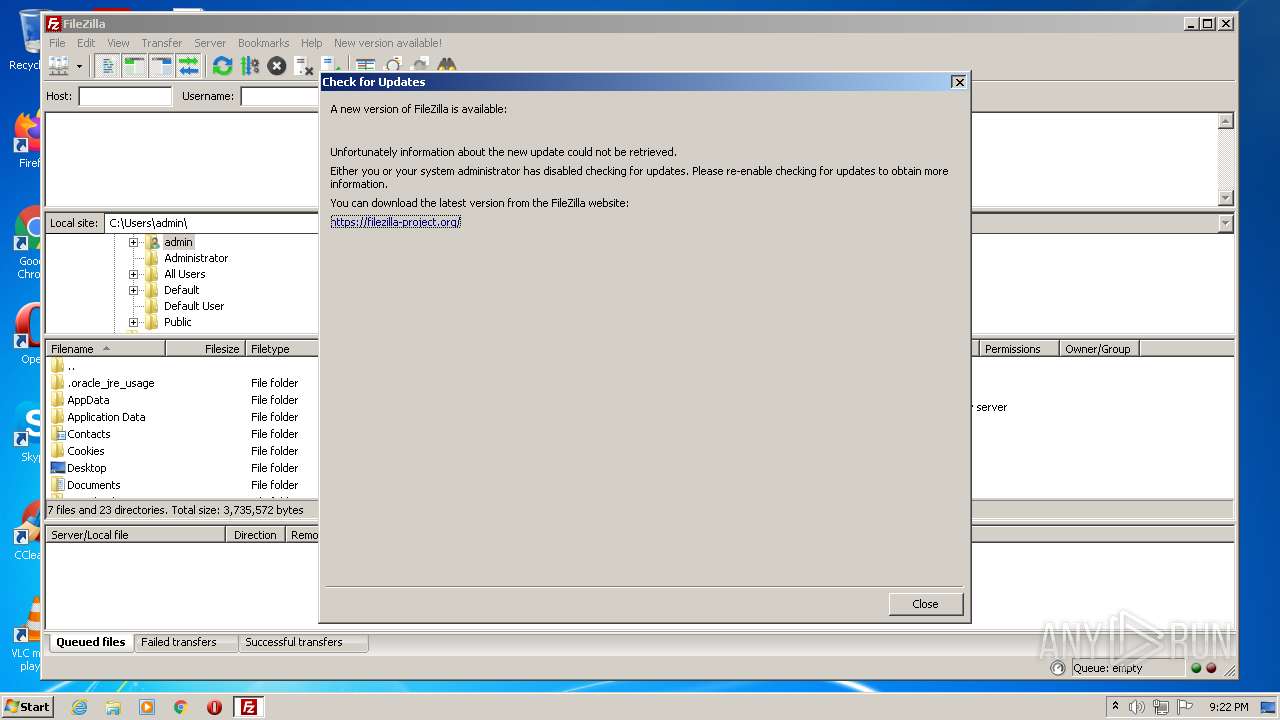
Creates files in the user directory
- filezilla.exe (PID: 1600)
Reads the computer name
- filezilla.exe (PID: 1600)
- WinRAR.exe (PID: 4012)
- WinRAR.exe (PID: 2792)
- Spider.exe (PID: 1872)
- Spider.exe (PID: 1760)
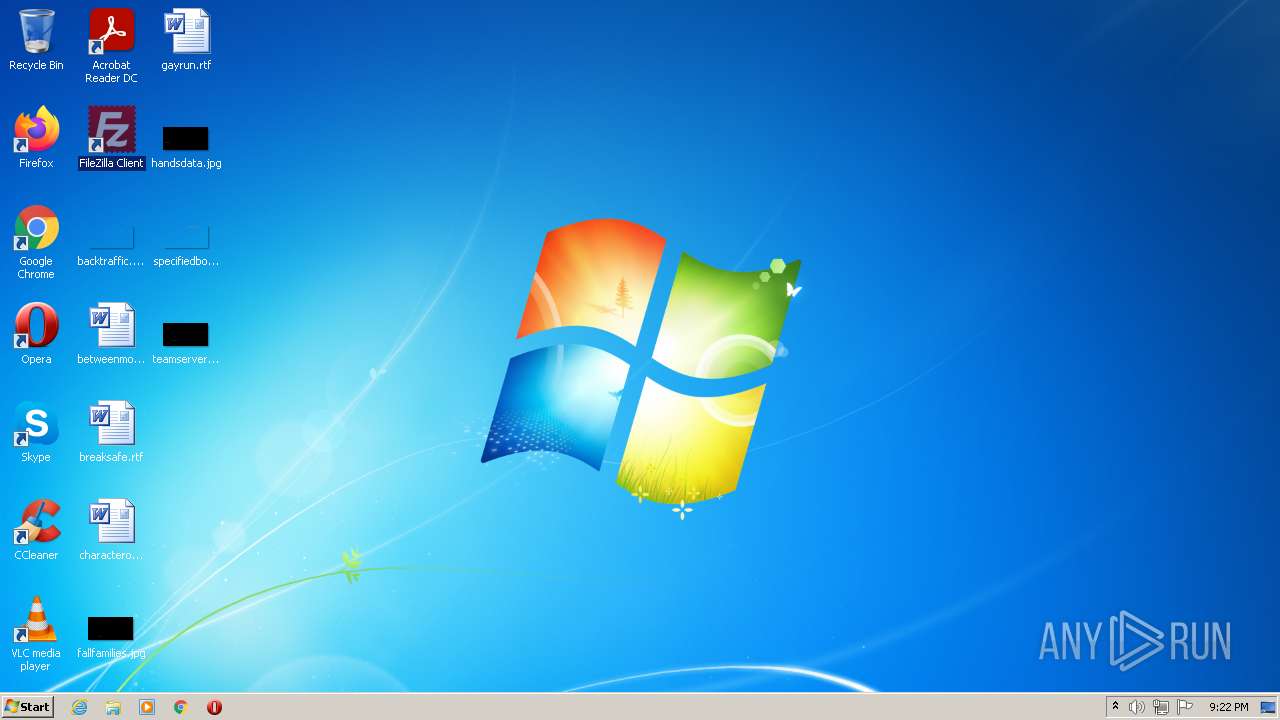
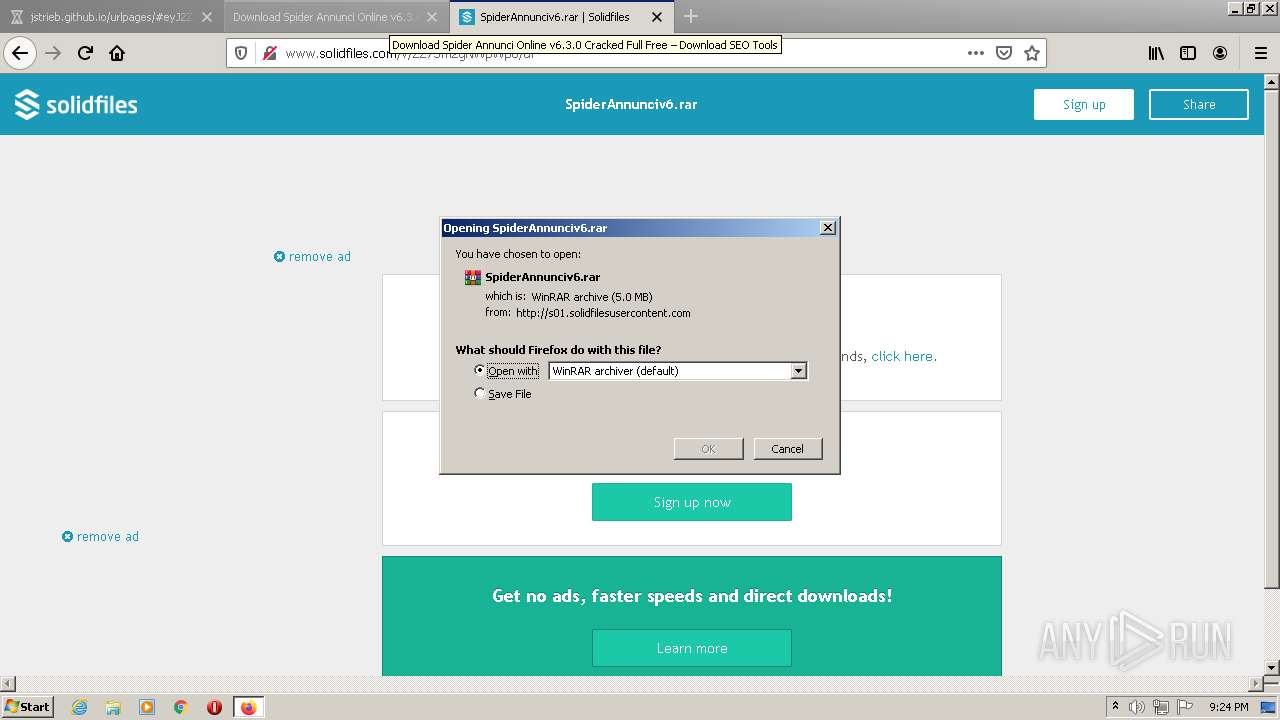
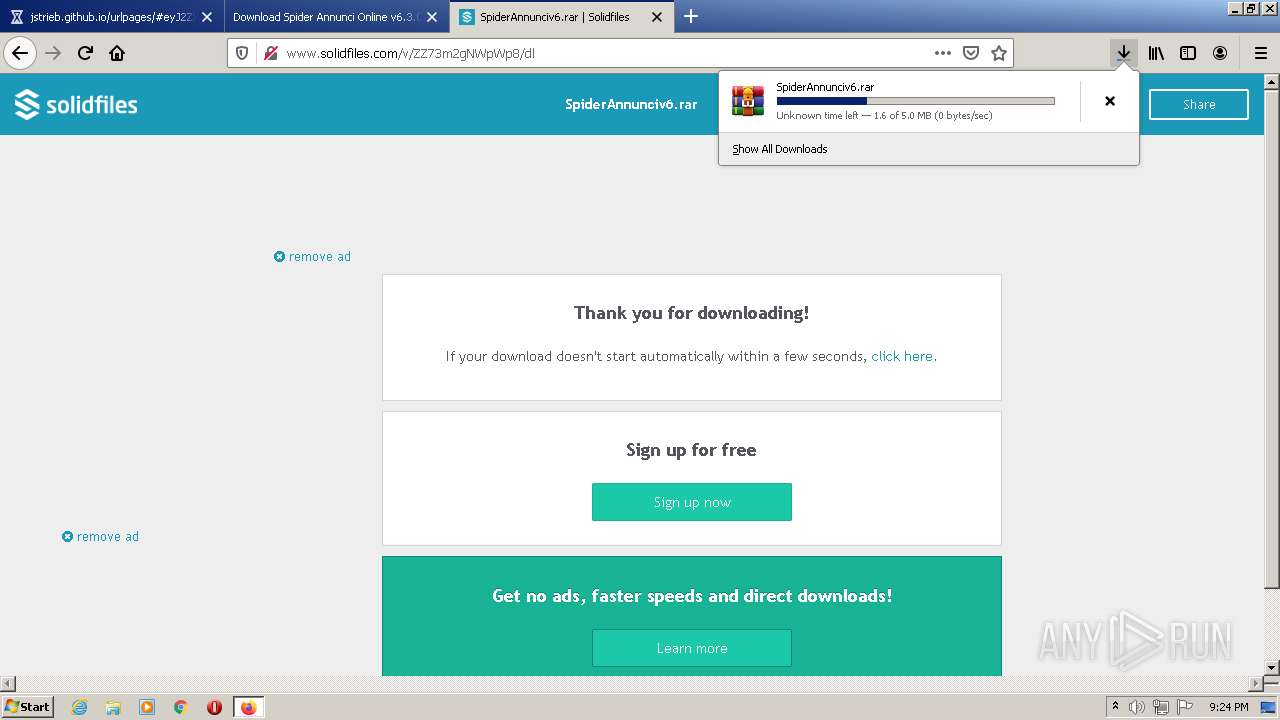
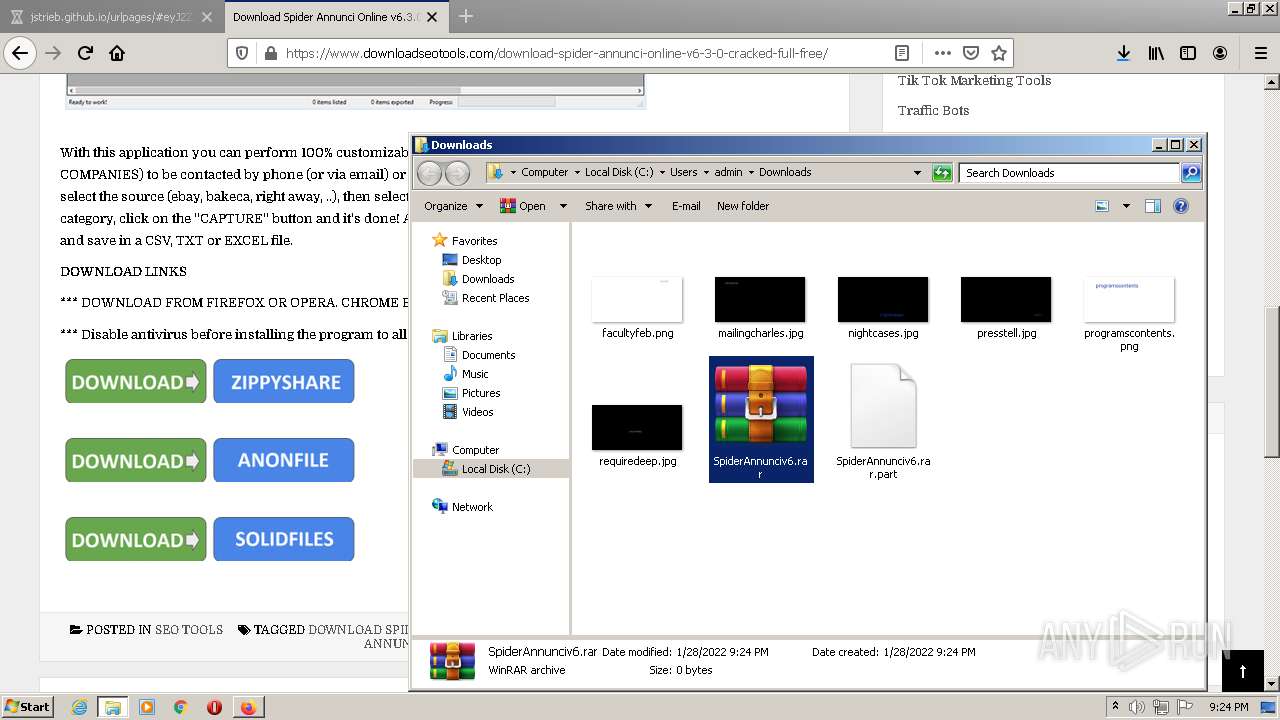
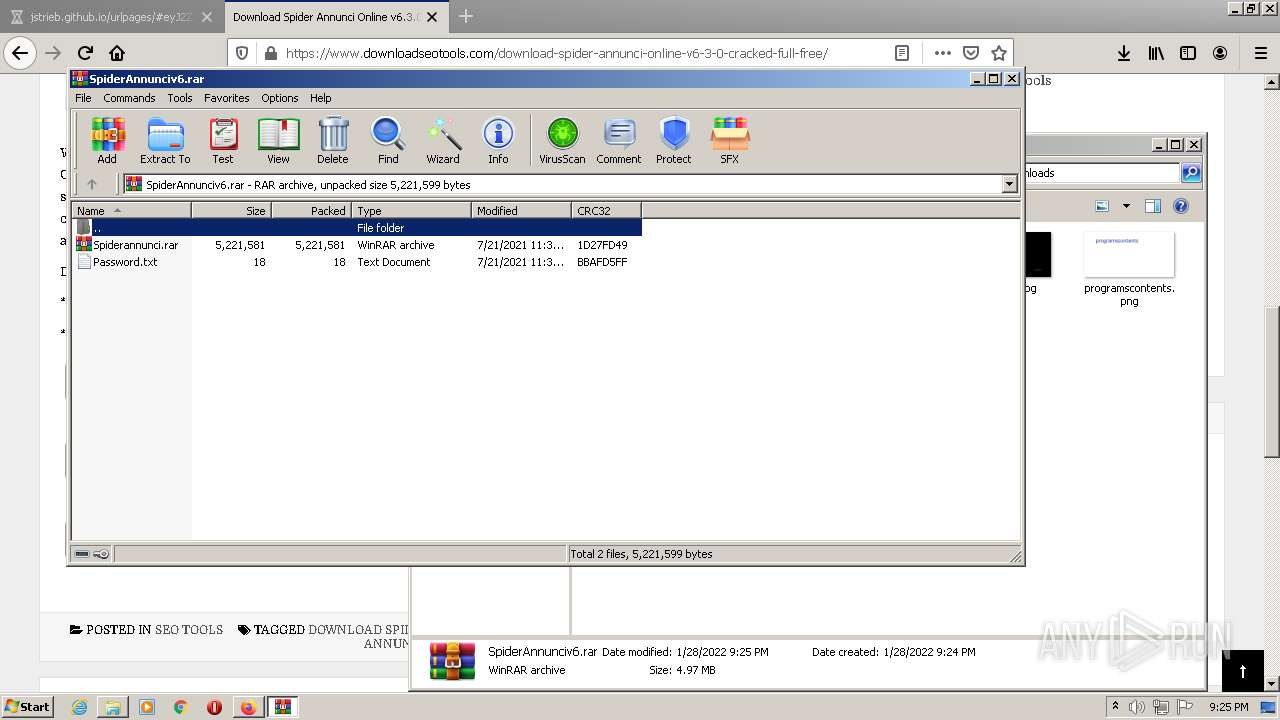
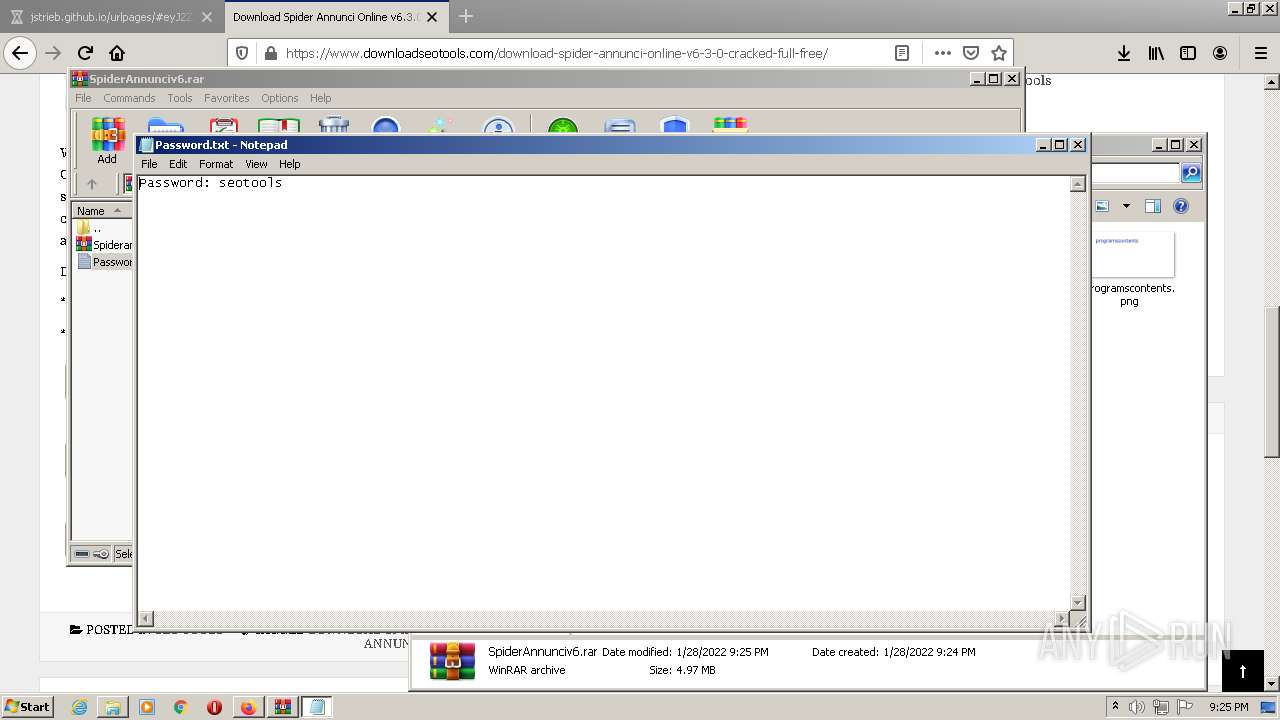
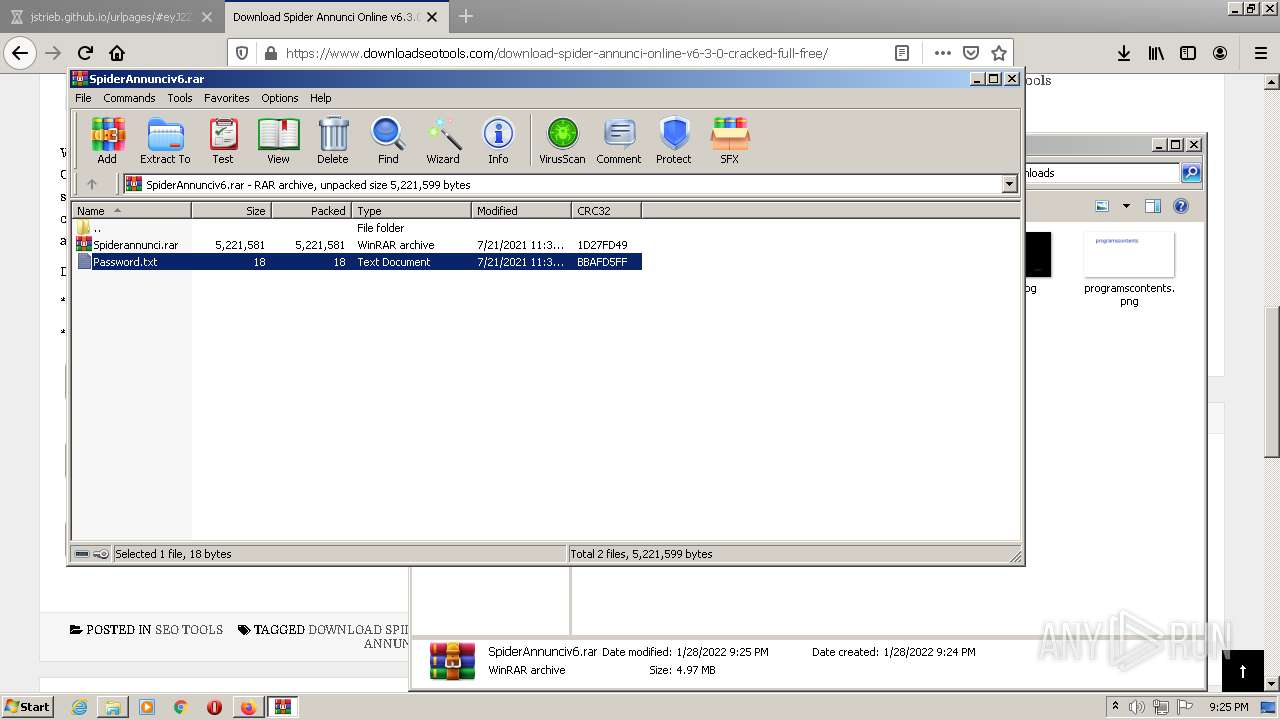
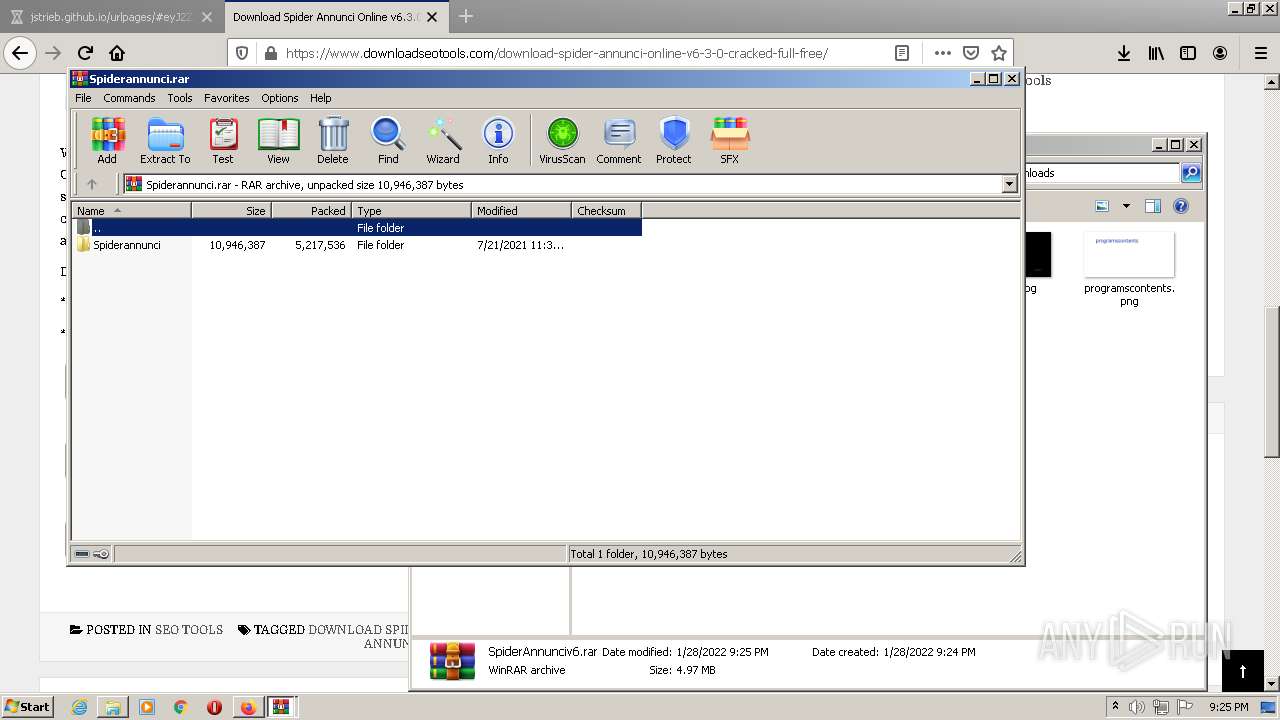
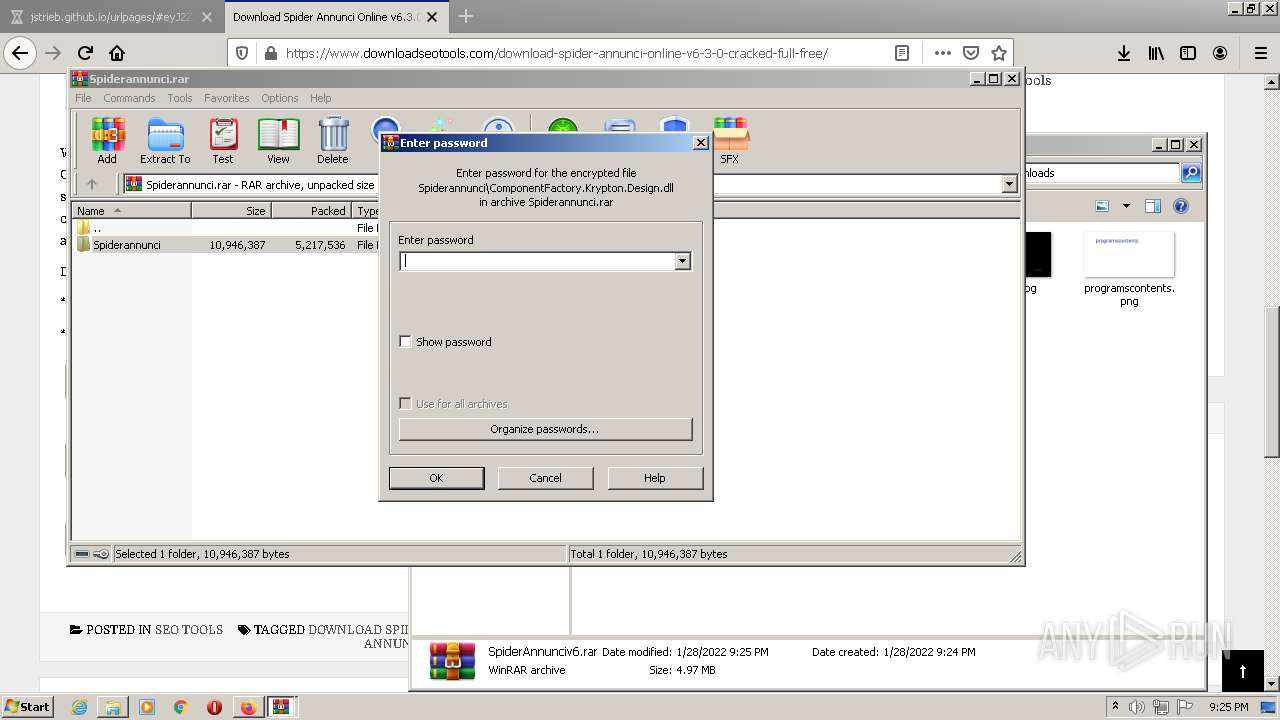
Executable content was dropped or overwritten
- firefox.exe (PID: 3444)
- WinRAR.exe (PID: 2792)
Drops a file that was compiled in debug mode
- firefox.exe (PID: 3444)
- WinRAR.exe (PID: 2792)
Checks supported languages
- WinRAR.exe (PID: 4012)
- WinRAR.exe (PID: 2792)
- Spider.exe (PID: 1872)
- Spider.exe (PID: 1760)
- filezilla.exe (PID: 1600)
Application launched itself
- WinRAR.exe (PID: 4012)
Reads Windows Product ID
- Spider.exe (PID: 1872)
- Spider.exe (PID: 1760)
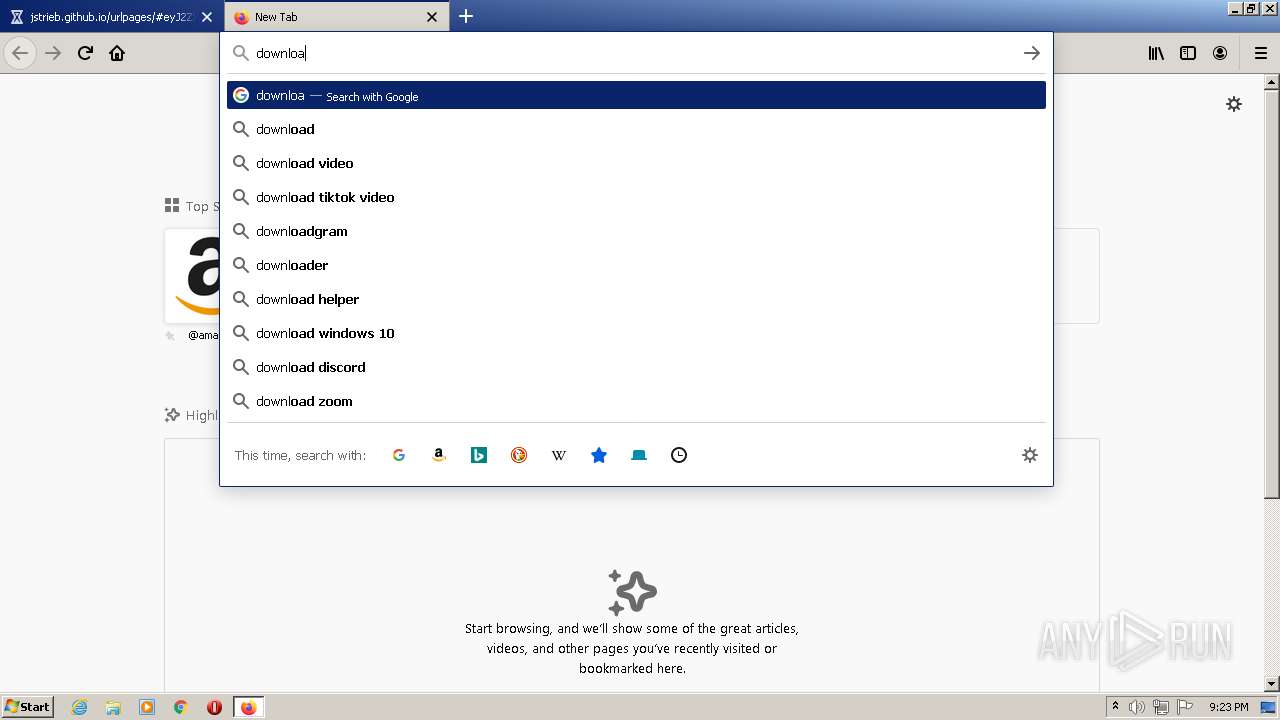
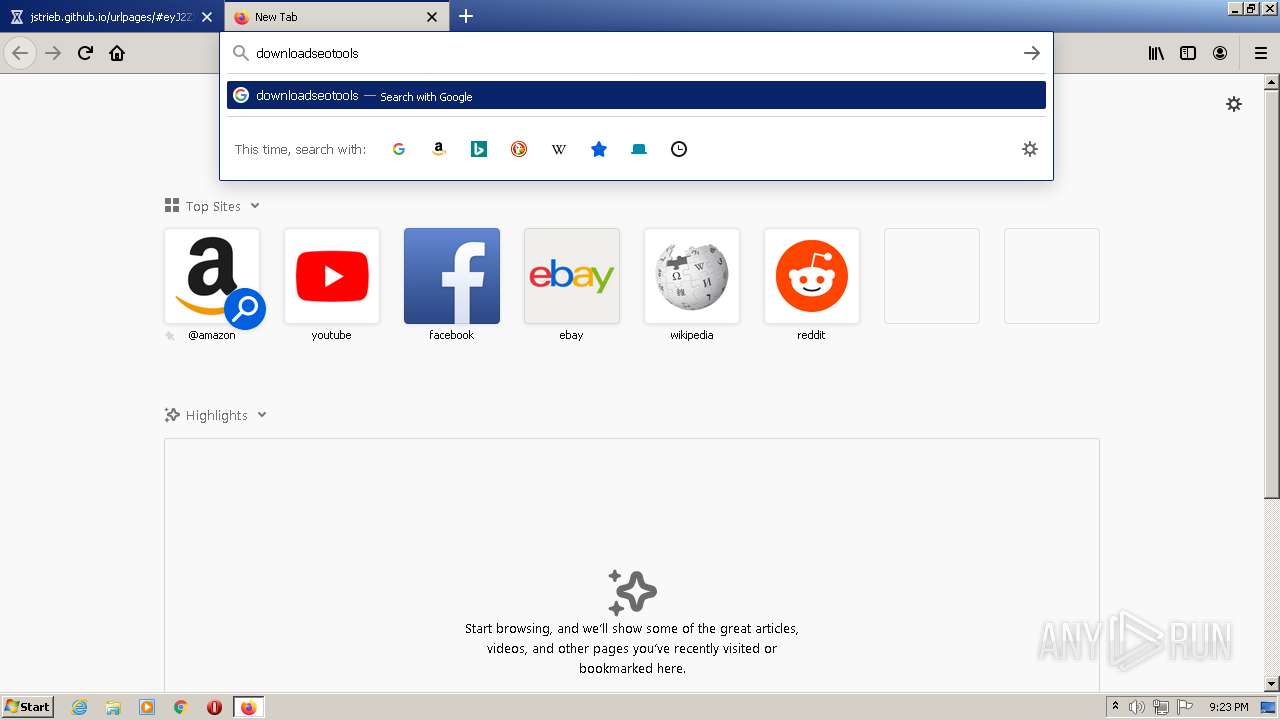
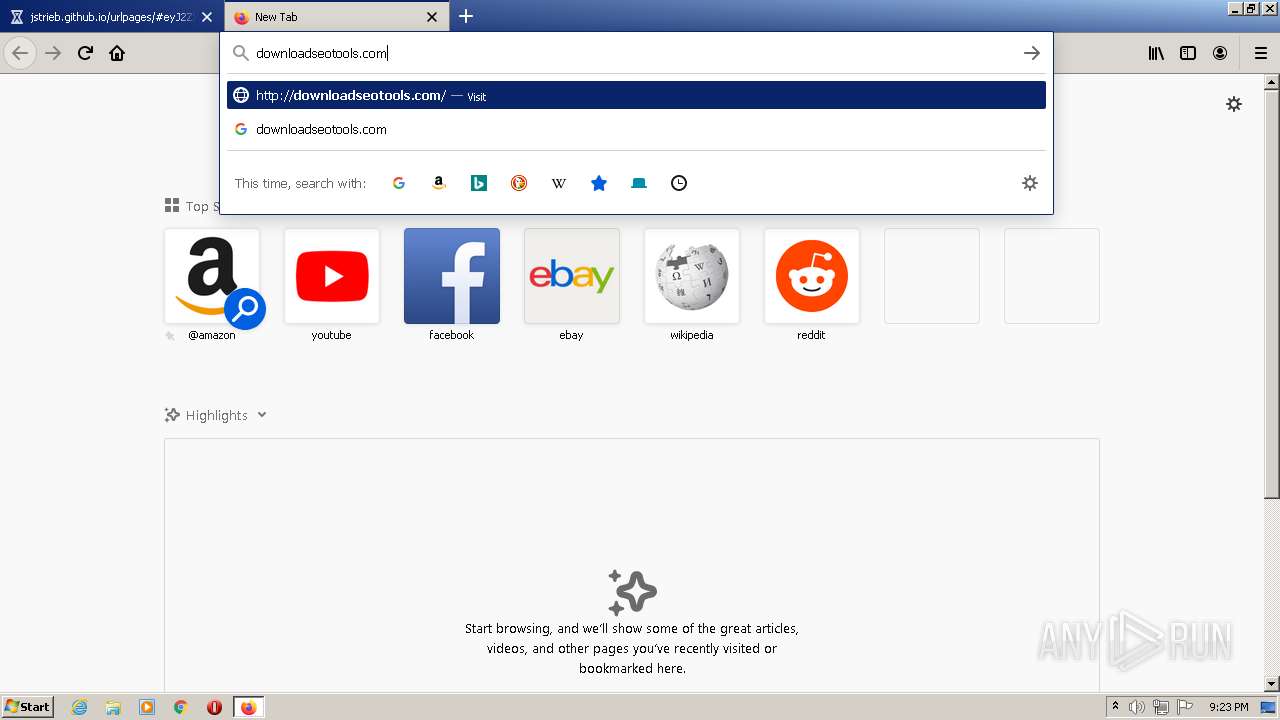
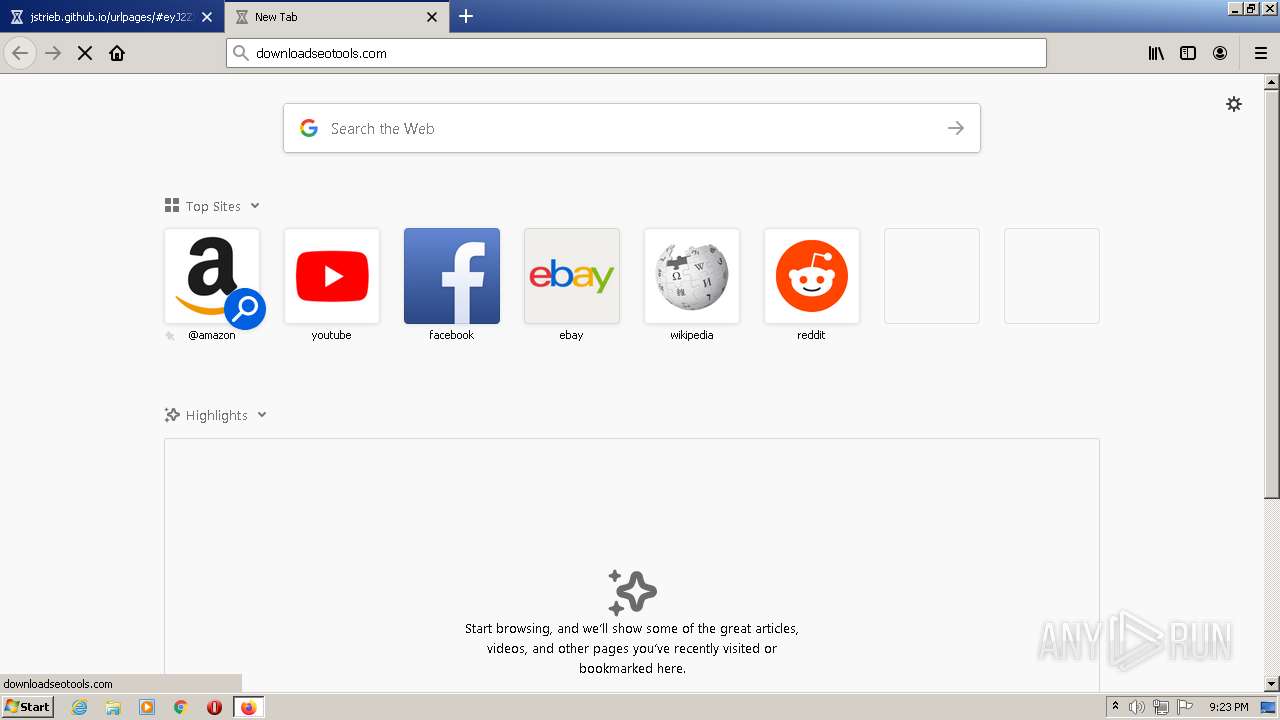
Starts Internet Explorer
- Spider.exe (PID: 1760)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3348)
INFO
Checks supported languages
- chrome.exe (PID: 3004)
- chrome.exe (PID: 2172)
- chrome.exe (PID: 2948)
- chrome.exe (PID: 3492)
- chrome.exe (PID: 1200)
- chrome.exe (PID: 3956)
- firefox.exe (PID: 3508)
- firefox.exe (PID: 3444)
- firefox.exe (PID: 3844)
- firefox.exe (PID: 648)
- firefox.exe (PID: 3952)
- firefox.exe (PID: 996)
- firefox.exe (PID: 1220)
- firefox.exe (PID: 2300)
- firefox.exe (PID: 2964)
- firefox.exe (PID: 3268)
- SearchProtocolHost.exe (PID: 2836)
- NOTEPAD.EXE (PID: 3244)
- chrome.exe (PID: 3924)
- iexplore.exe (PID: 3000)
- chrome.exe (PID: 1160)
- iexplore.exe (PID: 3348)
Reads the computer name
- chrome.exe (PID: 1200)
- chrome.exe (PID: 2948)
- chrome.exe (PID: 1160)
- firefox.exe (PID: 648)
- firefox.exe (PID: 3444)
- firefox.exe (PID: 3844)
- firefox.exe (PID: 3952)
- firefox.exe (PID: 996)
- firefox.exe (PID: 2300)
- firefox.exe (PID: 1220)
- firefox.exe (PID: 2964)
- firefox.exe (PID: 3268)
- SearchProtocolHost.exe (PID: 2836)
- chrome.exe (PID: 3004)
- iexplore.exe (PID: 3000)
- iexplore.exe (PID: 3348)
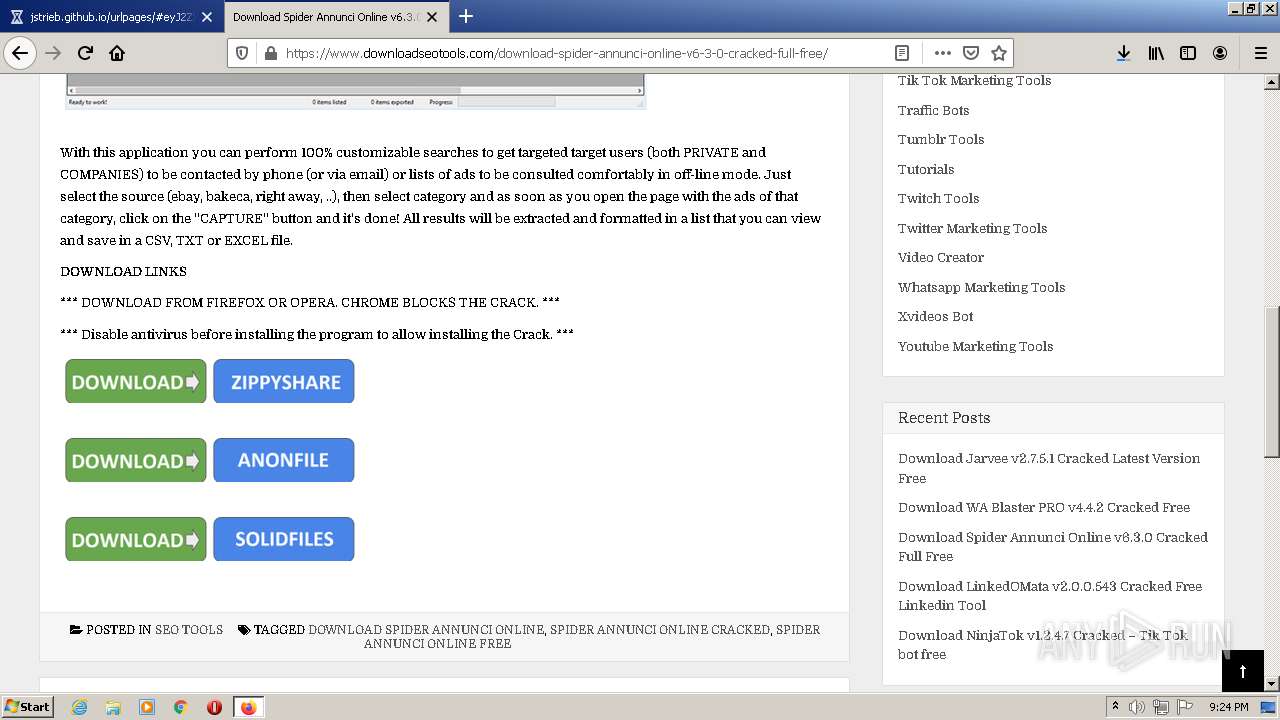
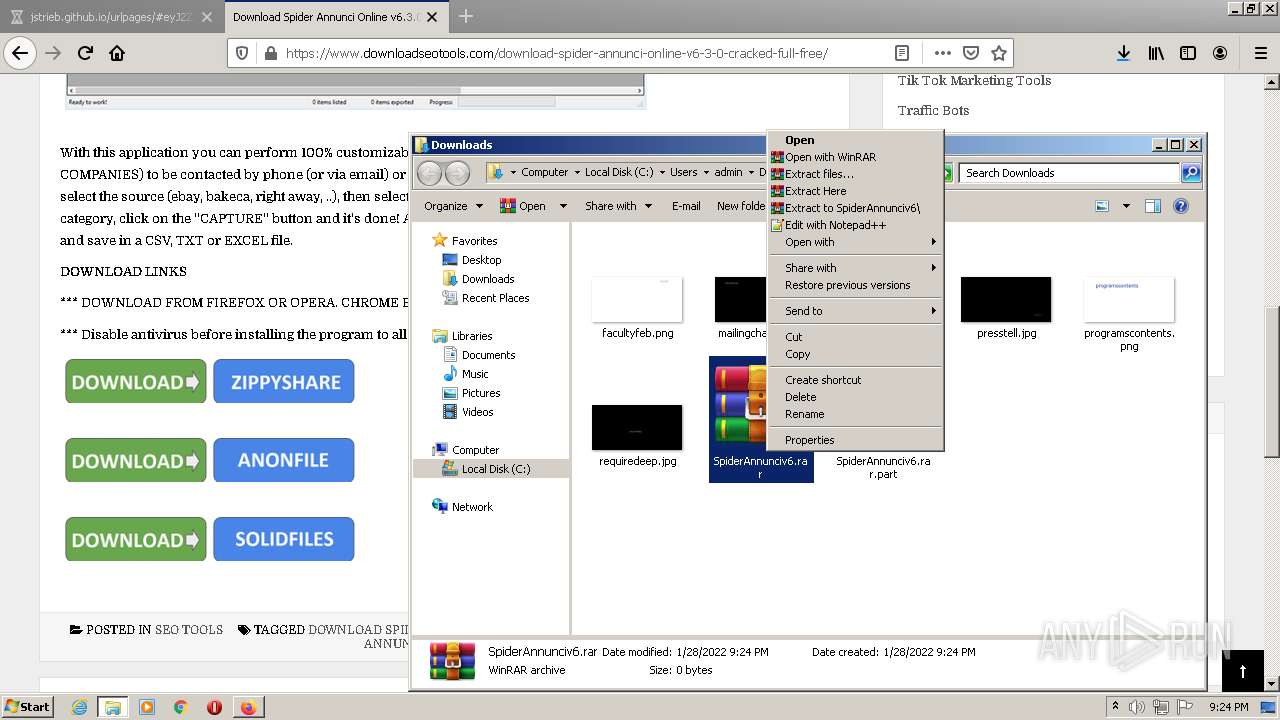
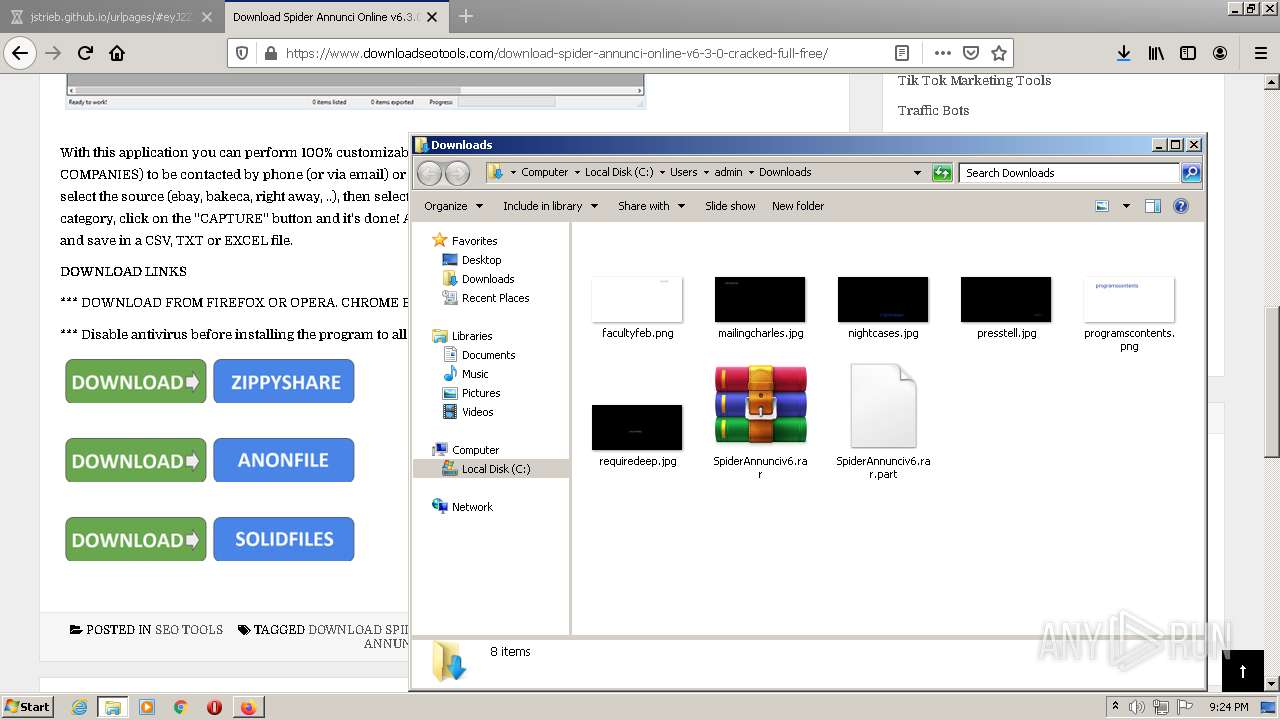
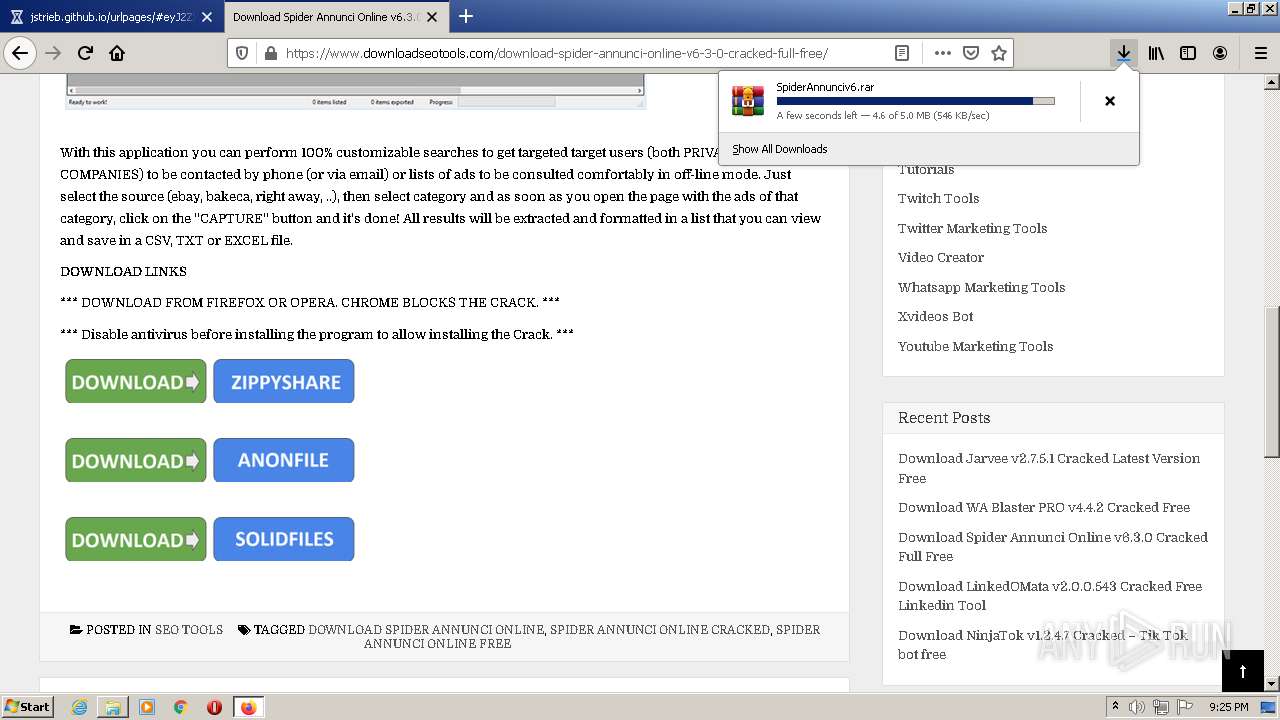
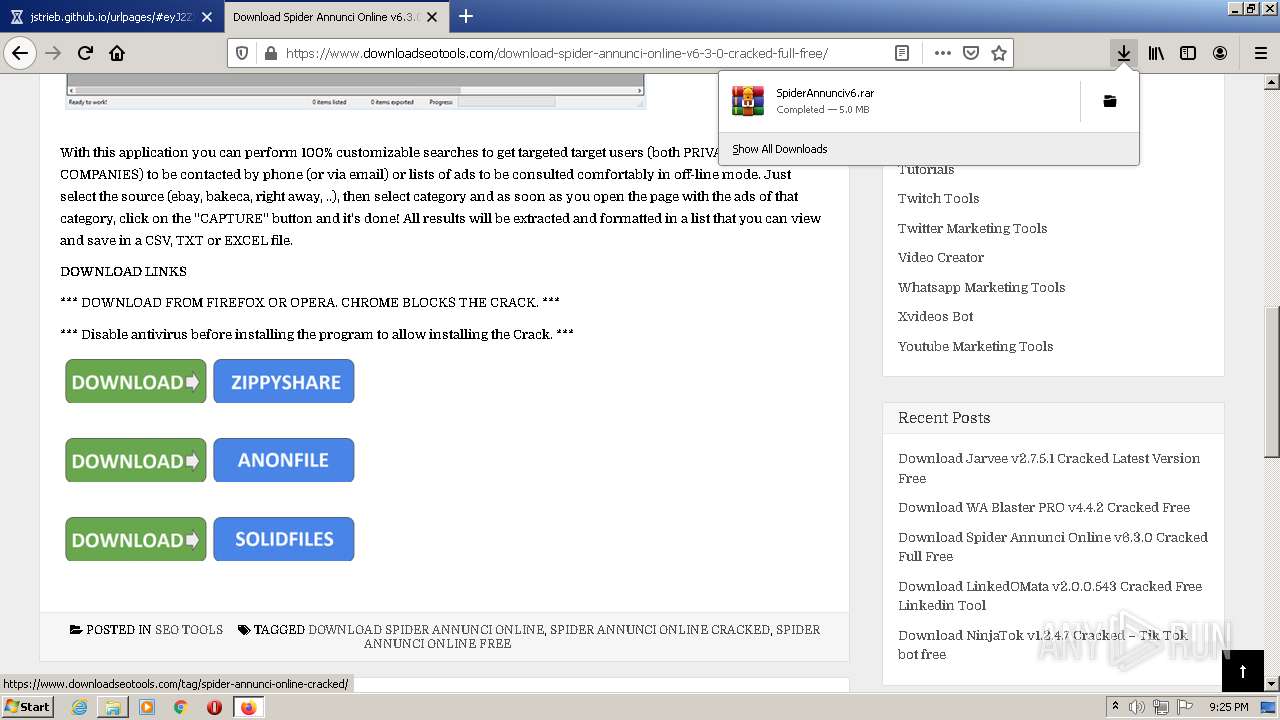
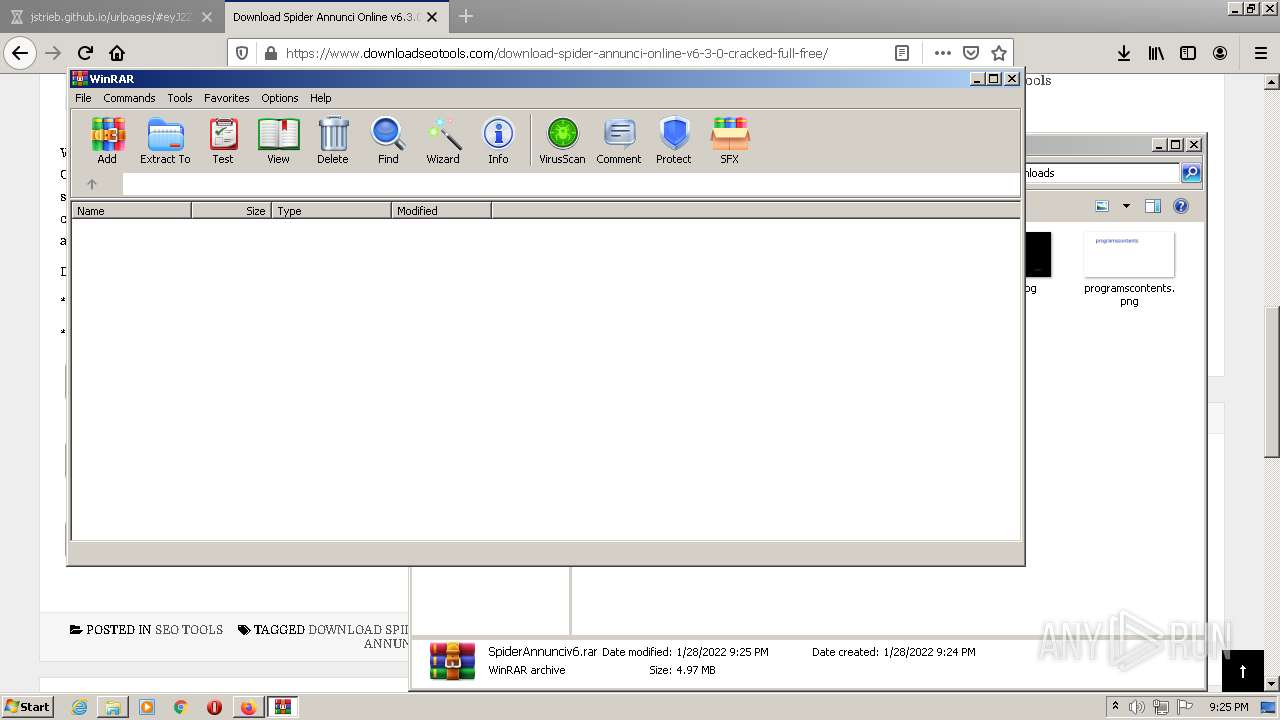
Manual execution by user
- filezilla.exe (PID: 1600)
- firefox.exe (PID: 3508)
- WinRAR.exe (PID: 4012)
- Spider.exe (PID: 1872)
- Spider.exe (PID: 1760)
Reads settings of System Certificates
- filezilla.exe (PID: 1600)
- chrome.exe (PID: 2948)
- iexplore.exe (PID: 3348)
- iexplore.exe (PID: 3000)
Application launched itself
- firefox.exe (PID: 3508)
- firefox.exe (PID: 3444)
- chrome.exe (PID: 3004)
- iexplore.exe (PID: 3000)
Reads CPU info
- firefox.exe (PID: 3444)
Creates files in the program directory
- firefox.exe (PID: 3444)
Creates files in the user directory
- firefox.exe (PID: 3444)
- iexplore.exe (PID: 3348)
Reads the date of Windows installation
- firefox.exe (PID: 3444)
- iexplore.exe (PID: 3000)
Dropped object may contain Bitcoin addresses
- firefox.exe (PID: 3444)
- iexplore.exe (PID: 3348)
Checks Windows Trust Settings
- firefox.exe (PID: 3444)
- iexplore.exe (PID: 3348)
- iexplore.exe (PID: 3000)
Reads the hosts file
- chrome.exe (PID: 3004)
- chrome.exe (PID: 2948)
Changes internet zones settings
- iexplore.exe (PID: 3000)
Reads internet explorer settings
- iexplore.exe (PID: 3348)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
70
Monitored processes
27
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 648 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3444.6.1766081164\938225669" -childID 1 -isForBrowser -prefsHandle 2156 -prefMapHandle 2152 -prefsLen 245 -prefMapSize 238726 -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 3444 "\\.\pipe\gecko-crash-server-pipe.3444" 2168 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 996 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3444.20.1015106008\1227343240" -childID 3 -isForBrowser -prefsHandle 3440 -prefMapHandle 3480 -prefsLen 7399 -prefMapSize 238726 -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 3444 "\\.\pipe\gecko-crash-server-pipe.3444" 3520 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 1160 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=976,11373123984495570394,12710461487532574670,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=1044 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1200 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=976,11373123984495570394,12710461487532574670,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1056 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1220 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3444.21.883472481\1564306335" -childID 4 -isForBrowser -prefsHandle 3488 -prefMapHandle 2852 -prefsLen 7399 -prefMapSize 238726 -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 3444 "\\.\pipe\gecko-crash-server-pipe.3444" 3560 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 1600 | "C:\Program Files\FileZilla FTP Client\filezilla.exe" | C:\Program Files\FileZilla FTP Client\filezilla.exe | — | Explorer.EXE | |||||||||||
User: admin Company: FileZilla Project Integrity Level: MEDIUM Description: FileZilla FTP Client Exit code: 0 Version: 3, 51, 0, 0 Modules
| |||||||||||||||
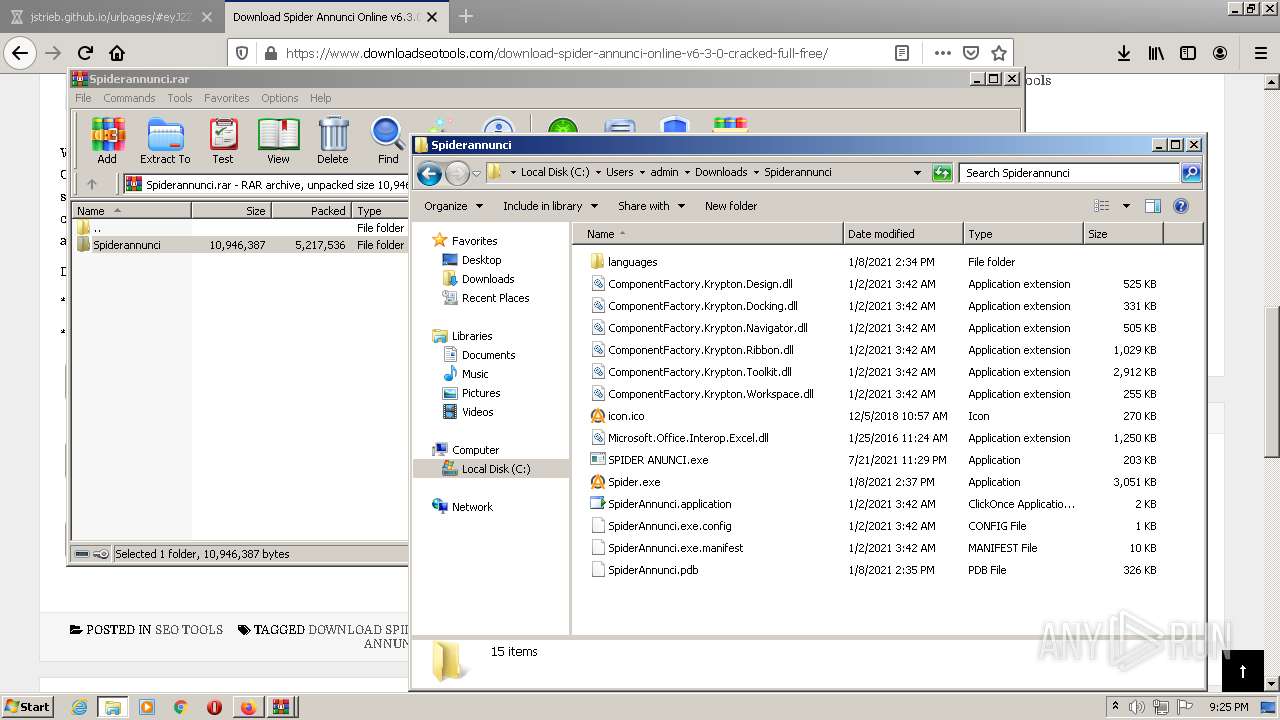
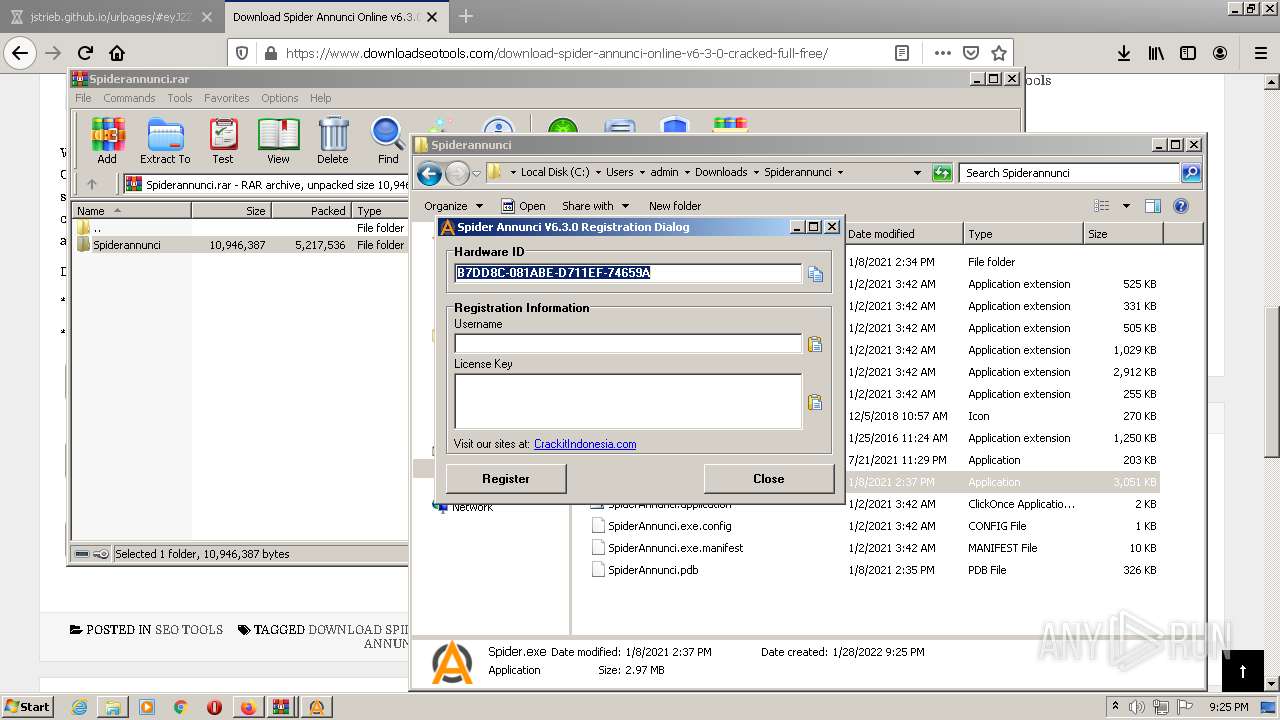
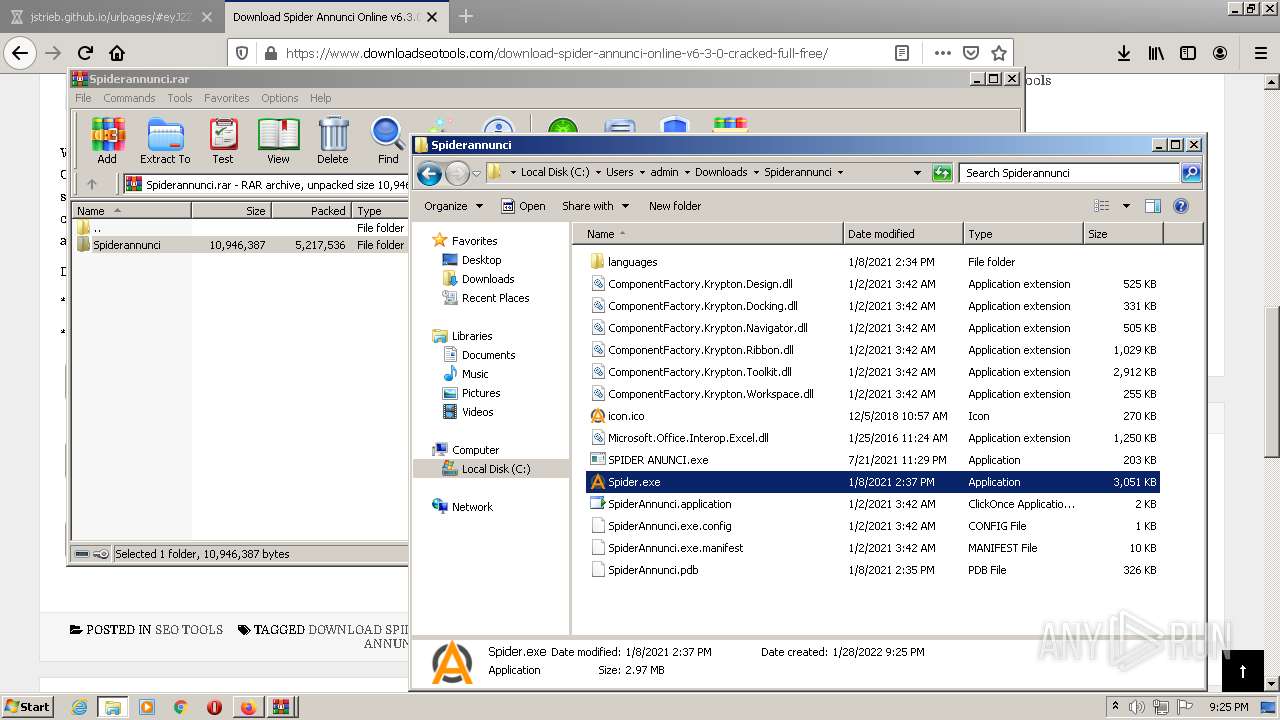
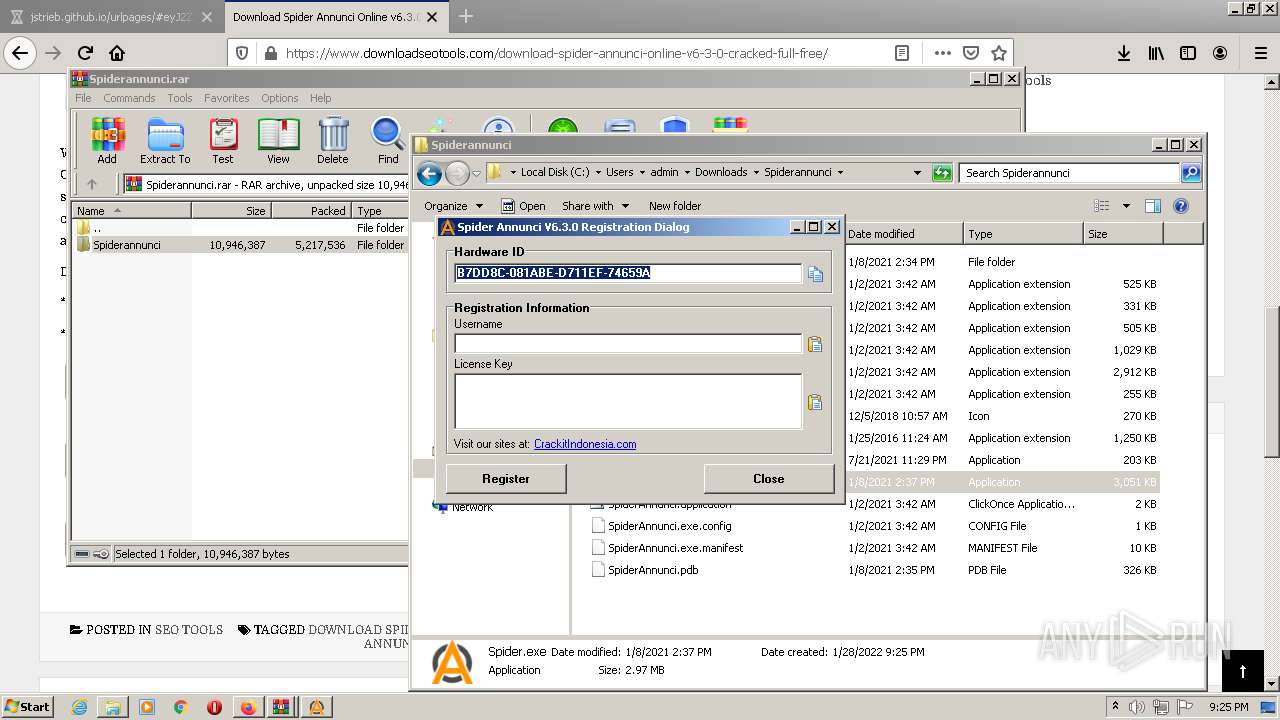
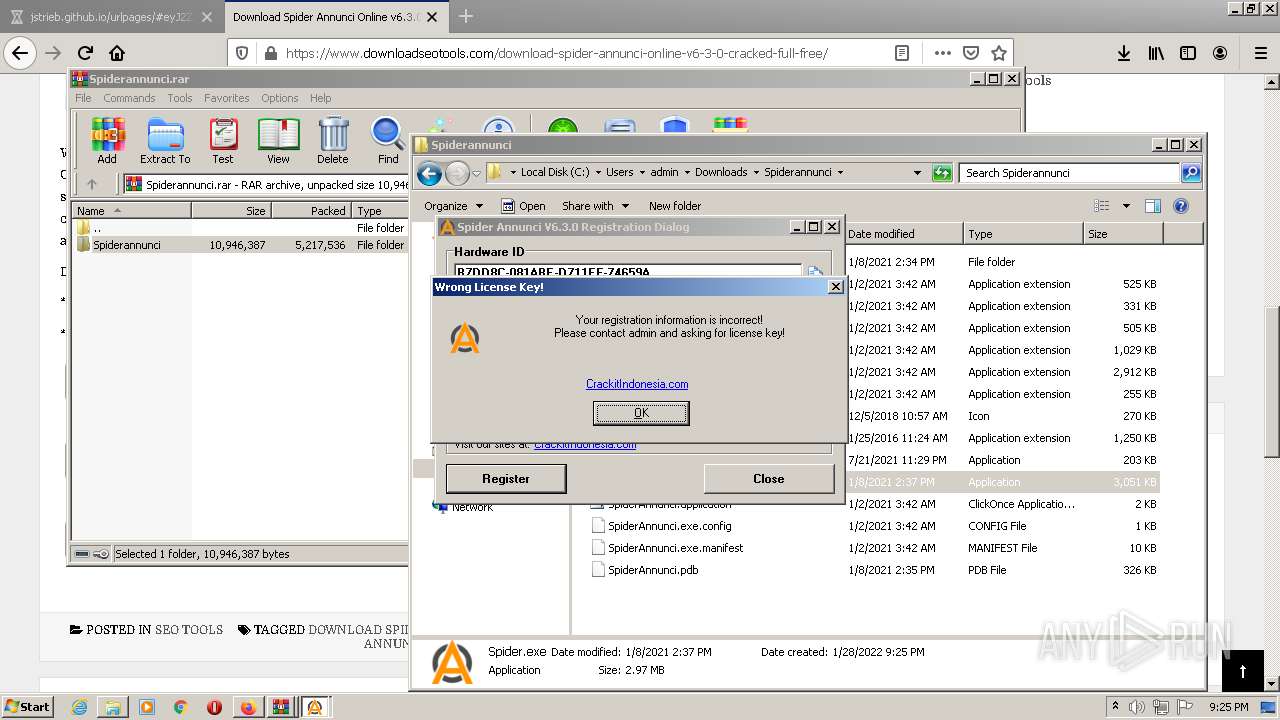
| 1760 | "C:\Users\admin\Downloads\Spiderannunci\Spider.exe" | C:\Users\admin\Downloads\Spiderannunci\Spider.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Description: OYP Scarper Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1872 | "C:\Users\admin\Downloads\Spiderannunci\Spider.exe" | C:\Users\admin\Downloads\Spiderannunci\Spider.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Description: OYP Scarper Exit code: 12522186 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2172 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x71aed988,0x71aed998,0x71aed9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2300 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3444.34.920648086\1027961308" -childID 5 -isForBrowser -prefsHandle 3888 -prefMapHandle 3896 -prefsLen 7982 -prefMapSize 238726 -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 3444 "\\.\pipe\gecko-crash-server-pipe.3444" 3848 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
Total events
42 984
Read events
42 781
Write events
201
Delete events
2
Modification events
| (PID) Process: | (3004) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3004) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3004) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3004) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3004) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3004) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3004) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3004) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3004) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (3004) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
13
Suspicious files
199
Text files
191
Unknown types
74
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-61F45E8B-BBC.pma | — | |
MD5:— | SHA256:— | |||
| 3004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 3004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
| 3004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF13ebea.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 3004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF13ece4.TMP | text | |
MD5:B628564B8042F6E2CC2F53710AAECDC0 | SHA256:1D3B022BDEE9F48D79E3EC1E93F519036003642D3D72D10B05CFD47F43EFBF13 | |||
| 3004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF13ec19.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
| 3004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 3004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
| 3004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences~RF13ed80.TMP | text | |
MD5:8304B8F42465198890090F52D3F80A4C | SHA256:80C32AC2585E7E81200104B1630F19560A156C4ABF51B5888B0FBF07323FAB34 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
102
TCP/UDP connections
188
DNS requests
269
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3444 | firefox.exe | GET | 301 | 188.114.97.7:80 | http://ballost.org/ | US | — | — | malicious |
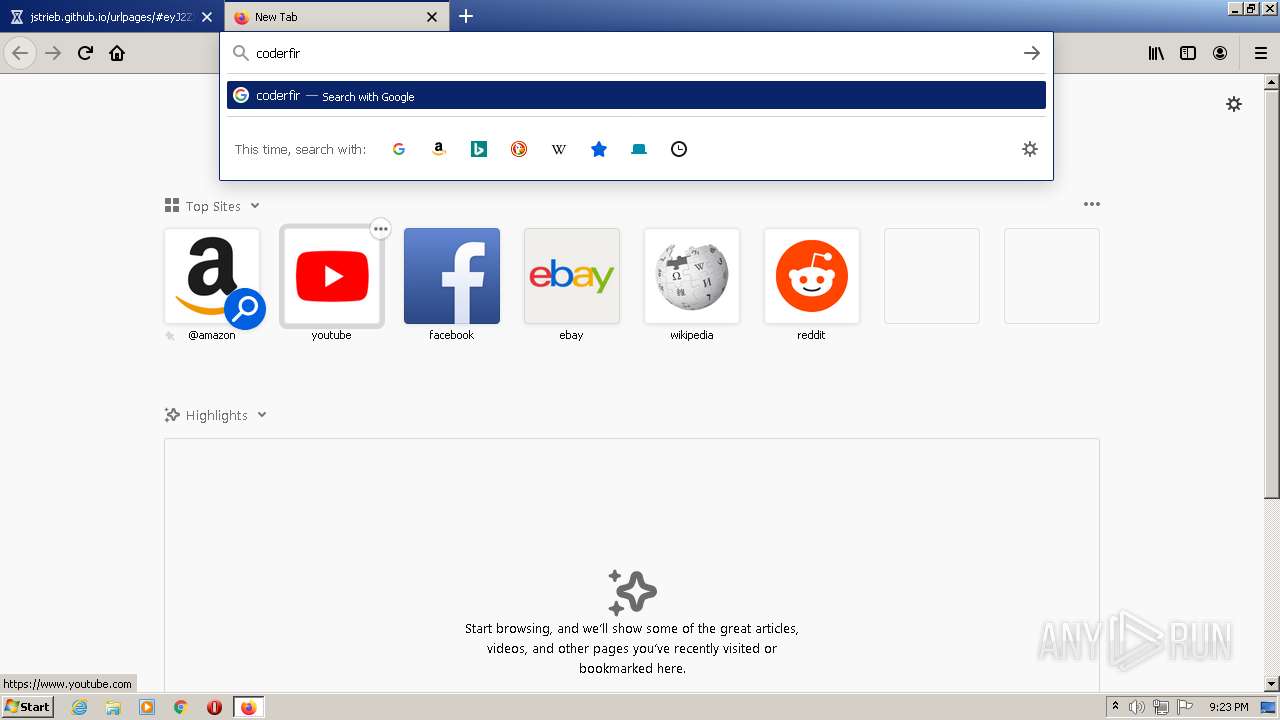
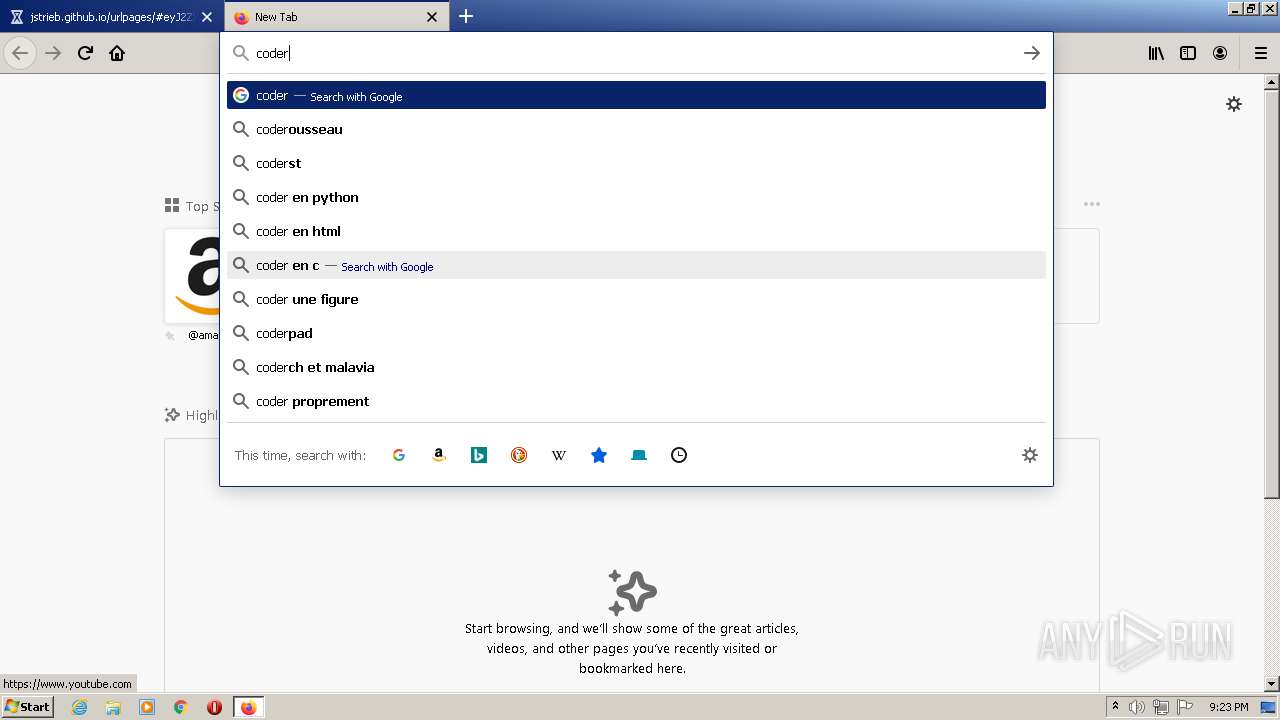
3444 | firefox.exe | GET | — | 131.106.34.90:80 | http://coderforlife.com/ | US | — | — | unknown |
3444 | firefox.exe | GET | 302 | 103.224.212.244:80 | http://www.qfind.net/?_inv | AU | — | — | whitelisted |
3444 | firefox.exe | GET | 302 | 103.224.212.244:80 | http://www.qfind.net/?_inv | AU | — | — | whitelisted |
3444 | firefox.exe | GET | 200 | 104.21.82.142:80 | http://file.fan/.well-known/http-opportunistic | US | text | 39 b | malicious |
3444 | firefox.exe | GET | 200 | 188.114.96.7:80 | http://www.ballost.org/.well-known/http-opportunistic | US | text | 46 b | malicious |
3444 | firefox.exe | GET | 200 | 188.114.97.7:80 | http://ballost.org/.well-known/http-opportunistic | US | text | 42 b | malicious |
3444 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | US | text | 8 b | whitelisted |
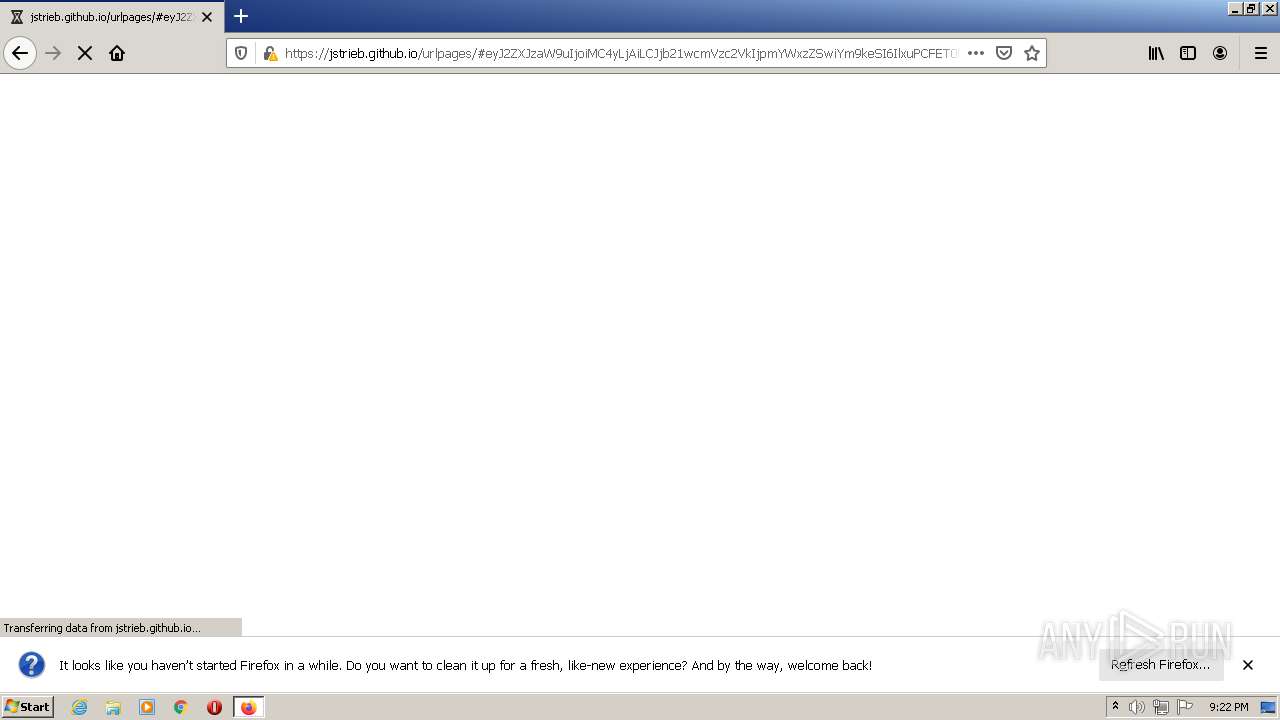
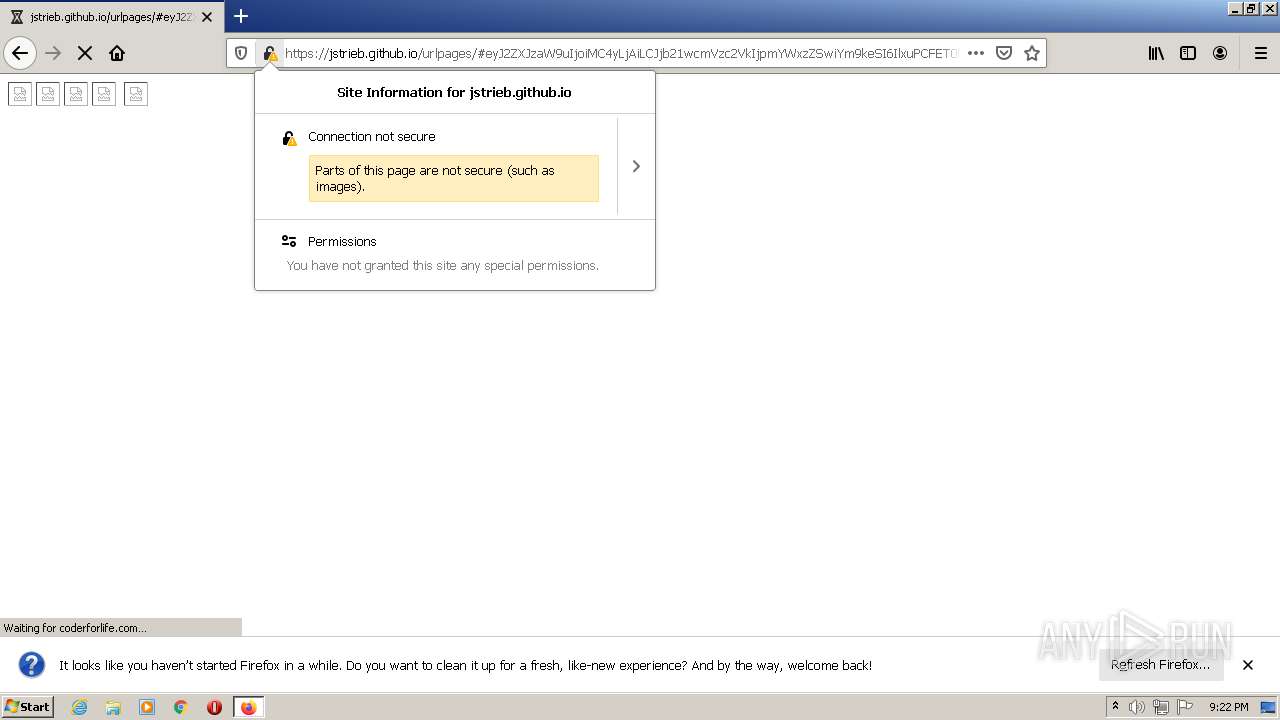
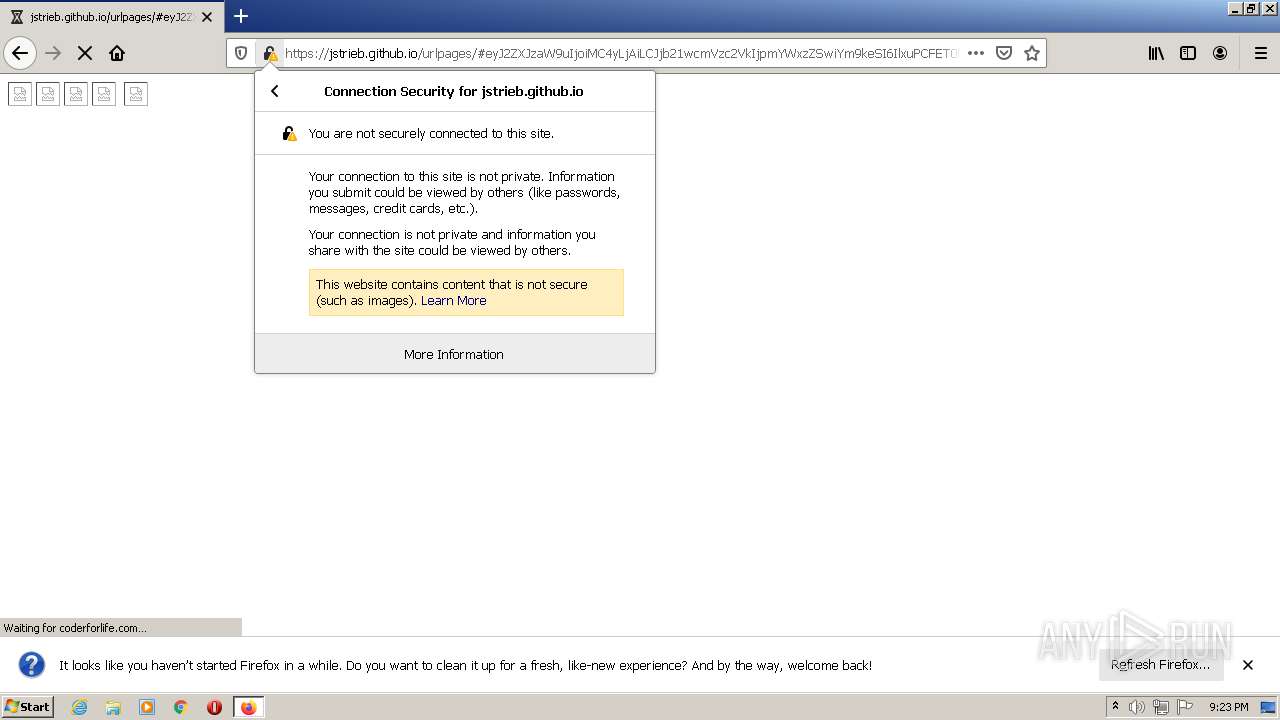
2948 | chrome.exe | GET | 301 | 185.199.108.153:80 | http://jstrieb.github.io/urlpages/ | NL | html | 162 b | whitelisted |
3444 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt | US | text | 8 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3444 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3444 | firefox.exe | 34.215.36.246:443 | push.services.mozilla.com | Amazon.com, Inc. | US | unknown |
— | — | 13.224.111.101:443 | content-signature-2.cdn.mozilla.net | — | US | unknown |
— | — | 192.168.100.2:53 | — | — | — | whitelisted |
2948 | chrome.exe | 142.250.186.45:443 | accounts.google.com | Google Inc. | US | suspicious |
2948 | chrome.exe | 185.199.108.153:80 | jstrieb.github.io | GitHub, Inc. | NL | shared |
2948 | chrome.exe | 142.250.185.227:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3444 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | — | US | whitelisted |
3444 | firefox.exe | 185.199.110.153:80 | jstrieb.github.io | GitHub, Inc. | NL | shared |
3444 | firefox.exe | 185.199.110.153:443 | jstrieb.github.io | GitHub, Inc. | NL | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.microsoft.com |
| whitelisted |
tinyurl.com |
| shared |
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
jstrieb.github.io |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.google.com |
| malicious |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
example.org |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3444 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
3444 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
3444 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
3444 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
3444 | firefox.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |