| File name: | bluestacks.bin.exe |
| Full analysis: | https://app.any.run/tasks/359f6693-80e0-4f2b-8edc-9b88fc3f927e |
| Verdict: | Malicious activity |
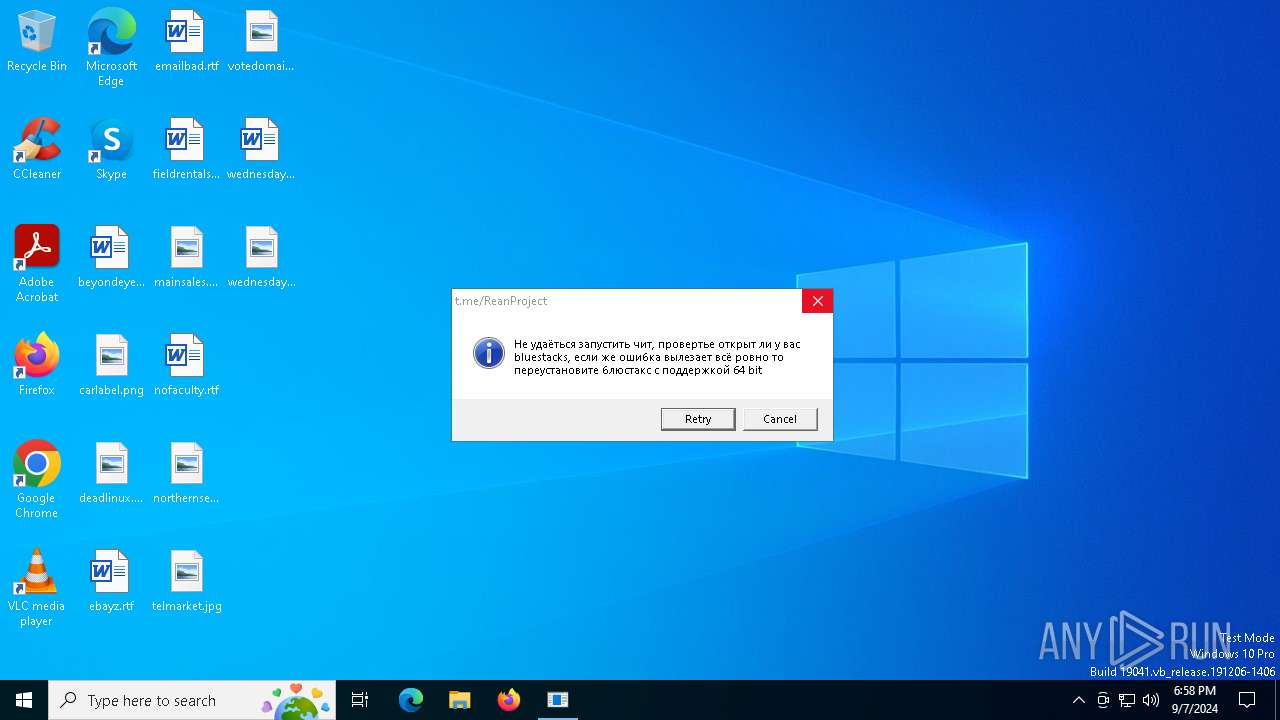
| Threats: | DCrat, also known as Dark Crystal RAT, is a remote access trojan (RAT), which was first introduced in 2018. It is a modular malware that can be customized to perform different tasks. For instance, it can steal passwords, crypto wallet information, hijack Telegram and Steam accounts, and more. Attackers may use a variety of methods to distribute DCrat, but phishing email campaigns are the most common. |
| Analysis date: | September 07, 2024, 18:58:06 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 305BF538C9235C44C6169712F007AFD0 |
| SHA1: | 68159D7EC467E42B9809134A08F7C061948CCFC9 |
| SHA256: | 410CC83DFDCC76655B8AA4A627464D87FB671F5845E041E81AF42FCB5858824F |
| SSDEEP: | 98304:Jyi3+R8UTRIscvHv2mGDapJR+ZE5OU5P2l6sQoiMLP6zb37irtcx53SOdTfT2HF5:/M |
MALICIOUS
DcRAT is detected
- Bluestacks.exe (PID: 5532)
- Bluestacks.exe (PID: 208)
- RuntimeBroker.exe (PID: 6952)
- RuntimeBroker.exe (PID: 9132)
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 3208)
Adds path to the Windows Defender exclusion list
- Bluestacks.exe (PID: 208)
DCRAT has been detected (YARA)
- RuntimeBroker.exe (PID: 6952)
SUSPICIOUS
The executable file from the user directory is run by the CMD process
- Bluestacks.exe (PID: 5532)
- Bluestacks.exe (PID: 208)
Runs shell command (SCRIPT)
- wscript.exe (PID: 3208)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 3208)
- Bluestacks.exe (PID: 5532)
- RuntimeBroker.exe (PID: 6952)
- Bluestacks.exe (PID: 208)
Reads security settings of Internet Explorer
- Bluestacks.exe (PID: 5532)
- bluestacks.bin.exe (PID: 2456)
- Bluestacks.exe (PID: 208)
- RuntimeBroker.exe (PID: 6952)
Executable content was dropped or overwritten
- Bluestacks.exe (PID: 5532)
- Bluestacks.exe (PID: 208)
- RuntimeBroker.exe (PID: 6952)
- RuntimeBroker.exe (PID: 9132)
Reads the date of Windows installation
- Bluestacks.exe (PID: 5532)
- Bluestacks.exe (PID: 208)
- RuntimeBroker.exe (PID: 6952)
Executed via WMI
- schtasks.exe (PID: 6248)
- schtasks.exe (PID: 6020)
- schtasks.exe (PID: 368)
- schtasks.exe (PID: 2096)
- schtasks.exe (PID: 5888)
- schtasks.exe (PID: 1840)
- schtasks.exe (PID: 2368)
- schtasks.exe (PID: 2684)
- schtasks.exe (PID: 7160)
- schtasks.exe (PID: 876)
- schtasks.exe (PID: 1556)
- schtasks.exe (PID: 3972)
- schtasks.exe (PID: 3112)
- schtasks.exe (PID: 4068)
- schtasks.exe (PID: 6892)
- schtasks.exe (PID: 5104)
- schtasks.exe (PID: 6204)
- schtasks.exe (PID: 6828)
The process creates files with name similar to system file names
- Bluestacks.exe (PID: 208)
Executing commands from a ".bat" file
- wscript.exe (PID: 3208)
- Bluestacks.exe (PID: 208)
- RuntimeBroker.exe (PID: 6952)
Script adds exclusion path to Windows Defender
- Bluestacks.exe (PID: 208)
Starts POWERSHELL.EXE for commands execution
- Bluestacks.exe (PID: 208)
Starts application with an unusual extension
- cmd.exe (PID: 7668)
- cmd.exe (PID: 6236)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 7668)
Probably delay the execution using 'w32tm.exe'
- cmd.exe (PID: 6236)
INFO
Checks supported languages
- bluestacks.bin.exe (PID: 2456)
- Bluestacks.exe (PID: 5532)
- Bluestacks.exe (PID: 208)
- chcp.com (PID: 8020)
- RuntimeBroker.exe (PID: 6952)
- chcp.com (PID: 7824)
- RuntimeBroker.exe (PID: 9132)
Reads the computer name
- bluestacks.bin.exe (PID: 2456)
- Bluestacks.exe (PID: 5532)
- Bluestacks.exe (PID: 208)
- RuntimeBroker.exe (PID: 9132)
- RuntimeBroker.exe (PID: 6952)
The process uses the downloaded file
- bluestacks.bin.exe (PID: 2456)
- wscript.exe (PID: 3208)
- Bluestacks.exe (PID: 5532)
- Bluestacks.exe (PID: 208)
- RuntimeBroker.exe (PID: 6952)
Process checks computer location settings
- bluestacks.bin.exe (PID: 2456)
- Bluestacks.exe (PID: 5532)
- Bluestacks.exe (PID: 208)
- RuntimeBroker.exe (PID: 6952)
Reads Environment values
- Bluestacks.exe (PID: 5532)
- Bluestacks.exe (PID: 208)
- RuntimeBroker.exe (PID: 6952)
- RuntimeBroker.exe (PID: 9132)
Reads the machine GUID from the registry
- Bluestacks.exe (PID: 5532)
- Bluestacks.exe (PID: 208)
- RuntimeBroker.exe (PID: 6952)
- RuntimeBroker.exe (PID: 9132)
Create files in a temporary directory
- Bluestacks.exe (PID: 208)
- bluestacks.bin.exe (PID: 2456)
- RuntimeBroker.exe (PID: 6952)
Creates files in the program directory
- Bluestacks.exe (PID: 208)
Changes the display of characters in the console
- cmd.exe (PID: 7668)
- cmd.exe (PID: 6236)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7040)
- powershell.exe (PID: 6844)
- powershell.exe (PID: 6168)
- powershell.exe (PID: 5692)
- powershell.exe (PID: 304)
- powershell.exe (PID: 8)
- powershell.exe (PID: 5000)
- powershell.exe (PID: 5708)
- powershell.exe (PID: 6172)
- powershell.exe (PID: 4008)
- powershell.exe (PID: 4284)
- powershell.exe (PID: 4880)
- powershell.exe (PID: 6832)
- powershell.exe (PID: 6784)
- powershell.exe (PID: 6416)
- powershell.exe (PID: 6836)
- powershell.exe (PID: 6932)
- powershell.exe (PID: 4920)
- powershell.exe (PID: 6808)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6416)
- powershell.exe (PID: 5692)
- powershell.exe (PID: 4880)
- powershell.exe (PID: 6836)
- powershell.exe (PID: 6932)
- powershell.exe (PID: 7040)
- powershell.exe (PID: 6172)
- powershell.exe (PID: 6784)
- powershell.exe (PID: 304)
- powershell.exe (PID: 5708)
- powershell.exe (PID: 4284)
- powershell.exe (PID: 4008)
- powershell.exe (PID: 6844)
- powershell.exe (PID: 4920)
- powershell.exe (PID: 5000)
- powershell.exe (PID: 8)
- powershell.exe (PID: 6168)
- powershell.exe (PID: 6808)
- powershell.exe (PID: 6832)
Disables trace logs
- RuntimeBroker.exe (PID: 6952)
- RuntimeBroker.exe (PID: 9132)
Checks proxy server information
- RuntimeBroker.exe (PID: 6952)
- RuntimeBroker.exe (PID: 9132)
.NET Reactor protector has been detected
- RuntimeBroker.exe (PID: 6952)
Found Base64 encoded reference to WMI classes (YARA)
- RuntimeBroker.exe (PID: 6952)
Found Base64 encoded access to Windows Defender via PowerShell (YARA)
- RuntimeBroker.exe (PID: 6952)
Found Base64 encoded reference to AntiVirus WMI classes (YARA)
- RuntimeBroker.exe (PID: 6952)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
DcRat
(PID) Process(6952) RuntimeBroker.exe
C2 (1)http://847702cm.nyashtech.top/PythonauthProtectUploads
C2 (1)http://847702cm.nyashtech.top/PythonauthProtectUploads
Options
Plugins (2)TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAgAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAABQRQAATAEDAAKX/2QAAAAAAAAAAOAAIiALAQgAAEYBAAAGAAAAAAAA7mUBAAAgAAAAgAEAAABAAAAgAAAAAgAABAAAAAAAAAAEAAAAAAAAAADAAQAAAgAAm0ACAAMAQIUA...
TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAgAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAABQRQAATAEDALI7+mQAAAAAAAAAAOAAIiALAQgAAAgBAAAGAAAAAAAAricBAAAgAAAAQAEAAABAAAAgAAAAAgAABAAAAAAAAAAEAAAAAAAAAACAAQAAAgAArNABAAMAQIUA...
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2022:03:03 13:15:57+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.3 |
| CodeSize: | 203776 |
| InitializedDataSize: | 91136 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1f530 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
206
Monitored processes
77
Malicious processes
9
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 8 | "powershell" -Command Add-MpPreference -ExclusionPath 'C:/ProgramData/' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Bluestacks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 208 | C:\Users\admin\AppData\Local\Temp\chrome_BITS_1968_19427403443\Bluestacks.exe | C:\Users\admin\AppData\Local\Temp\chrome_BITS_1968_19427403443\Bluestacks.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.2.7.1277 Modules
| |||||||||||||||
| 304 | "powershell" -Command Add-MpPreference -ExclusionPath 'C:\Recovery\OEM\UserOOBEBroker.exe' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Bluestacks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 368 | schtasks.exe /create /tn "RUXIMICSR" /sc MINUTE /mo 7 /tr "'C:\Windows\ModemLogs\RUXIMICS.exe'" /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 780 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 876 | schtasks.exe /create /tn "services" /sc ONLOGON /tr "'C:\Program Files\rempl\Logs\services.exe'" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1224 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1432 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1556 | schtasks.exe /create /tn "uhssvc" /sc ONLOGON /tr "'C:\Program Files (x86)\Common Files\uhssvc.exe'" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1840 | schtasks.exe /create /tn "RUXIMICSR" /sc MINUTE /mo 13 /tr "'C:\Windows\ModemLogs\RUXIMICS.exe'" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
110 572
Read events
110 565
Write events
7
Delete events
0
Modification events
| (PID) Process: | (2456) bluestacks.bin.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.vbe\OpenWithProgids |
| Operation: | write | Name: | VBEFile |
Value: | |||
| (PID) Process: | (208) Bluestacks.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\43628757a6b1b8987d0b1133d9f0d31a1f7bfb58 |
| Operation: | write | Name: | 9771d559b82c661383a2e075b6ff21285c9f8417 |
Value: H4sIAAAAAAAEAHWOWwuCQBCF/0r4VBDRRezylmYgJEYXCpqIZR1q0XVkV63+fduNguhl4DDfOXw7yxsBLJBTheoKMKOjNrnMCiHRVZSgauEFreaD24gsprMBQopRvtj1NggDb/mFzRUdFZO1qUjREAplnr6nNapKcNT/8Fr9MnAaAB5JSdl7ojxpXfGvzsc48kOAtZmNItf/Mb4/TJ/FUmQA4zyfsILdXTgzSitjBsBPiiQe3GC1PHSGzsAcu9u32z3b7gG4aYm6YDx5Ku9vLcDPeTIBAAA= | |||
| (PID) Process: | (208) Bluestacks.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\WINDOWS\System32\cmd.exe.FriendlyAppName |
Value: Windows Command Processor | |||
| (PID) Process: | (208) Bluestacks.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\WINDOWS\System32\cmd.exe.ApplicationCompany |
Value: Microsoft Corporation | |||
| (PID) Process: | (6952) RuntimeBroker.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\cYDXXYOcIYUpChxSFwUyRPlYCzHLMAcN |
| Operation: | write | Name: | cYDXXYOcIYUpChxSFwUyRPlYCzHLMAcN |
Value: cYDXXYOcIYUpChxSFwUyRPlYCzHLMAcN | |||
| (PID) Process: | (9132) RuntimeBroker.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\cYDXXYOcIYUpChxSFwUyRPlYCzHLMAcN |
| Operation: | write | Name: | cYDXXYOcIYUpChxSFwUyRPlYCzHLMAcN |
Value: cYDXXYOcIYUpChxSFwUyRPlYCzHLMAcN | |||
Executable files
28
Suspicious files
2
Text files
49
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2456 | bluestacks.bin.exe | C:\Users\admin\AppData\Local\Temp\chrome_BITS_1968_19427403443\Bluestacks.exe | — | |
MD5:— | SHA256:— | |||
| 208 | Bluestacks.exe | C:\Recovery\OEM\UserOOBEBroker.exe | — | |
MD5:— | SHA256:— | |||
| 208 | Bluestacks.exe | C:\Program Files (x86)\Common Files\uhssvc.exe | — | |
MD5:— | SHA256:— | |||
| 208 | Bluestacks.exe | C:\Program Files\rempl\Logs\services.exe | — | |
MD5:— | SHA256:— | |||
| 208 | Bluestacks.exe | C:\Windows\ModemLogs\RUXIMICS.exe | — | |
MD5:— | SHA256:— | |||
| 5532 | Bluestacks.exe | C:\Users\admin\Desktop\mcbCmKca.log | executable | |
MD5:E9CE850DB4350471A62CC24ACB83E859 | SHA256:7C95D3B38114E7E4126CB63AADAF80085ED5461AB0868D2365DD6A18C946EA3A | |||
| 208 | Bluestacks.exe | C:\Recovery\Logs\RuntimeBroker.exe | — | |
MD5:— | SHA256:— | |||
| 208 | Bluestacks.exe | C:\Users\admin\Desktop\BMvrjEFt.log | executable | |
MD5:E9CE850DB4350471A62CC24ACB83E859 | SHA256:7C95D3B38114E7E4126CB63AADAF80085ED5461AB0868D2365DD6A18C946EA3A | |||
| 208 | Bluestacks.exe | C:\Users\admin\Desktop\qYQBztKL.log | executable | |
MD5:1DCDE09C6A8CE8F5179FB24D0C5A740D | SHA256:1F02230A8536ADB1D6F8DADFD7CA8CA66B5528EC98B15693E3E2F118A29D49D8 | |||
| 2456 | bluestacks.bin.exe | C:\Users\admin\AppData\Local\Temp\chrome_BITS_1968_19427403443\xVJr4auV1S4a.vbe | vbe | |
MD5:AE77D63897A20B813BF90A3E654790D6 | SHA256:69FFFD0EE7EFE8361165E3700C0CB77C10D177BF6B873BE421A2E8A38FEC63AB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
27
DNS requests
16
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7072 | svchost.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2028 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8656 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8656 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7072 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6420 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7072 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7072 | svchost.exe | 23.52.120.96:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3260 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2028 | svchost.exe | 40.126.32.136:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
847702cm.nyashtech.top |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2256 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |