| File name: | HDD Regenerator.exe |
| Full analysis: | https://app.any.run/tasks/82f62e5b-0daf-48e4-bf5e-2180a19507aa |
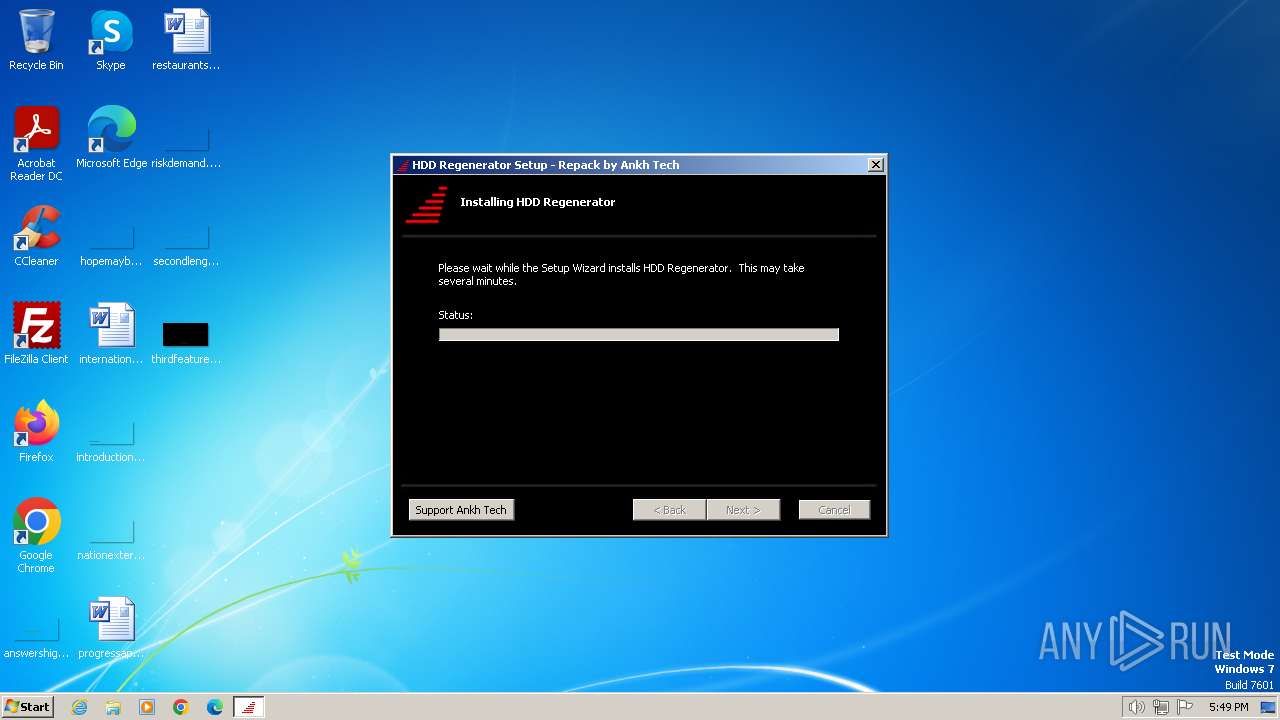
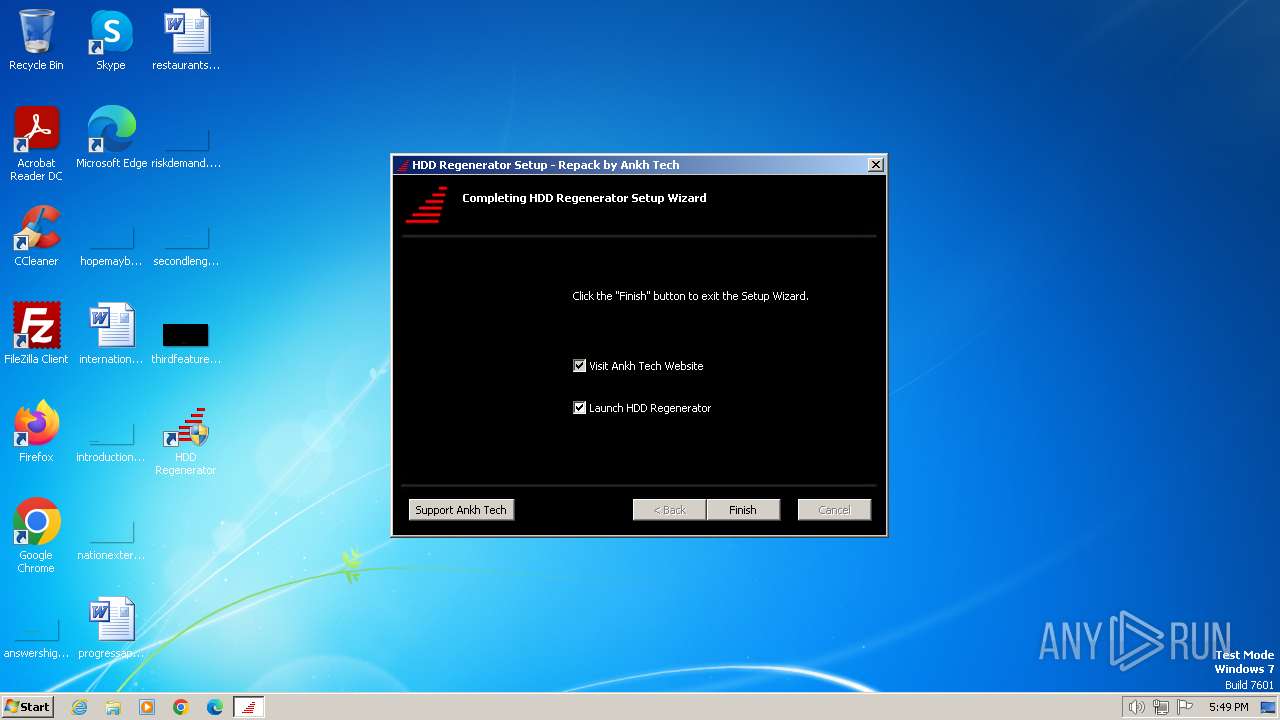
| Verdict: | Malicious activity |
| Analysis date: | January 31, 2024, 17:49:13 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 5FC95A642506890E43088F9B36CE571C |
| SHA1: | ECA84BEACC4A8B46BBC7018DC7C62DA721C8ACBD |
| SHA256: | 413C57748D5B1845BA7C6382608381A8CA5406CA74F40EA330F61E60C7E992E6 |
| SSDEEP: | 98304:/taUhlp4txNUz9M9ly2HPk9DWPnOoN6Myz5+Wsu0dfv9UXMBVSAq+rtHxKdDMrTG:IcsTGRo2bVxFv |
MALICIOUS
Drops the executable file immediately after the start
- HDD Regenerator.exe (PID: 1392)
SUSPICIOUS
Executable content was dropped or overwritten
- HDD Regenerator.exe (PID: 1392)
Reads the Windows owner or organization settings
- HDD Regenerator.exe (PID: 1392)
Reads Internet Explorer settings
- HDD Regenerator.exe (PID: 1392)
Reads the Internet Settings
- HDD Regenerator.exe (PID: 1392)
Application launched itself
- HDD Regenerator.exe (PID: 1392)
INFO
Reads the computer name
- wmpnscfg.exe (PID: 4084)
- HDD Regenerator.exe (PID: 1392)
- HDD Regenerator.exe (PID: 2824)
Checks supported languages
- HDD Regenerator.exe (PID: 1392)
- wmpnscfg.exe (PID: 4084)
- HDD Regenerator.exe (PID: 2824)
Create files in a temporary directory
- HDD Regenerator.exe (PID: 1392)
Reads Environment values
- HDD Regenerator.exe (PID: 1392)
Reads the machine GUID from the registry
- HDD Regenerator.exe (PID: 1392)
Creates files or folders in the user directory
- HDD Regenerator.exe (PID: 1392)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:12:20 12:17:56+01:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.38 |
| CodeSize: | 2710528 |
| InitializedDataSize: | 1114112 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x20b100 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.71.12.0 |
| ProductVersionNumber: | 1.71.12.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Debug |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Abstradome |
| FileDescription: | HDD Regenerator Installer |
| FileVersion: | 1.71.0012 |
| InternalName: | HDD Regenerator |
| LegalCopyright: | Copyright (C) 2024 Abstradome |
| OriginalFileName: | HDD Regenerator.exe |
| ProductName: | HDD Regenerator |
| ProductVersion: | 1.71.0012 |
Total processes
45
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1392 | "C:\Users\admin\AppData\Local\Temp\HDD Regenerator.exe" | C:\Users\admin\AppData\Local\Temp\HDD Regenerator.exe | explorer.exe | ||||||||||||
User: admin Company: Abstradome Integrity Level: MEDIUM Description: HDD Regenerator Installer Exit code: 0 Version: 1.71.0012 Modules
| |||||||||||||||
| 2764 | "C:\Windows\system32\msiexec.exe" /i "C:\Users\admin\AppData\Roaming\Abstradome\HDD Regenerator 1.71.0012\install\369B01C\Software.msi" AI_EUIMSI=1 APPDIR="C:\Program Files\HDD Regenerator" SHORTCUTDIR="C:\ProgramData\Microsoft\Windows\Start Menu\Programs\HDD Regenerator" SECONDSEQUENCE=1 CLIENTPROCESSID=1392 CHAINERUIPROCESSID=1392Chainer ACTION=INSTALL EXECUTEACTION=INSTALL CLIENTUILEVEL=0 ADDLOCAL=MainFeature,AI32BitFiles,AIOtherFiles PRIMARYFOLDER=APPDIR ROOTDRIVE=C:\ AI_SETUPEXEPATH="C:\Users\admin\AppData\Local\Temp\HDD Regenerator.exe" SETUPEXEDIR=C:\Users\admin\AppData\Local\Temp\ EXE_CMD_LINE="/exenoupdates /forcecleanup /wintime 1706721908 " TARGETDIR=C:\ AI_SETUPEXEPATH_ORIGINAL="C:\Users\admin\AppData\Local\Temp\HDD Regenerator.exe" AI_INSTALL=1 ARPSIZE=16156 AiProductCode={EE2DF8B2-7925-4266-A615-FF93E369B01C} FASTOEM=1 /qn | C:\Windows\System32\msiexec.exe | — | HDD Regenerator.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2824 | "C:\Users\admin\AppData\Local\Temp\HDD Regenerator.exe" /i "C:\Users\admin\AppData\Roaming\Abstradome\HDD Regenerator 1.71.0012\install\369B01C\Software.msi" AI_EUIMSI=1 APPDIR="C:\Program Files\HDD Regenerator" SHORTCUTDIR="C:\ProgramData\Microsoft\Windows\Start Menu\Programs\HDD Regenerator" SECONDSEQUENCE="1" CLIENTPROCESSID="1392" CHAINERUIPROCESSID="1392Chainer" ACTION="INSTALL" EXECUTEACTION="INSTALL" CLIENTUILEVEL="0" ADDLOCAL="MainFeature,AI32BitFiles,AIOtherFiles" PRIMARYFOLDER="APPDIR" ROOTDRIVE="C:\" AI_SETUPEXEPATH="C:\Users\admin\AppData\Local\Temp\HDD Regenerator.exe" SETUPEXEDIR="C:\Users\admin\AppData\Local\Temp\" EXE_CMD_LINE="/exenoupdates /forcecleanup /wintime 1706721908 " TARGETDIR="C:\" AI_SETUPEXEPATH_ORIGINAL="C:\Users\admin\AppData\Local\Temp\HDD Regenerator.exe" AI_INSTALL="1" ARPSIZE=16156 AiProductCode={EE2DF8B2-7925-4266-A615-FF93E369B01C} FASTOEM=1 /qn | C:\Users\admin\AppData\Local\Temp\HDD Regenerator.exe | HDD Regenerator.exe | ||||||||||||
User: admin Company: Abstradome Integrity Level: HIGH Description: HDD Regenerator Installer Exit code: 0 Version: 1.71.0012 Modules
| |||||||||||||||
| 4084 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
882
Read events
872
Write events
9
Delete events
1
Modification events
| (PID) Process: | (1392) HDD Regenerator.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1392) HDD Regenerator.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1392) HDD Regenerator.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1392) HDD Regenerator.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2764) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 115 | |||
| (PID) Process: | (1392) HDD Regenerator.exe | Key: | HKEY_CURRENT_USER\Software\AiTemp |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
16
Suspicious files
2
Text files
18
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1392 | HDD Regenerator.exe | C:\Users\admin\AppData\Roaming\Abstradome\HDD Regenerator 1.71.0012\install\holder0.aiph | — | |
MD5:— | SHA256:— | |||
| 1392 | HDD Regenerator.exe | C:\Users\admin\AppData\Roaming\Abstradome\HDD Regenerator 1.71.0012\install\369B01C\Software.x64.msi | executable | |
MD5:B9F0329BB970B4F60D78D75530A0B062 | SHA256:DBF742E2FE807F18F2A6F8E9DE3BDCADC9BBE5D5A03CAA3E0A6E1C1B124AA984 | |||
| 1392 | HDD Regenerator.exe | C:\Users\admin\AppData\Local\Temp\MSI3695.tmp | executable | |
MD5:B158D8D605571EA47A238DF5AB43DFAA | SHA256:CA763693CC25D316F14A9EBAD80EBF00590329550C45ADB7E5205486533C2504 | |||
| 1392 | HDD Regenerator.exe | C:\Users\admin\AppData\Local\Temp\MSI3714.tmp | executable | |
MD5:B158D8D605571EA47A238DF5AB43DFAA | SHA256:CA763693CC25D316F14A9EBAD80EBF00590329550C45ADB7E5205486533C2504 | |||
| 1392 | HDD Regenerator.exe | C:\Users\admin\AppData\Local\Temp\AI_EXTUI_BIN_1392\custicon | image | |
MD5:BE6D2F48AA6634FB2101C273C798D4D9 | SHA256:0E22BC2BF7184DFDB55223A11439304A453FB3574E3C9034A6497AF405C628EF | |||
| 1392 | HDD Regenerator.exe | C:\Users\admin\AppData\Local\Temp\AI_EXTUI_BIN_1392\dialog.jpg | image | |
MD5:8A372C8339A8FACC35088CE99A977D96 | SHA256:6A9F617AD2117B3756188FF46AE14E43981F0672904D68B9BA0B9C5AB3525ECF | |||
| 1392 | HDD Regenerator.exe | C:\Users\admin\AppData\Local\Temp\AI_EXTUI_BIN_1392\tabback | binary | |
MD5:4C3DDA35E23D44E273D82F7F4C38470A | SHA256:E728F79439E07DF1AFBCF03E8788FA0B8B08CF459DB31FC8568BC511BF799537 | |||
| 1392 | HDD Regenerator.exe | C:\Users\admin\AppData\Local\Temp\AI_EXTUI_BIN_1392\info | image | |
MD5:8595D2A2D58310B448729E28649443D6 | SHA256:27F13C4829994B214BB1A26EEF474DA67C521FD429536CB8421BA2F7C3E02B5F | |||
| 1392 | HDD Regenerator.exe | C:\Users\admin\AppData\Local\Temp\AI_EXTUI_BIN_1392\repairic | image | |
MD5:915E40A576FA41DC5F8486103341673E | SHA256:BF21B2BC3E7253968405F3D244CDB1C136672A5BDB088B524A333264898A2D11 | |||
| 1392 | HDD Regenerator.exe | C:\Users\admin\AppData\Local\Temp\AI_EXTUI_BIN_1392\Icon9.png | image | |
MD5:4EAD039BBB3AF7F9E6C50730FD15DC3C | SHA256:047EE71ED14AE8A6BA2ADABE751EBD881E36B565B6BC5941BDFA2ECCF462E3B8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
5
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |