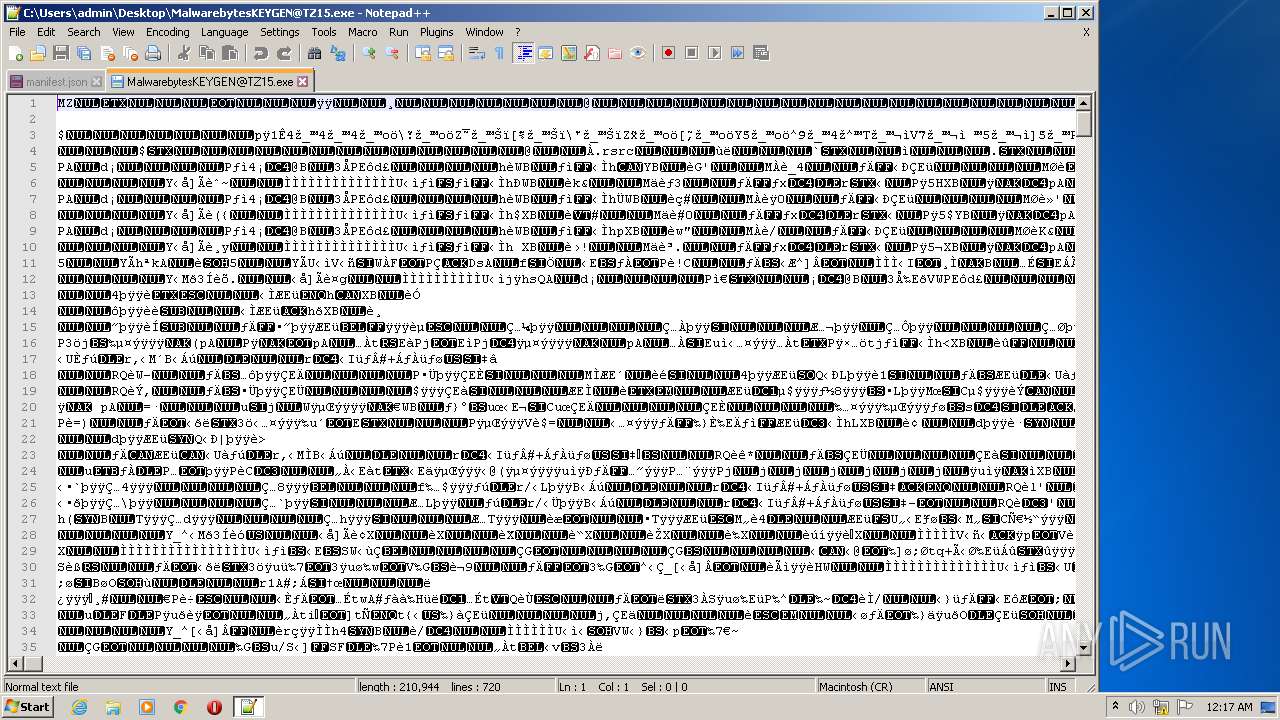
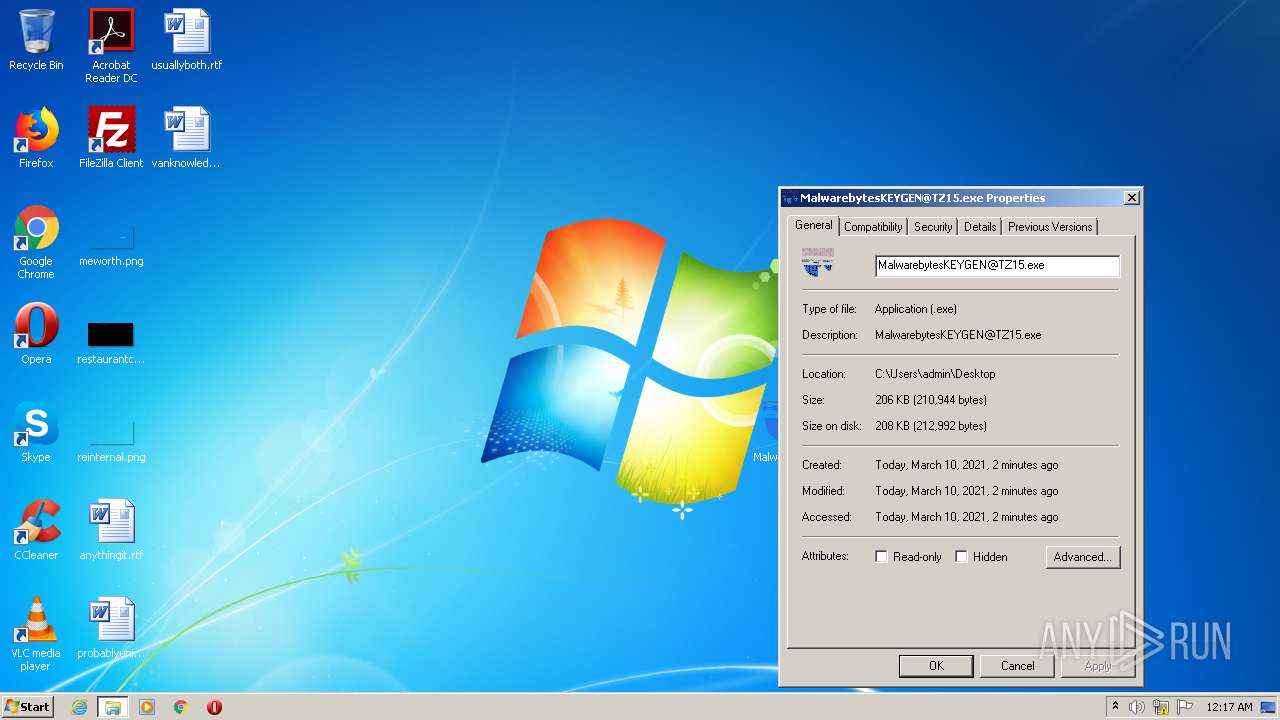
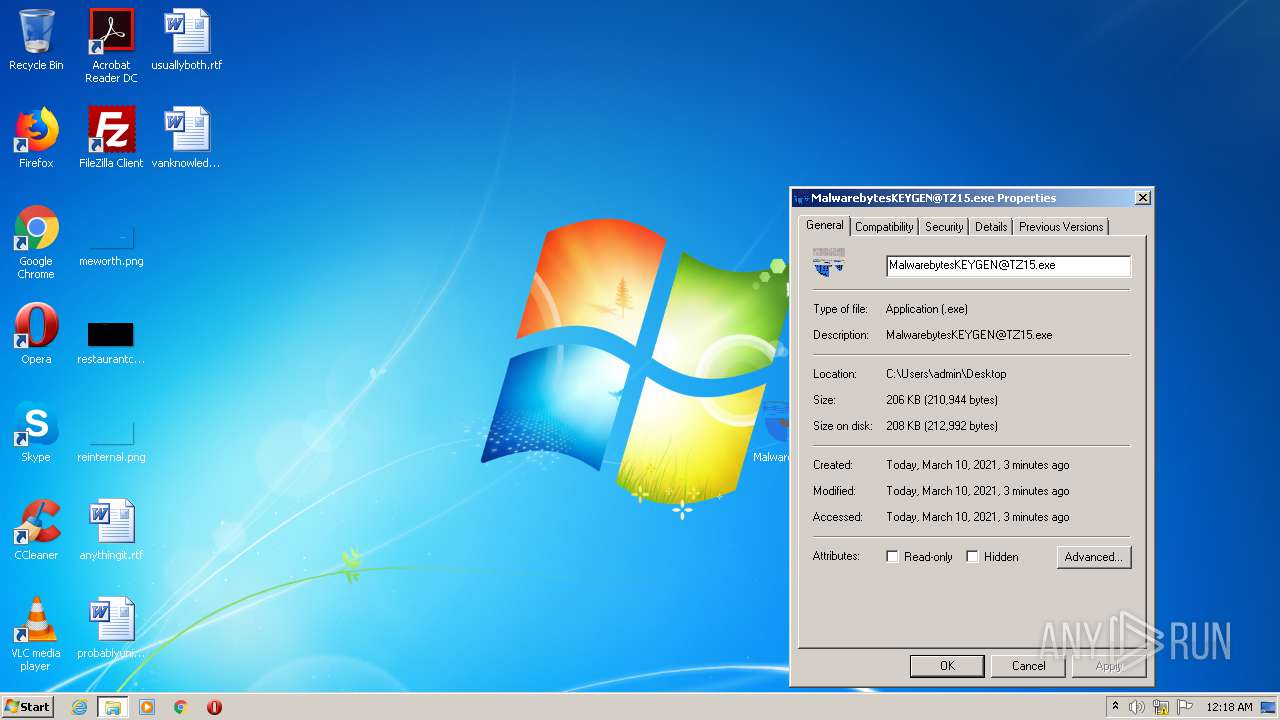
| File name: | MalwarebytesKEYGEN@TZ15.exe |
| Full analysis: | https://app.any.run/tasks/c9ee1c95-2a9a-483d-a4cd-4fc807d27e04 |
| Verdict: | Malicious activity |
| Analysis date: | March 10, 2021, 00:15:36 |
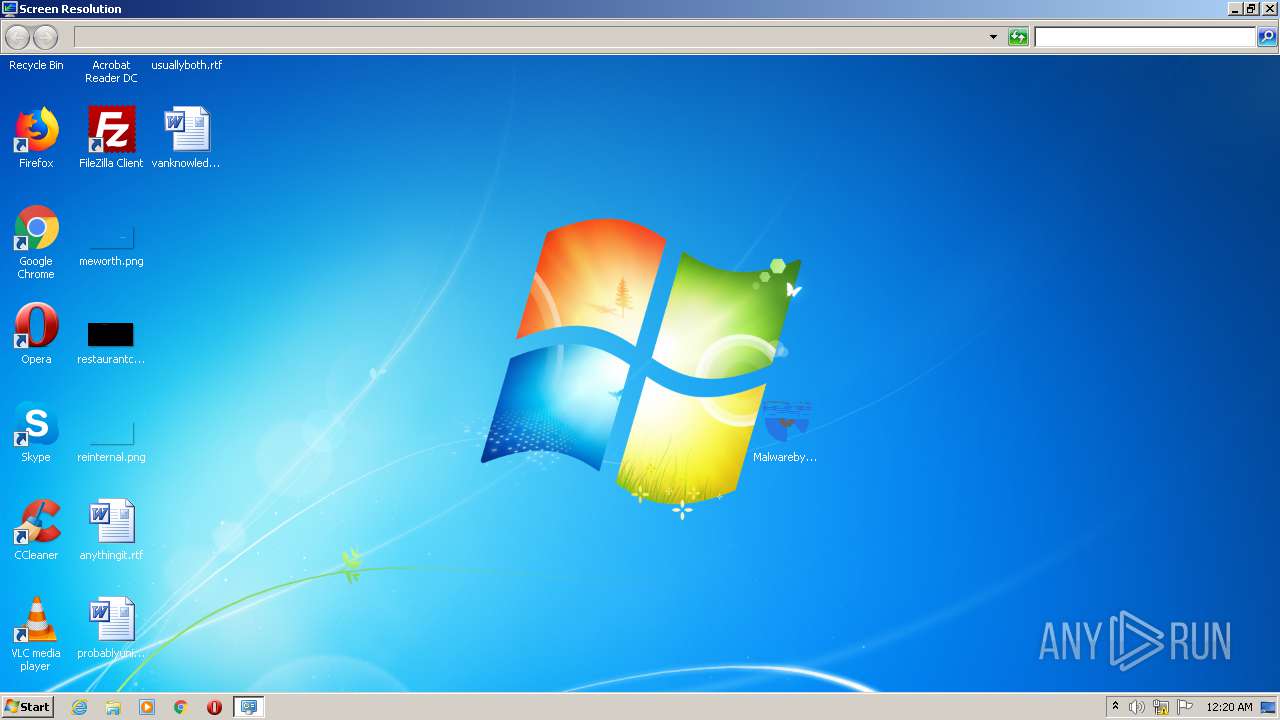
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | 5713DCAD897D5FB710730776753D02B2 |
| SHA1: | CFF3DDB444CE931E94485A3F3D8CF2B2F7DDCF94 |
| SHA256: | 414164BA0E472110EE7188B3AC27A601D4EF4BDDF8BB137946224128B42571D3 |
| SSDEEP: | 3072:ieA5tSGCblDZz0++cuJ9f4JHQaAPVhAg0FuD0+YmXRD6Bzh/BT0:iztSGC8+VuJ9lAOprD6Bzh50 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executed via COM
- DllHost.exe (PID: 1748)
- DllHost.exe (PID: 3872)
- DllHost.exe (PID: 2784)
Creates files in the program directory
- wermgr.exe (PID: 2192)
- wermgr.exe (PID: 2532)
INFO
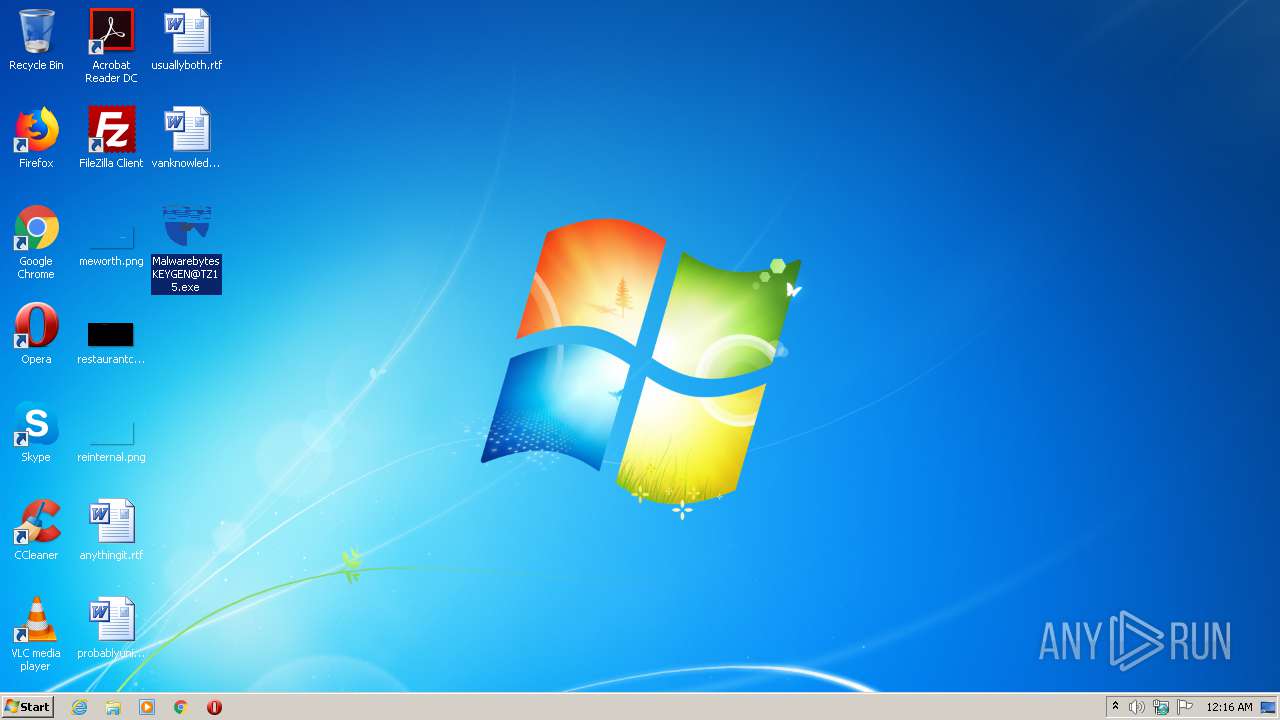
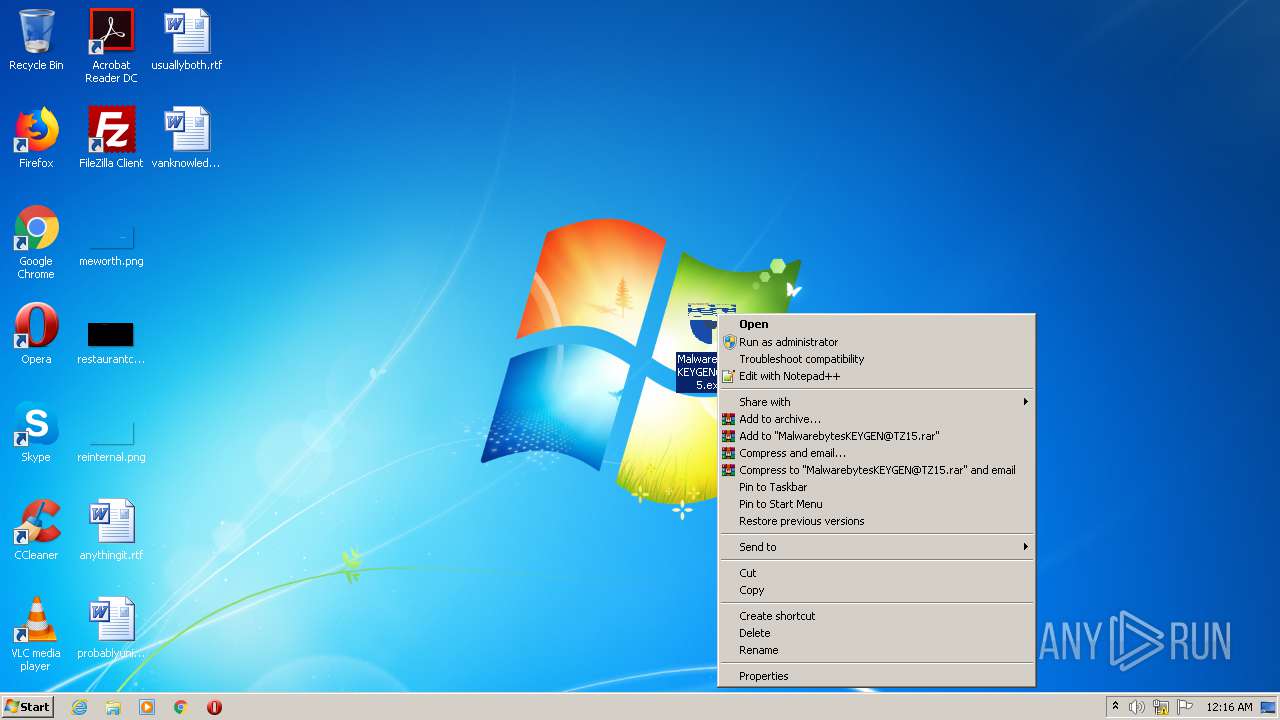
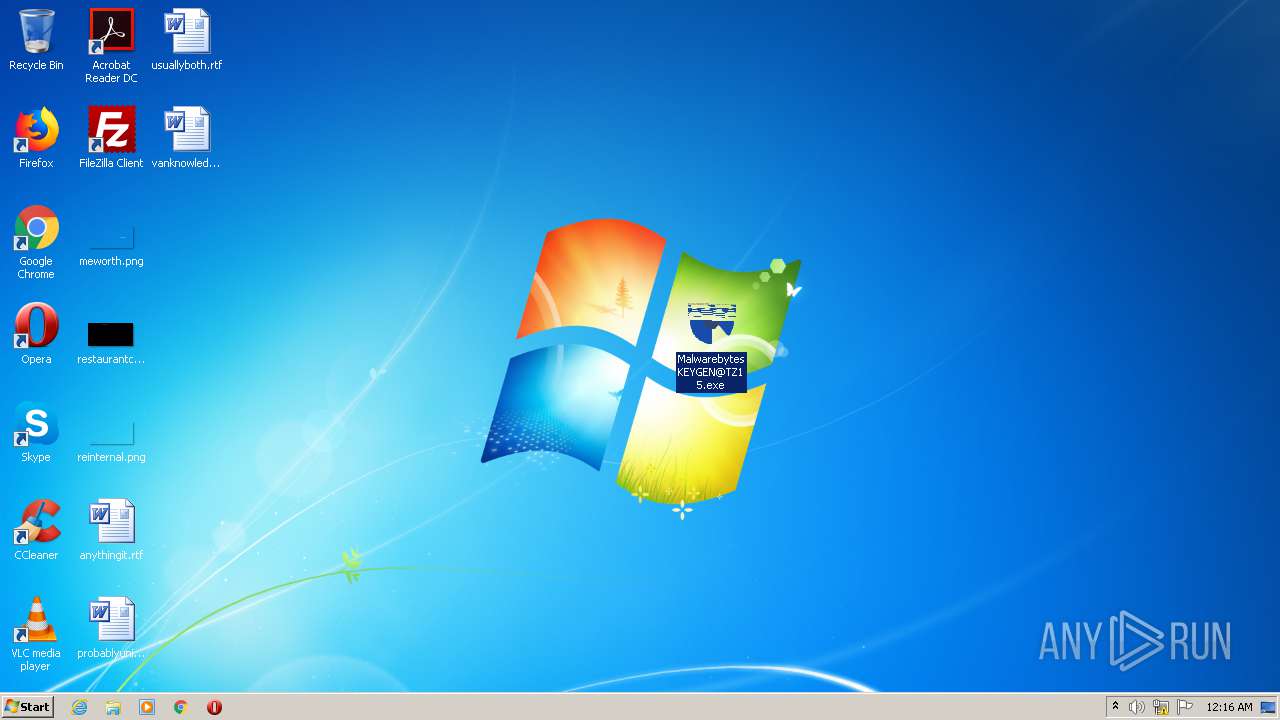
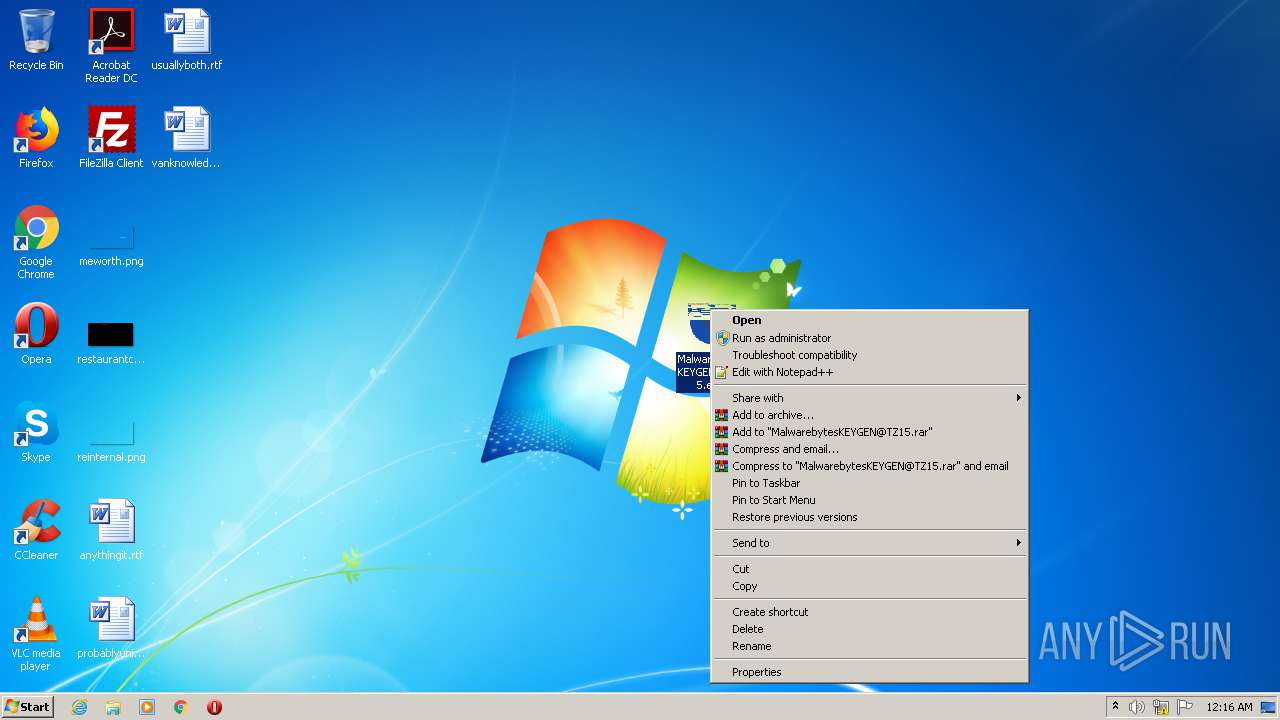
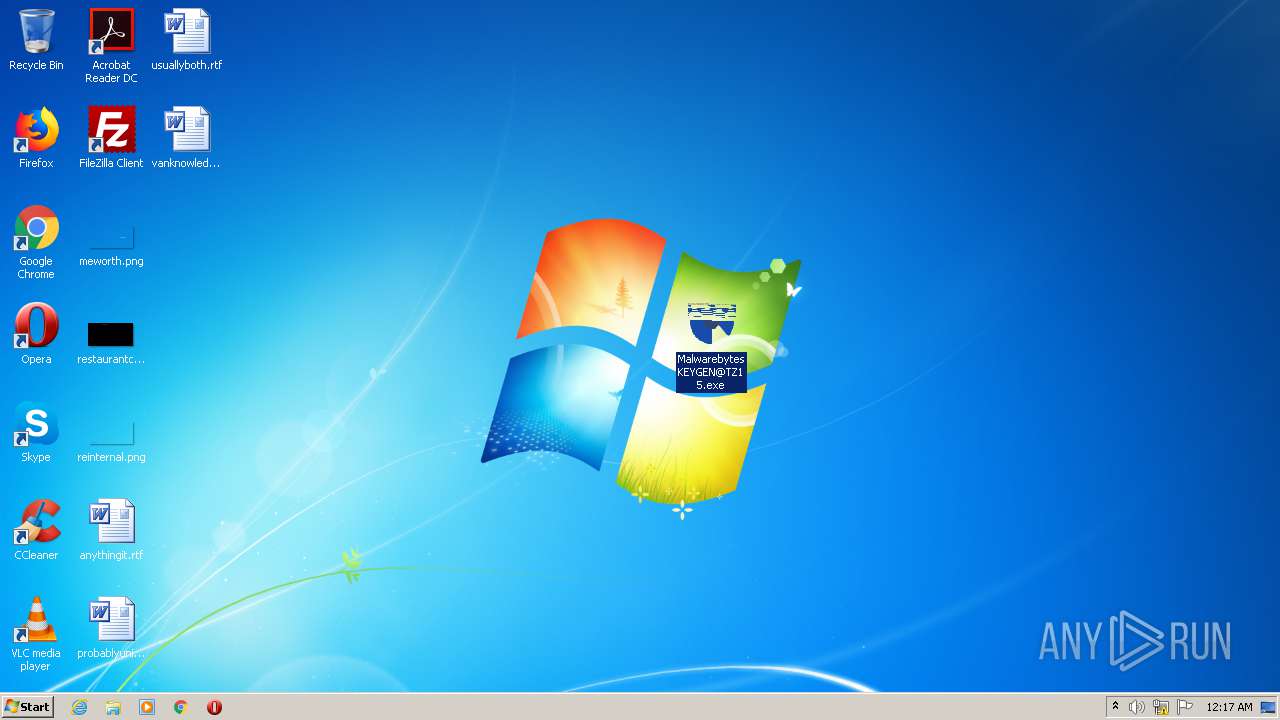
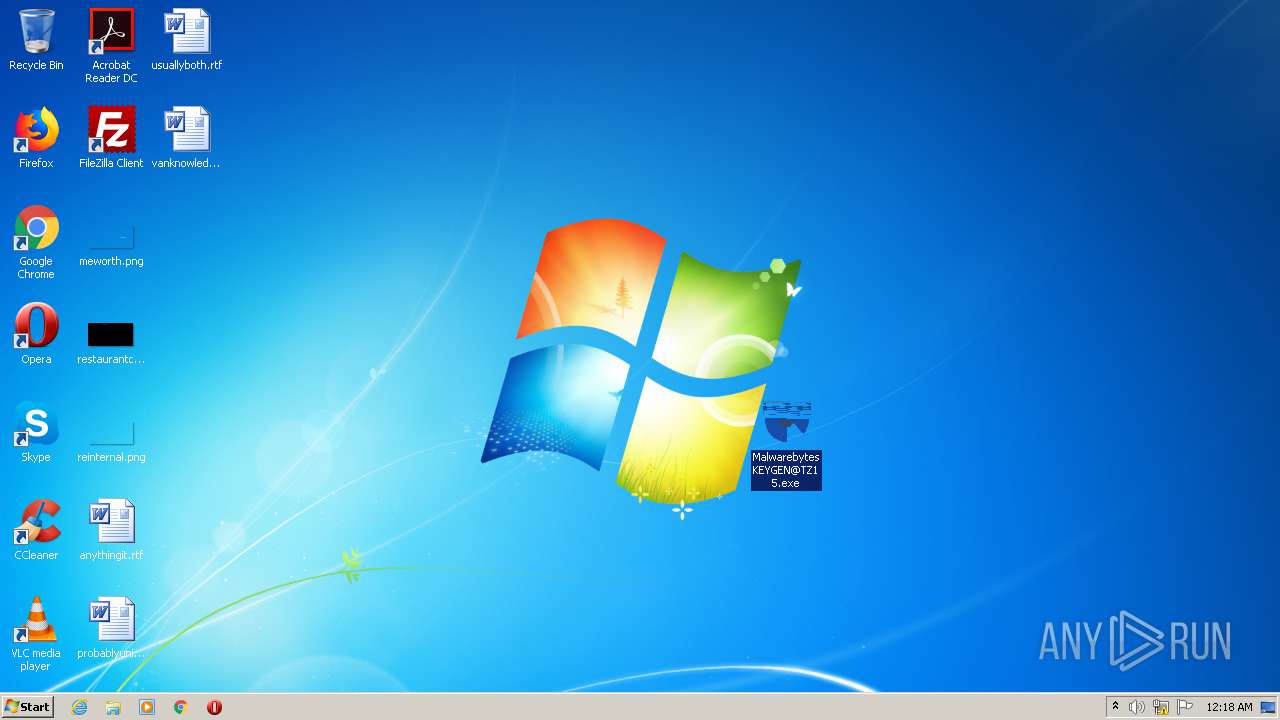
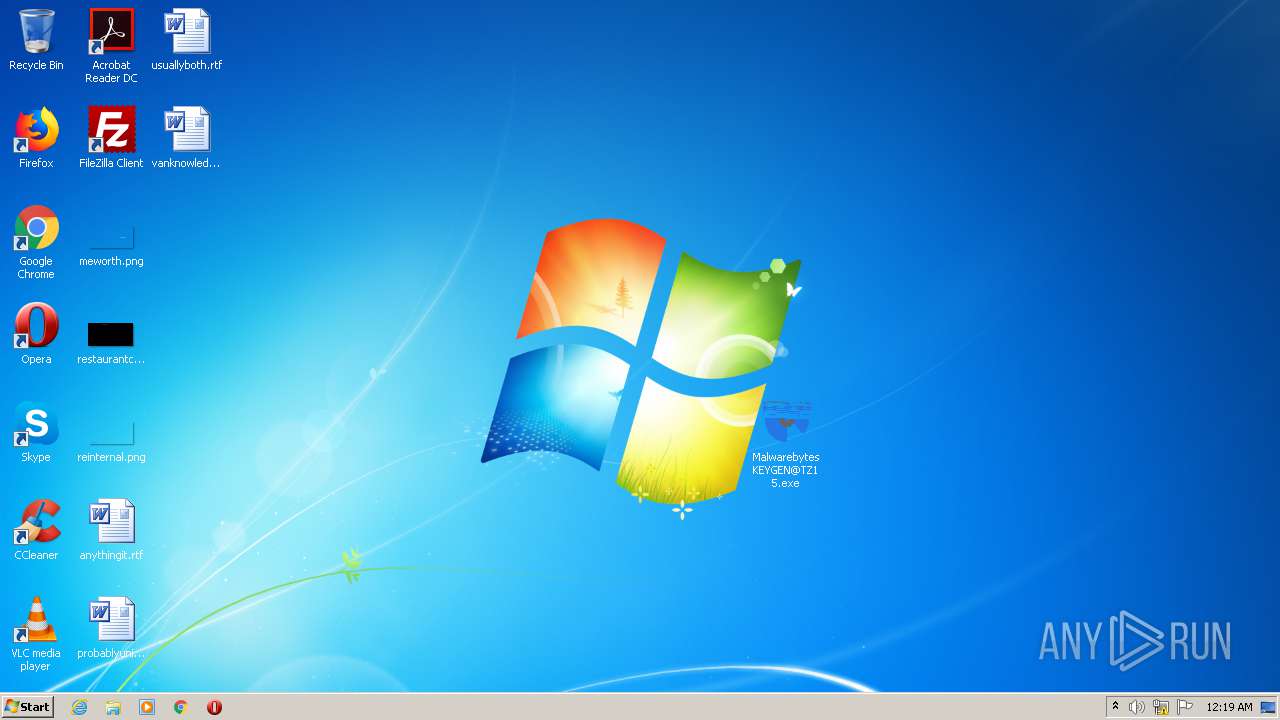
Manual execution by user
- MalwarebytesKEYGEN@TZ15.exe (PID: 1644)
- MalwarebytesKEYGEN@TZ15.exe (PID: 2680)
- MalwarebytesKEYGEN@TZ15.exe (PID: 556)
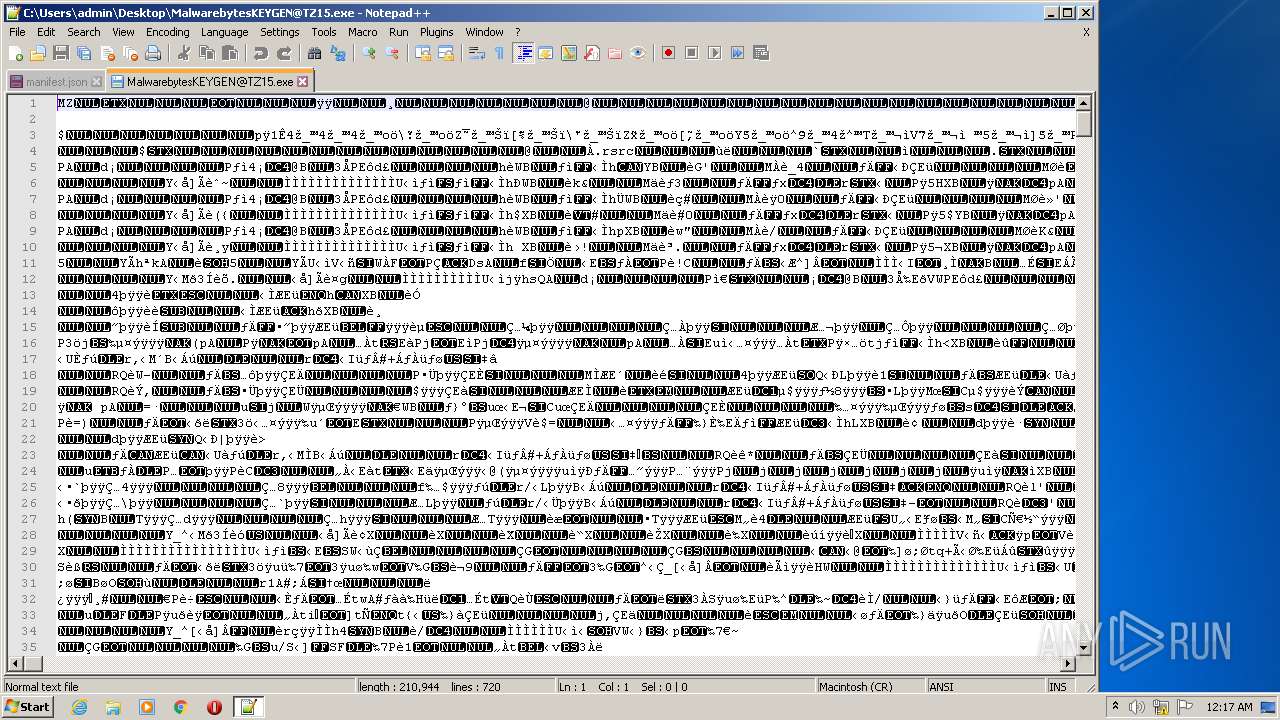
- notepad++.exe (PID: 1392)
- MalwarebytesKEYGEN@TZ15.exe (PID: 1800)
- MalwarebytesKEYGEN@TZ15.exe (PID: 584)
- MalwarebytesKEYGEN@TZ15.exe (PID: 2988)
- MalwarebytesKEYGEN@TZ15.exe (PID: 3596)
- MalwarebytesKEYGEN@TZ15.exe (PID: 3920)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:03:02 15:29:15+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.28 |
| CodeSize: | 89088 |
| InitializedDataSize: | 125440 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x68ca |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 02-Mar-2021 14:29:15 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 02-Mar-2021 14:29:15 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00015BBE | 0x00015C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.61443 |
.rdata | 0x00017000 | 0x0000C33A | 0x0000C400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.48671 |
.data | 0x00024000 | 0x00001AC4 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.41887 |
.rsrc | 0x00026000 | 0x0000EBF9 | 0x0000EC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.10618 |
.reloc | 0x00035000 | 0x00001D78 | 0x00001E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.57481 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.91161 | 381 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 0.0375109 | 2216 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 0.0600547 | 1384 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 2.62068 | 37019 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 2.4249 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 2.39143 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 1.36481 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
Imports
ADVAPI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
81
Monitored processes
16
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 556 | "C:\Users\admin\Desktop\MalwarebytesKEYGEN@TZ15.exe" | C:\Users\admin\Desktop\MalwarebytesKEYGEN@TZ15.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 584 | "C:\Users\admin\Desktop\MalwarebytesKEYGEN@TZ15.exe" | C:\Users\admin\Desktop\MalwarebytesKEYGEN@TZ15.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1392 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\admin\Desktop\MalwarebytesKEYGEN@TZ15.exe" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.51 Modules
| |||||||||||||||
| 1644 | "C:\Users\admin\Desktop\MalwarebytesKEYGEN@TZ15.exe" | C:\Users\admin\Desktop\MalwarebytesKEYGEN@TZ15.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1748 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1800 | "C:\Users\admin\Desktop\MalwarebytesKEYGEN@TZ15.exe" | C:\Users\admin\Desktop\MalwarebytesKEYGEN@TZ15.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2192 | "C:\Windows\system32\wermgr.exe" "-outproc" "3872" "568" | C:\Windows\system32\wermgr.exe | — | DllHost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2532 | "C:\Windows\system32\wermgr.exe" "-outproc" "2784" "568" | C:\Windows\system32\wermgr.exe | — | DllHost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
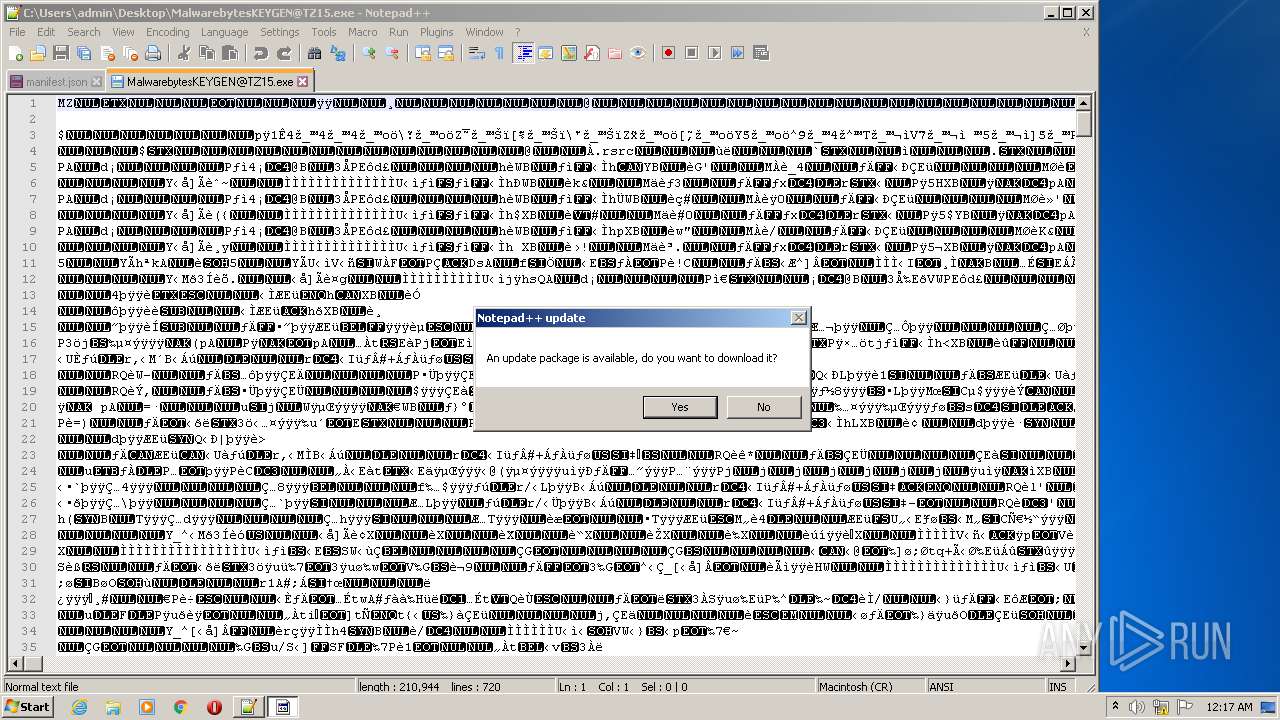
| 2604 | "C:\Program Files\Notepad++\updater\gup.exe" -v7.51 | C:\Program Files\Notepad++\updater\gup.exe | notepad++.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: GUP : a free (LGPL) Generic Updater Exit code: 0 Version: 4.1 Modules
| |||||||||||||||
| 2680 | "C:\Users\admin\Desktop\MalwarebytesKEYGEN@TZ15.exe" | C:\Users\admin\Desktop\MalwarebytesKEYGEN@TZ15.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
274
Read events
225
Write events
49
Delete events
0
Modification events
| (PID) Process: | (1392) notepad++.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1392) notepad++.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1392) notepad++.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1748) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: DllHost.exe | |||
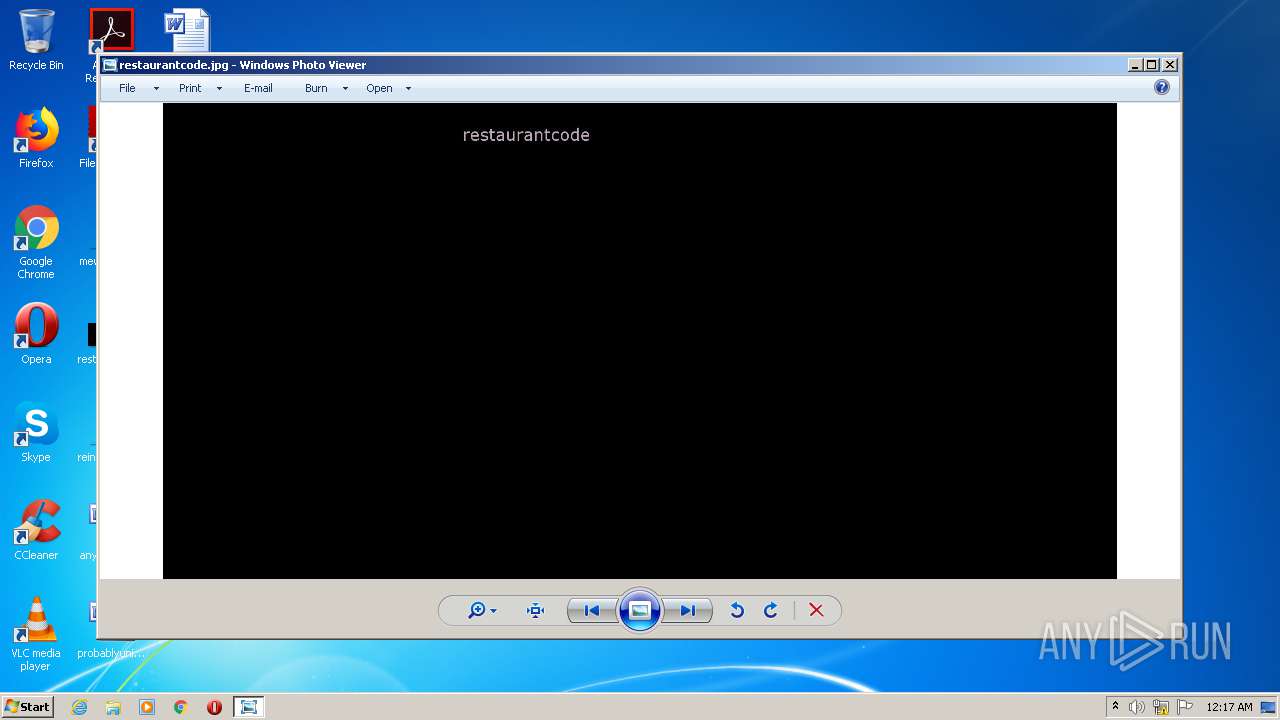
| (PID) Process: | (1748) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows Photo Viewer\Viewer |
| Operation: | write | Name: | MainWndPos |
Value: 6000000034000000A00400008002000000000000 | |||
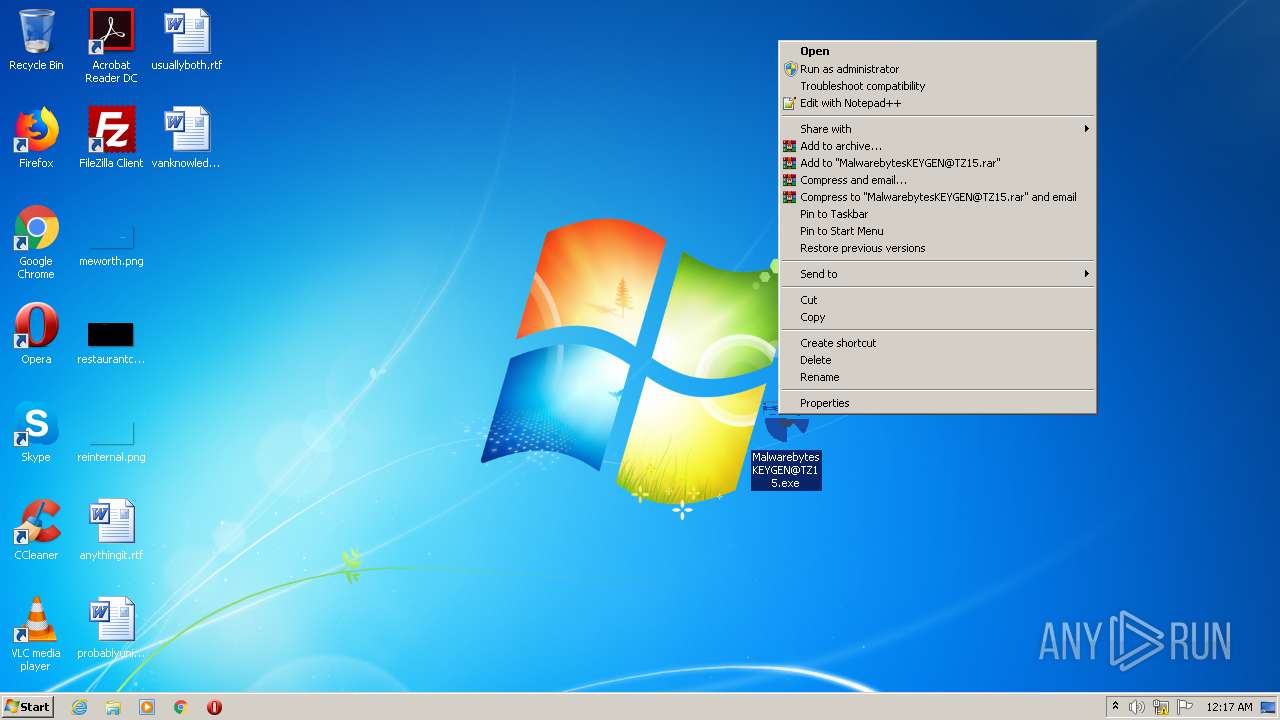
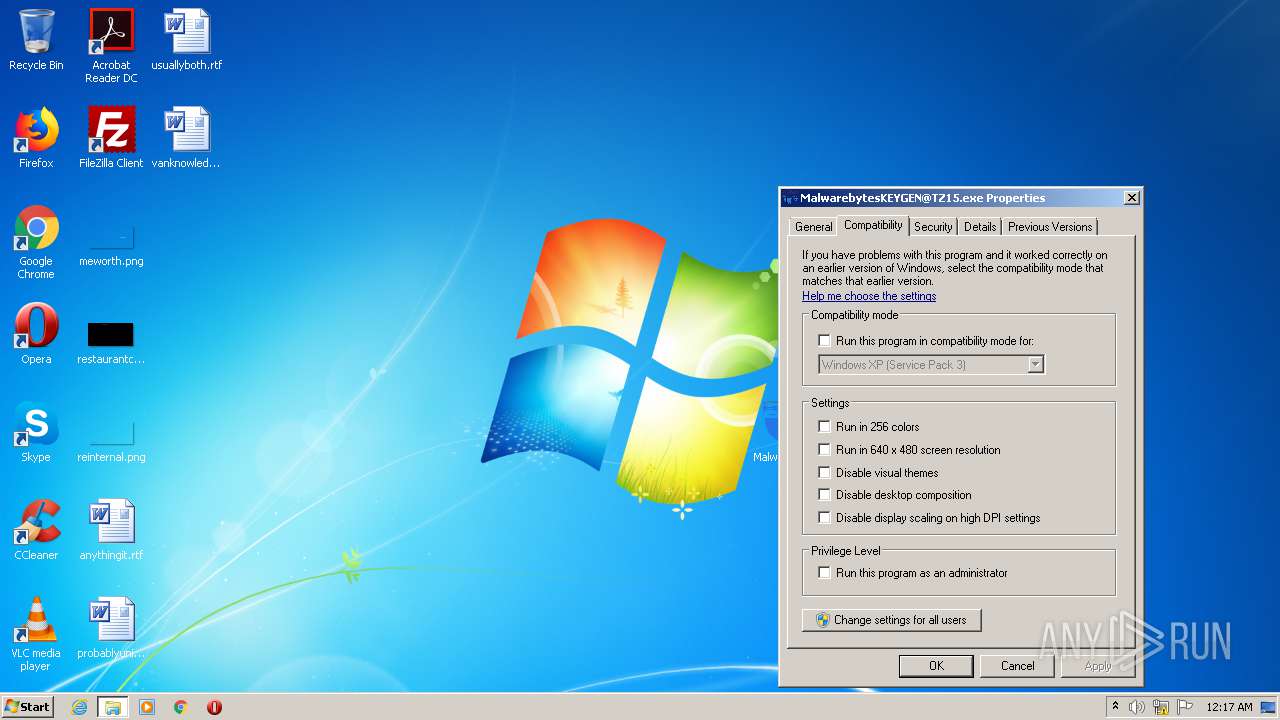
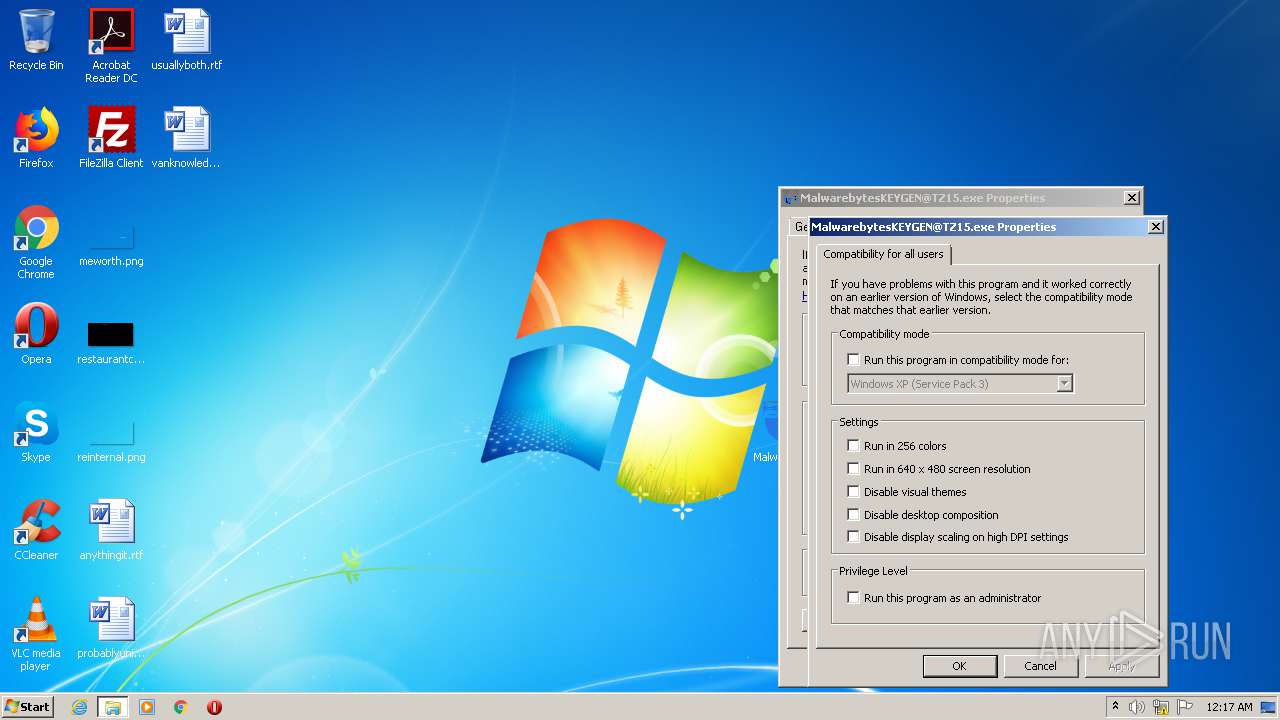
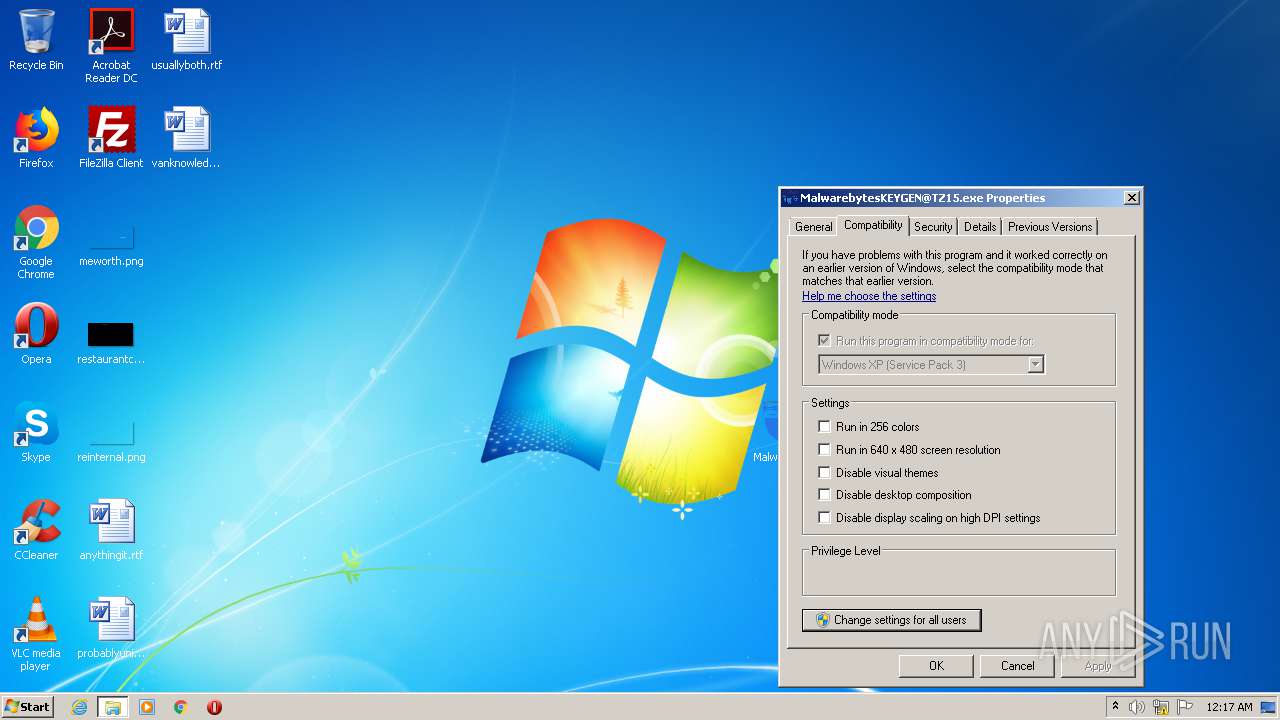
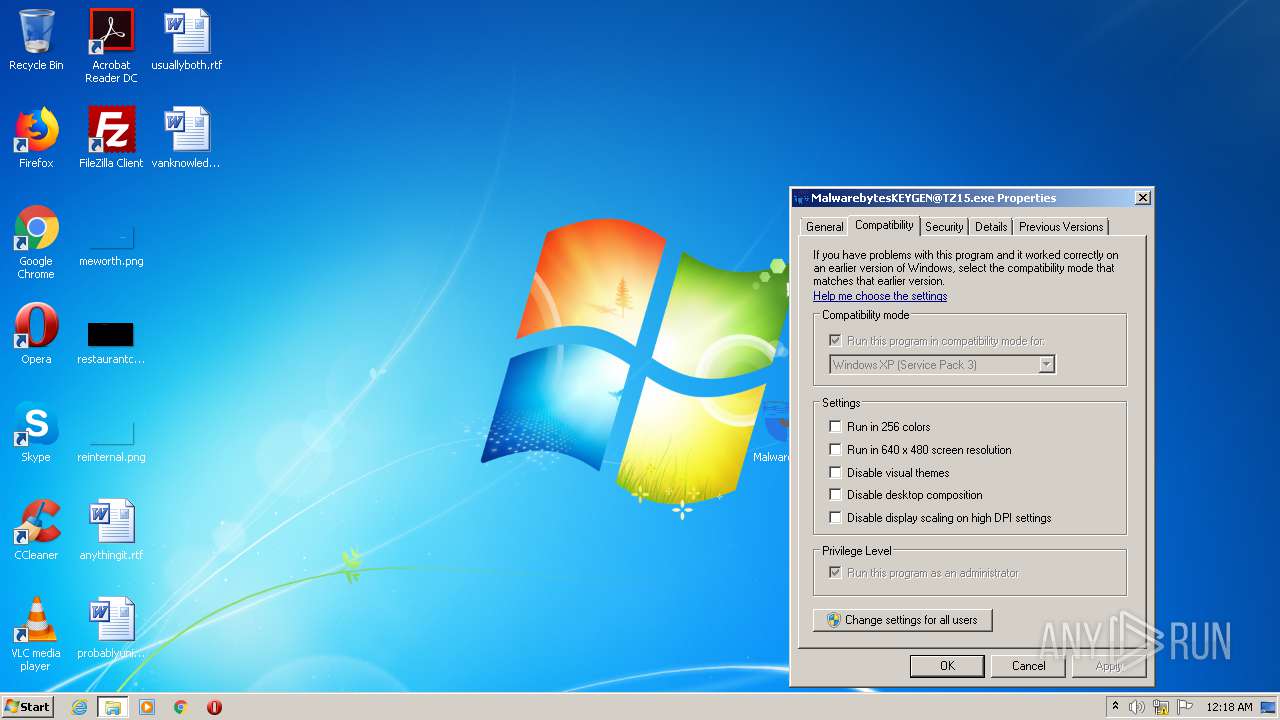
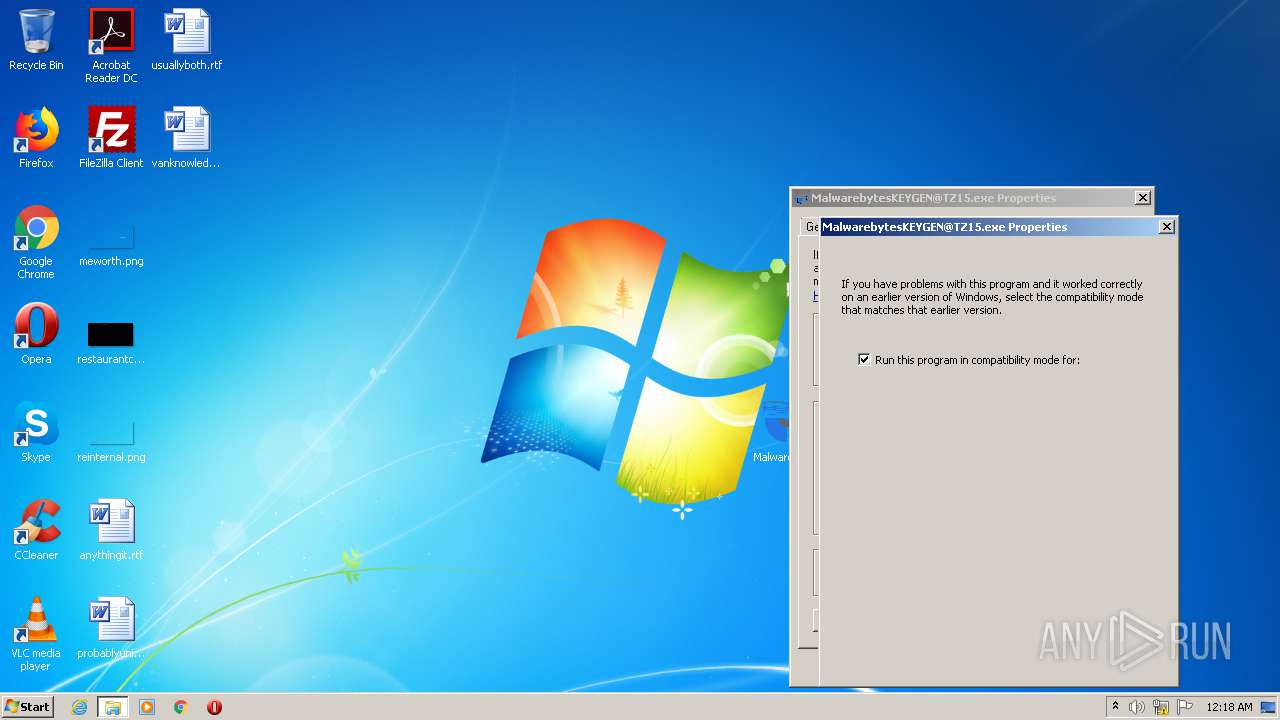
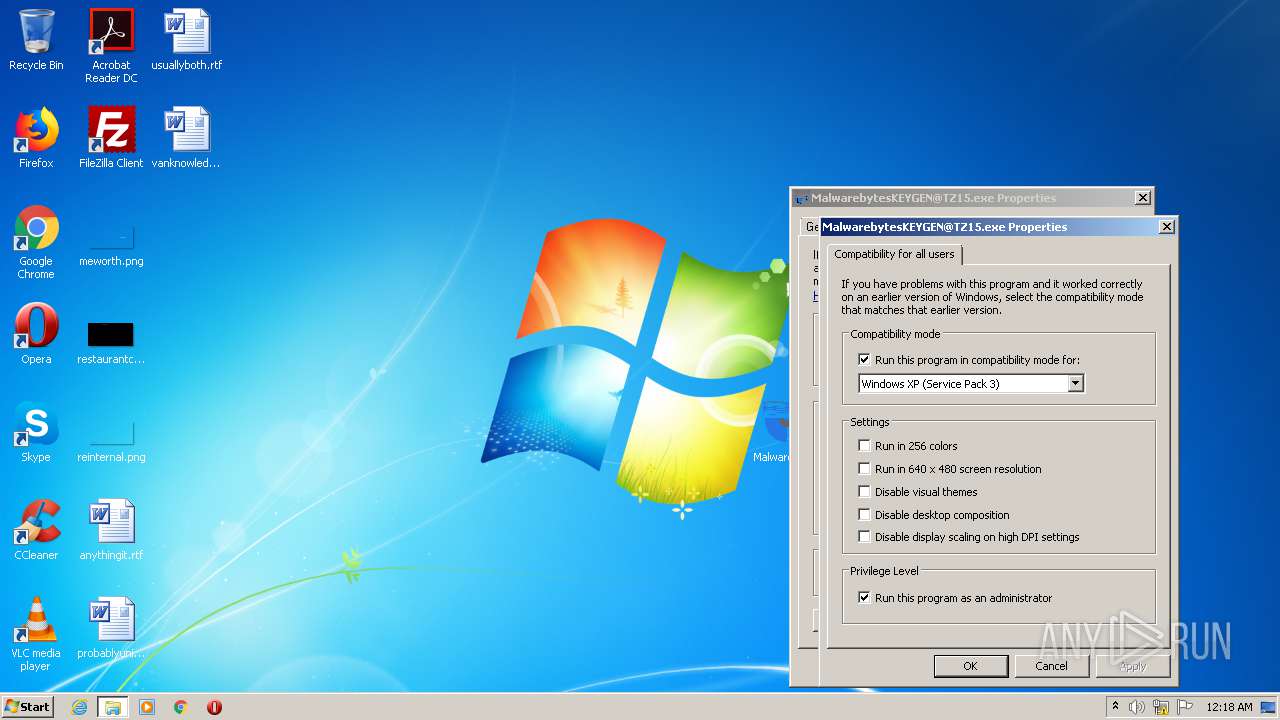
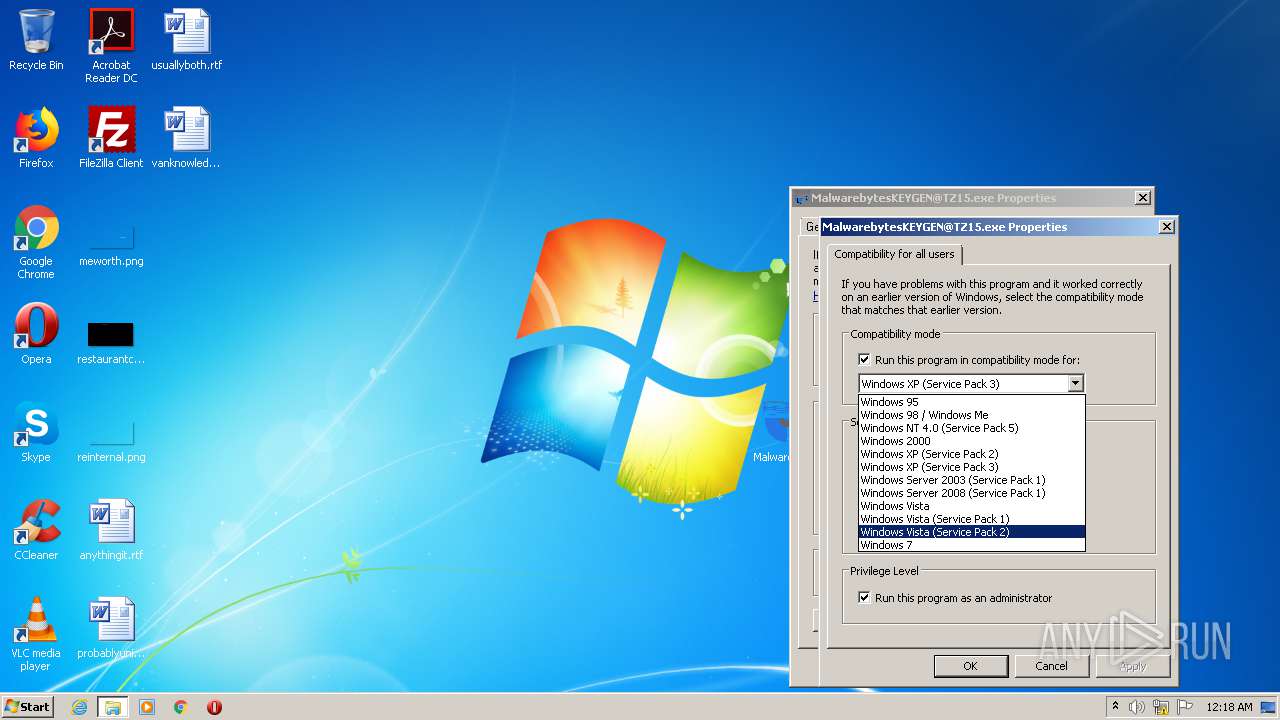
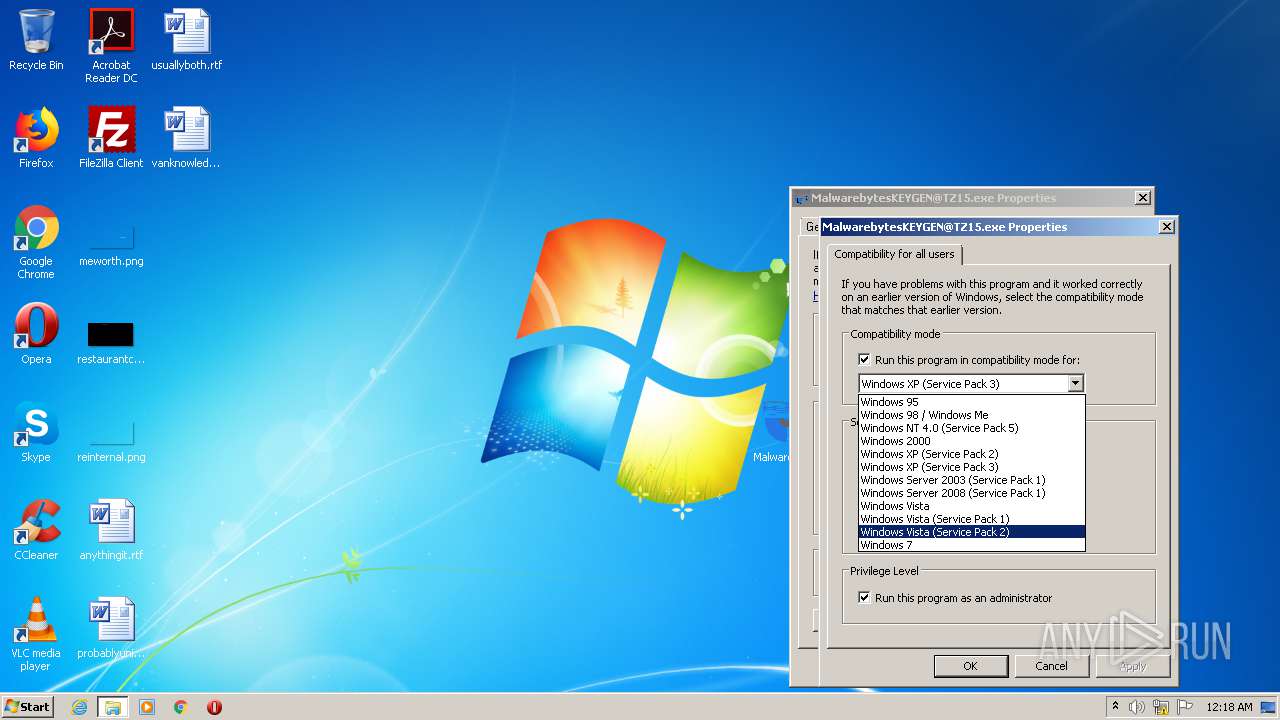
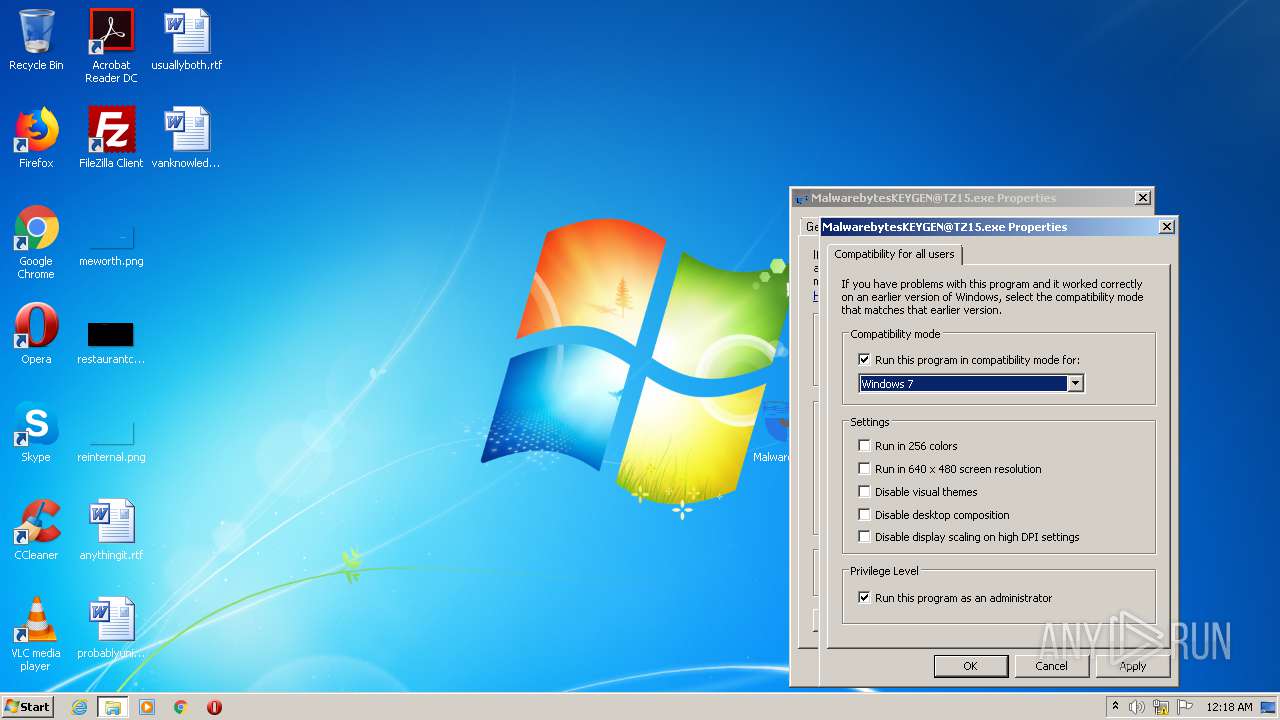
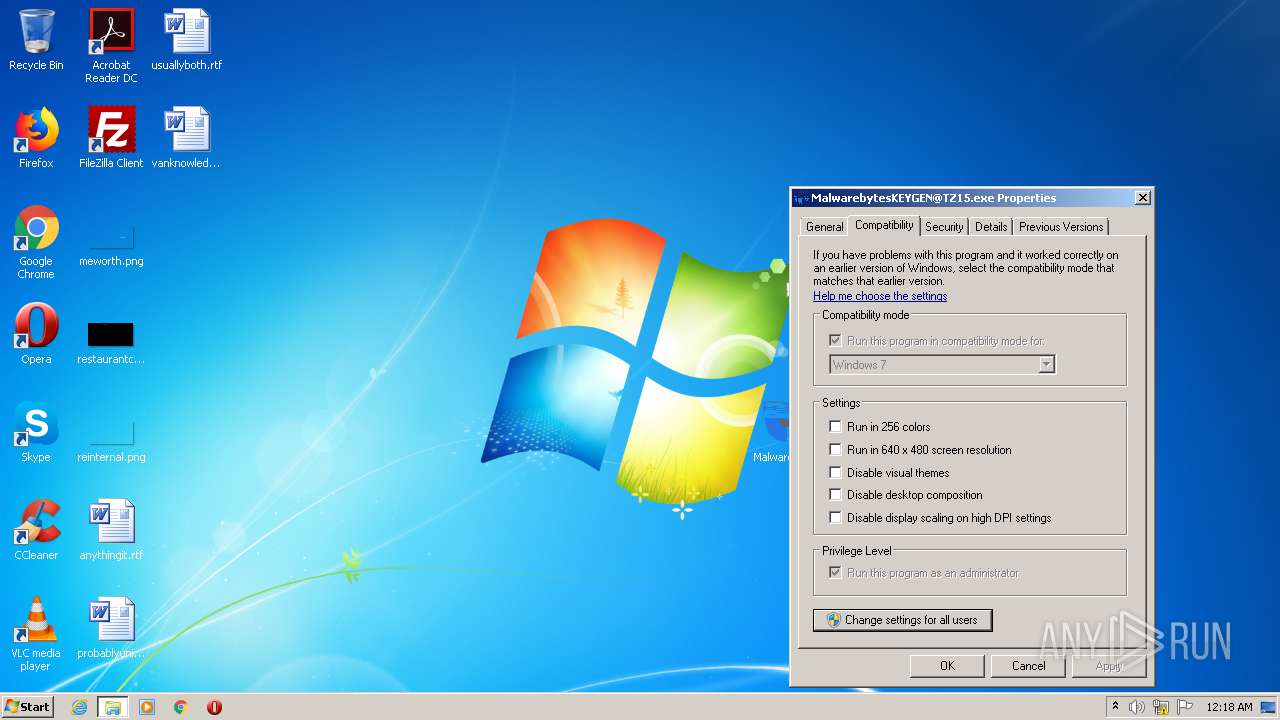
| (PID) Process: | (3872) DllHost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\AppCompatFlags\Layers |
| Operation: | write | Name: | C:\Users\admin\Desktop\MalwarebytesKEYGEN@TZ15.exe |
Value: WINXPSP3 | |||
| (PID) Process: | (3872) DllHost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\AppCompatFlags\Layers |
| Operation: | write | Name: | C:\Users\admin\Desktop\MalwarebytesKEYGEN@TZ15.exe |
Value: WINXPSP3 RUNASADMIN | |||
| (PID) Process: | (2784) DllHost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\AppCompatFlags\Layers |
| Operation: | write | Name: | C:\Users\admin\Desktop\MalwarebytesKEYGEN@TZ15.exe |
Value: WINXPSP3 RUNASADMIN | |||
| (PID) Process: | (2784) DllHost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\AppCompatFlags\Layers |
| Operation: | write | Name: | C:\Users\admin\Desktop\MalwarebytesKEYGEN@TZ15.exe |
Value: RUNASADMIN | |||
| (PID) Process: | (2784) DllHost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\AppCompatFlags\Layers |
| Operation: | write | Name: | C:\Users\admin\Desktop\MalwarebytesKEYGEN@TZ15.exe |
Value: RUNASADMIN WIN7RTM | |||
Executable files
0
Suspicious files
2
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3872 | DllHost.exe | C:\Users\admin\AppData\Local\Temp\Tab8997.tmp | — | |
MD5:— | SHA256:— | |||
| 3872 | DllHost.exe | C:\Users\admin\AppData\Local\Temp\{8920293f-0133-43d8-b538-02a652b5a1ef}\appcompat.txt | — | |
MD5:— | SHA256:— | |||
| 3872 | DllHost.exe | C:\Users\admin\AppData\Local\Temp\OutofProcReport1476246.txt | — | |
MD5:— | SHA256:— | |||
| 2784 | DllHost.exe | C:\Users\admin\AppData\Local\Temp\Tab8D4C.tmp | — | |
MD5:— | SHA256:— | |||
| 2784 | DllHost.exe | C:\Users\admin\AppData\Local\Temp\{806258f9-d9db-4cc0-9809-d5fb62215fa5}\appcompat.txt | — | |
MD5:— | SHA256:— | |||
| 2784 | DllHost.exe | C:\Users\admin\AppData\Local\Temp\OutofProcReport1542075.txt | — | |
MD5:— | SHA256:— | |||
| 1392 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\session.xml | text | |
MD5:— | SHA256:— | |||
| 1392 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\config.xml | xml | |
MD5:— | SHA256:— | |||
| 2192 | wermgr.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\NonCritical_MalwarebytesKEYG_31c94c44f15dba1ca953815b1e2cf7630e248e9_cab_08868a14\appcompat.txt | xml | |
MD5:— | SHA256:— | |||
| 2532 | wermgr.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\NonCritical_MalwarebytesKEYG_31c94c44f15dba1ca953815b1e2cf7630e248e9_09f38d9a\Report.wer | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQS14tALDViBvqCf47YkiQRtKz1BAQUpc436uuwdQ6UZ4i0RfrZJBCHlh8CEA7yTSbUNi7CXXtef0luXqk%3D | US | der | 279 b | whitelisted |
— | — | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2604 | gup.exe | 104.21.26.128:443 | notepad-plus-plus.org | Cloudflare Inc | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
notepad-plus-plus.org |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | 42C4C5846BB675C74E2B2C90C69AB44366401093
|
MalwarebytesKEYGEN@TZ15.exe | FTH: (1800): *** Fault tolerant heap shim applied to current process. This is usually due to previous crashes. ***
|
MalwarebytesKEYGEN@TZ15.exe | FTH: (584): *** Fault tolerant heap shim applied to current process. This is usually due to previous crashes. ***
|
MalwarebytesKEYGEN@TZ15.exe | FTH: (3920): *** Fault tolerant heap shim applied to current process. This is usually due to previous crashes. ***
|